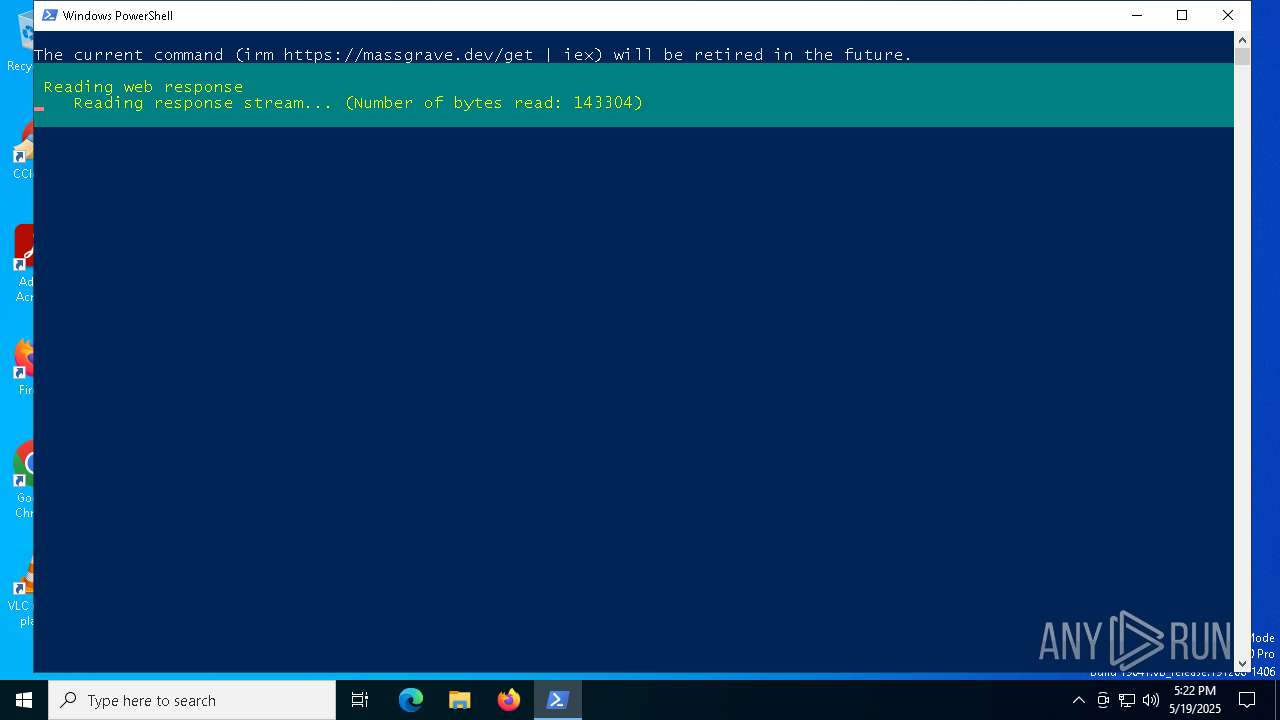
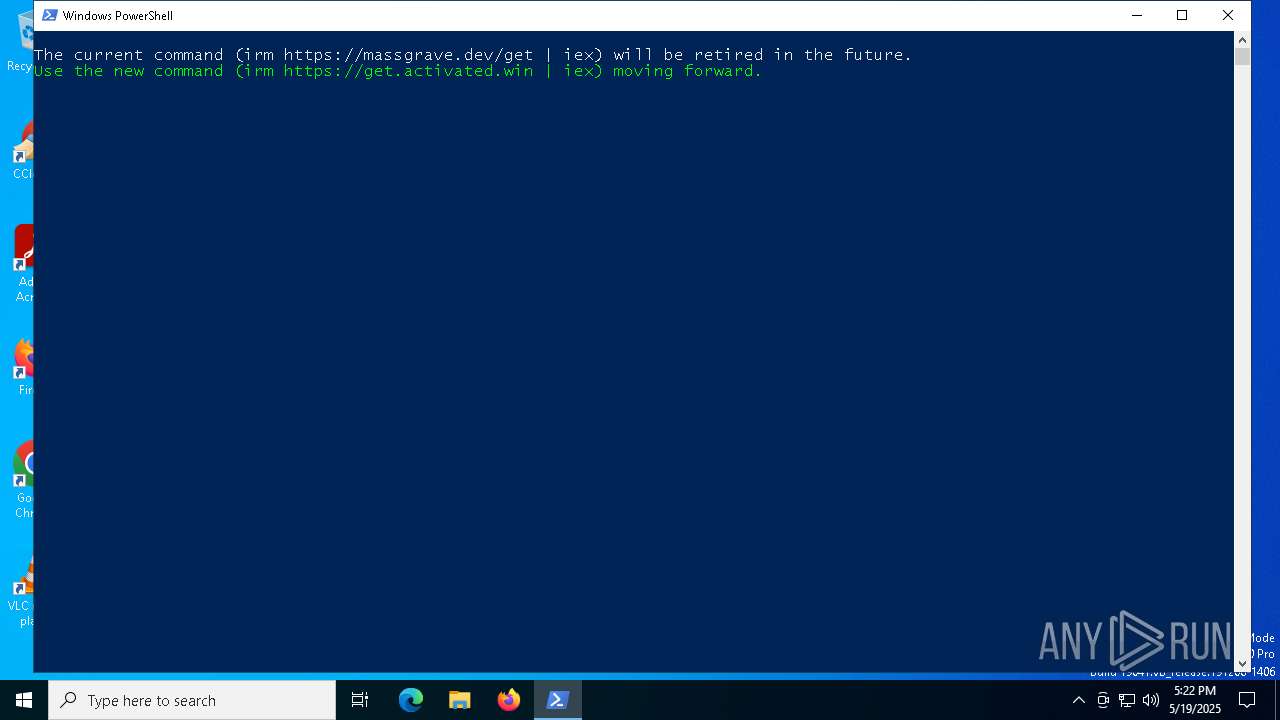
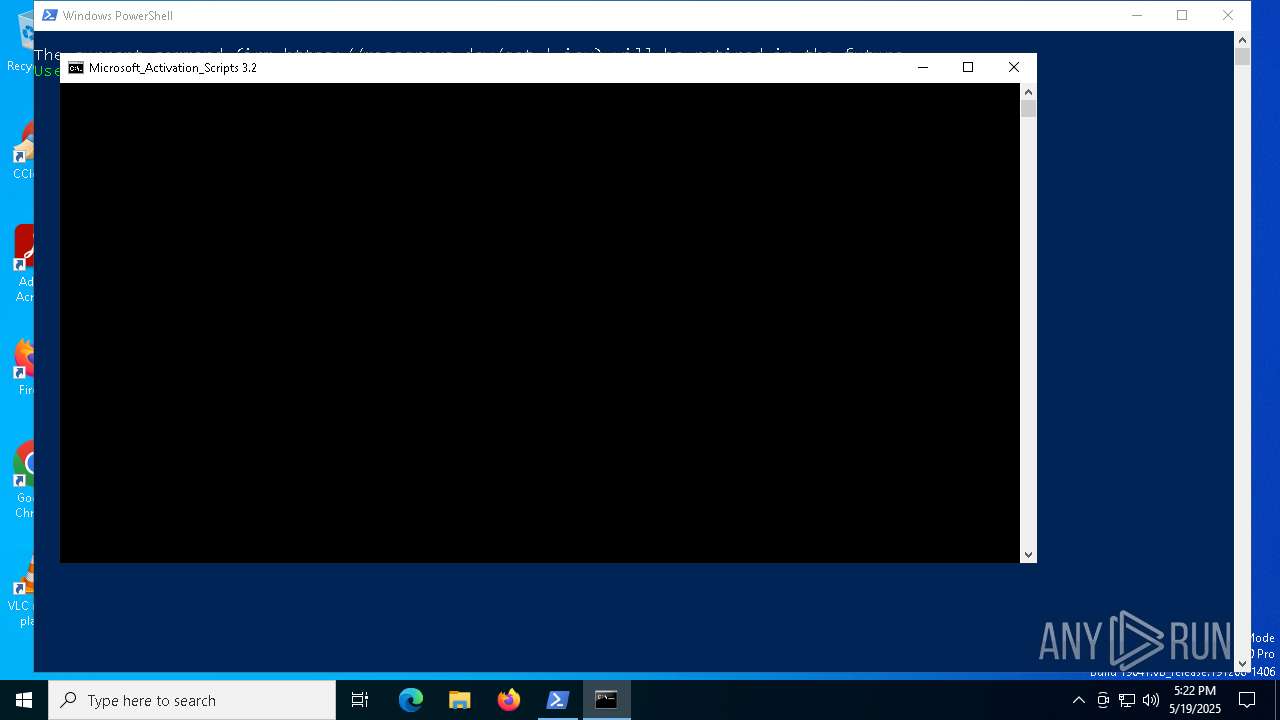
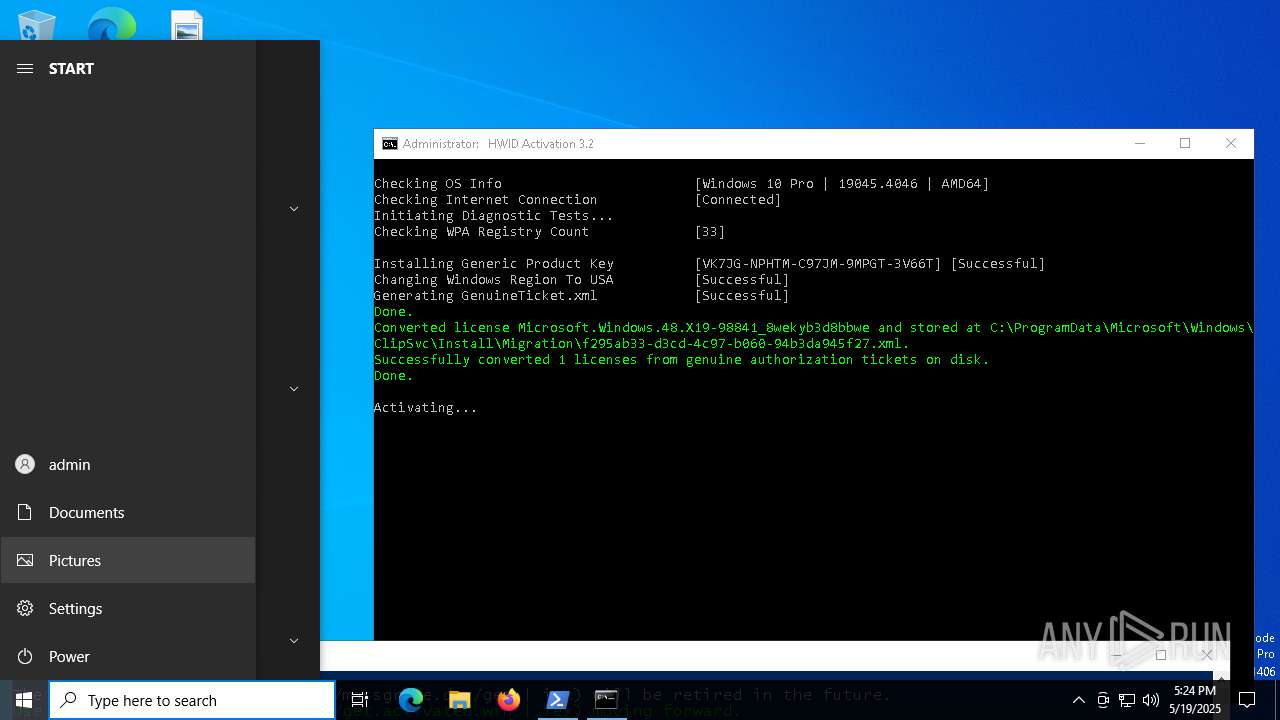
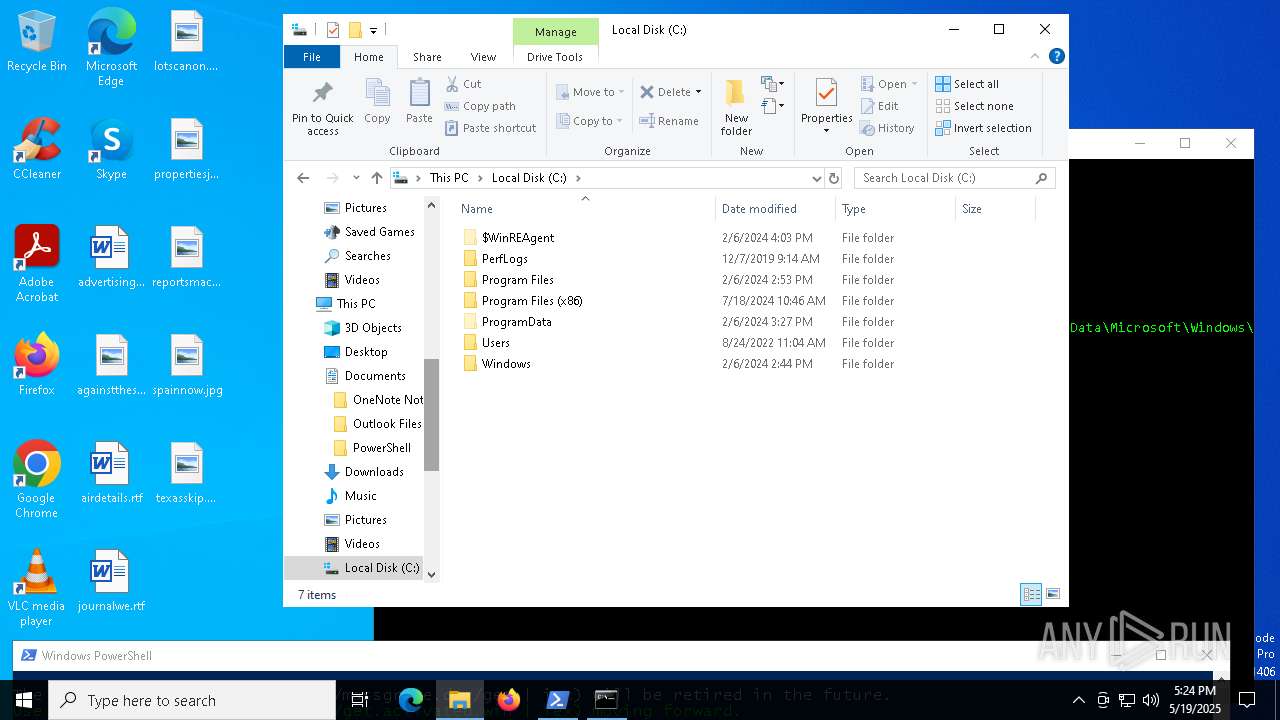
| File name: | massgrave.ps1 |
| Full analysis: | https://app.any.run/tasks/d0bcaf7b-3d43-4c6c-96f0-5477d3340855 |
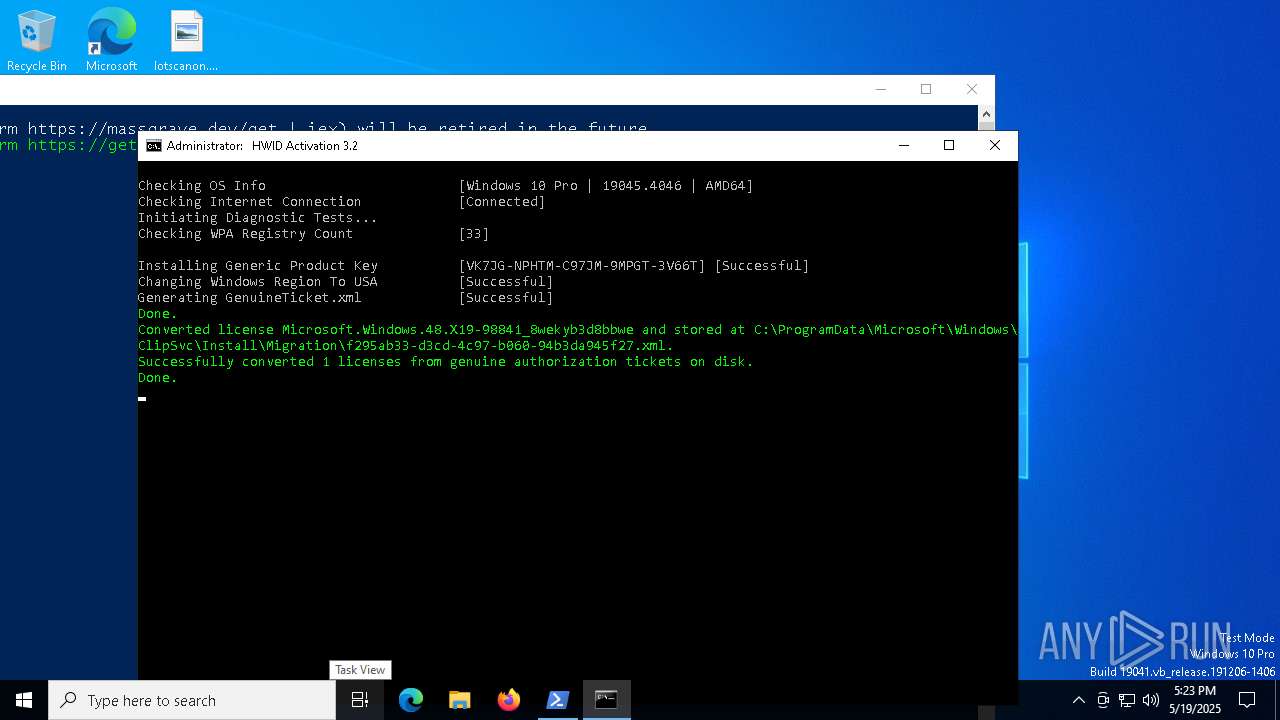
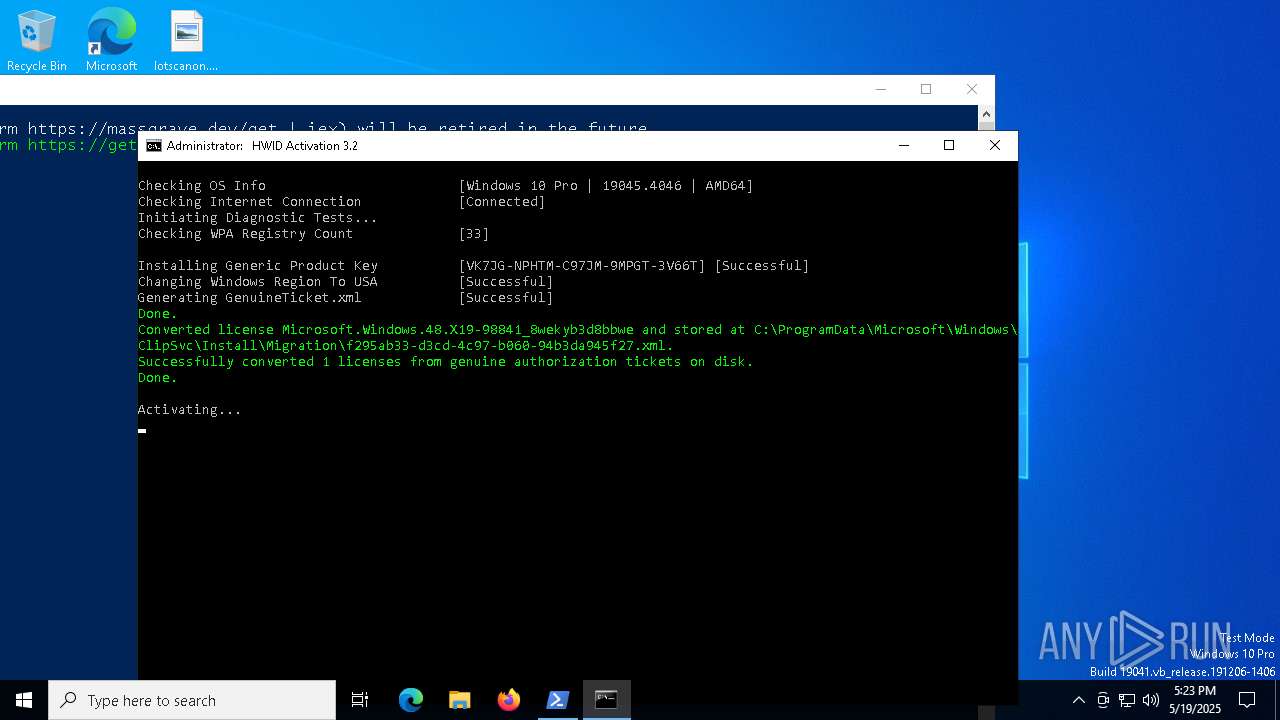
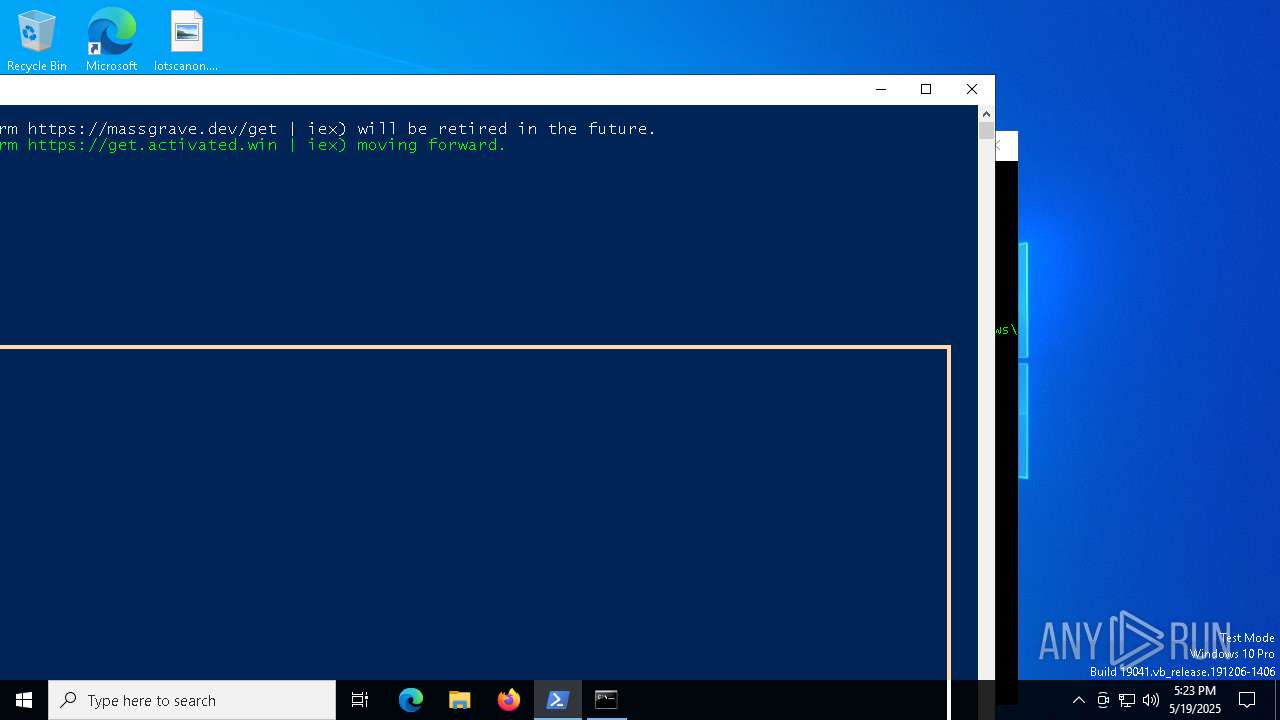
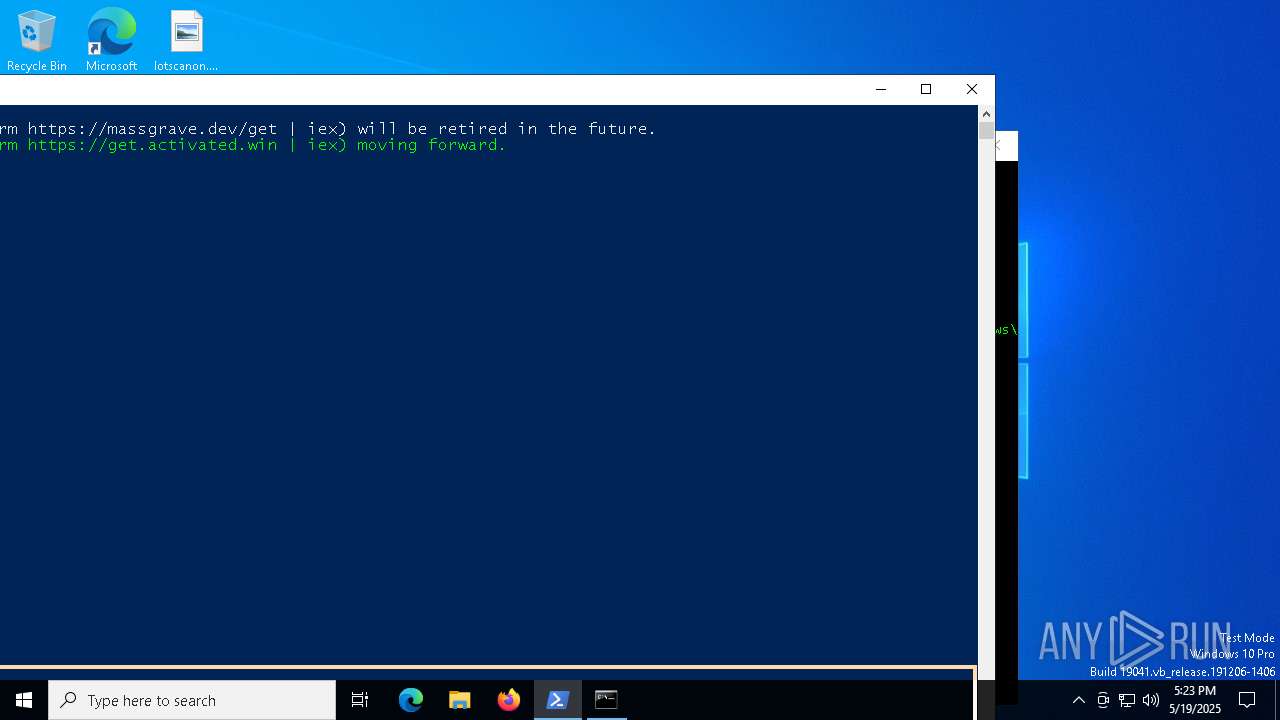
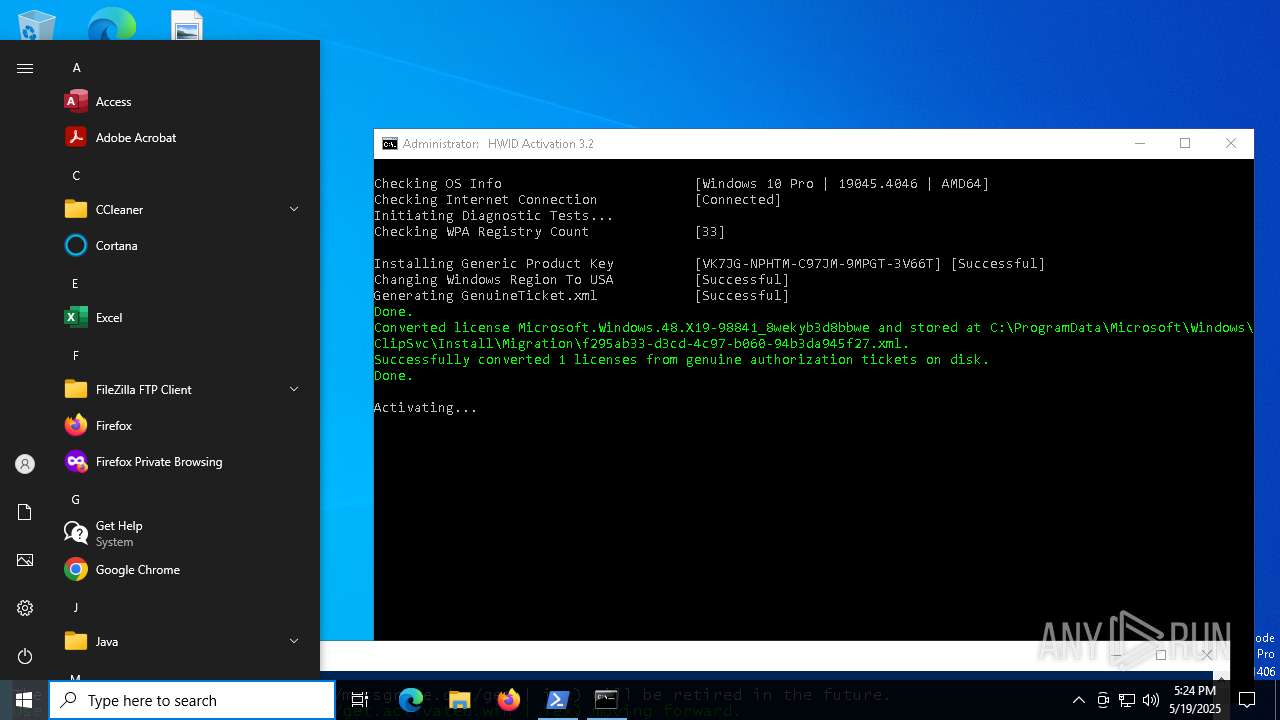
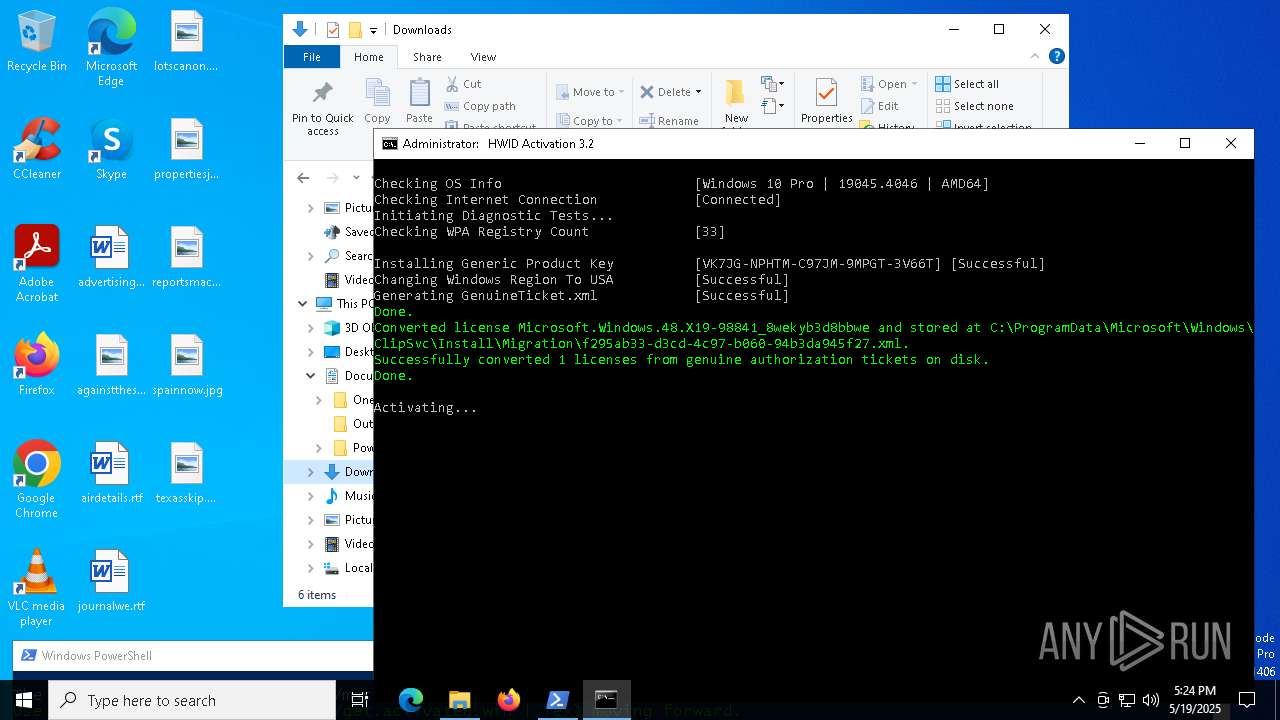
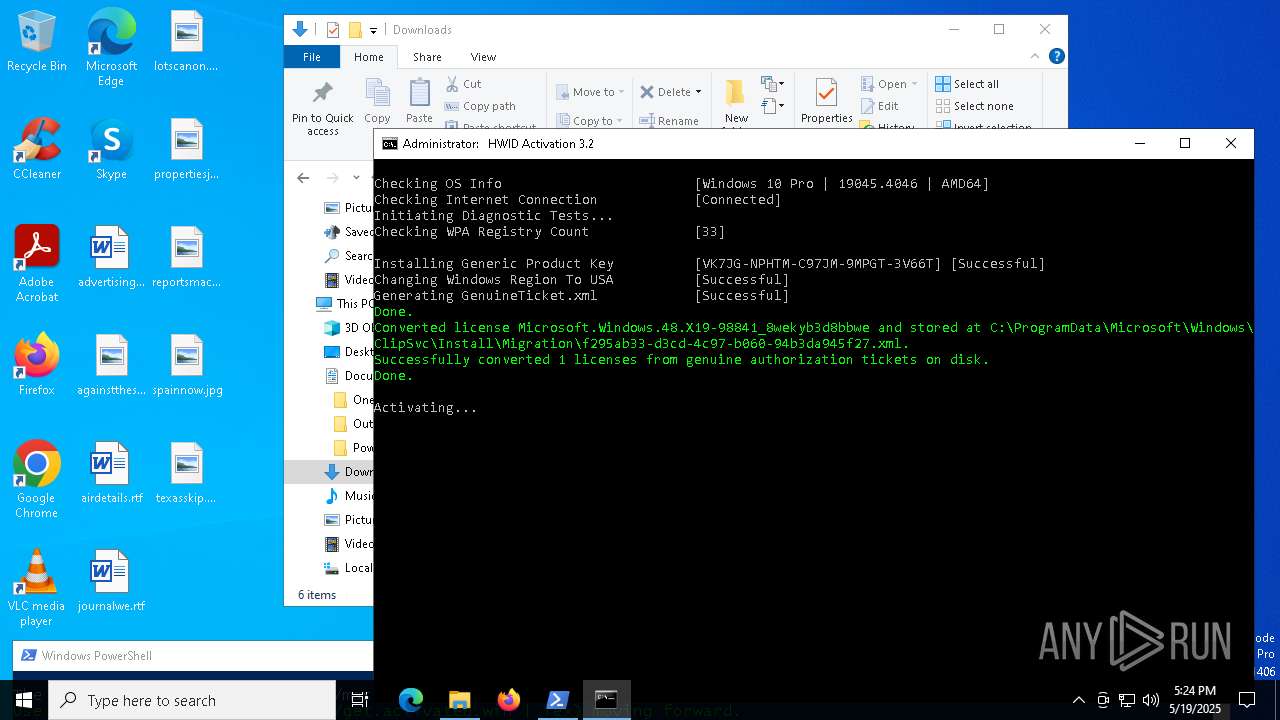
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2025, 17:21:54 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 9BAF9ADBF87C57D97EFD1730B1D37921 |
| SHA1: | 794BF0E8F3535737C9D91DAC3FD4630451C29667 |
| SHA256: | 736B72A9846A1F29B142CB2E3D207EE1C74A5F5F495104B04777F98F2BA1BAB7 |
| SSDEEP: | 96:HKFUuBVkDx+uy6OphNHOSqSSSmQ4S1ABymlkXeQo6CGefWrG/v:qFUOVk1+uyp/7zmQt1ABymlkO7BGE |
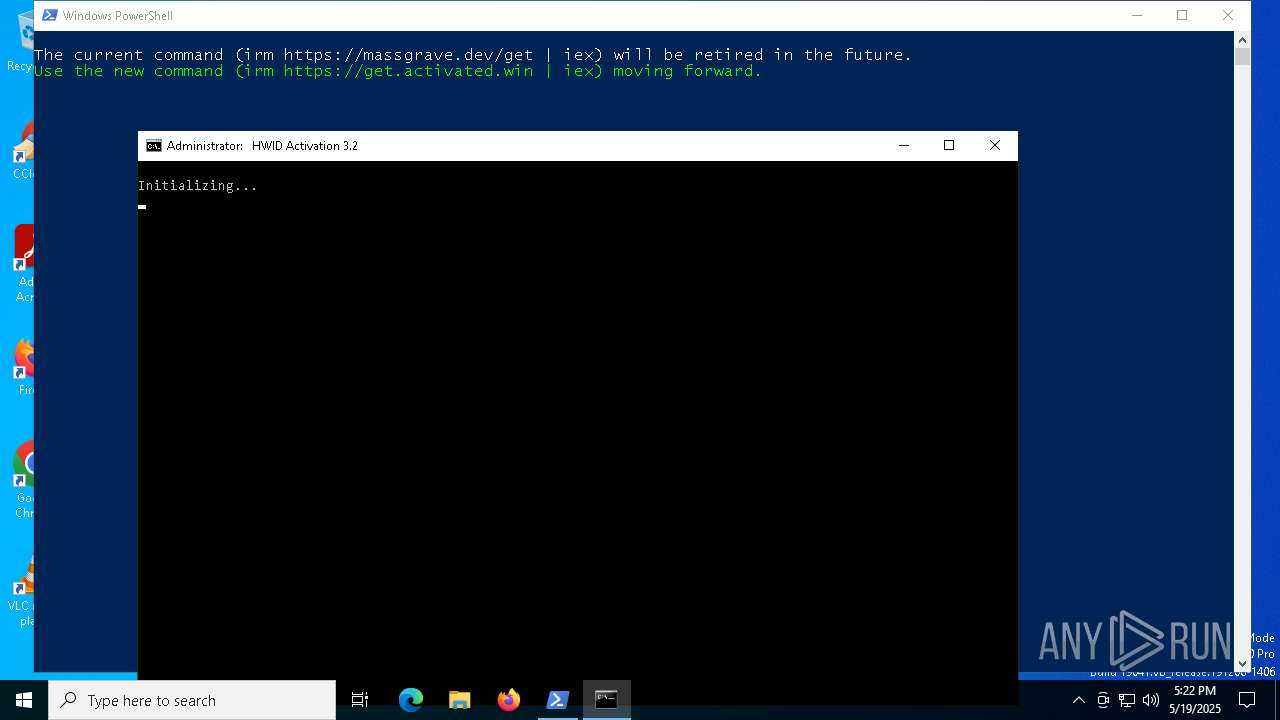
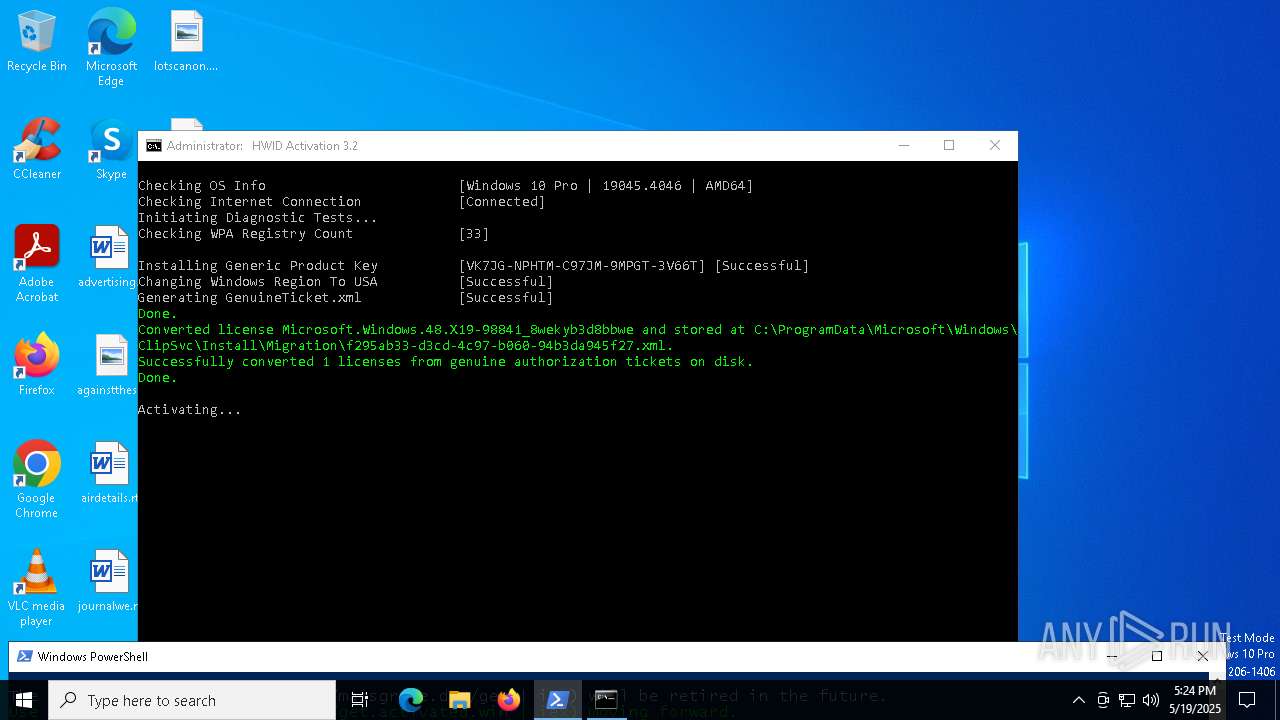
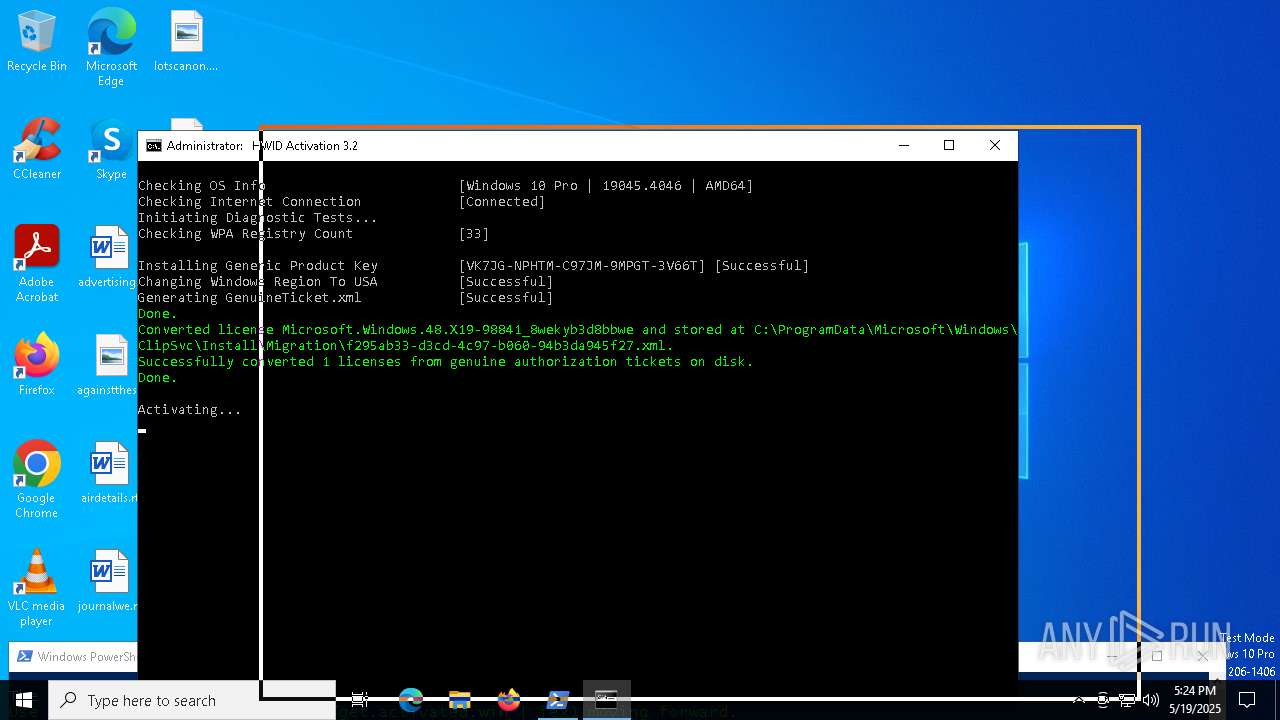
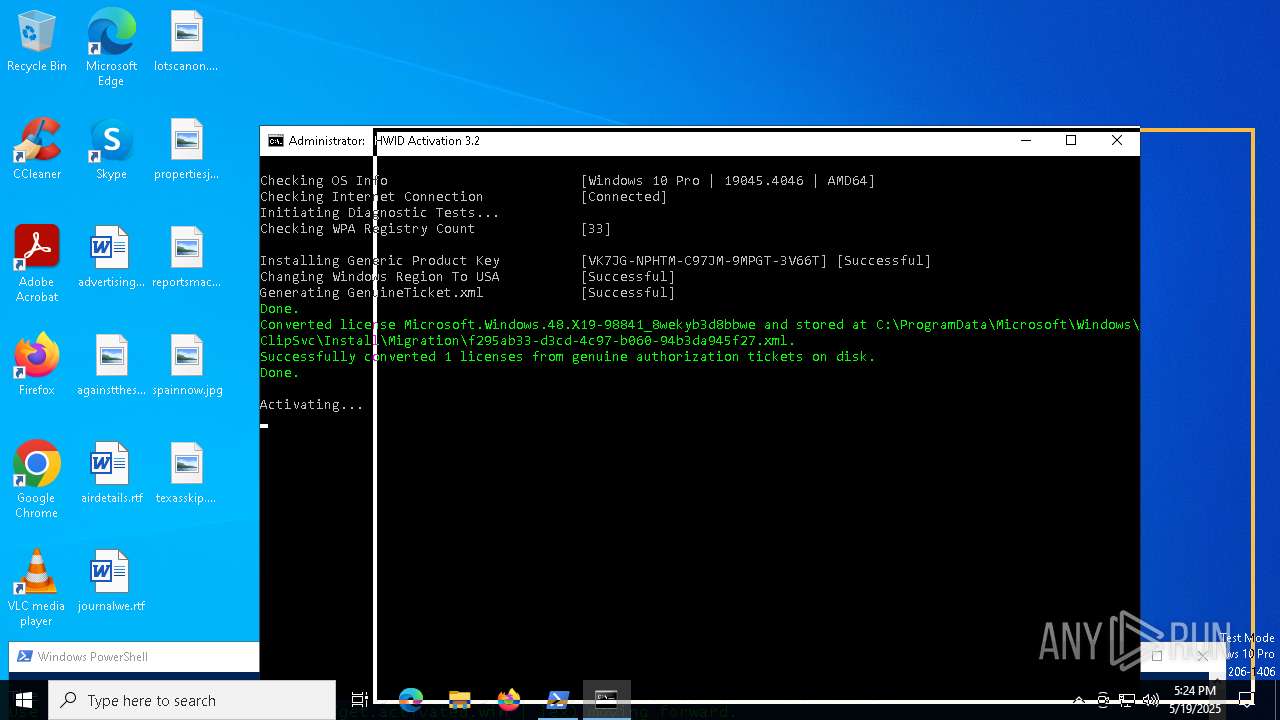
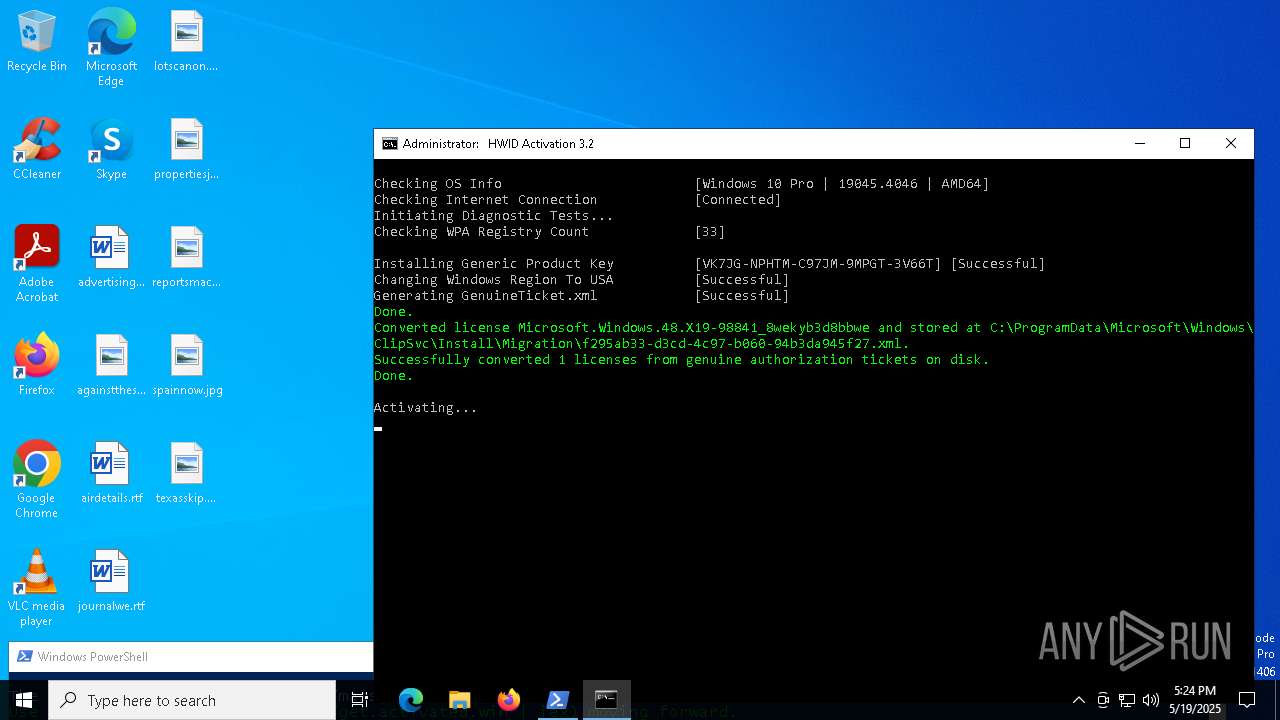
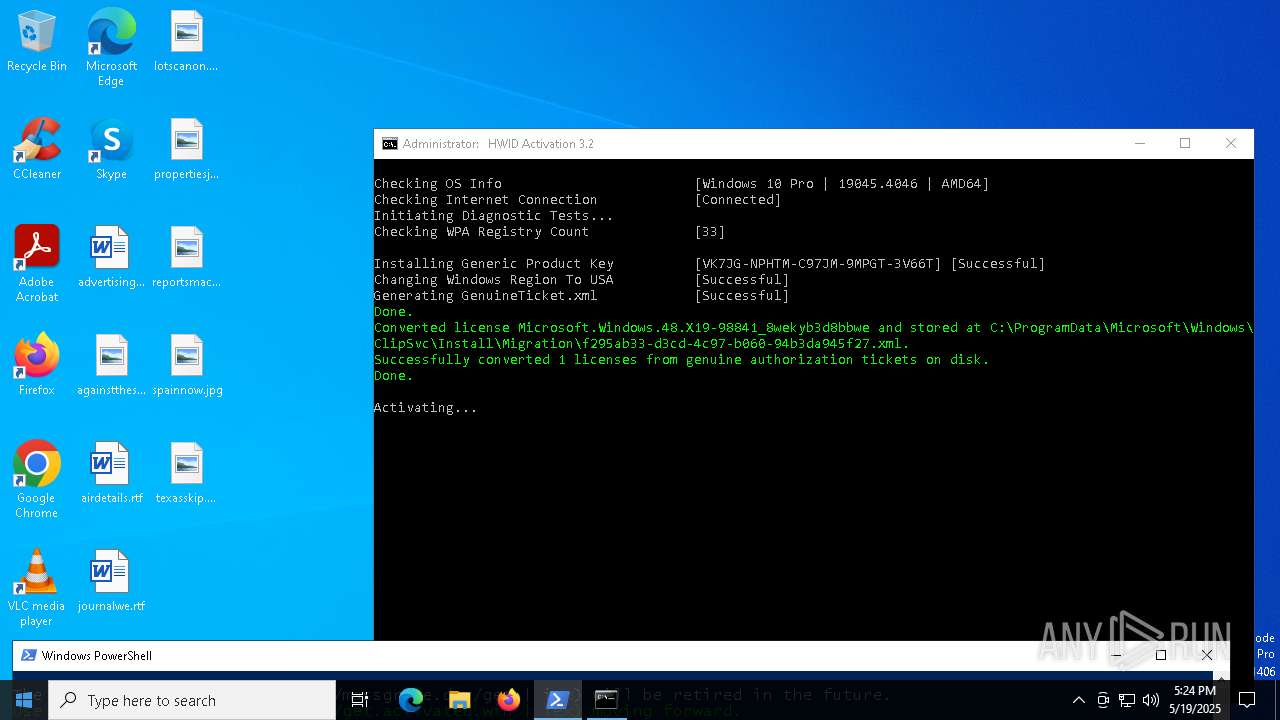
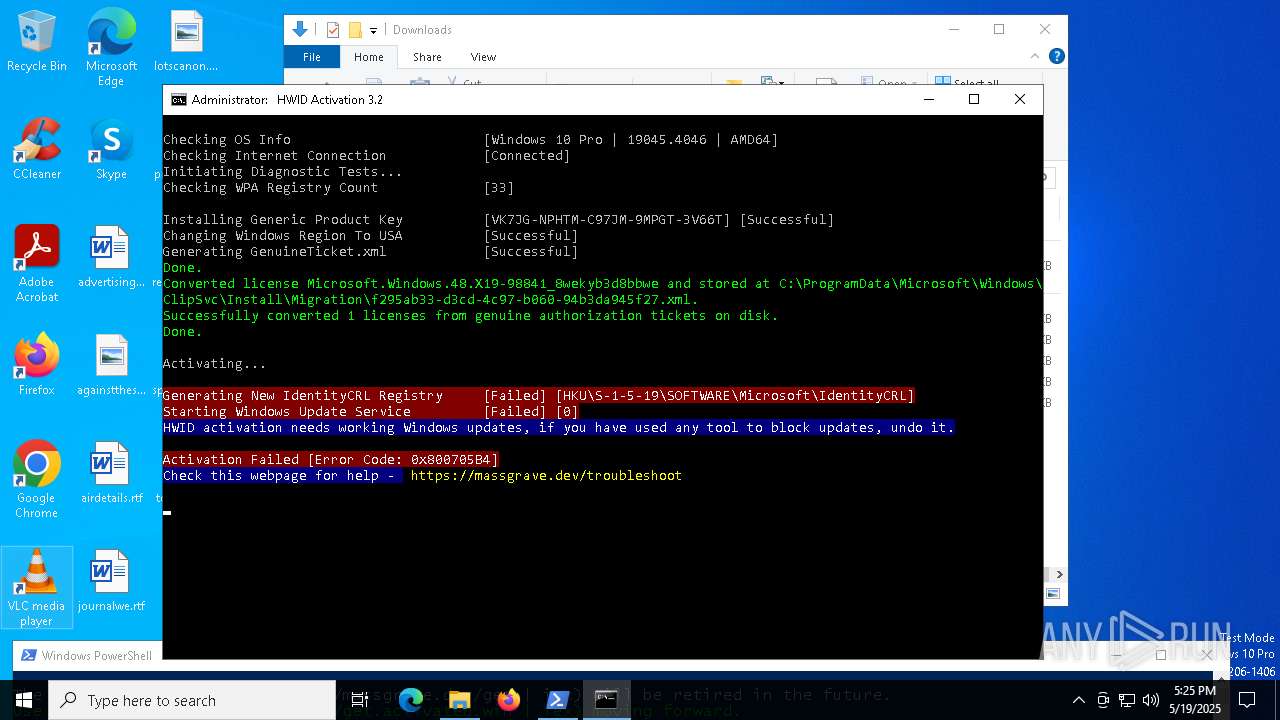
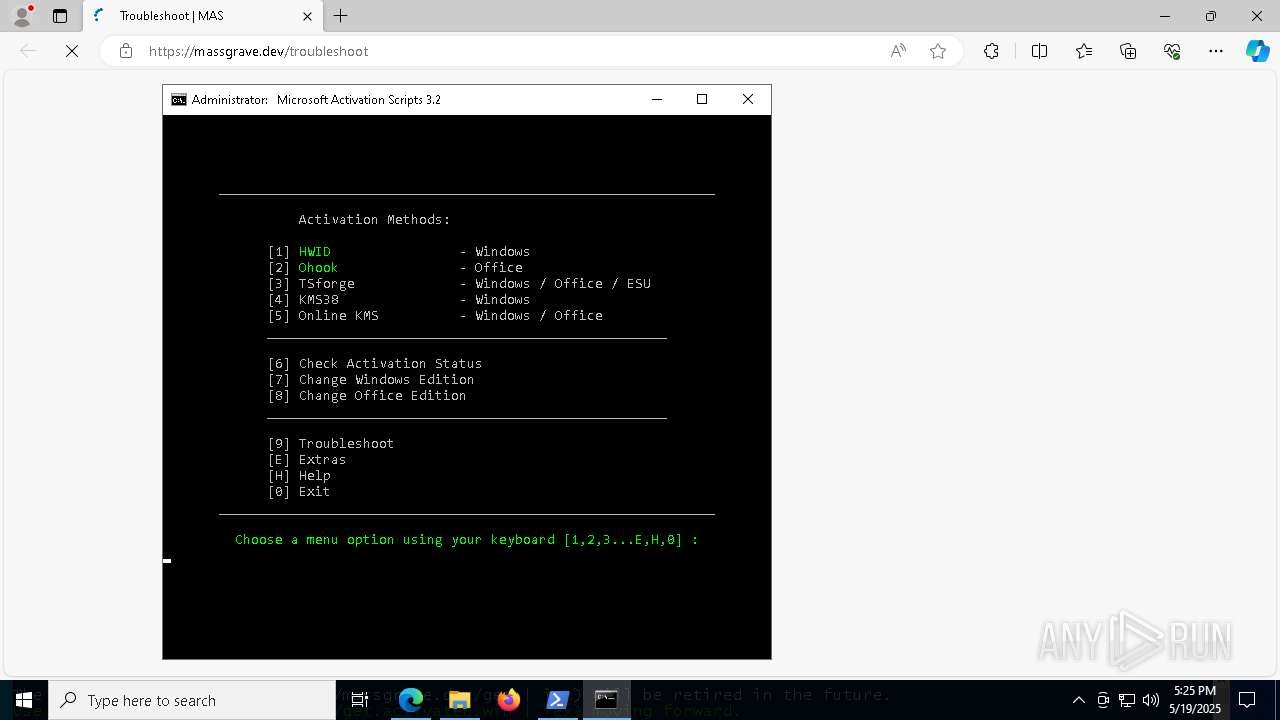
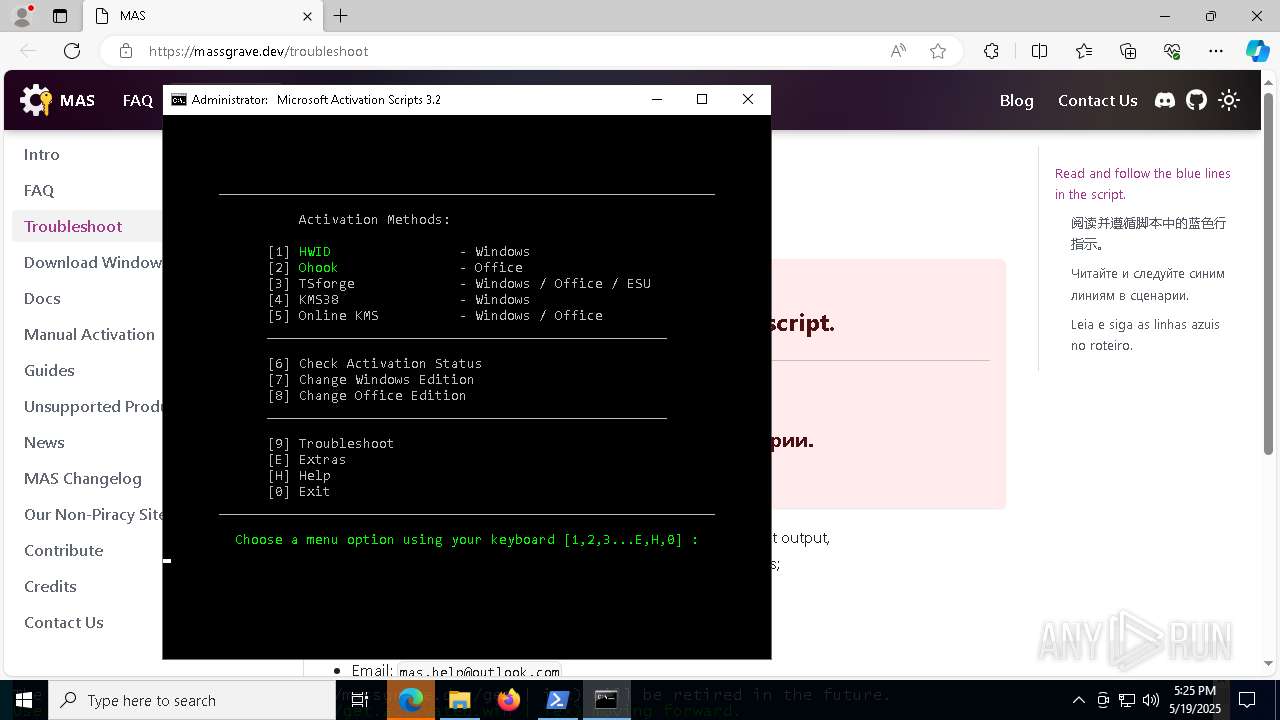
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 2384)
SUSPICIOUS
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2384)
- powershell.exe (PID: 1096)
- powershell.exe (PID: 3268)
- powershell.exe (PID: 872)
- powershell.exe (PID: 2268)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 2384)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 2384)
- powershell.exe (PID: 1096)
- powershell.exe (PID: 3268)
- powershell.exe (PID: 872)
- powershell.exe (PID: 2268)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 2384)
- powershell.exe (PID: 1096)
- powershell.exe (PID: 3268)
- powershell.exe (PID: 872)
- powershell.exe (PID: 2268)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 2384)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 2384)
- cmd.exe (PID: 4976)
- cmd.exe (PID: 2616)
- cmd.exe (PID: 6132)
- cmd.exe (PID: 2268)
- powershell.exe (PID: 4464)
- cmd.exe (PID: 1616)
- cmd.exe (PID: 6080)
Executing commands from ".cmd" file
- powershell.exe (PID: 2384)
- cmd.exe (PID: 6132)
- cmd.exe (PID: 4976)
- powershell.exe (PID: 4464)
- cmd.exe (PID: 1616)
Starts SC.EXE for service management
- cmd.exe (PID: 4976)
- cmd.exe (PID: 6132)
- cmd.exe (PID: 1616)
Windows service management via SC.EXE
- sc.exe (PID: 6700)
- sc.exe (PID: 1184)
- sc.exe (PID: 5436)
- sc.exe (PID: 4724)
- sc.exe (PID: 5360)
- sc.exe (PID: 3240)
- sc.exe (PID: 5776)
- sc.exe (PID: 6516)
- sc.exe (PID: 5544)
- sc.exe (PID: 5392)
- sc.exe (PID: 2664)
- sc.exe (PID: 6644)
- sc.exe (PID: 3268)
- sc.exe (PID: 6960)
- sc.exe (PID: 2432)
- sc.exe (PID: 2664)
- sc.exe (PID: 2096)
- sc.exe (PID: 924)
- sc.exe (PID: 3968)
- sc.exe (PID: 5048)
- sc.exe (PID: 6724)
- sc.exe (PID: 3156)
- sc.exe (PID: 5600)
- sc.exe (PID: 4728)
- sc.exe (PID: 872)
- sc.exe (PID: 2332)
- sc.exe (PID: 6940)
- sc.exe (PID: 3024)
- sc.exe (PID: 3888)
- sc.exe (PID: 5116)
- sc.exe (PID: 4724)
- sc.exe (PID: 3828)
- sc.exe (PID: 1388)
- sc.exe (PID: 5936)
- sc.exe (PID: 1132)
- sc.exe (PID: 6760)
- sc.exe (PID: 5384)
- sc.exe (PID: 672)
- sc.exe (PID: 616)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 4976)
- cmd.exe (PID: 6132)
- cmd.exe (PID: 1616)
Application launched itself
- cmd.exe (PID: 4976)
- cmd.exe (PID: 2616)
- cmd.exe (PID: 2268)
- cmd.exe (PID: 6132)
- cmd.exe (PID: 1616)
- cmd.exe (PID: 6080)
- powershell.exe (PID: 3132)
- powershell.exe (PID: 3888)
- ClipUp.exe (PID: 5544)
- powershell.exe (PID: 6980)
- powershell.exe (PID: 1096)
- powershell.exe (PID: 6028)
- powershell.exe (PID: 5964)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4976)
- cmd.exe (PID: 5360)
- cmd.exe (PID: 1324)
- cmd.exe (PID: 6184)
- cmd.exe (PID: 1616)
- cmd.exe (PID: 3240)
- powershell.exe (PID: 3132)
- cmd.exe (PID: 7156)
- cmd.exe (PID: 1012)
- cmd.exe (PID: 2552)
- powershell.exe (PID: 3888)
- cmd.exe (PID: 2852)
- powershell.exe (PID: 6028)
- powershell.exe (PID: 6980)
- powershell.exe (PID: 1096)
- powershell.exe (PID: 5964)
Executes script without checking the security policy
- powershell.exe (PID: 4464)
- powershell.exe (PID: 1096)
- powershell.exe (PID: 3268)
- powershell.exe (PID: 6584)
- powershell.exe (PID: 872)
- powershell.exe (PID: 4380)
- powershell.exe (PID: 3132)
- powershell.exe (PID: 2268)
- powershell.exe (PID: 1280)
- powershell.exe (PID: 5680)
- powershell.exe (PID: 1760)
- powershell.exe (PID: 3888)
- powershell.exe (PID: 7100)
- powershell.exe (PID: 7152)
- powershell.exe (PID: 5176)
- powershell.exe (PID: 3032)
- powershell.exe (PID: 5116)
- powershell.exe (PID: 6072)
- powershell.exe (PID: 6028)
- powershell.exe (PID: 6980)
- powershell.exe (PID: 1096)
- powershell.exe (PID: 2064)
- powershell.exe (PID: 5436)
- powershell.exe (PID: 6136)
- powershell.exe (PID: 5964)
- powershell.exe (PID: 2904)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 5360)
- cmd.exe (PID: 4976)
- cmd.exe (PID: 1324)
- cmd.exe (PID: 6184)
- cmd.exe (PID: 1616)
- cmd.exe (PID: 3240)
- powershell.exe (PID: 3132)
- cmd.exe (PID: 7156)
- cmd.exe (PID: 1012)
- cmd.exe (PID: 2552)
- powershell.exe (PID: 3888)
- cmd.exe (PID: 2852)
- powershell.exe (PID: 6028)
- powershell.exe (PID: 6980)
- powershell.exe (PID: 1096)
- powershell.exe (PID: 5964)
Hides command output
- cmd.exe (PID: 5360)
- cmd.exe (PID: 1324)
- cmd.exe (PID: 6228)
- cmd.exe (PID: 2344)
- cmd.exe (PID: 7156)
- cmd.exe (PID: 4380)
- cmd.exe (PID: 4724)
- cmd.exe (PID: 5772)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 1012)
- cmd.exe (PID: 4220)
- cmd.exe (PID: 4284)
- cmd.exe (PID: 1328)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 5360)
- cmd.exe (PID: 1324)
- cmd.exe (PID: 1616)
- cmd.exe (PID: 7156)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 5360)
- cmd.exe (PID: 1324)
- cmd.exe (PID: 1616)
- cmd.exe (PID: 3240)
- cmd.exe (PID: 7156)
- cmd.exe (PID: 2852)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6132)
- cmd.exe (PID: 1616)
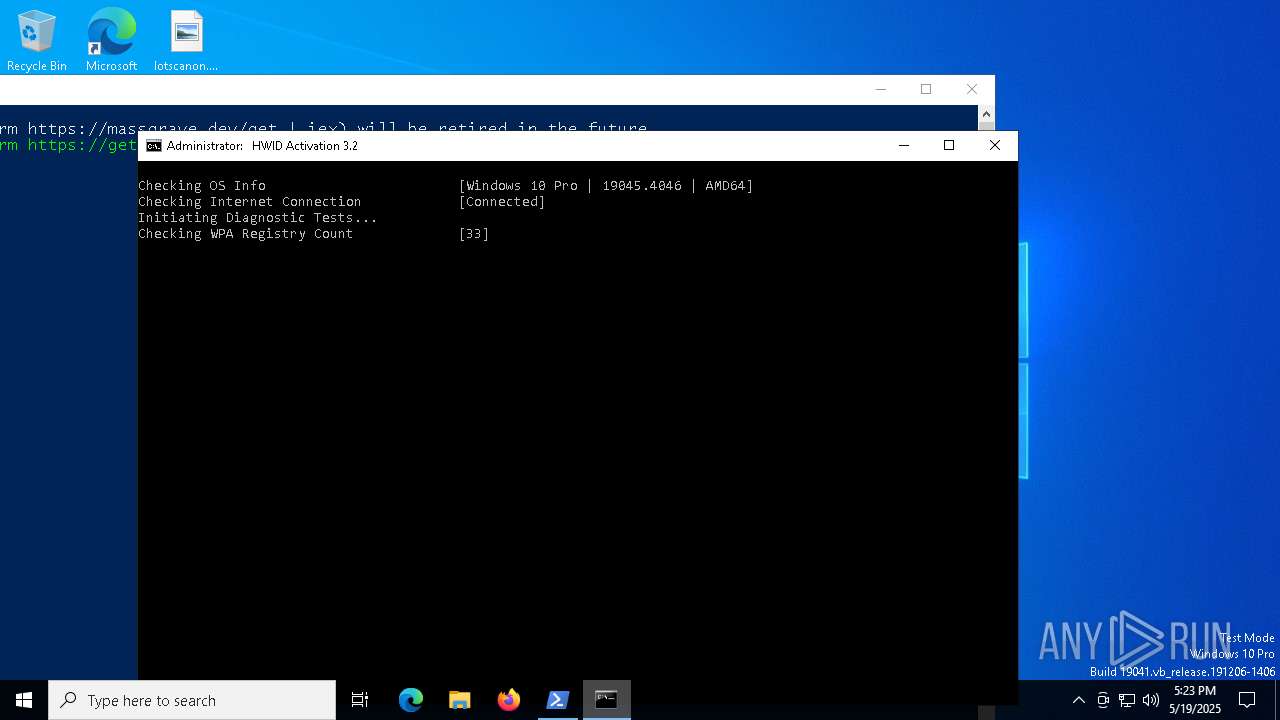
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 2344)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 4120)
- cmd.exe (PID: 1616)
Probably file/command deobfuscation
- cmd.exe (PID: 3240)
- cmd.exe (PID: 2852)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 3132)
- powershell.exe (PID: 3888)
- powershell.exe (PID: 6028)
- powershell.exe (PID: 6980)
- powershell.exe (PID: 1096)
- powershell.exe (PID: 5964)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 1616)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 5772)
- cmd.exe (PID: 4220)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 1616)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 1616)
Executes application which crashes
- powershell.exe (PID: 6576)
Process uses IPCONFIG to clear DNS cache
- cmd.exe (PID: 1616)
INFO
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 2384)
- powershell.exe (PID: 1096)
- powershell.exe (PID: 3268)
- powershell.exe (PID: 872)
- powershell.exe (PID: 2268)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 2384)
- powershell.exe (PID: 1096)
- powershell.exe (PID: 3268)
- powershell.exe (PID: 872)
- powershell.exe (PID: 2268)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 2384)
- powershell.exe (PID: 1096)
- powershell.exe (PID: 3268)
- powershell.exe (PID: 872)
- powershell.exe (PID: 2268)
Checks proxy server information
- powershell.exe (PID: 2384)
Disables trace logs
- powershell.exe (PID: 2384)
Checks operating system version
- cmd.exe (PID: 4976)
- cmd.exe (PID: 6132)
- cmd.exe (PID: 1616)
Checks supported languages
- mode.com (PID: 5392)
- mode.com (PID: 6676)
- mode.com (PID: 6644)
- mode.com (PID: 208)
Starts MODE.COM to configure console settings
- mode.com (PID: 5392)
- mode.com (PID: 6676)
- mode.com (PID: 208)
- mode.com (PID: 6644)
- mode.com (PID: 616)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 6676)
- WMIC.exe (PID: 6728)
- WMIC.exe (PID: 2240)
- WMIC.exe (PID: 6268)
- WMIC.exe (PID: 6712)
- WMIC.exe (PID: 5036)
- WMIC.exe (PID: 672)
Reads the software policy settings
- slui.exe (PID: 1272)
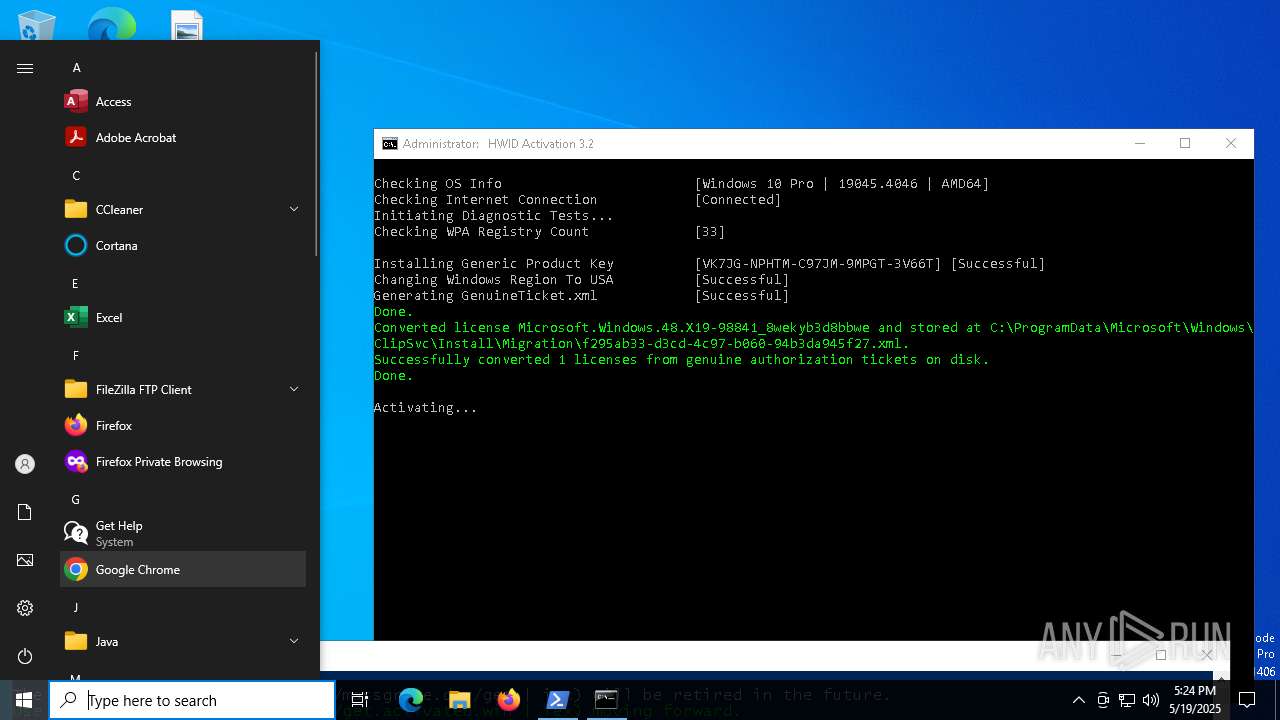
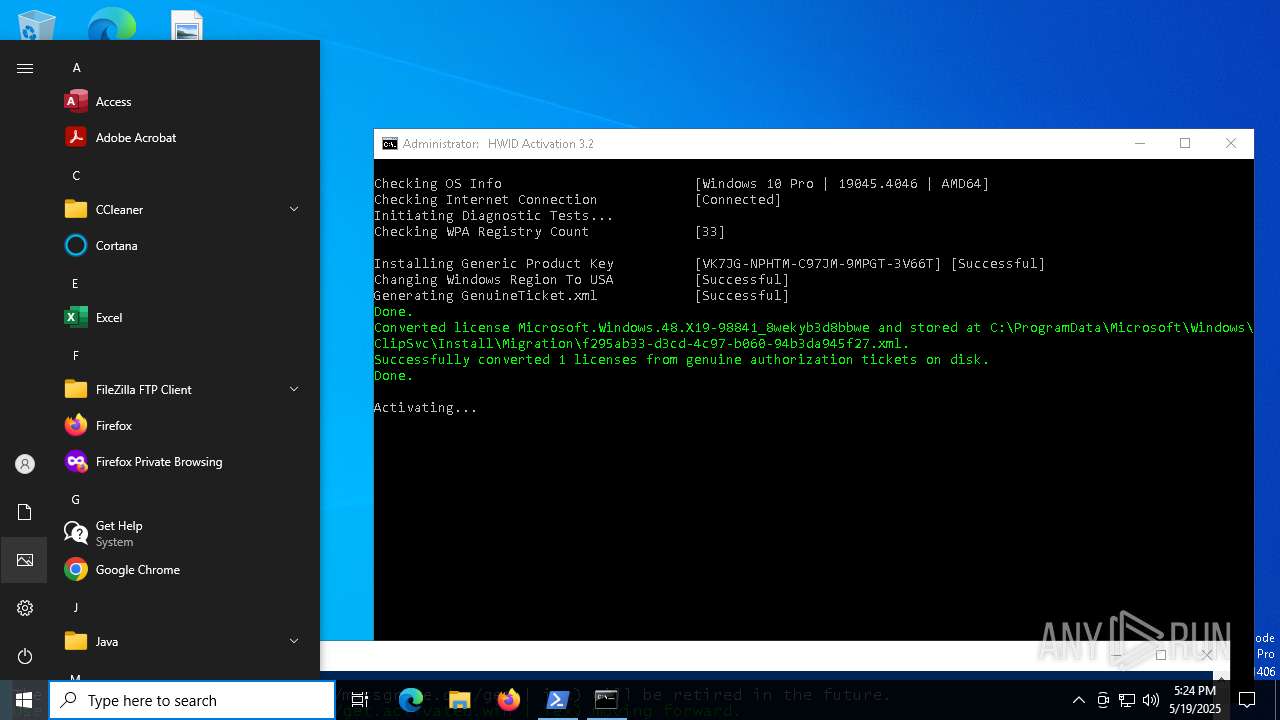
Manual execution by a user
- msedge.exe (PID: 5204)
Application launched itself
- msedge.exe (PID: 728)
- msedge.exe (PID: 5204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
516
Monitored processes
368
Malicious processes
10
Suspicious processes
11
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | reg query HKLM\SYSTEM\CurrentControlSet\Services\wuauserv /v DisplayName | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | find /i "ARM64" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | mode 76, 34 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | find /i "Ready" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | timeout /t 2 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | find /i "RUNNING" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform" /v "SkipRearm" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | sc query wuauserv | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | mode 76, 34 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
166 357
Read events
166 297
Write events
50
Delete events
10
Modification events
| (PID) Process: | (1760) powershell.exe | Key: | HKEY_CURRENT_USER\Control Panel\International\Geo |
| Operation: | write | Name: | Name |
Value: US | |||
| (PID) Process: | (1760) powershell.exe | Key: | HKEY_CURRENT_USER\Control Panel\International\Geo |
| Operation: | write | Name: | Nation |
Value: 244 | |||
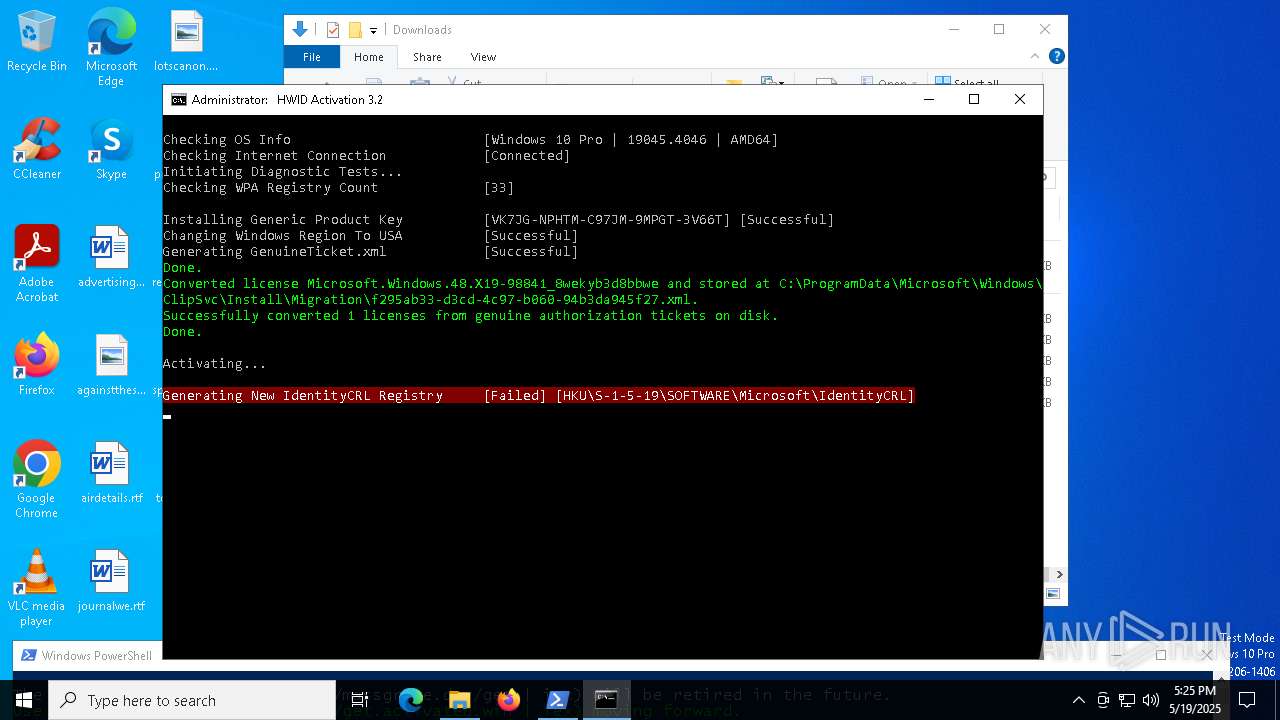
| (PID) Process: | (4700) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\ExtendedProperties |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4700) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\Immersive\production\Property |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4700) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\Immersive\production\Token\{D6D5A677-0872-4AB0-9442-BB792FCE85C5} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4700) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\Immersive\production\Token |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4700) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\Immersive\production |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4700) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\Immersive |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4700) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6940) WerFault.exe | Key: | \REGISTRY\A\{cb3f6878-c91f-cef7-2790-3cd305a5d3f6}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
Executable files
5
Suspicious files
55
Text files
99
Unknown types
0
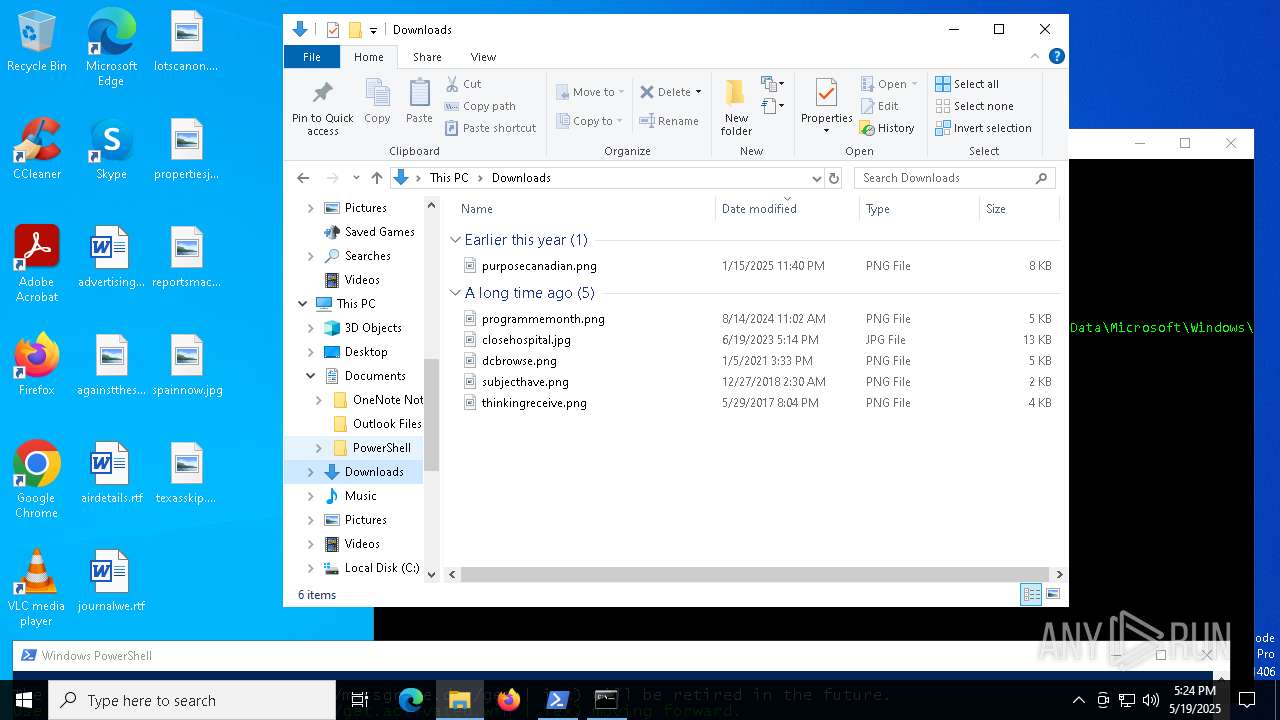
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2384 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qqckkf2f.ads.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2384 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10b6fd.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 2384 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:CEF05BA648DCBC61BAB8B09B767FF872 | SHA256:C52F269DB5DDCE7A02CF81B1F690B4B61ABA033E1C522788CE5A31BD86C65CEE | |||
| 2384 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\G7X6XA5T2YV4BPW1XNQP.temp | binary | |
MD5:CEF05BA648DCBC61BAB8B09B767FF872 | SHA256:C52F269DB5DDCE7A02CF81B1F690B4B61ABA033E1C522788CE5A31BD86C65CEE | |||
| 4464 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bvrjrdmn.142.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2384 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_rfydpzz5.zgz.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1096 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_brt0y1vs.4p4.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4464 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:27C7DD2942AD33EE0AE4F6E946570644 | SHA256:32C195150A58BFDDE9CE17845429F869EE43F254D7EAFB4F9035F010B4EE2BF9 | |||
| 1096 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_3hgtzk2p.hel.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3268 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ycocgint.tnb.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
51
DNS requests
70
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.20.154.94:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.20.154.94:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.18.121.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 2.20.154.94:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 2.18.121.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.18.121.147:80 | crl.microsoft.com | AKAMAI-AS | FR | whitelisted |
2104 | svchost.exe | 2.18.121.147:80 | crl.microsoft.com | AKAMAI-AS | FR | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.20.154.94:80 | www.microsoft.com | Telkom-Internet | ZA | whitelisted |
— | — | 2.20.154.94:80 | www.microsoft.com | Telkom-Internet | ZA | whitelisted |
2104 | svchost.exe | 2.20.154.94:80 | www.microsoft.com | Telkom-Internet | ZA | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
dev.azure.com |
| whitelisted |
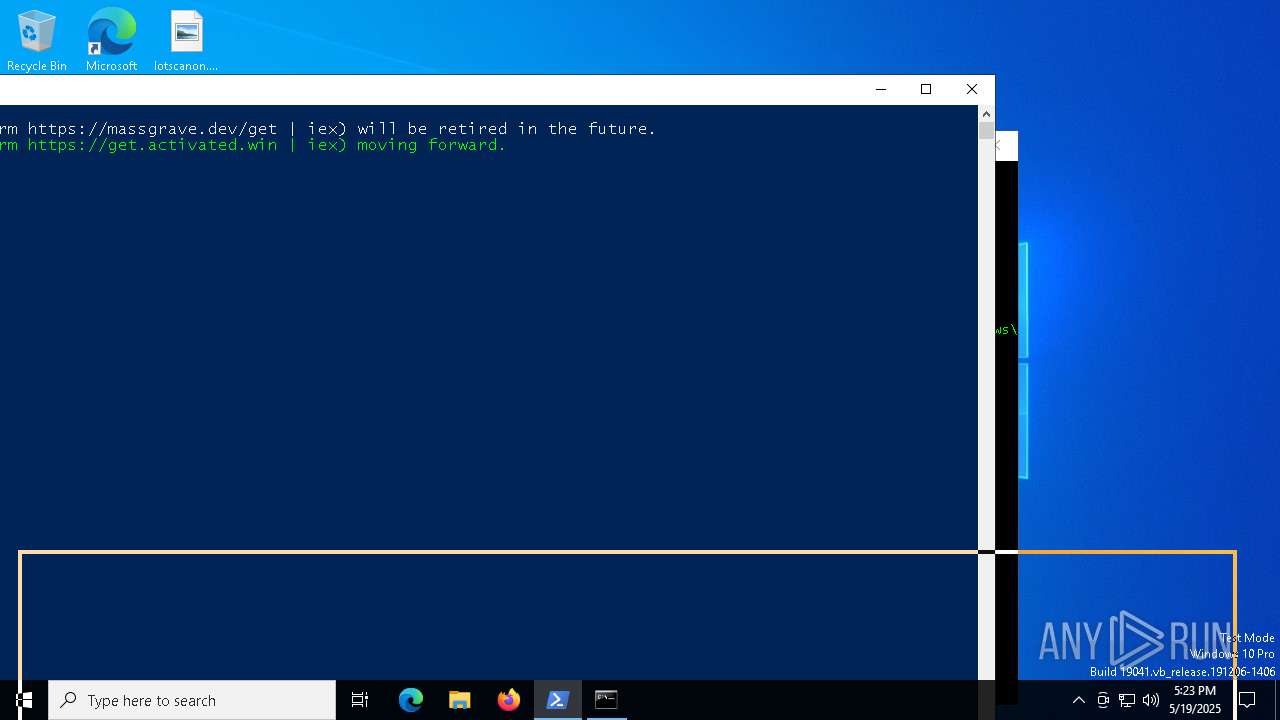
activated.win |
| unknown |
updatecheck32.activated.win |
| unknown |
l.root-servers.net |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |