| File name: | a la papa.exe |
| Full analysis: | https://app.any.run/tasks/732d7735-8dae-4821-b0bd-d7831d0ab423 |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 20:45:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B35DF0ED6EA0BD2309AC19A694549B57 |
| SHA1: | 5C36FA33FD543BA57825000213CF5135211901ED |
| SHA256: | 73D750B73164F55181EB2BD941741ADE0BD93739782CF9ED383A6A4A0F7702DA |
| SSDEEP: | 12288:jKyNTn2puBaFln3ZSfOvhNJZcc9Tv2IVbAsUGZs/Lu+JCeQ9UKoEJ3KLbI:jTTn2gQZrNJvHVbAsUGZs/LFCLoEYL0 |
MALICIOUS
Actions looks like stealing of personal data
- 7z.exe (PID: 2608)
- 7z.exe (PID: 1952)
- 7z.exe (PID: 1924)
- 7z.exe (PID: 2216)
Application was dropped or rewritten from another process
- 7z.exe (PID: 2608)
- 7z.exe (PID: 1952)
- 7z.exe (PID: 1924)
- 7z.exe (PID: 2216)
Loads dropped or rewritten executable
- 7z.exe (PID: 2608)
- 7z.exe (PID: 1952)
- 7z.exe (PID: 2216)
- 7z.exe (PID: 1924)
Deletes shadow copies
- cmd.exe (PID: 1576)
SUSPICIOUS
Creates files in the user directory
- a la papa.exe (PID: 2772)
Starts CMD.EXE for commands execution
- a la papa.exe (PID: 2772)
Executable content was dropped or overwritten
- a la papa.exe (PID: 2772)
Reads the cookies of Mozilla Firefox
- 7z.exe (PID: 2608)
- 7z.exe (PID: 1952)
- 7z.exe (PID: 1924)
- 7z.exe (PID: 2216)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:01 21:18:00+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 67584 |
| InitializedDataSize: | 717824 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Feb-2018 20:18:00 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Feb-2018 20:18:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x000037F0 | 0x00003800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.61236 |
.text | 0x00005000 | 0x0000CFA2 | 0x0000D000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58582 |
.rdata | 0x00012000 | 0x000033A0 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.11024 |
.data | 0x00016000 | 0x00001724 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.93668 |
.rsrc | 0x00018000 | 0x000AAC7C | 0x000AAE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99955 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.92322 | 611 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
12ED752D1CA2FABCC10C915380C64674 | 3.88418 | 20 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
4A834689CFA298752EDF72CBB03623CD23112EB4 | 7.99857 | 145633 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
5745ED58B96F88CE90F910CD399408AF | 7.57922 | 531 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
751070F0668E6F583B9519232CA6E9E5 | 6.41456 | 108 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
7825C31152 | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
95FCE43C09530D5CC562A5298410DE6058E8CCD5 | 7.70546 | 629 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
B7D0101E80432B0A6DDB78B68F2514E2D8A1D72A | 7.99966 | 550920 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
C6BAB4707723F7C39205C8C3F0A495F7D723B9AC | 2.58496 | 6 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.dll |
MSVCRT.dll |
OLE32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
USER32.DLL |
WINMM.DLL |
Total processes
39
Monitored processes
8
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1576 | "C:\Windows\system32\cmd.exe" /c "C:\Users\admin\AppData\Local\Temp\8A16.tmp\8A17.tmp\8A18.bat "C:\Users\admin\AppData\Local\Temp\a la papa.exe"" | C:\Windows\system32\cmd.exe | — | a la papa.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1924 | C:\Users\admin\AppData\Roaming\7z.exe a -p[!#RnNJpYQX-+#2GTGKy=e] -r C:\Users\admin\Documents | C:\Users\admin\AppData\Roaming\7z.exe | cmd.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Console Exit code: 0 Version: 16.02 Modules
| |||||||||||||||
| 1952 | C:\Users\admin\AppData\Roaming\7z.exe a -p[!#RnNJpYQX-+#2GTGKy=e] -r C:\Users\admin\Downloads | C:\Users\admin\AppData\Roaming\7z.exe | cmd.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Console Exit code: 0 Version: 16.02 Modules
| |||||||||||||||
| 2216 | C:\Users\admin\AppData\Roaming\7z.exe a -p[!#RnNJpYQX-+#2GTGKy=e] -r C:\Users\admin\Pictures | C:\Users\admin\AppData\Roaming\7z.exe | cmd.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Console Exit code: 0 Version: 16.02 Modules
| |||||||||||||||
| 2268 | wmic shadowcopy delete | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2608 | C:\Users\admin\AppData\Roaming\7z.exe a -p[!#RnNJpYQX-+#2GTGKy=e] -r C:\Users\admin\Desktop | C:\Users\admin\AppData\Roaming\7z.exe | cmd.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Console Exit code: 0 Version: 16.02 Modules
| |||||||||||||||
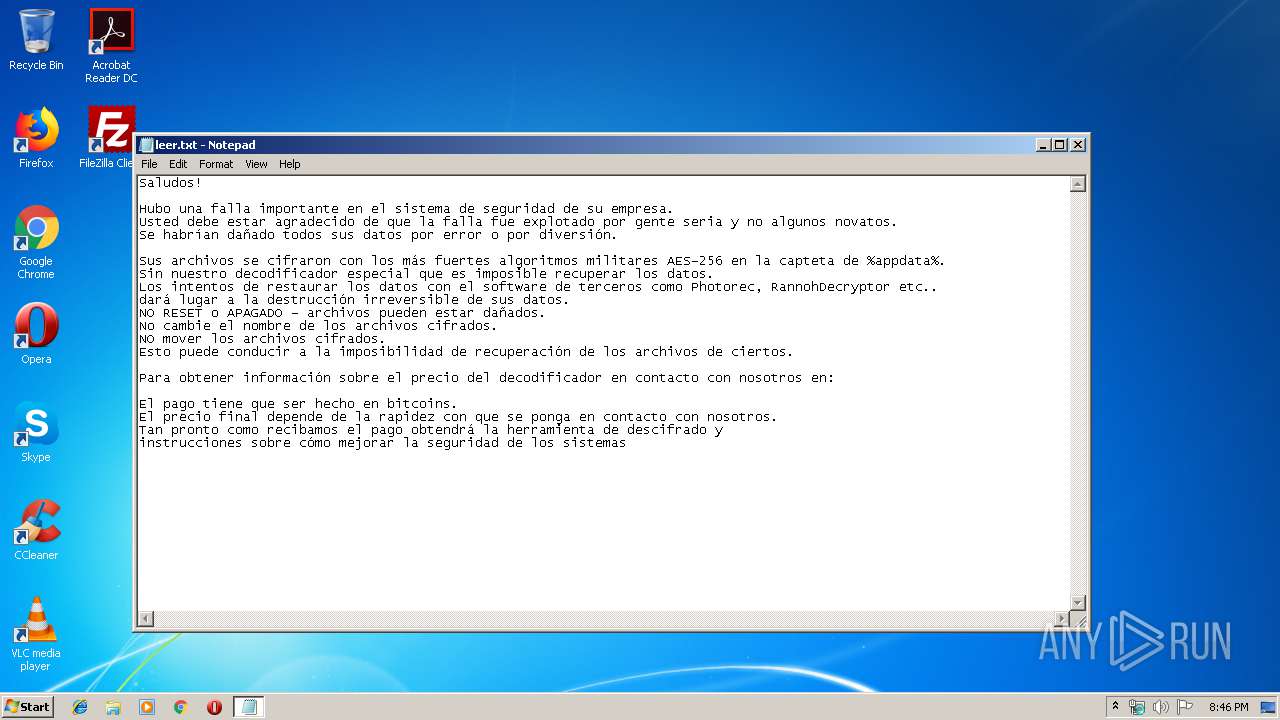
| 2716 | notepad C:\Users\admin\AppData\Roaming\leer.txt | C:\Windows\system32\notepad.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2772 | "C:\Users\admin\AppData\Local\Temp\a la papa.exe" | C:\Users\admin\AppData\Local\Temp\a la papa.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
71
Read events
67
Write events
4
Delete events
0
Modification events
| (PID) Process: | (2772) a la papa.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2772) a la papa.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2608 | 7z.exe | C:\Users\admin\Desktop.7z | — | |
MD5:— | SHA256:— | |||
| 1952 | 7z.exe | C:\Users\admin\Downloads.7z | — | |
MD5:— | SHA256:— | |||
| 1924 | 7z.exe | C:\Users\admin\Documents.7z | — | |
MD5:— | SHA256:— | |||
| 2216 | 7z.exe | C:\Users\admin\Pictures.7z | — | |
MD5:— | SHA256:— | |||
| 2772 | a la papa.exe | C:\Users\admin\AppData\Local\Temp\8A16.tmp\8A17.tmp\8A18.bat | text | |
MD5:— | SHA256:— | |||
| 2772 | a la papa.exe | C:\Users\admin\AppData\Roaming\leer.txt | text | |
MD5:— | SHA256:— | |||
| 2772 | a la papa.exe | C:\Users\admin\AppData\Roaming\7z.exe | executable | |
MD5:A10BF0E8D40B78C8B0B43A6A6FED9207 | SHA256:3D921CC9C553941D646C34CC6A79259E530C4A7652ABCDD4B680E923F45090F6 | |||
| 2772 | a la papa.exe | C:\Users\admin\AppData\Roaming\7z.dll | executable | |
MD5:20005925D98D1A31E2940337AEC9AFC0 | SHA256:AB35D0798F0548FA4C55EA14A4E129372BAF01B1FF3DA5BFD5CDD55FE72D1F1E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report