| download: | index.html |
| Full analysis: | https://app.any.run/tasks/b4ae5cdc-50bc-4733-8544-43f5c53f0876 |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2019, 20:30:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators |
| MD5: | 982BCC56E739043CE50B5C2B4FE81CDF |
| SHA1: | 313F51F46A841890B8532F70946BFE954E730414 |
| SHA256: | 730E9D84C645045F3347BA9D3896A2FAC99DA4E820586BA172E5FA639A1360DA |
| SSDEEP: | 192:uilJD0fYmiA4eF3m6Yeh11N8kHsP854NN58unmaNSOAgPOuKXKWInX:XrjeF3msZN8kHsP8SKgmaNSO3YInX |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
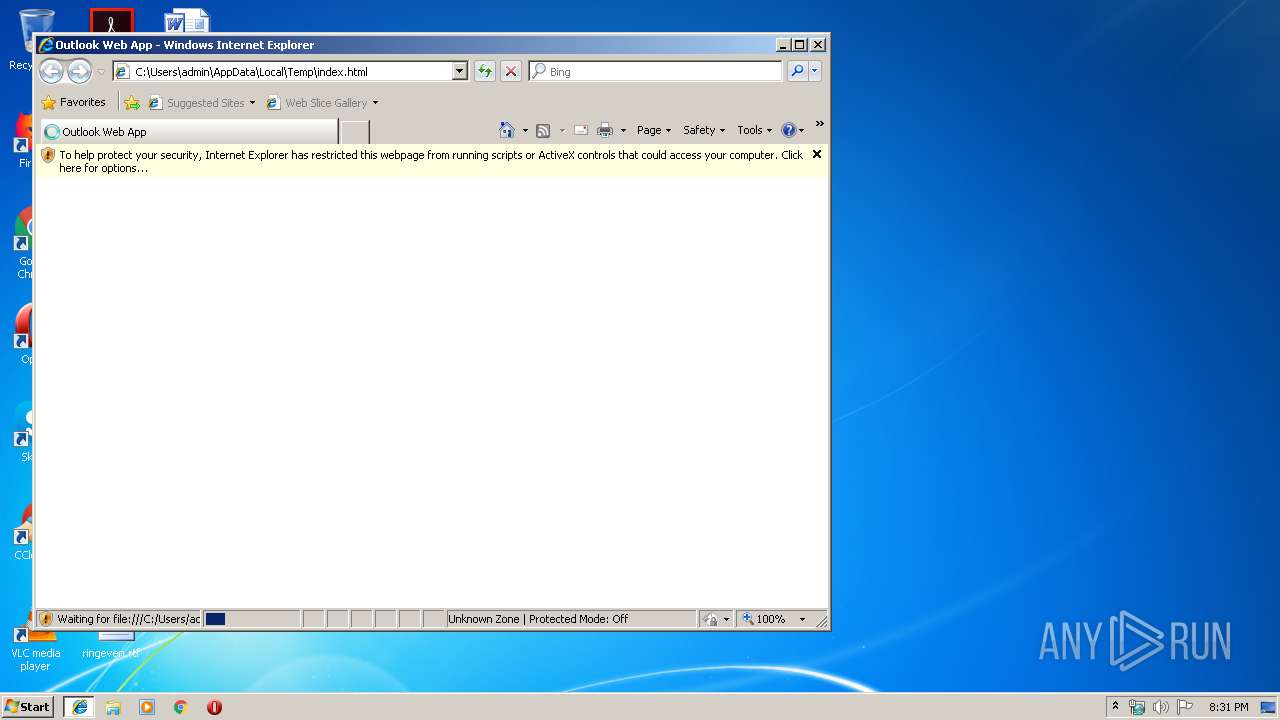
Application launched itself
- iexplore.exe (PID: 2388)
Reads internet explorer settings
- iexplore.exe (PID: 892)
Reads Internet Cache Settings
- iexplore.exe (PID: 892)
Changes internet zones settings
- iexplore.exe (PID: 2388)
Reads settings of System Certificates
- iexplore.exe (PID: 892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| ContentType: | text/html; charset=utf-8 |
|---|---|
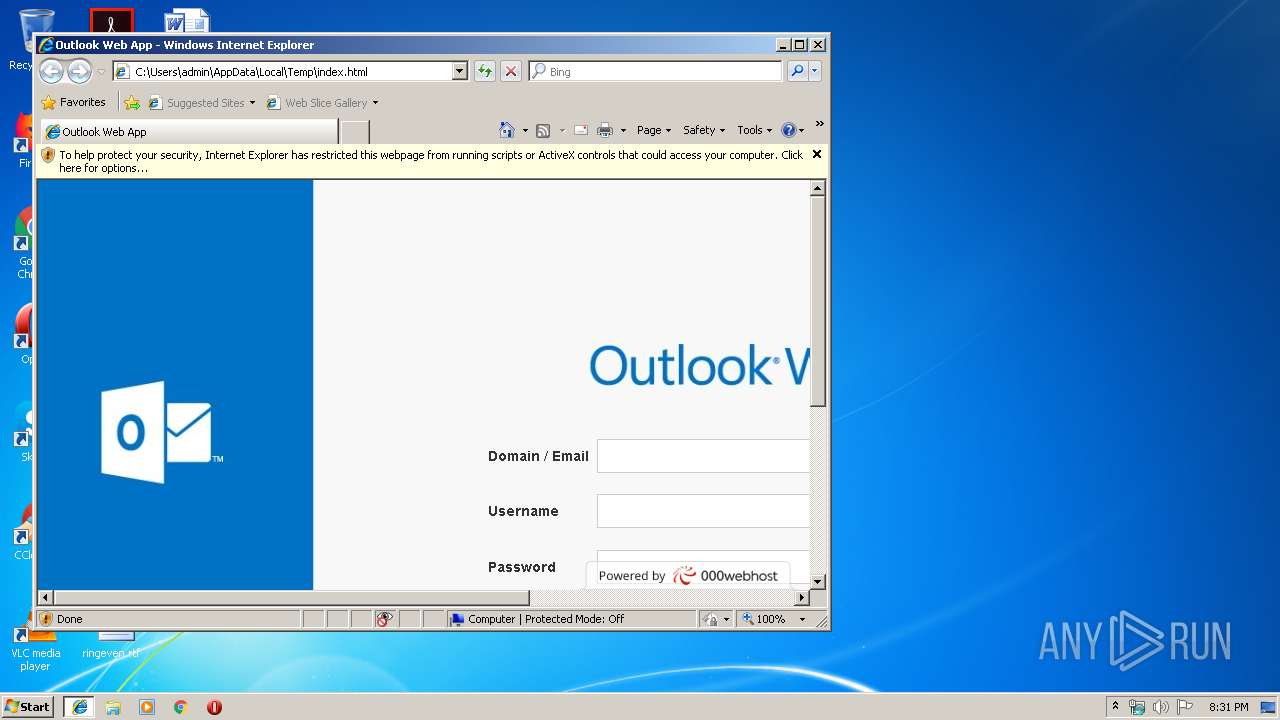
| Title: | Outlook Web App |
| viewport: | width=1200 |
| Description: | - |
| Keywords: | - |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 892 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2388 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2388 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
445
Read events
365
Write events
79
Delete events
1
Modification events
| (PID) Process: | (2388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Type |
Value: 3 | |||
| (PID) Process: | (892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070C000100020014001E0036008501 | |||
| (PID) Process: | (892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | LoadTime |
Value: 9 | |||
Executable files
0
Suspicious files
0
Text files
24
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2388 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2388 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\main[1].js | text | |
MD5:B8C09A01EF708ED518165B975767890B | SHA256:26BA2542EB936B980FEA2F581CD3A3C2E27172FF7B1F99E705C0B861FBCEA5B4 | |||
| 892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\font-awesome.min[1].css | text | |
MD5:269550530CC127B6AA5A35925A7DE6CE | SHA256:799AEB25CC0373FDEE0E1B1DB7AD6C2F6A0E058DFADAA3379689F583213190BD | |||
| 892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\css[2].txt | text | |
MD5:— | SHA256:— | |||
| 892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\css[3].txt | text | |
MD5:— | SHA256:— | |||
| 892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\css[1].txt | text | |
MD5:— | SHA256:— | |||
| 892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\css[1].txt | text | |
MD5:— | SHA256:— | |||
| 892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\glyphicons-halflings-regular[1].eot | eot | |
MD5:F4769F9BDB7466BE65088239C12046D1 | SHA256:13634DA87D9E23F8C3ED9108CE1724D183A39AD072E73E1B3D8CBF646D2D0407 | |||
| 892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\common[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
31
DNS requests
5
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
892 | iexplore.exe | GET | 200 | 145.14.145.231:80 | http://microsoft-webmail-x.000webhostapp.com/gallery_gen/119e653850c44965d6a4bedce5e7c872.jpeg | US | image | 82.5 Kb | shared |
892 | iexplore.exe | GET | 200 | 145.14.145.231:80 | http://microsoft-webmail-x.000webhostapp.com/css/common.css?ts=1574116292 | US | text | 1.53 Kb | shared |
892 | iexplore.exe | GET | 200 | 145.14.145.231:80 | http://microsoft-webmail-x.000webhostapp.com/css/1.css?ts=1574116292 | US | text | 619 b | shared |
892 | iexplore.exe | GET | 200 | 145.14.145.231:80 | http://microsoft-webmail-x.000webhostapp.com/css/flag-icon-css/css/flag-icon.min.css | US | text | 332 b | shared |
892 | iexplore.exe | GET | 200 | 145.14.145.231:80 | http://microsoft-webmail-x.000webhostapp.com/gallery_gen/61b289127e86651f58283068c7032a07.jpg | US | image | 92.4 Kb | shared |
892 | iexplore.exe | GET | 200 | 145.14.145.231:80 | http://microsoft-webmail-x.000webhostapp.com/css/bootstrap.min.css | US | text | 24.1 Kb | shared |
892 | iexplore.exe | GET | 200 | 145.14.145.231:80 | http://microsoft-webmail-x.000webhostapp.com/js/bootstrap.min.js | US | text | 11.4 Kb | shared |
892 | iexplore.exe | GET | 200 | 145.14.145.231:80 | http://microsoft-webmail-x.000webhostapp.com/fonts/glyphicons-halflings-regular.eot? | US | eot | 19.6 Kb | shared |
892 | iexplore.exe | GET | 200 | 145.14.145.231:80 | http://microsoft-webmail-x.000webhostapp.com/js/main.js?v=20190117142751 | US | text | 5.45 Kb | shared |
892 | iexplore.exe | GET | 200 | 145.14.145.231:80 | http://microsoft-webmail-x.000webhostapp.com/css/font-awesome/font-awesome.min.css?v=4.7.0 | US | text | 7.65 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2388 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
892 | iexplore.exe | 145.14.145.231:80 | microsoft-webmail-x.000webhostapp.com | Hostinger International Limited | US | shared |
892 | iexplore.exe | 172.217.22.99:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
892 | iexplore.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
892 | iexplore.exe | 172.217.22.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
892 | iexplore.exe | 104.20.68.46:443 | cdn.000webhost.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
microsoft-webmail-x.000webhostapp.com |
| shared |
www.bing.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdn.000webhost.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |