| URL: | http://www.3amer.com/r/rw/cpal-trk1.html |
| Full analysis: | https://app.any.run/tasks/c97ba6b2-3f9d-4efc-b1d7-6ecb77ed758e |
| Verdict: | Malicious activity |
| Analysis date: | May 14, 2019, 22:19:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BDDC70FF1BA9EEA6D82F601EE900BCBD |
| SHA1: | 02232C570EB645FFF9AC2BCC2DF17CFC0FCD68C7 |
| SHA256: | 73EB8179476D90118498882DC7DB1F8EE94E9625AFD8C5BEC1AF4CAEA479AF6C |
| SSDEEP: | 3:N1KJS4D1QXSKCgseUwJ:Cc42X4gsep |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2688)
INFO
Application launched itself
- chrome.exe (PID: 2688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
57
Monitored processes
26
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11769700010783752453 --mojo-platform-channel-handle=4552 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=964,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16053236461502174932 --mojo-platform-channel-handle=2152 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1705664782249945159 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1705664782249945159 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3924 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=8457111103276497914 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8457111103276497914 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2340 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=964,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=66203899630775436 --mojo-platform-channel-handle=956 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4089893385037970839 --mojo-platform-channel-handle=4232 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=9111015412320501200 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9111015412320501200 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3880 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7661632991599699635 --mojo-platform-channel-handle=2540 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --service-pipe-token=6540198023234917099 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6540198023234917099 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1988 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4372794782019156715 --mojo-platform-channel-handle=4104 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
553
Read events
460
Write events
88
Delete events
5
Modification events
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2688-13202345974969000 |
Value: 259 | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
23
Text files
127
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f83d95c4-d131-4416-aa73-a5e425c33f4d.tmp | — | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
32
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2688 | chrome.exe | GET | 302 | 108.168.193.189:80 | http://p244728.mybestmv.com/adServe/domainClick?ai=d7384lOUKAX-7rmy4Wy1XFpXO9_3fNiPHxec1ZuWC5UlhtVVymQvsQK8sczUyG_FAz4mvdD0n7T5PQC-Ns7H0UP4ihGJaOYX5Yl0uCS11v4GvLcNuFljMPmHDyN51WZbdDJ15Fw0SSXt4prhaFuJLrAIyiLGumliT46l2T_EIzIPAe_L4WAxra5h9fysnwvKLJgJ-sR7xF8nLjLGxshgkyZggkaL9NJRZN_F-zUlvRWh8HfcFb6b2kMb4Do7y-b-De0rL-F5kinpl0elefIU4TScjdjF1tJCaygrY9BHdw_UdqdcHeTAytQNy0EHlsrgDOnEXZ7OoQmRFmgORM3pNC4OL1mnImvE_T1XpkVx2uomDW_olsHQNA&ui=Jd06nSairX2jwX67LqRlH4BVNmK1S2tVrCb4pJFOznbCWE5rDEAavZcro8i54XU2zZiDBVcKpaRS8NyO8ZAQWIJBYT3lXDa1K_K8zHAG9b4glQUMy1Tj-g&si=1&oref=c86f1896dfbf4619f9bf66a4c40c2b86&rb=z0w6EDa1zVE&rr=0 | US | — | — | suspicious |
2688 | chrome.exe | GET | 302 | 108.168.193.189:80 | http://mybestmv.com/aS/feedclick?s=Jd06nSairX3kqDRj3GHvnQ4YJXHNR5cxGCJeMqQw6rlSdX3UqwssAZ1B-kb1vwChg2RvEwrk2epbC7U30TJp2cV8yPnUQt6JFCBqXiRpw321w0gE8W7ufvb5np8cxJs0YFos_XX7JtPGVWViaJip_jpMtngPby6qLlHjd5as0z_EbeHdzHoDnpjbEP0km3OO_ycDzs3tCXO2Bisa9w-BTfgJdMI9MIl3WmrpvFzLJV6XGM5iDsIBC6nN_-sdQB9hOI7XEfZpPdmI2qC6bGs4GyUq9Gis7Nkbr7cHyKZNW949YebE6vxavg5r6hmu_DuJh0DzehqzIGTwOtfr-a-uQHUM7GKSZBtvFI50xF3qQmzPXTzkpQlwKEHj4swi49hiMG1QSlT61FPGdlHpd-LTguPX8aeCC-ocKdoA_yBa58Jxk3jy4yUhdmRBnVRMhBaw3ckXYVC7yKez_JFwZGHQ-n6hR5Zyphun2jXKNNEAJ_9LwRZUAtuNwqCcqy1G7eeHNduwD4c18rwpBPi9xdihwc5C-9l2BDP7pTg8Dc9XrugbZfOc-1ZteDYG-4FG-49xyrU5V2t-hhxmgZcr5HJPy3mQY5Lx0uDvkRq8NUuoTyU4-ba0q0l_sFYUEQ_4JLksyjTCEZTxshopqryBmkAYegx0XMgztEgVV5_K81As_FzEbkjl-FaHmYsJw6UwnnC_rcX6-L9EgAdeqSoaoMFCIiD2KAsrbpetM6gVYBHkEUVZSG7TpOUX12f1GpIkdXZ7rcK1HL_R7zImGkRvMOKu3POyVoLfsdCWWvJGJECZ6LQnzg0qHrsHwpyHE9f3pvV3JA-1dwlN5xAdicX-4YoiF1HJkbVj8YtJzOFgqu3bUHOzhWZdGGGg5WLhJzmK5tEBHw8pSU9atgdHQJpsyxV7m4MRXfqc9uZLa4fRBFckWAPJmtu8aic405KxGFdFdS3aaKcnnOVCa1gtVodyh16Nu-Zngk2rC-1_E2NNxA6ib-IVMIyQQKPBQEVP-nMKsyLvnHuKuHMw3rbzEQ5xemAZSbDjUTTSz1h4Q_kHyAjmZhkcUP-SMW92sk8eRPFaIwzIU3GYszRV8vYOUKyEmdZVKo_JZxloFAIlpzd-BgFX4bIXkn7xHfMPym_Vzr68ubF5DclwkCbMHIMcefSl7_dD6Y48RxycbqYHoyEOp_uQSuZJMiYX_y5jZm9TN5FLAbQn | US | — | — | suspicious |
2688 | chrome.exe | GET | 200 | 95.216.161.60:80 | http://www.3amer.com/r/rw/cpal-trk1.html | DE | html | 1.06 Kb | malicious |
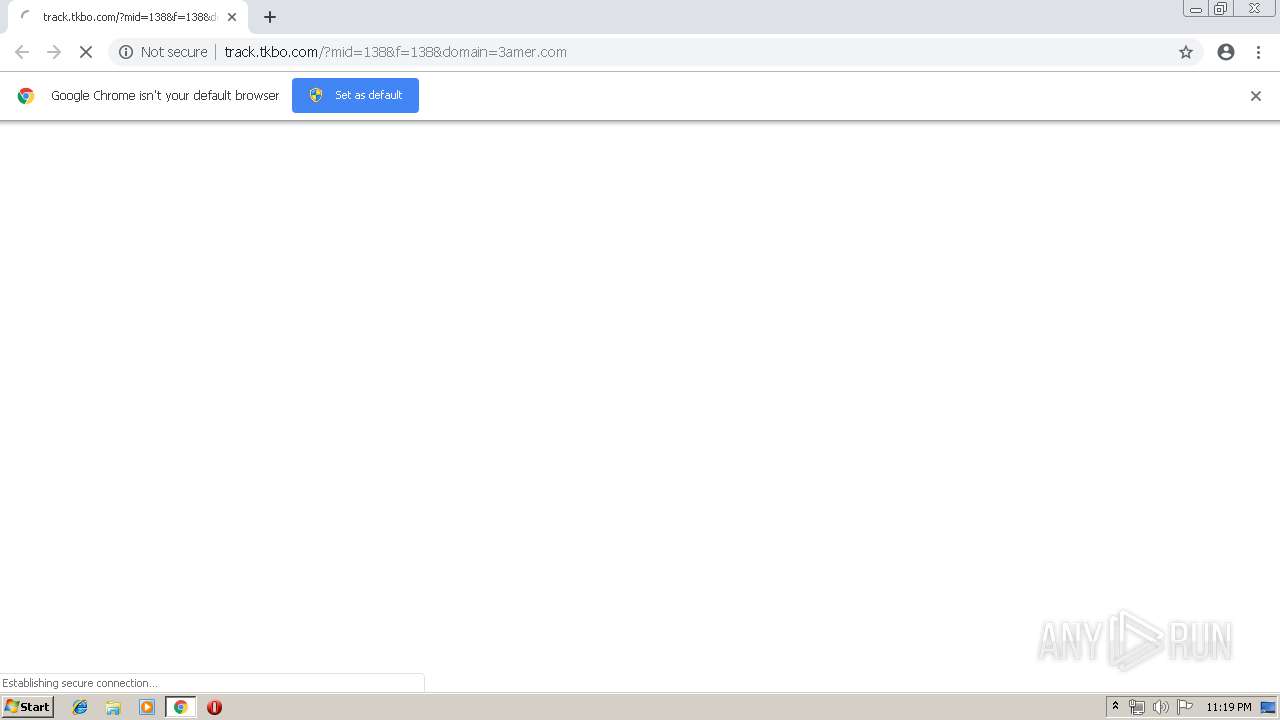
2688 | chrome.exe | GET | 200 | 144.76.1.130:80 | http://track.tkbo.com/?mid=138&f=138&domain=3amer.com | DE | html | 461 b | malicious |
2688 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 502 b | whitelisted |
2688 | chrome.exe | GET | 200 | 18.195.23.231:80 | http://re.labooone.com/redirect?target=BASE64aHR0cHM6Ly9nb29nbGUuY29t&ts=1557872379455&hash=yxxiLIhrbrHb3oM4rYp5kQ4ahp23ue5NiVOcRCRs8Kc&rm=D | DE | html | 230 b | shared |
2688 | chrome.exe | GET | 200 | 74.125.100.105:80 | http://r4---sn-5hnekn7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.76.9.72&mm=28&mn=sn-5hnekn7z&ms=nvh&mt=1557871853&mv=u&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2688 | chrome.exe | 172.217.16.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2688 | chrome.exe | 144.76.0.242:443 | track.tkbo.com | Hetzner Online GmbH | DE | suspicious |
2688 | chrome.exe | 144.76.1.130:443 | track.tkbo.com | Hetzner Online GmbH | DE | malicious |
2688 | chrome.exe | 108.168.193.189:80 | mybestmv.com | SoftLayer Technologies Inc. | US | suspicious |
— | — | 144.76.1.130:80 | track.tkbo.com | Hetzner Online GmbH | DE | malicious |
2688 | chrome.exe | 172.217.22.68:443 | www.google.com | Google Inc. | US | whitelisted |
2688 | chrome.exe | 172.217.16.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2688 | chrome.exe | 172.217.23.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2688 | chrome.exe | 172.217.23.174:443 | consent.google.com | Google Inc. | US | whitelisted |
2688 | chrome.exe | 216.58.207.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.3amer.com |
| malicious |
accounts.google.com |
| shared |
track.tkbo.com |
| unknown |
www.google-analytics.com |
| whitelisted |
track.traffic.club |
| suspicious |
mybestmv.com |
| unknown |
p244728.mybestmv.com |
| unknown |
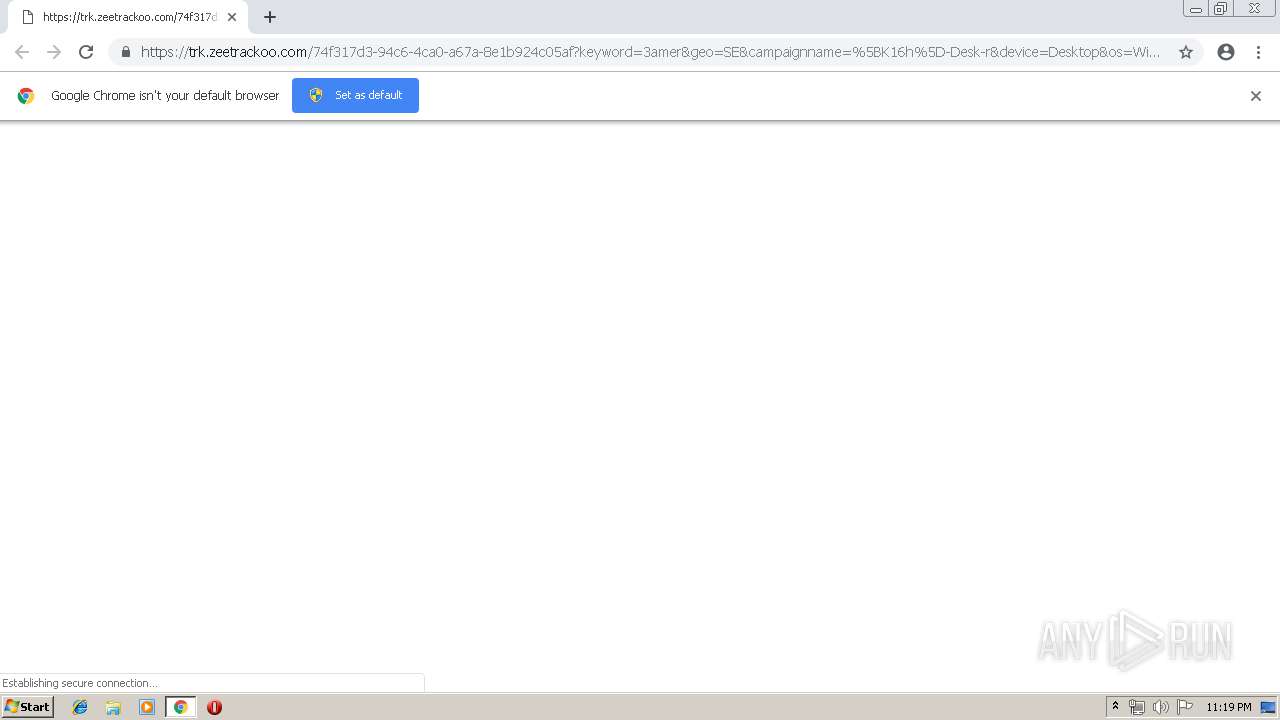
trk.zeetrackoo.com |
| shared |
re.labooone.com |
| shared |