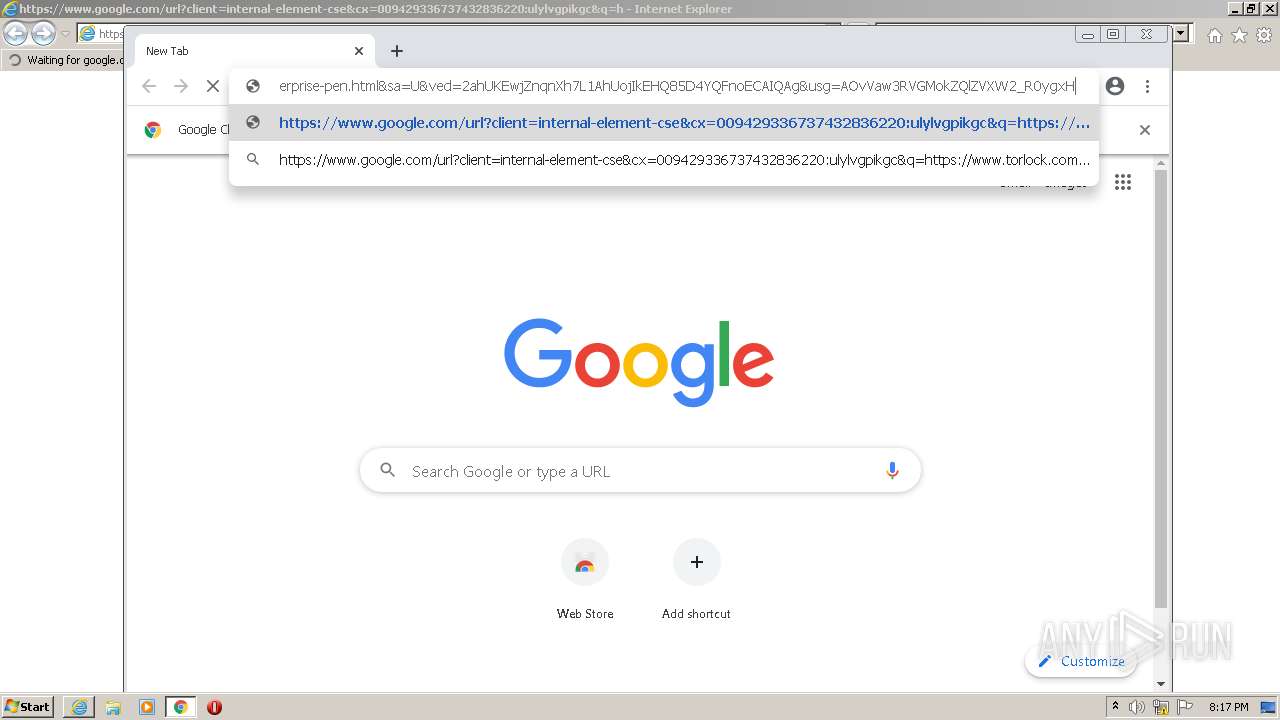
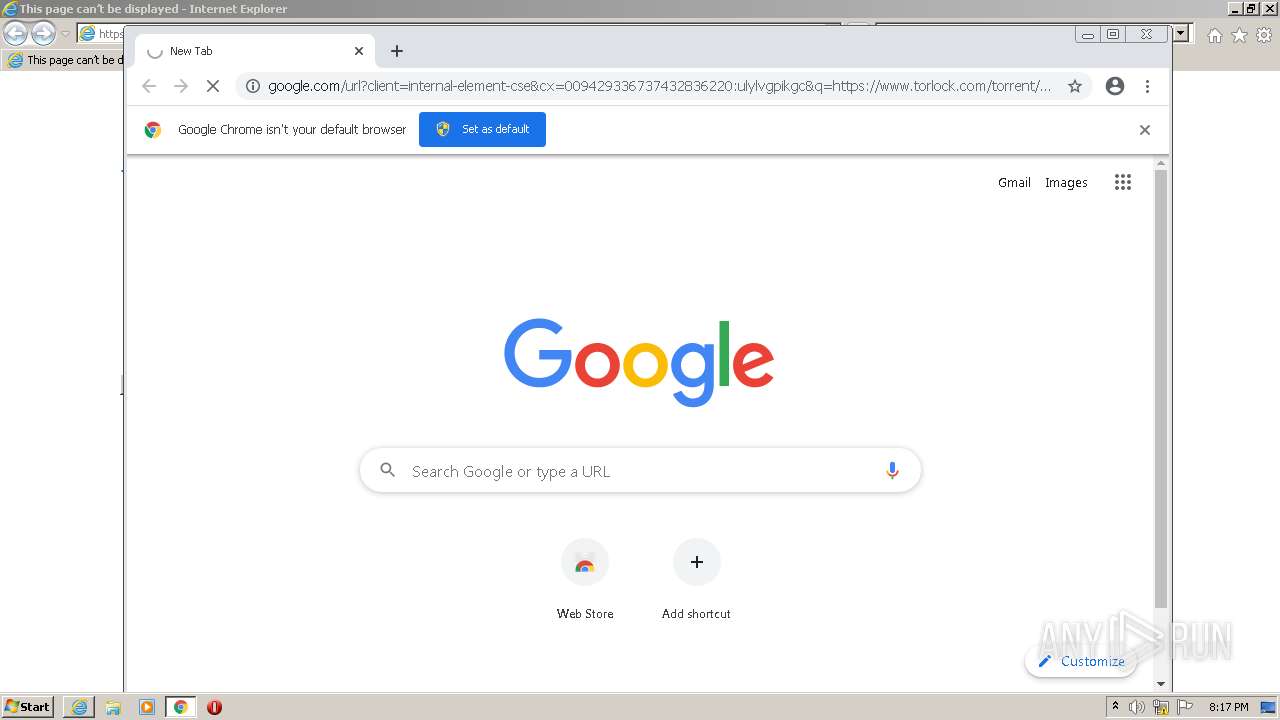
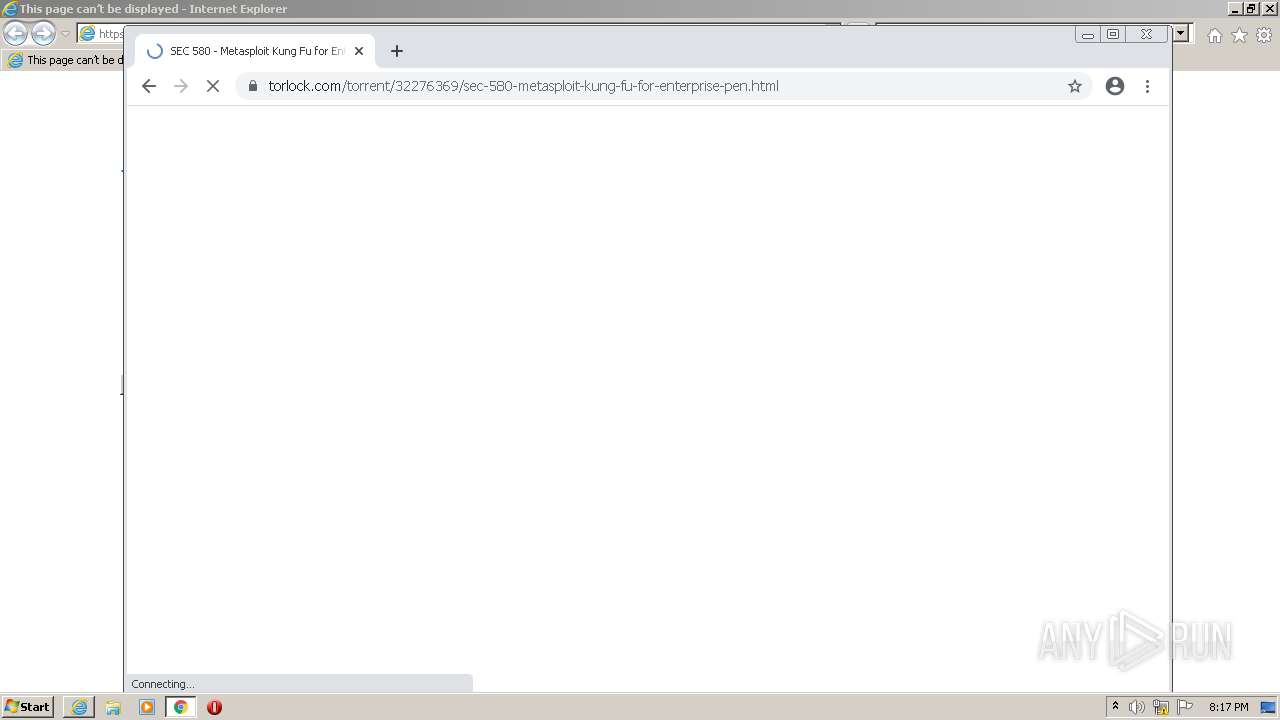
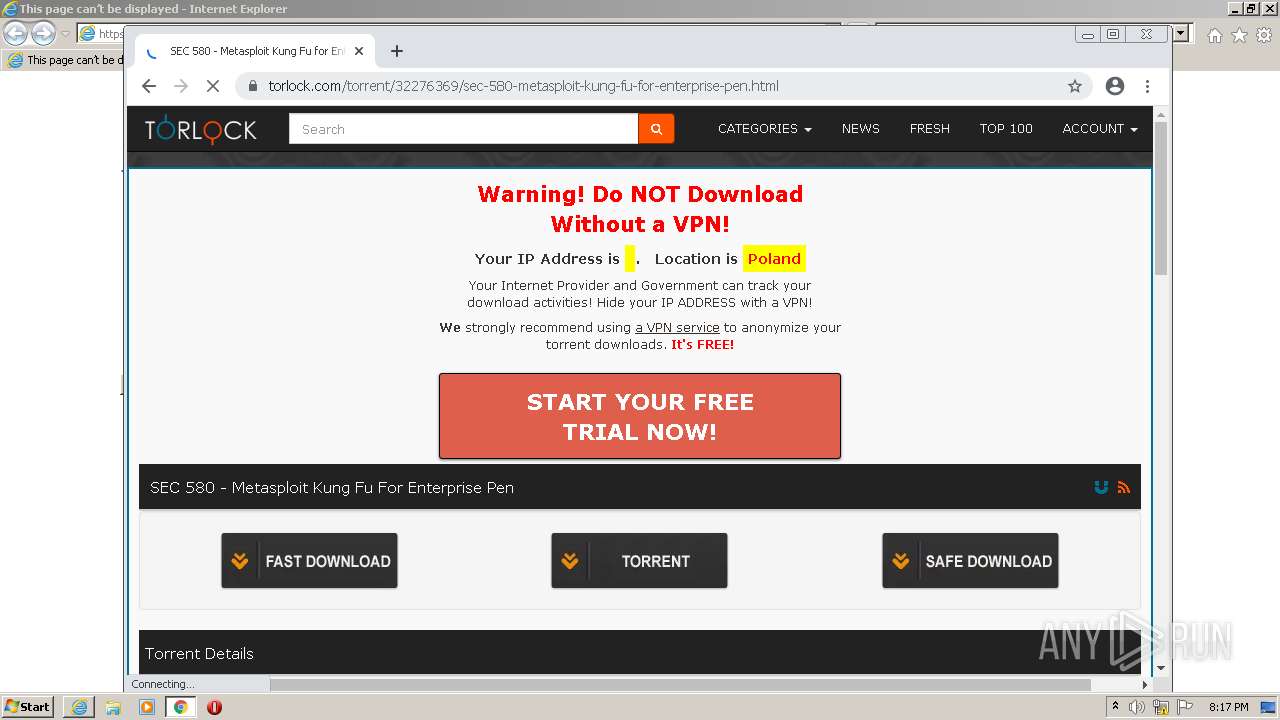
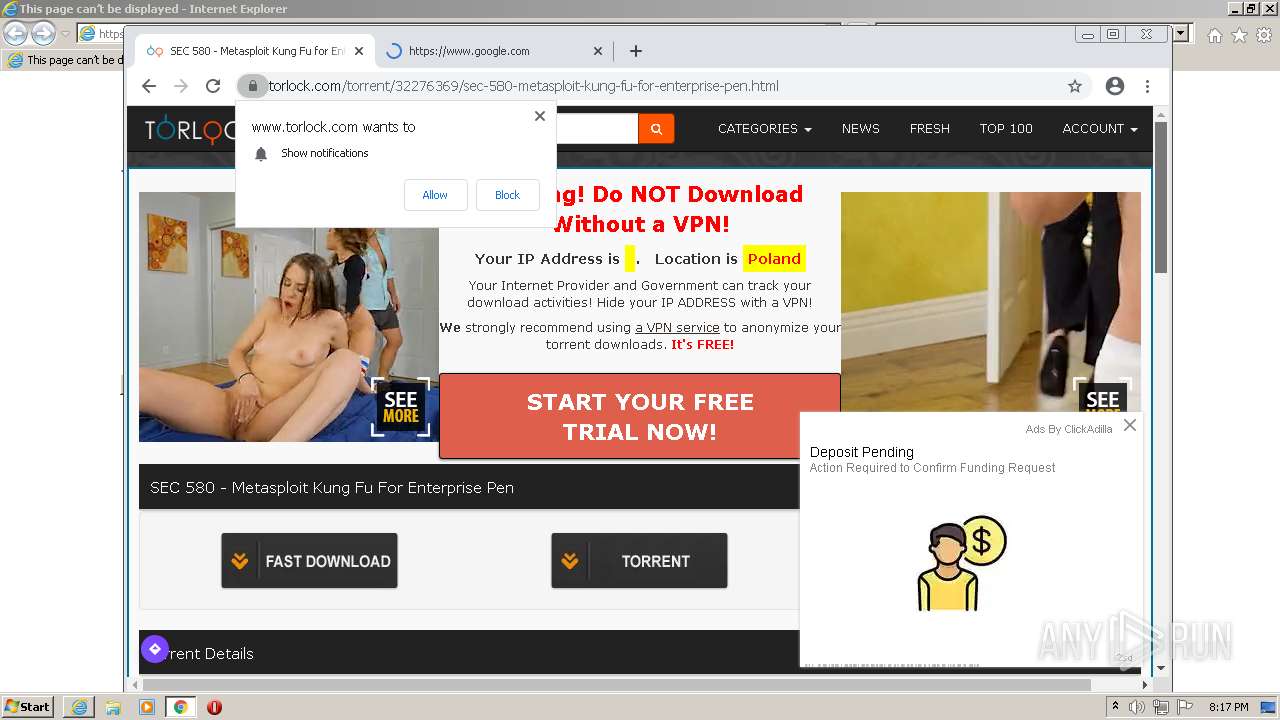
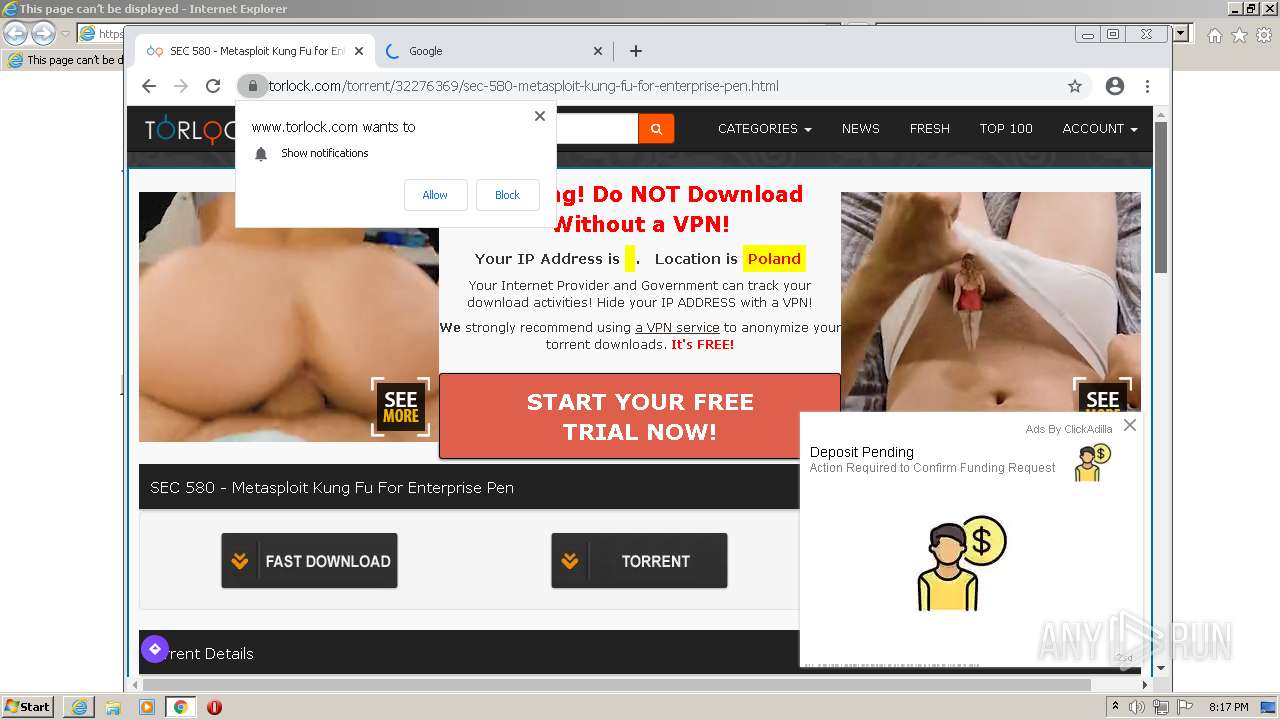
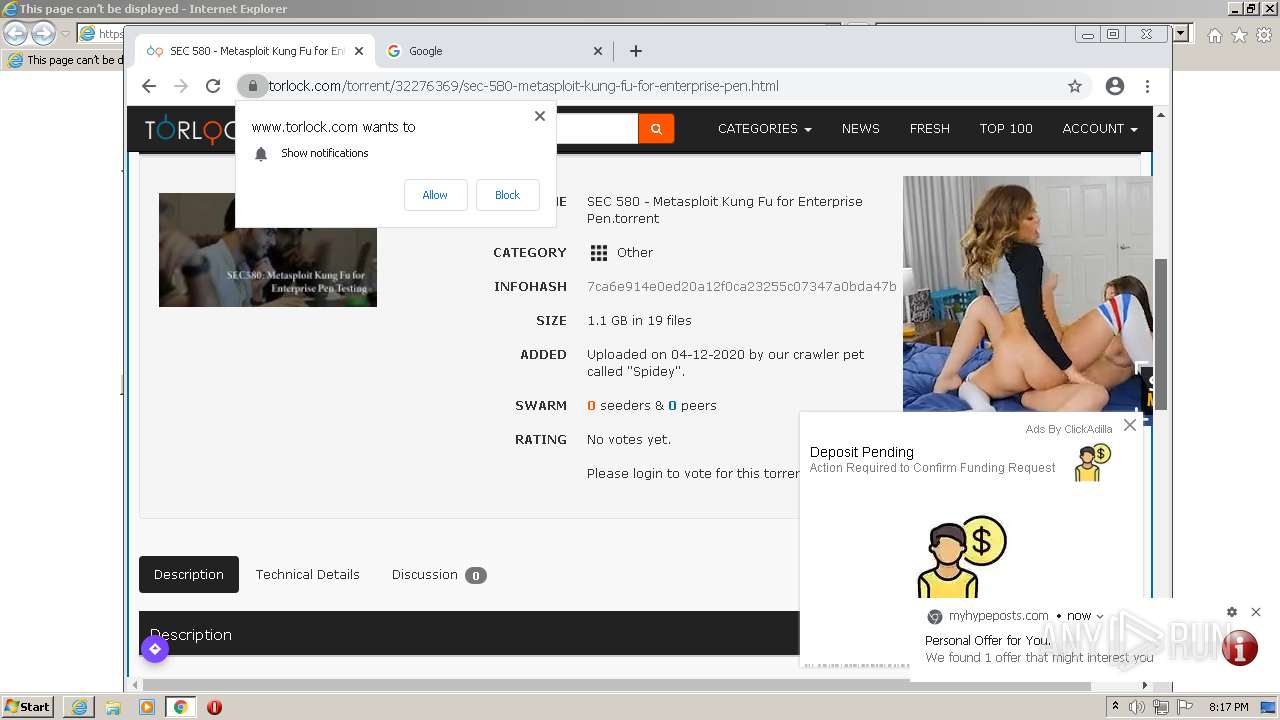
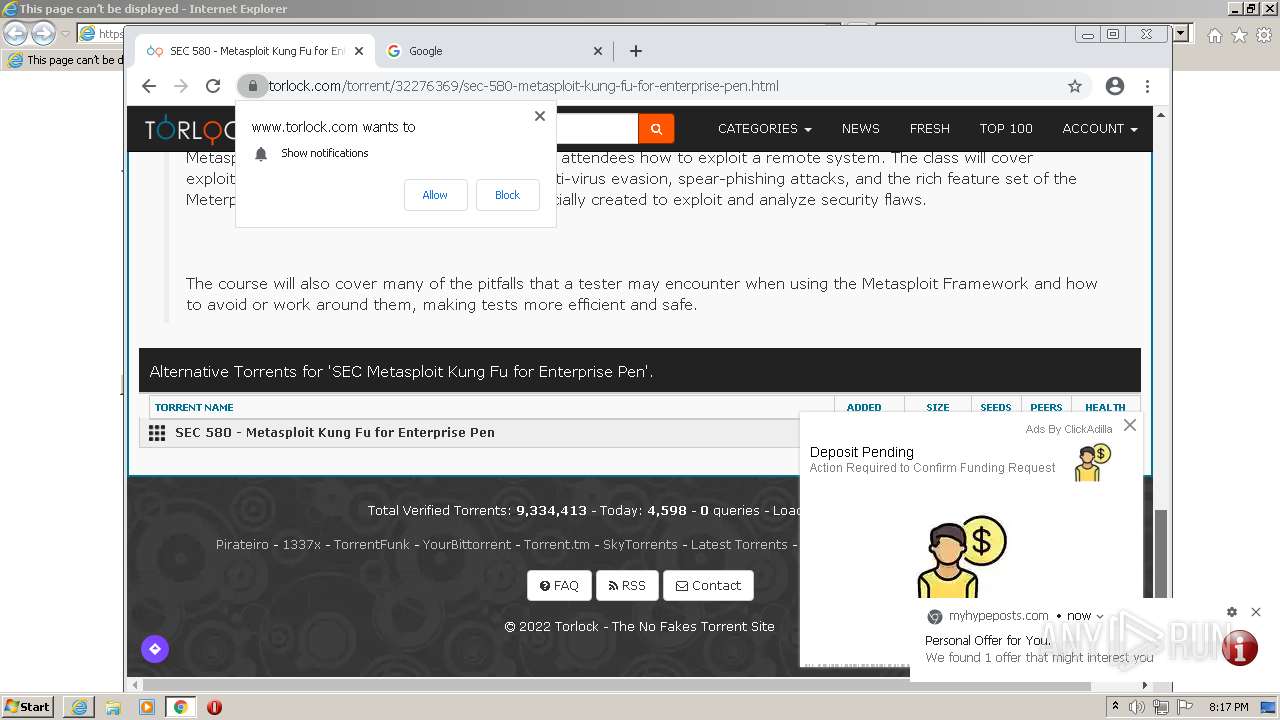
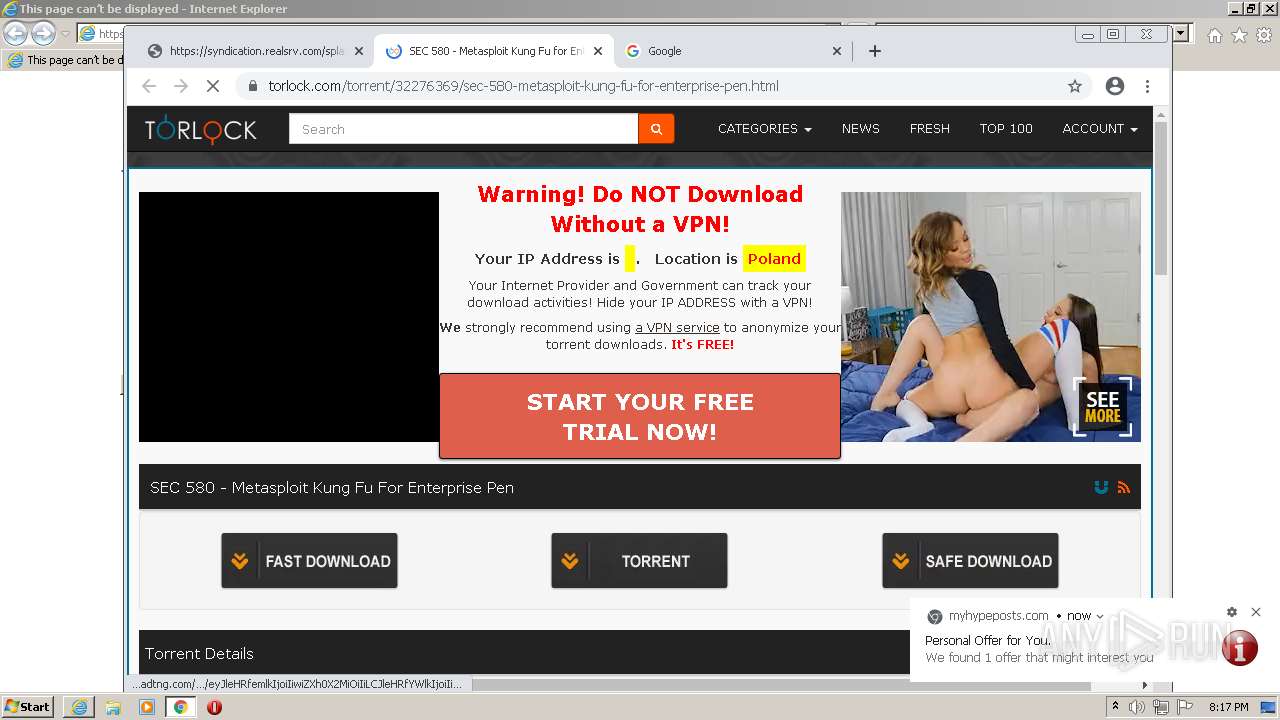
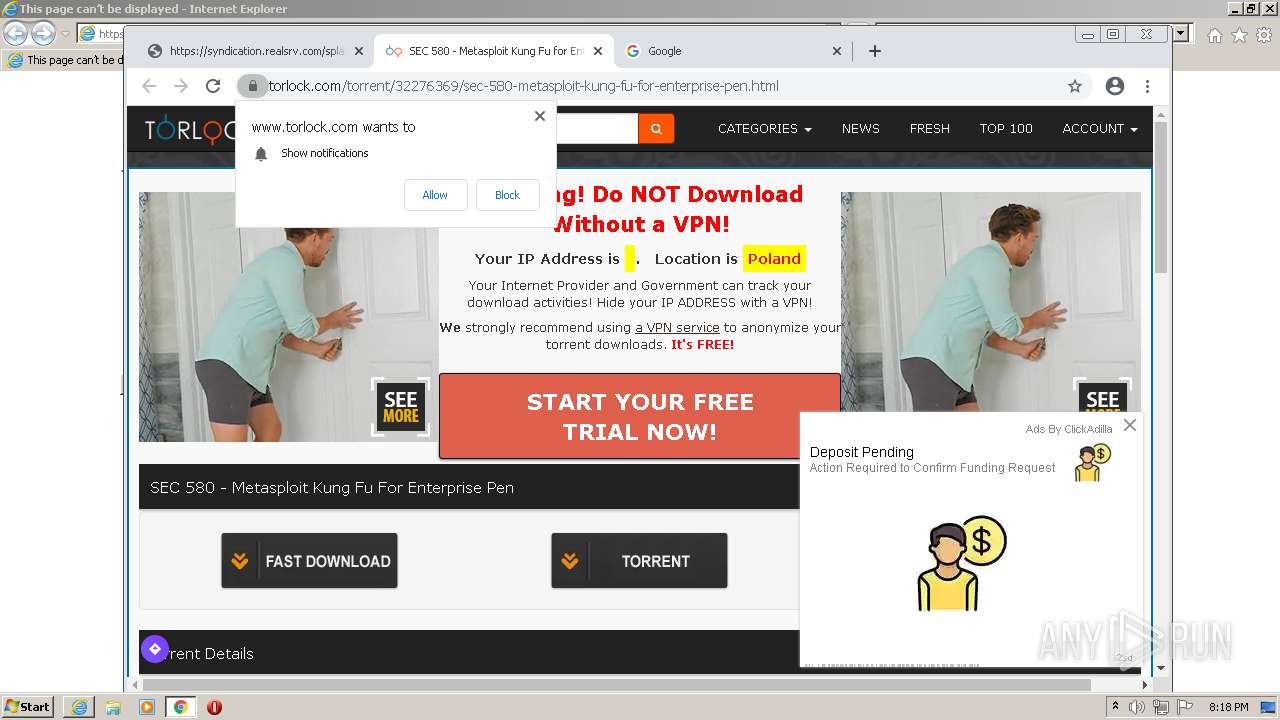
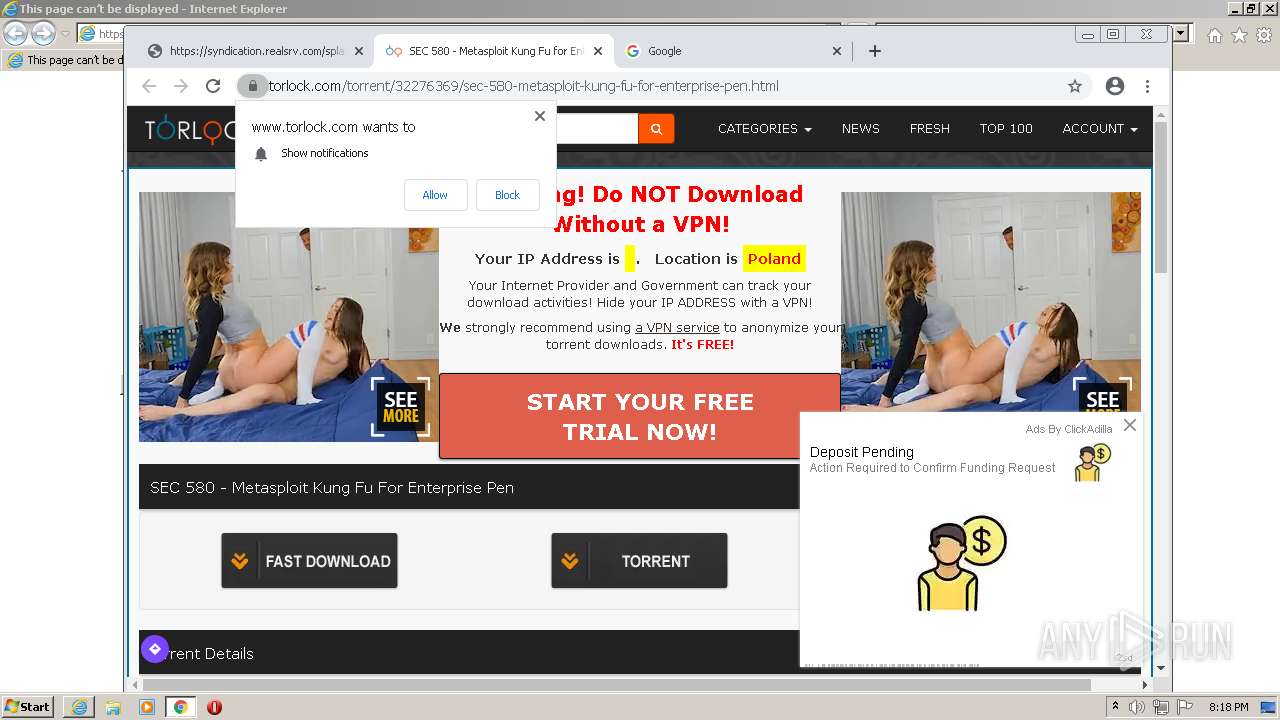
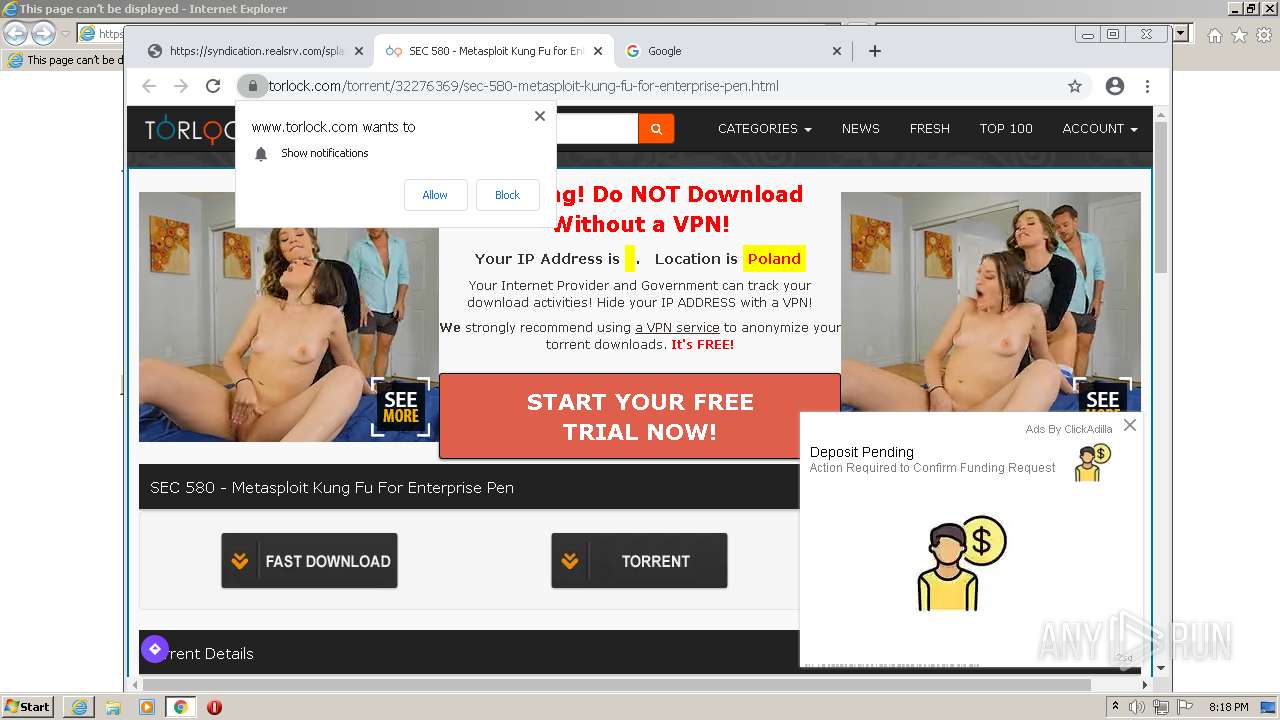
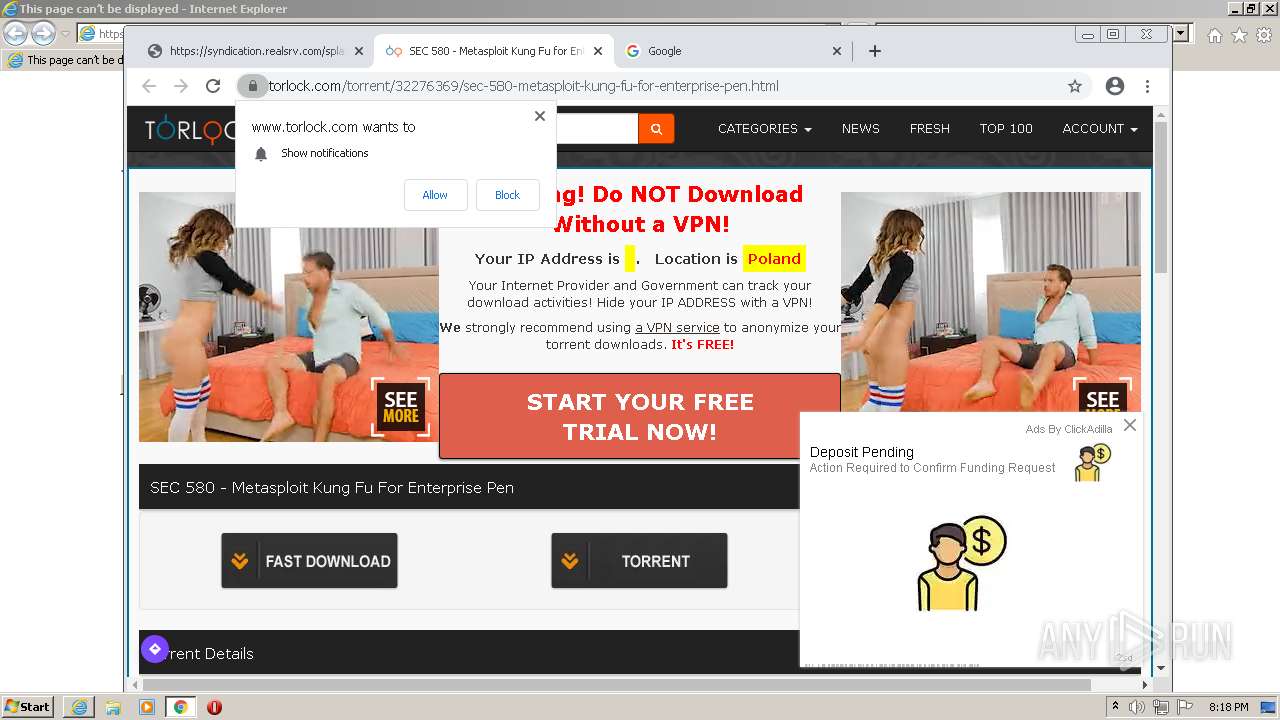
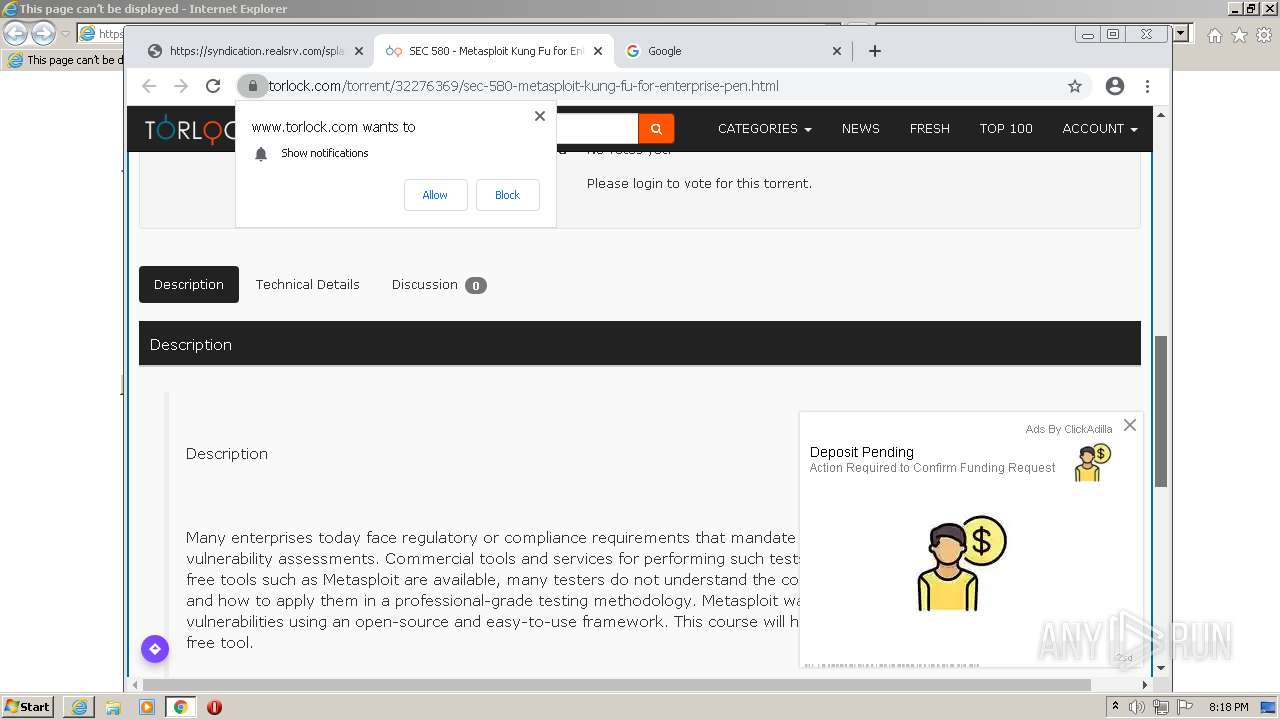
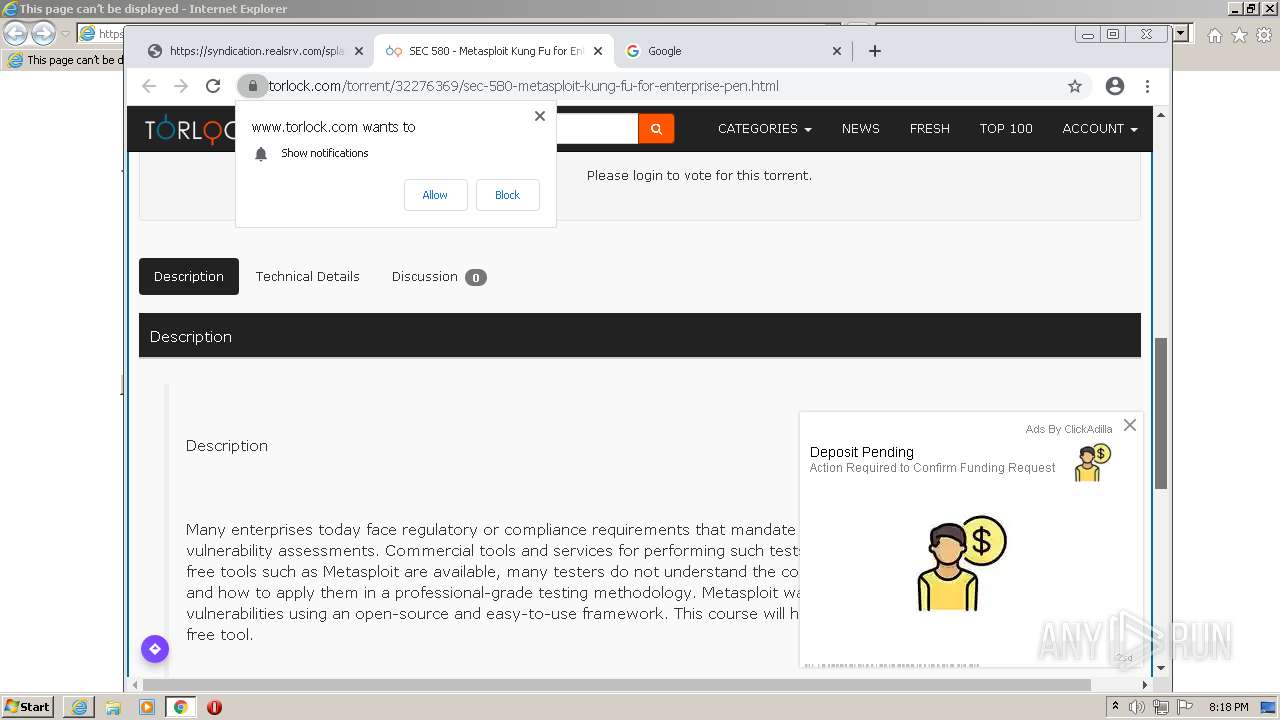
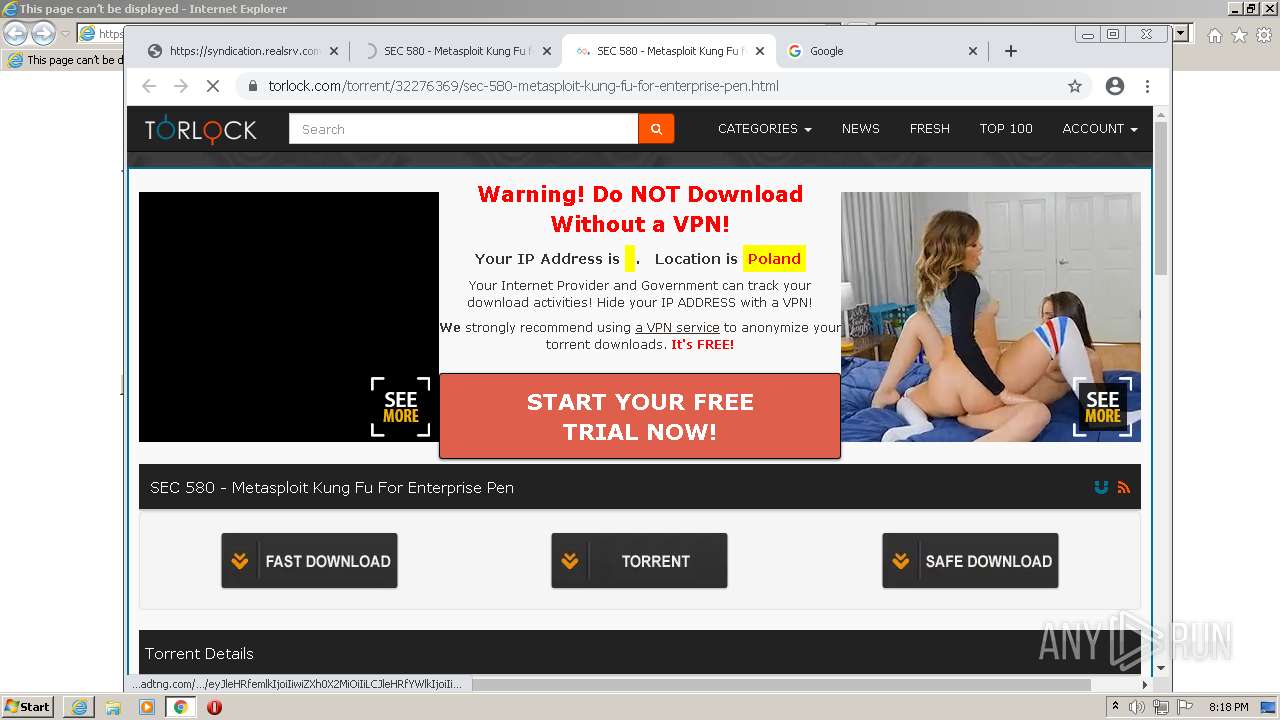
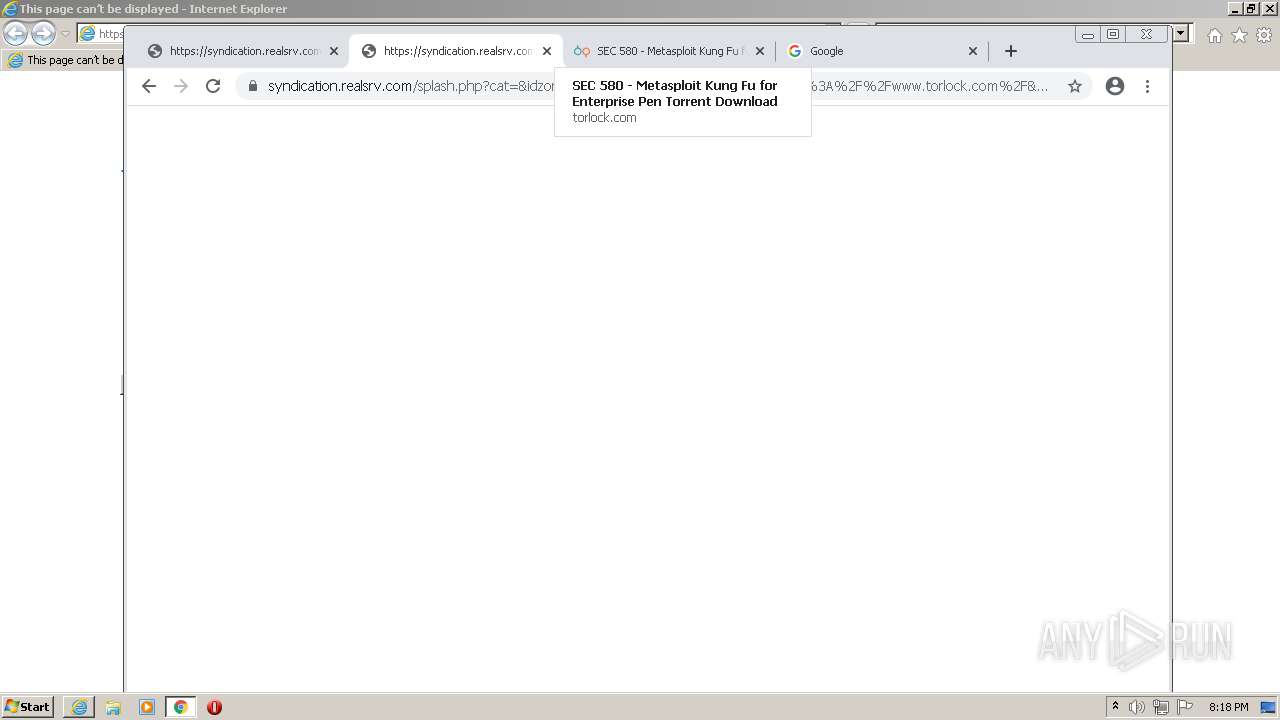
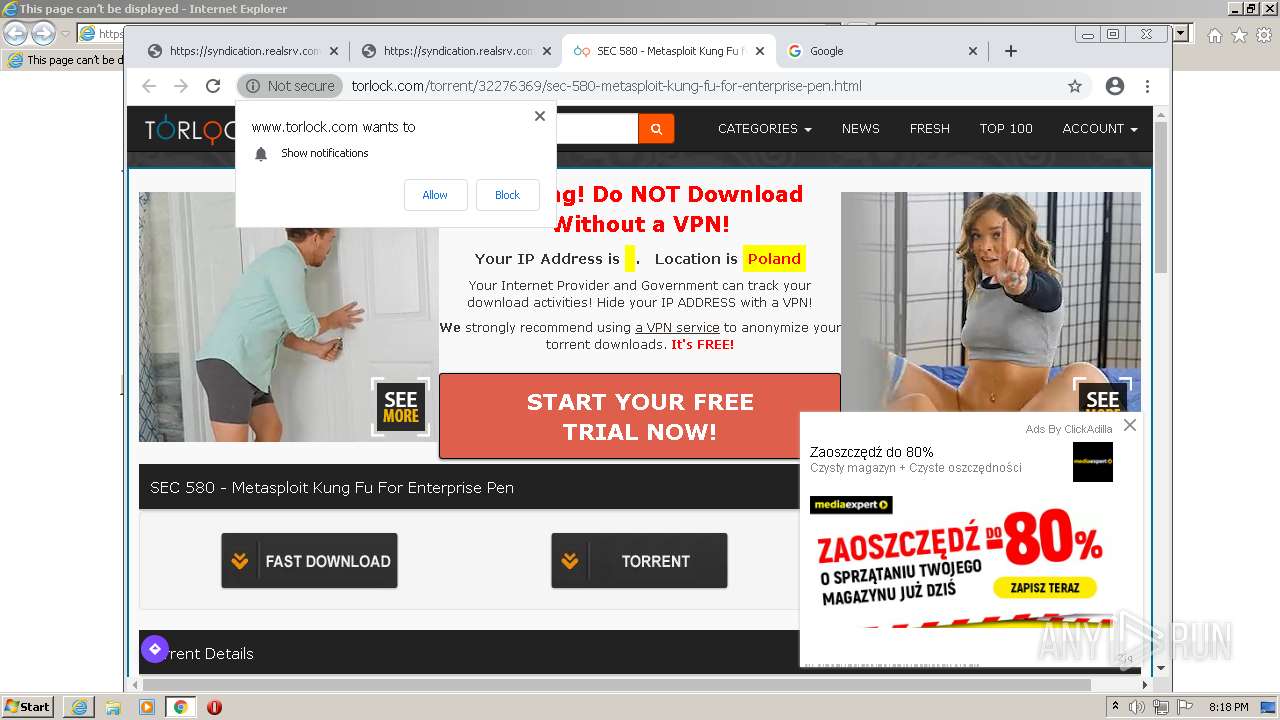
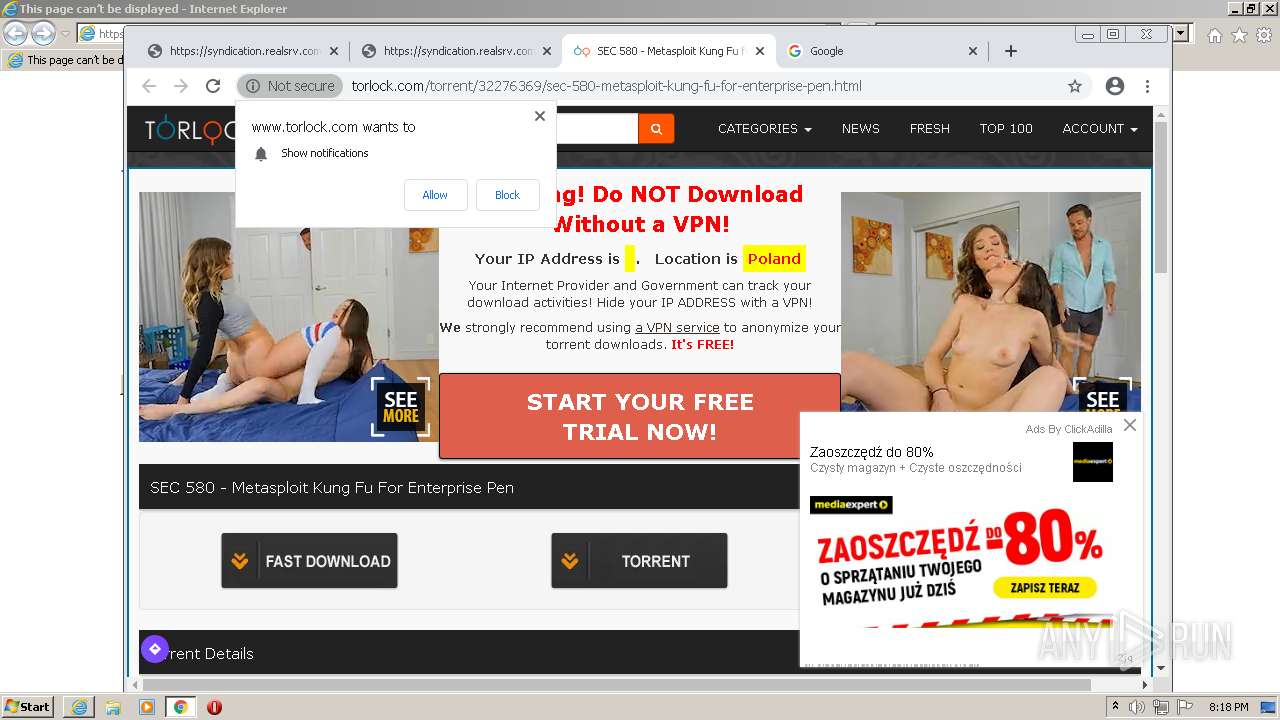
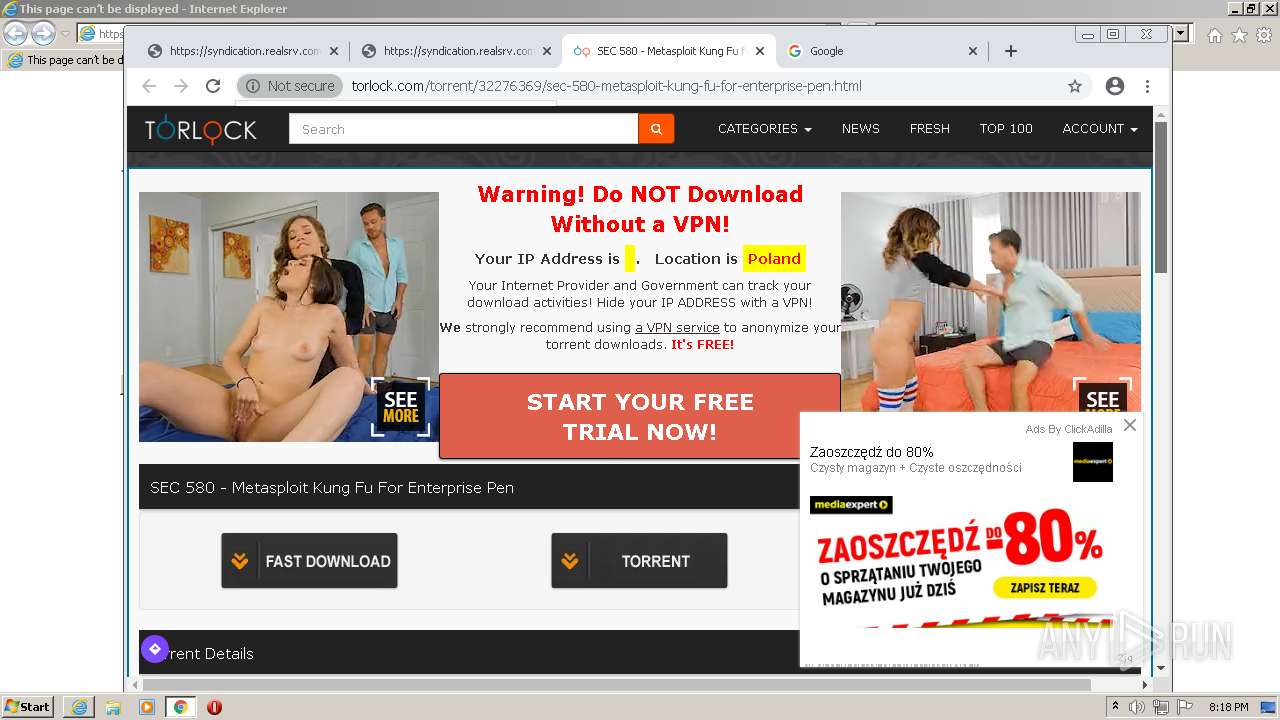
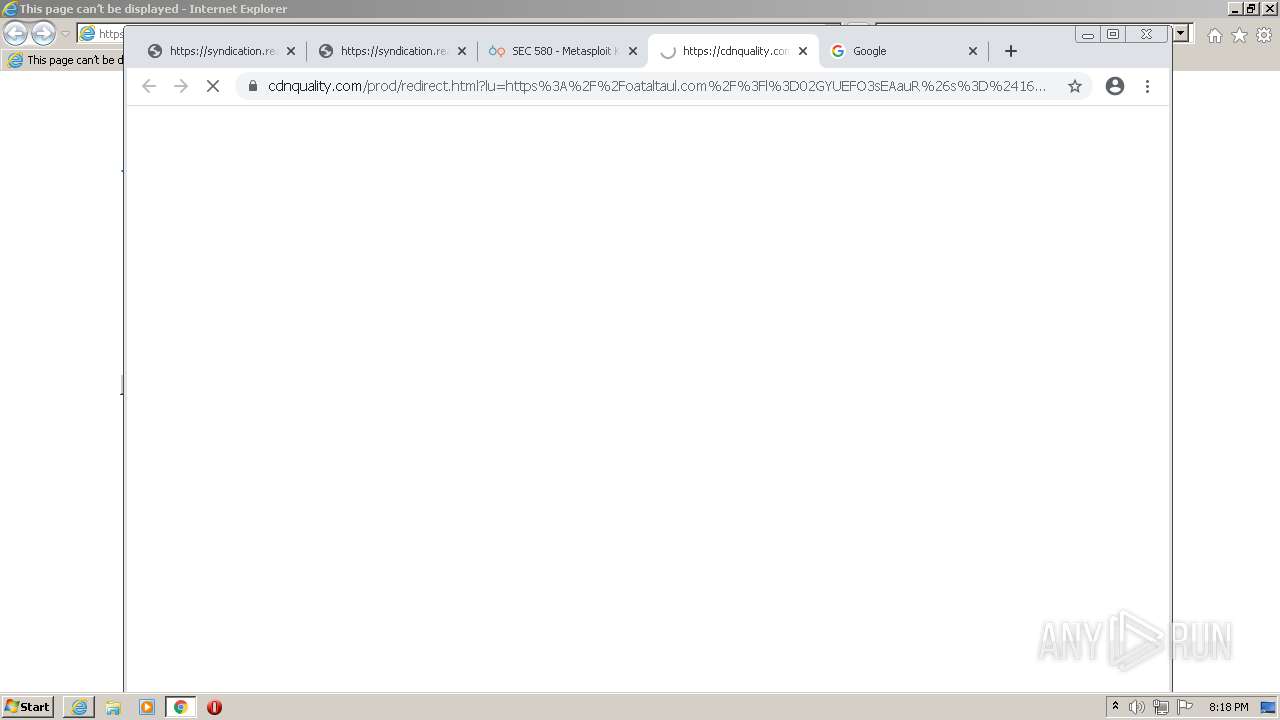
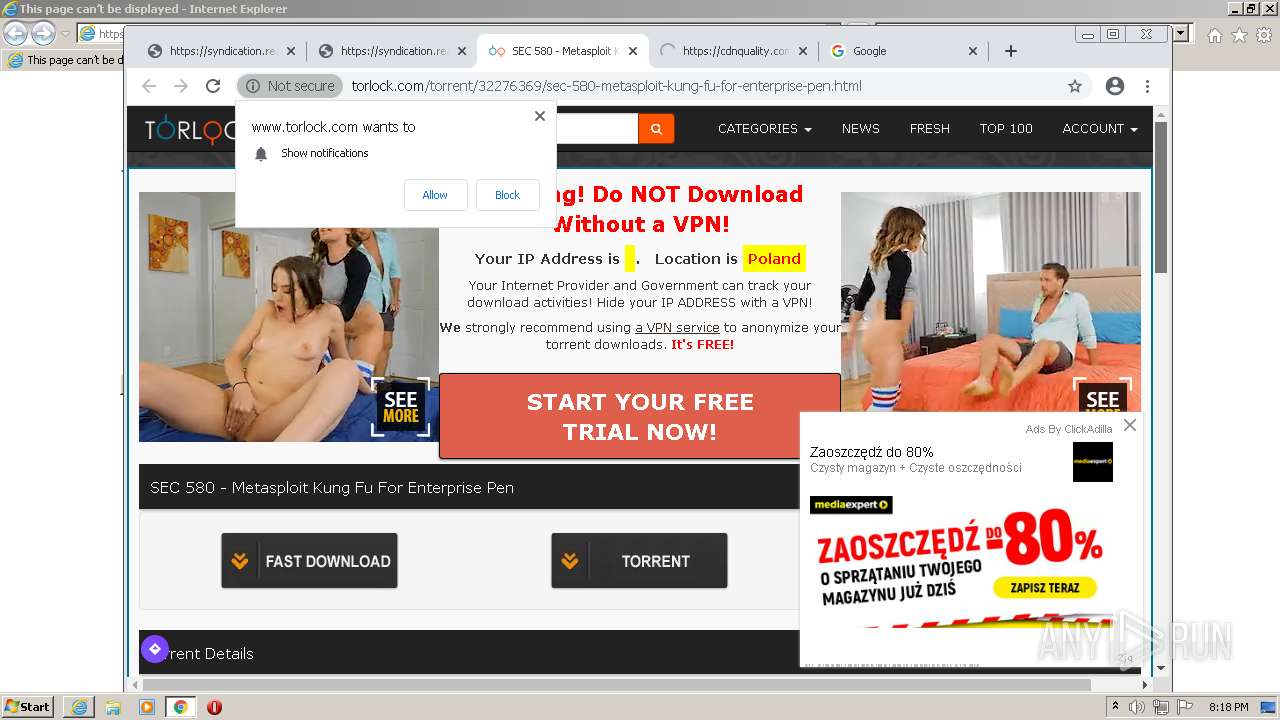
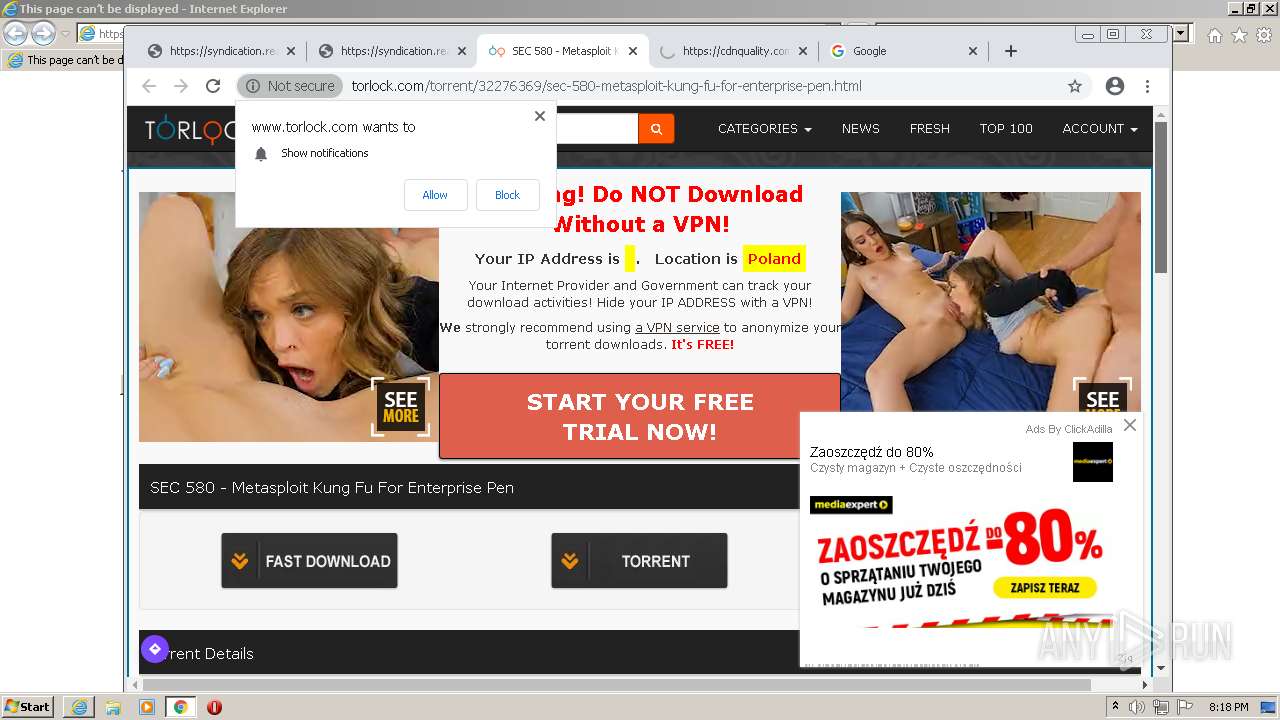
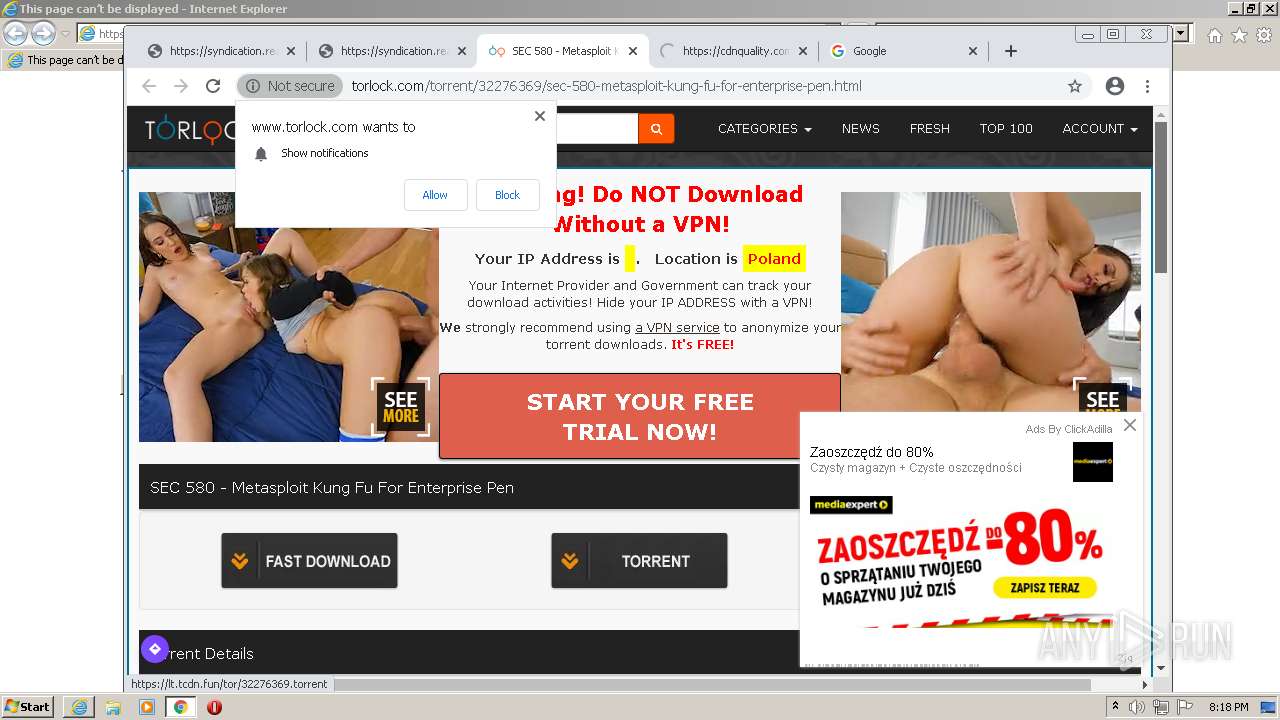
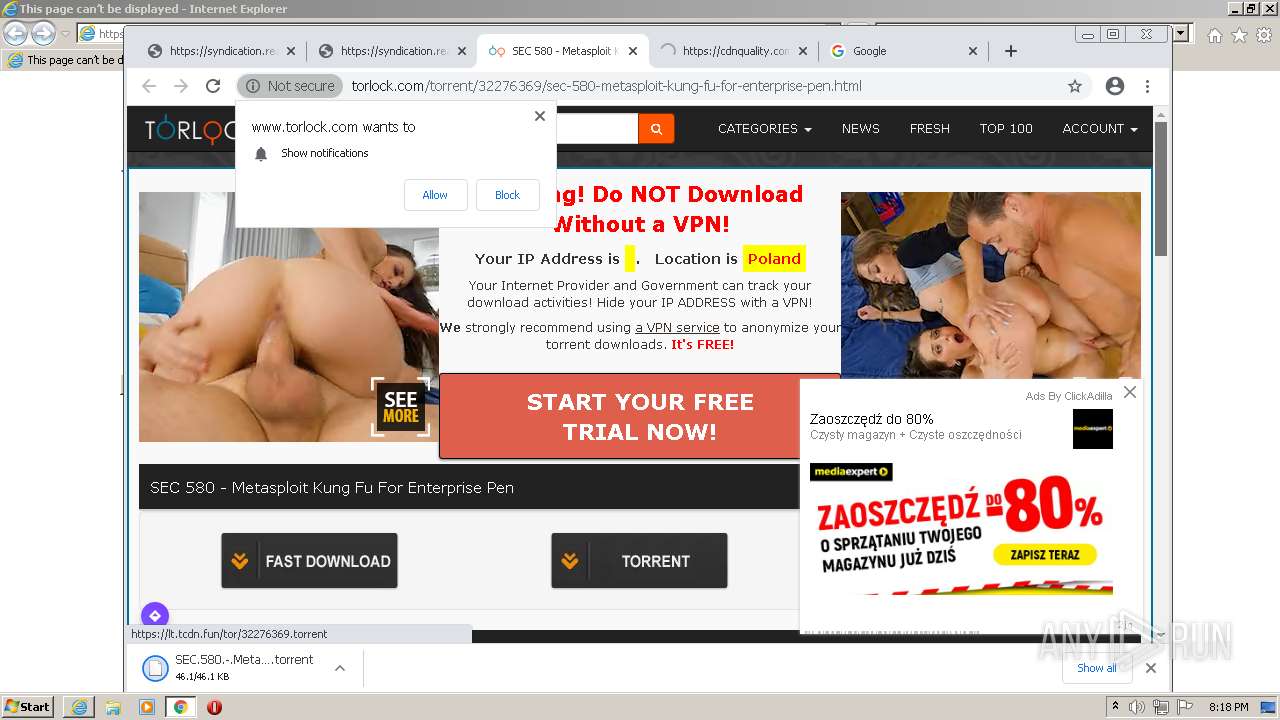
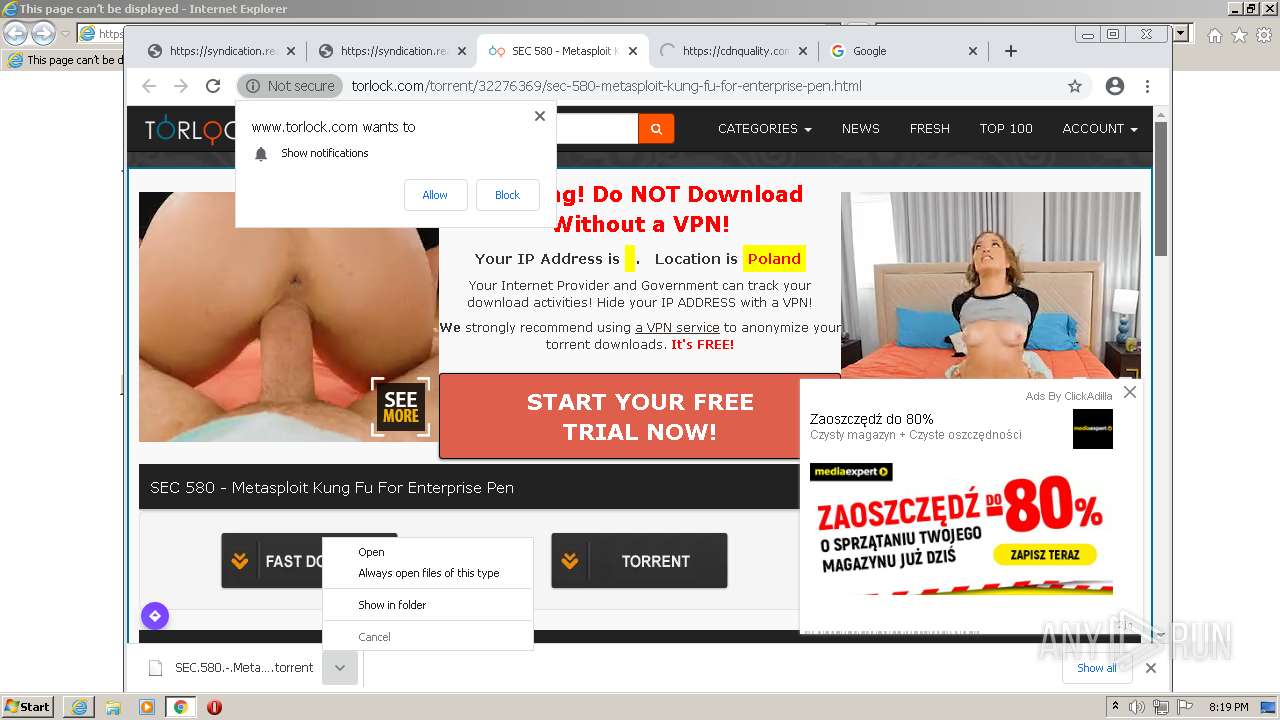
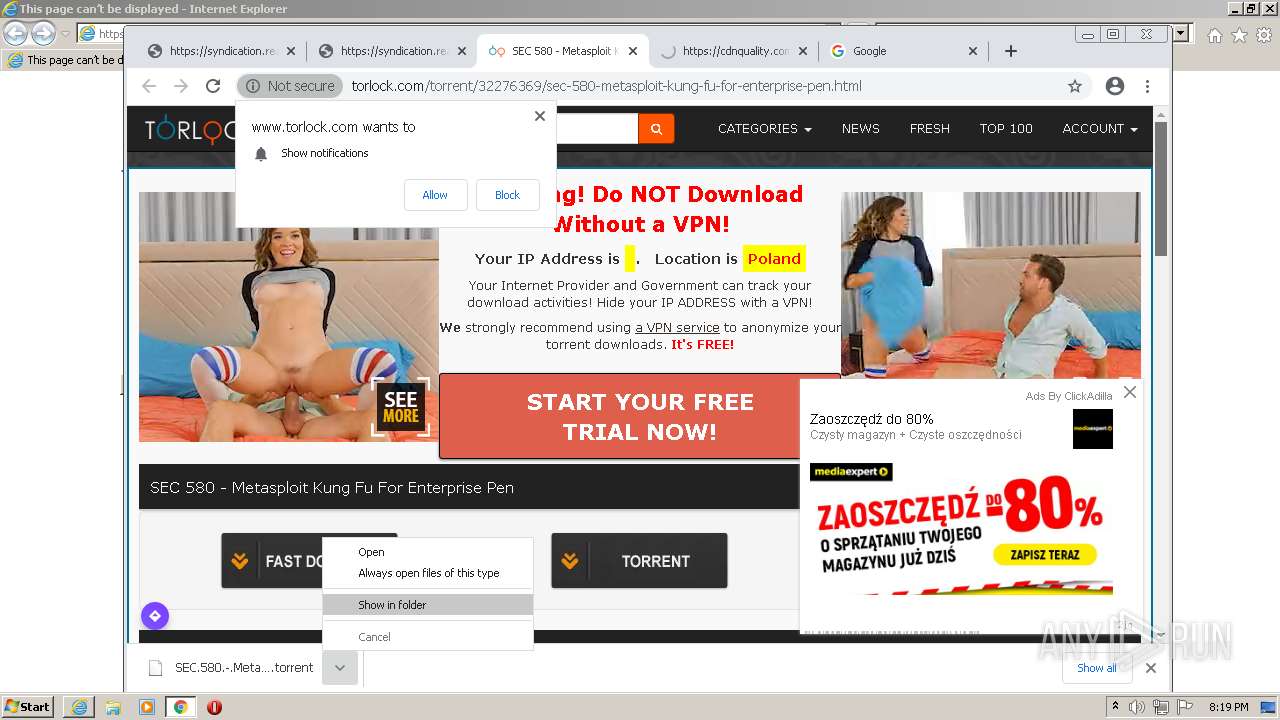
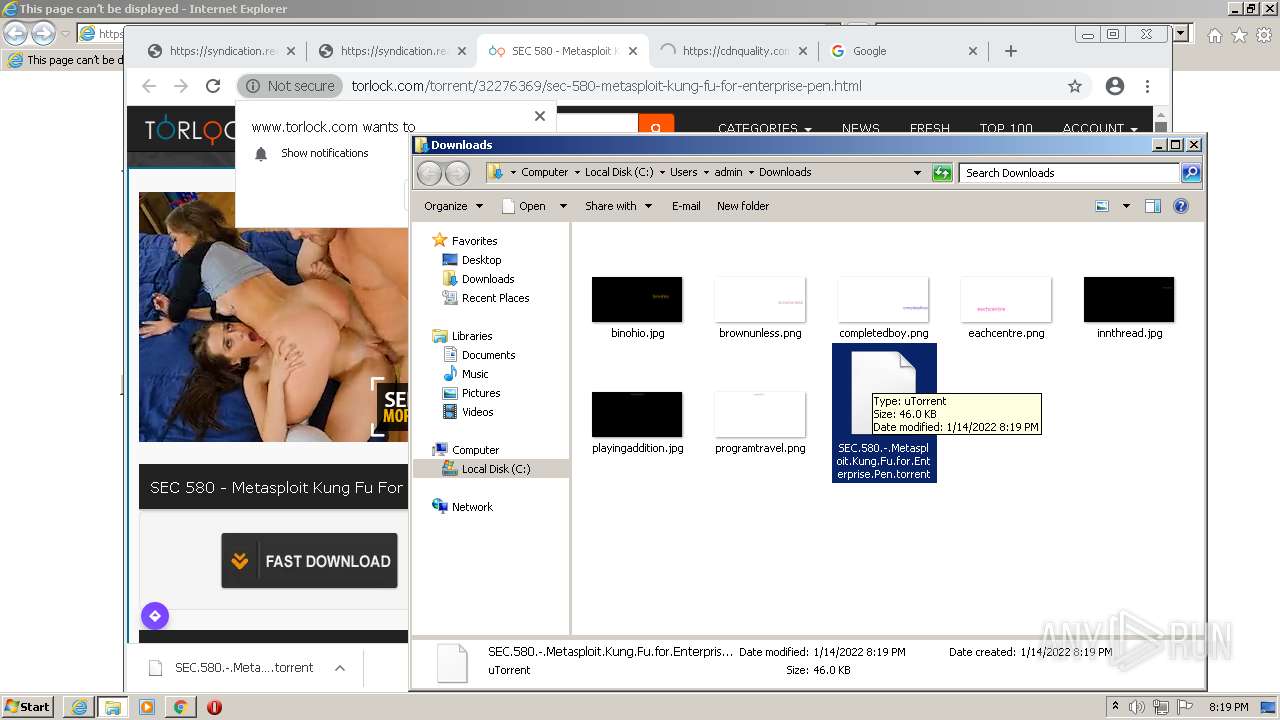
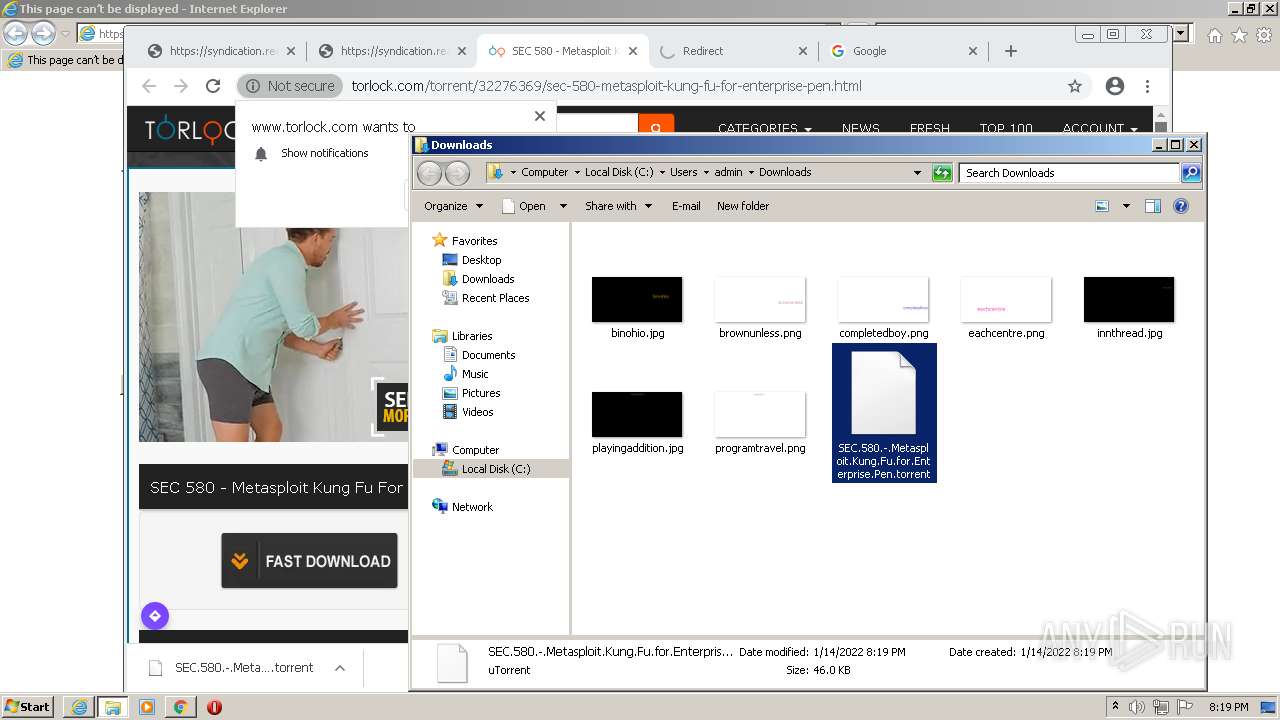
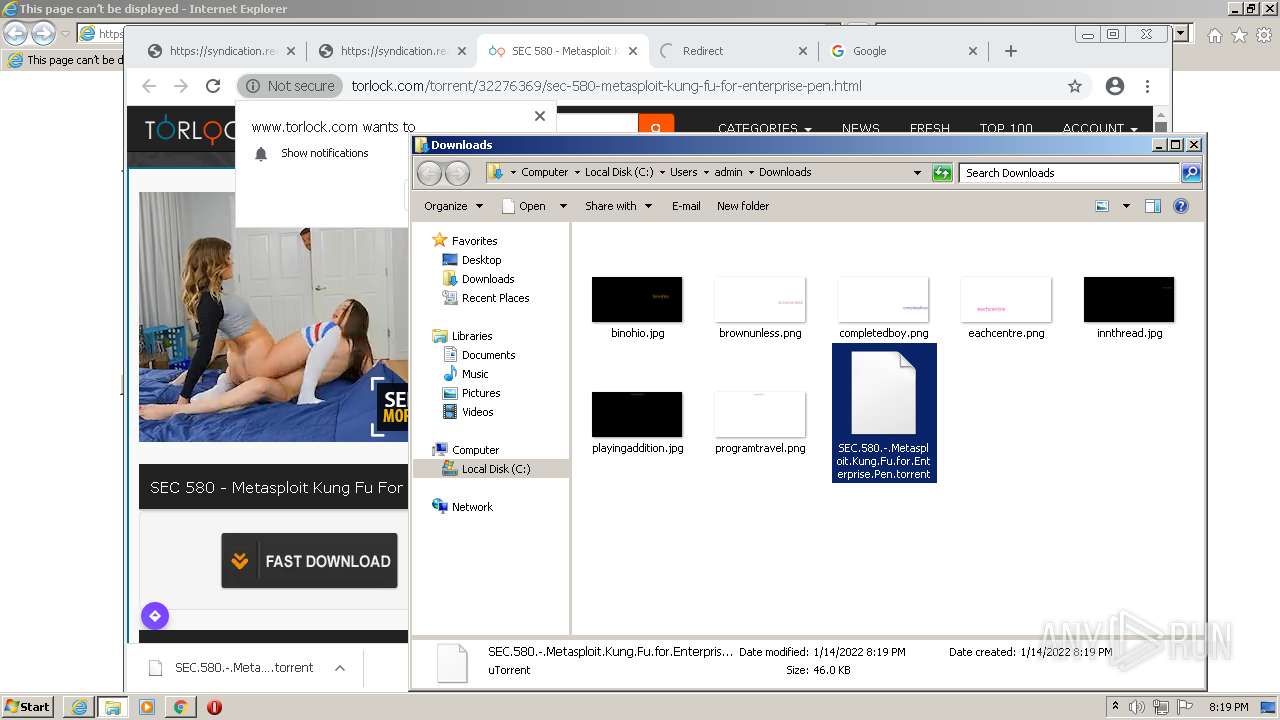
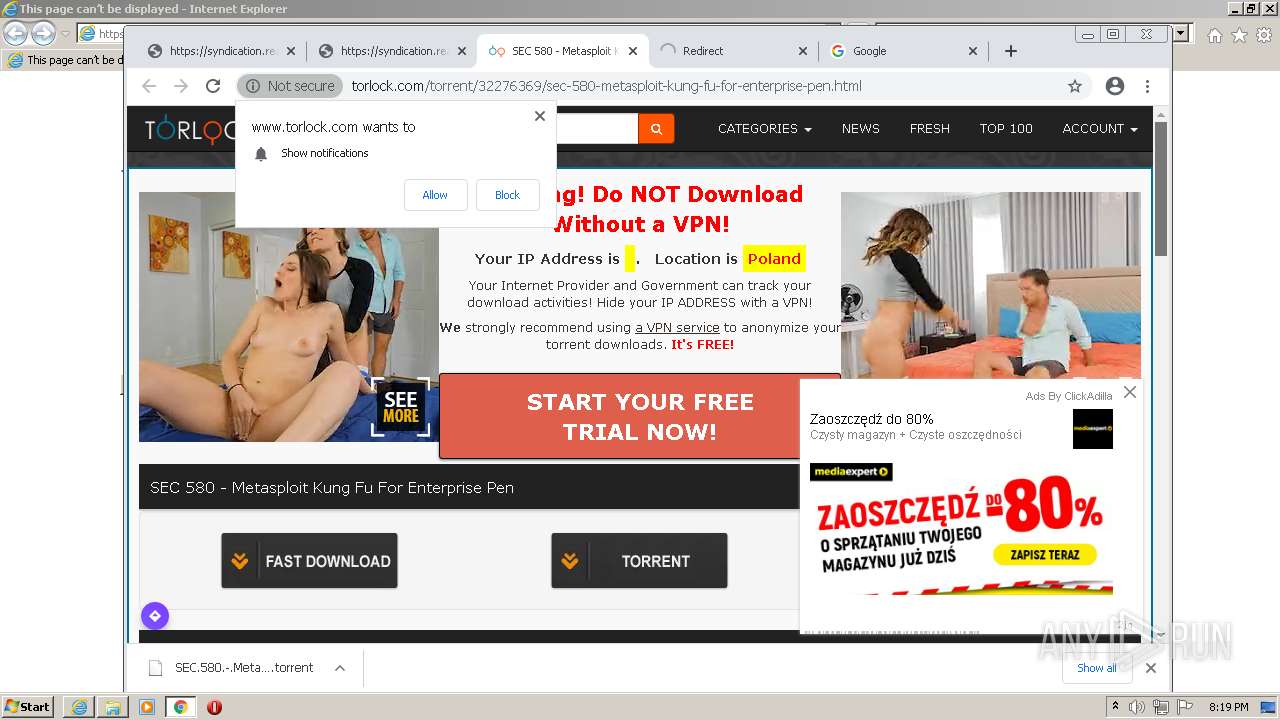
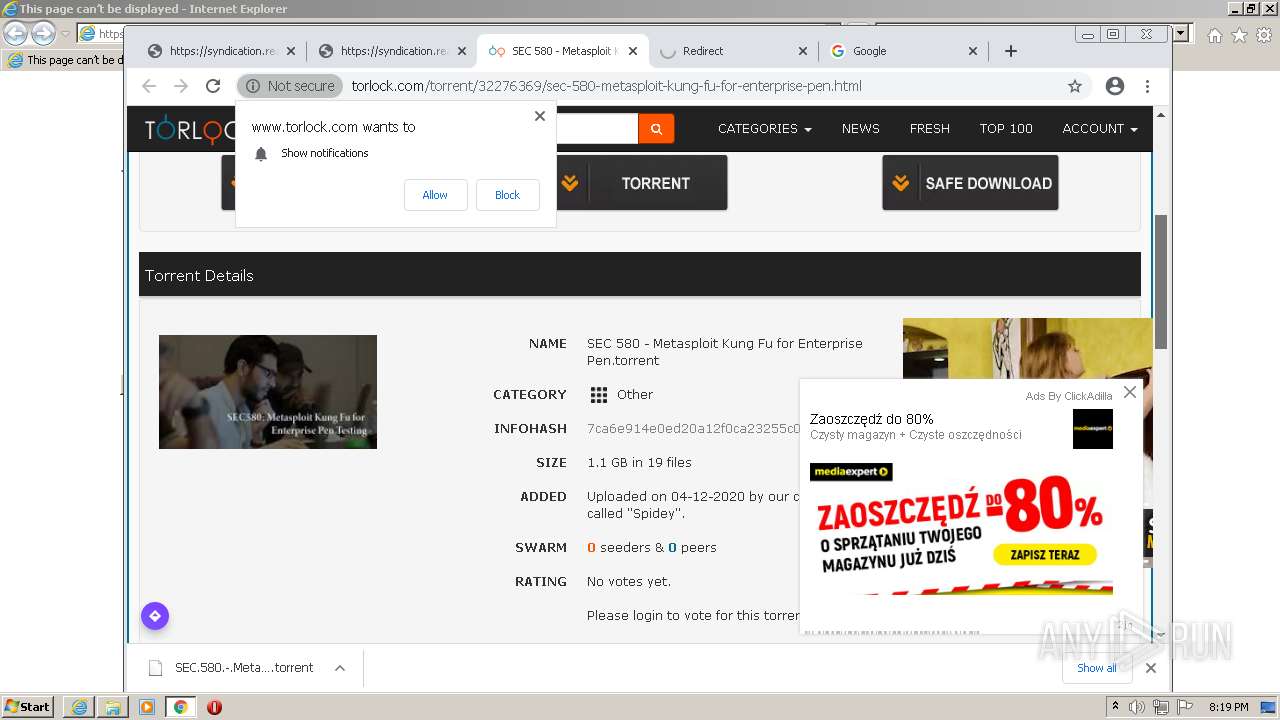
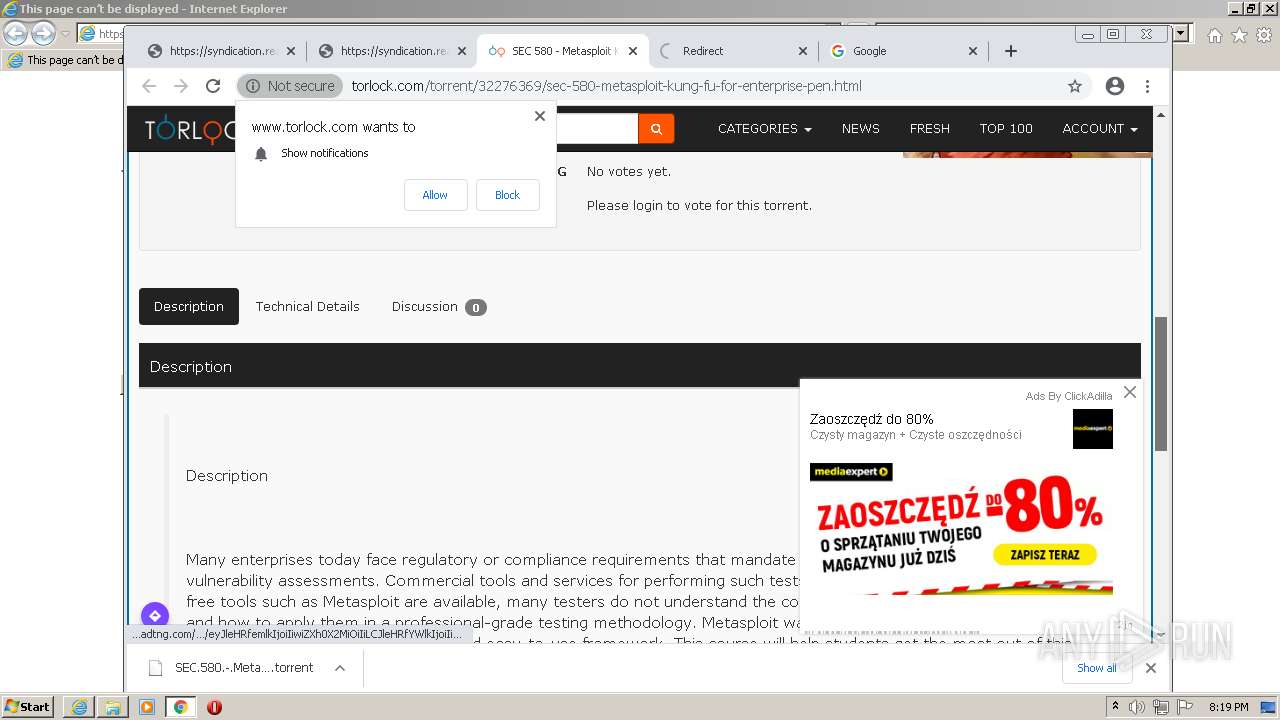
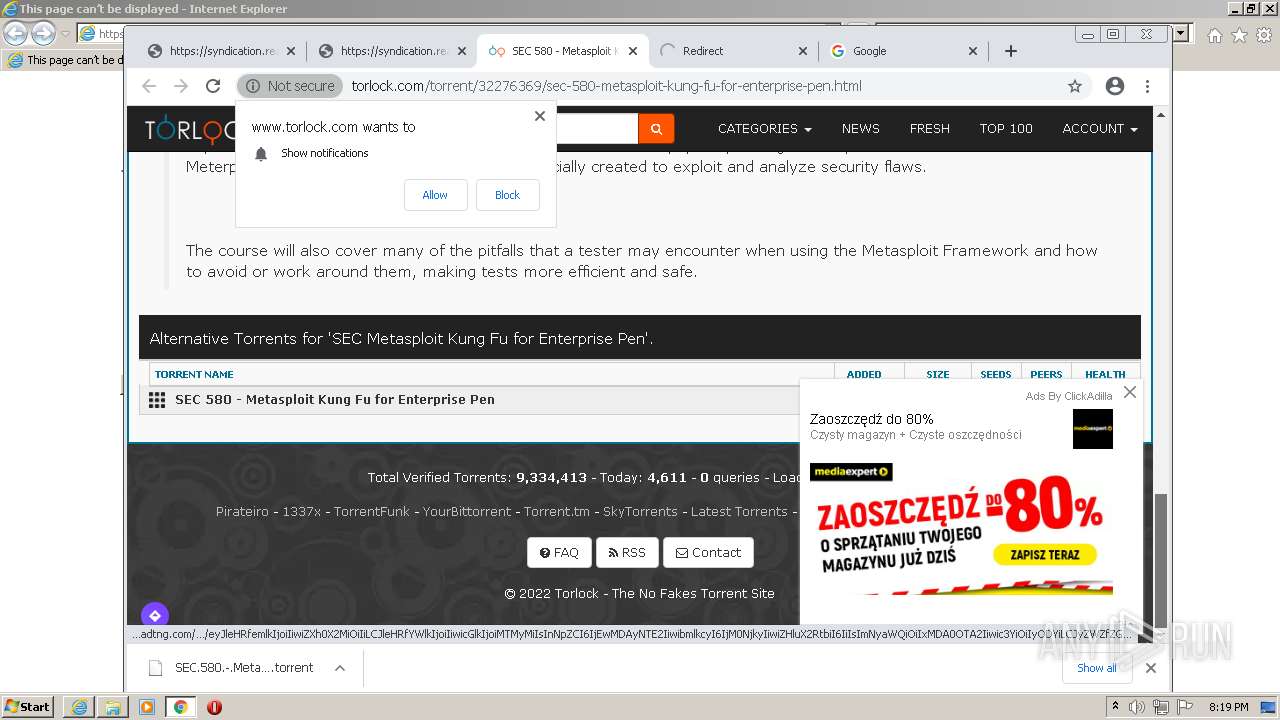
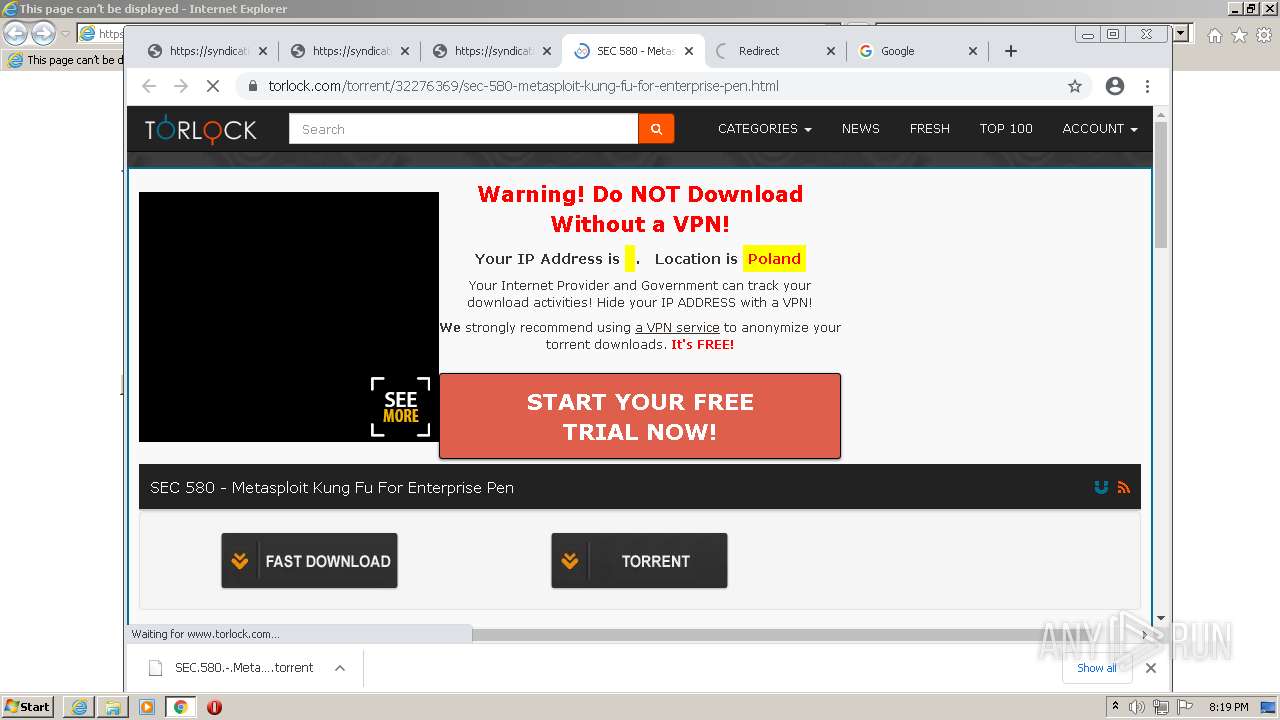
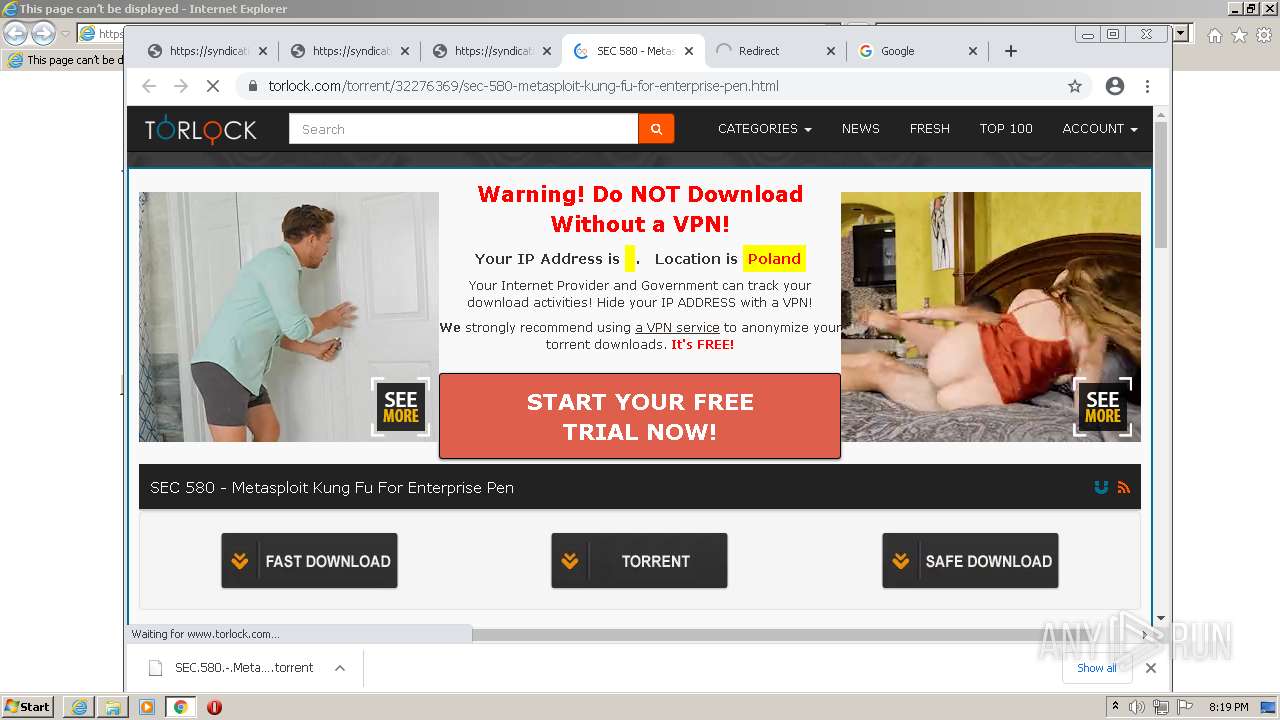
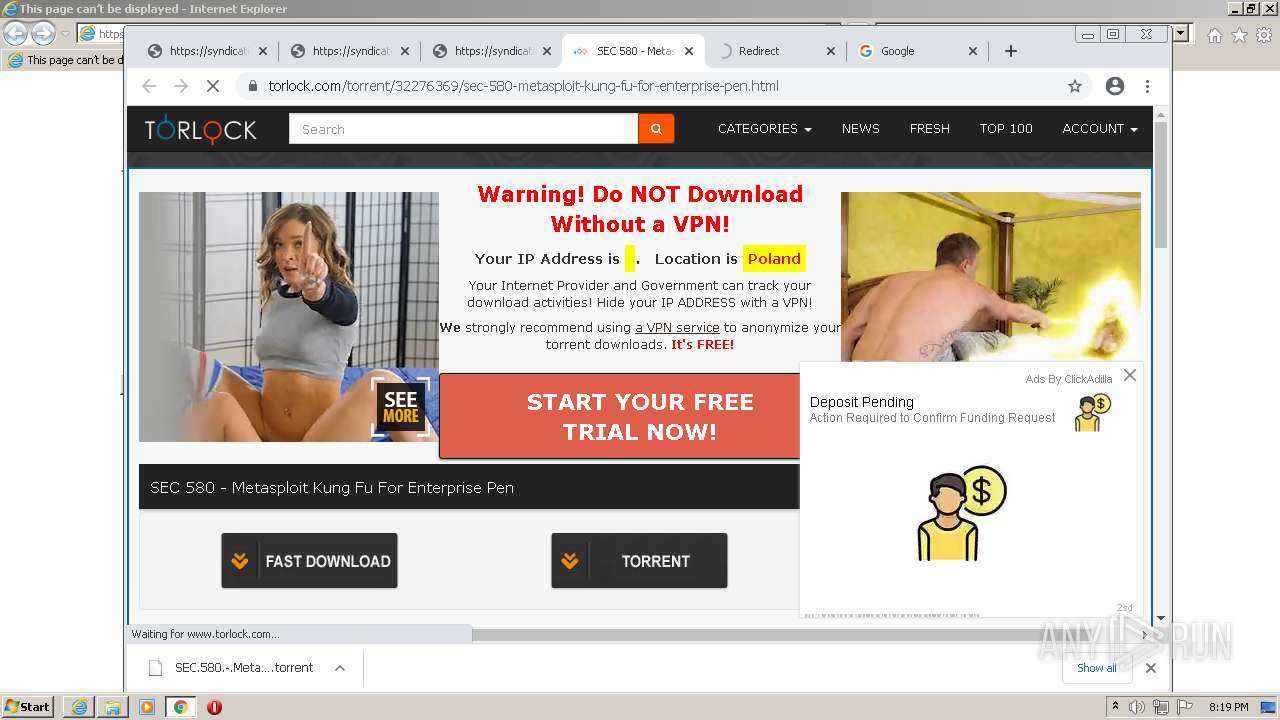
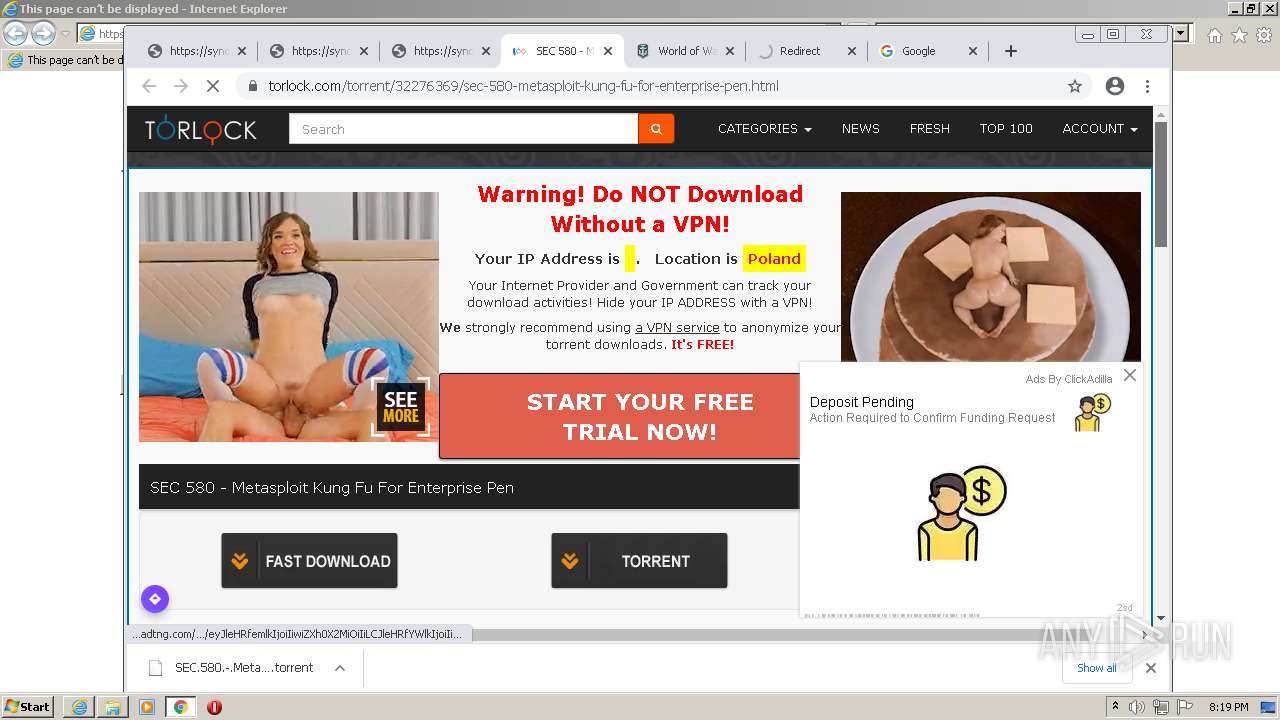
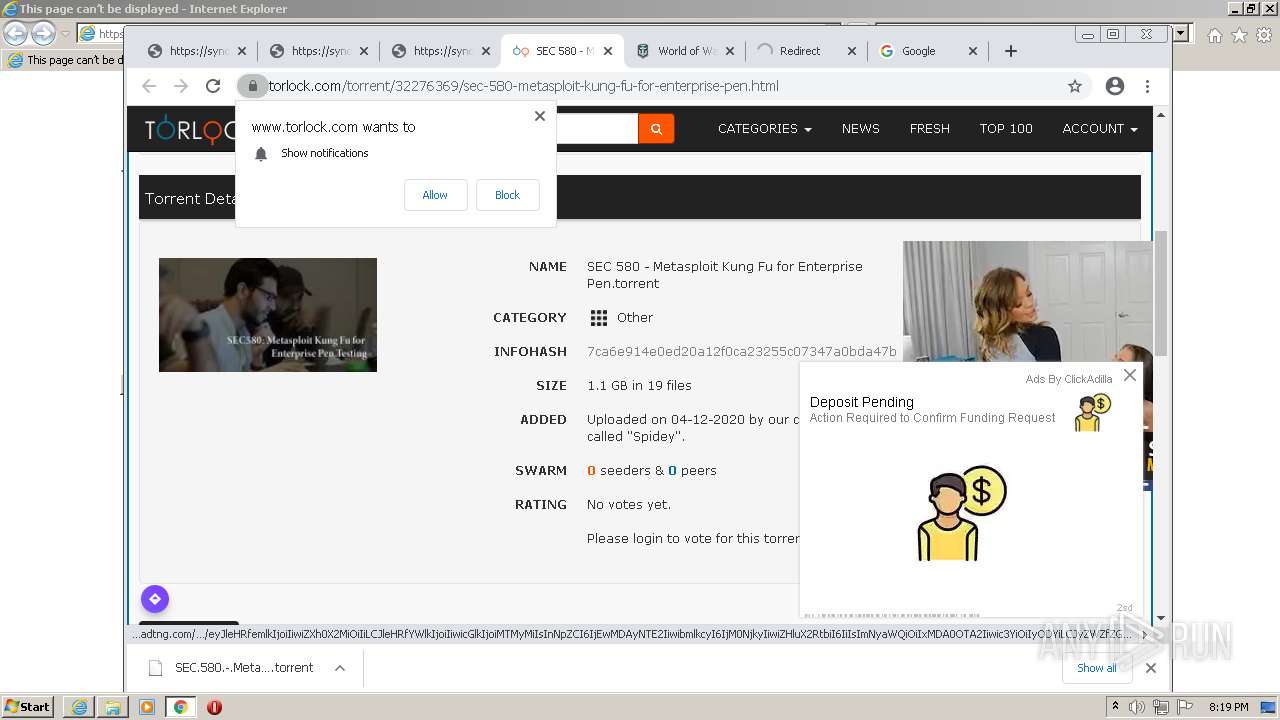
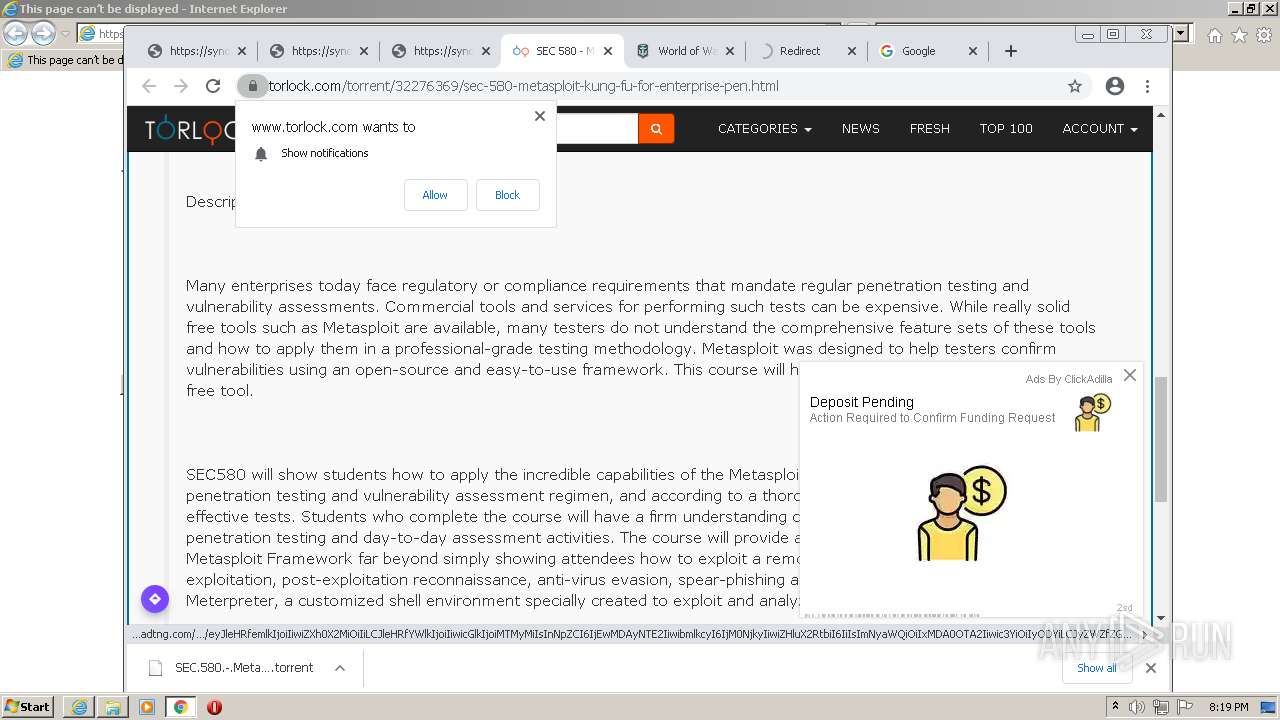
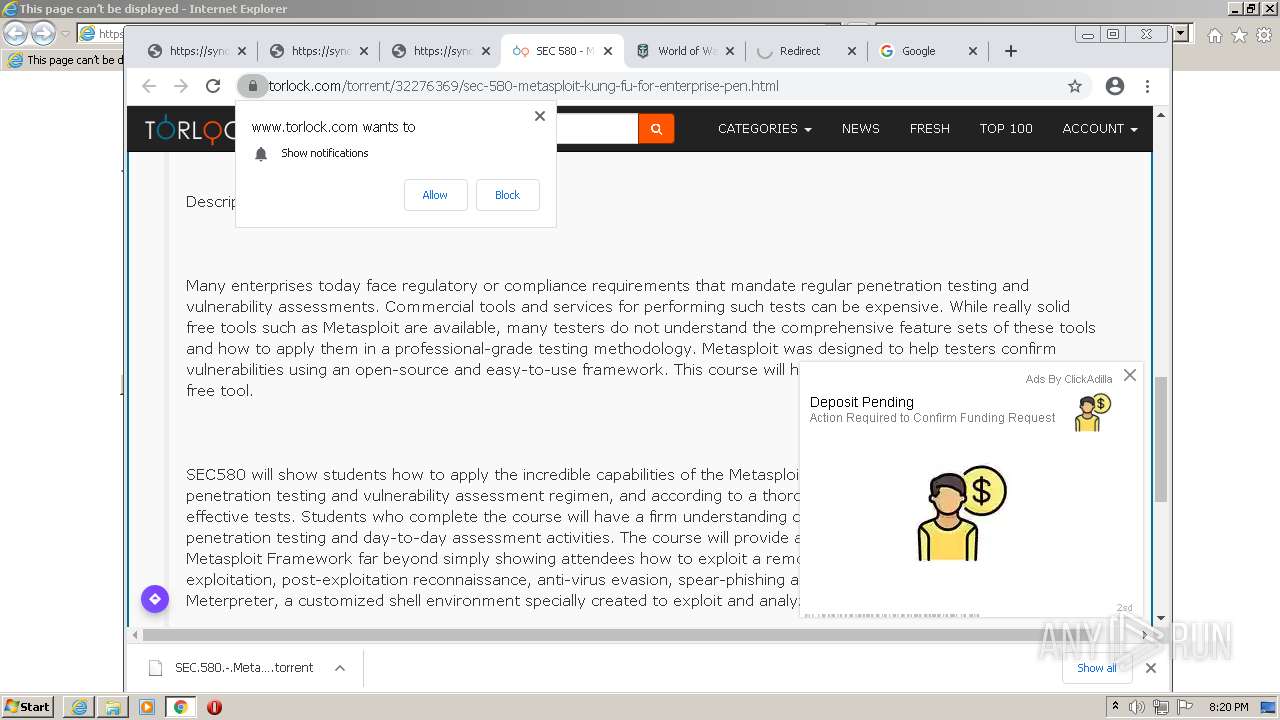
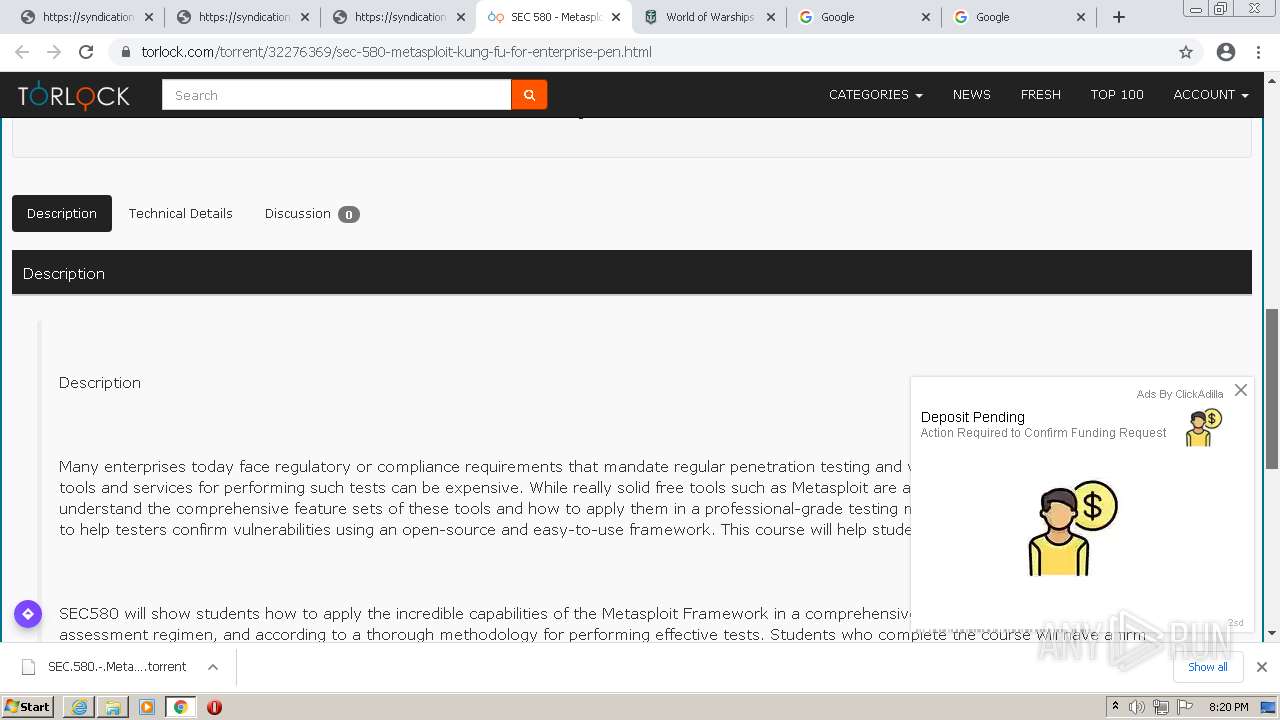
| URL: | https://www.google.com/url?client=internal-element-cse&cx=009429336737432836220:ulylvgpikgc&q=https://www.torlock.com/torrent/32276369/sec-580-metasploit-kung-fu-for-enterprise-pen.html&sa=U&ved=2ahUKEwjZnqnXh7L1AhUojIkEHQ85D4YQFnoECAIQAg&usg=AOvVaw3RVGMokZQlZVXW2_R0ygxH |
| Full analysis: | https://app.any.run/tasks/9790d106-da4f-4e3f-86d7-2ac6e9013450 |
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2022, 20:16:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EFE35F276F12BF36F2F7FA73603AD7D7 |
| SHA1: | E3097AB4842605B7CC67F57FB6780D07B77301C3 |
| SHA256: | 73B0BBEF4DDE093A0CB3B3322A357B492B36769A1C945CC24422A6C7725104BE |
| SSDEEP: | 6:2OLI2LlUIX2aHRXbbXatSrGLuzHet0OB91ecWu8wnN9NMxi5FJSg8xMy:2V2KIfxnXYStzHeVYwnN96w5ro |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 4020)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 572)
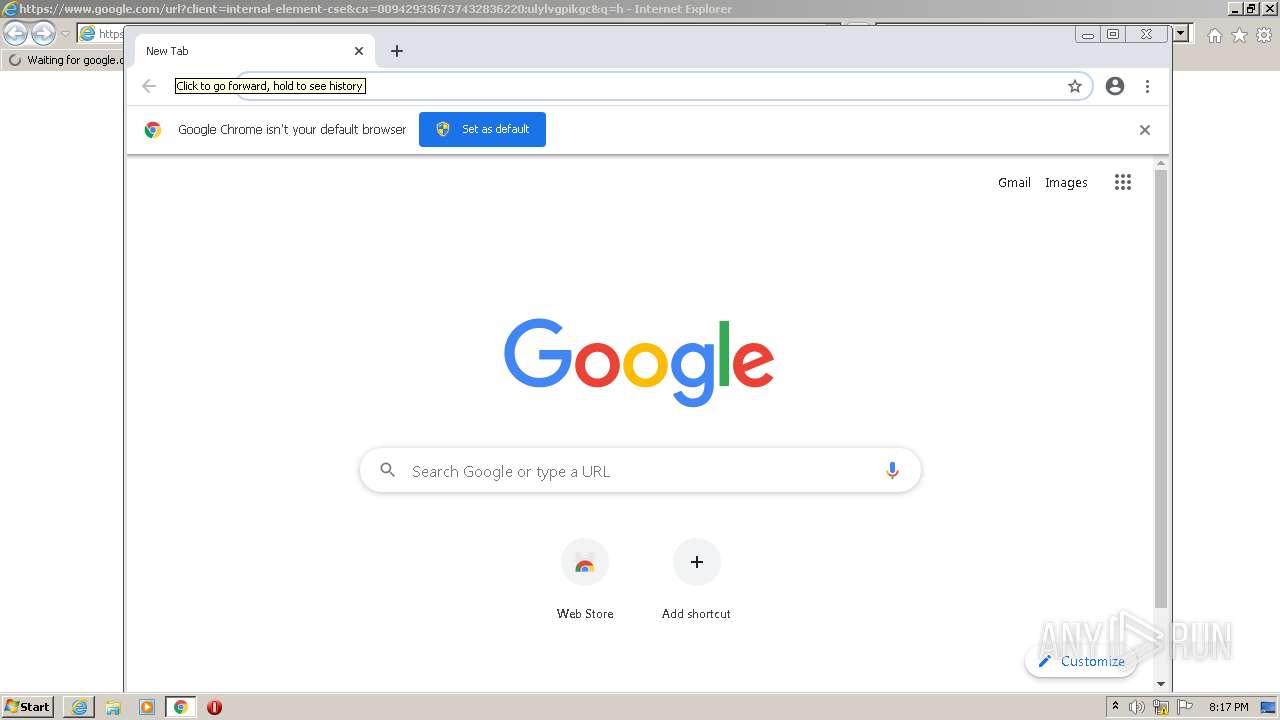
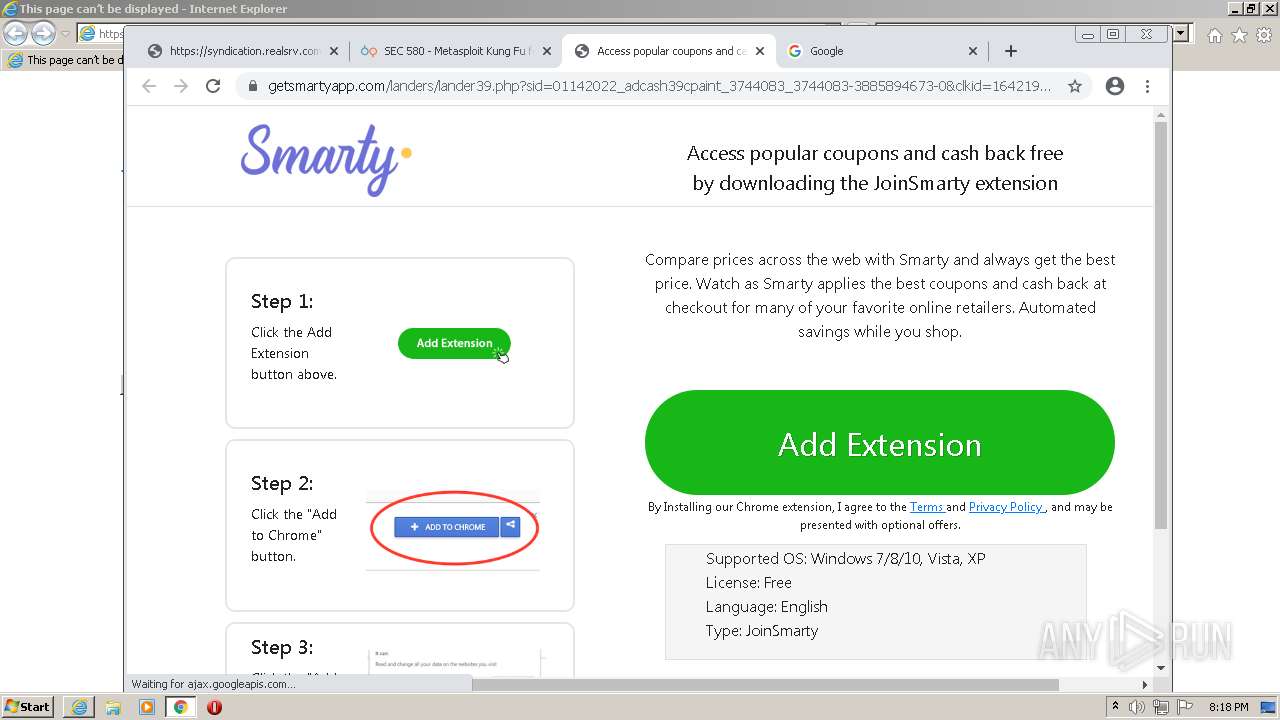
Modifies files in Chrome extension folder
- chrome.exe (PID: 2788)
Drops a file with a compile date too recent
- chrome.exe (PID: 2788)
Executable content was dropped or overwritten
- chrome.exe (PID: 4020)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 4020)
INFO
Checks supported languages
- iexplore.exe (PID: 2256)
- chrome.exe (PID: 3488)
- chrome.exe (PID: 1168)
- iexplore.exe (PID: 572)
- chrome.exe (PID: 2788)
- chrome.exe (PID: 1604)
- chrome.exe (PID: 3792)
- chrome.exe (PID: 2456)
- chrome.exe (PID: 636)
- chrome.exe (PID: 3492)
- chrome.exe (PID: 2752)
- chrome.exe (PID: 3000)
- chrome.exe (PID: 3052)
- chrome.exe (PID: 2732)
- chrome.exe (PID: 2104)
- chrome.exe (PID: 1404)
- chrome.exe (PID: 1704)
- chrome.exe (PID: 4004)
- chrome.exe (PID: 2172)
- chrome.exe (PID: 2312)
- chrome.exe (PID: 3580)
- chrome.exe (PID: 1696)
- chrome.exe (PID: 1384)
- chrome.exe (PID: 3088)
- chrome.exe (PID: 3584)
- chrome.exe (PID: 964)
- chrome.exe (PID: 4004)
- chrome.exe (PID: 2208)
- chrome.exe (PID: 2172)
- chrome.exe (PID: 2552)
- chrome.exe (PID: 1948)
- chrome.exe (PID: 3780)
- chrome.exe (PID: 1696)
- chrome.exe (PID: 2964)
- chrome.exe (PID: 392)
- chrome.exe (PID: 3080)
- chrome.exe (PID: 2900)
- chrome.exe (PID: 1200)
- chrome.exe (PID: 3876)
- chrome.exe (PID: 852)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 4036)
- chrome.exe (PID: 2152)
- chrome.exe (PID: 2716)
- chrome.exe (PID: 2552)
- chrome.exe (PID: 2464)
- chrome.exe (PID: 1520)
- chrome.exe (PID: 2992)
- chrome.exe (PID: 3840)
- chrome.exe (PID: 2436)
- chrome.exe (PID: 1524)
- chrome.exe (PID: 1124)
- chrome.exe (PID: 1544)
- chrome.exe (PID: 576)
- chrome.exe (PID: 3568)
- chrome.exe (PID: 3132)
- chrome.exe (PID: 1760)
- chrome.exe (PID: 3708)
- chrome.exe (PID: 3764)
- chrome.exe (PID: 356)
- chrome.exe (PID: 2716)
- chrome.exe (PID: 2536)
- chrome.exe (PID: 3064)
- chrome.exe (PID: 2188)
- chrome.exe (PID: 3340)
- chrome.exe (PID: 1604)
- chrome.exe (PID: 3392)
- chrome.exe (PID: 508)
- chrome.exe (PID: 2348)
- chrome.exe (PID: 4020)
- chrome.exe (PID: 3624)
- chrome.exe (PID: 4020)
- chrome.exe (PID: 4060)
- chrome.exe (PID: 824)
- chrome.exe (PID: 3056)
- chrome.exe (PID: 1176)
- chrome.exe (PID: 2536)
- chrome.exe (PID: 1388)
- chrome.exe (PID: 2040)
- chrome.exe (PID: 3088)
- chrome.exe (PID: 3428)
- chrome.exe (PID: 3504)
- chrome.exe (PID: 1240)
Changes internet zones settings
- iexplore.exe (PID: 2256)
Reads the computer name
- chrome.exe (PID: 2788)
- iexplore.exe (PID: 2256)
- iexplore.exe (PID: 572)
- chrome.exe (PID: 1168)
- chrome.exe (PID: 1604)
- chrome.exe (PID: 2732)
- chrome.exe (PID: 2552)
- chrome.exe (PID: 1948)
- chrome.exe (PID: 2152)
- chrome.exe (PID: 2464)
- chrome.exe (PID: 576)
- chrome.exe (PID: 3132)
- chrome.exe (PID: 1760)
Reads the hosts file
- chrome.exe (PID: 2788)
- chrome.exe (PID: 1168)
Reads settings of System Certificates
- iexplore.exe (PID: 572)
- chrome.exe (PID: 1168)
- iexplore.exe (PID: 2256)
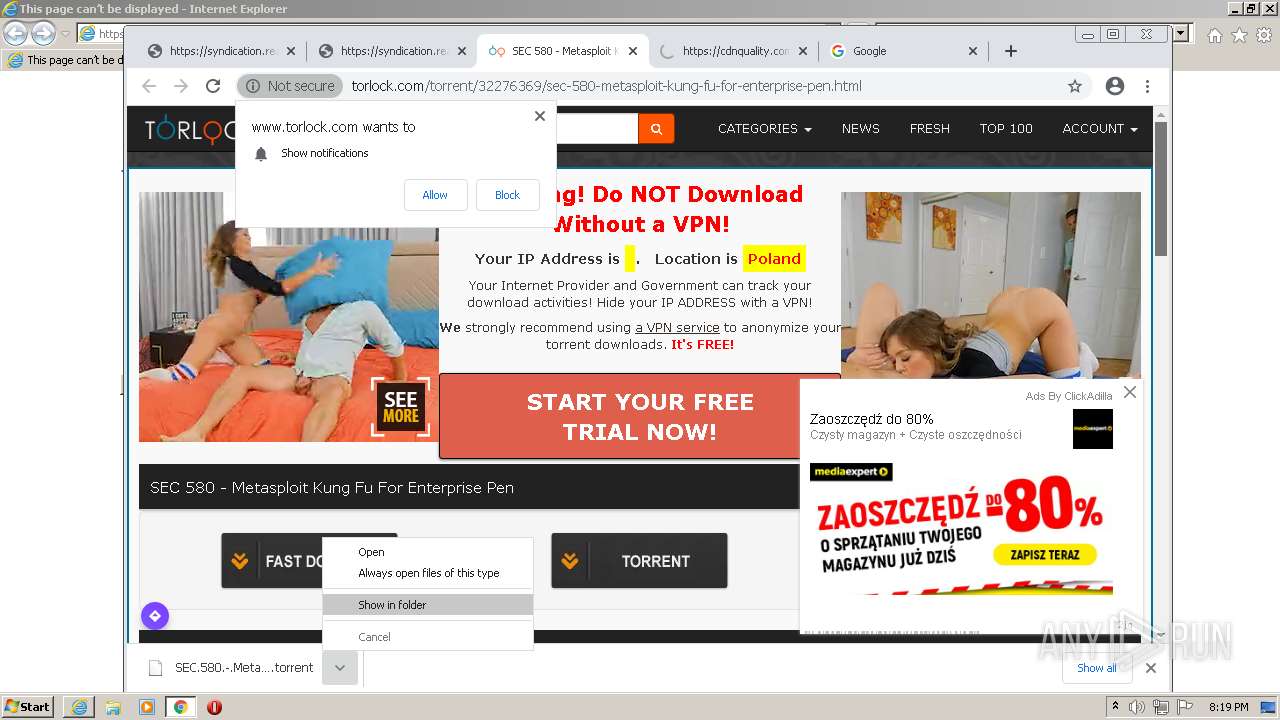
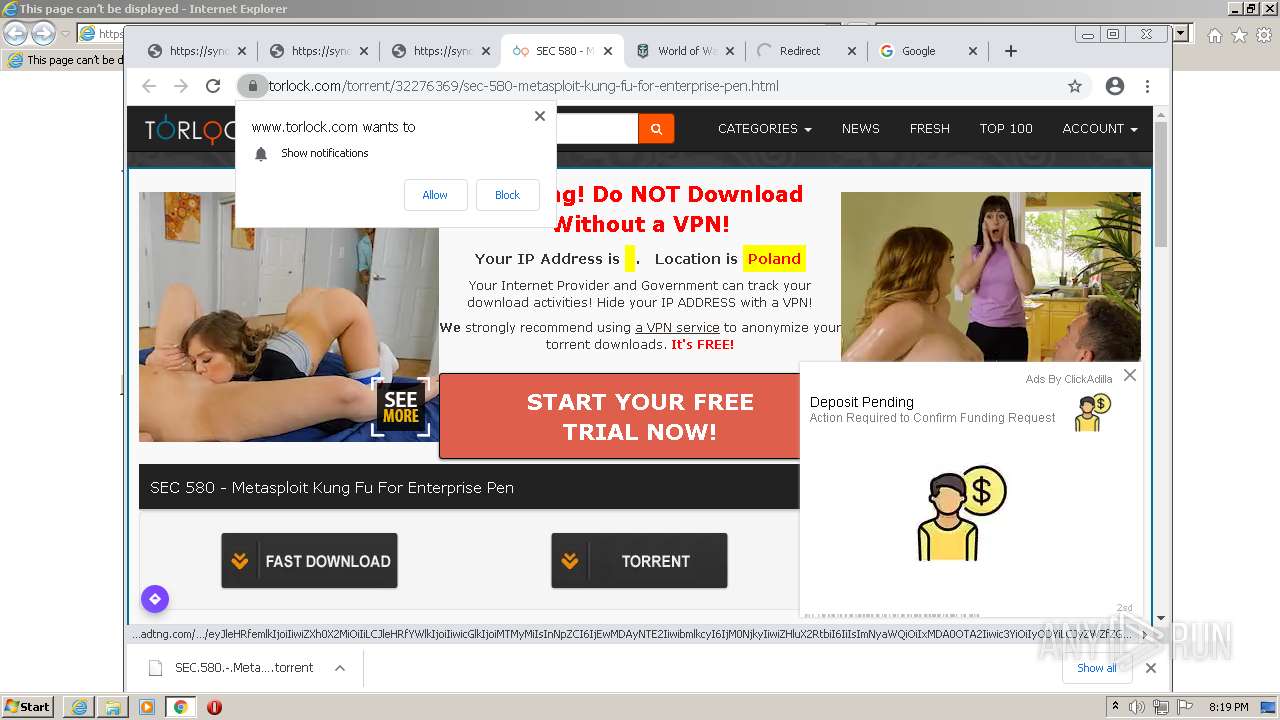
Manual execution by user
- chrome.exe (PID: 2788)
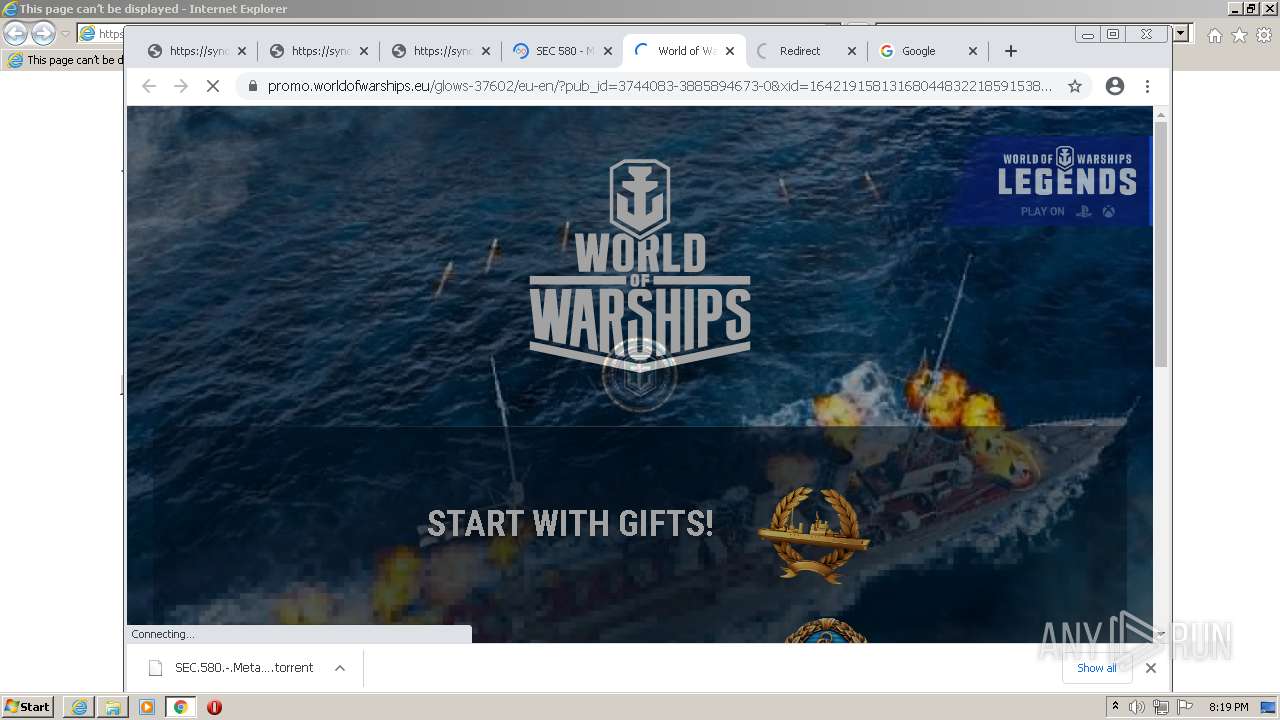
Application launched itself
- iexplore.exe (PID: 2256)
- chrome.exe (PID: 2788)
Checks Windows Trust Settings
- iexplore.exe (PID: 572)
- iexplore.exe (PID: 2256)
- chrome.exe (PID: 2788)
Reads internet explorer settings
- iexplore.exe (PID: 572)
Reads the date of Windows installation
- chrome.exe (PID: 2152)
Creates files in the user directory
- iexplore.exe (PID: 2256)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2256)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2256)
Changes settings of System certificates
- iexplore.exe (PID: 2256)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
123
Monitored processes
83
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,6287709278811499560,17664091498999666519,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=58 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4196 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,6287709278811499560,17664091498999666519,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2288 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,6287709278811499560,17664091498999666519,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=65 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3776 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2256 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,6287709278811499560,17664091498999666519,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=5388 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,6287709278811499560,17664091498999666519,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2868 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,6287709278811499560,17664091498999666519,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=68 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4284 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,6287709278811499560,17664091498999666519,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2296 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1044,6287709278811499560,17664091498999666519,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4536 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,6287709278811499560,17664091498999666519,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=52 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2800 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
32 374
Read events
32 023
Write events
340
Delete events
11
Modification events
| (PID) Process: | (2256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30935427 | |||
| (PID) Process: | (2256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30935427 | |||
| (PID) Process: | (2256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
366
Text files
286
Unknown types
33
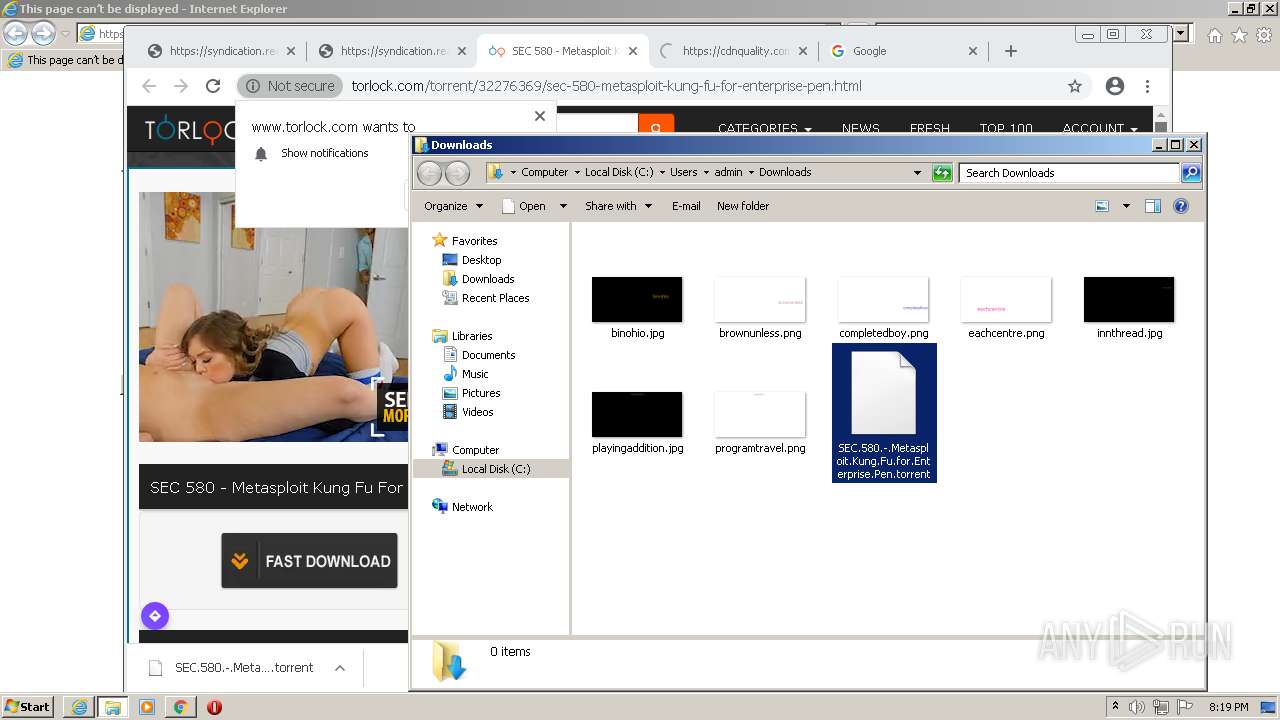
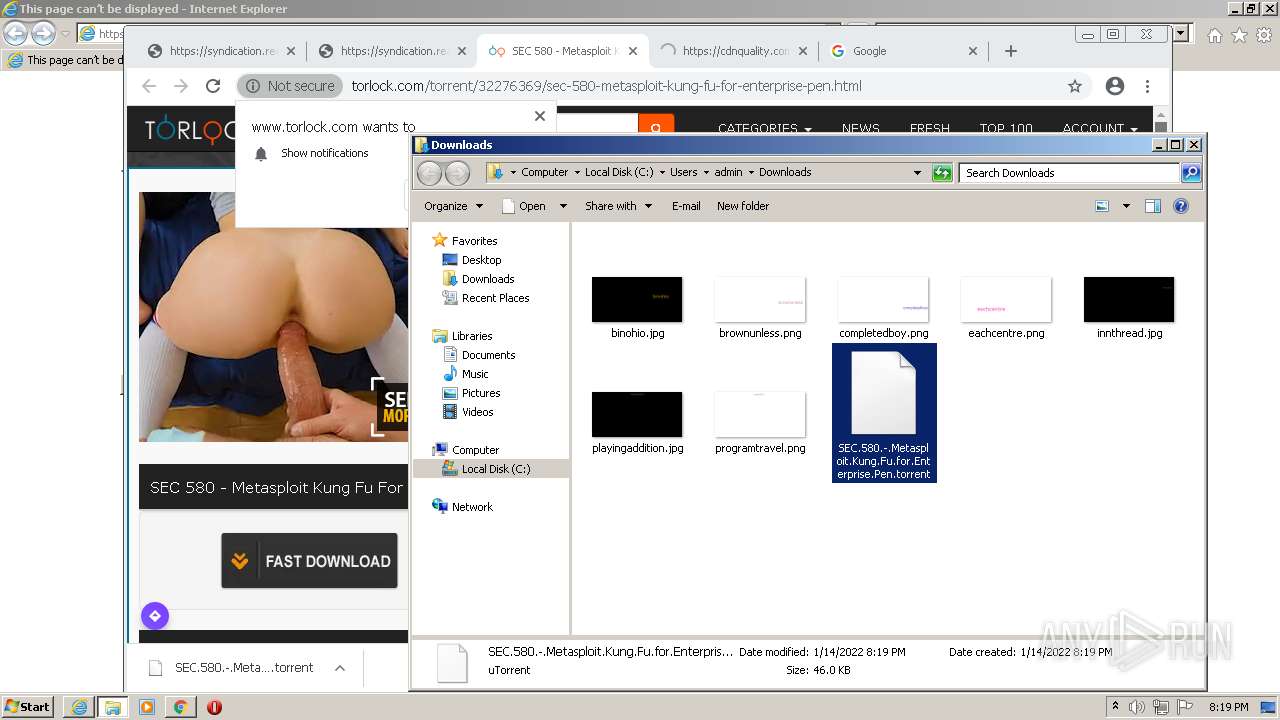
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61E1DA3F-AE4.pma | — | |
MD5:— | SHA256:— | |||
| 572 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a78fe76b-37d5-473c-94fa-5804930216f3.tmp | text | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8925c758-079d-4930-a50a-0cfeddb5cedd.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 572 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF140463.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF140463.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
318
DNS requests
168
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1168 | chrome.exe | GET | — | 67.26.137.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?1055dbc4c10cbe10 | US | — | — | whitelisted |
1168 | chrome.exe | GET | — | 67.26.137.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?9cec39cc0760a1b3 | US | — | — | whitelisted |
1168 | chrome.exe | GET | 302 | 174.137.133.16:80 | http://click.pclk.name/thumbnail?i=joiBKgurjy4_0&imgt=icon | US | — | — | suspicious |
924 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | — | — | whitelisted |
2256 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
2256 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
1168 | chrome.exe | GET | 204 | 142.250.184.227:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
572 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 5.67 Kb | whitelisted |
2256 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
572 | iexplore.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
572 | iexplore.exe | 67.26.137.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
572 | iexplore.exe | 216.58.212.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1168 | chrome.exe | 142.250.186.45:443 | accounts.google.com | Google Inc. | US | suspicious |
1168 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
1168 | chrome.exe | 142.250.181.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1168 | chrome.exe | 142.250.185.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1168 | chrome.exe | 104.21.75.107:443 | l.tcdn.fun | Cloudflare Inc | US | malicious |
1168 | chrome.exe | 142.250.185.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
1168 | chrome.exe | 142.250.184.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
ocsp.digicert.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1168 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
1168 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |