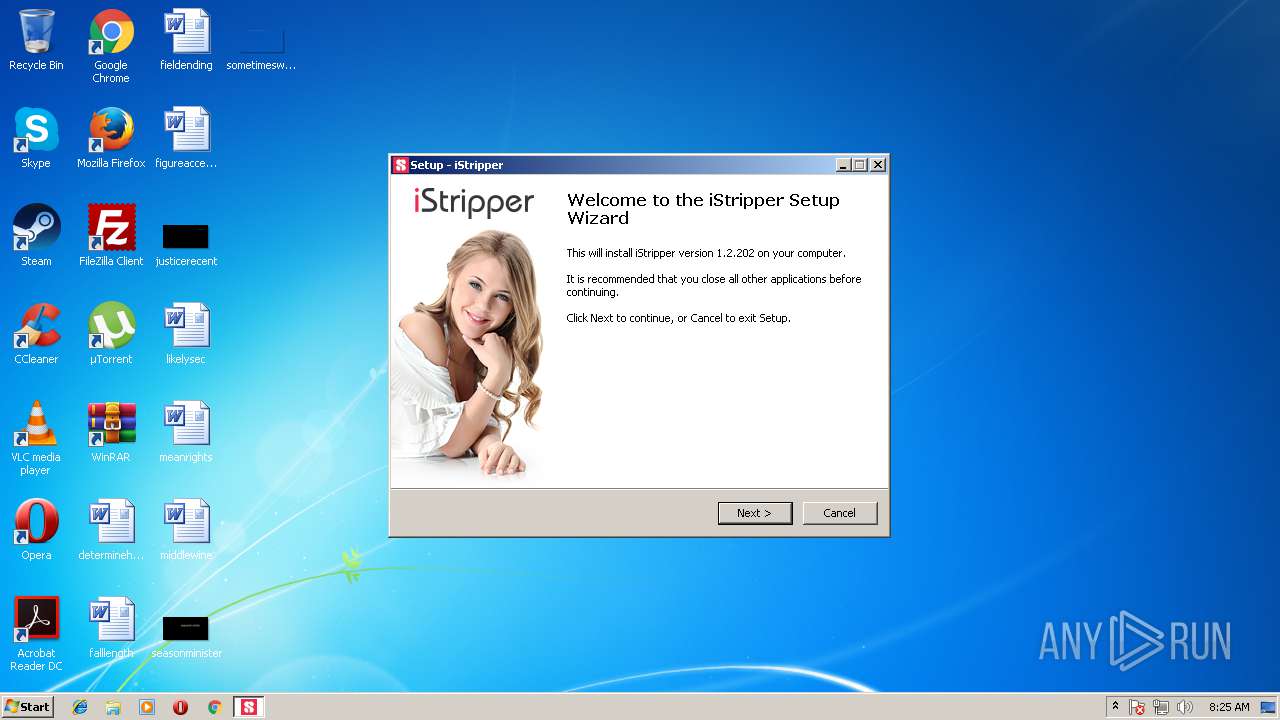
| download: | setup-istripper_39MCZoGWYV4PhzWg.exe |
| Full analysis: | https://app.any.run/tasks/818c3bc3-2441-42f2-b9be-b2cd3deb0aec |
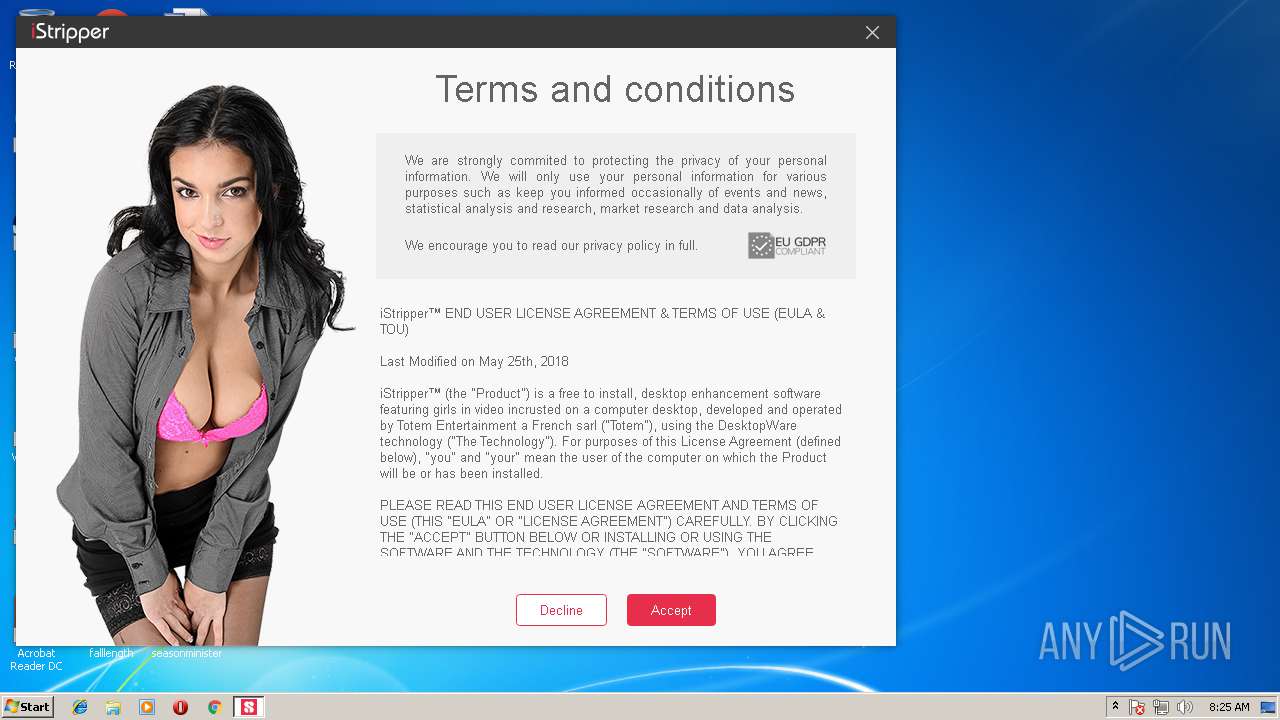
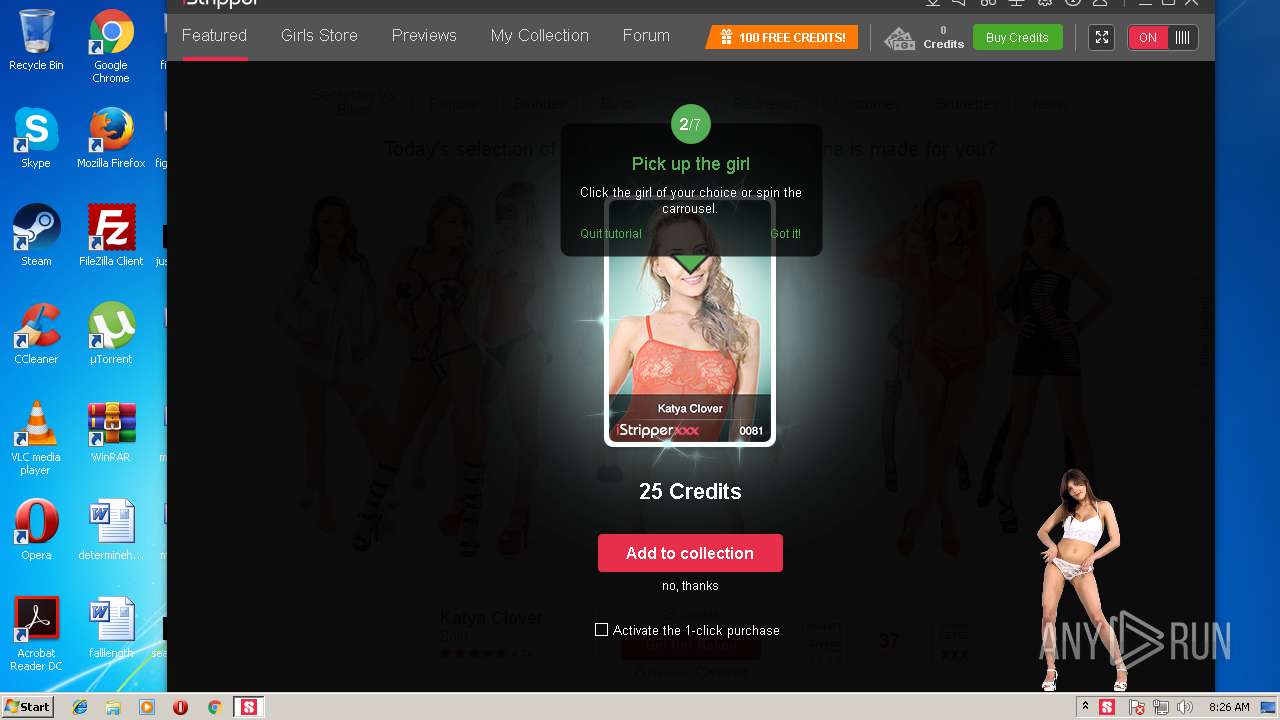
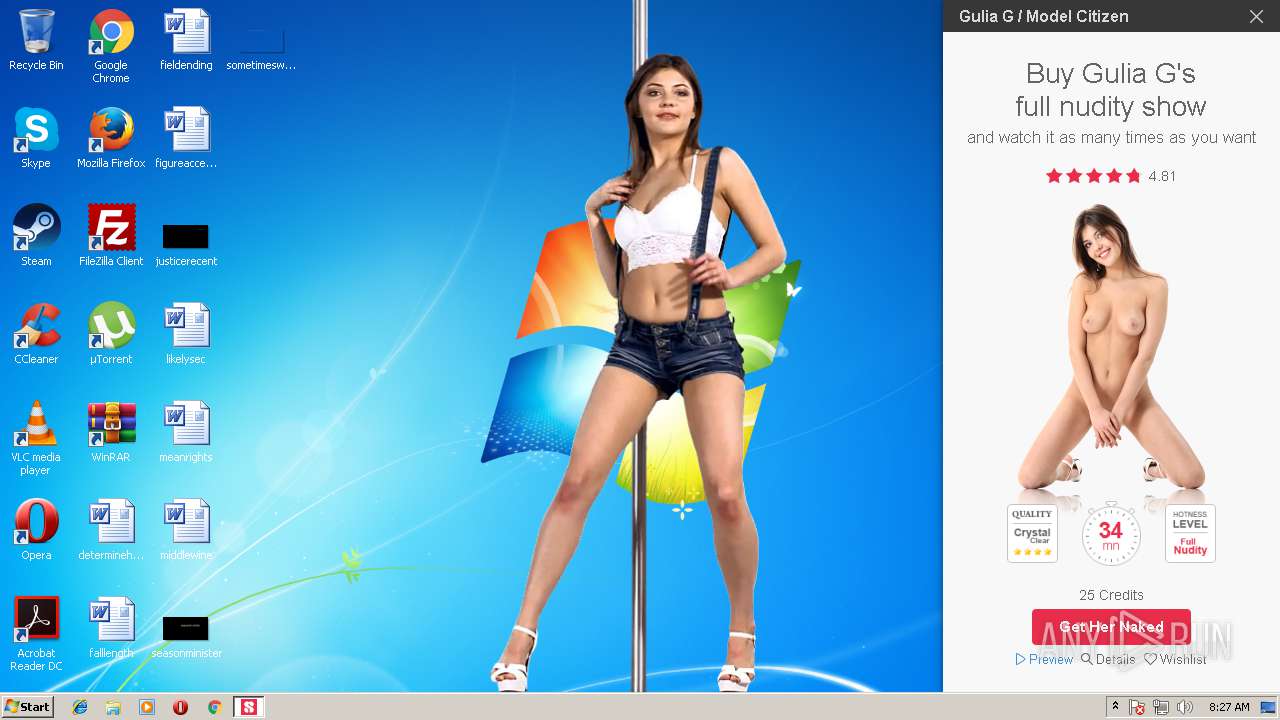
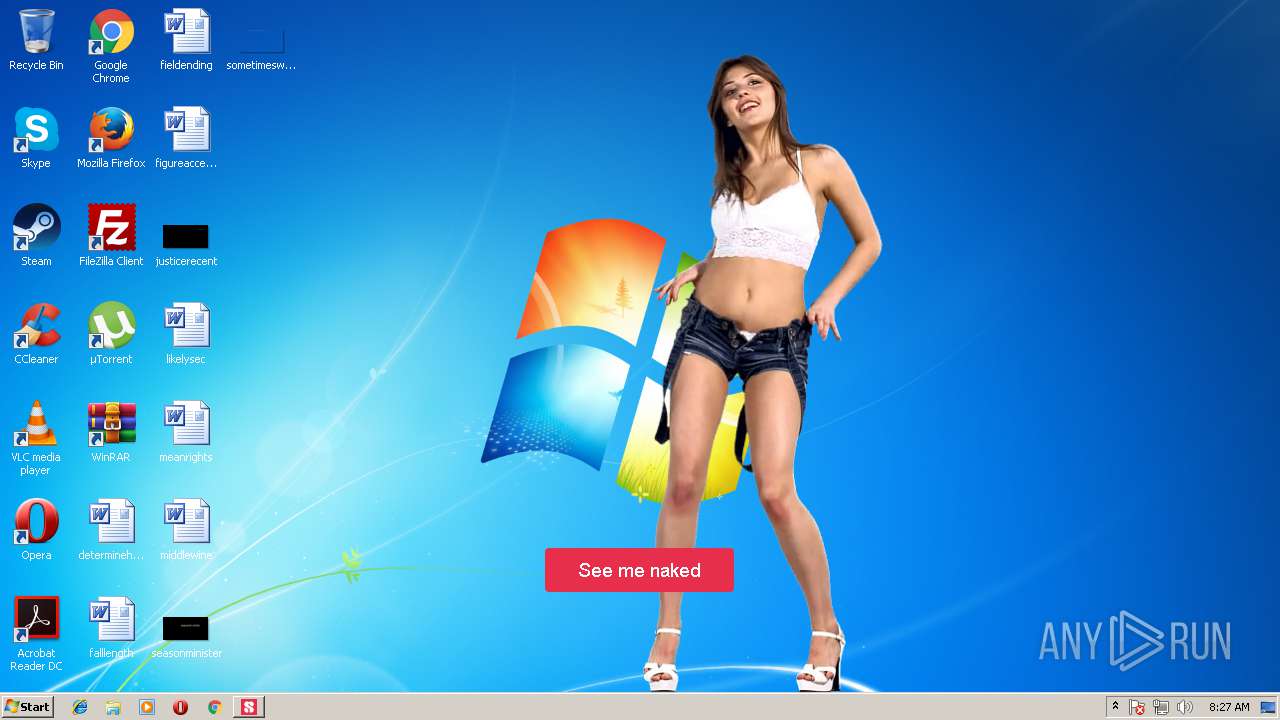
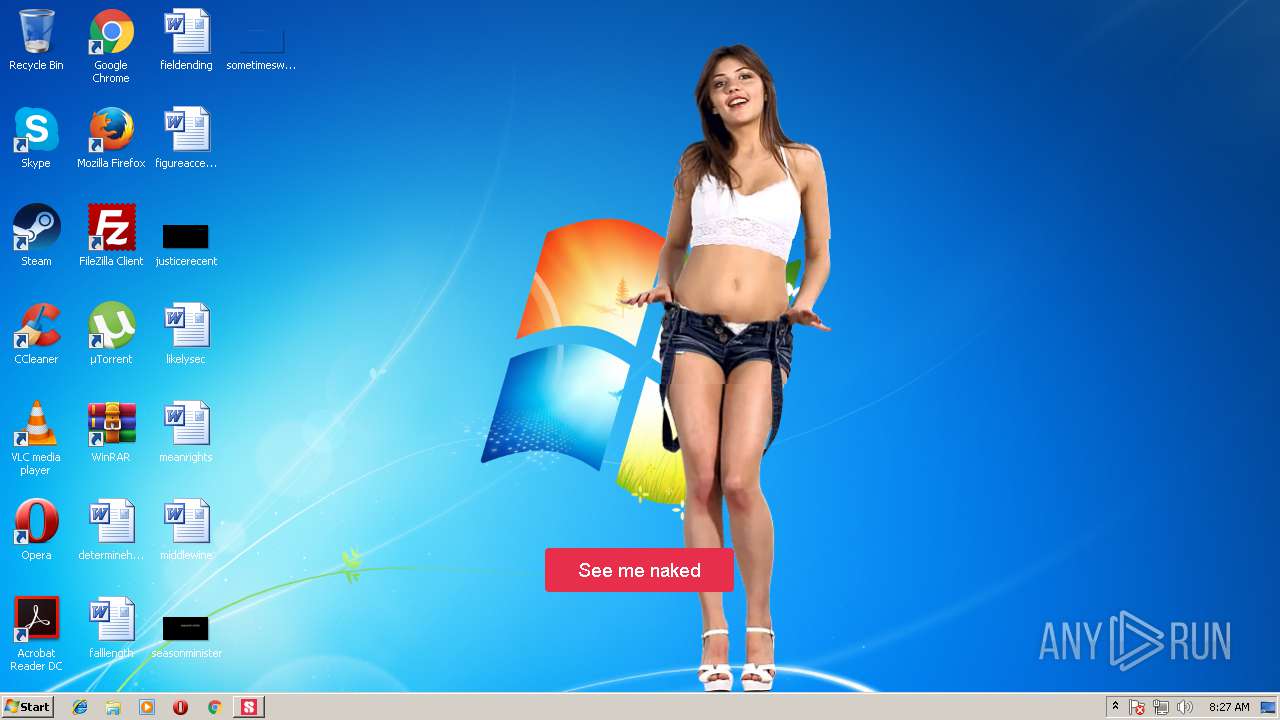
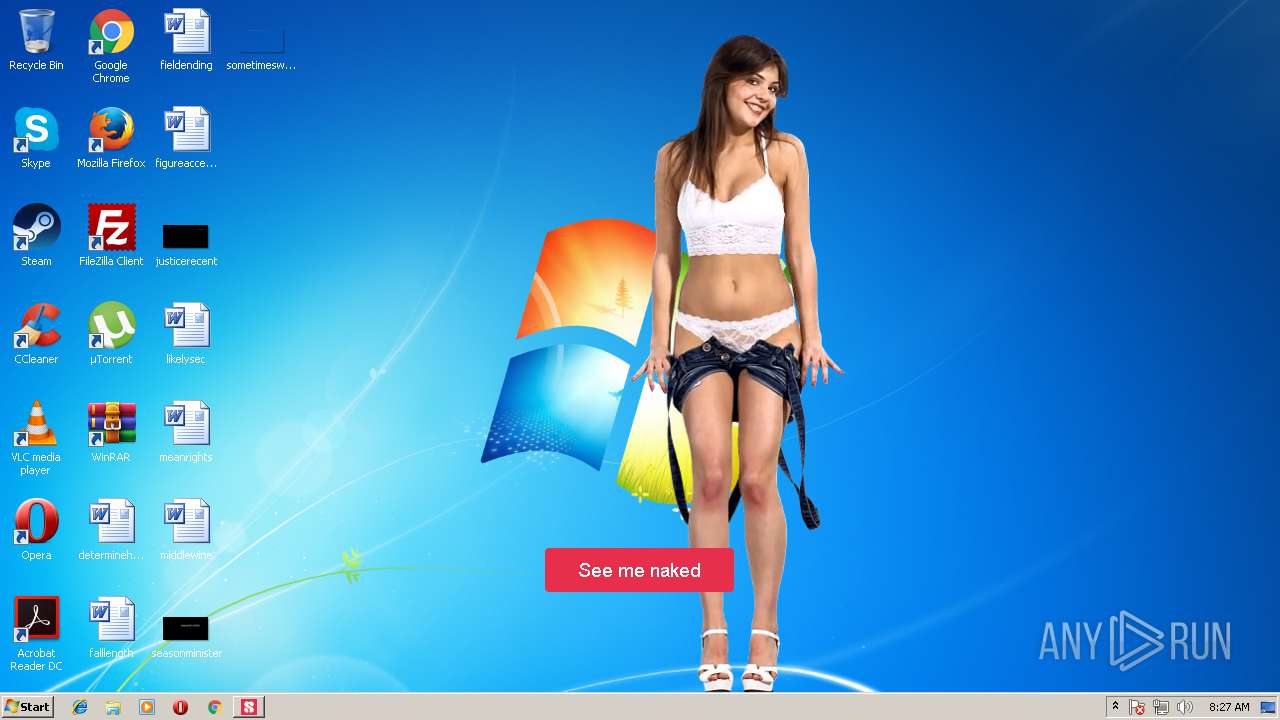
| Verdict: | Malicious activity |
| Analysis date: | July 22, 2018, 07:24:43 |
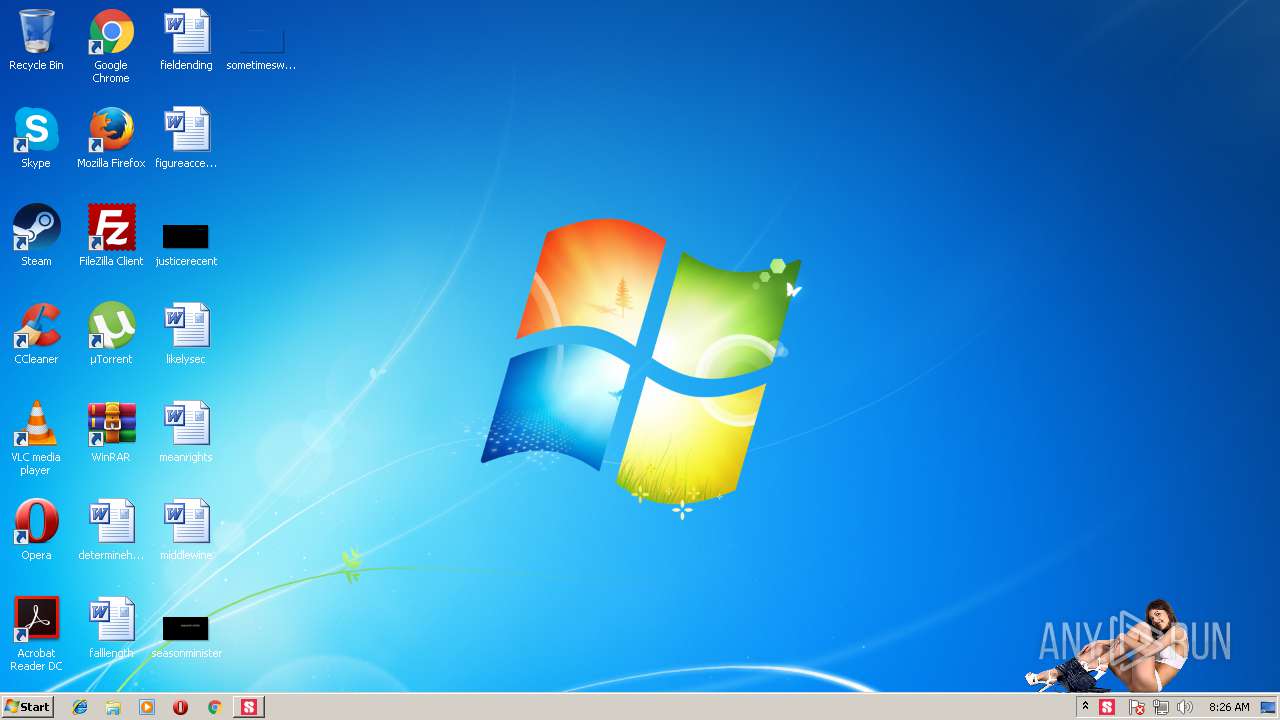
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9A97D2DCAEBFEEB6621A2826BB39369A |
| SHA1: | FA099CE97242FD489CD772AB7E0E4EE5CB84C36F |
| SHA256: | 73D77D6B8A91F43283AD4E486A917B9EEFC2603D9274951FF6A54999CB6406F3 |
| SSDEEP: | 786432:ZQnQ3ZiAOLgqN+jvwzjE4pgULTEDXcc1kKTqqWU7AfEOf:+mZxQdzY4pgU0grKTq7U74ff |
MALICIOUS
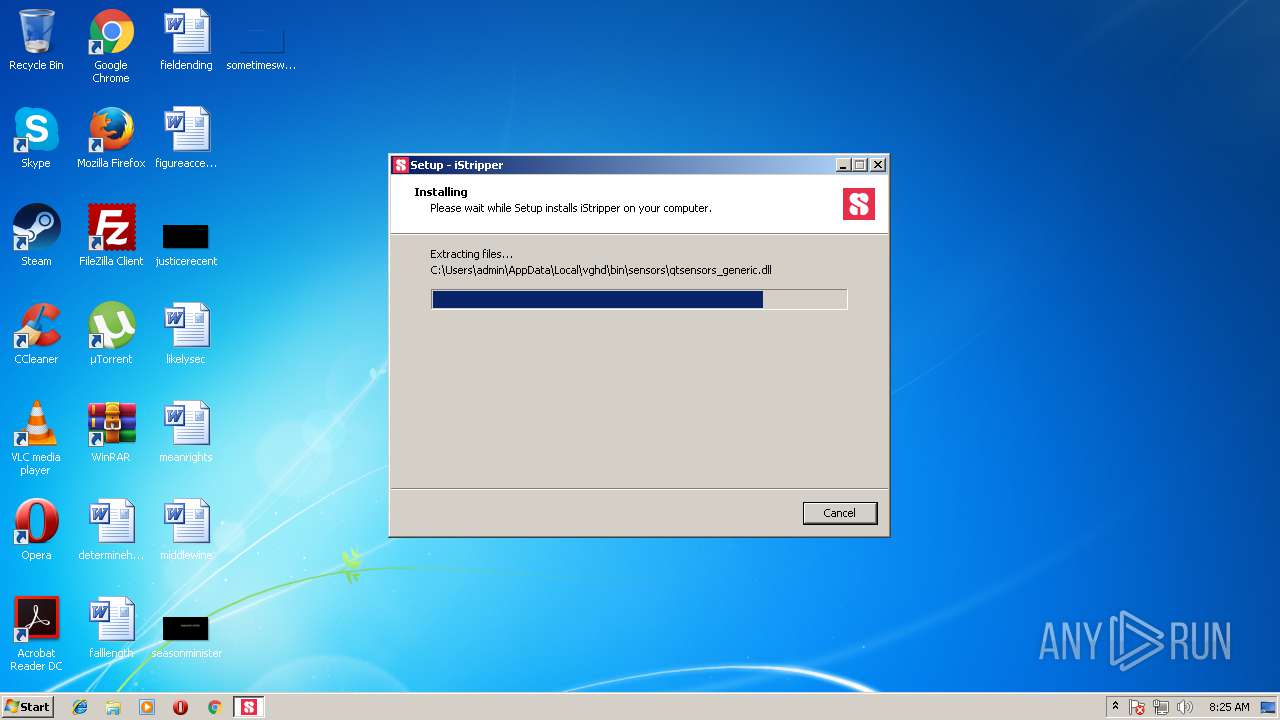
Loads dropped or rewritten executable
- vghd.exe (PID: 3972)
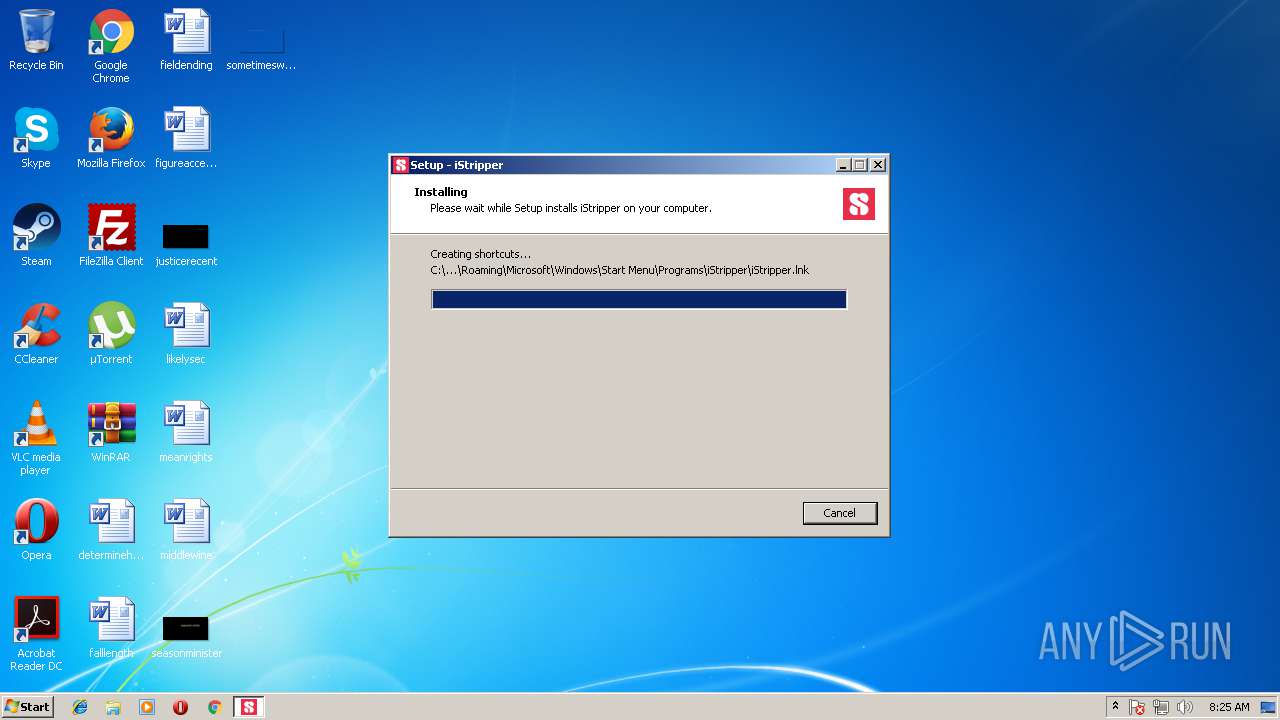
Writes to a start menu file
- setup-istripper_39MCZoGWYV4PhzWg.tmp (PID: 3996)
Application was dropped or rewritten from another process
- vghd.exe (PID: 3972)
SUSPICIOUS
Executable content was dropped or overwritten
- setup-istripper_39MCZoGWYV4PhzWg.exe (PID: 3732)
- setup-istripper_39MCZoGWYV4PhzWg.tmp (PID: 3996)
Reads Windows owner settings
- setup-istripper_39MCZoGWYV4PhzWg.tmp (PID: 3996)
Reads the Windows organization settings
- setup-istripper_39MCZoGWYV4PhzWg.tmp (PID: 3996)
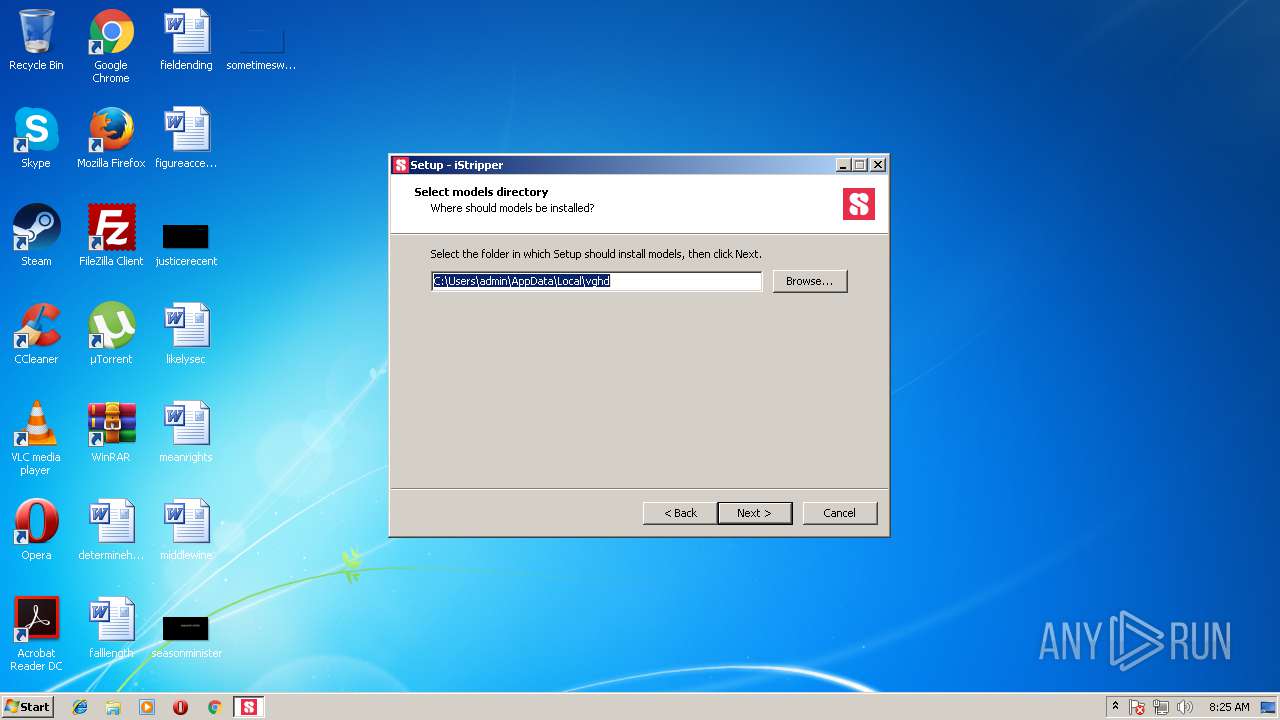
Creates files in the user directory
- setup-istripper_39MCZoGWYV4PhzWg.tmp (PID: 3996)
Reads the BIOS version
- vghd.exe (PID: 3972)
INFO
Application was dropped or rewritten from another process
- setup-istripper_39MCZoGWYV4PhzWg.tmp (PID: 3996)
Loads dropped or rewritten executable
- setup-istripper_39MCZoGWYV4PhzWg.tmp (PID: 3996)
Creates a software uninstall entry
- setup-istripper_39MCZoGWYV4PhzWg.tmp (PID: 3996)
Dropped object may contain URL's
- setup-istripper_39MCZoGWYV4PhzWg.tmp (PID: 3996)
- vghd.exe (PID: 3972)
Reads Microsoft Office registry keys
- vghd.exe (PID: 3972)
Dropped object may contain Bitcoin addresses
- setup-istripper_39MCZoGWYV4PhzWg.tmp (PID: 3996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.6) |
|---|---|---|
| .exe | | | Win16/32 Executable Delphi generic (19.5) |
| .exe | | | Generic Win/DOS Executable (18.9) |
| .exe | | | DOS Executable Generic (18.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:01:15 09:22:50+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 65024 |
| InitializedDataSize: | 70656 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x113bc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.2.2.2 |
| ProductVersionNumber: | 1.2.2.2 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
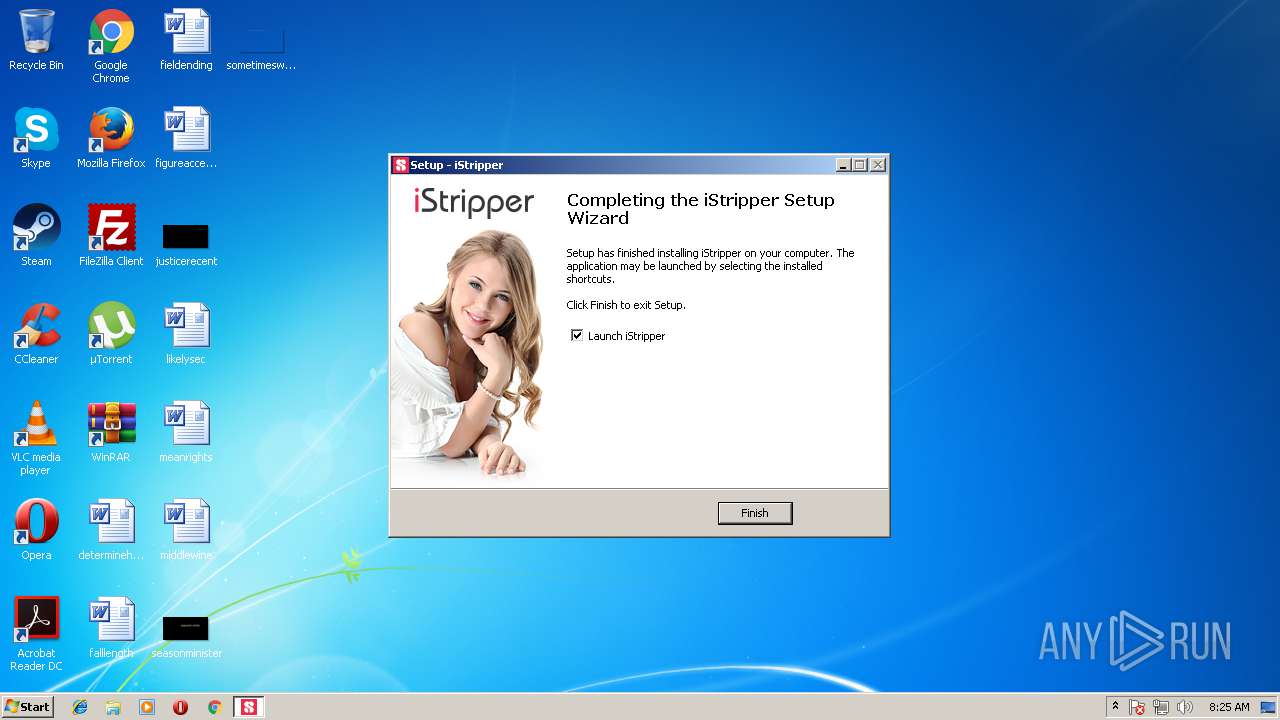
| CompanyName: | Totem Entertainment |
| FileDescription: | DesktopWare Installer |
| FileVersion: | 1.2.2.2 |
| LegalCopyright: | Copyright 1998-2018 Totem Entertainment |
| ProductName: | DesktopWare Installer |
| ProductVersion: | 1.2.202 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Jan-2016 08:22:50 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Totem Entertainment |
| FileDescription: | DesktopWare Installer |
| FileVersion: | 1.2.2.2 |
| LegalCopyright: | Copyright 1998-2018 Totem Entertainment |
| ProductName: | DesktopWare Installer |
| ProductVersion: | 1.2.202 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 15-Jan-2016 08:22:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F134 | 0x0000F200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.39169 |
.itext | 0x00011000 | 0x00000B44 | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.74305 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.24753 |
.bss | 0x00013000 | 0x000056B8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000DD0 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.97188 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0000F564 | 0x0000F600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04418 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.65329 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.91085 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.49962 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4096 | 3.28057 | 660 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
34
Monitored processes
3
Malicious processes
3
Suspicious processes
0
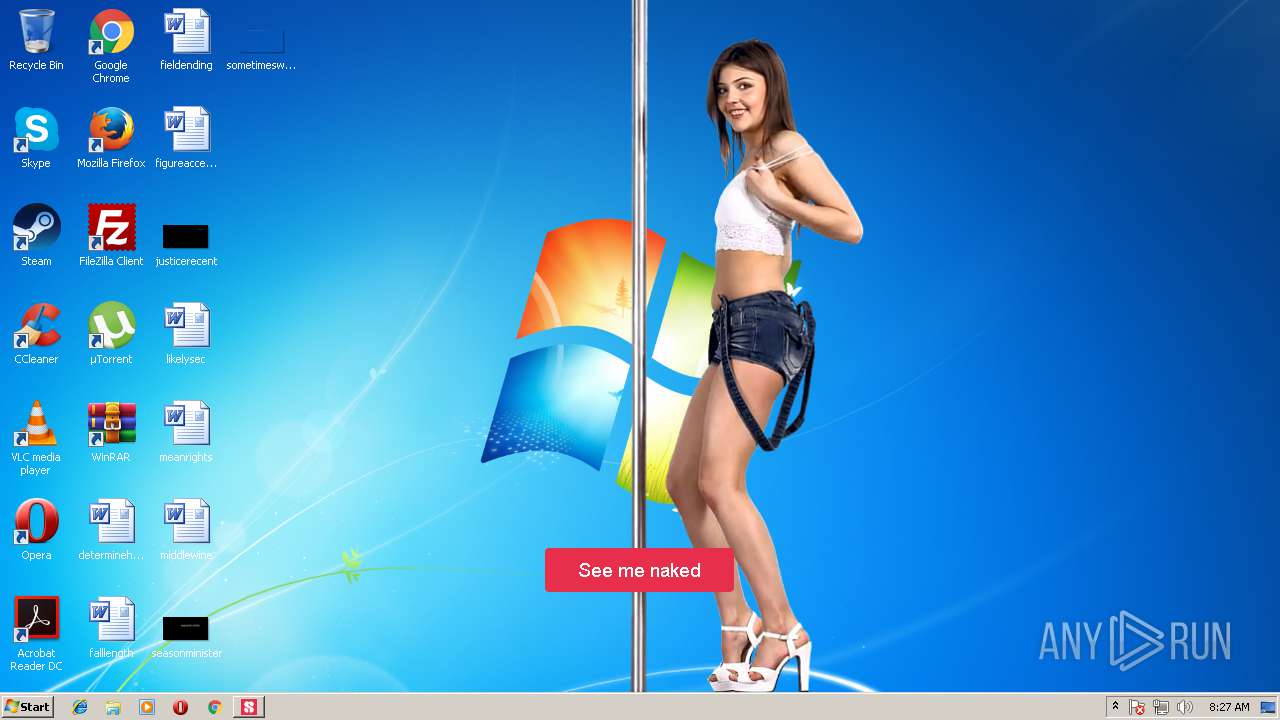
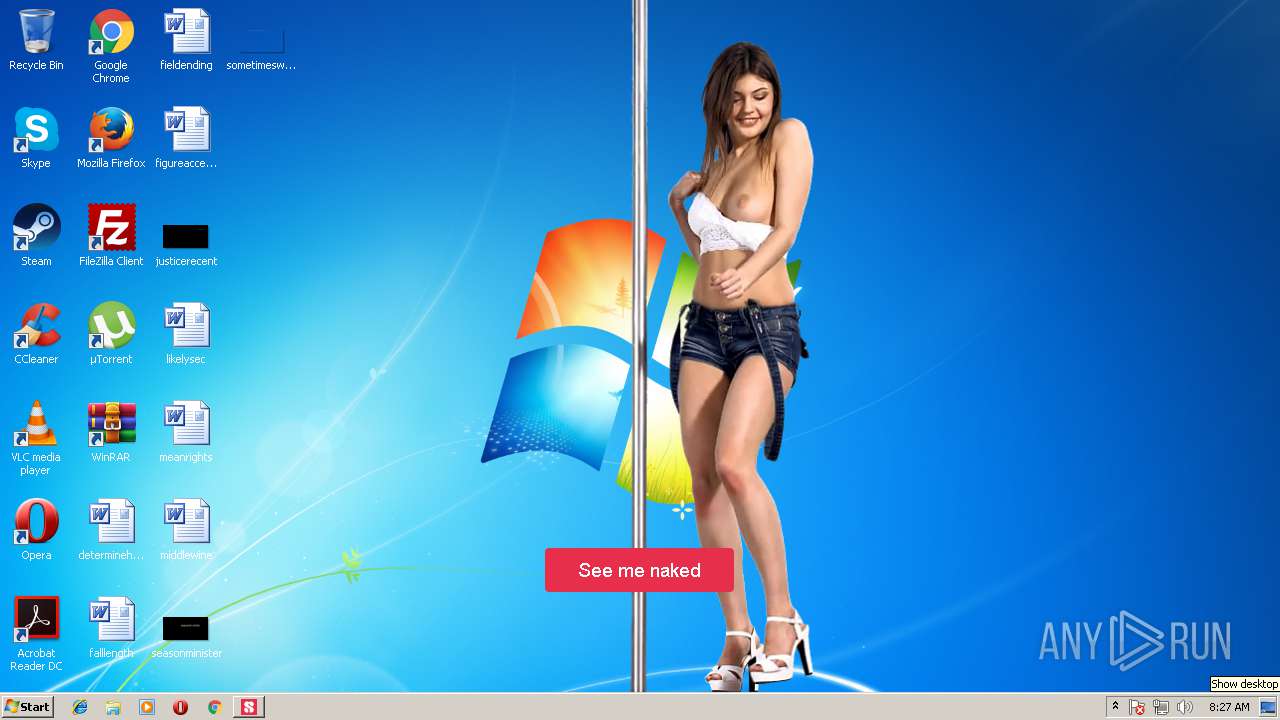
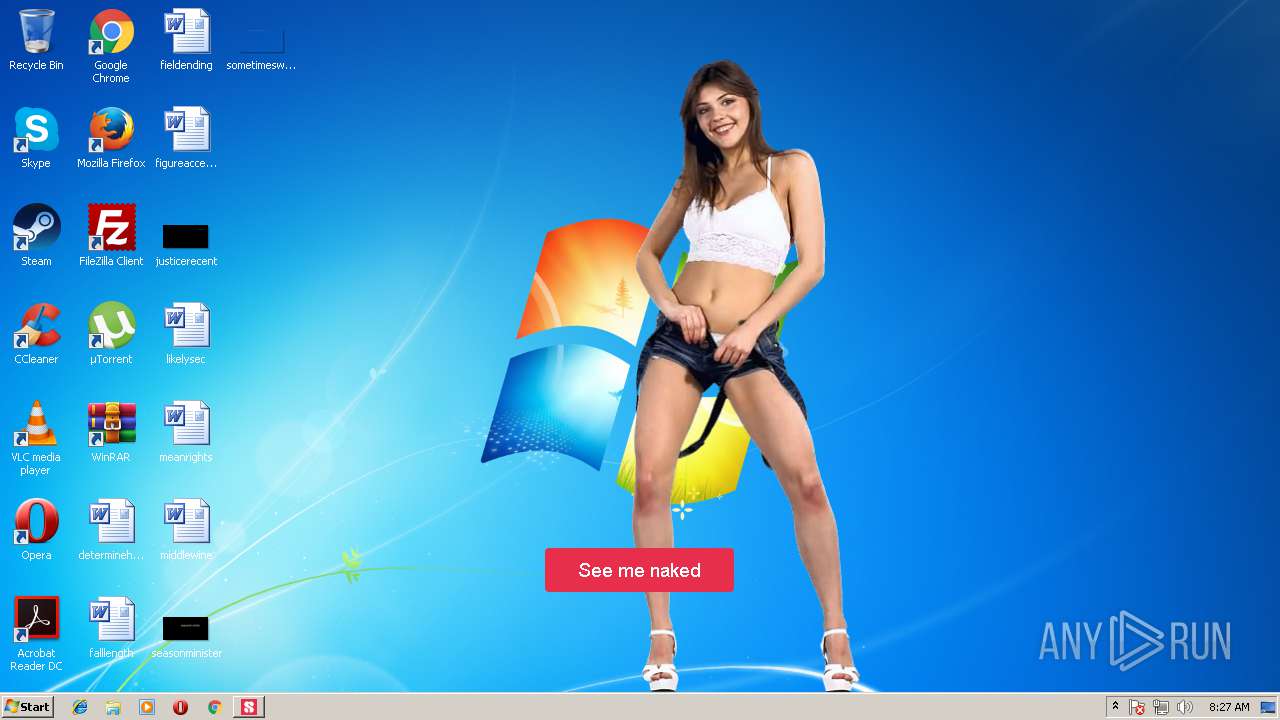
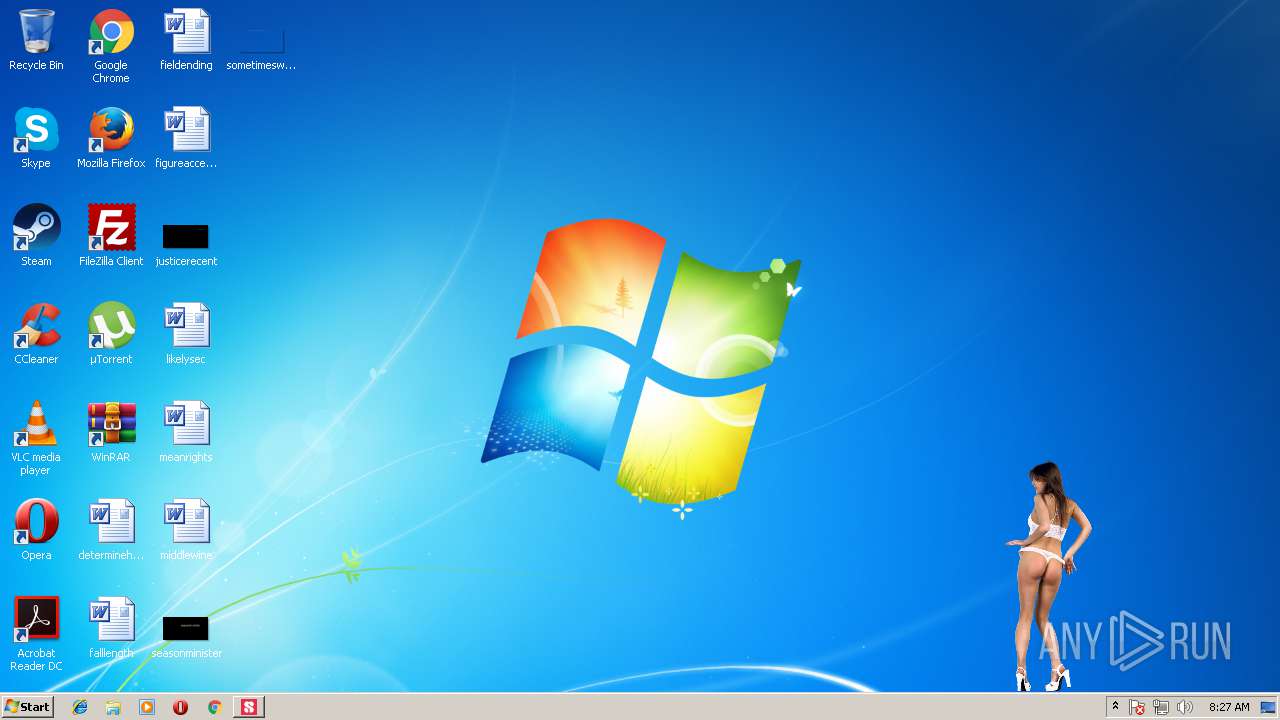
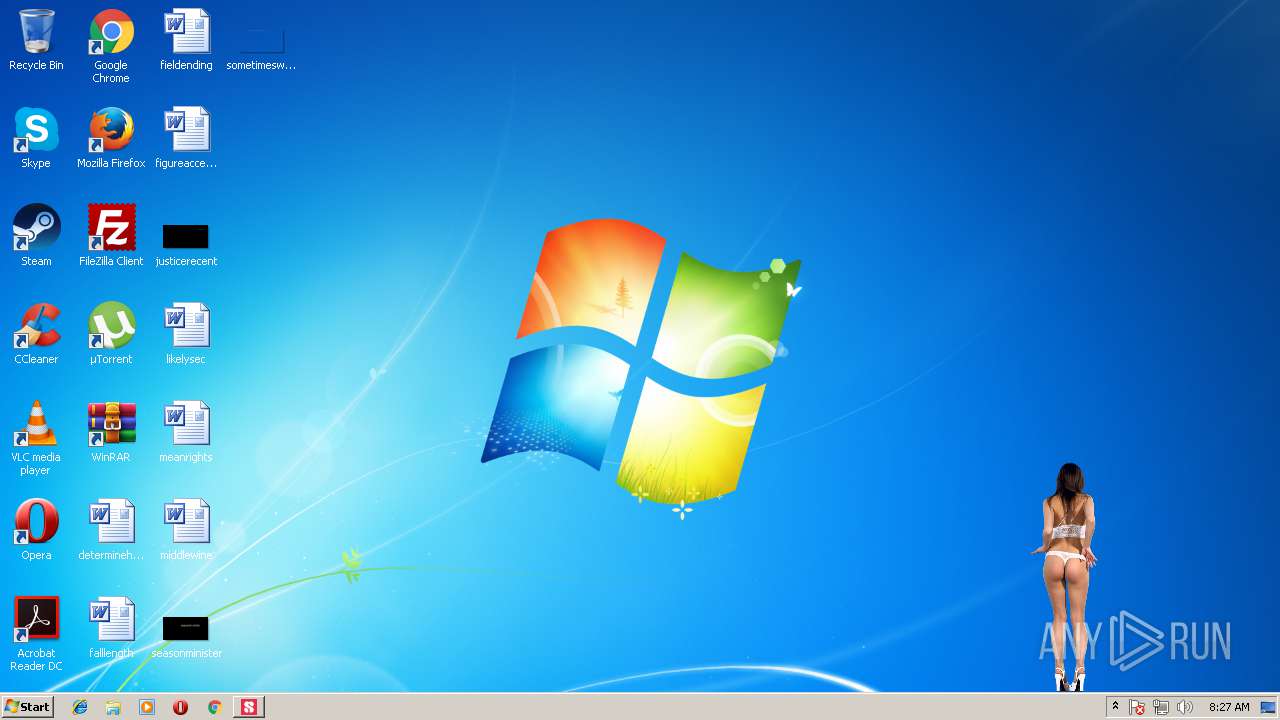
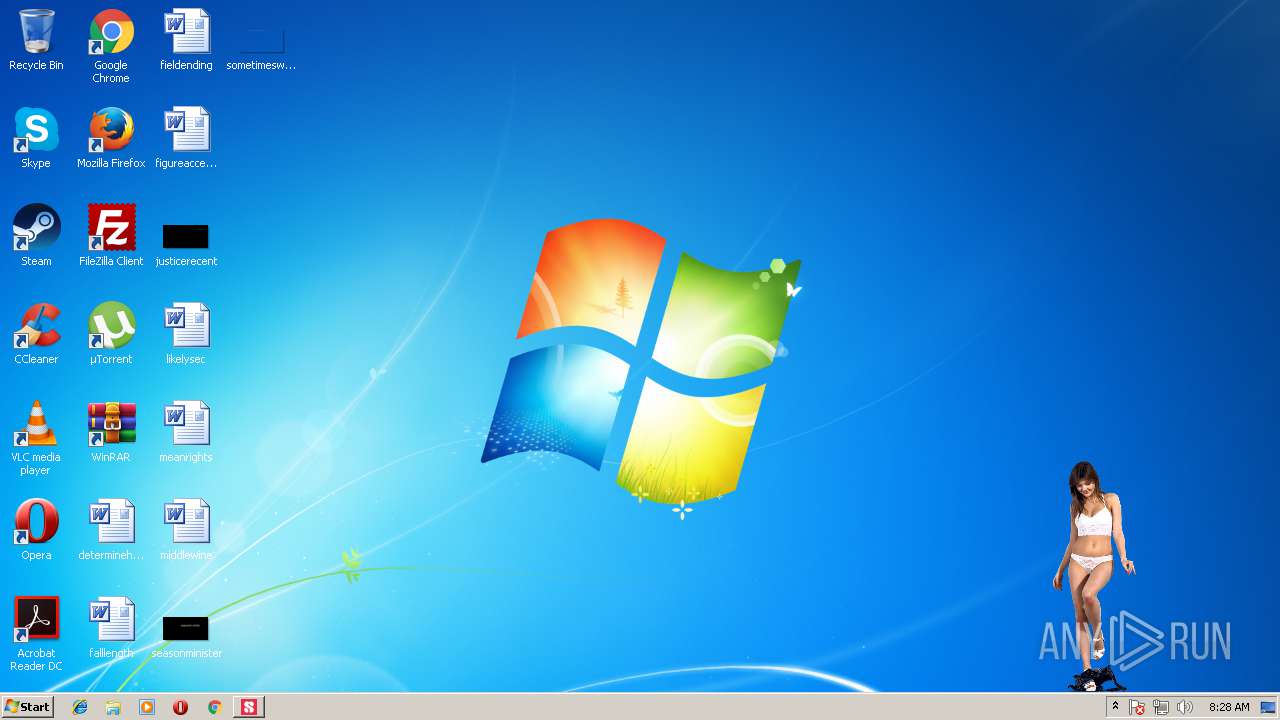
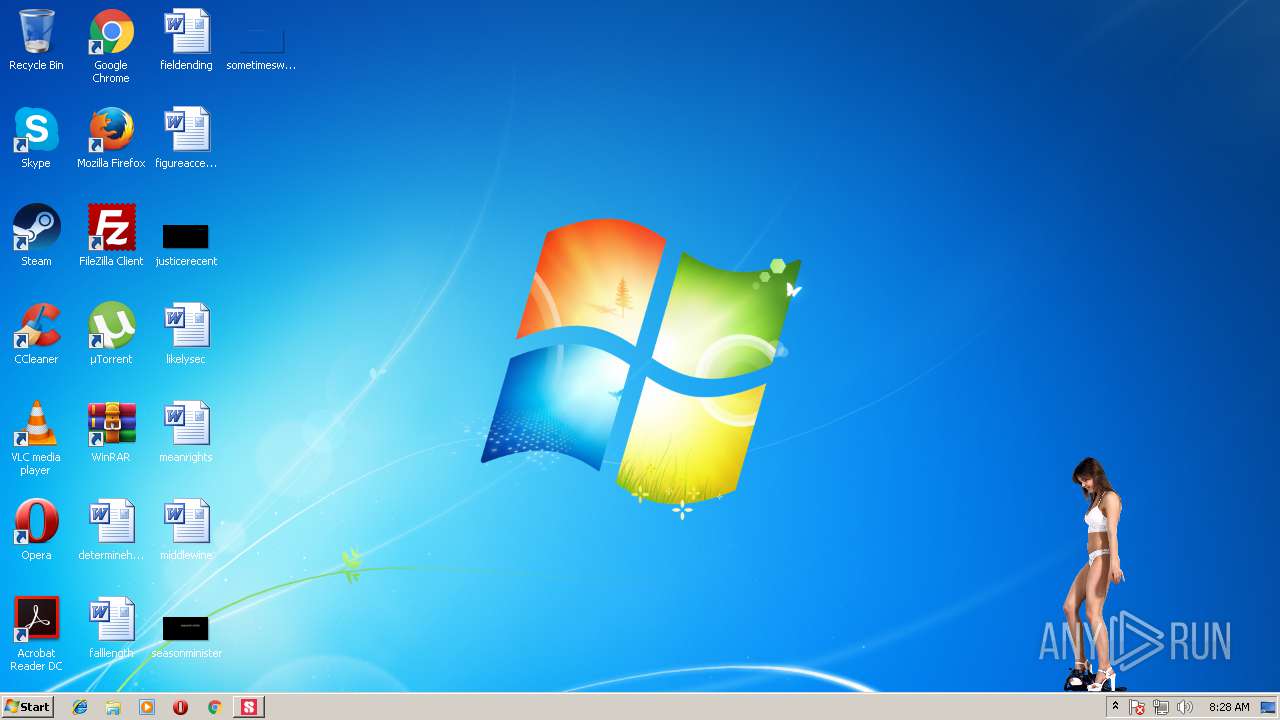
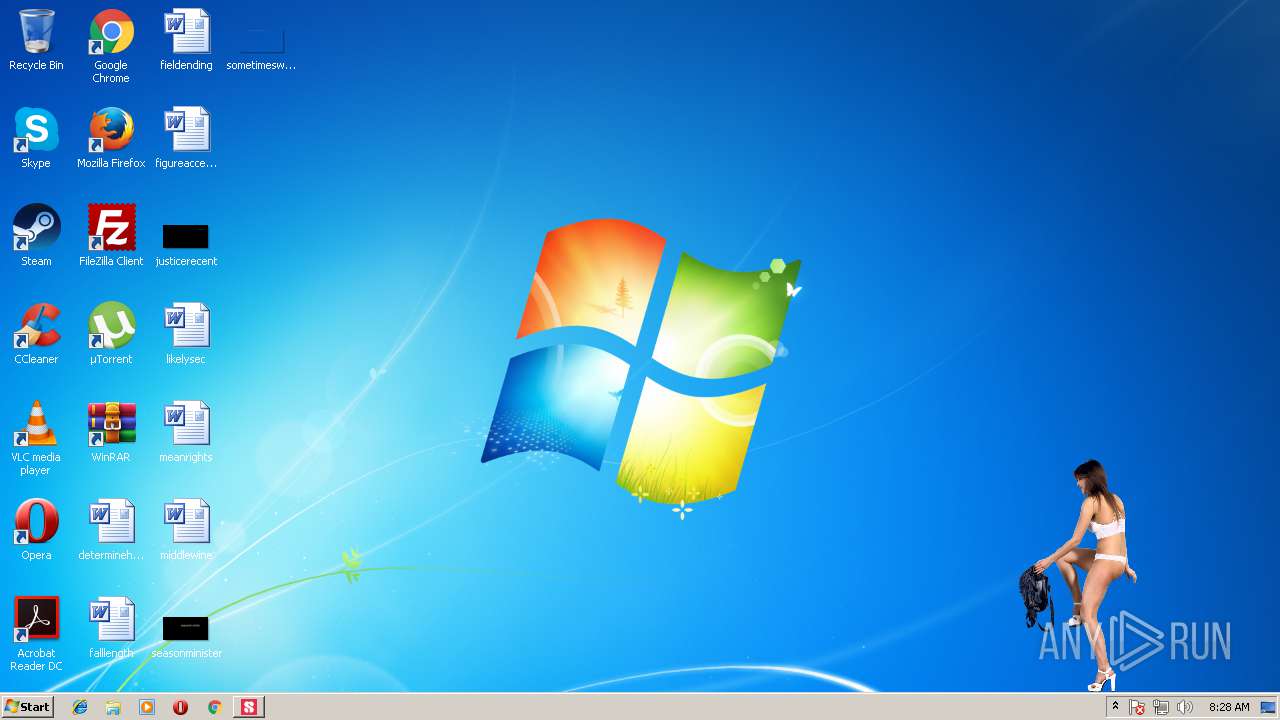
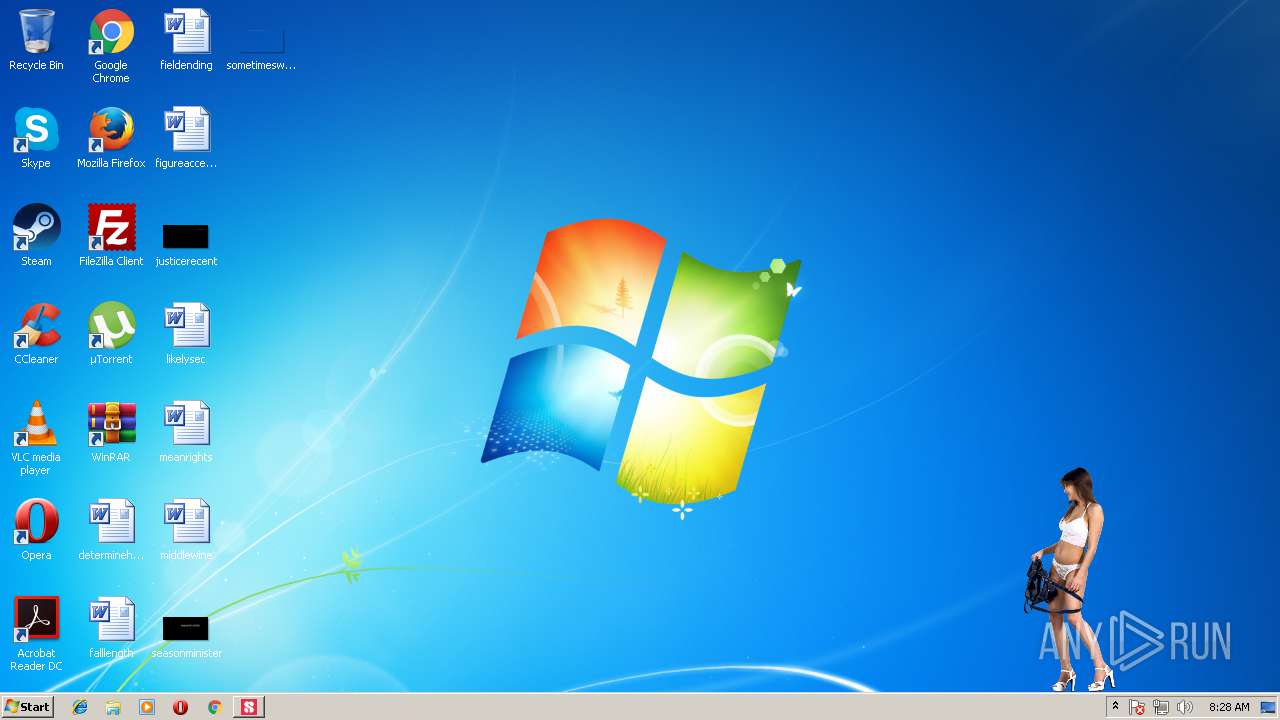
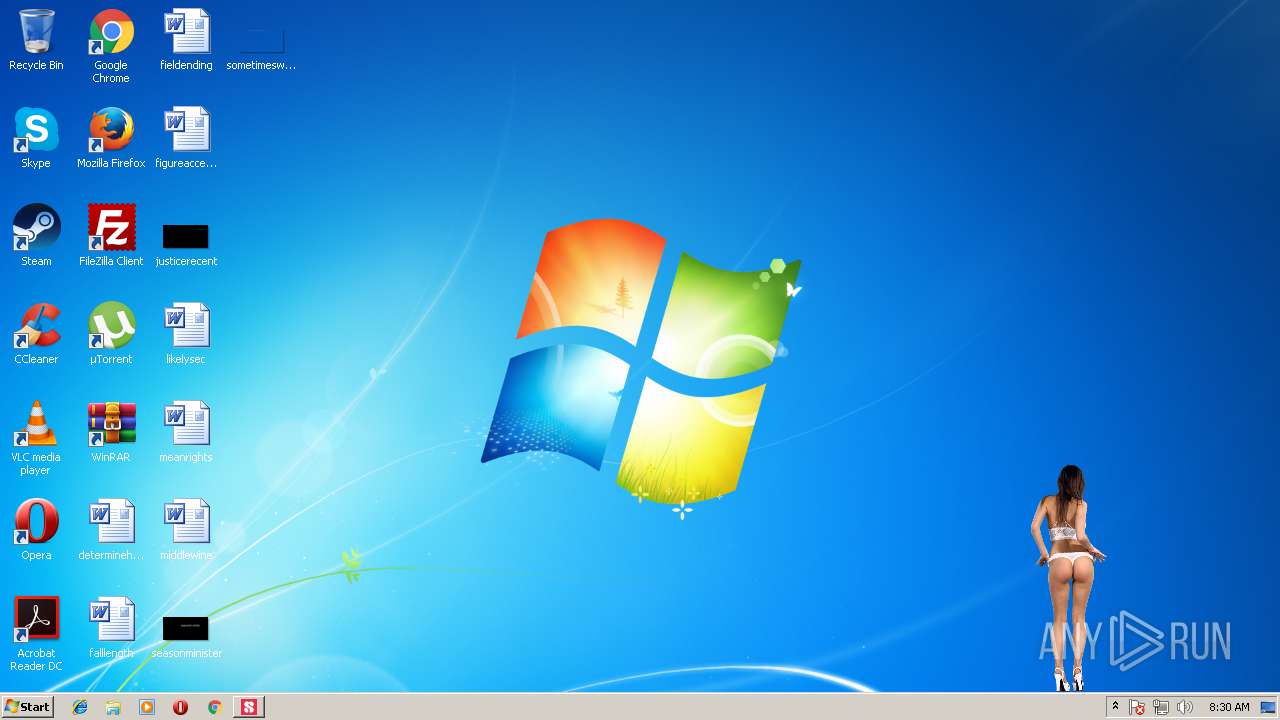
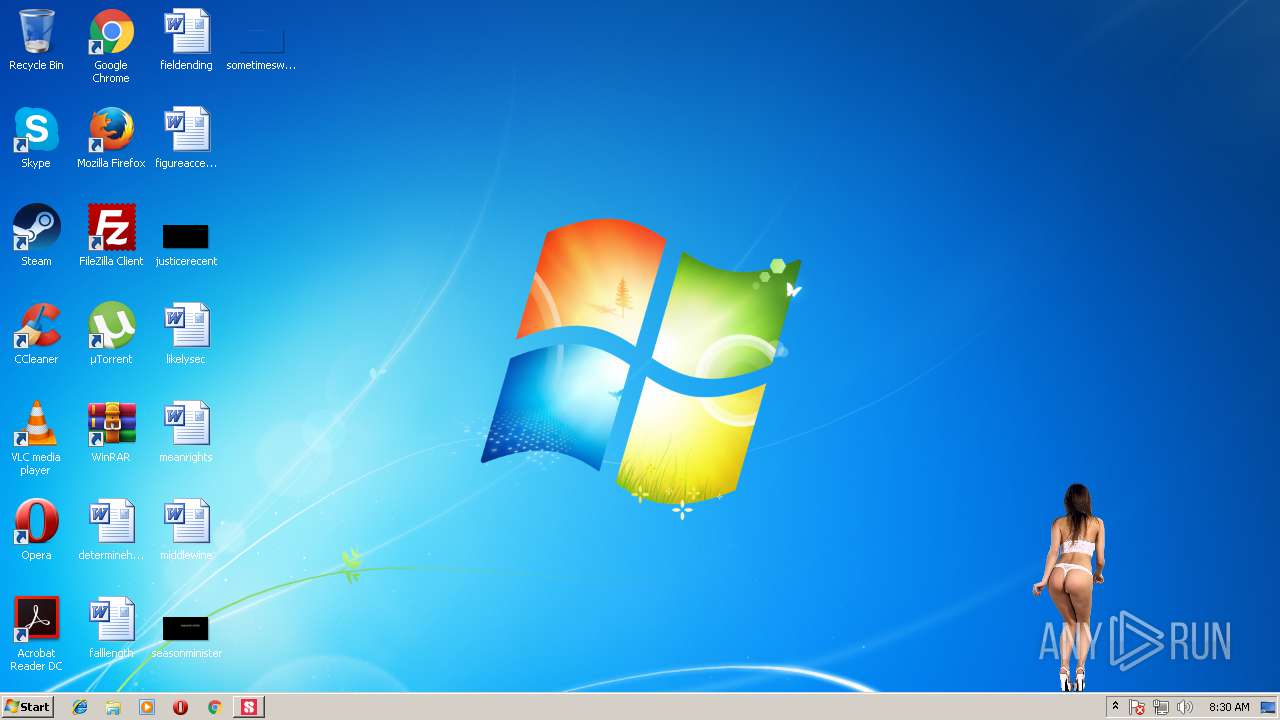
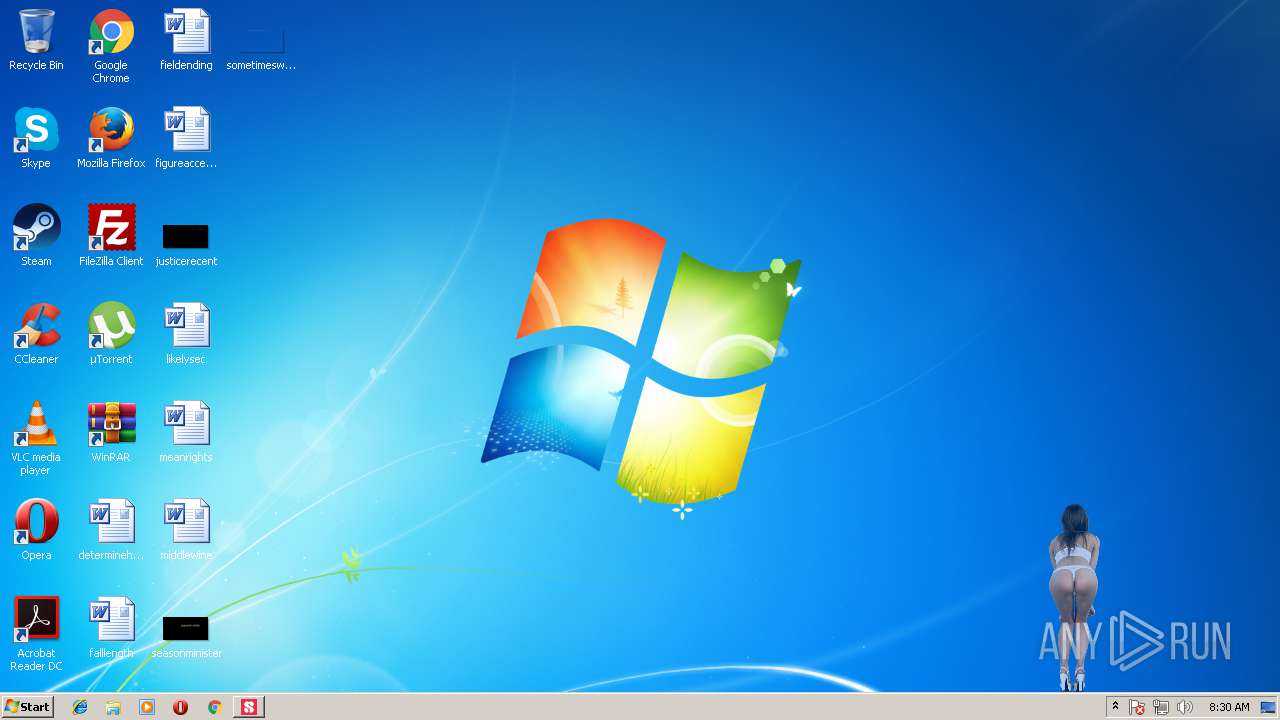
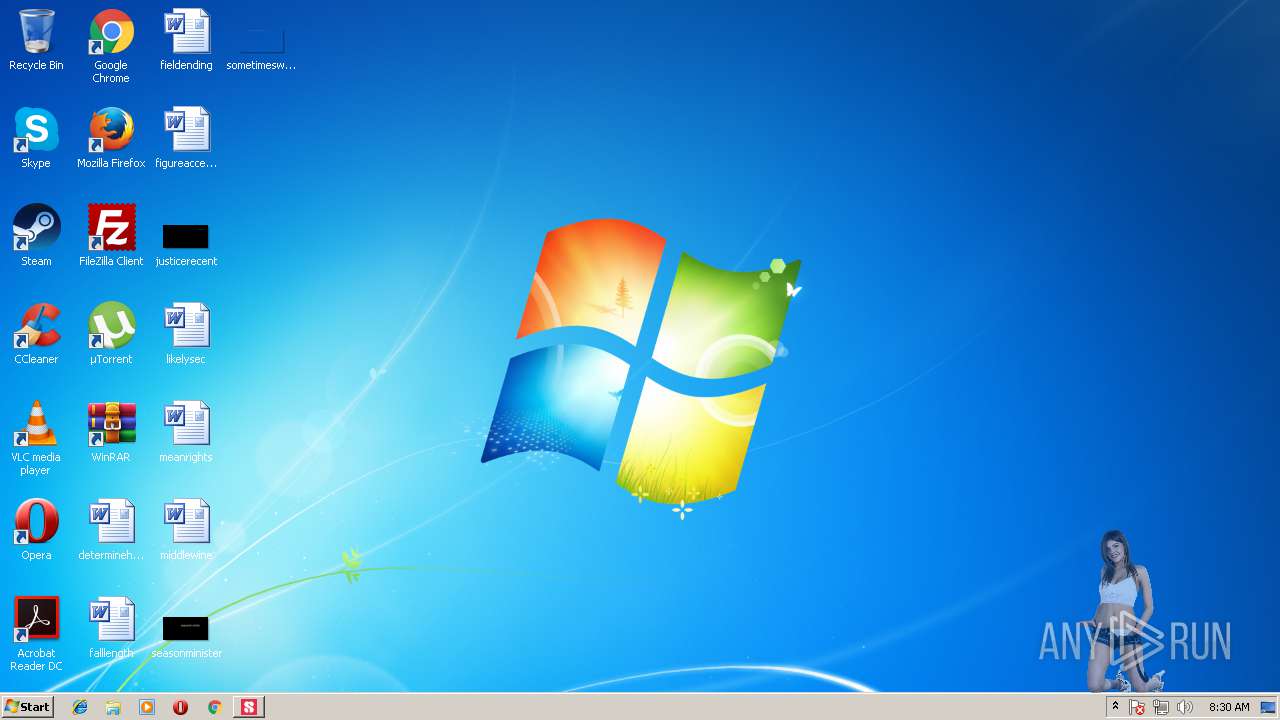
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
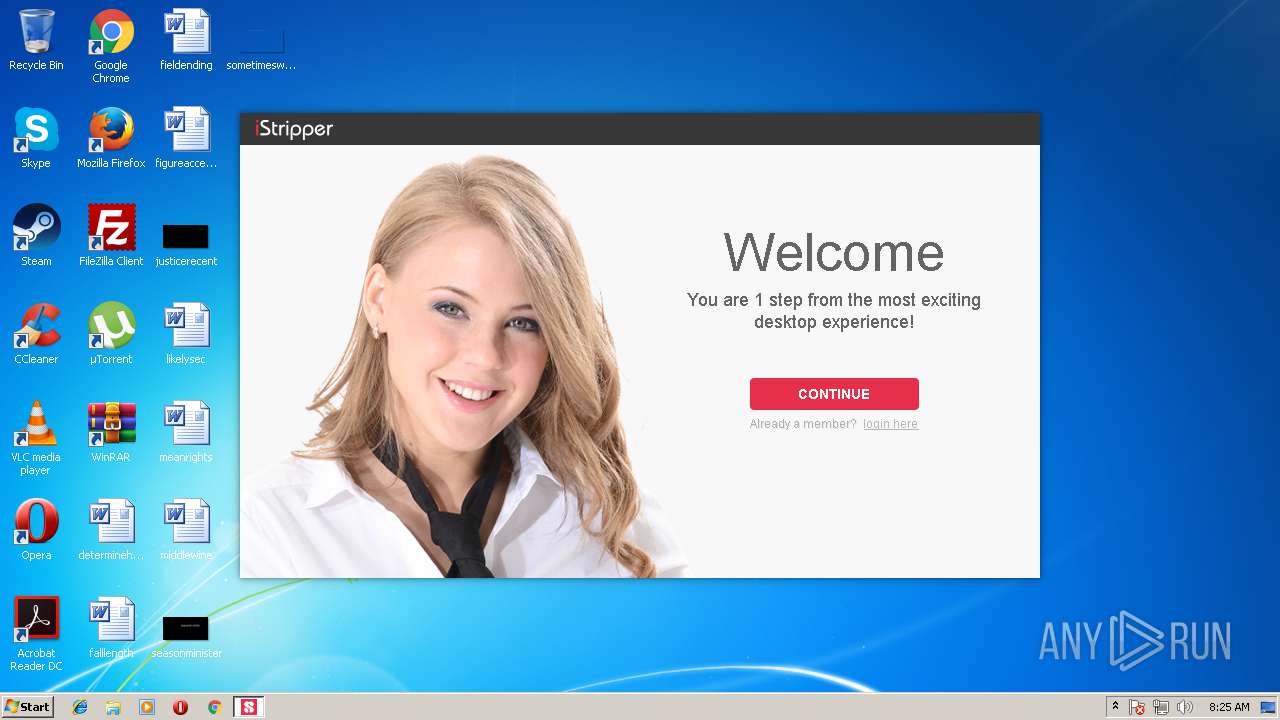
| 3732 | "C:\Users\admin\AppData\Local\Temp\setup-istripper_39MCZoGWYV4PhzWg.exe" | C:\Users\admin\AppData\Local\Temp\setup-istripper_39MCZoGWYV4PhzWg.exe | explorer.exe | ||||||||||||
User: admin Company: Totem Entertainment Integrity Level: MEDIUM Description: DesktopWare Installer Exit code: 0 Version: 1.2.2.2 Modules
| |||||||||||||||
| 3972 | "C:\Users\admin\AppData\Local\vghd\bin\vghd.exe" -fromSetup | C:\Users\admin\AppData\Local\vghd\bin\vghd.exe | setup-istripper_39MCZoGWYV4PhzWg.tmp | ||||||||||||
User: admin Company: Totem Entertainment Integrity Level: MEDIUM Description: DesktopWare / iStripper Exit code: 0 Version: 1.2.2.02 Modules
| |||||||||||||||
| 3996 | "C:\Users\admin\AppData\Local\Temp\is-TU12K.tmp\setup-istripper_39MCZoGWYV4PhzWg.tmp" /SL5="$230160,32320140,136704,C:\Users\admin\AppData\Local\Temp\setup-istripper_39MCZoGWYV4PhzWg.exe" | C:\Users\admin\AppData\Local\Temp\is-TU12K.tmp\setup-istripper_39MCZoGWYV4PhzWg.tmp | setup-istripper_39MCZoGWYV4PhzWg.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
753
Read events
581
Write events
164
Delete events
8
Modification events
| (PID) Process: | (3996) setup-istripper_39MCZoGWYV4PhzWg.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 9C0F0000D415D02A8D21D401 | |||
| (PID) Process: | (3996) setup-istripper_39MCZoGWYV4PhzWg.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 13C9114347D8DB00204ABDC07746F741F22D87BB0C3C9B9035B60F50A7DC2528 | |||
| (PID) Process: | (3996) setup-istripper_39MCZoGWYV4PhzWg.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3996) setup-istripper_39MCZoGWYV4PhzWg.tmp | Key: | HKEY_CURRENT_USER\Software\Totem\vghd |
| Operation: | write | Name: | quit |
Value: quitfrominstall | |||
| (PID) Process: | (3996) setup-istripper_39MCZoGWYV4PhzWg.tmp | Key: | HKEY_CURRENT_USER\Software\Totem\DLManager |
| Operation: | write | Name: | quit |
Value: quitfrominstall | |||
| (PID) Process: | (3996) setup-istripper_39MCZoGWYV4PhzWg.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Users\admin\AppData\Local\vghd\bin\libeay32.dll | |||
| (PID) Process: | (3996) setup-istripper_39MCZoGWYV4PhzWg.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: B864FC20A2926BA7C6CD075C1DC07FA4C91DAF38D5516A4EDC6E8F26379A5A05 | |||
| (PID) Process: | (3996) setup-istripper_39MCZoGWYV4PhzWg.tmp | Key: | HKEY_CURRENT_USER\Software\Totem\vghd\System |
| Operation: | write | Name: | Langage |
Value: EN | |||
| (PID) Process: | (3996) setup-istripper_39MCZoGWYV4PhzWg.tmp | Key: | HKEY_CURRENT_USER\Software\Totem\vghd\System |
| Operation: | write | Name: | MainPath |
Value: C:\Users\admin\AppData\Local\vghd\bin | |||
| (PID) Process: | (3996) setup-istripper_39MCZoGWYV4PhzWg.tmp | Key: | HKEY_CURRENT_USER\Software\Totem\vghd\System |
| Operation: | write | Name: | DataPath |
Value: C:\Users\admin\AppData\Local\vghd\data\ | |||
Executable files
71
Suspicious files
38
Text files
343
Unknown types
61
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3996 | setup-istripper_39MCZoGWYV4PhzWg.tmp | C:\Users\admin\AppData\Local\vghd\bin\is-T9C3T.tmp | — | |
MD5:— | SHA256:— | |||
| 3996 | setup-istripper_39MCZoGWYV4PhzWg.tmp | C:\Users\admin\AppData\Local\vghd\bin\is-VISJ6.tmp | — | |
MD5:— | SHA256:— | |||
| 3996 | setup-istripper_39MCZoGWYV4PhzWg.tmp | C:\Users\admin\AppData\Local\vghd\bin\is-SAB6R.tmp | — | |
MD5:— | SHA256:— | |||
| 3996 | setup-istripper_39MCZoGWYV4PhzWg.tmp | C:\Users\admin\AppData\Local\vghd\bin\is-PM9DB.tmp | — | |
MD5:— | SHA256:— | |||
| 3996 | setup-istripper_39MCZoGWYV4PhzWg.tmp | C:\Users\admin\AppData\Local\vghd\bin\is-EFI35.tmp | — | |
MD5:— | SHA256:— | |||
| 3996 | setup-istripper_39MCZoGWYV4PhzWg.tmp | C:\Users\admin\AppData\Local\vghd\bin\is-QUTQF.tmp | — | |
MD5:— | SHA256:— | |||
| 3996 | setup-istripper_39MCZoGWYV4PhzWg.tmp | C:\Users\admin\AppData\Local\vghd\bin\is-UJ22B.tmp | — | |
MD5:— | SHA256:— | |||
| 3996 | setup-istripper_39MCZoGWYV4PhzWg.tmp | C:\Users\admin\AppData\Local\vghd\bin\is-RNF9U.tmp | — | |
MD5:— | SHA256:— | |||
| 3996 | setup-istripper_39MCZoGWYV4PhzWg.tmp | C:\Users\admin\AppData\Local\vghd\bin\is-0KHH4.tmp | — | |
MD5:— | SHA256:— | |||
| 3996 | setup-istripper_39MCZoGWYV4PhzWg.tmp | C:\Users\admin\AppData\Local\vghd\bin\is-EI4RA.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
80
TCP/UDP connections
40
DNS requests
12
Threats
0
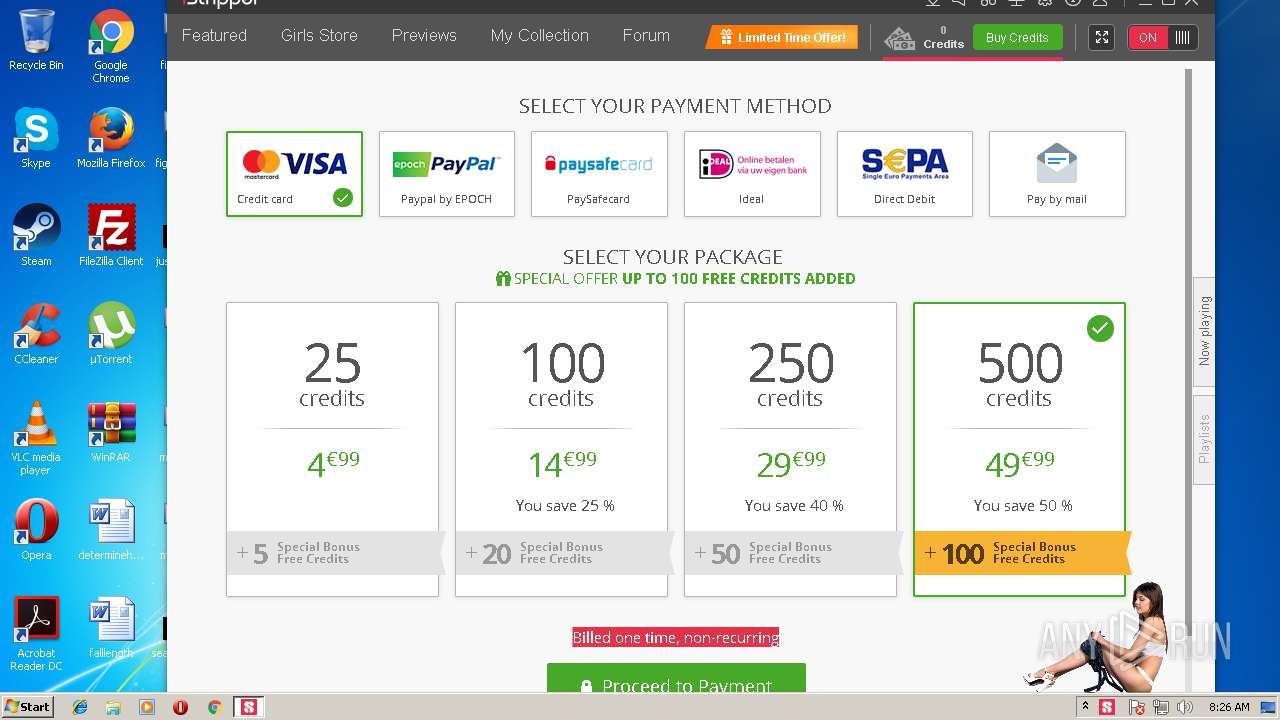
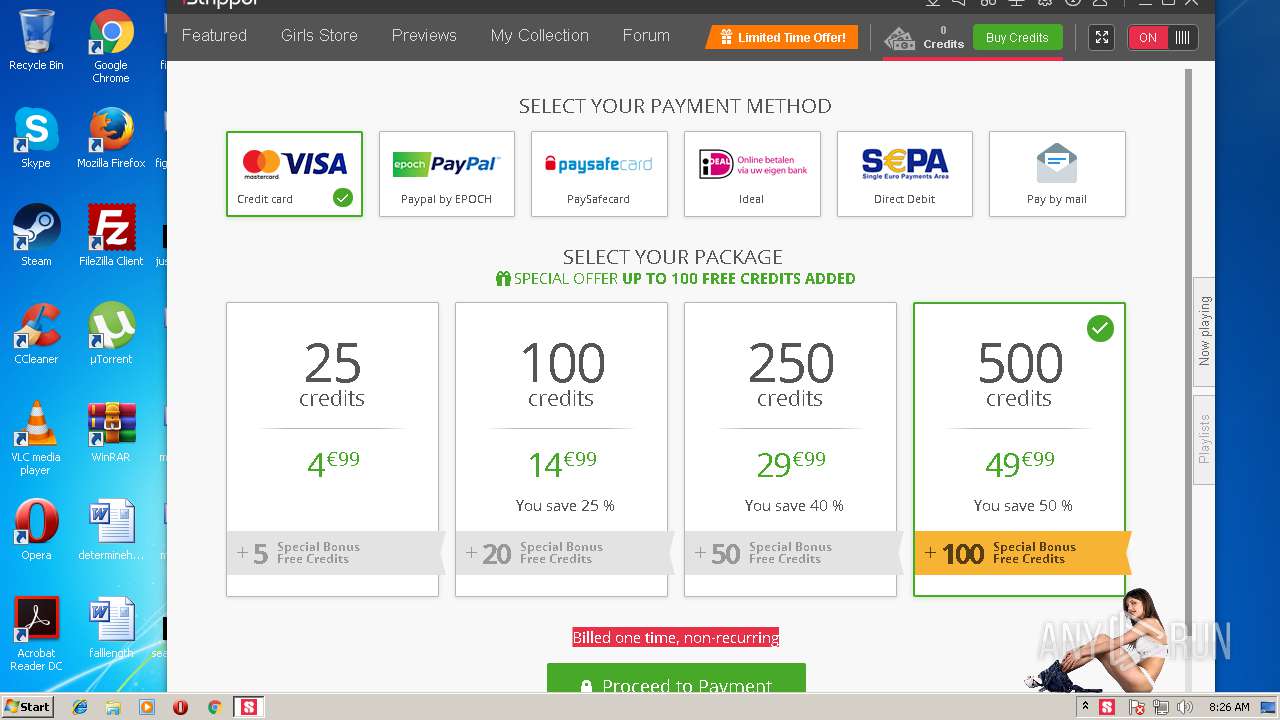
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3972 | vghd.exe | HEAD | 200 | 130.185.144.4:80 | http://www.istripper.com/bof/featuredEvents.htm | GB | text | 9 b | suspicious |
3972 | vghd.exe | POST | 200 | 130.185.144.4:80 | http://www.istripper.com/bof/askserver8.php | GB | text | 536 b | suspicious |
3972 | vghd.exe | GET | 200 | 104.25.71.114:80 | http://democdn.desktopware.com/e0925/e0925_it01_6144101.jar | US | binary | 2.46 Mb | suspicious |
3972 | vghd.exe | GET | 200 | 130.185.144.4:80 | http://www.istripper.com/bof/price/4_price.xml | GB | xml | 15.2 Kb | suspicious |
3972 | vghd.exe | GET | 200 | 104.25.71.114:80 | http://democdn.desktopware.com/e0925/e0925_9101.jar | US | binary | 6.21 Mb | suspicious |
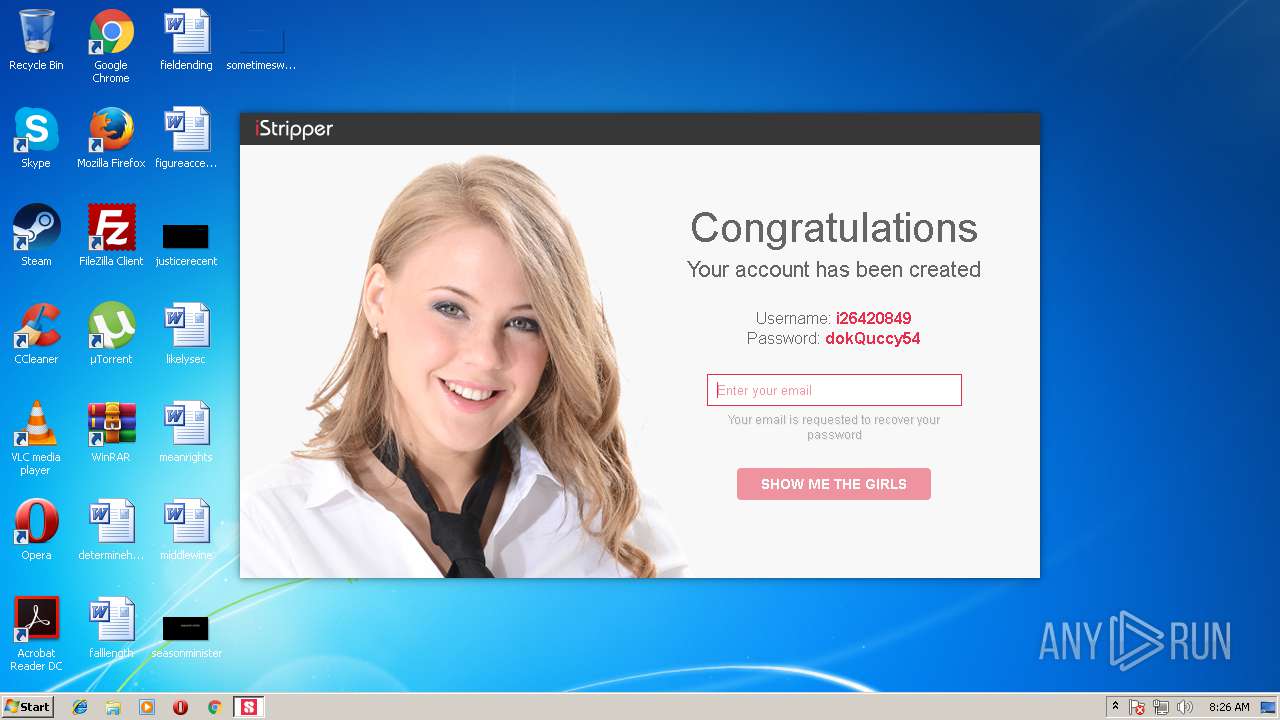
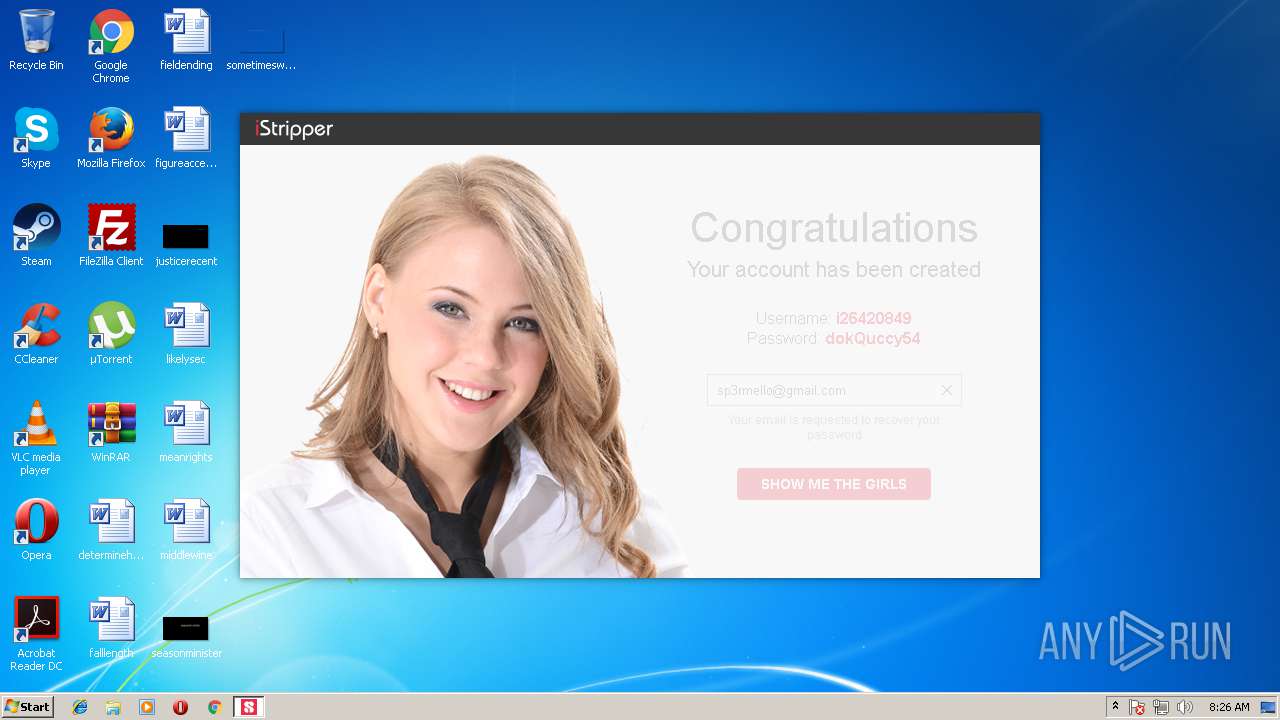
3972 | vghd.exe | GET | 200 | 130.185.144.4:80 | http://www.istripper.com/action/featured?uik=i26420849&explicit=1 | GB | text | 11.7 Kb | suspicious |
3972 | vghd.exe | GET | 200 | 130.185.144.4:80 | http://www.istripper.com/bof/properties/properties_iStripper.xml.gz | GB | compressed | 41.3 Kb | suspicious |
3972 | vghd.exe | GET | 200 | 130.185.144.4:80 | http://www.istripper.com/bof/mselistGenerator/staticProperties_iStripper.xml.gz | GB | compressed | 626 Kb | suspicious |
3972 | vghd.exe | GET | 200 | 104.25.71.114:80 | http://democdn.desktopware.com/e0925/e0925_4201.jar | US | binary | 6.64 Mb | suspicious |
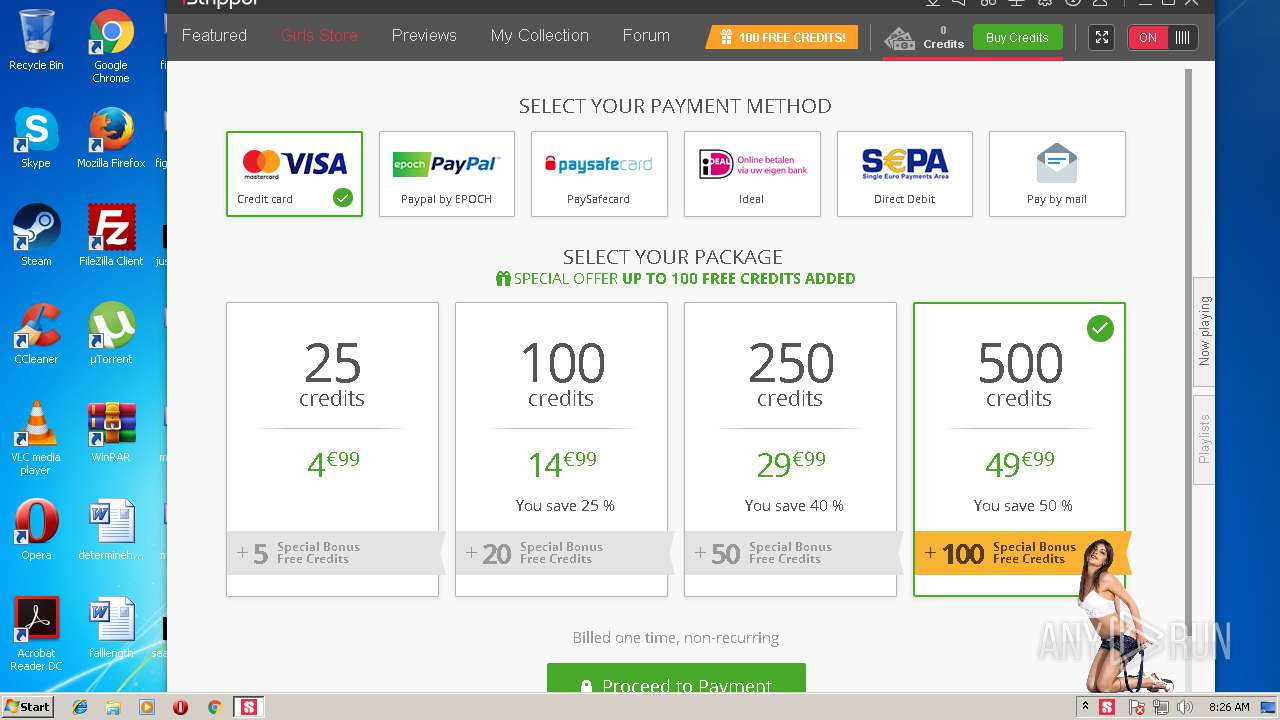
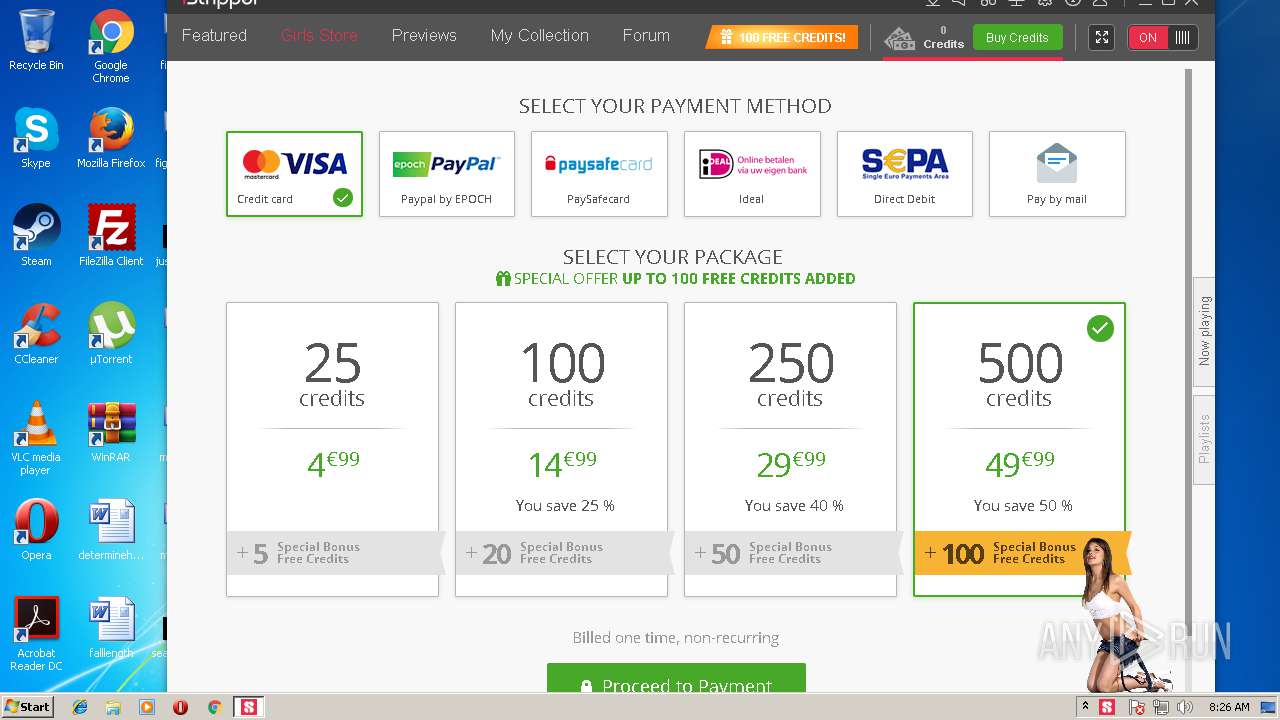
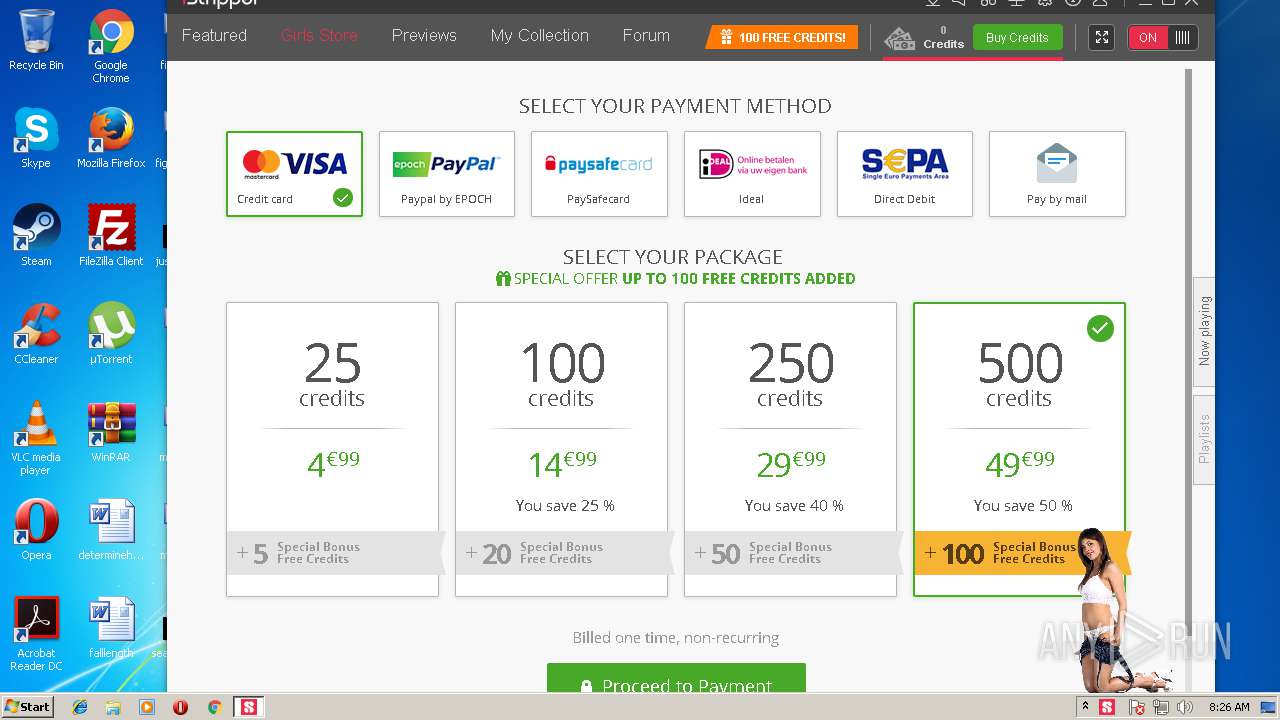
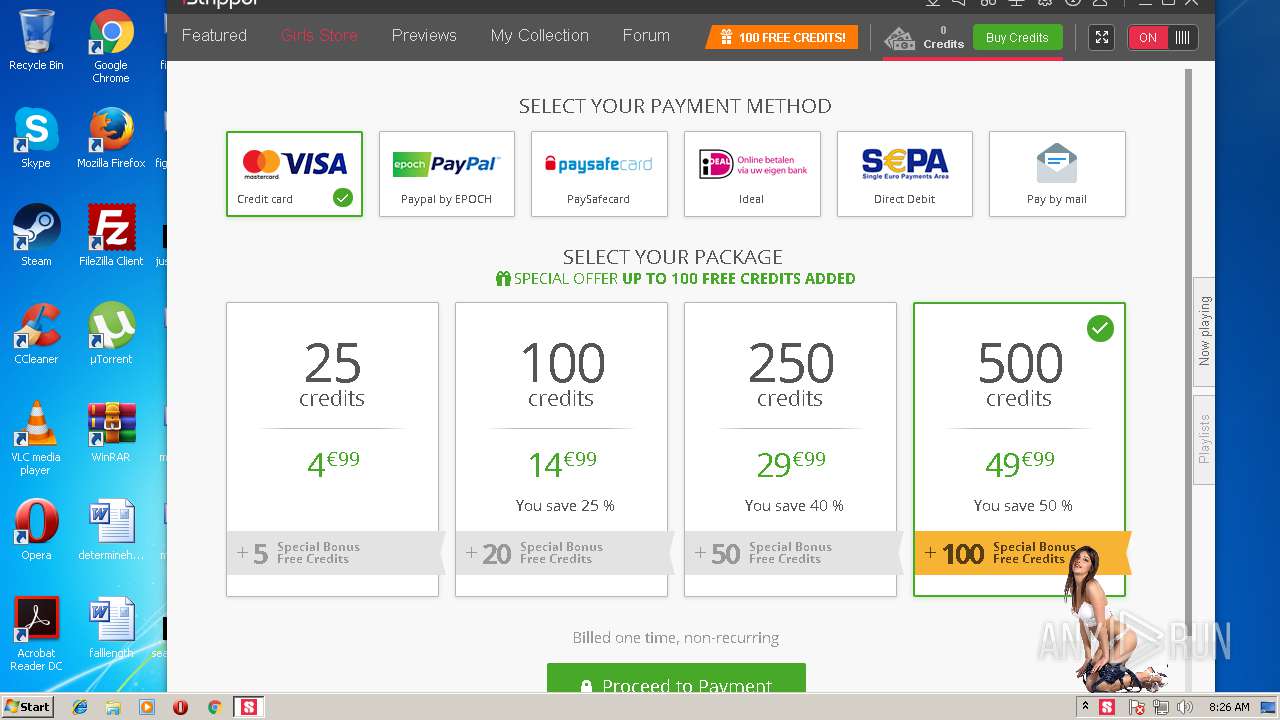
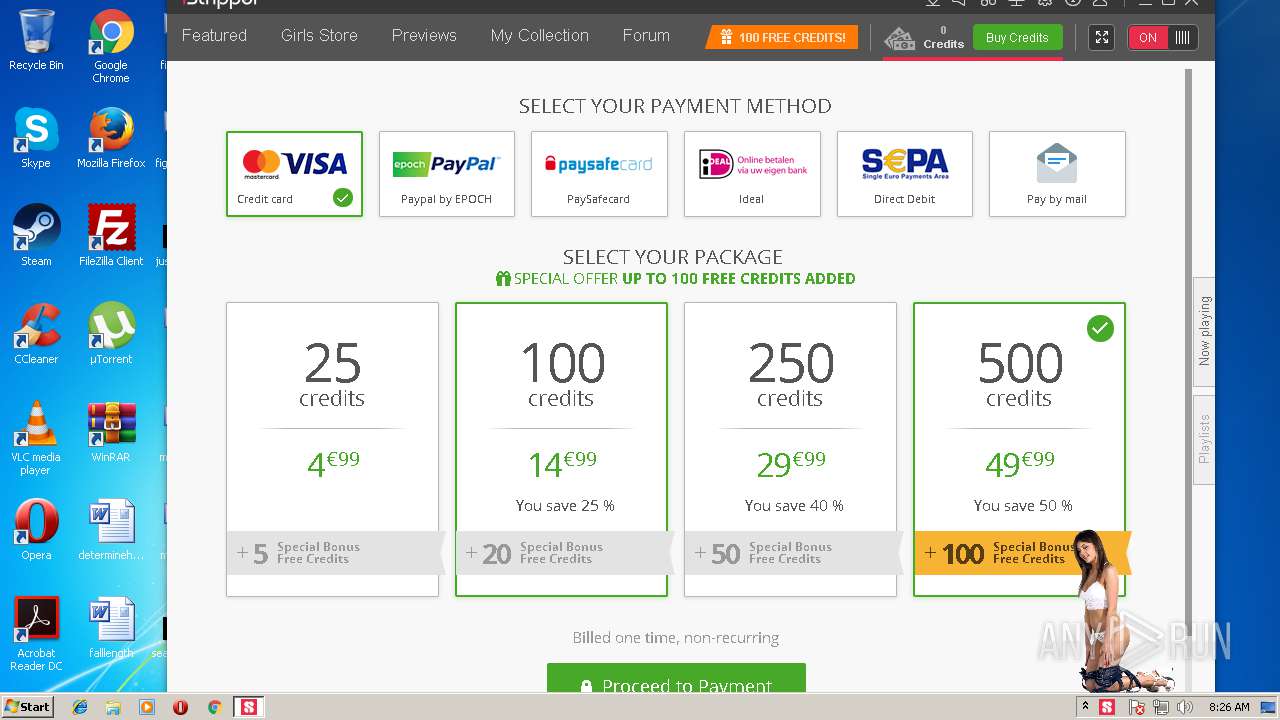
3972 | vghd.exe | GET | 200 | 130.185.144.4:80 | http://www.istripper.com/booster/versus/bikinisecretary?noreload=1&hew=1&ui=i26420849&uk=EGLELIPABNBBKJJEBCLLIAGMBLEBGBDN&explicit=1&language=en&sessionReset=1 | GB | html | 1.89 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3972 | vghd.exe | 130.185.144.60:443 | ws.istripper.com | iomart Cloud Services Limited. | GB | unknown |
3972 | vghd.exe | 192.35.177.64:80 | apps.identrust.com | IdenTrust | US | malicious |
3972 | vghd.exe | 130.185.144.4:80 | www.istripper.com | iomart Cloud Services Limited. | GB | unknown |
3972 | vghd.exe | 104.25.71.114:80 | democdn.desktopware.com | Cloudflare Inc | US | shared |
3972 | vghd.exe | 172.217.168.42:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3972 | vghd.exe | 172.217.168.14:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3972 | vghd.exe | 104.25.72.114:80 | democdn.desktopware.com | Cloudflare Inc | US | shared |
3972 | vghd.exe | 216.58.215.227:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3972 | vghd.exe | 104.16.84.55:80 | v2.zopim.com | Cloudflare Inc | US | shared |
3972 | vghd.exe | 108.177.127.154:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ws.istripper.com |
| unknown |
apps.identrust.com |
| shared |
www.istripper.com |
| suspicious |
democdn.desktopware.com |
| suspicious |
webcdn.desktopware.com |
| suspicious |
www.google-analytics.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
vhdp2p.actiondesk.com |
| unknown |
Threats
Process | Message |
|---|---|
vghd.exe | Qt version: 5.4.2
|
vghd.exe | Qt version: 5.4.2
|
vghd.exe | WebSocketSession::instance Benchmarked: 188.09 ms
|
vghd.exe | CVgMain::CVgMain Benchmarked: 233.90 ms
|
vghd.exe | Models Directories: ("C:\Users\admin\AppData\Local\vghd\models")
|
vghd.exe | QLocale default: "en_US" , system: "en_US"
|
vghd.exe | Skin Directories changed: ("C:\Users\admin\AppData\Local\vghd\data\skins/iStripper/basic")
|
vghd.exe | CardImageCache::instance Benchmarked: 39.24 ms
|
vghd.exe | network: SSL version: "OpenSSL 1.0.1j 15 Oct 2014"
|
vghd.exe | NetworkAccessManager::instance Benchmarked: 80.46 ms
|