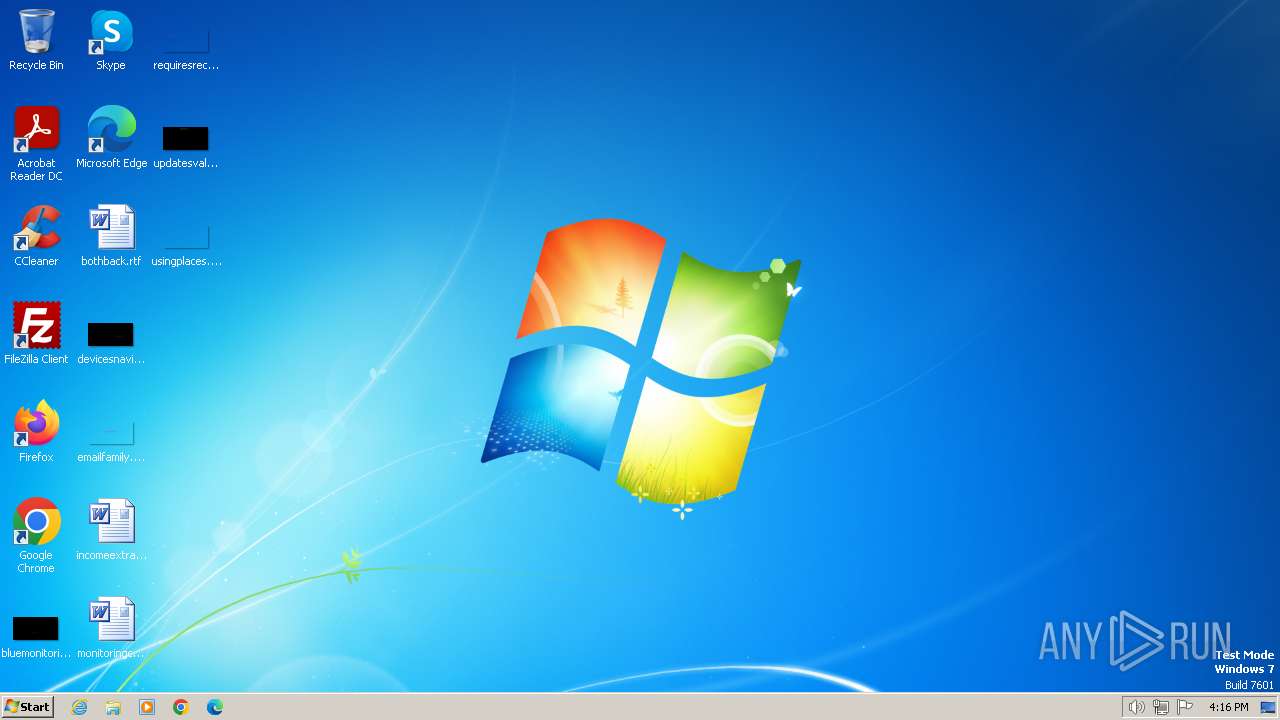
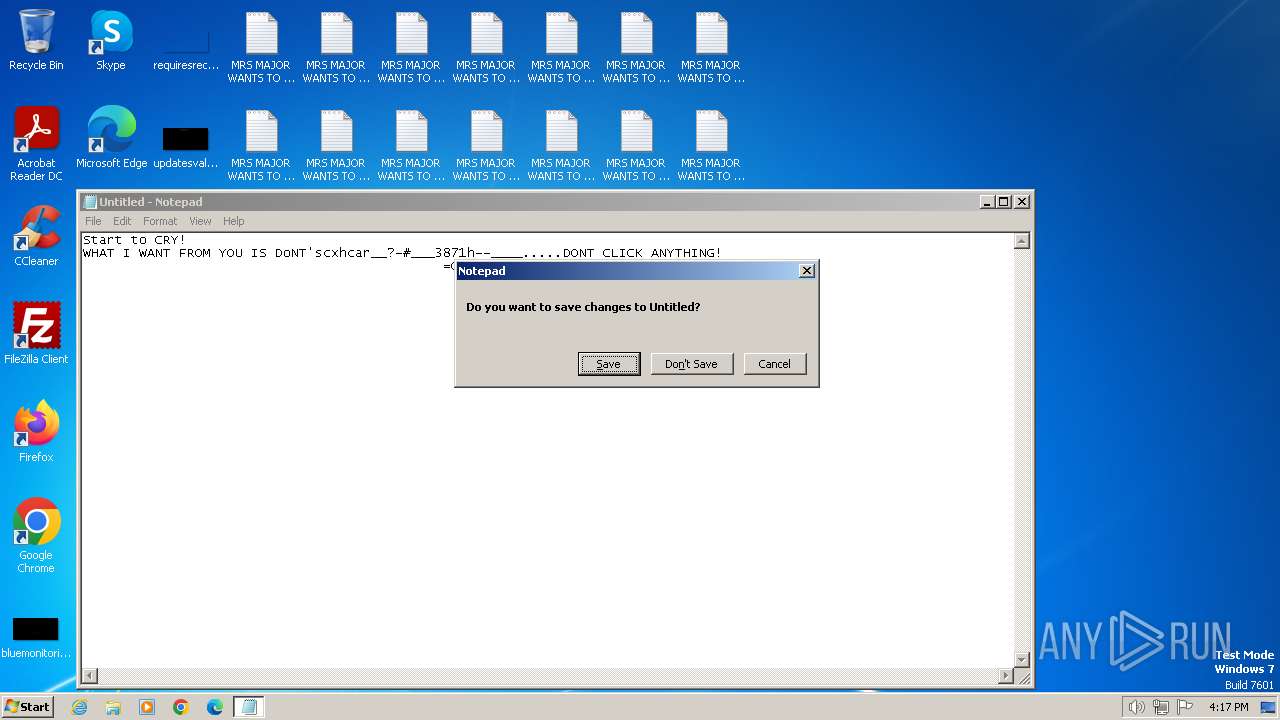
| File name: | BossDaMajor.exe |
| Full analysis: | https://app.any.run/tasks/60d2088c-cae7-4da3-a702-6830b5b93cdc |
| Verdict: | Malicious activity |
| Analysis date: | April 04, 2024, 15:16:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 38FF71C1DEE2A9ADD67F1EDB1A30FF8C |
| SHA1: | 10F0DEFD98D4E5096FBEB321B28D6559E44D66DB |
| SHA256: | 730A41A7656F606A22E9F0D68782612D6E00AB8CFE1260160B9E0B00BC2E442A |
| SSDEEP: | 49152:veG3J7FtM9SbJakTiTBMGSARaspyyx979PSxgKFdGlYU:2GZxSoJrTiTBMGtRa8t7EFddU |
MALICIOUS
Drops the executable file immediately after the start
- BossDaMajor.exe (PID: 2892)
- wscript.exe (PID: 2908)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 2908)
- wscript.exe (PID: 696)
Checks whether a specified folder exists (SCRIPT)
- wscript.exe (PID: 2908)
Gets TEMP folder path (SCRIPT)
- wscript.exe (PID: 2908)
- wscript.exe (PID: 696)
Gets path to any of the special folders (SCRIPT)
- wscript.exe (PID: 2908)
- wscript.exe (PID: 696)
Creates a new registry key or changes the value of an existing one (SCRIPT)
- wscript.exe (PID: 2908)
- wscript.exe (PID: 696)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 2908)
- wscript.exe (PID: 696)
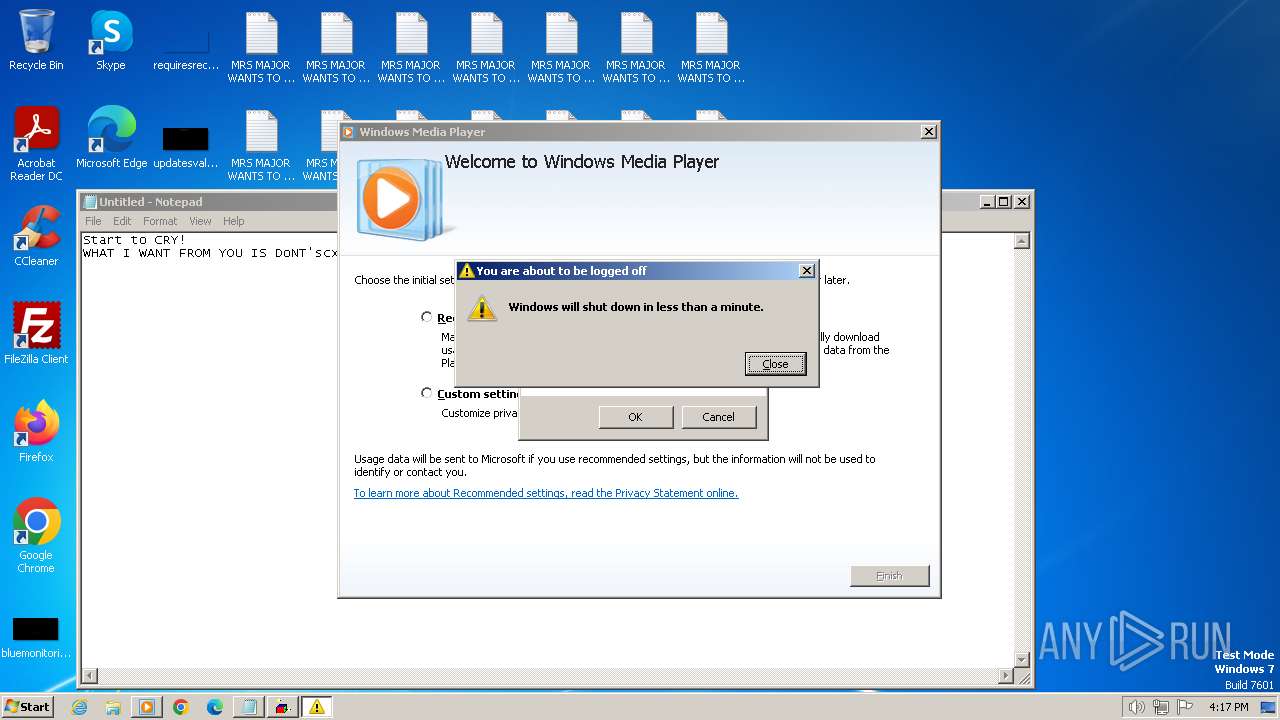
Changes the login/logoff helper path in the registry
- wscript.exe (PID: 696)
Disables Windows Defender
- wscript.exe (PID: 696)
Copies file to a new location (SCRIPT)
- wscript.exe (PID: 696)
SUSPICIOUS
The process executes VB scripts
- BossDaMajor.exe (PID: 2892)
- wscript.exe (PID: 2908)
Reads the Internet Settings
- BossDaMajor.exe (PID: 2892)
- wscript.exe (PID: 2908)
- wscript.exe (PID: 696)
- wmplayer.exe (PID: 1740)
- setup_wm.exe (PID: 2372)
- sipnotify.exe (PID: 1808)
Reads security settings of Internet Explorer
- BossDaMajor.exe (PID: 2892)
- setup_wm.exe (PID: 2372)
- wmplayer.exe (PID: 1740)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 2908)
- wscript.exe (PID: 696)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2908)
- wscript.exe (PID: 696)
Application launched itself
- wscript.exe (PID: 2908)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 696)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 696)
Blank space has been found in the path
- wscript.exe (PID: 696)
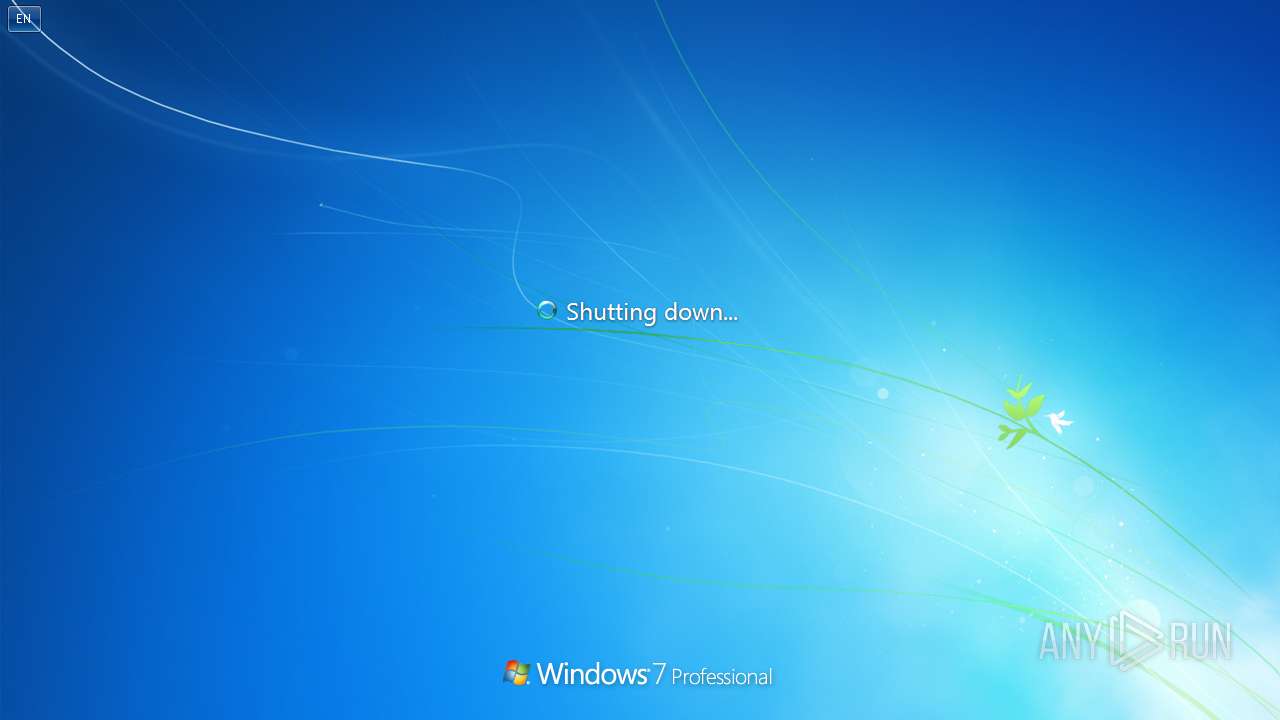
The system shut down or reboot
- wscript.exe (PID: 696)
The process executes via Task Scheduler
- ctfmon.exe (PID: 1464)
- sipnotify.exe (PID: 1808)
Reads settings of System Certificates
- sipnotify.exe (PID: 1808)
INFO
Checks supported languages
- BossDaMajor.exe (PID: 2892)
- wmplayer.exe (PID: 1740)
- IMEKLMG.EXE (PID: 2208)
- IMEKLMG.EXE (PID: 2196)
- setup_wm.exe (PID: 2372)
- wmpnscfg.exe (PID: 2672)
- wmpnscfg.exe (PID: 2692)
Reads the computer name
- BossDaMajor.exe (PID: 2892)
- wmplayer.exe (PID: 1740)
- setup_wm.exe (PID: 2372)
- wmpnscfg.exe (PID: 2672)
- wmpnscfg.exe (PID: 2692)
- IMEKLMG.EXE (PID: 2208)
- IMEKLMG.EXE (PID: 2196)
Create files in a temporary directory
- BossDaMajor.exe (PID: 2892)
- setup_wm.exe (PID: 2372)
Creates files in the program directory
- wscript.exe (PID: 2908)
- wscript.exe (PID: 696)
Process checks computer location settings
- setup_wm.exe (PID: 2372)
Reads the machine GUID from the registry
- setup_wm.exe (PID: 2372)
Checks proxy server information
- setup_wm.exe (PID: 2372)
Manual execution by a user
- IMEKLMG.EXE (PID: 2208)
- IMEKLMG.EXE (PID: 2196)
- wmpnscfg.exe (PID: 2692)
- wmpnscfg.exe (PID: 2672)
Reads Environment values
- setup_wm.exe (PID: 2372)
Process checks whether UAC notifications are on
- IMEKLMG.EXE (PID: 2208)
- IMEKLMG.EXE (PID: 2196)
Reads security settings of Internet Explorer
- sipnotify.exe (PID: 1808)
Reads the software policy settings
- sipnotify.exe (PID: 1808)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (35) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (30.9) |
| .scr | | | Windows screen saver (14.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.3) |
| .exe | | | Win32 Executable (generic) (5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:05:04 07:30:05+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 49152 |
| InitializedDataSize: | 1964032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release, Private build |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Corporation Corporation © 2017 All rights reserved |
| FileVersion: | 1,0,0,0 |
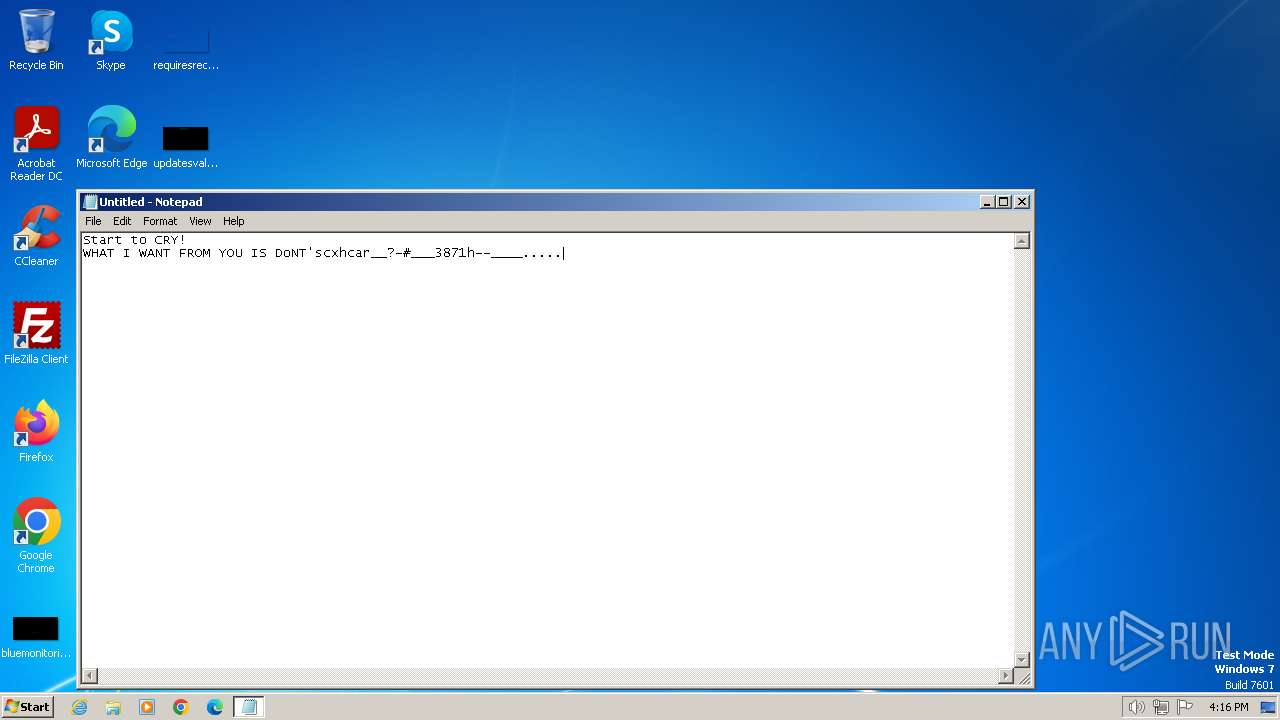
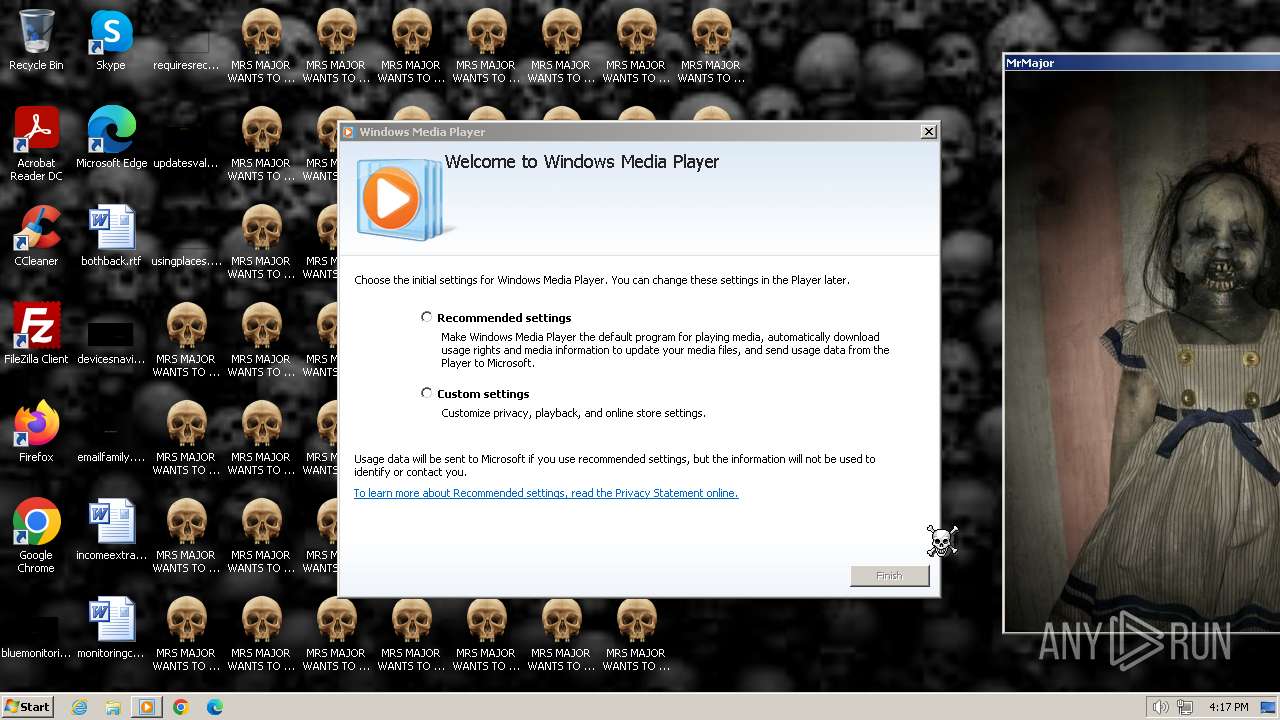
| ProductName: | Mrsmajor.exe |
| InternalName: | mrsmajoruserinterface.exe |
| ProductVersion: | 1.0.0.0 |
Total processes
145
Monitored processes
14
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 696 | "C:\Windows\System32\wscript.exe" "C:\Program files\mrsmajor\mrsmajorlauncher.vbs" RunAsAdministrator | C:\Windows\System32\wscript.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 1073807364 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1464 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
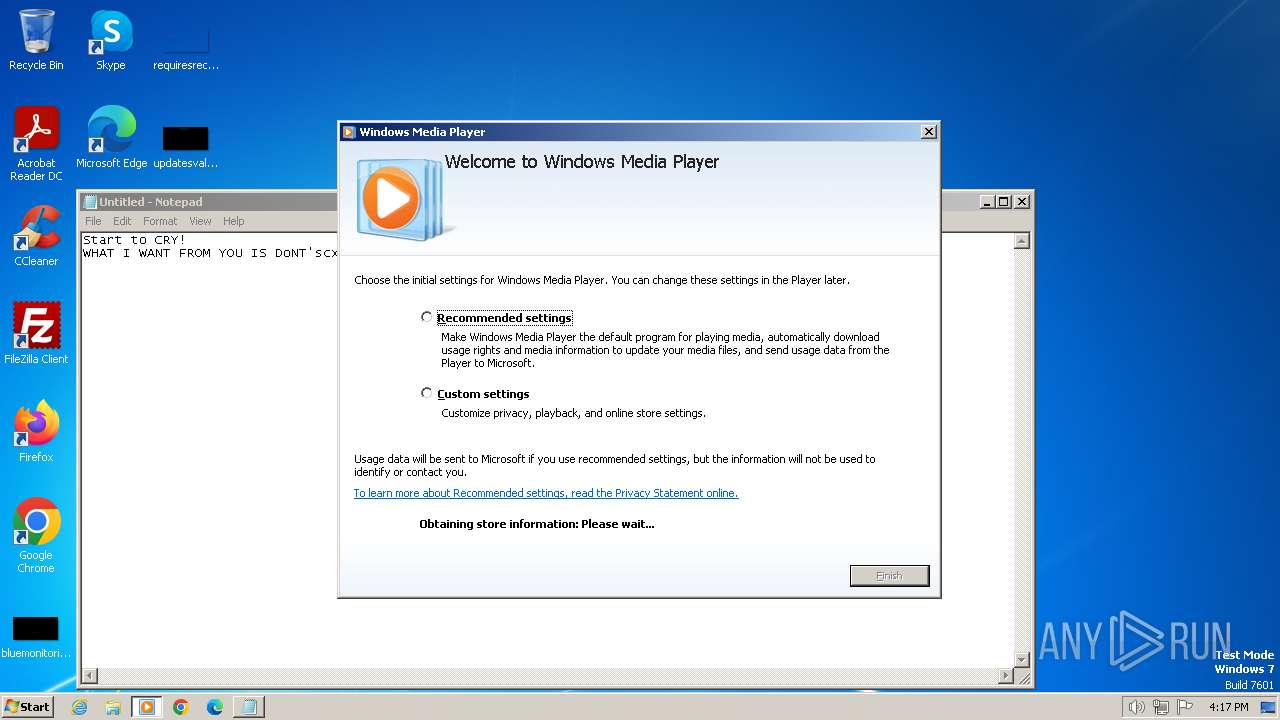
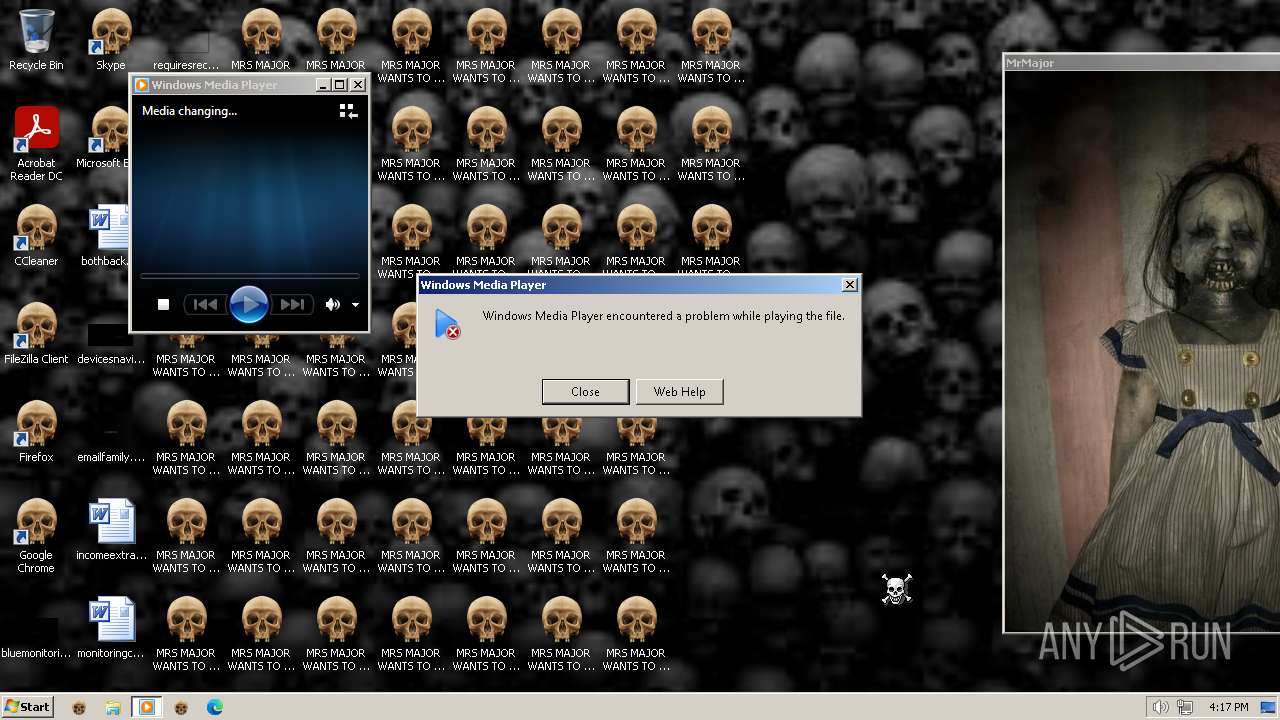
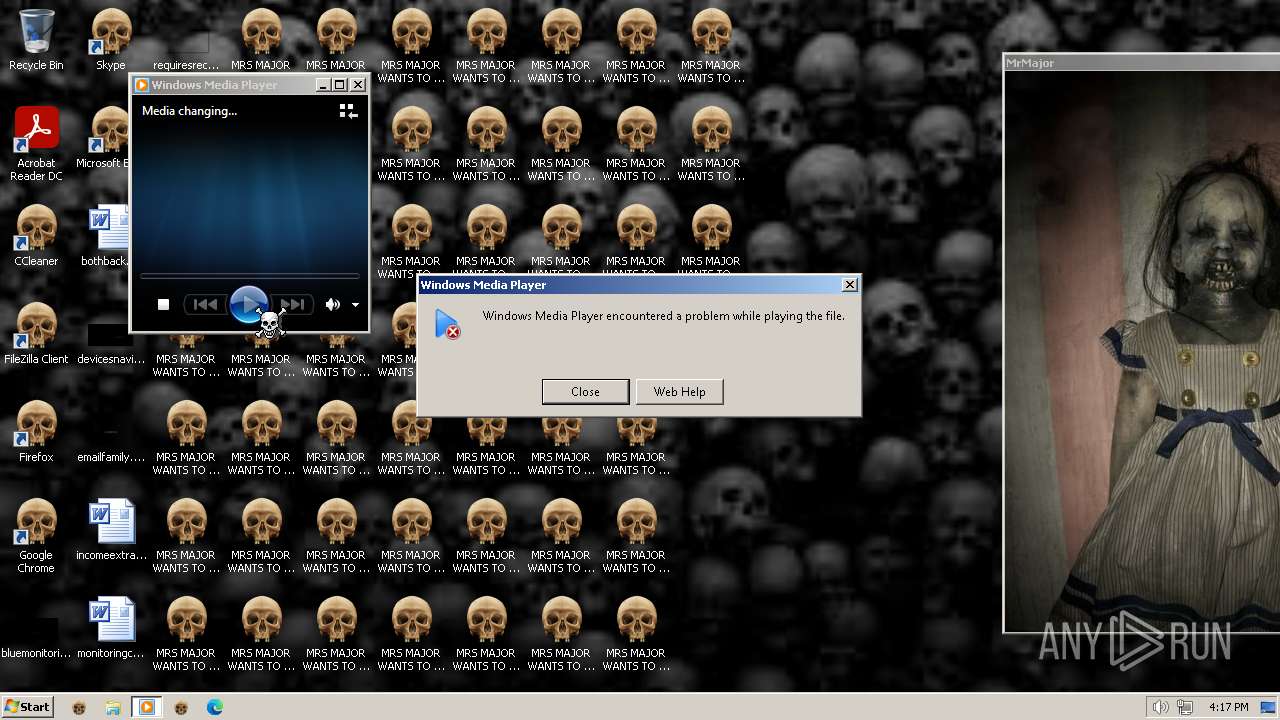
| 1740 | "C:\Program Files\Windows Media Player\wmplayer.exe" "C:\Program Files\mrsmajor\def_resource\f11.mp4" | C:\Program Files\Windows Media Player\wmplayer.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Media Player Exit code: 0 Version: 12.0.7601.23517 (win7sp1_ldr.160812-0732) Modules
| |||||||||||||||
| 1808 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 2064 | "C:\Windows\System32\notepad.exe" | C:\Windows\System32\notepad.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 1073807364 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2196 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /JPN /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /KOR /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Windows Media Player\setup_wm.exe" /RunOnce:"C:\Program Files\Windows Media Player\wmplayer.exe" "C:\Program Files\mrsmajor\def_resource\f11.mp4" | C:\Program Files\Windows Media Player\setup_wm.exe | wmplayer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Windows Media Configuration Utility Exit code: 1073807364 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2488 | "C:\Windows\System32\shutdown.exe" -r -t 03 | C:\Windows\System32\shutdown.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2672 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
8 851
Read events
8 715
Write events
109
Delete events
27
Modification events
| (PID) Process: | (2892) BossDaMajor.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2892) BossDaMajor.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2892) BossDaMajor.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2892) BossDaMajor.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2908) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2908) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2908) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2908) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
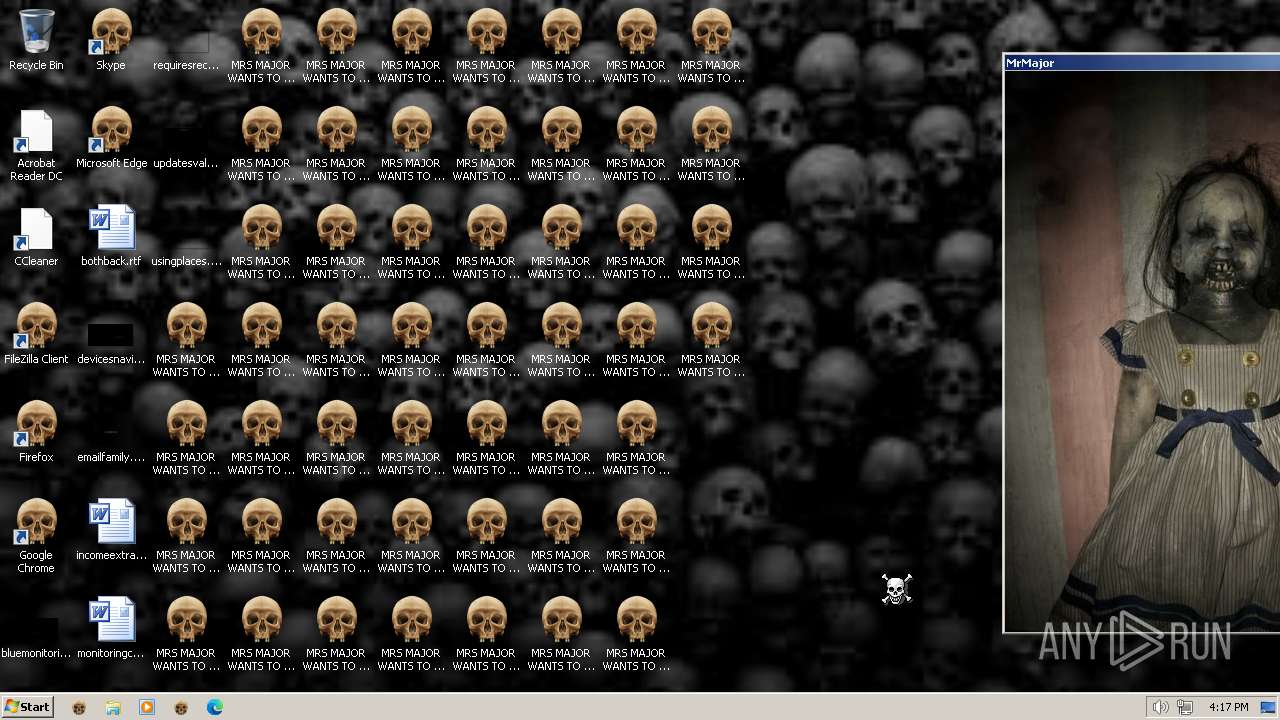
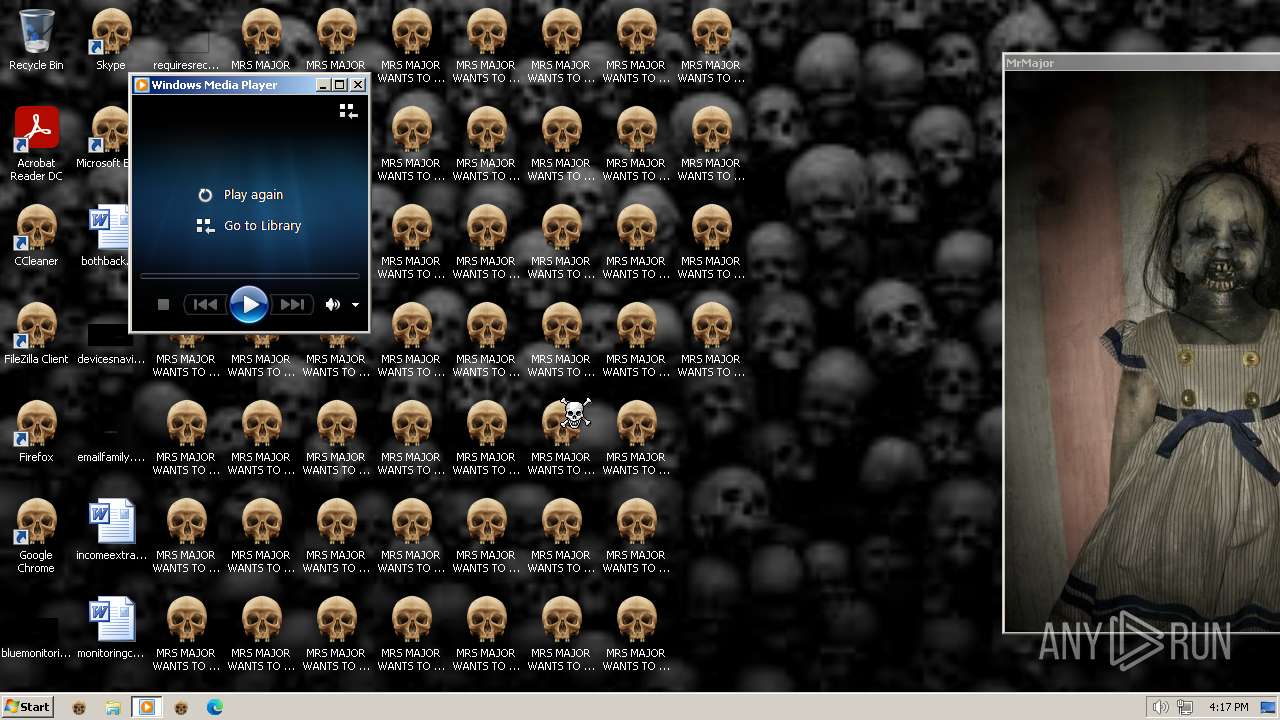
| (PID) Process: | (696) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\system |
| Operation: | write | Name: | wallpaper |
Value: C:\Users\admin\AppData\Local\Temp\@tile@@.jpg | |||
| (PID) Process: | (696) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\ActiveDesktop |
| Operation: | write | Name: | NoChangingWallPaper |
Value: 1 | |||
Executable files
2
Suspicious files
6
Text files
80
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2892 | BossDaMajor.exe | C:\Users\admin\AppData\Local\Temp\22D5.tmp\22D6.vbs | text | |
MD5:— | SHA256:— | |||
| 2892 | BossDaMajor.exe | C:\Users\admin\AppData\Local\Temp\22D5.tmp\mrsmajor\CPUUsage.vbs | text | |
MD5:— | SHA256:— | |||
| 2892 | BossDaMajor.exe | C:\Users\admin\AppData\Local\Temp\22D5.tmp\mrsmajor\default.txt | text | |
MD5:— | SHA256:— | |||
| 2892 | BossDaMajor.exe | C:\Users\admin\AppData\Local\Temp\22D5.tmp\mrsmajor\def_resource\@Tile@@.jpg | image | |
MD5:— | SHA256:— | |||
| 2892 | BossDaMajor.exe | C:\Users\admin\AppData\Local\Temp\22D5.tmp\mrsmajor\def_resource\creepysound.mp3 | binary | |
MD5:— | SHA256:— | |||
| 2892 | BossDaMajor.exe | C:\Users\admin\AppData\Local\Temp\22D5.tmp\mrsmajor\def_resource\f11.mp4 | binary | |
MD5:— | SHA256:— | |||
| 2892 | BossDaMajor.exe | C:\Users\admin\AppData\Local\Temp\22D5.tmp\mrsmajor\def_resource\Skullcur.cur | binary | |
MD5:— | SHA256:— | |||
| 2892 | BossDaMajor.exe | C:\Users\admin\AppData\Local\Temp\22D5.tmp\mrsmajor\DreS_X.bat | text | |
MD5:— | SHA256:— | |||
| 2892 | BossDaMajor.exe | C:\Users\admin\AppData\Local\Temp\22D5.tmp\mrsmajor\Icon_resource\SkullIco.ico | image | |
MD5:— | SHA256:— | |||
| 2892 | BossDaMajor.exe | C:\Users\admin\AppData\Local\Temp\22D5.tmp\mrsmajor\Launcher.vbs | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
15
DNS requests
5
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2372 | setup_wm.exe | GET | 302 | 2.21.20.154:80 | http://redir.metaservices.microsoft.com/redir/allservices/?sv=5&version=12.0.7601.17514&locale=409&userlocale=409&geoid=f4&parch=x86&arch=x86 | unknown | — | — | unknown |
2372 | setup_wm.exe | GET | 200 | 23.48.23.133:80 | http://onlinestores.metaservices.microsoft.com/serviceswitching/AllServices.aspx?sv=5&version=12.0.7601.17514&locale=409&userlocale=409&geoid=f4&parch=x86&arch=x86 | unknown | — | — | unknown |
1808 | sipnotify.exe | HEAD | 200 | 23.212.215.38:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133567210578280000 | unknown | — | — | unknown |
2372 | setup_wm.exe | GET | 200 | 23.48.23.133:80 | http://onlinestores.metaservices.microsoft.com/bing/bing.xml | unknown | — | — | unknown |
3412 | wmplayer.exe | GET | — | 204.79.197.203:80 | http://www.msn.com/sqm/wmp/sqmserver.dll | unknown | — | — | unknown |
3412 | wmplayer.exe | POST | 301 | 204.79.197.203:80 | http://sqm.msn.com/sqm/wmp/sqmserver.dll | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2372 | setup_wm.exe | 2.21.20.154:80 | redir.metaservices.microsoft.com | Akamai International B.V. | DE | unknown |
2372 | setup_wm.exe | 23.48.23.133:80 | onlinestores.metaservices.microsoft.com | Akamai International B.V. | DE | unknown |
1116 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1808 | sipnotify.exe | 23.212.215.38:80 | query.prod.cms.rt.microsoft.com | AKAMAI-AS | AU | unknown |
3484 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
3412 | wmplayer.exe | 204.79.197.203:80 | sqm.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
redir.metaservices.microsoft.com |
| whitelisted |
onlinestores.metaservices.microsoft.com |
| whitelisted |
query.prod.cms.rt.microsoft.com |
| whitelisted |
sqm.msn.com |
| whitelisted |
www.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3412 | wmplayer.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |