| File name: | gcapi.dll |
| Full analysis: | https://app.any.run/tasks/a83c2ac9-36c4-4f27-8c04-5c04009afccb |
| Verdict: | Malicious activity |
| Analysis date: | May 22, 2024, 19:37:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (console) Intel 80386, for MS Windows |
| MD5: | 1CE7D5A1566C8C449D0F6772A8C27900 |
| SHA1: | 60854185F6338E1BFC7497FD41AA44C5C00D8F85 |
| SHA256: | 73170761D6776C0DEBACFBBC61B6988CB8270A20174BF5C049768A264BB8FFAF |
| SSDEEP: | 6144:Tv/ioKdMF+LZD/ZRj1vwWrrUFMNoz4pFGxjEB1NYAOrabN2GZvFcD77:Td+LZrNwWrrwMNoz4vG1OYZabtK77 |
MALICIOUS
Drops the executable file immediately after the start
- rundll32.exe (PID: 3968)
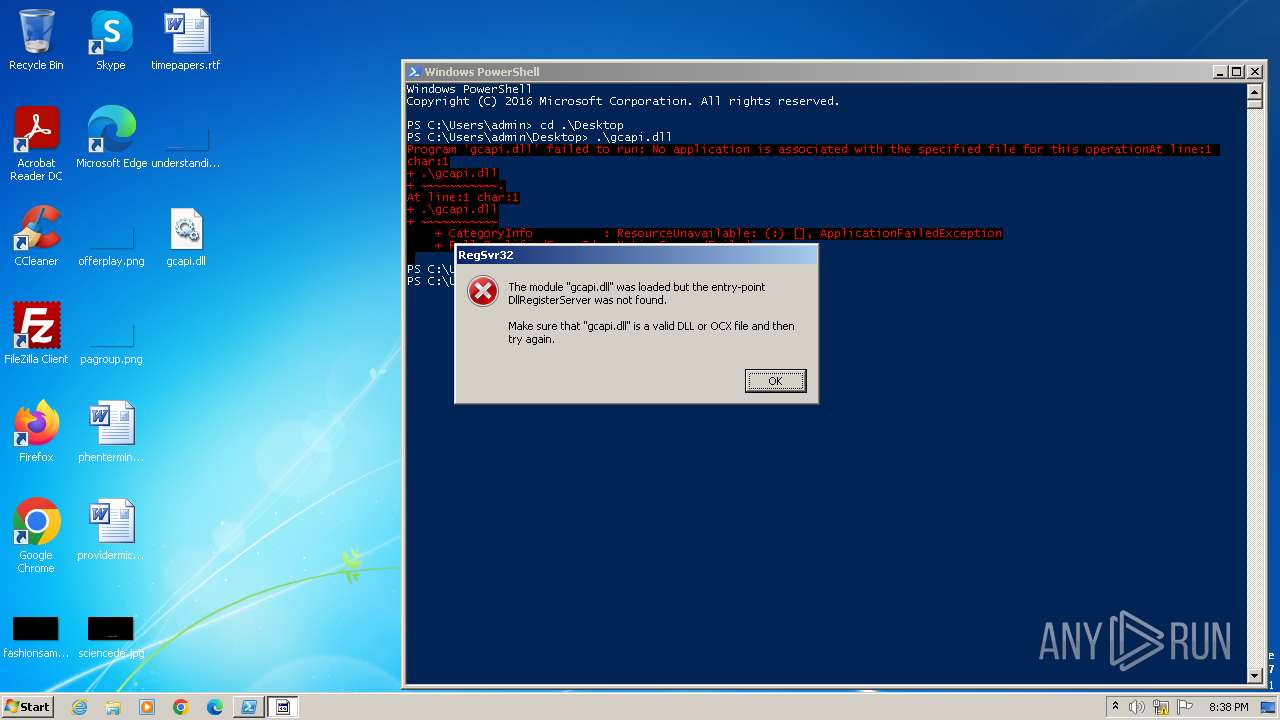
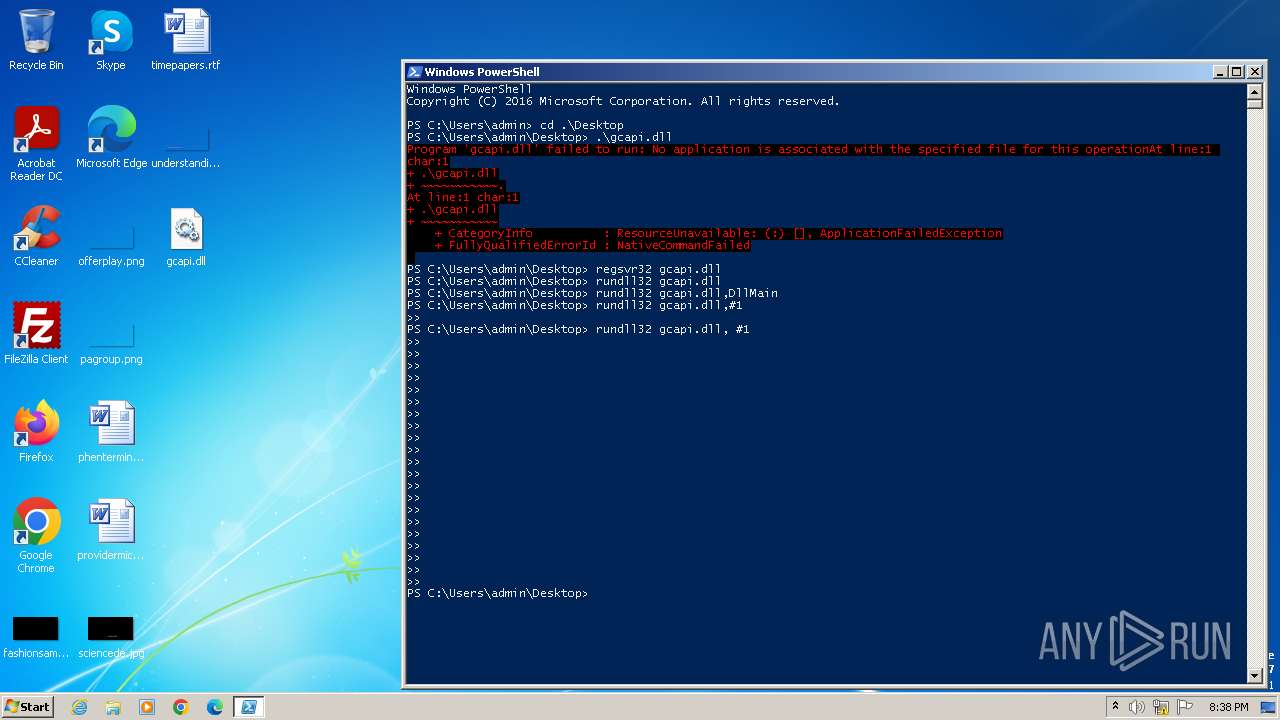
Registers / Runs the DLL via REGSVR32.EXE
- powershell.exe (PID: 4024)
SUSPICIOUS
Using PowerShell to operate with local accounts
- powershell.exe (PID: 4024)
Reads the Internet Settings
- powershell.exe (PID: 4024)
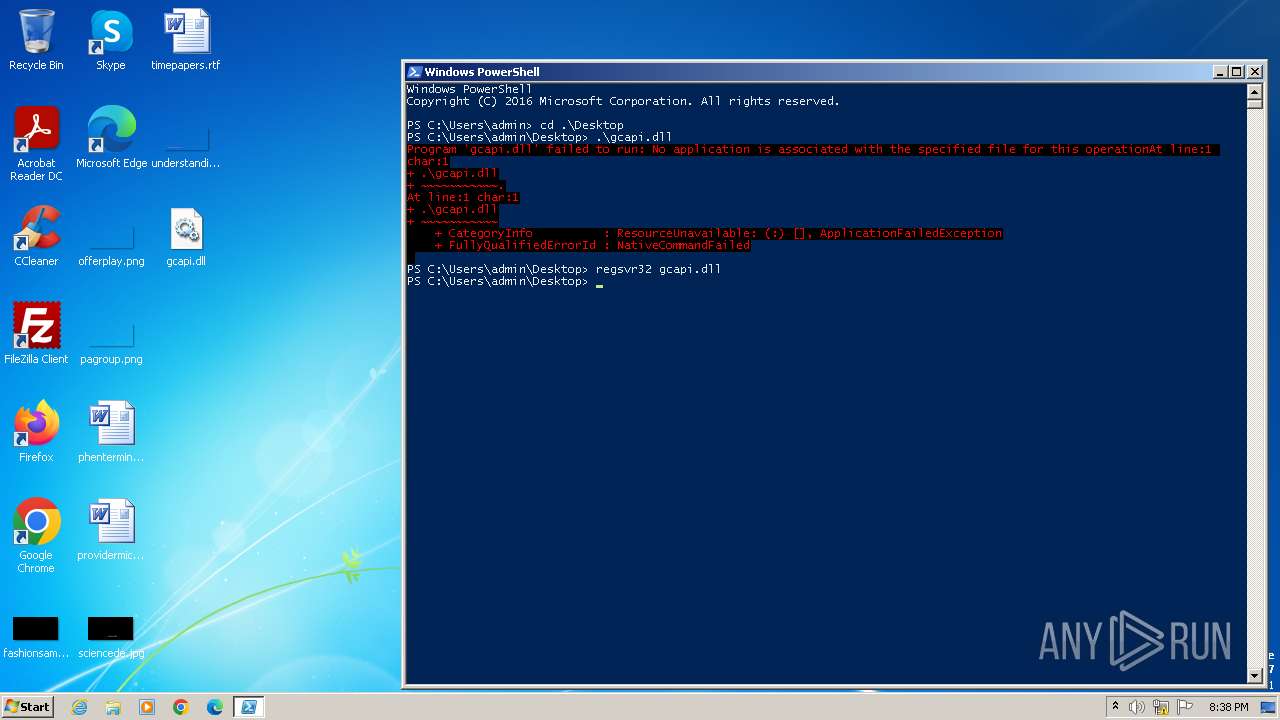
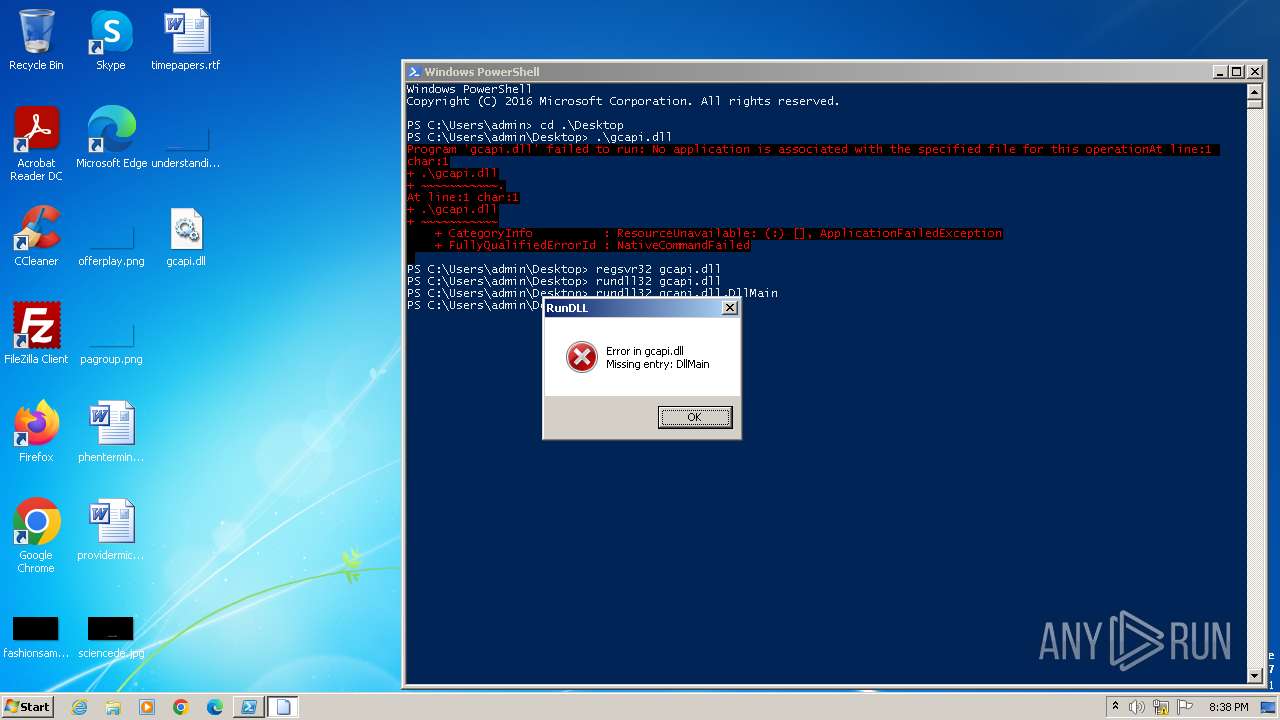
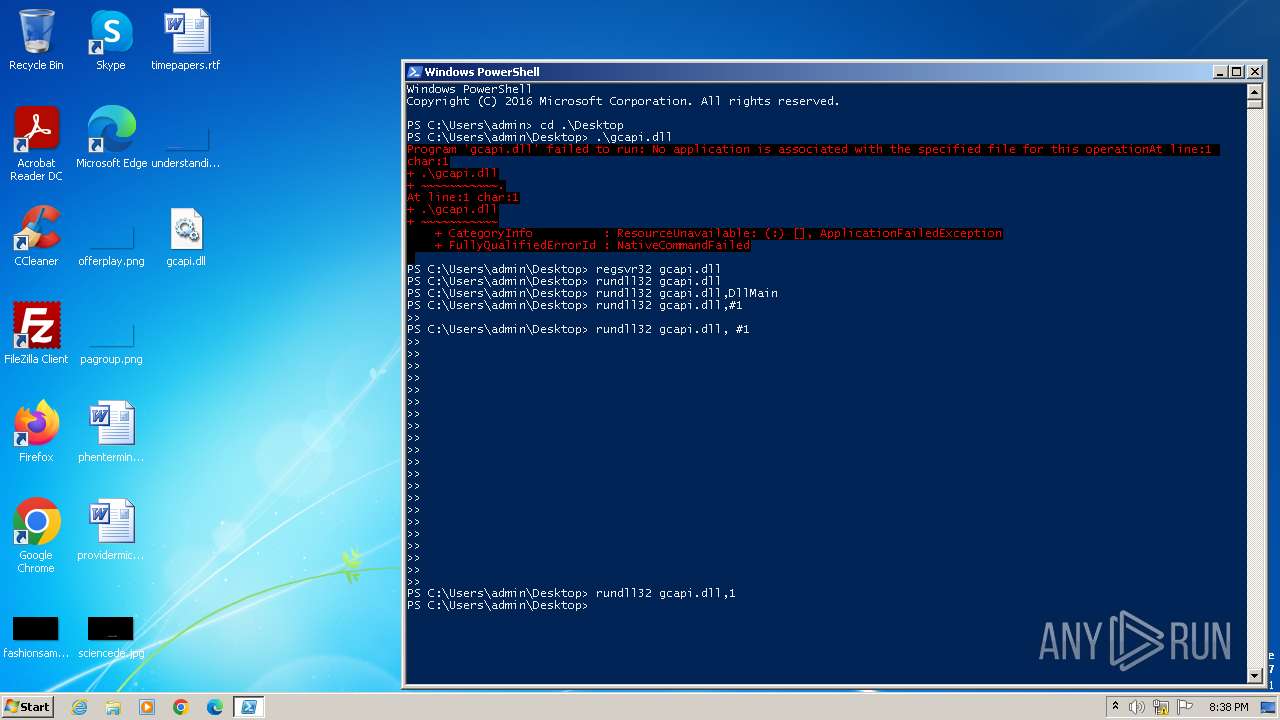
Uses RUNDLL32.EXE to load library
- powershell.exe (PID: 4024)
INFO
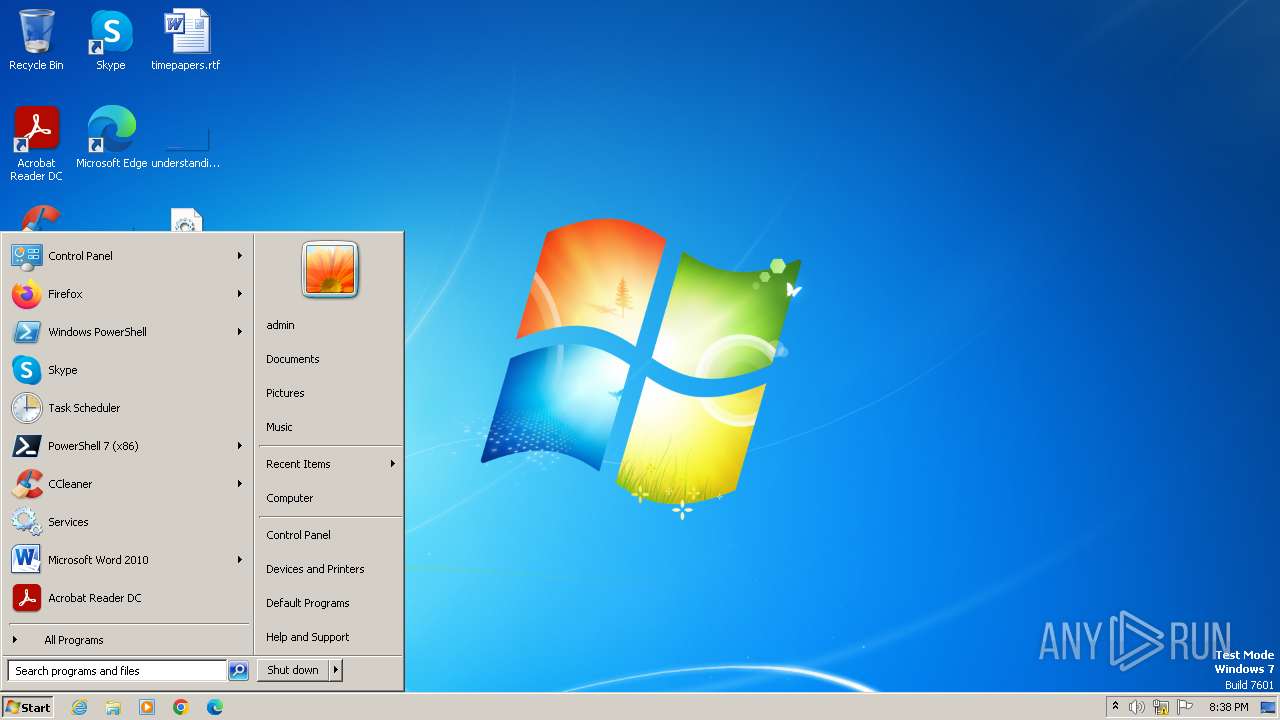
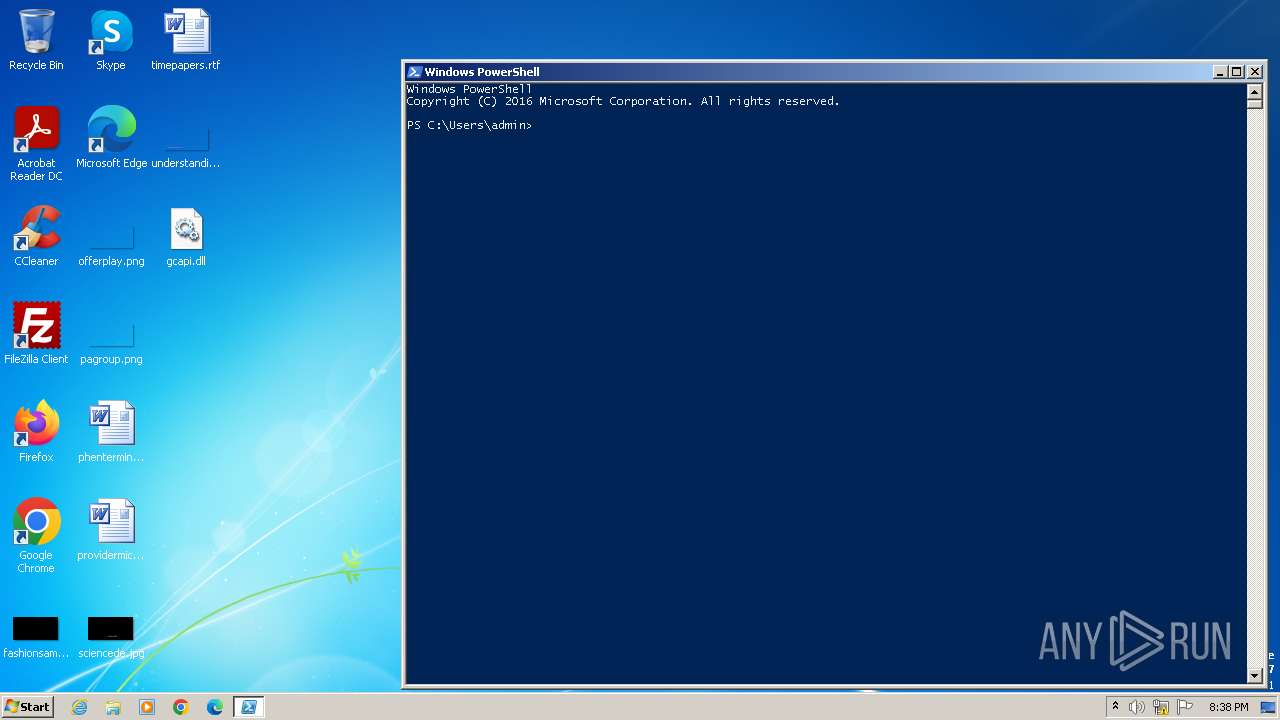
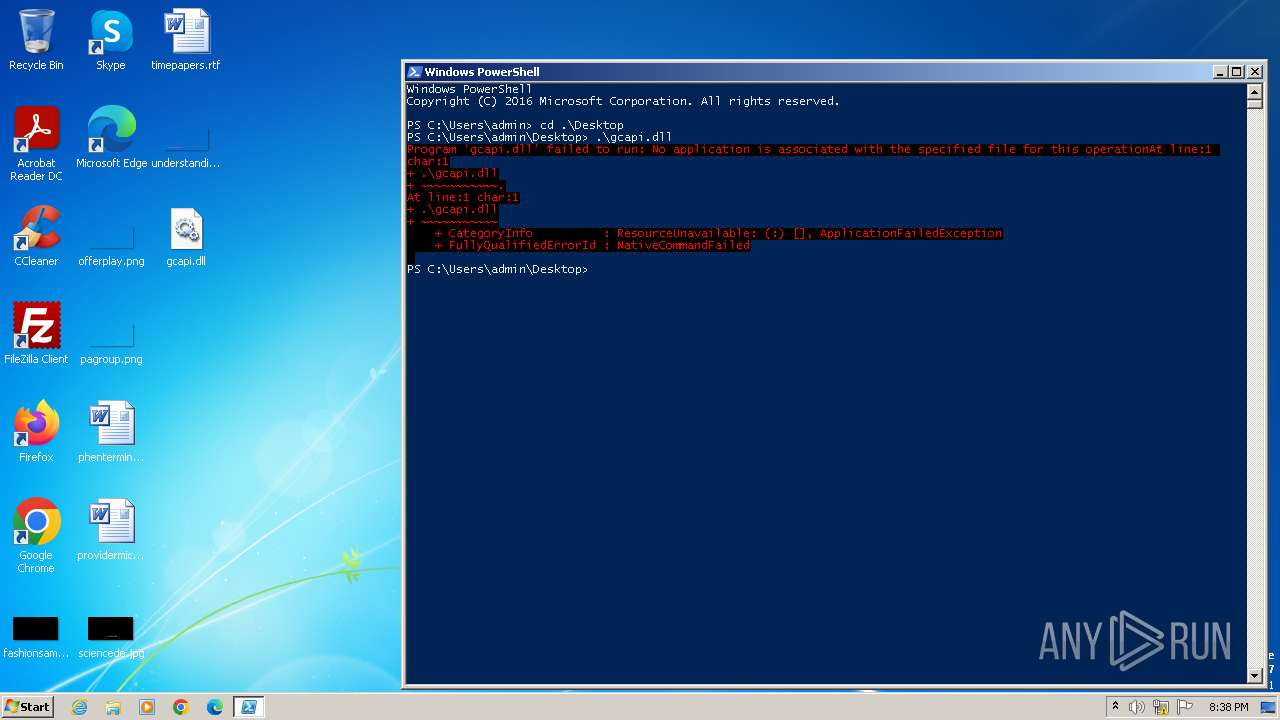
Manual execution by a user
- powershell.exe (PID: 4024)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4024)
Checks current location (POWERSHELL)
- powershell.exe (PID: 4024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:08:01 20:14:23+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit, DLL |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 295424 |
| InitializedDataSize: | 107520 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x20c3a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 52.0.2743.114 |
| ProductVersionNumber: | 52.0.2743.114 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Google Inc. |
| FileDescription: | gcapi |
| FileVersion: | 52.0.2743.114 |
| InternalName: | gcapi |
| LegalCopyright: | Copyright 2016 Google Inc. All rights reserved. |
| ProductName: | gcapi |
| ProductVersion: | 52.0.2743.114 |
| CompanyShortName: | |
| ProductShortName: | gcapi |
| LastChange: | 97a0f09bd385a340fe5c6509ccd3e3c2f358181e-refs/branch-heads/2743@{#720} |
| OfficialBuild: | 1 |
Total processes
39
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 748 | "C:\Windows\system32\regsvr32.exe" gcapi.dll | C:\Windows\System32\regsvr32.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 4 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1112 | "C:\Windows\system32\rundll32.exe" gcapi.dll,1 | C:\Windows\System32\rundll32.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1872 | "C:\Windows\system32\rundll32.exe" gcapi.dll,DllMain | C:\Windows\System32\rundll32.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2036 | "C:\Windows\system32\rundll32.exe" gcapi.dll | C:\Windows\System32\rundll32.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3968 | "C:\Windows\System32\rundll32.exe" C:\Users\admin\Desktop\gcapi.dll, #1 | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4024 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
2 945
Read events
2 885
Write events
60
Delete events
0
Modification events
| (PID) Process: | (4024) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4024) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4024) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4024) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4024) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
6
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4024 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ERUG6PR1XLT0BBWKNJ40.temp | binary | |
MD5:DEA0DE52DFF2E328551A6BB67224CBDF | SHA256:5CF19C8374CF57F136F1E098E2FBC36D50B68B98FAE0A0D173BBA9634C77C9B7 | |||
| 4024 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:DEA0DE52DFF2E328551A6BB67224CBDF | SHA256:5CF19C8374CF57F136F1E098E2FBC36D50B68B98FAE0A0D173BBA9634C77C9B7 | |||
| 4024 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF104681.TMP | binary | |
MD5:0268C3470C936E6FBAC2945B9E1C2099 | SHA256:DF2AF58E8879B48826D8A418ED3B02CC8D484BCFC231C5B7A11BD153ED3998E9 | |||
| 4024 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:DE3E389E155C6845D43C07185A11ACF1 | SHA256:6761E2D1F087BBAA8A8DB8B1294E66088FDBE0B9B7FC6E43476D8B2ABDB79E56 | |||
| 4024 | powershell.exe | C:\Users\admin\AppData\Local\Temp\jx3b524v.dnt.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:6B86B273FF34FCE19D6B804EFF5A3F5747ADA4EAA22F1D49C01E52DDB7875B4B | |||
| 4024 | powershell.exe | C:\Users\admin\AppData\Local\Temp\u23irplt.sr4.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:6B86B273FF34FCE19D6B804EFF5A3F5747ADA4EAA22F1D49C01E52DDB7875B4B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |