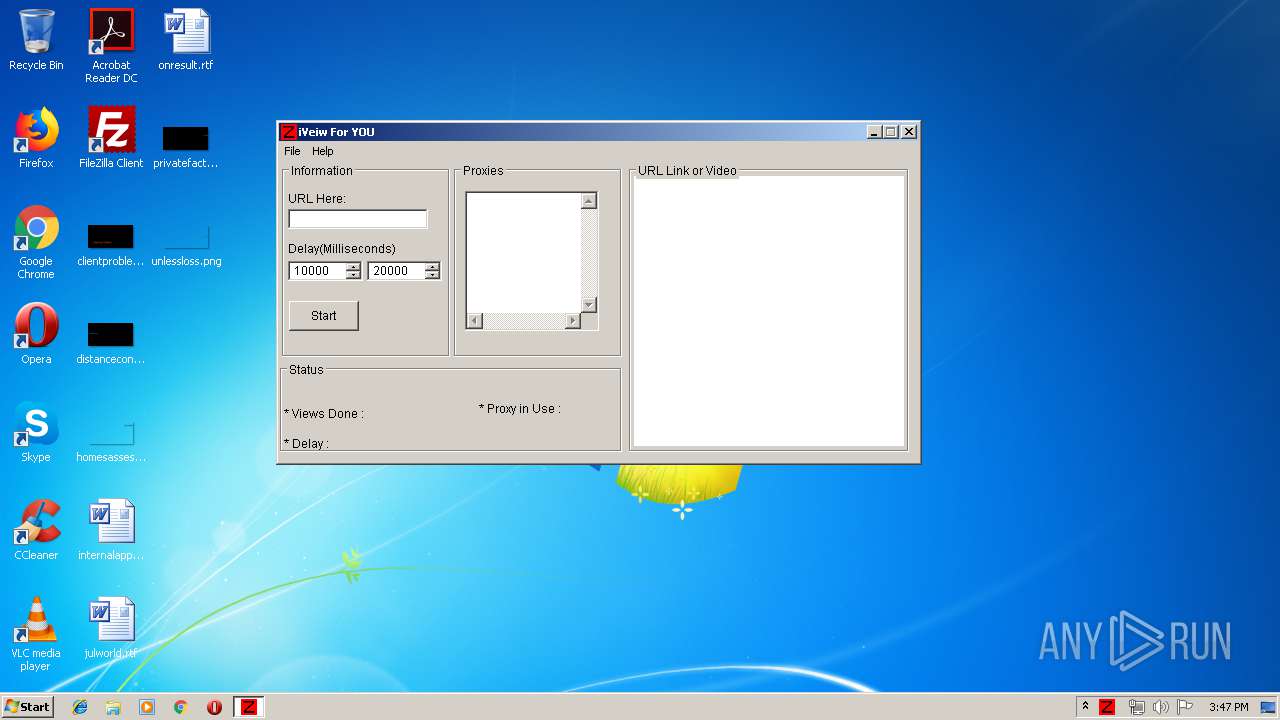
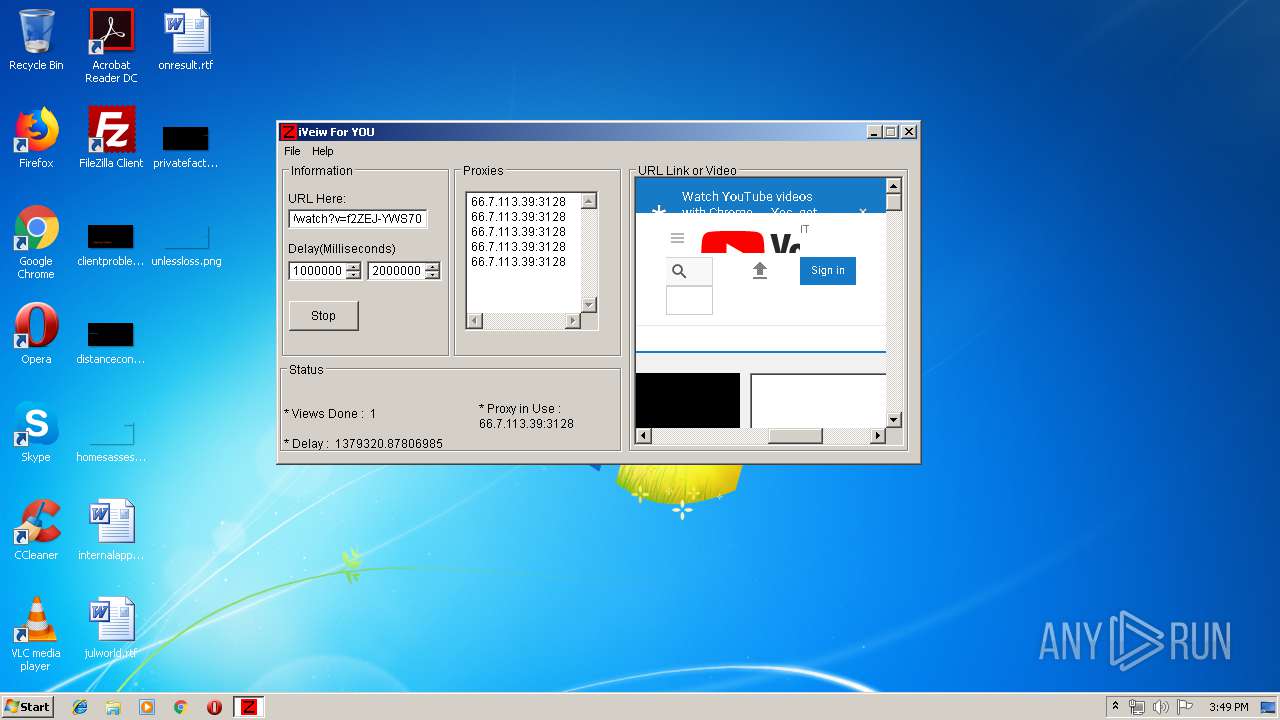
| File name: | iView Fur U v2!.exe |
| Full analysis: | https://app.any.run/tasks/ec45d771-ae38-4ae5-9c35-2c7d503a98ea |
| Verdict: | No threats detected |
| Analysis date: | June 25, 2019, 14:46:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | BA9409E272CCD7BB5A43E9D28F1B7440 |
| SHA1: | 2DD25ABD0C6E55E05F596671C839ED035E00E61D |
| SHA256: | 73B7FEA4754E8BE18812ADC0DDD7B3C3C8C3797A889CC801CC94C7195027AA11 |
| SSDEEP: | 12288:aHLUMuiv9RgfSjAzRtyEHnD3ZVuRL/zrIUgS:4tARXHnDXuRLPIe |
MALICIOUS
No malicious indicators.SUSPICIOUS
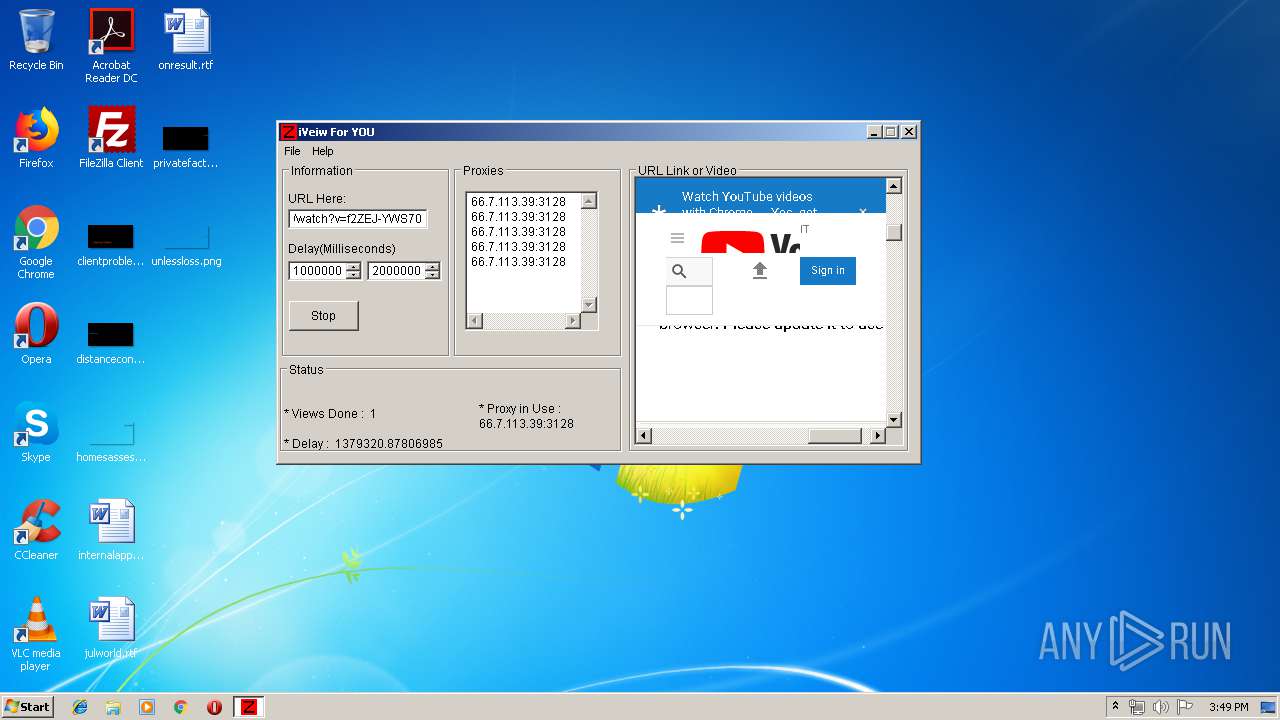
Reads internet explorer settings
- iView Fur U v2!.exe (PID: 3960)
Creates files in the user directory
- iView Fur U v2!.exe (PID: 3960)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | AutoIt3 compiled script executable (88.1) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (4.6) |
| .exe | | | Win32 EXE Yoda's Crypter (4.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.1) |
| .exe | | | Win32 Executable (generic) (0.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2008:12:24 10:00:07+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 262144 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | 430080 |
| EntryPoint: | 0xa91d0 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.3.0.0 |
| ProductVersionNumber: | 3.3.0.0 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileDescription: | - |
| FileVersion: | 3, 3, 0, 0 |
| CompiledScript: | AutoIt v3 Script : 3, 3, 0, 0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Dec-2008 09:00:07 |
| Detected languages: |
|
| FileDescription: | - |
| FileVersion: | 3, 3, 0, 0 |
| CompiledScript: | AutoIt v3 Script : 3, 3, 0, 0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 24-Dec-2008 09:00:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00069000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0006A000 | 0x00040000 | 0x0003F400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.92663 |
.rsrc | 0x000AA000 | 0x00002000 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.29286 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.11386 | 931 | UNKNOWN | English - United Kingdom | RT_MANIFEST |
7 | 7.78459 | 1432 | UNKNOWN | English - United Kingdom | RT_STRING |
8 | 7.79676 | 1680 | UNKNOWN | English - United Kingdom | RT_STRING |
9 | 7.57055 | 1102 | UNKNOWN | English - United Kingdom | RT_STRING |
10 | 7.74643 | 1476 | UNKNOWN | English - United Kingdom | RT_STRING |
11 | 7.64061 | 1628 | UNKNOWN | English - United Kingdom | RT_STRING |
12 | 7.31515 | 904 | UNKNOWN | English - United Kingdom | RT_STRING |
161 | 1.81924 | 20 | UNKNOWN | English - United Kingdom | RT_GROUP_ICON |
162 | 2.02322 | 20 | UNKNOWN | English - United Kingdom | RT_GROUP_ICON |
164 | 2.02322 | 20 | UNKNOWN | English - United Kingdom | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.DLL |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
USER32.dll |
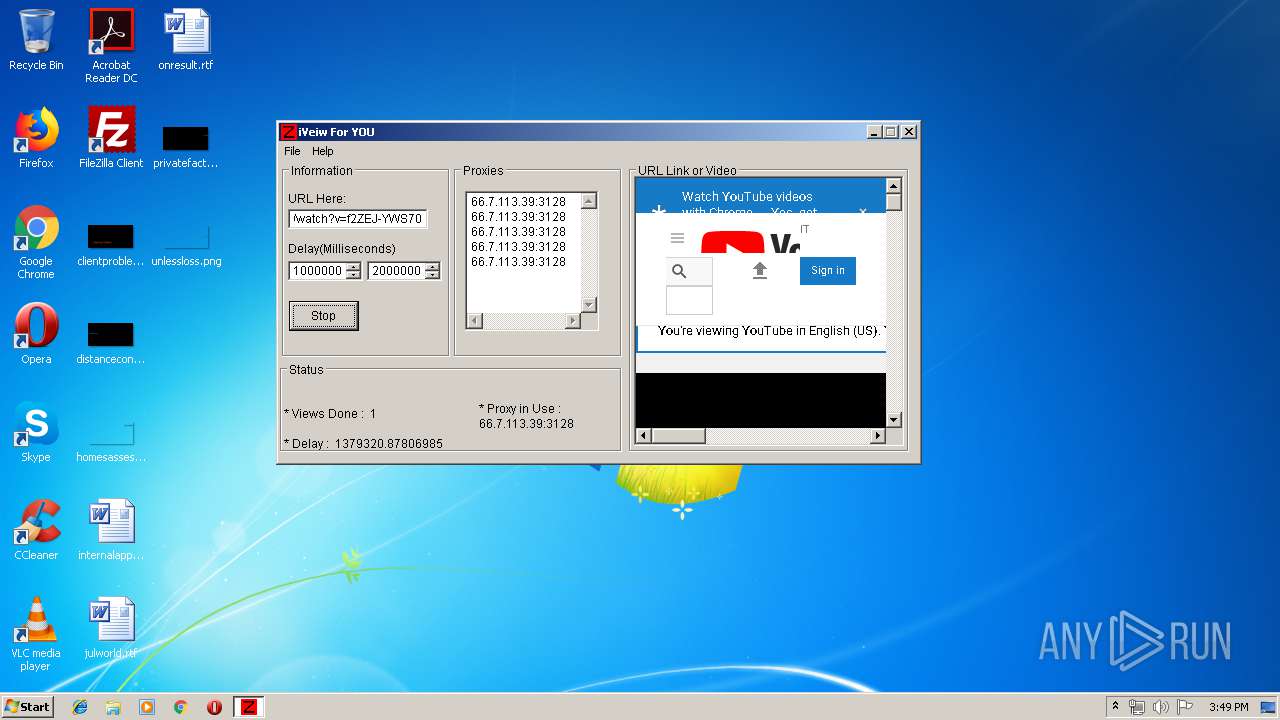
Total processes
32
Monitored processes
1
Malicious processes
0
Suspicious processes
0
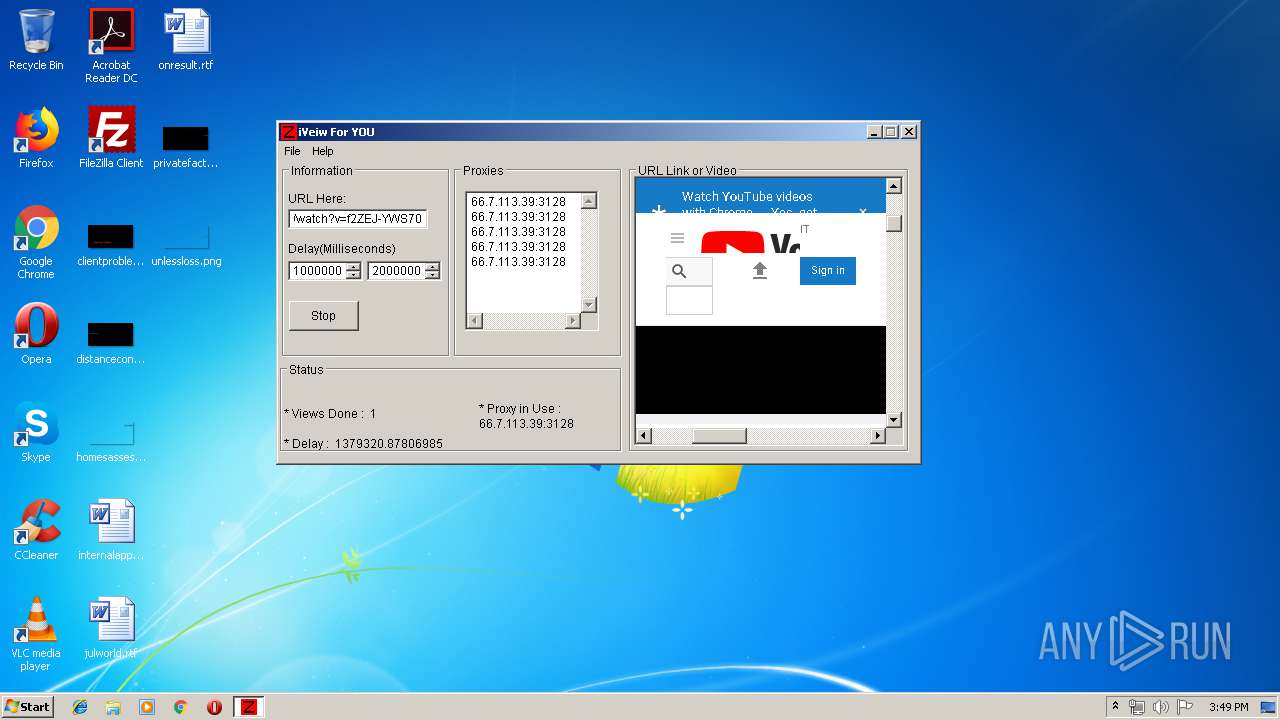
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3960 | "C:\Users\admin\AppData\Local\Temp\iView Fur U v2!.exe" | C:\Users\admin\AppData\Local\Temp\iView Fur U v2!.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 3, 3, 0, 0 Modules
| |||||||||||||||
Total events
192
Read events
164
Write events
28
Delete events
0
Modification events
| (PID) Process: | (3960) iView Fur U v2!.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3960) iView Fur U v2!.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3960) iView Fur U v2!.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\iView Fur U v2!_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3960) iView Fur U v2!.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\iView Fur U v2!_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3960) iView Fur U v2!.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\iView Fur U v2!_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3960) iView Fur U v2!.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\iView Fur U v2!_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3960) iView Fur U v2!.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\iView Fur U v2!_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3960) iView Fur U v2!.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\iView Fur U v2!_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3960) iView Fur U v2!.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\iView Fur U v2!_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3960) iView Fur U v2!.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\iView Fur U v2!_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
24
Unknown types
4
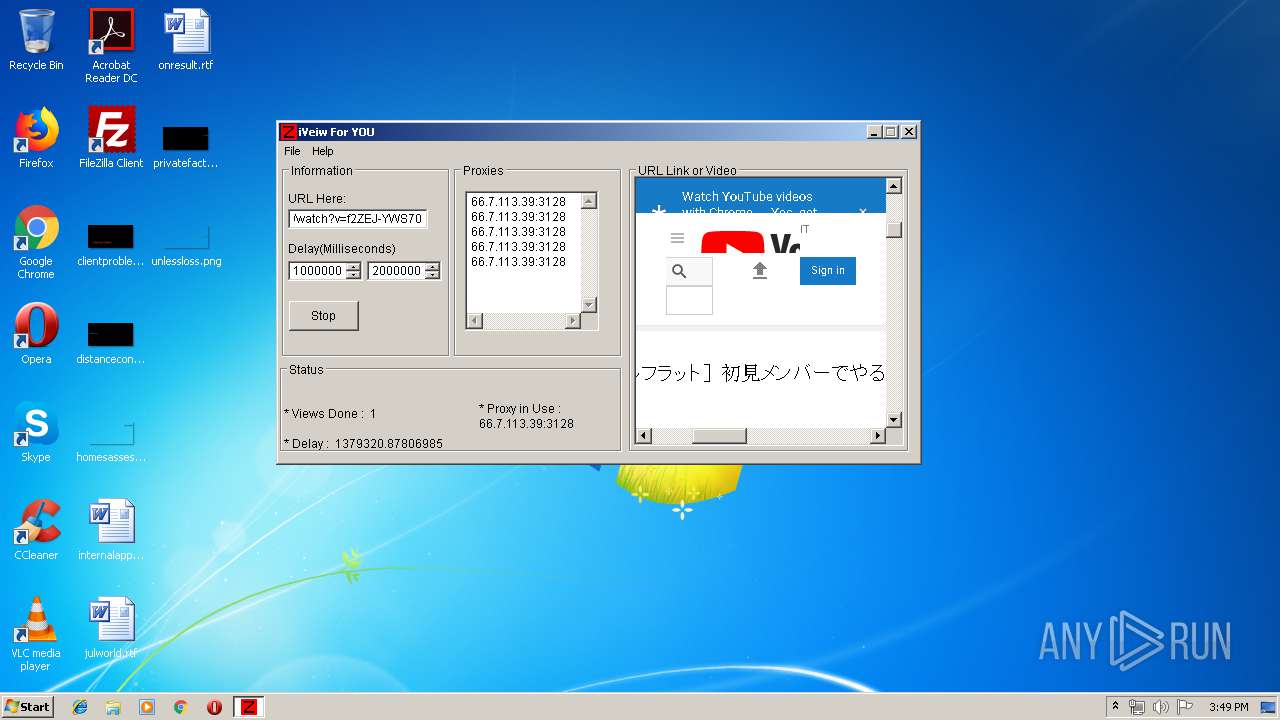
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3960 | iView Fur U v2!.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@youtube[2].txt | — | |
MD5:— | SHA256:— | |||
| 3960 | iView Fur U v2!.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\ServiceLogin[1].txt | — | |
MD5:— | SHA256:— | |||
| 3960 | iView Fur U v2!.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@youtube[1].txt | text | |
MD5:— | SHA256:— | |||
| 3960 | iView Fur U v2!.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\scheduler[1].js | text | |
MD5:— | SHA256:— | |||
| 3960 | iView Fur U v2!.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\www-pagead-id[1].js | text | |
MD5:— | SHA256:— | |||
| 3960 | iView Fur U v2!.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\watch[1].txt | html | |
MD5:— | SHA256:— | |||
| 3960 | iView Fur U v2!.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\KFOlCnqEu92Fr1MmEU9fBBc8[1].eot | eot | |
MD5:03BB29D6722BF52F7FE88A6ED47D9E6E | SHA256:DAA5D6292A35A6DC7E075436D0567DBE02515D5E886731FA5CA230E3D8FE26DD | |||
| 3960 | iView Fur U v2!.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\www-core-vflMxh-5O[1].css | text | |
MD5:— | SHA256:— | |||
| 3960 | iView Fur U v2!.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\base[1].js | text | |
MD5:— | SHA256:— | |||
| 3960 | iView Fur U v2!.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\spf[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
15
DNS requests
8
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
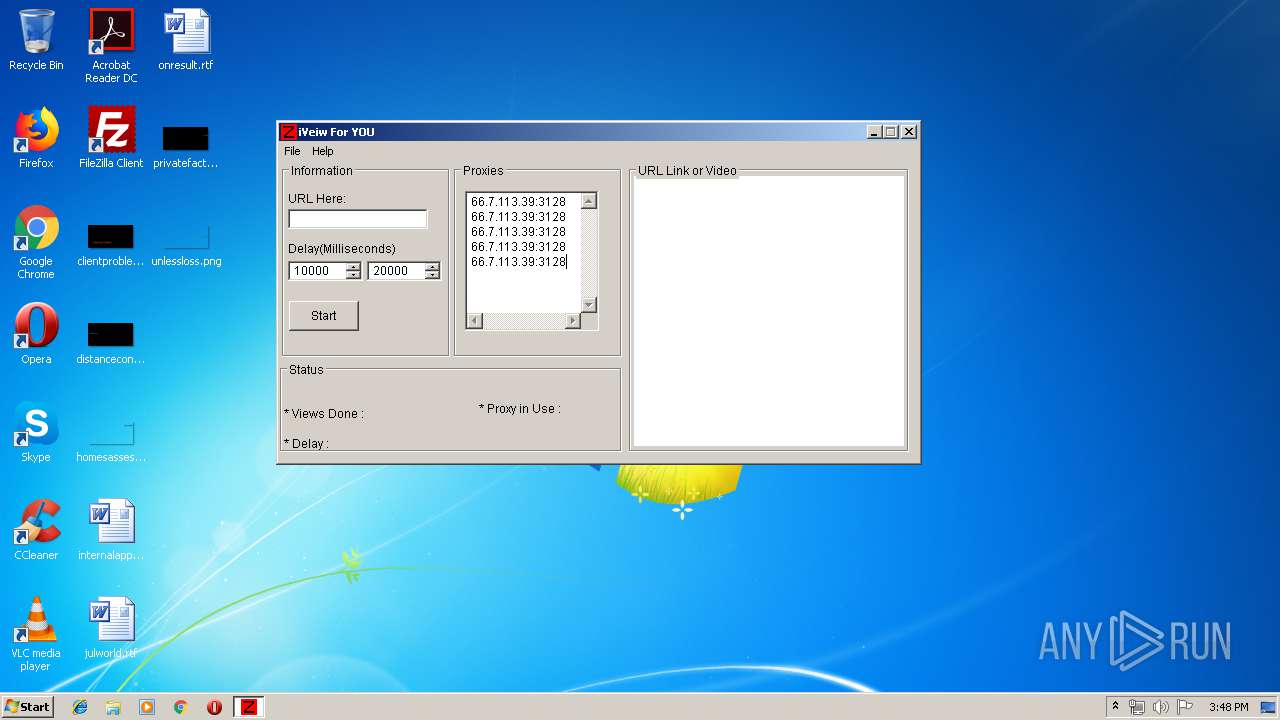
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3960 | iView Fur U v2!.exe | 172.217.22.78:443 | www.youtube.com | Google Inc. | US | whitelisted |
3960 | iView Fur U v2!.exe | 216.58.206.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3960 | iView Fur U v2!.exe | 216.58.206.14:443 | www.youtube.com | Google Inc. | US | whitelisted |
3960 | iView Fur U v2!.exe | 172.217.21.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
3960 | iView Fur U v2!.exe | 216.58.207.33:443 | yt3.ggpht.com | Google Inc. | US | whitelisted |
3960 | iView Fur U v2!.exe | 216.58.207.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3960 | iView Fur U v2!.exe | 172.217.16.142:443 | www.youtube.com | Google Inc. | US | whitelisted |
3960 | iView Fur U v2!.exe | 173.194.76.155:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.youtube.com |
| whitelisted |
s.ytimg.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
yt3.ggpht.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |