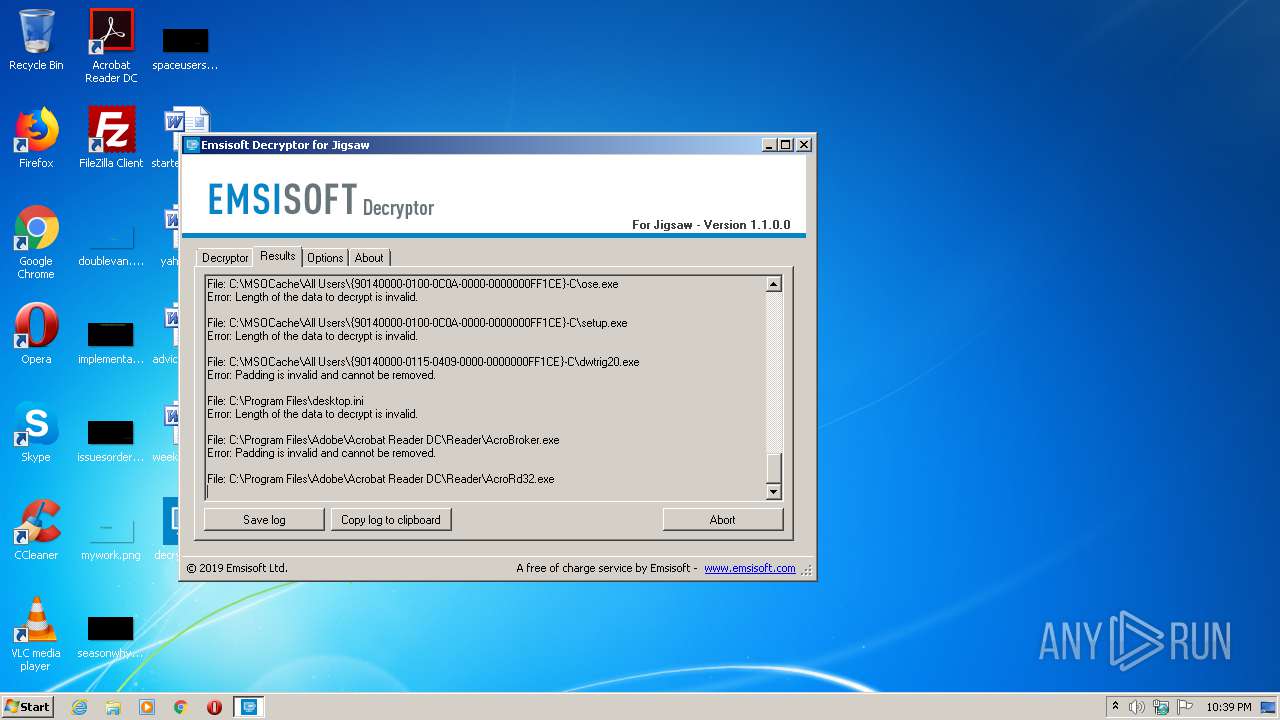
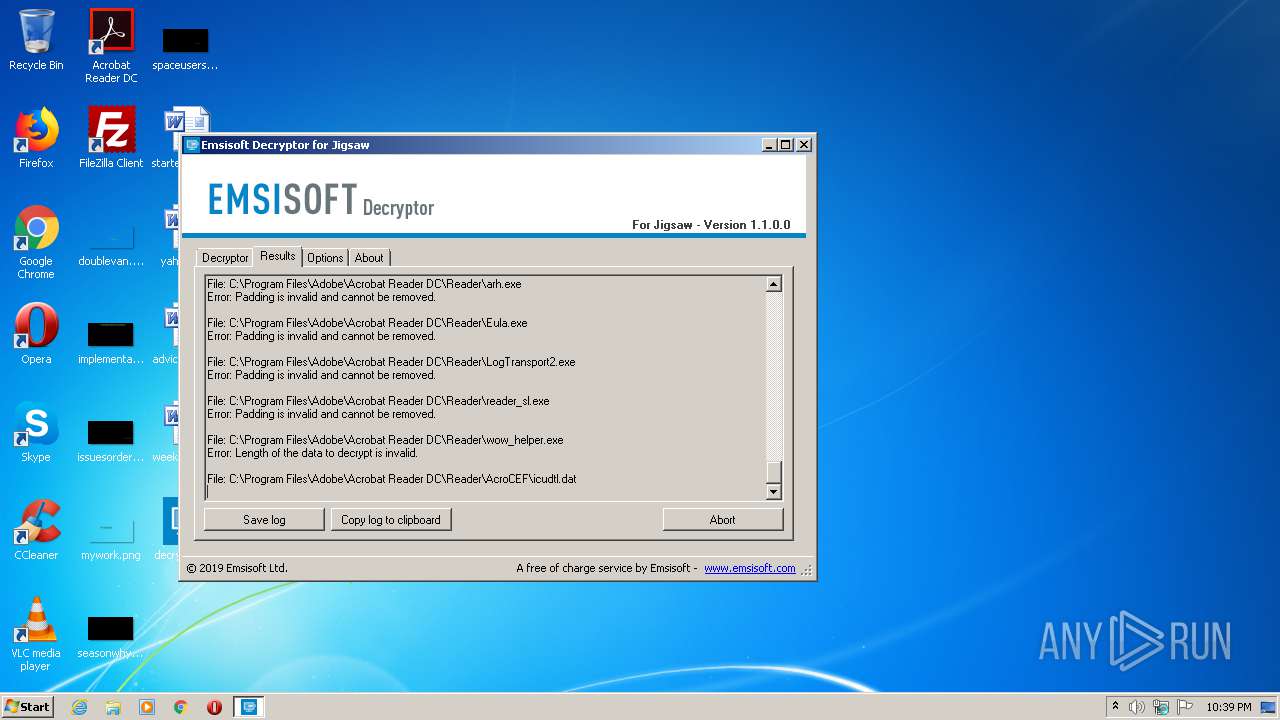
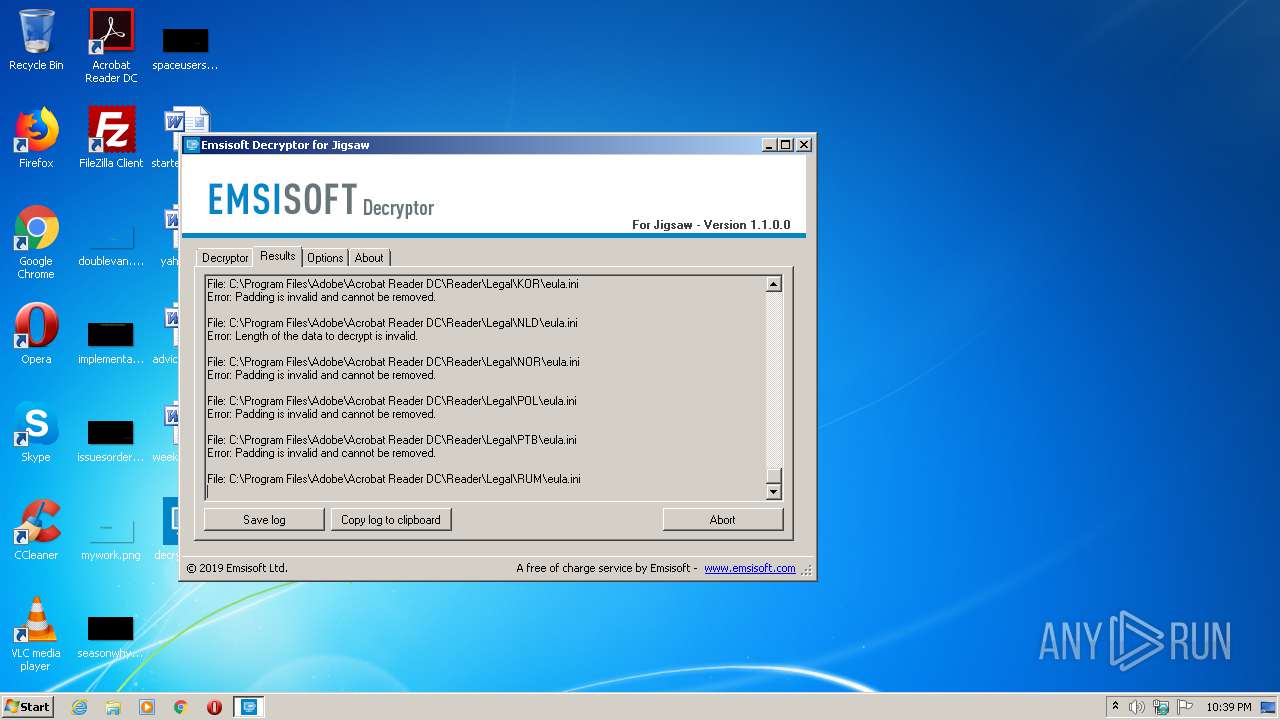
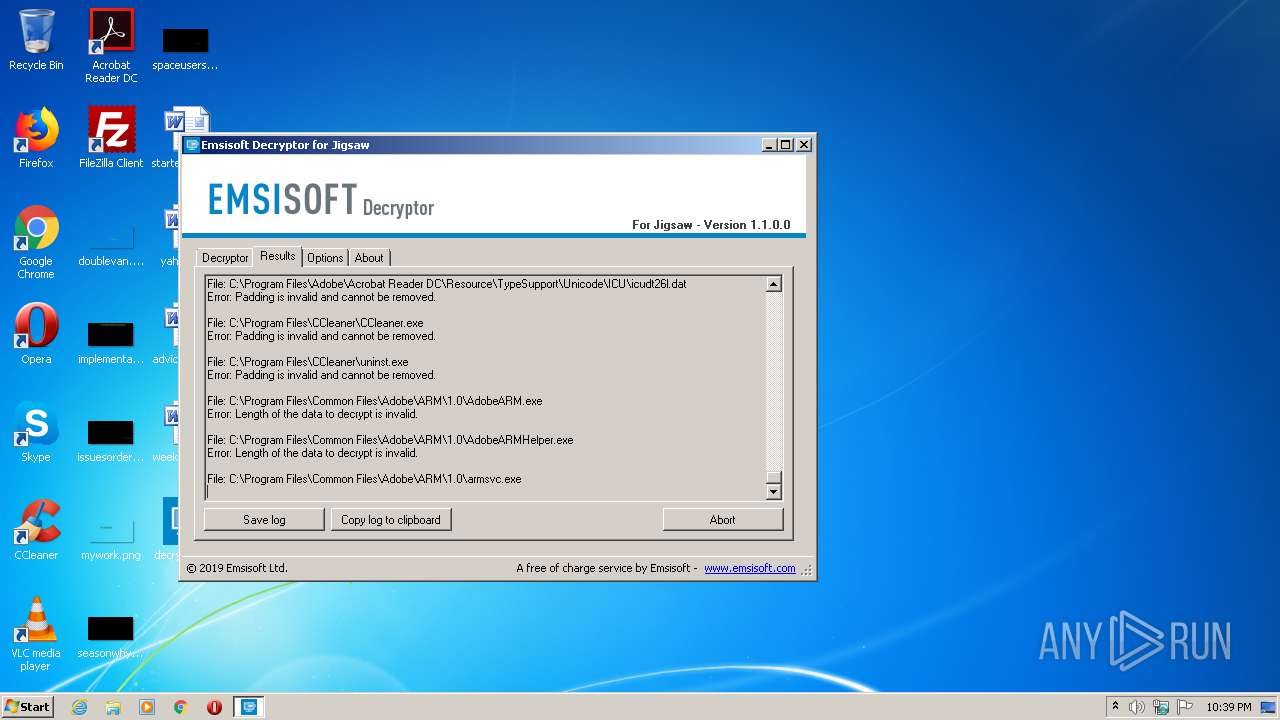
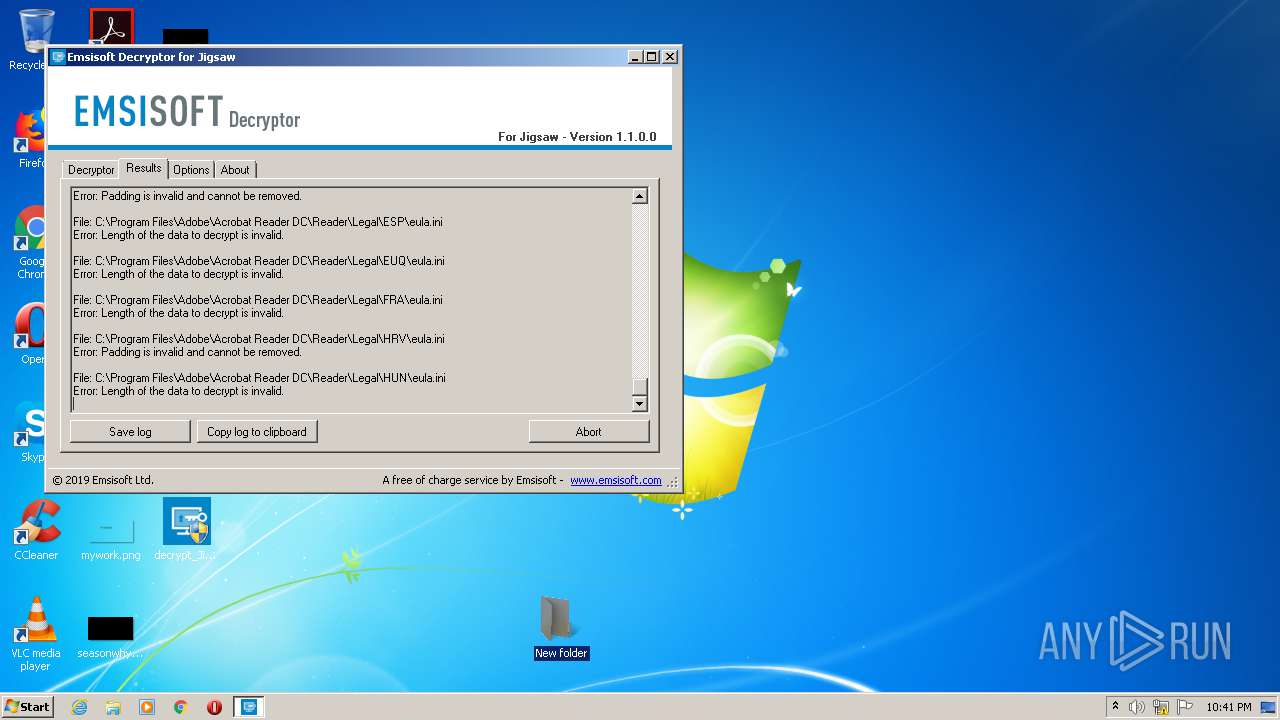
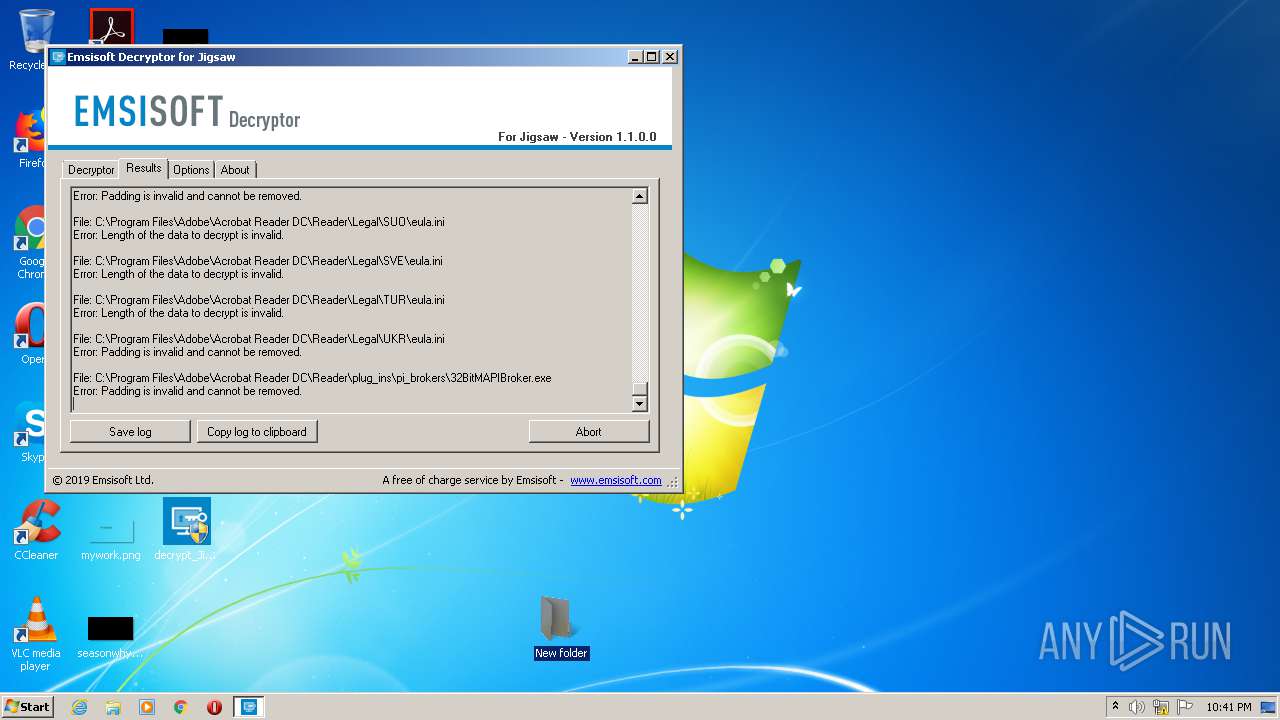
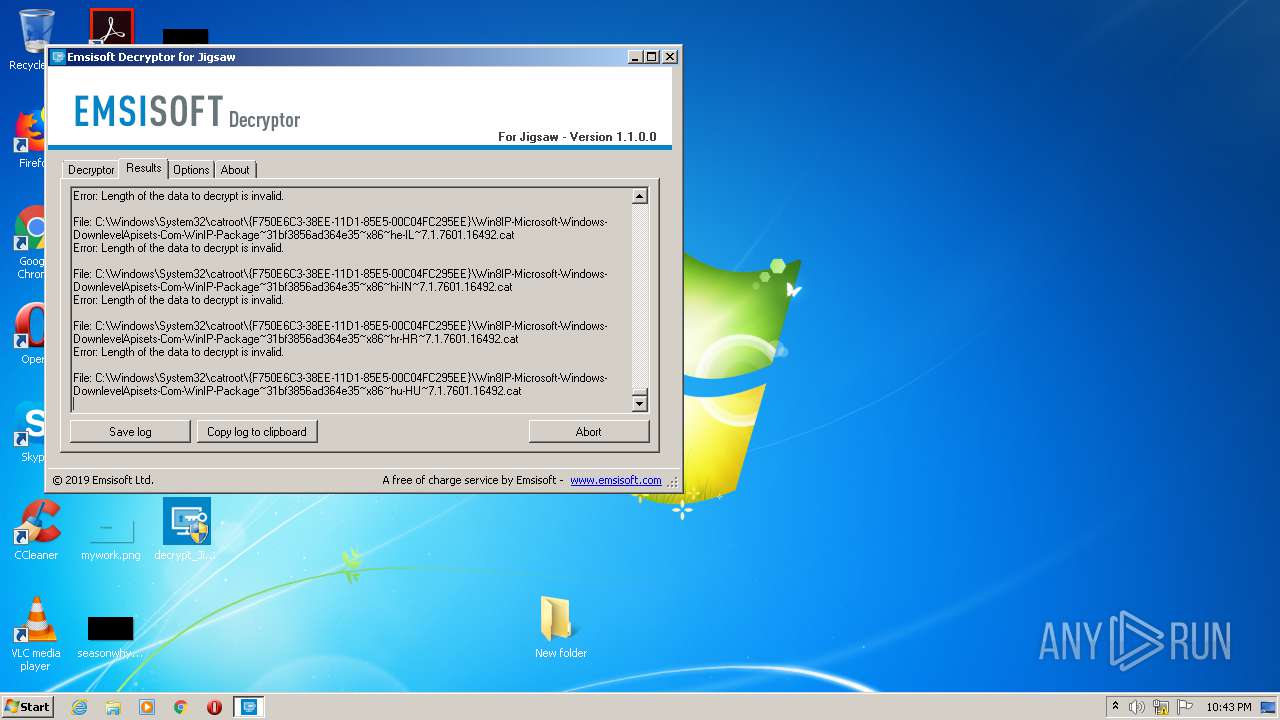
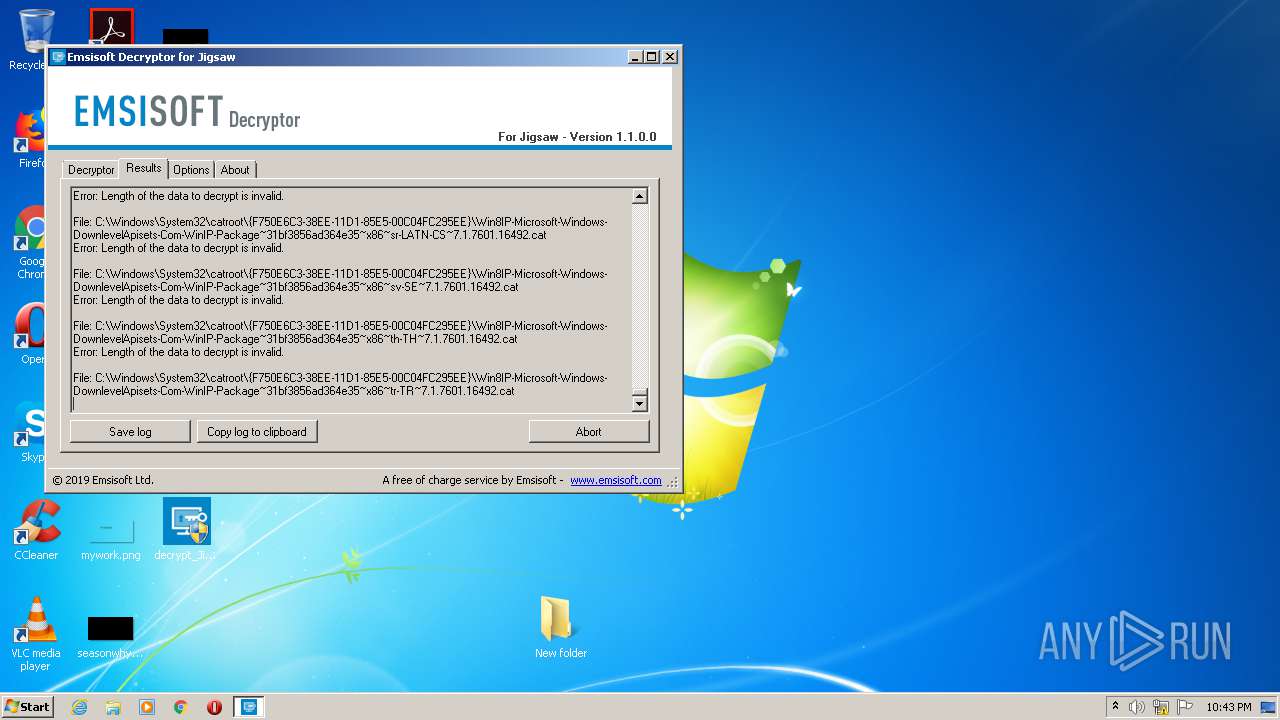
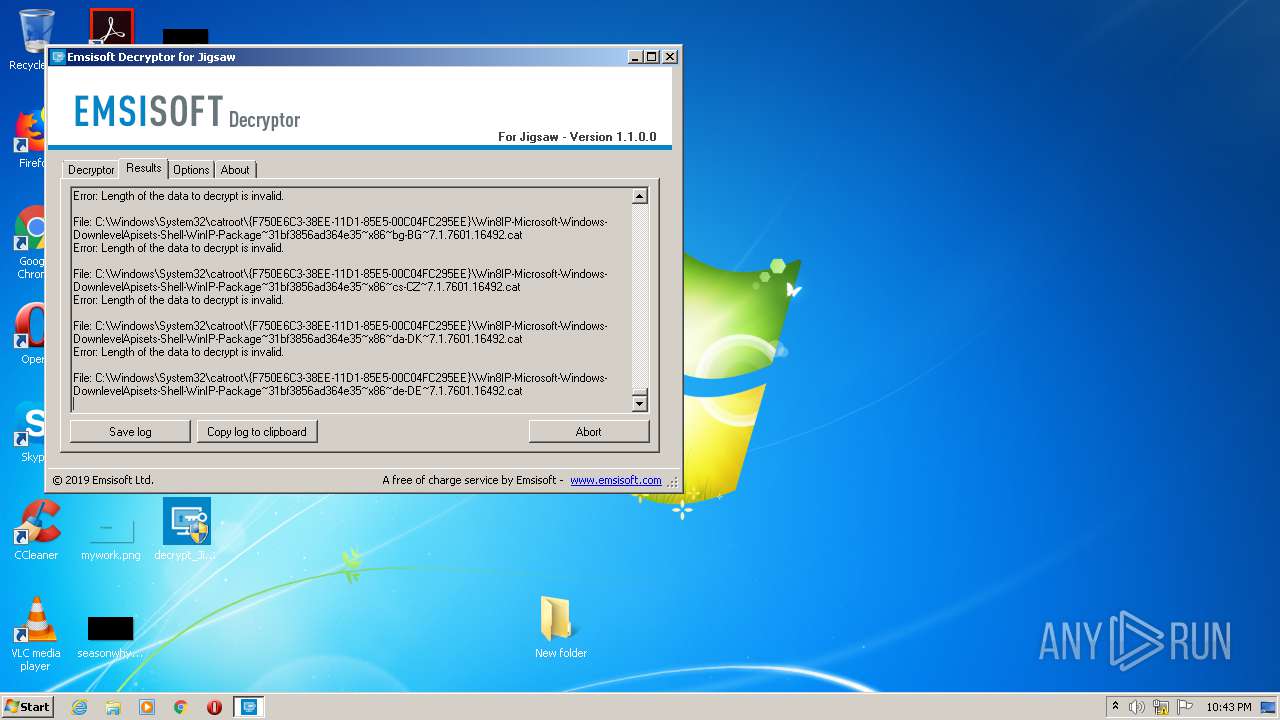
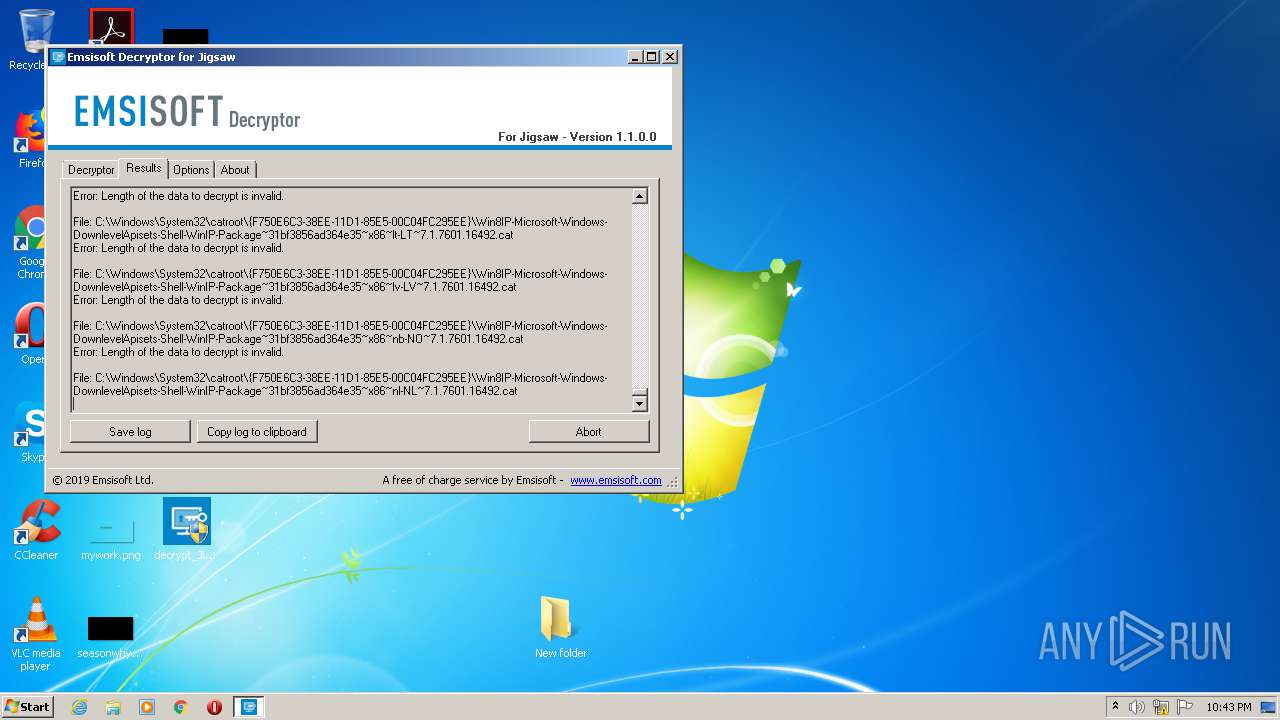
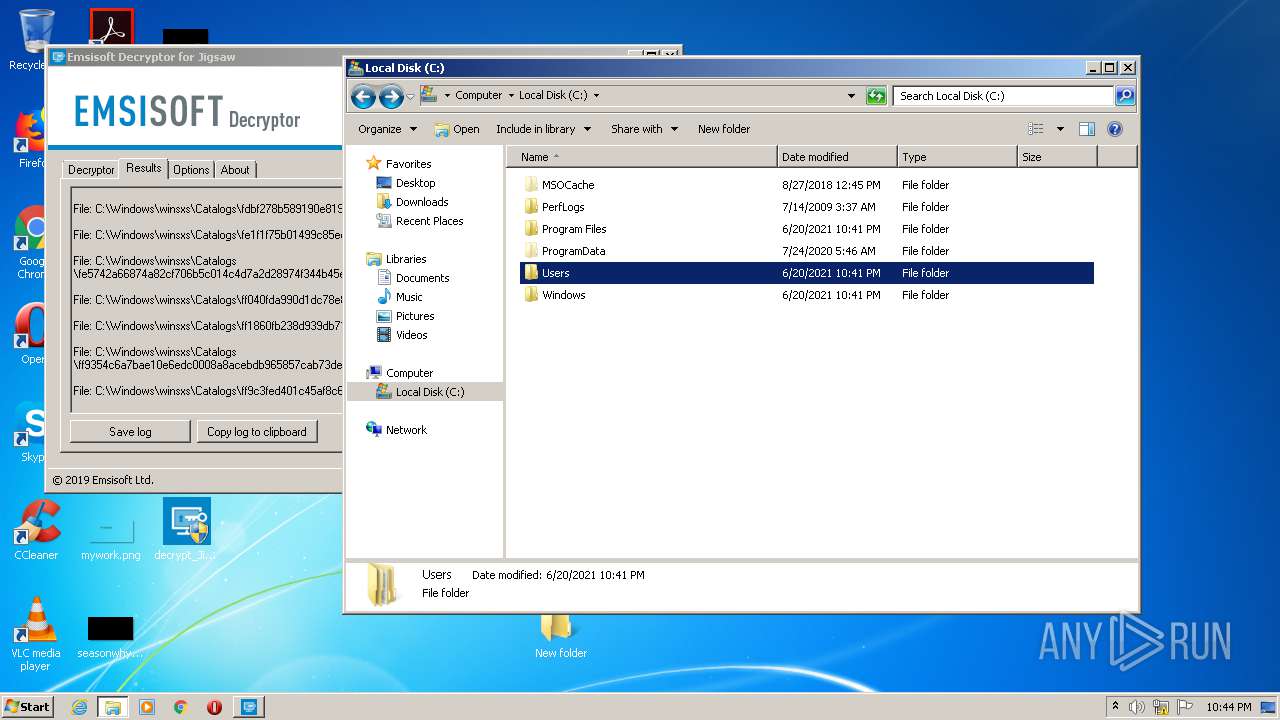
| File name: | decrypt_Jigsaw.exe |
| Full analysis: | https://app.any.run/tasks/b781eb3a-e525-4f5c-87a7-551a12871e1f |
| Verdict: | Malicious activity |
| Analysis date: | June 20, 2021, 21:39:01 |
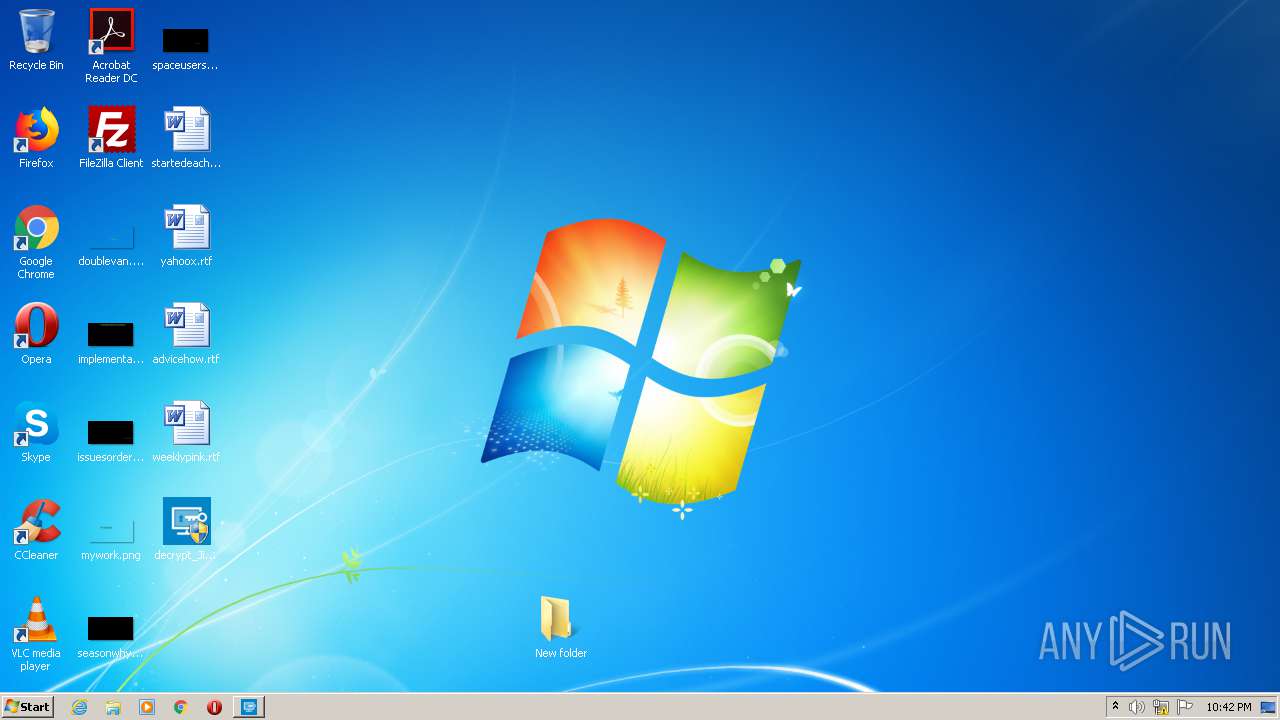
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 85FE7340CB07F340FCAB397E0A0712F7 |
| SHA1: | 360F13FC90236FAE5FD6FBC329E54F09C167AC64 |
| SHA256: | 7374FF40226ADECAB471BC8D91D256FA4A3FF3C830ECD66A38996D034277B22F |
| SSDEEP: | 24576:NuESZ2xVLTpHR52hfZJCYRVFe7b8MKHhSiOTr7pD9d9gW2Zj3YsDClQXWn:oEhxlpx52pZJPVOKNOfVdP2J3Y2pX4 |
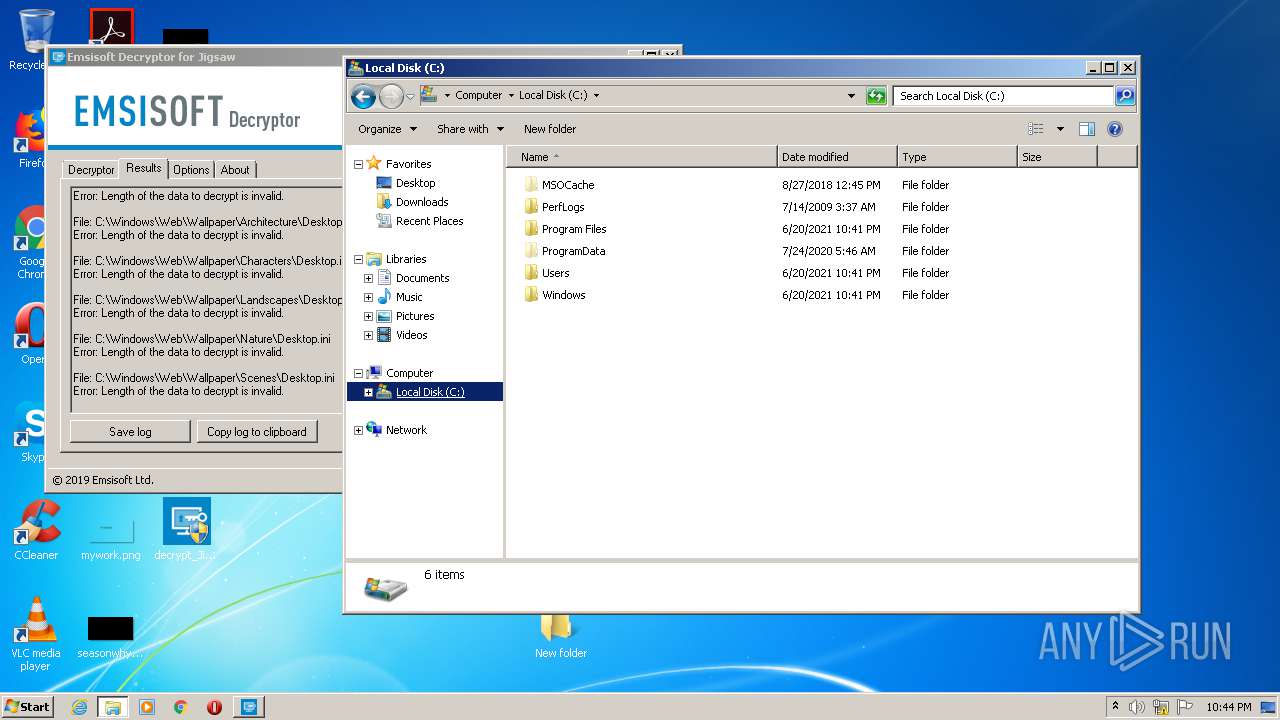
MALICIOUS
Changes settings of System certificates
- decrypt_Jigsaw.exe (PID: 1044)
Writes to a start menu file
- decrypt_Jigsaw.exe (PID: 1044)
- decrypt_Jigsaw.exe (PID: 3360)
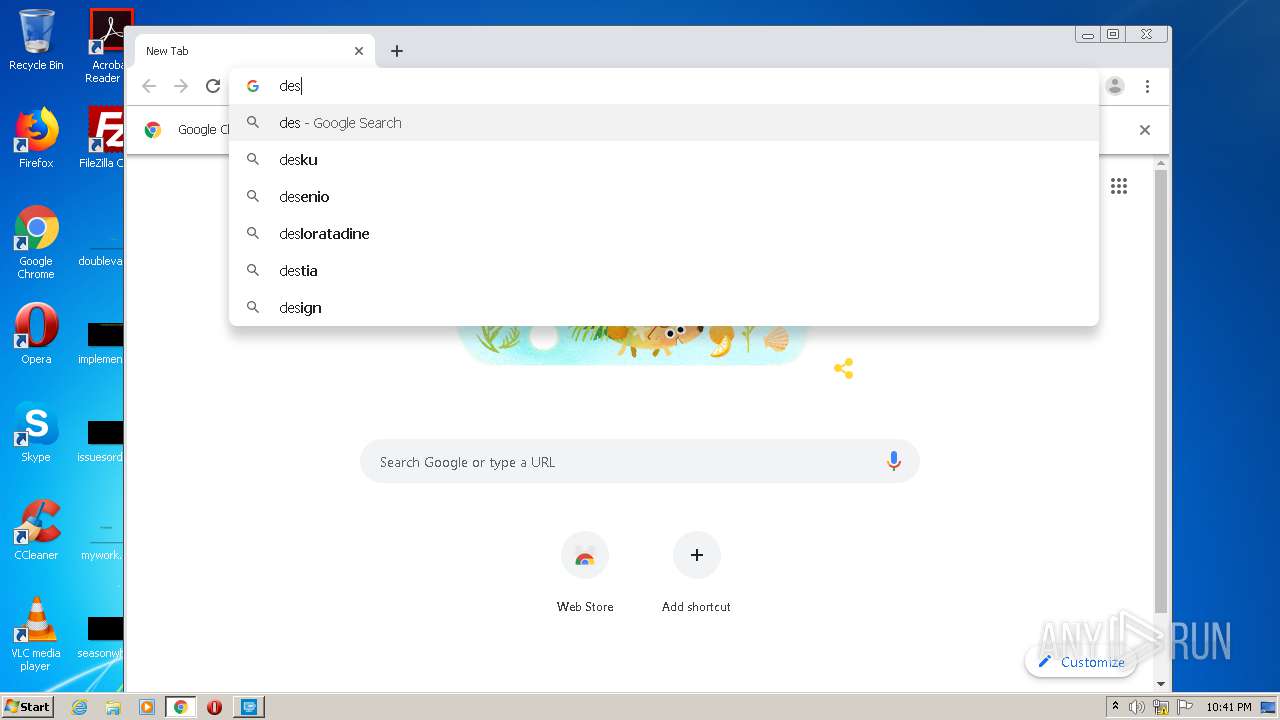
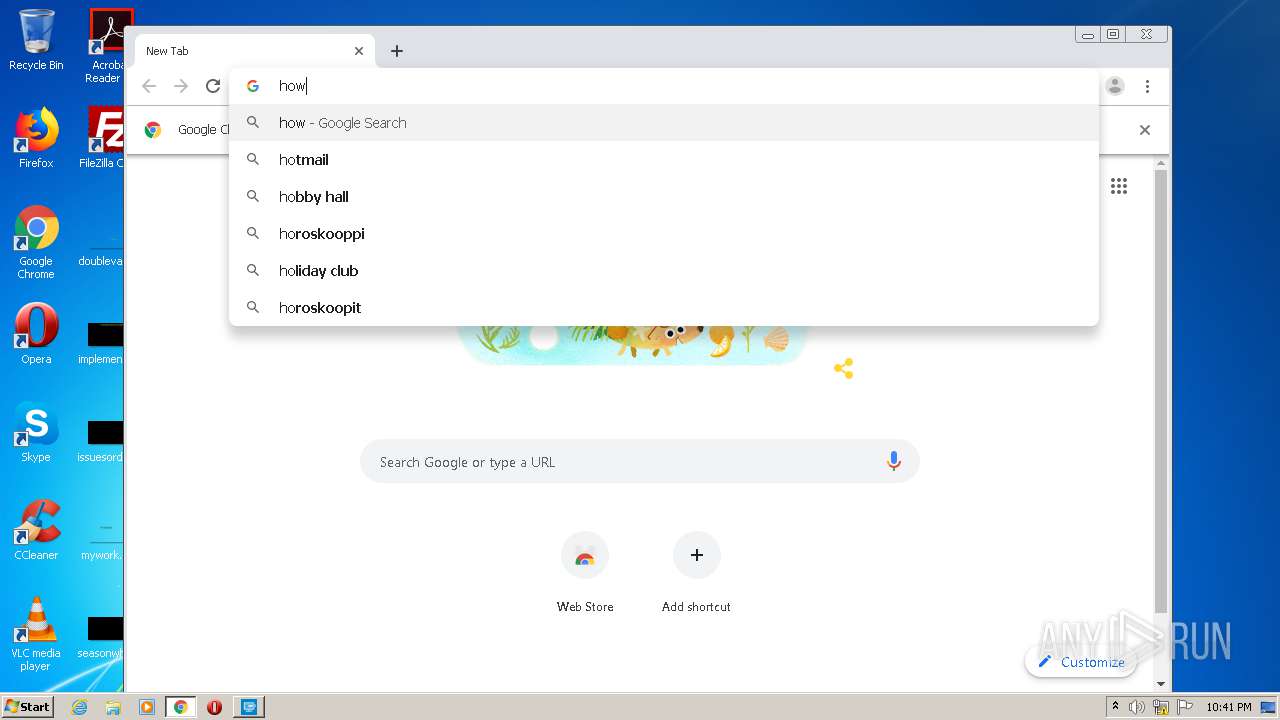
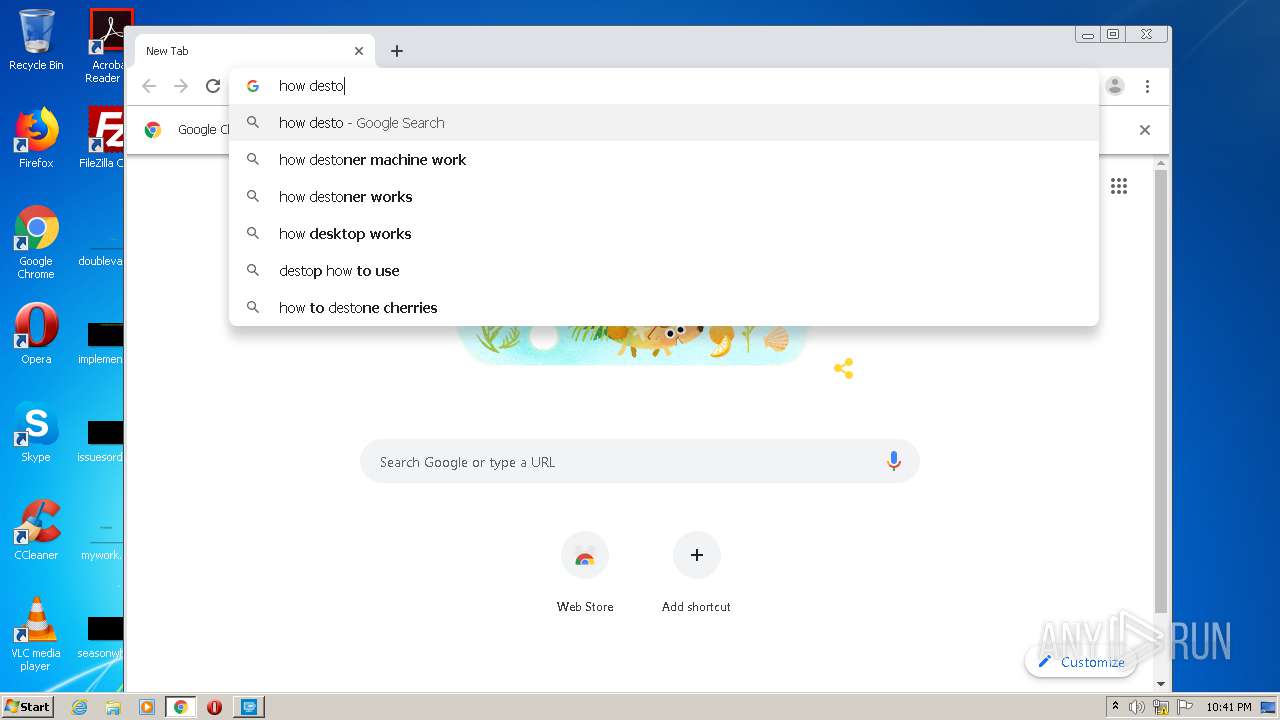
Steals credentials from Web Browsers
- decrypt_Jigsaw.exe (PID: 1044)
- decrypt_Jigsaw.exe (PID: 3360)
Actions looks like stealing of personal data
- decrypt_Jigsaw.exe (PID: 1044)
- decrypt_Jigsaw.exe (PID: 3360)
Application was dropped or rewritten from another process
- SearchProtocolHost.exe (PID: 2712)
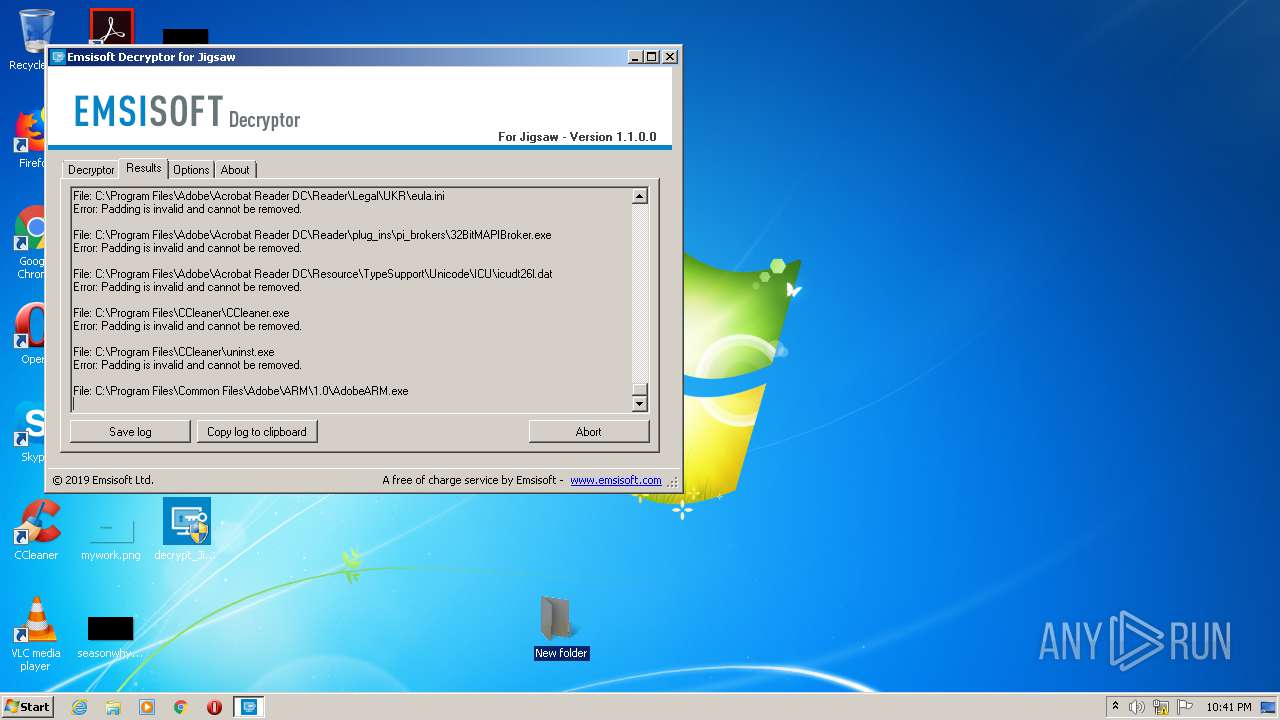
SUSPICIOUS
Reads Environment values
- decrypt_Jigsaw.exe (PID: 1044)
- decrypt_Jigsaw.exe (PID: 3360)
Adds / modifies Windows certificates
- decrypt_Jigsaw.exe (PID: 1044)
Drops a file that was compiled in debug mode
- decrypt_Jigsaw.exe (PID: 1044)
- decrypt_Jigsaw.exe (PID: 3360)
Executable content was dropped or overwritten
- decrypt_Jigsaw.exe (PID: 1044)
- decrypt_Jigsaw.exe (PID: 3360)
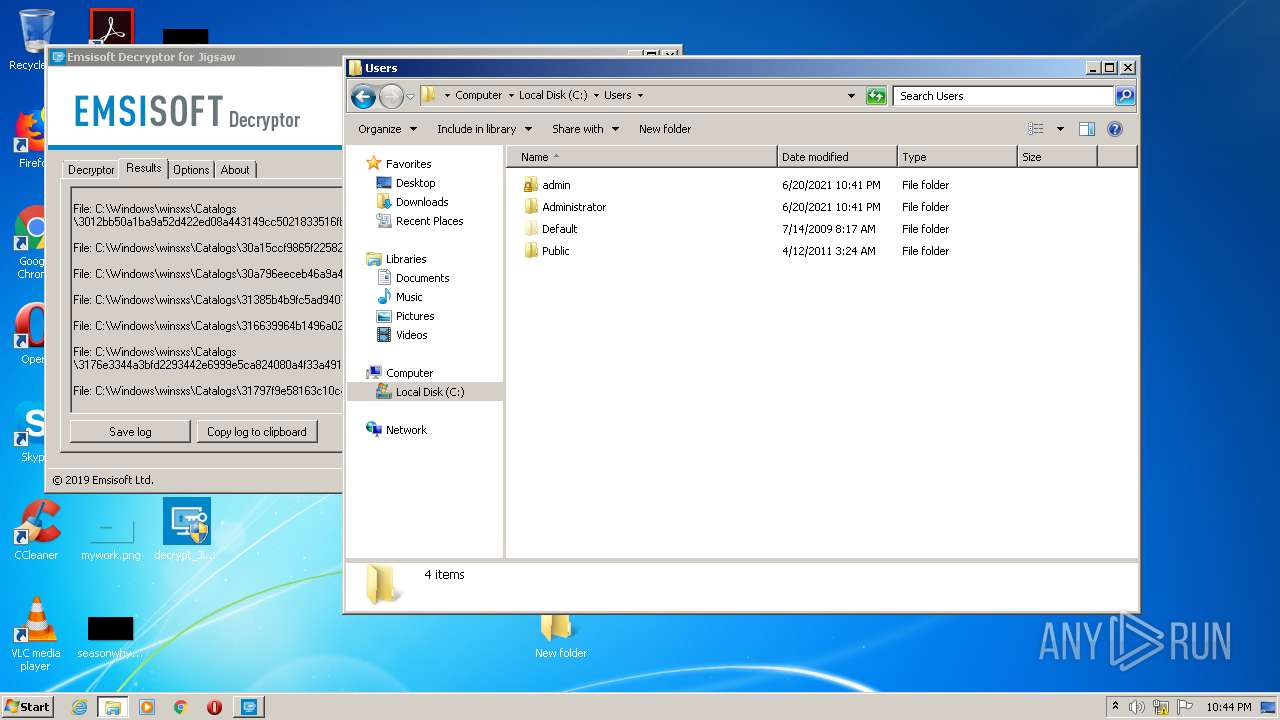
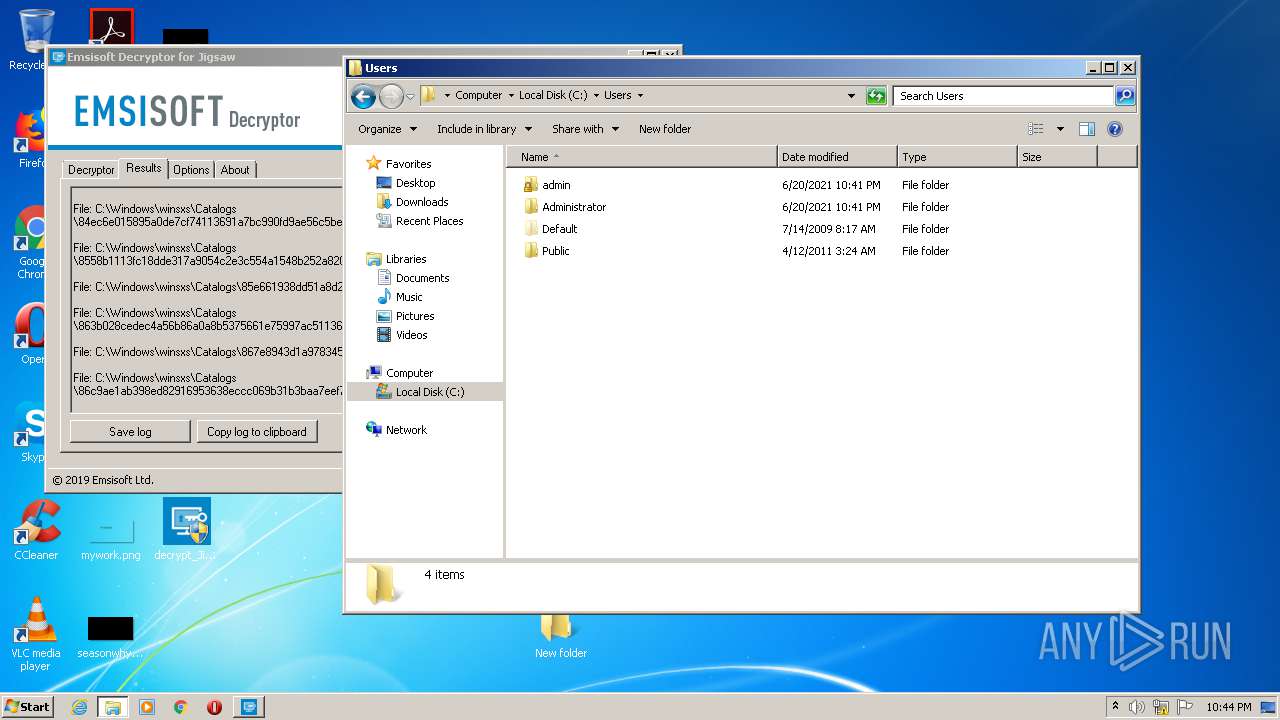
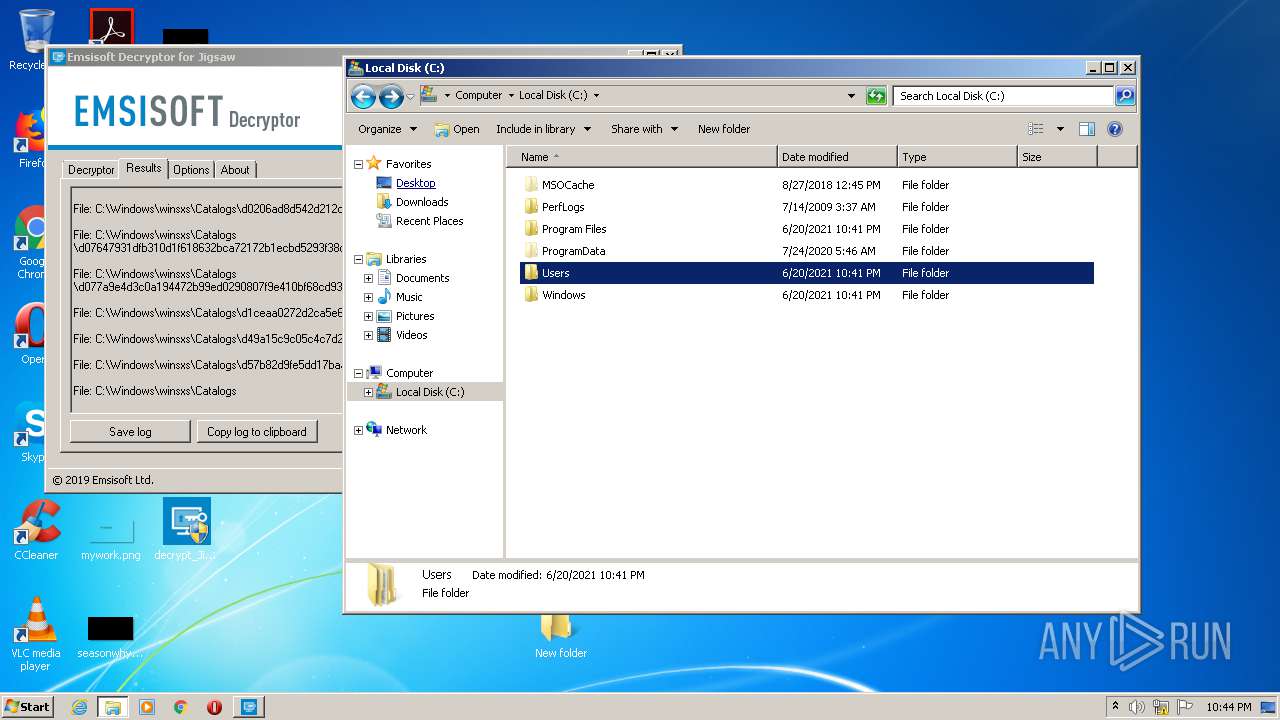
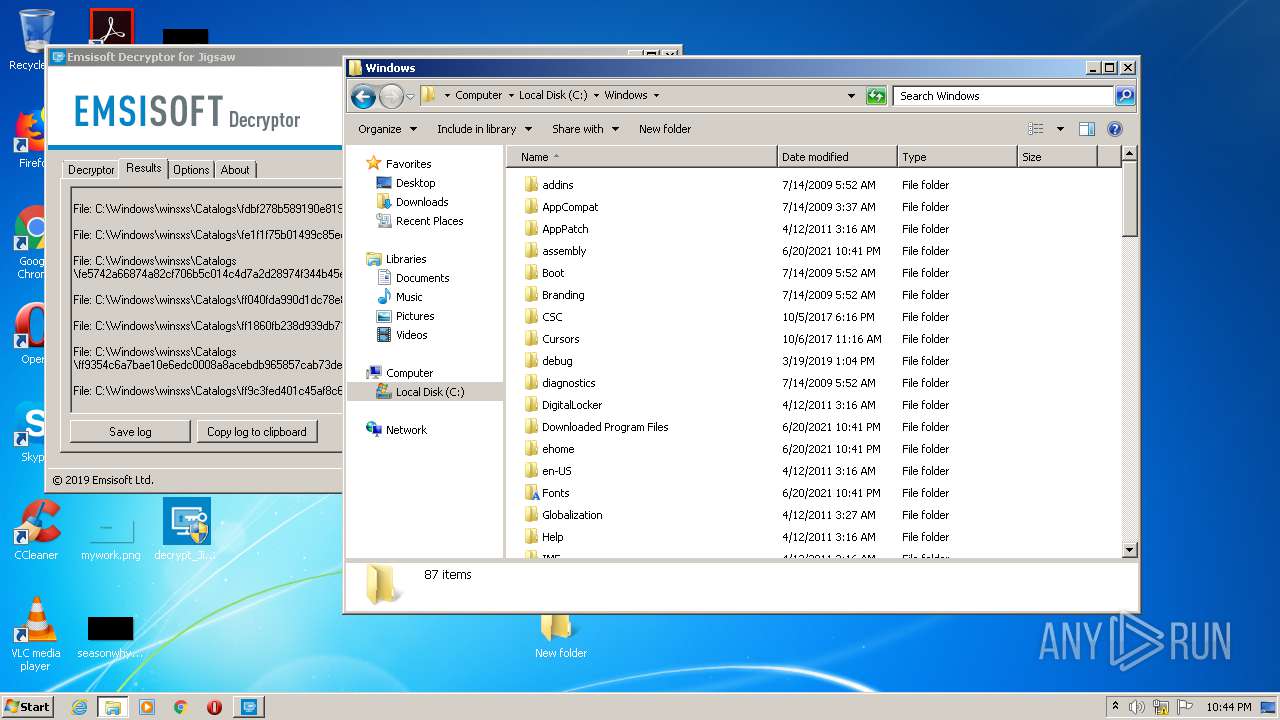
Creates files in the user directory
- decrypt_Jigsaw.exe (PID: 1044)
- decrypt_Jigsaw.exe (PID: 3360)
Creates files in the program directory
- decrypt_Jigsaw.exe (PID: 1044)
- decrypt_Jigsaw.exe (PID: 3360)
Drops a file with too old compile date
- decrypt_Jigsaw.exe (PID: 3360)
Drops a file with a compile date too recent
- decrypt_Jigsaw.exe (PID: 3360)
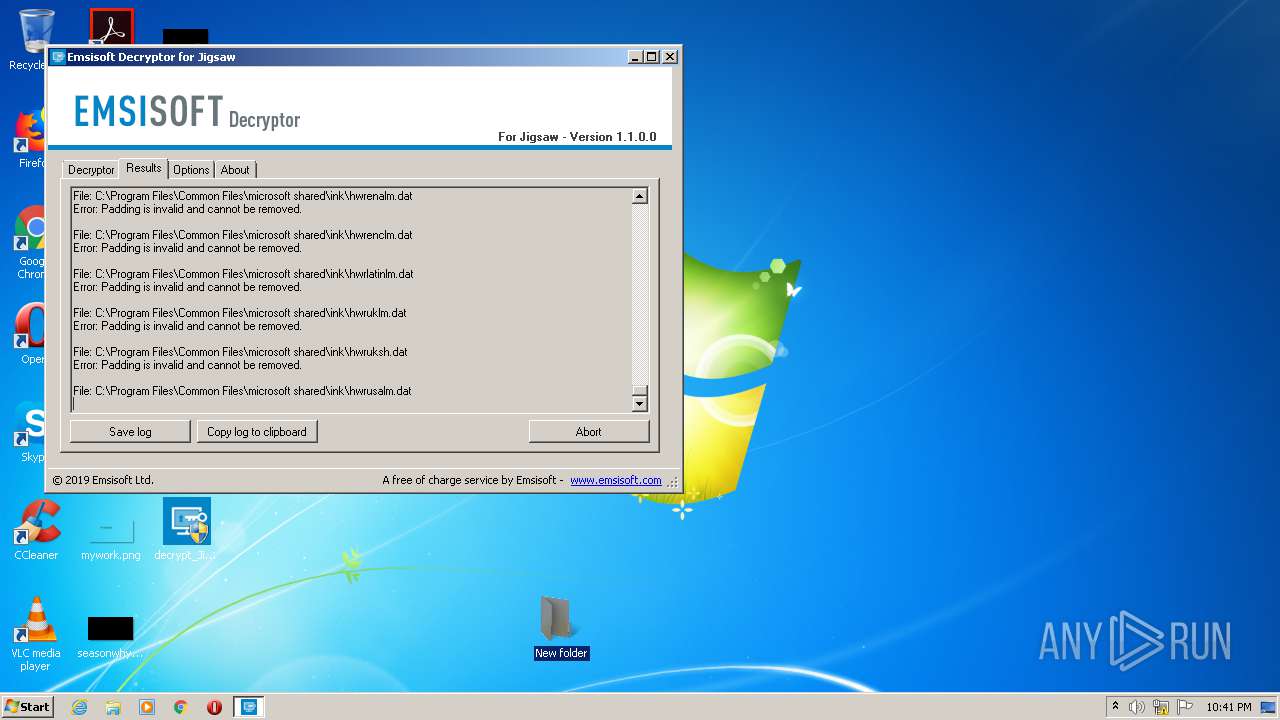
Modifies files in Chrome extension folder
- chrome.exe (PID: 3448)
Creates files in the Windows directory
- decrypt_Jigsaw.exe (PID: 3360)
Removes files from Windows directory
- decrypt_Jigsaw.exe (PID: 3360)
INFO
Dropped object may contain Bitcoin addresses
- decrypt_Jigsaw.exe (PID: 1044)
- decrypt_Jigsaw.exe (PID: 3360)
Reads settings of System Certificates
- decrypt_Jigsaw.exe (PID: 1044)
- chrome.exe (PID: 2420)
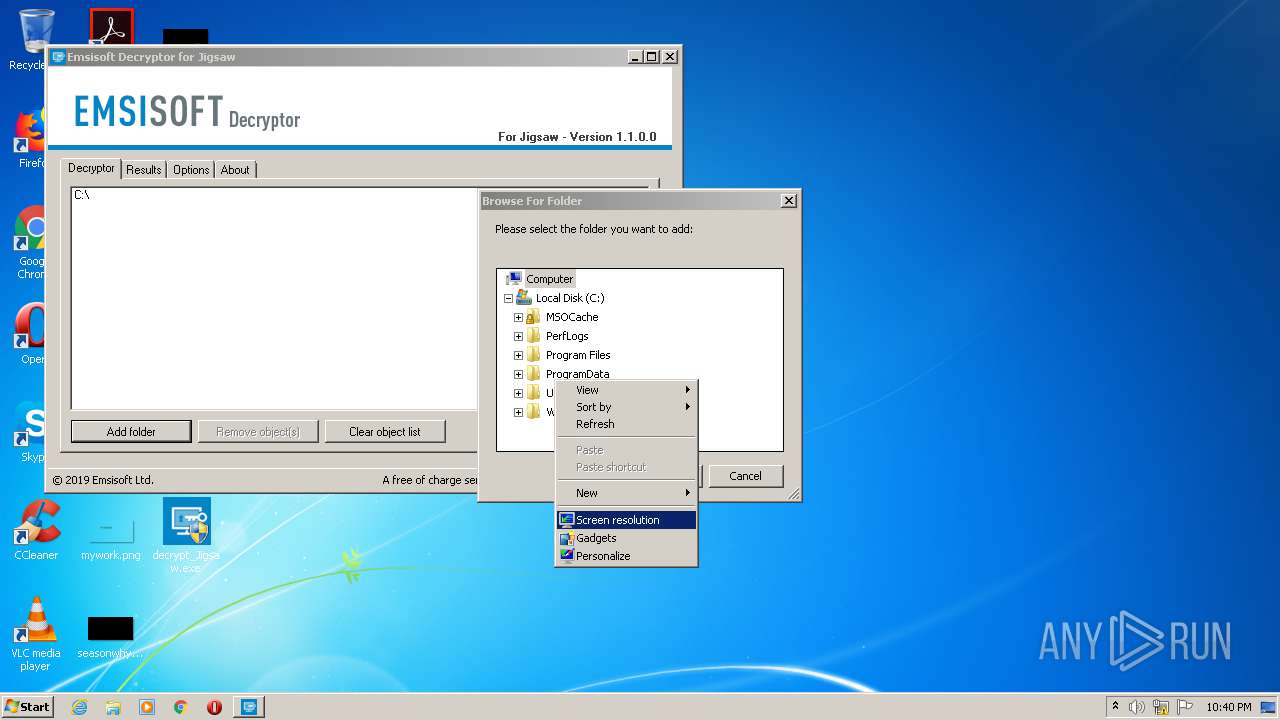
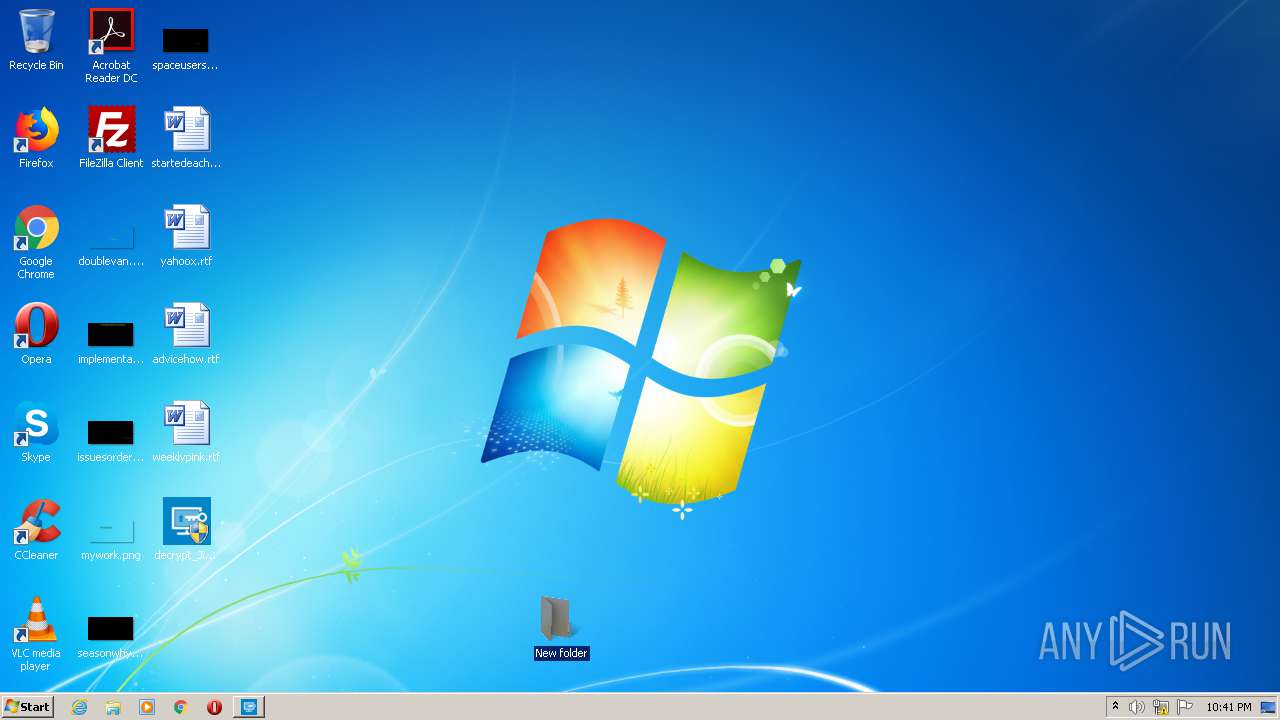
Manual execution by user
- decrypt_Jigsaw.exe (PID: 1452)
- decrypt_Jigsaw.exe (PID: 3360)
- chrome.exe (PID: 3448)
- opera.exe (PID: 2104)
Application launched itself
- chrome.exe (PID: 3448)
Reads the hosts file
- chrome.exe (PID: 2420)
- chrome.exe (PID: 3448)
Creates files in the user directory
- opera.exe (PID: 2104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| AssemblyVersion: | 1.1.0.0 |
|---|---|
| ProductVersion: | 1.1.0.0 |
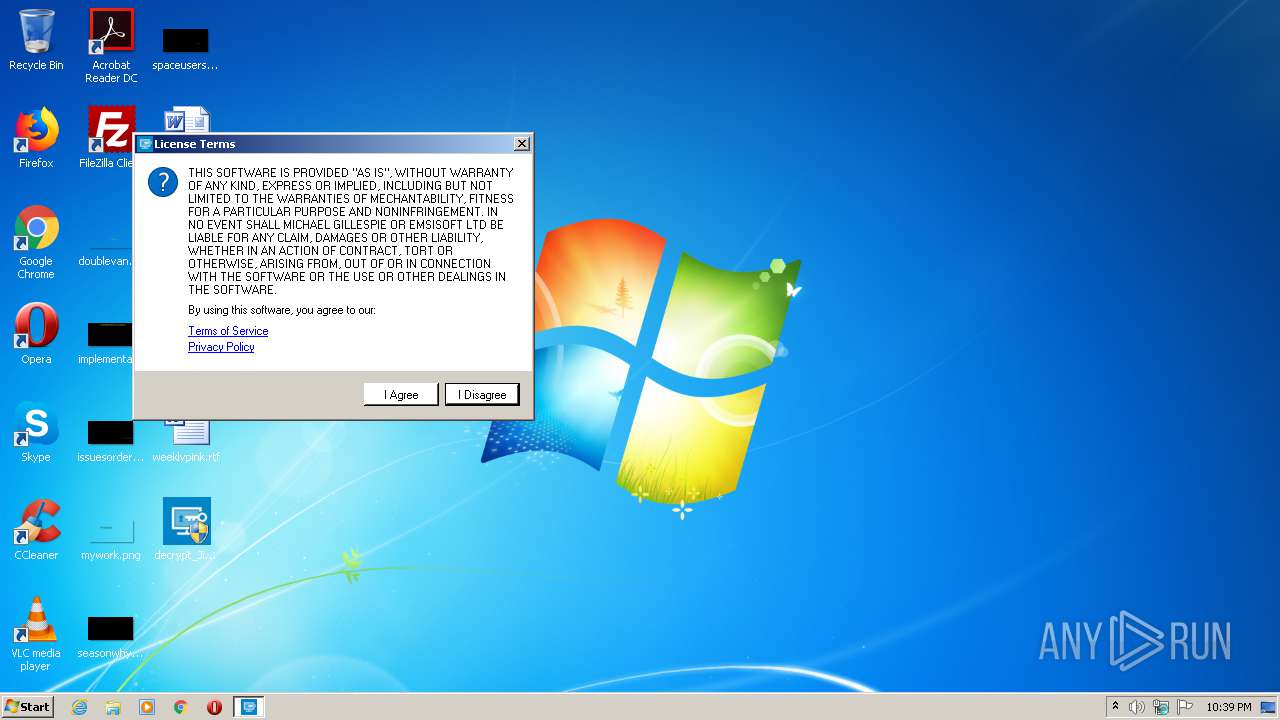
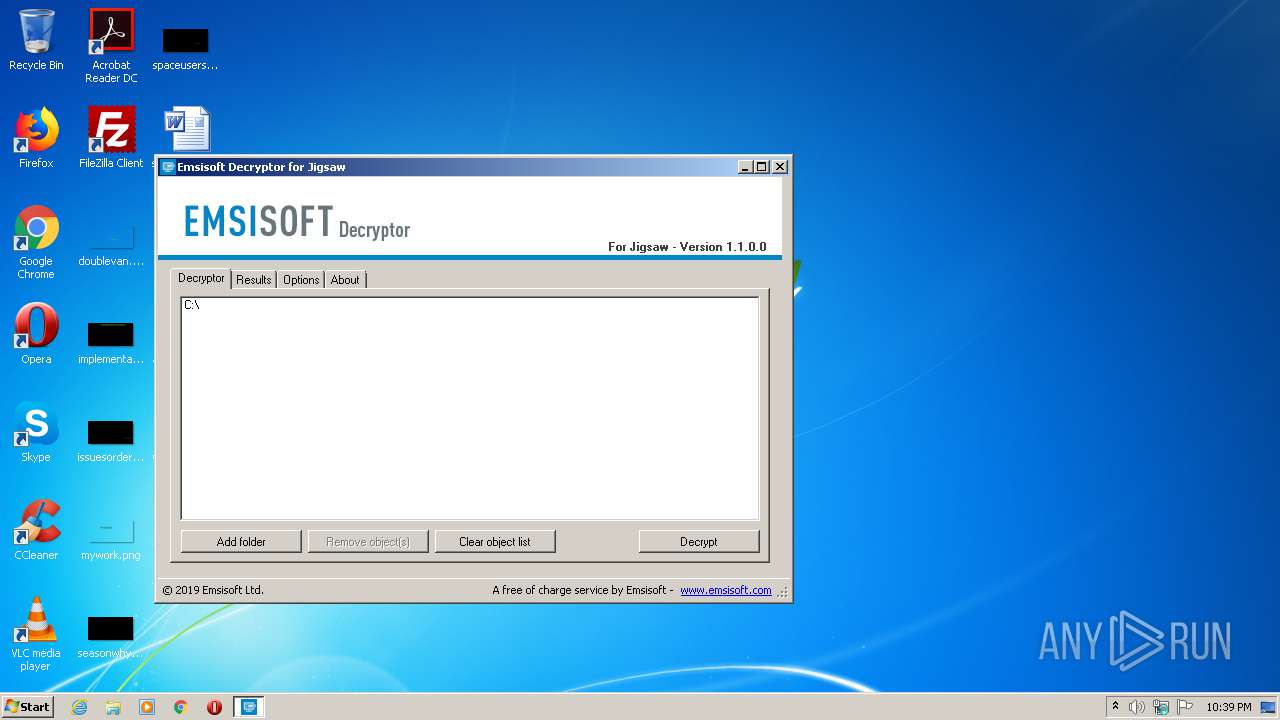
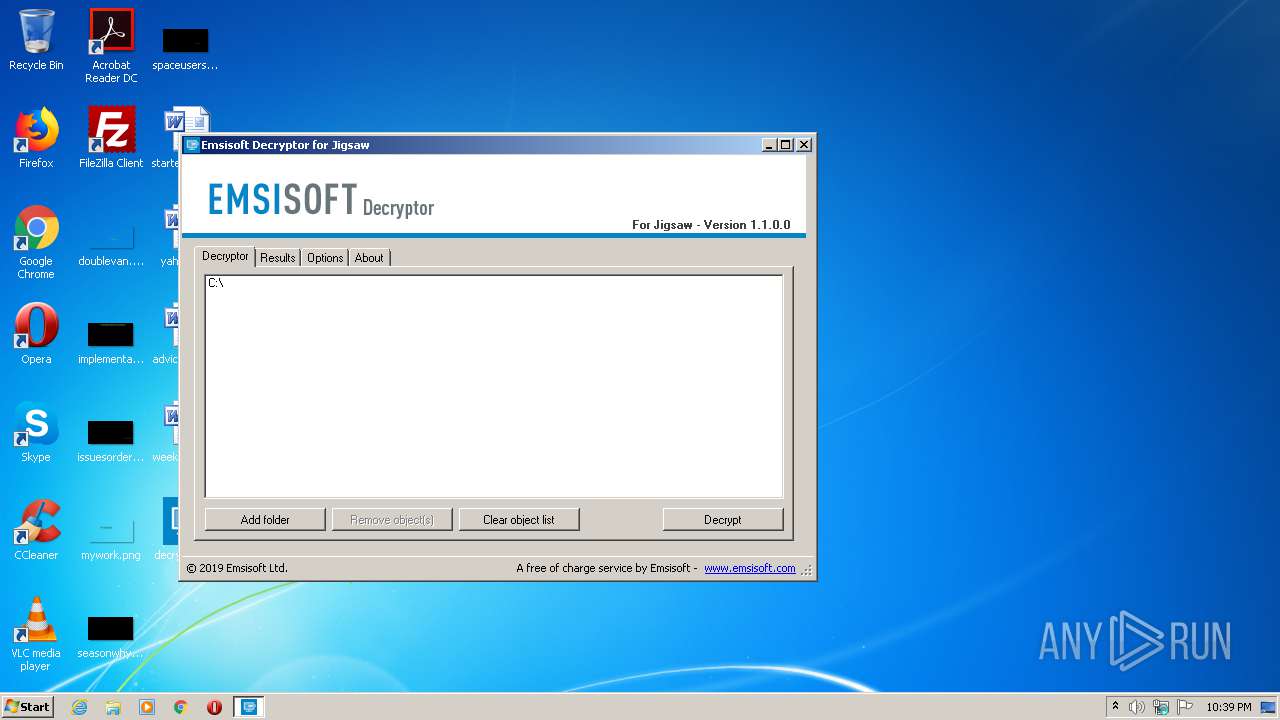
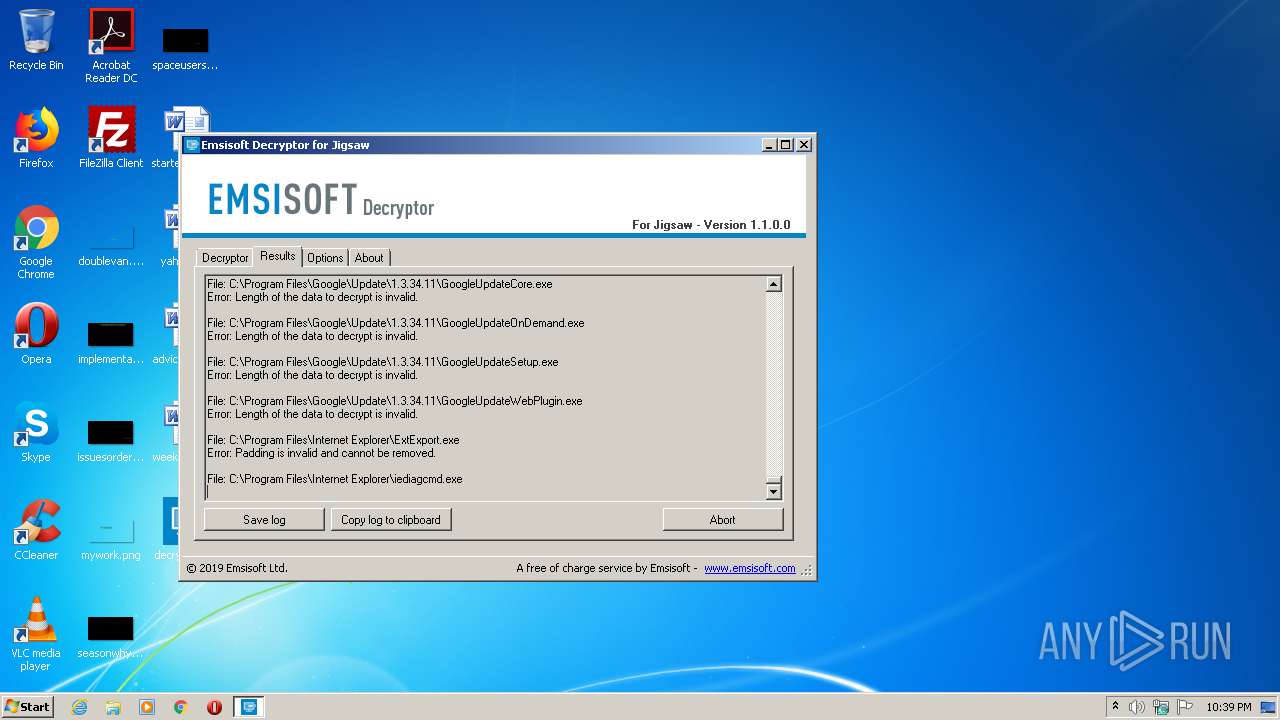
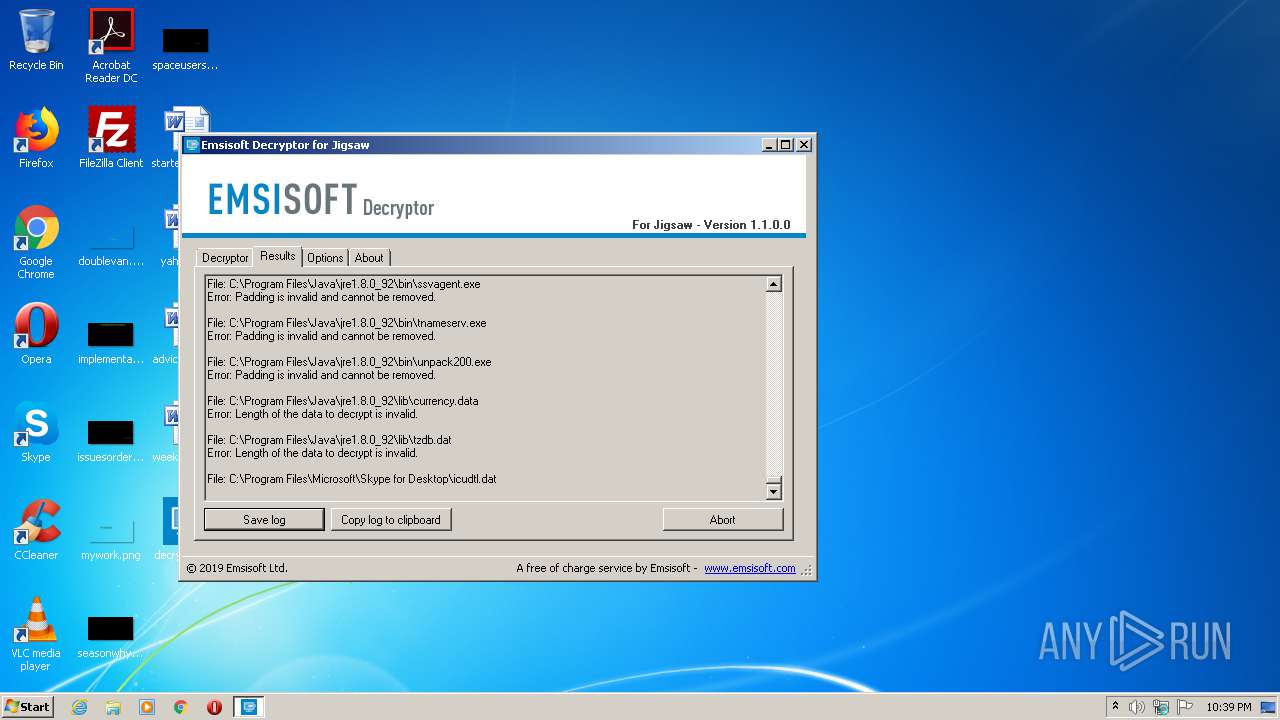
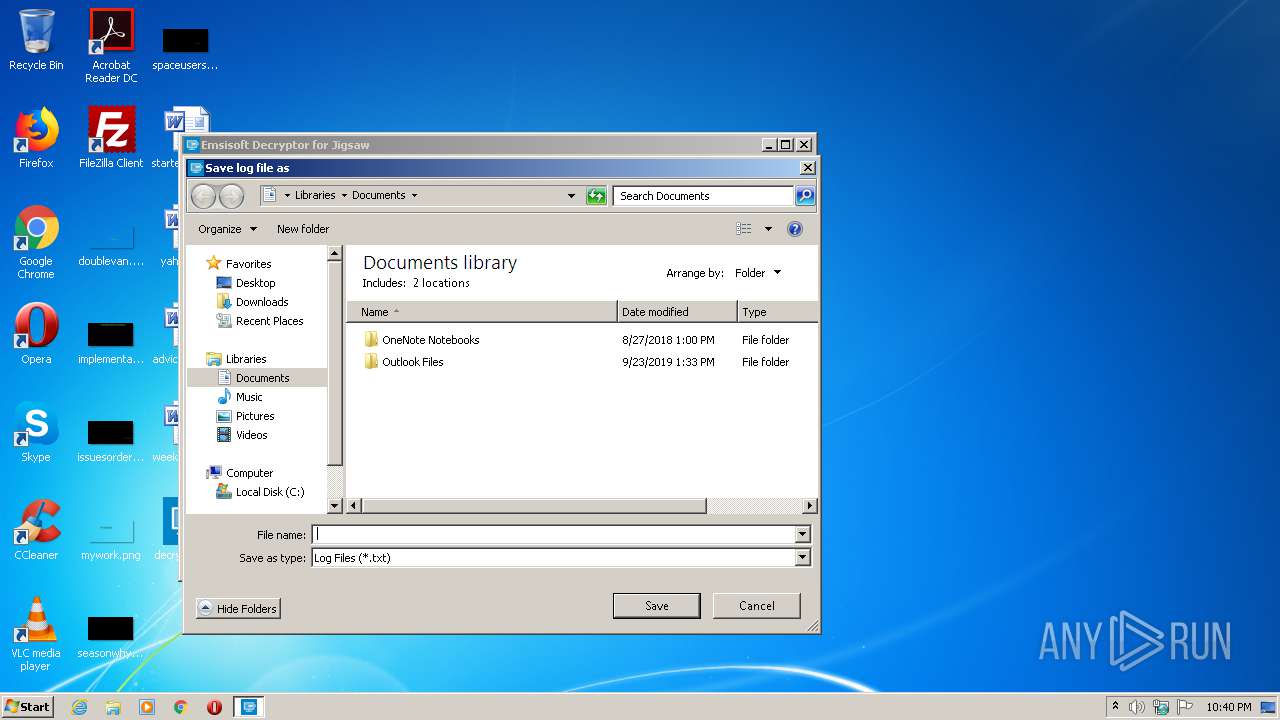
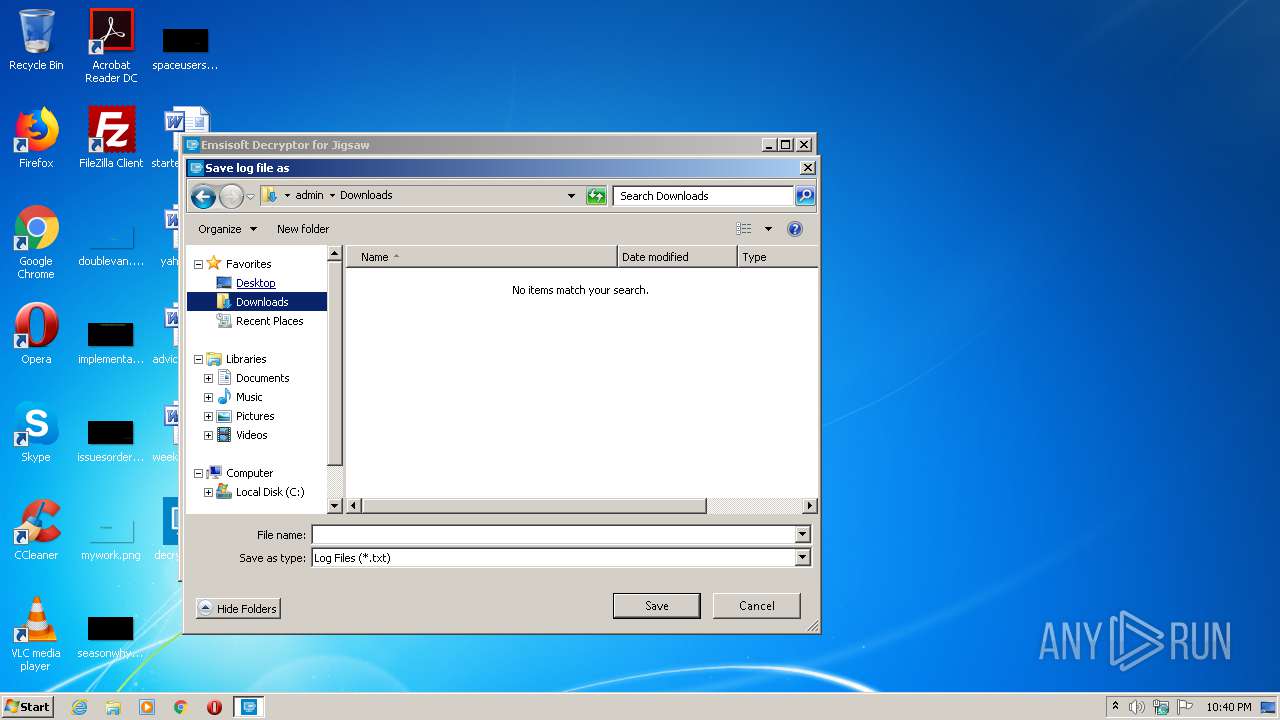
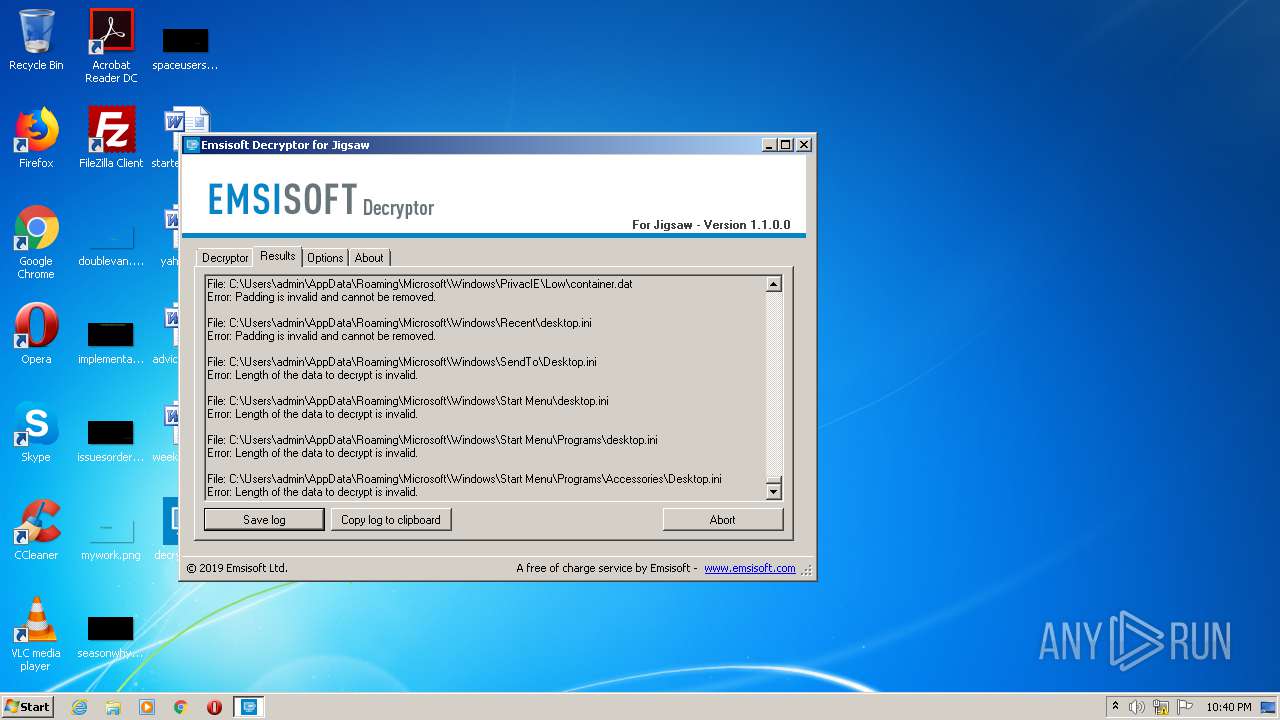
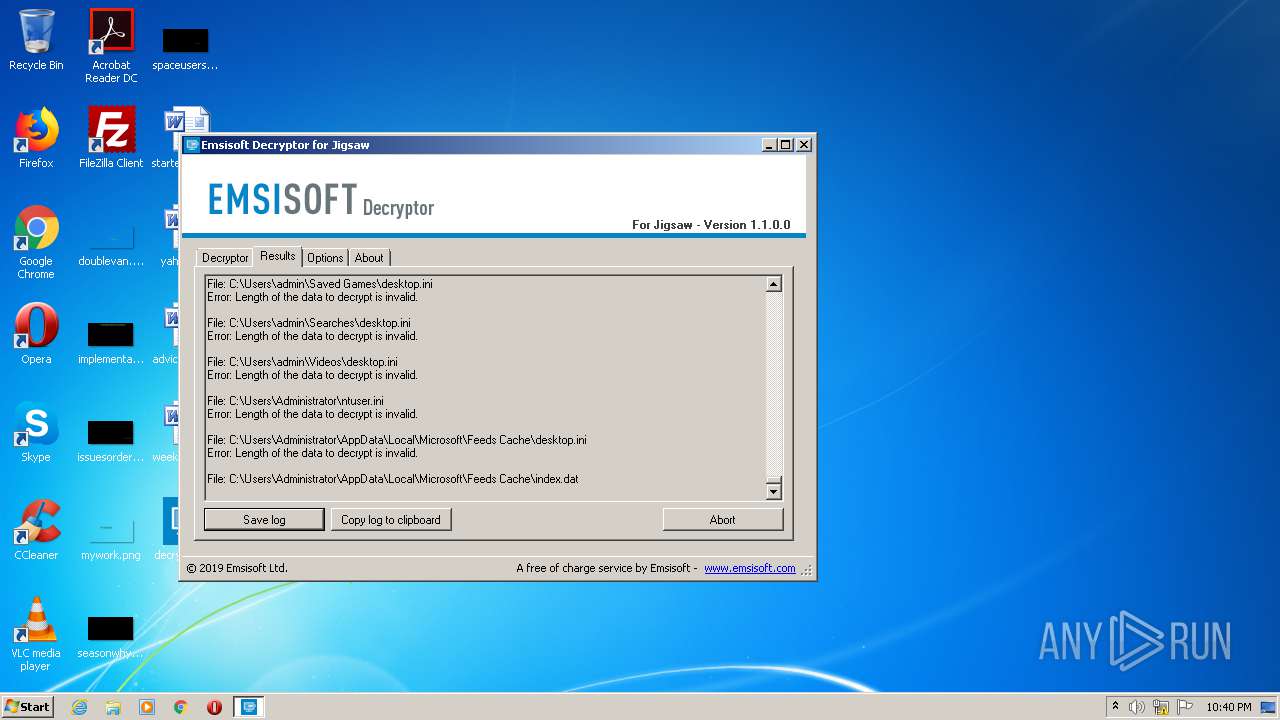
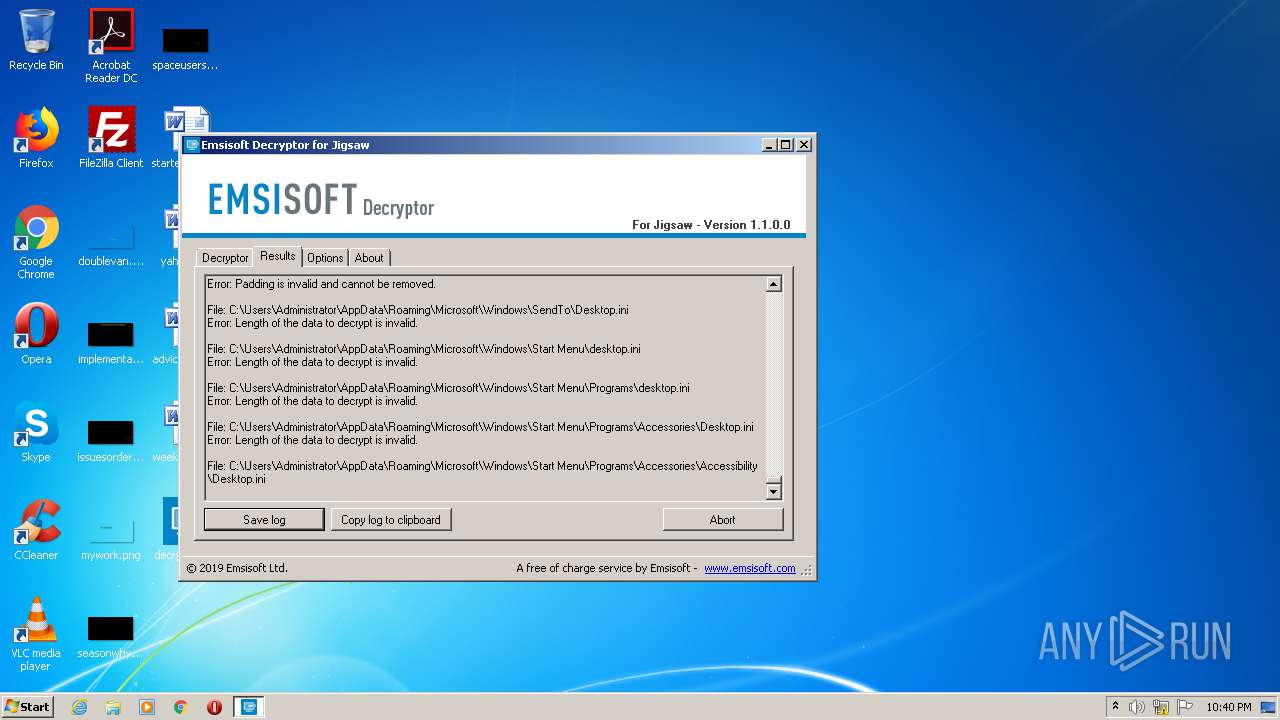
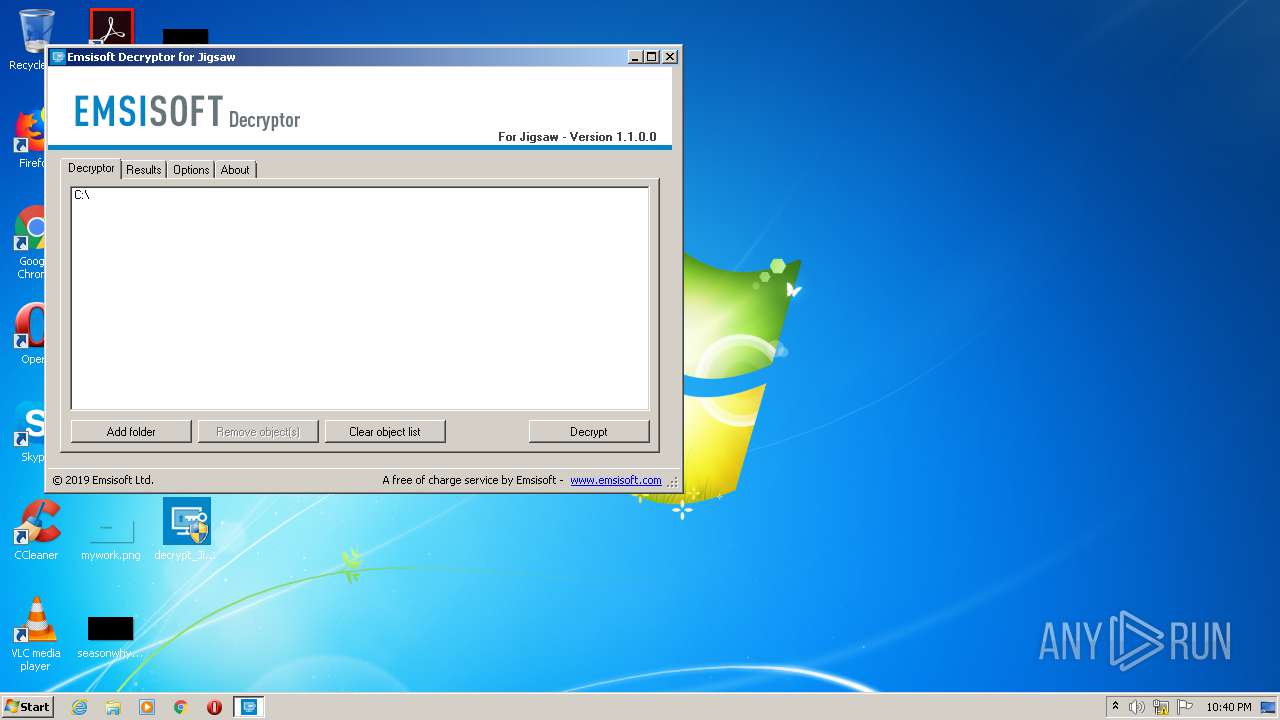
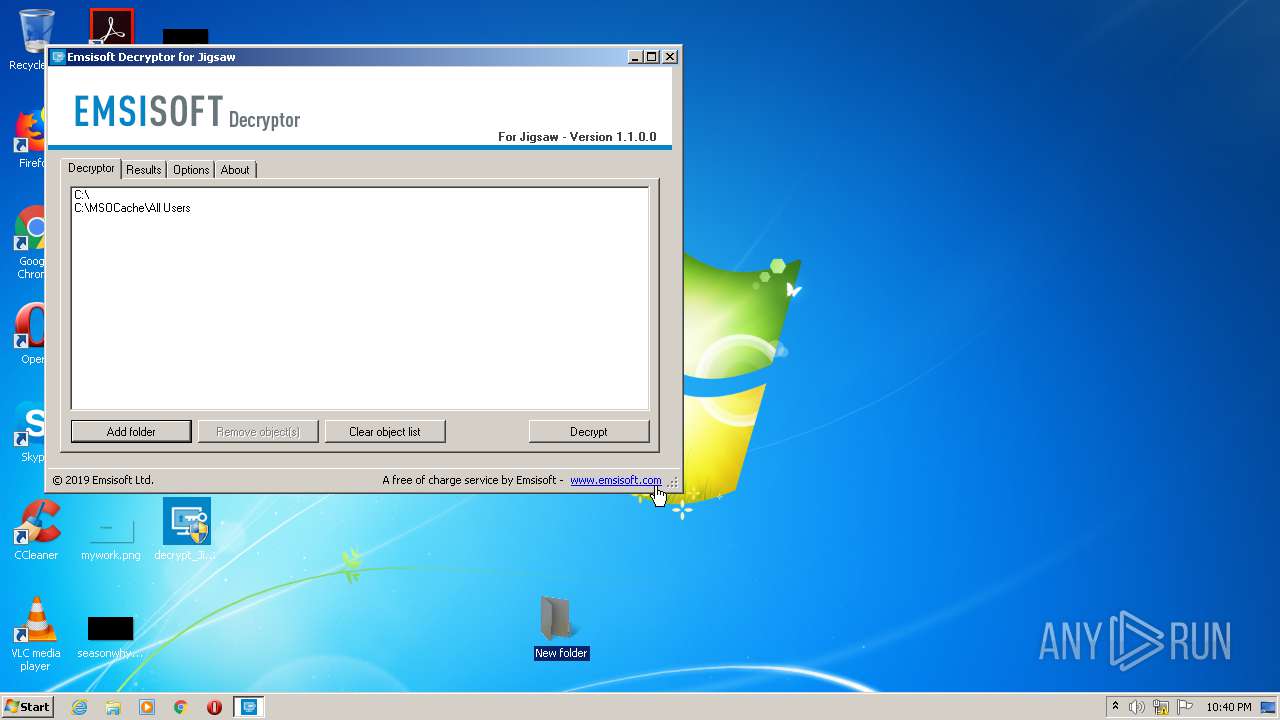
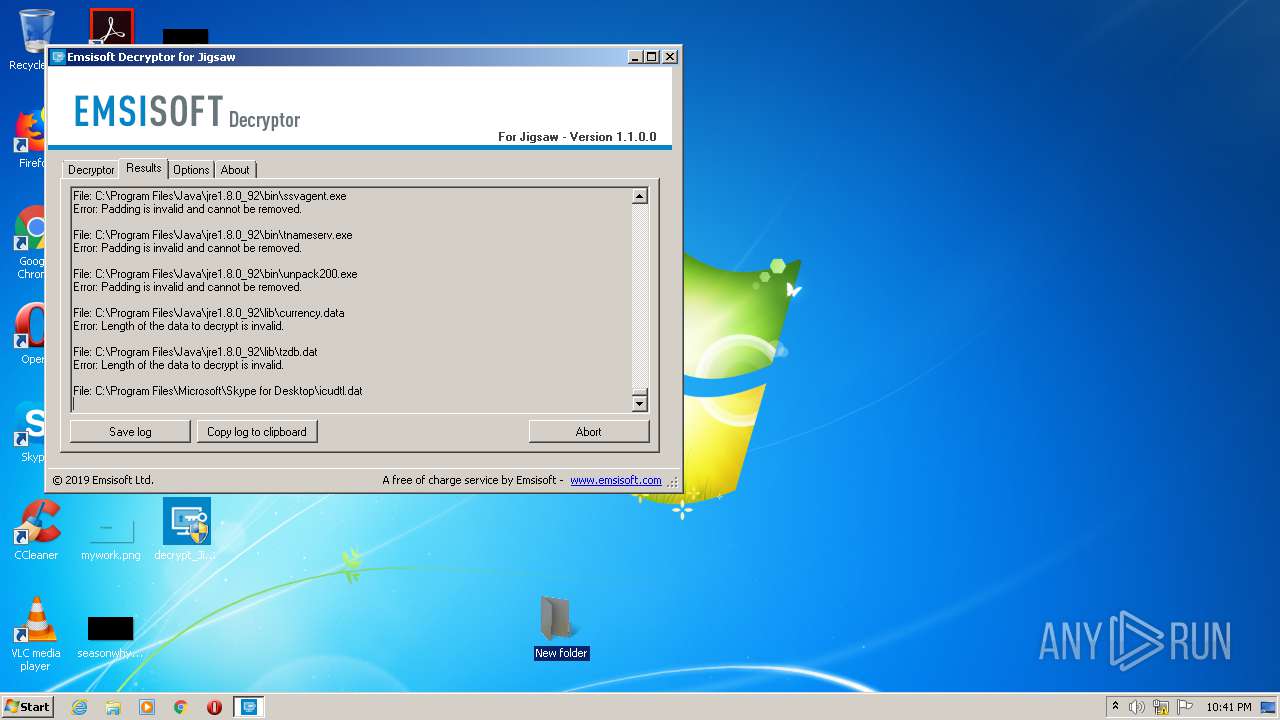
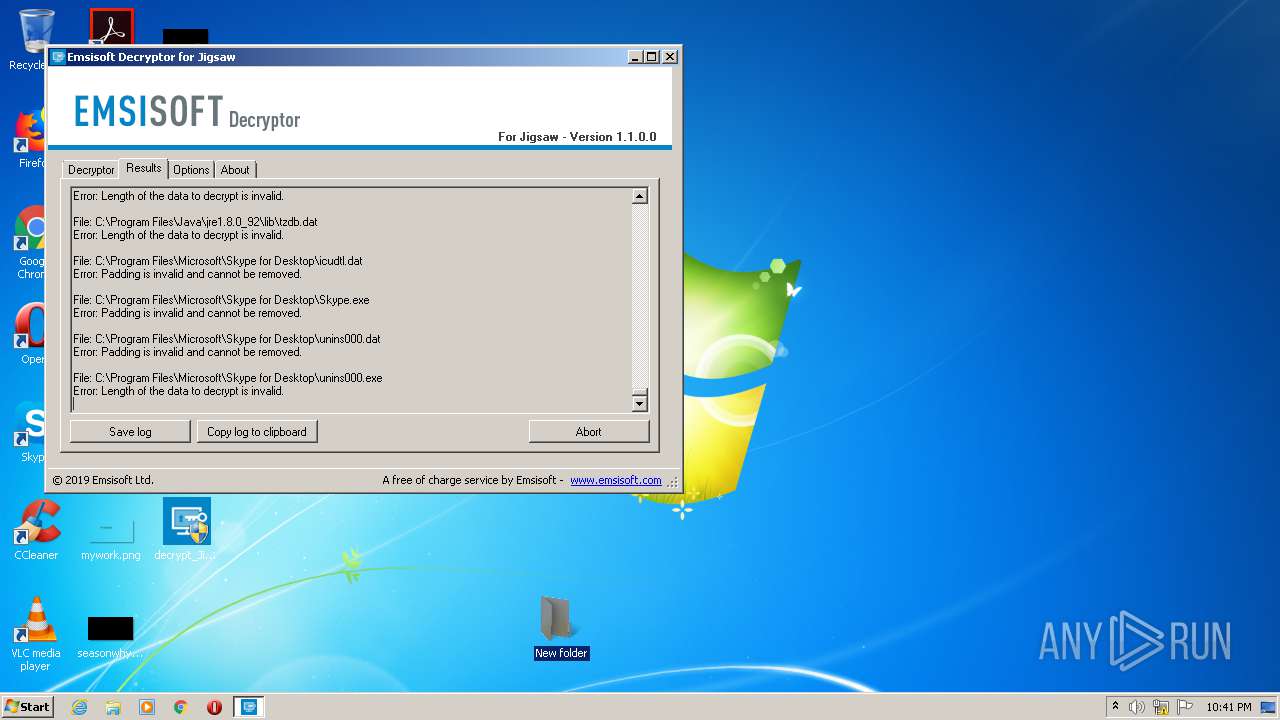
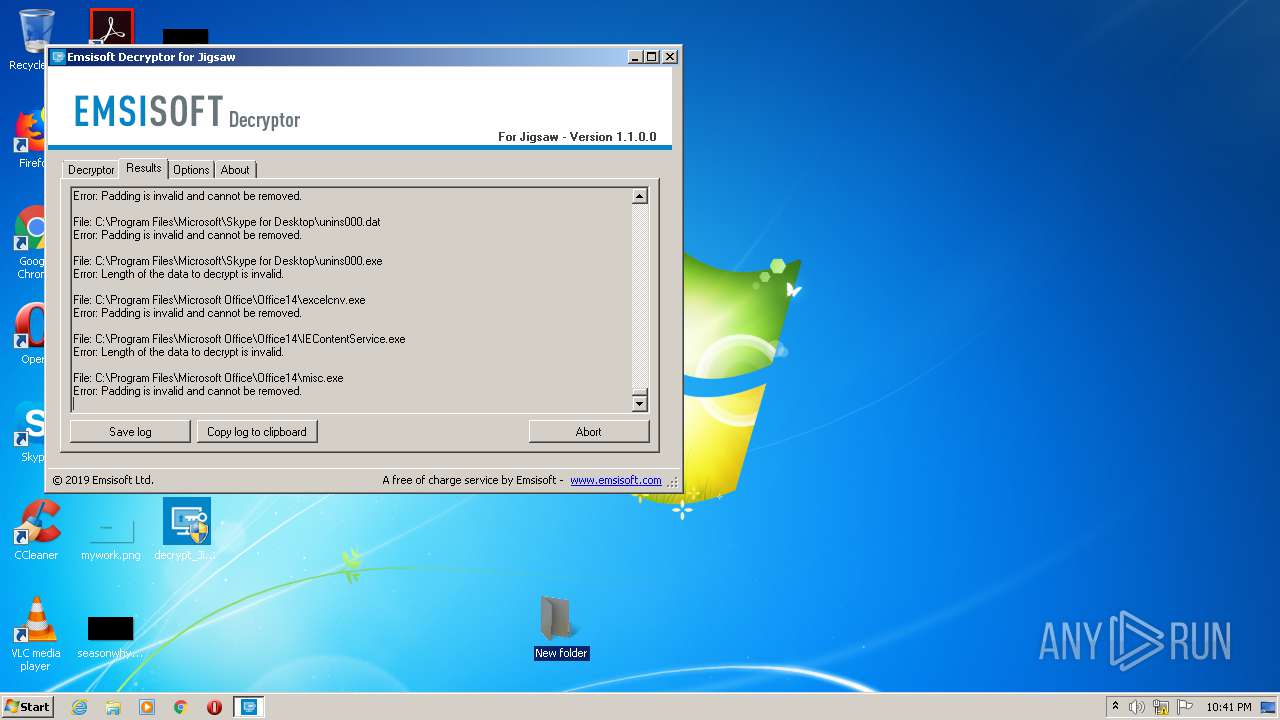
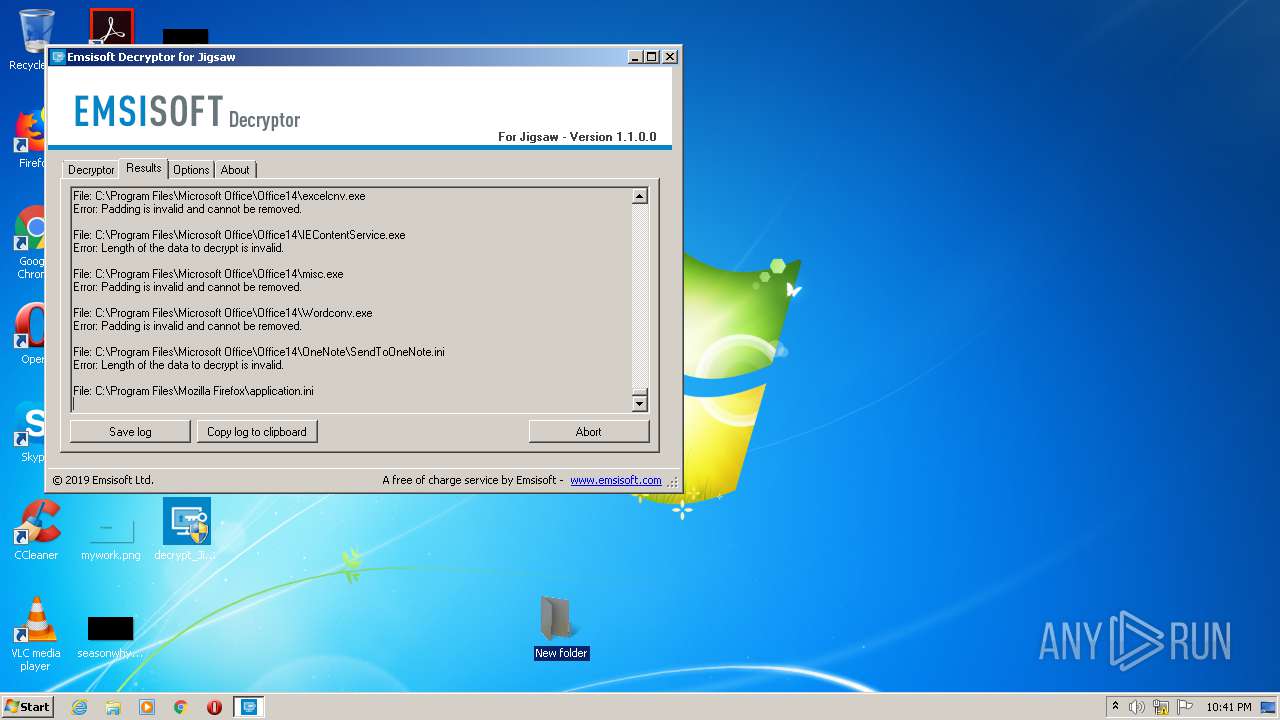
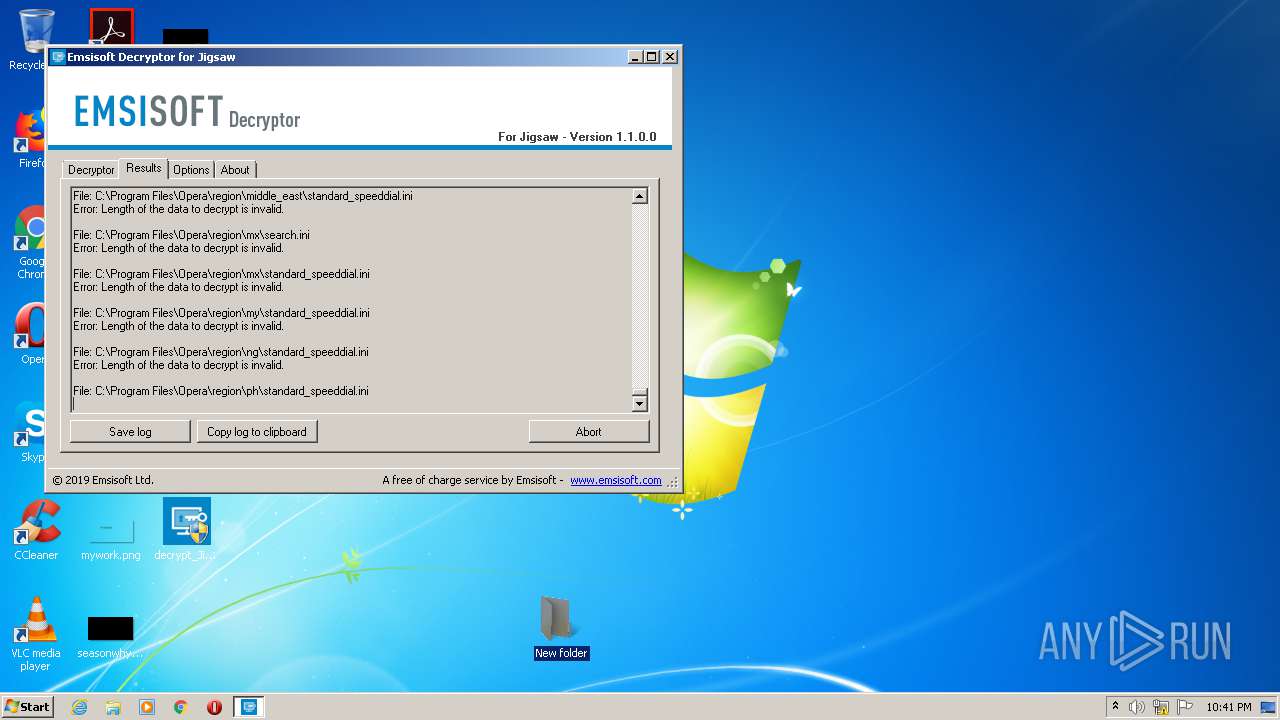
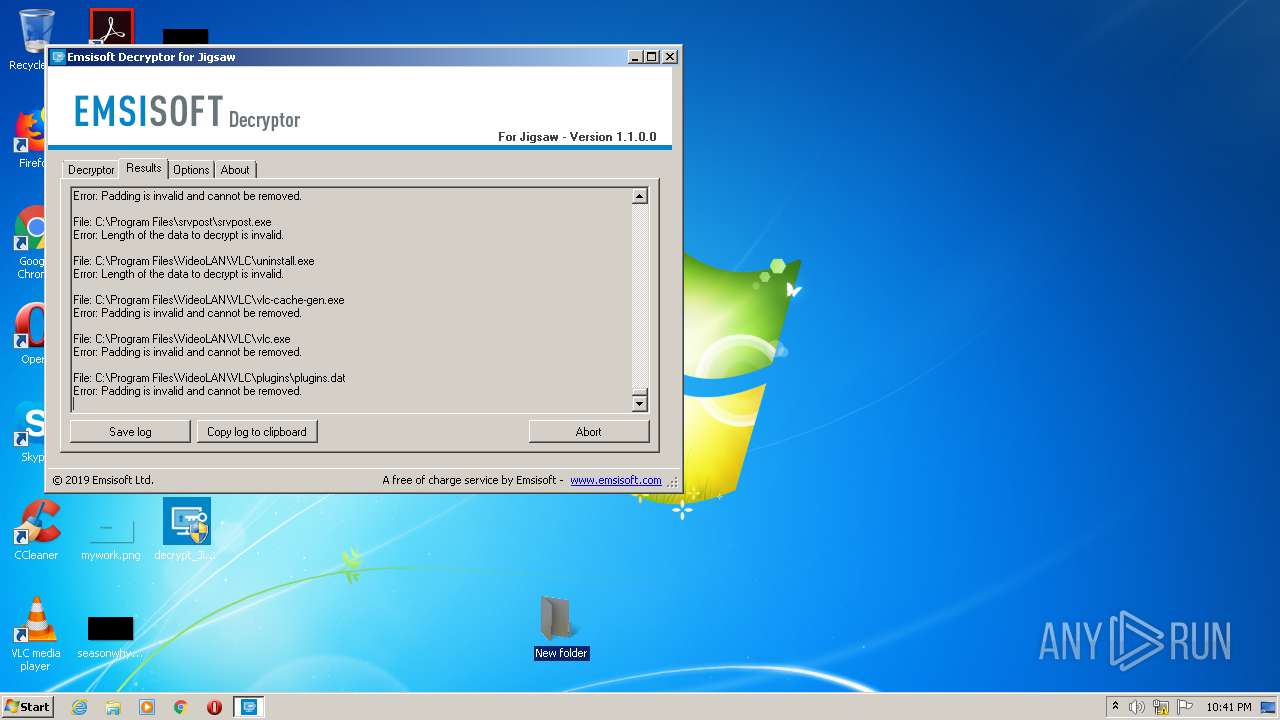
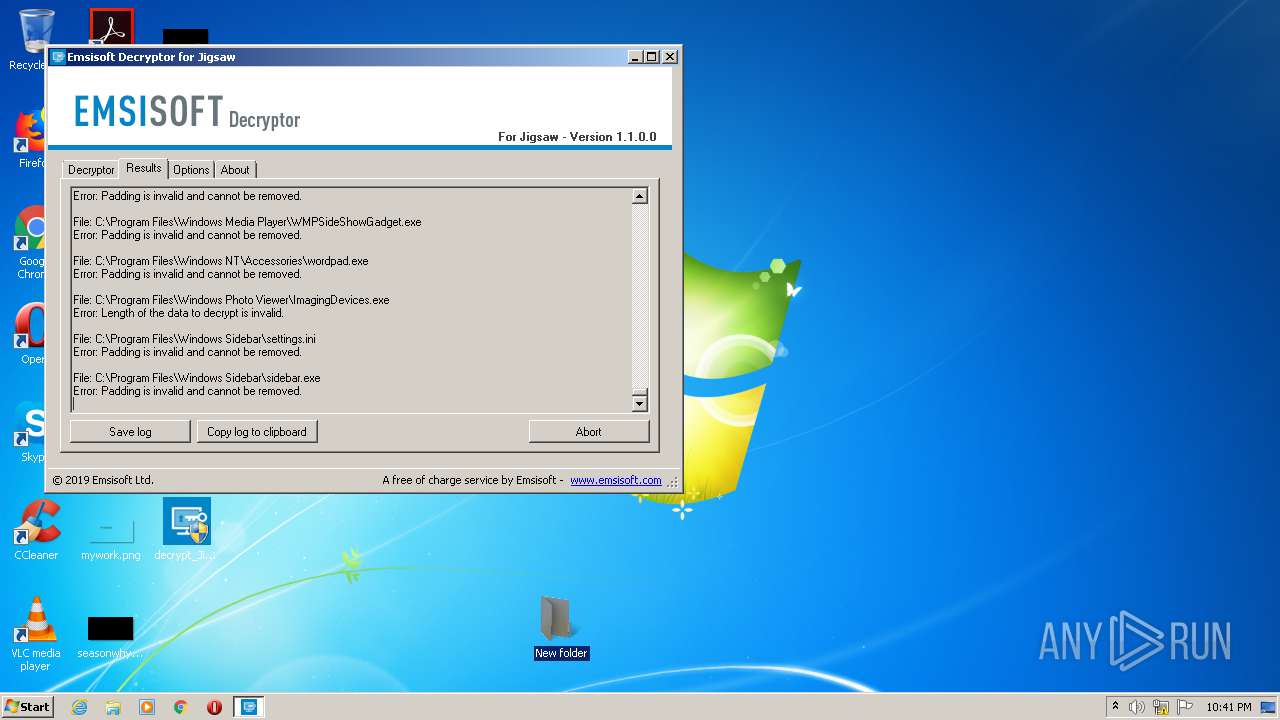
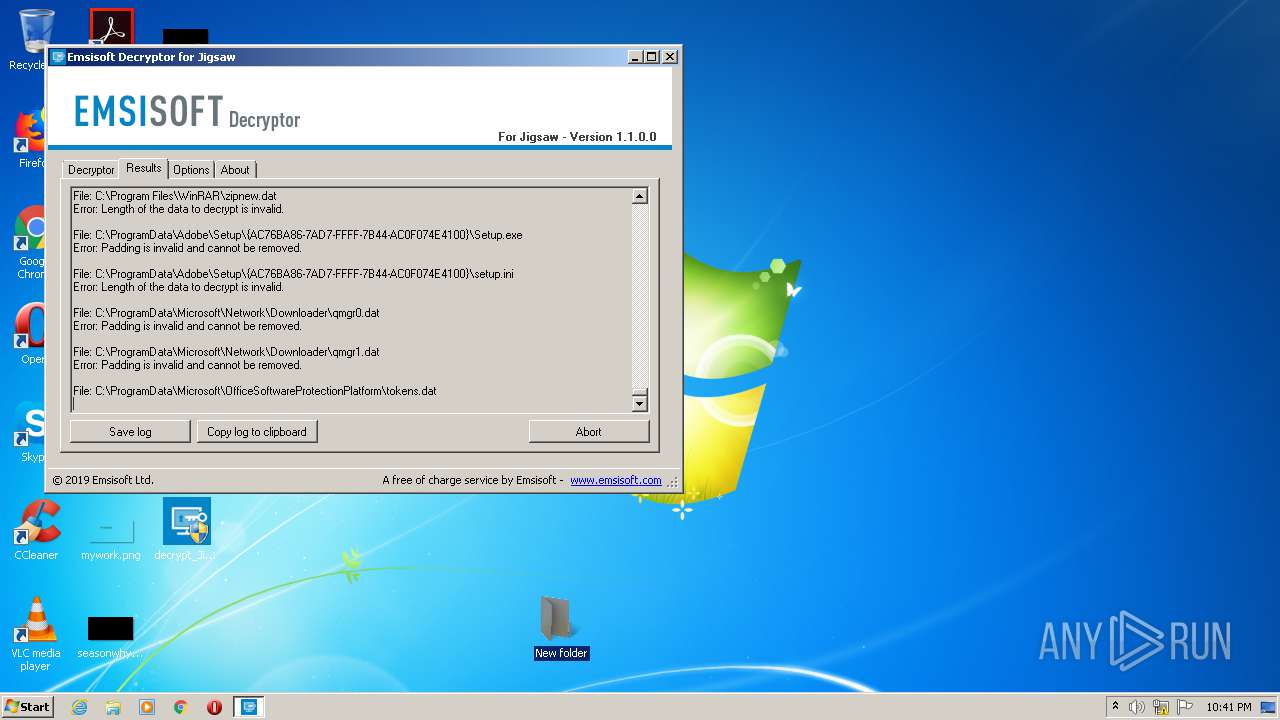
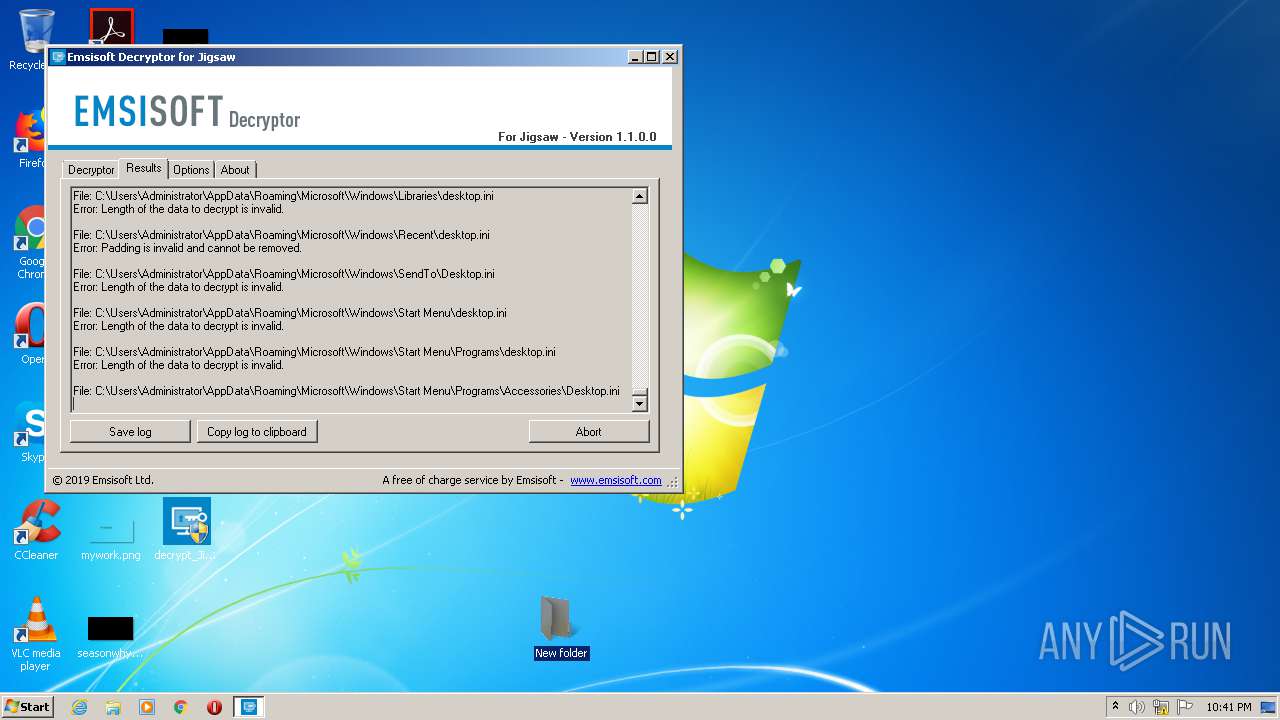
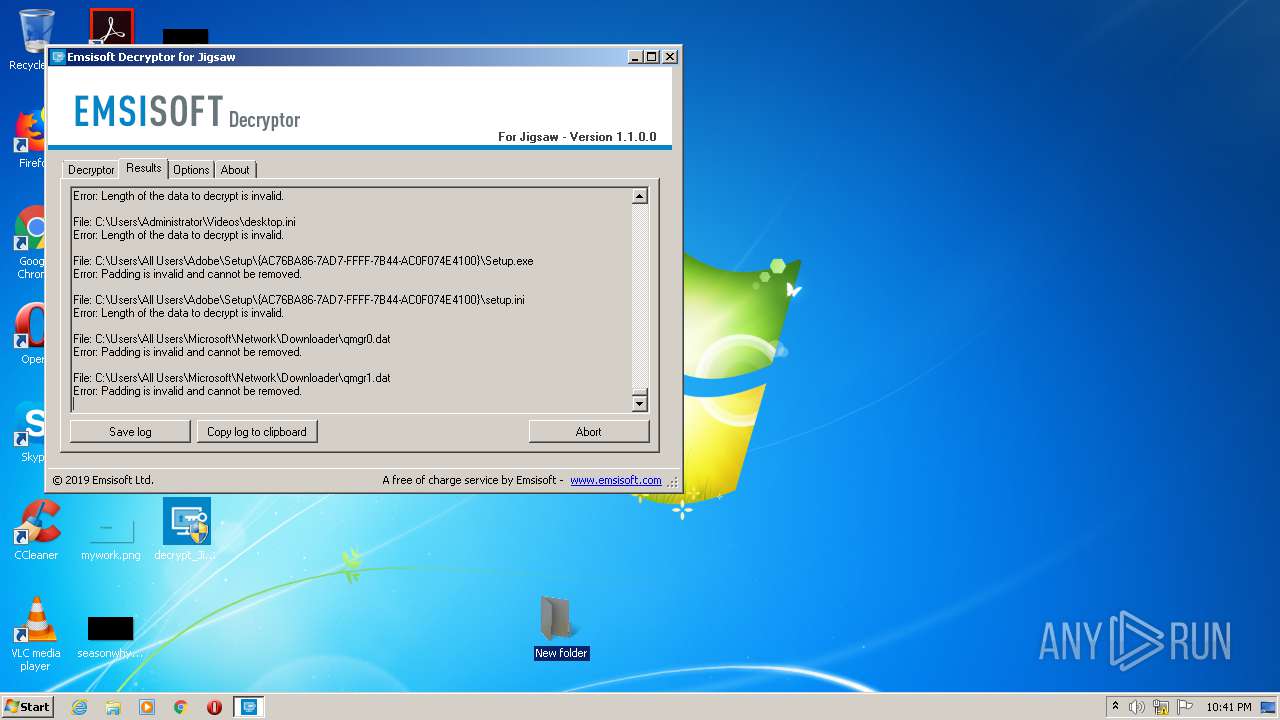
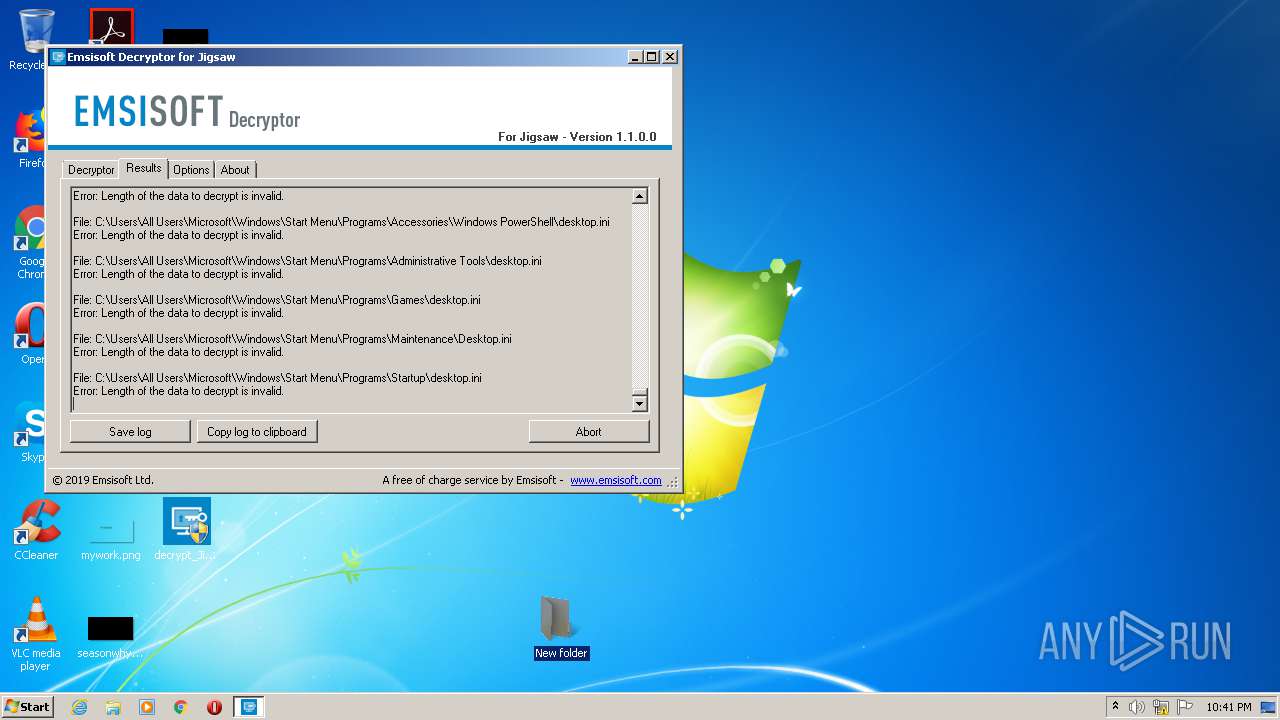
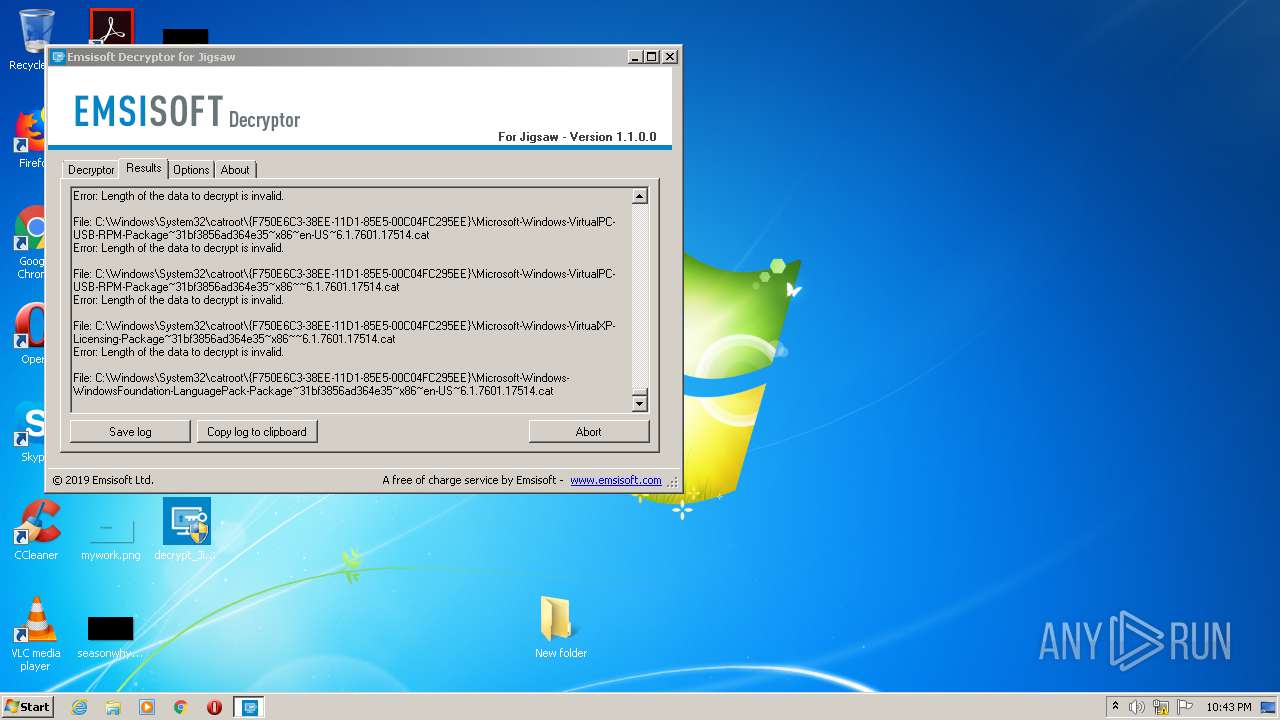
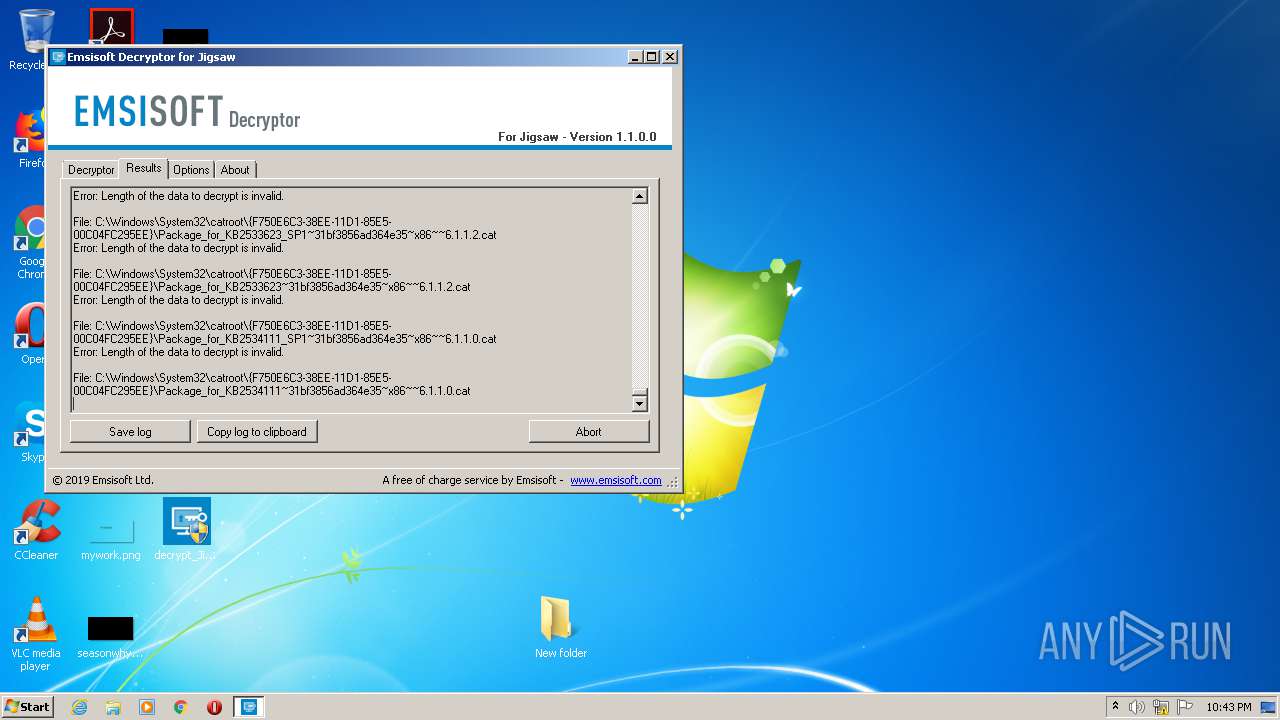
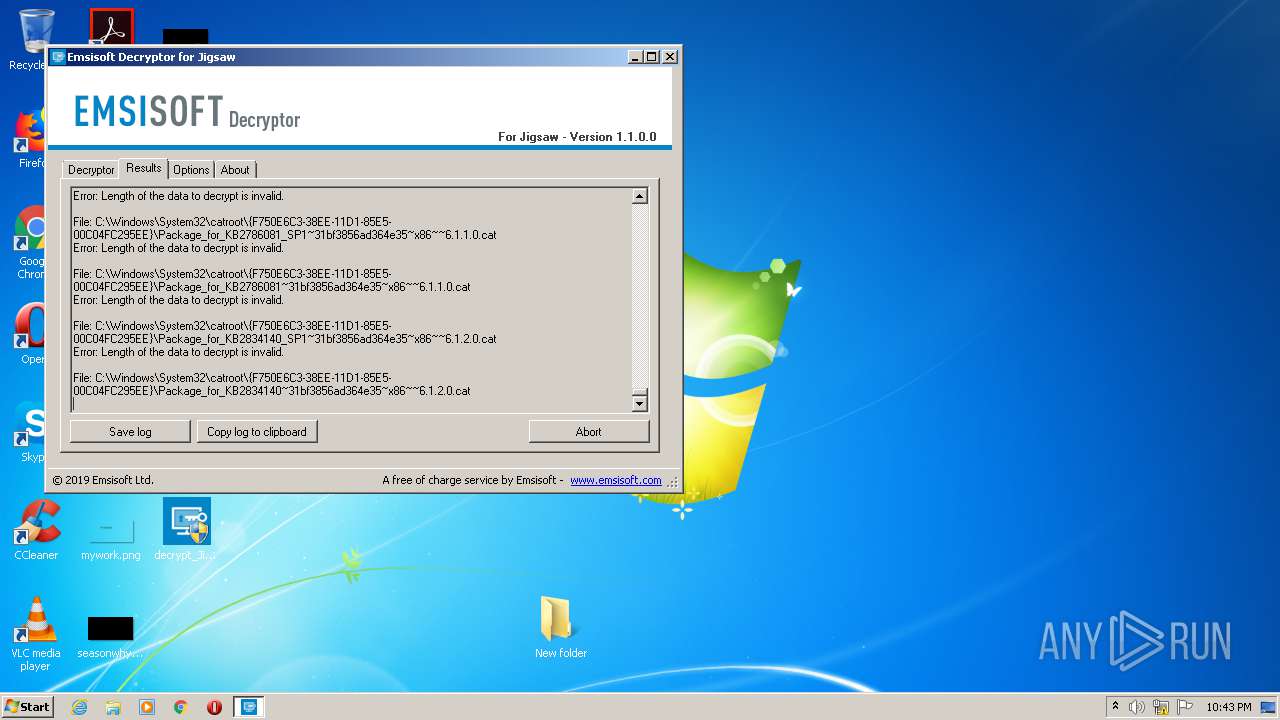
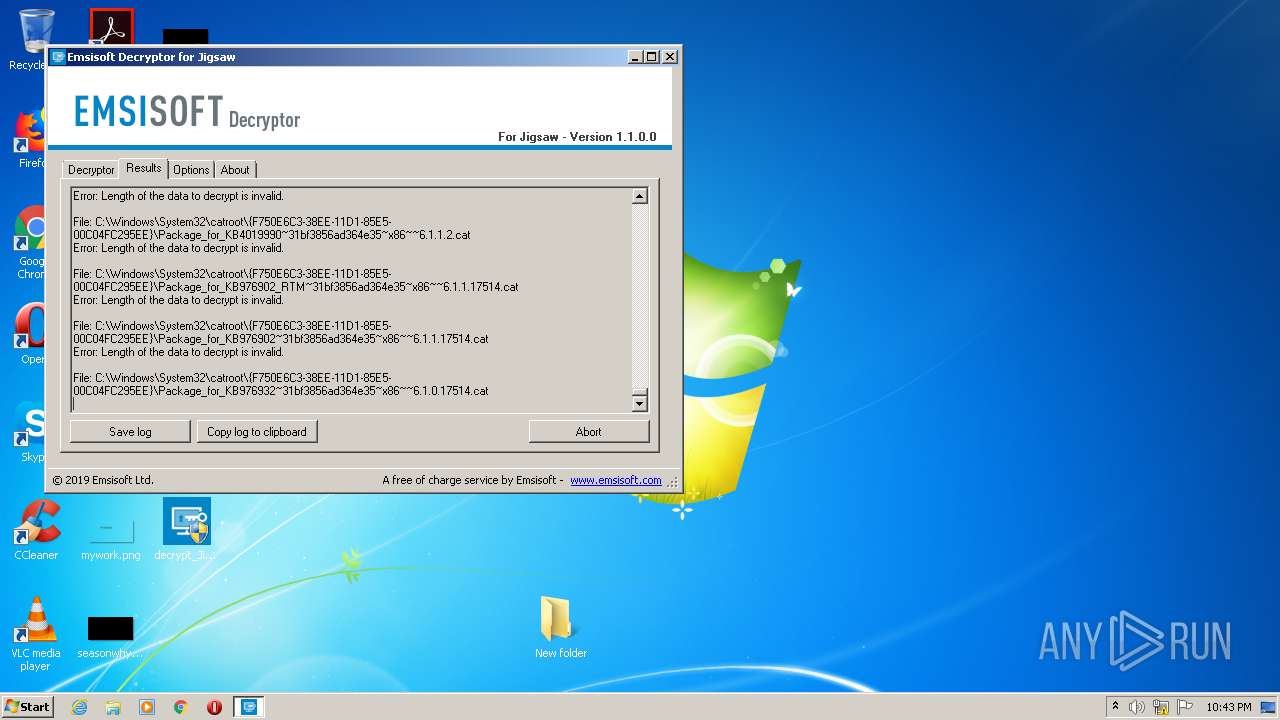
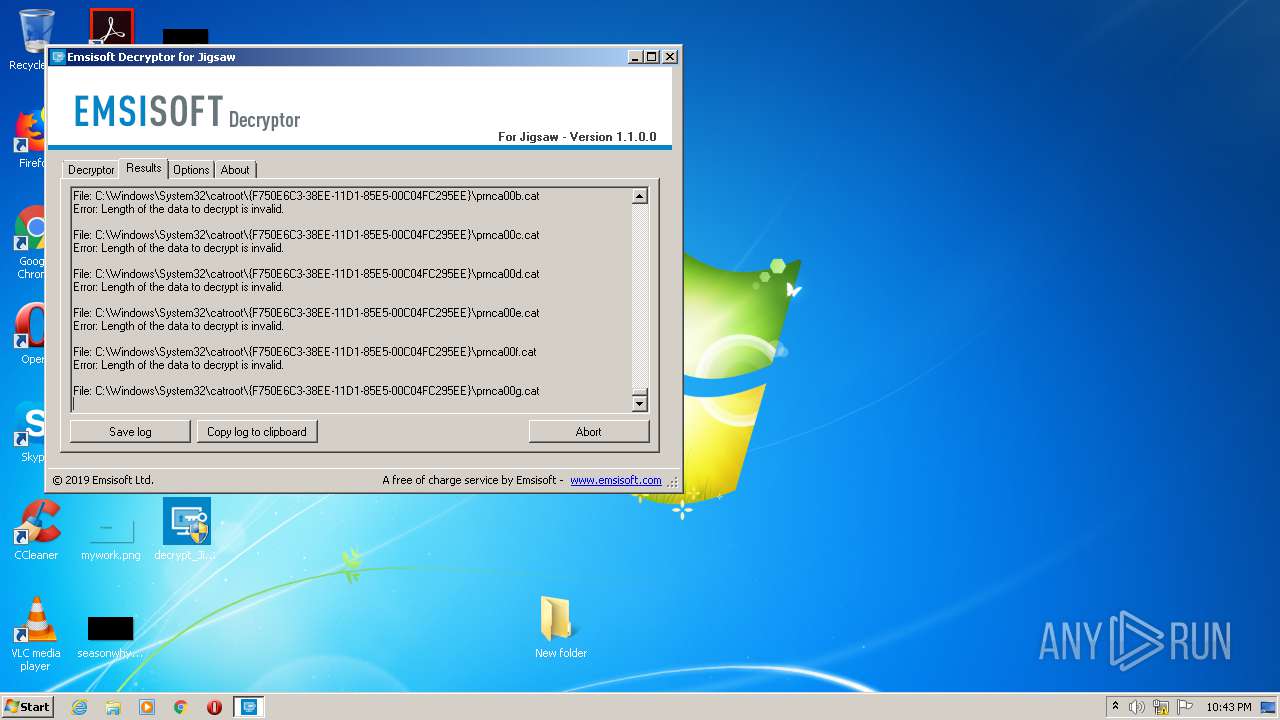
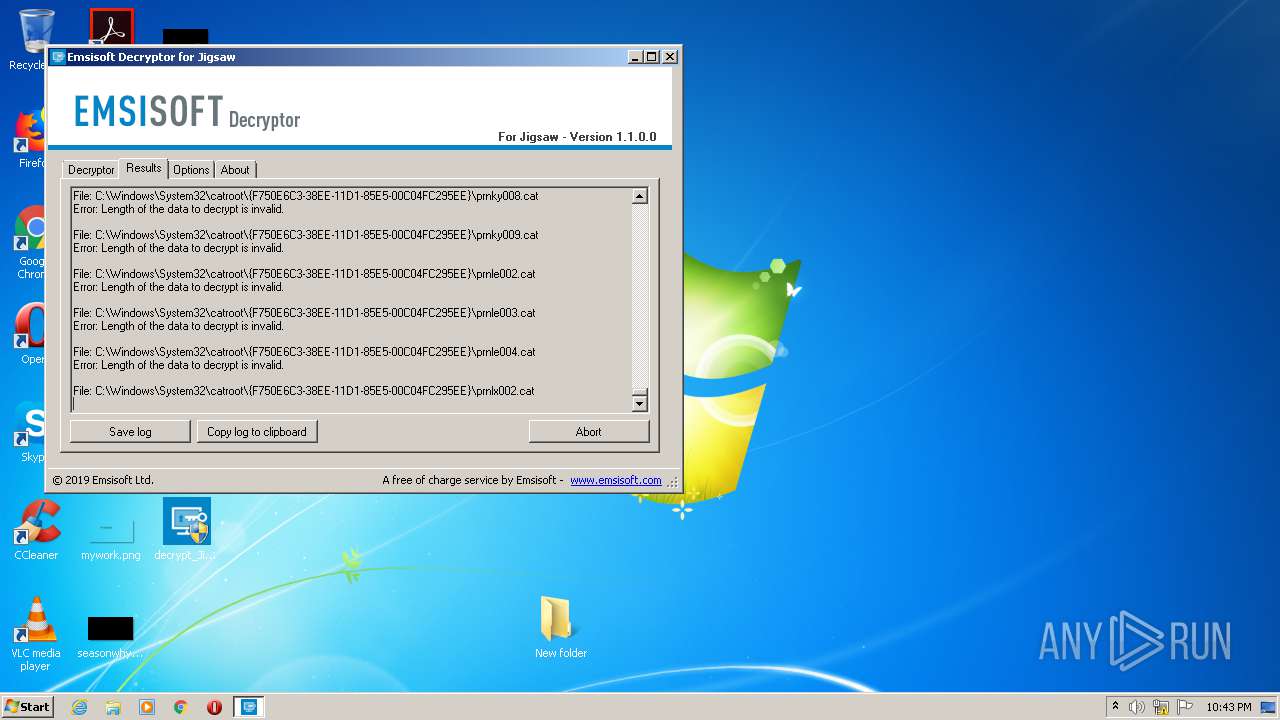
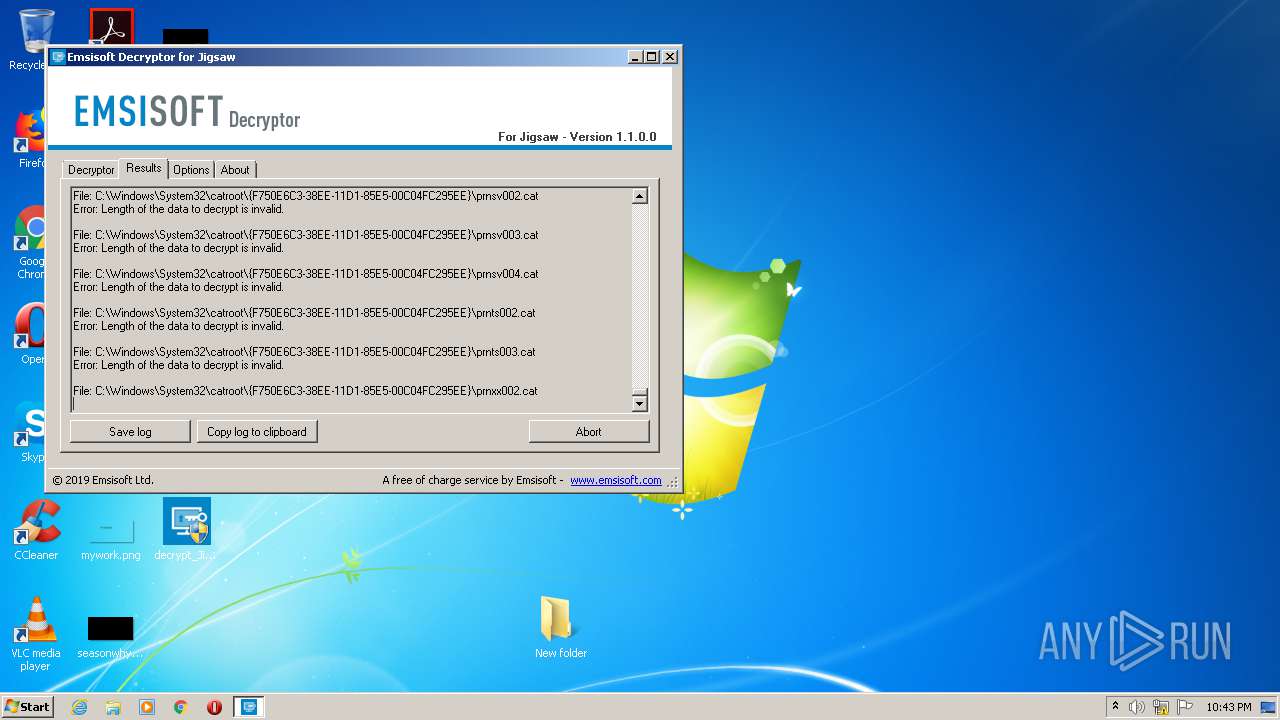
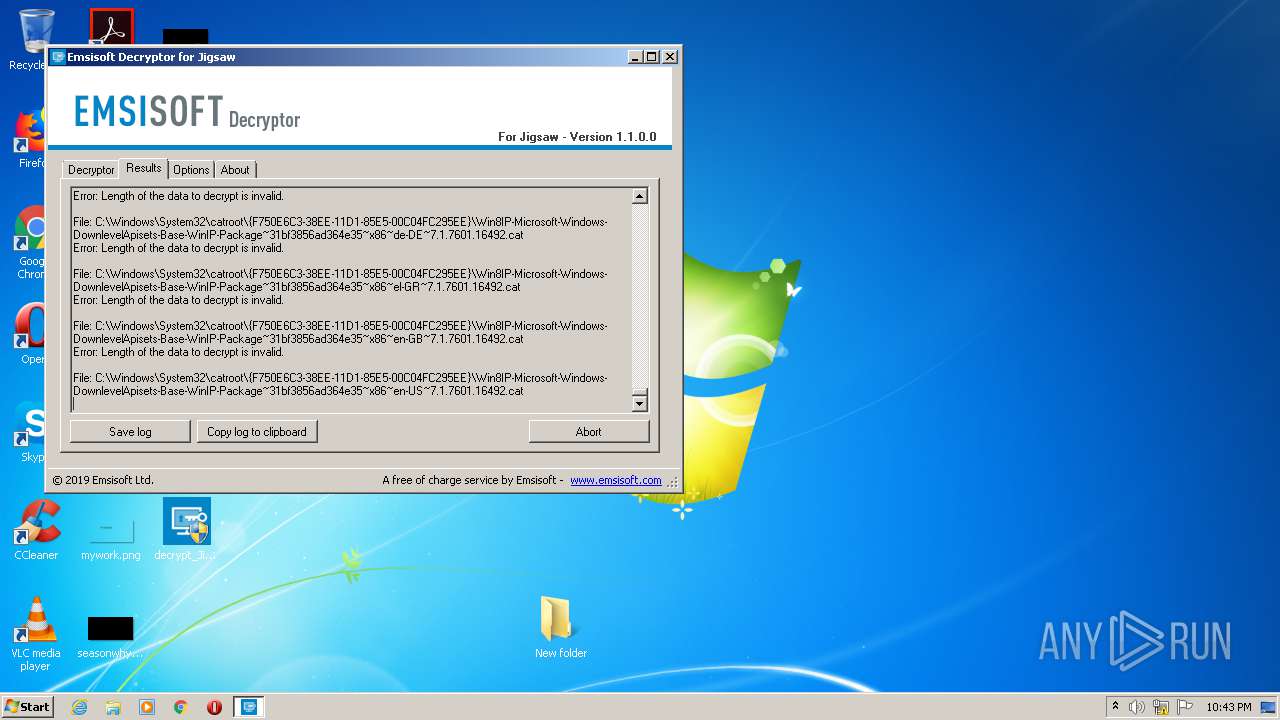
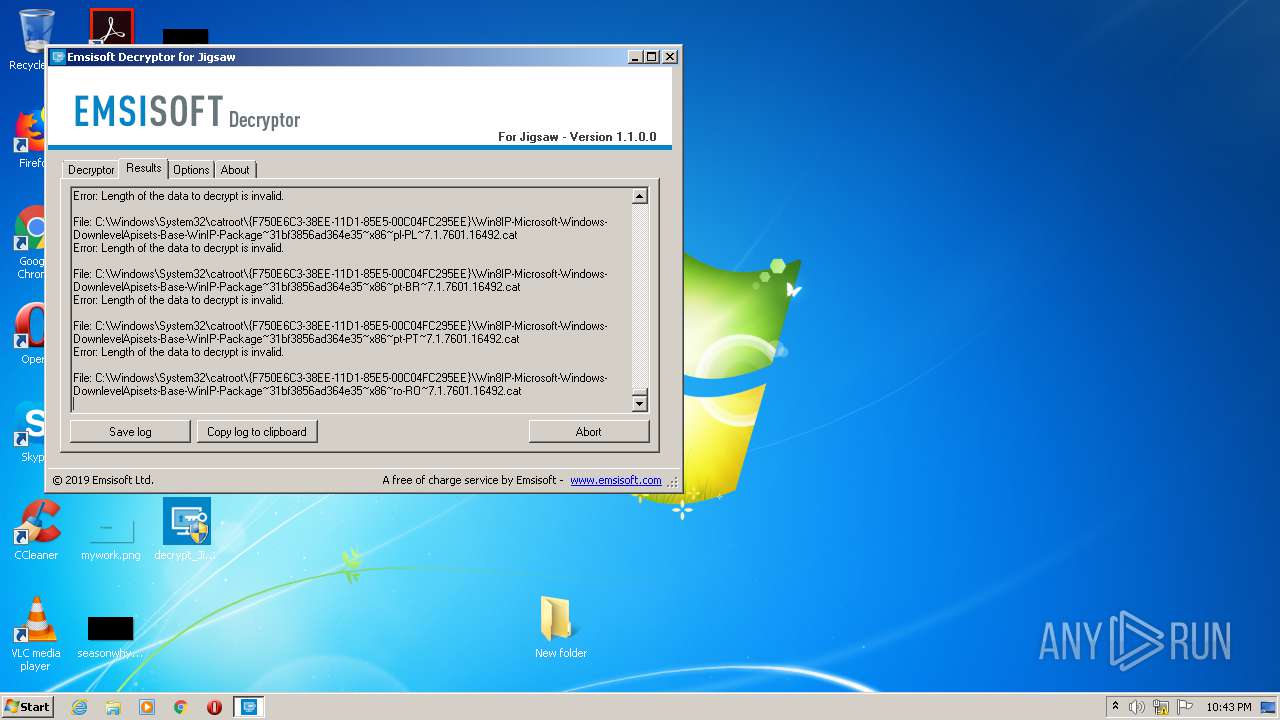
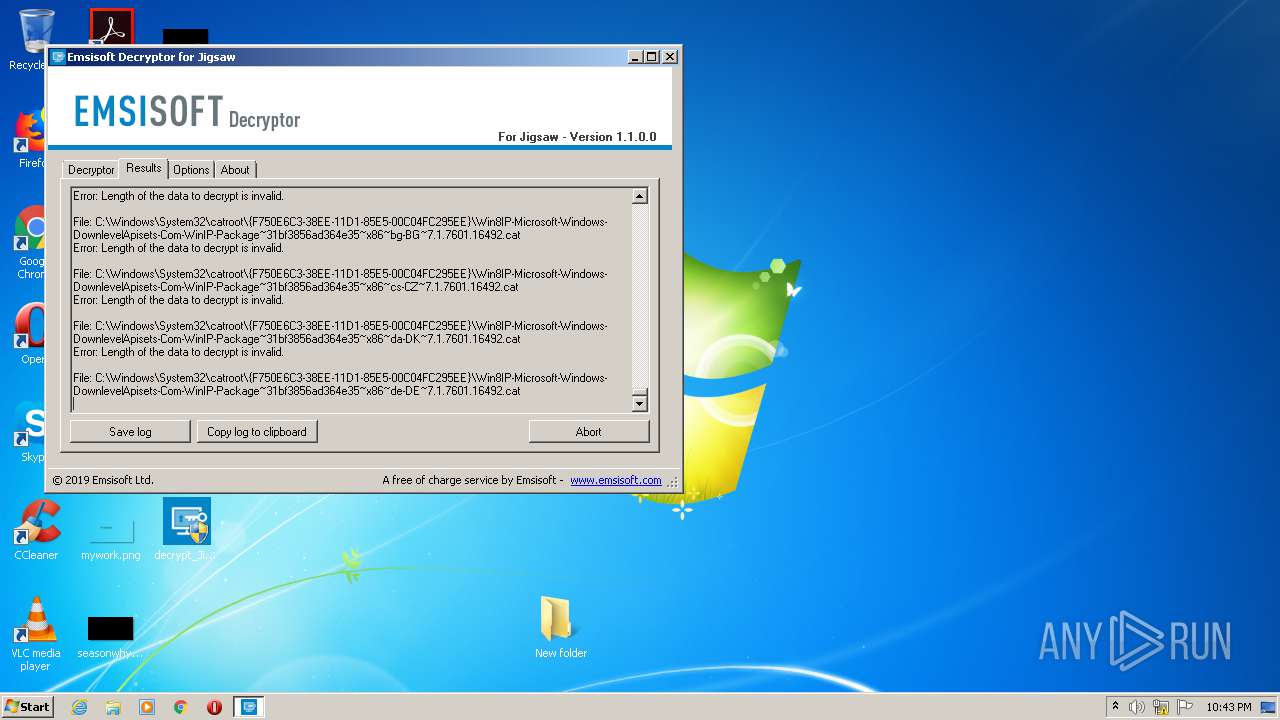
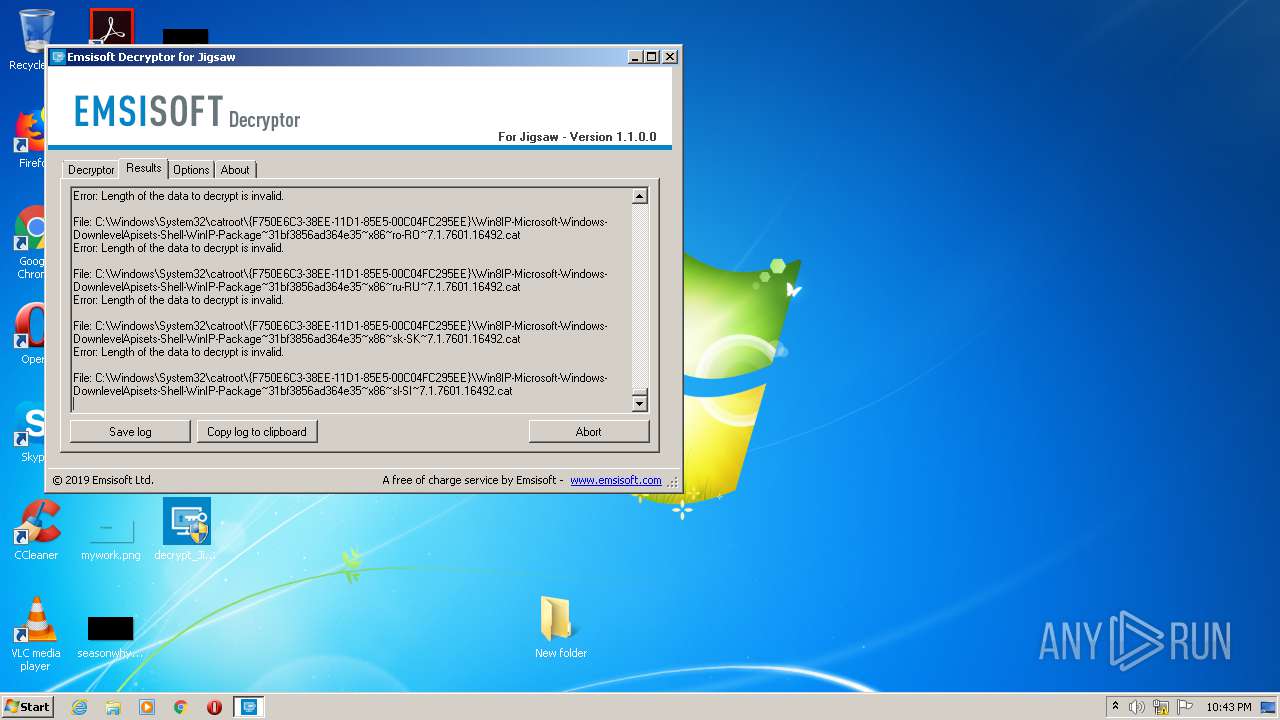
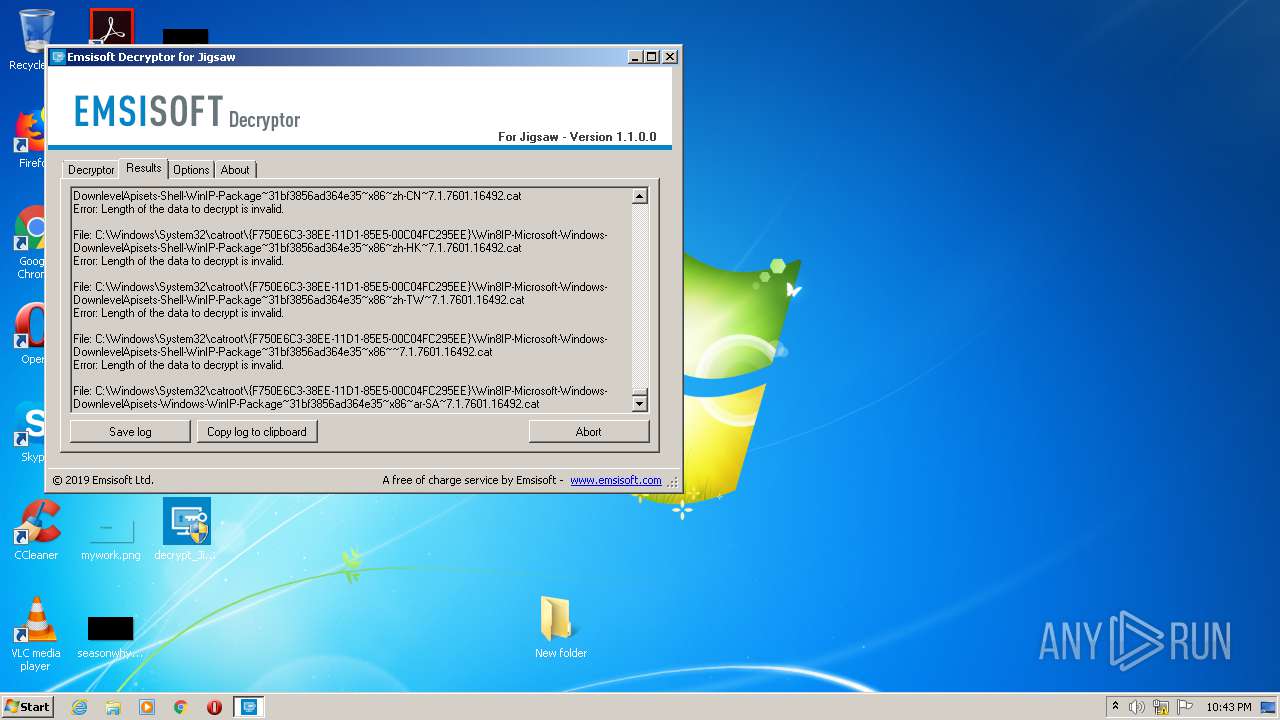
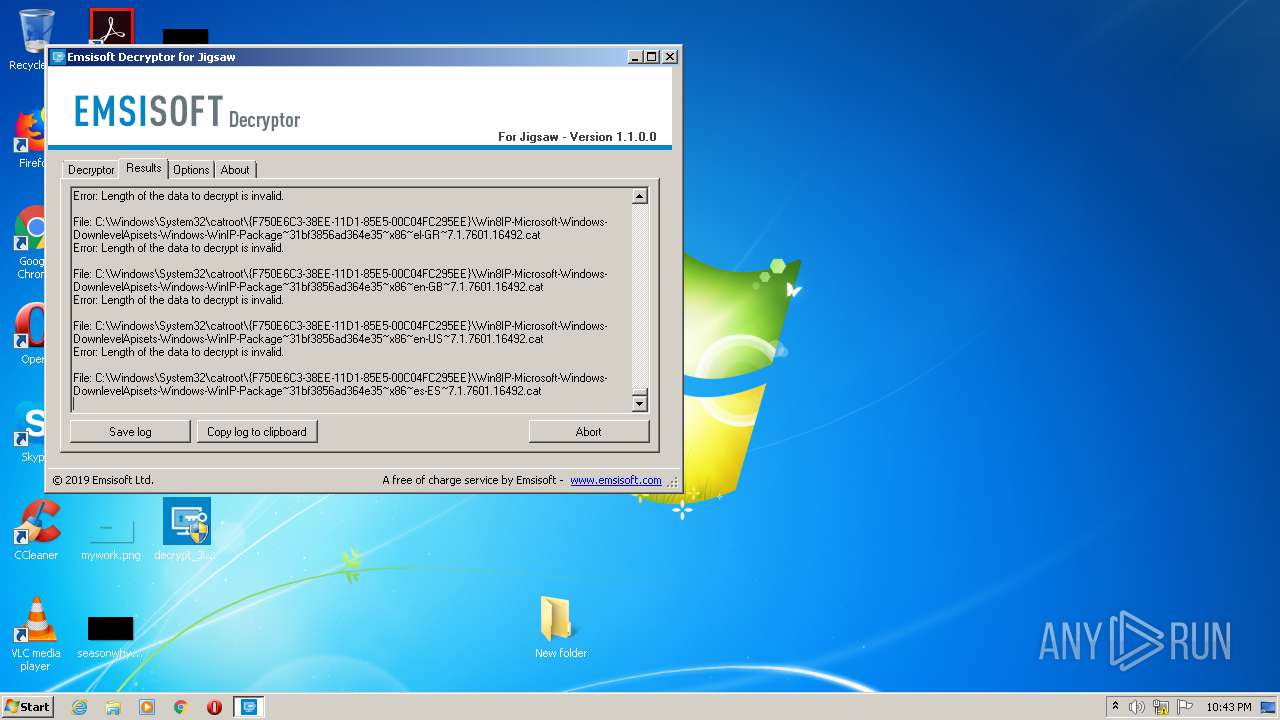
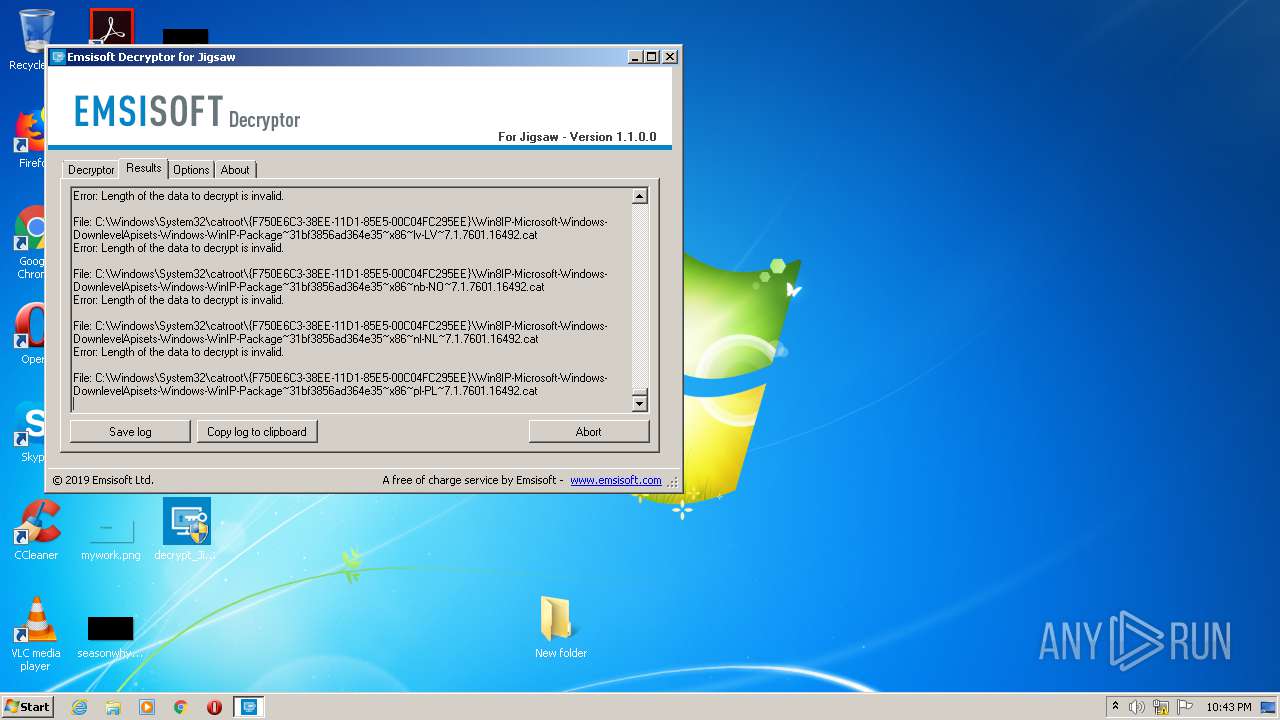
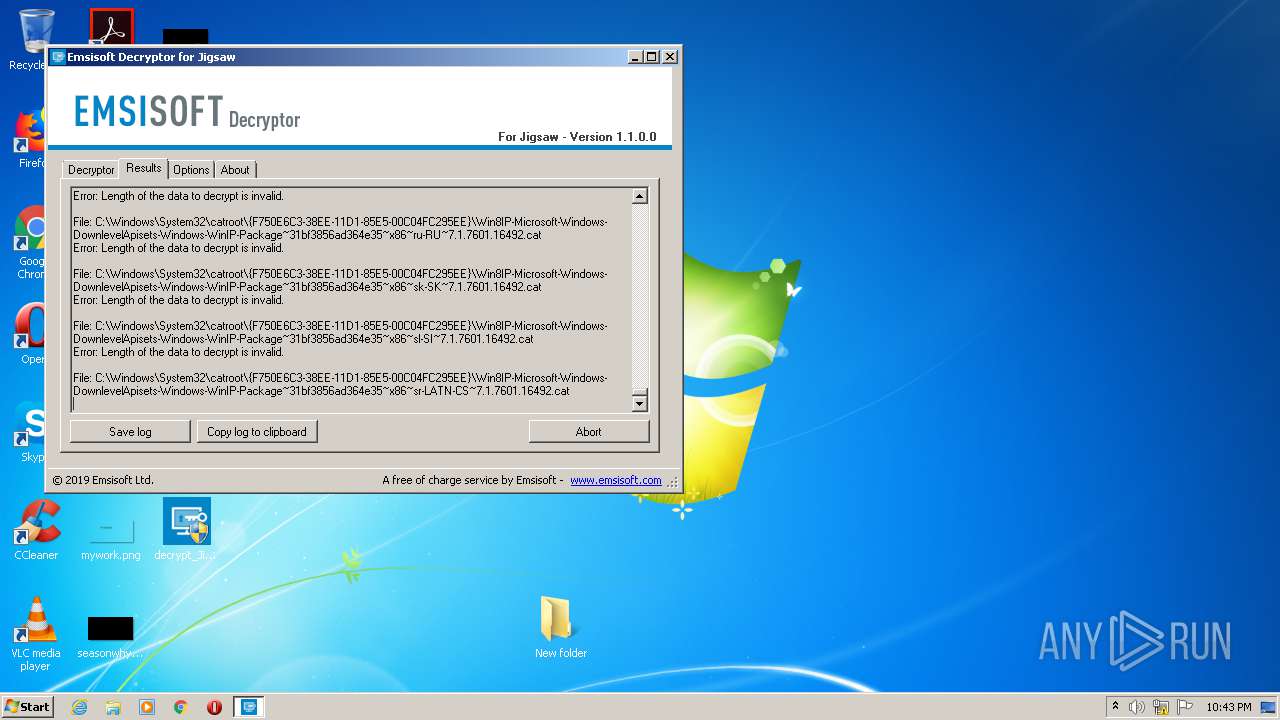
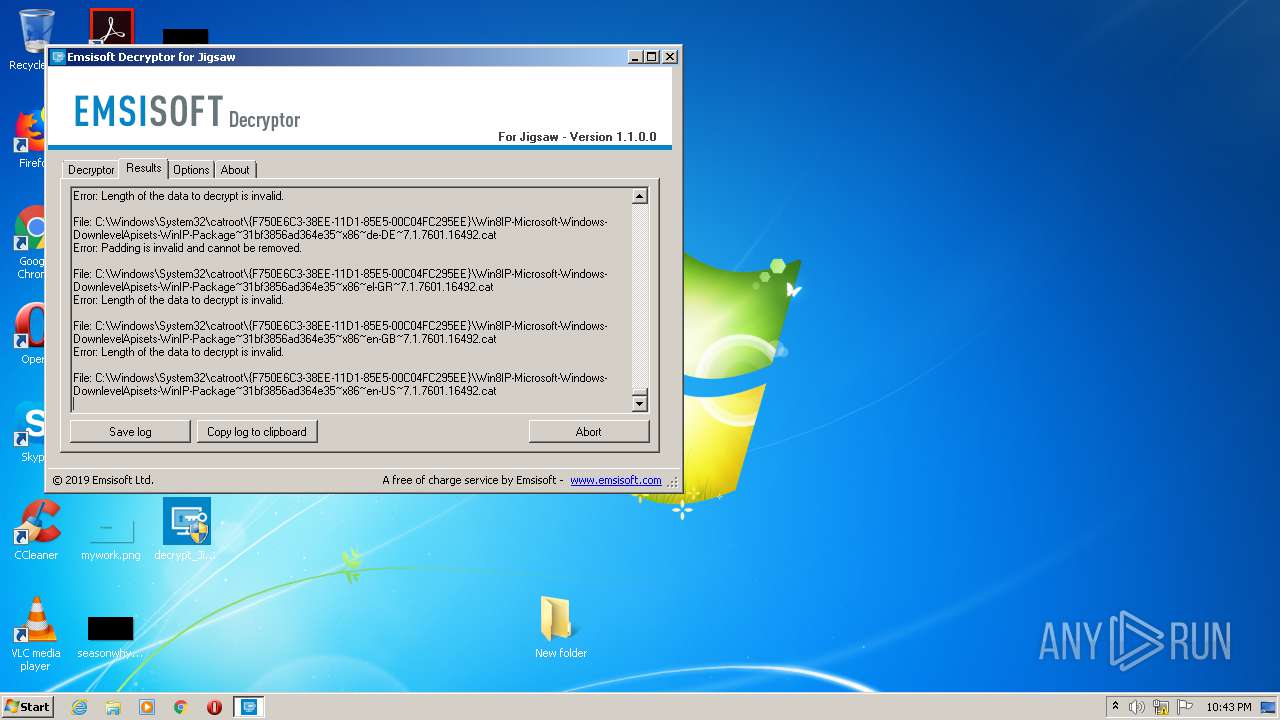
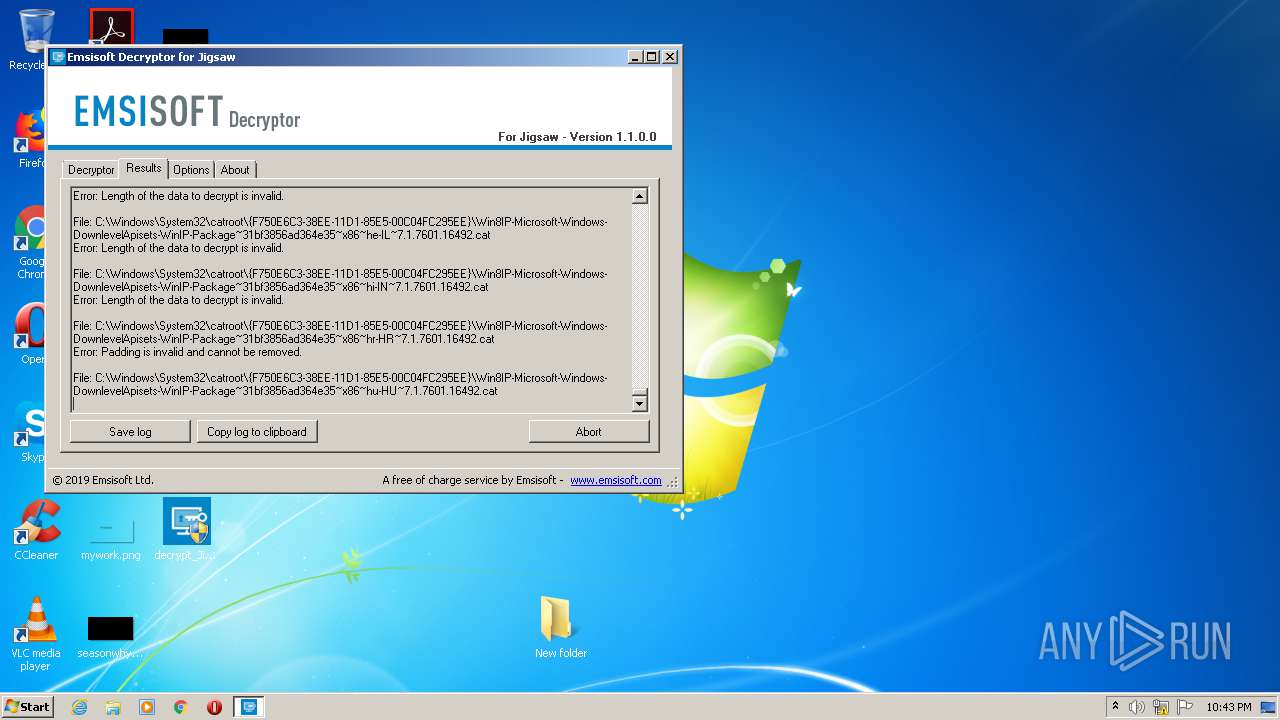
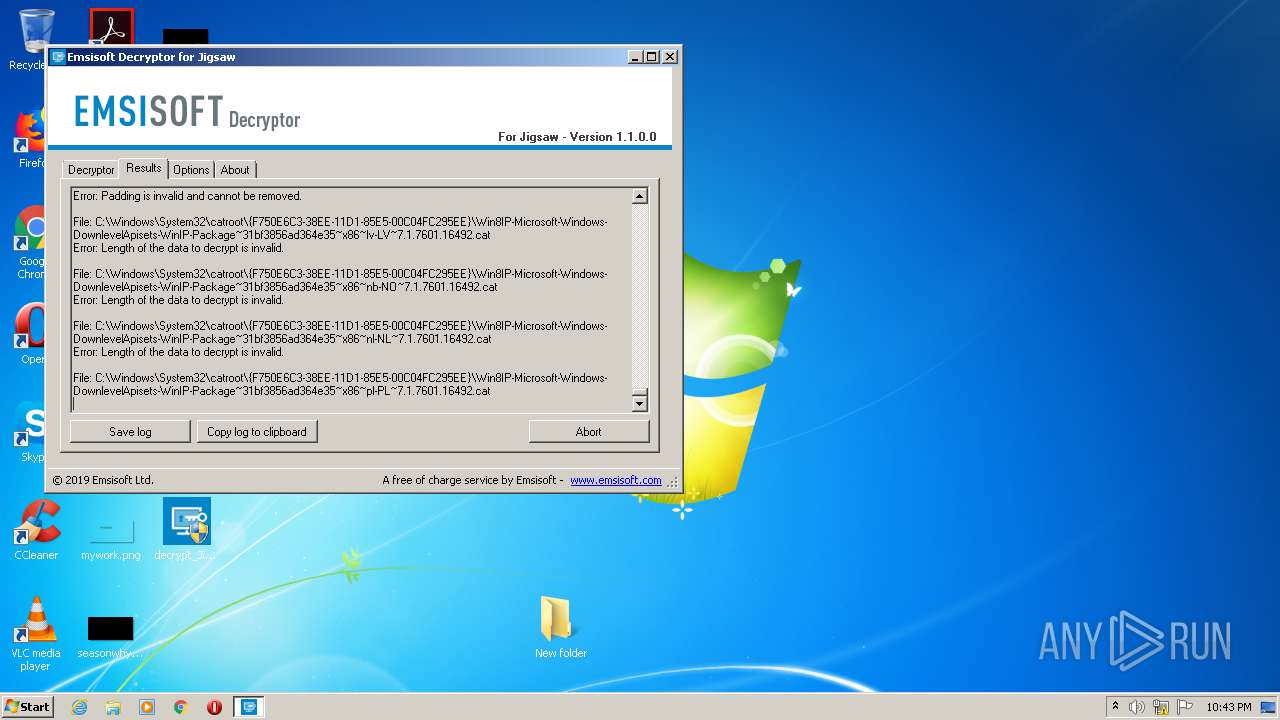
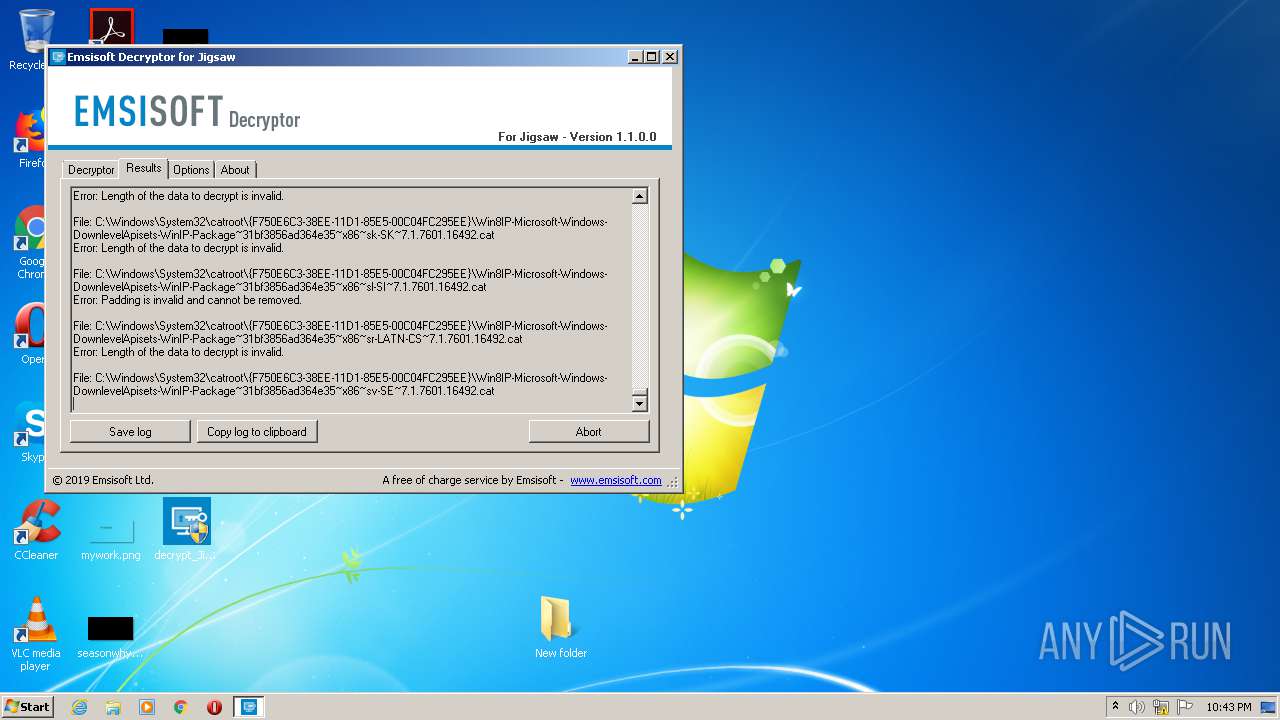
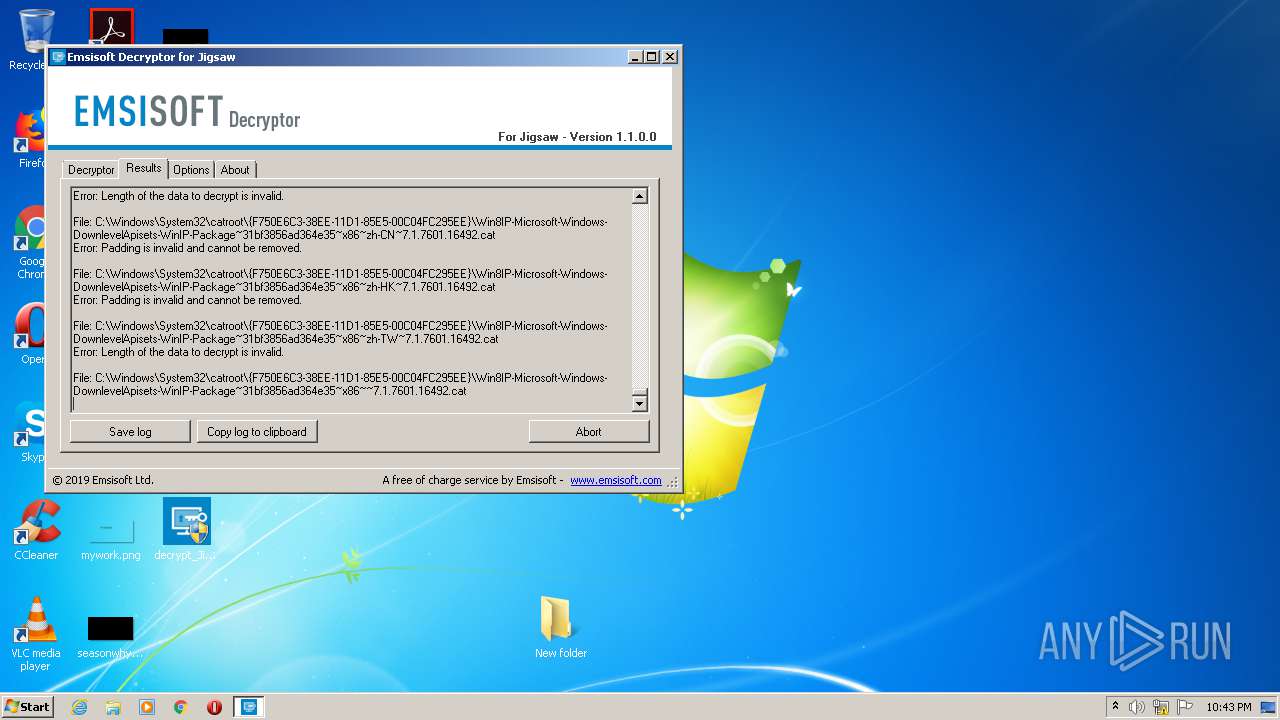
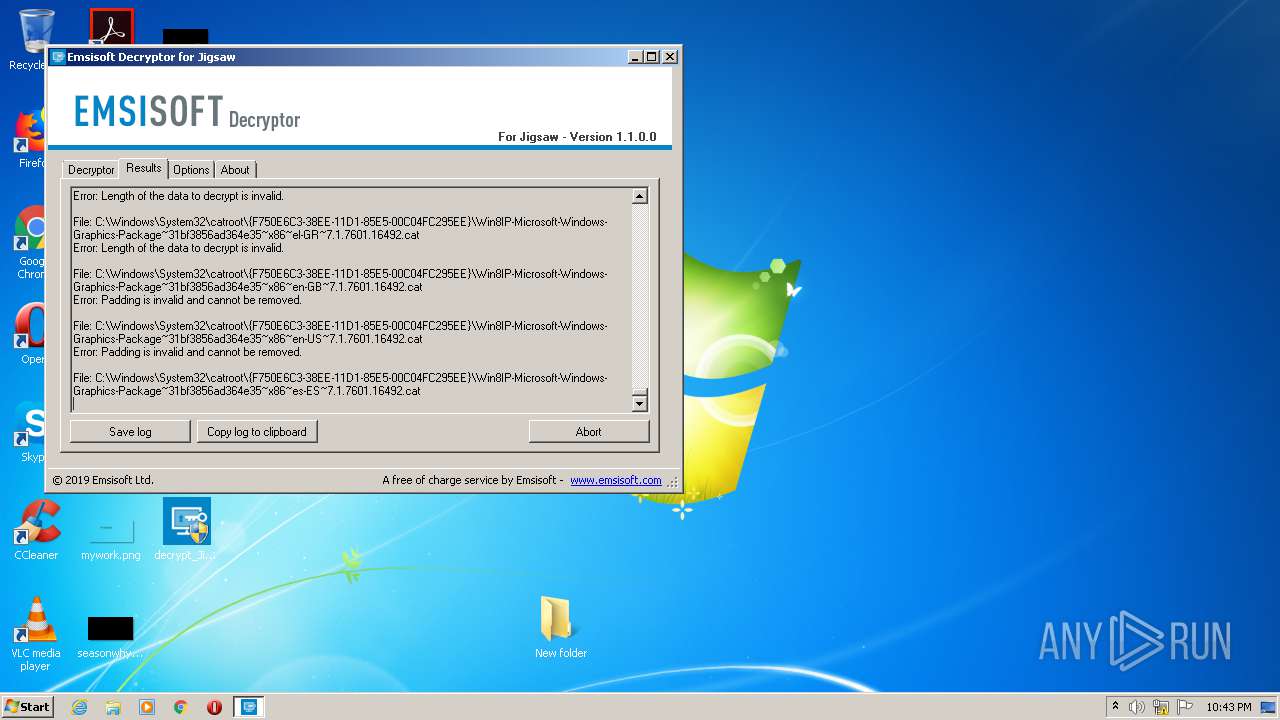
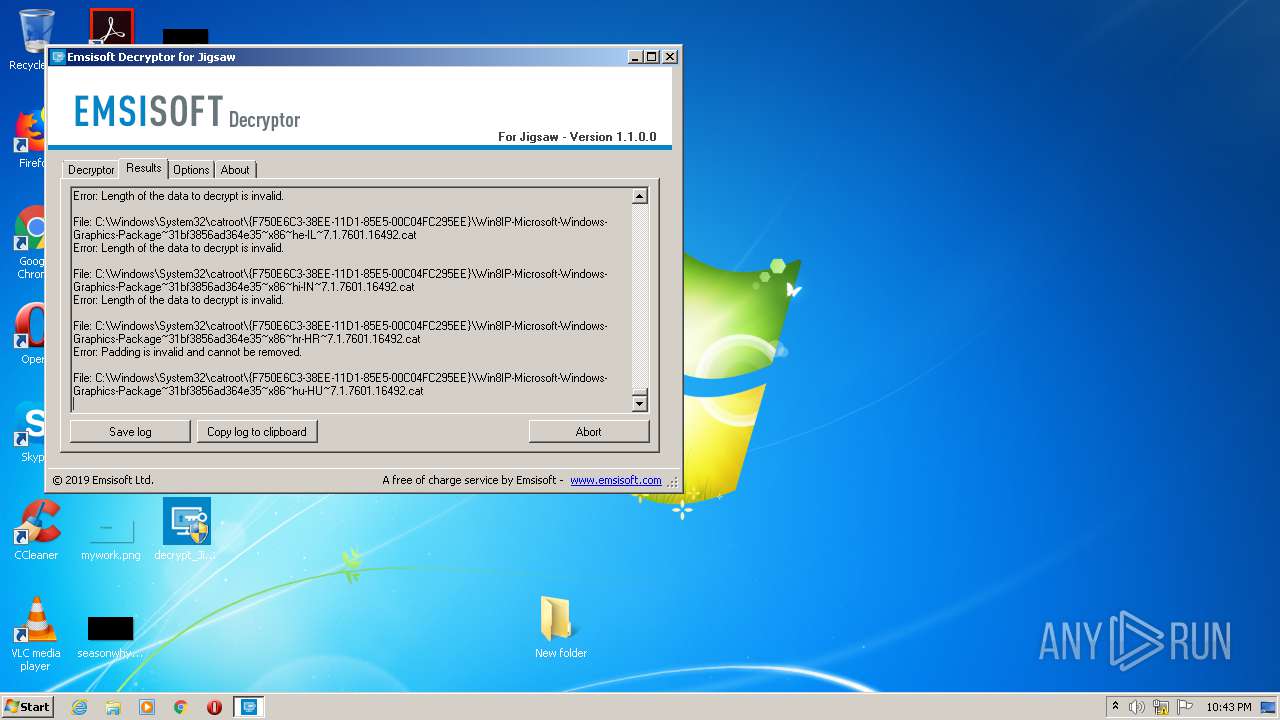
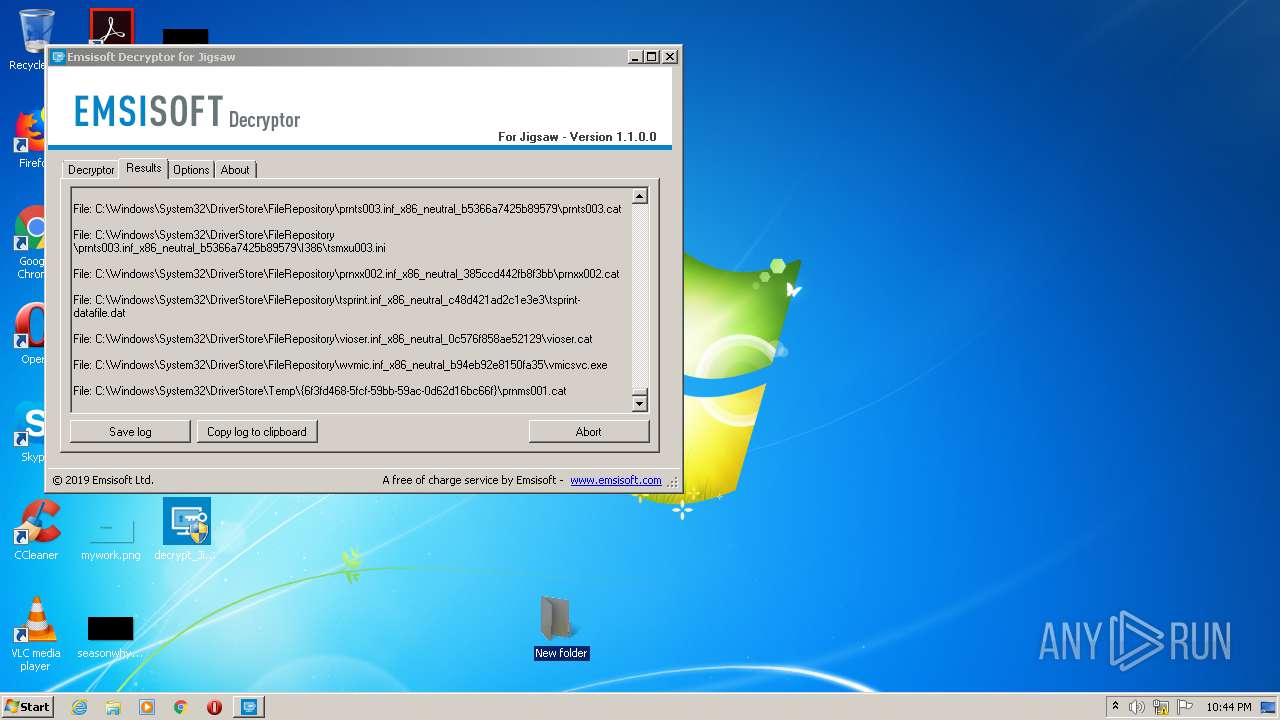
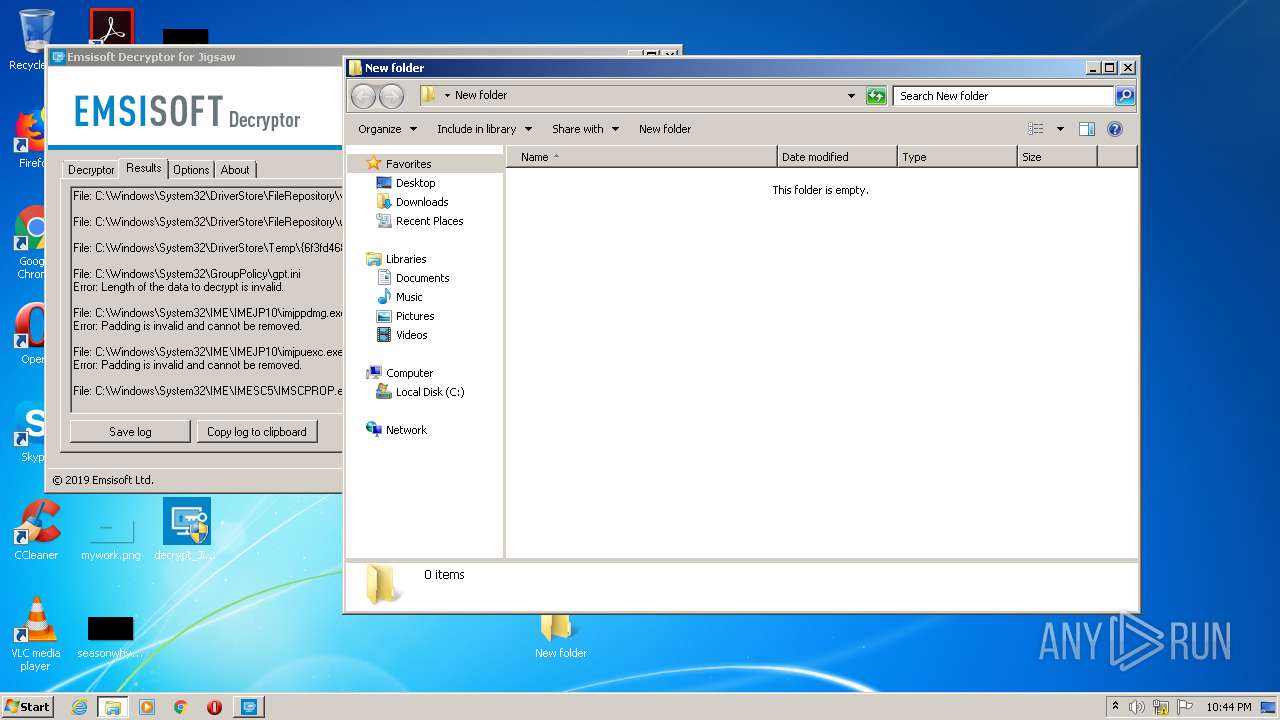
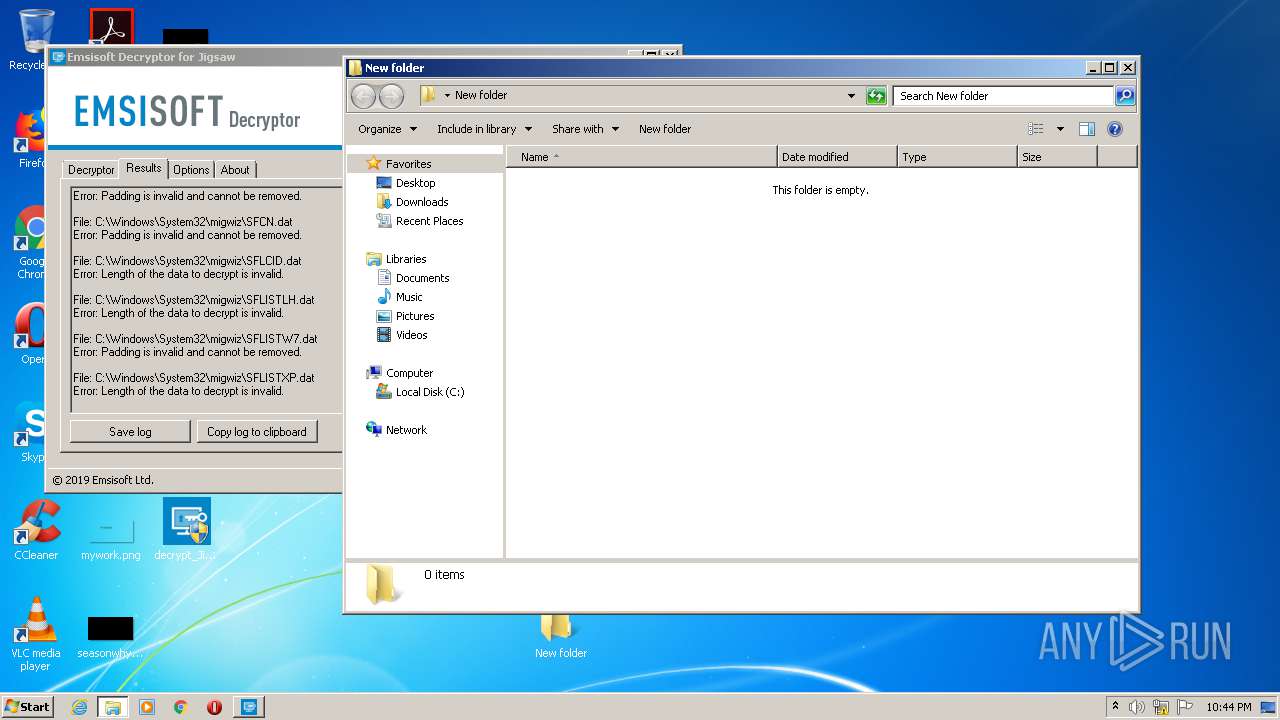
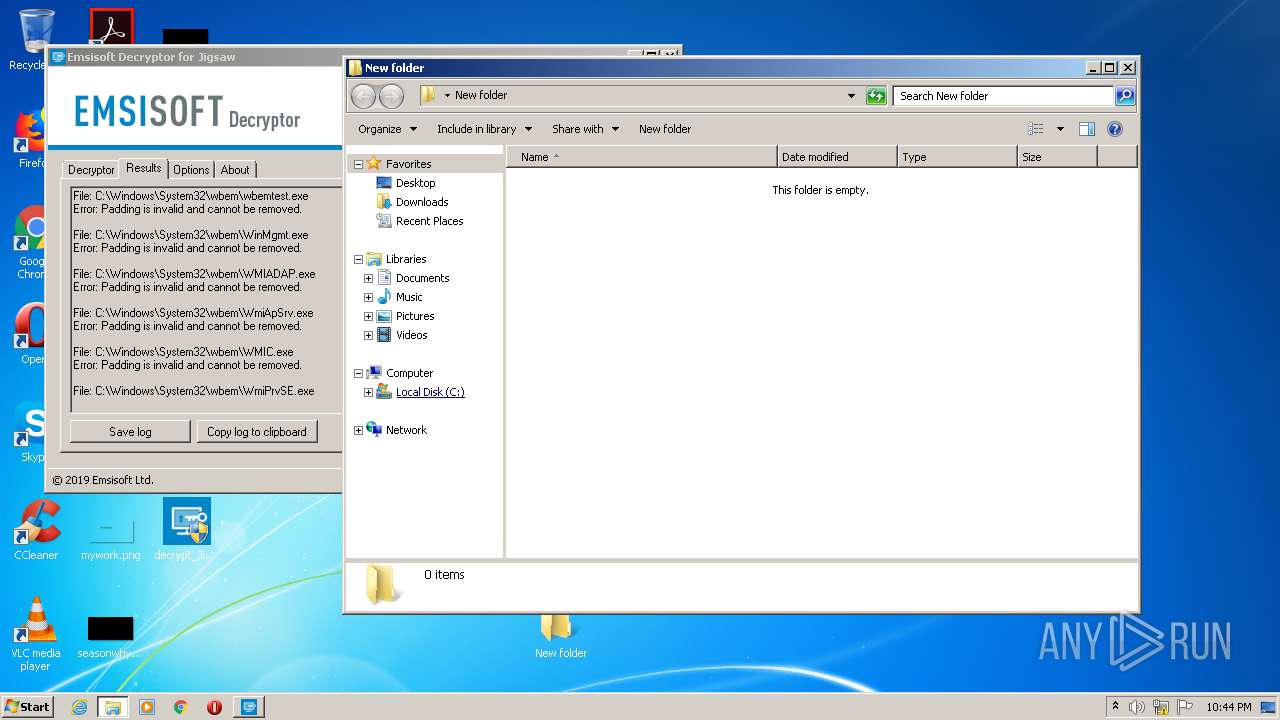
| ProductName: | Emsisoft Decryptor for Jigsaw |
| OriginalFileName: | decrypt_Jigsaw.exe |
| LegalTrademarks: | - |
| LegalCopyright: | © 2019 Emsisoft Ltd. |
| InternalName: | decrypt_Jigsaw.exe |
| FileVersion: | 1.1.0.0 |
| FileDescription: | Emsisoft Decryptor for Jigsaw |
| CompanyName: | Emsisoft Ltd. |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.1.0.0 |
| FileVersionNumber: | 1.1.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x11220e |
| UninitializedDataSize: | - |
| InitializedDataSize: | 30720 |
| CodeSize: | 1115136 |
| LinkerVersion: | 48 |
| PEType: | PE32 |
| TimeStamp: | 2021:06:17 16:29:30+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Jun-2021 14:29:30 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | Emsisoft Ltd. |
| FileDescription: | Emsisoft Decryptor for Jigsaw |
| FileVersion: | 1.1.0.0 |
| InternalName: | decrypt_Jigsaw.exe |
| LegalCopyright: | © 2019 Emsisoft Ltd. |
| LegalTrademarks: | - |
| OriginalFilename: | decrypt_Jigsaw.exe |
| ProductName: | Emsisoft Decryptor for Jigsaw |
| ProductVersion: | 1.1.0.0 |
| Assembly Version: | 1.1.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 17-Jun-2021 14:29:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00110214 | 0x00110400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.99571 |
.rsrc | 0x00114000 | 0x00007578 | 0x00007600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.20983 |
.reloc | 0x0011C000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00772 | 3168 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 4.71209 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.56201 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 4.20179 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 7.90281 | 7921 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.64638 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
89
Monitored processes
41
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,3393149714553662476,17926852429914452258,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16160692687272183588 --mojo-platform-channel-handle=4276 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,3393149714553662476,17926852429914452258,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6689136190394828428 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2488 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,3393149714553662476,17926852429914452258,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17964808910491043236 --mojo-platform-channel-handle=1372 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,3393149714553662476,17926852429914452258,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8810110081167376229 --mojo-platform-channel-handle=4008 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
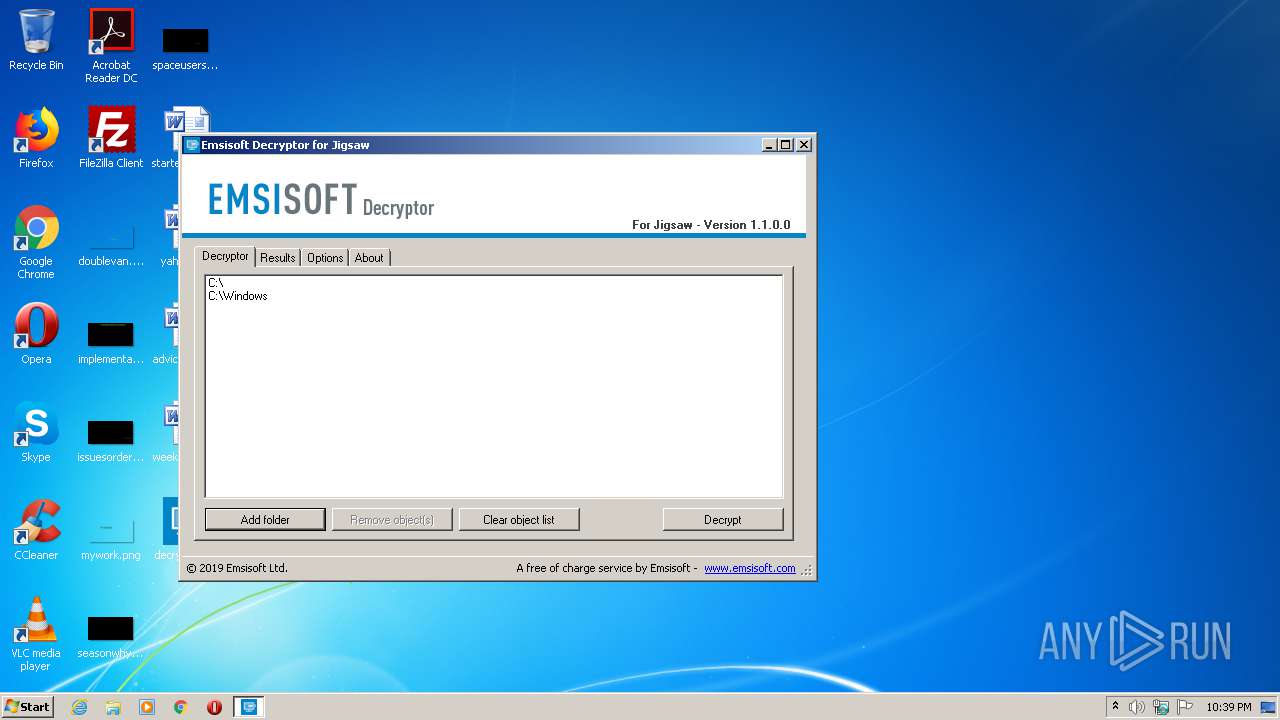
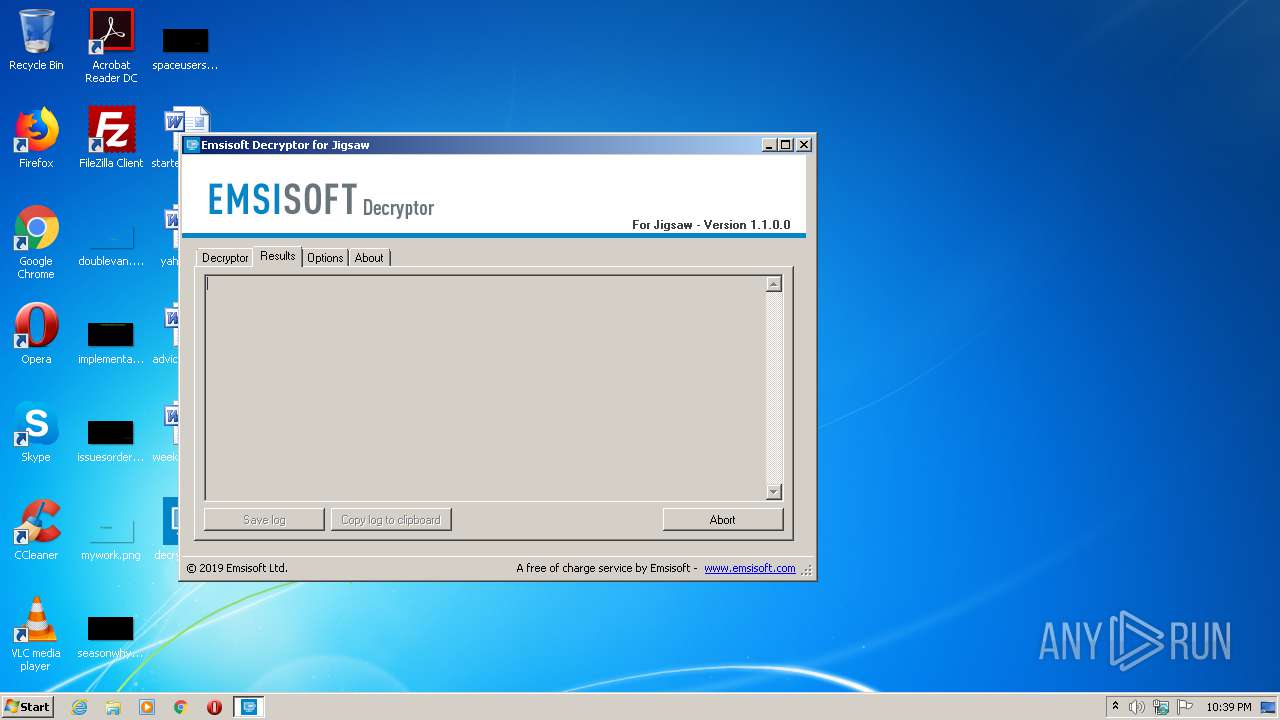
| 1044 | "C:\Users\admin\Desktop\decrypt_Jigsaw.exe" | C:\Users\admin\Desktop\decrypt_Jigsaw.exe | explorer.exe | ||||||||||||
User: admin Company: Emsisoft Ltd. Integrity Level: HIGH Description: Emsisoft Decryptor for Jigsaw Exit code: 0 Version: 1.1.0.0 Modules
| |||||||||||||||
| 1452 | "C:\Users\admin\Desktop\decrypt_Jigsaw.exe" | C:\Users\admin\Desktop\decrypt_Jigsaw.exe | — | explorer.exe | |||||||||||
User: admin Company: Emsisoft Ltd. Integrity Level: MEDIUM Description: Emsisoft Decryptor for Jigsaw Exit code: 3221226540 Version: 1.1.0.0 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,3393149714553662476,17926852429914452258,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1894903414799433376 --mojo-platform-channel-handle=3724 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,3393149714553662476,17926852429914452258,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1572925548621370818 --mojo-platform-channel-handle=3408 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,3393149714553662476,17926852429914452258,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=560358064421884040 --mojo-platform-channel-handle=2844 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,3393149714553662476,17926852429914452258,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6286904926330526425 --mojo-platform-channel-handle=3788 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 111
Read events
1 793
Write events
310
Delete events
8
Modification events
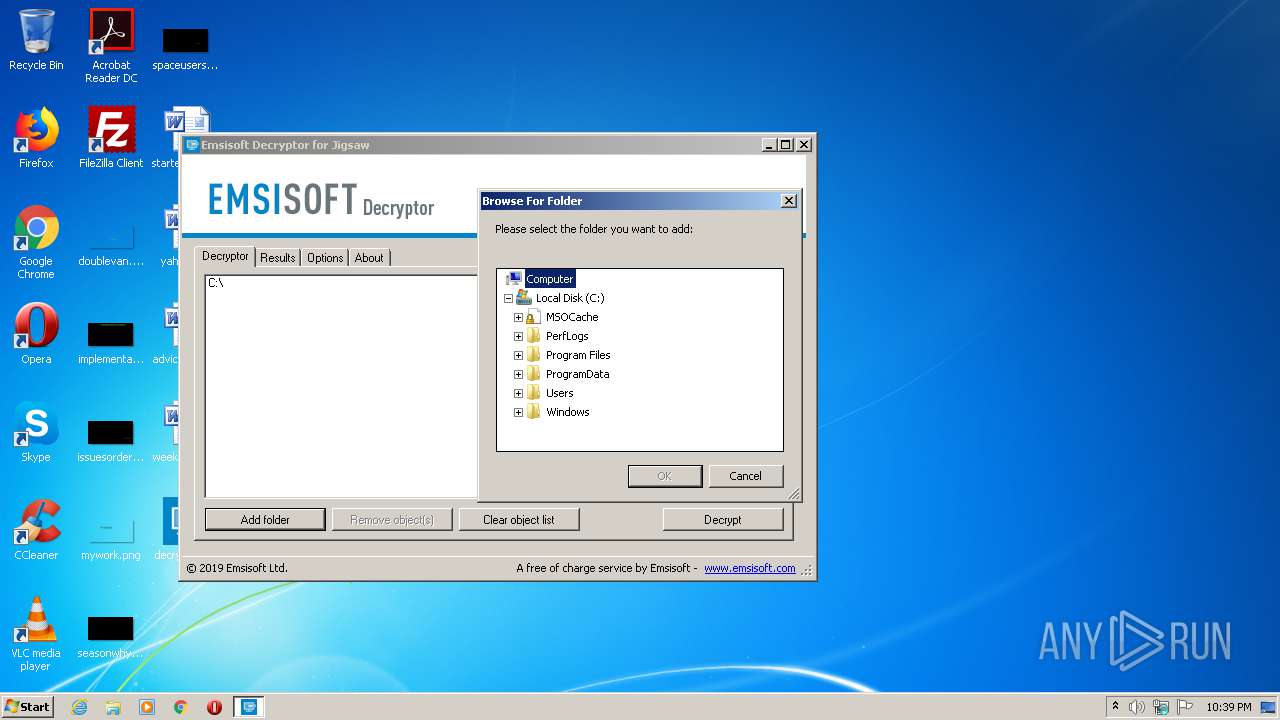
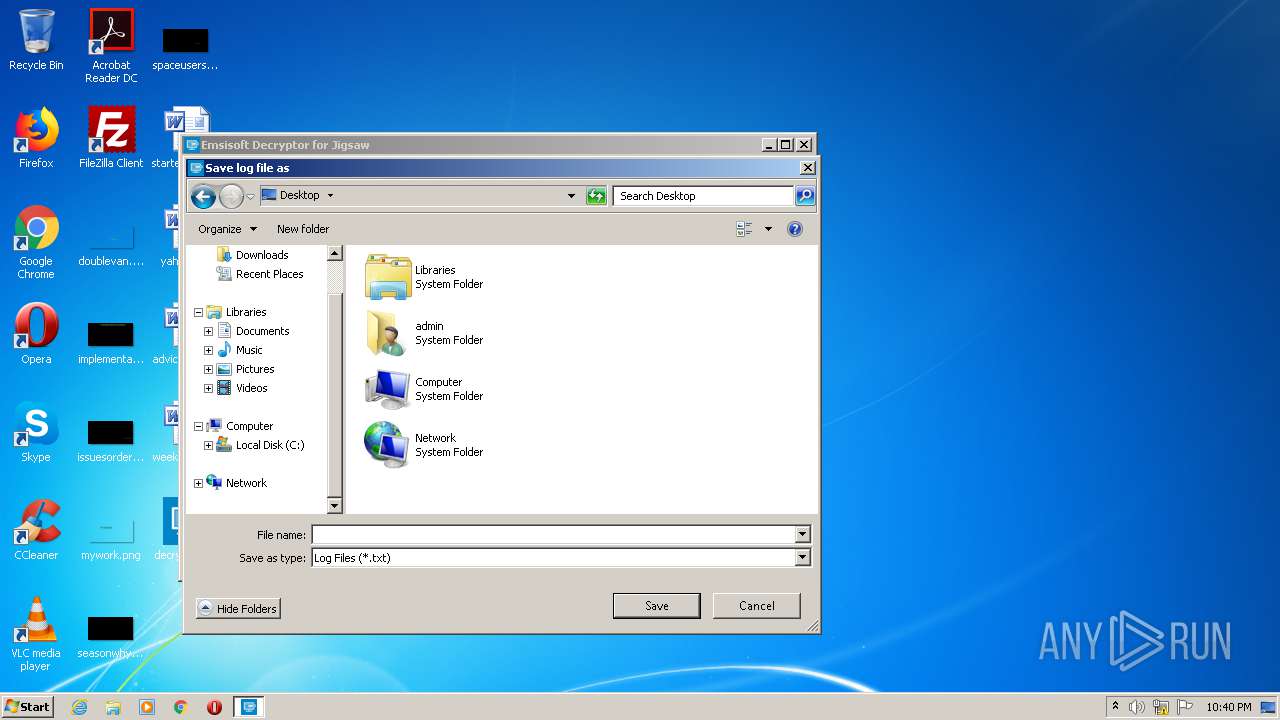
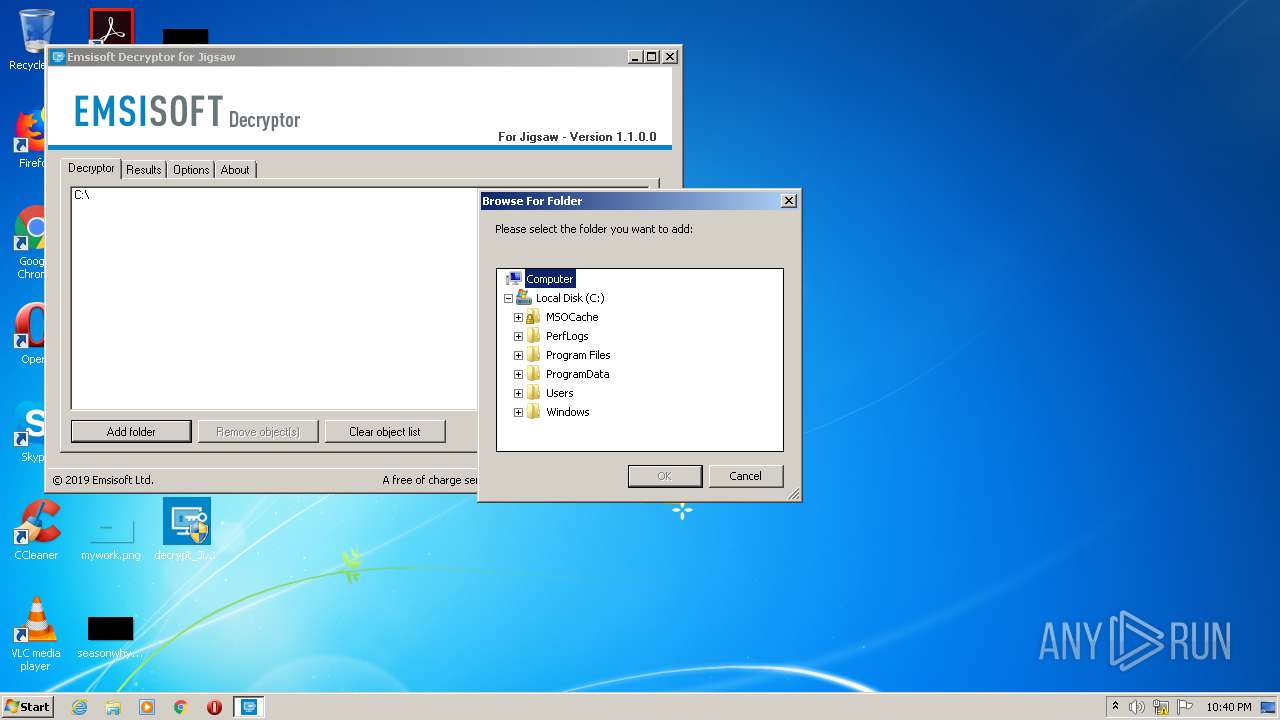
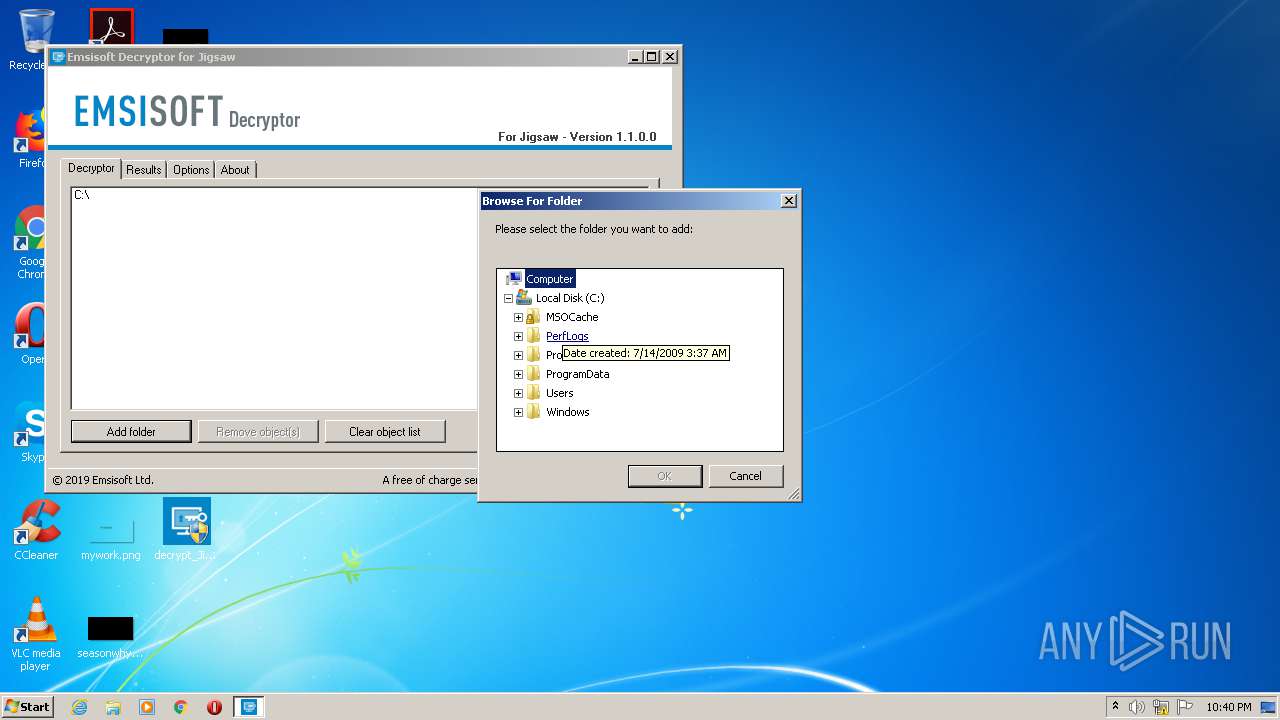
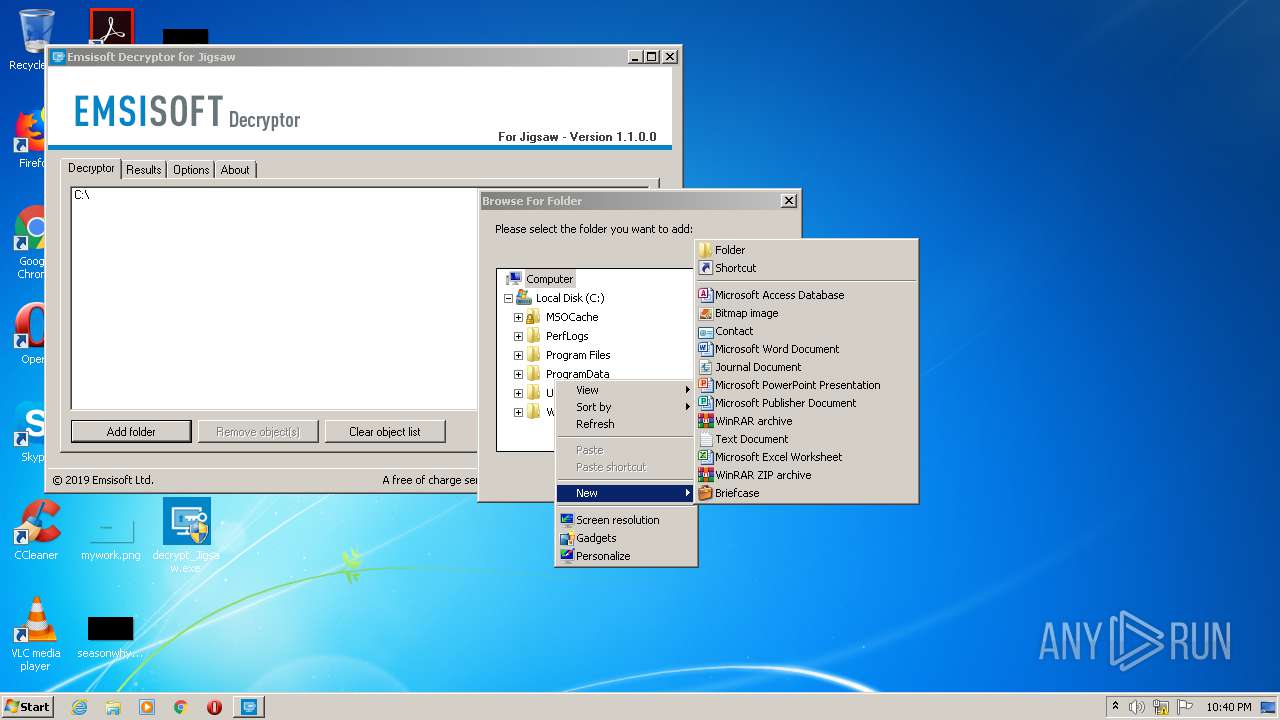
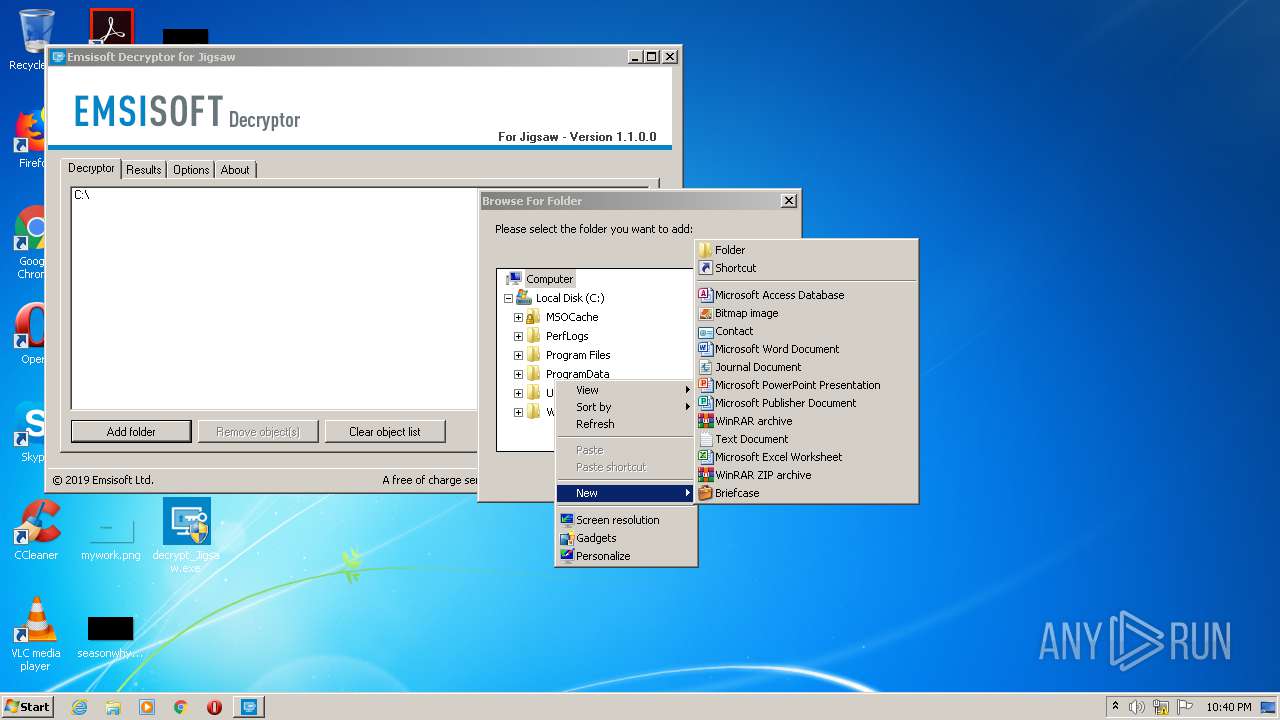
| (PID) Process: | (1044) decrypt_Jigsaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Width |
Value: 318 | |||
| (PID) Process: | (1044) decrypt_Jigsaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Height |
Value: 288 | |||
| (PID) Process: | (1044) decrypt_Jigsaw.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\decrypt_Jigsaw_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1044) decrypt_Jigsaw.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\decrypt_Jigsaw_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1044) decrypt_Jigsaw.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\decrypt_Jigsaw_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1044) decrypt_Jigsaw.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\decrypt_Jigsaw_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1044) decrypt_Jigsaw.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\decrypt_Jigsaw_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1044) decrypt_Jigsaw.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\decrypt_Jigsaw_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1044) decrypt_Jigsaw.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\decrypt_Jigsaw_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1044) decrypt_Jigsaw.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\decrypt_Jigsaw_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
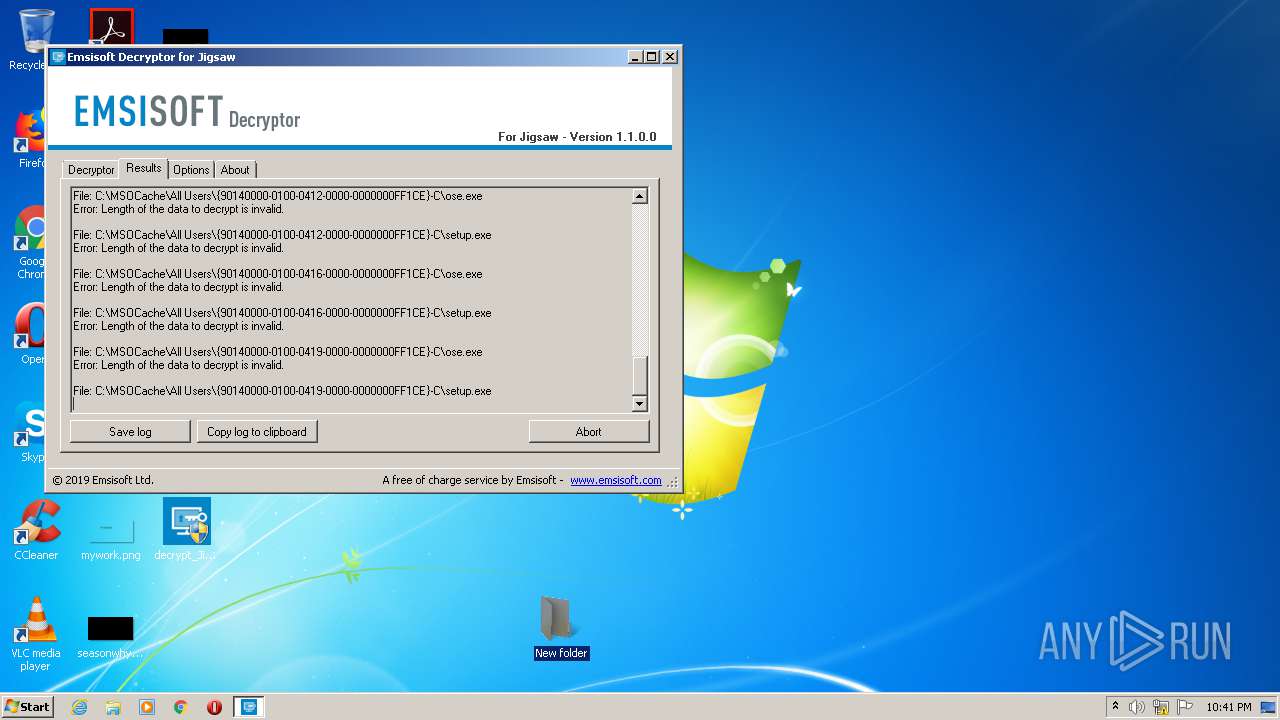
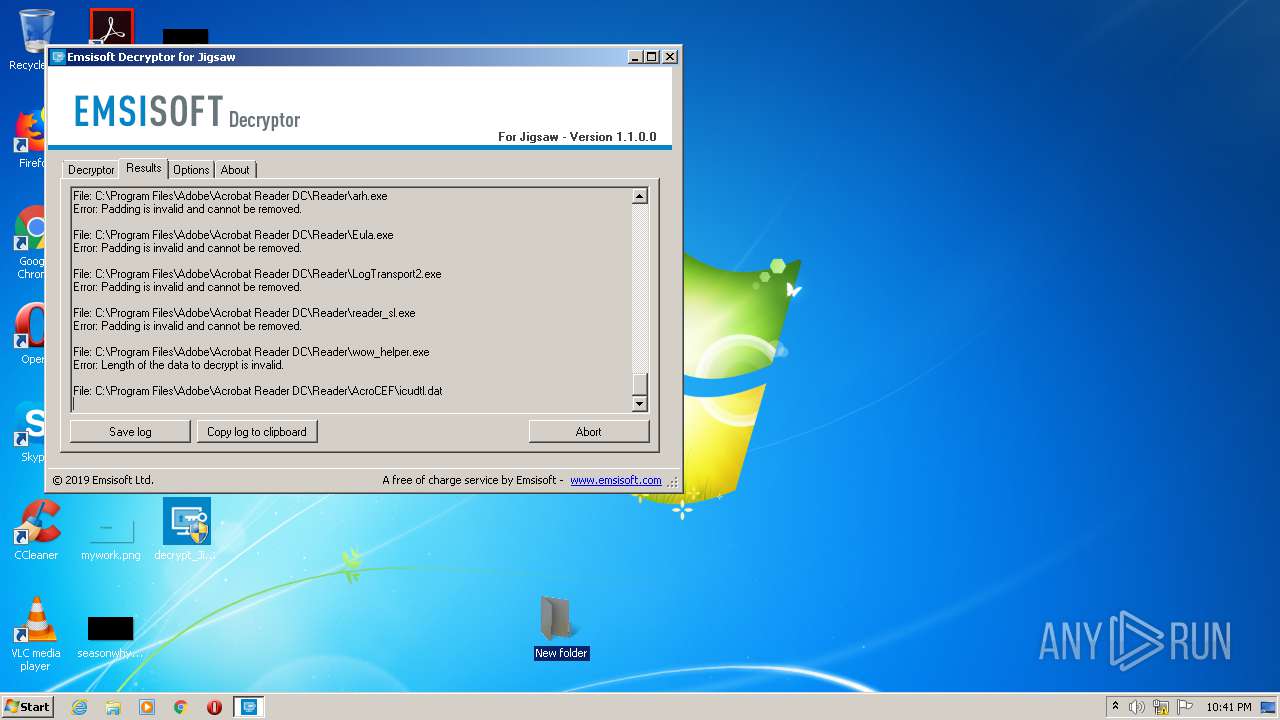
Executable files
102
Suspicious files
95
Text files
337
Unknown types
121
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
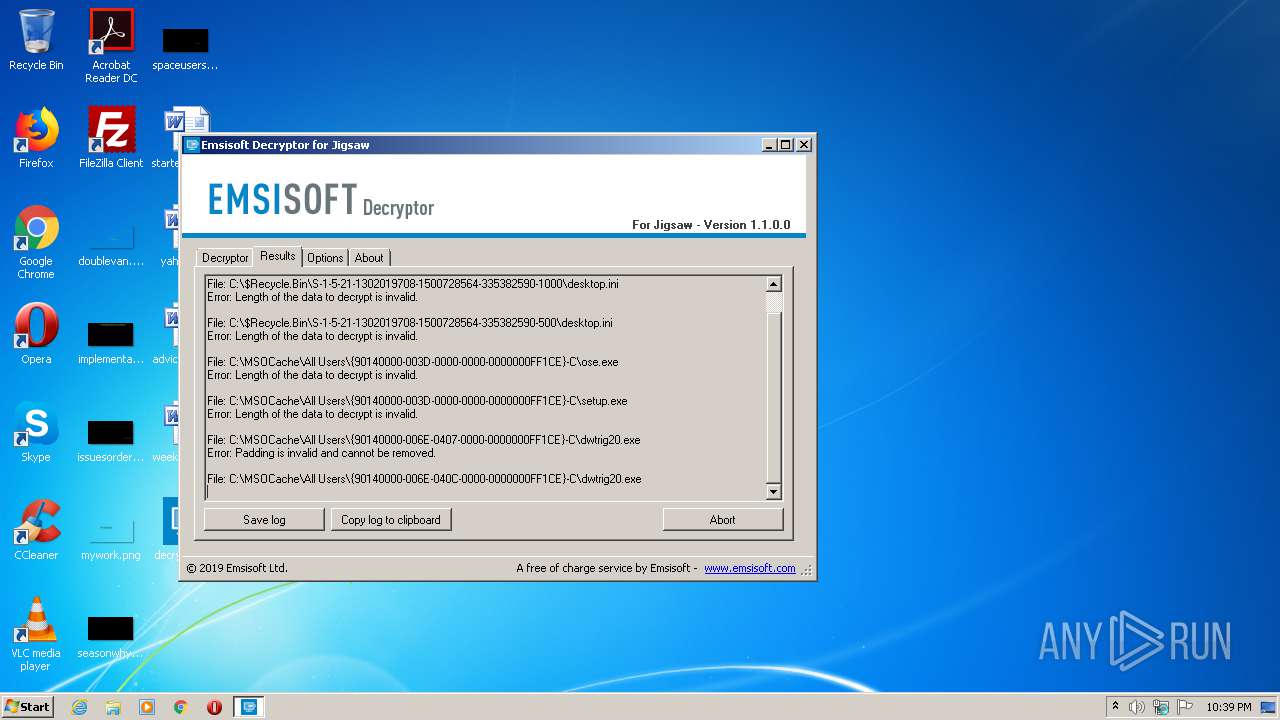
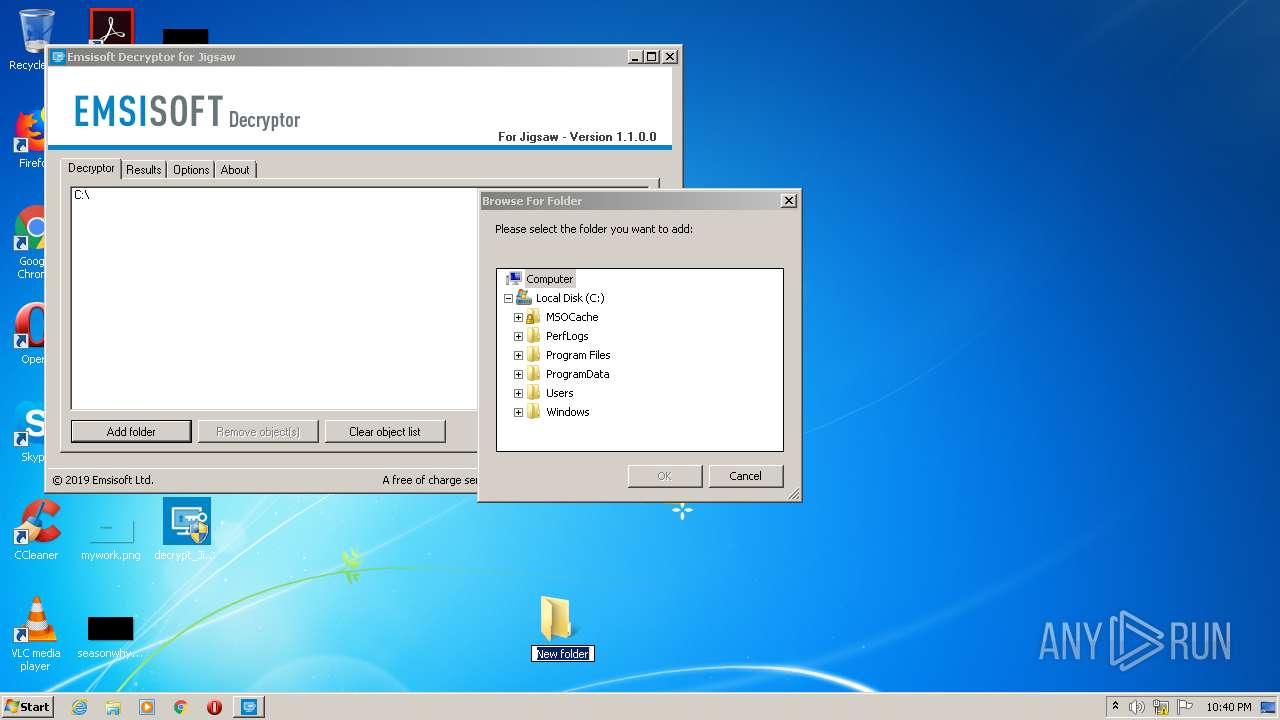
| 1044 | decrypt_Jigsaw.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-500\desktop | — | |
MD5:— | SHA256:— | |||
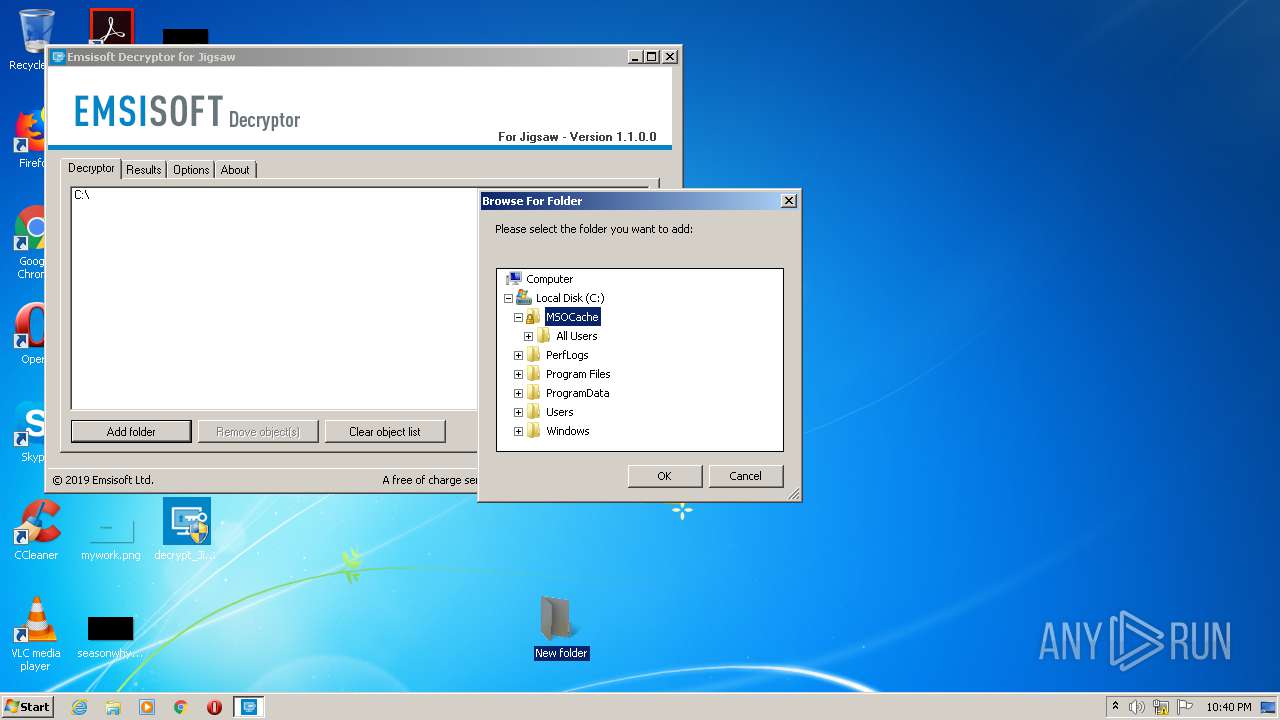
| 1044 | decrypt_Jigsaw.exe | C:\MSOCache\All Users\{90140000-003D-0000-0000-0000000FF1CE}-C\setup | — | |
MD5:— | SHA256:— | |||
| 1044 | decrypt_Jigsaw.exe | C:\MSOCache\All Users\{90140000-006E-0407-0000-0000000FF1CE}-C\dwtrig20 | — | |
MD5:— | SHA256:— | |||
| 1044 | decrypt_Jigsaw.exe | C:\MSOCache\All Users\{90140000-006E-040C-0000-0000000FF1CE}-C\dwtrig20 | — | |
MD5:— | SHA256:— | |||
| 1044 | decrypt_Jigsaw.exe | C:\MSOCache\All Users\{90140000-006E-0410-0000-0000000FF1CE}-C\dwtrig20 | — | |
MD5:— | SHA256:— | |||
| 1044 | decrypt_Jigsaw.exe | C:\MSOCache\All Users\{90140000-006E-0411-0000-0000000FF1CE}-C\dwtrig20 | — | |
MD5:— | SHA256:— | |||
| 1044 | decrypt_Jigsaw.exe | C:\MSOCache\All Users\{90140000-006E-0412-0000-0000000FF1CE}-C\dwtrig20 | — | |
MD5:— | SHA256:— | |||
| 1044 | decrypt_Jigsaw.exe | C:\MSOCache\All Users\{90140000-006E-0416-0000-0000000FF1CE}-C\dwtrig20 | — | |
MD5:— | SHA256:— | |||
| 1044 | decrypt_Jigsaw.exe | C:\MSOCache\All Users\{90140000-006E-041F-0000-0000000FF1CE}-C\dwtrig20 | — | |
MD5:— | SHA256:— | |||
| 1044 | decrypt_Jigsaw.exe | C:\MSOCache\All Users\{90140000-006E-0C0A-0000-0000000FF1CE}-C\dwtrig20 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report