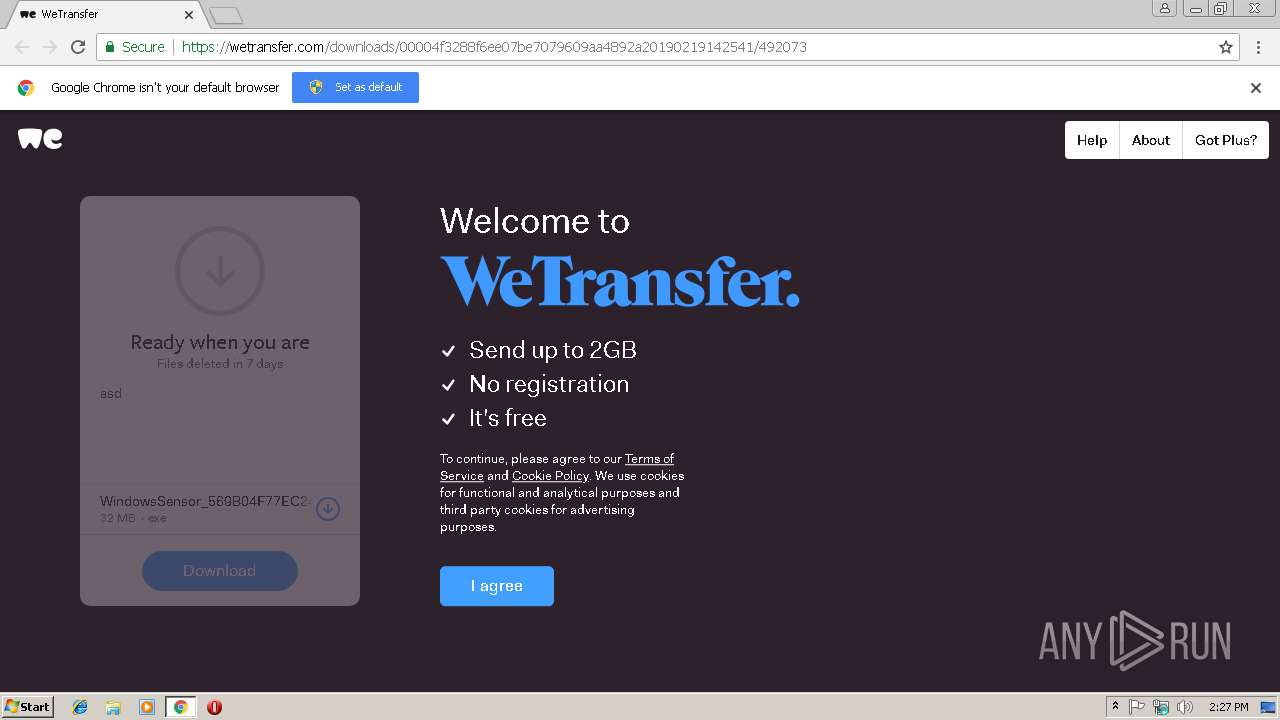
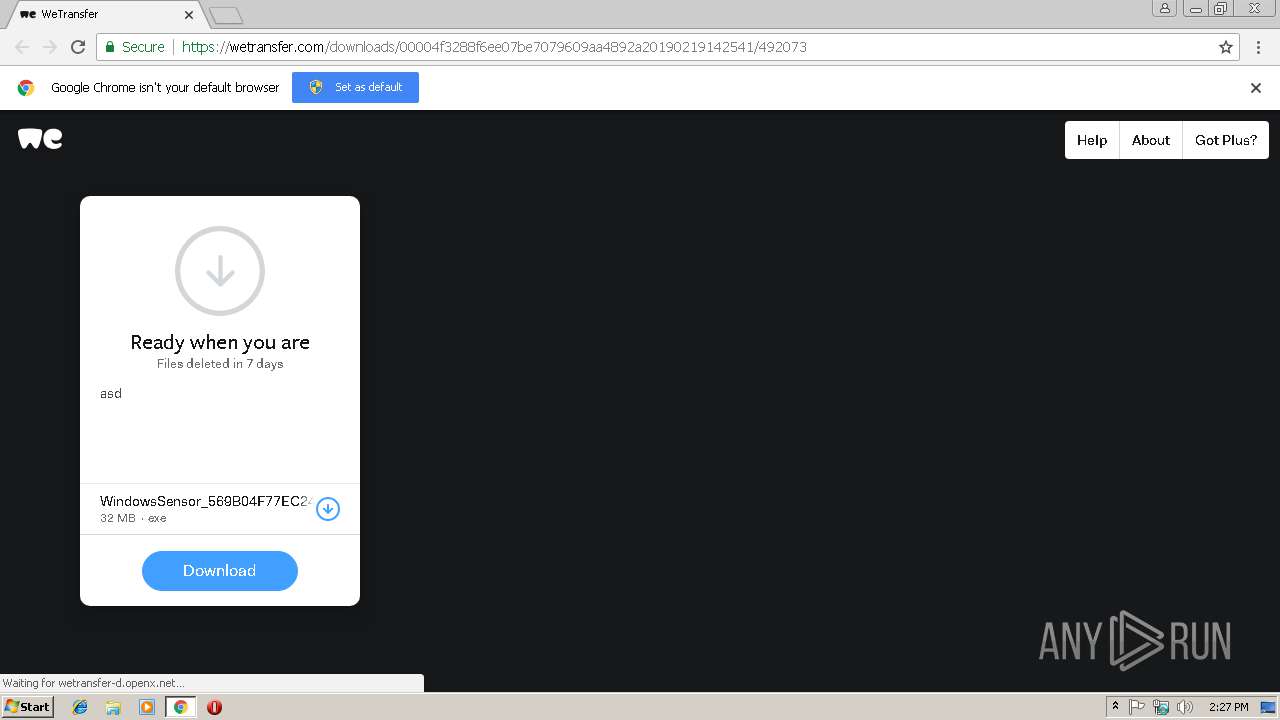
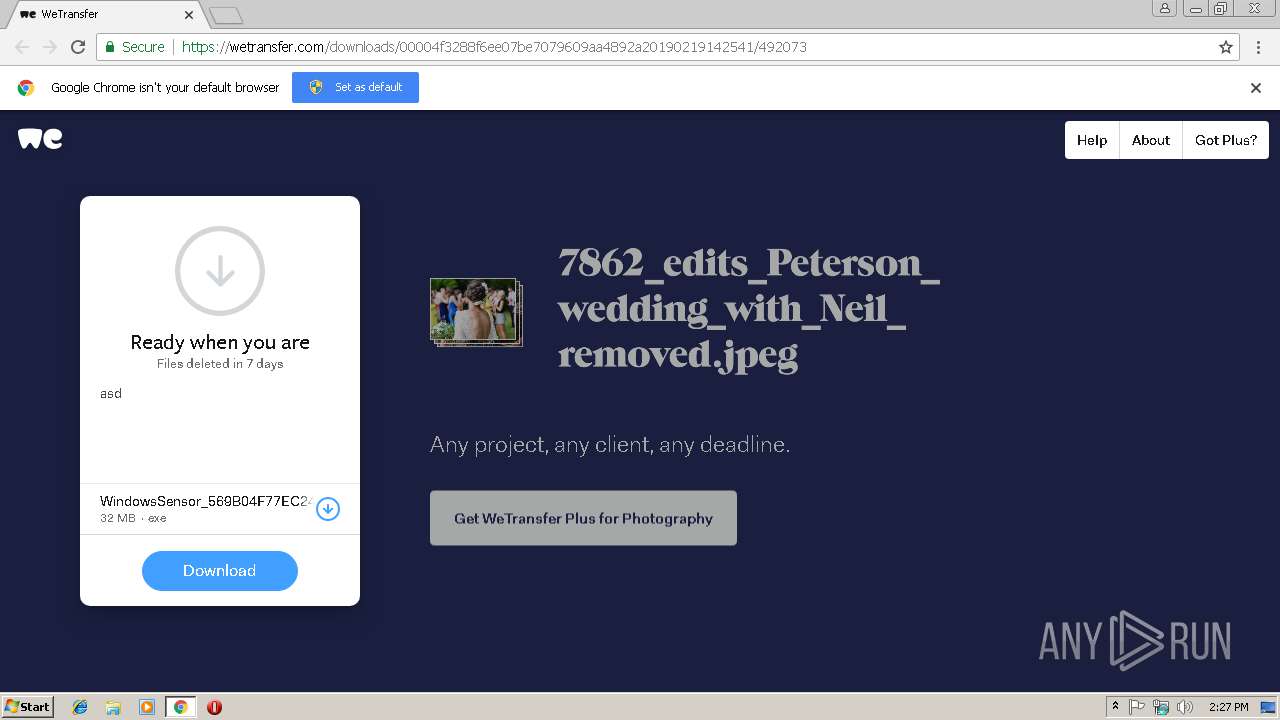
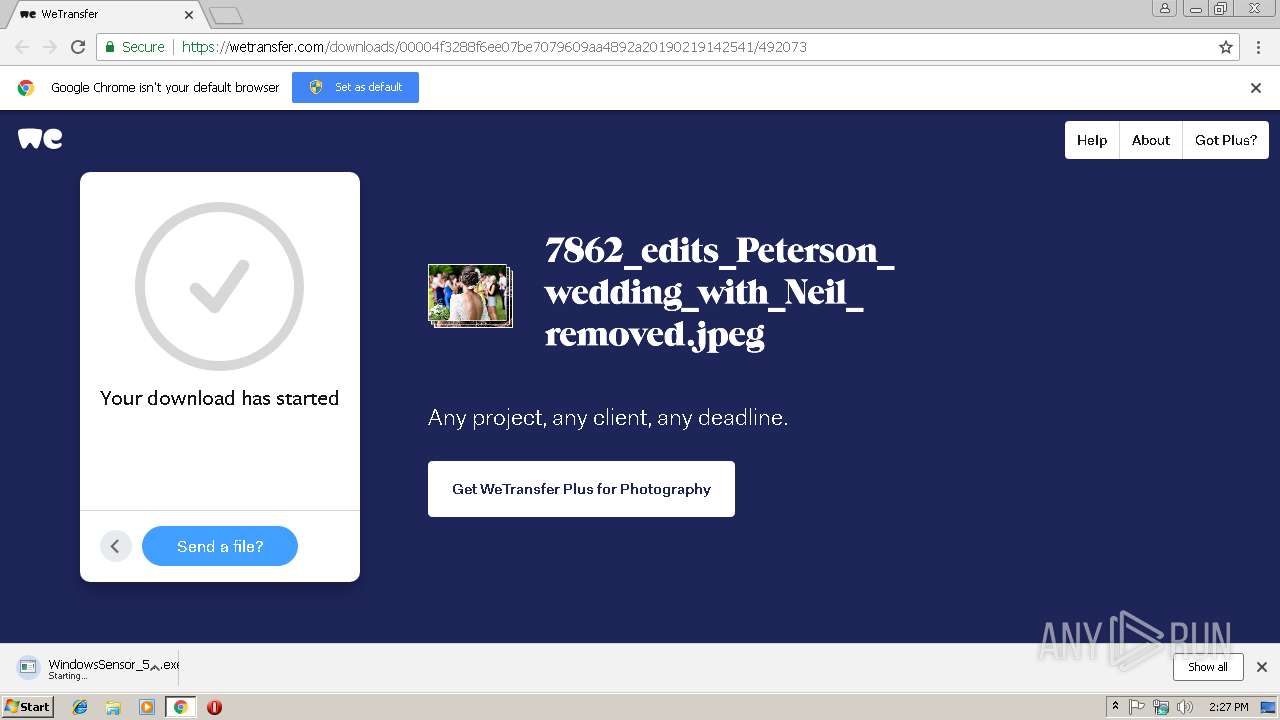
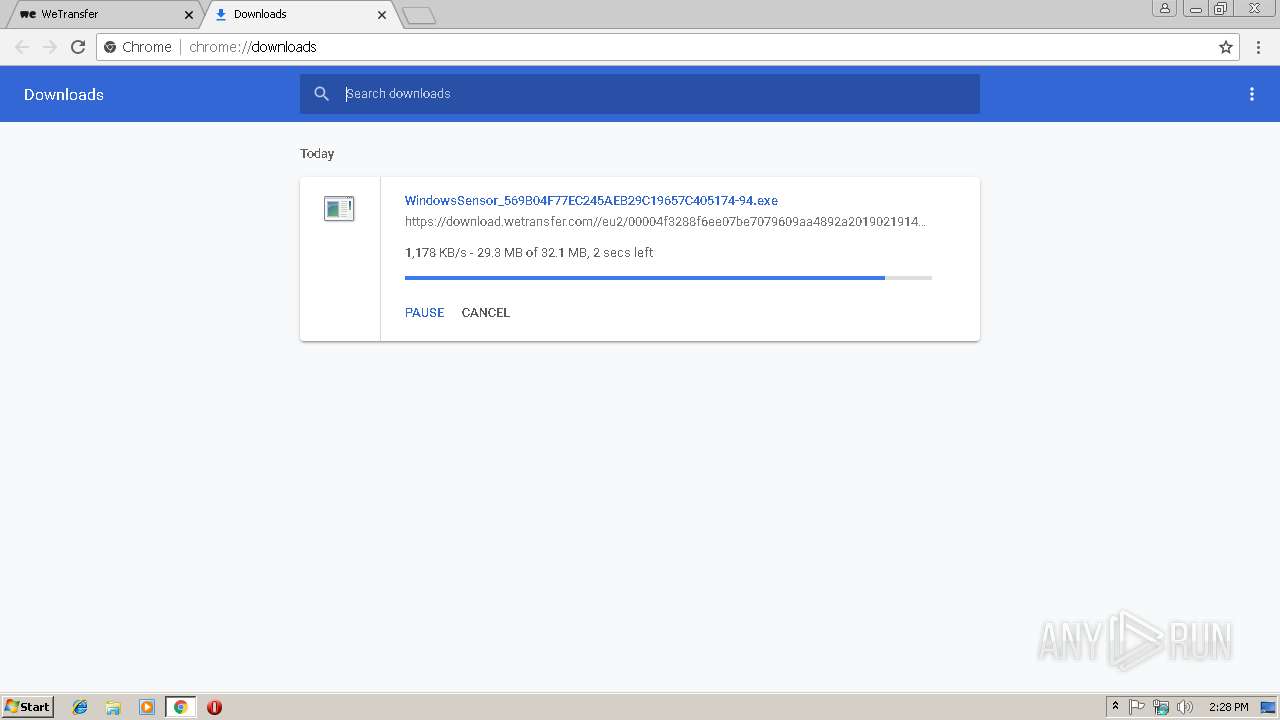
| URL: | https://we.tl/t-JWvaDnf64n |
| Full analysis: | https://app.any.run/tasks/d7f77739-accb-4a3d-95c2-9e0ced0706dc |
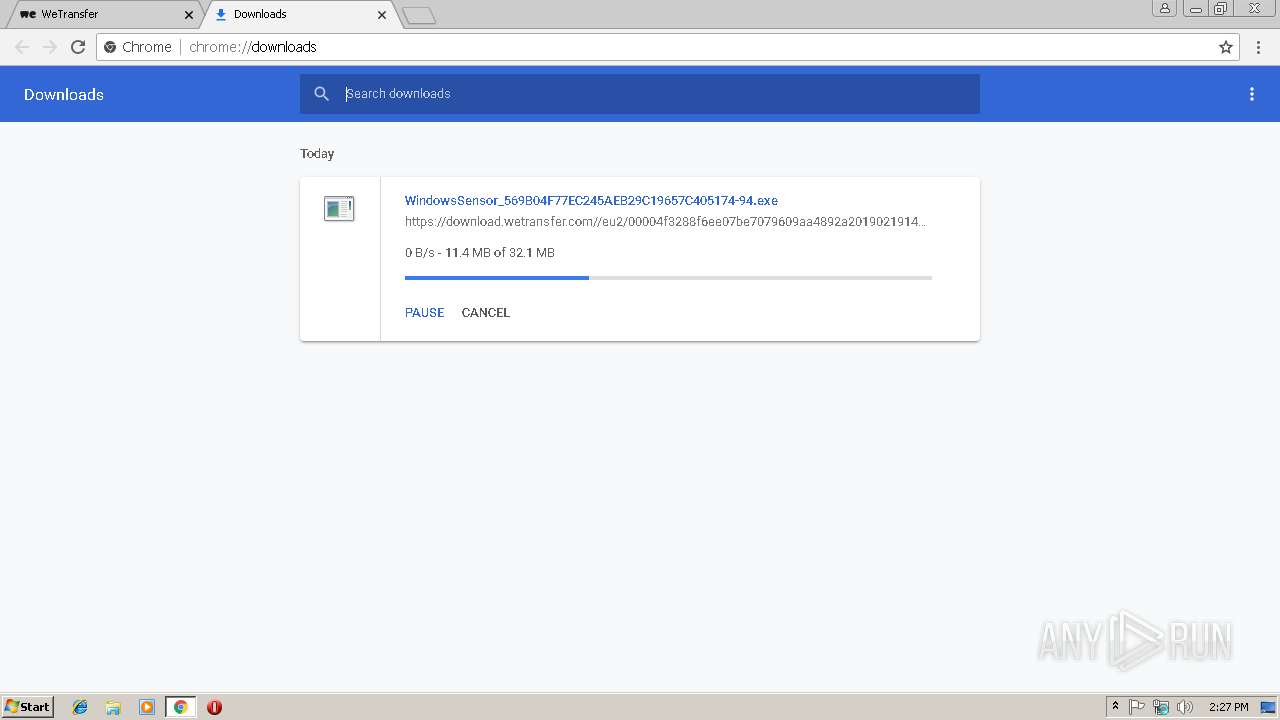
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2019, 14:27:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9C0EA617FC6AEB03E5B032330DB6FDC8 |
| SHA1: | 08DA4446817F6C36C277D5C2CFBD12E384A2DB80 |
| SHA256: | 7395B0E8A6DF7DEE968FAFDED0EC21172410E82D0B833BF2F7483C20D9B912FD |
| SSDEEP: | 3:N8RlJKgyOt:2c0 |
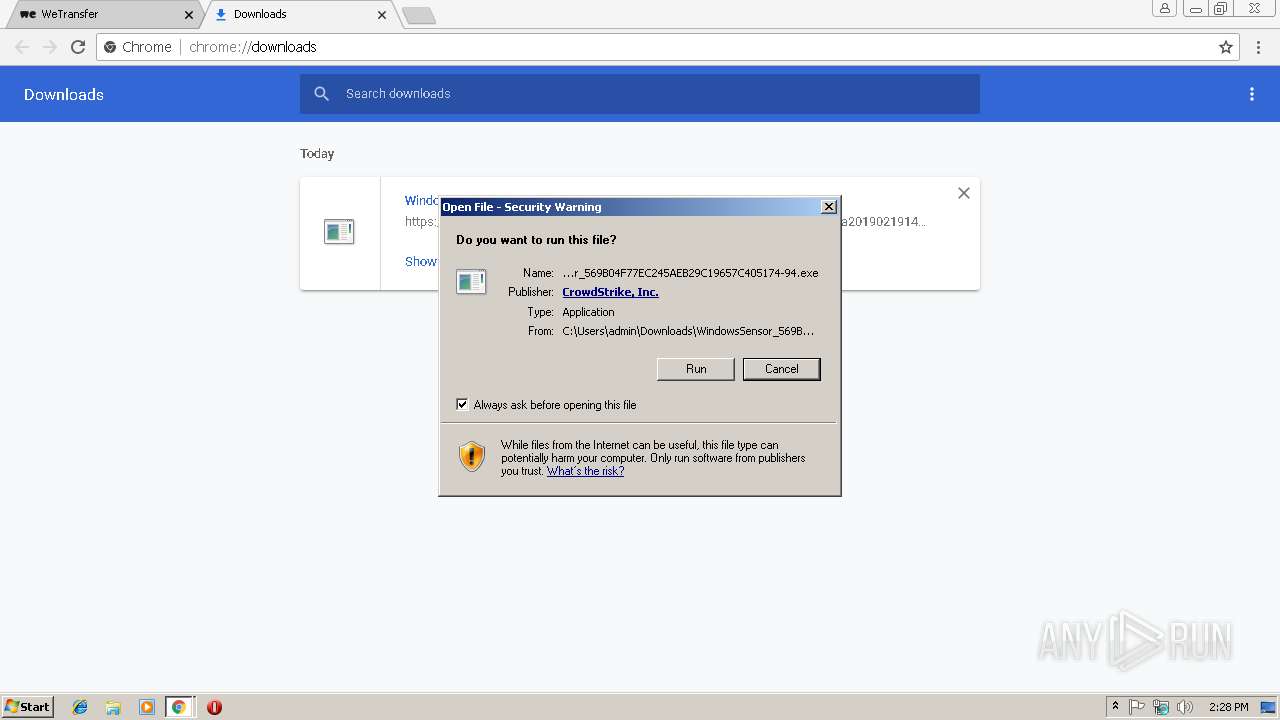
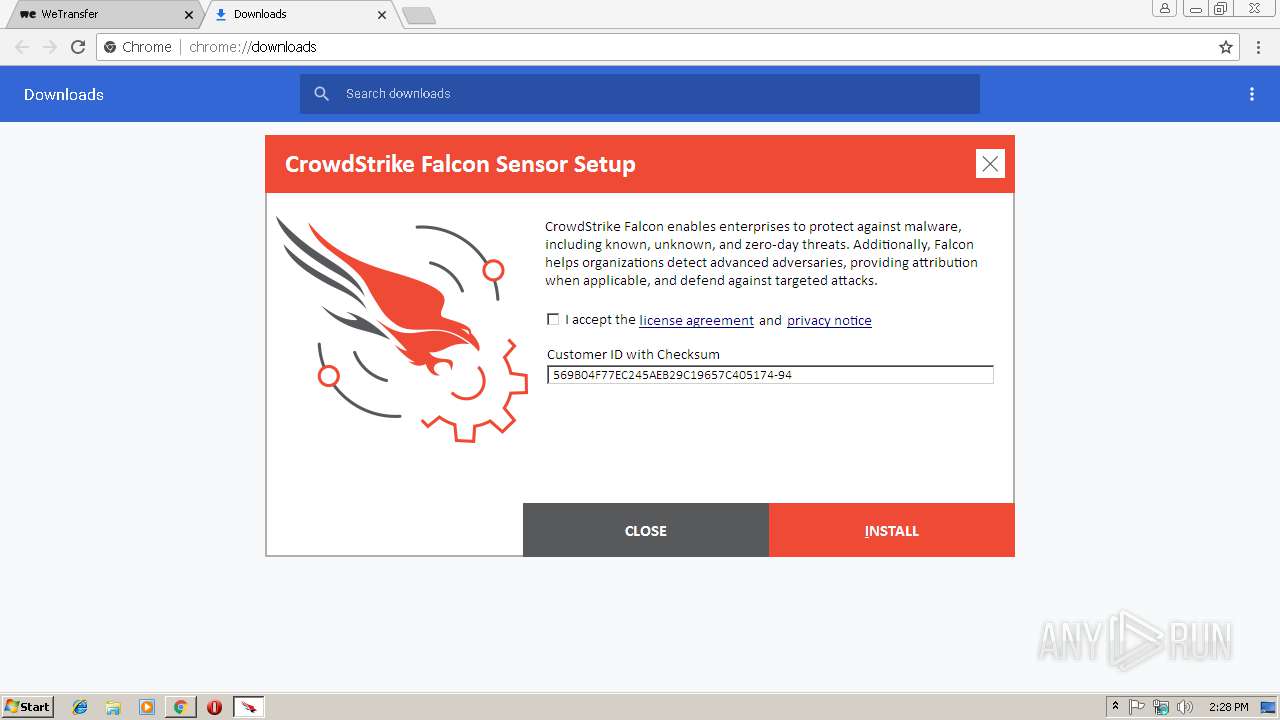
MALICIOUS
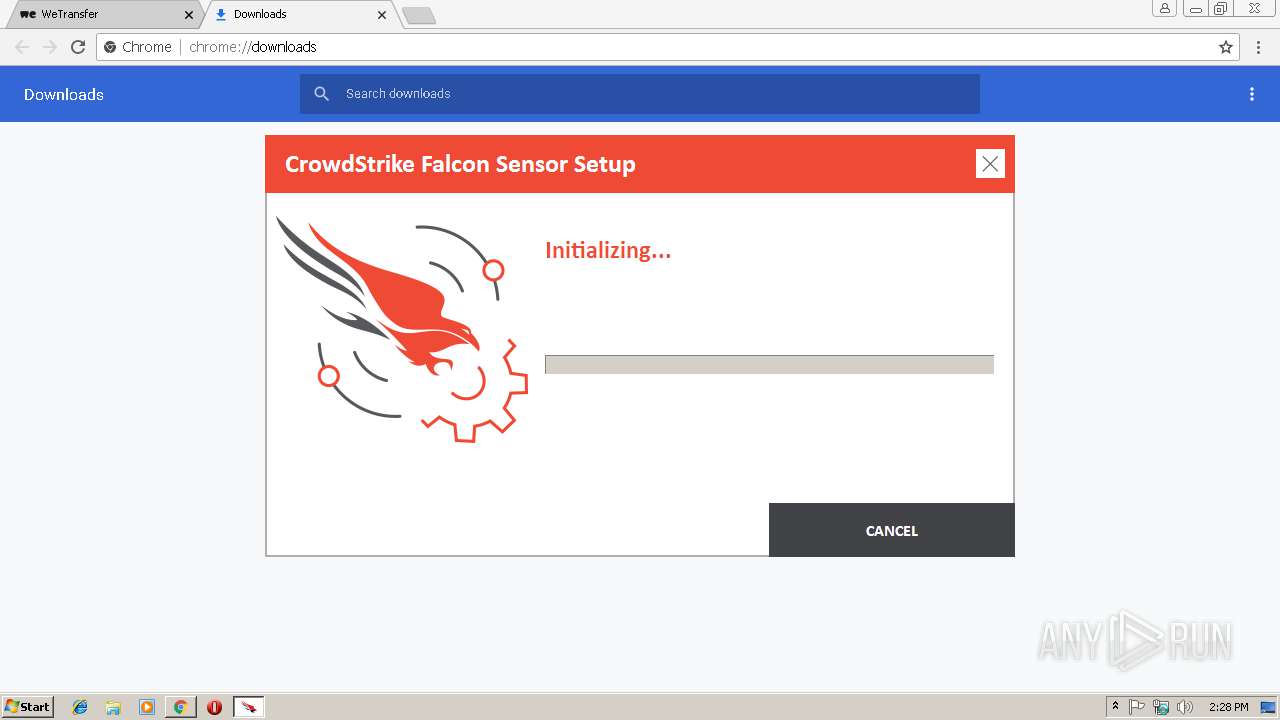
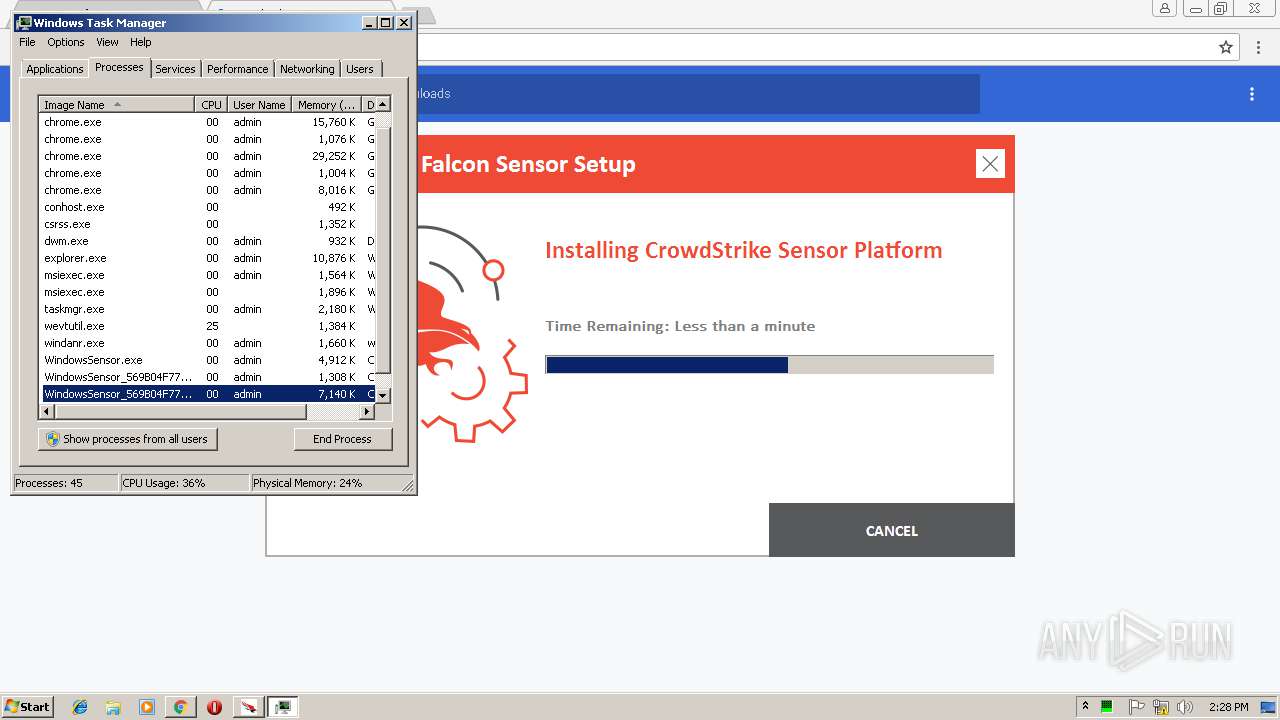
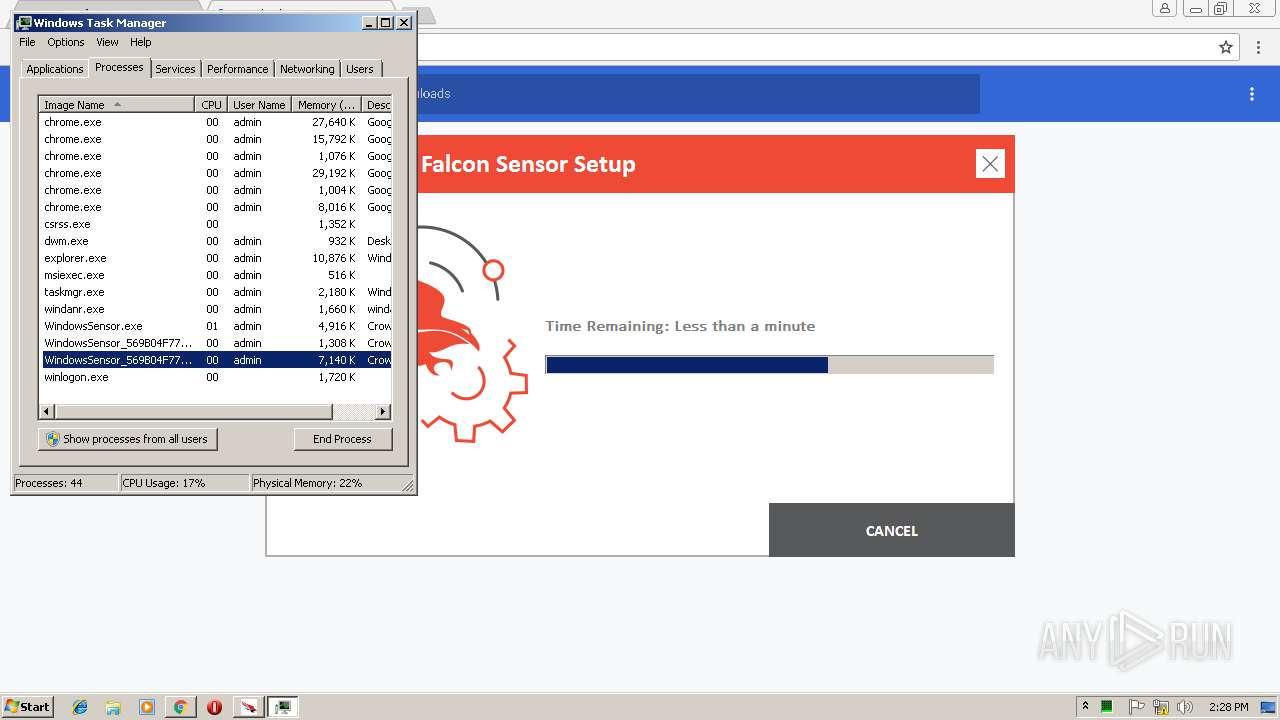
Application was dropped or rewritten from another process
- WindowsSensor_569B04F77EC245AEB29C19657C405174-94.exe (PID: 3952)
- WindowsSensor_569B04F77EC245AEB29C19657C405174-94.exe (PID: 3008)
- WindowsSensor.exe (PID: 3424)
- CSFalconServiceUninstallTool_x86.exe (PID: 1692)
- CSFalconService.exe (PID: 2760)
- CSFalconContainer.exe (PID: 3852)
- ProvisioningGatekeeper.exe (PID: 2516)
Loads dropped or rewritten executable
- WindowsSensor_569B04F77EC245AEB29C19657C405174-94.exe (PID: 3952)
- MsiExec.exe (PID: 4028)
- MsiExec.exe (PID: 3568)
SUSPICIOUS
Executable content was dropped or overwritten
- WindowsSensor_569B04F77EC245AEB29C19657C405174-94.exe (PID: 3008)
- chrome.exe (PID: 2980)
- WindowsSensor_569B04F77EC245AEB29C19657C405174-94.exe (PID: 3952)
- WindowsSensor.exe (PID: 3424)
- msiexec.exe (PID: 3528)
- MsiExec.exe (PID: 3056)
- DrvInst.exe (PID: 2500)
Starts itself from another location
- WindowsSensor_569B04F77EC245AEB29C19657C405174-94.exe (PID: 3952)
Creates files in the program directory
- WindowsSensor.exe (PID: 3424)
- WindowsSensor_569B04F77EC245AEB29C19657C405174-94.exe (PID: 3008)
- WindowsSensor_569B04F77EC245AEB29C19657C405174-94.exe (PID: 3952)
Creates a software uninstall entry
- WindowsSensor.exe (PID: 3424)
Searches for installed software
- WindowsSensor.exe (PID: 3424)
Creates COM task schedule object
- msiexec.exe (PID: 3528)
- MsiExec.exe (PID: 3568)
Creates files in the Windows directory
- msiexec.exe (PID: 3528)
- DrvInst.exe (PID: 2500)
- DrvInst.exe (PID: 3128)
Creates files in the driver directory
- msiexec.exe (PID: 3528)
- DrvInst.exe (PID: 2500)
Removes files from Windows directory
- DrvInst.exe (PID: 2500)
Creates or modifies windows services
- DrvInst.exe (PID: 3128)
INFO
Application launched itself
- chrome.exe (PID: 2980)
- msiexec.exe (PID: 3528)
Reads settings of System Certificates
- chrome.exe (PID: 2980)
Reads Internet Cache Settings
- chrome.exe (PID: 2980)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2928)
Changes settings of System certificates
- DrvInst.exe (PID: 3696)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 3696)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2548)
- MsiExec.exe (PID: 4060)
- MsiExec.exe (PID: 3056)
Creates files in the program directory
- msiexec.exe (PID: 3528)
Creates a software uninstall entry
- msiexec.exe (PID: 3528)
Creates or modifies windows services
- msiexec.exe (PID: 3528)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
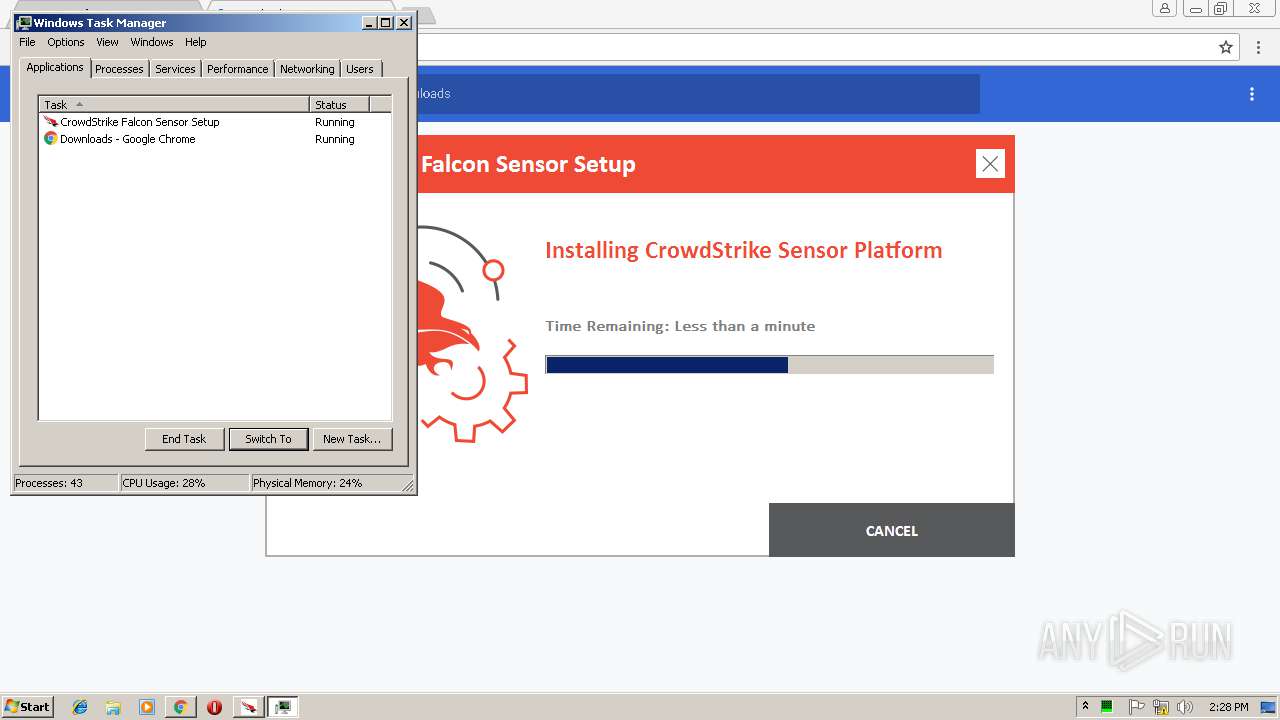
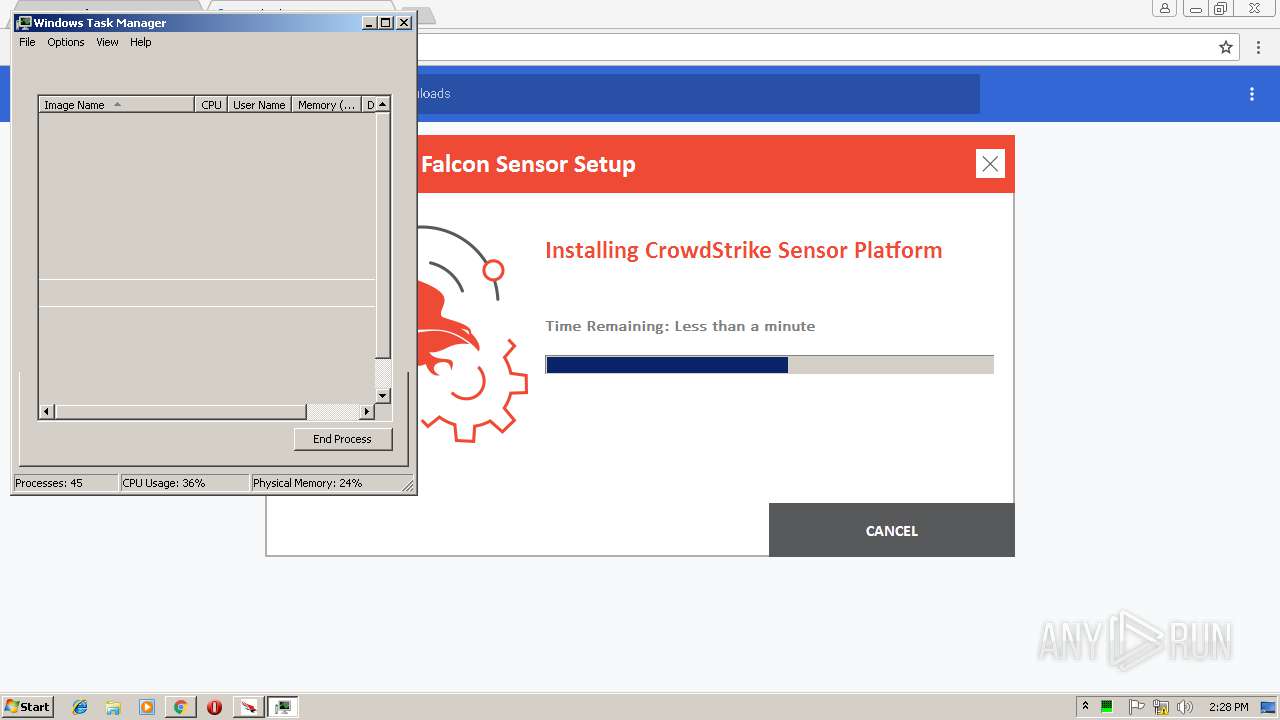
Total processes
69
Monitored processes
31
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=896,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=13BB9CDF1241A331C920FF45C02CC828 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13BB9CDF1241A331C920FF45C02CC828 --renderer-client-id=5 --mojo-platform-channel-handle=3492 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1268 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1692 | "C:\ProgramData\Package Cache\9D4066A375A1F1529F8525BBCB4F9DBA3D378842\CSFalconServiceUninstallTool_x86.exe" | C:\ProgramData\Package Cache\9D4066A375A1F1529F8525BBCB4F9DBA3D378842\CSFalconServiceUninstallTool_x86.exe | — | WindowsSensor.exe | |||||||||||
User: admin Company: CrowdStrike, Inc. Integrity Level: HIGH Description: CrowdStrike Falcon Service Uninstall Tool Exit code: 0 Version: 4.21.8404.0 Modules
| |||||||||||||||
| 2252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=896,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=A3E7E2D18FF84F64740741D123195D83 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=A3E7E2D18FF84F64740741D123195D83 --renderer-client-id=8 --mojo-platform-channel-handle=2344 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=896,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --service-pipe-token=7902E1C7612ABD71EF83087B4AAD65DB --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7902E1C7612ABD71EF83087B4AAD65DB --renderer-client-id=4 --mojo-platform-channel-handle=1900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2500 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{6082489e-8d23-4476-e687-133a238d7644}\CsDeviceControl.inf" "0" "6f54a9d2b" "000005C8" "WinSta0\Default" "000003C0" "208" "C:\Windows\system32\drivers\crowdstrike" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=896,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=93427A790D8D4AC08D2DC3A71D9A98F9 --mojo-platform-channel-handle=4288 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
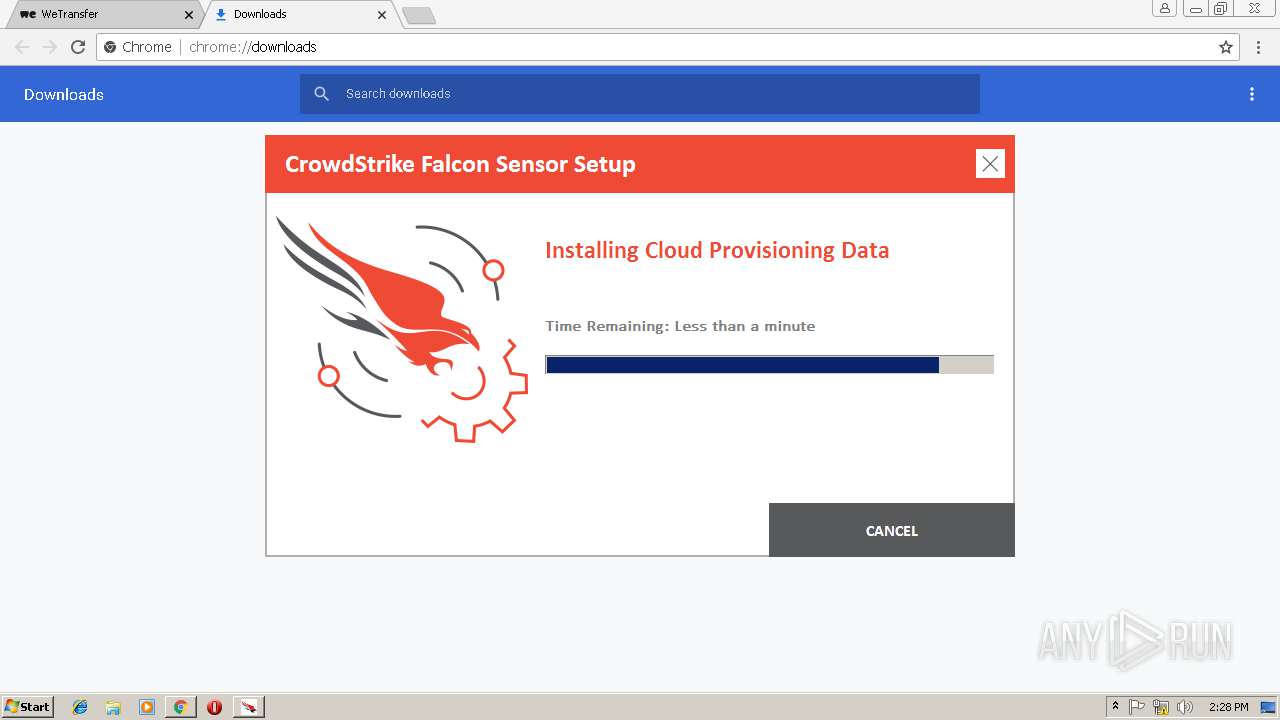
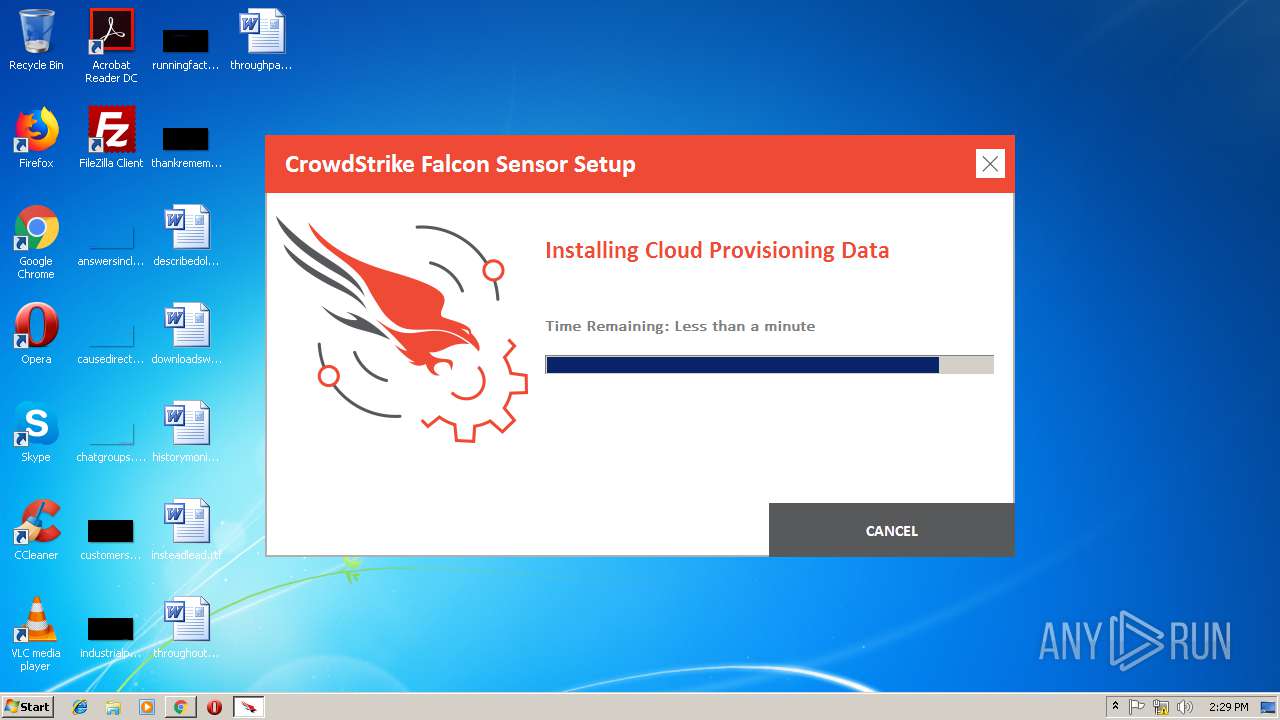
| 2516 | "C:\ProgramData\Package Cache\4CB3BA02620A51F1D3CC5BBB8434A92220CBBE09\ProvisioningGatekeeper.exe" /log "C:\Users\admin\AppData\Local\Temp\CrowdStrike Windows Sensor_20190219142813_003_ProvisioningGatekeeper.exe.log" /waittime 600000 | C:\ProgramData\Package Cache\4CB3BA02620A51F1D3CC5BBB8434A92220CBBE09\ProvisioningGatekeeper.exe | — | WindowsSensor.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2548 | C:\Windows\system32\MsiExec.exe -Embedding B68122D98124C156DFF15EBDE99FC5DB | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2760 | "C:\Program Files\CrowdStrike\CSFalconService.exe" | C:\Program Files\CrowdStrike\CSFalconService.exe | — | services.exe | |||||||||||
User: SYSTEM Company: CrowdStrike, Inc. Integrity Level: SYSTEM Description: CrowdStrike Falcon Sensor Service Exit code: 0 Version: 4.21.8404.0 Modules
| |||||||||||||||
Total events
3 154
Read events
2 502
Write events
622
Delete events
30
Modification events
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2980-13195060045108125 |
Value: 259 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2980-13195060045108125 |
Value: 259 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
36
Suspicious files
70
Text files
277
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c6a484de-d67a-4c9d-b966-e6a0837a8f8f.tmp | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\632fc952-9b2a-4e80-b244-a89fb114b82f.tmp | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:1AA66EFDB743FB0A8DCC1CD79B0B6542 | SHA256:28D56532CCED7375A2A1C7731E57C1A1C2EC1AC9827F3E5BEEE7F8069A5F87DD | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF20ebfa.TMP | text | |
MD5:92BE6B127E72365885AD4C3FB6534EE2 | SHA256:54302A2573ACC775720E7DB0AD85873276713302B4F72596A8DCC44B01C70E51 | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Temp\CabEF36.tmp | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Temp\TarEF37.tmp | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Temp\CabEF57.tmp | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Temp\TarEF58.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
76
DNS requests
38
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2980 | chrome.exe | GET | 200 | 8.253.95.249:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
2980 | chrome.exe | GET | 200 | 143.204.208.42:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2980 | chrome.exe | 143.204.214.8:443 | assets.wetransfer.net | — | US | suspicious |
2980 | chrome.exe | 151.101.2.2:443 | app.launchdarkly.com | Fastly | US | shared |
2980 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 172.217.16.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 143.204.214.105:443 | we.tl | — | US | suspicious |
2980 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 143.204.208.42:80 | x.ss2.us | — | US | unknown |
2980 | chrome.exe | 8.253.95.249:80 | www.download.windowsupdate.com | Global Crossing | US | suspicious |
2980 | chrome.exe | 52.16.134.74:443 | wtplus.wetransfer.com | Amazon.com, Inc. | IE | unknown |
2980 | chrome.exe | 54.194.245.117:443 | wetransfer.com | Amazon.com, Inc. | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
we.tl |
| shared |
accounts.google.com |
| shared |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
wetransfer.com |
| shared |
prod-cdn.wetransfer.net |
| whitelisted |
backgrounds.wetransfer.net |
| whitelisted |
wtplus.wetransfer.com |
| shared |