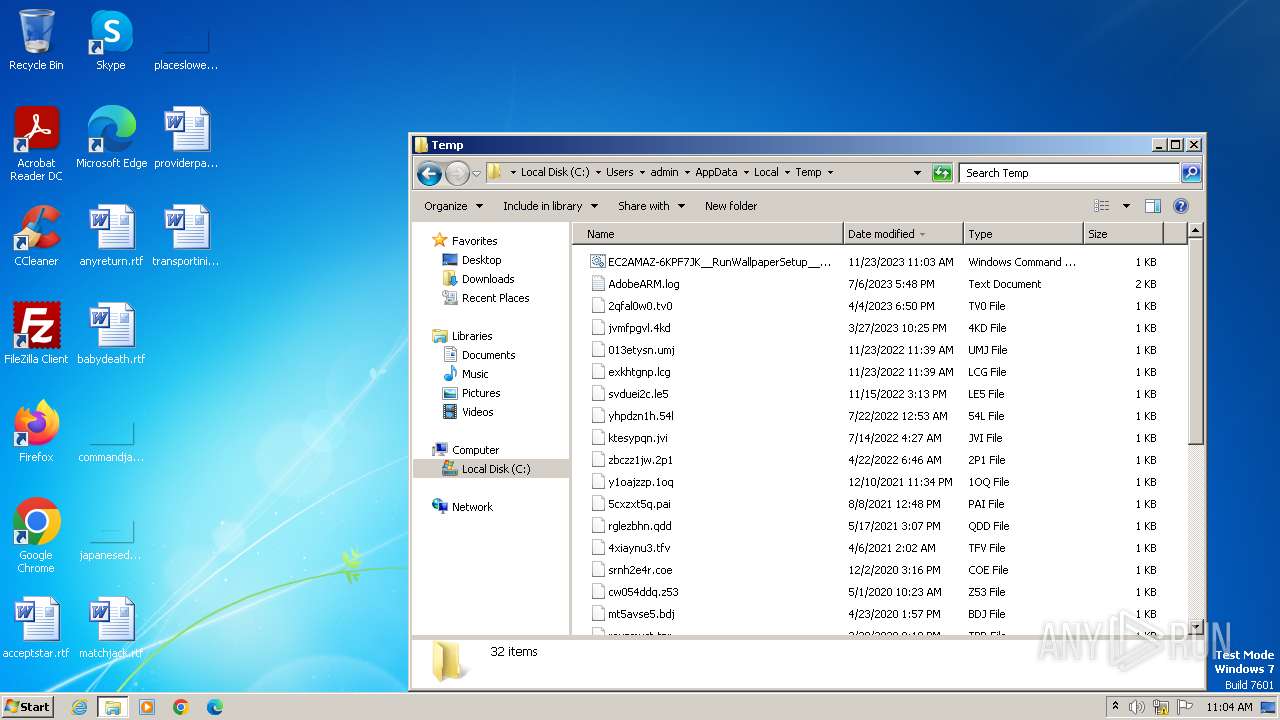
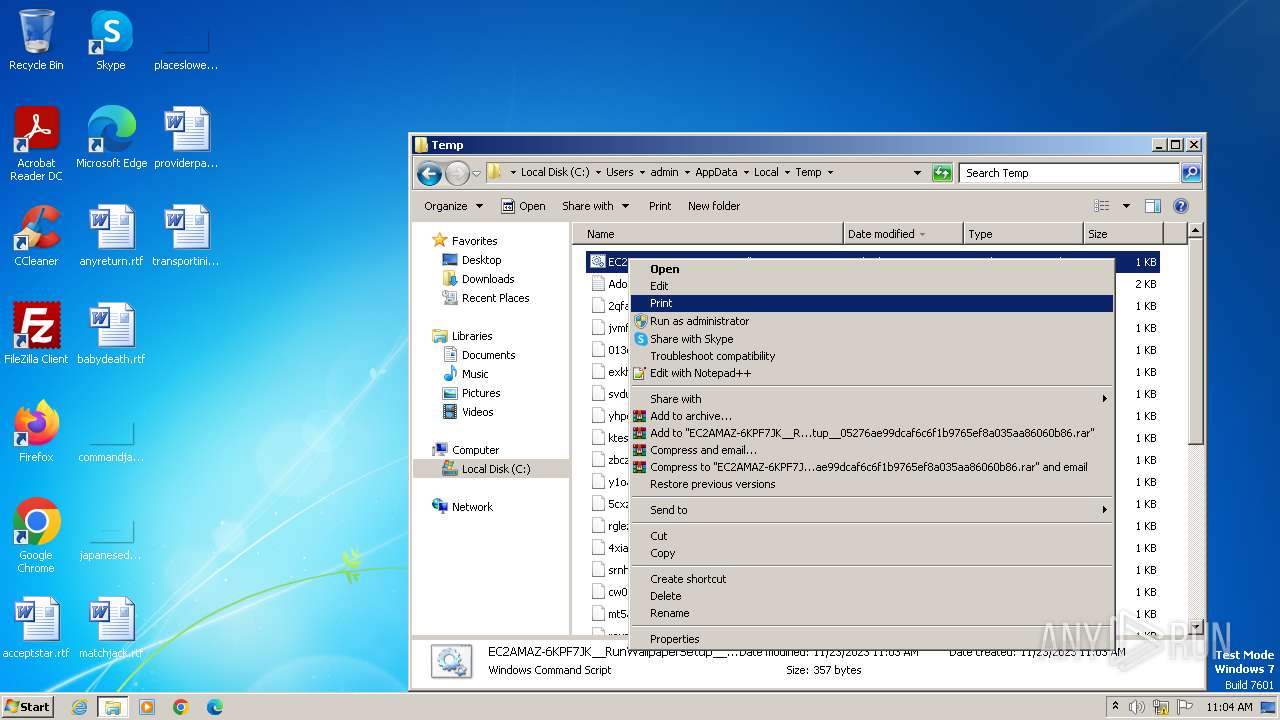
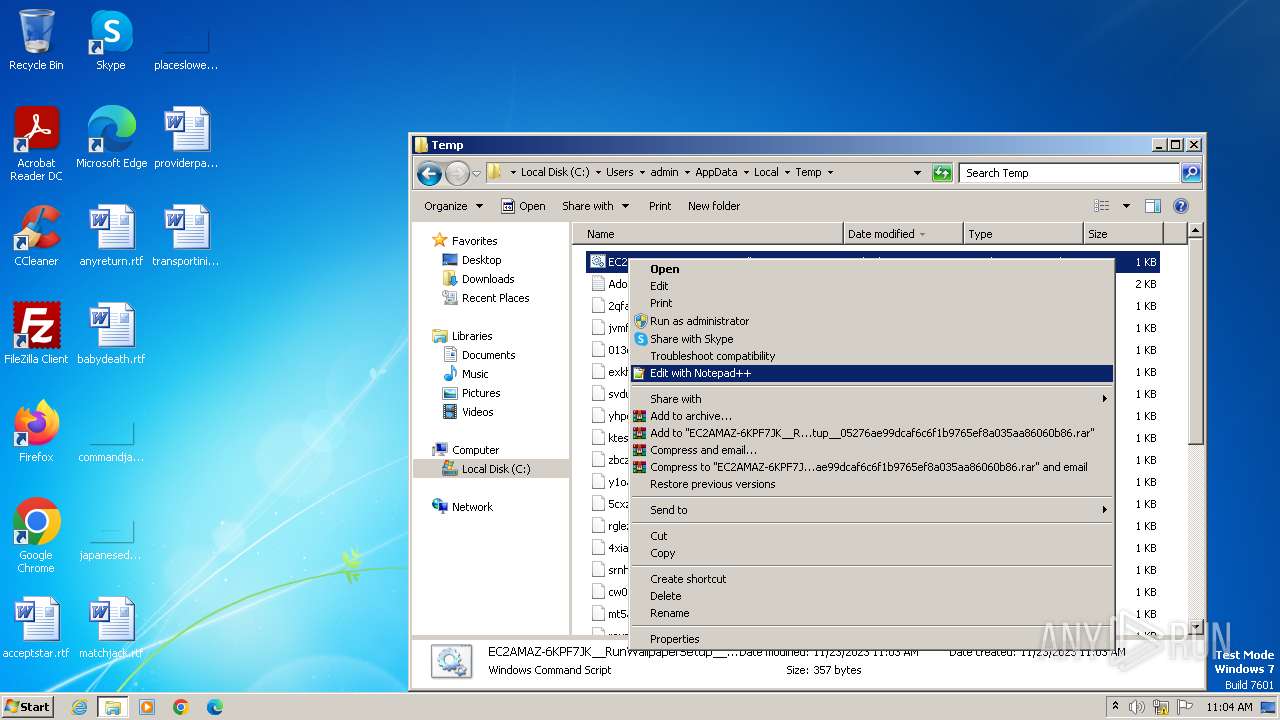
| File name: | EC2AMAZ-6KPF7JK__RunWallpaperSetup__05276ae99dcaf6c6f1b9765ef8a035aa86060b86.cmd |
| Full analysis: | https://app.any.run/tasks/882e24b1-53d6-4265-a541-a5db5833452a |
| Verdict: | Malicious activity |
| Analysis date: | November 23, 2023, 11:03:11 |
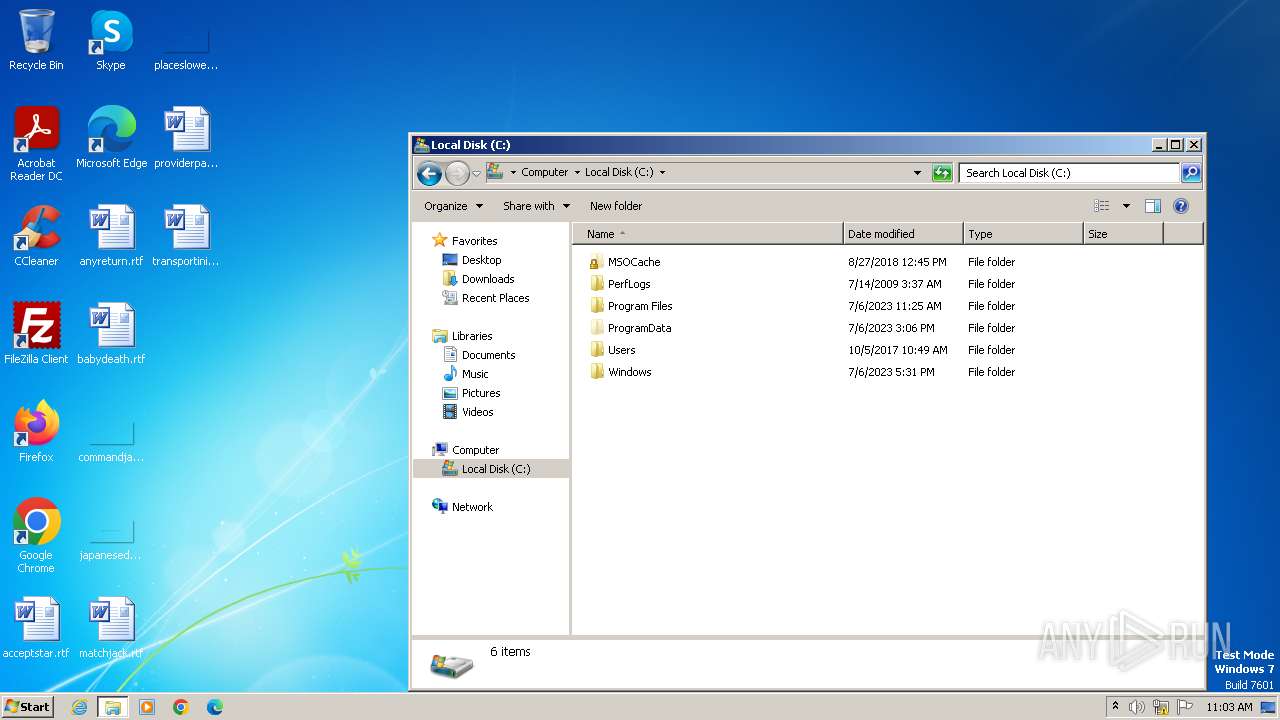
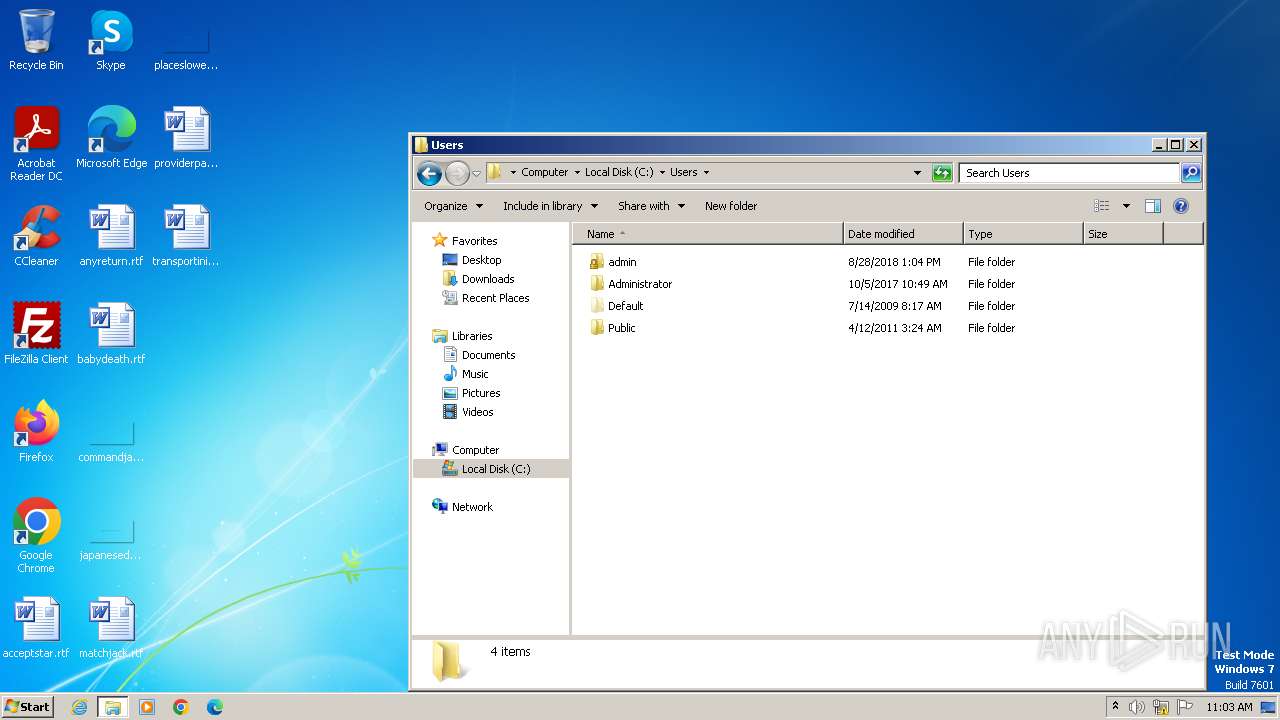
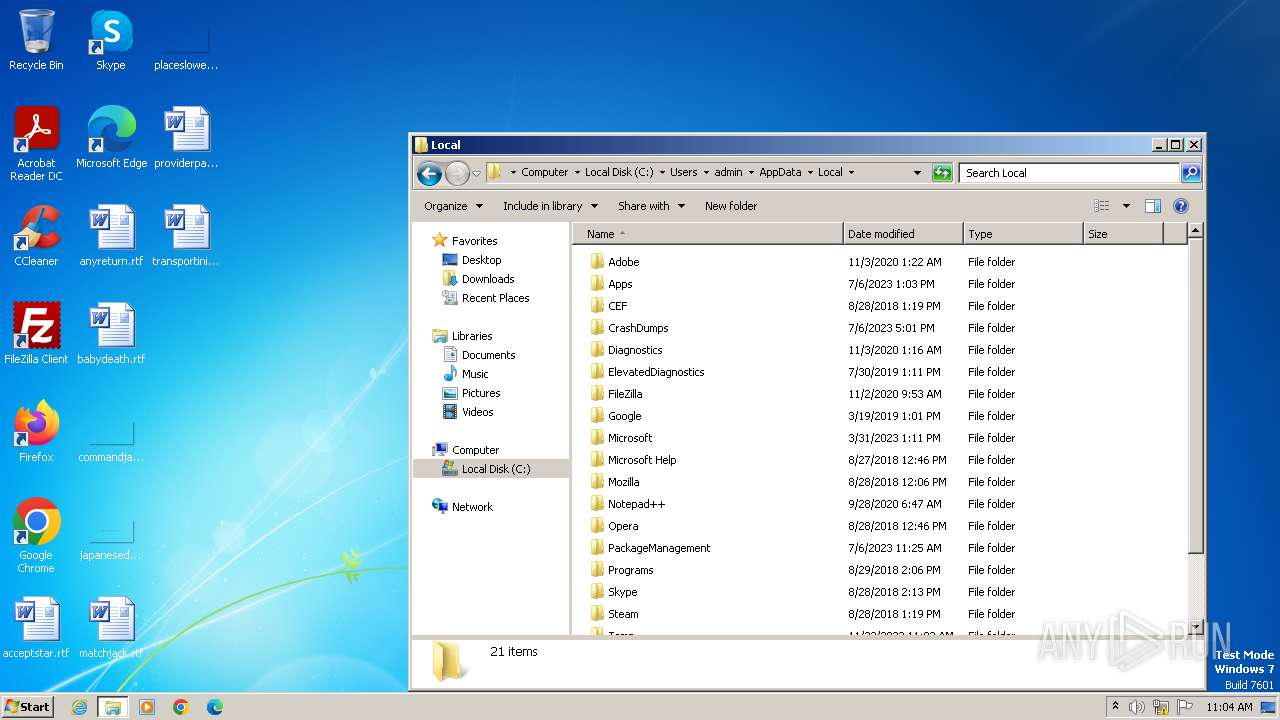
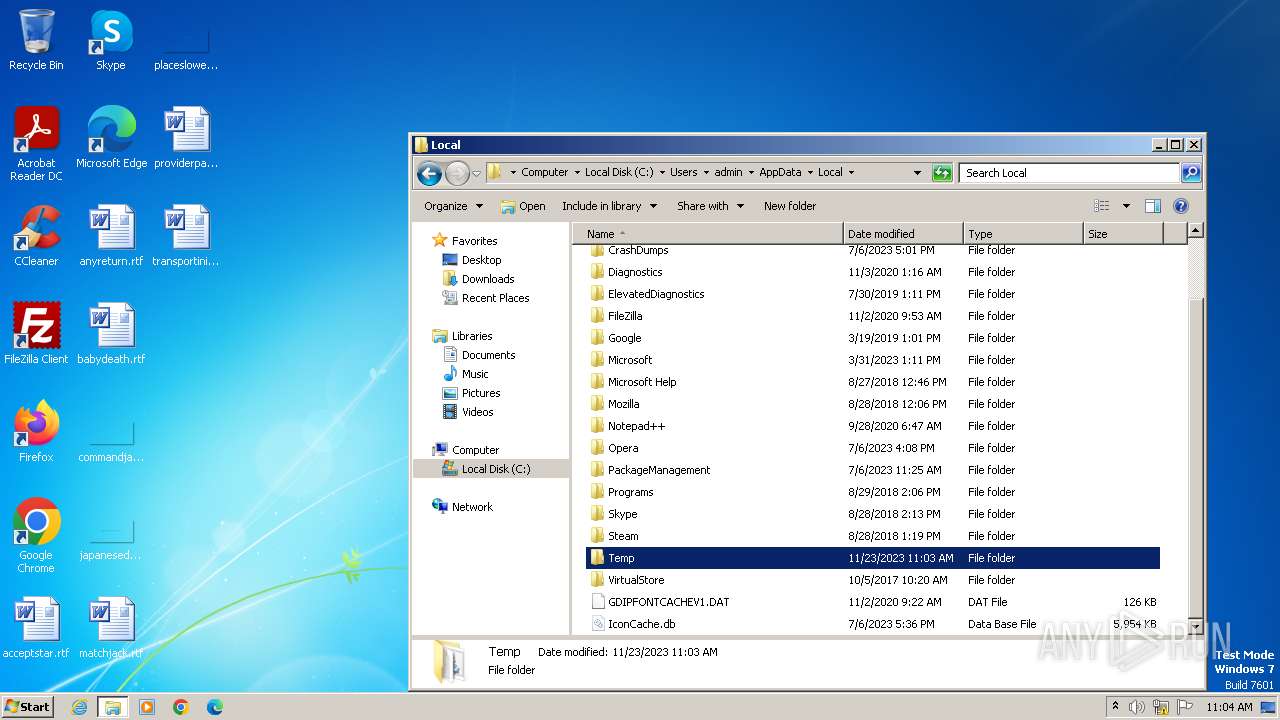
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | FA9D7A03029739B5B2001E922E850A64 |
| SHA1: | 05276AE99DCAF6C6F1B9765EF8A035AA86060B86 |
| SHA256: | 73BA33FE75051877AFED93B3644B9B824E82E68E2A11EA1694A445EB4A5EBFD7 |
| SSDEEP: | 6:/E+rLGgM3K/MKe6HwQCGRWVe2jInye+IA5X9xQQO0zNMfrGS5DKabAY0R:/BfG5KjenQCGRWVjjIneIAJ9SQpZS5ep |
MALICIOUS
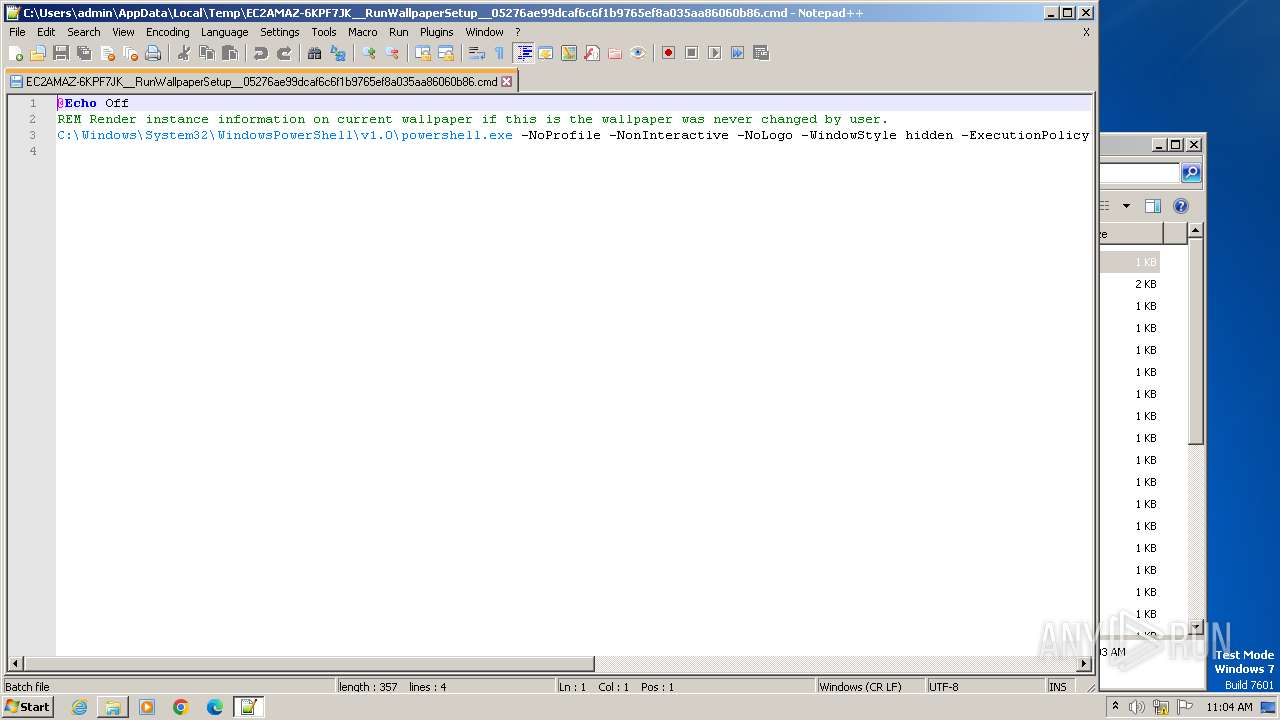
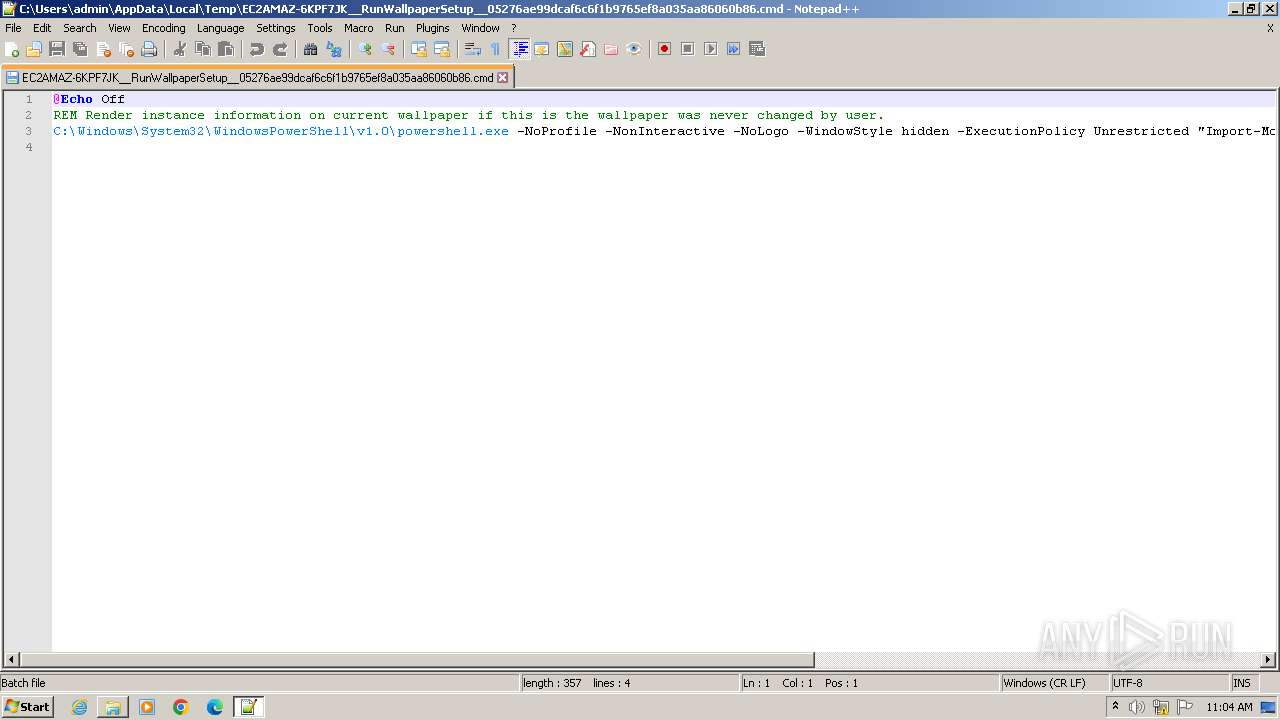
Run PowerShell with an invisible window
- powershell.exe (PID: 3204)
Changes powershell execution policy (Unrestricted)
- cmd.exe (PID: 3428)
SUSPICIOUS
The process hides Powershell's copyright startup banner
- cmd.exe (PID: 3428)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3428)
The process hide an interactive prompt from the user
- cmd.exe (PID: 3428)
Base64-obfuscated command line is found
- cmd.exe (PID: 3428)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 3428)
Powershell version downgrade attack
- powershell.exe (PID: 3204)
INFO
Manual execution by a user
- wmpnscfg.exe (PID: 3196)
- explorer.exe (PID: 3500)
- notepad++.exe (PID: 2056)
Reads the computer name
- wmpnscfg.exe (PID: 3196)
Checks supported languages
- wmpnscfg.exe (PID: 3196)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3196)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
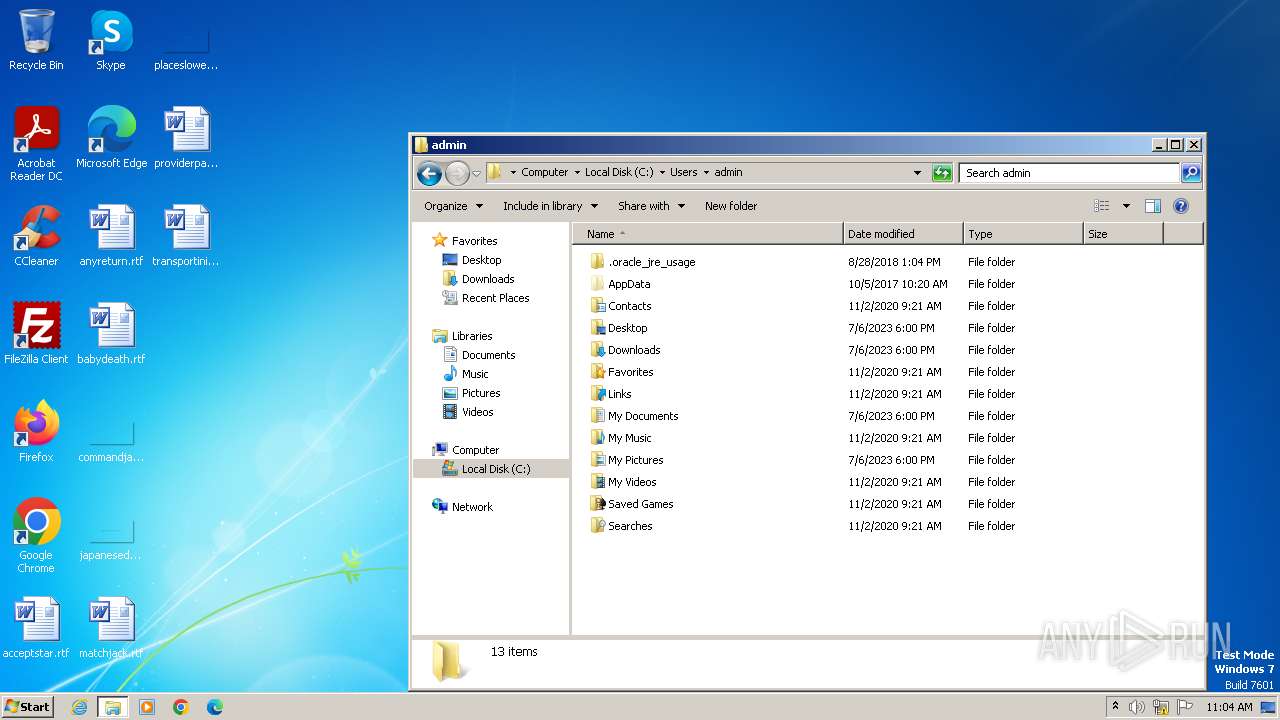
| 2056 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\AppData\Local\Temp\EC2AMAZ-6KPF7JK__RunWallpaperSetup__05276ae99dcaf6c6f1b9765ef8a035aa86060b86.cmd" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 3196 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
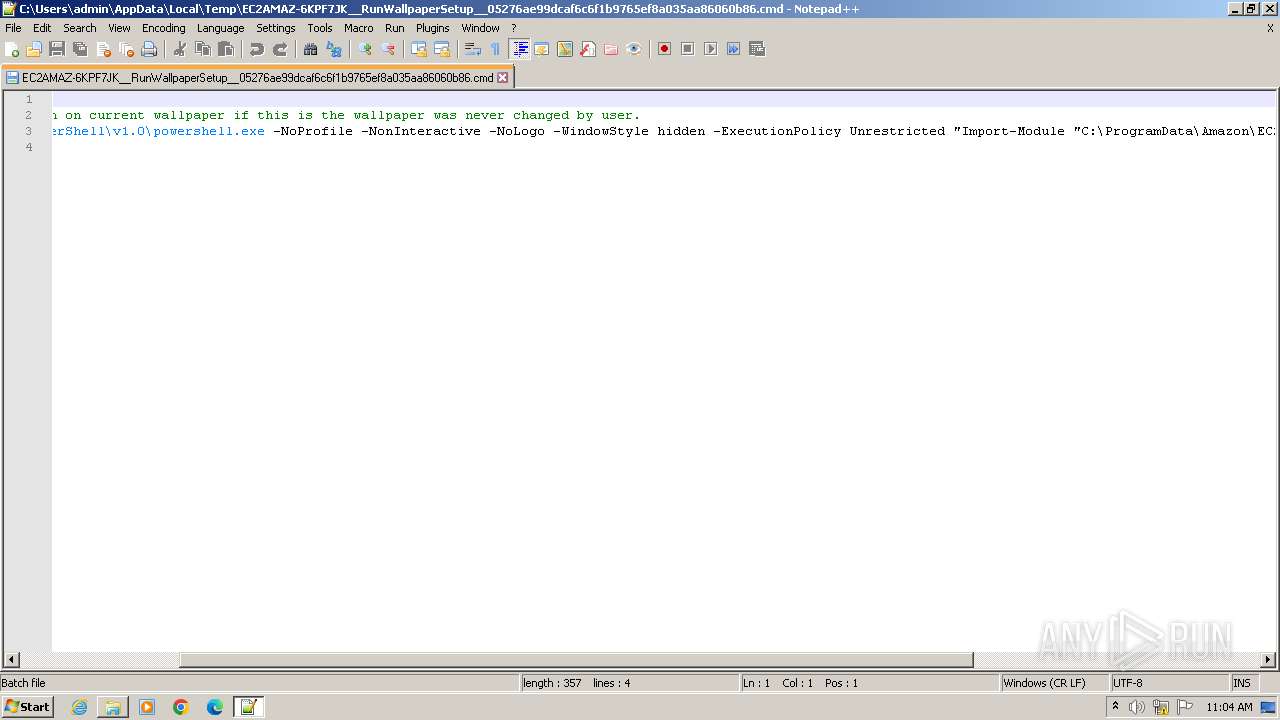
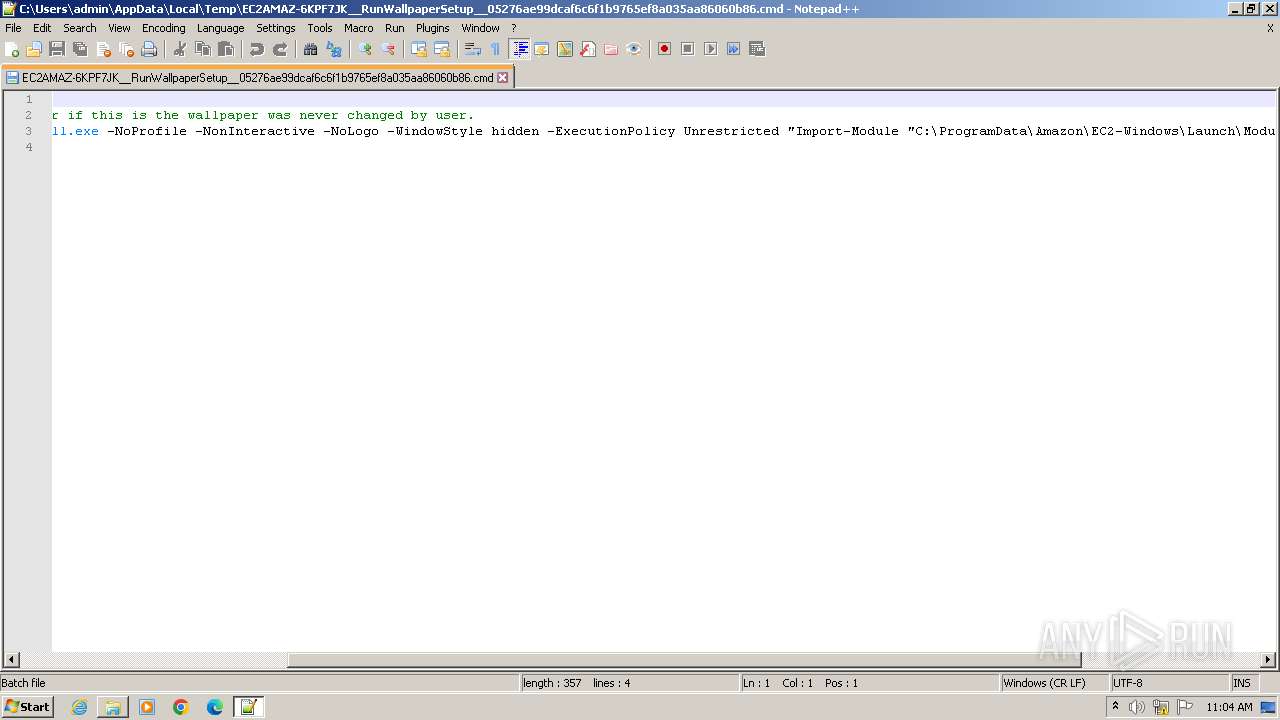
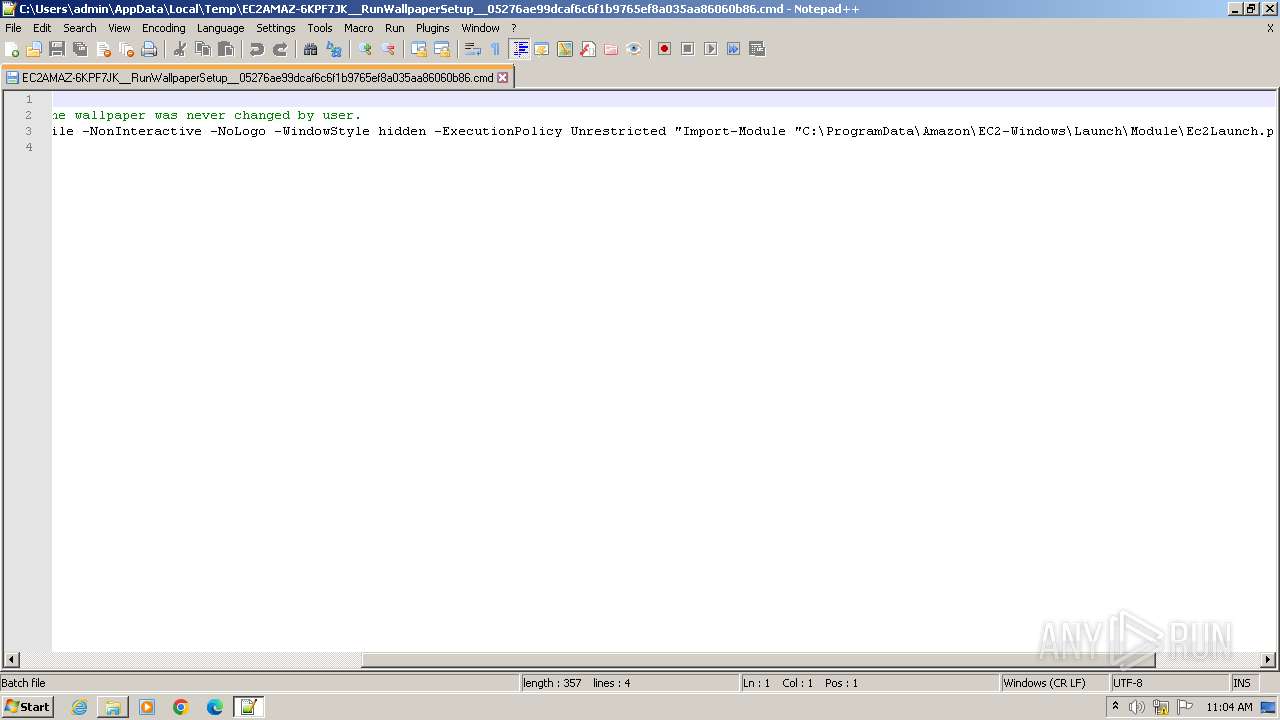
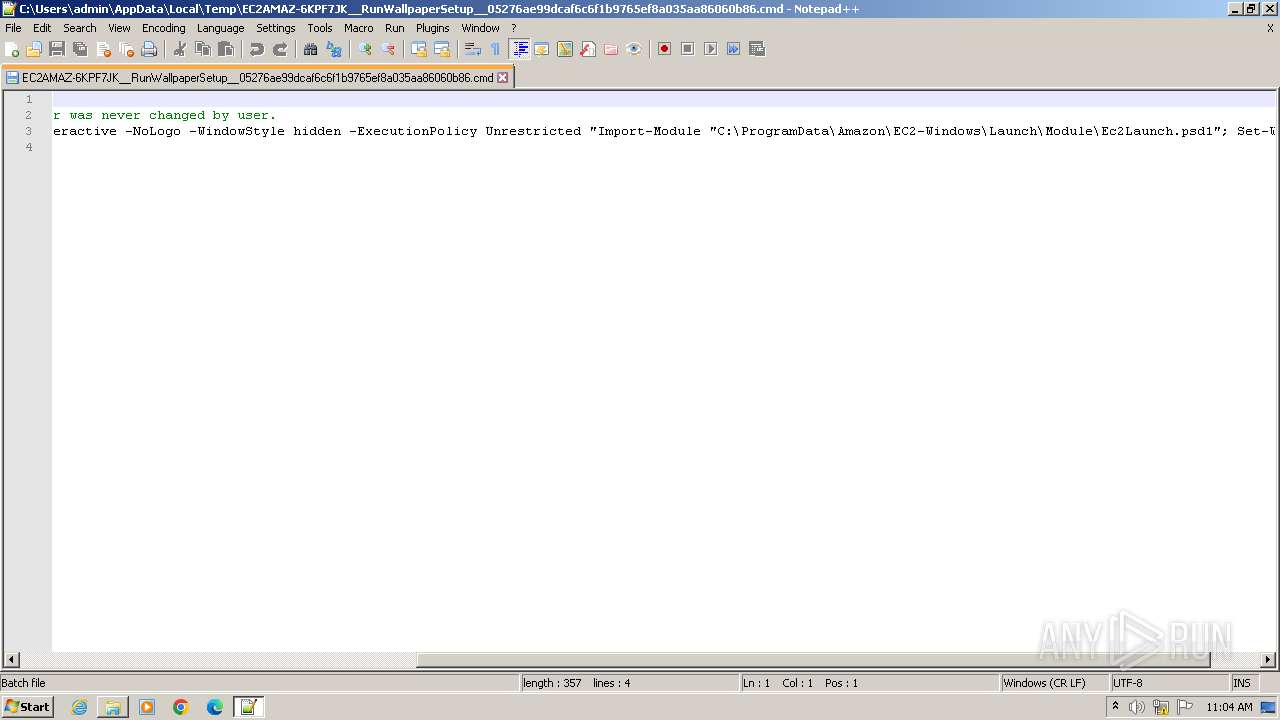
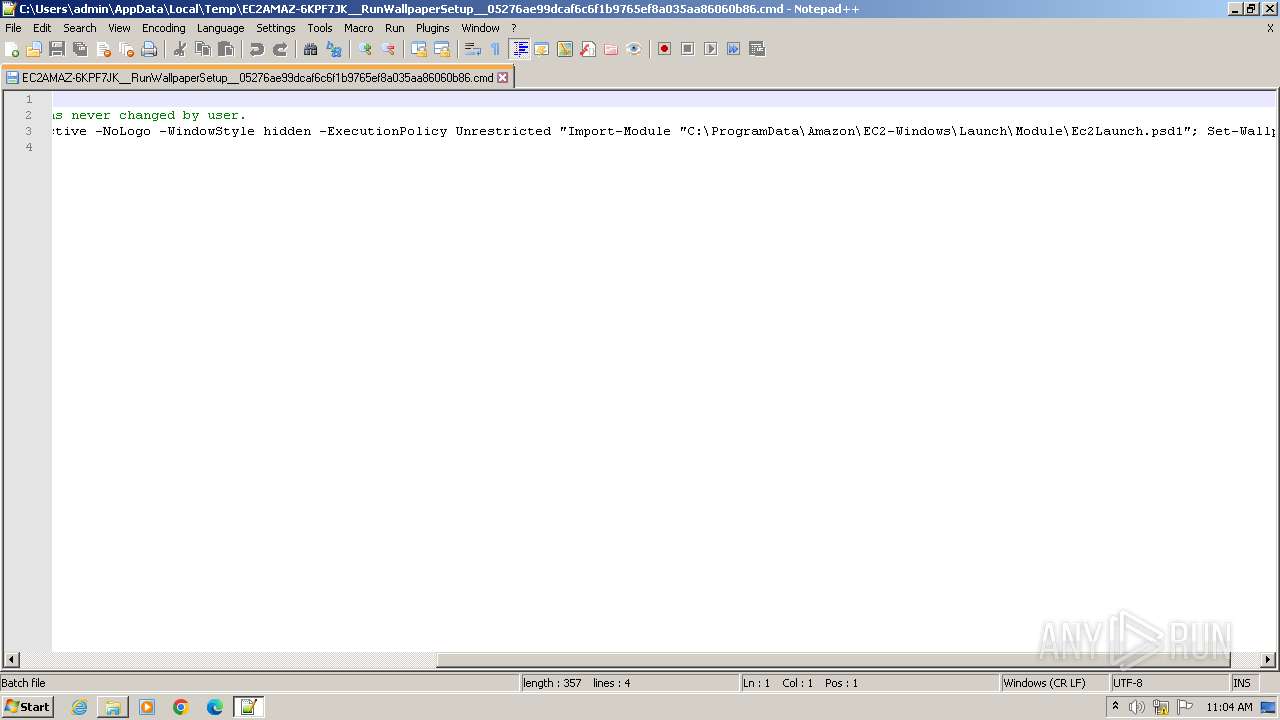
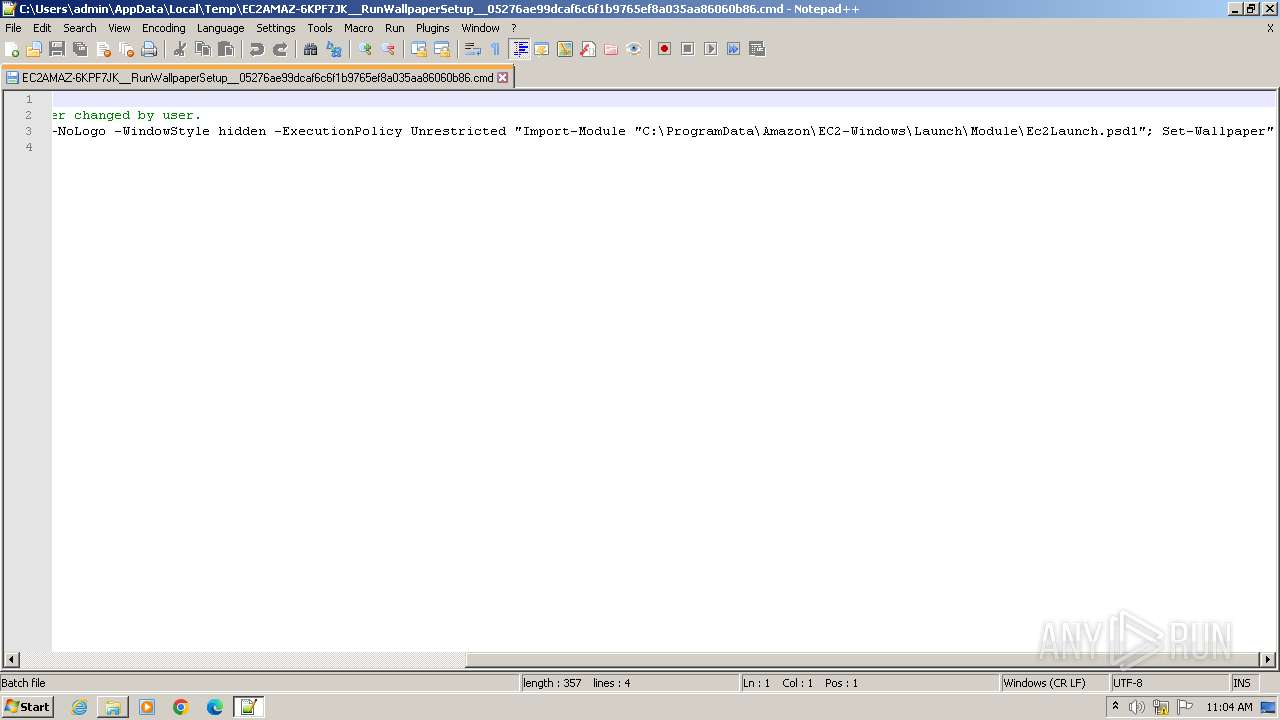
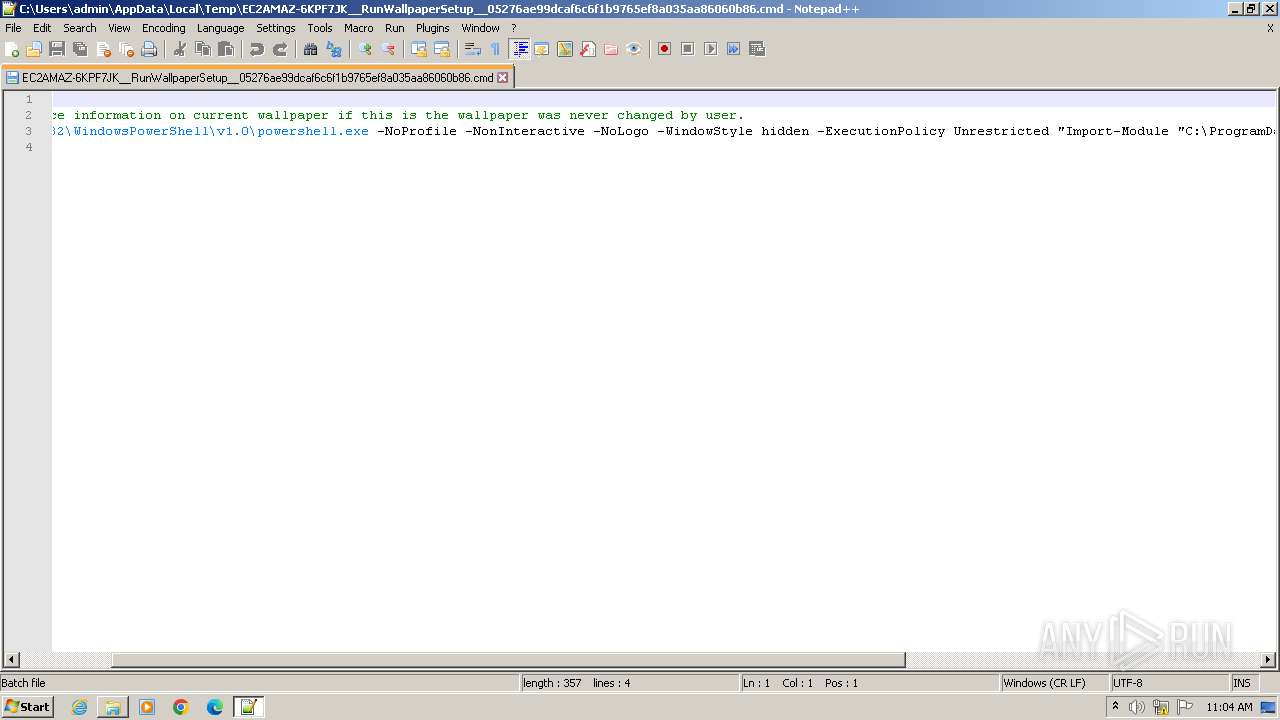
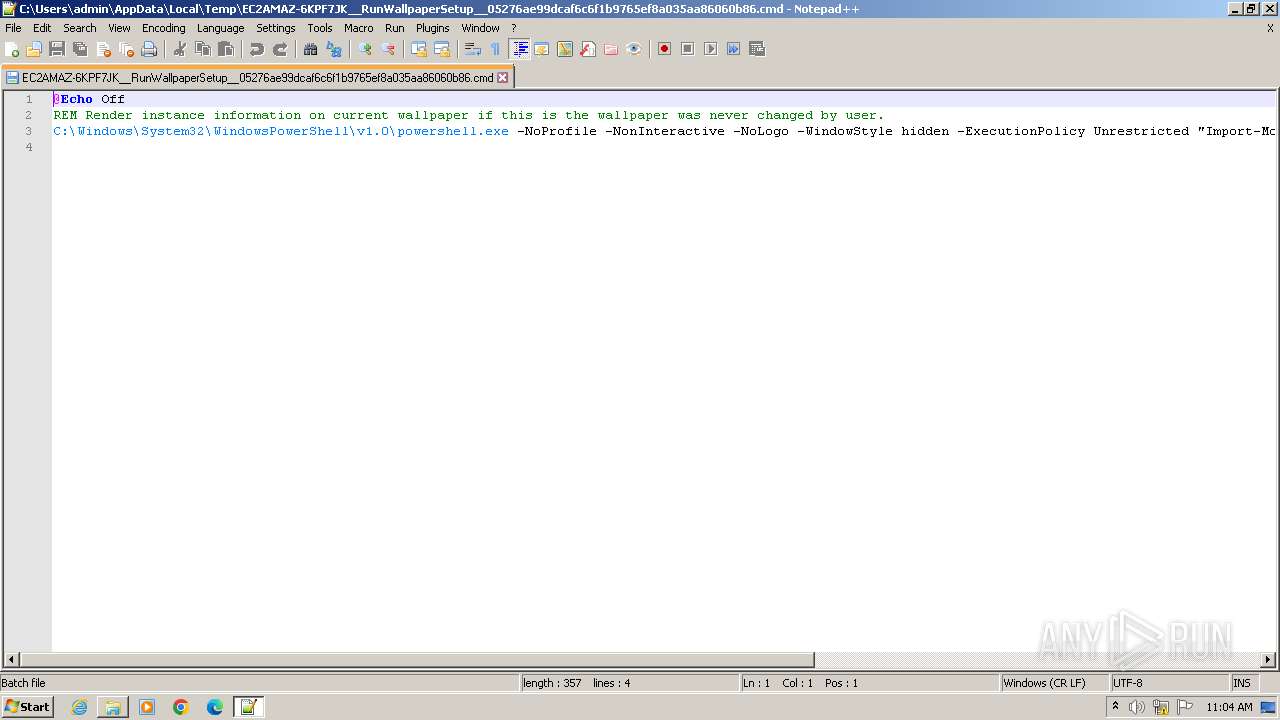
| 3204 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -NoProfile -NonInteractive -NoLogo -WindowStyle hidden -ExecutionPolicy Unrestricted "Import-Module "C:\ProgramData\Amazon\EC2-Windows\Launch\Module\Ec2Launch.psd1"; Set-Wallpaper" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3428 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\EC2AMAZ-6KPF7JK__RunWallpaperSetup__05276ae99dcaf6c6f1b9765ef8a035aa86060b86.cmd" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3500 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 411
Read events
1 342
Write events
66
Delete events
3
Modification events
| (PID) Process: | (3204) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3196) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{AF7A62D2-5F5E-4037-93C1-CB0DFBAE7ADD}\{DDCD5A81-3E8A-445C-B655-2E3223AB95A6} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3196) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{AF7A62D2-5F5E-4037-93C1-CB0DFBAE7ADD} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3196) wmpnscfg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Health\{297D50D0-7399-4F9E-A10F-6F85BD9180DF} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2056) notepad++.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
3
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
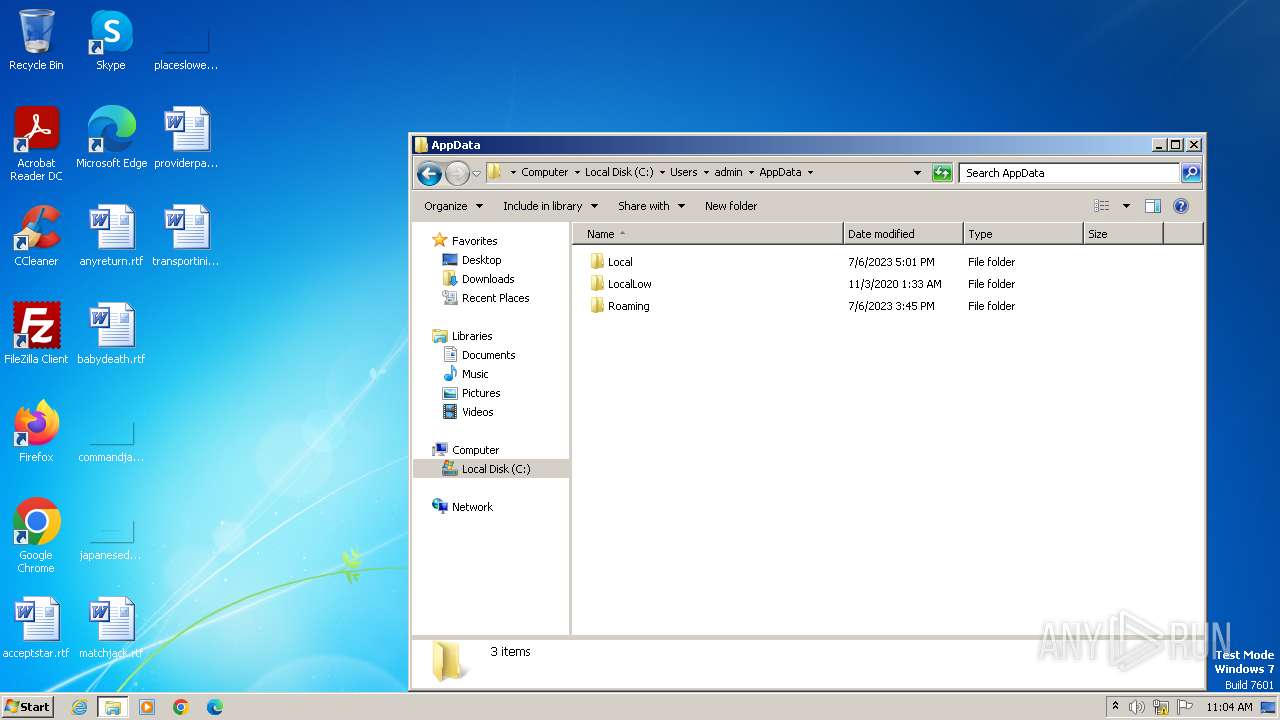
| 3204 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\UJ2J1TJNOQZFS6QI2IYQ.temp | binary | |
MD5:C681106A4168B935996B10134404F885 | SHA256:89AB4ECFBB5C1FD07CF99465E36B1A08F51E2512AA60DDD616D4A37753FC112D | |||
| 3204 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF166bce.TMP | binary | |
MD5:C681106A4168B935996B10134404F885 | SHA256:89AB4ECFBB5C1FD07CF99465E36B1A08F51E2512AA60DDD616D4A37753FC112D | |||
| 3204 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:C681106A4168B935996B10134404F885 | SHA256:89AB4ECFBB5C1FD07CF99465E36B1A08F51E2512AA60DDD616D4A37753FC112D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\plugins\Config\nppPluginList.dll
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|