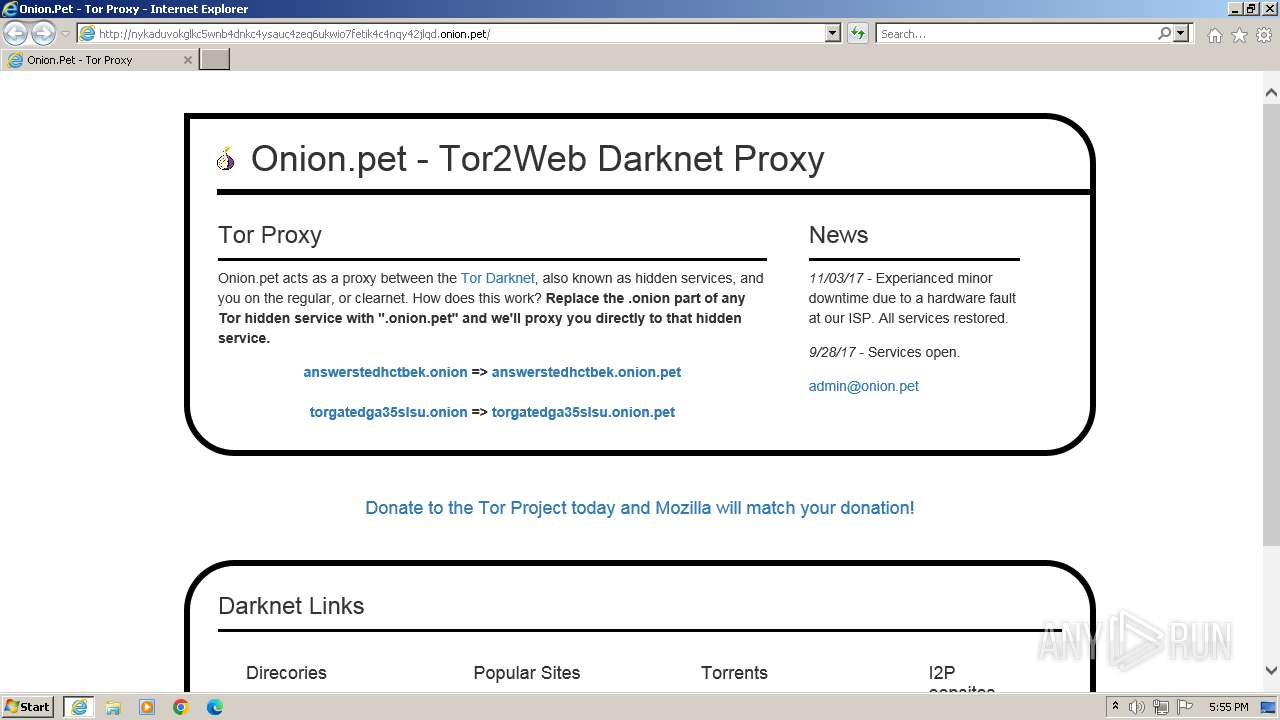
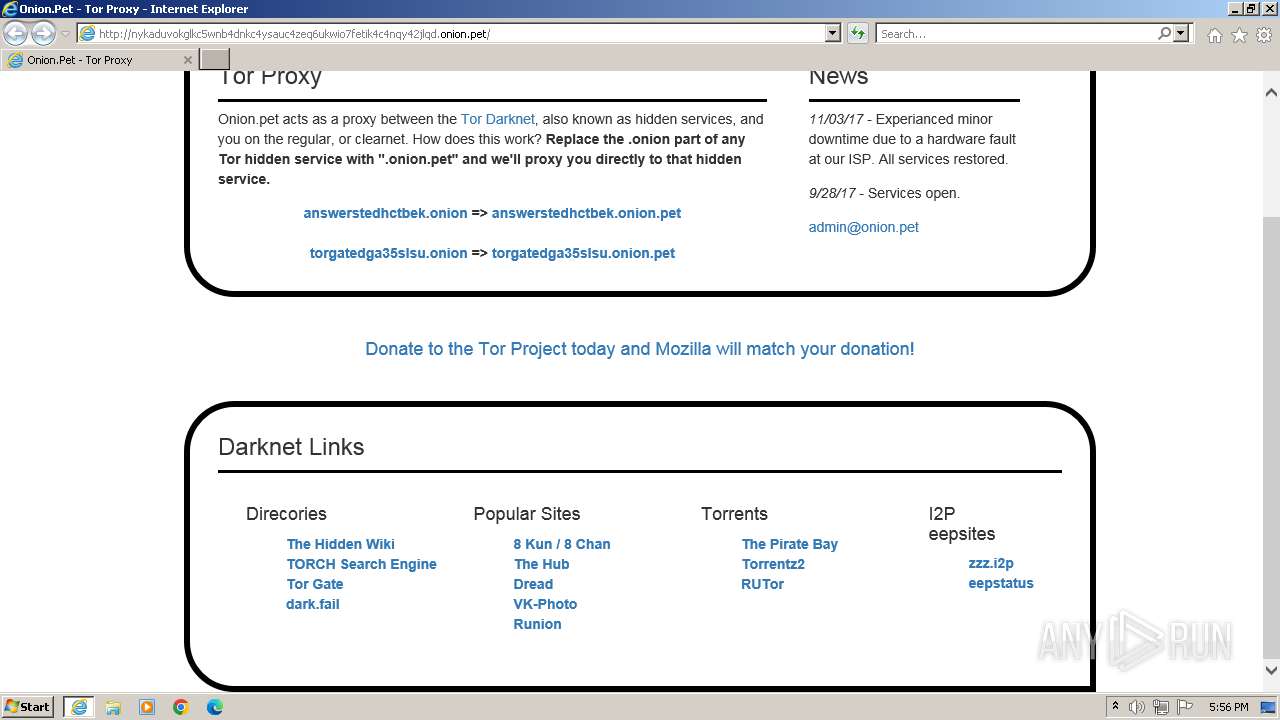
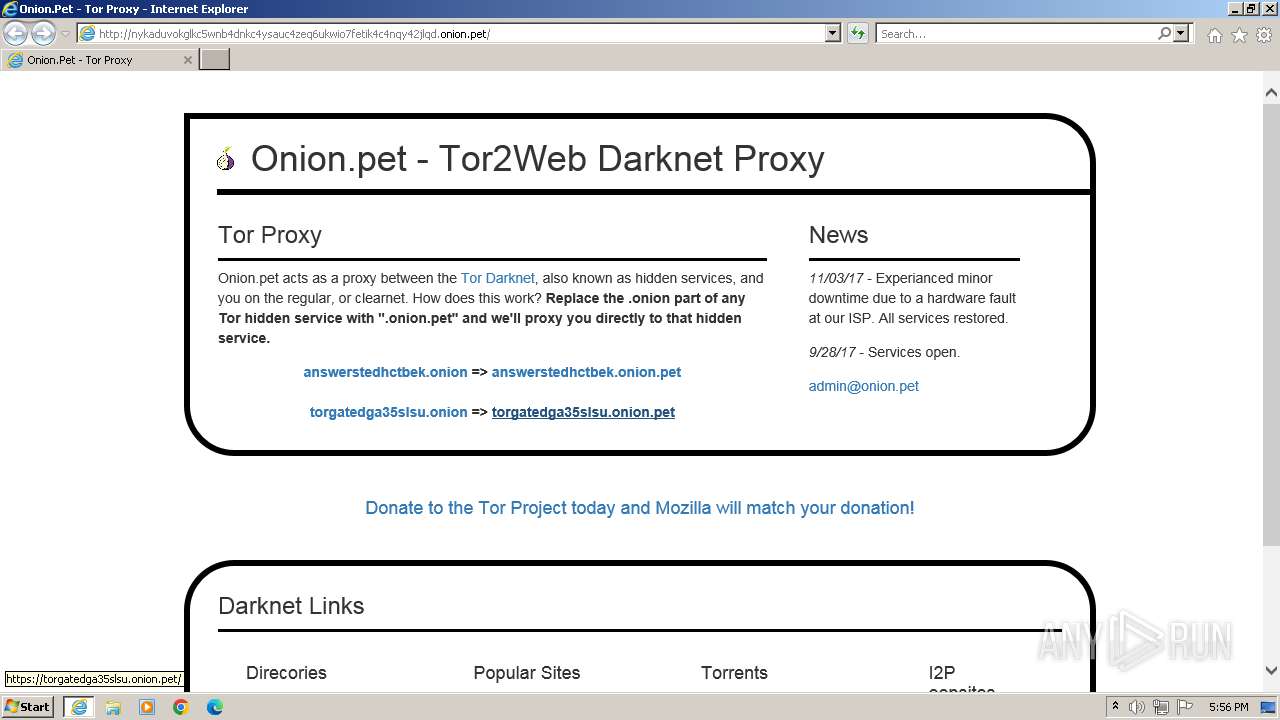
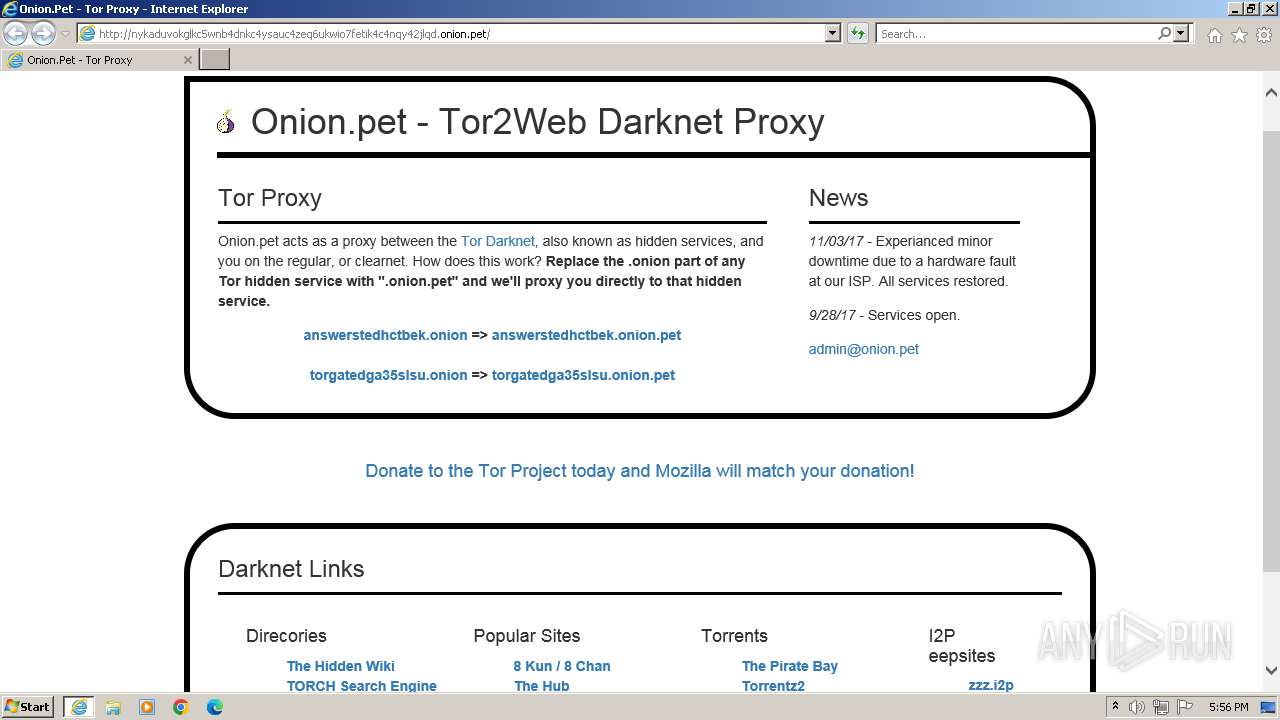
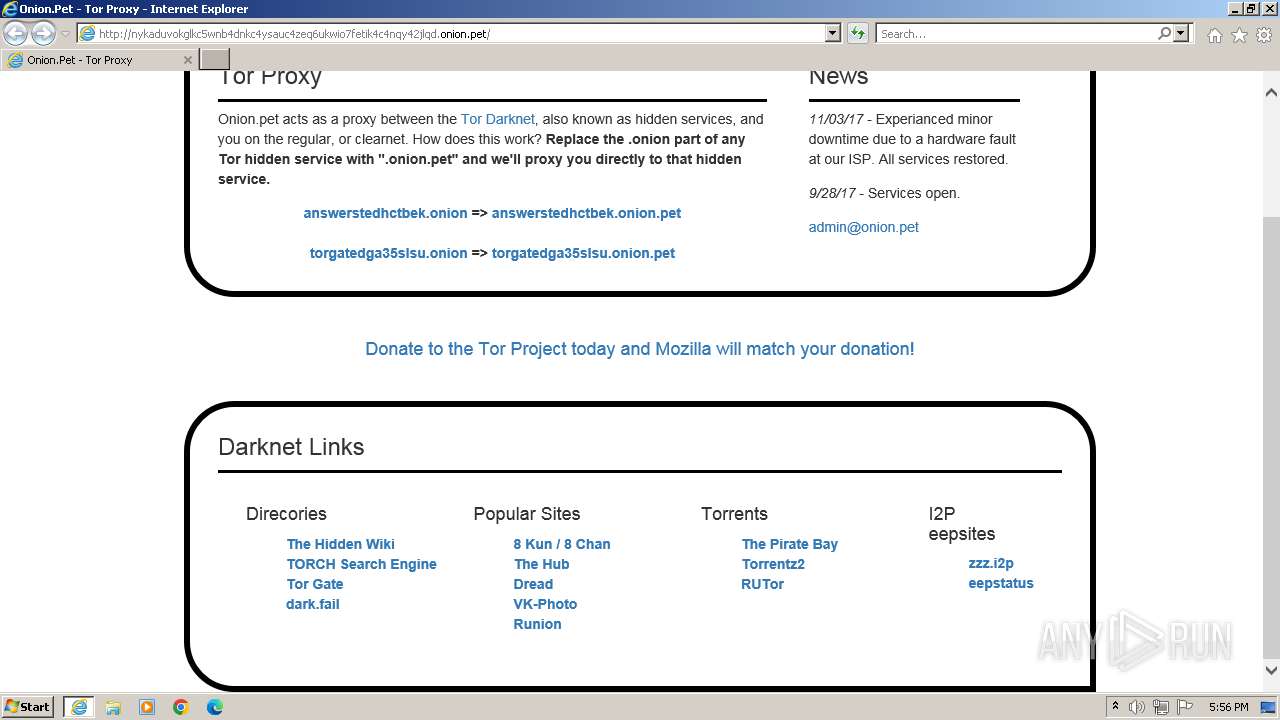
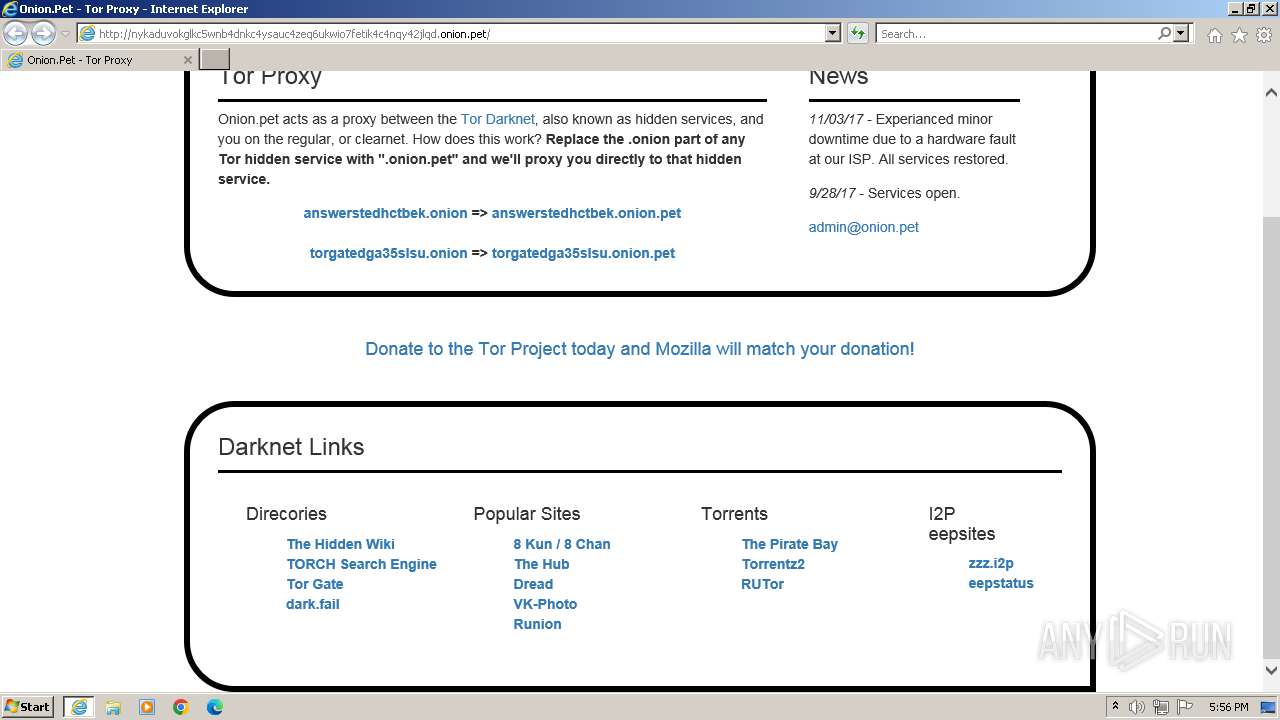
| URL: | nykaduvokglkc5wnb4dnkc4ysauc4zeq6ukwio7fetik4c4nqy42jlqd.onion.pet |
| Full analysis: | https://app.any.run/tasks/7b2e1119-6435-4e0f-9d4b-c887d1261a45 |
| Verdict: | Malicious activity |
| Analysis date: | November 01, 2023, 17:55:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| SHA1: | 51218FE2A2161C023B7A92230AF5DBCBB222FA4B |
| SHA256: | 73BC983751FF2AA9D789533283D4B006499379697FAF79A092AB01D1FCE5E3FE |
| SSDEEP: | 3:IDKGHLxR5GRoUTQOCDgfJmK4eqn:MYRoU/CD8Jw |
MALICIOUS
TOR2WEB has been detected (SURICATA)
- iexplore.exe (PID: 1576)
- iexplore.exe (PID: 1360)
SUSPICIOUS
Block-list domains
- iexplore.exe (PID: 1360)
INFO
Application launched itself
- iexplore.exe (PID: 1360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1360 | "C:\Program Files\Internet Explorer\iexplore.exe" "nykaduvokglkc5wnb4dnkc4ysauc4zeq6ukwio7fetik4c4nqy42jlqd.onion.pet" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1360 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
30 480
Read events
30 421
Write events
59
Delete events
0
Modification events
| (PID) Process: | (1360) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1360) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1360) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1360) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1360) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1360) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1360) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1360) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1360) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1360) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
30
Text files
20
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1576 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:8A7D5114505C18A59800AB97883A7ADA | SHA256:A7ED0F495B71D17FDF73890116D153229B04F9EEC6C0065C7E297D54E79AF257 | |||
| 1576 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | binary | |
MD5:AF77BFBBCB05EDD2D2FDBCF0A04D7E48 | SHA256:B0F25FCDE0CA63C08B3CA99BC793ABCBA00A675FF391A6DCAE548DCBE5156CB7 | |||
| 1576 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:F9C07A968F2D8D43F95385C7FCFCEB47 | SHA256:A5D90112F5A74B84C870CD213C29156CE073CA38176E28B97B843FC4E2A2644E | |||
| 1576 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:87F29C5F54D6EC749A76BF909A637767 | SHA256:2C658CC55EF3441EC556BF0BAB25B9A50B4F288CDA4780A89822DCFFAEBB1BE0 | |||
| 1576 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 1576 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 1576 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\F7TLWGF5.htm | html | |
MD5:E7199CB108E2D9FF317197EFDA39BC6E | SHA256:42E86C028679DE9D3B6CDB7792C47CDFEE405D6FF599489B07588C7D4DF191DC | |||
| 1576 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:947E4F16C47960895DFE4E8DBBAD83C0 | SHA256:3DC6830B4D1FF3A78C8458643C104682C4905C3DA982051DE5C8958246FF5673 | |||
| 1576 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\bootstrap.min[1].css | text | |
MD5:EC3BB52A00E176A7181D454DFFAEA219 | SHA256:F75E846CC83BD11432F4B1E21A45F31BC85283D11D372F7B19ACCD1BF6A2635C | |||
| 1576 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar77F2.tmp | binary | |
MD5:9441737383D21192400ECA82FDA910EC | SHA256:BC3A6E84E41FAEB57E7C21AA3B60C2A64777107009727C5B7C0ED8FE658909E5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
25
DNS requests
15
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1576 | iexplore.exe | GET | 200 | 23.37.41.57:80 | http://x2.c.lencr.org/ | unknown | binary | 300 b | unknown |
1576 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDCjDk6BcP0YRJkTzSsQwBD | unknown | binary | 472 b | unknown |
1576 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?13015be60488e11f | unknown | compressed | 4.66 Kb | unknown |
1576 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2a25e3e01d324762 | unknown | compressed | 4.66 Kb | unknown |
1576 | iexplore.exe | GET | 200 | 23.37.41.57:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
1576 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?69a731e12ea5aaac | unknown | compressed | 4.66 Kb | unknown |
1576 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d51b094548b95d1b | unknown | compressed | 4.66 Kb | unknown |
1576 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6ff646cb81a5448e | unknown | compressed | 4.66 Kb | unknown |
1576 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?80691e2fa7e6656f | unknown | compressed | 4.66 Kb | unknown |
1576 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7bedc6fa4b2942f4 | unknown | compressed | 4.66 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1576 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1576 | iexplore.exe | 142.250.185.99:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
1576 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1576 | iexplore.exe | 192.124.249.23:80 | ocsp.godaddy.com | SUCURI-SEC | US | unknown |
1576 | iexplore.exe | 23.37.41.57:80 | x1.c.lencr.org | AKAMAI-AS | DE | unknown |
2656 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1576 | iexplore.exe | 142.250.185.142:443 | www.google-analytics.com | GOOGLE | US | whitelisted |
1576 | iexplore.exe | 216.239.34.36:443 | region1.google-analytics.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
www.google-analytics.com |
| whitelisted |
region1.google-analytics.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1088 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to .onion proxy domain (onion .pet) |
1576 | iexplore.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Tor2Web Host Proxy HTTP Request (.onion.) |
1360 | iexplore.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Tor2Web Host Proxy HTTP Request (.onion.) |