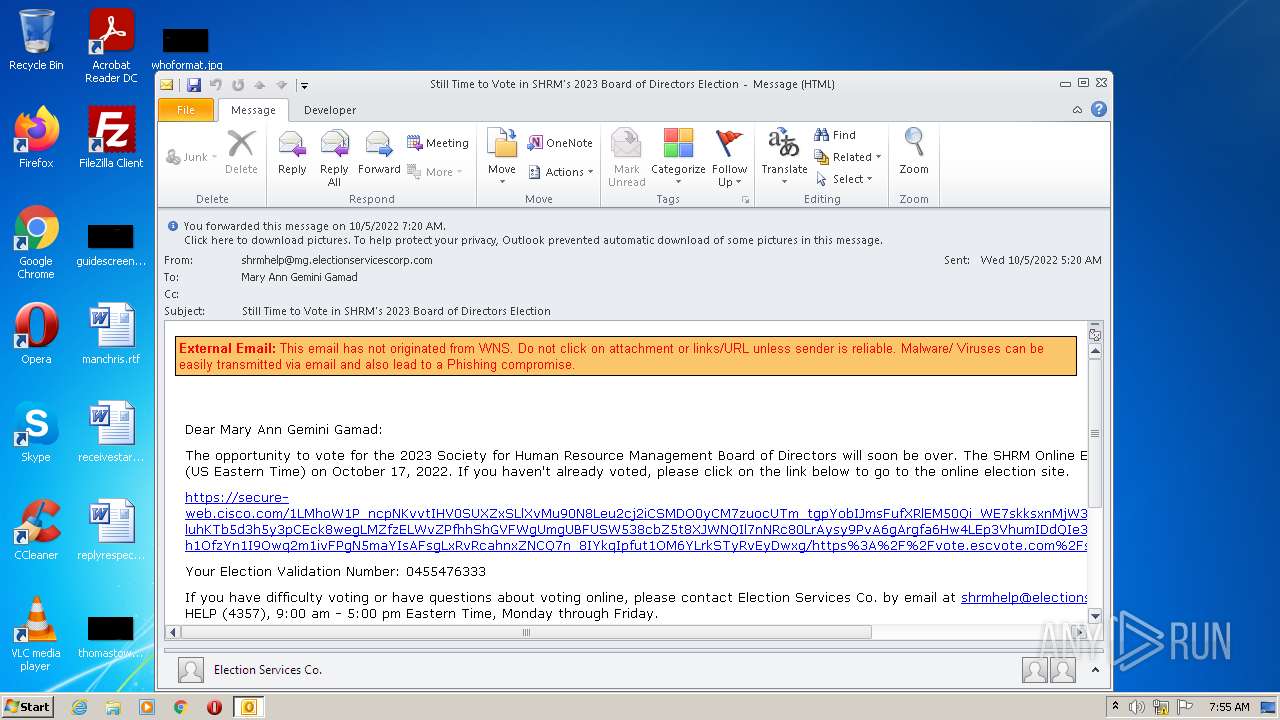
| File name: | Still Time to Vote in SHRM's 2023 Board of Directors Election.msg |
| Full analysis: | https://app.any.run/tasks/a969359b-5f80-4d7c-9d60-ad14333aa6d3 |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2022, 06:55:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 014A849233CB8E1D0037E04FE3F9BBD9 |
| SHA1: | D0D04FE78CB4299726B44FF7B141CB0963ACC84D |
| SHA256: | 739E99416EF7CC31BCF33B737FAFC5AC312936404A55317C88BC4C3F4E06FDE9 |
| SSDEEP: | 768:dxo8k3+QsKOQkmMSdss4G4IhSna6fYOqQLJ2GsKJsK4UunFn6n4L0uWtWHYfboZ6:Lo8e+QBMS6G4IgJLxjunFn6n4L07 |
MALICIOUS
Saves itself using an automatic execution at the hidden registry location
- OUTLOOK.EXE (PID: 3052)
SUSPICIOUS
No suspicious indicators.INFO
Reads the machine GUID from the registry
- OUTLOOK.EXE (PID: 3052)
Process checks LSA protection
- OUTLOOK.EXE (PID: 3052)
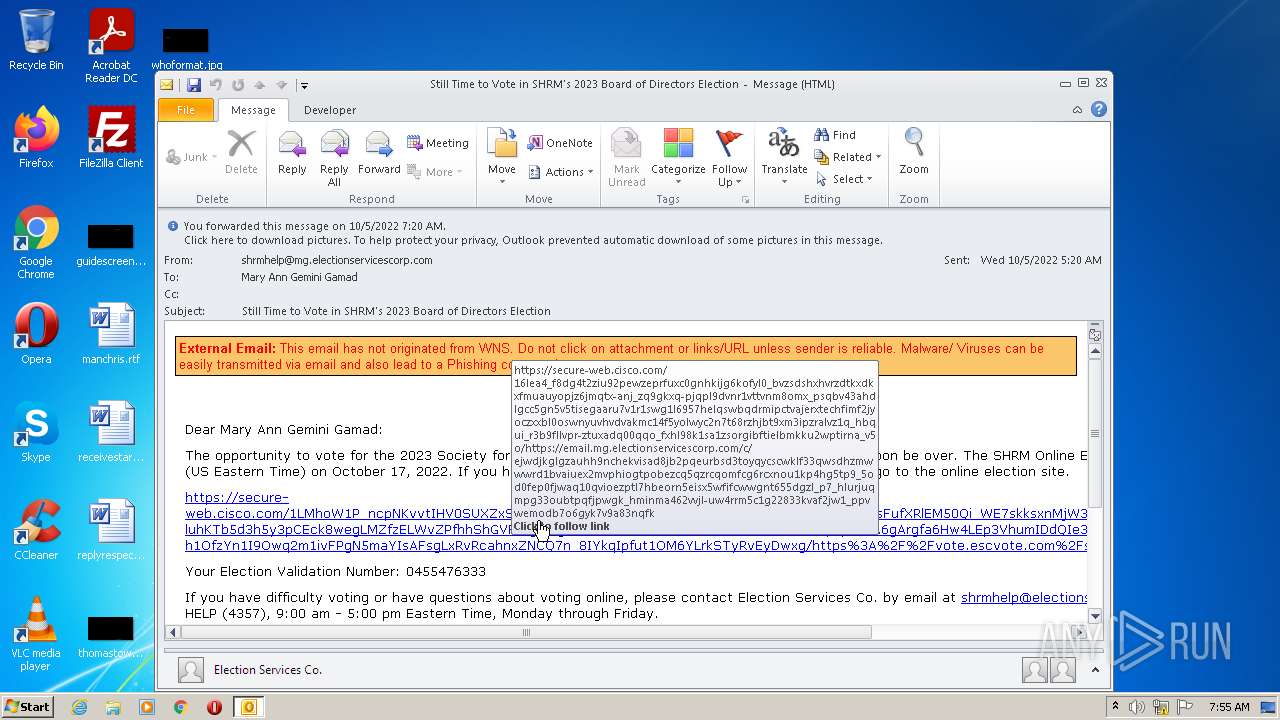
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3052)
Process checks computer location settings
- OUTLOOK.EXE (PID: 3052)
Application launched itself
- iexplore.exe (PID: 3188)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3052)
Searches for installed software
- OUTLOOK.EXE (PID: 3052)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (45.3) |
|---|---|---|
| .oft | | | Outlook Form Template (26.5) |
Total processes
42
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1712 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3188 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3052 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Still Time to Vote in SHRM's 2023 Board of Directors Election.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
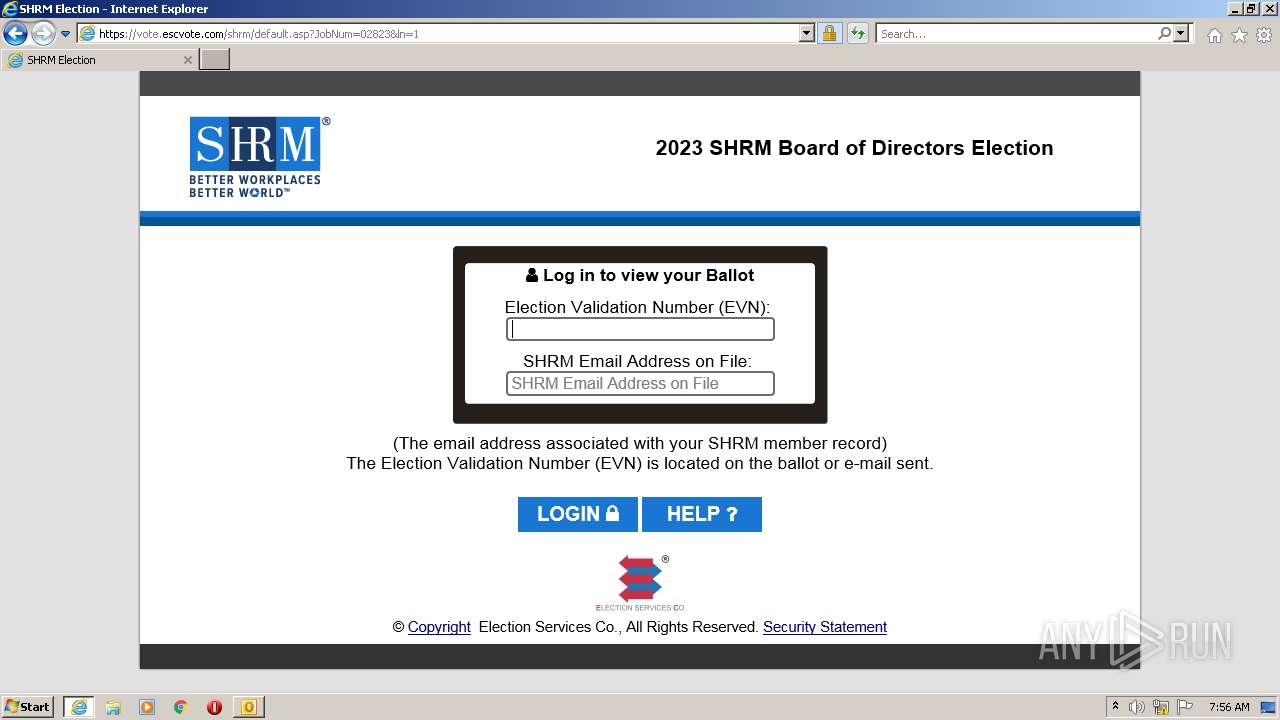
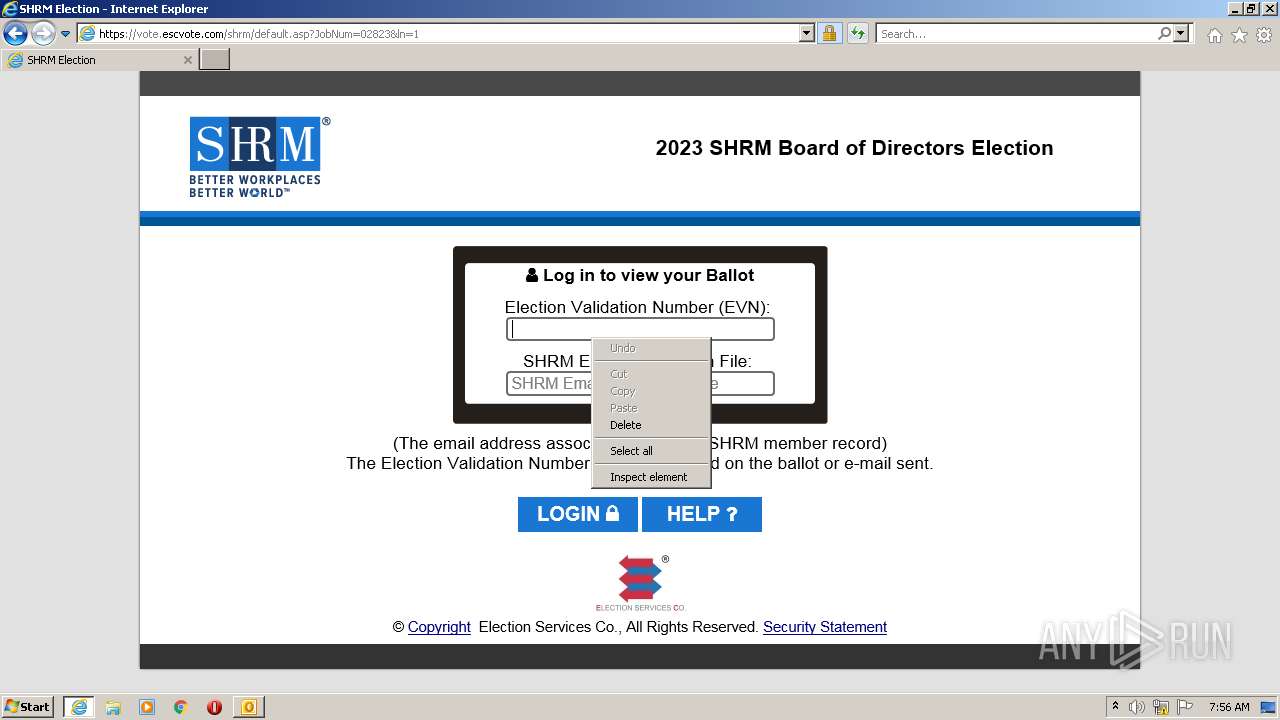
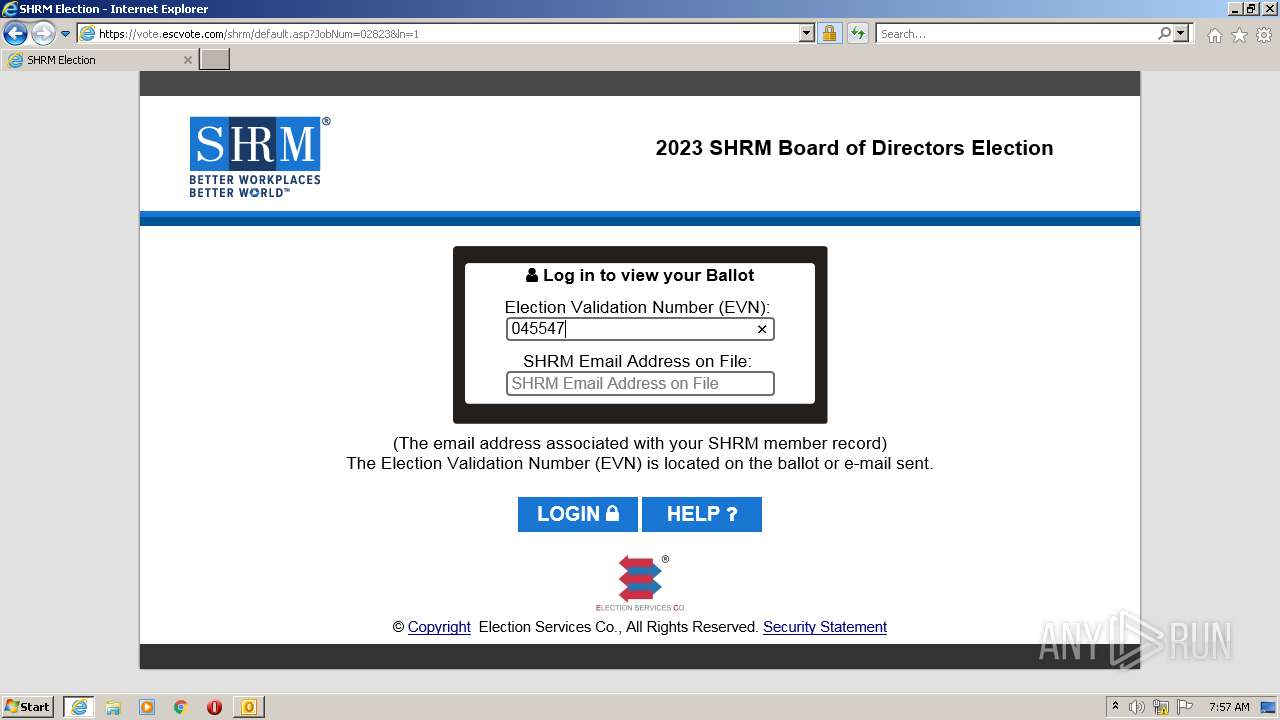
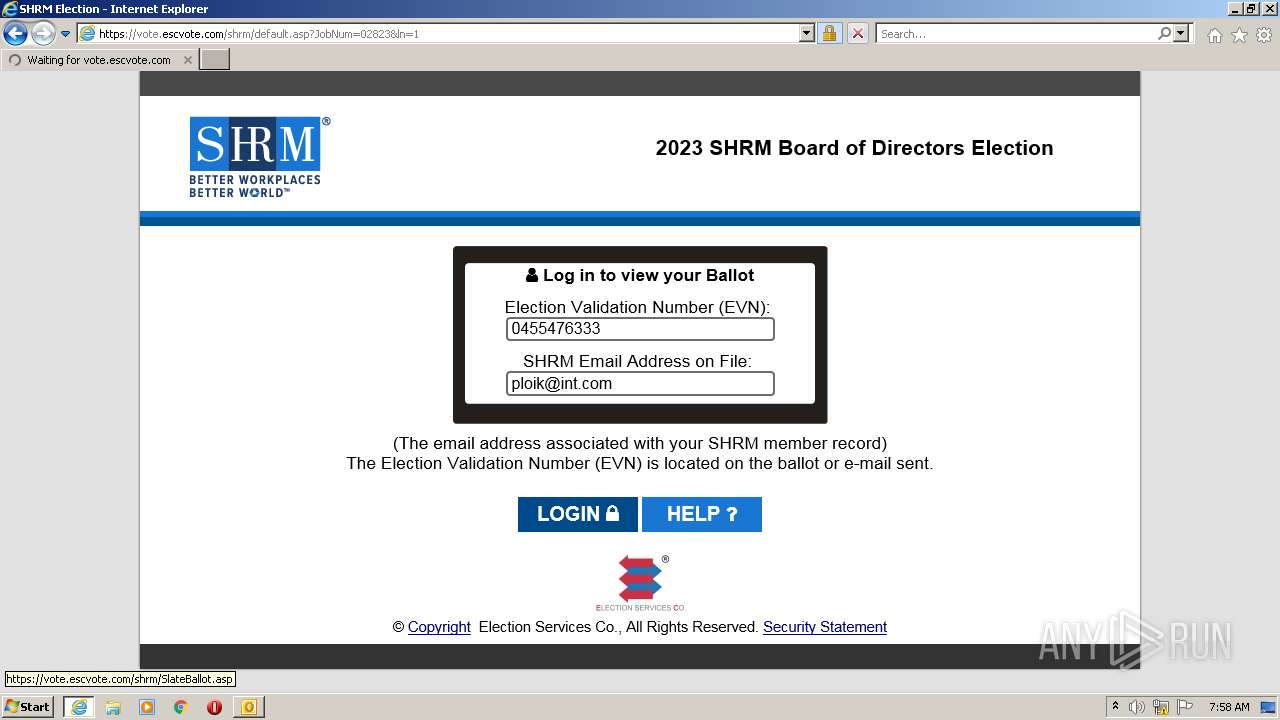
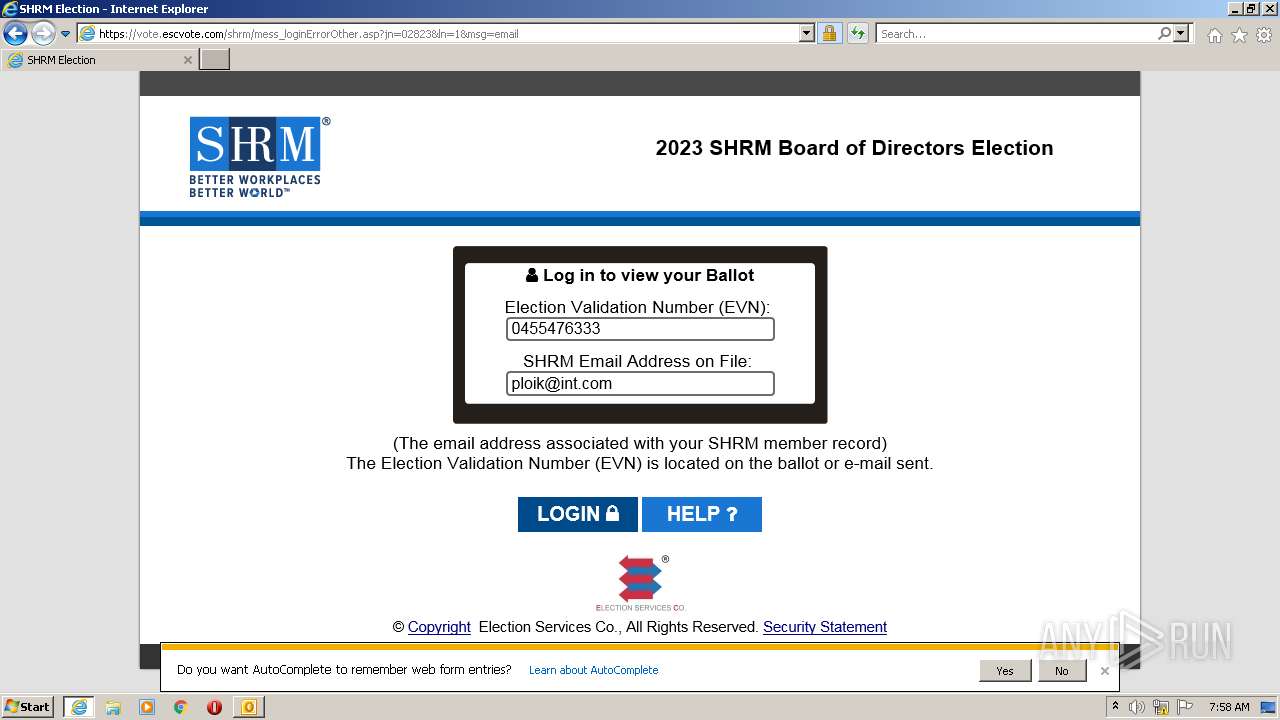
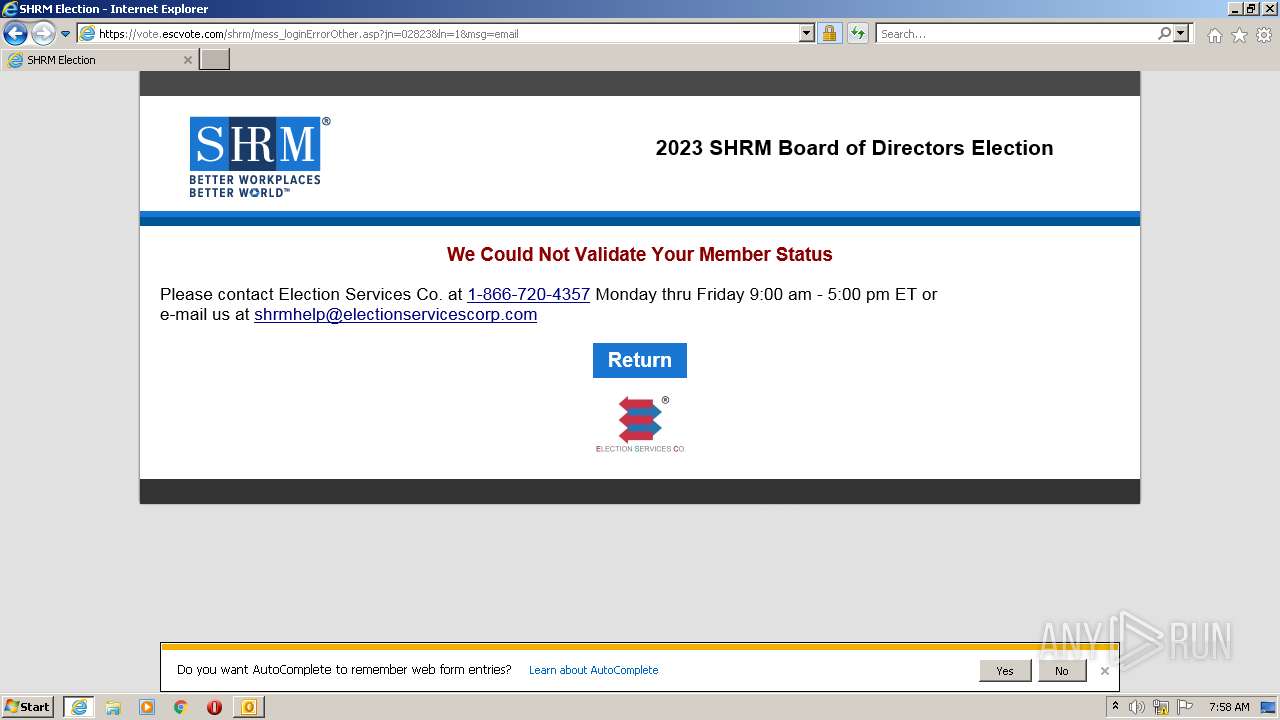
| 3188 | "C:\Program Files\Internet Explorer\iexplore.exe" https://secure-web.cisco.com/16LEa4_f8dG4T2ZiU92PEwZEPRfuxc0gNhkIjg6kofYL0_BVZsdSHXhvRZdTKXDKXFmuAuyopjz6jmqTx-aNj_zQ9GkXq-PJqPl9Dvnr1VttVNM8Omx_psQBV43ahDlGCc5gN5V5TisEGaaru7v1r1swg1l6957HELqSwBqDrMIPCtVaJERXteCHFImF2JyOCZxXbL0oswNYUVHvDvakMC14f5YOLwYc2N7T68rZHJBt9xm3iPZralVZ1q_HBqUI_r3B9FLlVpR-zTUxADq00qQO_fxHl98k1Sa1zsorGIBFTIELbMkkU2wptIrNA_V5O/https%3A%2F%2Femail.mg.electionservicescorp.com%2Fc%2FeJwdjkGLgzAUhH9NchEkviSad8jB2pQeurBsD3tOYqyCscWkLf33qwsDHzMwwwRd1bVAIUEx2mvpHIOGTpobeZCq5QZRCQOmFcg6rCXnou1kp4hg5tp9_5oD0FEP0FjwAq10qvIoEZptL7hBeORN5eisx5wfifCWwGnT655DGZL_p7_HLUrjuqMPg33OubTpQfjpwgk_hminma462vVjl-UW4rRM5c1G22833kvaF2jW1_PPVwEMoDB7o6gYk7v9A83NQfk | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
21 044
Read events
20 324
Write events
696
Delete events
24
Modification events
| (PID) Process: | (3052) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3052) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3052) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3052) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3052) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3052) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3052) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3052) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3052) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (3052) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
18
Text files
34
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3052 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR4C6E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3052 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 3052 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 3052 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3052 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_TCPrefs_2_A0C414B173C0A74C8D63413DEB622EA7.dat | xml | |
MD5:F194B1FA12F9B6F46A47391FAE8BEEC2 | SHA256:FCD8D7E030BE6EA7588E5C6CB568E3F1BDFC263942074B693942A27DF9521A74 | |||
| 3052 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_29F56949C1460647A800FFBBED40382F.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
| 1712 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6CFED4E1A8866BE87BE17622BFB4D726_FBADB8F7FD7B56EE191ACF24A8989D94 | der | |
MD5:— | SHA256:— | |||
| 3052 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_Calendar_2_2C04471F9EF5594AA65A05696304755C.dat | xml | |
MD5:B21ED3BD946332FF6EBC41A87776C6BB | SHA256:B1AAC4E817CD10670B785EF8E5523C4A883F44138E50486987DC73054A46F6F4 | |||
| 1712 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 3052 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ContactPrefs_2_52AAD1AED30DF1449C8179A37B8A3878.dat | xml | |
MD5:BBCF400BD7AE536EB03054021D6A6398 | SHA256:383020065C1F31F4FB09F448599A6D5E532C390AF4E5B8AF0771FE17A23222AD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
48
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3052 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
1712 | iexplore.exe | GET | — | 23.45.105.185:80 | http://x1.c.lencr.org/ | NL | — | — | whitelisted |
1712 | iexplore.exe | GET | 200 | 178.79.242.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?b4fc1b2f20fe6bb5 | DE | compressed | 60.9 Kb | whitelisted |
1712 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQDjmTL5NIrO9%2B84JPrh00LV | US | der | 472 b | whitelisted |
1712 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 2.18 Kb | whitelisted |
3188 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
1712 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3188 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3188 | iexplore.exe | GET | 200 | 178.79.242.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?396408a45b3f325b | DE | compressed | 4.70 Kb | whitelisted |
1712 | iexplore.exe | GET | 200 | 178.79.242.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0065e35d80482235 | DE | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3188 | iexplore.exe | 95.140.236.128:80 | ctldl.windowsupdate.com | LLNW | US | malicious |
3188 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | EDGECAST | US | whitelisted |
3188 | iexplore.exe | 96.16.143.41:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
3052 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1712 | iexplore.exe | 146.112.255.69:443 | secure-web.cisco.com | OPENDNS | US | suspicious |
3188 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3188 | iexplore.exe | 178.79.242.0:80 | ctldl.windowsupdate.com | LLNW | DE | whitelisted |
3188 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
1712 | iexplore.exe | 3.226.157.7:443 | email.mg.electionservicescorp.com | AMAZON-AES | US | suspicious |
1712 | iexplore.exe | 178.79.242.0:80 | ctldl.windowsupdate.com | LLNW | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
secure-web.cisco.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
commercial.ocsp.identrust.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
email.mg.electionservicescorp.com |
| suspicious |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |