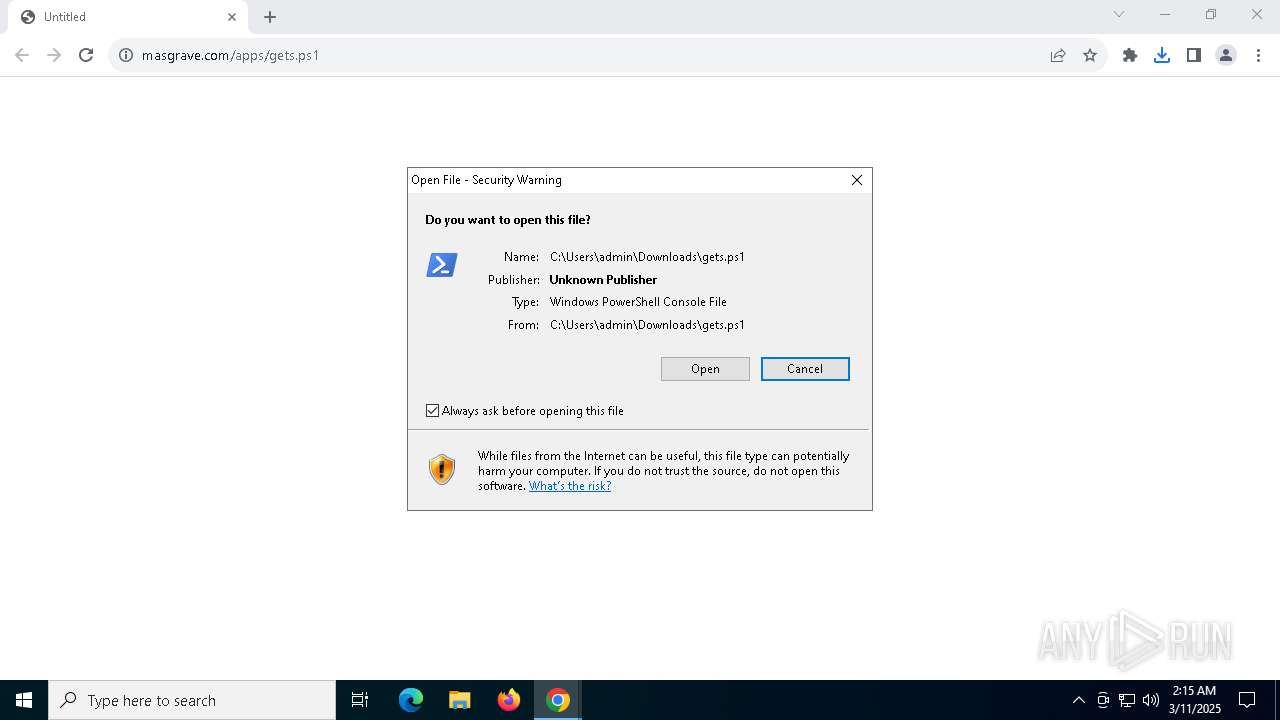
| URL: | https://masgrave.com/apps/gets.ps1 |
| Full analysis: | https://app.any.run/tasks/3a9ecd60-b3d8-416e-b98f-f8d6969bd25e |
| Verdict: | Malicious activity |
| Analysis date: | March 11, 2025, 02:15:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9D2BD6F7BBF3790103D71F33408FFE0A |
| SHA1: | 50BCA3CEABD03A2ED6B56CBC24CFEC25EE5A512A |
| SHA256: | 73D67DF5E9DA7C4744A46EA2B79FD2ED5A0C514425BAD4622853B2E7677F0C30 |
| SSDEEP: | 3:N8aKKfaLF:2aKiaLF |
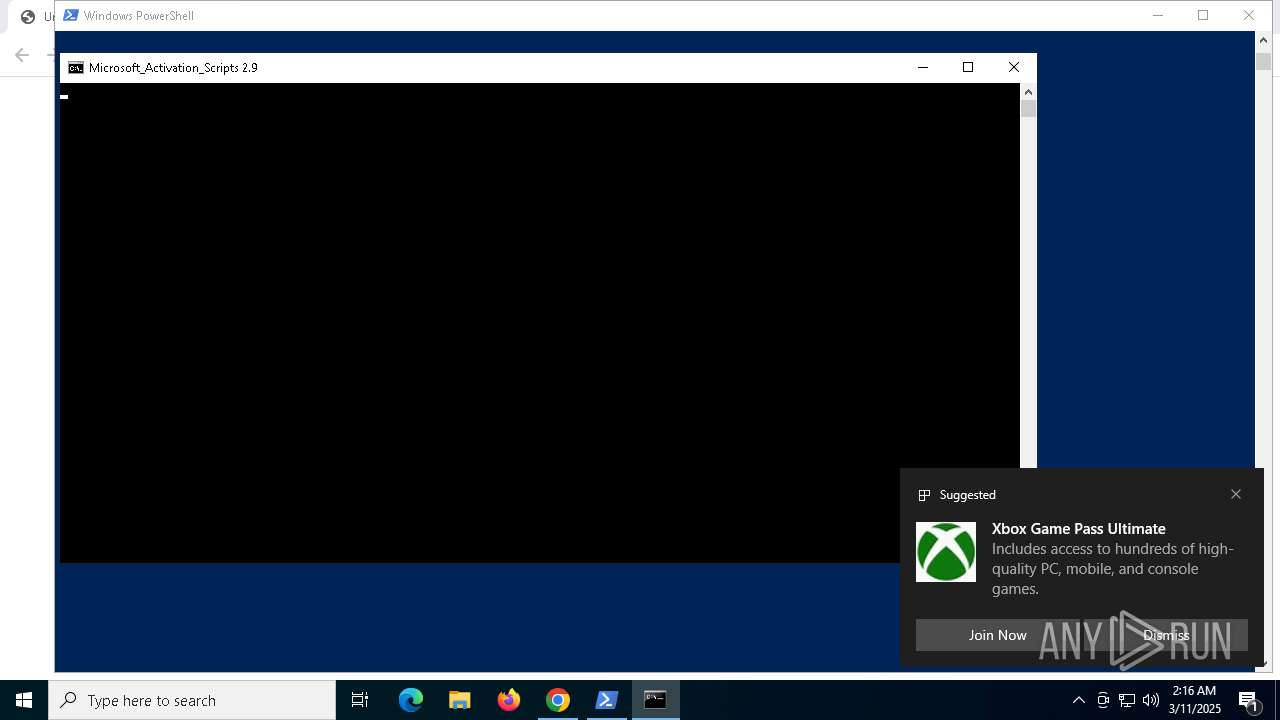
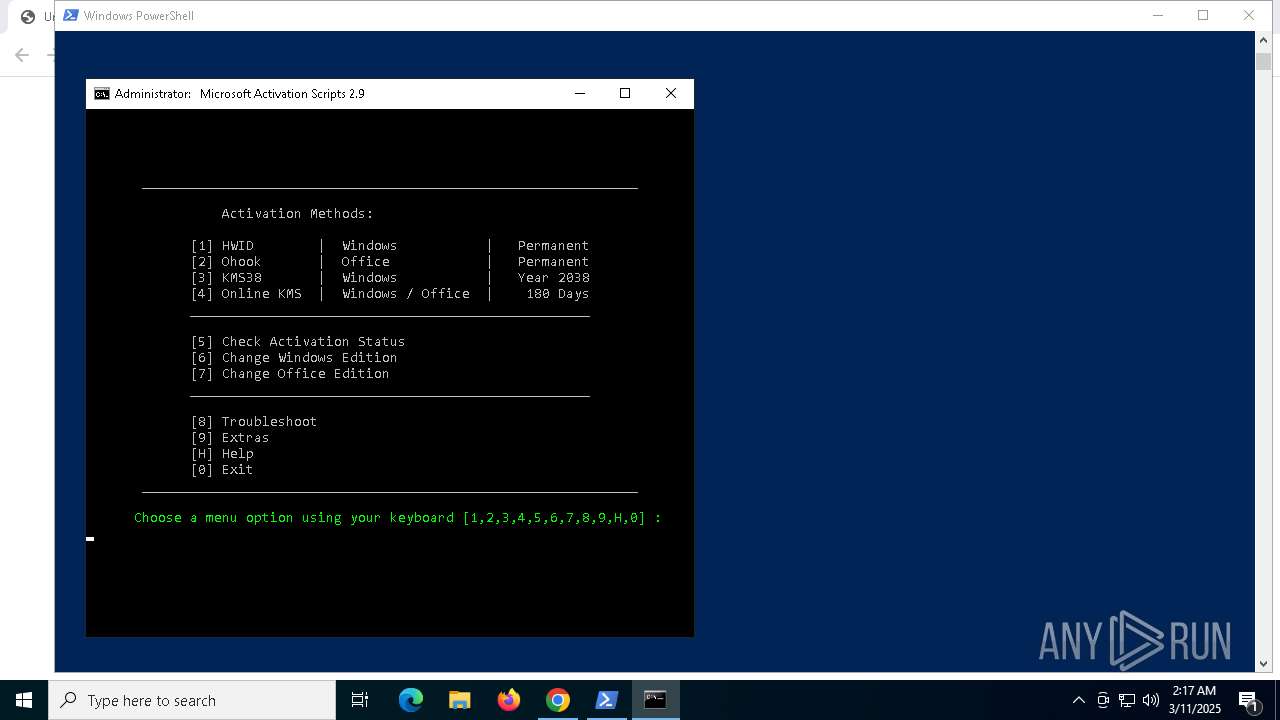
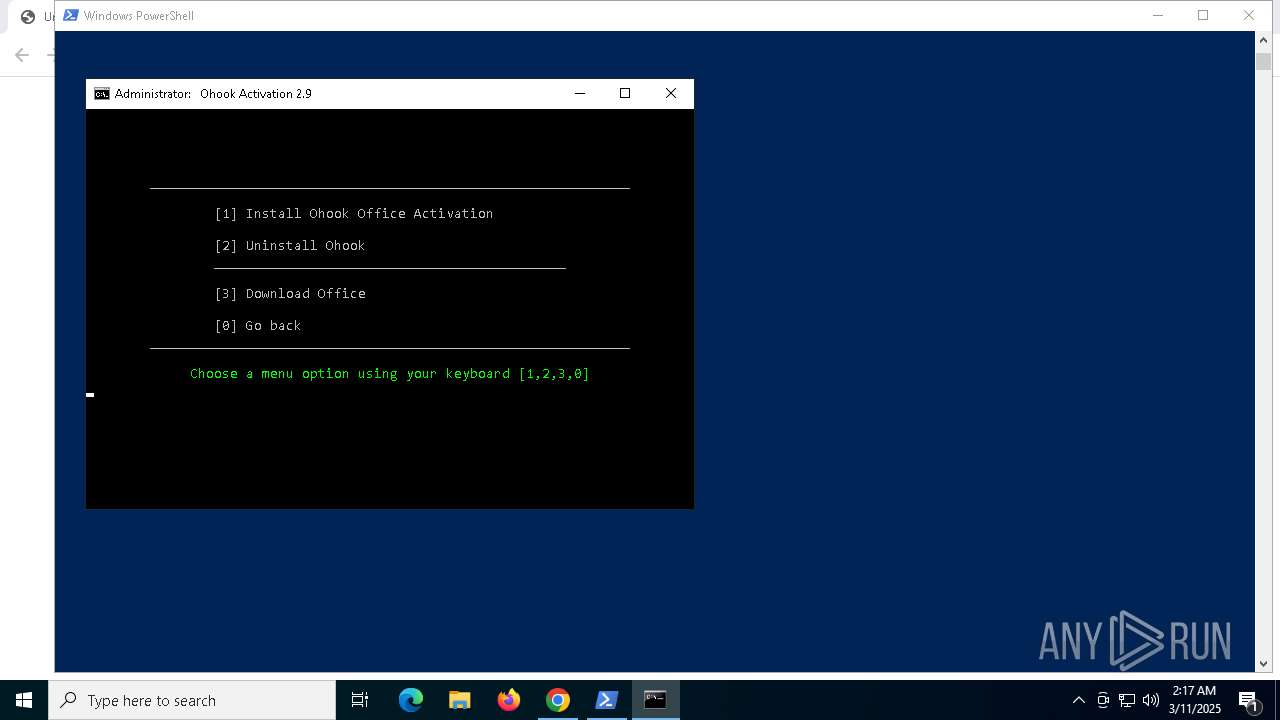
MALICIOUS
Starts POWERSHELL.EXE for commands execution
- chrome.exe (PID: 1276)
Changes powershell execution policy (Bypass)
- chrome.exe (PID: 1276)
- cmd.exe (PID: 7844)
- cmd.exe (PID: 5436)
Bypass execution policy to execute commands
- powershell.exe (PID: 7820)
- powershell.exe (PID: 2088)
- powershell.exe (PID: 8000)
Disables Windows Defender
- regedit.exe (PID: 6436)
Create files in the Startup directory
- powershell.exe (PID: 7820)
Changes the autorun value in the registry
- VC_redist.x86.exe (PID: 7800)
SUSPICIOUS
The process executes Powershell scripts
- chrome.exe (PID: 1276)
- powershell.exe (PID: 7820)
- cmd.exe (PID: 7844)
- powershell.exe (PID: 2088)
- cmd.exe (PID: 5436)
Uses REG/REGEDIT.EXE to modify registry
- powershell.exe (PID: 7820)
- cmd.exe (PID: 8460)
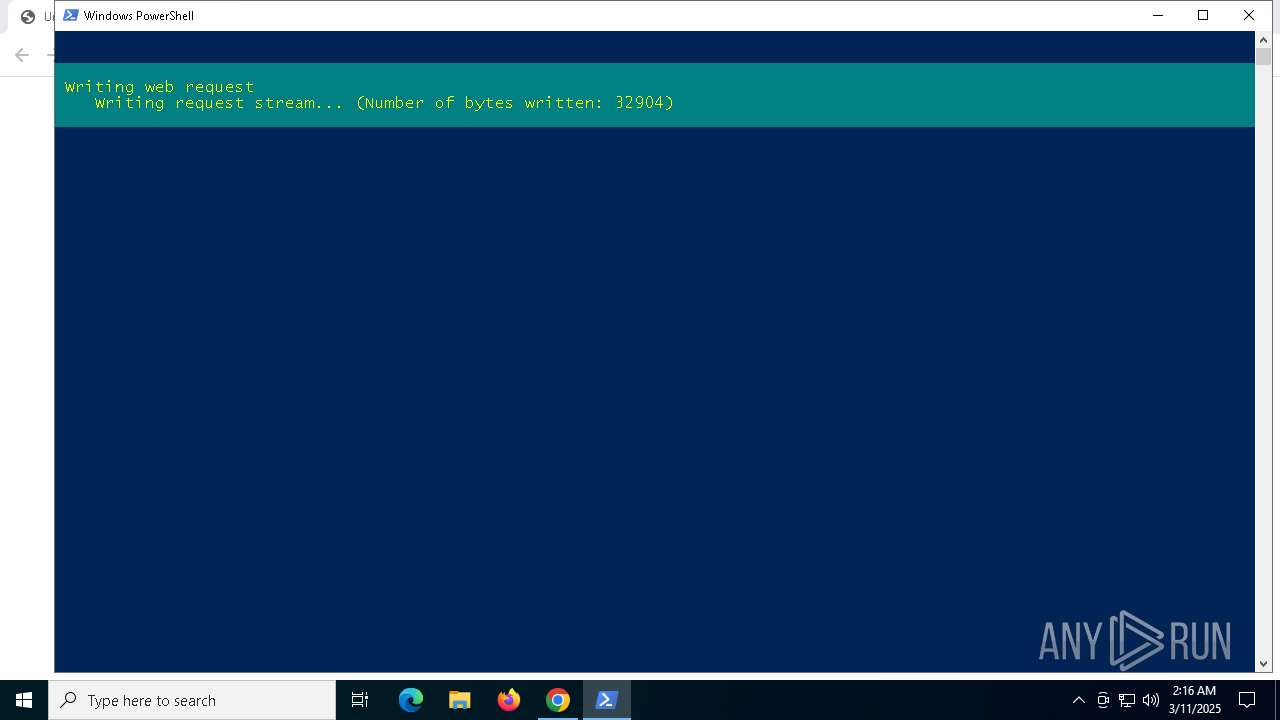
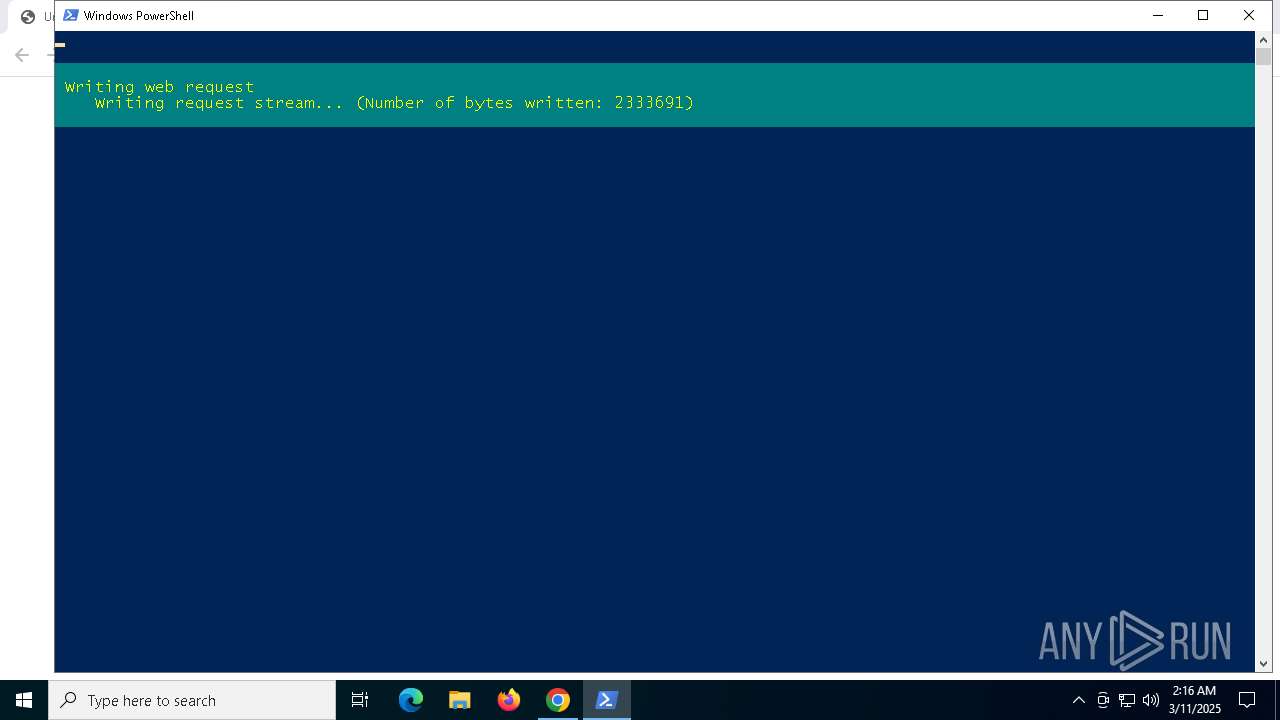
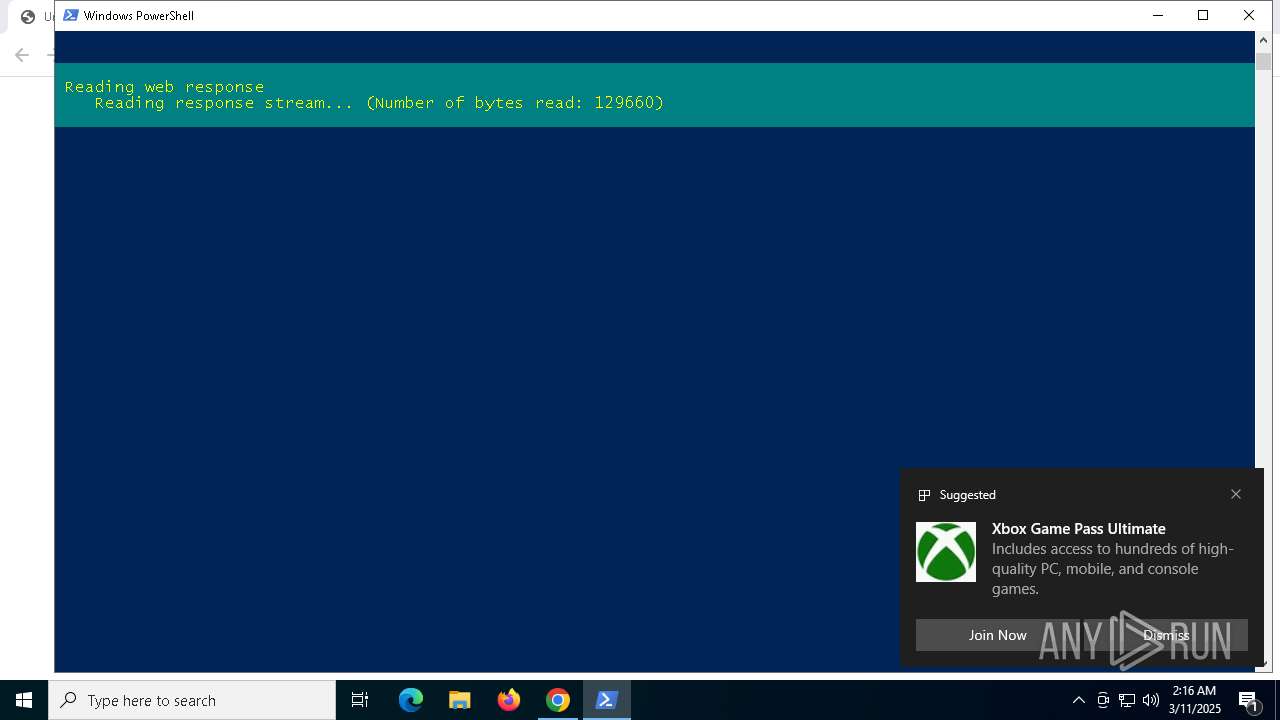
Downloads file from URI via Powershell
- powershell.exe (PID: 7964)
- powershell.exe (PID: 5360)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 7820)
- cmd.exe (PID: 7844)
- powershell.exe (PID: 2088)
- cmd.exe (PID: 5436)
- cmd.exe (PID: 7084)
- cmd.exe (PID: 8044)
- cmd.exe (PID: 7556)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 8788)
- cmd.exe (PID: 8460)
- cmd.exe (PID: 4024)
- powershell.exe (PID: 6876)
- cmd.exe (PID: 5324)
- cmd.exe (PID: 8660)
Application launched itself
- powershell.exe (PID: 7820)
- powershell.exe (PID: 2088)
- VC_redist.x86.exe (PID: 8096)
- VC_redist.x86.exe (PID: 4452)
- cmd.exe (PID: 8044)
- cmd.exe (PID: 5324)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 6416)
- cmd.exe (PID: 8460)
- cmd.exe (PID: 8680)
- powershell.exe (PID: 6876)
The process executes VB scripts
- cmd.exe (PID: 7944)
- cmd.exe (PID: 6228)
Starts CMD.EXE for commands execution
- cscript.exe (PID: 8112)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 2088)
- cscript.exe (PID: 6652)
- cmd.exe (PID: 8044)
- cmd.exe (PID: 5324)
- powershell.exe (PID: 3760)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 6416)
- powershell.exe (PID: 8364)
- cmd.exe (PID: 8680)
- cmd.exe (PID: 8460)
Runs shell command (SCRIPT)
- cscript.exe (PID: 8112)
- cscript.exe (PID: 6652)
Executing commands from a ".bat" file
- powershell.exe (PID: 7820)
- powershell.exe (PID: 2088)
Executable content was dropped or overwritten
- powershell.exe (PID: 7820)
- vc_redist.x86.exe (PID: 1676)
- vc_redist.x86.exe (PID: 6656)
- VC_redist.x86.exe (PID: 4452)
- VC_redist.x86.exe (PID: 6668)
- VC_redist.x86.exe (PID: 7800)
- powershell.exe (PID: 8000)
Process drops legitimate windows executable
- powershell.exe (PID: 7820)
- vc_redist.x86.exe (PID: 1676)
- vc_redist.x86.exe (PID: 6656)
- msiexec.exe (PID: 5228)
- VC_redist.x86.exe (PID: 6668)
- VC_redist.x86.exe (PID: 7800)
Searches for installed software
- vc_redist.x86.exe (PID: 6656)
- dllhost.exe (PID: 7516)
- VC_redist.x86.exe (PID: 6668)
- VC_redist.x86.exe (PID: 4452)
Starts a Microsoft application from unusual location
- vc_redist.x86.exe (PID: 6656)
- VC_redist.x86.exe (PID: 7800)
Starts itself from another location
- vc_redist.x86.exe (PID: 6656)
Reads security settings of Internet Explorer
- vc_redist.x86.exe (PID: 6656)
- VC_redist.x86.exe (PID: 4452)
- ShellExperienceHost.exe (PID: 928)
- Enigma32g.exe (PID: 7844)
Executes as Windows Service
- VSSVC.exe (PID: 7396)
Creates a software uninstall entry
- VC_redist.x86.exe (PID: 7800)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5228)
The process drops C-runtime libraries
- msiexec.exe (PID: 5228)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 7544)
- powershell.exe (PID: 2800)
- powershell.exe (PID: 8820)
- powershell.exe (PID: 1132)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7820)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 7544)
- powershell.exe (PID: 2800)
- powershell.exe (PID: 8820)
- powershell.exe (PID: 1132)
Executing commands from ".cmd" file
- powershell.exe (PID: 7820)
- cmd.exe (PID: 8044)
- powershell.exe (PID: 3760)
- cmd.exe (PID: 8068)
- powershell.exe (PID: 8364)
- cmd.exe (PID: 8460)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 8044)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 8460)
- cmd.exe (PID: 8604)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 7820)
Starts SC.EXE for service management
- cmd.exe (PID: 8044)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 8460)
Windows service management via SC.EXE
- sc.exe (PID: 6436)
- sc.exe (PID: 5044)
- sc.exe (PID: 8476)
- sc.exe (PID: 8324)
- sc.exe (PID: 8120)
- sc.exe (PID: 8776)
- sc.exe (PID: 9140)
- sc.exe (PID: 5416)
- sc.exe (PID: 6632)
- sc.exe (PID: 8888)
- sc.exe (PID: 6940)
- sc.exe (PID: 9156)
- sc.exe (PID: 8964)
- sc.exe (PID: 7748)
- sc.exe (PID: 9176)
- sc.exe (PID: 7528)
- sc.exe (PID: 5864)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 7084)
- cmd.exe (PID: 7556)
- cmd.exe (PID: 8788)
- cmd.exe (PID: 5324)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 7084)
- cmd.exe (PID: 7556)
- cmd.exe (PID: 8788)
- cmd.exe (PID: 5324)
Get information on the list of running processes
- cmd.exe (PID: 8604)
- cmd.exe (PID: 8460)
Hides command output
- cmd.exe (PID: 8604)
- cmd.exe (PID: 5324)
- cmd.exe (PID: 7476)
- cmd.exe (PID: 3896)
- cmd.exe (PID: 5960)
- cmd.exe (PID: 8660)
- cmd.exe (PID: 8484)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 4220)
- cmd.exe (PID: 8460)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 6876)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 6876)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 8000)
Reads the BIOS version
- Enigma32g.exe (PID: 7844)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 7476)
- cmd.exe (PID: 8484)
INFO
Reads Microsoft Office registry keys
- chrome.exe (PID: 1276)
Application launched itself
- chrome.exe (PID: 1276)
- msedge.exe (PID: 8120)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 8084)
- BackgroundTransferHost.exe (PID: 6048)
- BackgroundTransferHost.exe (PID: 4188)
- BackgroundTransferHost.exe (PID: 8088)
- BackgroundTransferHost.exe (PID: 7256)
- cscript.exe (PID: 8112)
- cscript.exe (PID: 6652)
- WMIC.exe (PID: 7932)
- WMIC.exe (PID: 4844)
- WMIC.exe (PID: 5728)
- WMIC.exe (PID: 6824)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 6048)
- msiexec.exe (PID: 5228)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 6048)
- msiexec.exe (PID: 5228)
- slui.exe (PID: 7720)
- slui.exe (PID: 1272)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 6048)
- powershell.exe (PID: 7964)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 5360)
- powershell.exe (PID: 8000)
- slui.exe (PID: 1272)
Disables trace logs
- powershell.exe (PID: 7964)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 5360)
- powershell.exe (PID: 8000)
The executable file from the user directory is run by the Powershell process
- vc_redist.x86.exe (PID: 1676)
- Enigma32g.exe (PID: 7844)
Checks supported languages
- vc_redist.x86.exe (PID: 1676)
- vc_redist.x86.exe (PID: 6656)
- VC_redist.x86.exe (PID: 7800)
- msiexec.exe (PID: 5228)
- VC_redist.x86.exe (PID: 8096)
- VC_redist.x86.exe (PID: 4452)
- VC_redist.x86.exe (PID: 6668)
- ShellExperienceHost.exe (PID: 928)
- mode.com (PID: 5776)
- mode.com (PID: 5720)
- mode.com (PID: 7764)
- Enigma32g.exe (PID: 7844)
- identity_helper.exe (PID: 6404)
The sample compiled with english language support
- powershell.exe (PID: 7820)
- vc_redist.x86.exe (PID: 1676)
- vc_redist.x86.exe (PID: 6656)
- msiexec.exe (PID: 5228)
- VC_redist.x86.exe (PID: 4452)
- VC_redist.x86.exe (PID: 6668)
- VC_redist.x86.exe (PID: 7800)
- chrome.exe (PID: 8180)
- powershell.exe (PID: 8000)
Create files in a temporary directory
- vc_redist.x86.exe (PID: 1676)
- vc_redist.x86.exe (PID: 6656)
- VC_redist.x86.exe (PID: 7800)
- VC_redist.x86.exe (PID: 4452)
Reads the computer name
- vc_redist.x86.exe (PID: 6656)
- VC_redist.x86.exe (PID: 7800)
- VC_redist.x86.exe (PID: 4452)
- VC_redist.x86.exe (PID: 6668)
- ShellExperienceHost.exe (PID: 928)
- msiexec.exe (PID: 5228)
- Enigma32g.exe (PID: 7844)
- identity_helper.exe (PID: 6404)
Process checks computer location settings
- vc_redist.x86.exe (PID: 6656)
- VC_redist.x86.exe (PID: 4452)
Manages system restore points
- SrTasks.exe (PID: 2332)
Reads the machine GUID from the registry
- VC_redist.x86.exe (PID: 7800)
- msiexec.exe (PID: 5228)
Creates a software uninstall entry
- msiexec.exe (PID: 5228)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5228)
- chrome.exe (PID: 8180)
Creates files in the program directory
- VC_redist.x86.exe (PID: 7800)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 7544)
- powershell.exe (PID: 2800)
- powershell.exe (PID: 8820)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 1132)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 7544)
- powershell.exe (PID: 2800)
- powershell.exe (PID: 8820)
- powershell.exe (PID: 1132)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 7544)
- powershell.exe (PID: 2800)
- powershell.exe (PID: 8820)
- powershell.exe (PID: 1132)
Checks operating system version
- cmd.exe (PID: 8044)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 8460)
Starts MODE.COM to configure console settings
- mode.com (PID: 5776)
- mode.com (PID: 5720)
- mode.com (PID: 7764)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 8640)
Reads Environment values
- identity_helper.exe (PID: 6404)
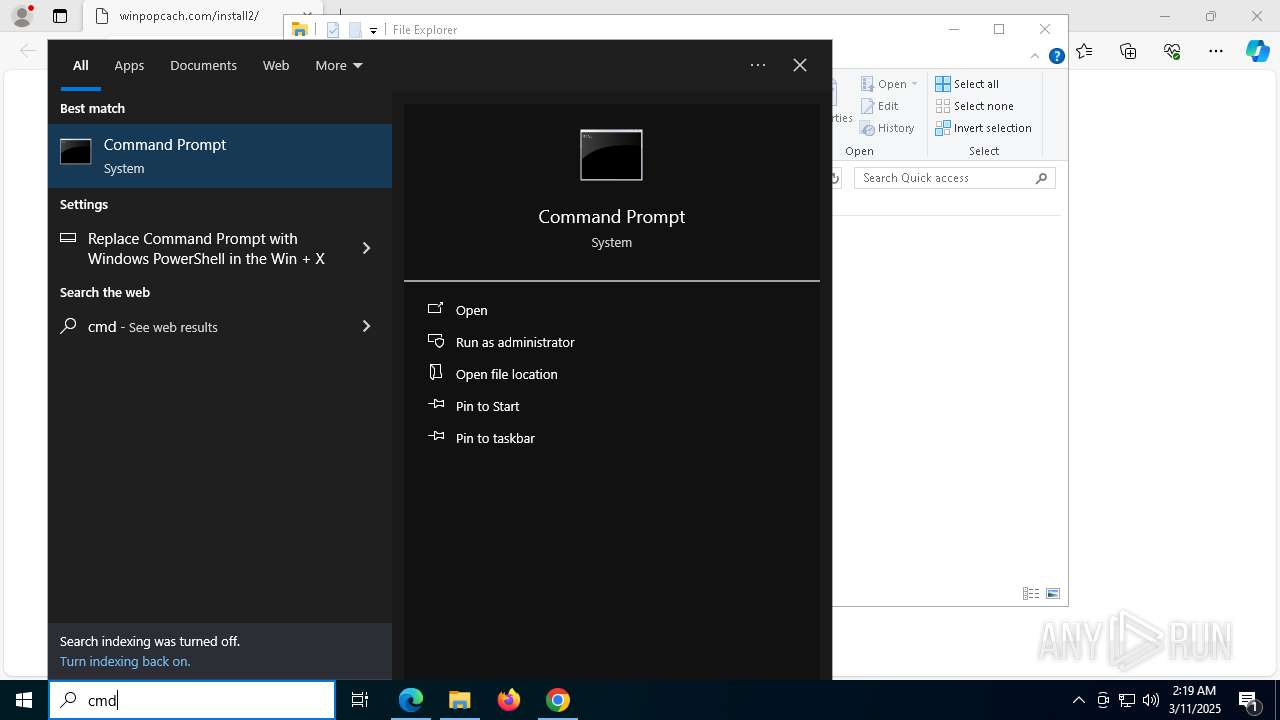
Manual execution by a user
- cmd.exe (PID: 8468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
442
Monitored processes
289
Malicious processes
16
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 540 | find /i "computersystem" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | powershell.exe "&{$W=$Host.UI.RawUI.WindowSize;$B=$Host.UI.RawUI.BufferSize;$W.Height=32;$B.Height=300;$Host.UI.RawUI.WindowSize=$W;$Host.UI.RawUI.BufferSize=$B;}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | find /i "/S" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | find /i "AutoPico" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | reg query "HKU\S-1-5-20\Software\Microsoft\Windows NT\CurrentVersion" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 928 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | powershell.exe "$f=[io.file]::ReadAllText('C:\Users\admin\AppData\Local\Temp\MAS_a4638f81-947b-4b69-beab-997ac6873a1a.cmd') -split ':wpatest\:.*';iex ($f[1])" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1272 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://masgrave.com/apps/gets.ps1" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1388 | find /i "ARM64" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
127 941
Read events
127 003
Write events
669
Delete events
269
Modification events
| (PID) Process: | (1276) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1276) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1276) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1276) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1276) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7756) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000CE565B802B92DB01 | |||
| (PID) Process: | (1276) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.ps1\OpenWithProgids |
| Operation: | write | Name: | Microsoft.PowerShellConsole.1 |
Value: | |||
| (PID) Process: | (8084) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8084) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (8084) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
83
Suspicious files
464
Text files
184
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10c640.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10c64f.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c64f.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c64f.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c64f.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10c64f.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
84
DNS requests
85
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7268 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6048 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
8080 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8080 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5228 | msiexec.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5084 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
5228 | msiexec.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
5084 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
5084 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7192 | chrome.exe | 185.255.122.94:443 | masgrave.com | — | GB | unknown |
1276 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7192 | chrome.exe | 142.250.110.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
6544 | svchost.exe | 20.190.160.65:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7192 | chrome.exe | 216.58.206.78:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
masgrave.com |
| unknown |
accounts.google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |