| download: | samanta.exe |
| Full analysis: | https://app.any.run/tasks/e7f62848-08ee-43f7-a585-772476134e56 |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
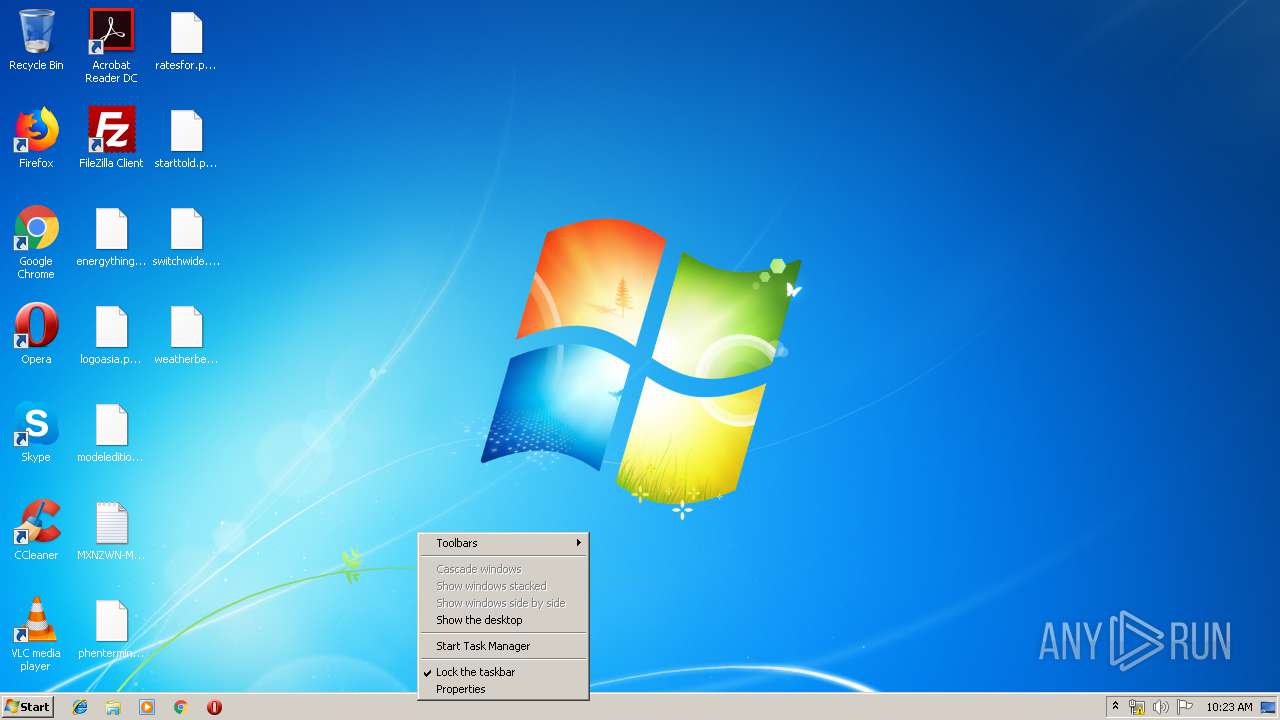
| Analysis date: | March 21, 2019, 10:22:38 |
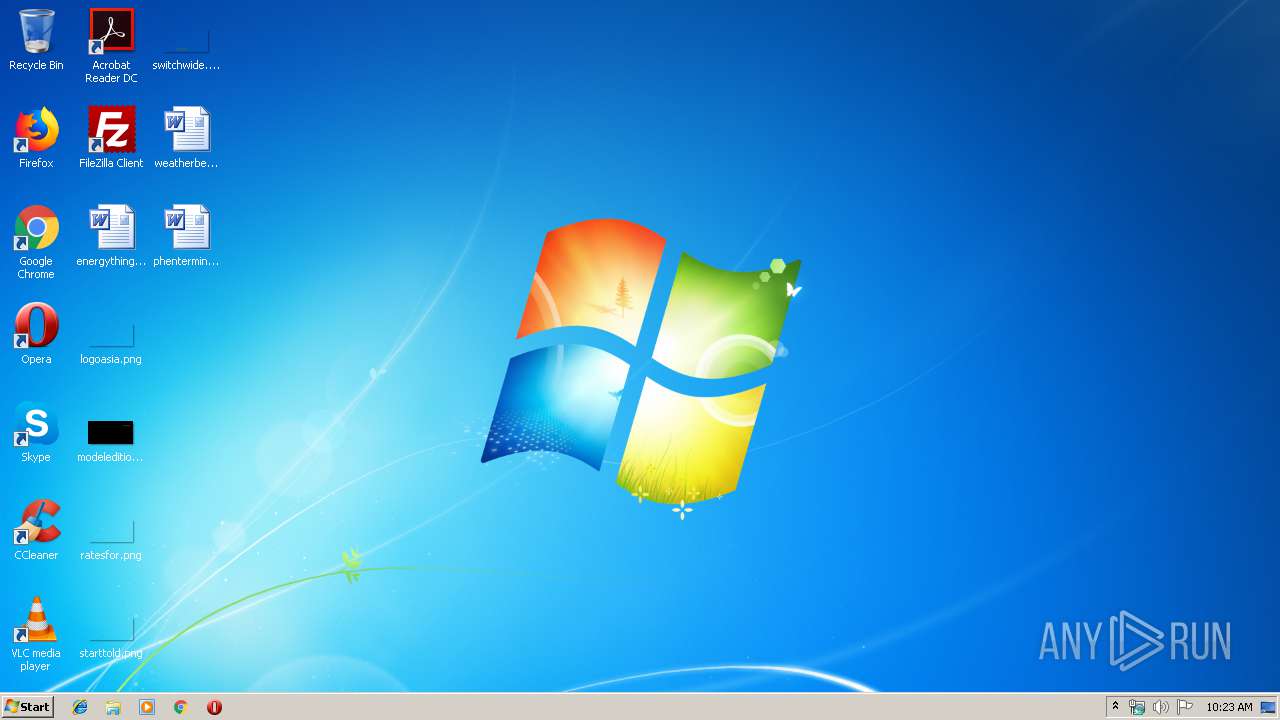
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 27FA5F1EF590EE5E503C3D15F210DAB7 |
| SHA1: | 6069666610D09085DC7926CDE3D242427E67B167 |
| SHA256: | 73A994E9FA2804AFCEAF1286E4ABA8522EB3C555B85766B03F03106118165736 |
| SSDEEP: | 12288:abPmDX5k1ousNv+MDZZ+tilL/pfv2R8oIGU2bzvO3y2av9x:XDXNNv+MZrL/pfveo23229x |
MALICIOUS
Actions looks like stealing of personal data
- samanta.exe (PID: 2376)
Writes file to Word startup folder
- samanta.exe (PID: 2376)
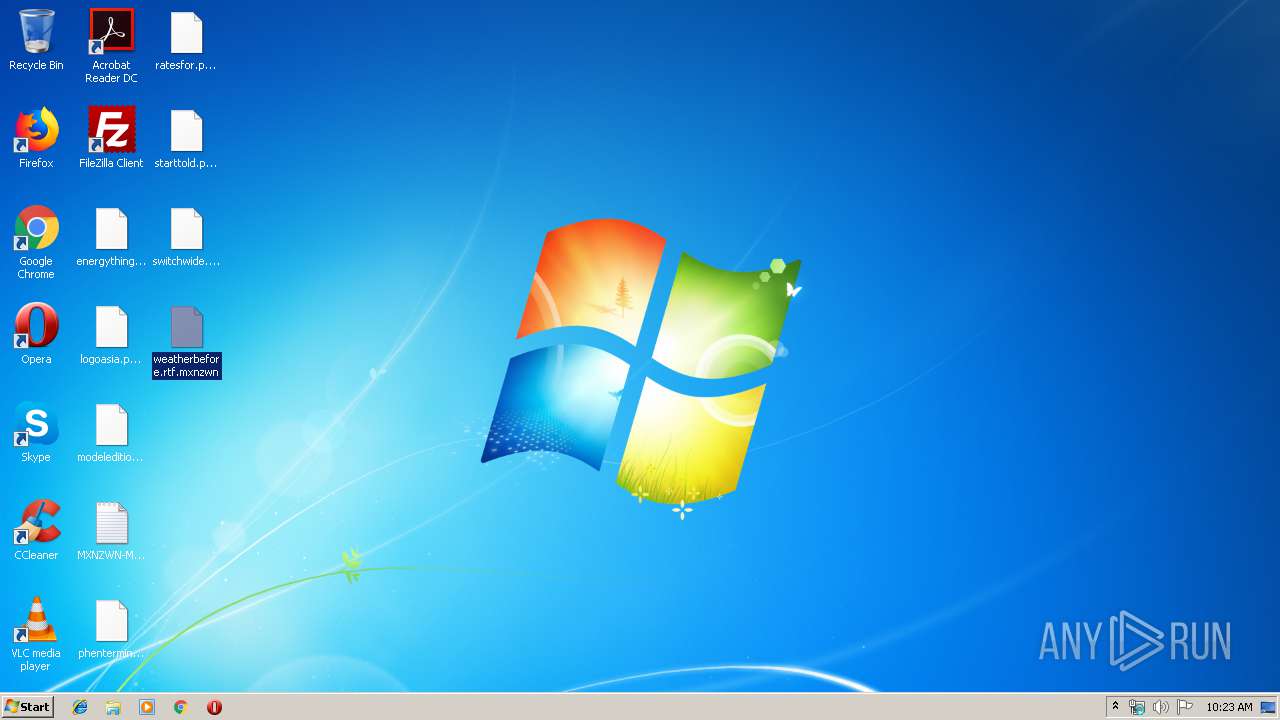
Renames files like Ransomware
- samanta.exe (PID: 2376)
Dropped file may contain instructions of ransomware
- samanta.exe (PID: 2376)
Connects to CnC server
- samanta.exe (PID: 2376)
Changes settings of System certificates
- samanta.exe (PID: 2376)
Deletes shadow copies
- samanta.exe (PID: 2376)
GANDCRAB detected
- samanta.exe (PID: 2376)
SUSPICIOUS
Creates files in the program directory
- samanta.exe (PID: 2376)
Adds / modifies Windows certificates
- samanta.exe (PID: 2376)
Reads the cookies of Mozilla Firefox
- samanta.exe (PID: 2376)
Creates files in the user directory
- samanta.exe (PID: 2376)
INFO
Dropped object may contain Bitcoin addresses
- samanta.exe (PID: 2376)
Dropped object may contain TOR URL's
- samanta.exe (PID: 2376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (53) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (34) |
| .exe | | | Win32 Executable (generic) (5.5) |
| .exe | | | Clipper DOS Executable (2.4) |
| .exe | | | Generic Win/DOS Executable (2.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:12 20:22:40+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 290304 |
| InitializedDataSize: | 437760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc030 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.5.91.671 |
| ProductVersionNumber: | 4.5.91.671 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| LegalTrademarks: | Copyright ©. All rights reserved. |
| CompanyName: | www.BitComet.com |
| FileVersion: | 4.5.91.671 |
| LegalCopyright: | Copyright ©. All rights reserved. |
| FileDescription: | Students Trend Deeply Survive Bitnet |
| ProductName: | FactualEloquence |
| ProductVersion: | 4.5.91.671 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Mar-2019 19:22:40 |
| Detected languages: |
|
| Debug artifacts: |
|
| LegalTrademarks: | Copyright ©. All rights reserved. |
| CompanyName: | www.BitComet.com |
| FileVersion: | 4.5.91.671 |
| LegalCopyright: | Copyright ©. All rights reserved. |
| FileDescription: | Students Trend Deeply Survive Bitnet |
| ProductName: | FactualEloquence |
| ProductVersion: | 4.5.91.671 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 12-Mar-2019 19:22:40 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00046DDF | 0x00046E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.39263 |
.rdata | 0x00048000 | 0x00034BA2 | 0x00034C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.38987 |
.data | 0x0007D000 | 0x0000AE08 | 0x00007400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.89994 |
.rsrc | 0x00088000 | 0x0002EC88 | 0x0002EE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.33803 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.94555 | 658 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.12704 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.48882 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.46275 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.96085 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.2929 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
101 | 2.94141 | 90 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
389 | 4.68215 | 734 | Latin 1 / Western European | English - United States | RT_RCDATA |
702 | 4.36769 | 91 | Latin 1 / Western European | English - United States | UNKNOWN |
2174 | 4.64419 | 163 | Latin 1 / Western European | English - United States | UNKNOWN |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
MSIMG32.dll |
MSVFW32.dll |
RASAPI32.dll |
RPCRT4.dll |
SHELL32.dll |
SHLWAPI.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
Launch | 1 | 0x0000B100 |
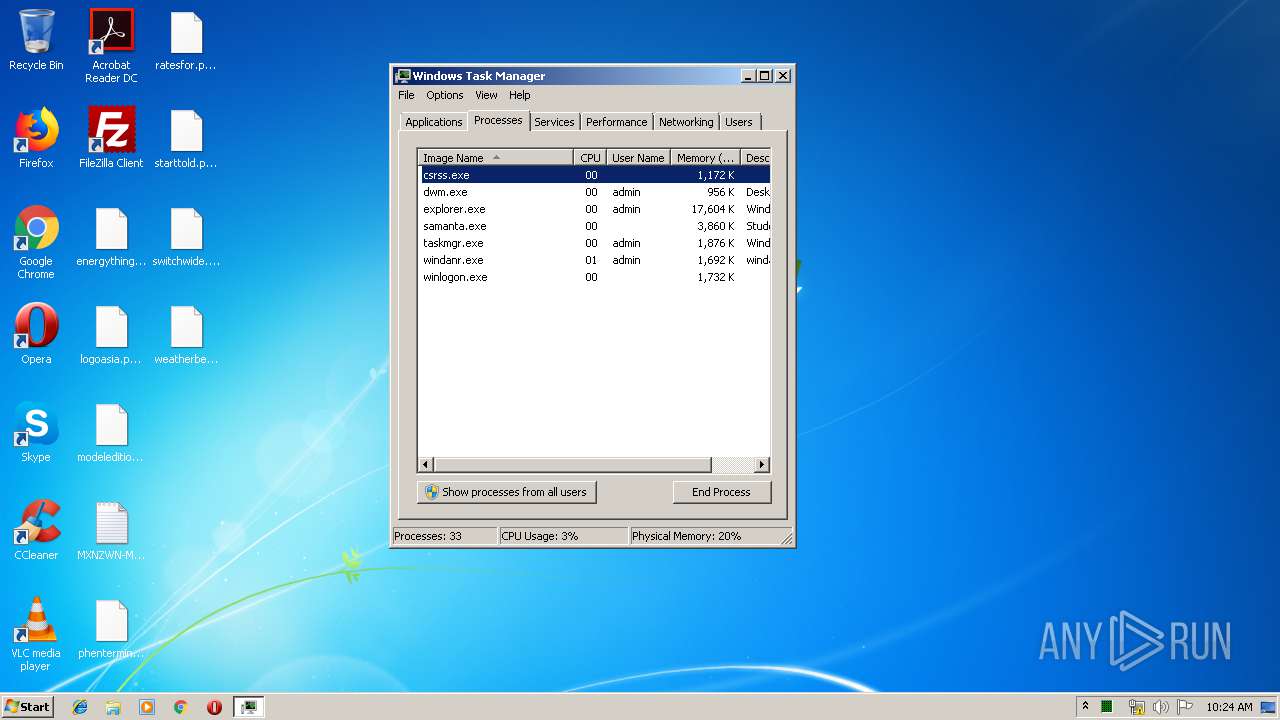
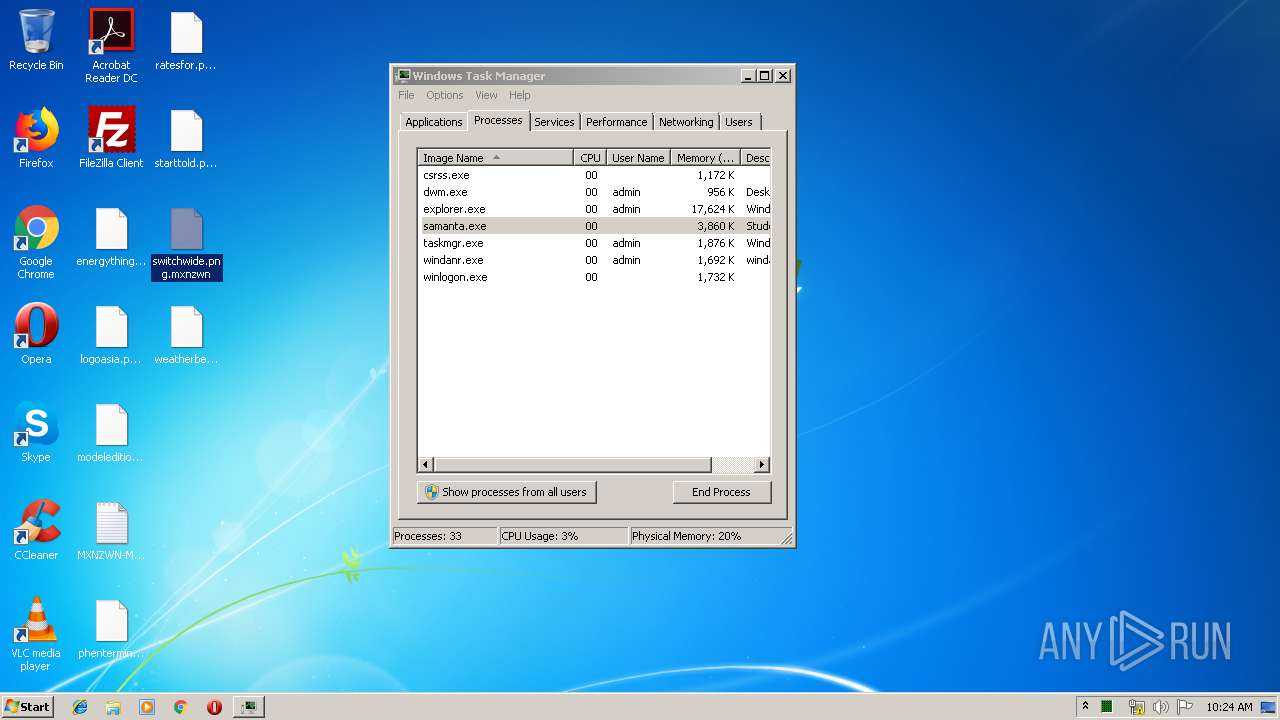
Total processes
37
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 952 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | samanta.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2376 | "C:\Users\admin\AppData\Local\Temp\samanta.exe" | C:\Users\admin\AppData\Local\Temp\samanta.exe | explorer.exe | ||||||||||||
User: admin Company: www.BitComet.com Integrity Level: MEDIUM Description: Students Trend Deeply Survive Bitnet Exit code: 0 Version: 4.5.91.671 Modules
| |||||||||||||||
| 3324 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
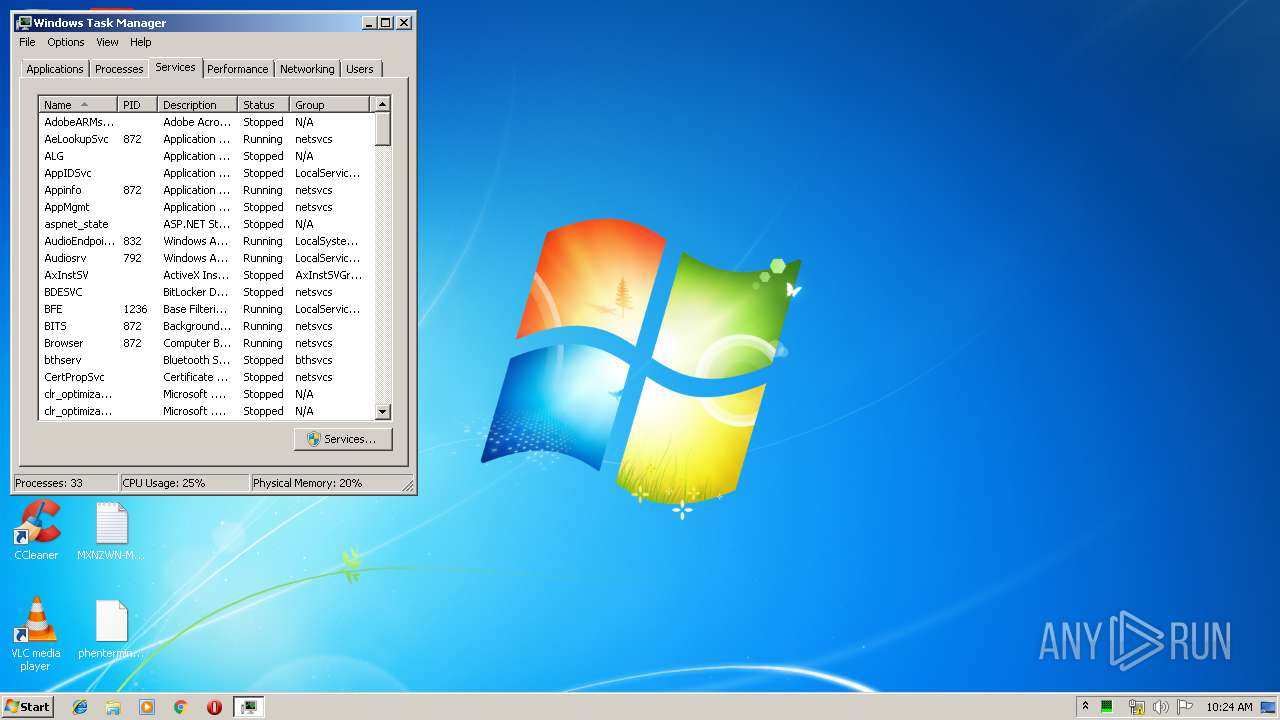
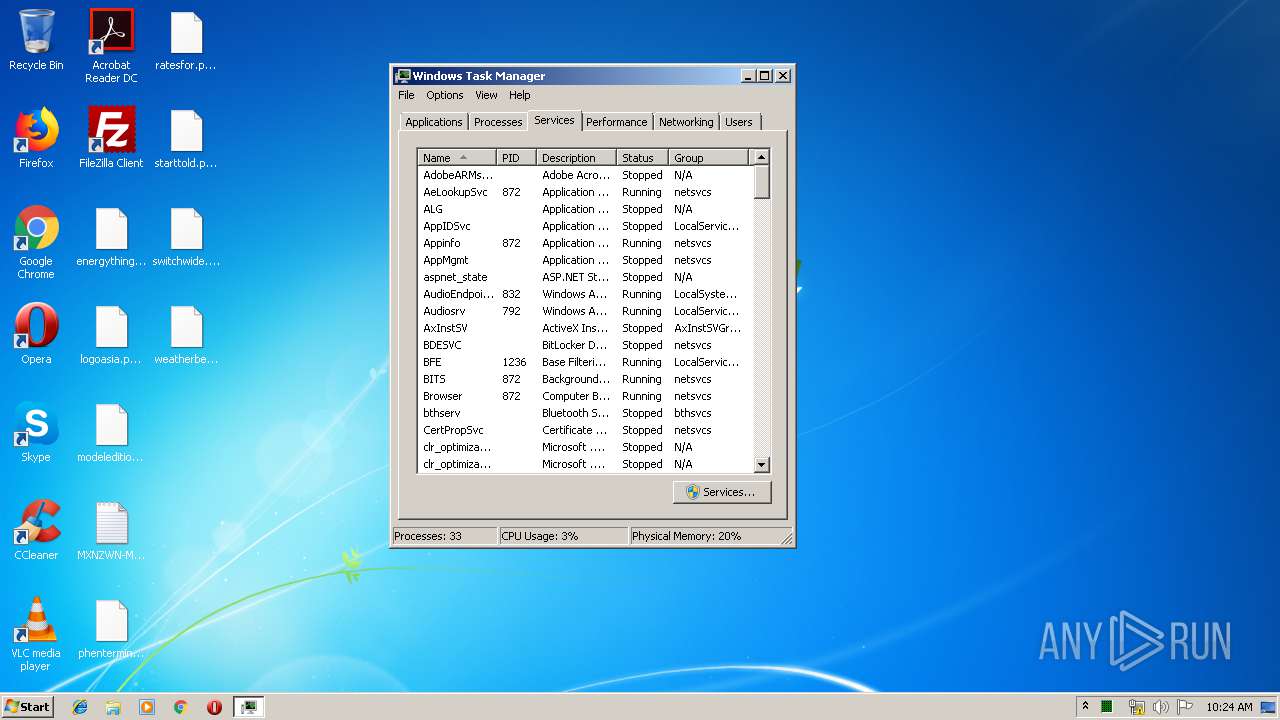
| 4008 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
151
Read events
118
Write events
33
Delete events
0
Modification events
| (PID) Process: | (2376) samanta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2376) samanta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2376) samanta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\samanta_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2376) samanta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\samanta_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2376) samanta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\samanta_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2376) samanta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\samanta_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2376) samanta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\samanta_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2376) samanta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\samanta_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2376) samanta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\samanta_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2376) samanta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\samanta_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
422
Text files
318
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2376 | samanta.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
| 2376 | samanta.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 2376 | samanta.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.mxnzwn | — | |
MD5:— | SHA256:— | |||
| 2376 | samanta.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{05ed3515-06b3-48f6-8cf2-bf24b1bf0727}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2376 | samanta.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{16d74681-6bc3-4c44-97f0-8b8dfefe2355}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2376 | samanta.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{38e8535f-27d0-4352-aa3a-ce4178930102}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2376 | samanta.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{3cc0f82b-873a-4e59-b89f-689fbdf88af9}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2376 | samanta.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{5c4beaff-a038-4df7-9b35-072a18f8e3d6}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2376 | samanta.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\MXNZWN-MANUAL.txt | text | |
MD5:— | SHA256:— | |||
| 2376 | samanta.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{6af49b38-a69b-4427-8e0d-1d7f53ed58e8}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2376 | samanta.exe | GET | 301 | 107.173.49.208:80 | http://www.kakaocorp.link/ | US | html | 162 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2376 | samanta.exe | 107.173.49.208:80 | www.kakaocorp.link | ColoCrossing | US | malicious |
2376 | samanta.exe | 107.173.49.208:443 | www.kakaocorp.link | ColoCrossing | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kakaocorp.link |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2376 | samanta.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklisted GandCrab Ransomware C2 Server |
2376 | samanta.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklisted GandCrab Ransomware C2 Server |
2376 | samanta.exe | A Network Trojan was detected | MALWARE [PTsecurity] GandCrab v.5 SSL Connection |
2 ETPRO signatures available at the full report