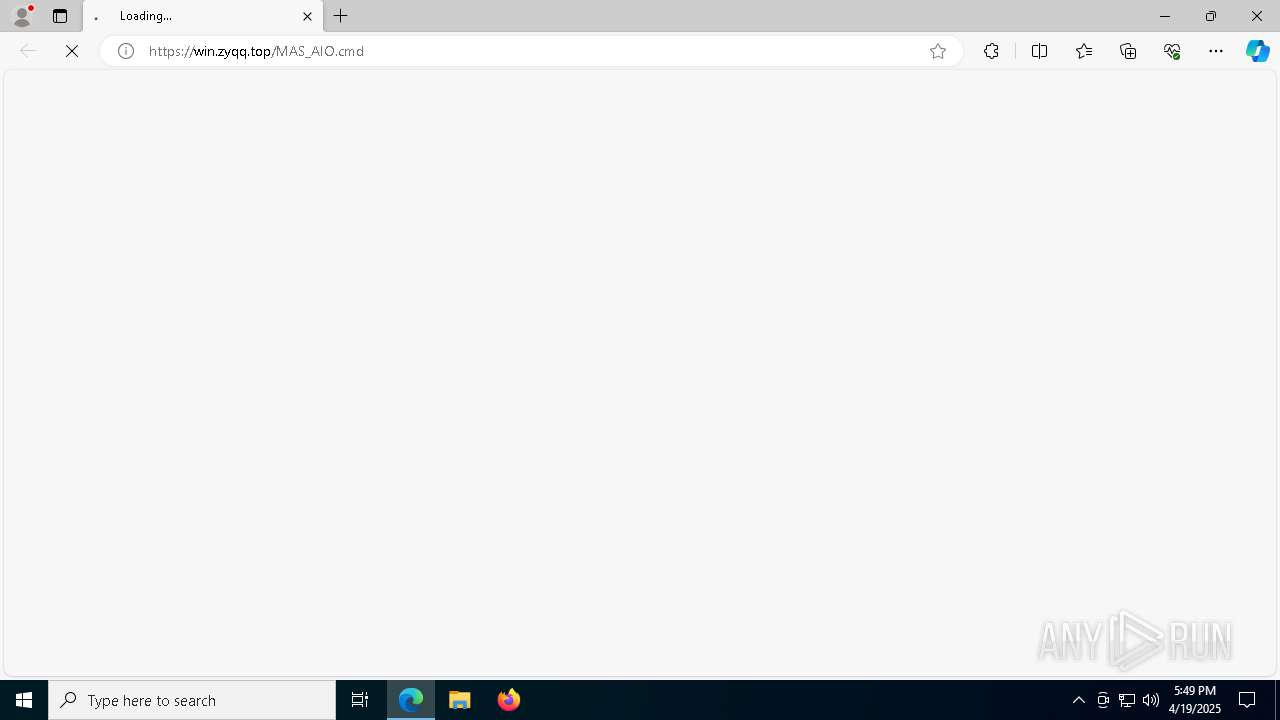
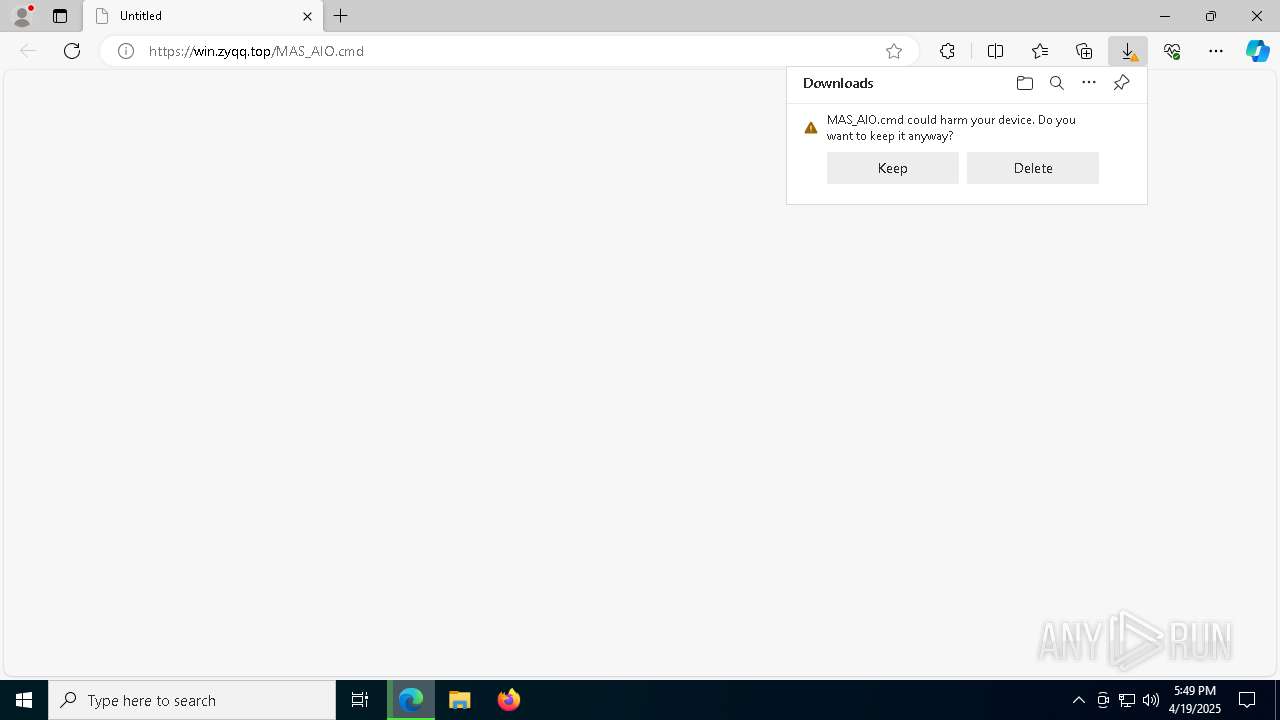
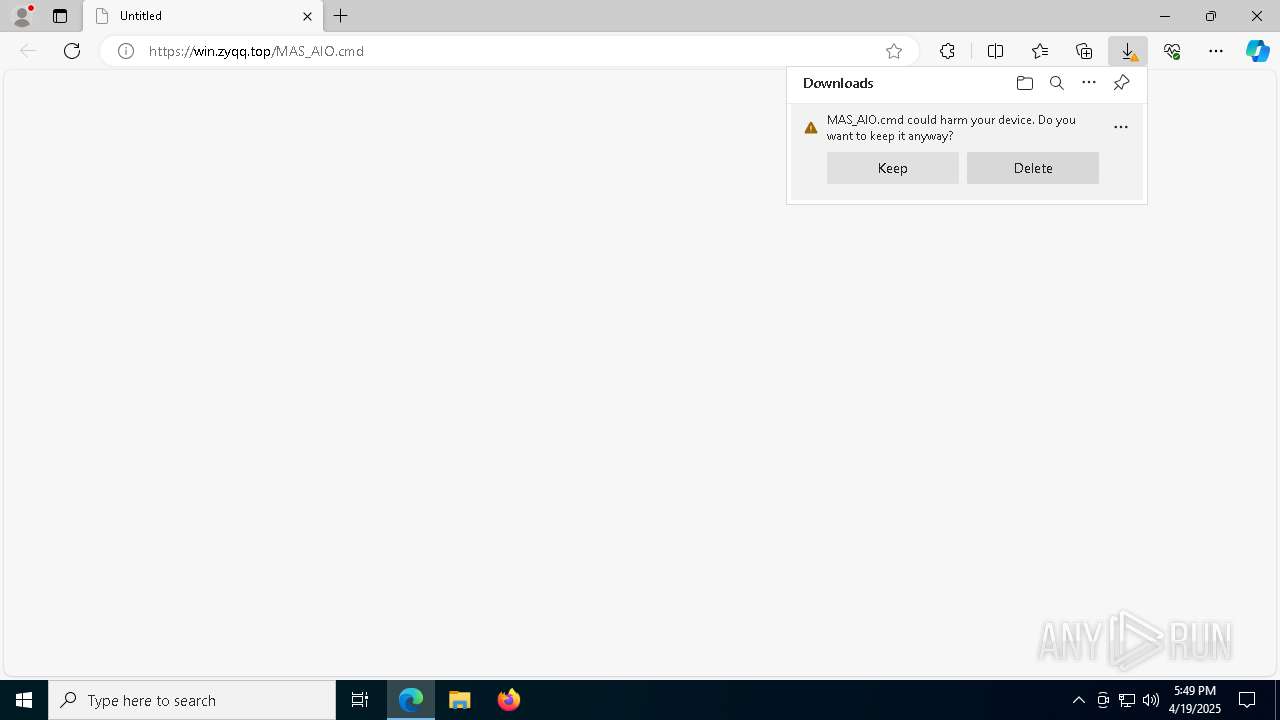
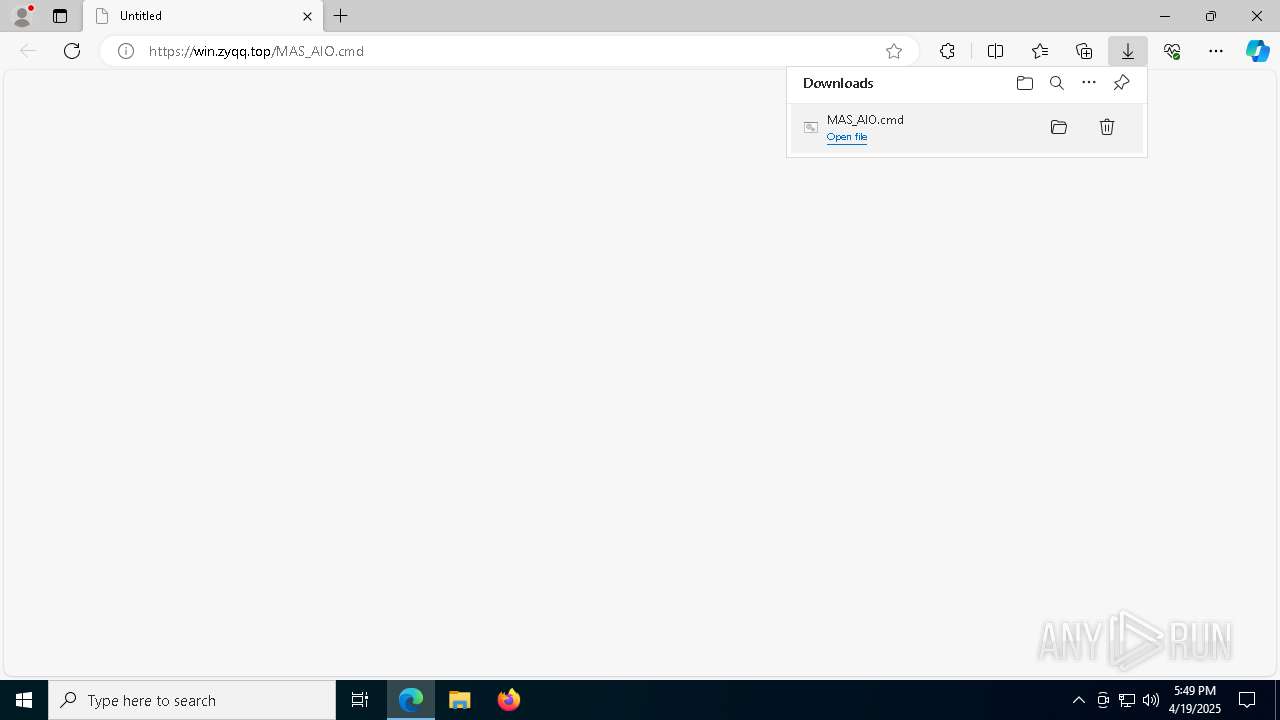
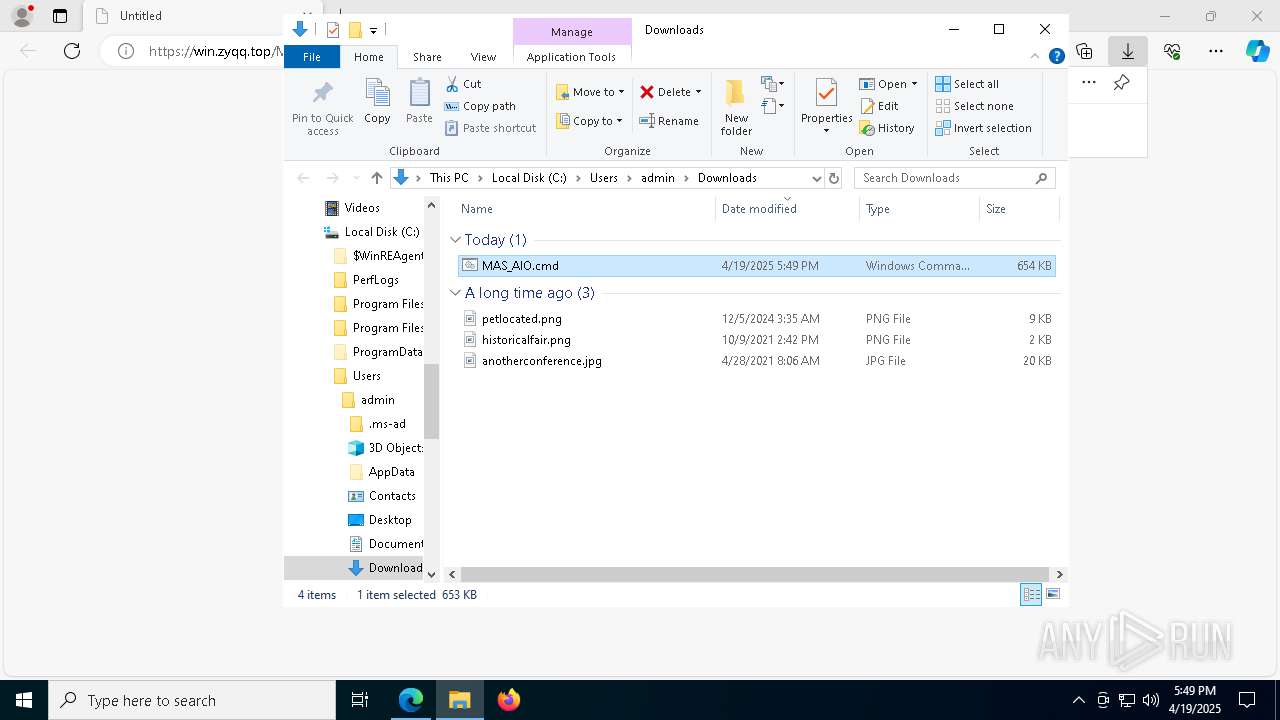
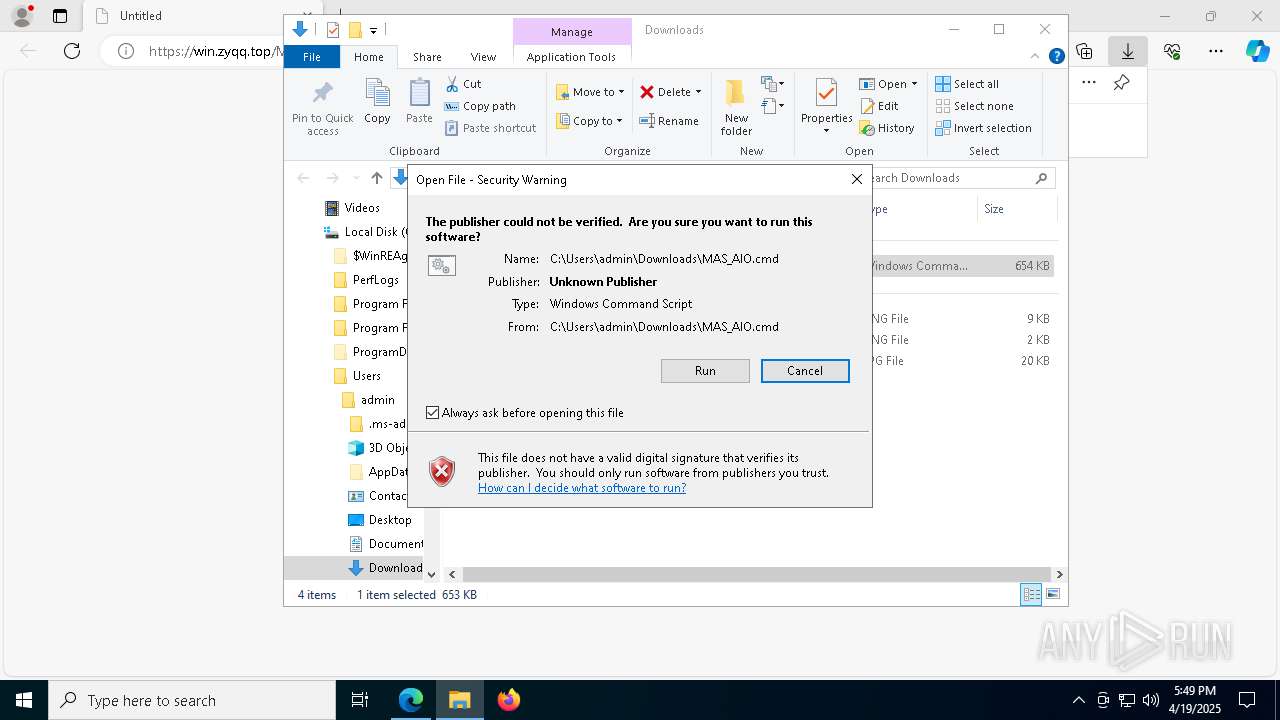
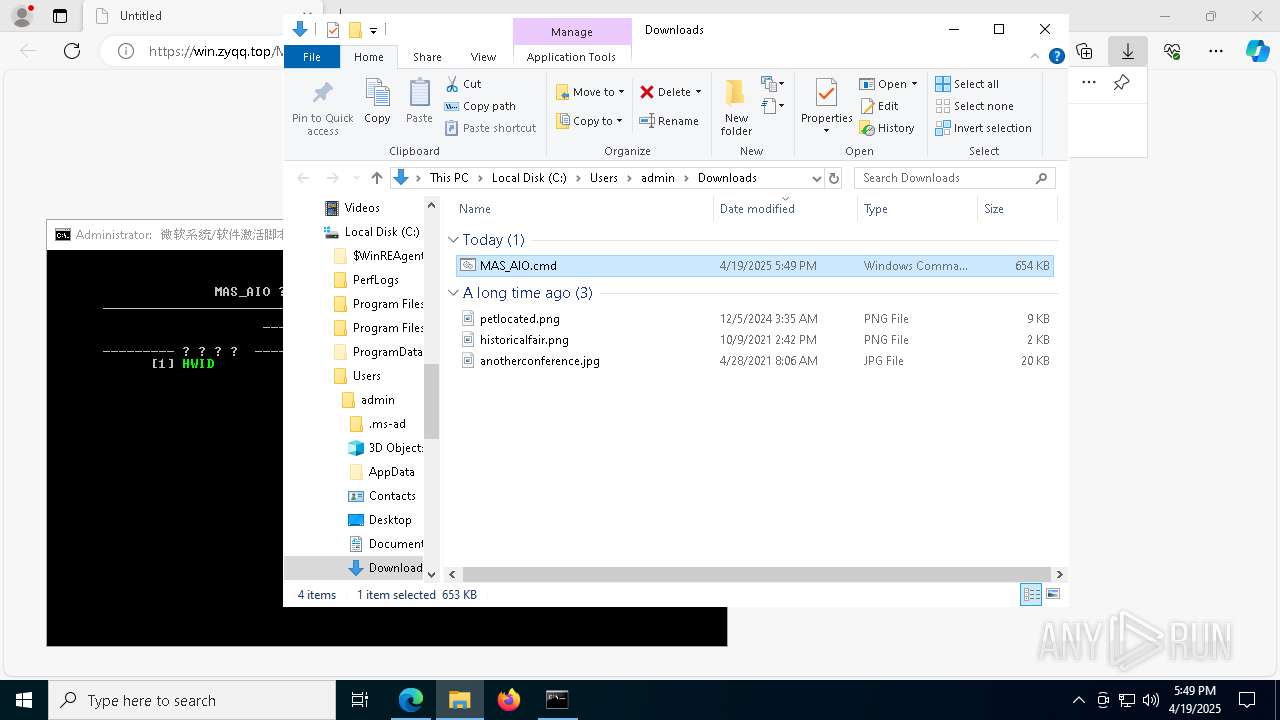
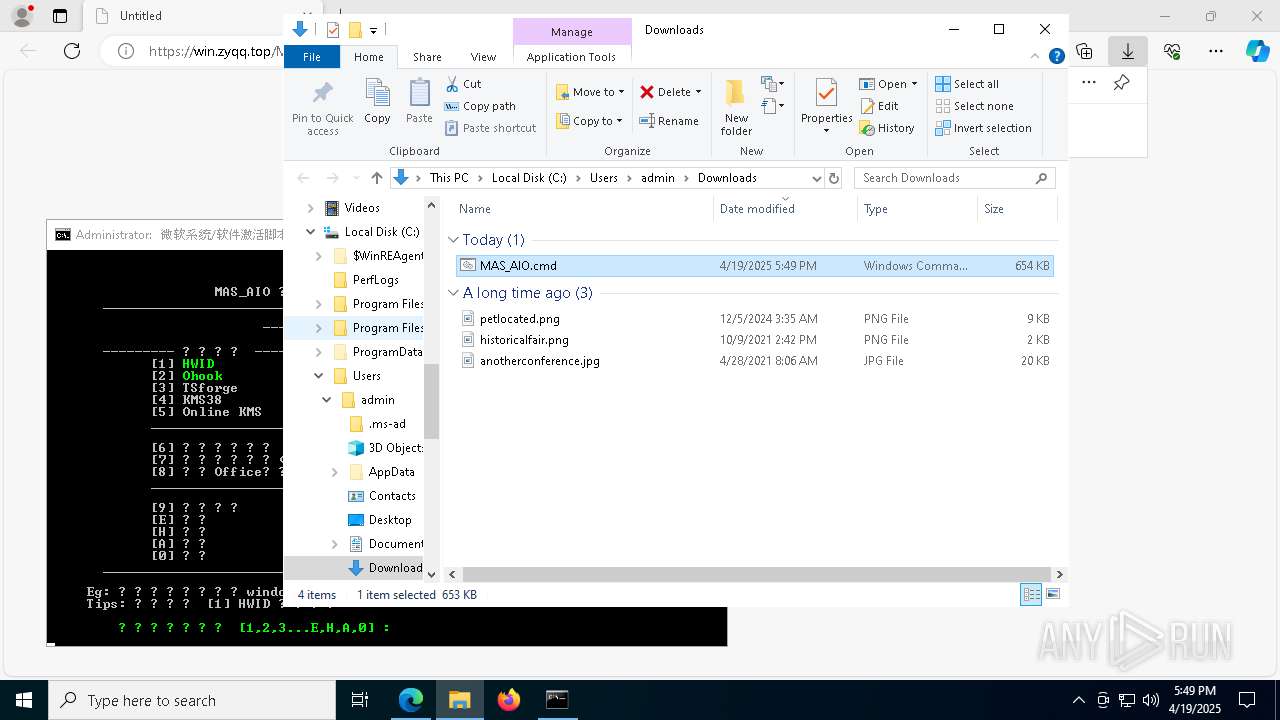
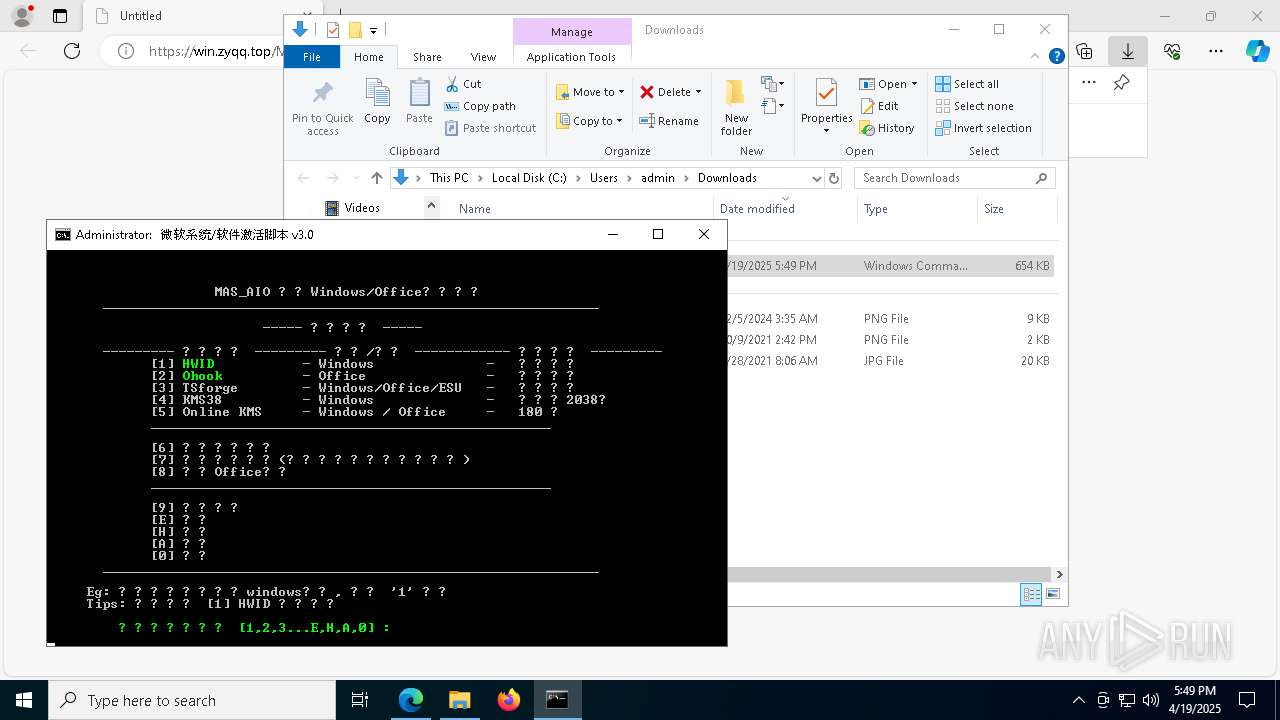
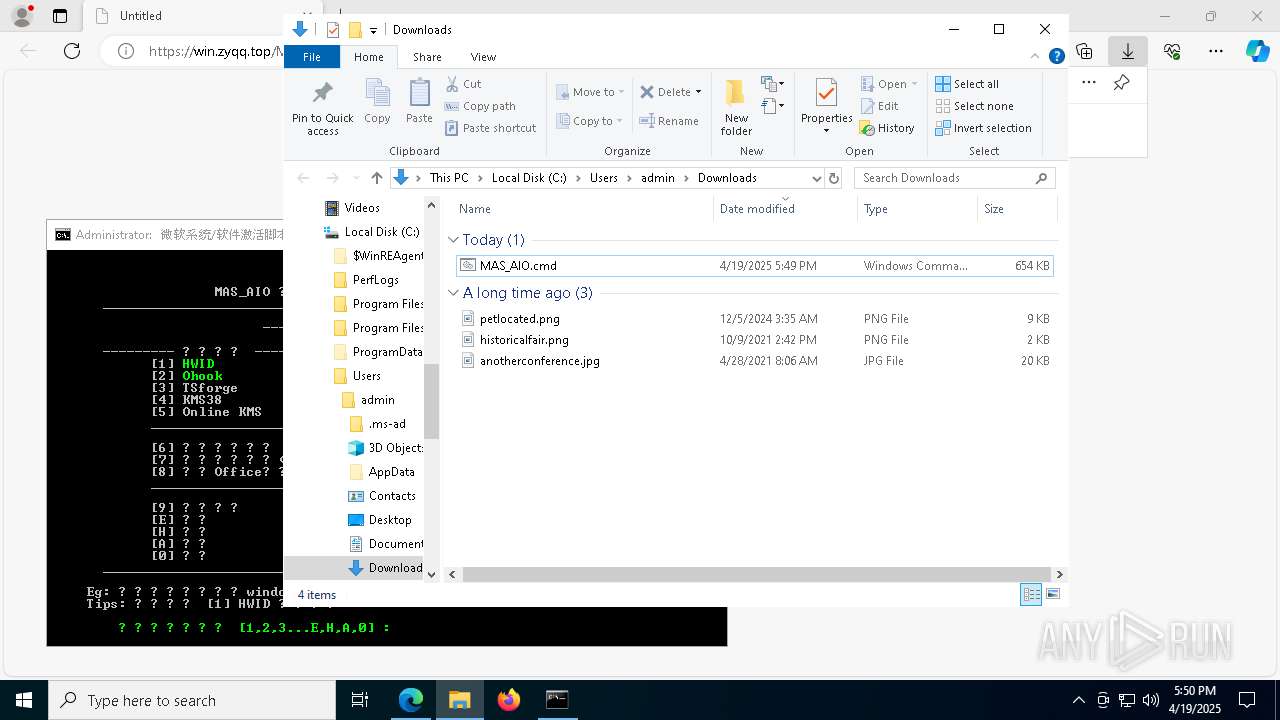
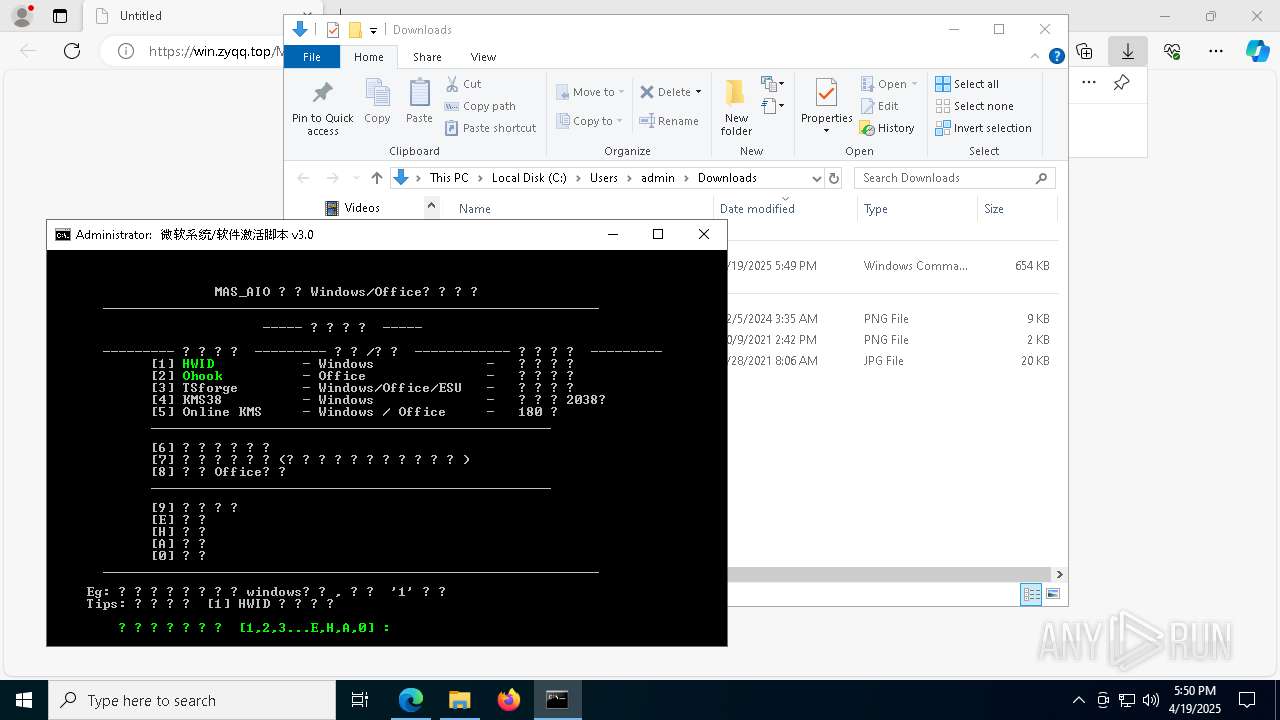
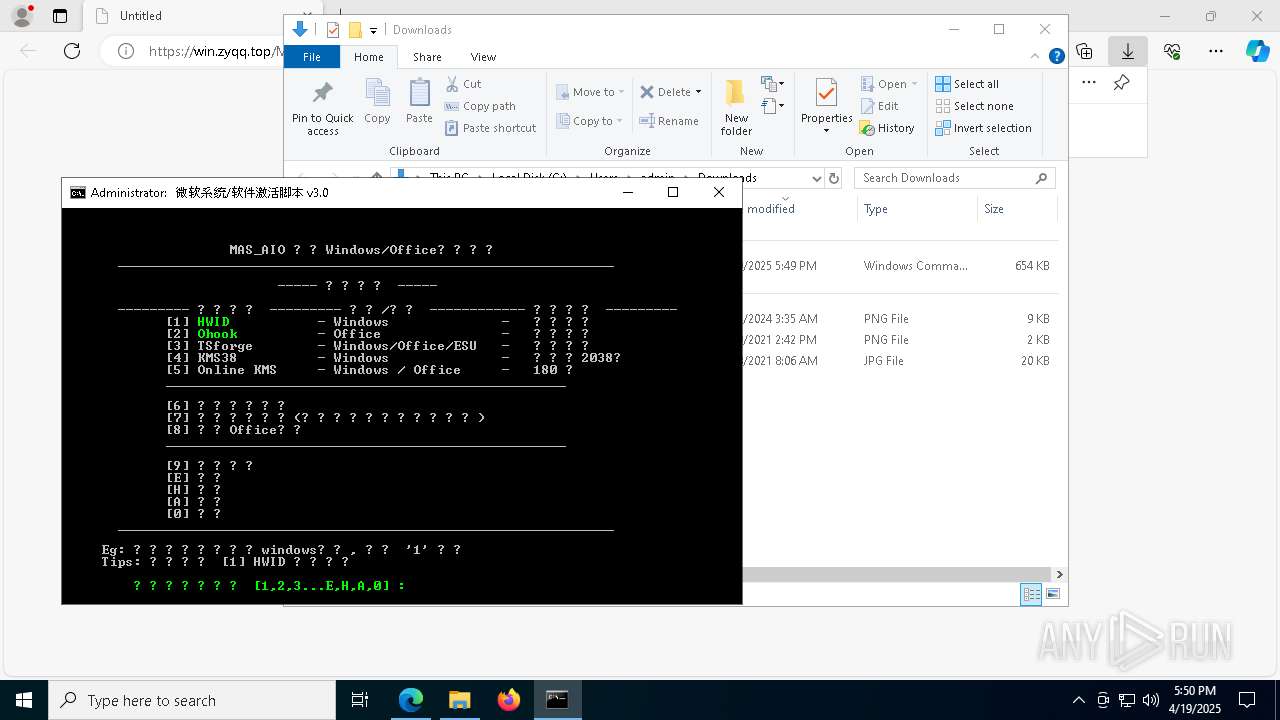
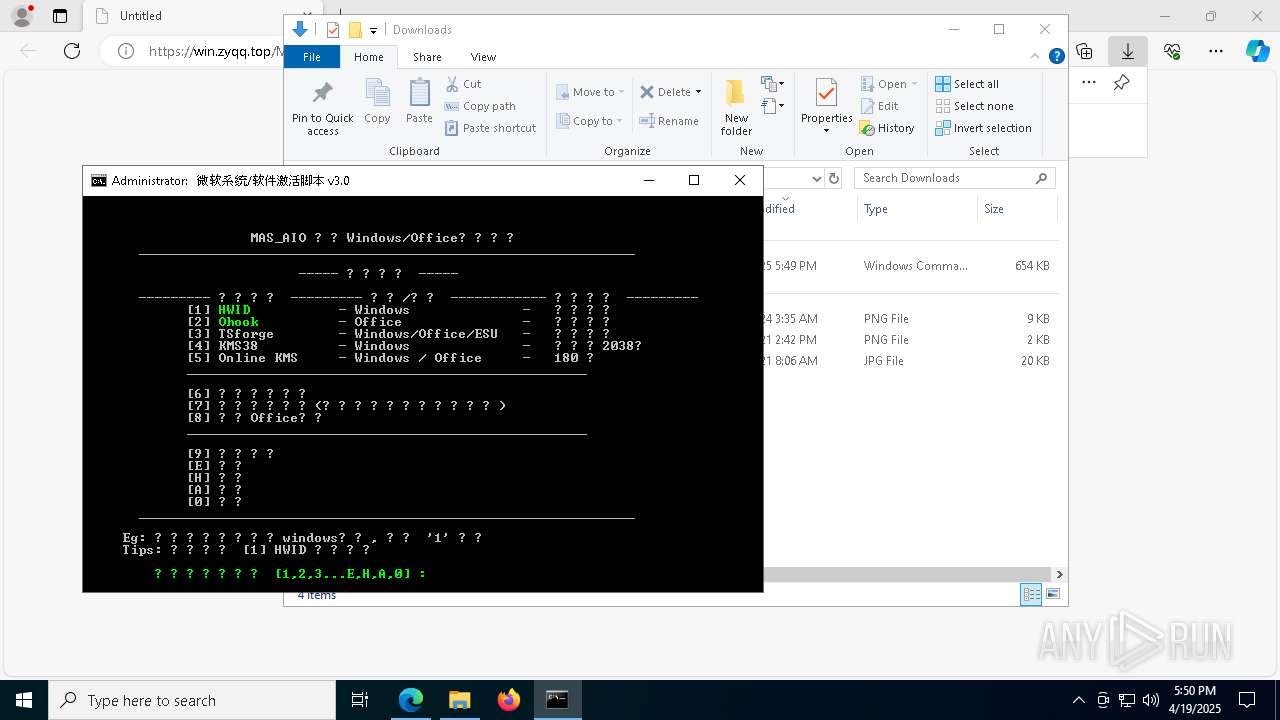
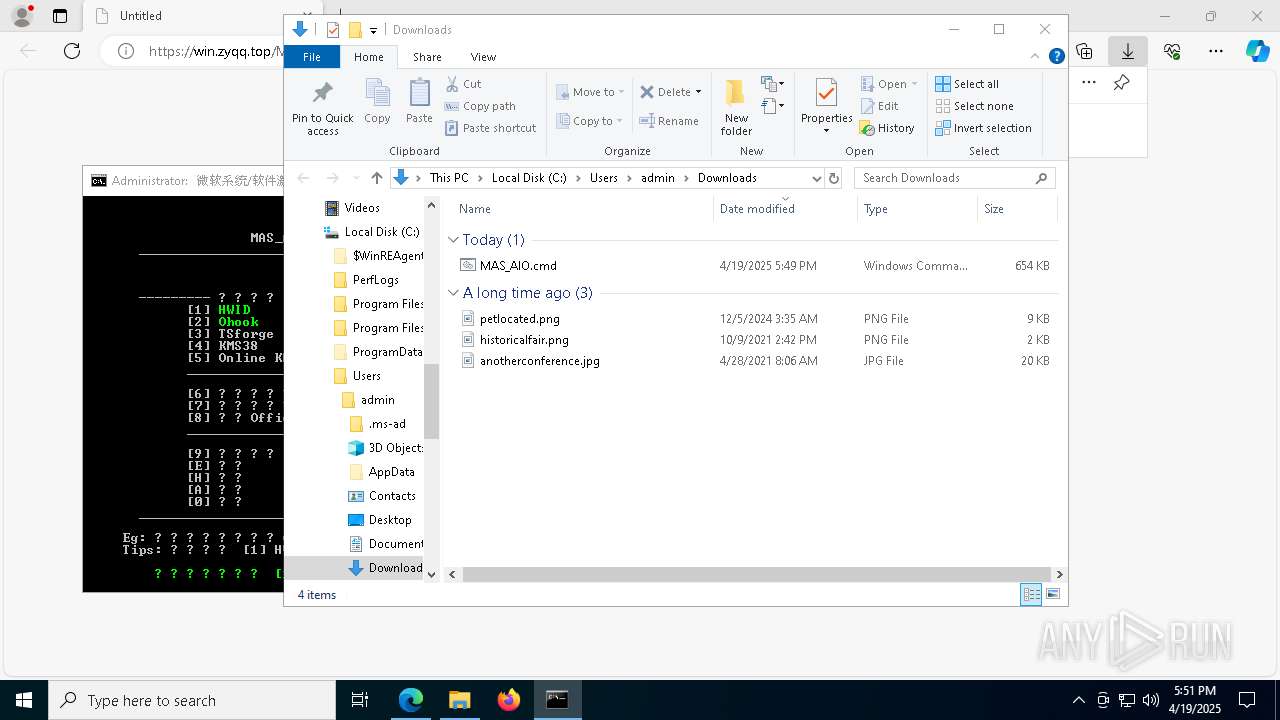
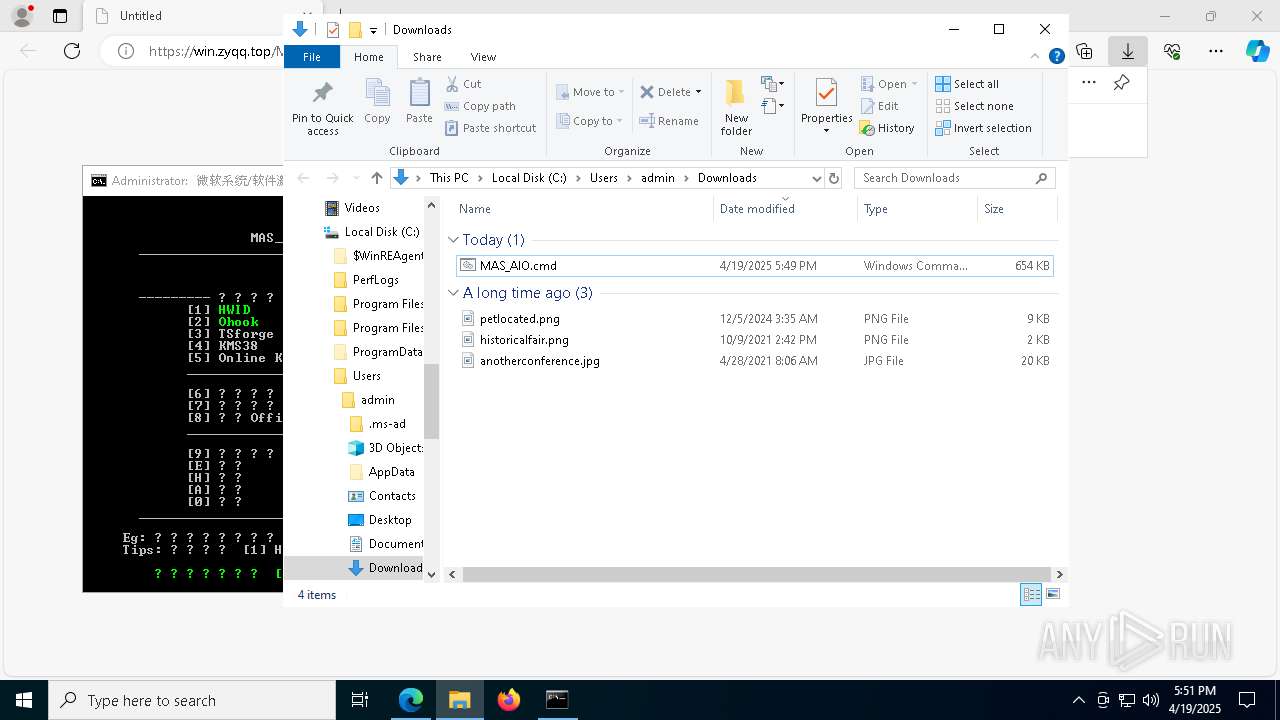
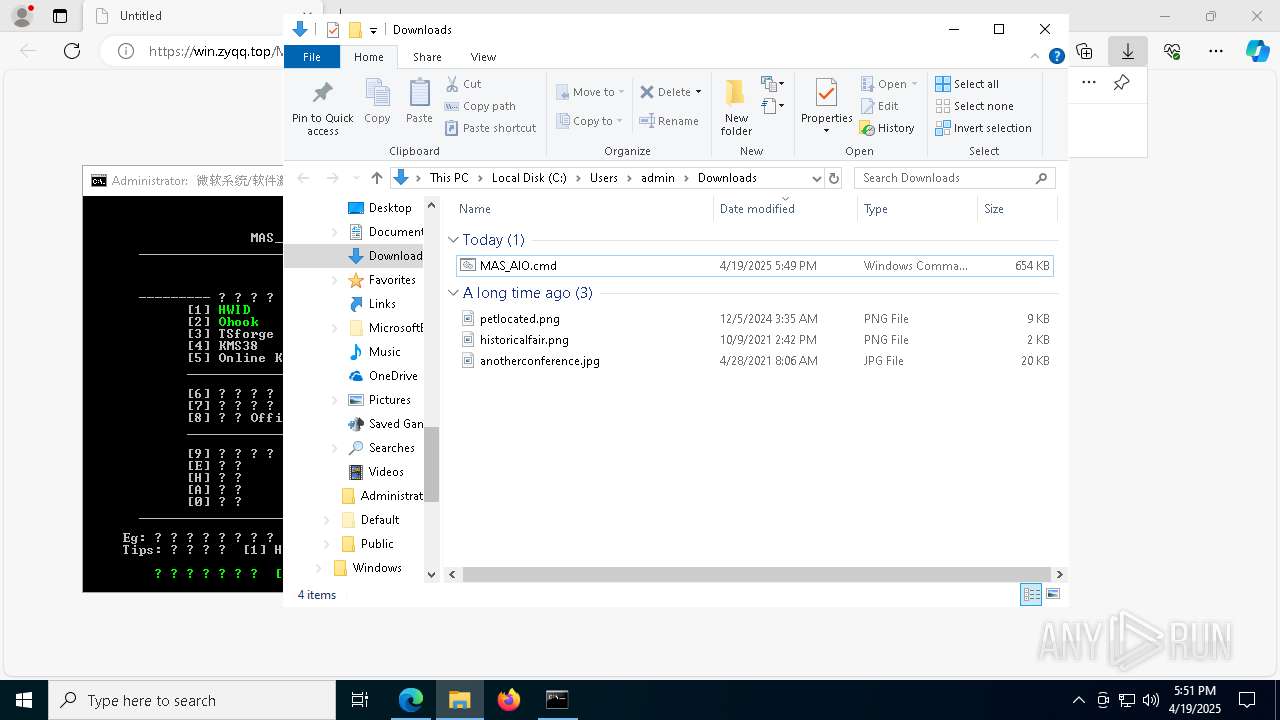
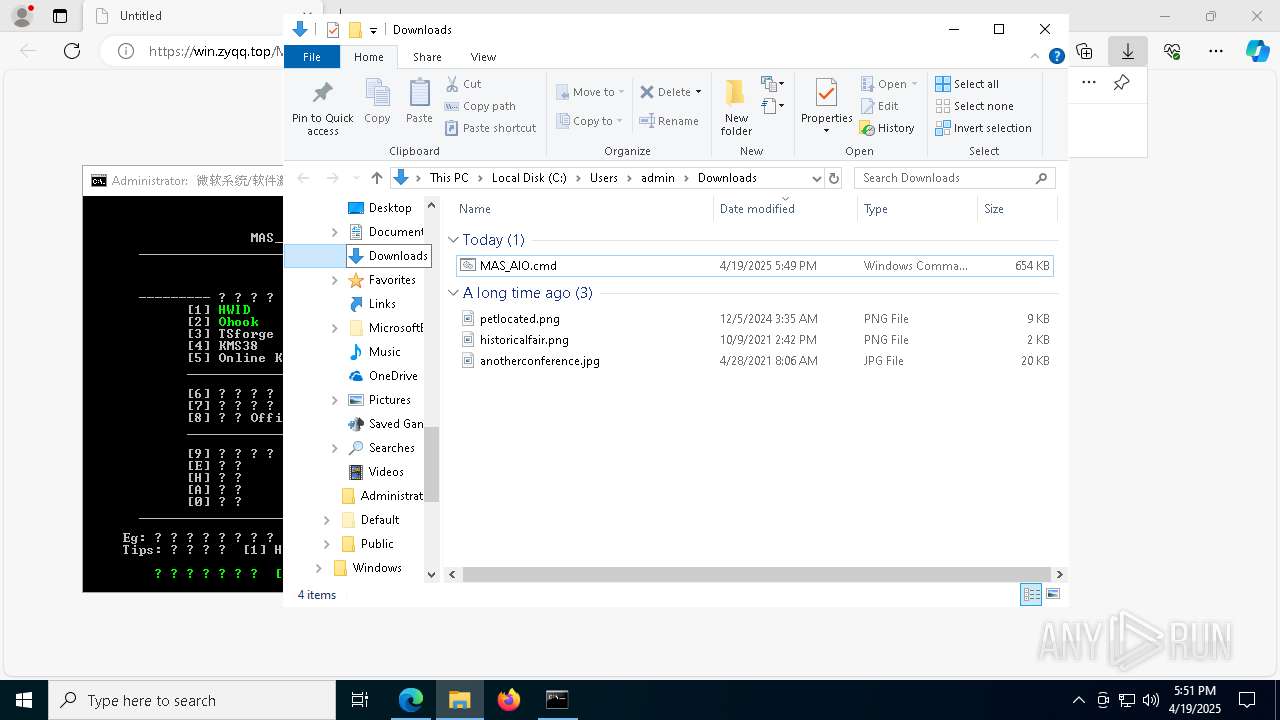
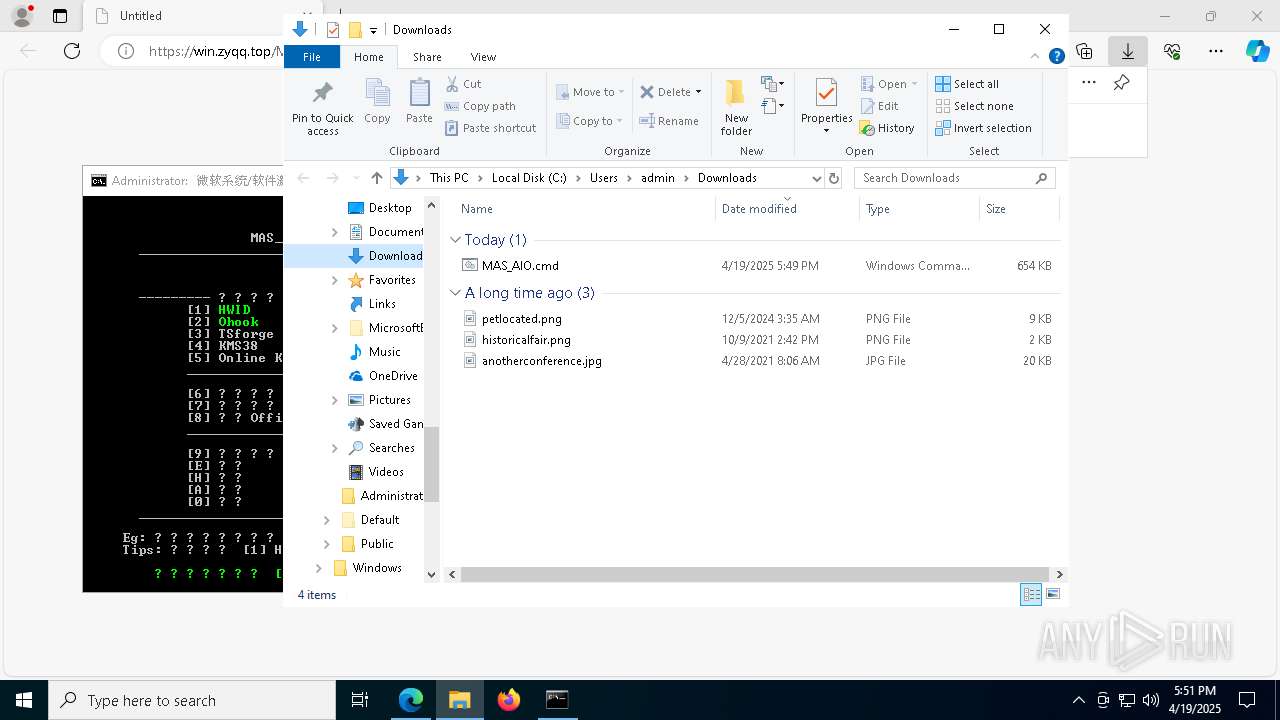
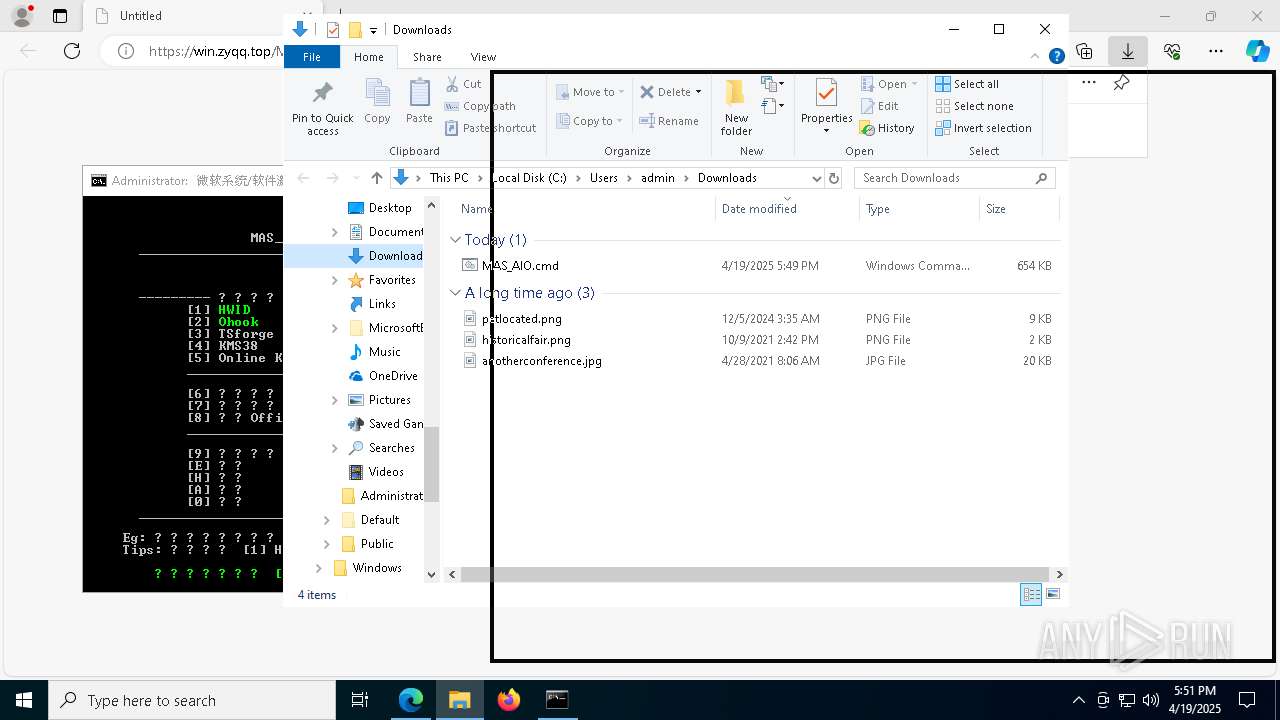
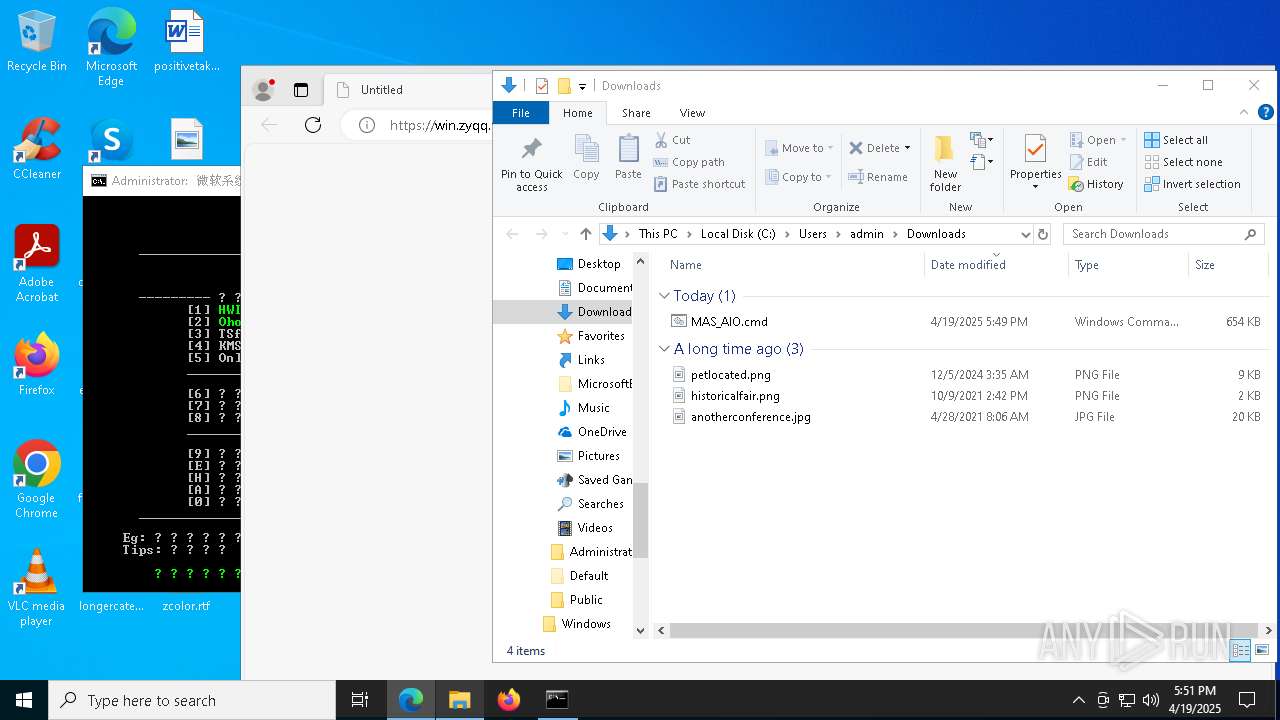
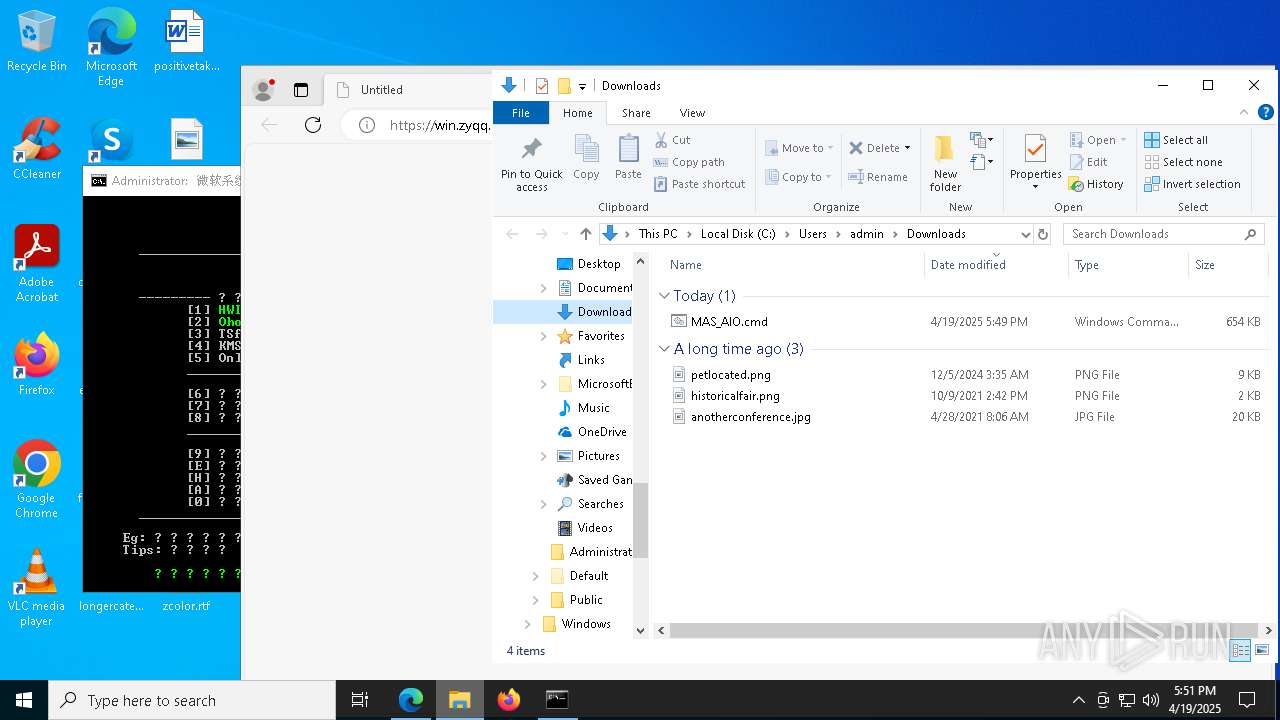
| URL: | https://win.zyqq.top/MAS_AIO.cmd |
| Full analysis: | https://app.any.run/tasks/f40592a3-1fcf-4e1b-99bc-10078f0e1f24 |
| Verdict: | Malicious activity |
| Analysis date: | April 19, 2025, 17:48:57 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 92A197E5903718CB3F8028EB3D03D839 |
| SHA1: | 6A2D3C4F6F9ABD0862A0702431832C1AEE52EB21 |
| SHA256: | 733260C266766B98E047E91777569CE634343A47FFFA0BE2F61BB22E74574983 |
| SSDEEP: | 3:N8d/mLkzln:2F |
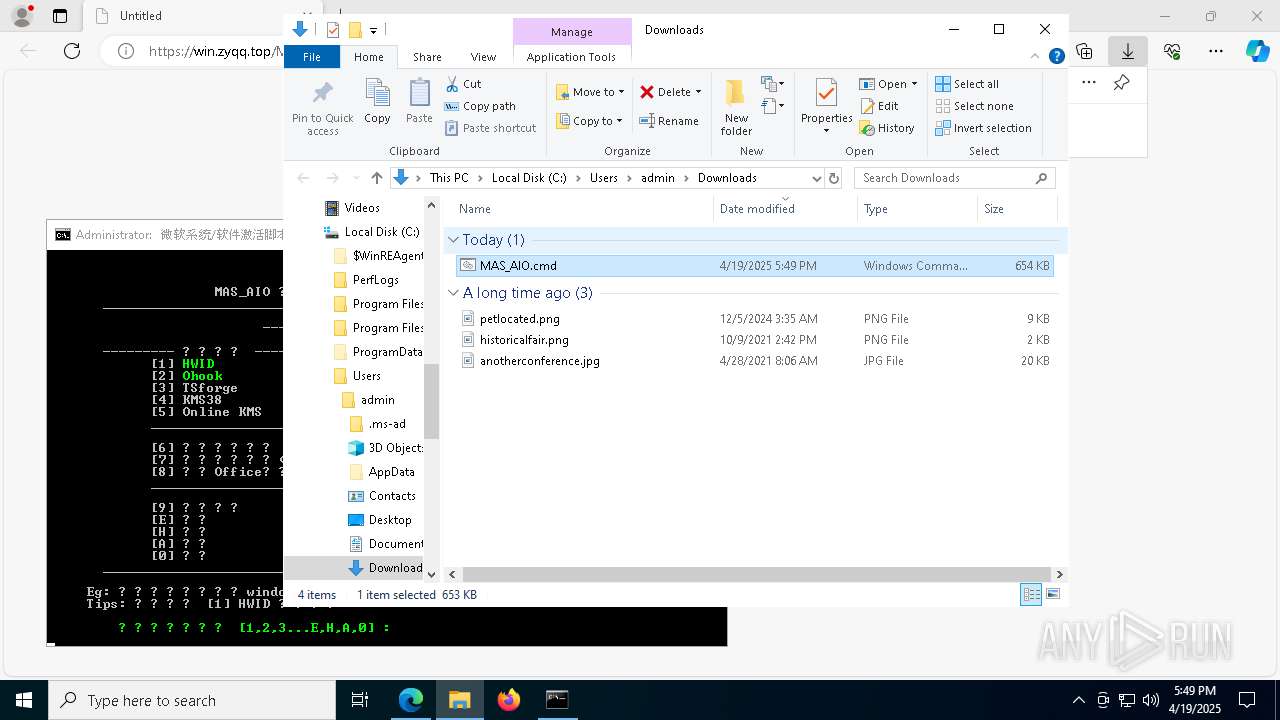
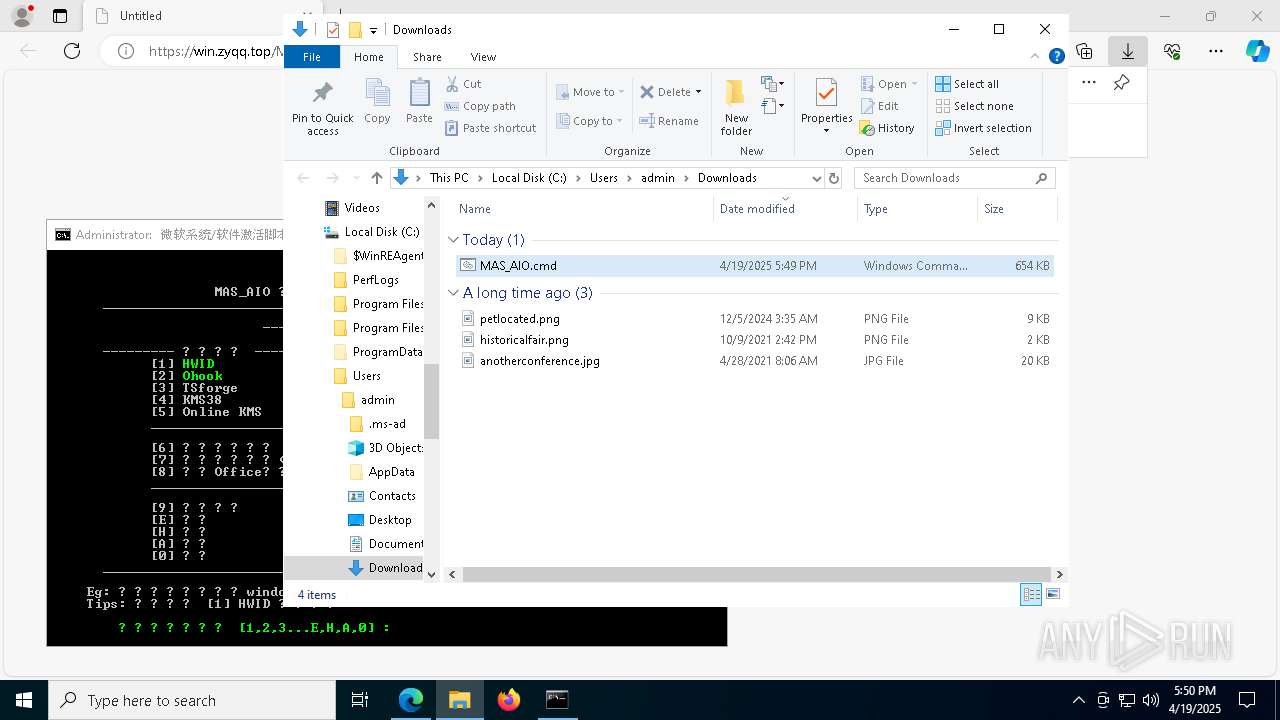
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts application with an unusual extension
- cmd.exe (PID: 1676)
- cmd.exe (PID: 960)
- cmd.exe (PID: 6468)
Windows service management via SC.EXE
- sc.exe (PID: 6816)
- sc.exe (PID: 6676)
- sc.exe (PID: 5988)
Starts SC.EXE for service management
- cmd.exe (PID: 1676)
- cmd.exe (PID: 960)
- cmd.exe (PID: 6468)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1676)
- cmd.exe (PID: 960)
- cmd.exe (PID: 6468)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6512)
- cmd.exe (PID: 1676)
- powershell.exe (PID: 3300)
- cmd.exe (PID: 6048)
- powershell.exe (PID: 4740)
- cmd.exe (PID: 960)
- cmd.exe (PID: 6468)
- cmd.exe (PID: 4528)
Application launched itself
- cmd.exe (PID: 1676)
- cmd.exe (PID: 6512)
- cmd.exe (PID: 6048)
- cmd.exe (PID: 960)
- cmd.exe (PID: 6468)
- cmd.exe (PID: 4528)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 2984)
- cmd.exe (PID: 6004)
- cmd.exe (PID: 4428)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2984)
- cmd.exe (PID: 1676)
- cmd.exe (PID: 6004)
- cmd.exe (PID: 960)
- cmd.exe (PID: 4428)
- cmd.exe (PID: 6468)
Executing commands from ".cmd" file
- cmd.exe (PID: 1676)
- powershell.exe (PID: 3300)
- cmd.exe (PID: 960)
- powershell.exe (PID: 4740)
- cmd.exe (PID: 6468)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 2984)
- cmd.exe (PID: 6004)
- cmd.exe (PID: 4428)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 3784)
- powershell.exe (PID: 4000)
- powershell.exe (PID: 5352)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 3784)
- powershell.exe (PID: 4000)
- powershell.exe (PID: 5352)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 3784)
- powershell.exe (PID: 4000)
- powershell.exe (PID: 5352)
INFO
Application launched itself
- msedge.exe (PID: 7356)
Reads the computer name
- identity_helper.exe (PID: 5344)
Manual execution by a user
- cmd.exe (PID: 1676)
Checks supported languages
- identity_helper.exe (PID: 5344)
- chcp.com (PID: 1660)
- chcp.com (PID: 5384)
- chcp.com (PID: 732)
- mode.com (PID: 6760)
Changes the display of characters in the console
- cmd.exe (PID: 1676)
- cmd.exe (PID: 960)
- cmd.exe (PID: 6468)
Checks operating system version
- cmd.exe (PID: 1676)
- cmd.exe (PID: 960)
- cmd.exe (PID: 6468)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 3784)
- powershell.exe (PID: 4000)
- powershell.exe (PID: 5352)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 3784)
- powershell.exe (PID: 4000)
- powershell.exe (PID: 5352)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 3784)
- powershell.exe (PID: 4000)
- powershell.exe (PID: 5352)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 3784)
- powershell.exe (PID: 4000)
- powershell.exe (PID: 5352)
Starts MODE.COM to configure console settings
- mode.com (PID: 6760)
Checks proxy server information
- slui.exe (PID: 8104)
Reads the software policy settings
- slui.exe (PID: 8104)
Executable content was dropped or overwritten
- msedge.exe (PID: 7448)
The sample compiled with english language support
- msedge.exe (PID: 7448)
Reads Environment values
- identity_helper.exe (PID: 5344)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
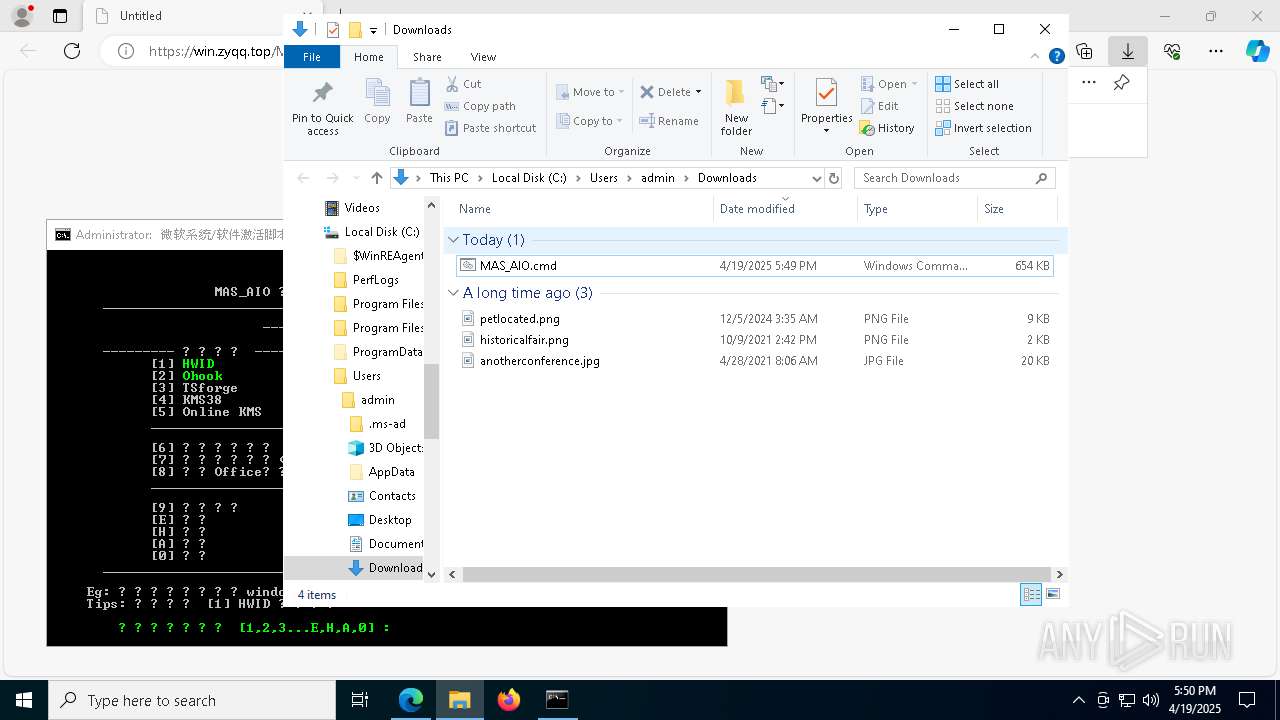
Total processes
266
Monitored processes
130
Malicious processes
4
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5504 --field-trial-handle=2400,i,4952009309081839569,215558927959826955,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 208 | fltmc | C:\Windows\System32\fltMC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Filter Manager Control Program Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "-el" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6648 --field-trial-handle=2400,i,4952009309081839569,215558927959826955,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 728 | choice /C:123456789EHA0 /N | C:\Windows\System32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Offers the user a choice Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo prompt $E " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 896 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=4432 --field-trial-handle=2400,i,4952009309081839569,215558927959826955,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 960 | "C:\WINDOWS\System32\cmd.exe" /c ""C:\Users\admin\Downloads\MAS_AIO.cmd" -el " | C:\Windows\System32\cmd.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4296 --field-trial-handle=2400,i,4952009309081839569,215558927959826955,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
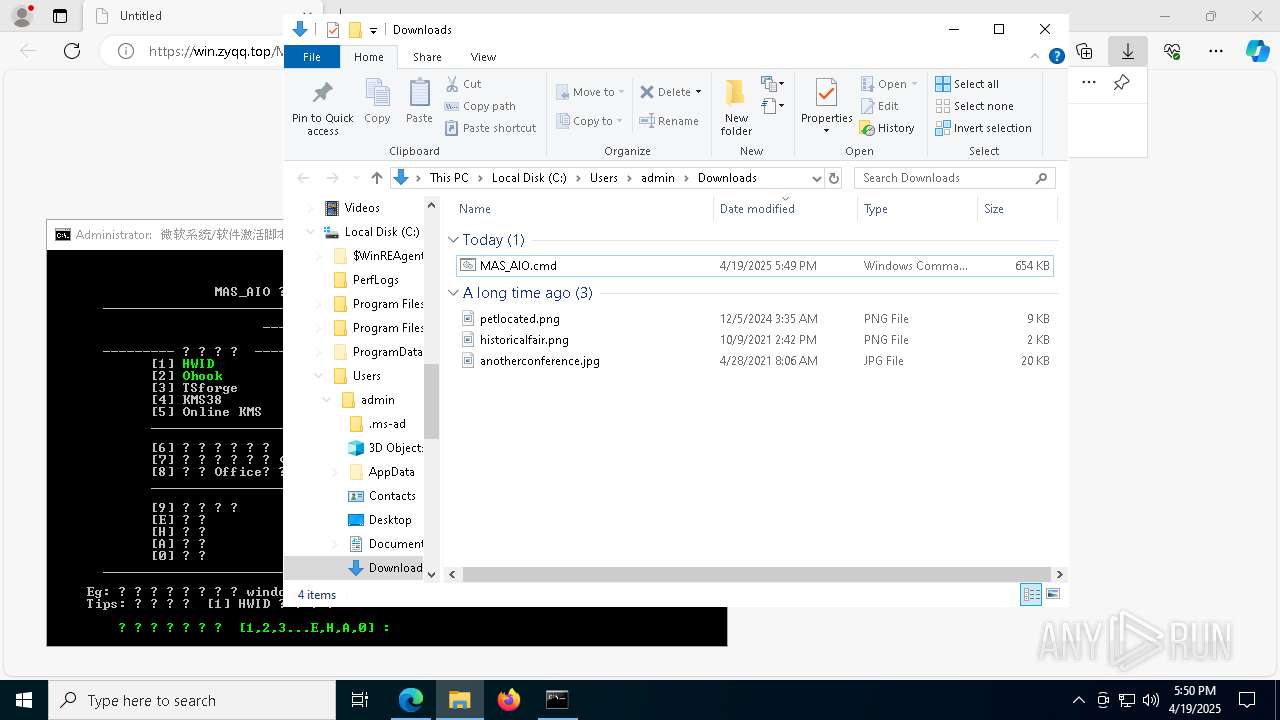
Total events
35 800
Read events
35 788
Write events
12
Delete events
0
Modification events
| (PID) Process: | (7356) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7356) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7356) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7356) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7356) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: BBB9B288BB912F00 | |||
| (PID) Process: | (7356) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 56E4BC88BB912F00 | |||
| (PID) Process: | (7356) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328332 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {16B0397A-2510-442D-9086-0B4CD996CB84} | |||
| (PID) Process: | (7356) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (7356) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (7356) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
Executable files
15
Suspicious files
398
Text files
102
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7356 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10ba0b.TMP | — | |
MD5:— | SHA256:— | |||
| 7356 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7356 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10ba1a.TMP | — | |
MD5:— | SHA256:— | |||
| 7356 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7356 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10ba0b.TMP | — | |
MD5:— | SHA256:— | |||
| 7356 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7356 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10ba3a.TMP | — | |
MD5:— | SHA256:— | |||
| 7356 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7356 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10ba49.TMP | — | |
MD5:— | SHA256:— | |||
| 7356 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
52
DNS requests
68
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1388 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7432 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1745625040&P2=404&P3=2&P4=GtLPpBAcIlVSs16KjT8EvaMYkS5t5oHTFZZG7BdzoAk3ak0j8kRYHOp8dAYPK0OxWd3rfgSN0P95LKP4I%2blaEA%3d%3d | unknown | — | — | whitelisted |
1388 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7432 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1745625040&P2=404&P3=2&P4=GtLPpBAcIlVSs16KjT8EvaMYkS5t5oHTFZZG7BdzoAk3ak0j8kRYHOp8dAYPK0OxWd3rfgSN0P95LKP4I%2blaEA%3d%3d | unknown | — | — | whitelisted |
7432 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1745625040&P2=404&P3=2&P4=GtLPpBAcIlVSs16KjT8EvaMYkS5t5oHTFZZG7BdzoAk3ak0j8kRYHOp8dAYPK0OxWd3rfgSN0P95LKP4I%2blaEA%3d%3d | unknown | — | — | whitelisted |
7432 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cf34b06a-2f53-4bd0-9d11-b58cf2e820a4?P1=1745625039&P2=404&P3=2&P4=XYM2oNR57T7FH7yXmqSVTxBMd7cfAiV9bzRuxR7X042ffQiFnsdktaP3cc0SwaExc3CvgBbHngvZkbxwQDIDGw%3d%3d | unknown | — | — | whitelisted |
7432 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cf34b06a-2f53-4bd0-9d11-b58cf2e820a4?P1=1745625039&P2=404&P3=2&P4=XYM2oNR57T7FH7yXmqSVTxBMd7cfAiV9bzRuxR7X042ffQiFnsdktaP3cc0SwaExc3CvgBbHngvZkbxwQDIDGw%3d%3d | unknown | — | — | whitelisted |
7432 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cf34b06a-2f53-4bd0-9d11-b58cf2e820a4?P1=1745625039&P2=404&P3=2&P4=XYM2oNR57T7FH7yXmqSVTxBMd7cfAiV9bzRuxR7X042ffQiFnsdktaP3cc0SwaExc3CvgBbHngvZkbxwQDIDGw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7356 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
win.zyqq.top |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |