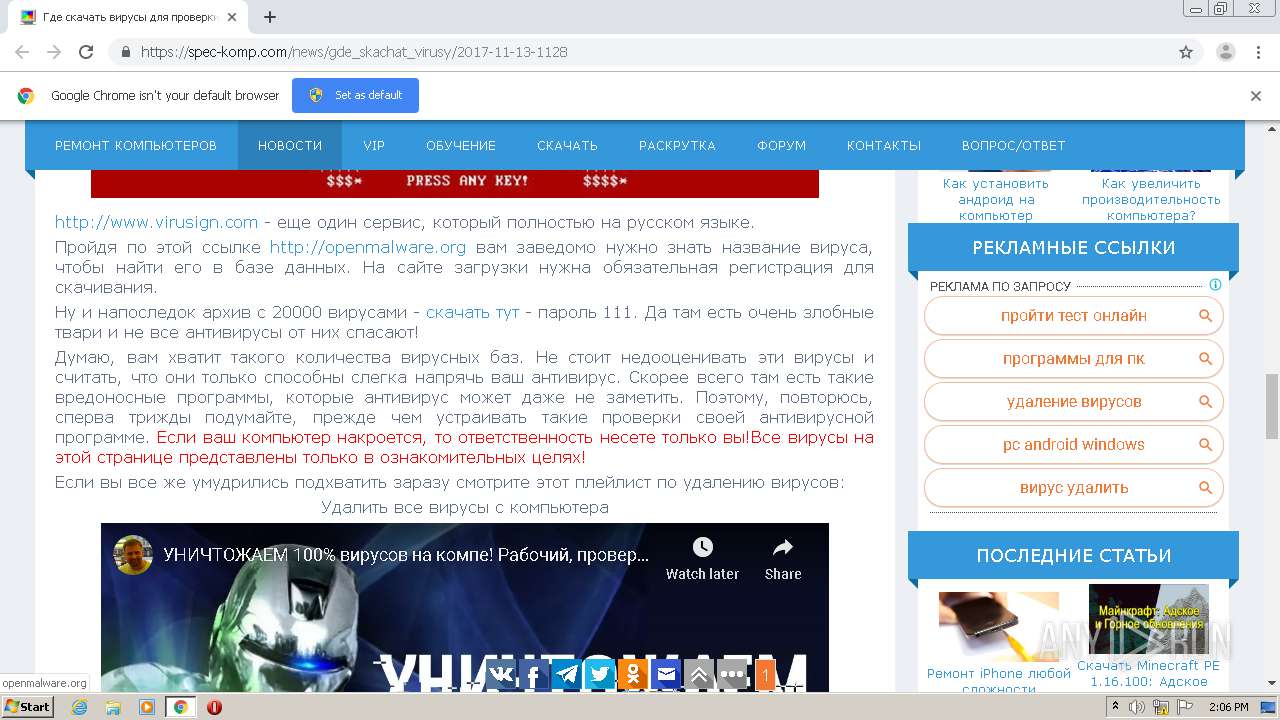
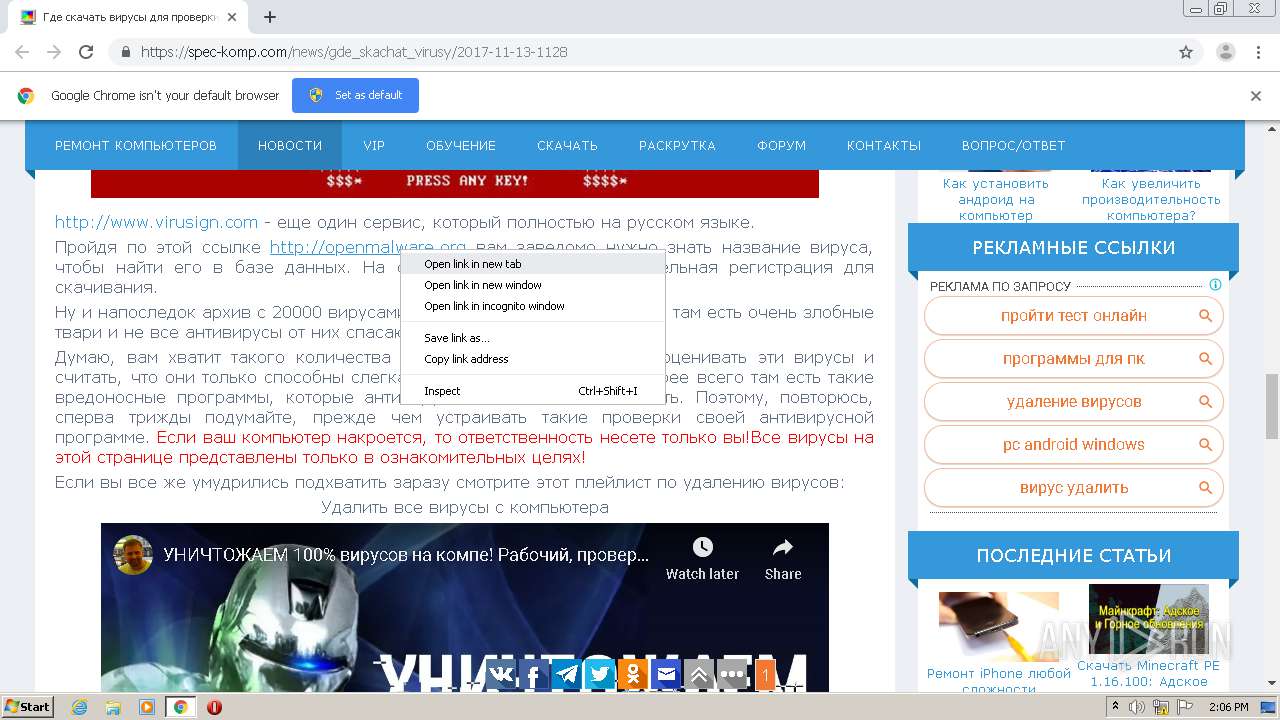
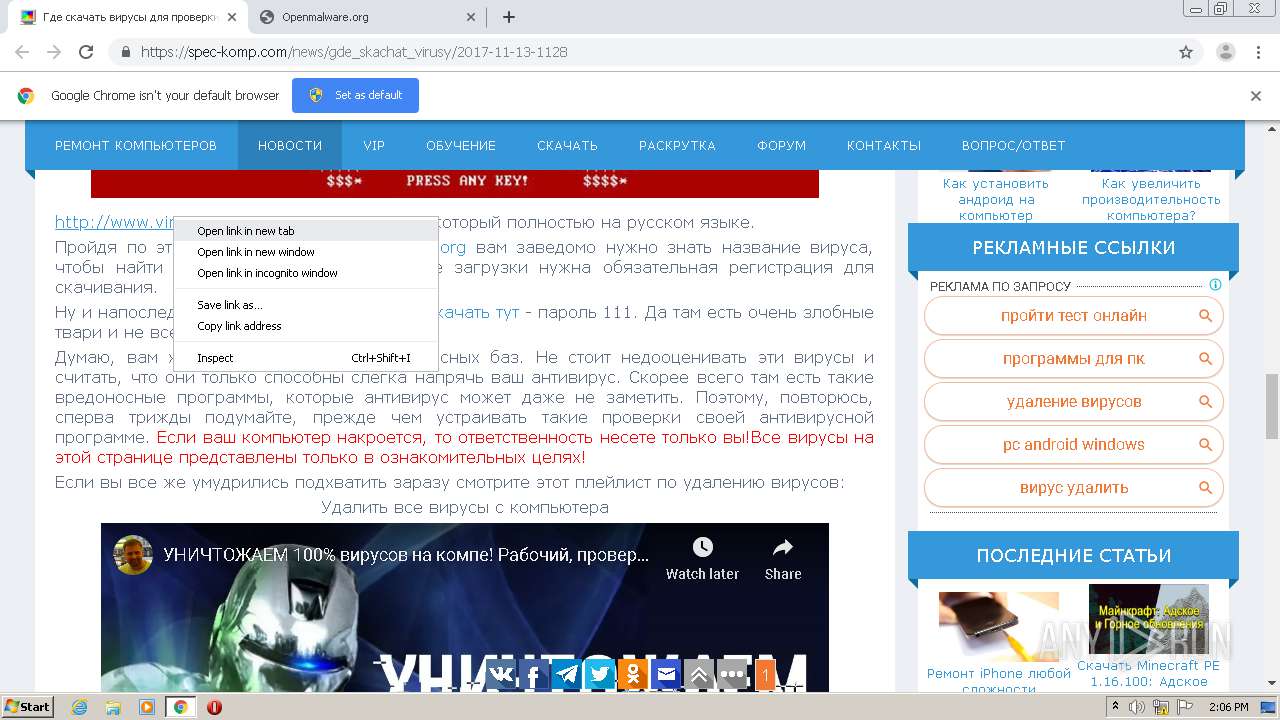
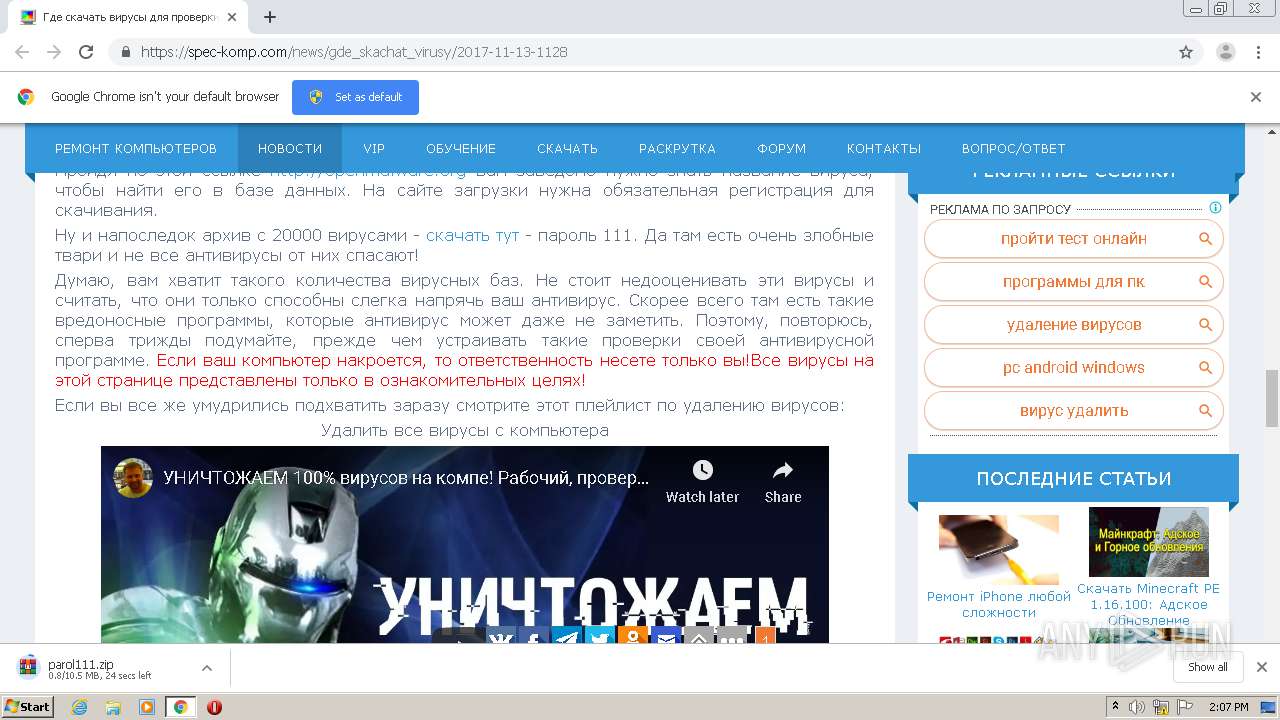
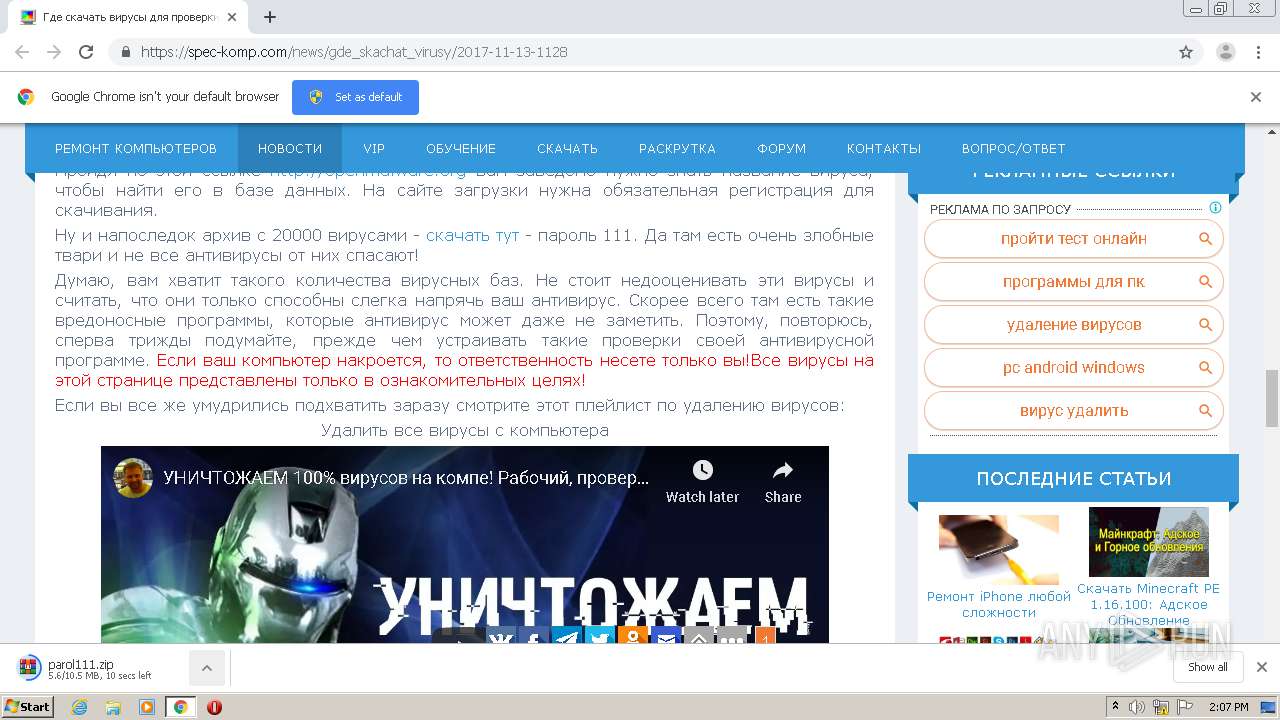
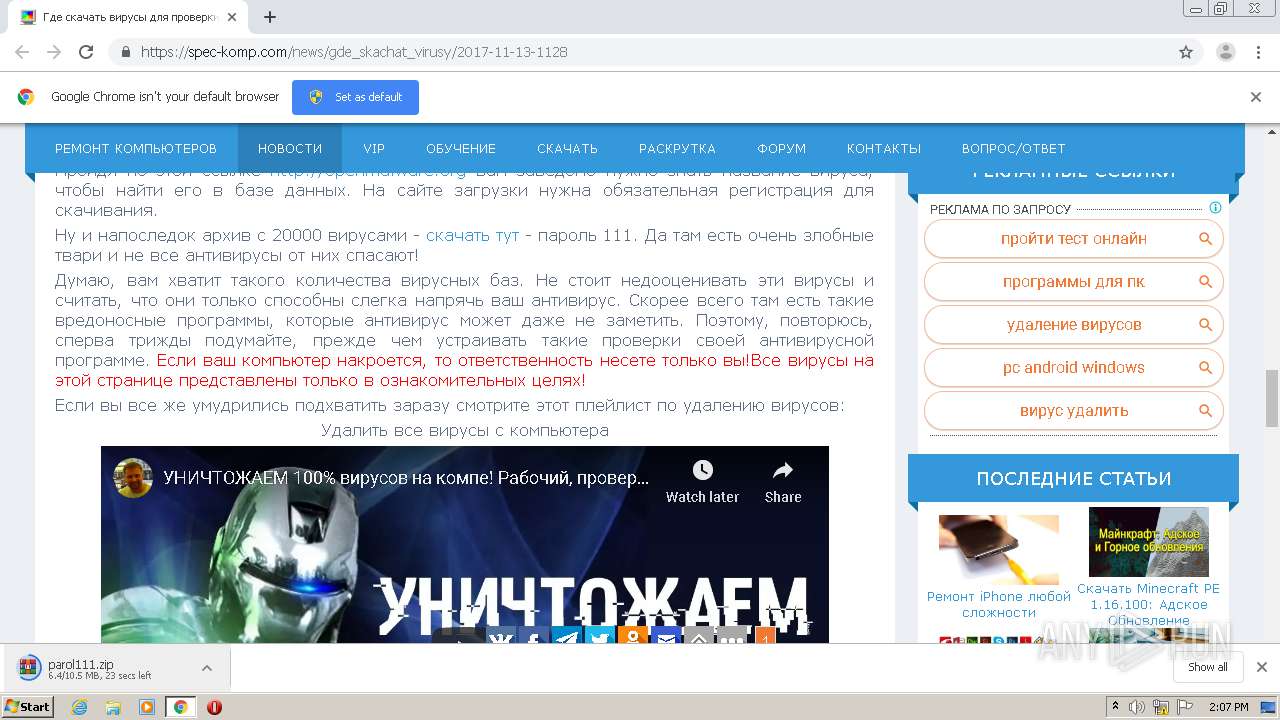
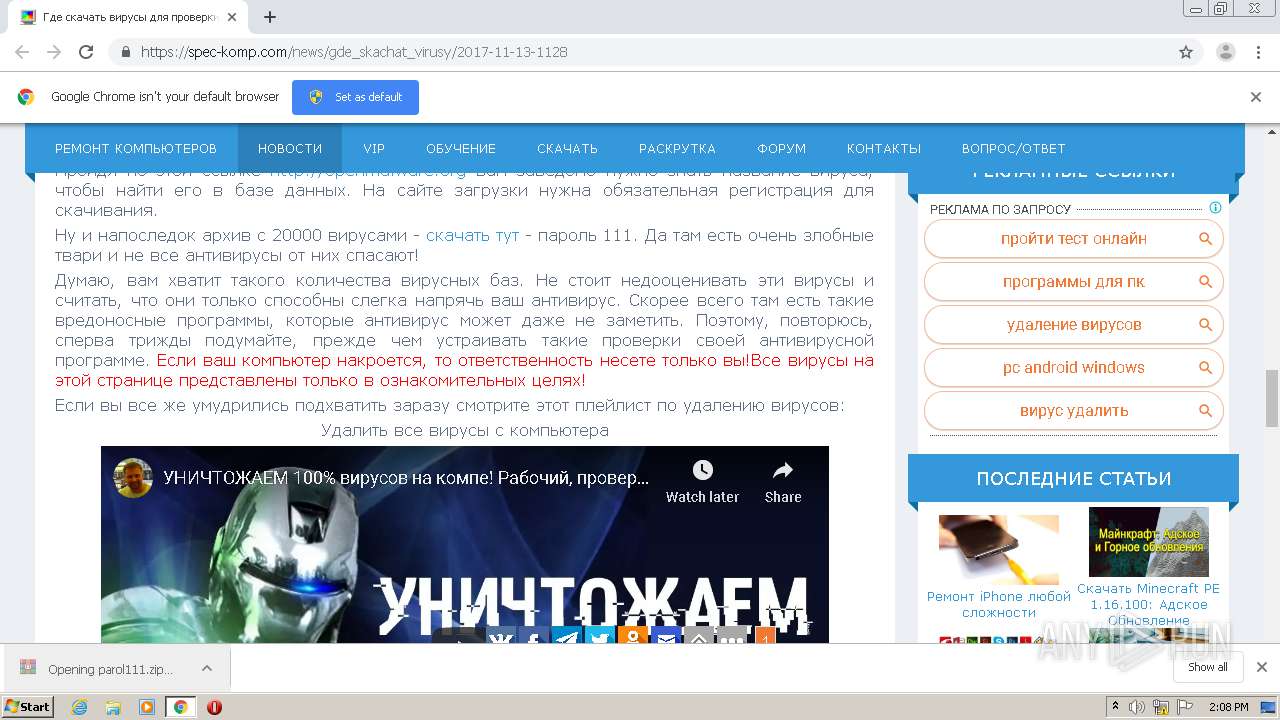
| URL: | https://spec-komp.com/news/gde_skachat_virusy/2017-11-13-1128 |
| Full analysis: | https://app.any.run/tasks/36966dd5-4ac3-4245-9dc3-cba9535dbd6f |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 14:05:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 71B5D15C5D9086442C8F9E3B948CB0BF |
| SHA1: | 460C0188E44AEC07D09BD1A2E874D86CA010A0C4 |
| SHA256: | 7302A7AE89DE21541904FF547E46777864957D13C67230CAEB1202C036BCA34E |
| SSDEEP: | 3:N8Y0XKI4W/fKNv6N:2Y0XKIb/Cy |
MALICIOUS
No malicious indicators.SUSPICIOUS
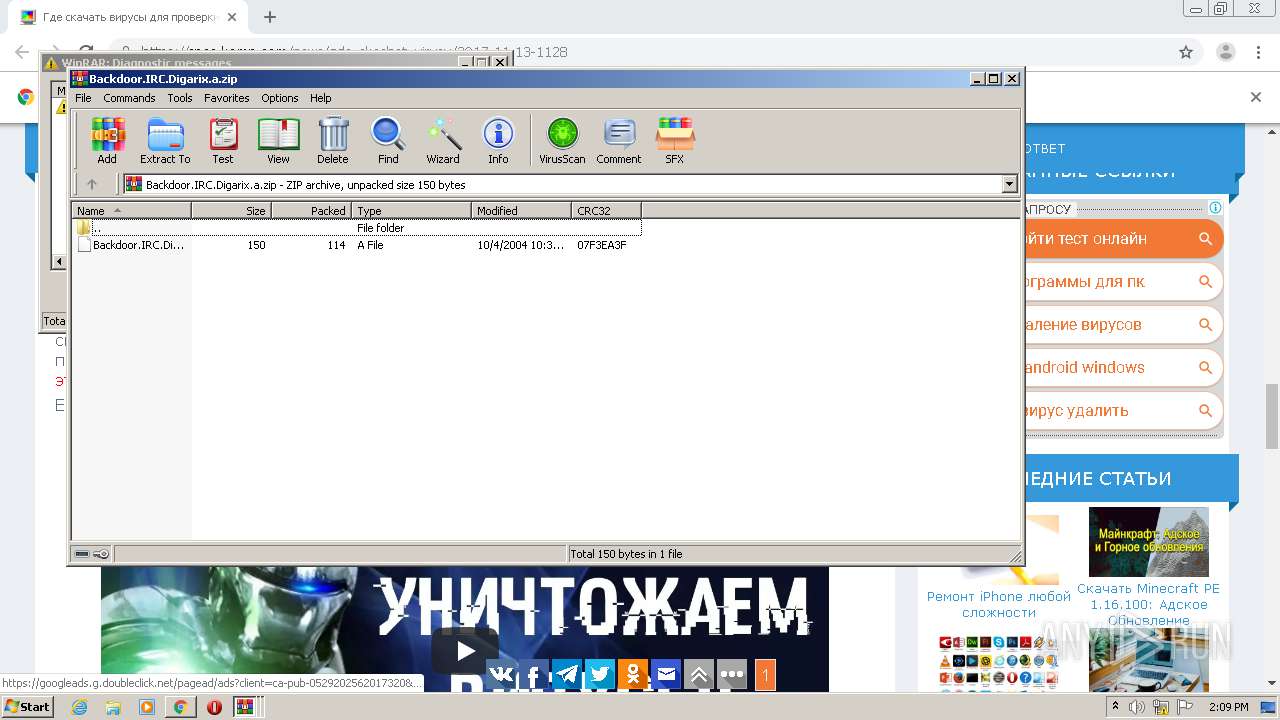
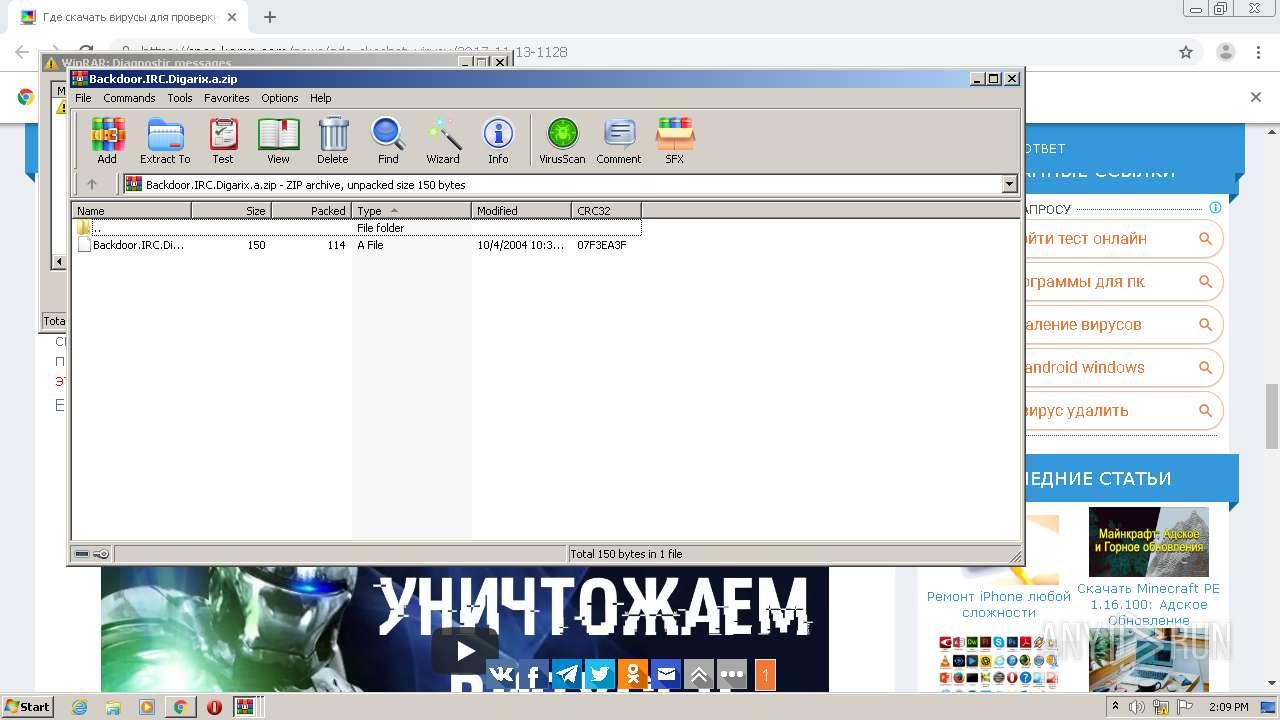
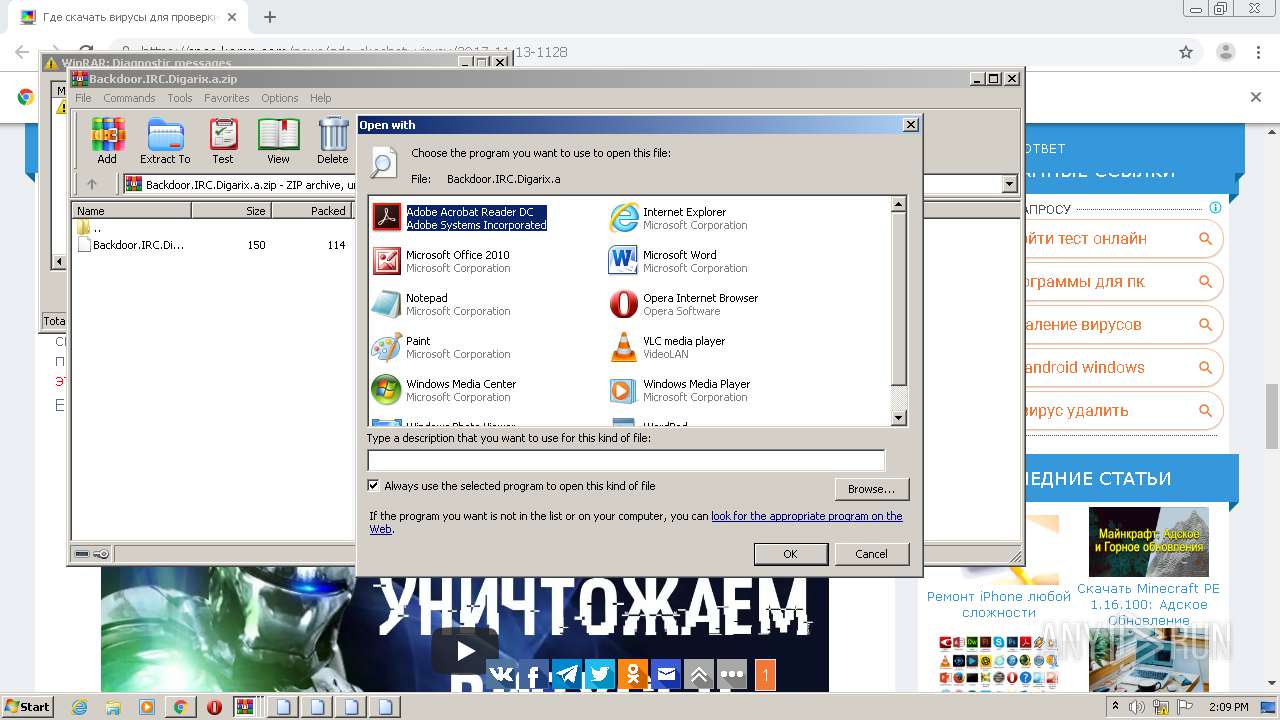
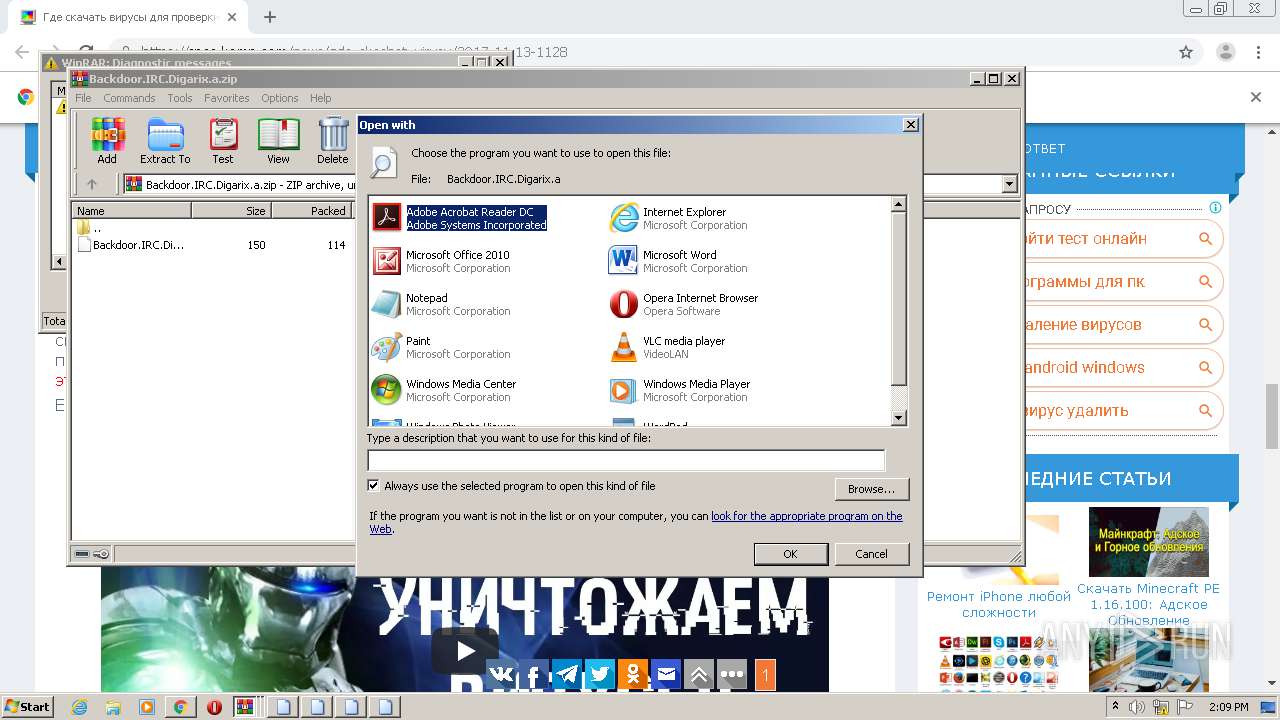
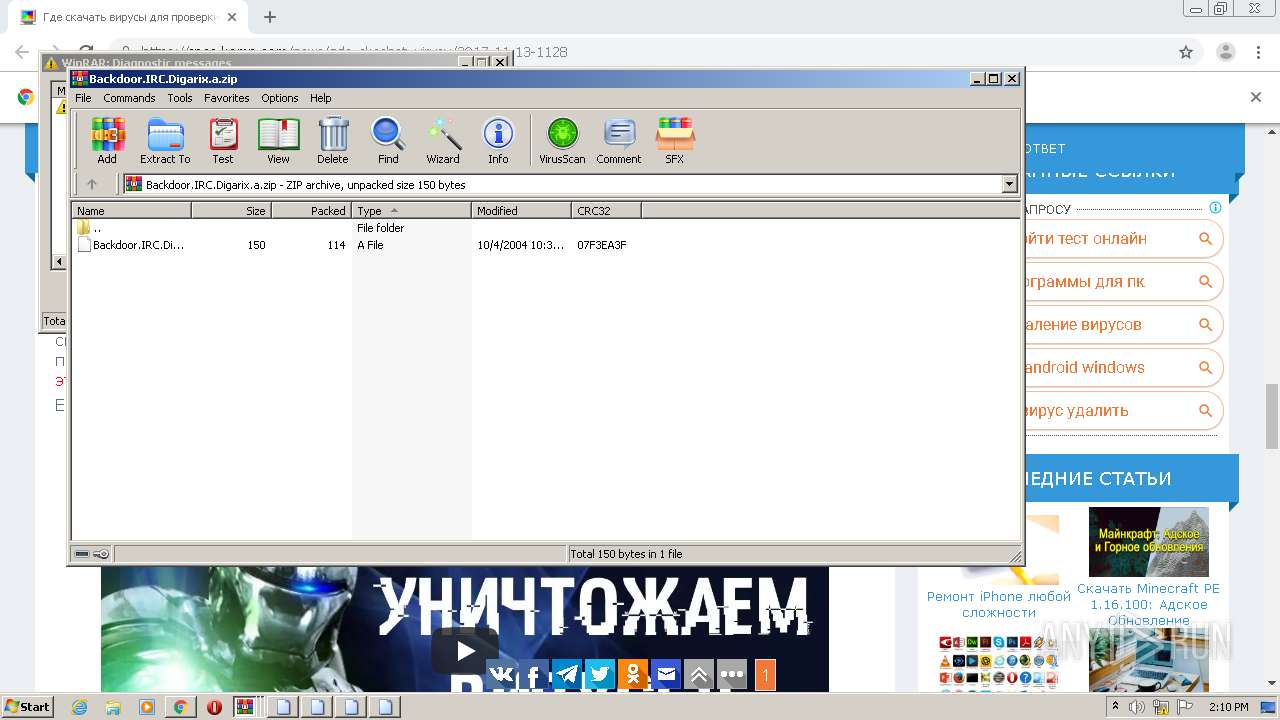
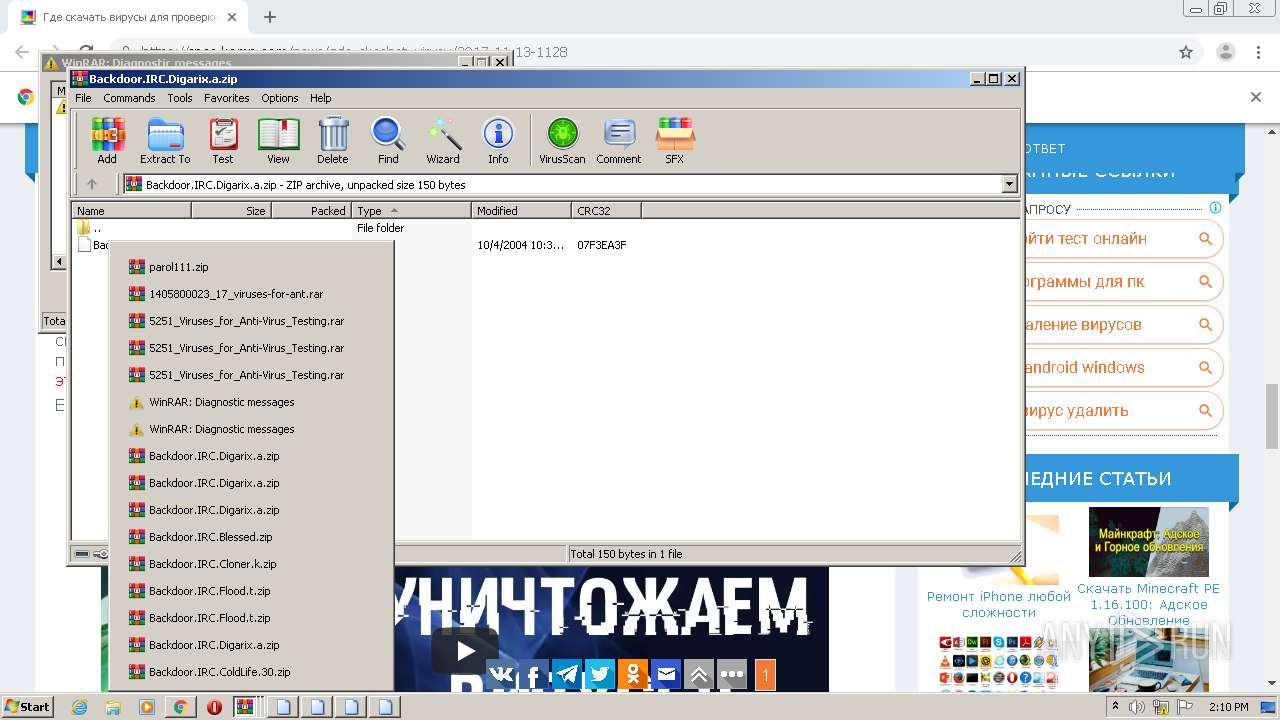
Application launched itself
- WinRAR.exe (PID: 1448)
- WinRAR.exe (PID: 2700)
- WinRAR.exe (PID: 2216)
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 2688)
INFO
Reads the hosts file
- chrome.exe (PID: 1004)
- chrome.exe (PID: 2568)
- RdrCEF.exe (PID: 2820)
Reads settings of System Certificates
- chrome.exe (PID: 1004)
- AcroRd32.exe (PID: 3376)
Creates files in the user directory
- chrome.exe (PID: 2568)
Application launched itself
- chrome.exe (PID: 2568)
- AcroRd32.exe (PID: 3376)
- RdrCEF.exe (PID: 2820)
Changes IE settings (feature browser emulation)
- AcroRd32.exe (PID: 3376)
Changes settings of System certificates
- chrome.exe (PID: 1004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
90
Monitored processes
53
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,17484310629103190347,7202997728971803930,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2442718470204678902 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3108 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,17484310629103190347,7202997728971803930,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17995463561732236739 --mojo-platform-channel-handle=1024 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,17484310629103190347,7202997728971803930,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6346343288936002231 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2176 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,17484310629103190347,7202997728971803930,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3963341022061241471 --mojo-platform-channel-handle=4604 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,17484310629103190347,7202997728971803930,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15141041978372324384 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2056 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,17484310629103190347,7202997728971803930,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=335769221938669729 --mojo-platform-channel-handle=1580 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,17484310629103190347,7202997728971803930,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=13979658253137558015 --mojo-platform-channel-handle=4332 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,17484310629103190347,7202997728971803930,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12859672993170380150 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2168 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
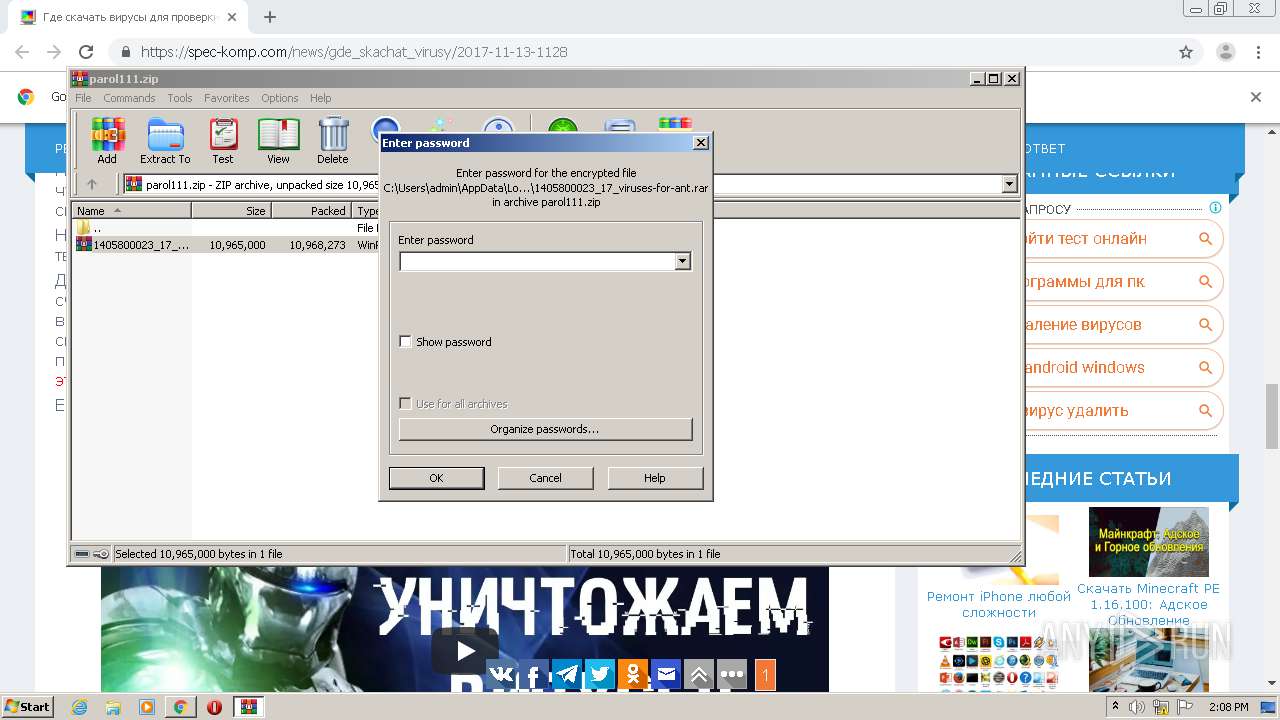
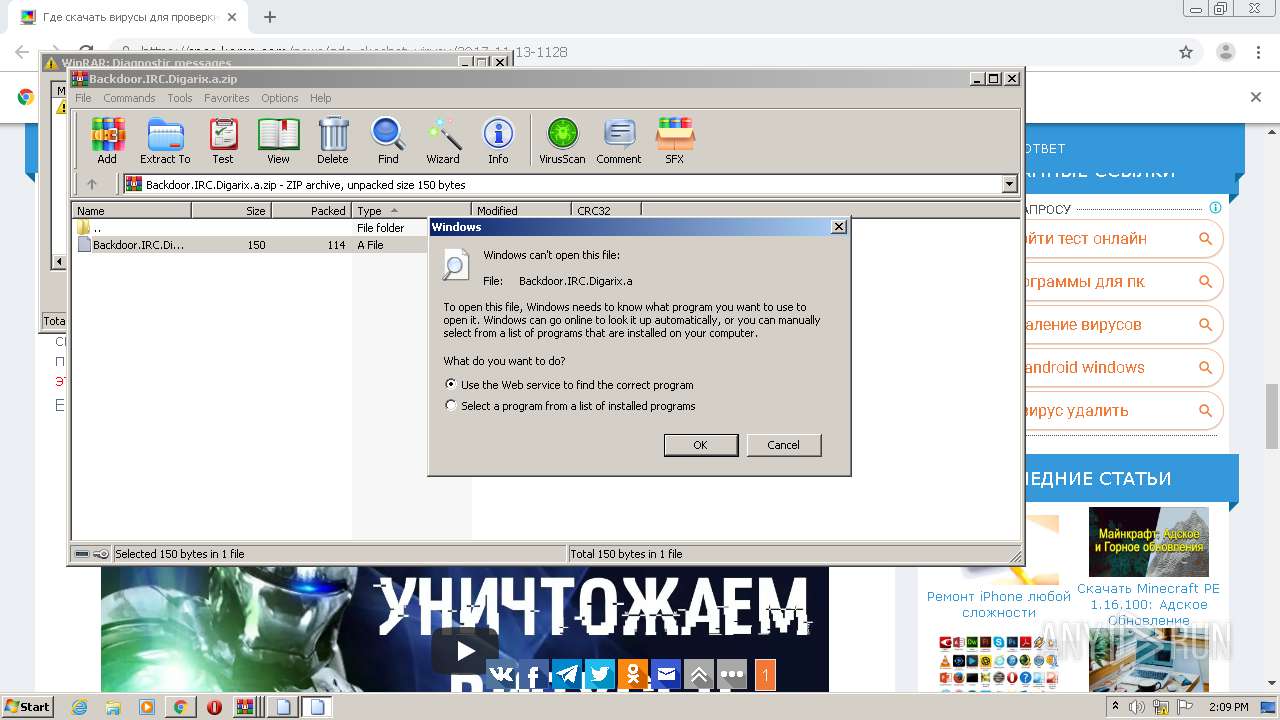
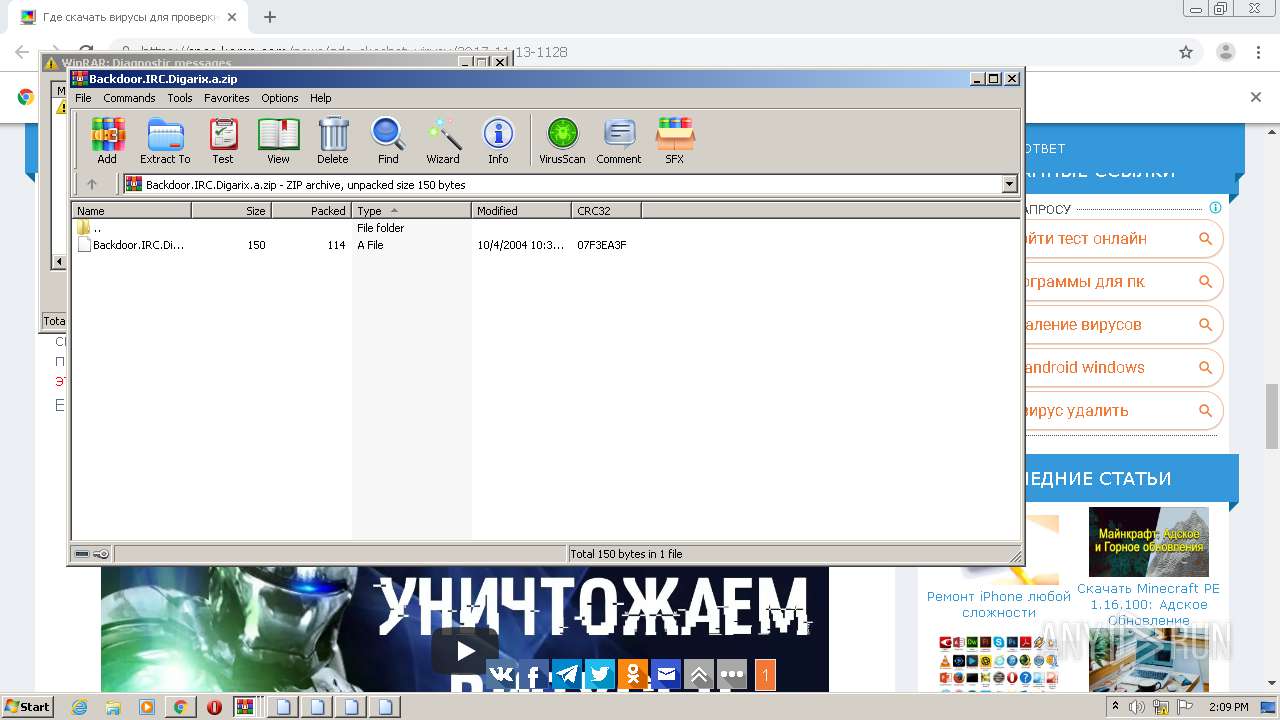
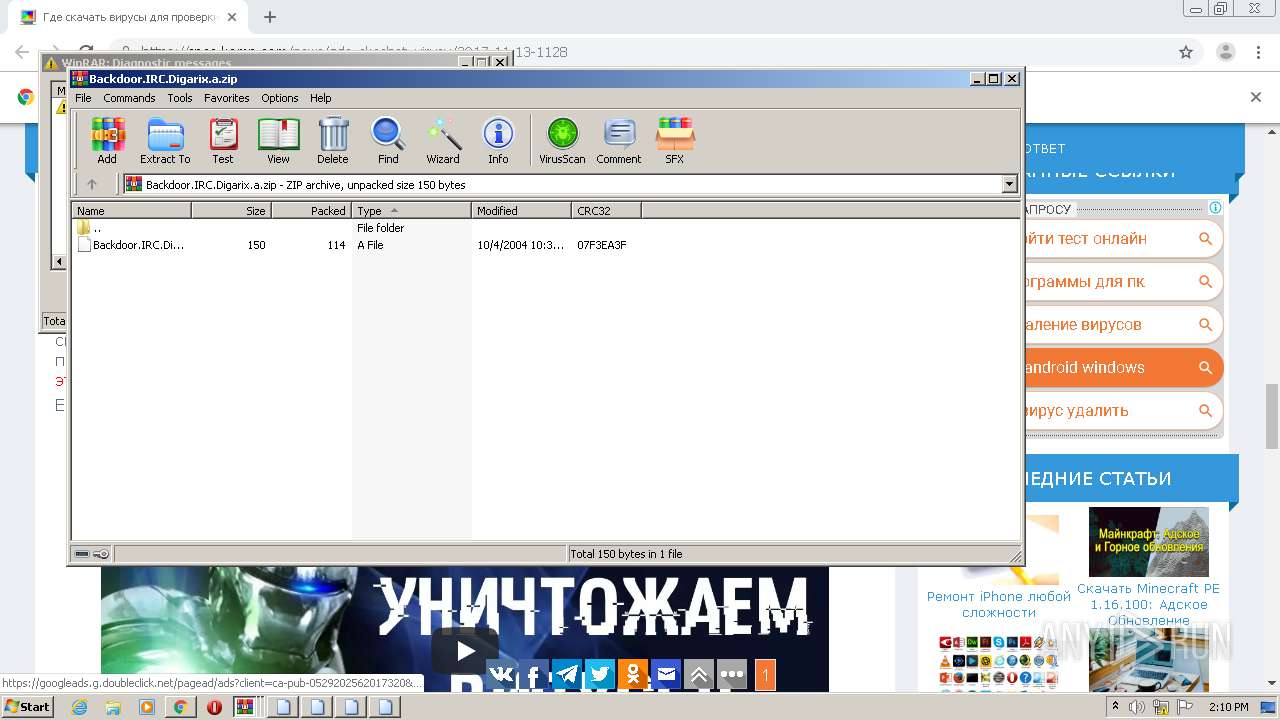
| 1304 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa2216.25944\Backdoor.IRC.Digarix.a.zip | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
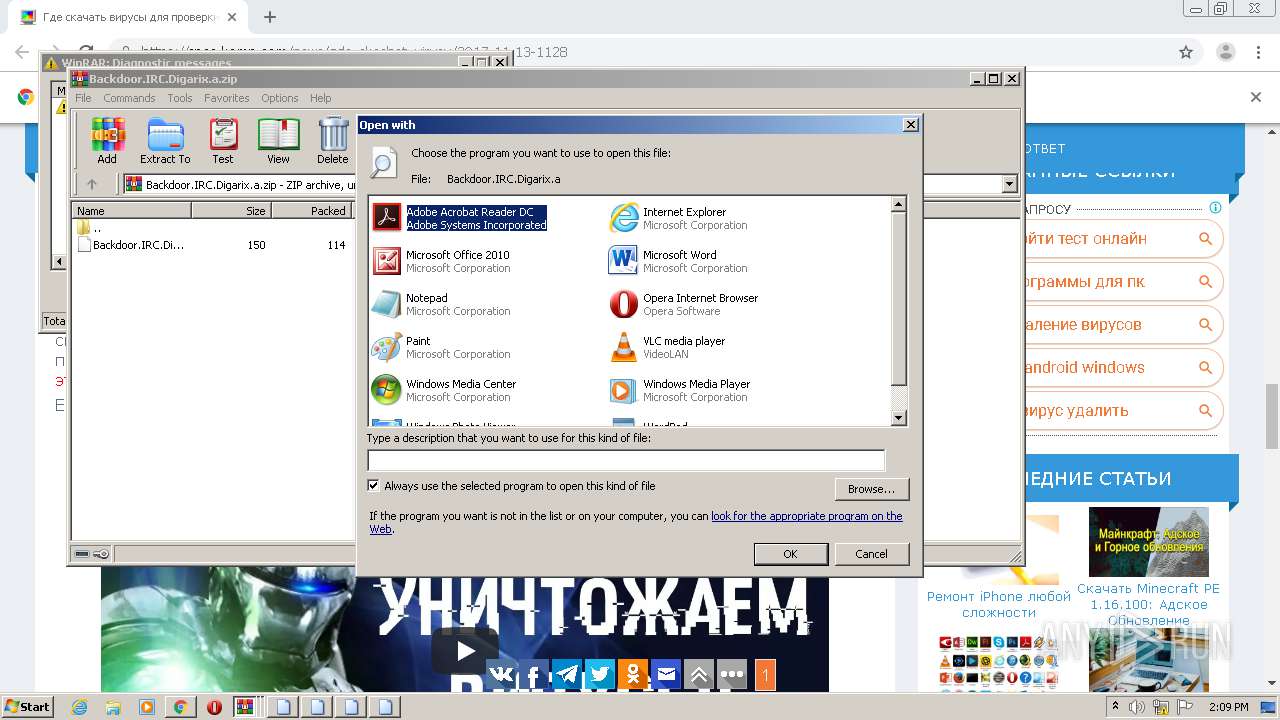
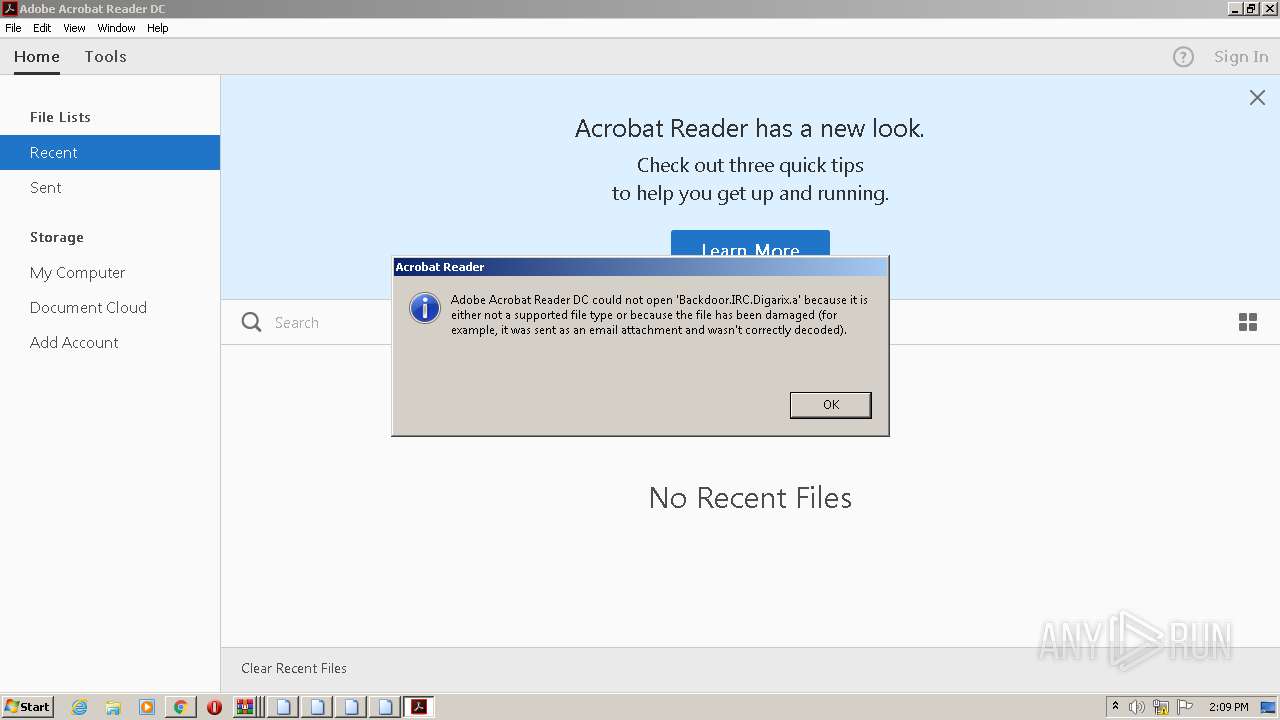
| 1332 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIa2688.29699\Backdoor.IRC.Digarix.a | C:\Windows\system32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
9 011
Read events
8 650
Write events
357
Delete events
4
Modification events
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3692) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2568-13251132332893750 |
Value: 259 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2568-13251132332893750 |
Value: 259 | |||
Executable files
0
Suspicious files
133
Text files
115
Unknown types
14
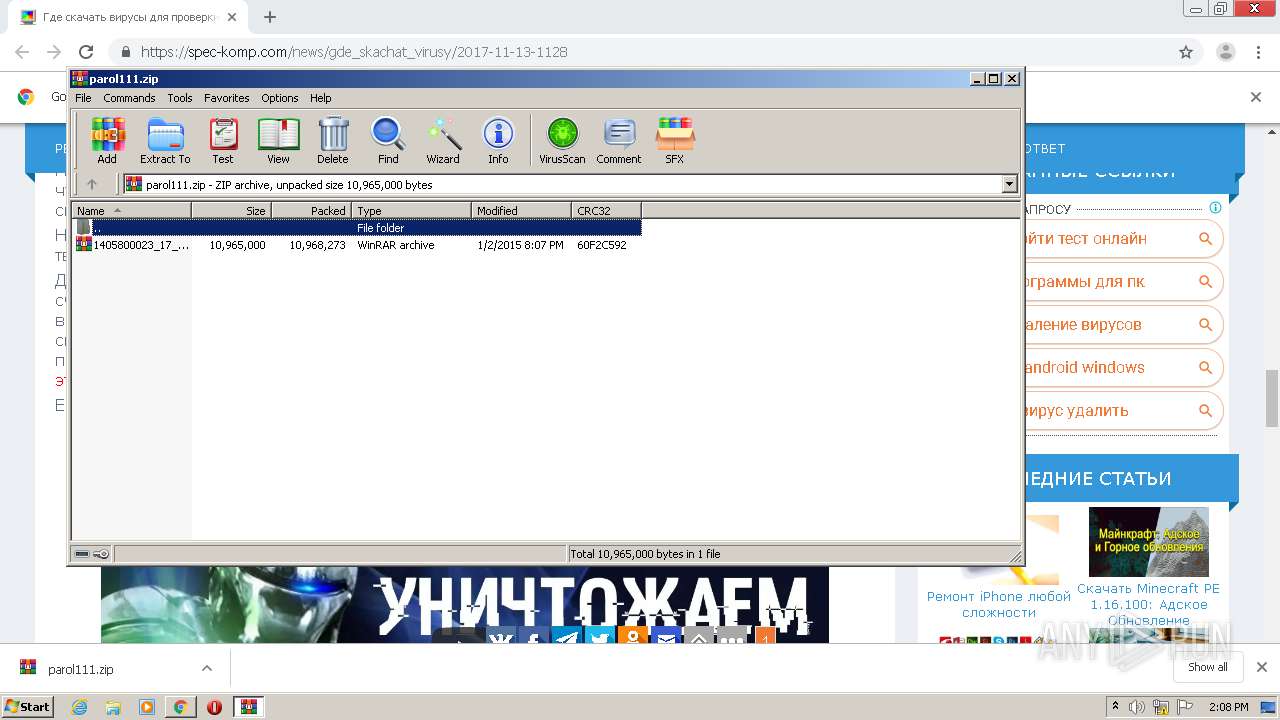
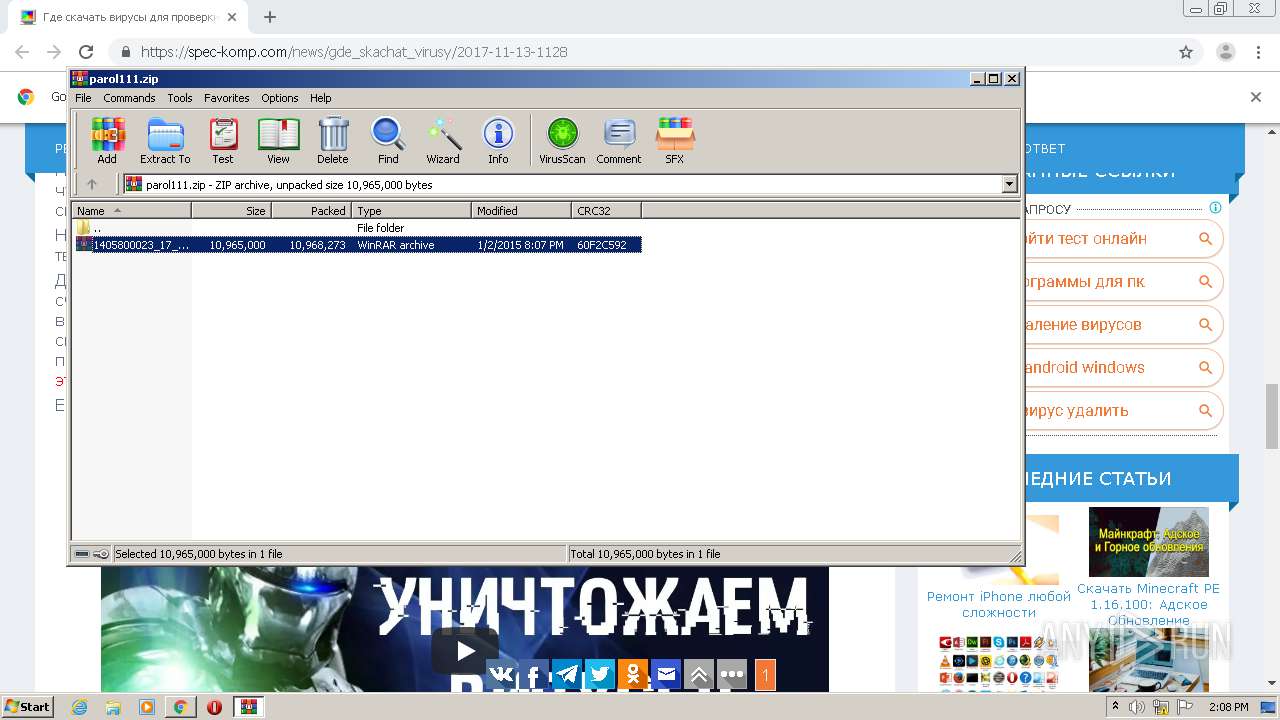
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC3AAAD-A08.pma | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\31db482b-0e34-4372-85e8-854f922fe8a5.tmp | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1278f1.TMP | text | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF12793f.TMP | text | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF127c1d.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
137
DNS requests
79
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1004 | chrome.exe | GET | 200 | 199.59.242.155:80 | http://tracking.bodis.com/tlpv?d=eyJkb21haW5fbmFtZSI6Im9wZW5tYWx3YXJlLm9yZyIsInNlcnZlciI6MTYxLCJ0ZXJtcyI6WyIzMTc5MzgzIiwiMzE3OTM4NCIsIjMxNzkzODUiLCIzMTc5Mzg2IiwiMzE3OTM4NyJdLCJVUkwiOiJodHRwOlwvXC9vcGVubWFsd2FyZS5vcmdcLyIsInJlZmVycmVyIjoiIiwiZHciOjEyODAsImRoIjo1NzIsInJ3IjoxMjgwLCJyaCI6NzIwfQ&t=1606658812&abp=0 | US | — | — | whitelisted |
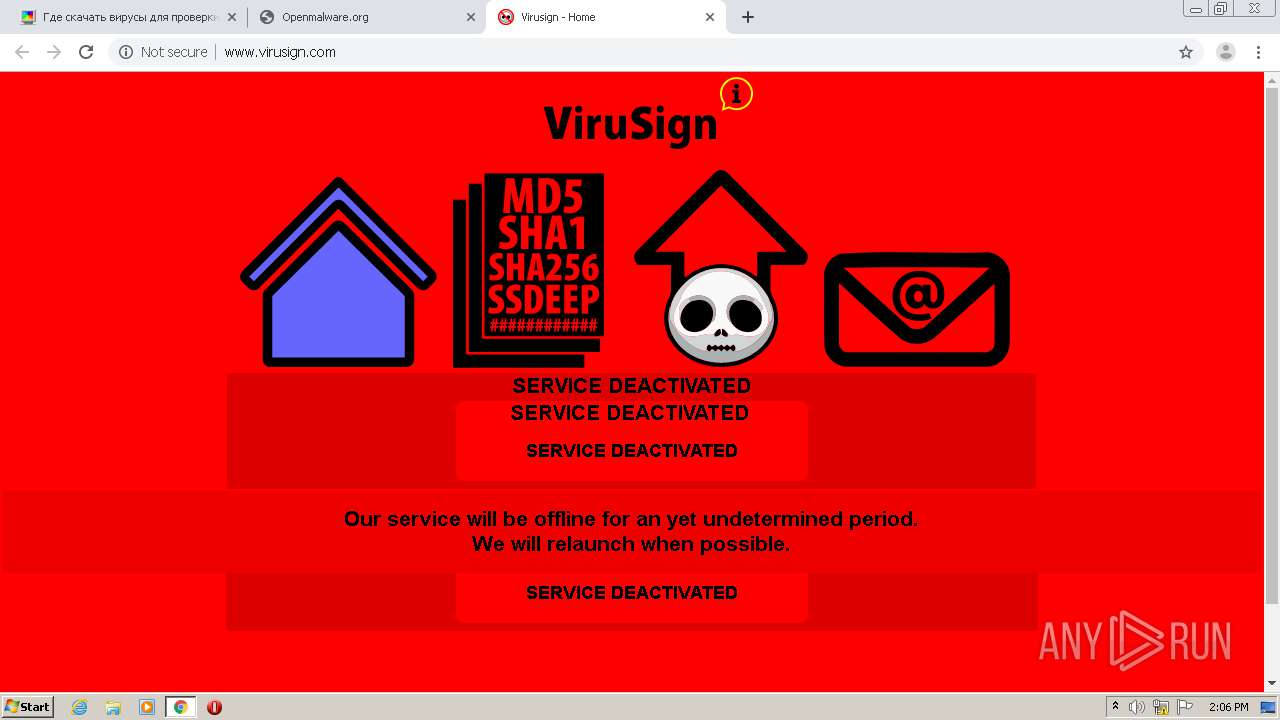
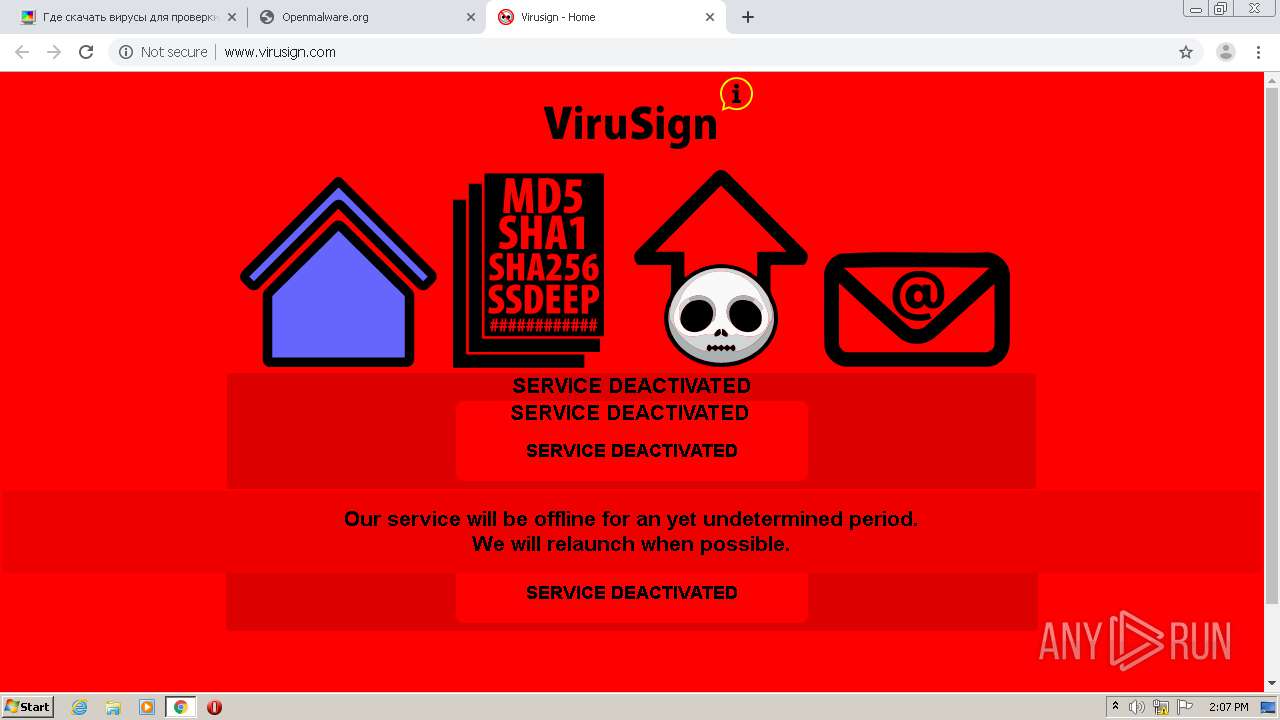
1004 | chrome.exe | GET | — | 65.9.68.13:80 | http://www.virusign.com/images/doc_hashes.svg | US | — | — | whitelisted |
1004 | chrome.exe | GET | — | 65.9.68.13:80 | http://www.virusign.com/images/virusign_logo.svg | US | — | — | whitelisted |
1004 | chrome.exe | GET | — | 65.9.68.13:80 | http://www.virusign.com/images/email.svg | US | — | — | whitelisted |
1004 | chrome.exe | GET | — | 65.9.68.13:80 | http://www.virusign.com/images/info_balloon.svg | US | — | — | whitelisted |
1004 | chrome.exe | GET | — | 65.9.68.13:80 | http://www.virusign.com/images/upload_skull.svg | US | — | — | whitelisted |
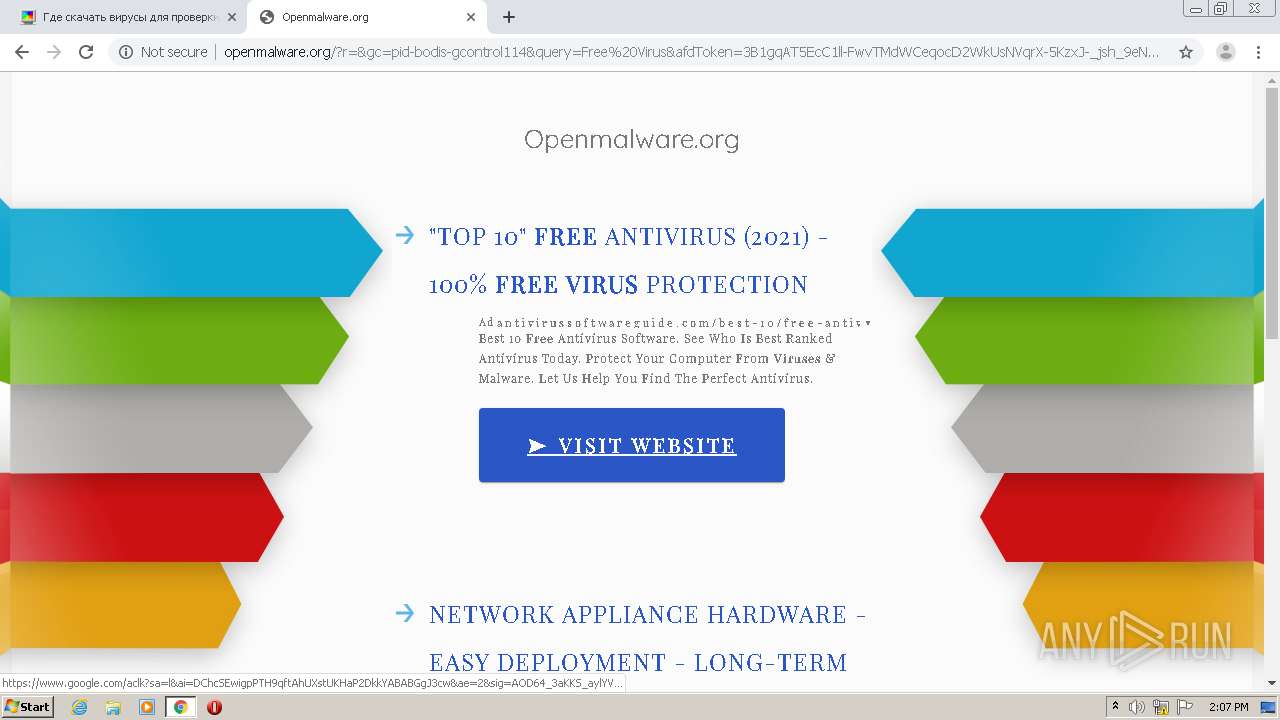
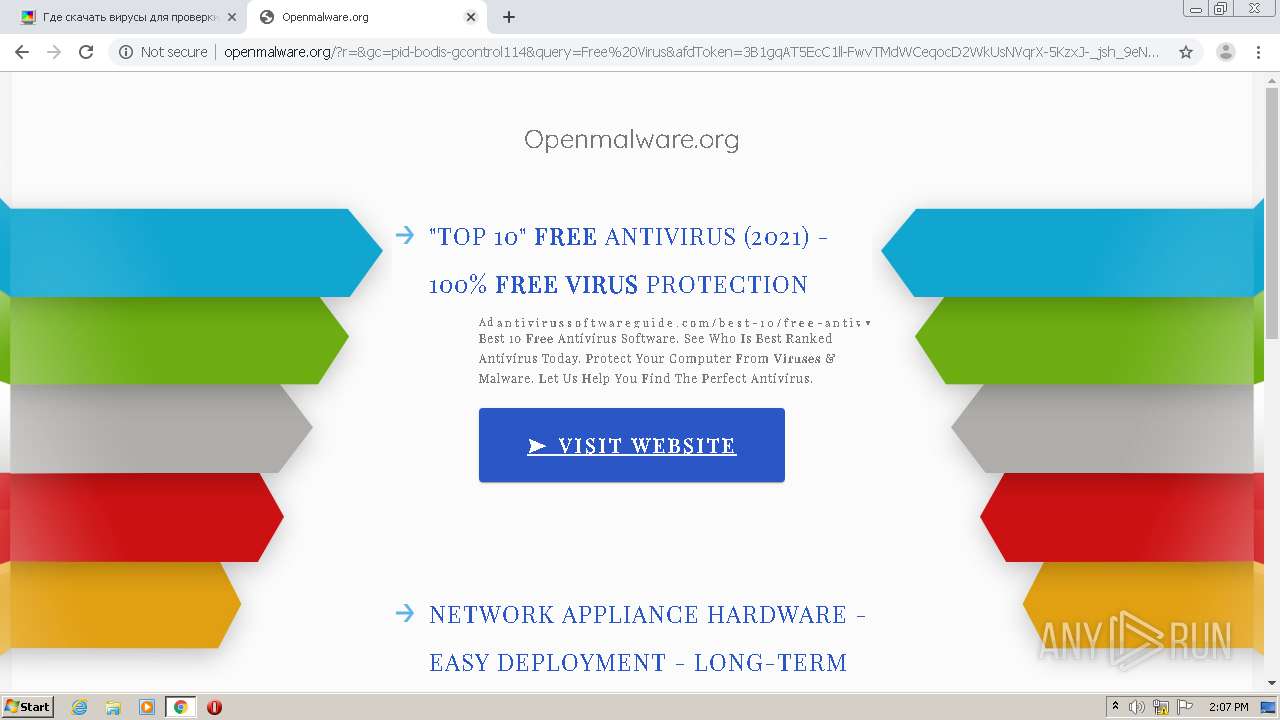
1004 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://openmalware.org/public/legacy/10354/resources/arrows-bg-ext.png | US | image | 1.12 Kb | whitelisted |
1004 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://openmalware.org/glp?r=&u=http%3A%2F%2Fopenmalware.org%2F&rw=1280&rh=720&ww=1280&wh=572 | US | text | 9.16 Kb | whitelisted |
1004 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://openmalware.org/public/legacy/10354/resources/arrows-bg.jpg | US | image | 93.6 Kb | whitelisted |
1004 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://openmalware.org/ | US | html | 3.99 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1004 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
1004 | chrome.exe | 91.199.212.52:80 | crt.sectigo.com | Comodo CA Ltd | GB | suspicious |
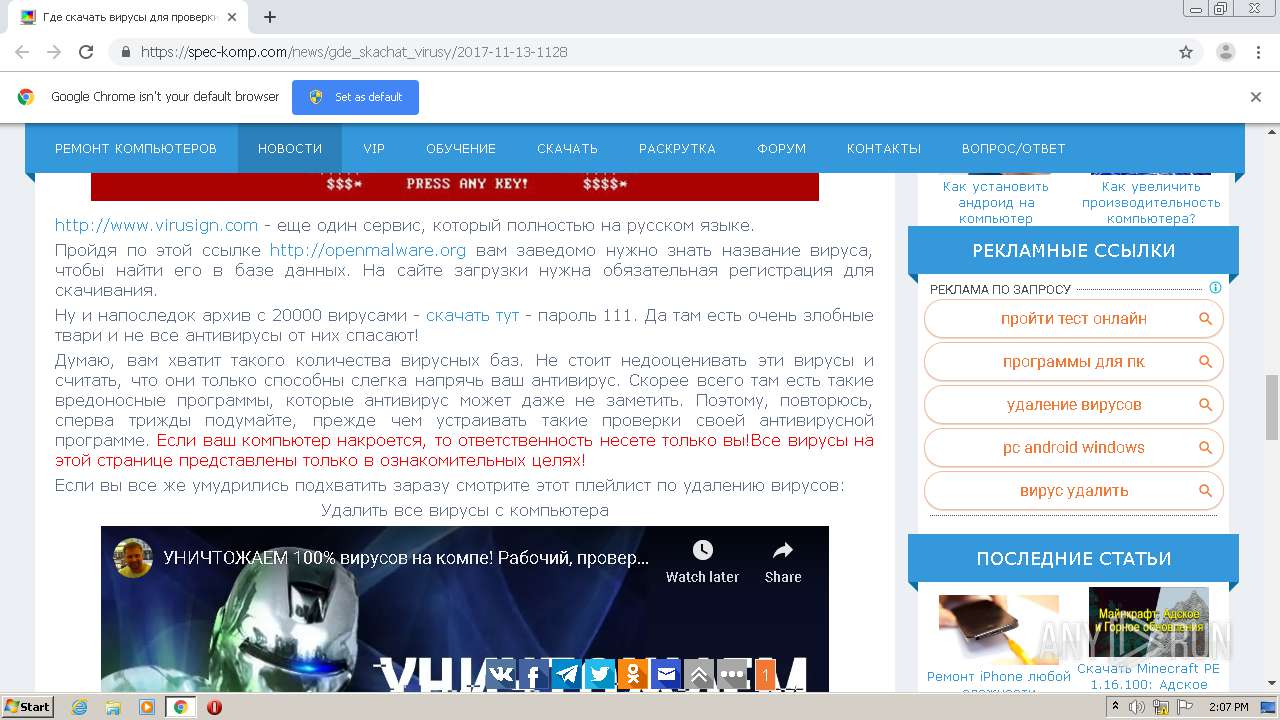
1004 | chrome.exe | 213.174.157.152:443 | spec-komp.com | DataWeb Global Group B.V. | US | suspicious |
1004 | chrome.exe | 172.217.16.130:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
1004 | chrome.exe | 172.217.16.196:443 | www.google.com | Google Inc. | US | whitelisted |
1004 | chrome.exe | 91.231.186.44:443 | sys000.ucoz.net | Krasnaya Zarya Telekom Ltd. | RU | unknown |
1004 | chrome.exe | 95.142.204.162:443 | sun1-87.userapi.com | VKontakte Ltd | RU | unknown |
1004 | chrome.exe | 193.109.247.239:443 | s4.ucoz.net | Filanco, ltd. | RU | suspicious |
1004 | chrome.exe | 142.250.74.206:443 | www.youtube.com | Google Inc. | US | whitelisted |
1004 | chrome.exe | 172.217.21.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
spec-komp.com |
| whitelisted |
accounts.google.com |
| shared |
crt.sectigo.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
s107.ucoz.net |
| suspicious |
sys000.ucoz.net |
| unknown |
www.google.com |
| malicious |
s4.ucoz.net |
| suspicious |
sun1-87.userapi.com |
| unknown |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1004 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |
1004 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |