| download: | cool-android-recovery.exe |
| Full analysis: | https://app.any.run/tasks/5f3c3971-2249-4cd3-9d13-b301555a877f |
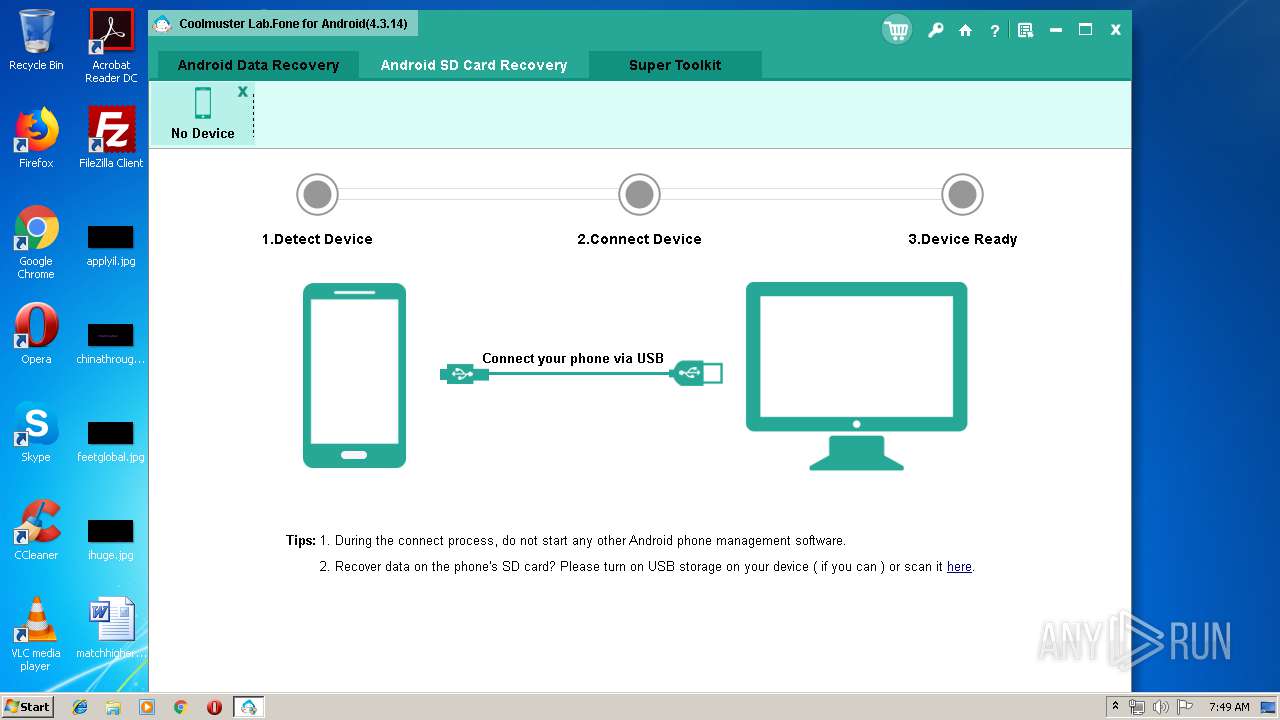
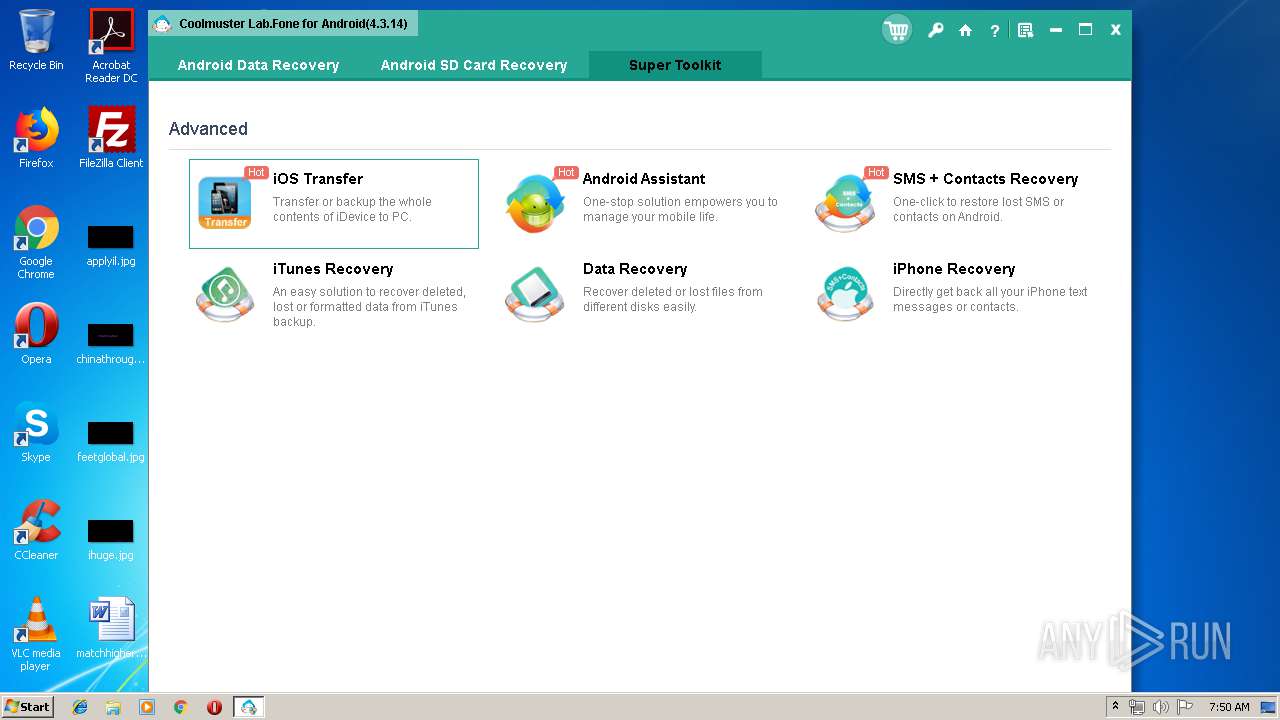
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 06:48:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 06EAE3976F2FE5D0624F007411A36C5A |
| SHA1: | D655D4653FC7CFFFF69D49CA5AD2DC2B6ADB182C |
| SHA256: | 73433DC8BD8A6C741225366CE91F8BCC3280B6D81F5D3FBDE1580385DD7B3A52 |
| SSDEEP: | 393216:B5TXyXxiNHuAjuL8WEq4vu0BaSEejQam1b+fnNSQDsKIBv:B5DyXxiNHRSL8zv5saZnNSRKIx |
MALICIOUS
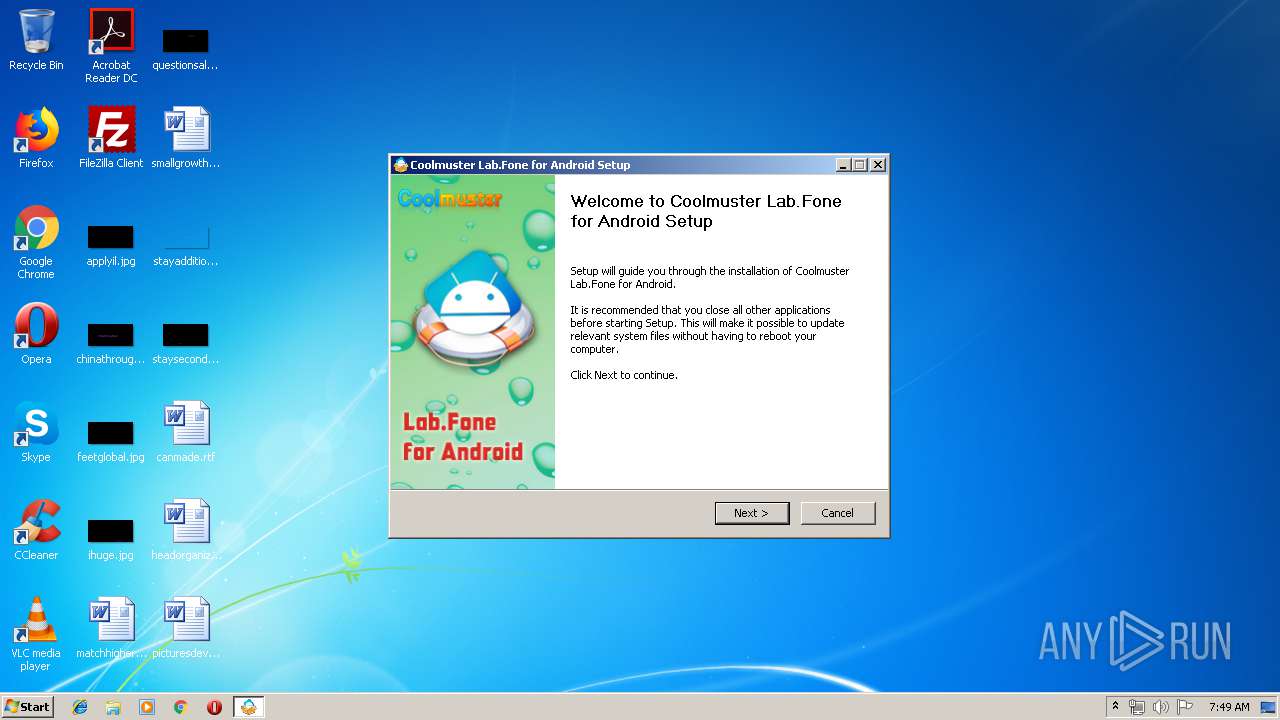
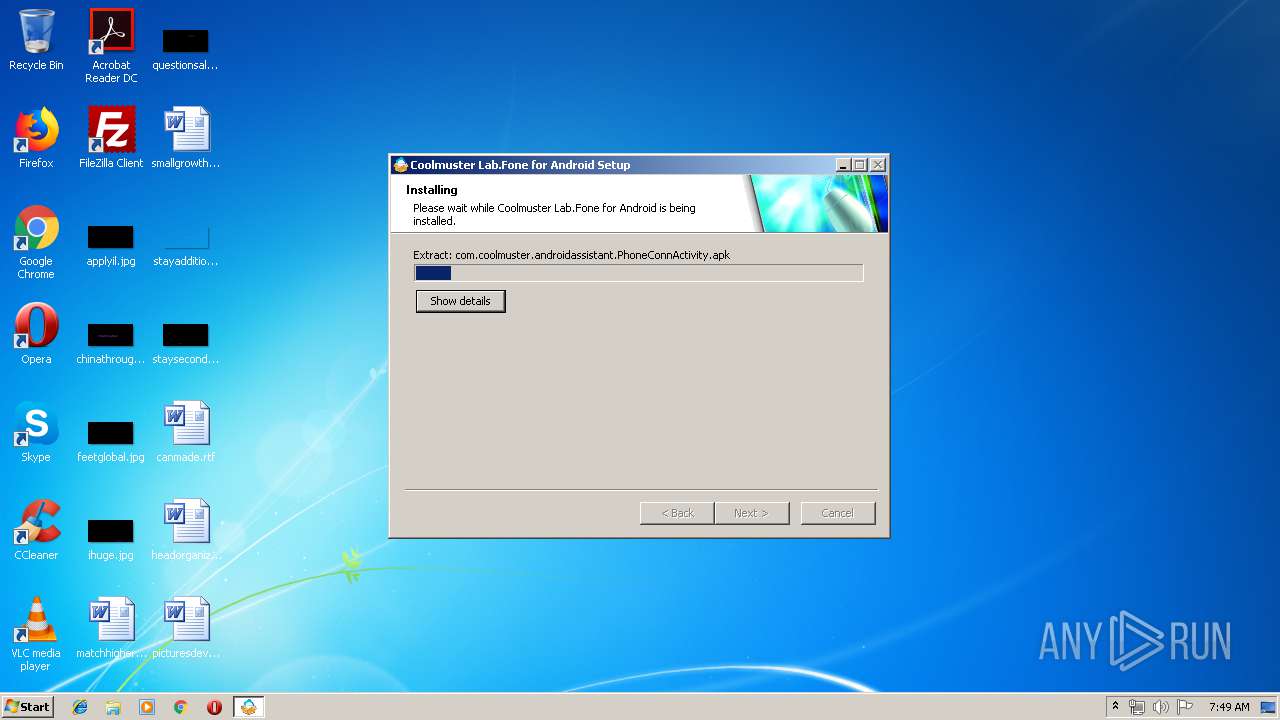
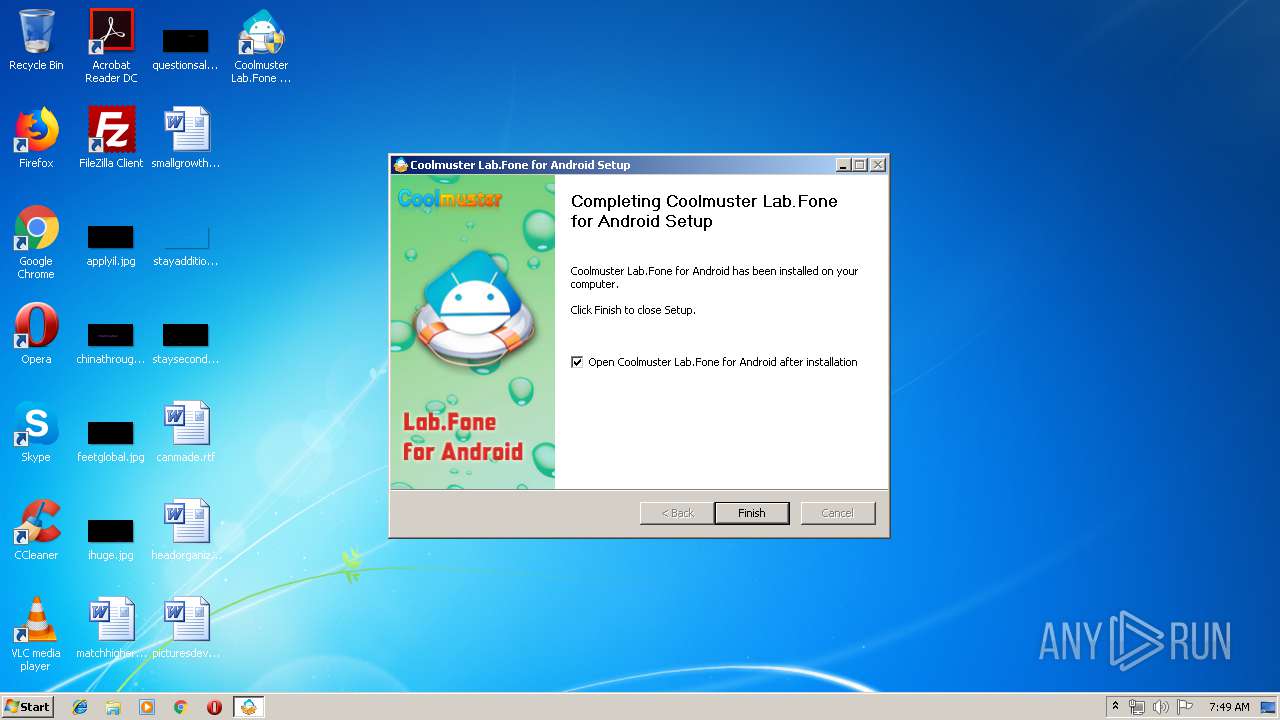
Loads dropped or rewritten executable
- cool-android-recovery.exe (PID: 3632)
- Coolmuster Lab.Fone for Android.exe (PID: 2764)
- adb.exe (PID: 2800)
- AndroidAssistServer.exe (PID: 2256)
- adb.exe (PID: 2404)
- adb.exe (PID: 3196)
Application was dropped or rewritten from another process
- Coolmuster Lab.Fone for Android.exe (PID: 2764)
- AndroidAssistServer.exe (PID: 2256)
- adb.exe (PID: 2800)
- adb.exe (PID: 2404)
- adb.exe (PID: 3196)
SUSPICIOUS
Executable content was dropped or overwritten
- cool-android-recovery.exe (PID: 3632)
- AndroidAssistServer.exe (PID: 2256)
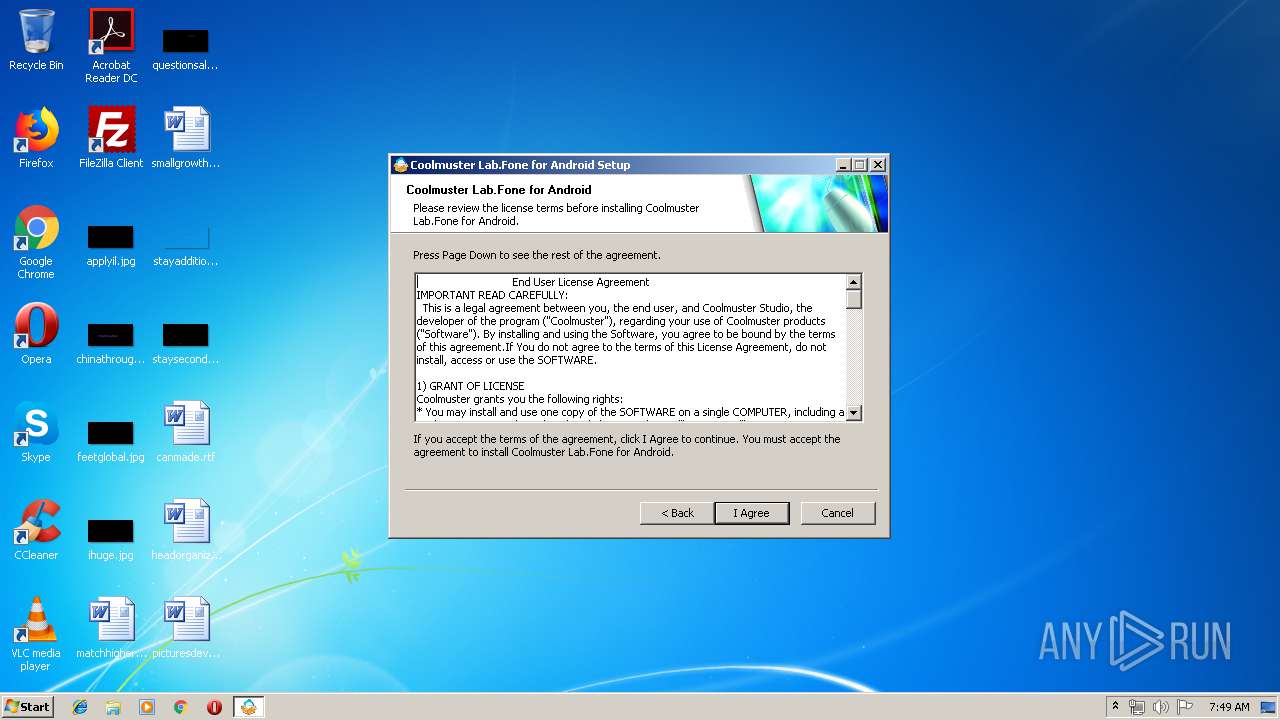
Creates a software uninstall entry
- cool-android-recovery.exe (PID: 3632)
Creates files in the user directory
- cool-android-recovery.exe (PID: 3632)
- AndroidAssistServer.exe (PID: 2256)
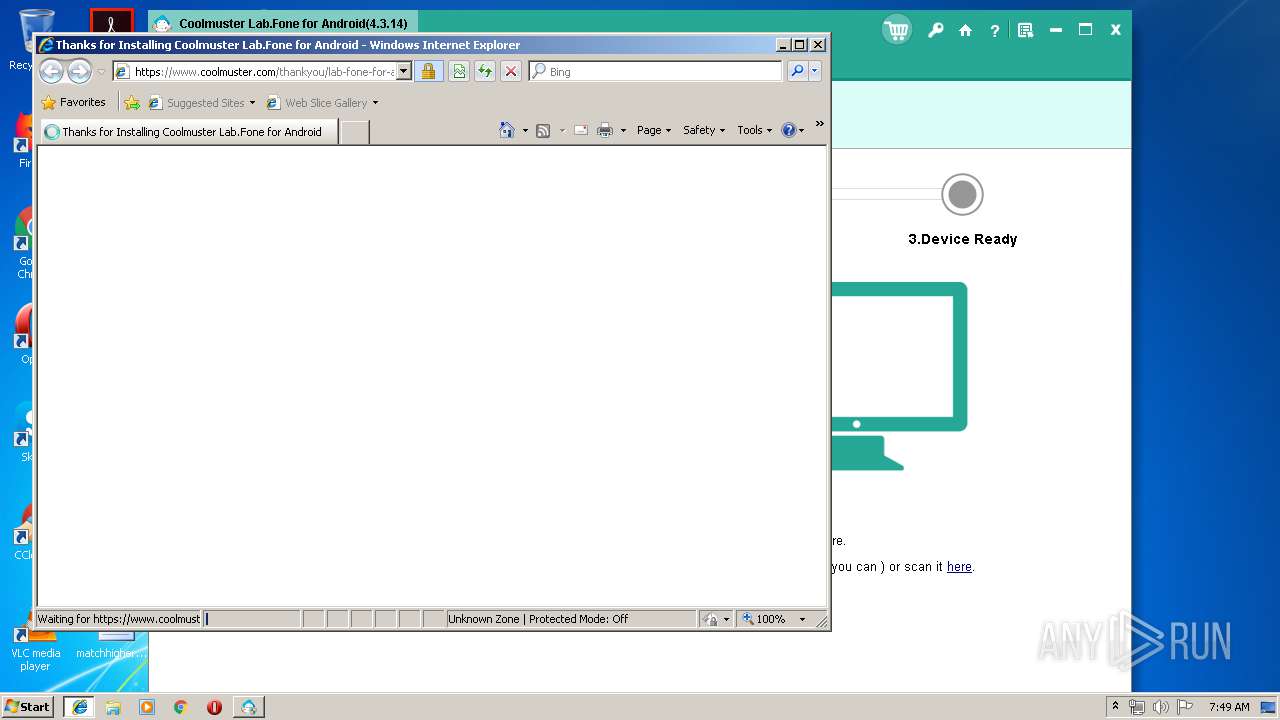
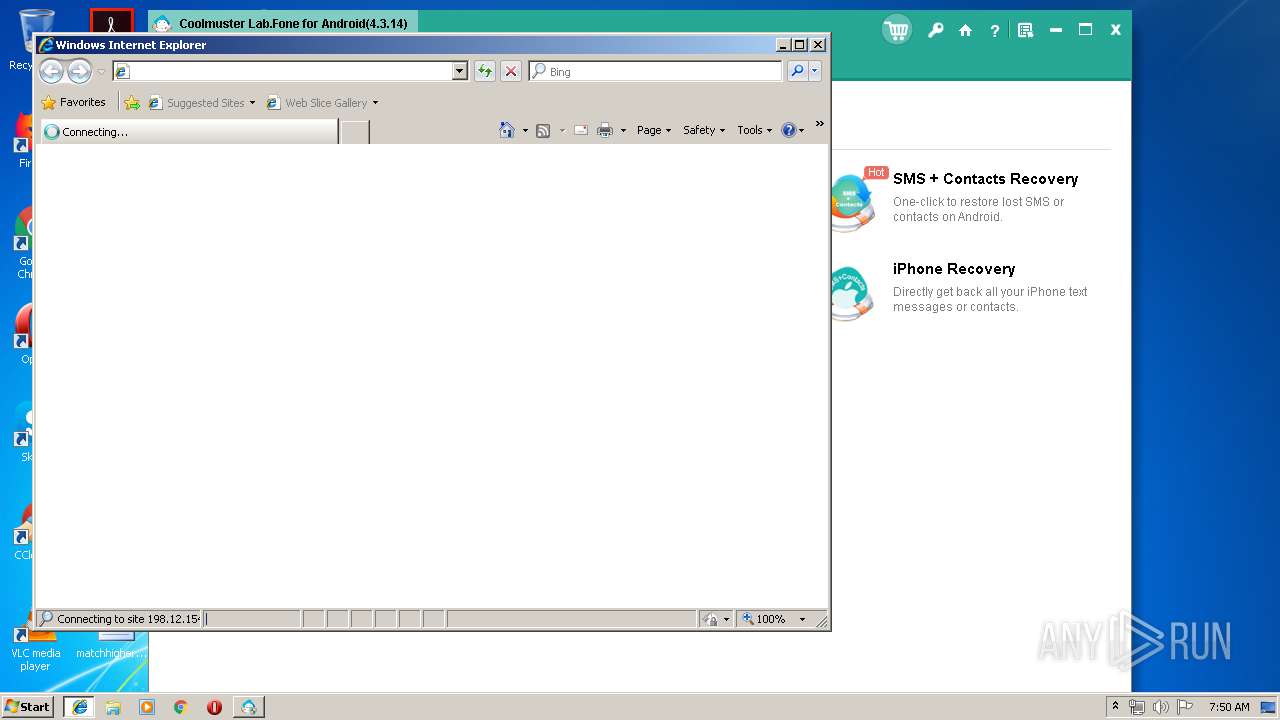
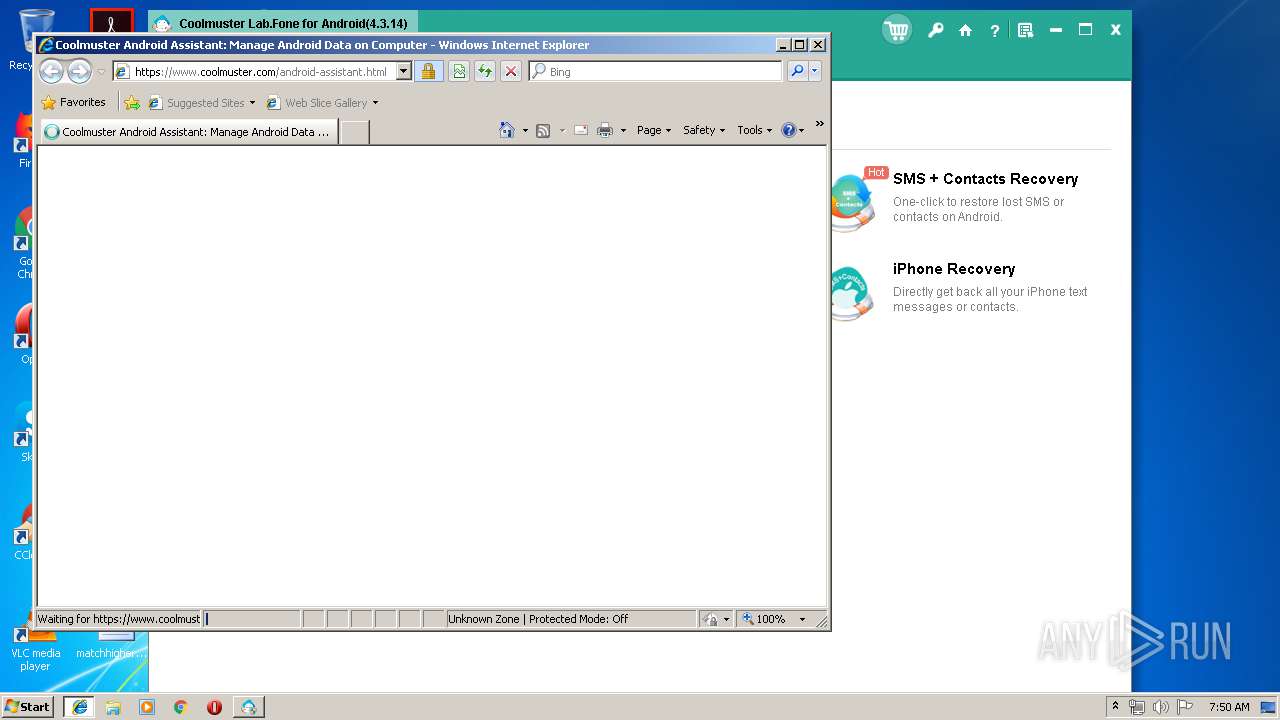
Starts Internet Explorer
- cool-android-recovery.exe (PID: 3632)
- Coolmuster Lab.Fone for Android.exe (PID: 2764)
Application launched itself
- adb.exe (PID: 2404)
Creates files in the program directory
- cool-android-recovery.exe (PID: 3632)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2900)
- iexplore.exe (PID: 2032)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2276)
- iexplore.exe (PID: 3876)
Changes settings of System certificates
- iexplore.exe (PID: 2276)
- iexplore.exe (PID: 3876)
Reads internet explorer settings
- iexplore.exe (PID: 2276)
- iexplore.exe (PID: 3876)
Creates files in the user directory
- iexplore.exe (PID: 3876)
- iexplore.exe (PID: 2276)
Application launched itself
- iexplore.exe (PID: 2032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:12:11 22:50:38+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 118272 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x316d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Dec-2016 21:50:38 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Dec-2016 21:50:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005CEF | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44129 |
.rdata | 0x00007000 | 0x00001246 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.00503 |
.data | 0x00009000 | 0x0001A7F8 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.1145 |
.ndata | 0x00024000 | 0x00014000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00038000 | 0x0005C410 | 0x0005C600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.69367 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28813 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.71286 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 5.06384 | 16936 | UNKNOWN | English - United States | RT_ICON |
4 | 5.14531 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 5.41231 | 4264 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.68364 | 76 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.68372 | 512 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
107 | 2.52183 | 160 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
47
Monitored processes
11
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2032 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | Coolmuster Lab.Fone for Android.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2256 | "C:\Program Files\Coolmuster\Coolmuster Lab.Fone for Android\Bin\AndroidAssistServer.exe" 38081 2764 4.3.14 Coolmuster "Coolmuster Lab.Fone for Android" 1 0 0 0 0 | C:\Program Files\Coolmuster\Coolmuster Lab.Fone for Android\Bin\AndroidAssistServer.exe | Coolmuster Lab.Fone for Android.exe | ||||||||||||
User: admin Company: AndroidAssistServer Integrity Level: HIGH Description: AndroidAssistServer Exit code: 0 Version: 4.4.36.0 Modules
| |||||||||||||||
| 2276 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2900 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2404 | C:\Users\admin\AppData\Roaming\Coolmuster\adb\1.0.36\adb.exe -P 5037 devices | C:\Users\admin\AppData\Roaming\Coolmuster\adb\1.0.36\adb.exe | AndroidAssistServer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2764 | "C:\Program Files\Coolmuster\Coolmuster Lab.Fone for Android\Bin\Coolmuster Lab.Fone for Android.exe" | C:\Program Files\Coolmuster\Coolmuster Lab.Fone for Android\Bin\Coolmuster Lab.Fone for Android.exe | — | cool-android-recovery.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Coolmuster Lab.Fone for Android Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 2800 | "C:\Program Files\Coolmuster\Coolmuster Lab.Fone for Android\Bin\adb.exe" version | C:\Program Files\Coolmuster\Coolmuster Lab.Fone for Android\Bin\adb.exe | — | AndroidAssistServer.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2900 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | cool-android-recovery.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2960 | "C:\Users\admin\AppData\Local\Temp\cool-android-recovery.exe" | C:\Users\admin\AppData\Local\Temp\cool-android-recovery.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3196 | adb -P 5037 fork-server server --reply-fd 208 | C:\Users\admin\AppData\Roaming\Coolmuster\adb\1.0.36\adb.exe | adb.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3632 | "C:\Users\admin\AppData\Local\Temp\cool-android-recovery.exe" | C:\Users\admin\AppData\Local\Temp\cool-android-recovery.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 092
Read events
966
Write events
125
Delete events
1
Modification events
| (PID) Process: | (3632) cool-android-recovery.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Coolmuster Lab.Fone for Android |
| Operation: | write | Name: | DisplayName |
Value: Coolmuster Lab.Fone for Android | |||
| (PID) Process: | (3632) cool-android-recovery.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Coolmuster Lab.Fone for Android |
| Operation: | write | Name: | DisplayIcon |
Value: "C:\Program Files\Coolmuster\Coolmuster Lab.Fone for Android\Bin\Coolmuster Lab.Fone for Android.exe" | |||
| (PID) Process: | (3632) cool-android-recovery.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Coolmuster Lab.Fone for Android |
| Operation: | write | Name: | Publisher |
Value: Coolmuster | |||
| (PID) Process: | (3632) cool-android-recovery.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Coolmuster Lab.Fone for Android |
| Operation: | write | Name: | DisplayVersion |
Value: 4.3.14 | |||
| (PID) Process: | (3632) cool-android-recovery.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Coolmuster Lab.Fone for Android |
| Operation: | write | Name: | VersionMajor |
Value: 4 | |||
| (PID) Process: | (3632) cool-android-recovery.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Coolmuster Lab.Fone for Android |
| Operation: | write | Name: | VersionMinor |
Value: 3 | |||
| (PID) Process: | (3632) cool-android-recovery.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Coolmuster Lab.Fone for Android |
| Operation: | write | Name: | EstimatedSize |
Value: 960 | |||
| (PID) Process: | (3632) cool-android-recovery.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Coolmuster Lab.Fone for Android |
| Operation: | write | Name: | HelpLink |
Value: http://www.coolmuster.com | |||
| (PID) Process: | (3632) cool-android-recovery.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Coolmuster Lab.Fone for Android |
| Operation: | write | Name: | URLInfoAbout |
Value: http://www.coolmuster.com | |||
| (PID) Process: | (3632) cool-android-recovery.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Coolmuster Lab.Fone for Android |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Coolmuster\Coolmuster Lab.Fone for Android | |||
Executable files
50
Suspicious files
3
Text files
183
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3632 | cool-android-recovery.exe | C:\Users\admin\AppData\Local\Temp\nsc89A5.tmp\modern-wizard.bmp | image | |
MD5:— | SHA256:— | |||
| 3632 | cool-android-recovery.exe | C:\Program Files\Coolmuster\Coolmuster Lab.Fone for Android\Option.json | text | |
MD5:— | SHA256:— | |||
| 3632 | cool-android-recovery.exe | C:\Program Files\Coolmuster\Coolmuster Lab.Fone for Android\Toolbox.json | text | |
MD5:— | SHA256:— | |||
| 3632 | cool-android-recovery.exe | C:\Program Files\Coolmuster\Coolmuster Lab.Fone for Android\uninst.exe | executable | |
MD5:— | SHA256:— | |||
| 3632 | cool-android-recovery.exe | C:\Users\admin\AppData\Local\Temp\nsc89A5.tmp\modern-header.bmp | image | |
MD5:4C0C819DCEF22E43AD036BDBC9B66719 | SHA256:9557469E065841D7F22F1CF34301CE2236FD314221DFC87AE17E7DFCF083526C | |||
| 3632 | cool-android-recovery.exe | C:\Users\admin\AppData\Local\Temp\nsc89A5.tmp\nsDialogs.dll | executable | |
MD5:B3070CF20DB659FDFB3CB2ED38130E8D | SHA256:F2C1409FAF2952C1C91F4B5495158EF5C7D1A1DB6EEA4A18F163574BD52FCAD0 | |||
| 3632 | cool-android-recovery.exe | C:\Program Files\Coolmuster\Coolmuster Lab.Fone for Android\license.txt | text | |
MD5:0D0E7BFC070329BC9DE822C18926C92E | SHA256:0D26A768725DEAB1E26EDC928505EC856CBB84F33134184038F1B562BB59A729 | |||
| 3632 | cool-android-recovery.exe | C:\Program Files\Coolmuster\Coolmuster Lab.Fone for Android\bubble.html | html | |
MD5:B9A299E155B97E784B46B3E59A4C5639 | SHA256:5CECEB15C6D81382F37C78B68F3AC800F66692C9060B4869BFDC9DA1E5C09418 | |||
| 3632 | cool-android-recovery.exe | C:\Program Files\Coolmuster\Coolmuster Lab.Fone for Android\template.html | html | |
MD5:4EB9E59C2BF44ED7B2912998C4532CFA | SHA256:8E4784C70028C251D75D80B1155C189984A1D6830DDF919DF11161C28F11E2A9 | |||
| 3632 | cool-android-recovery.exe | C:\Program Files\Coolmuster\Coolmuster Lab.Fone for Android\Bin\AdbWinApi.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
42
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2032 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2900 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
— | — | GET | 200 | 188.121.36.239:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | NL | der | 1.69 Kb | whitelisted |
— | — | GET | 200 | 188.121.36.239:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | NL | der | 1.66 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2276 | iexplore.exe | 198.12.154.136:443 | www.coolmuster.com | GoDaddy.com, LLC | US | unknown |
2256 | AndroidAssistServer.exe | 198.12.154.136:443 | www.coolmuster.com | GoDaddy.com, LLC | US | unknown |
— | — | 188.121.36.239:80 | ocsp.godaddy.com | GoDaddy.com, LLC | NL | unknown |
3876 | iexplore.exe | 198.12.154.136:443 | www.coolmuster.com | GoDaddy.com, LLC | US | unknown |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3876 | iexplore.exe | 2.23.104.167:443 | s7.addthis.com | Akamai International B.V. | — | whitelisted |
2900 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3876 | iexplore.exe | 173.194.76.97:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
3876 | iexplore.exe | 31.13.90.6:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
— | — | 198.12.154.136:443 | www.coolmuster.com | GoDaddy.com, LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.coolmuster.com |
| suspicious |
www.bing.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
connect.facebook.net |
| whitelisted |