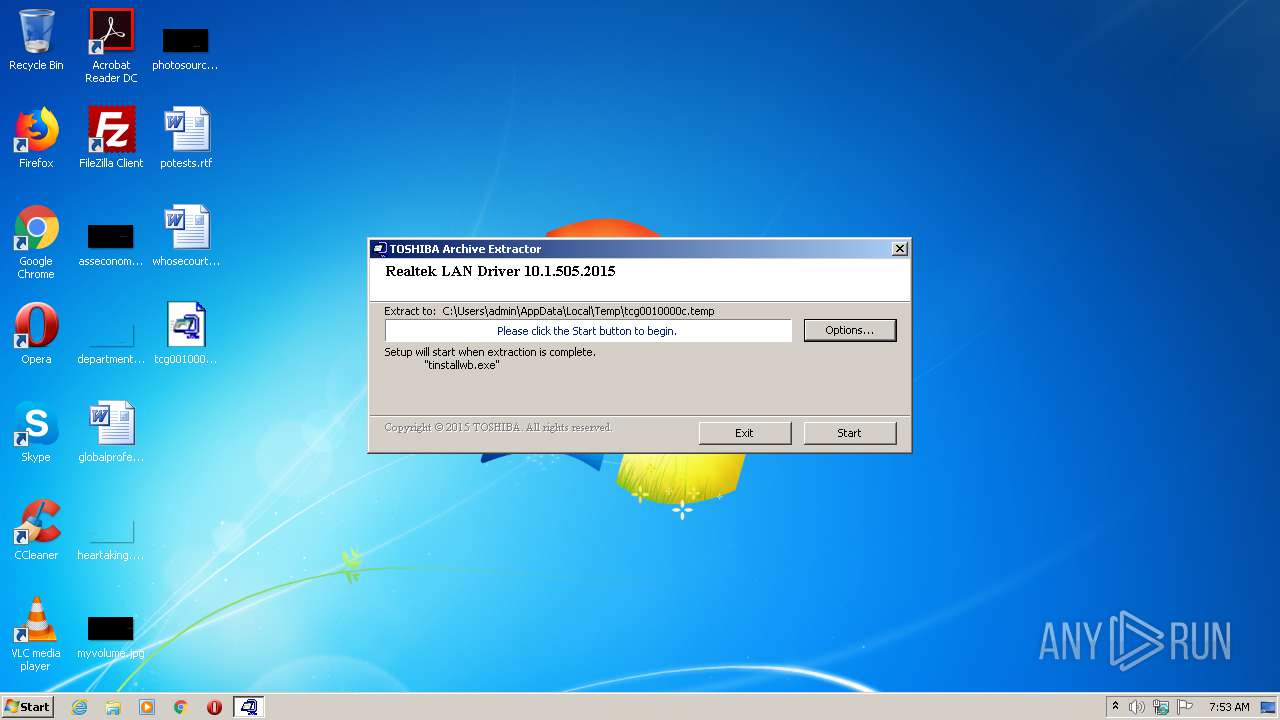
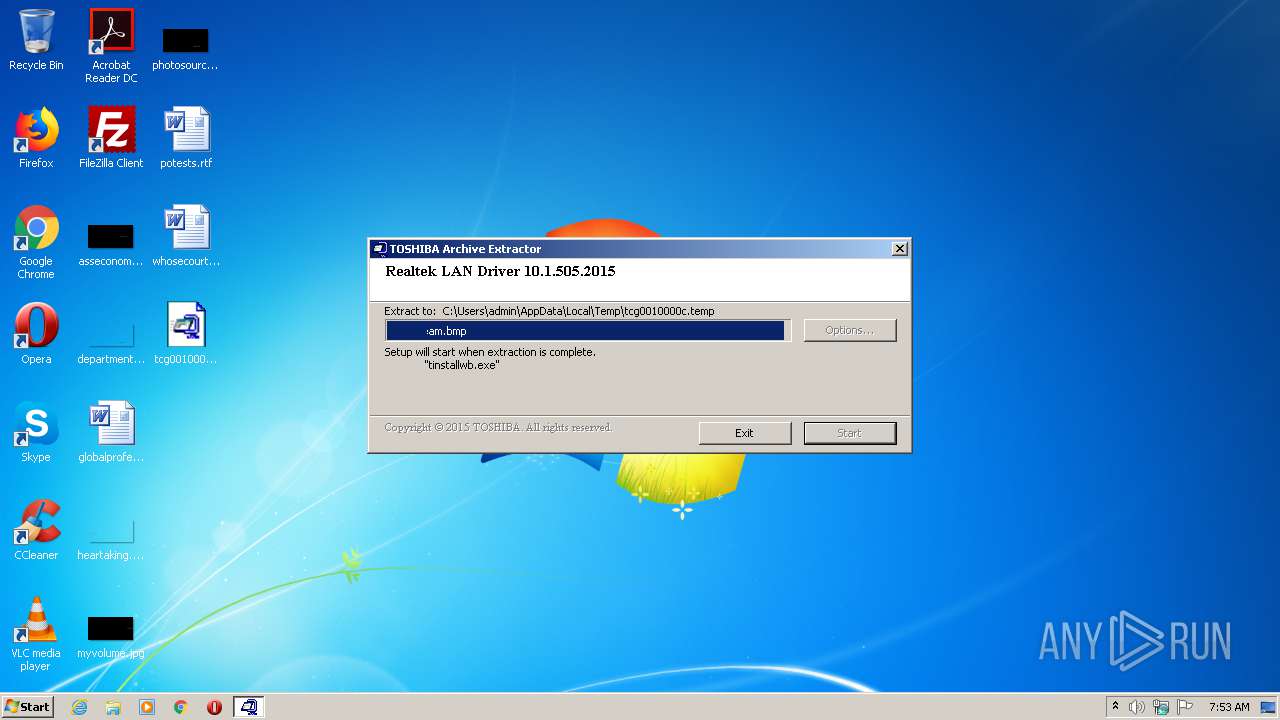
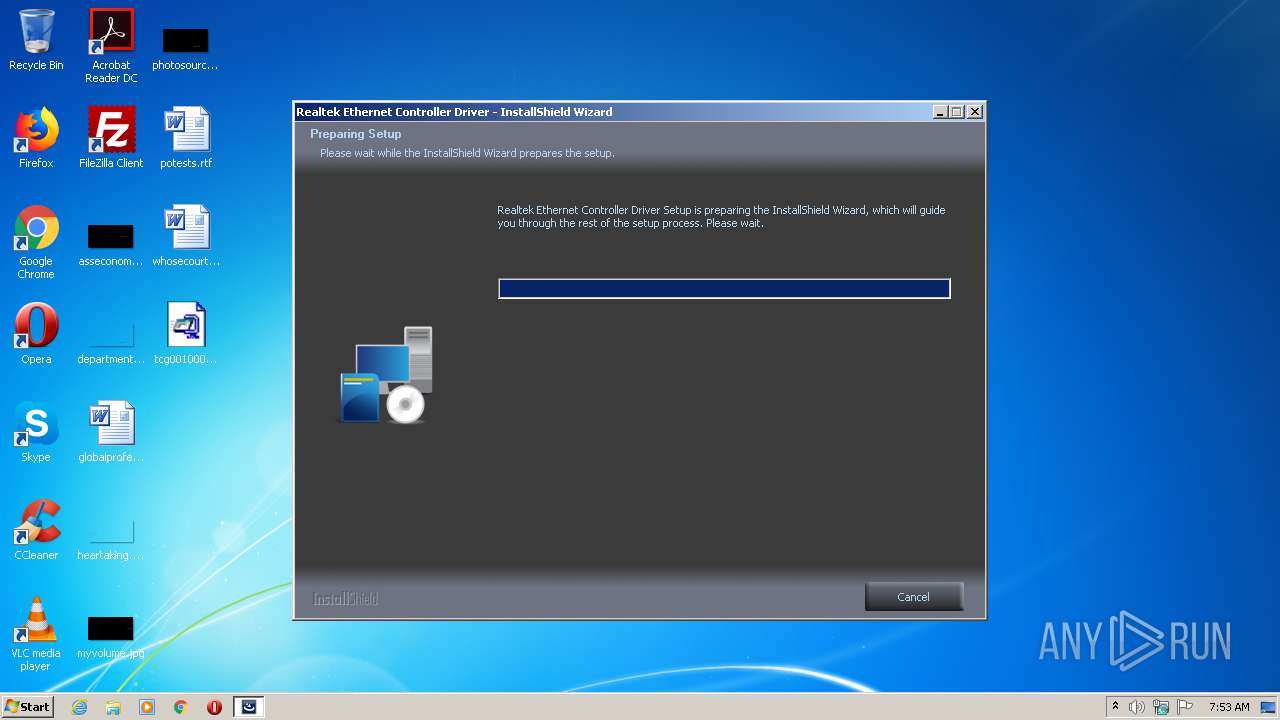
| File name: | tcg0010000c.exe |
| Full analysis: | https://app.any.run/tasks/524f8301-ff1b-45c9-8bbe-d73963a88e21 |
| Verdict: | Malicious activity |
| Analysis date: | June 16, 2020, 06:53:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 034418994D0D408A5F58CC59FC0DC7BE |
| SHA1: | AC1D92D3849332906A0975B4C4CE0B43EF1ADC13 |
| SHA256: | 732EE5E97C28A49C203EB28A0F1B67C3CE4E824633BD6F58F848F7D4D763FD0D |
| SSDEEP: | 393216:f3goynY7C6l+ScEjukmfjsr59aj6mqdYspb:fg9Y7/l65kusfHmqz9 |
MALICIOUS
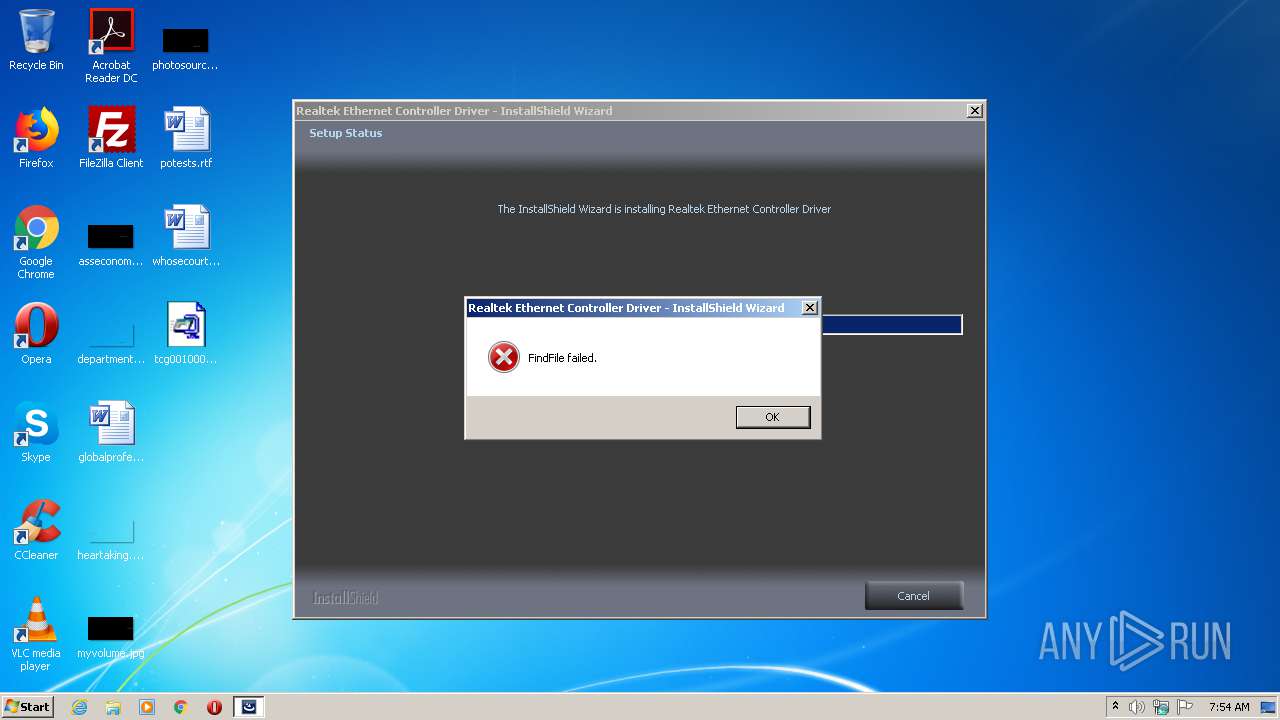
Application was dropped or rewritten from another process
- tinstallwb.exe (PID: 2504)
- setup.exe (PID: 4044)
- tinstallwb.exe (PID: 1944)
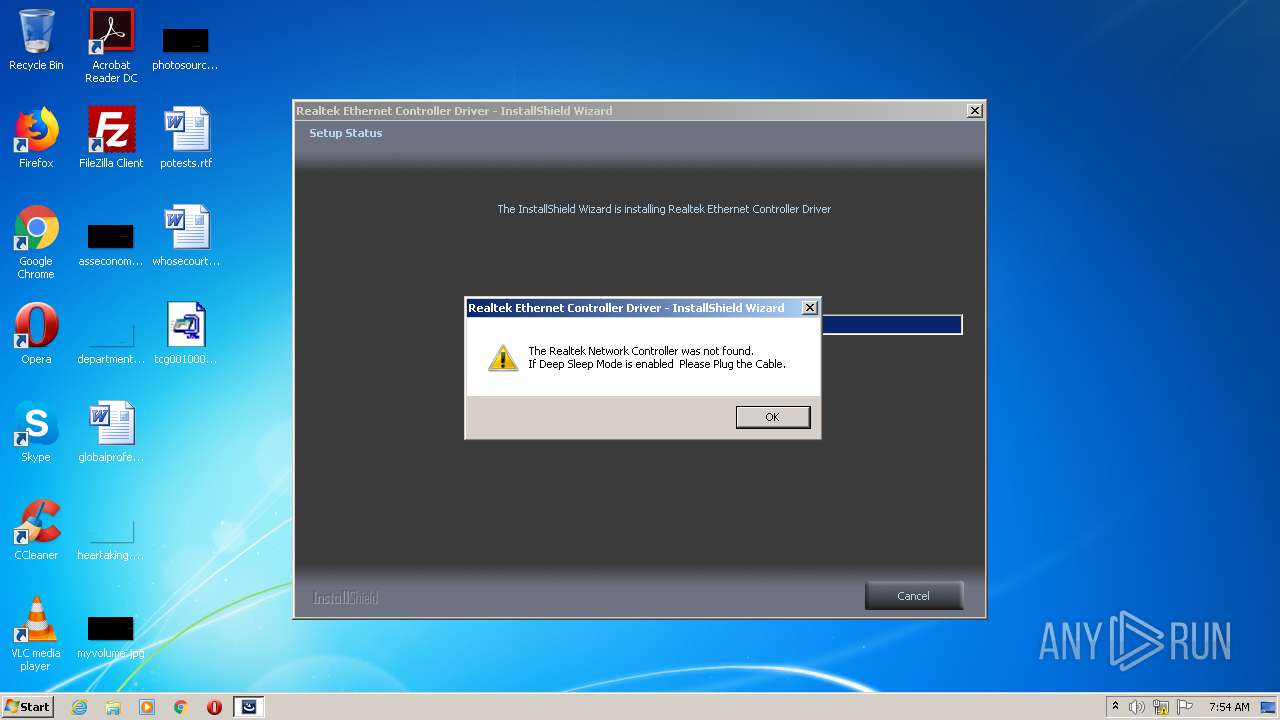
- RTINSTALLER32.EXE (PID: 1508)
- RTINSTALLER32.EXE (PID: 2720)
- RTINSTALLER32.EXE (PID: 1520)
Loads dropped or rewritten executable
- tinstallwb.exe (PID: 1944)
- setup.exe (PID: 4044)
Actions looks like stealing of personal data
- tinstallwb.exe (PID: 1944)
SUSPICIOUS
Reads Environment values
- tinstallwb.exe (PID: 1944)
Searches for installed software
- setup.exe (PID: 4044)
Executed as Windows Service
- vssvc.exe (PID: 3840)
Creates a software uninstall entry
- setup.exe (PID: 4044)
Executable content was dropped or overwritten
- setup.exe (PID: 4044)
- tcg0010000c.exe (PID: 3024)
Creates files in the program directory
- RTINSTALLER32.EXE (PID: 1520)
- setup.exe (PID: 4044)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 3840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:03:21 00:03:19+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 77824 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8425 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Mar-2013 23:03:19 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 20-Mar-2013 23:03:19 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00012EF6 | 0x00013000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67232 |
.rdata | 0x00014000 | 0x00005A2C | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.42261 |
.data | 0x0001A000 | 0x00005E1C | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.48975 |
.rsrc | 0x00020000 | 0x00014DC0 | 0x00015000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.56174 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.26144 | 1062 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.13753 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.3024 | 206 | Latin 1 / Western European | Indonesian - Indonesia (Bahasa) | RT_STRING |
8 | 3.20004 | 1128 | Latin 1 / Western European | Indonesian - Indonesia (Bahasa) | RT_STRING |
9 | 3.38105 | 1310 | Latin 1 / Western European | Indonesian - Indonesia (Bahasa) | RT_STRING |
10 | 3.26464 | 824 | Latin 1 / Western European | Indonesian - Indonesia (Bahasa) | RT_STRING |
103 | 2.93021 | 132 | Latin 1 / Western European | English - United States | RT_DIALOG |
107 | 2.37086 | 34 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
129 | 3.02503 | 356 | Latin 1 / Western European | English - United States | RT_DIALOG |
130 | 2.65329 | 96 | Latin 1 / Western European | English - United States | RT_DIALOG |
Imports
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
46
Monitored processes
8
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1508 | "C:\Program Files\Realtek\NICDRV_8169\RTINSTALLER32.EXE" /q /VISTA8169 /X86 /f WIN7\ | C:\Program Files\Realtek\NICDRV_8169\RTINSTALLER32.EXE | — | setup.exe | |||||||||||
User: admin Company: Realtek Semiconductor Corp. Integrity Level: HIGH Description: RTInstaller Exit code: 2 Version: 1.0.0.31 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Realtek\NICDRV_8169\RTINSTALLER32.EXE" /CHKNICEXIST /VISTA8169 /chkvid 10ec /chkpid 8168 /chksvid 0000 /chkssid 0000 | C:\Program Files\Realtek\NICDRV_8169\RTINSTALLER32.EXE | — | setup.exe | |||||||||||
User: admin Company: Realtek Semiconductor Corp. Integrity Level: HIGH Description: RTInstaller Exit code: 0 Version: 1.0.0.31 Modules
| |||||||||||||||
| 1944 | "C:\Users\admin\AppData\Local\Temp\tcg0010000c.temp\tinstallwb.exe" | C:\Users\admin\AppData\Local\Temp\tcg0010000c.temp\tinstallwb.exe | tcg0010000c.exe | ||||||||||||
User: admin Company: TOSHIBA Integrity Level: HIGH Description: Installer Exit code: 0 Version: 55.13.0320.22 Modules
| |||||||||||||||
| 2504 | "C:\Users\admin\AppData\Local\Temp\tcg0010000c.temp\tinstallwb.exe" | C:\Users\admin\AppData\Local\Temp\tcg0010000c.temp\tinstallwb.exe | — | tcg0010000c.exe | |||||||||||
User: admin Company: TOSHIBA Integrity Level: MEDIUM Description: Installer Exit code: 3221226540 Version: 55.13.0320.22 Modules
| |||||||||||||||
| 2720 | "C:\Program Files\Realtek\NICDRV_8169\RTINSTALLER32.EXE" /I /NCFI /VISTA8169 /X86 /spn WOL_SETTING /spv WOL_MAG_ONLY /spn WolShutdownLinkSpeed /spv 1 /f WIN7\ | C:\Program Files\Realtek\NICDRV_8169\RTINSTALLER32.EXE | — | setup.exe | |||||||||||
User: admin Company: Realtek Semiconductor Corp. Integrity Level: HIGH Description: RTInstaller Exit code: 2 Version: 1.0.0.31 Modules
| |||||||||||||||
| 3024 | "C:\Users\admin\Desktop\tcg0010000c.exe" | C:\Users\admin\Desktop\tcg0010000c.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3840 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
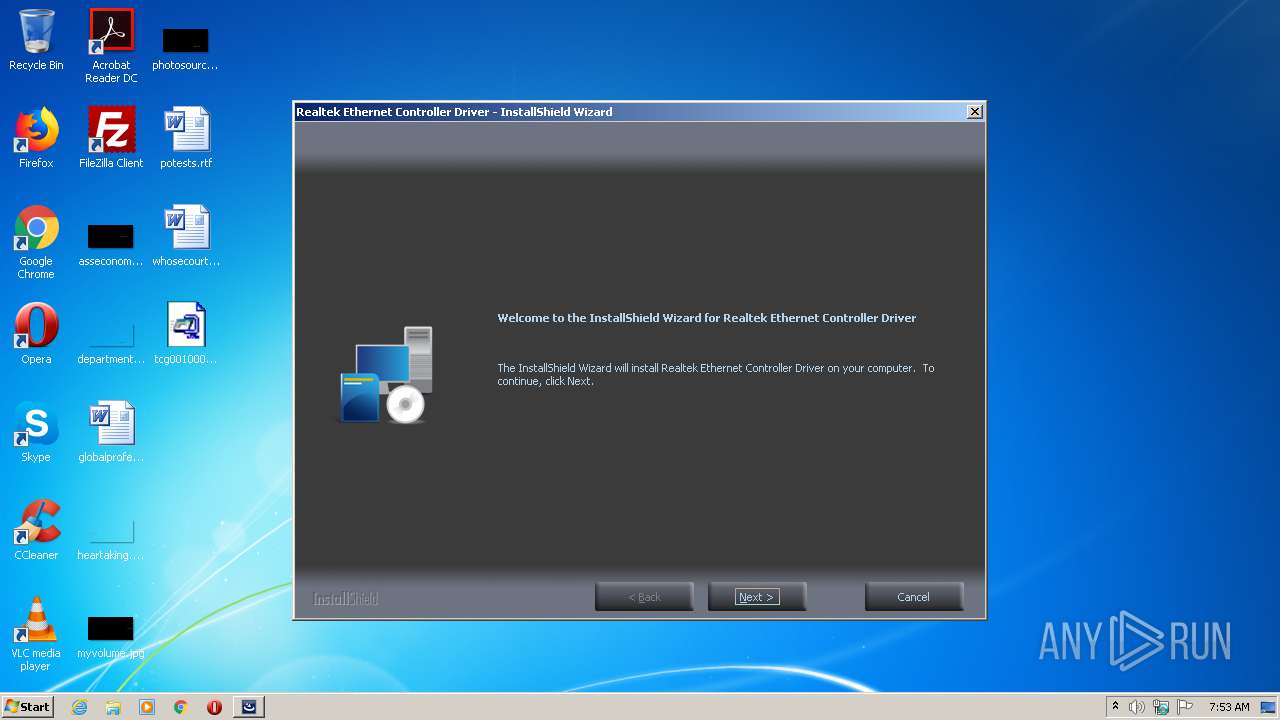
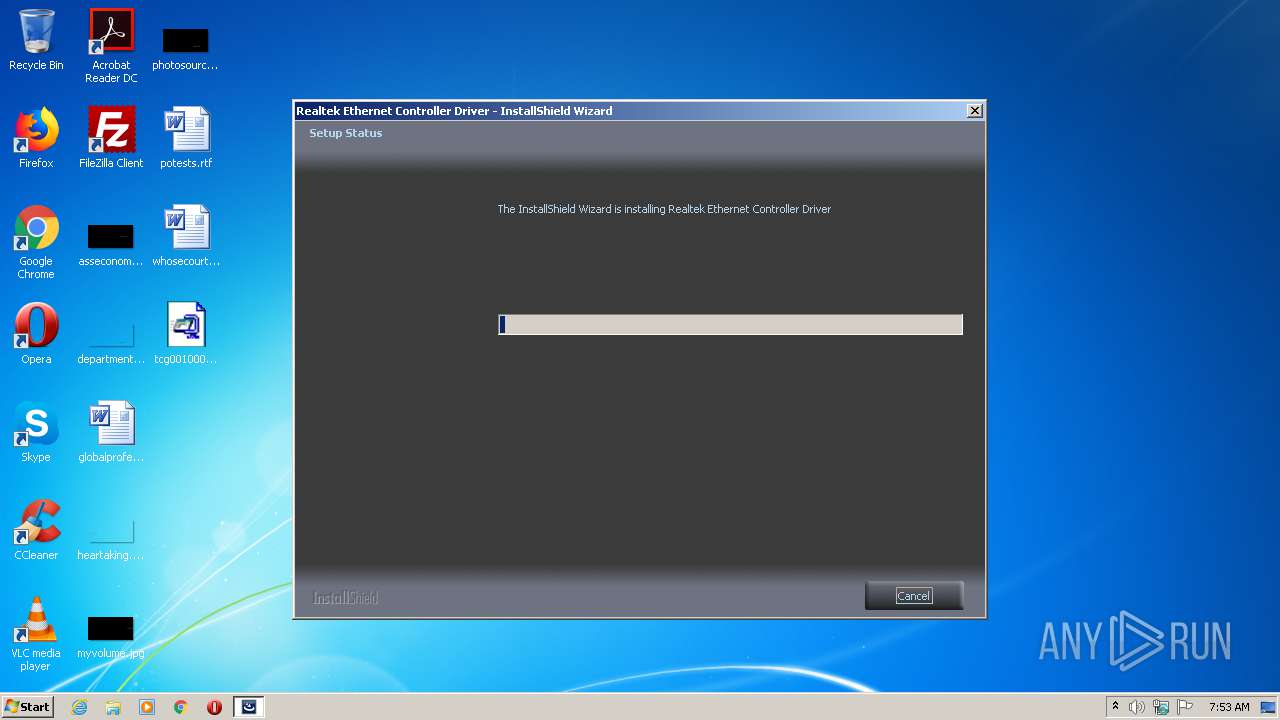
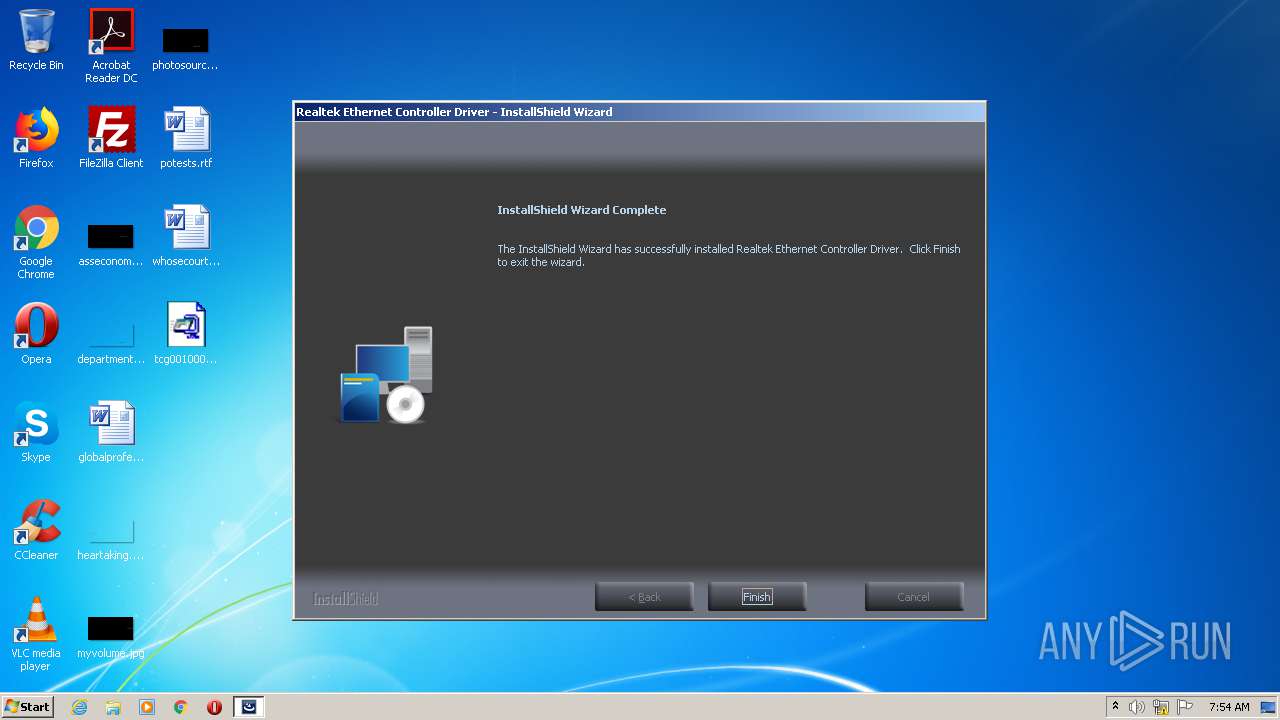
| 4044 | "setup.exe" | C:\Users\admin\AppData\Local\Temp\tcg0010000c.temp\setup.exe | tinstallwb.exe | ||||||||||||
User: admin Company: Realtek Integrity Level: HIGH Description: InstallScript Setup Launcher Unicode Exit code: 0 Version: 1.00.0033 Modules
| |||||||||||||||
Total events
698
Read events
520
Write events
177
Delete events
1
Modification events
| (PID) Process: | (1944) tinstallwb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\TOSHIBA\swtos |
| Operation: | write | Name: | DMIValid |
Value: 0 | |||
| (PID) Process: | (1944) tinstallwb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\TOSHIBA\swtos |
| Operation: | write | Name: | VNMODEL |
Value: DELL | |||
| (PID) Process: | (1944) tinstallwb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\TOSHIBA\swtos |
| Operation: | write | Name: | VNPRODUCT |
Value: DELL | |||
| (PID) Process: | (1944) tinstallwb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\TOSHIBA\swtos |
| Operation: | write | Name: | VNPARTNUM |
Value: | |||
| (PID) Process: | (1944) tinstallwb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\TOSHIBA\swtos |
| Operation: | write | Name: | VNDOWNLID |
Value: | |||
| (PID) Process: | (1944) tinstallwb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\TOSHIBA\swtos |
| Operation: | write | Name: | VNSOFTNUM |
Value: | |||
| (PID) Process: | (1944) tinstallwb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\TOSHIBA\swtos |
| Operation: | write | Name: | VNOEMSTRING |
Value: | |||
| (PID) Process: | (1944) tinstallwb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\TOSHIBA\swtos |
| Operation: | write | Name: | DMIValid |
Value: 1 | |||
| (PID) Process: | (1944) tinstallwb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\TOSHIBA\swtos |
| Operation: | write | Name: | DateDMIRead |
Value: 2020:06:16:07:53:37 | |||
| (PID) Process: | (4044) setup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 400000000000000058B28EE1AA43D601CC0F0000DC0F0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
23
Suspicious files
25
Text files
325
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3024 | tcg0010000c.exe | C:\Users\admin\AppData\Local\Temp\tcg0010000c.temp\0x0402.ini | text | |
MD5:6F82F2EFC4A5DA513E0222F47FB5FC2D | SHA256:BBE199DE9BB5156C543BC466DE606719389C93BCBFF2815D9FAE01659A415BD0 | |||
| 3024 | tcg0010000c.exe | C:\Users\admin\AppData\Local\Temp\tcg0010000c.temp\0x0405.ini | text | |
MD5:9FB56981DD06830B30CD9CADF54270D6 | SHA256:9302A3E694DE8CC84947B41350A7F8AE0880E5D2F3FDBD67CD56444BF0BC3A43 | |||
| 3024 | tcg0010000c.exe | C:\Users\admin\AppData\Local\Temp\tcg0010000c.temp\0x0403.ini | text | |
MD5:04B3D8BE6E6F17F13A3BE3F24E3AC1B0 | SHA256:BAD754F1F64BC40D1AA6D037179C4DEDB41E9237D3B5E05BFFF4F92ECF623E02 | |||
| 3024 | tcg0010000c.exe | C:\Users\admin\AppData\Local\Temp\tcg0010000c.temp\0x0408.ini | text | |
MD5:C7A740C71FB3779C8AE2626729A44389 | SHA256:D9610BF29EE0E73843595F246A58699ABE499B340AD9982831D068067161C120 | |||
| 3024 | tcg0010000c.exe | C:\Users\admin\AppData\Local\Temp\tcg0010000c.temp\0x0404.ini | text | |
MD5:EC1F8F71FA21C49BC96A17C81AD51598 | SHA256:60F176F3014342F48468FF7EA67280FA3A671C4721EBEFE7B4EE789FF65C87DF | |||
| 3024 | tcg0010000c.exe | C:\Users\admin\AppData\Local\Temp\tcg0010000c.temp\0x0413.ini | text | |
MD5:DC1C05A9FCE06CF659C20AED317DD417 | SHA256:98D6CEEF6A444B9E8450ABEFC5B72BD6B0DF1CD5D7C7CD2822EB1BD186FF8526 | |||
| 3024 | tcg0010000c.exe | C:\Users\admin\AppData\Local\Temp\tcg0010000c.temp\0x0418.ini | text | |
MD5:21B6308422FAC36FADD143BC7166D082 | SHA256:B1F0AC697CBD5C6A4E10EDAEDBFB28BA2EBDDFC5FD9E391B3B2EC15123119295 | |||
| 3024 | tcg0010000c.exe | C:\Users\admin\AppData\Local\Temp\tcg0010000c.temp\0x0411.ini | text | |
MD5:6EBBB5D67423D8D85F1688B561BF5304 | SHA256:E3B87E8B94AD50BBE21795B3408943F9A6D6F33813E96802962CB74B889EDFE7 | |||
| 3024 | tcg0010000c.exe | C:\Users\admin\AppData\Local\Temp\tcg0010000c.temp\0x0412.ini | text | |
MD5:73E70A6B9354E80237C8E2B3170830A0 | SHA256:316577CF74D3545D632B0DE55513A3511D654849655157CB84821B871EC081E9 | |||
| 3024 | tcg0010000c.exe | C:\Users\admin\AppData\Local\Temp\tcg0010000c.temp\0x0414.ini | text | |
MD5:E526541768A0B9A3618A2894A8E2447E | SHA256:7020C177A60A340C836576D5357305CAFEDAA4ADD1A8AD18A3E207D40BFCEAD4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report