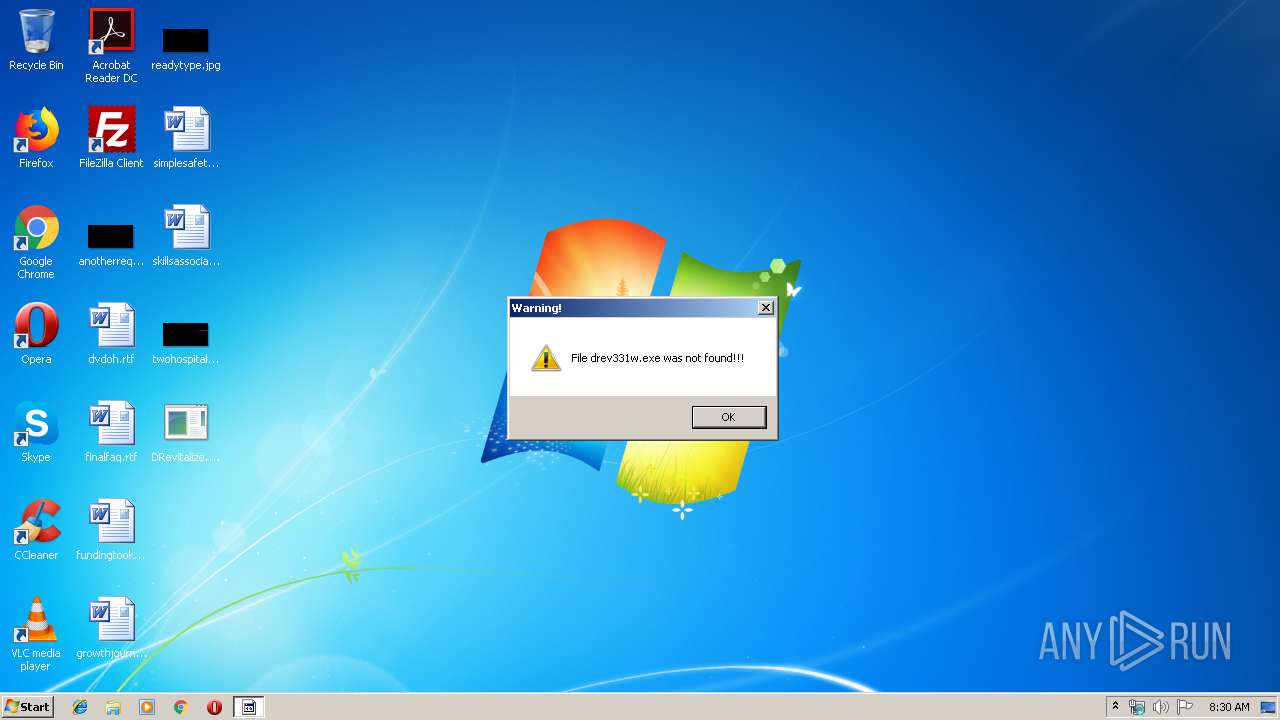
| File name: | DRevitalize.exe |
| Full analysis: | https://app.any.run/tasks/635d86ff-ae15-4106-b976-5abca9536c6e |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2020, 08:29:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FA5CB62A89496AC8E246E927C3766D95 |
| SHA1: | 50ADF6F5AA1F4F5B0894BD17D0F92824B8E8187F |
| SHA256: | 731BB15DD77FBE59626C880CB9356502873AC78179B3C8CF74A9832A0E4047E2 |
| SSDEEP: | 24:etGSI/t6dzHaIlvFUGoAZKIQ+XSBjeoH:6muz6YvGG5ZZCBCo |
MALICIOUS
Loads dropped or rewritten executable
- firefox.exe (PID: 1956)
- firefox.exe (PID: 3288)
- firefox.exe (PID: 3768)
- firefox.exe (PID: 2076)
- firefox.exe (PID: 1024)
- regsvr32.exe (PID: 2136)
- firefox.exe (PID: 1316)
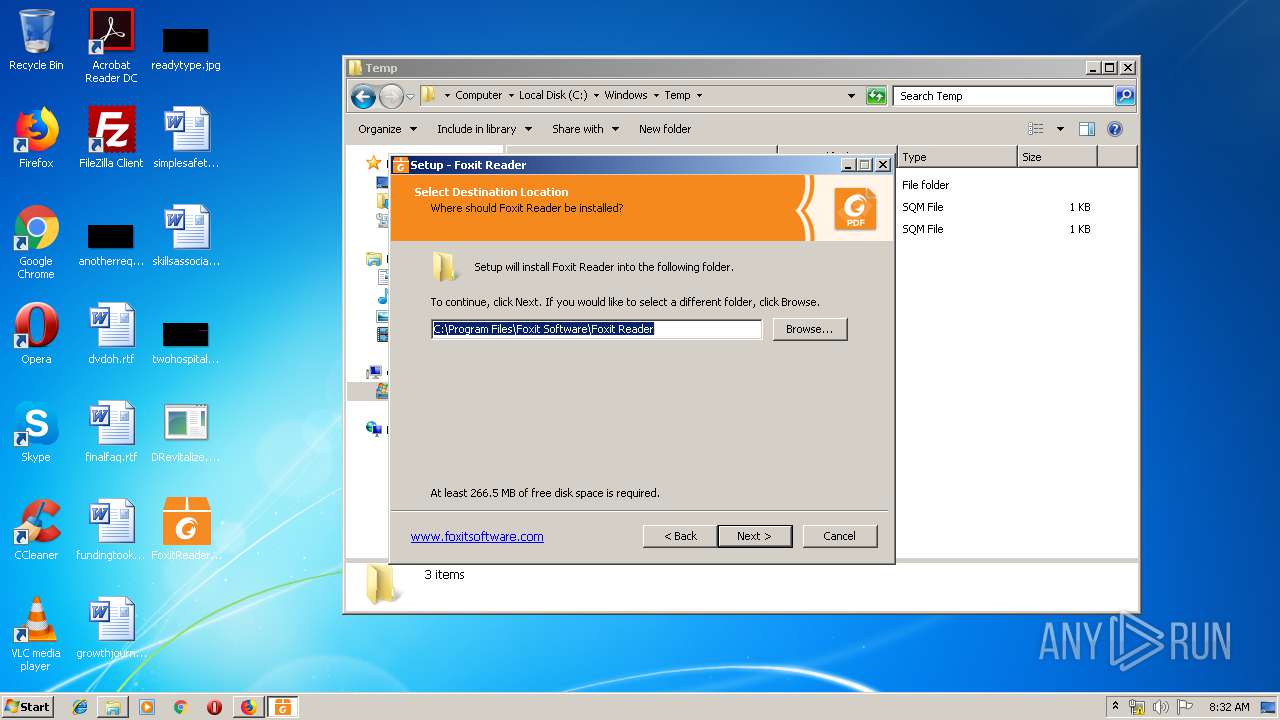
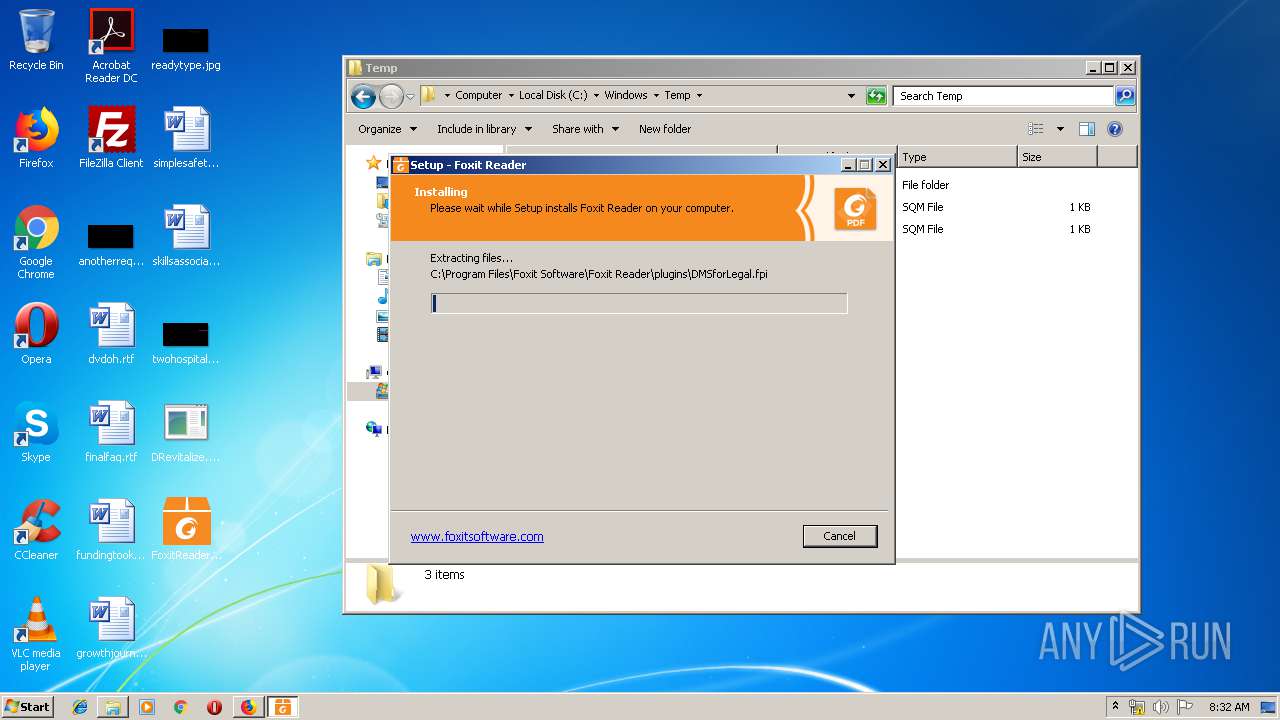
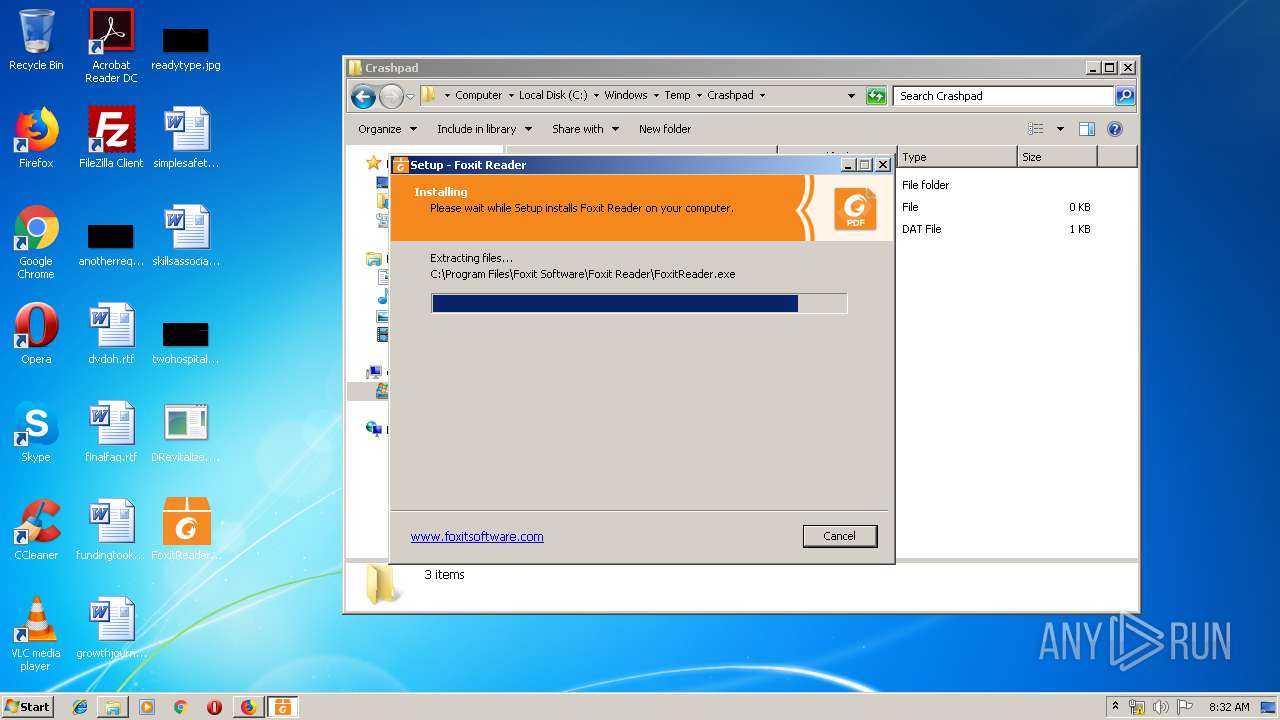
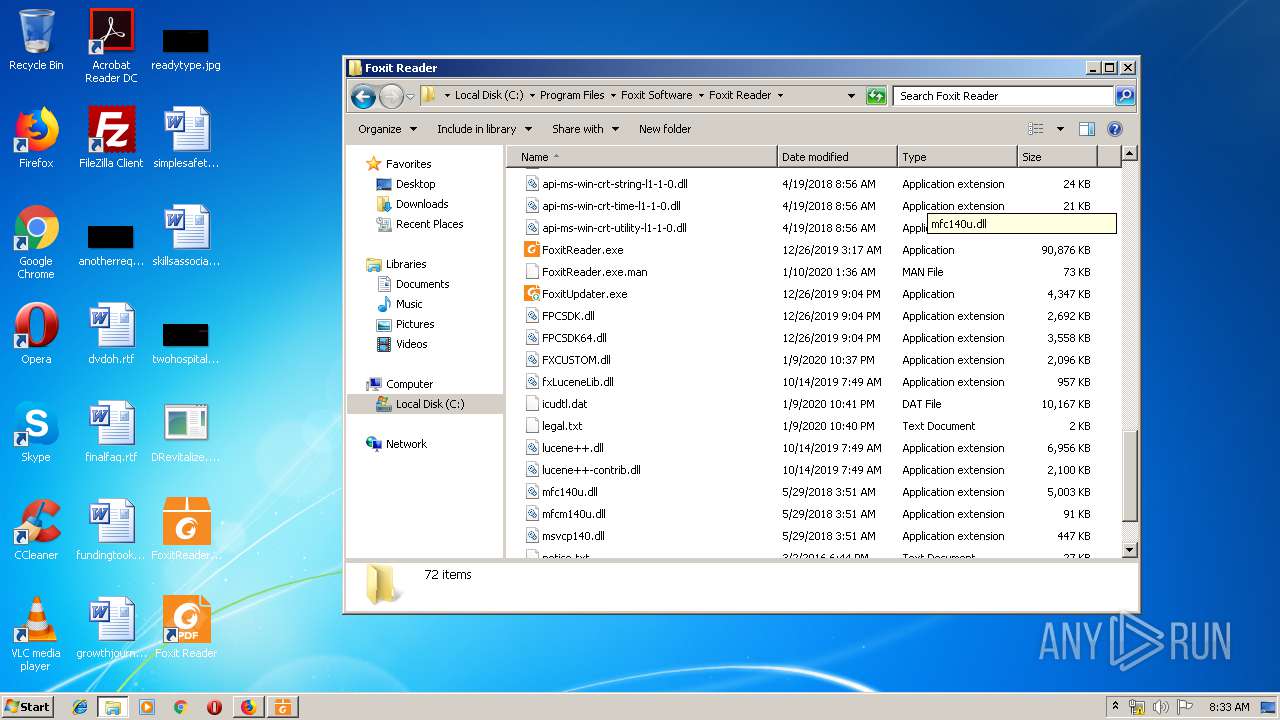
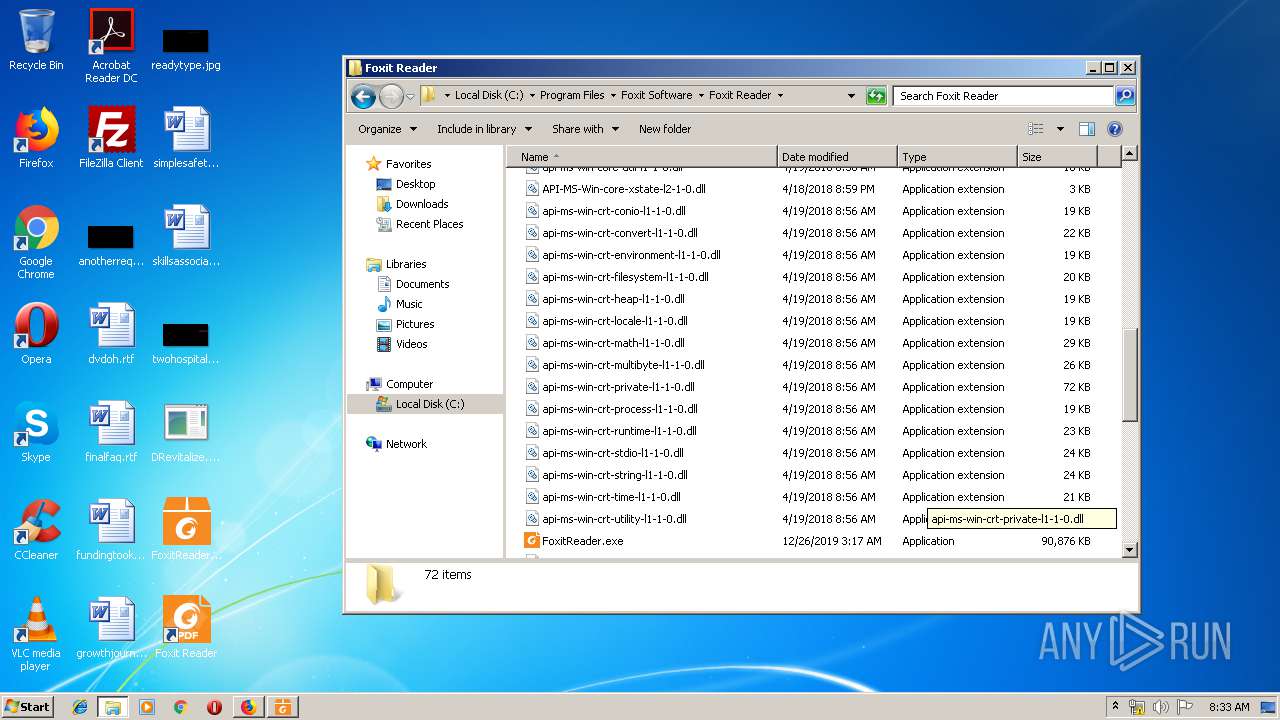
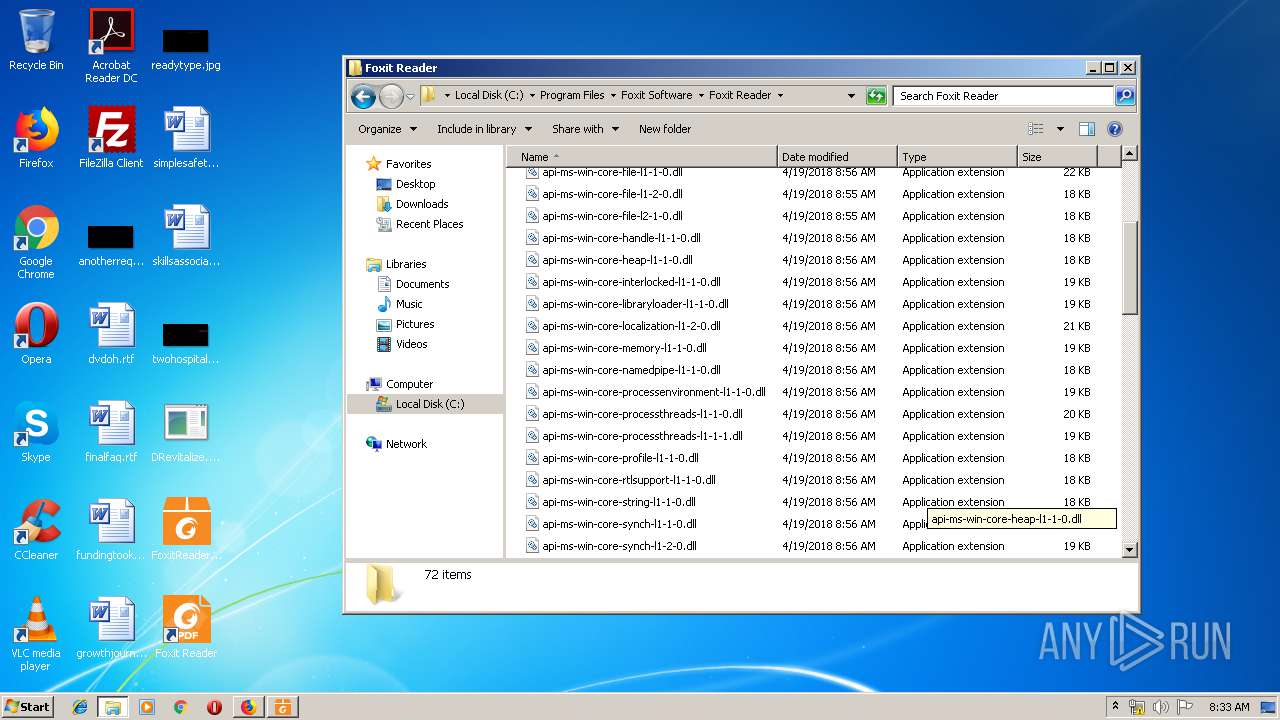
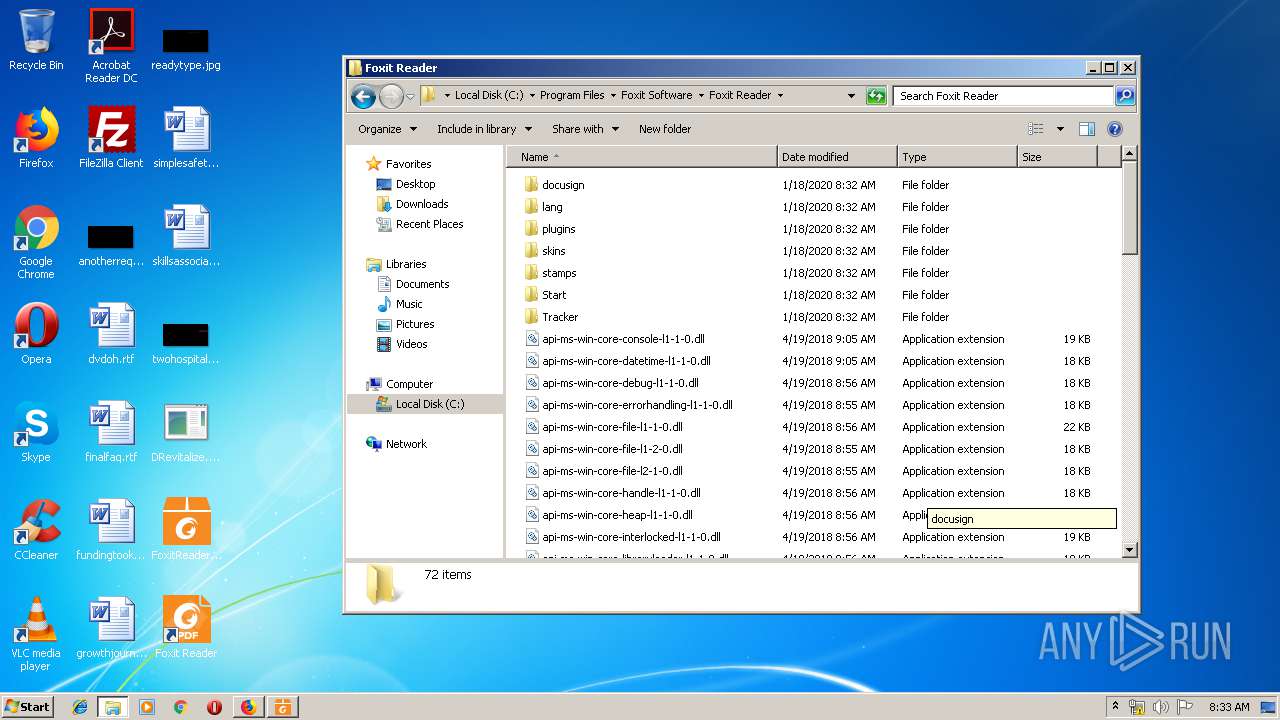
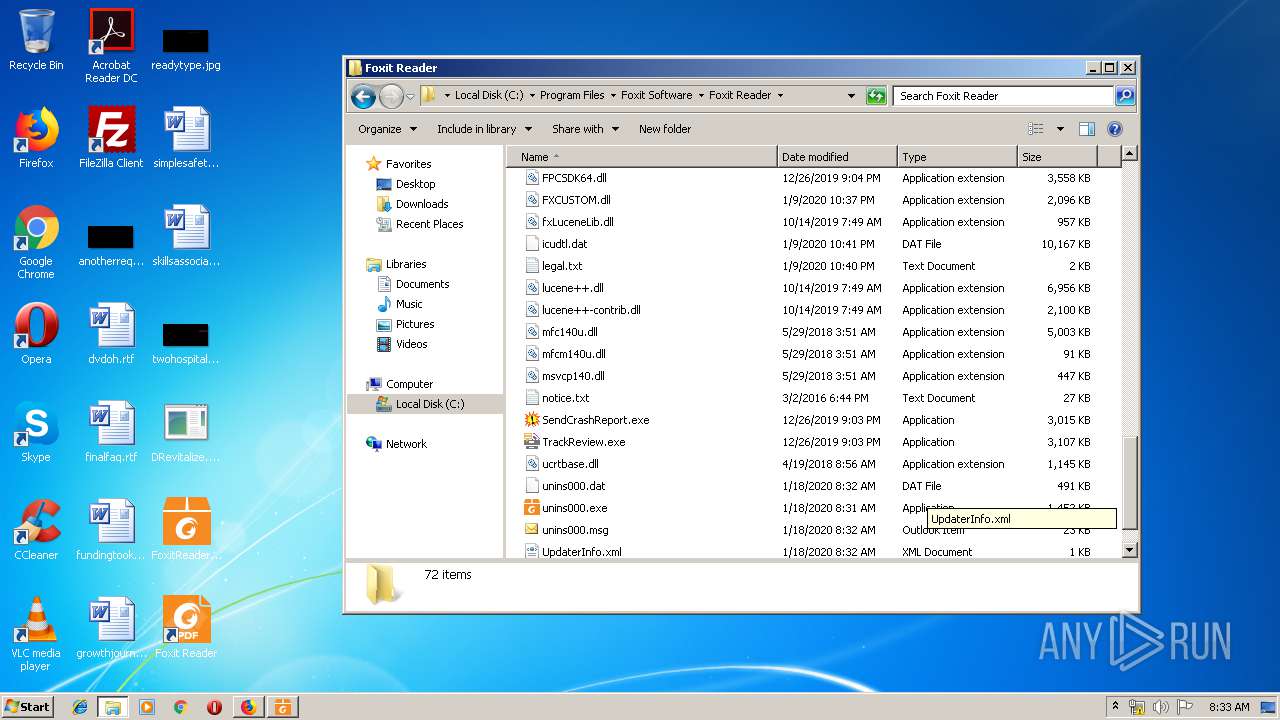
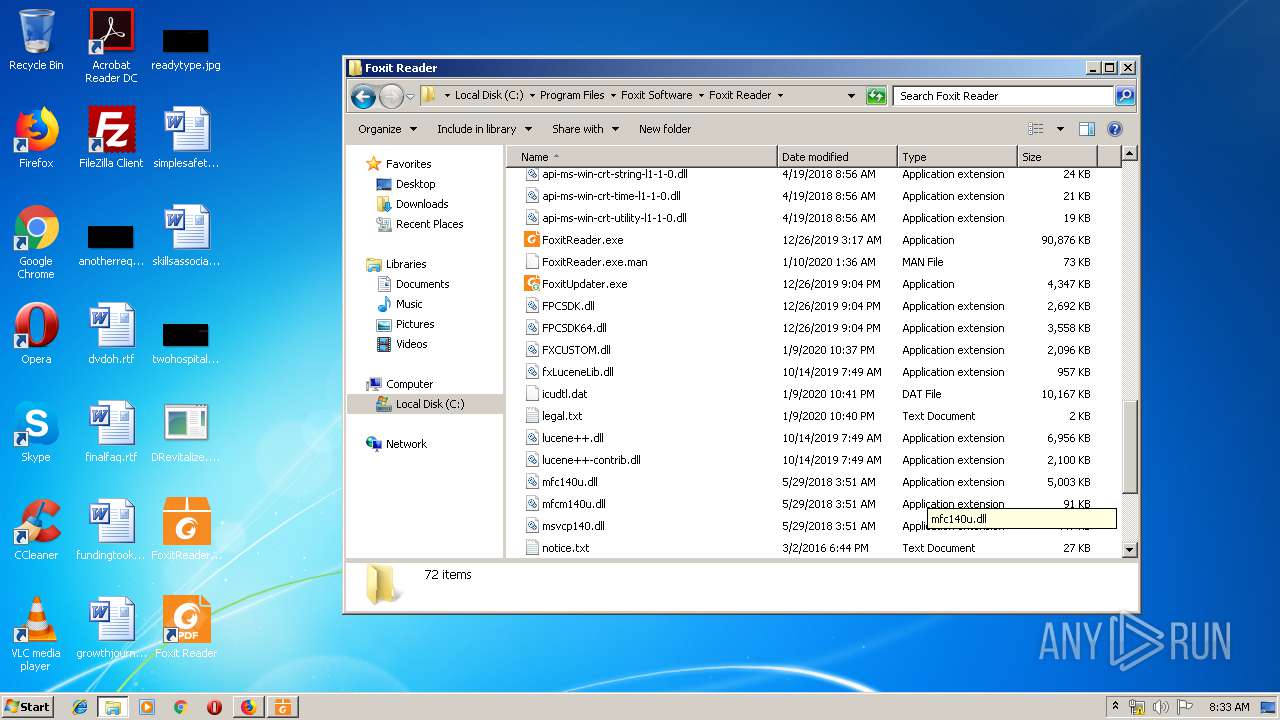
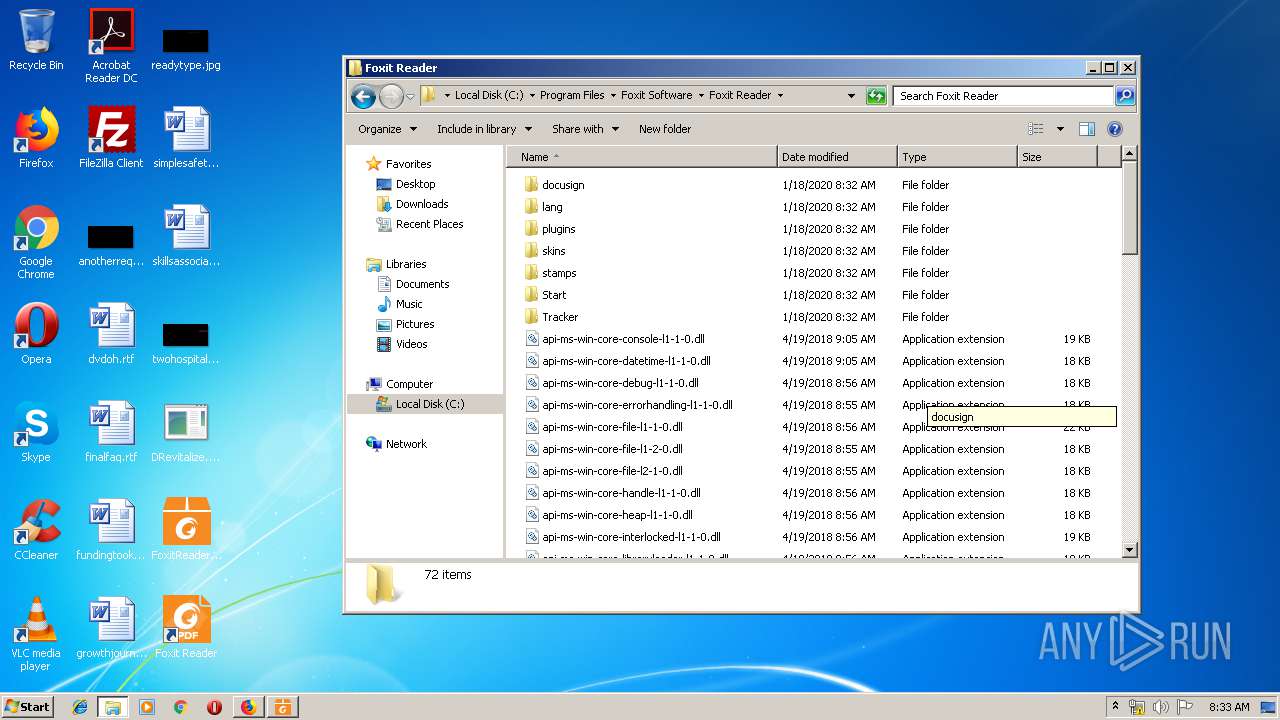
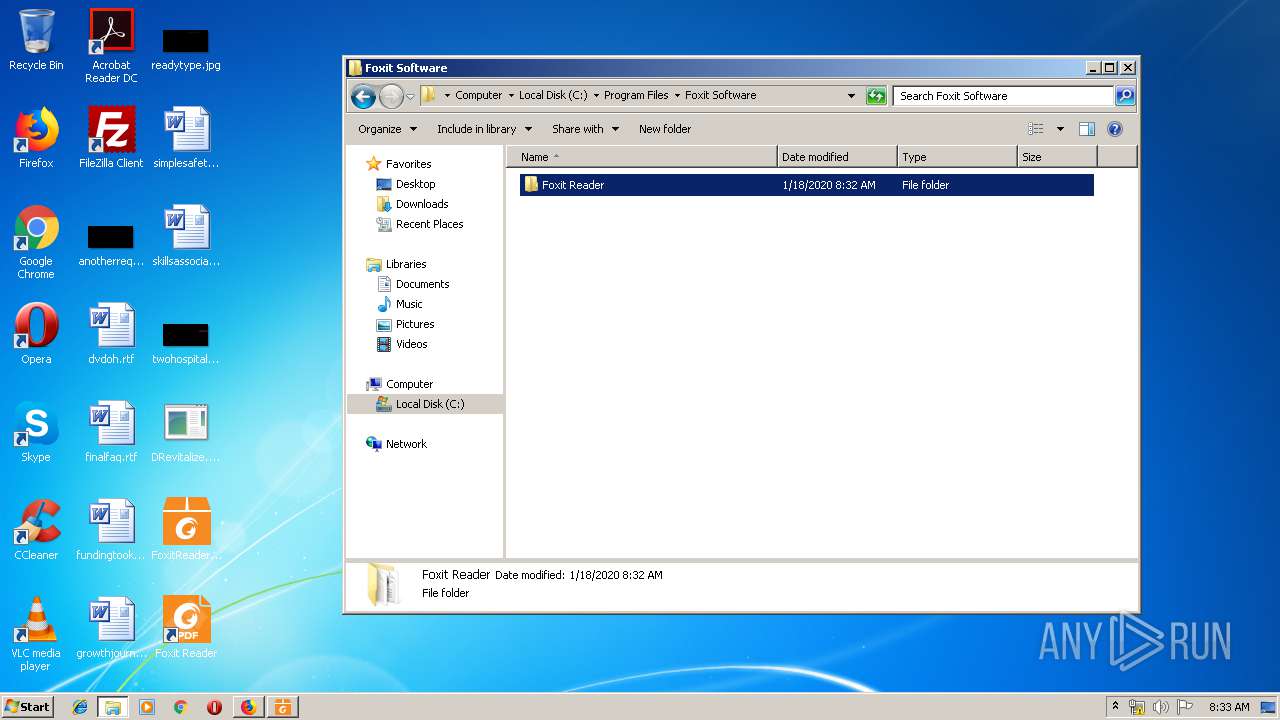
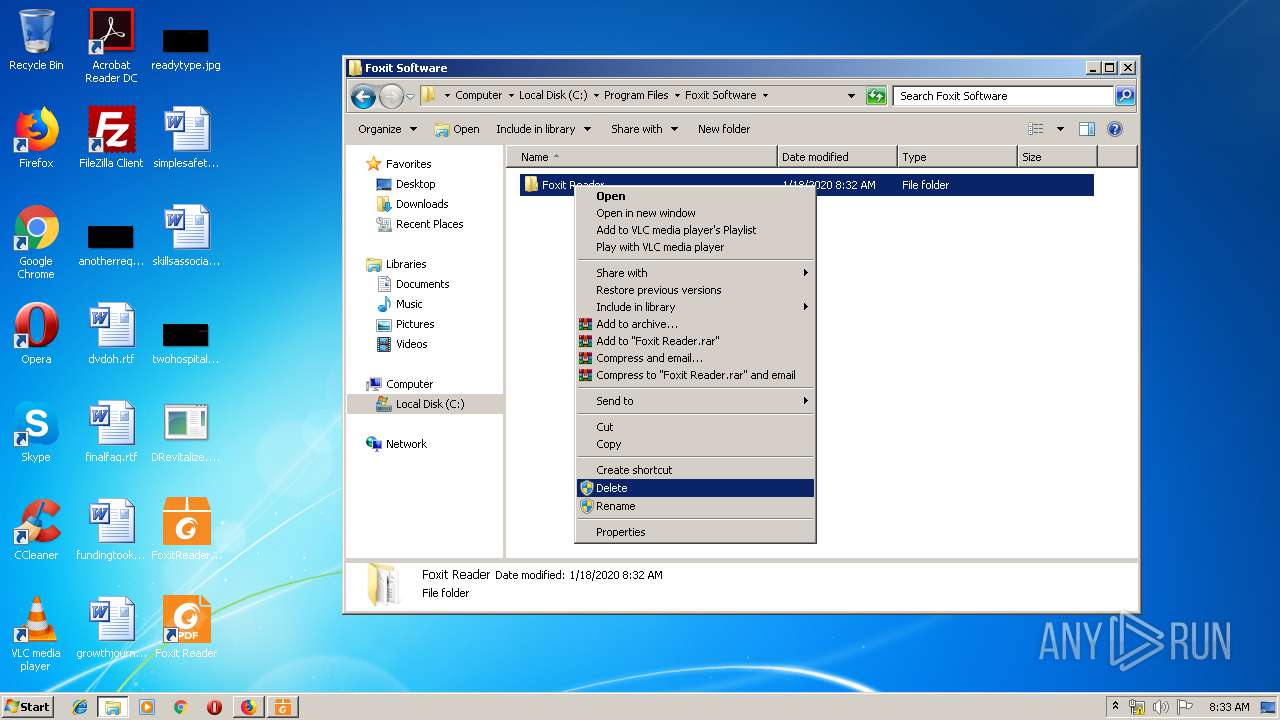
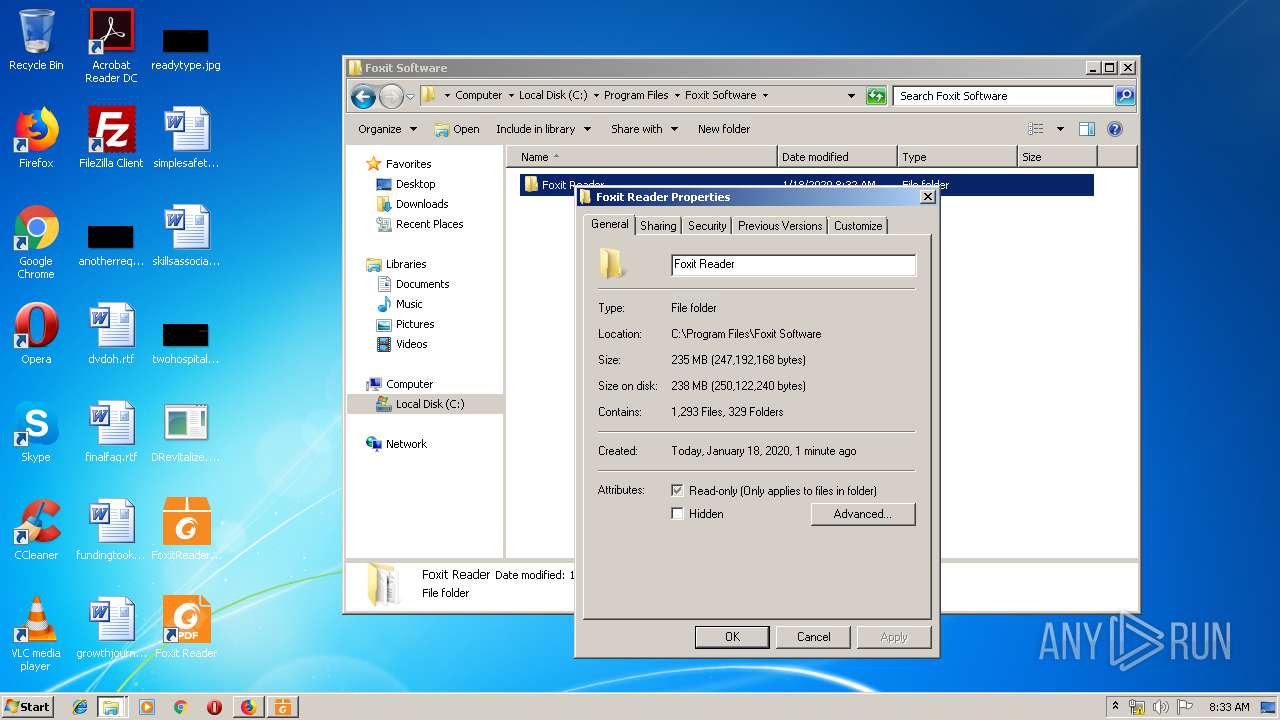
- FoxitReader.exe (PID: 3256)
- FoxitReader.exe (PID: 1252)
- FoxitReader.exe (PID: 3940)
Registers / Runs the DLL via REGSVR32.EXE
- FoxitReader971_L10N_Setup_Prom.tmp (PID: 2200)
- FoxitReader.exe (PID: 1252)
SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3000)
- DllHost.exe (PID: 2584)
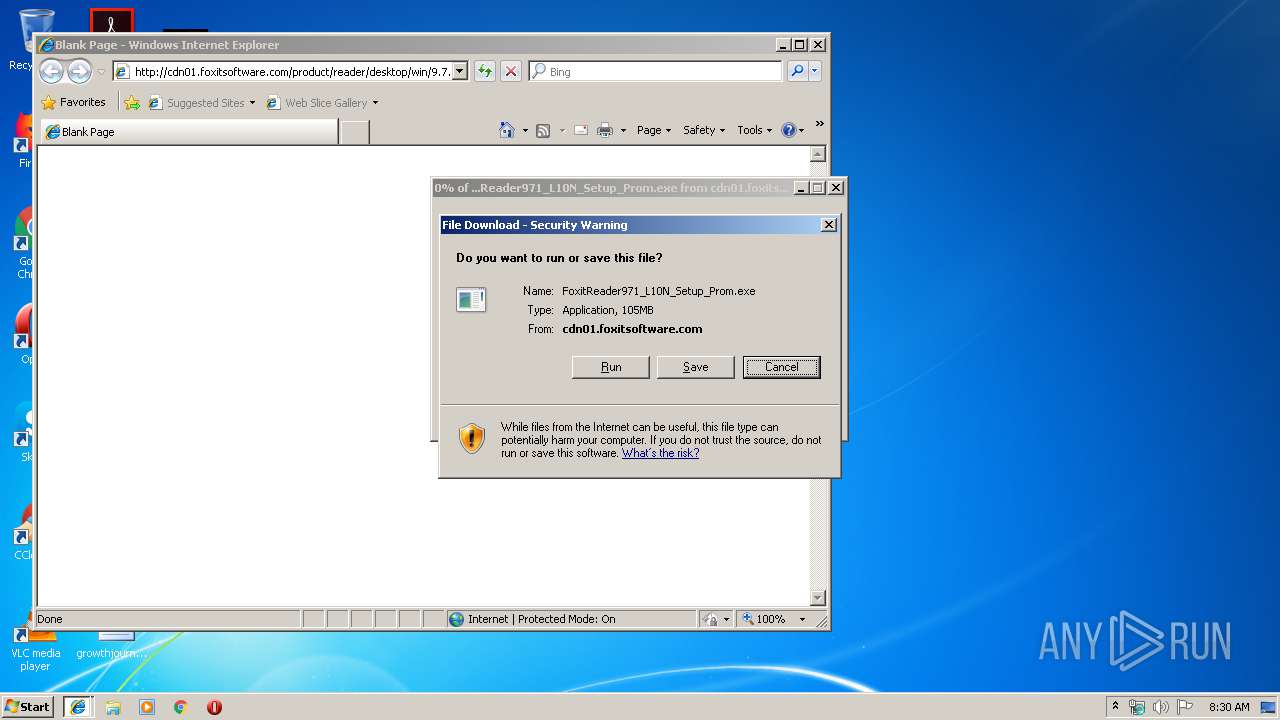
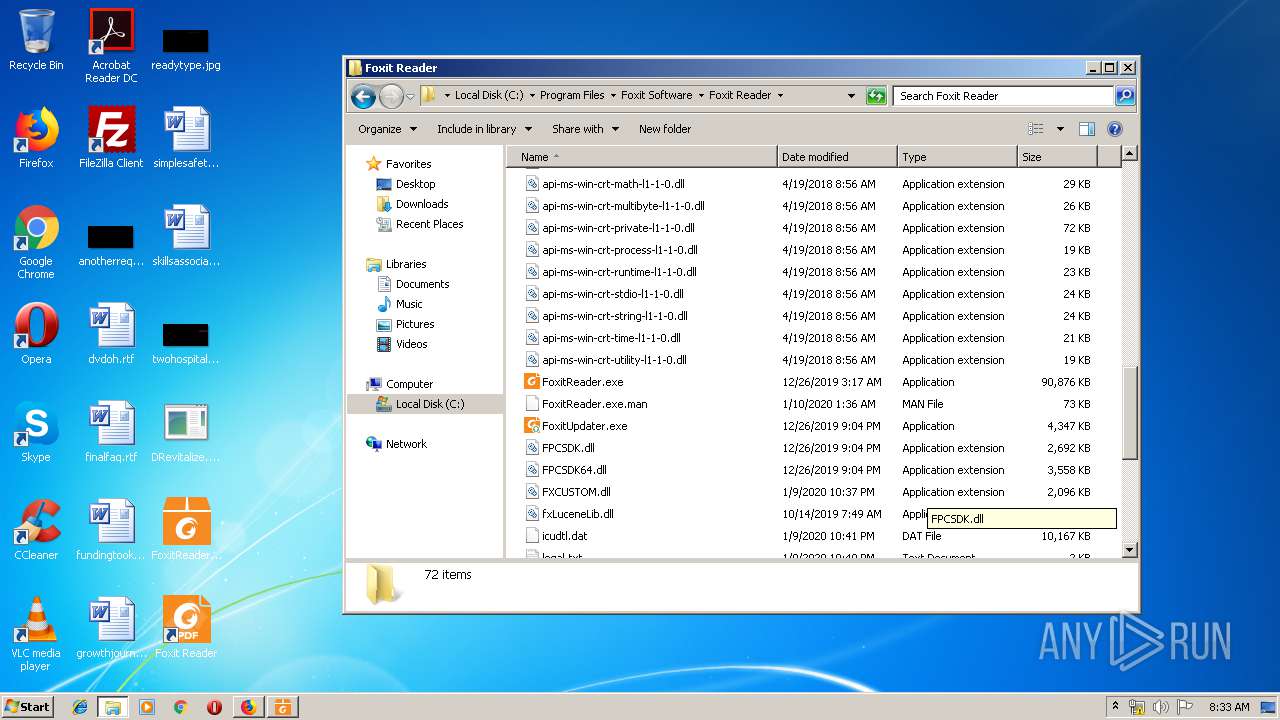
Executable content was dropped or overwritten
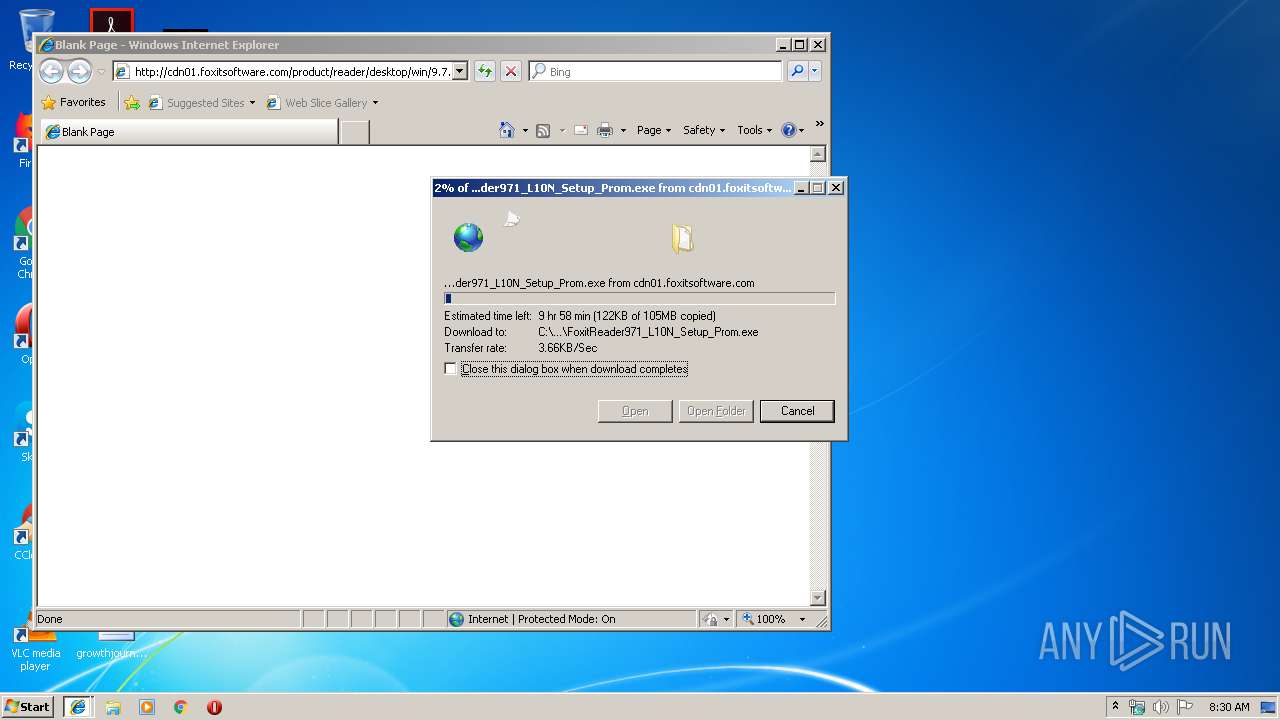
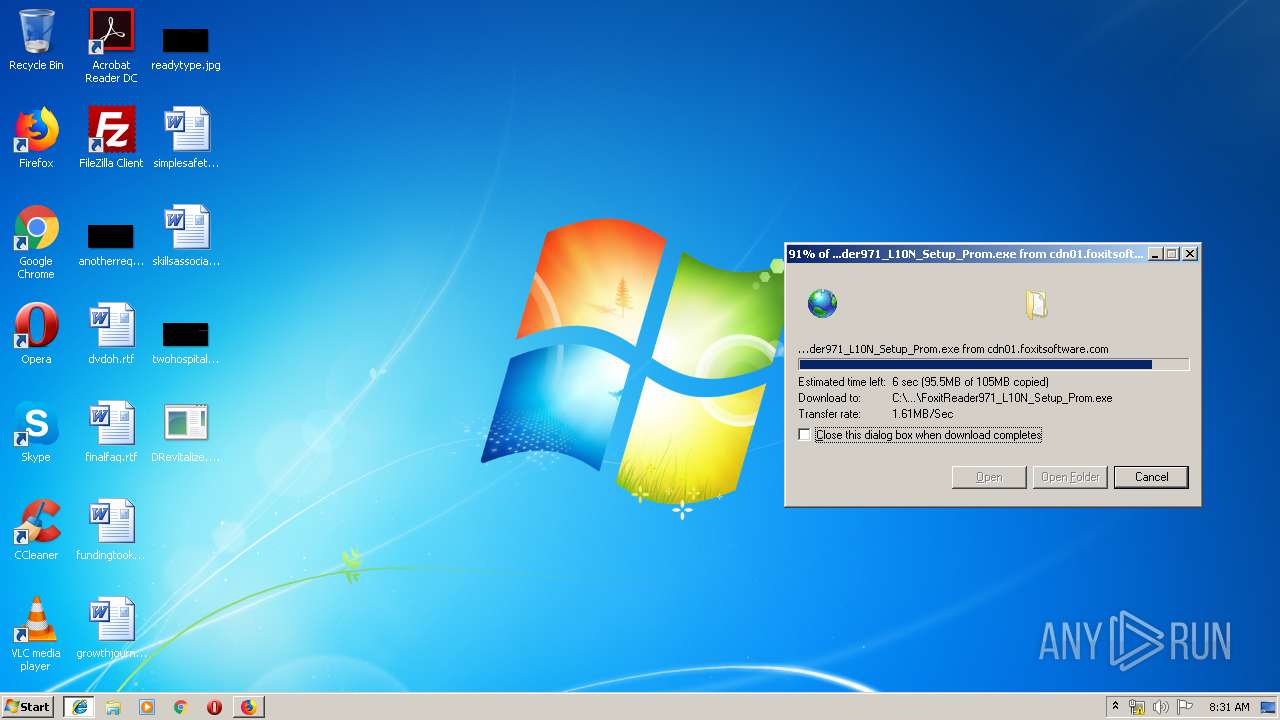
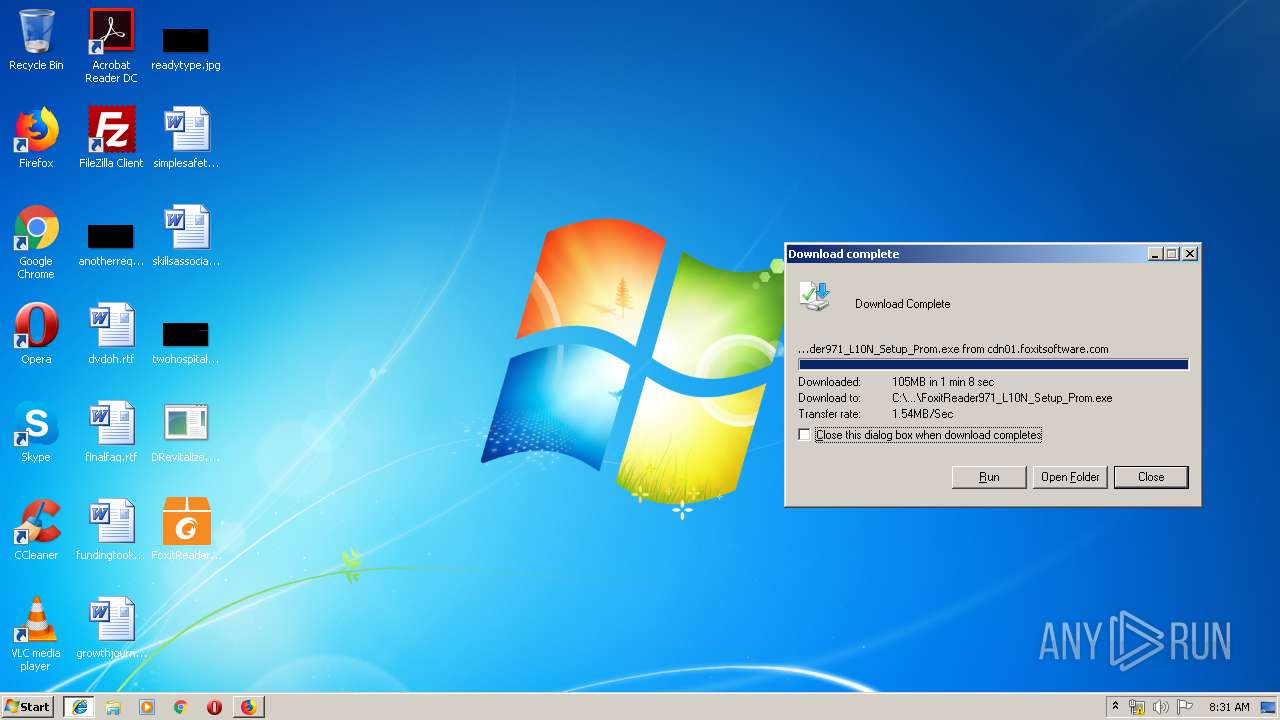
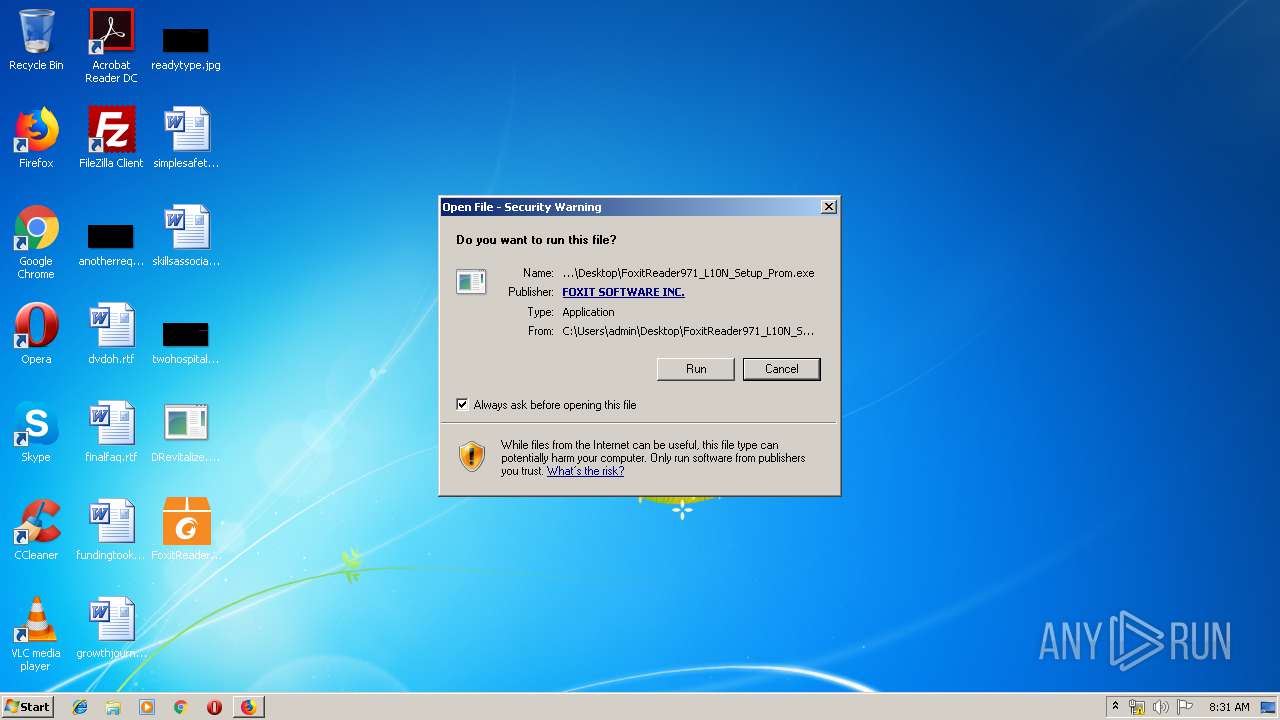
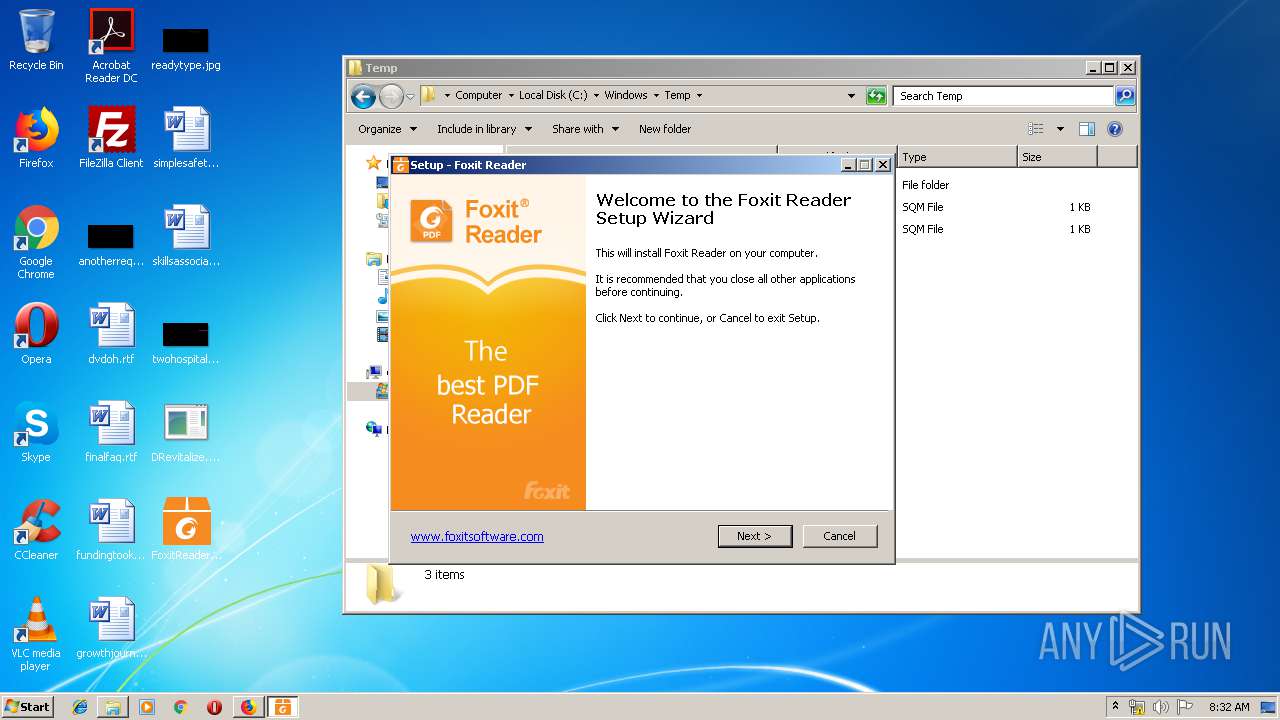
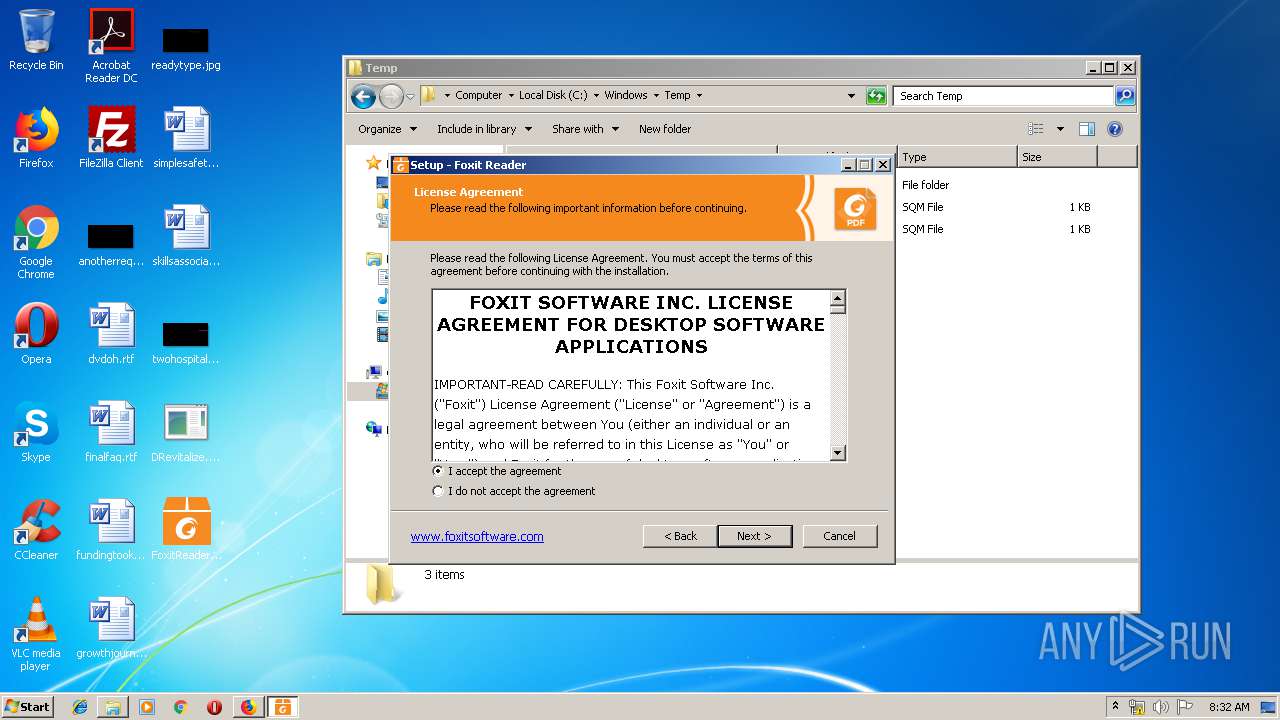
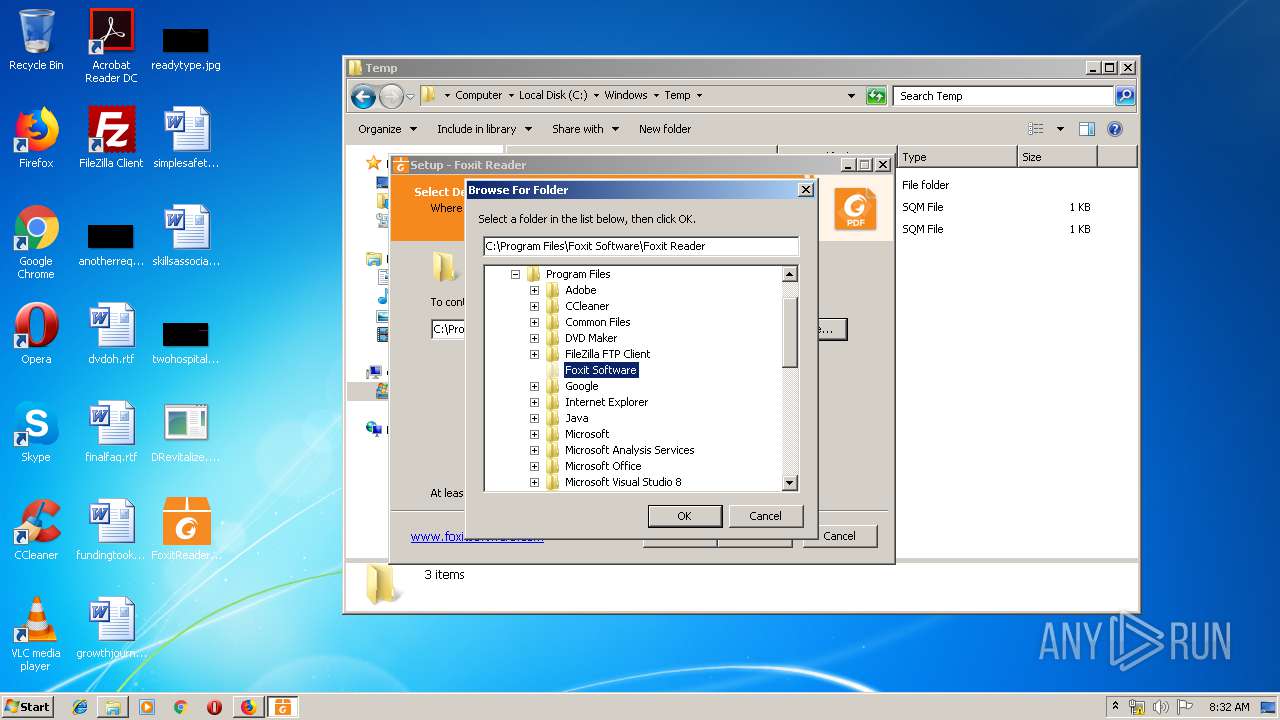
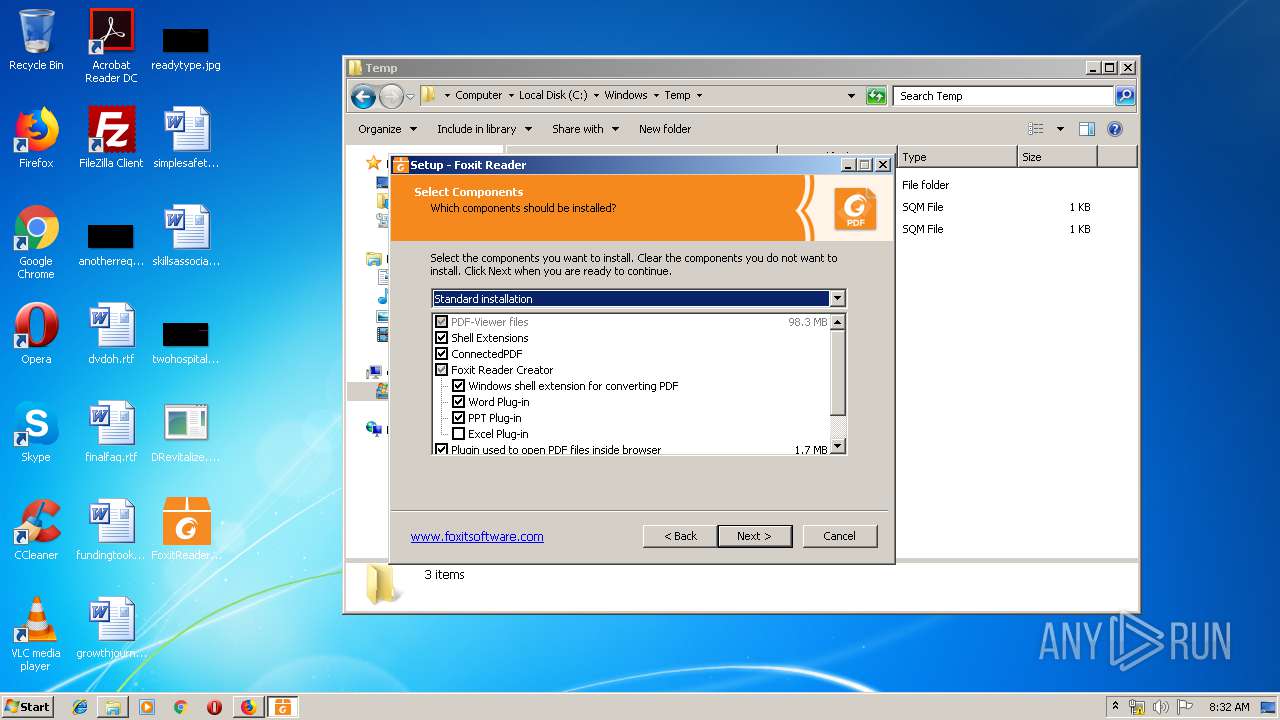
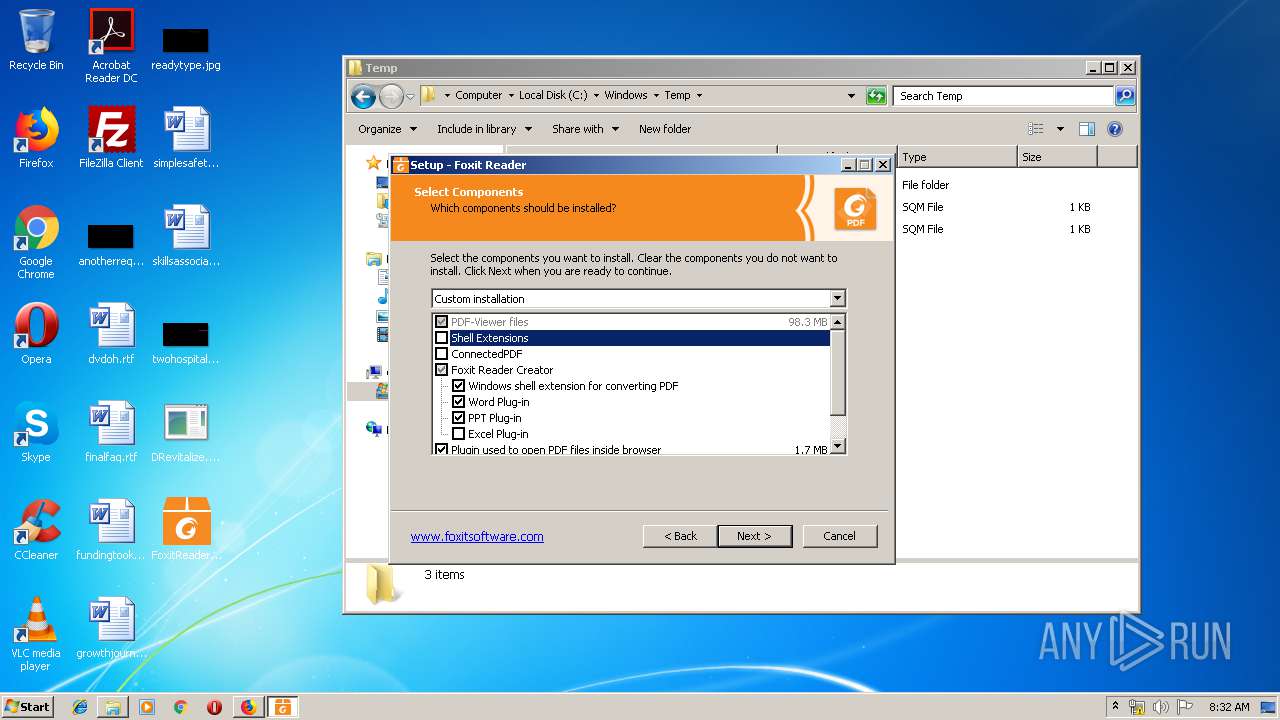
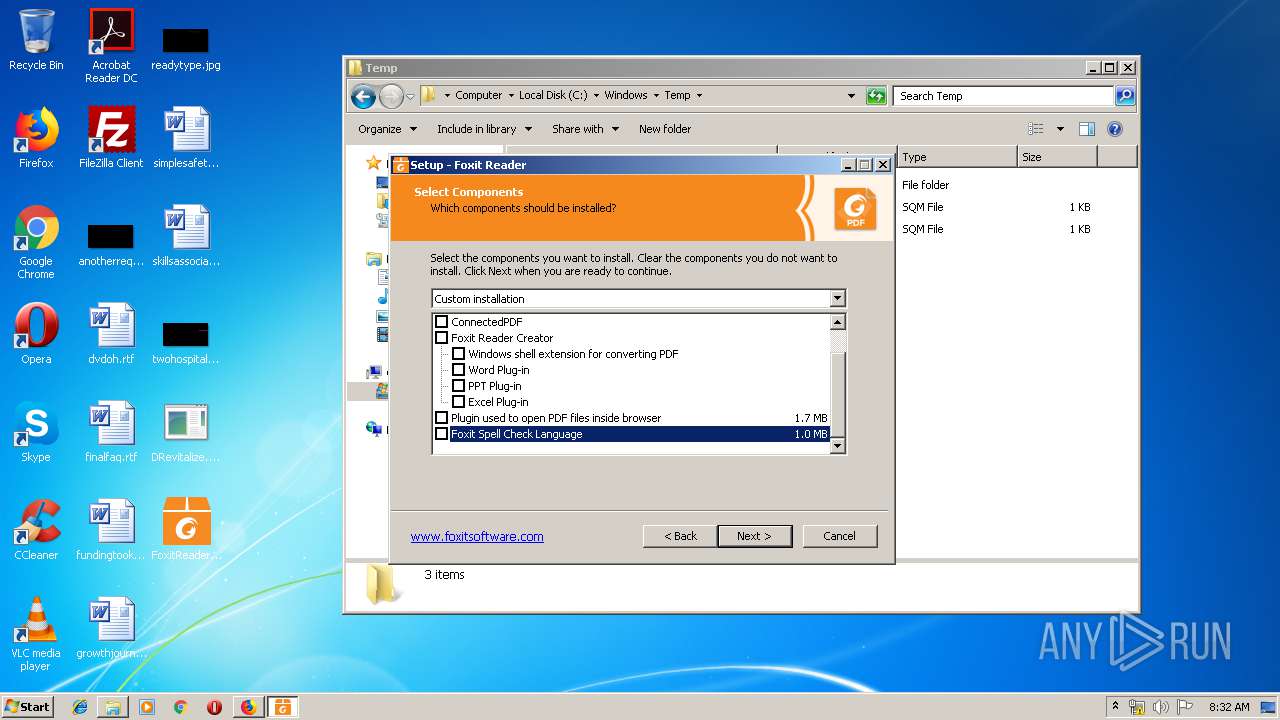
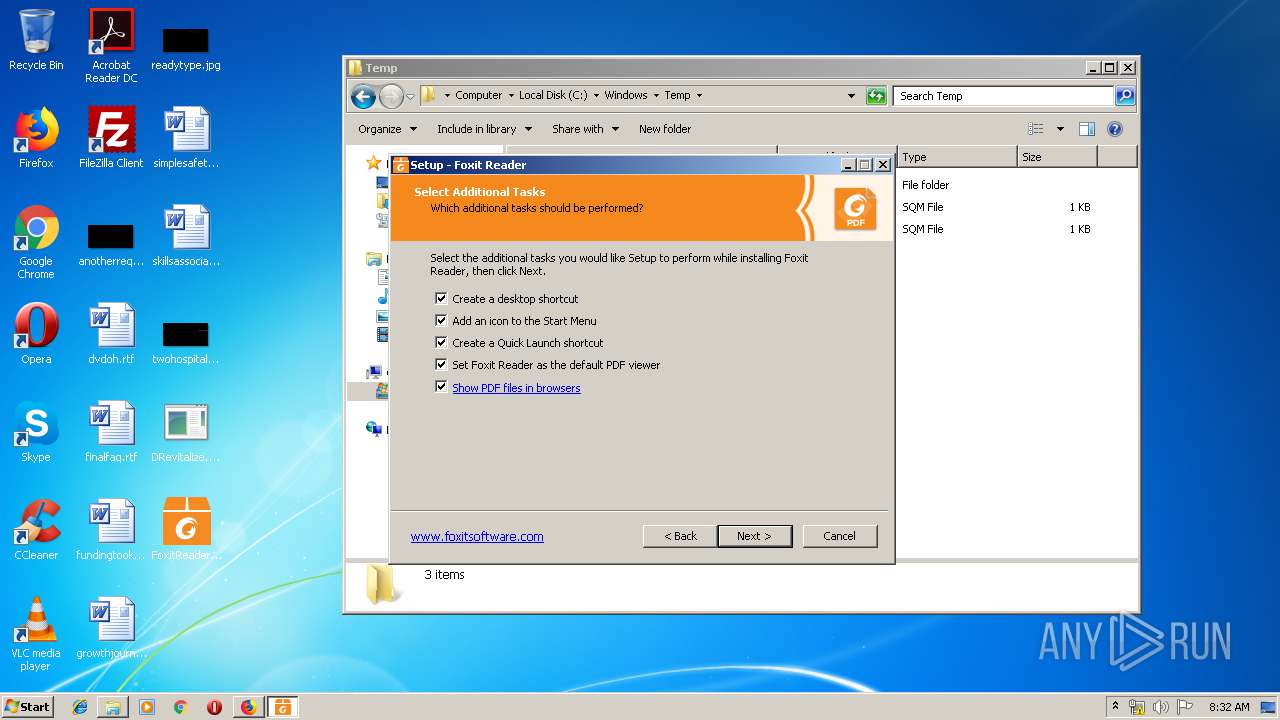
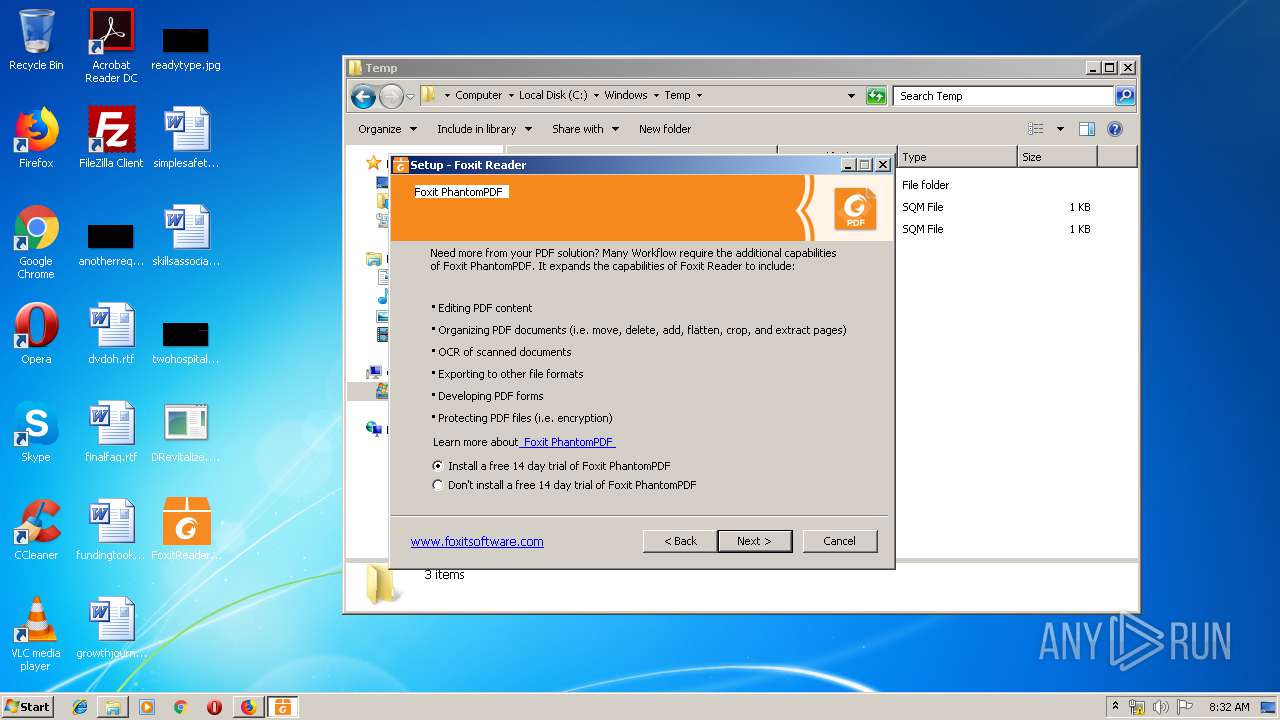
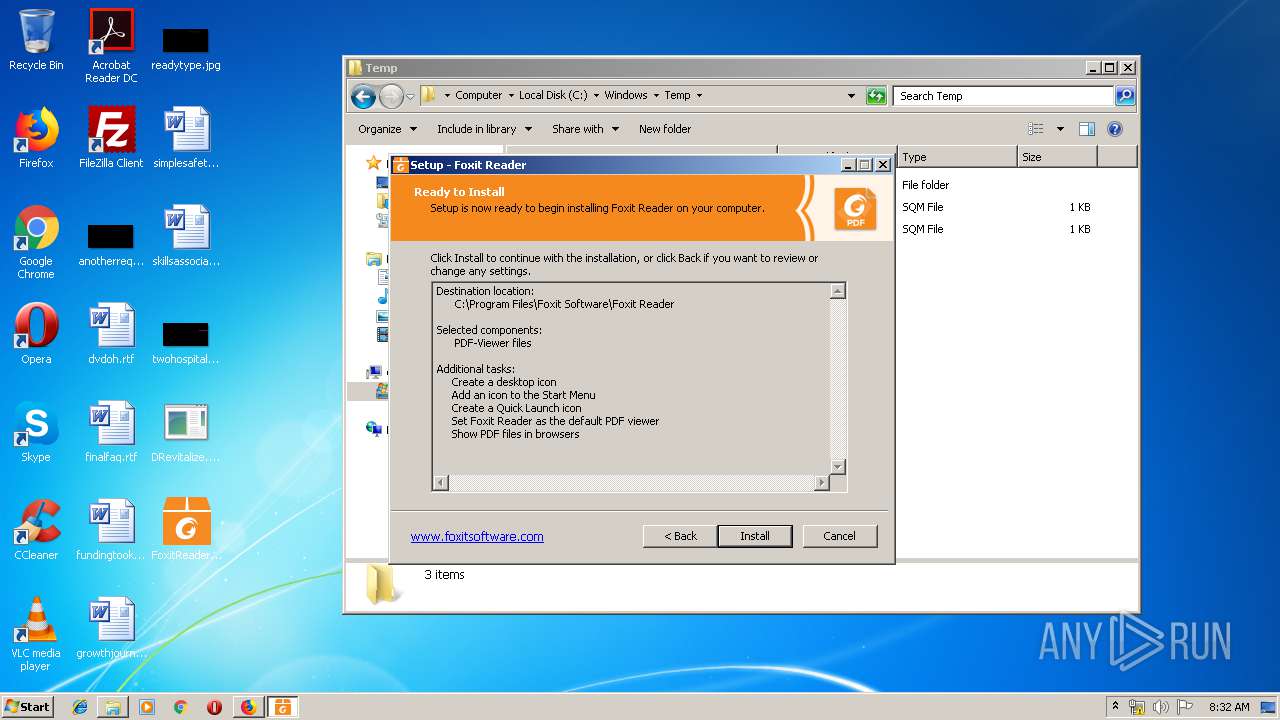
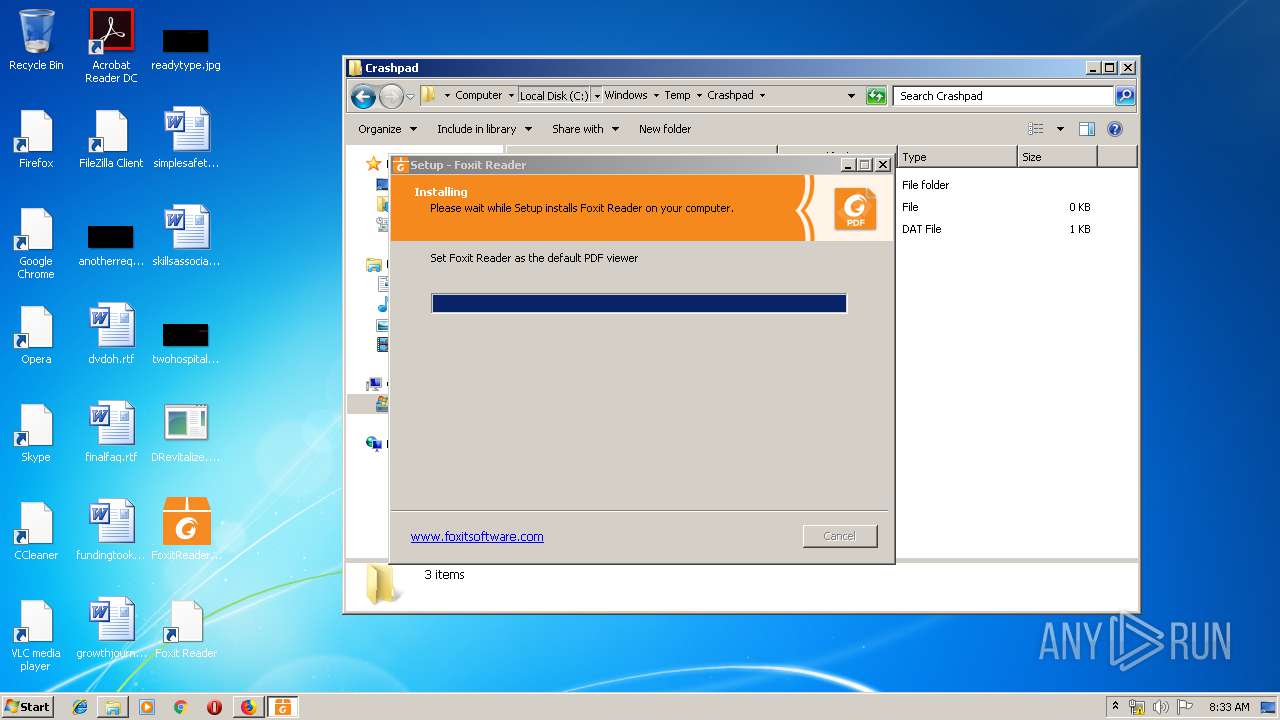
- FoxitReader971_L10N_Setup_Prom.exe (PID: 3876)
- FoxitReader971_L10N_Setup_Prom.exe (PID: 3140)
- FoxitReader971_L10N_Setup_Prom.tmp (PID: 2200)
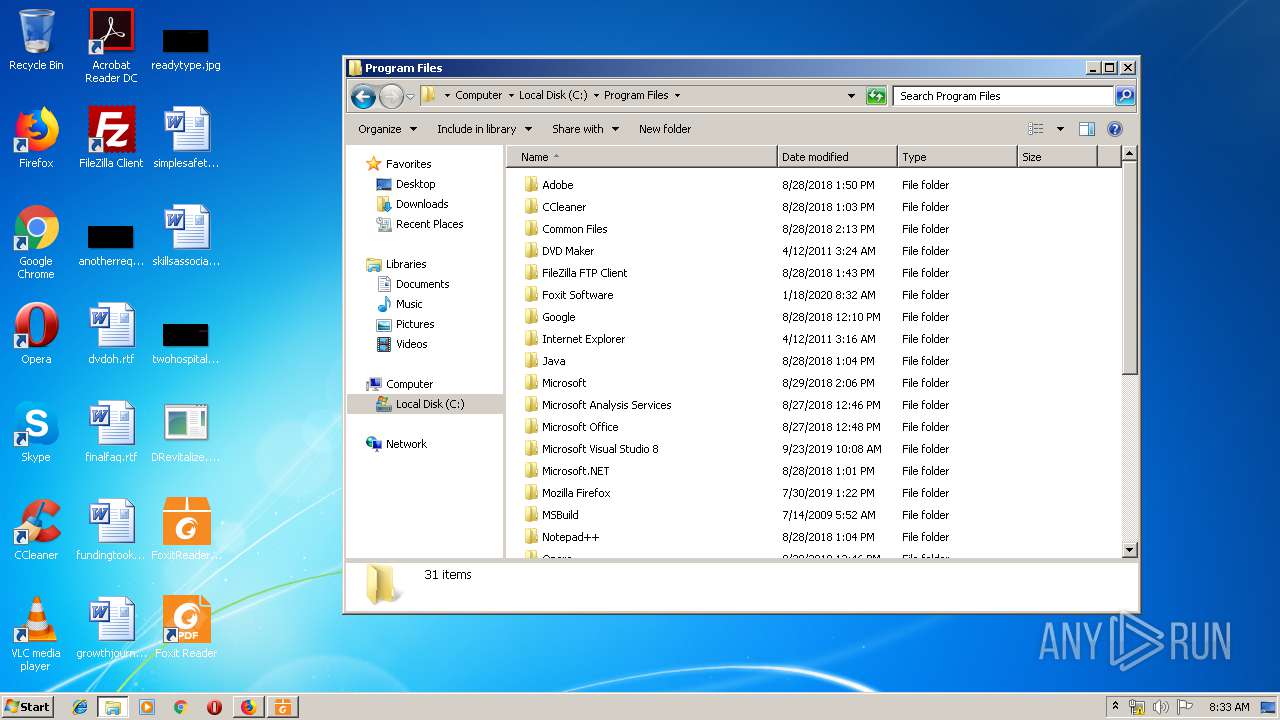
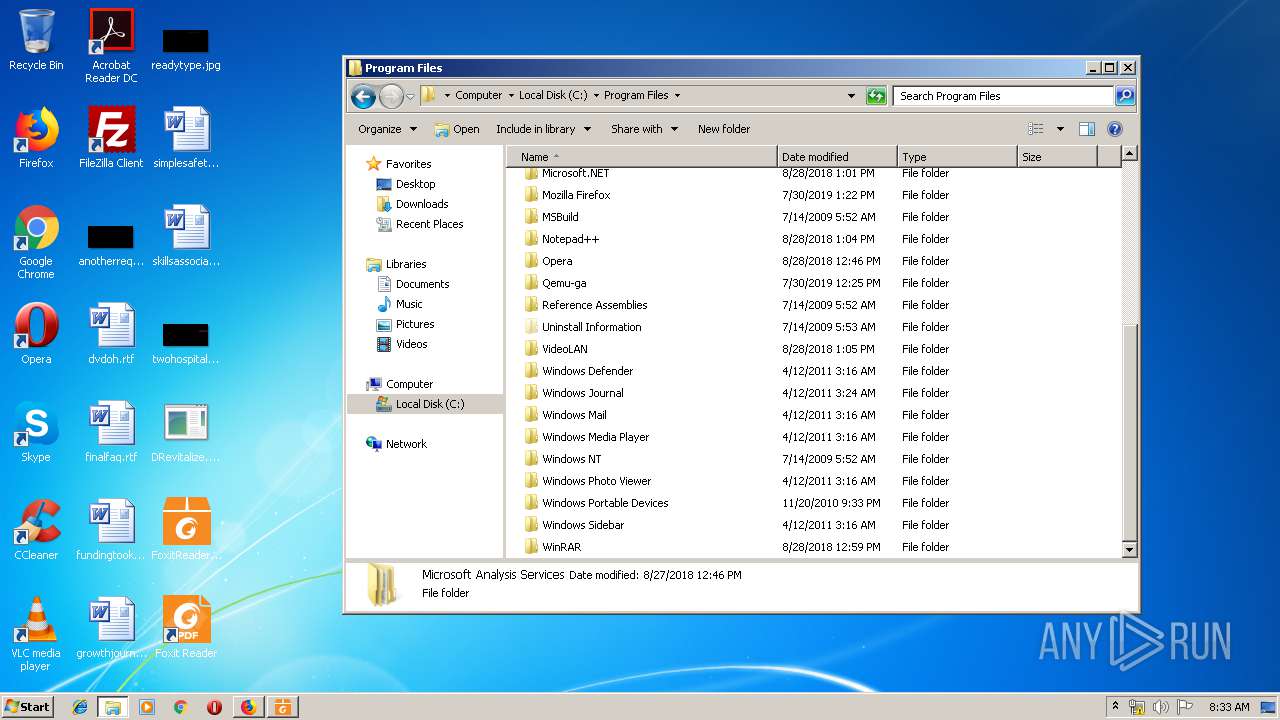
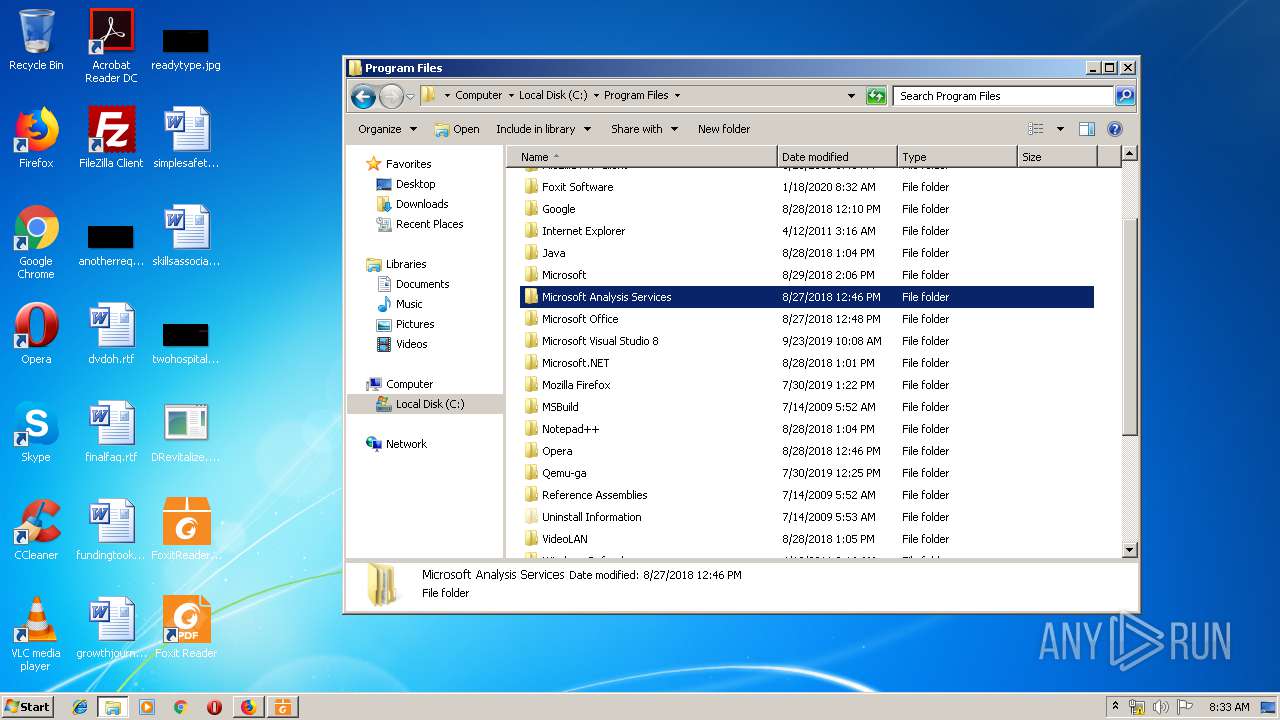
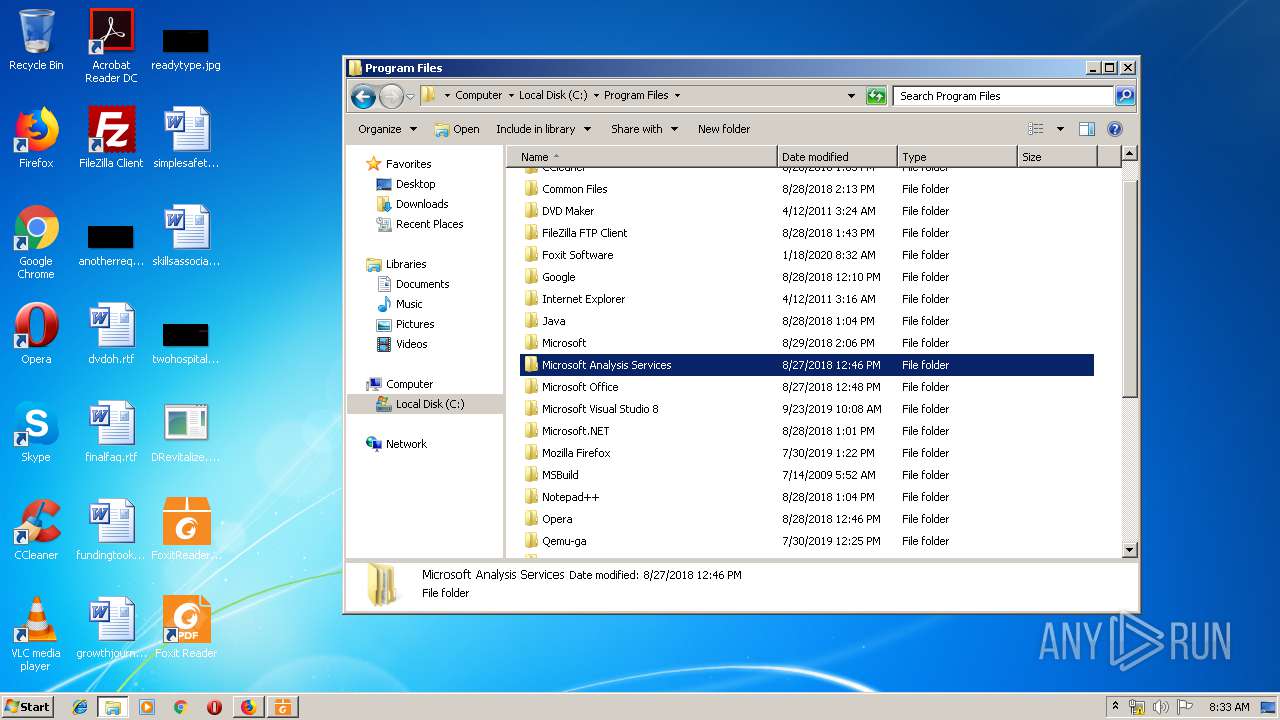
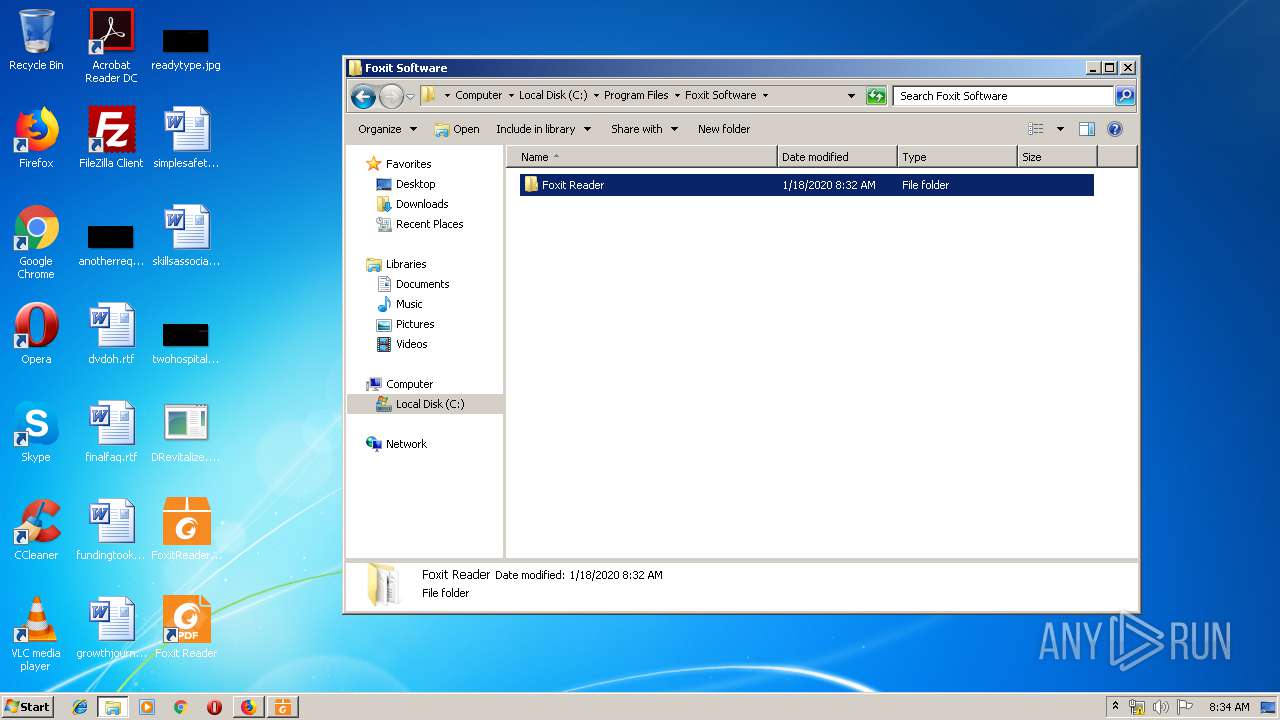
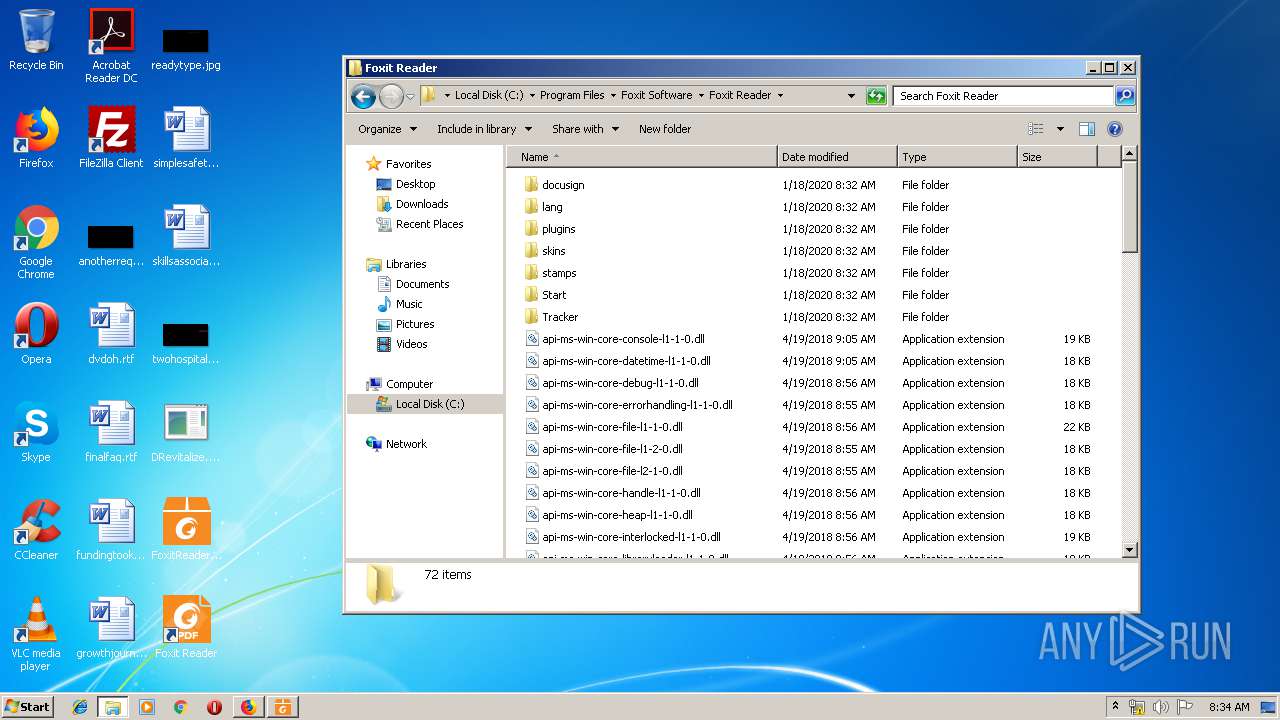
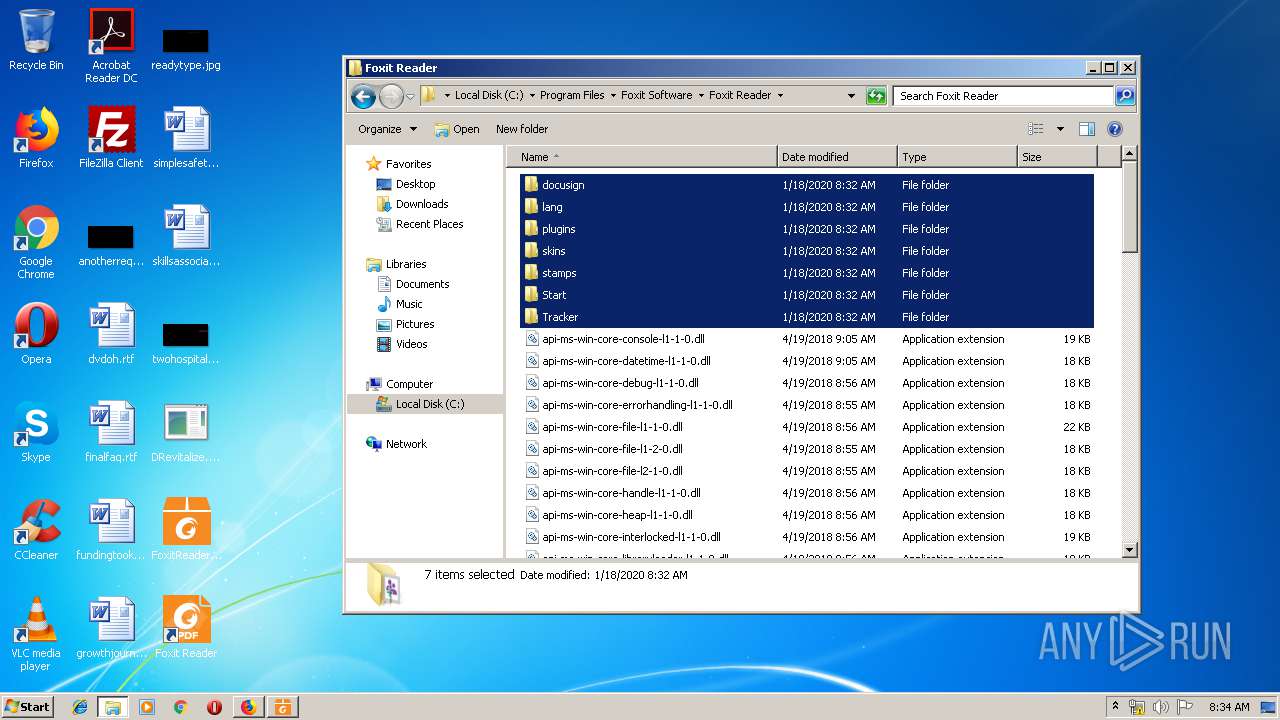
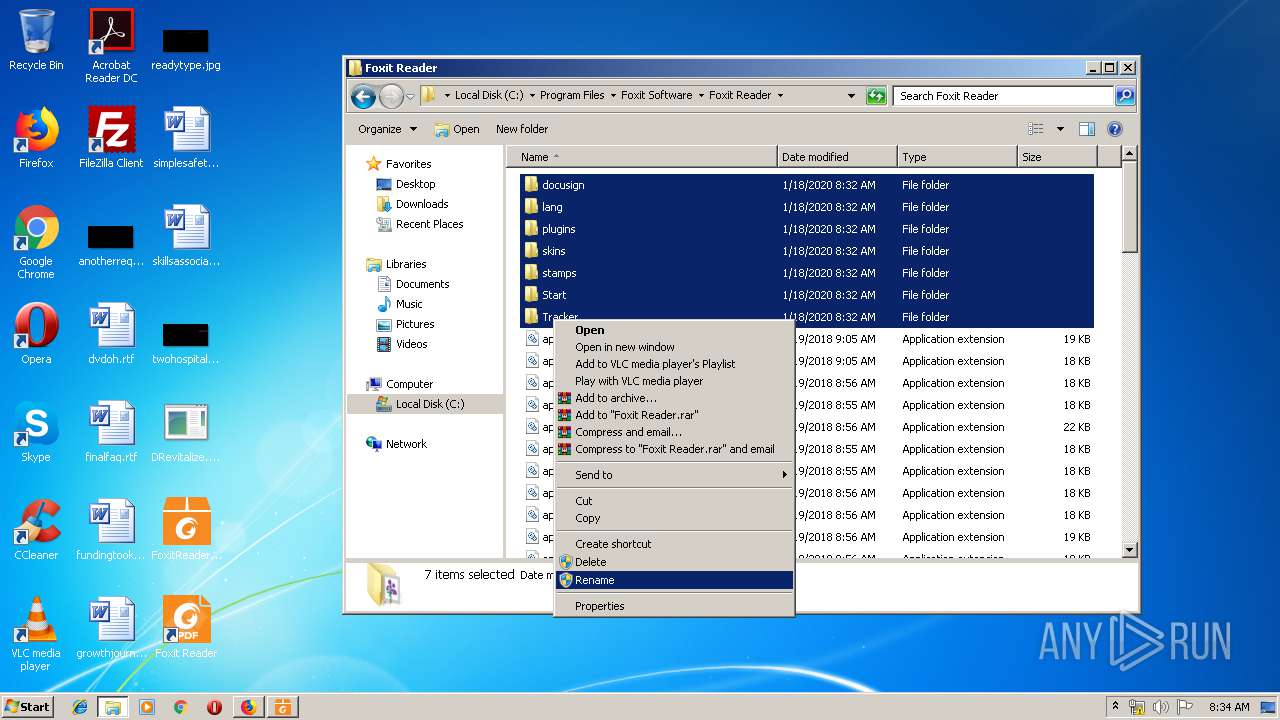
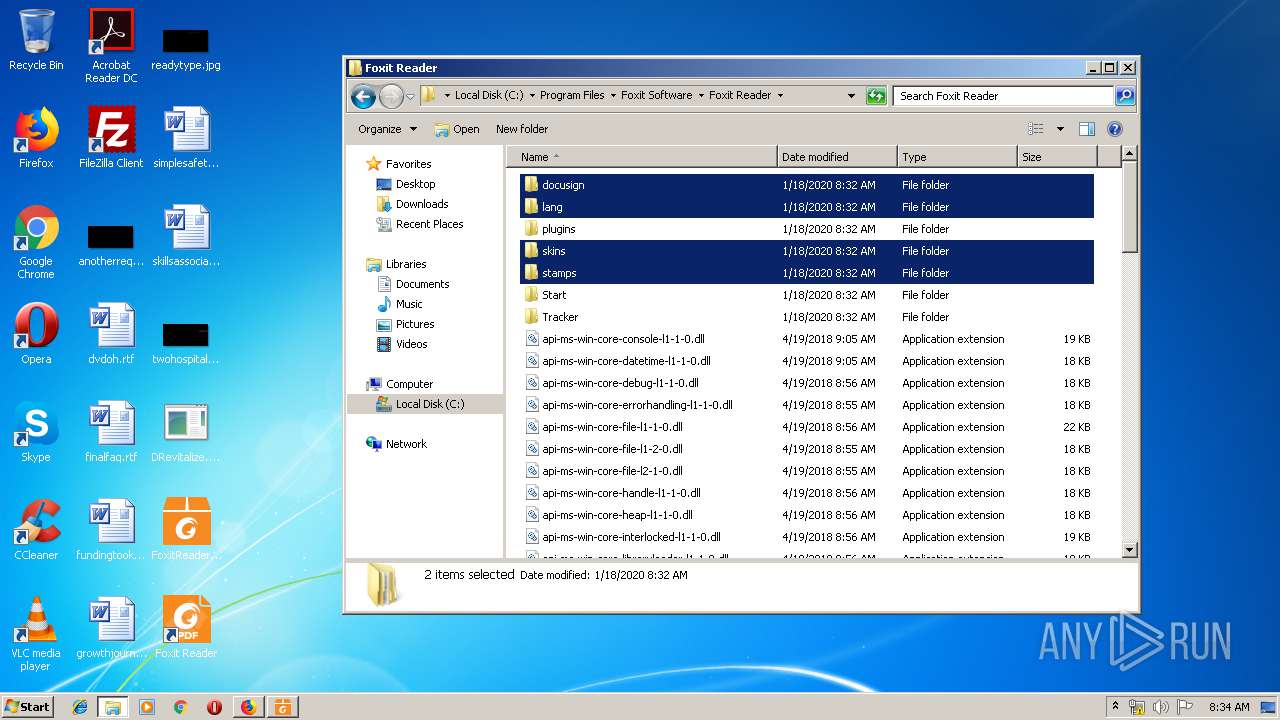
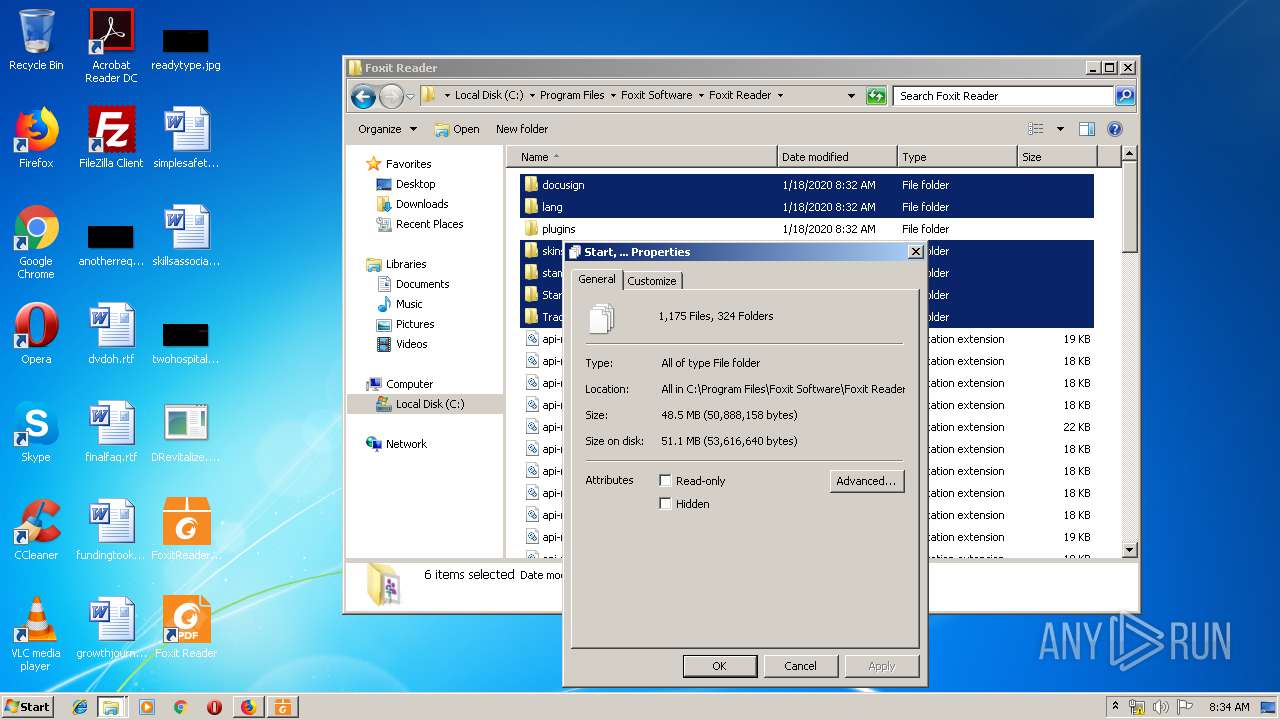
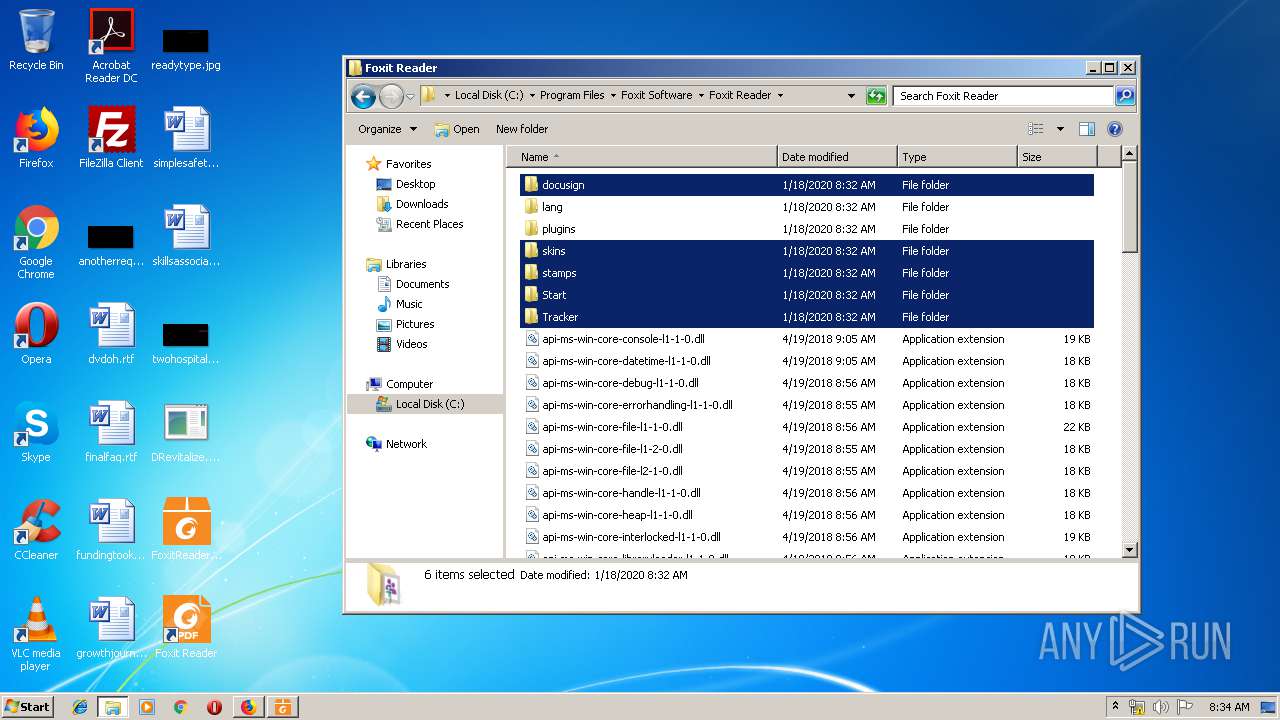
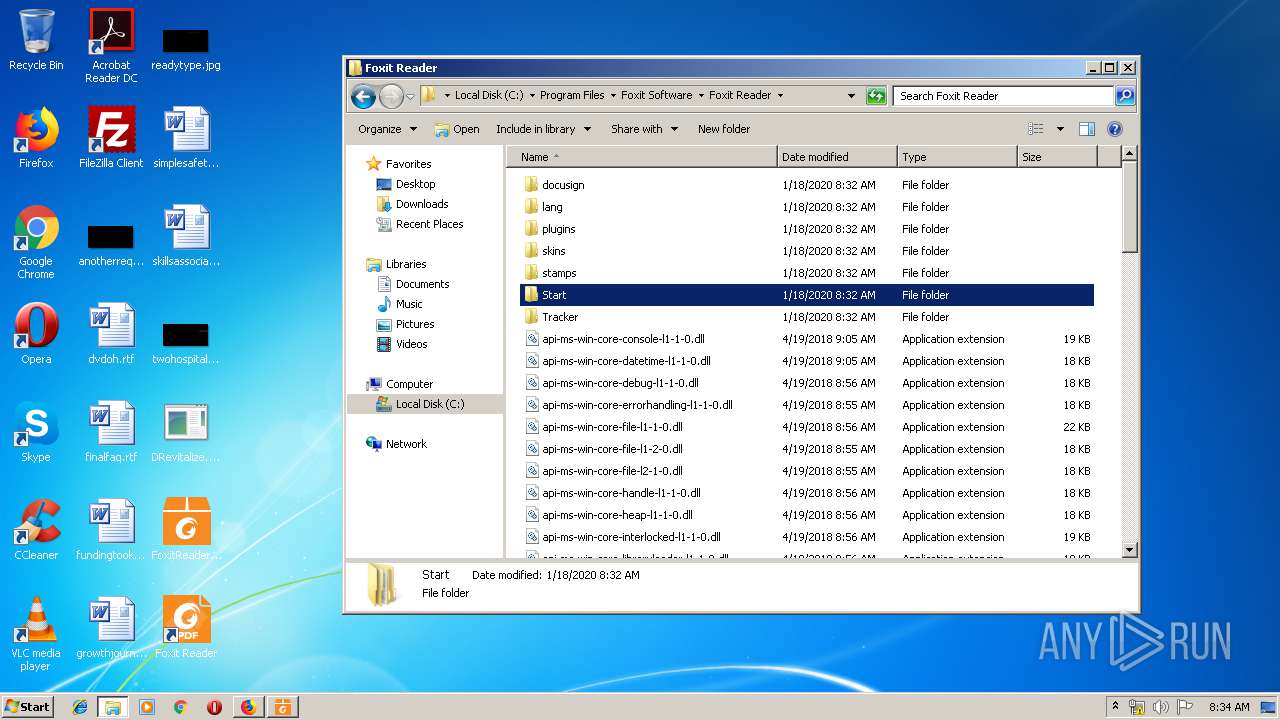
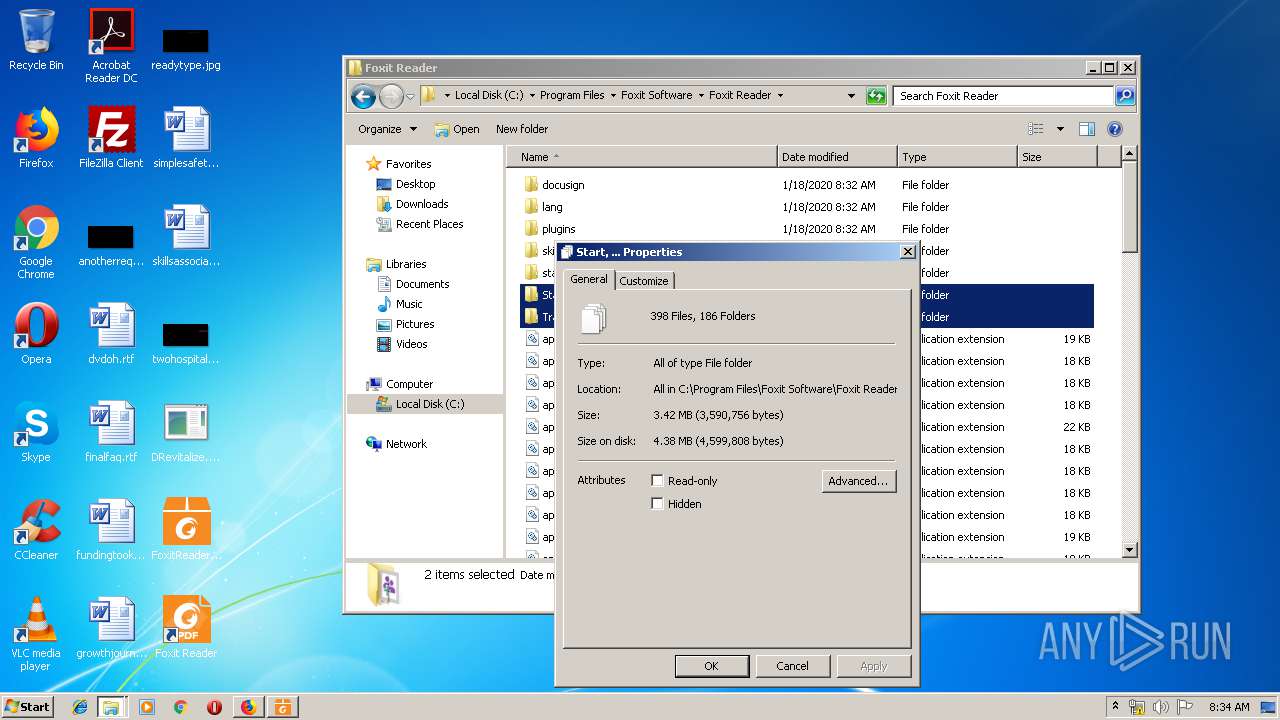
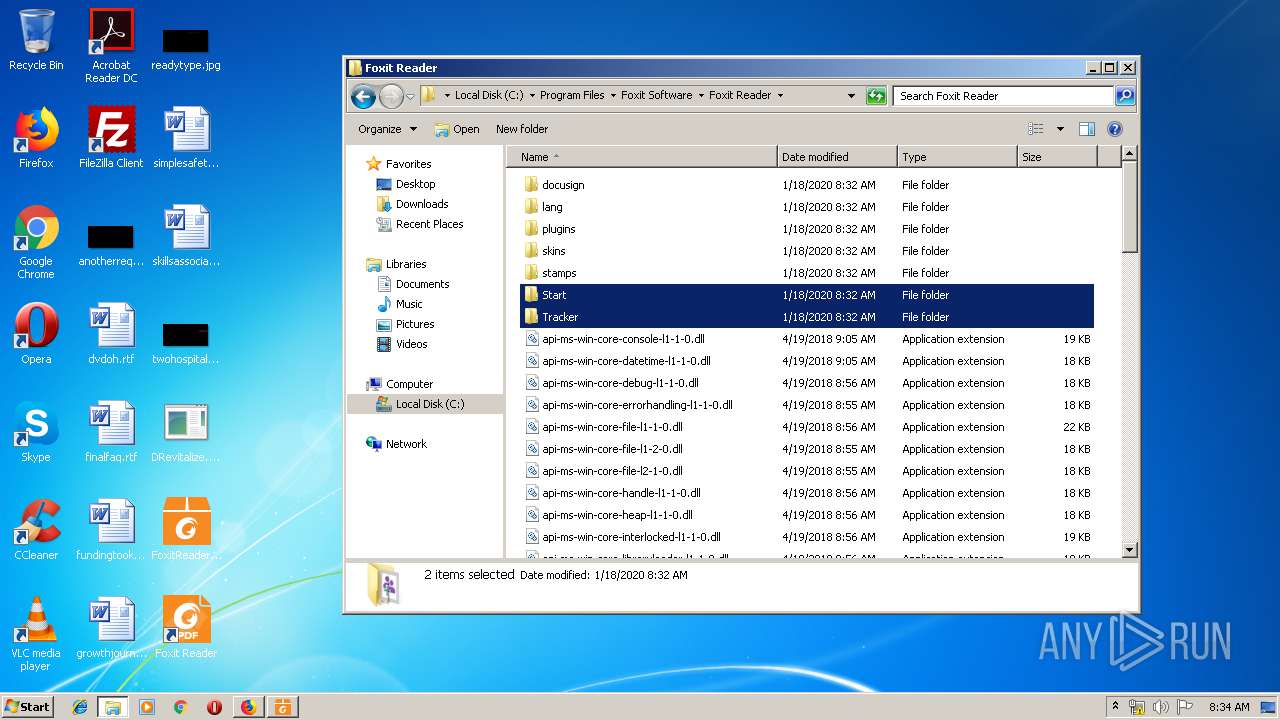
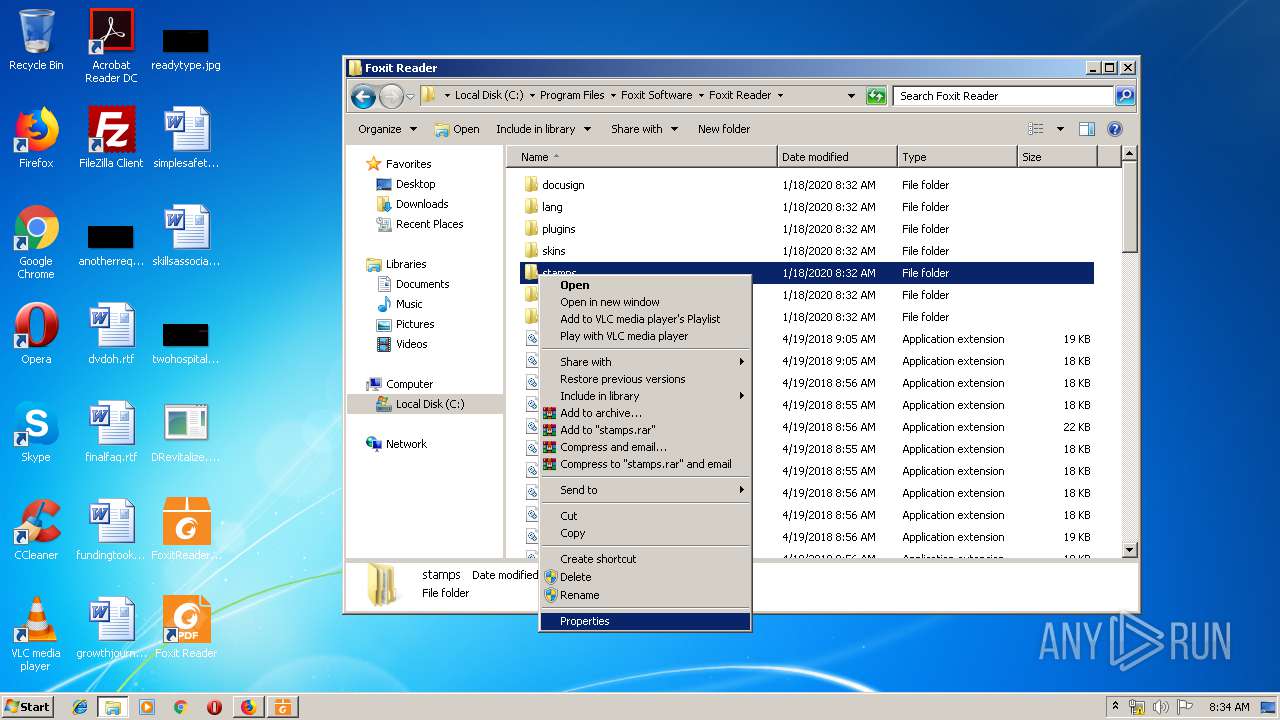
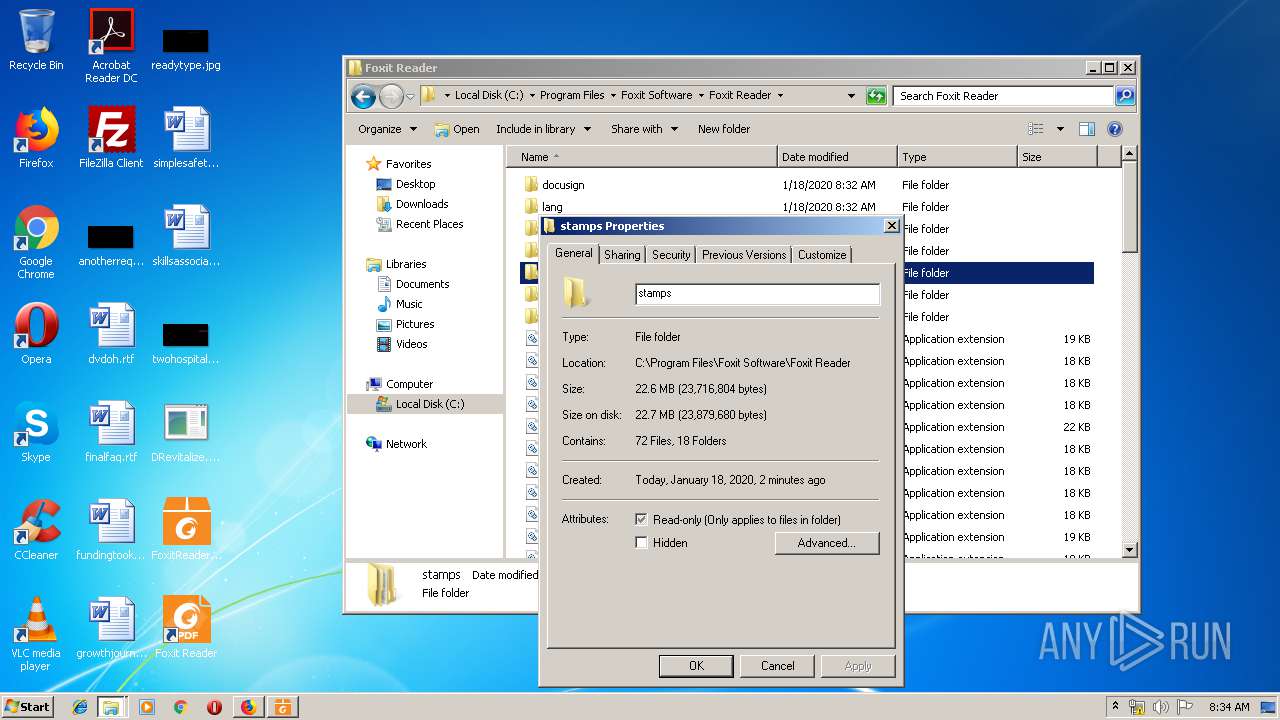
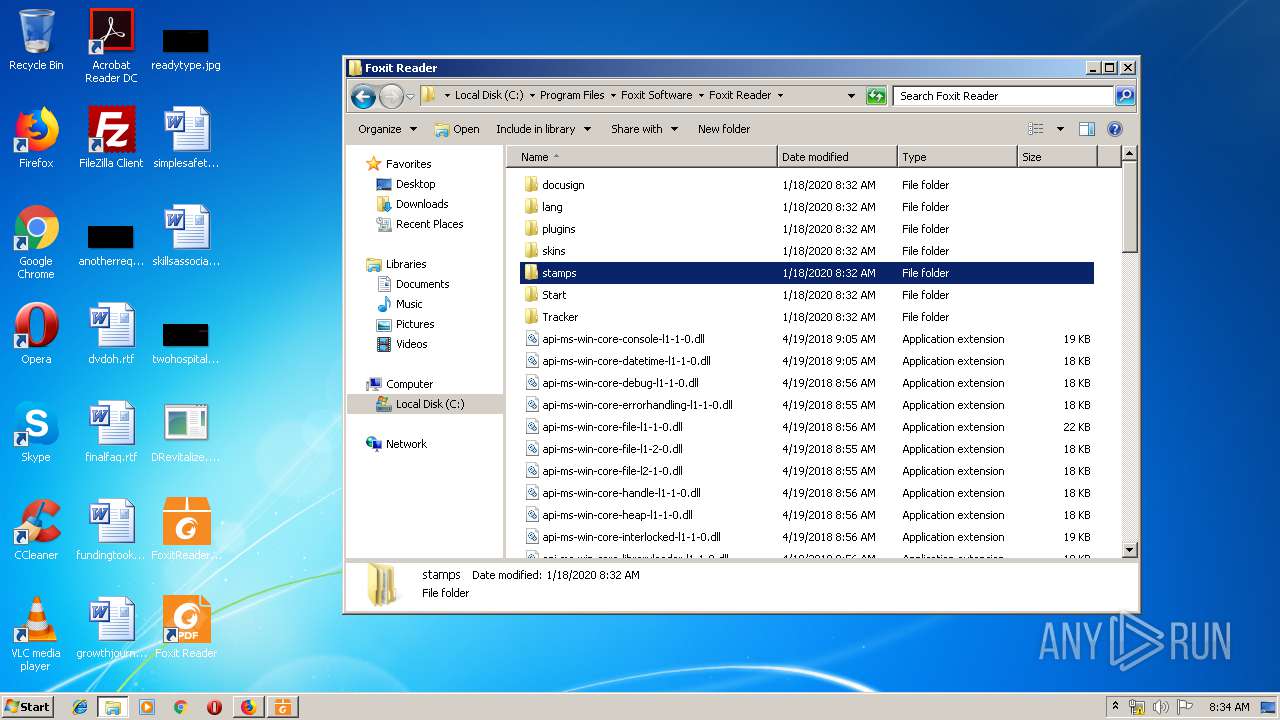
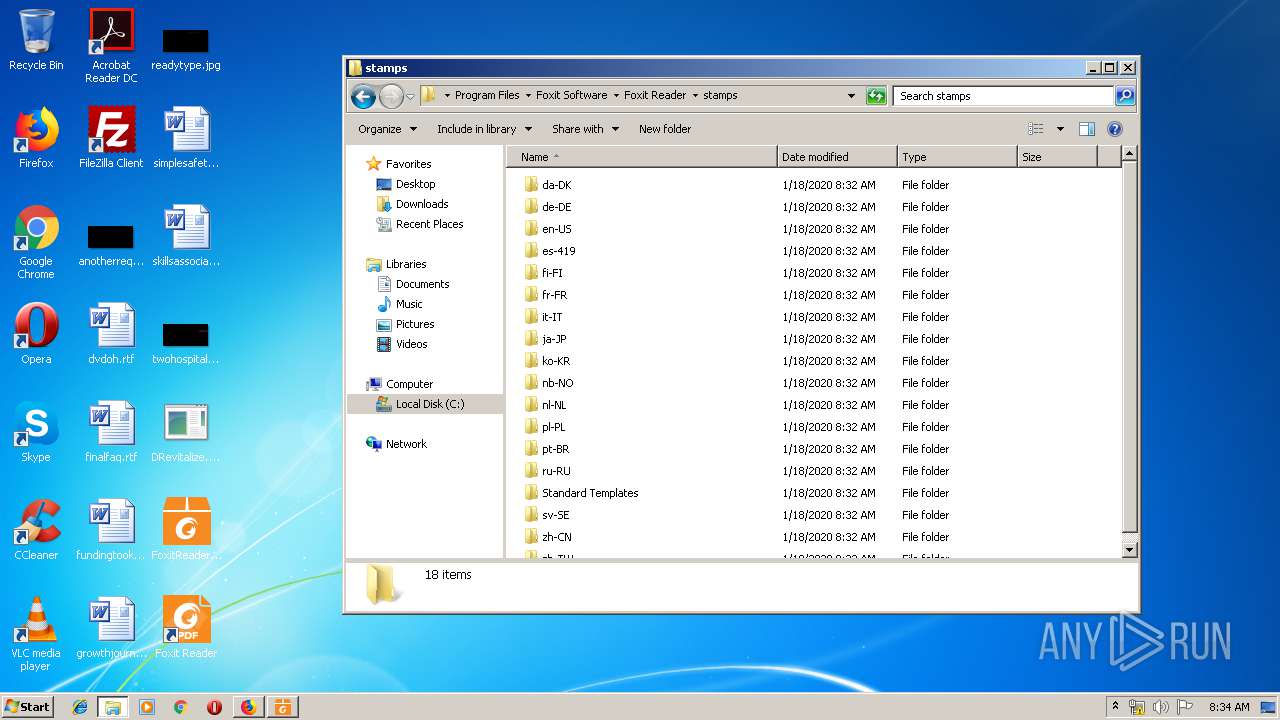
Creates files in the program directory
- firefox.exe (PID: 1956)
Reads Windows owner or organization settings
- FoxitReader971_L10N_Setup_Prom.tmp (PID: 2200)
Reads the Windows organization settings
- FoxitReader971_L10N_Setup_Prom.tmp (PID: 2200)
Creates COM task schedule object
- regsvr32.exe (PID: 2136)
- FoxitReader.exe (PID: 3256)
- FoxitReader.exe (PID: 1252)
Changes IE settings (feature browser emulation)
- FoxitReader971_L10N_Setup_Prom.tmp (PID: 2200)
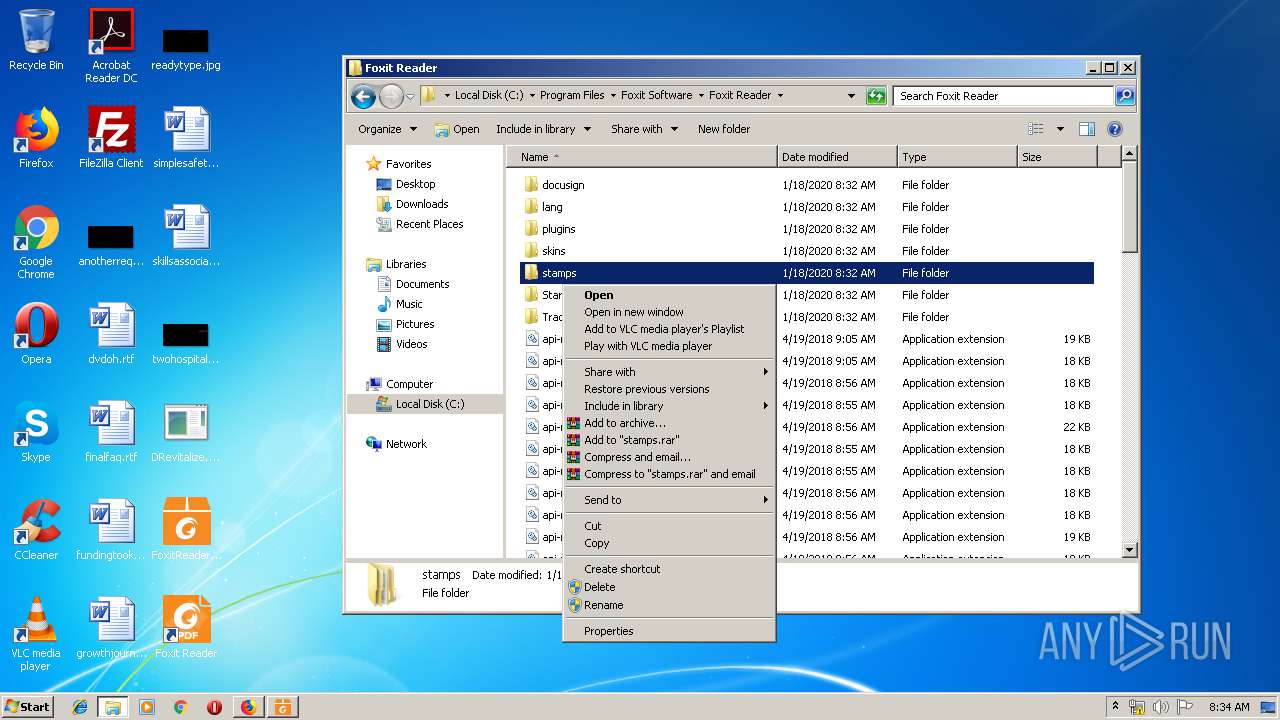
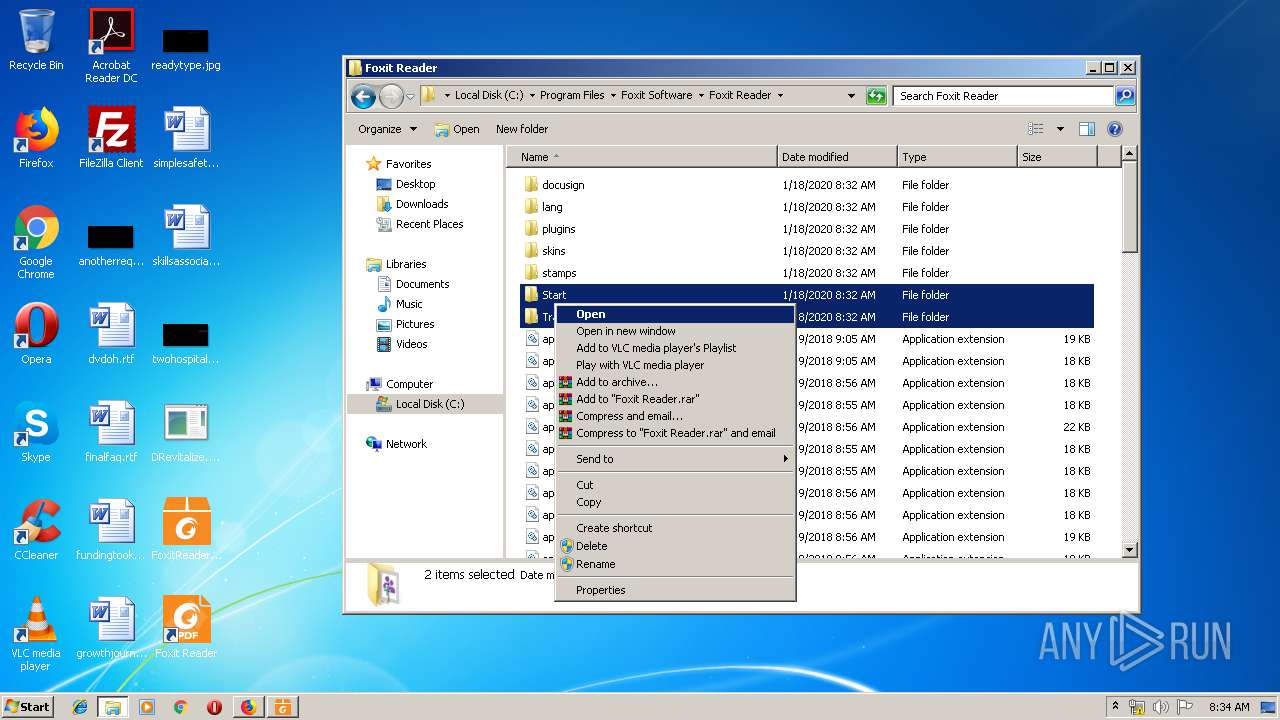
Modifies the open verb of a shell class
- FoxitReader971_L10N_Setup_Prom.tmp (PID: 2200)
- FoxitReader.exe (PID: 1252)
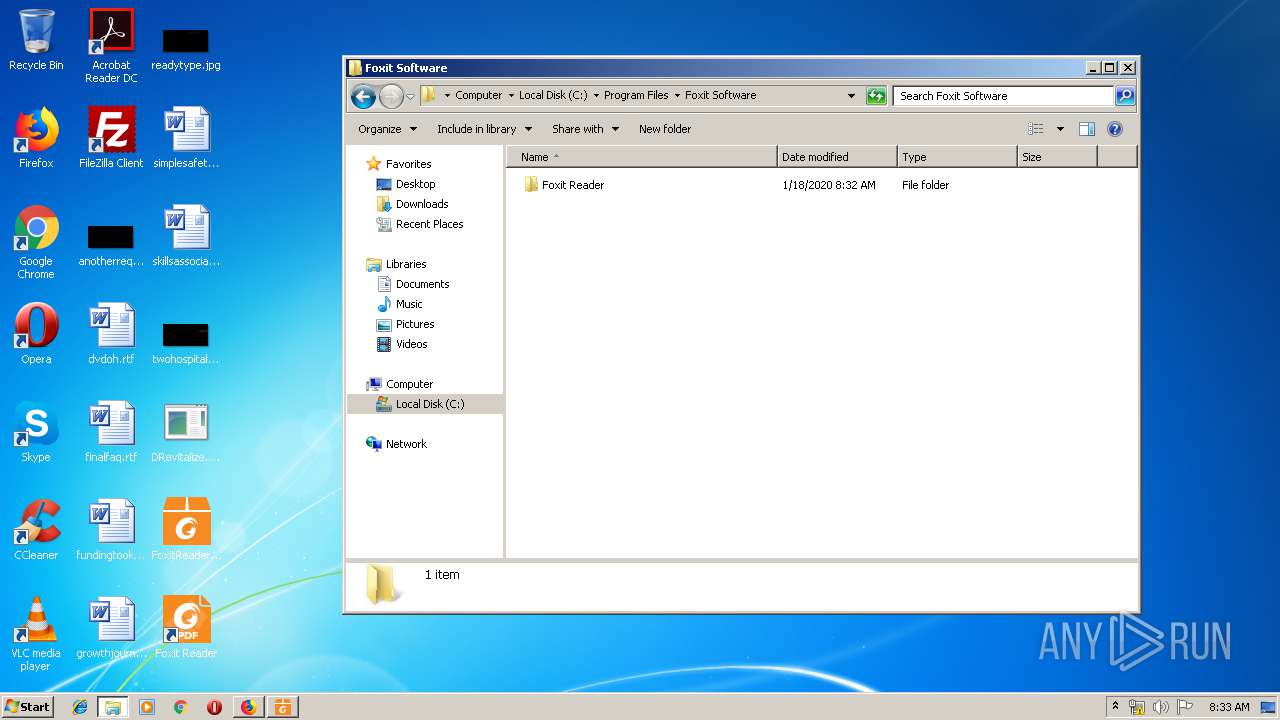
Creates files in the user directory
- FoxitReader.exe (PID: 3256)
- FoxitReader971_L10N_Setup_Prom.tmp (PID: 2200)
INFO
Changes internet zones settings
- iexplore.exe (PID: 1916)
Creates files in the user directory
- iexplore.exe (PID: 3176)
- iexplore.exe (PID: 1916)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3000)
- firefox.exe (PID: 1956)
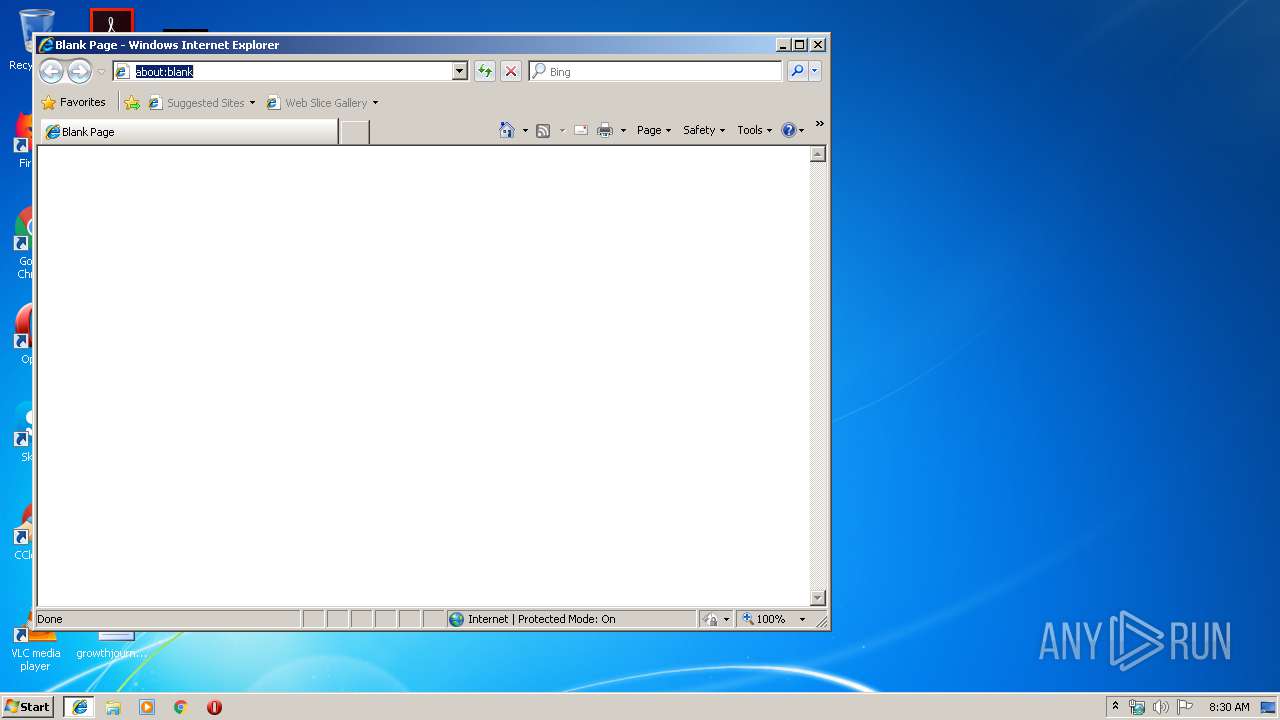
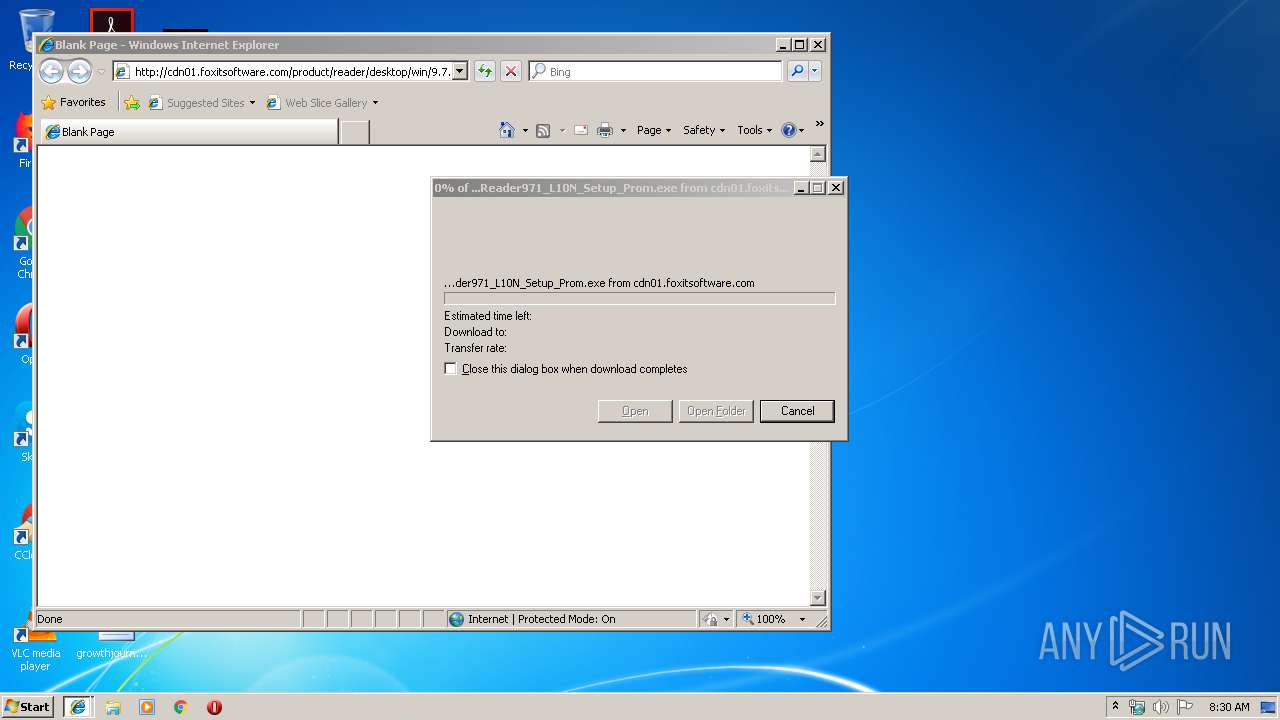
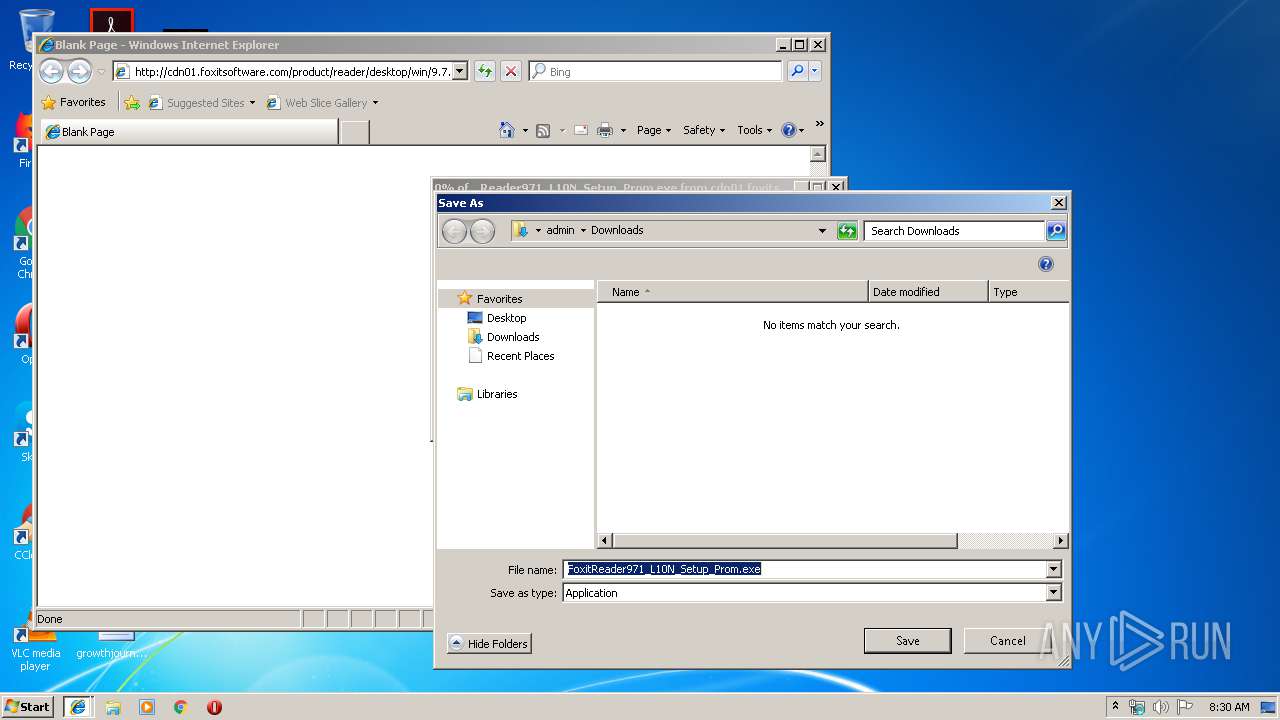
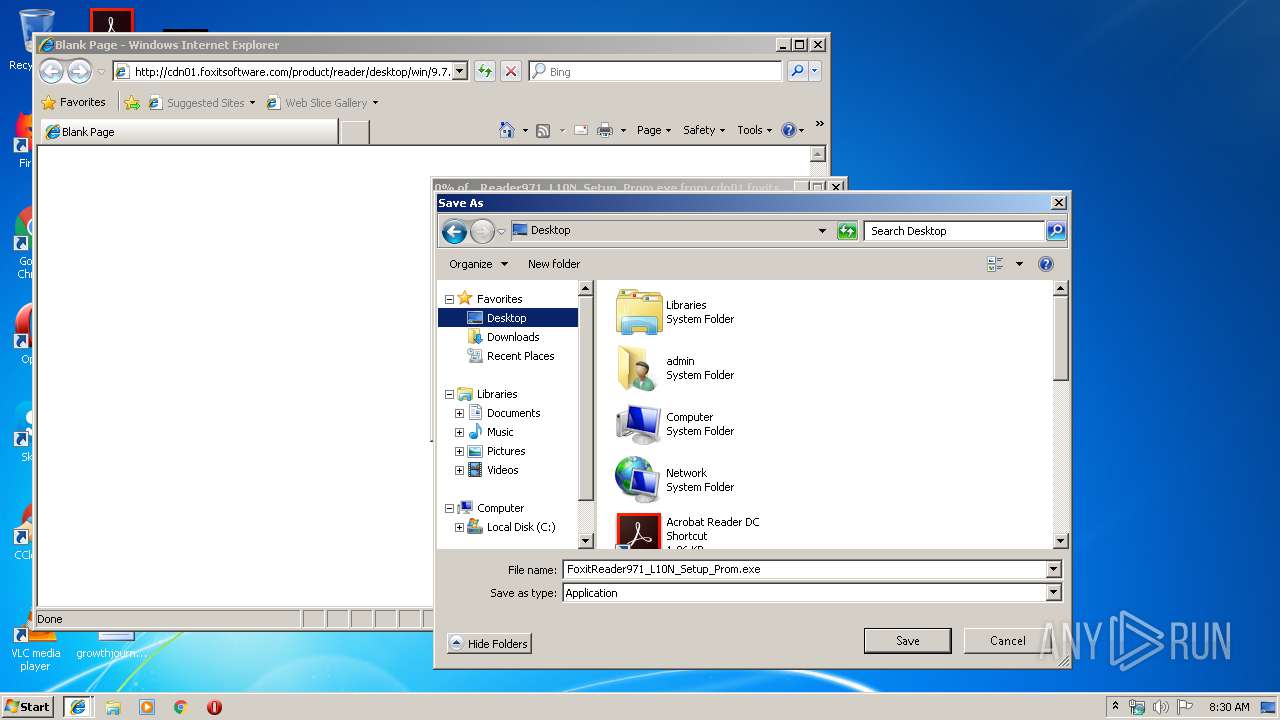
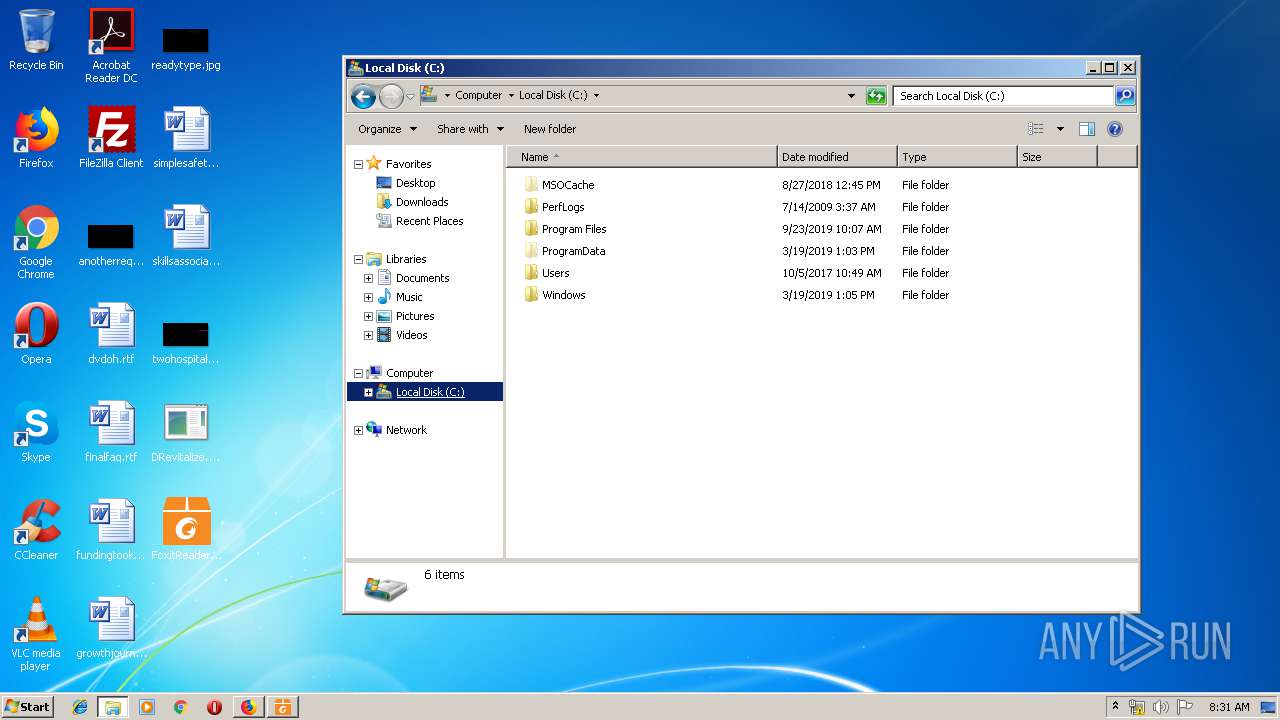
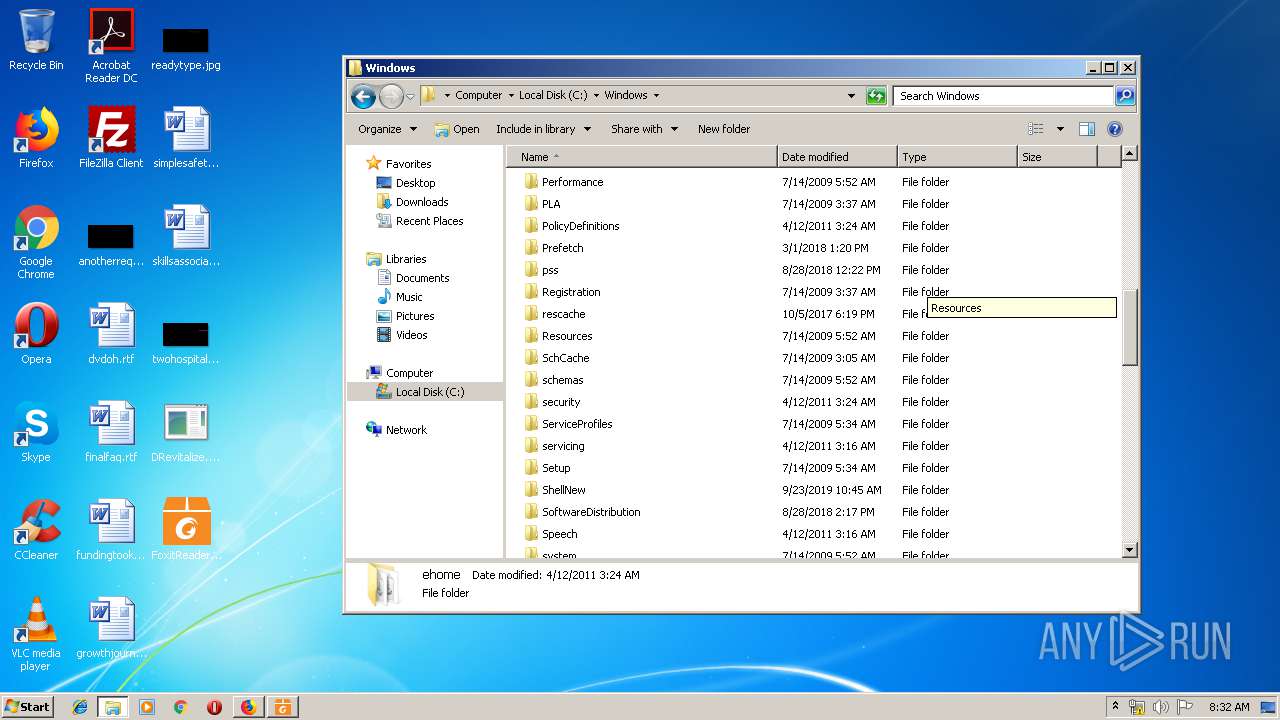
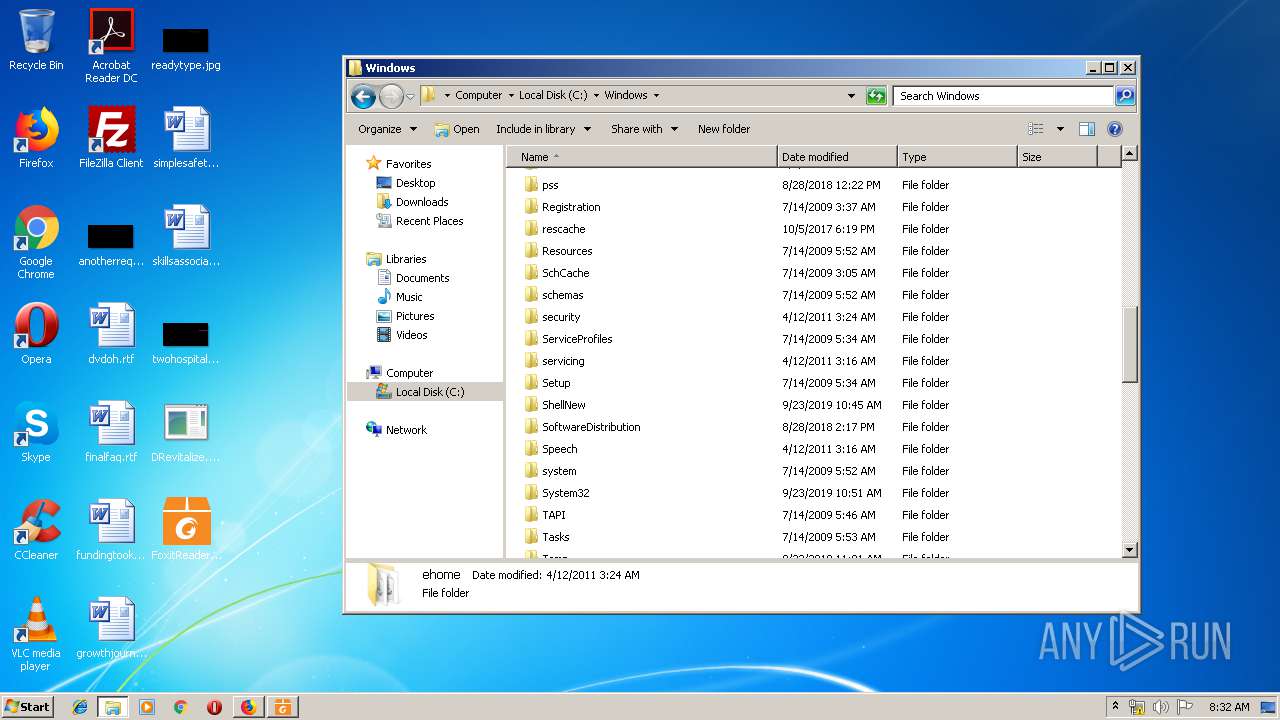
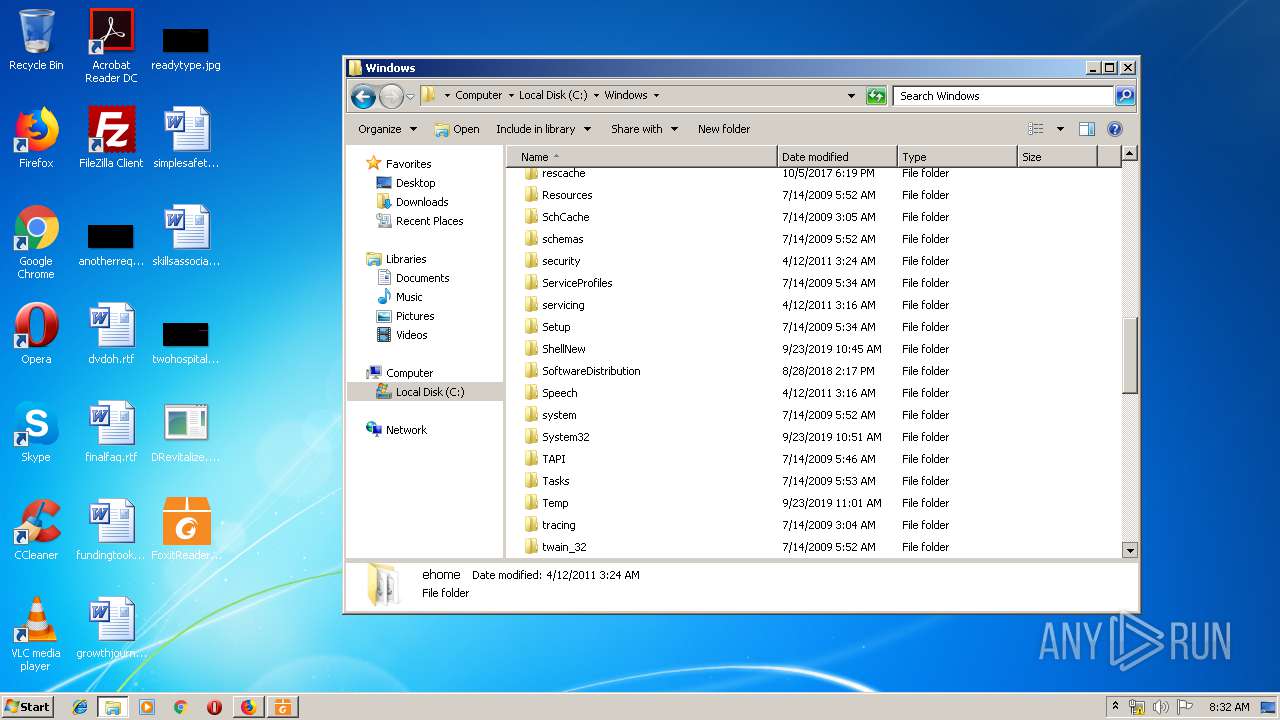
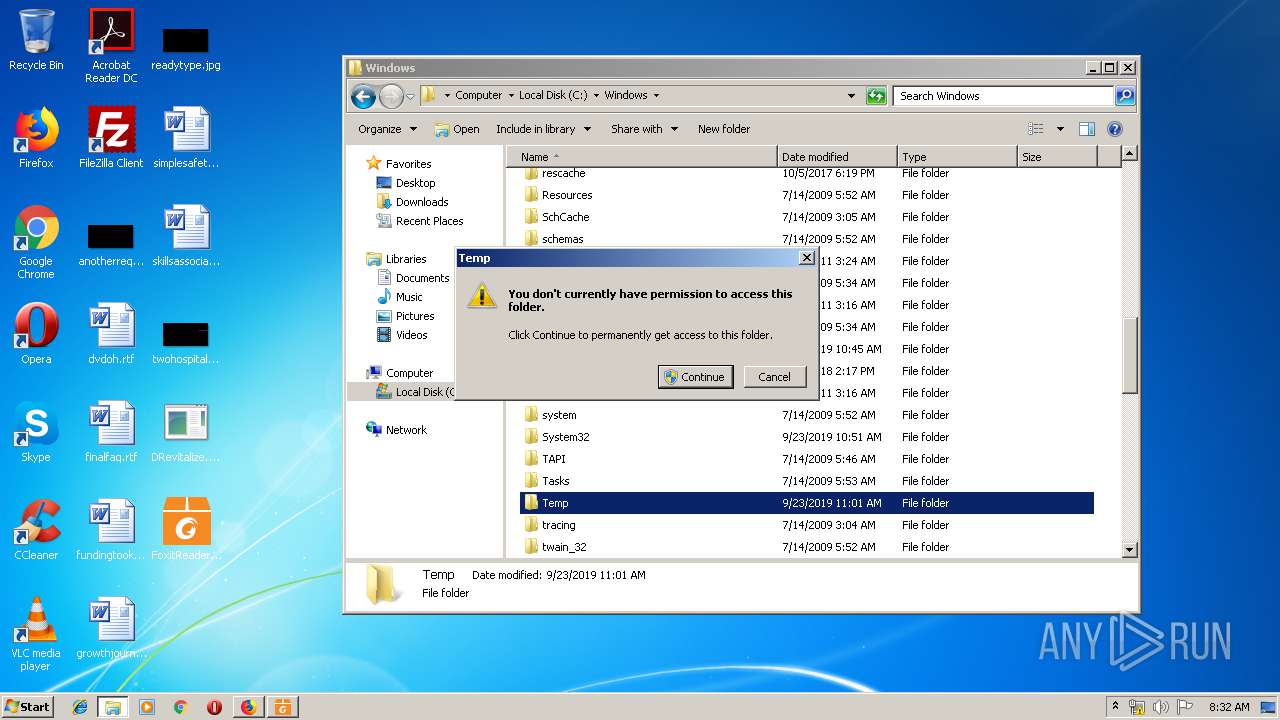
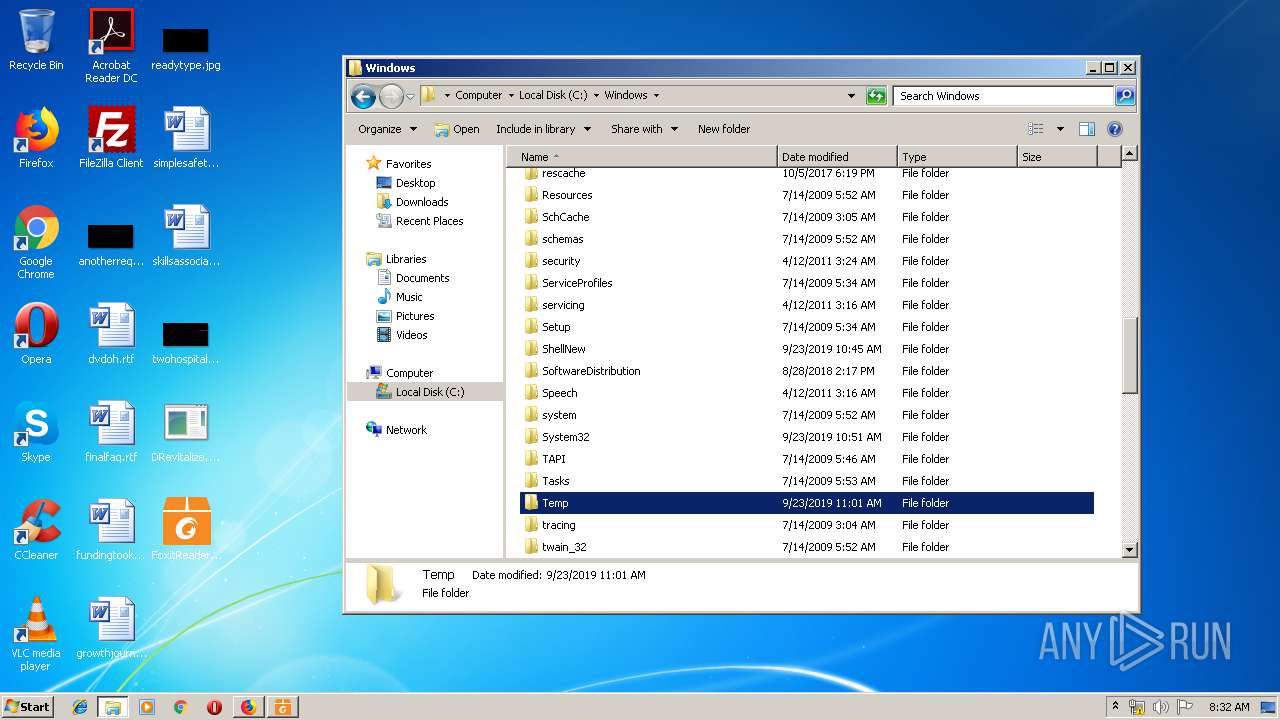
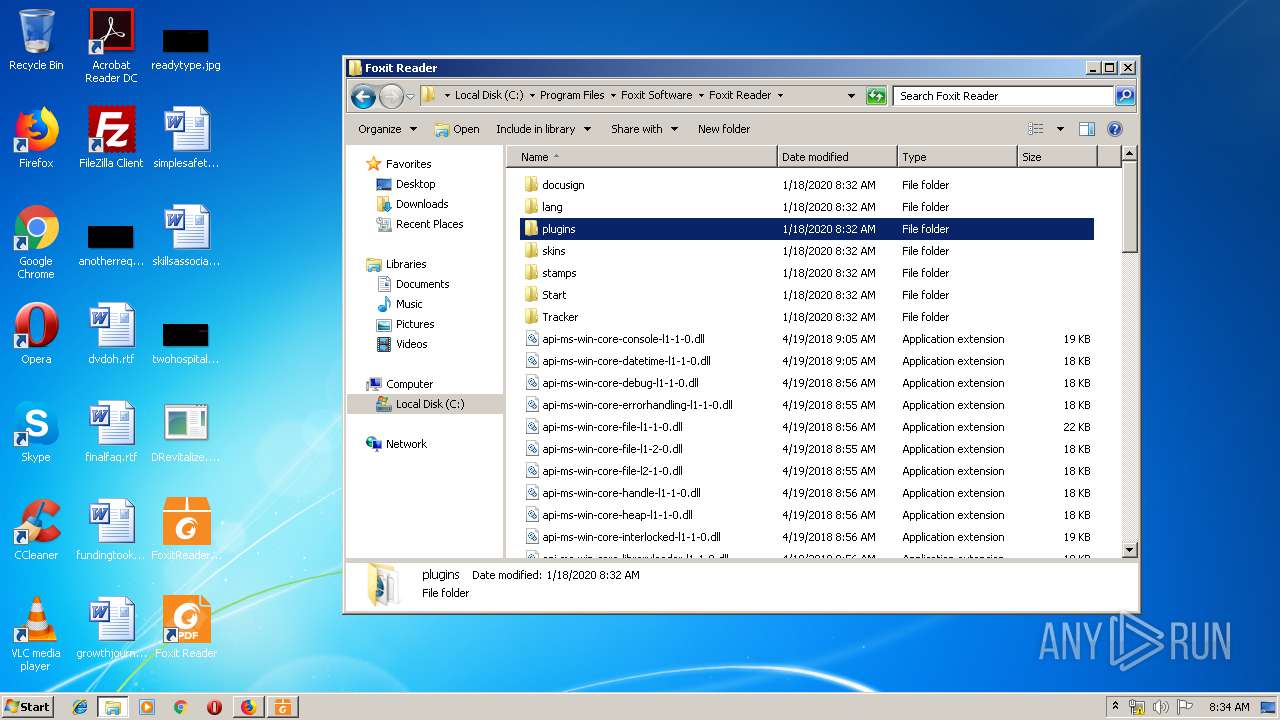
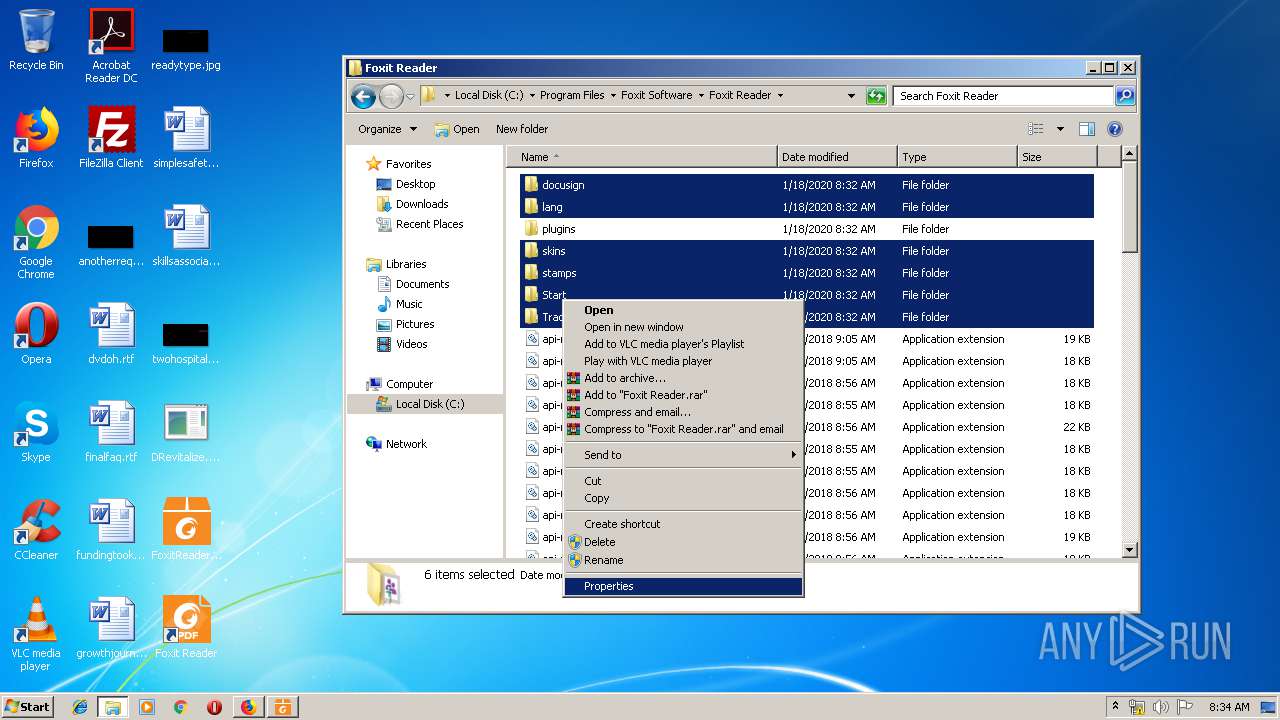
Manual execution by user
- iexplore.exe (PID: 1916)
- firefox.exe (PID: 1024)
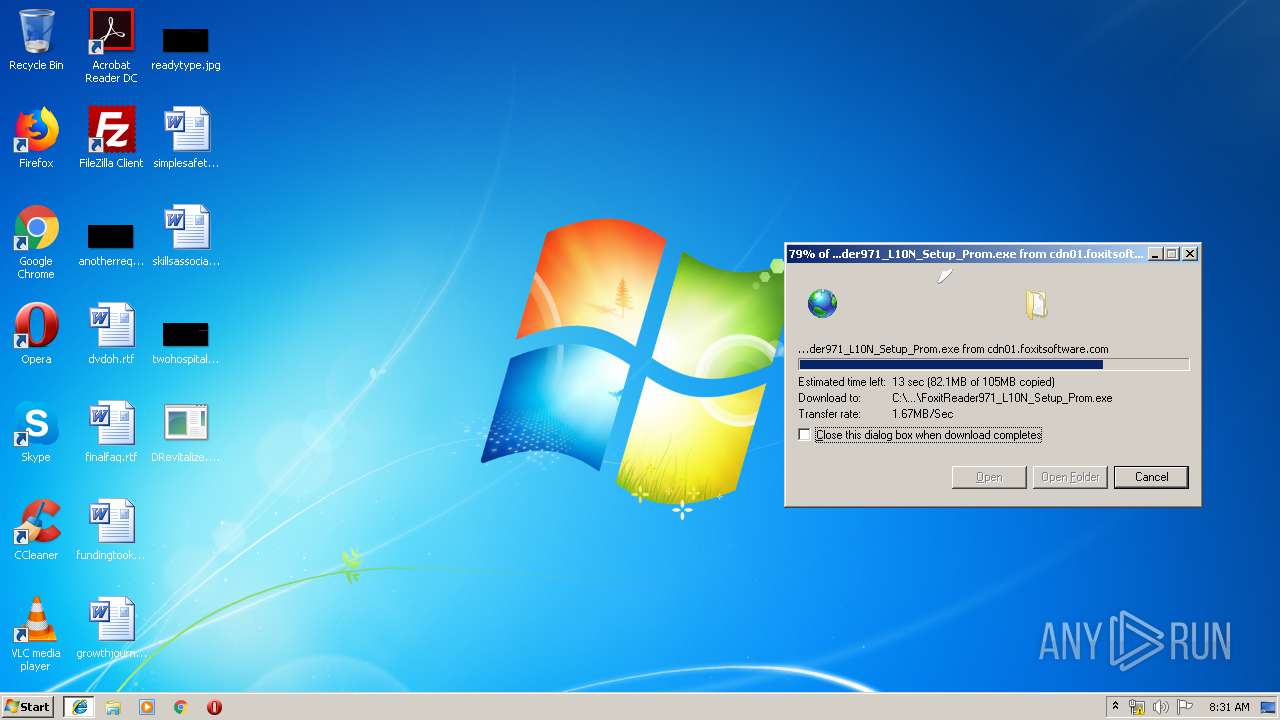
- FoxitReader971_L10N_Setup_Prom.exe (PID: 3140)
- explorer.exe (PID: 1904)
Reads Internet Cache Settings
- iexplore.exe (PID: 3176)
- iexplore.exe (PID: 1916)
Reads internet explorer settings
- iexplore.exe (PID: 3176)
Reads settings of System Certificates
- iexplore.exe (PID: 1916)
Reads CPU info
- firefox.exe (PID: 1956)
Application was dropped or rewritten from another process
- FoxitReader971_L10N_Setup_Prom.tmp (PID: 1708)
- FoxitReader971_L10N_Setup_Prom.tmp (PID: 2200)
- CountInstallation.exe (PID: 1412)
Writes to a desktop.ini file (may be used to cloak folders)
- firefox.exe (PID: 3768)
Application launched itself
- firefox.exe (PID: 1956)
Loads dropped or rewritten executable
- FoxitReader971_L10N_Setup_Prom.tmp (PID: 2200)
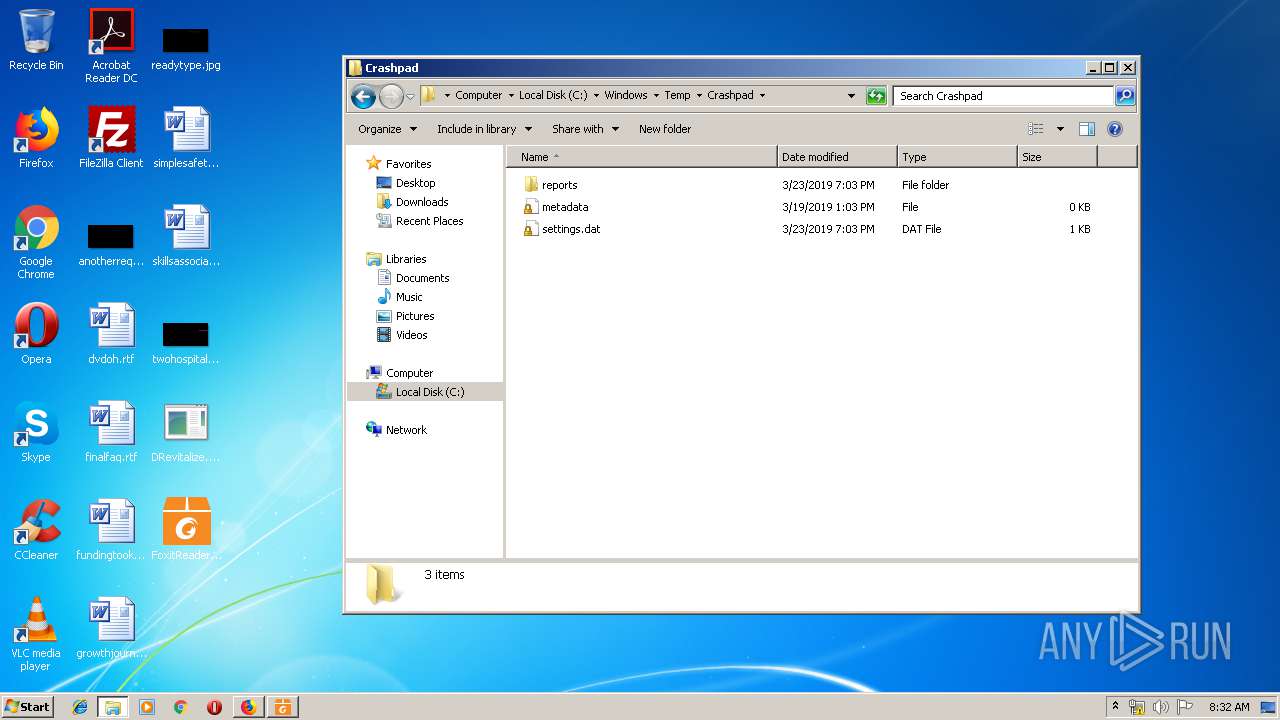
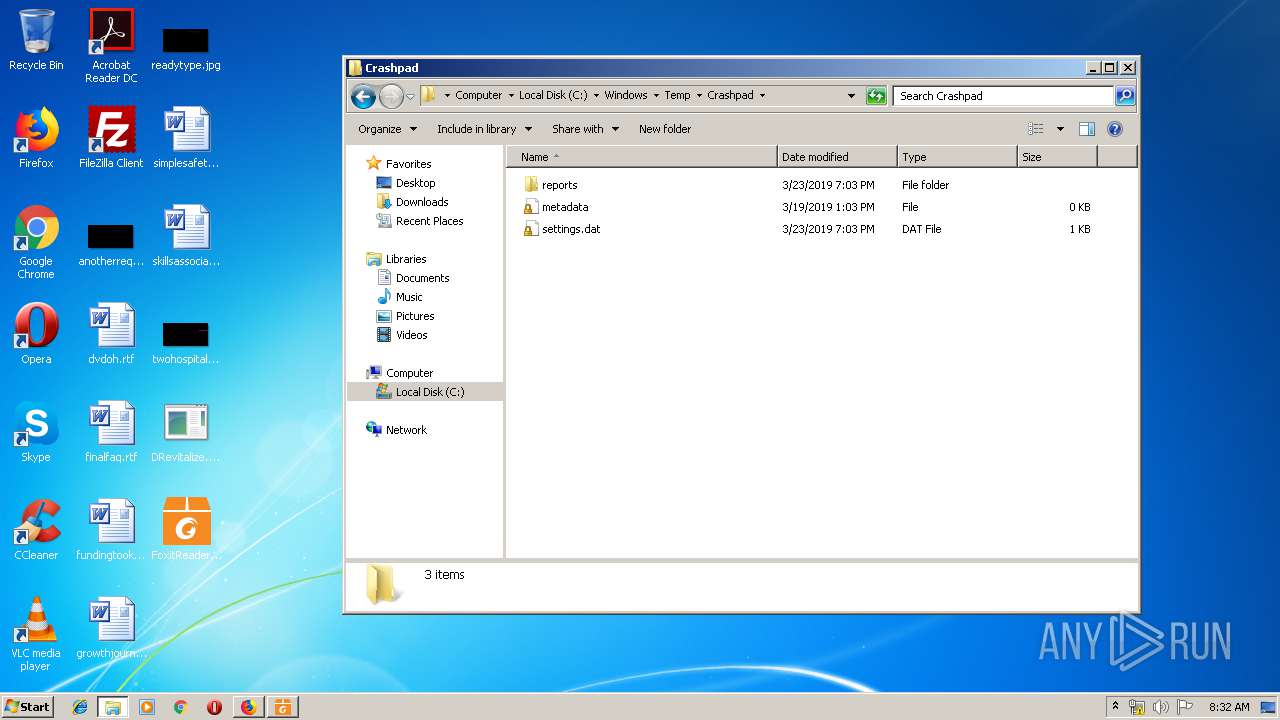
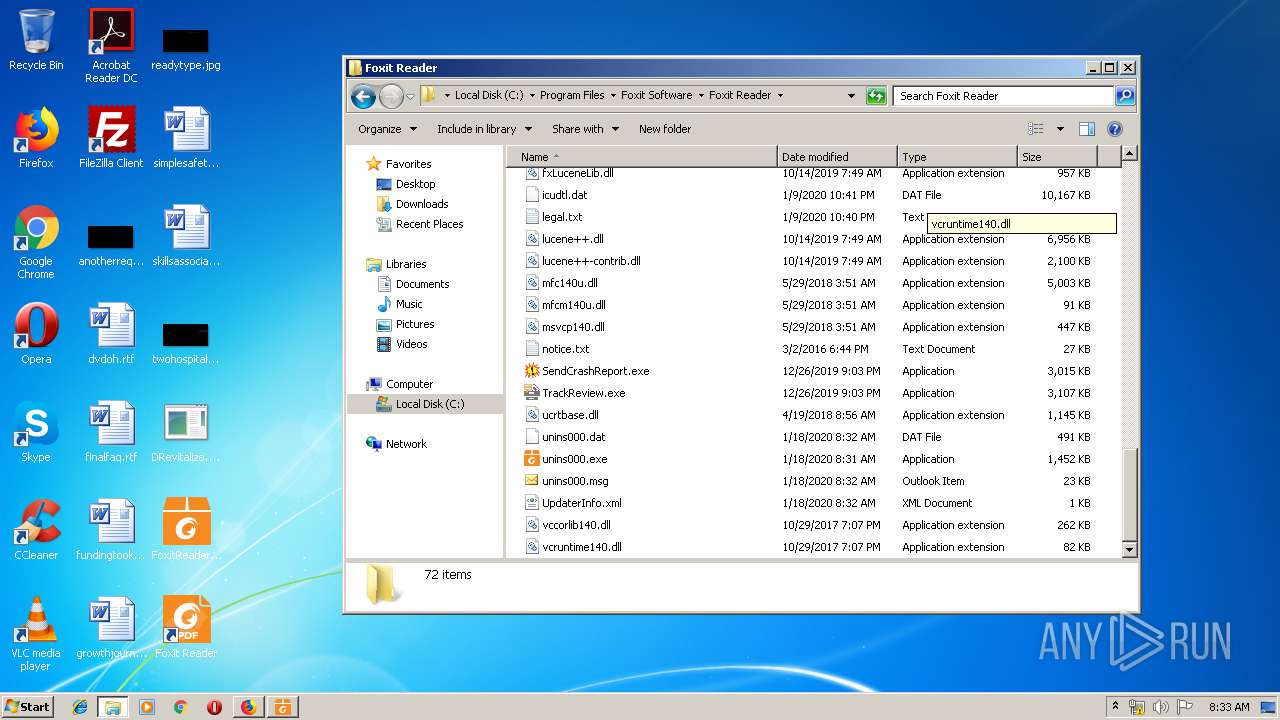
Creates a software uninstall entry
- FoxitReader971_L10N_Setup_Prom.tmp (PID: 2200)
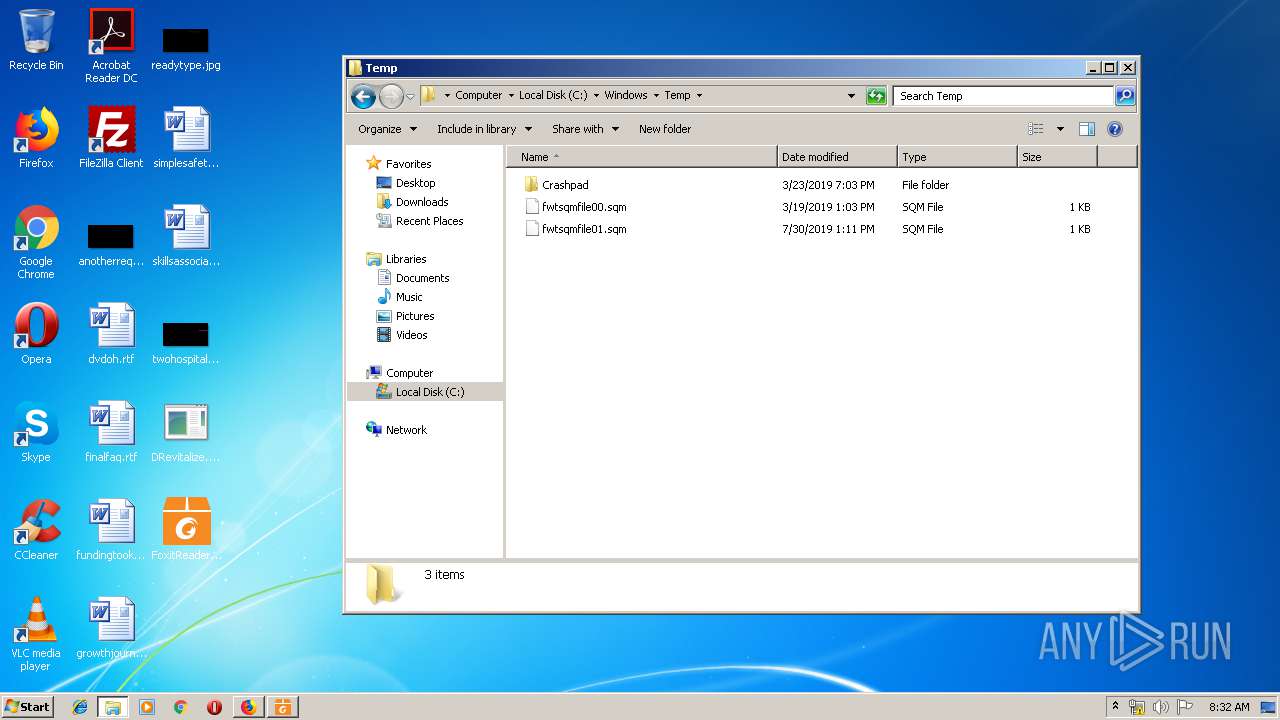
Dropped object may contain Bitcoin addresses
- FoxitReader971_L10N_Setup_Prom.tmp (PID: 2200)
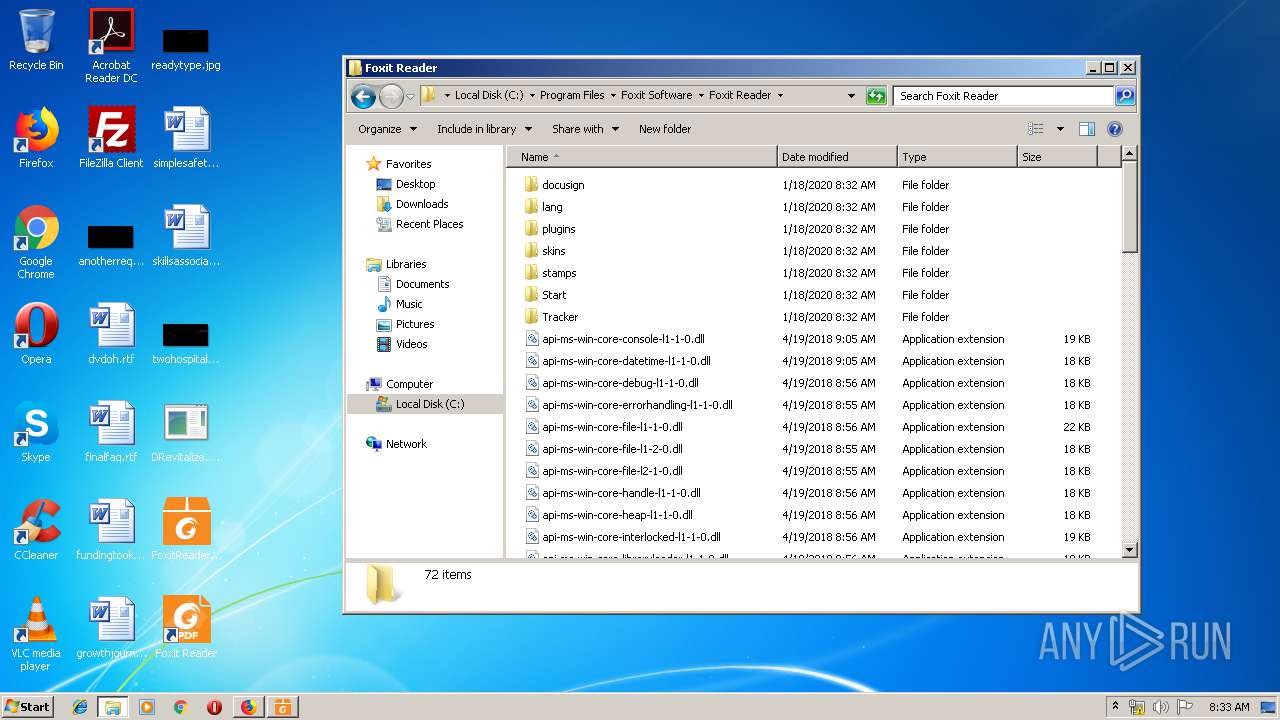
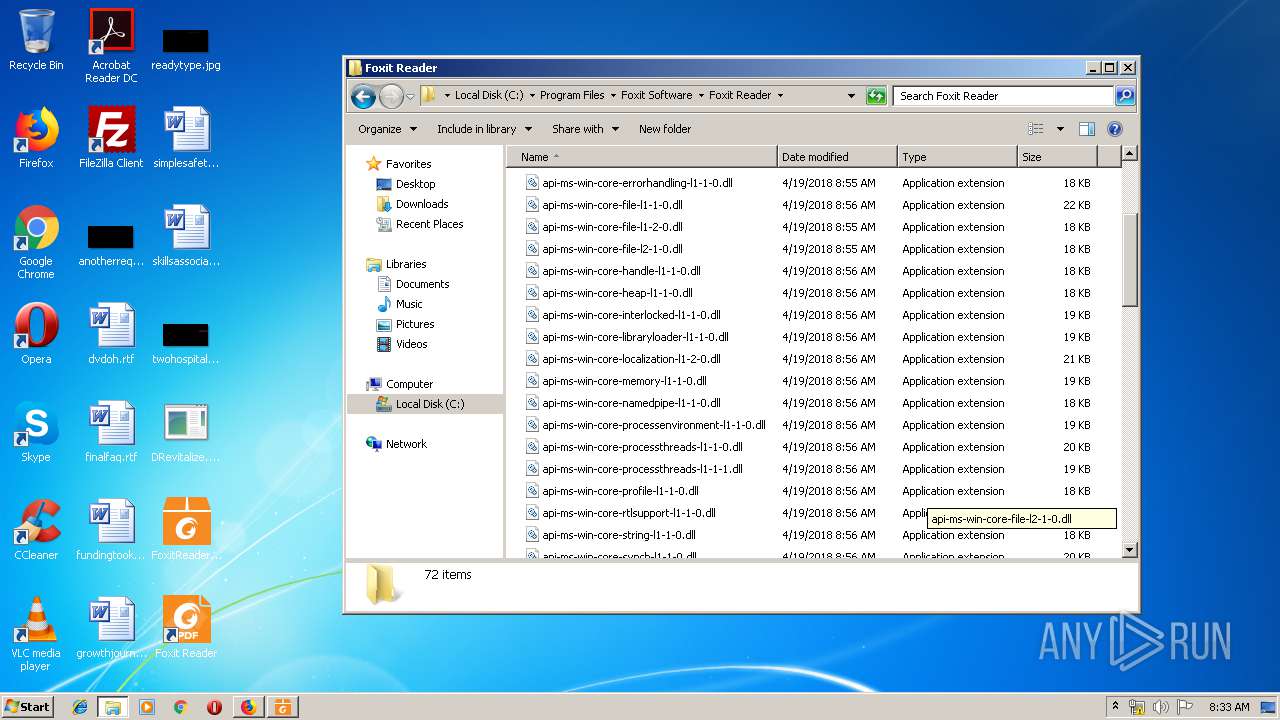
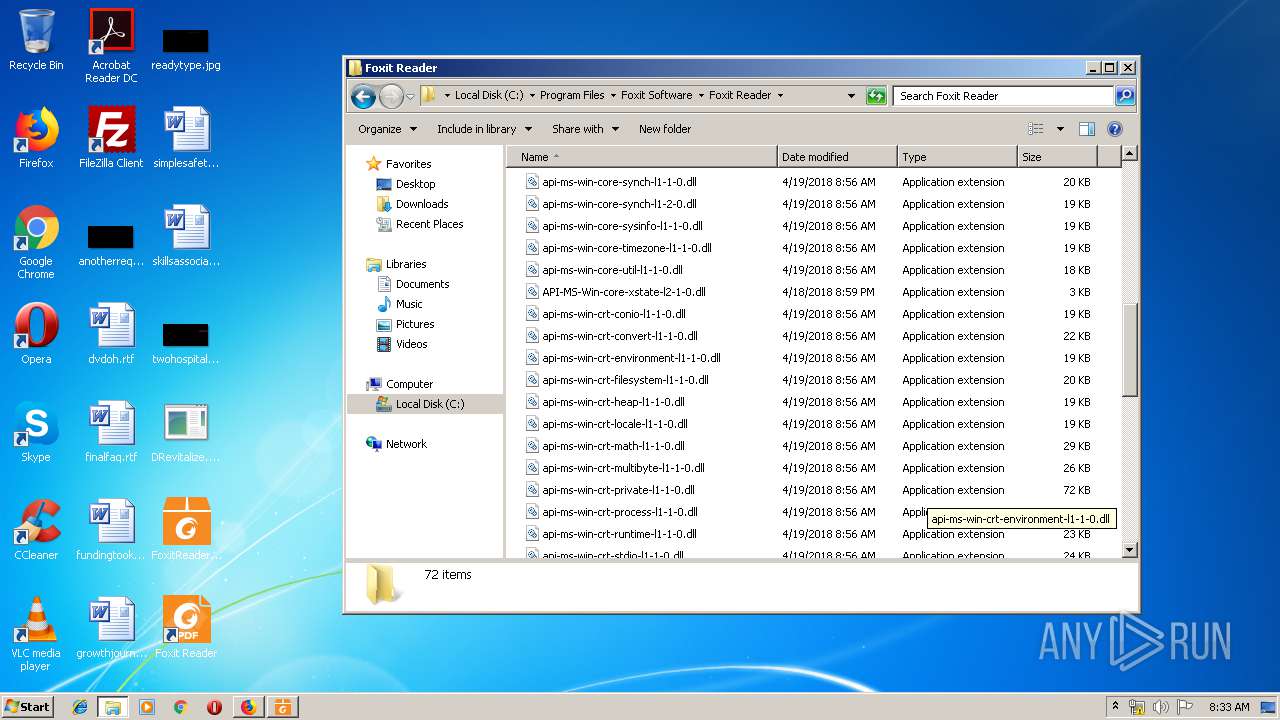
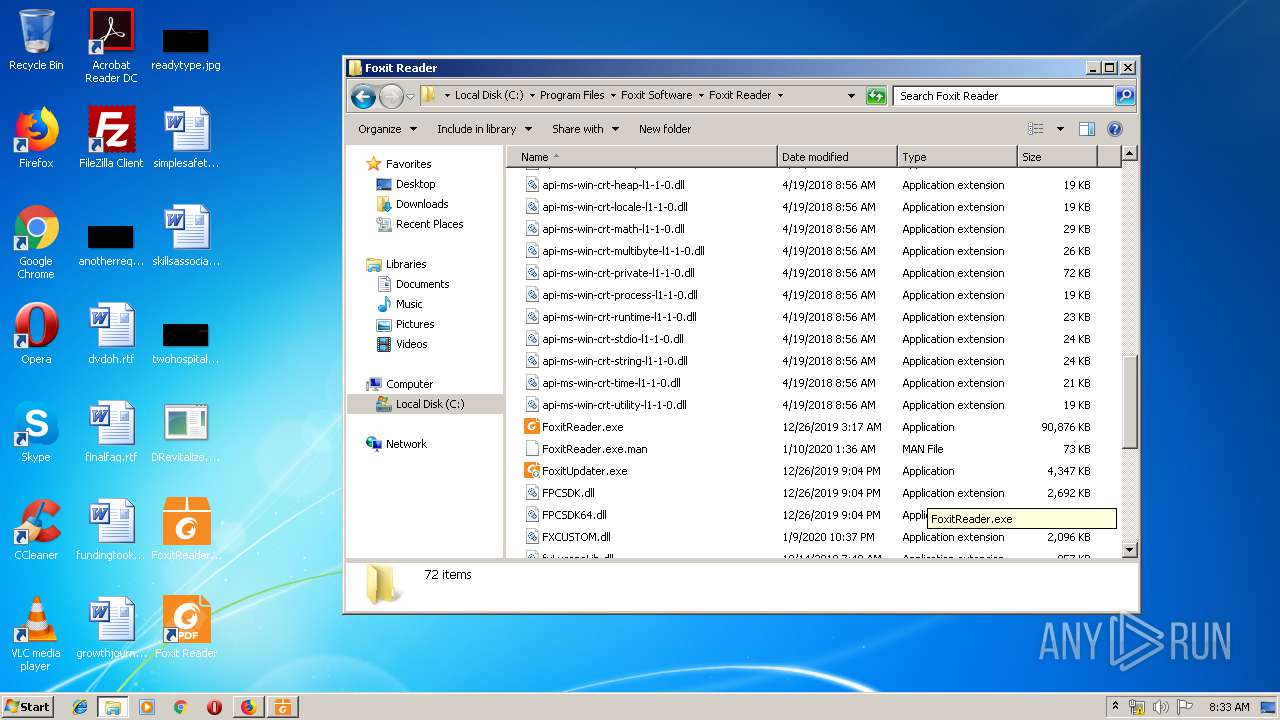
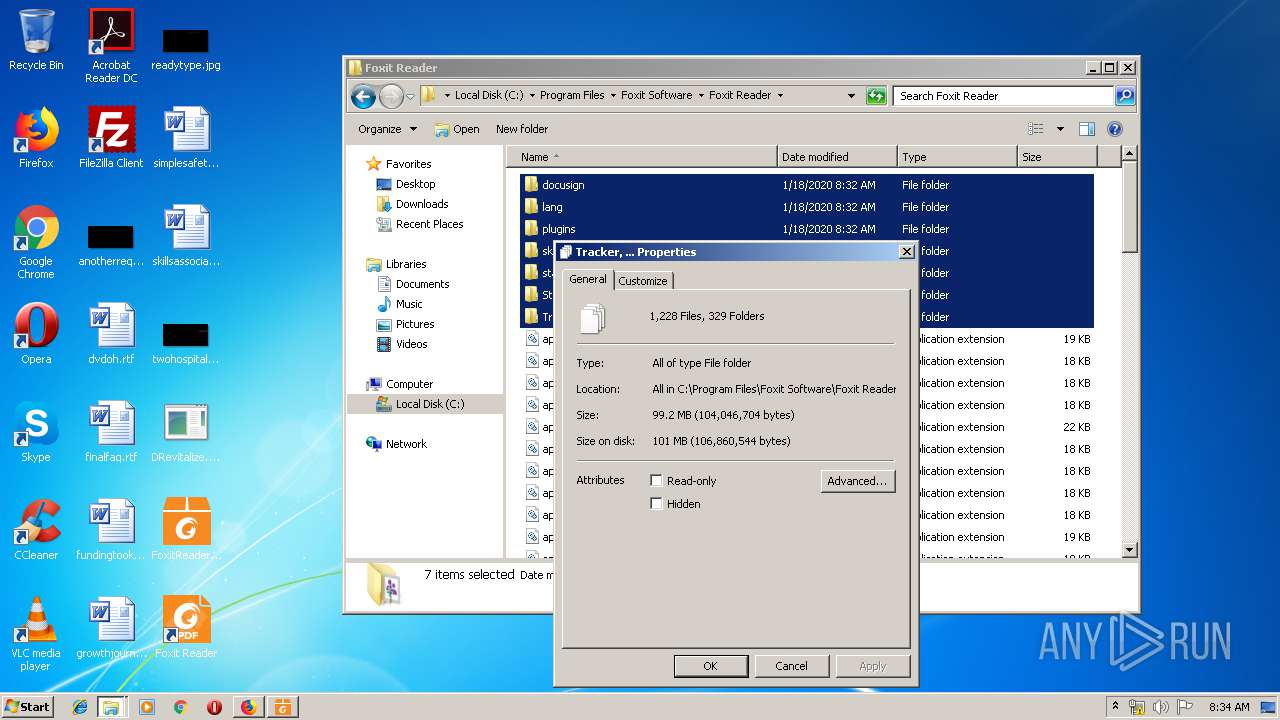
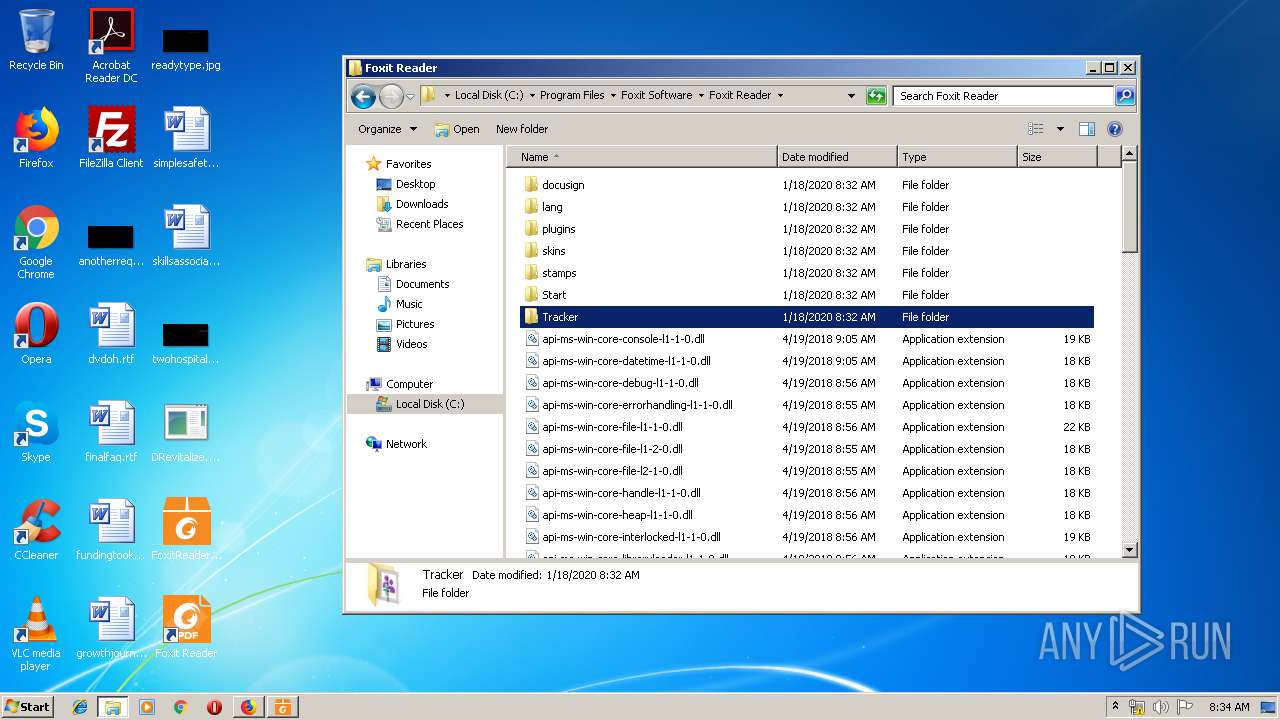
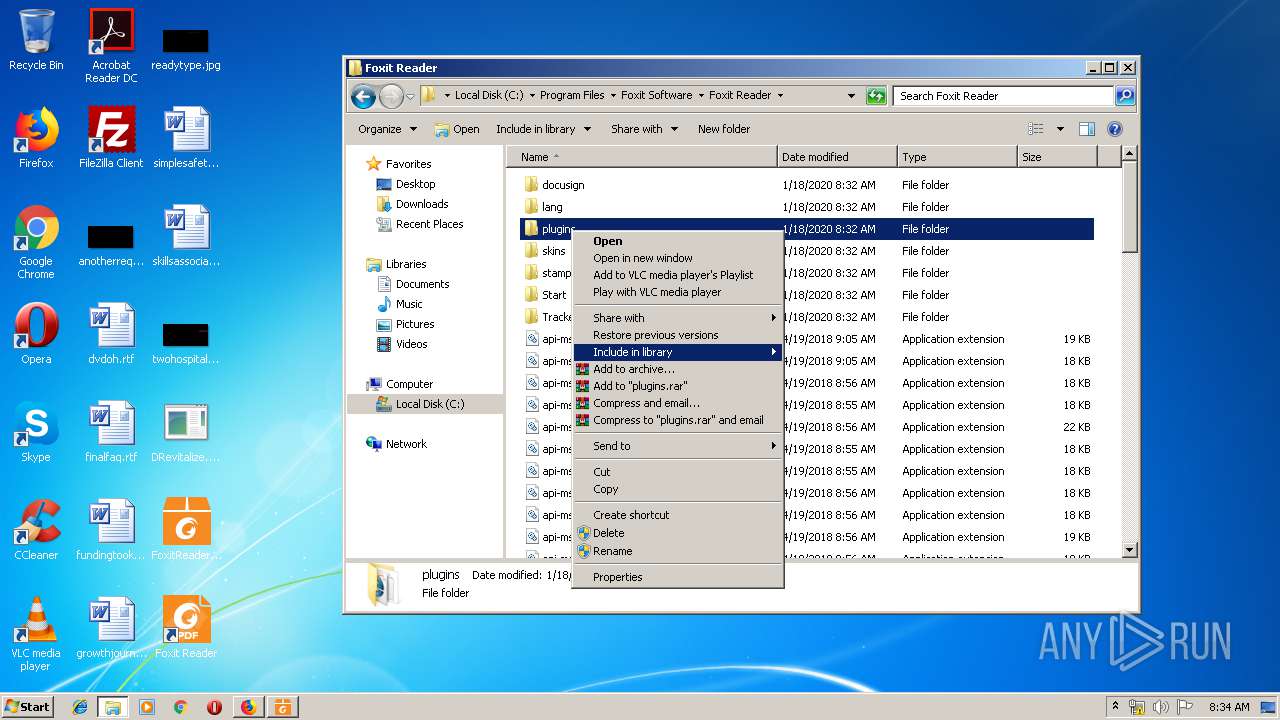
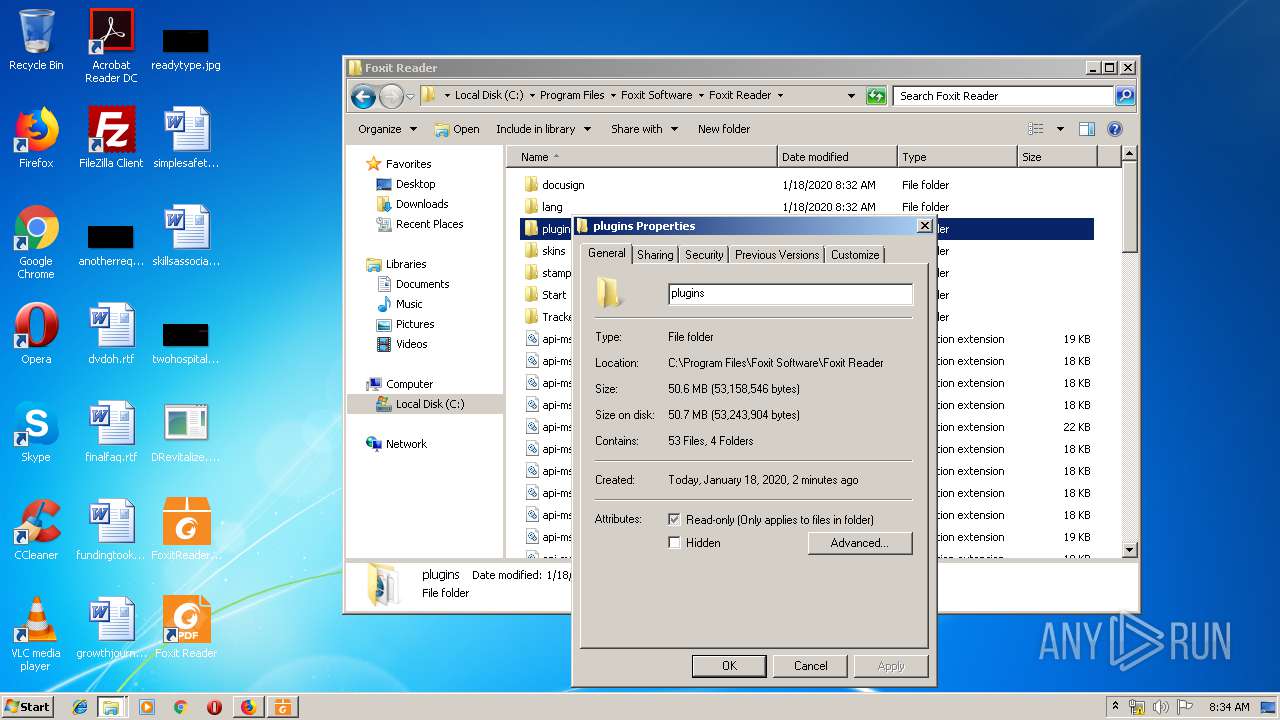
Creates files in the program directory
- FoxitReader971_L10N_Setup_Prom.tmp (PID: 2200)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.3) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:11:14 18:55:30+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 512 |
| InitializedDataSize: | 512 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Nov-2017 17:55:30 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 2 |
| Time date stamp: | 14-Nov-2017 17:55:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000000E2 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 2.36734 |
.data | 0x00002000 | 0x000001CA | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.475 |
Imports
kernel32.dll |
user32.dll |
Total processes
74
Monitored processes
23
Malicious processes
12
Suspicious processes
1
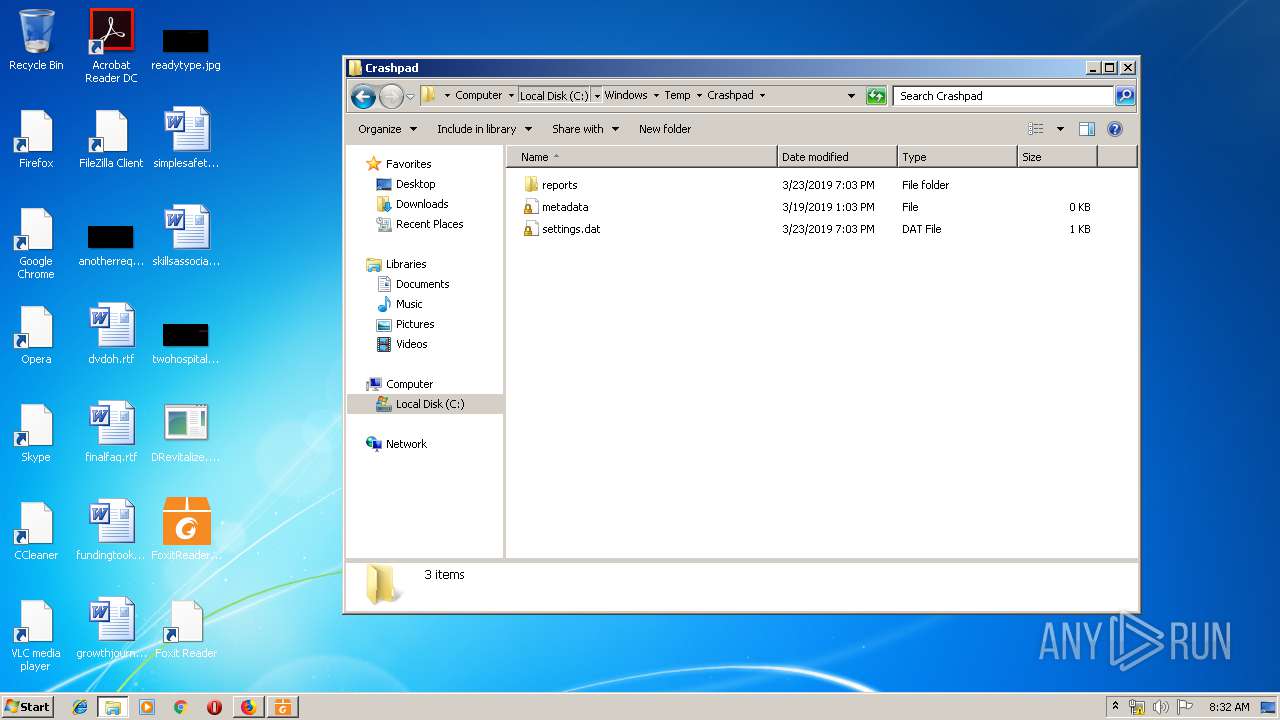
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 592 | "C:\Users\admin\Desktop\DRevitalize.exe" | C:\Users\admin\Desktop\DRevitalize.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Foxit Software\Foxit Reader\FoxitReader.exe" /register | C:\Program Files\Foxit Software\Foxit Reader\FoxitReader.exe | — | FoxitReader971_L10N_Setup_Prom.tmp | |||||||||||
User: admin Company: Foxit Software Inc. Integrity Level: HIGH Description: Foxit Reader 9.7 Exit code: 0 Version: 9.7.1.29511 Modules
| |||||||||||||||
| 1316 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1956.0.41305597\317599886" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1956 "\\.\pipe\gecko-crash-server-pipe.1956" 1168 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1412 | "C:\Users\admin\AppData\Local\Temp\is-NF5FS.tmp\CountInstallation.exe" /version 9.7.1.29511 /green 0 /appname "Foxit Reader" /productid 1 /ReaderLang en_us /AgentName "Foxit Reader(bundle PhantomStd)" /AgencyID 90 /isPhantom 0 /newuser 1 /updaterinstall Website /uninstall 0 | C:\Users\admin\AppData\Local\Temp\is-NF5FS.tmp\CountInstallation.exe | FoxitReader971_L10N_Setup_Prom.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 9.0.0.505 Modules
| |||||||||||||||
| 1708 | "C:\Users\admin\AppData\Local\Temp\is-RTF2H.tmp\FoxitReader971_L10N_Setup_Prom.tmp" /SL5="$701DA,109679116,421376,C:\Users\admin\Desktop\FoxitReader971_L10N_Setup_Prom.exe" | C:\Users\admin\AppData\Local\Temp\is-RTF2H.tmp\FoxitReader971_L10N_Setup_Prom.tmp | — | FoxitReader971_L10N_Setup_Prom.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
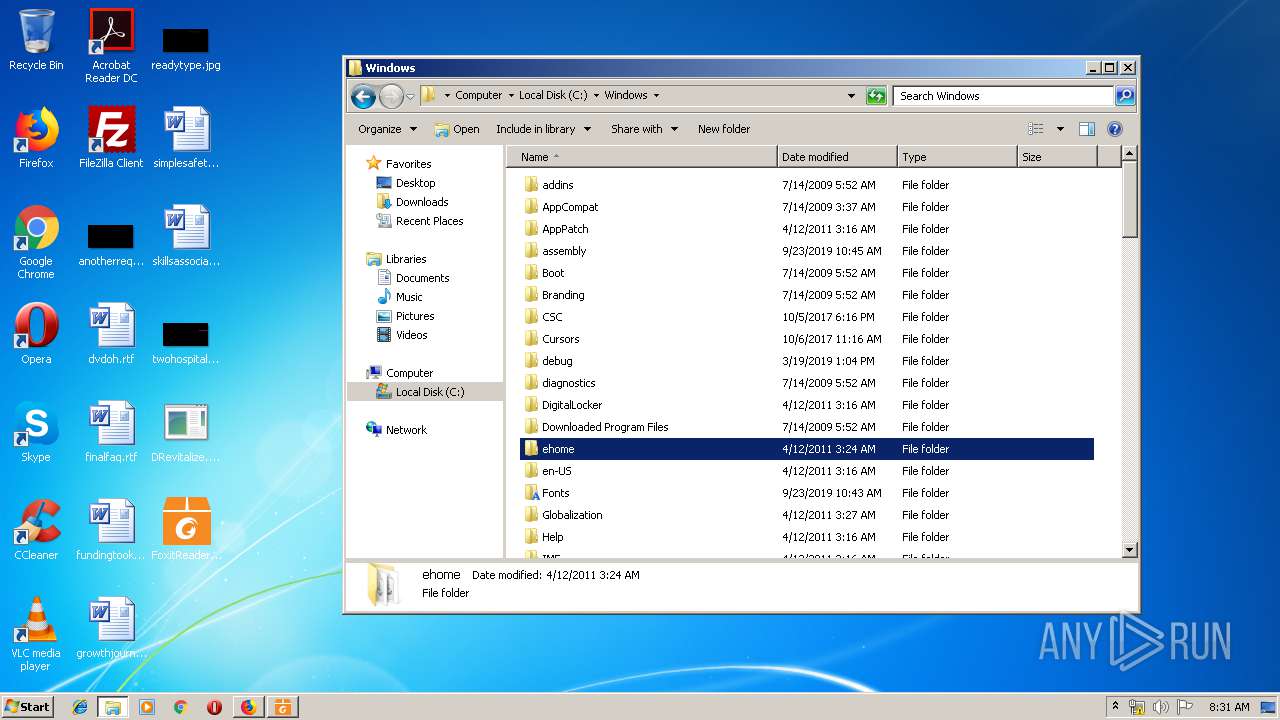
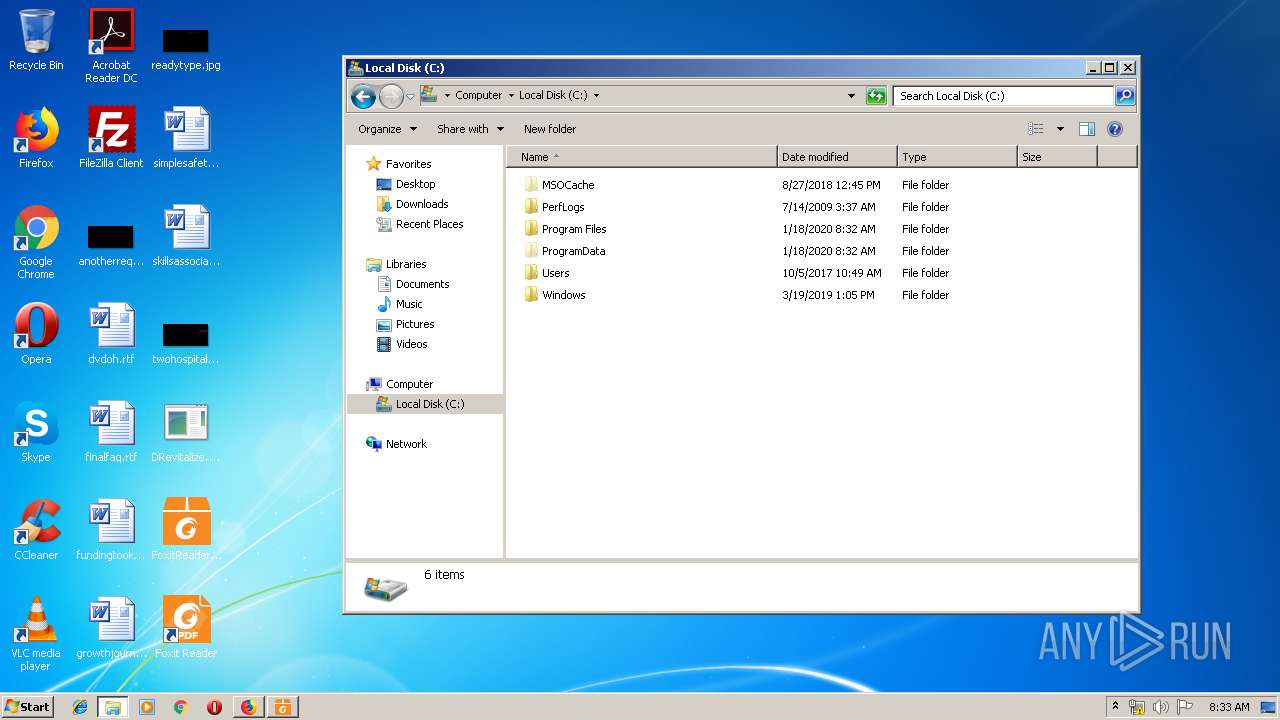
| 1904 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1916 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1940 | "C:\Windows\System32\regsvr32.exe" -s "C:\\Program Files\\Foxit Software\\Foxit Reader\\Shell Extensions\\FoxitPrevHndlr.dll" | C:\Windows\System32\regsvr32.exe | — | FoxitReader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1956 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
Total events
2 759
Read events
2 016
Write events
659
Delete events
84
Modification events
| (PID) Process: | (1916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (1916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {BC830A3F-39CC-11EA-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (1916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (1916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (1916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E40701000600120008001E0009008A03 | |||
Executable files
85
Suspicious files
217
Text files
1 812
Unknown types
76
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1916 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\D89EQNTJ\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\0G5YO6YK\jquery.bxslider[1].css | text | |
MD5:— | SHA256:— | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\D89EQNTJ\jquery-ui-1.8.21.custom[1].css | text | |
MD5:— | SHA256:— | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\D89EQNTJ\troubleTicket[1].css | text | |
MD5:— | SHA256:— | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\ZXOQXJVX\new[1].css | text | |
MD5:— | SHA256:— | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\TDRYHRER\jquery.mCustomScrollbar[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
47
DNS requests
86
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
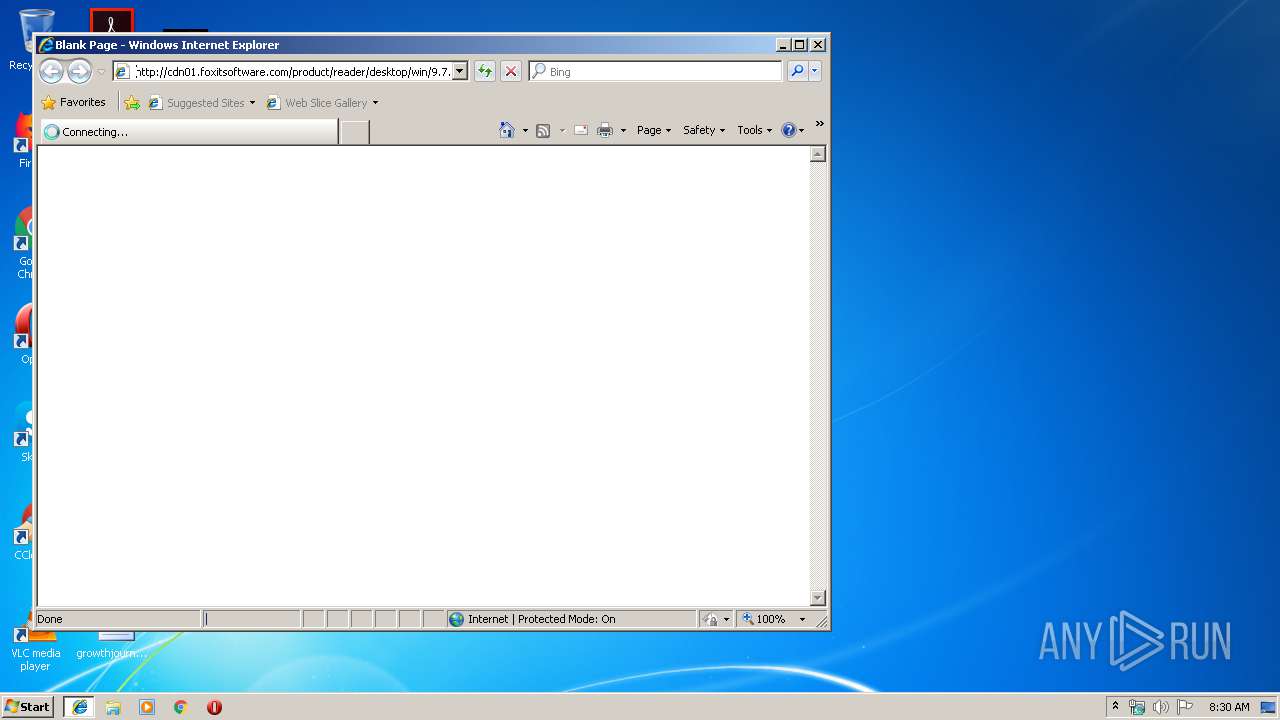
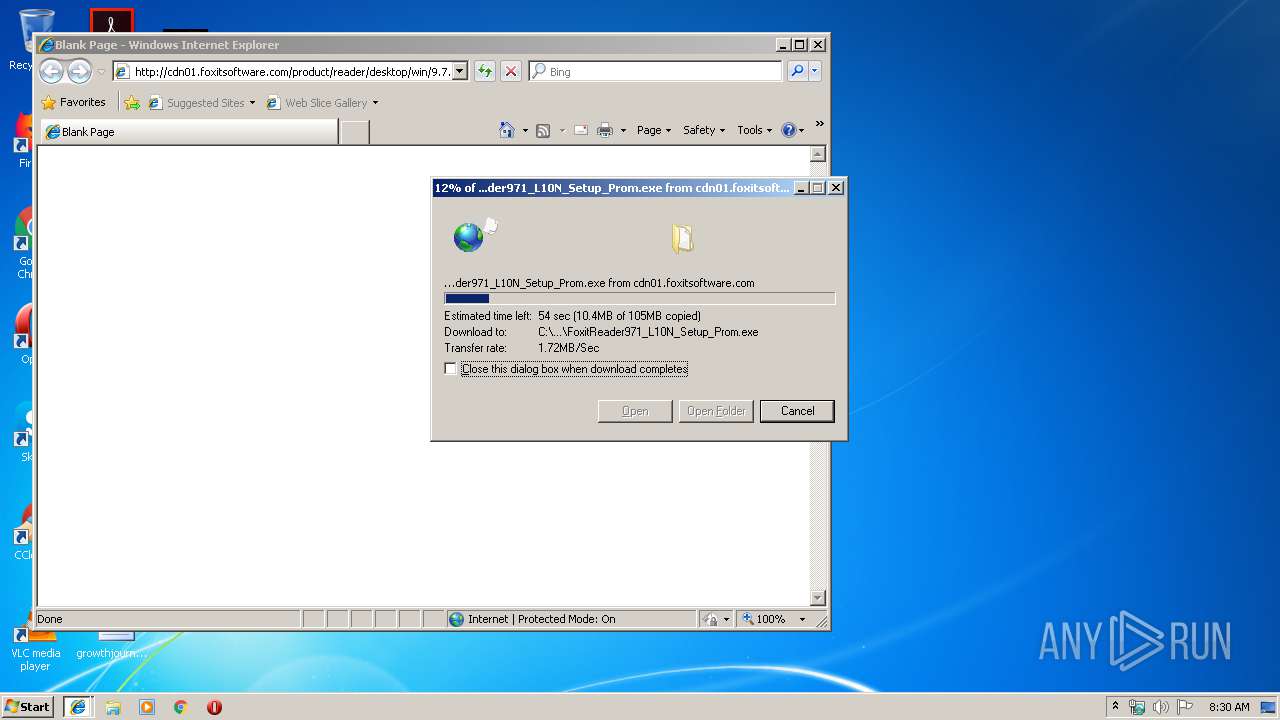
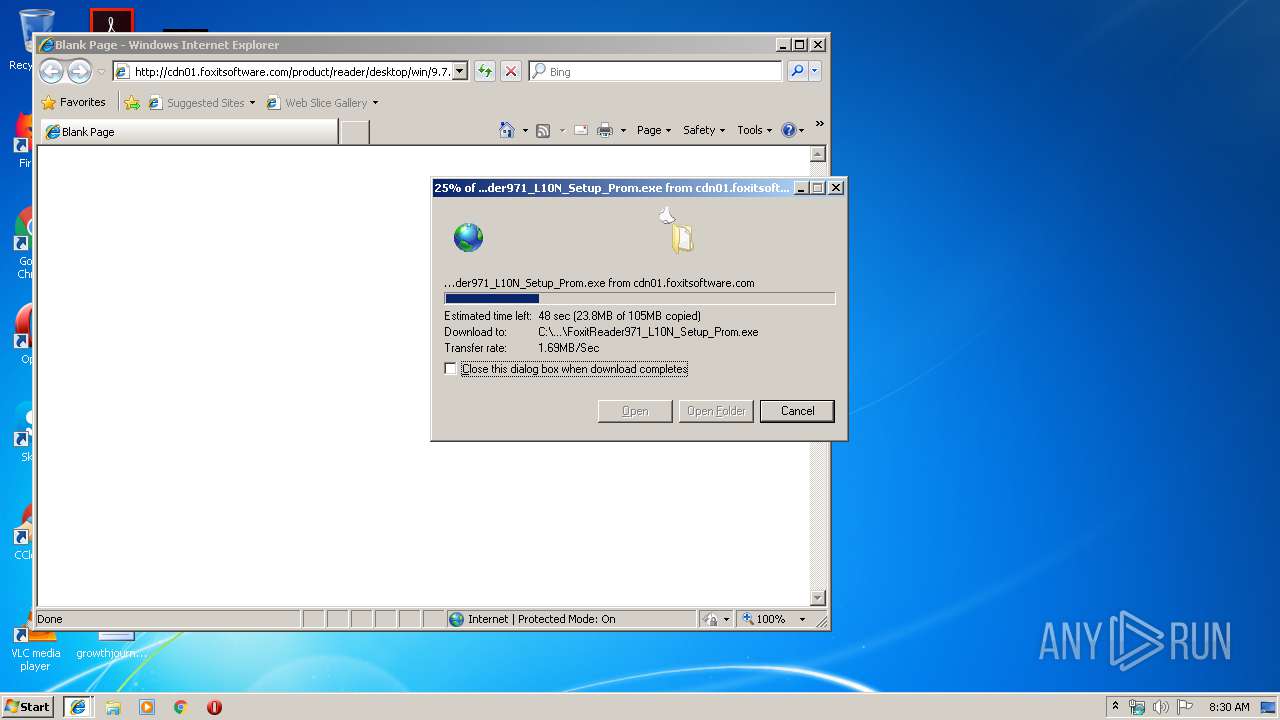
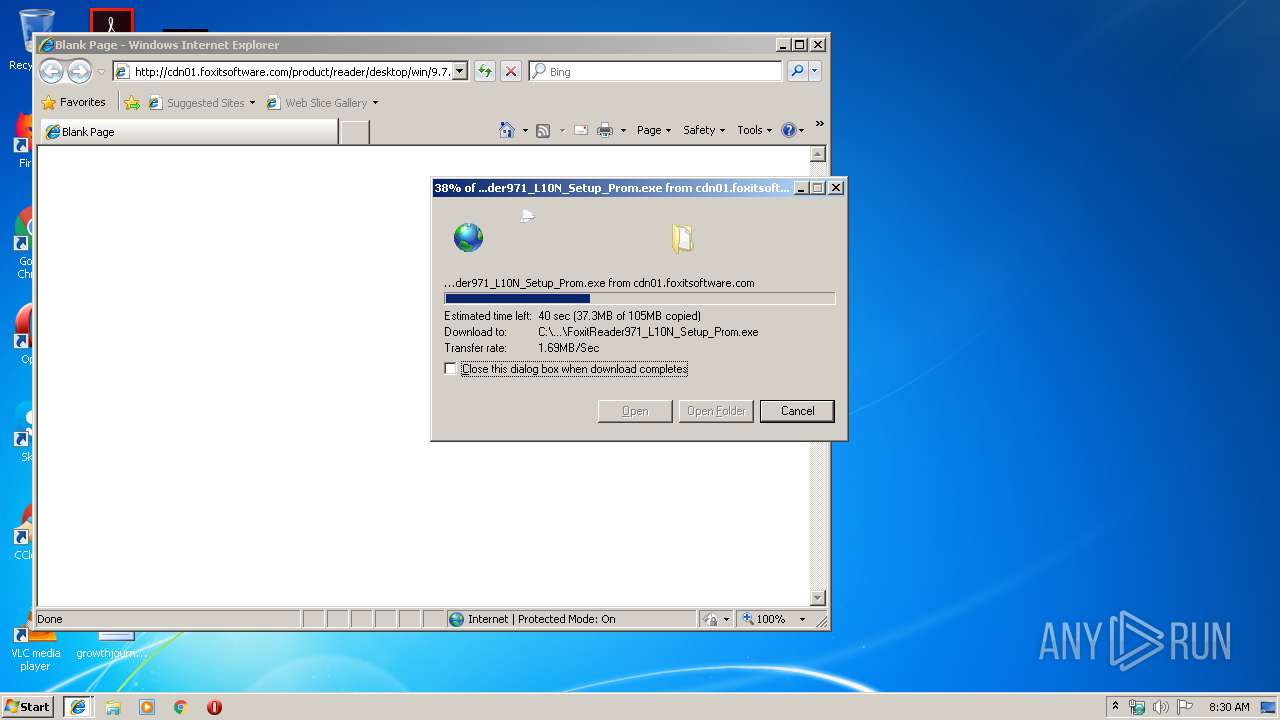
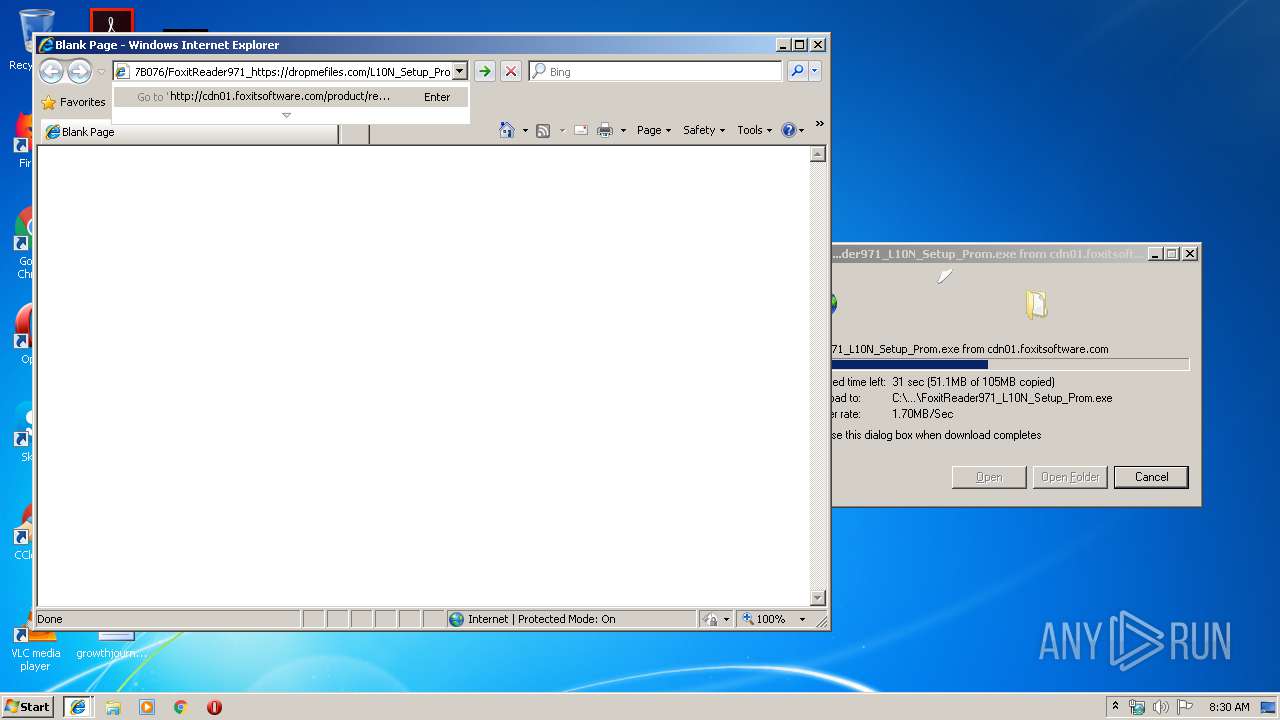
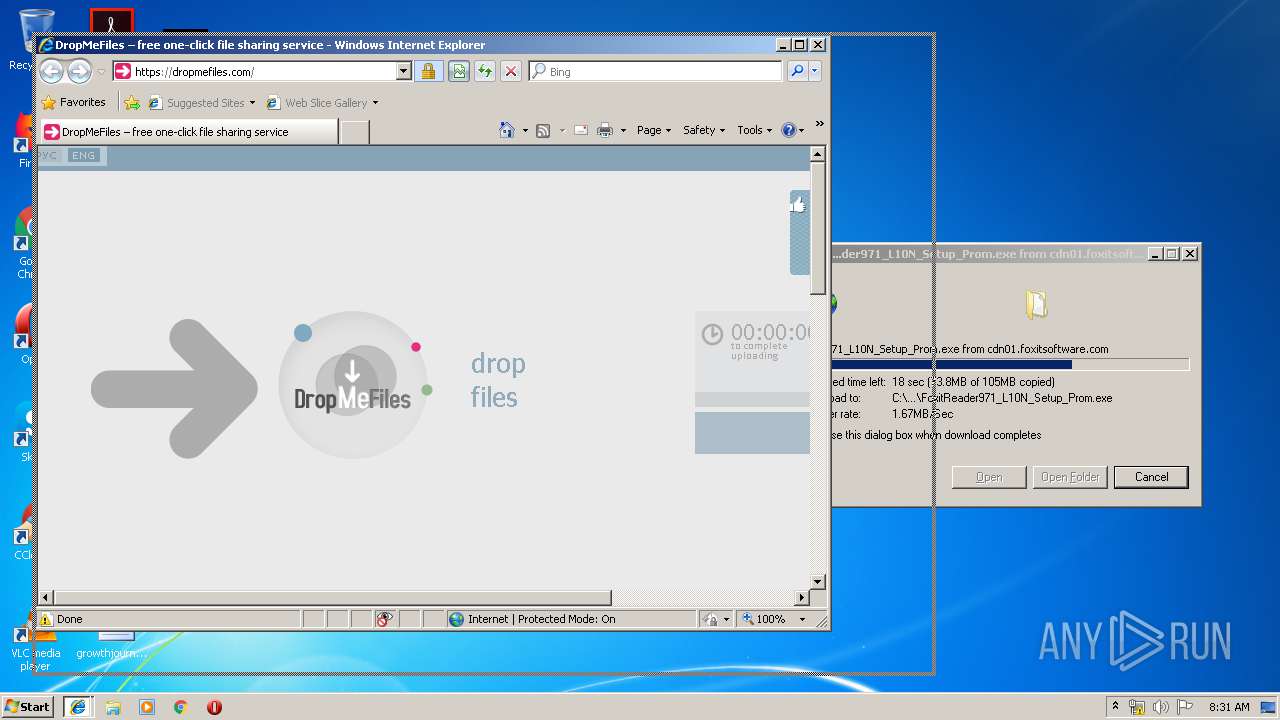
3176 | iexplore.exe | GET | — | 64.62.194.28:80 | http://cdn01.foxitsoftware.com/product/reader/desktop/win/9.7.1/C3DE0FFDF926B5E670543028BF47B076/FoxitReader971_L10N_Setup_Prom.exe | US | — | — | suspicious |
1956 | firefox.exe | POST | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
1956 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1956 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://status.rapidssl.com/ | US | der | 471 b | shared |
1956 | firefox.exe | POST | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
1956 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://status.rapidssl.com/ | US | der | 471 b | shared |
1956 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1956 | firefox.exe | POST | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
1956 | firefox.exe | GET | 200 | 2.16.186.50:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
1956 | firefox.exe | POST | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1916 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
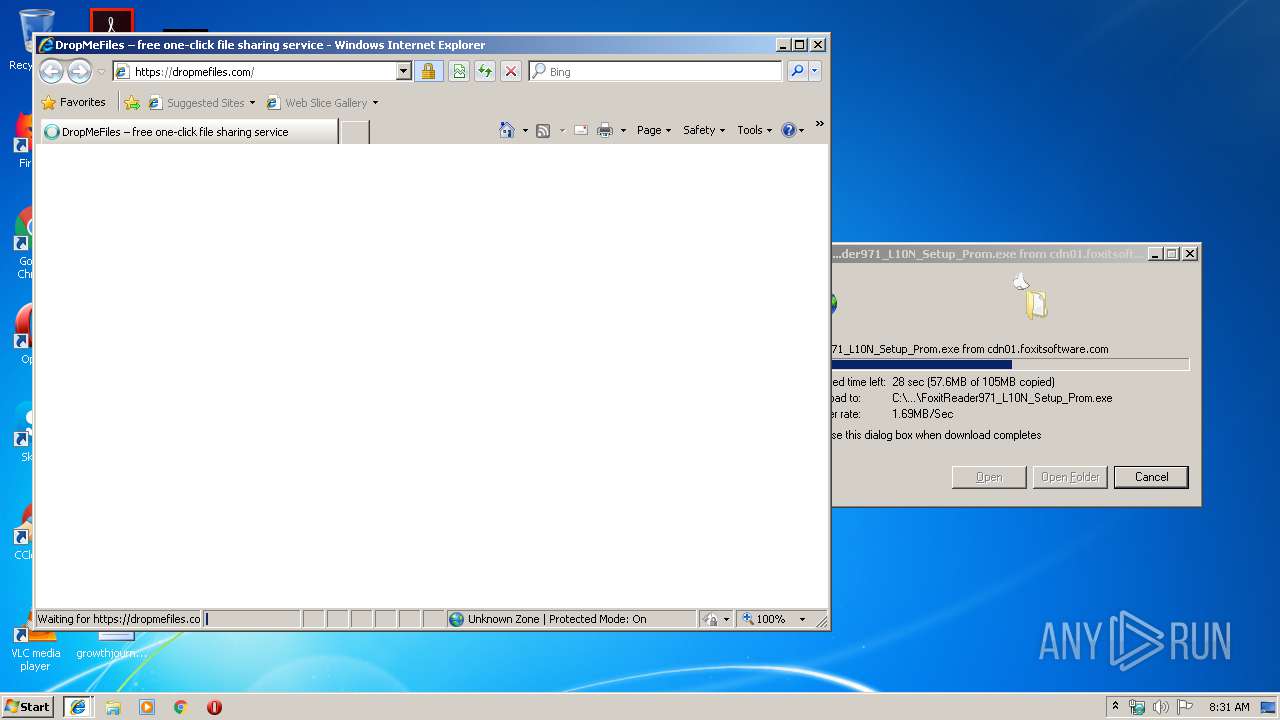
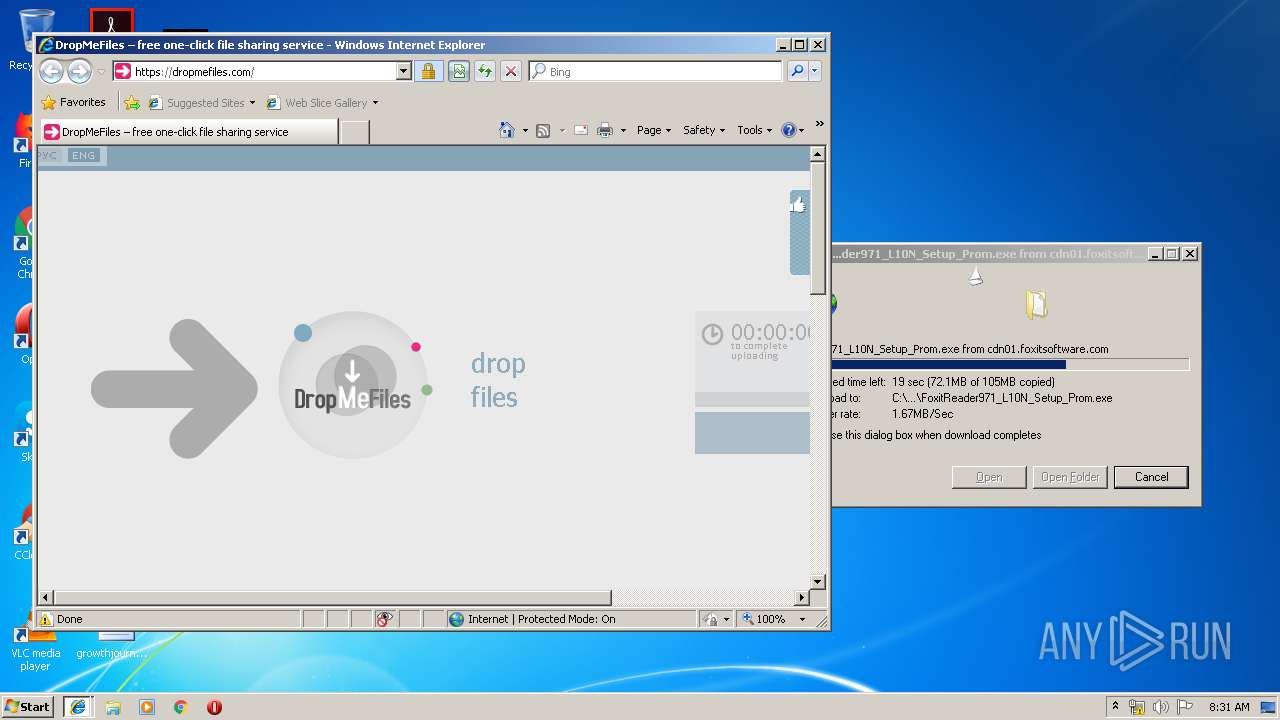
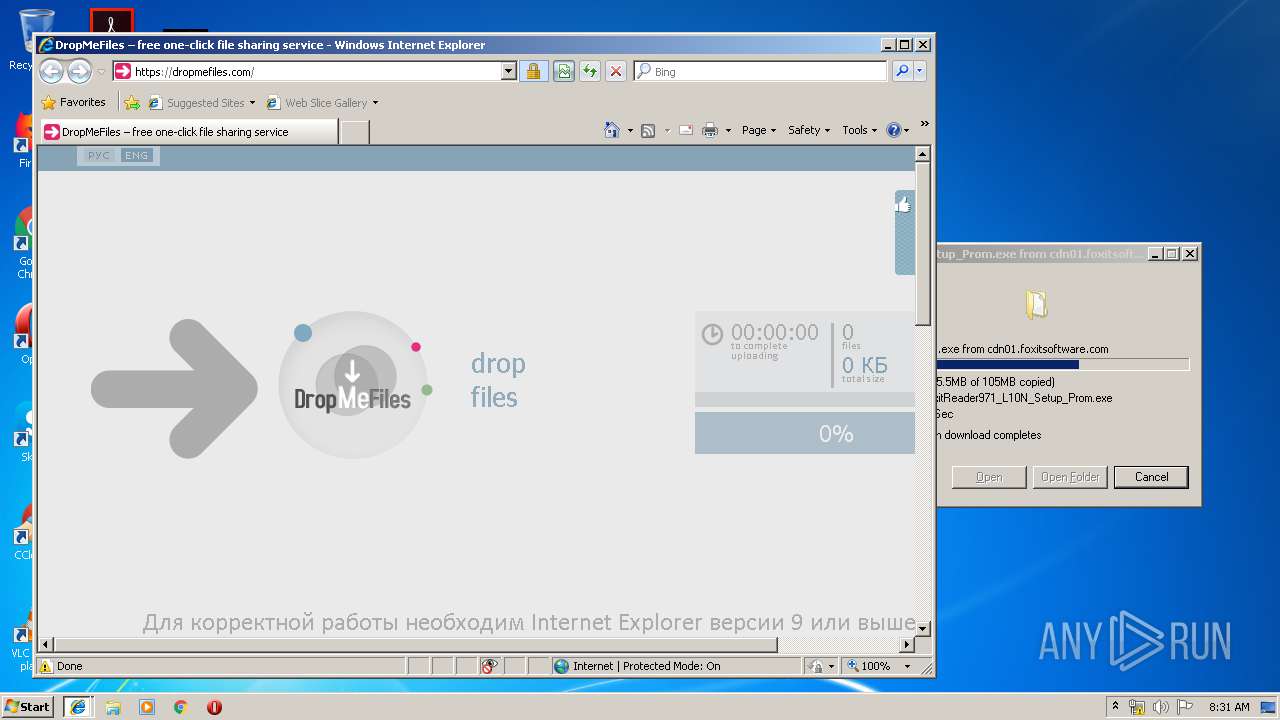
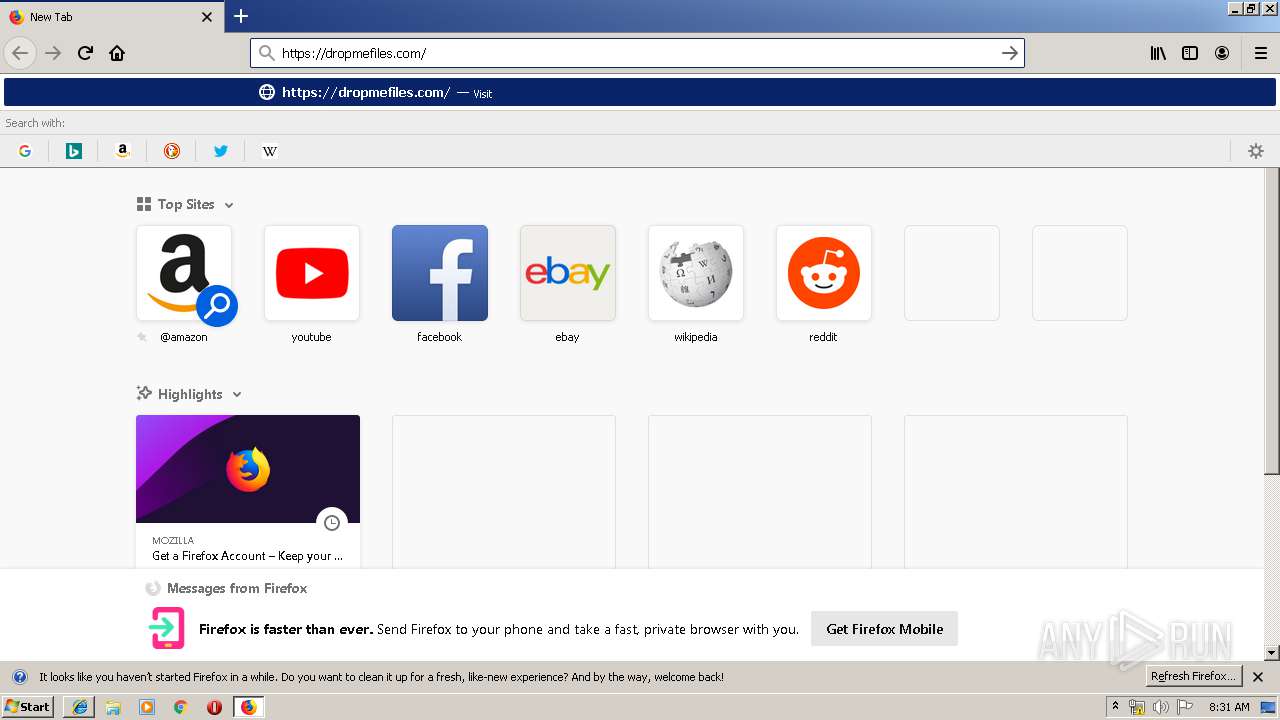
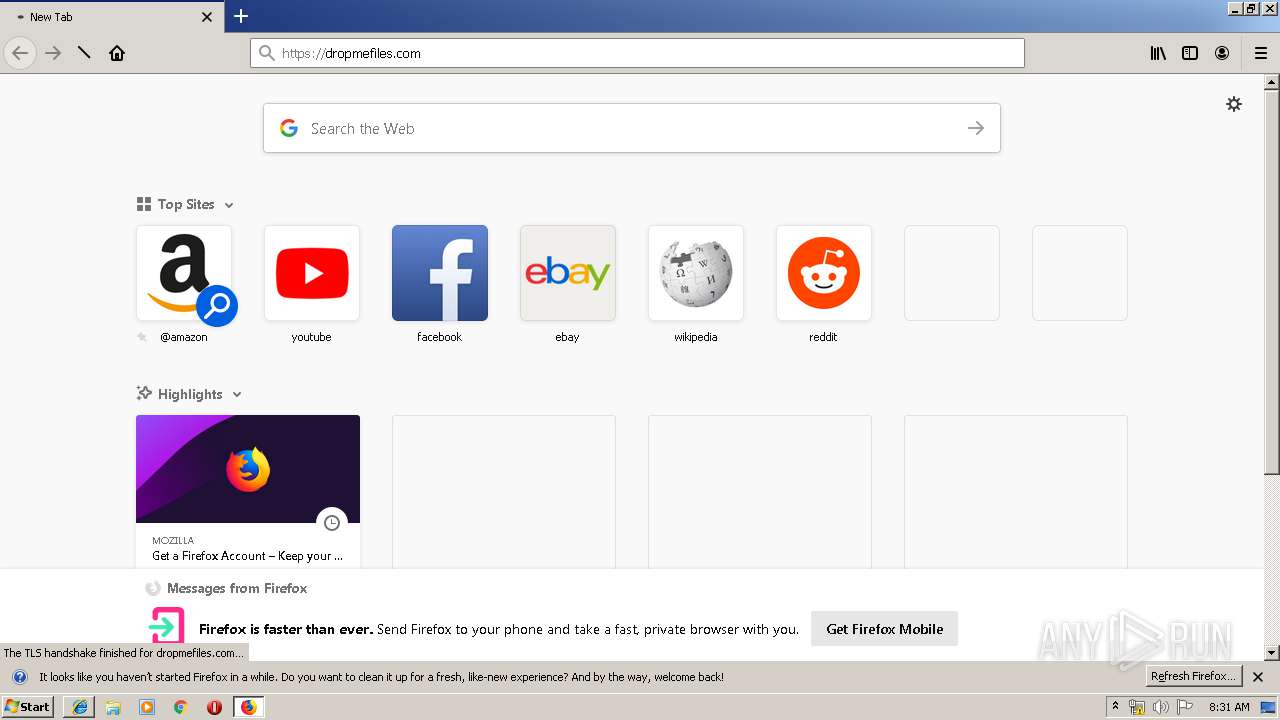
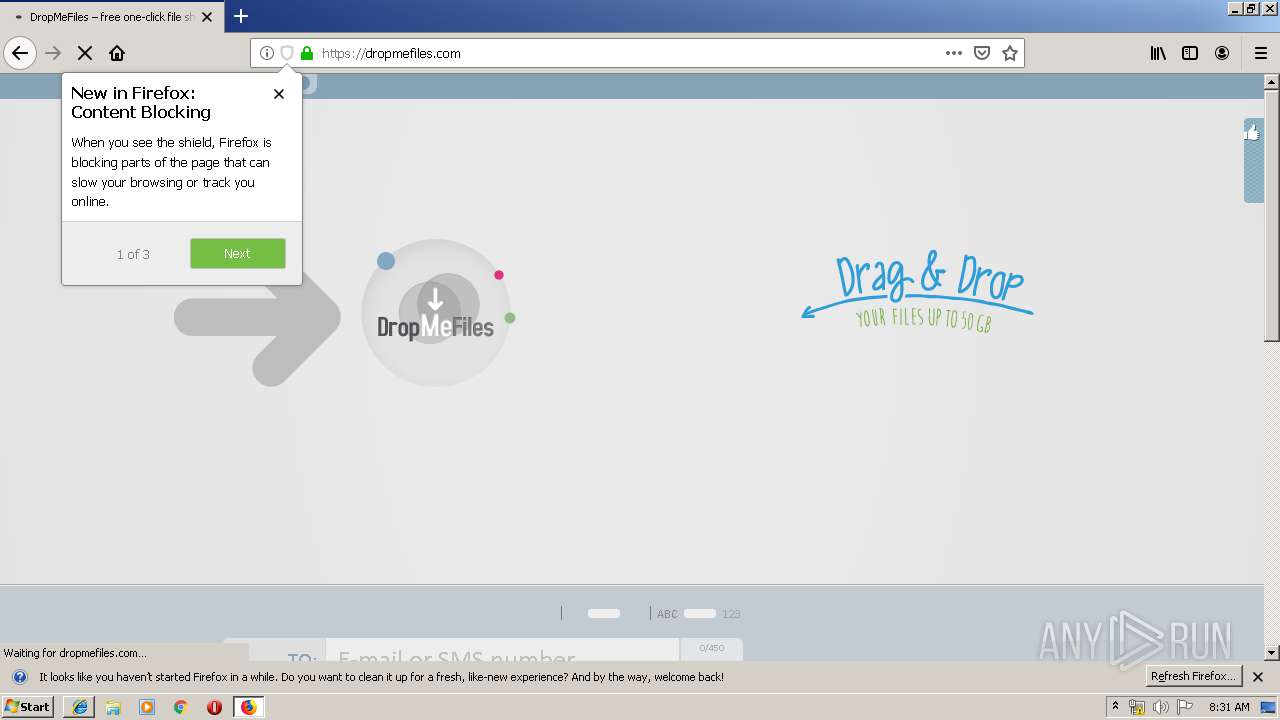
3176 | iexplore.exe | 176.99.128.18:443 | dropmefiles.com | Inetcom LLC | RU | suspicious |
3176 | iexplore.exe | 64.62.194.28:80 | cdn01.foxitsoftware.com | Hurricane Electric, Inc. | US | suspicious |
3176 | iexplore.exe | 216.58.208.34:443 | www.googletagservices.com | Google Inc. | US | whitelisted |
3176 | iexplore.exe | 93.158.134.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
3176 | iexplore.exe | 172.217.18.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3176 | iexplore.exe | 74.125.206.156:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
1916 | iexplore.exe | 176.99.128.18:443 | dropmefiles.com | Inetcom LLC | RU | suspicious |
1956 | firefox.exe | 52.222.174.80:443 | snippets.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
1956 | firefox.exe | 52.222.174.189:443 | firefox.settings.services.mozilla.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
cdn01.foxitsoftware.com |
| suspicious |
dropmefiles.com |
| whitelisted |
www.googletagservices.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
mc.yandex.ru |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3176 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |