| File name: | as100e_305.exe |
| Full analysis: | https://app.any.run/tasks/ed43db14-9ed7-4852-a458-f5dcb0fed7f5 |
| Verdict: | Malicious activity |
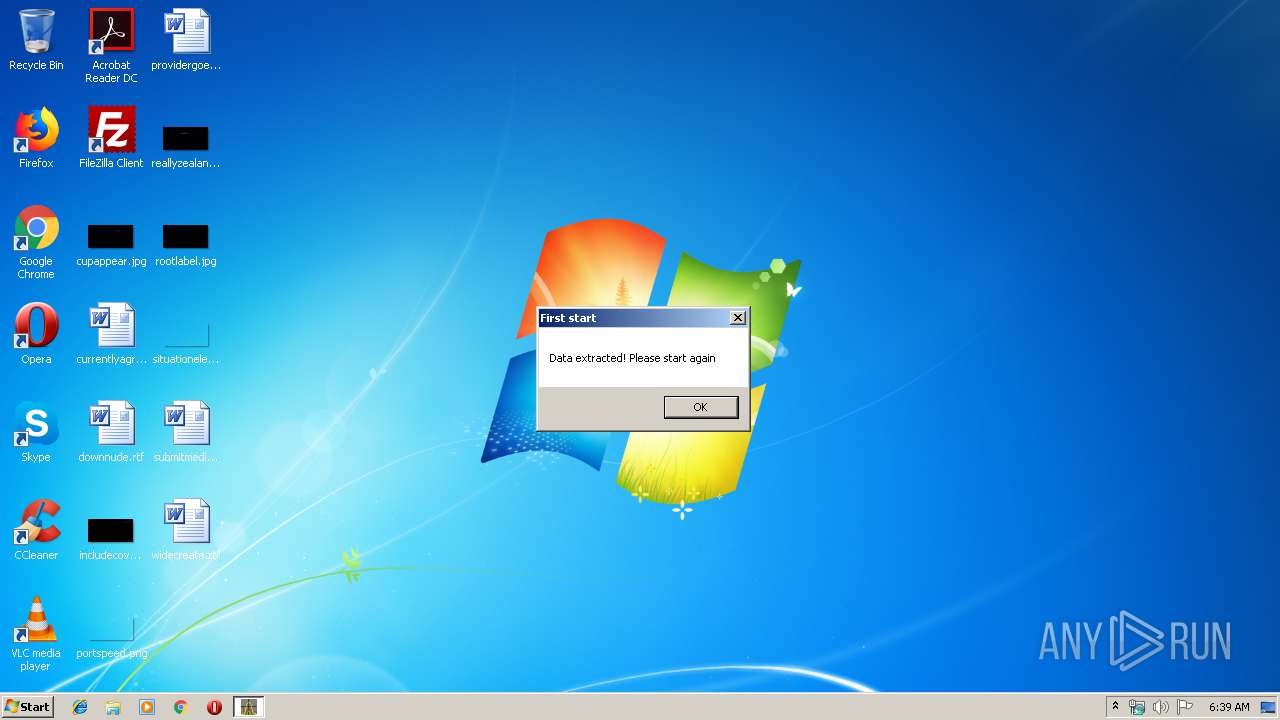
| Analysis date: | July 18, 2019, 05:39:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | E91915DAC54B28DD103079D2C5D2D7F4 |
| SHA1: | B4EC370D81209A0BF5FC50153F7EFB80C98B81E6 |
| SHA256: | 731FA388E1FB55310B72384FC8144E692A2CC87CDAE50CD0A07432492C98BB36 |
| SSDEEP: | 196608:PedC58YThaZrHHhtLZFDOjZjFnV0wAd44EwaRgWw:PW0haZrHH1JOFFmdhEw2gP |
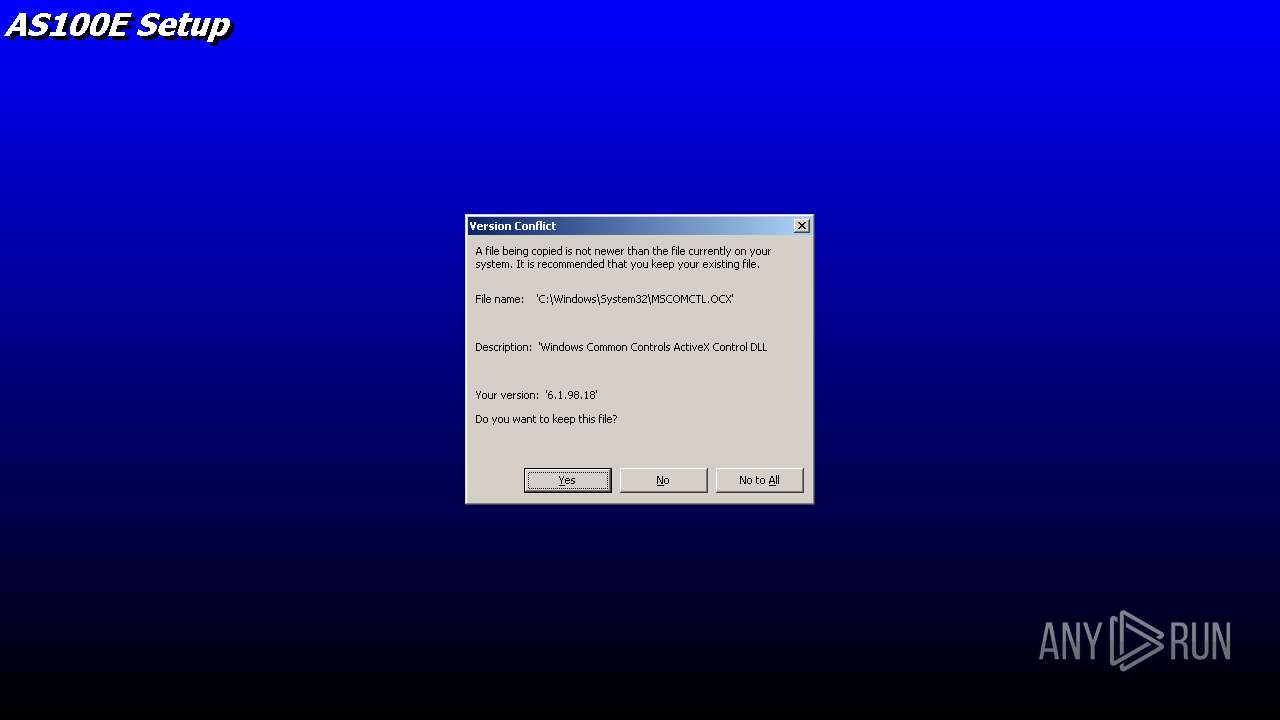
MALICIOUS
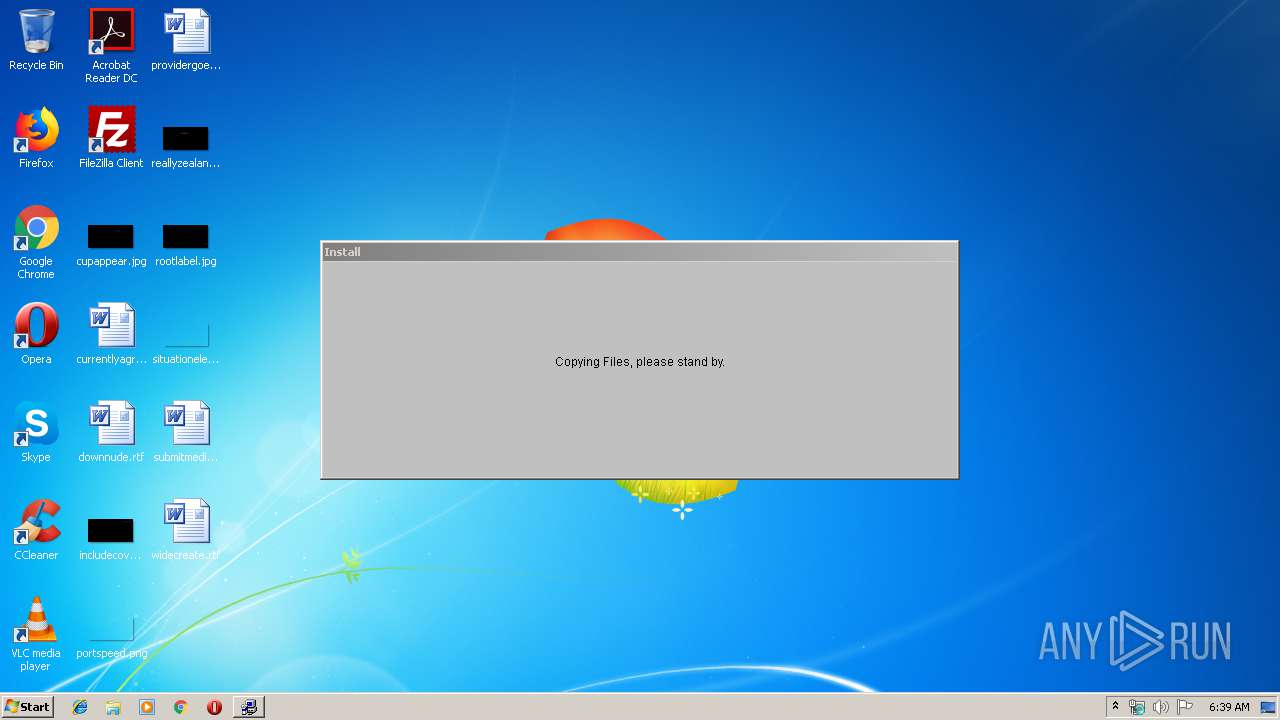
Application was dropped or rewritten from another process
- setup.exe (PID: 3116)
- setup.exe (PID: 2308)
- Setup1.exe (PID: 2052)
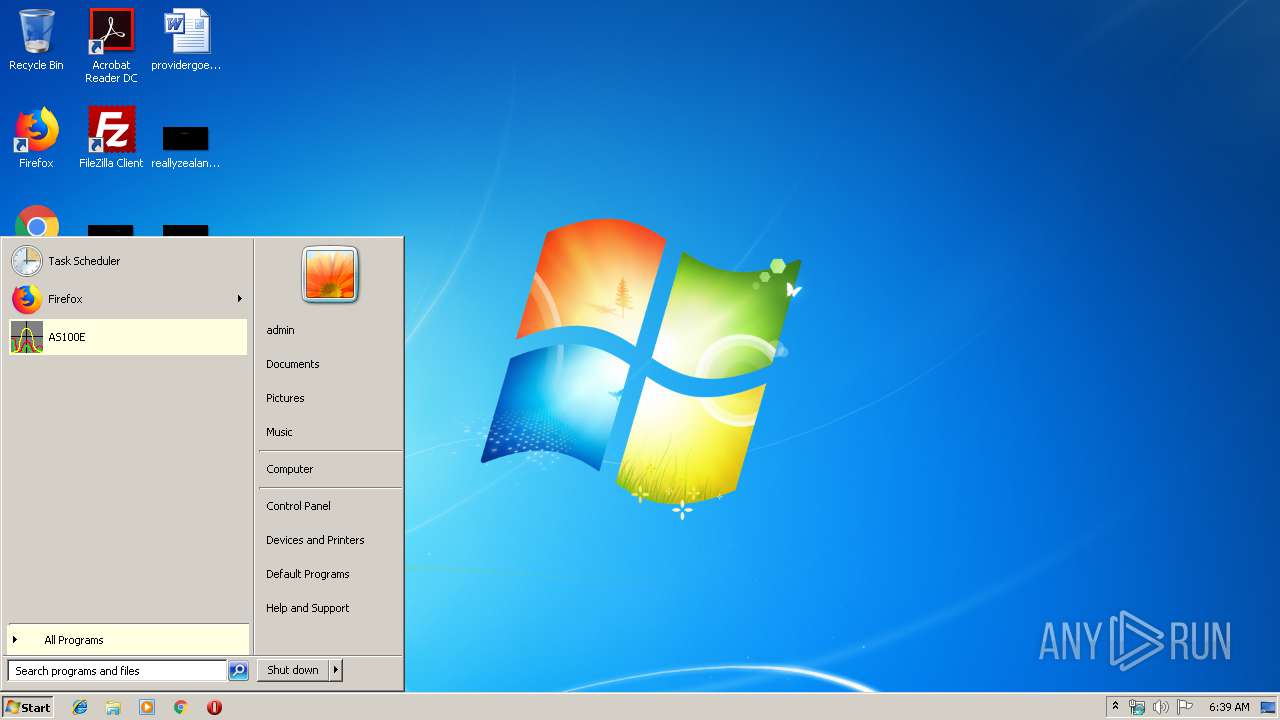
- AS100E.exe (PID: 2568)
- AS100E.exe (PID: 1864)
- AS100E.exe (PID: 3216)
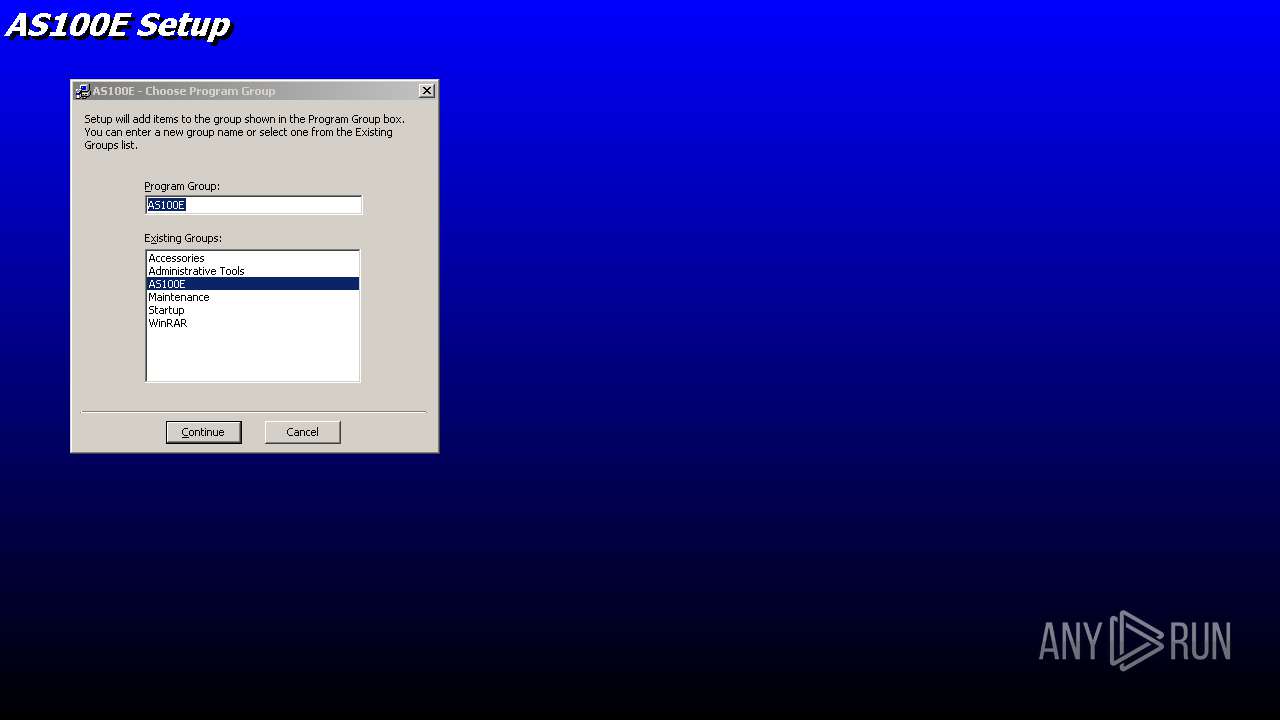
Writes to a start menu file
- setup.exe (PID: 2308)
Loads dropped or rewritten executable
- setup.exe (PID: 2308)
- Setup1.exe (PID: 2052)
- AS100E.exe (PID: 2568)
- AS100E.exe (PID: 1864)
- AS100E.exe (PID: 3216)
SUSPICIOUS
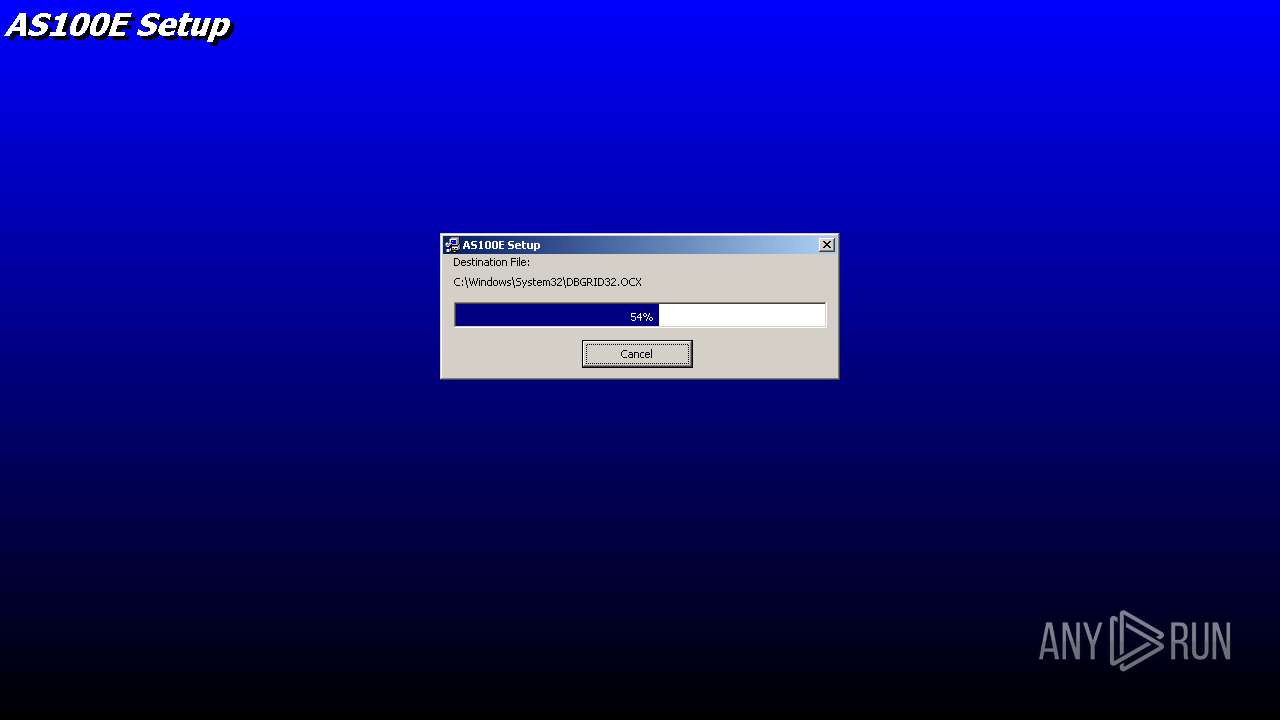
Creates files in the Windows directory
- setup.exe (PID: 2308)
- Setup1.exe (PID: 2052)
Executable content was dropped or overwritten
- as100e_305.exe (PID: 3800)
- setup.exe (PID: 2308)
- Setup1.exe (PID: 2052)
Creates files in the user directory
- setup.exe (PID: 2308)
Creates files in the program directory
- Setup1.exe (PID: 2052)
Removes files from Windows directory
- Setup1.exe (PID: 2052)
- setup.exe (PID: 2308)
Creates COM task schedule object
- Setup1.exe (PID: 2052)
Creates a software uninstall entry
- Setup1.exe (PID: 2052)
INFO
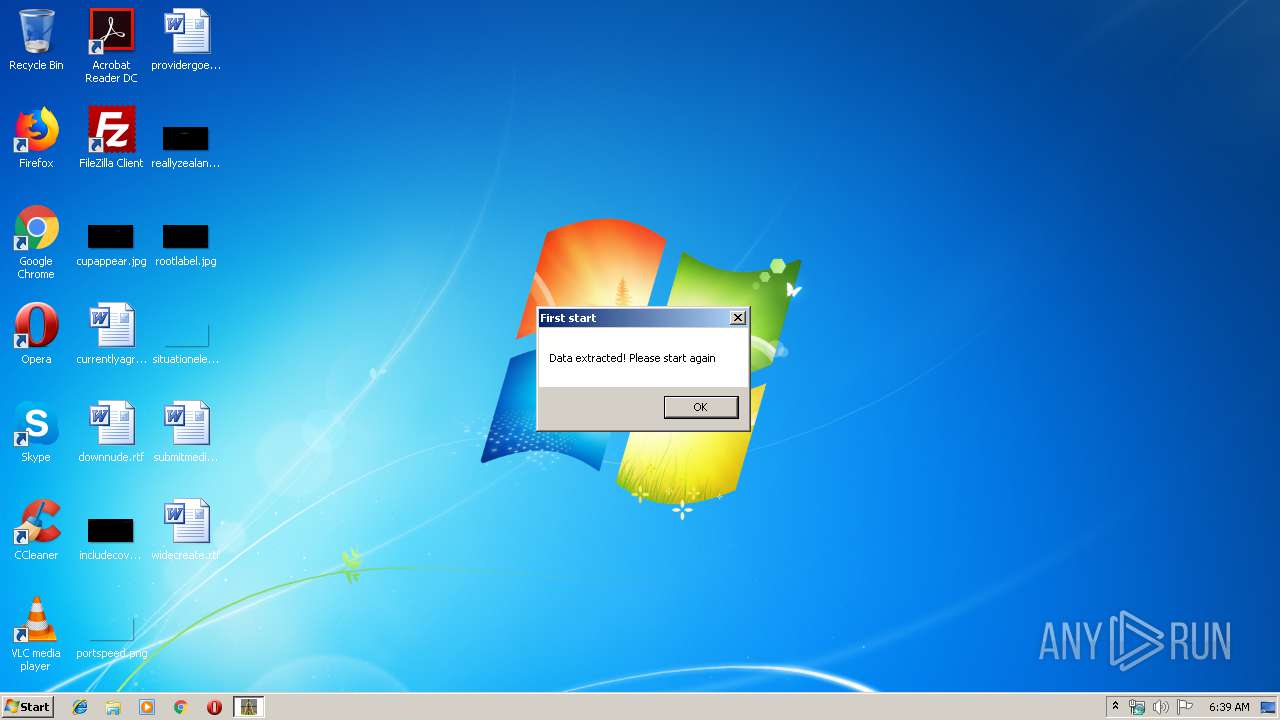
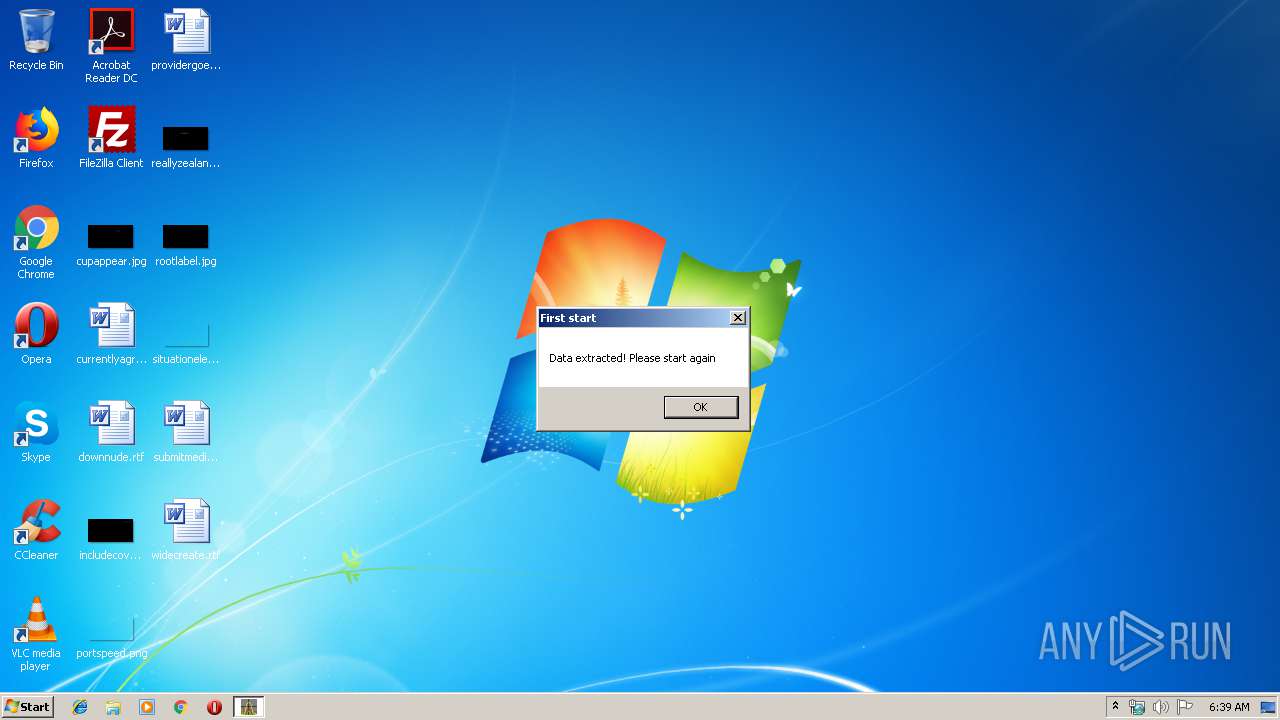
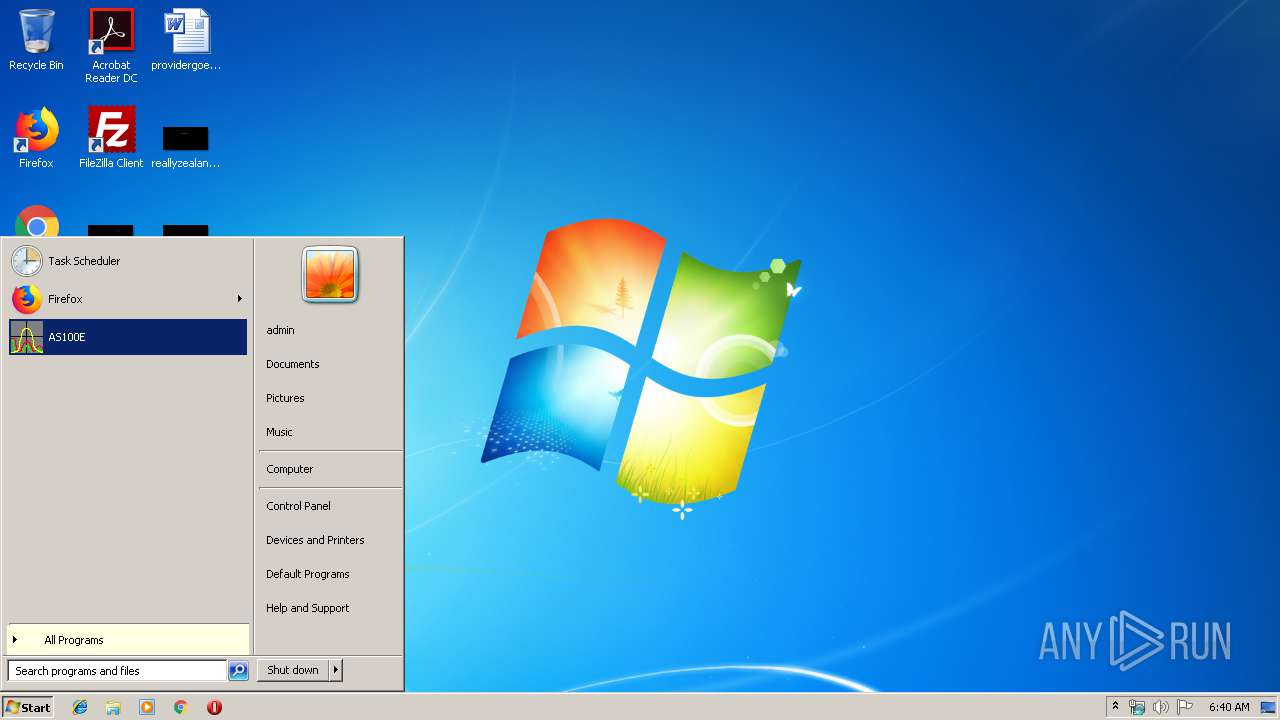
Manual execution by user
- AS100E.exe (PID: 2568)
- explorer.exe (PID: 3844)
- AS100E.exe (PID: 3216)
- AS100E.exe (PID: 1864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (38.2) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (37.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.2) |
| .exe | | | Win32 Executable (generic) (6.3) |
| .exe | | | Win16/32 Executable Delphi generic (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 28672 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 57344 |
| EntryPoint: | 0x15c70 |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0000E000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0000F000 | 0x00007000 | 0x00006E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.89332 |
.rsrc | 0x00016000 | 0x00001000 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.73582 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
4 | 3.82256 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
4092 | 6.9965 | 220 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 6.78665 | 228 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 7.42258 | 580 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 7.57182 | 892 | UNKNOWN | UNKNOWN | RT_STRING |
4096 | 7.50106 | 672 | UNKNOWN | UNKNOWN | RT_STRING |
DLGNEW | 7.31449 | 354 | UNKNOWN | UNKNOWN | RT_DIALOG |
FILEEXIST | 6.91497 | 254 | UNKNOWN | UNKNOWN | RT_DIALOG |
MAINDIALOG | 7.64039 | 866 | UNKNOWN | UNKNOWN | RT_DIALOG |
PASSWD | 6.65236 | 144 | UNKNOWN | UNKNOWN | RT_DIALOG |
Imports
KERNEL32.DLL |
advapi32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
Total processes
45
Monitored processes
11
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
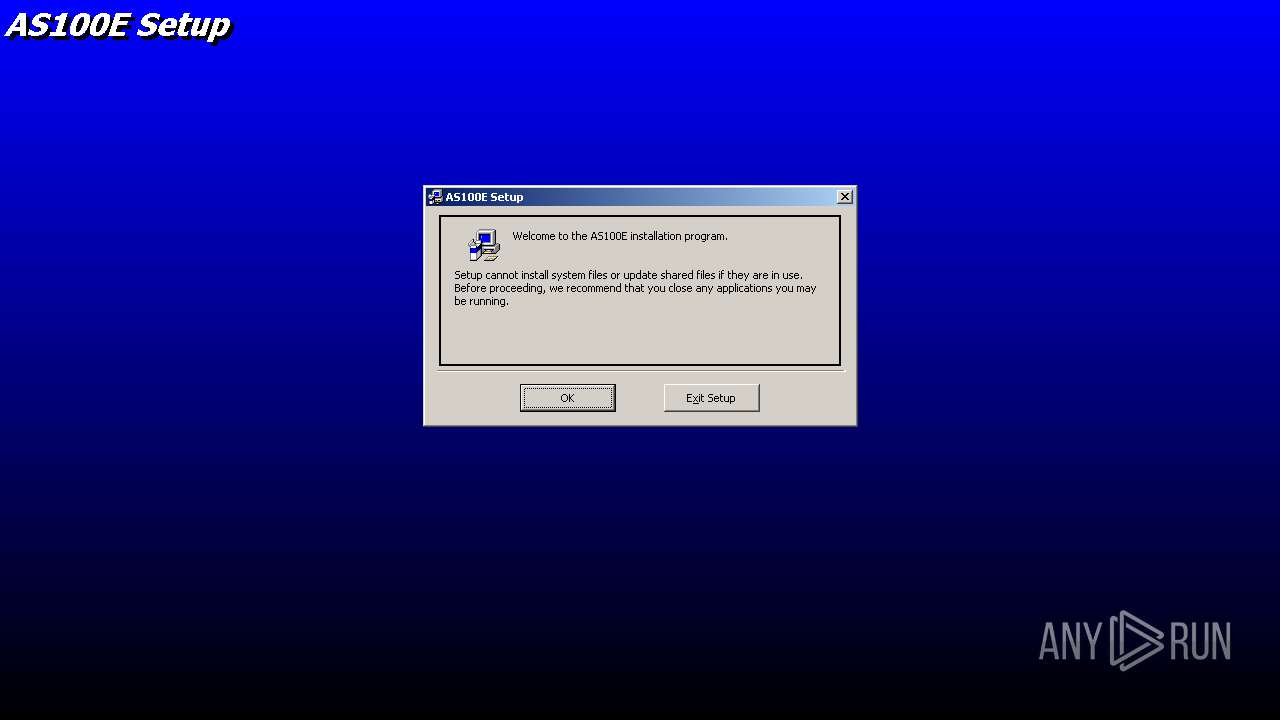
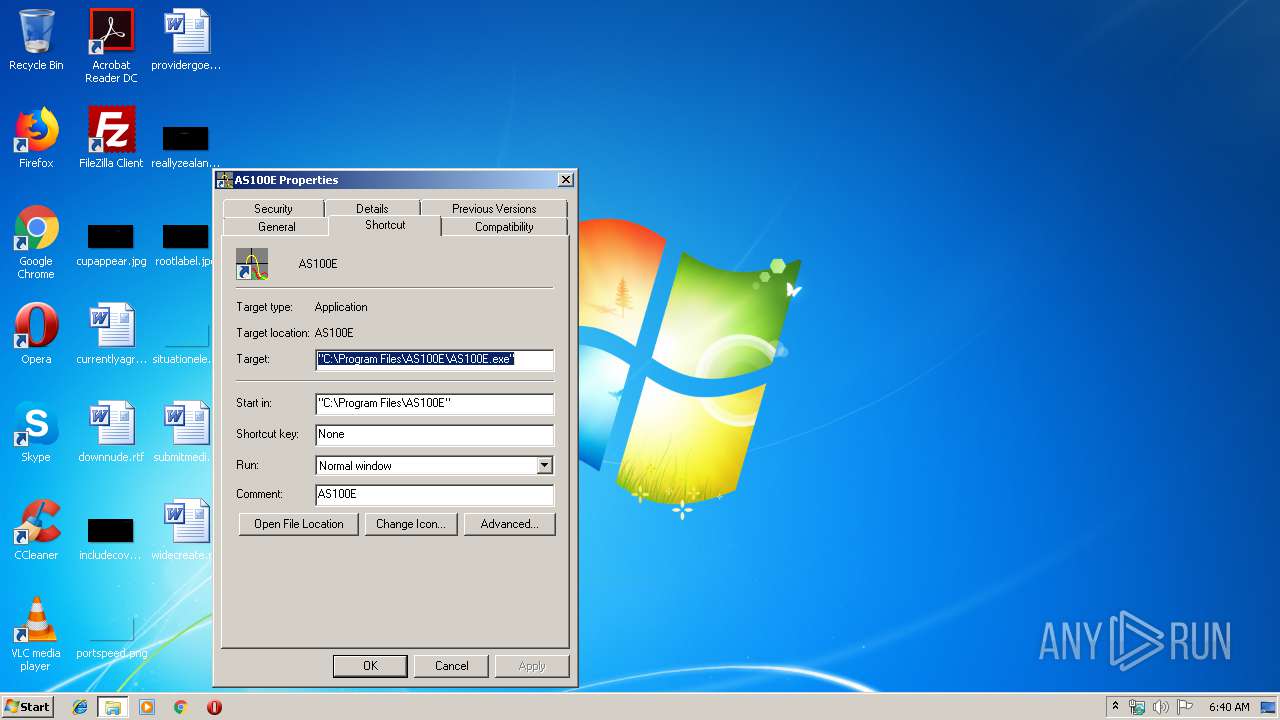
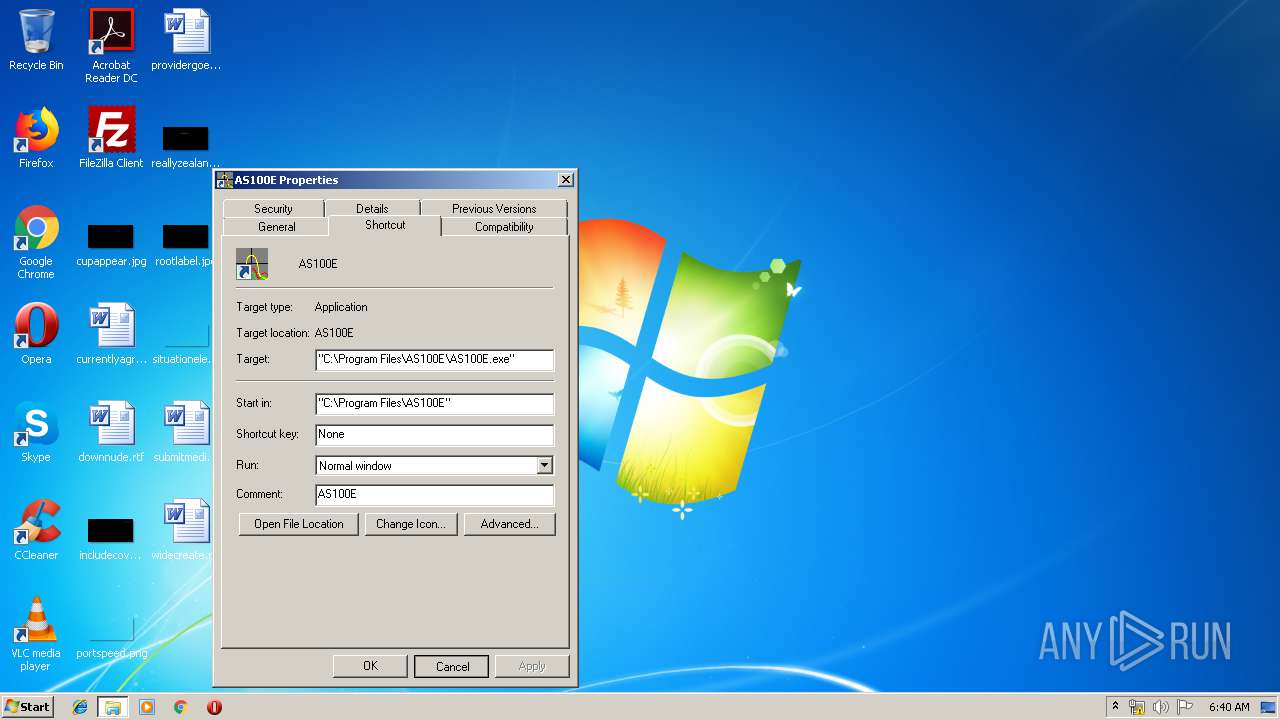
| 1864 | "C:\Program Files\AS100E\AS100E.exe" | C:\Program Files\AS100E\AS100E.exe | — | explorer.exe | |||||||||||
User: admin Company: Ullmann Microelectronic GmbH Integrity Level: MEDIUM Description: EMC-Software Exit code: 0 Version: 2.01.0007 Modules
| |||||||||||||||
| 2052 | C:\WINDOWS\Setup1.exe "C:\Users\admin\AppData\Local\Temp\" "C:\WINDOWS\ST6UNST.000" "C:\WINDOWS\st6unst.exe" | C:\WINDOWS\Setup1.exe | setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual Basic 6.0 Setup Toolkit Exit code: 0 Version: 6.00.8804 Modules
| |||||||||||||||
| 2308 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | as100e_305.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Setup Bootstrap for Visual Basic Setup Toolkit Exit code: 0 Version: 6.00.8804 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\AS100E\AS100E.exe" | C:\Program Files\AS100E\AS100E.exe | — | explorer.exe | |||||||||||
User: admin Company: Ullmann Microelectronic GmbH Integrity Level: MEDIUM Description: EMC-Software Exit code: 0 Version: 2.01.0007 Modules
| |||||||||||||||
| 3116 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | — | as100e_305.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Setup Bootstrap for Visual Basic Setup Toolkit Exit code: 3221226540 Version: 6.00.8804 Modules
| |||||||||||||||
| 3216 | "C:\Program Files\AS100E\AS100E.exe" | C:\Program Files\AS100E\AS100E.exe | — | explorer.exe | |||||||||||
User: admin Company: Ullmann Microelectronic GmbH Integrity Level: MEDIUM Description: EMC-Software Exit code: 0 Version: 2.01.0007 Modules
| |||||||||||||||
| 3476 | C:\Progra~1\AS100E\dllarc.exe | C:\Progra~1\AS100E\dllarc.exe | — | AS100E.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3784 | C:\Progra~1\AS100E\dllarc.exe | C:\Progra~1\AS100E\dllarc.exe | — | AS100E.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3800 | "C:\Users\admin\AppData\Local\Temp\as100e_305.exe" | C:\Users\admin\AppData\Local\Temp\as100e_305.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3844 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
Total events
2 004
Read events
933
Write events
989
Delete events
82
Modification events
| (PID) Process: | (3800) as100e_305.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3800) as100e_305.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2308) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Windows\System32\vb6stkit.dll |
Value: 1 | |||
| (PID) Process: | (2308) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\WINDOWS\SYSTEM32\COMCAT.DLL |
Value: 2 | |||
| (PID) Process: | (2308) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\WINDOWS\SYSTEM32\MSVCRT40.DLL |
Value: 2 | |||
| (PID) Process: | (2308) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\WINDOWS\SYSTEM32\STDOLE2.TLB |
Value: 2 | |||
| (PID) Process: | (2308) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\WINDOWS\SYSTEM32\ASYCFILT.DLL |
Value: 2 | |||
| (PID) Process: | (2308) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\WINDOWS\SYSTEM32\OLEPRO32.DLL |
Value: 2 | |||
| (PID) Process: | (2308) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\WINDOWS\SYSTEM32\OLEAUT32.DLL |
Value: 2 | |||
| (PID) Process: | (2308) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\WINDOWS\SYSTEM32\msvbvm60.dll |
Value: 2 | |||
Executable files
44
Suspicious files
3
Text files
135
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3800 | as100e_305.exe | C:\Users\admin\AppData\Local\Temp\AS100E.CAB | — | |
MD5:— | SHA256:— | |||
| 2308 | setup.exe | C:\WINDOWS\AS100E.CAB | — | |
MD5:— | SHA256:— | |||
| 2308 | setup.exe | C:\WINDOWS\temp.000 | — | |
MD5:— | SHA256:— | |||
| 2308 | setup.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\ST6UNST Uninstaller.LNK | — | |
MD5:— | SHA256:— | |||
| 2308 | setup.exe | C:\Windows\System32\temp.000 | — | |
MD5:— | SHA256:— | |||
| 2052 | Setup1.exe | C:\Users\admin\AppData\Local\Temp\msftqws.pdw\AS100.mdb | — | |
MD5:— | SHA256:— | |||
| 2052 | Setup1.exe | C:\Program Files\AS100E\temp.000 | — | |
MD5:— | SHA256:— | |||
| 2052 | Setup1.exe | C:\Users\admin\AppData\Local\Temp\msftqws.pdw\test.mes | — | |
MD5:— | SHA256:— | |||
| 2052 | Setup1.exe | C:\Users\admin\AppData\Local\Temp\msftqws.pdw\dllarc.exe | — | |
MD5:— | SHA256:— | |||
| 2052 | Setup1.exe | C:\Users\admin\AppData\Local\Temp\msftqws.pdw\as100e_e.pdf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report