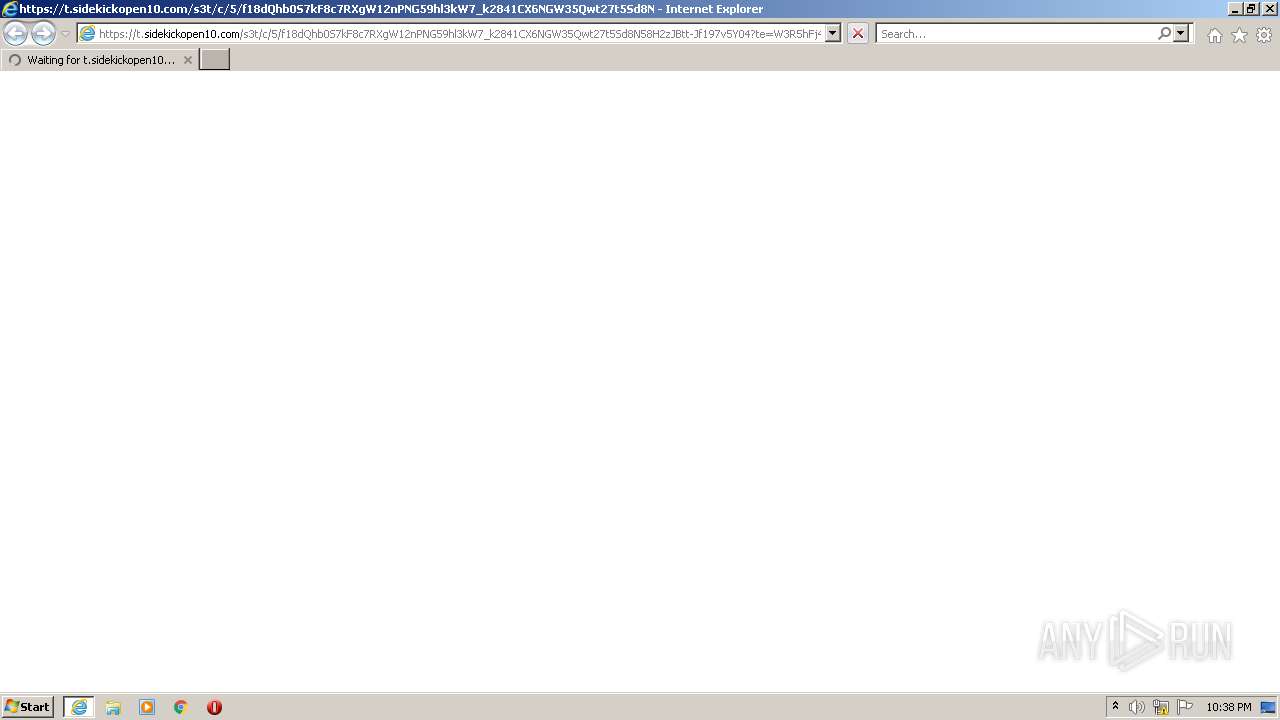
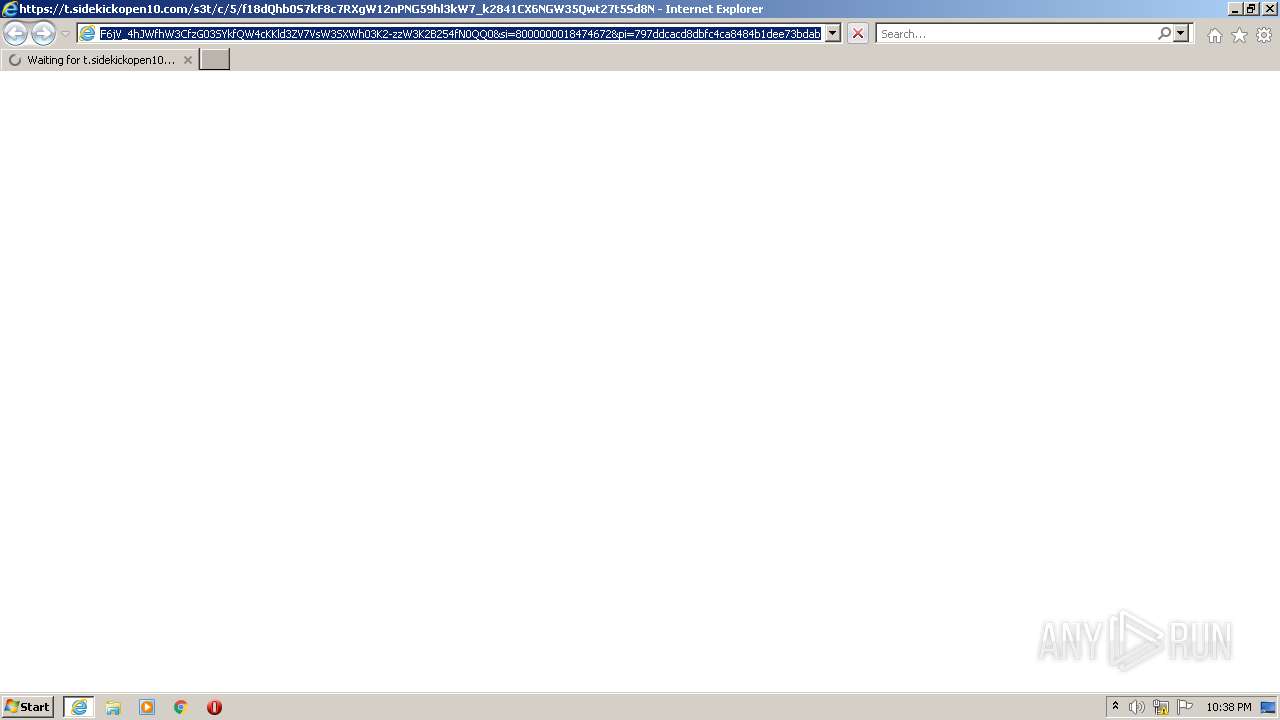
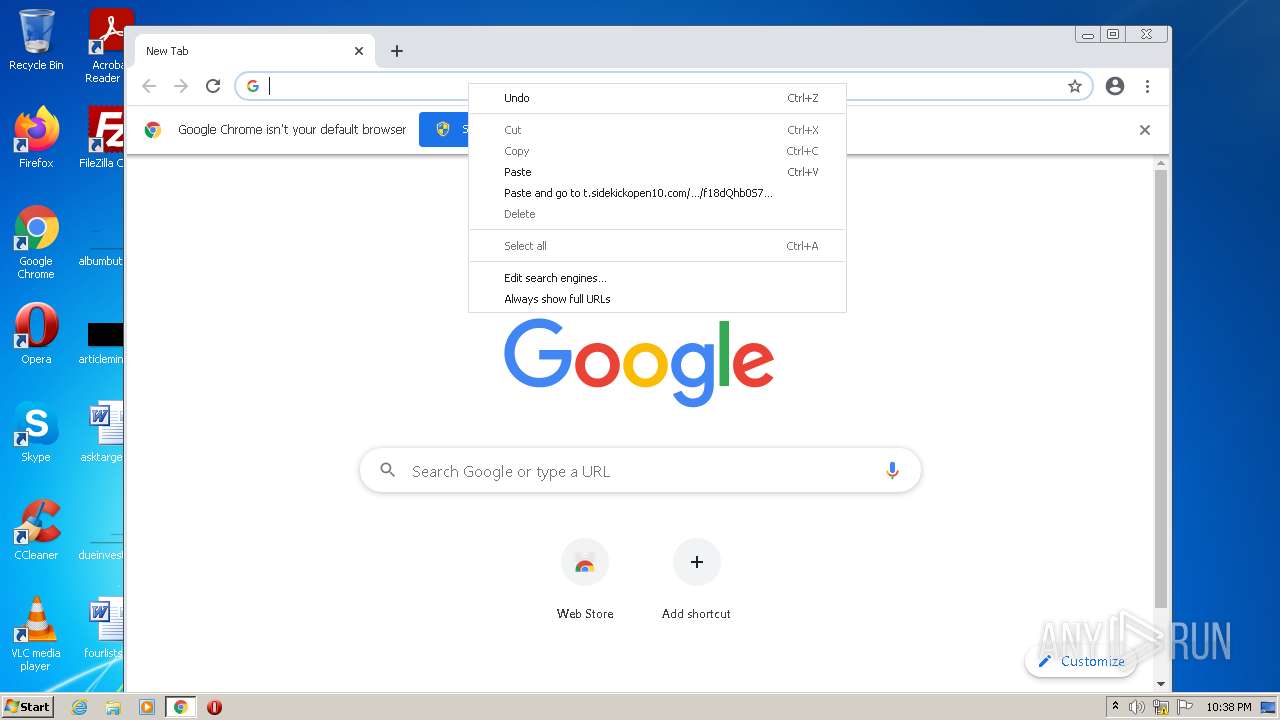
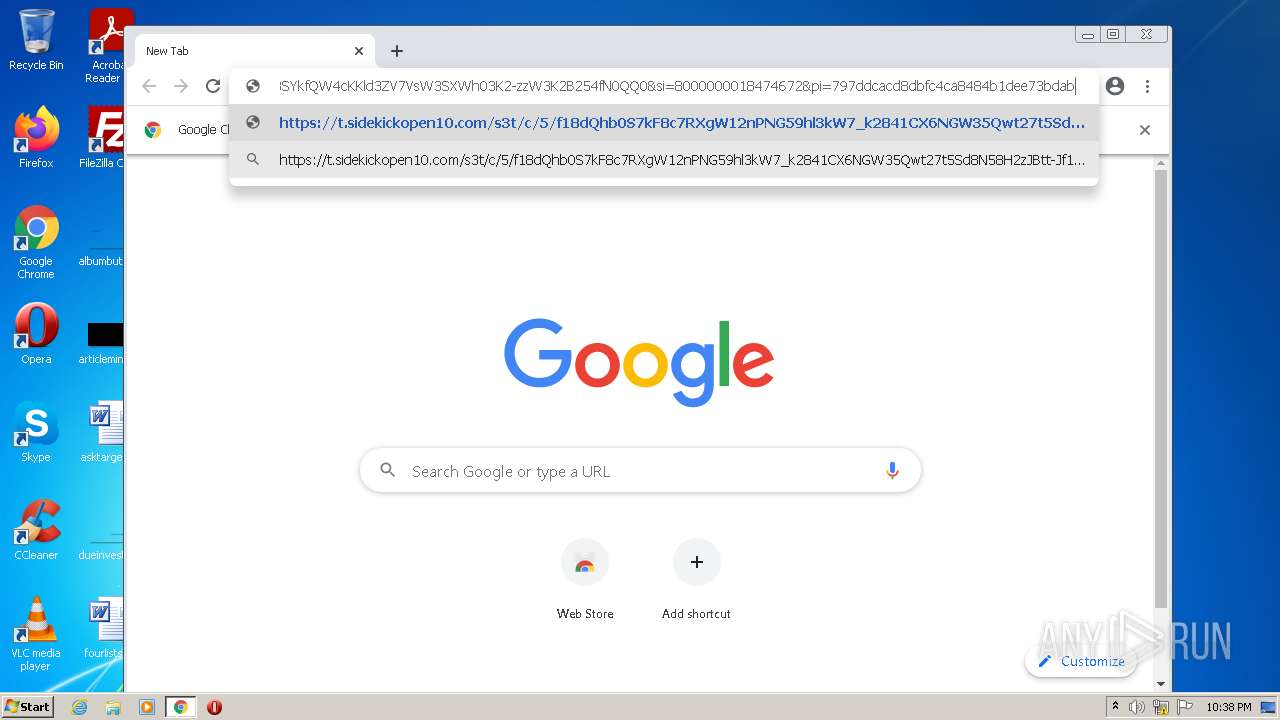
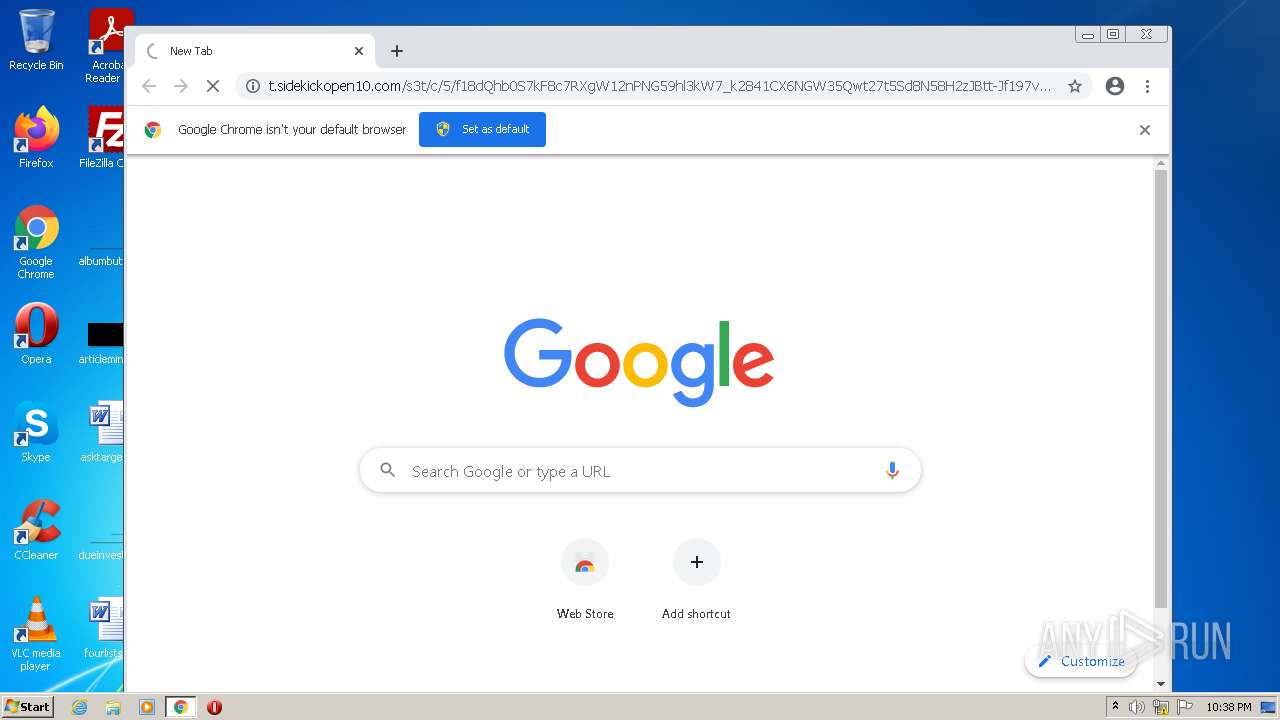
| URL: | https://t.sidekickopen10.com/s3t/c/5/f18dQhb0S7kF8c7RXgW12nPNG59hl3kW7_k2841CX6NGW35Qwt27t5Sd8N58H2zJBtt-Jf197v5Y04?te=W3R5hFj4cm2zwW4mKLS-3XWGKjW3K8K1w43nnmkW1LBbZd3zb1CtW45TQpd3K8PTlW3F6jV_4hJWfhW3CfzG03SYkfQW4cKKld3ZV7VsW3SXWh03K2-zzW3K2B254fN0QQ0&si=8000000018474672&pi=797ddcacd8dbfc4ca8484b1dee73bdab |
| Full analysis: | https://app.any.run/tasks/f3285851-9267-4efc-8fe0-051c14f234c9 |
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2022, 21:38:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E2F45032C91D91F7BBD402E09E3A1D27 |
| SHA1: | 15D9B039AF1B9E00CD2F0AD1C7D87F1A93532DF7 |
| SHA256: | 733EEB85E3FDEEB3FF2685534A471BED31AA912FDA849F738DA082CC256C2144 |
| SSDEEP: | 6:25YQkNdADq21UboDX0Tc5VEYRM8dUxBY+PtL6QeEg5g0122WWDLgcoTOM1w3ARHn:2uQkw1UFIoY+pa+p6QeEg+qMWD/OOLAh |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2540)
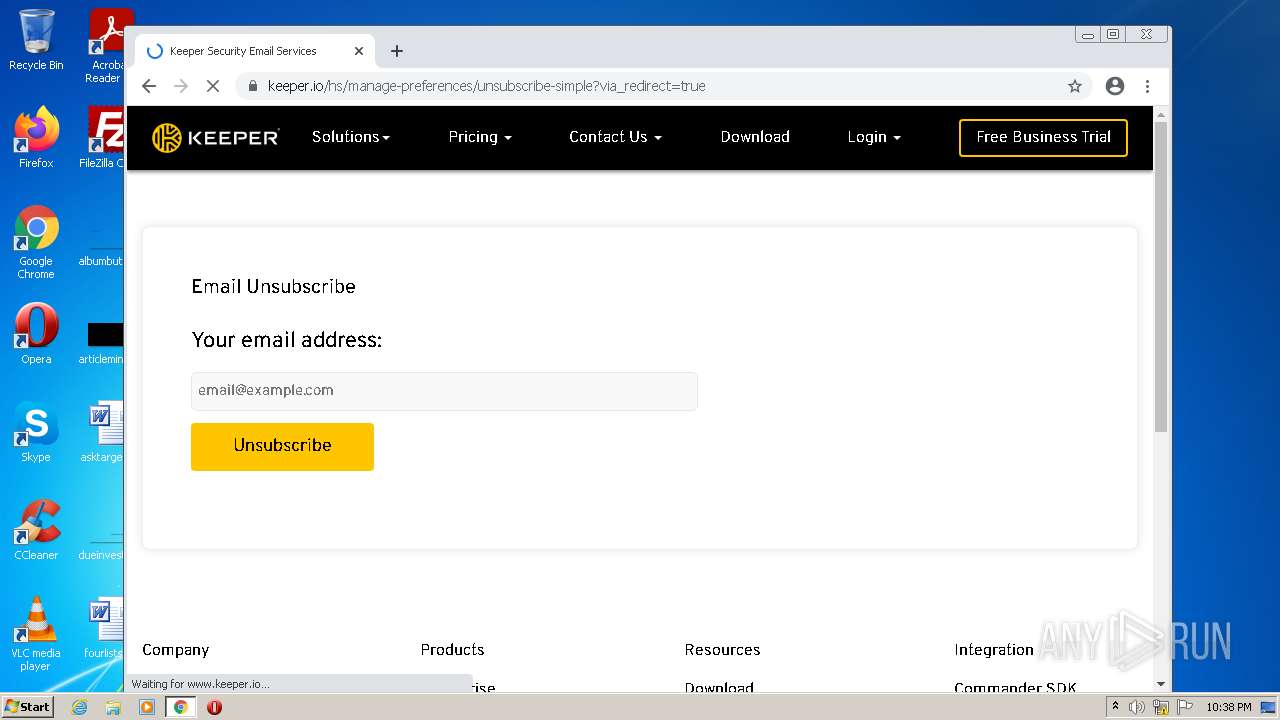
Modifies files in Chrome extension folder
- chrome.exe (PID: 892)
INFO
Checks supported languages
- iexplore.exe (PID: 3052)
- iexplore.exe (PID: 2540)
- chrome.exe (PID: 892)
- chrome.exe (PID: 4044)
- chrome.exe (PID: 3388)
- chrome.exe (PID: 952)
- chrome.exe (PID: 2608)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 3296)
- chrome.exe (PID: 3184)
- chrome.exe (PID: 2968)
- chrome.exe (PID: 2240)
- chrome.exe (PID: 2692)
- chrome.exe (PID: 2732)
- chrome.exe (PID: 872)
- chrome.exe (PID: 2460)
- chrome.exe (PID: 3632)
- chrome.exe (PID: 3624)
- chrome.exe (PID: 2440)
- chrome.exe (PID: 2872)
- chrome.exe (PID: 3528)
Reads the computer name
- iexplore.exe (PID: 3052)
- iexplore.exe (PID: 2540)
- chrome.exe (PID: 892)
- chrome.exe (PID: 872)
- chrome.exe (PID: 4044)
- chrome.exe (PID: 952)
- chrome.exe (PID: 2732)
- chrome.exe (PID: 3632)
- chrome.exe (PID: 3624)
- chrome.exe (PID: 2872)
Application launched itself
- iexplore.exe (PID: 3052)
- chrome.exe (PID: 892)
Checks Windows Trust Settings
- iexplore.exe (PID: 2540)
- iexplore.exe (PID: 3052)
Reads settings of System Certificates
- iexplore.exe (PID: 2540)
- iexplore.exe (PID: 3052)
- chrome.exe (PID: 952)
Changes internet zones settings
- iexplore.exe (PID: 3052)
Reads the date of Windows installation
- iexplore.exe (PID: 3052)
- chrome.exe (PID: 3624)
Manual execution by user
- chrome.exe (PID: 892)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3052)
Reads the hosts file
- chrome.exe (PID: 892)
- chrome.exe (PID: 952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
21
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1064,14977712366837094686,11405378146656641863,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1052 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1064,14977712366837094686,11405378146656641863,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1332 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,14977712366837094686,11405378146656641863,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3316 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1064,14977712366837094686,11405378146656641863,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2672 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,14977712366837094686,11405378146656641863,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1716 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3052 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,14977712366837094686,11405378146656641863,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1844 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,14977712366837094686,11405378146656641863,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1920 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1064,14977712366837094686,11405378146656641863,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3188 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
24 926
Read events
24 722
Write events
201
Delete events
3
Modification events
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30988345 | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30988345 | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
92
Text files
69
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2540 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{DADE8C83-442C-11ED-8F0B-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF1CF04523D788826C.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{42C873D0-1D90-11EB-BA2C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF932015C979B25444.TMP | gmc | |
MD5:— | SHA256:— | |||
| 892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFe01c1.TMP | — | |
MD5:— | SHA256:— | |||
| 892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF853A597F110FF12D.TMP | gmc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
44
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
880 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/hfipfy3rgnylxrozrrxqwe3c6u_7621/hfnkpimlhhgieaddgfemjhofmfblmnib_7621_all_acgvjtqviccews55thkw4jn6wvma.crx3 | US | — | — | whitelisted |
880 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/hfipfy3rgnylxrozrrxqwe3c6u_7621/hfnkpimlhhgieaddgfemjhofmfblmnib_7621_all_acgvjtqviccews55thkw4jn6wvma.crx3 | US | binary | 5.66 Kb | whitelisted |
880 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/hfipfy3rgnylxrozrrxqwe3c6u_7621/hfnkpimlhhgieaddgfemjhofmfblmnib_7621_all_acgvjtqviccews55thkw4jn6wvma.crx3 | US | binary | 8.29 Kb | whitelisted |
3052 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
880 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/hfipfy3rgnylxrozrrxqwe3c6u_7621/hfnkpimlhhgieaddgfemjhofmfblmnib_7621_all_acgvjtqviccews55thkw4jn6wvma.crx3 | US | binary | 9.70 Kb | whitelisted |
952 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
2540 | iexplore.exe | GET | 200 | 8.238.191.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a9528d093f22c3eb | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2540 | iexplore.exe | 104.18.13.122:443 | t.sidekickopen10.com | CLOUDFLARENET | — | suspicious |
2540 | iexplore.exe | 8.238.191.126:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
2540 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
3052 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
952 | chrome.exe | 142.250.186.142:443 | clients2.google.com | GOOGLE | US | whitelisted |
3052 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
952 | chrome.exe | 142.250.186.42:443 | ajax.googleapis.com | GOOGLE | US | whitelisted |
952 | chrome.exe | 142.250.185.106:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
952 | chrome.exe | 104.17.185.73:443 | js.hsforms.net | CLOUDFLARENET | — | shared |
952 | chrome.exe | 142.250.186.131:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
t.sidekickopen10.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |