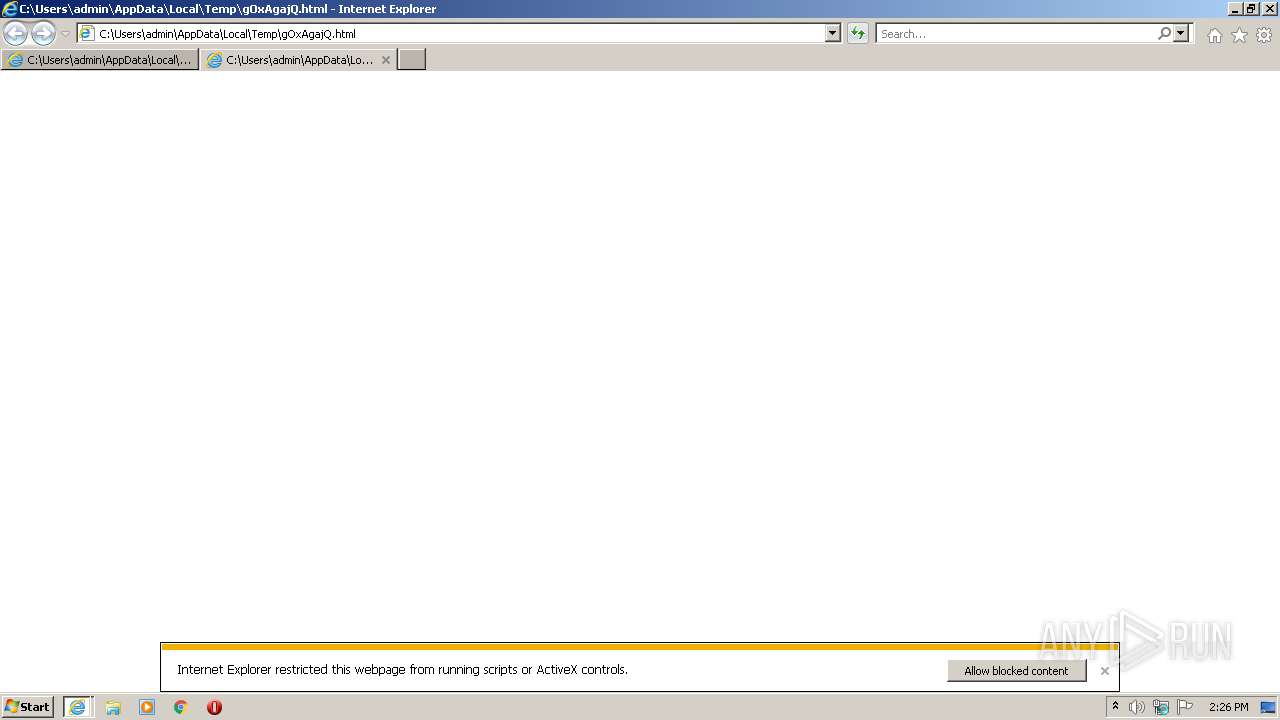
| File name: | gOxAgajQ |
| Full analysis: | https://app.any.run/tasks/e1eab55d-c3ed-4a88-bca8-a8ebafdcaf46 |
| Verdict: | Malicious activity |
| Analysis date: | June 28, 2021, 13:25:57 |
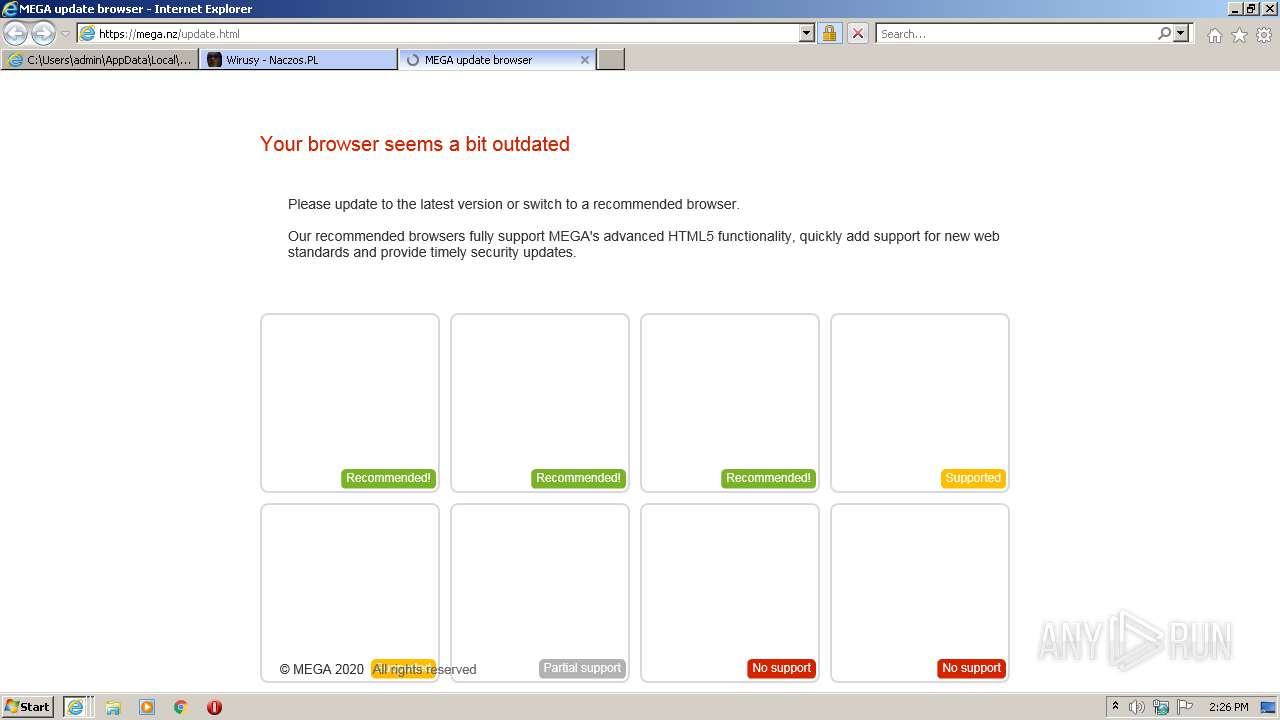
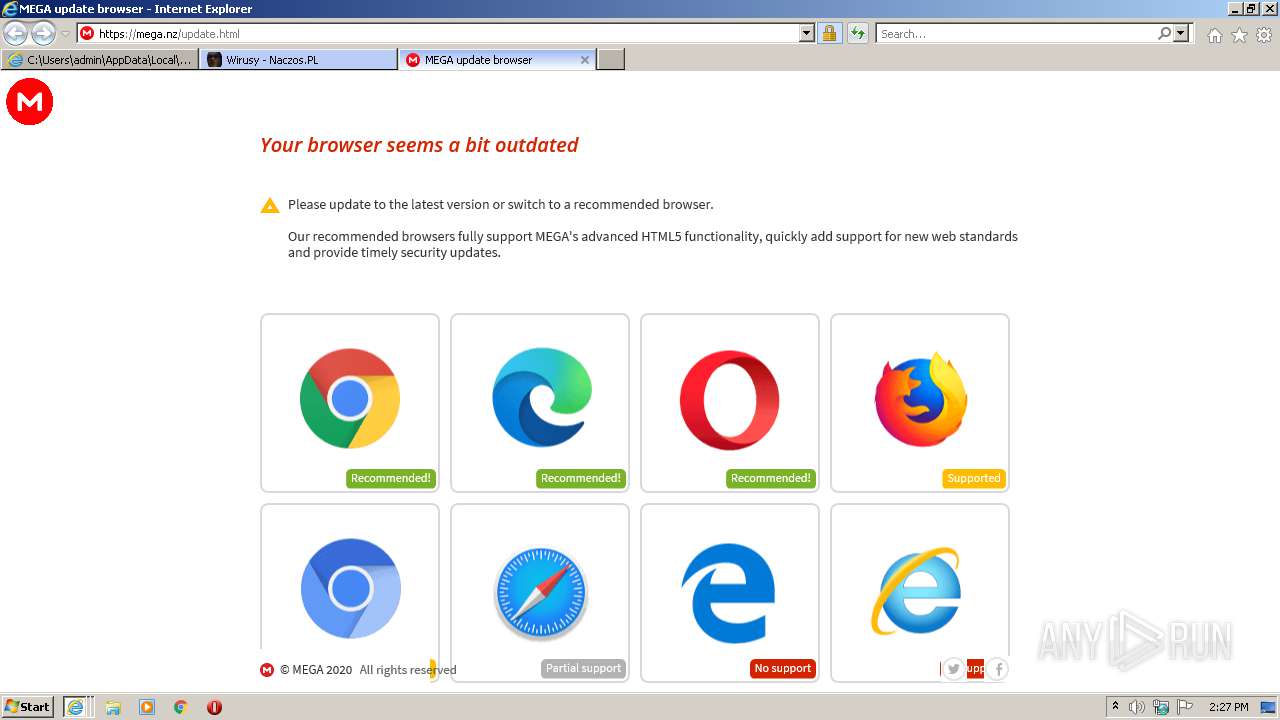
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text |
| MD5: | E3976AF3D3DB04EF3CB48757F61BC4FA |
| SHA1: | CF10EF028B58D853C85BC2023F13D8FD16FFEE66 |
| SHA256: | 72FDD6FB64B663DD438B641B6BB79C2EFBBD30A1EBF861F5783ABCF7E19F0AD8 |
| SSDEEP: | 48:/VkdymF2xI43up8Vs2Of8Nv3P3msU/FUjG:/ruWQf8IsU/FUjG |
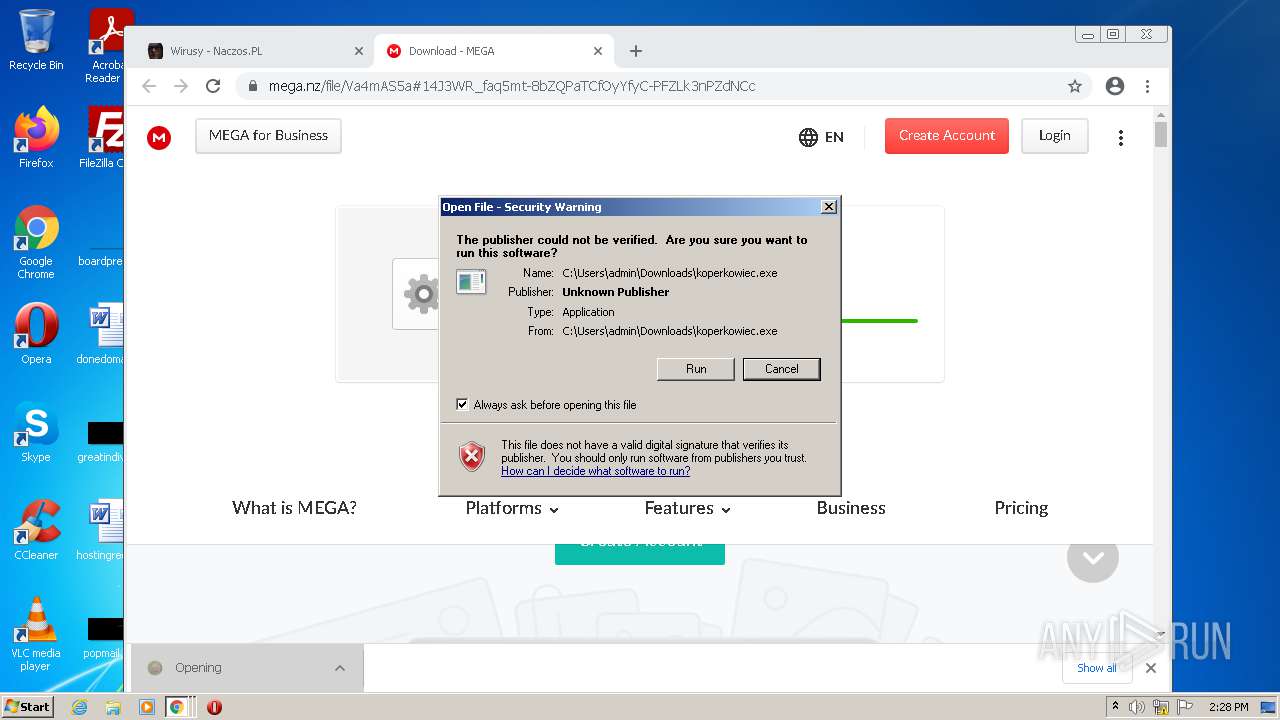
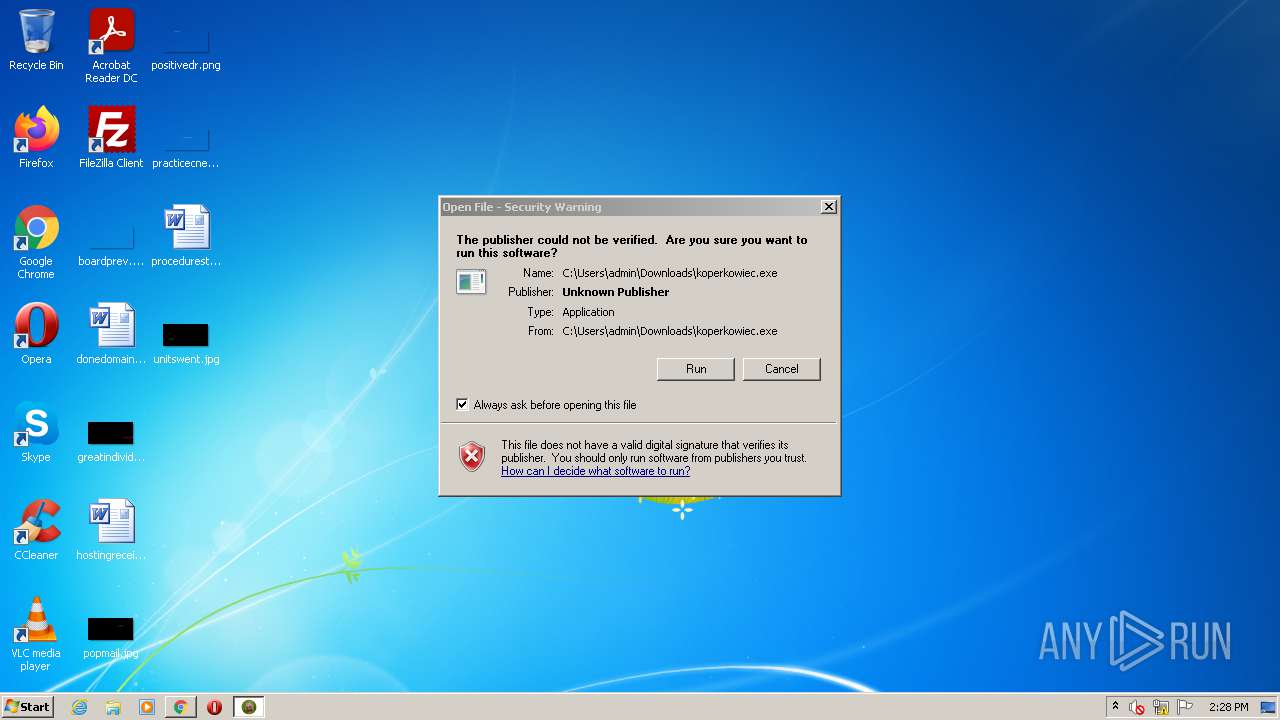
MALICIOUS
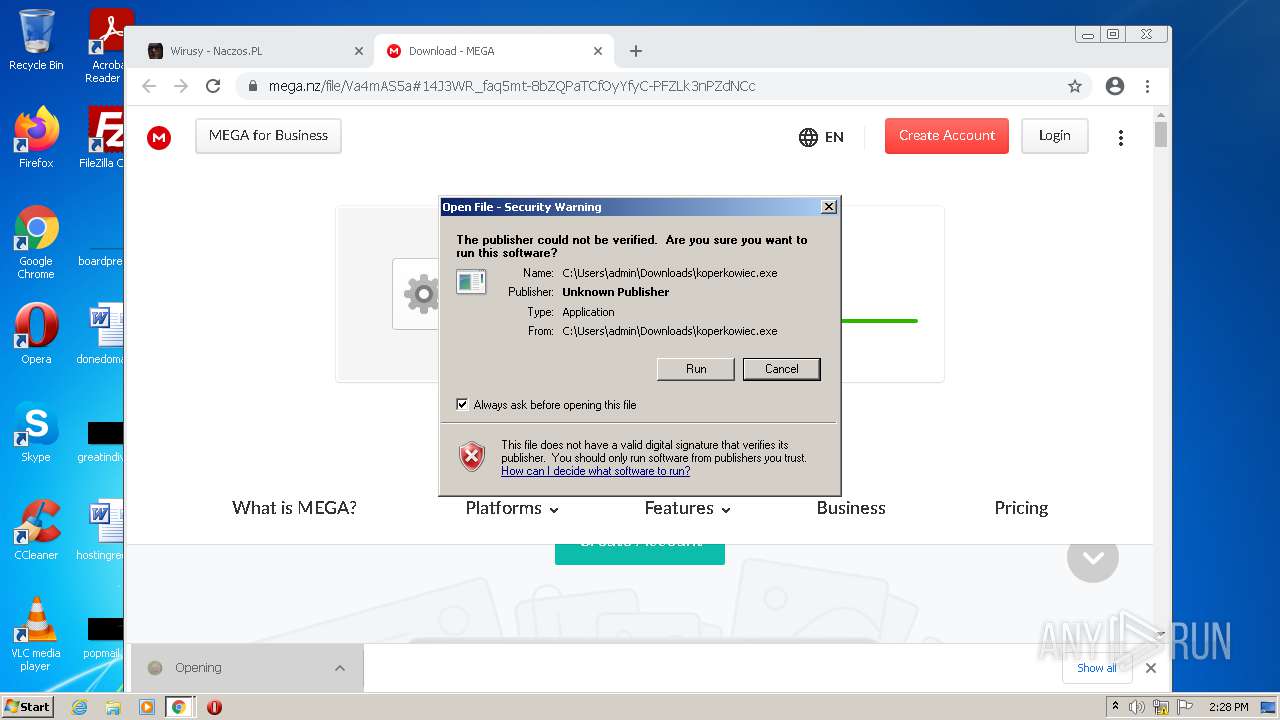
Application was dropped or rewritten from another process
- koperkowiec.exe (PID: 1824)
- koperkowiec.exe (PID: 1460)
Loads dropped or rewritten executable
- koperkowiec.exe (PID: 1824)
- koperkowiec.exe (PID: 1460)
Drops executable file immediately after starts
- koperkowiec.exe (PID: 1824)
- koperkowiec.exe (PID: 1460)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2344)
- iexplore.exe (PID: 3940)
- iexplore.exe (PID: 1540)
- chrome.exe (PID: 2760)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3764)
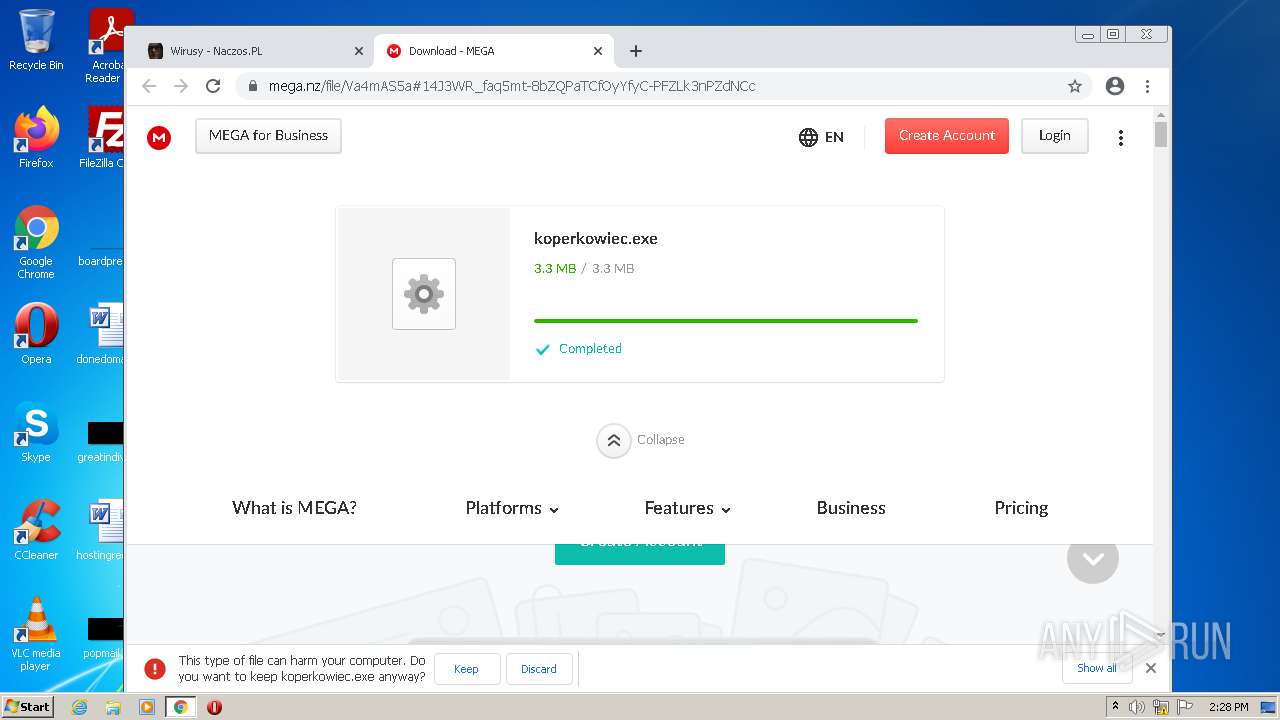
Cleans NTFS data-stream (Zone Identifier)
- chrome.exe (PID: 3764)
Executable content was dropped or overwritten
- koperkowiec.exe (PID: 1824)
- koperkowiec.exe (PID: 1460)
- chrome.exe (PID: 3764)
Drops a file with too old compile date
- koperkowiec.exe (PID: 1824)
- koperkowiec.exe (PID: 1460)
Reads the computer name
- koperkowiec.exe (PID: 1824)
- koperkowiec.exe (PID: 1460)
Checks supported languages
- koperkowiec.exe (PID: 1824)
- koperkowiec.exe (PID: 1460)
INFO
Reads internet explorer settings
- iexplore.exe (PID: 2344)
- iexplore.exe (PID: 3940)
- iexplore.exe (PID: 1540)
Checks Windows Trust Settings
- iexplore.exe (PID: 2100)
- iexplore.exe (PID: 3940)
- iexplore.exe (PID: 1540)
- chrome.exe (PID: 3764)
Checks supported languages
- iexplore.exe (PID: 2100)
- iexplore.exe (PID: 3940)
- iexplore.exe (PID: 2344)
- iexplore.exe (PID: 1540)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 3764)
- chrome.exe (PID: 744)
- chrome.exe (PID: 2608)
- chrome.exe (PID: 3704)
- chrome.exe (PID: 2060)
- chrome.exe (PID: 4088)
- chrome.exe (PID: 1568)
- chrome.exe (PID: 1932)
- chrome.exe (PID: 3840)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 2300)
- chrome.exe (PID: 2340)
- chrome.exe (PID: 3268)
- chrome.exe (PID: 3056)
- chrome.exe (PID: 2360)
- chrome.exe (PID: 2948)
- chrome.exe (PID: 2628)
- chrome.exe (PID: 3692)
- chrome.exe (PID: 1800)
- chrome.exe (PID: 2248)
- chrome.exe (PID: 1748)
- chrome.exe (PID: 3976)
- chrome.exe (PID: 3612)
- chrome.exe (PID: 3968)
- chrome.exe (PID: 1064)
- chrome.exe (PID: 2152)
- chrome.exe (PID: 3144)
- chrome.exe (PID: 2860)
- chrome.exe (PID: 2760)
- chrome.exe (PID: 1172)
- chrome.exe (PID: 3732)
- chrome.exe (PID: 2440)
- chrome.exe (PID: 2220)
- chrome.exe (PID: 3320)
Changes internet zones settings
- iexplore.exe (PID: 2100)
Reads the computer name
- iexplore.exe (PID: 2344)
- iexplore.exe (PID: 2100)
- iexplore.exe (PID: 3940)
- iexplore.exe (PID: 1540)
- chrome.exe (PID: 3764)
- chrome.exe (PID: 3704)
- chrome.exe (PID: 744)
- chrome.exe (PID: 2300)
- chrome.exe (PID: 1932)
- chrome.exe (PID: 2152)
- chrome.exe (PID: 1748)
- chrome.exe (PID: 2760)
- chrome.exe (PID: 3612)
- chrome.exe (PID: 3144)
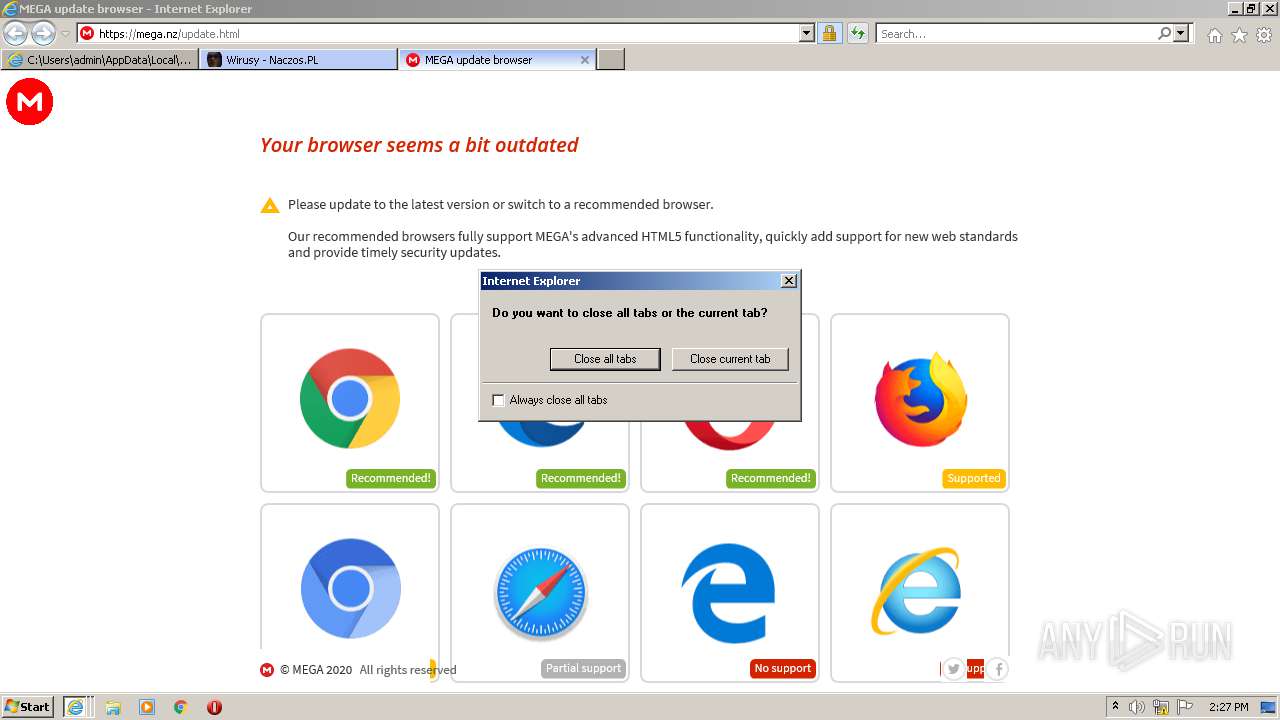
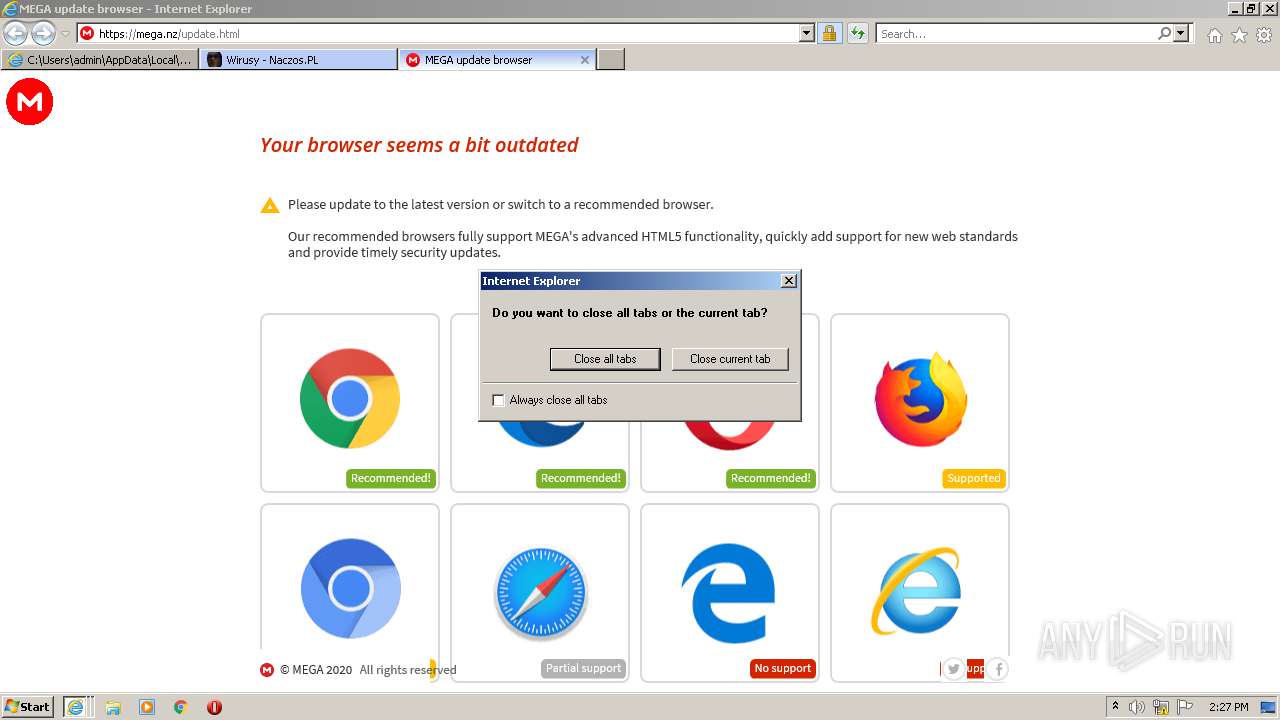
Application launched itself
- iexplore.exe (PID: 2100)
- iexplore.exe (PID: 2344)
- chrome.exe (PID: 3764)
Creates files in the user directory
- iexplore.exe (PID: 3940)
- iexplore.exe (PID: 2100)
Changes settings of System certificates
- iexplore.exe (PID: 2100)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2100)
Reads settings of System Certificates
- iexplore.exe (PID: 2100)
- iexplore.exe (PID: 3940)
- iexplore.exe (PID: 1540)
- chrome.exe (PID: 3704)
Reads the date of Windows installation
- iexplore.exe (PID: 2100)
- chrome.exe (PID: 3612)
Reads the hosts file
- chrome.exe (PID: 3704)
- chrome.exe (PID: 3764)
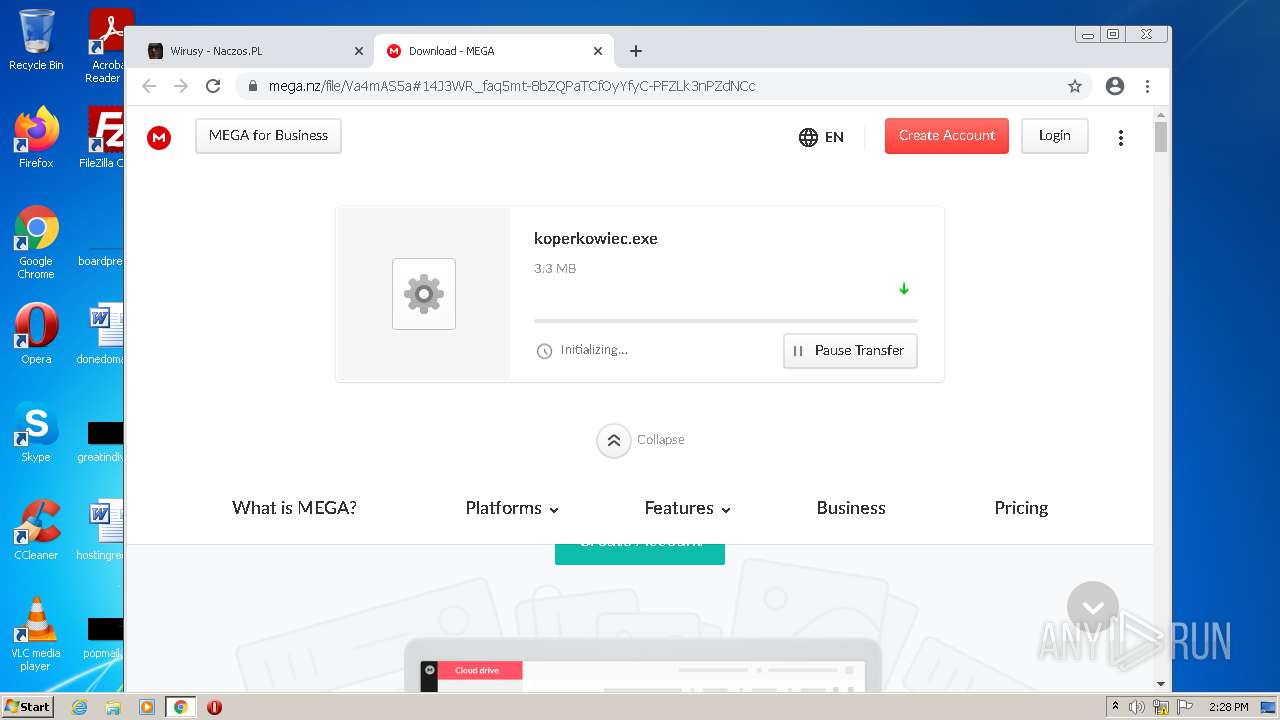
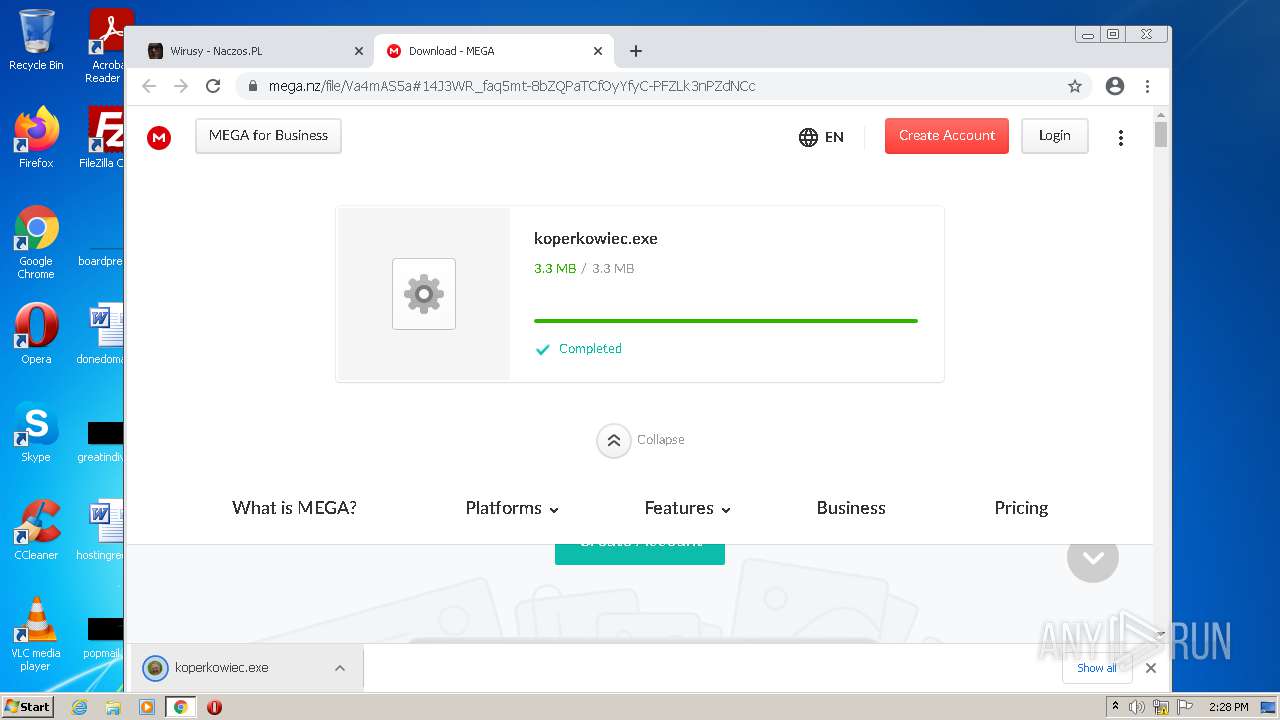
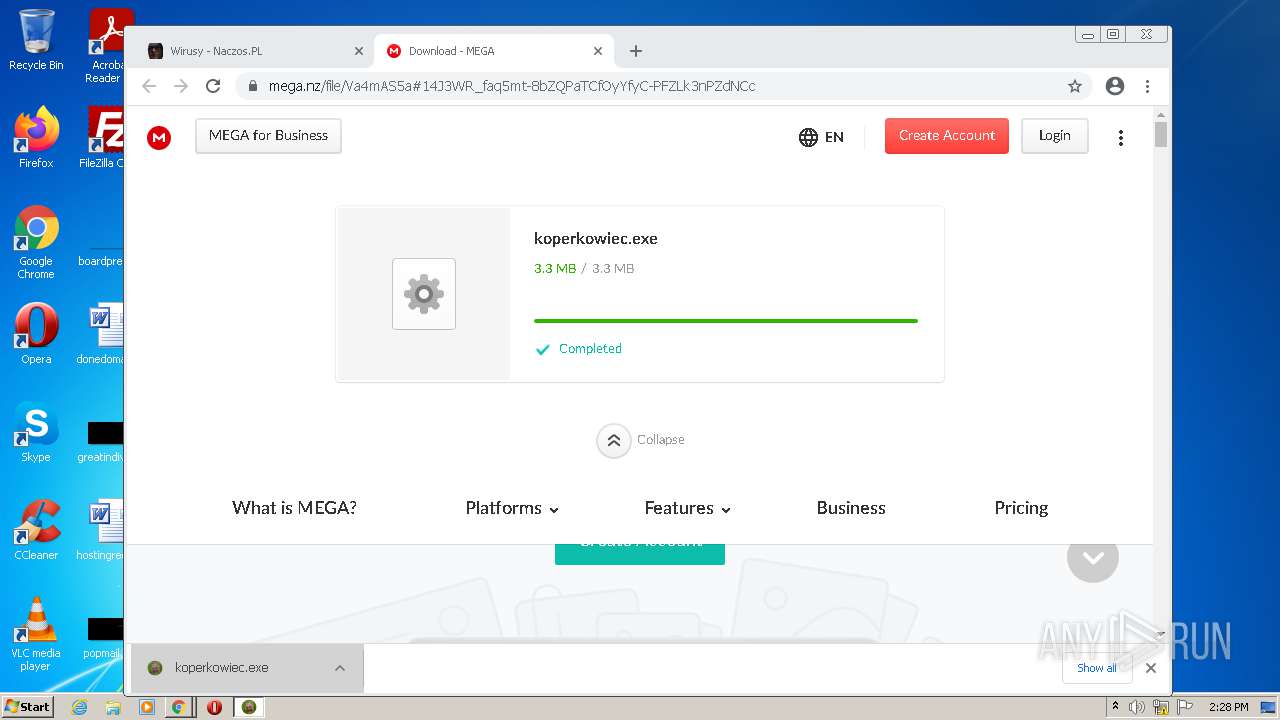
Manual execution by user
- chrome.exe (PID: 3764)
- koperkowiec.exe (PID: 1460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| appleItunesApp: | app-id=706857885 |
|---|---|
| viewport: | width=device-width, initial-scale=1.0, maximum-scale=1.0, user-scalable=0 |
| referrer: | strict-origin-when-cross-origin |
| ContentType: | text/html, charset=UTF-8 |
| HTTPEquivXUACompatible: | IE=Edge |
Total processes
79
Monitored processes
41
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1048,5102417002454968430,18382182353227914364,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1060 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,5102417002454968430,18382182353227914364,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3296 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1048,5102417002454968430,18382182353227914364,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=2176 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1460 | "C:\Users\admin\Downloads\koperkowiec.exe" | C:\Users\admin\Downloads\koperkowiec.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2100 CREDAT:857358 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,5102417002454968430,18382182353227914364,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1924 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1048,5102417002454968430,18382182353227914364,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1732 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1048,5102417002454968430,18382182353227914364,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4156 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1824 | "C:\Users\admin\Downloads\koperkowiec.exe" | C:\Users\admin\Downloads\koperkowiec.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1048,5102417002454968430,18382182353227914364,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2700 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
37 674
Read events
37 271
Write events
398
Delete events
5
Modification events
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 739390448 | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30895137 | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30895137 | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
19
Suspicious files
139
Text files
363
Unknown types
53
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3940 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\X8F276SX.txt | text | |
MD5:— | SHA256:— | |||
| 3940 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\0T8B6J0G.txt | text | |
MD5:— | SHA256:— | |||
| 2100 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3940 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\qsml[1].htm | xml | |
MD5:— | SHA256:— | |||
| 3940 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\qsml[3].xml | xml | |
MD5:— | SHA256:— | |||
| 3940 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\5Z7F3G7O.htm | html | |
MD5:— | SHA256:— | |||
| 2100 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3940 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\qsml[1].xml | xml | |
MD5:— | SHA256:— | |||
| 3940 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\QF2Q6ATU.txt | text | |
MD5:— | SHA256:— | |||
| 3940 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\S0HGRDIF.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
89
DNS requests
40
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1776 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | — | — | whitelisted |
2100 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
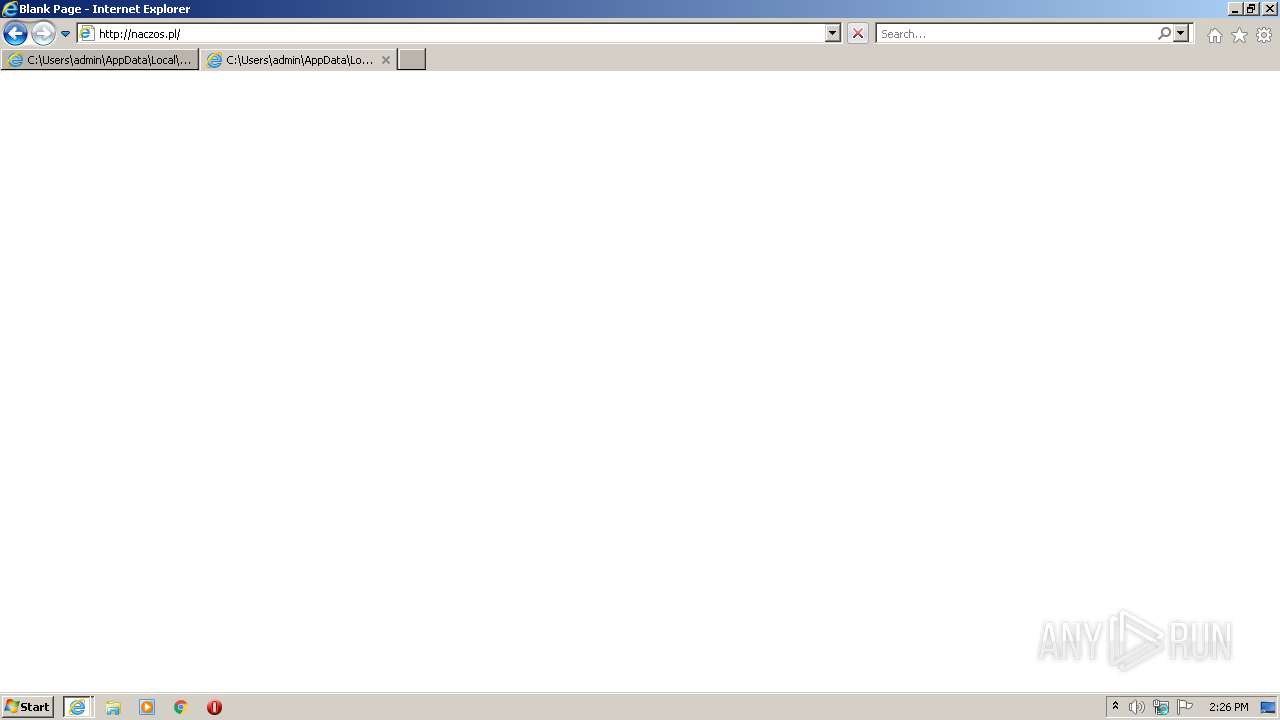
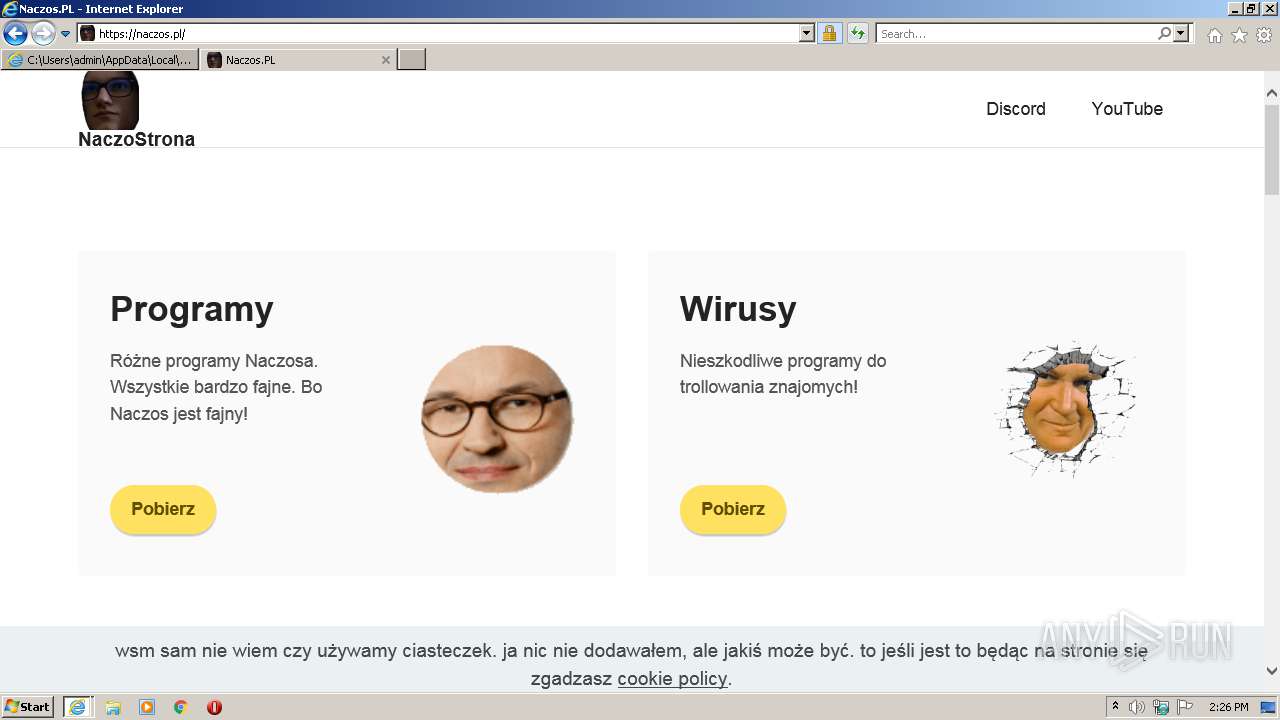
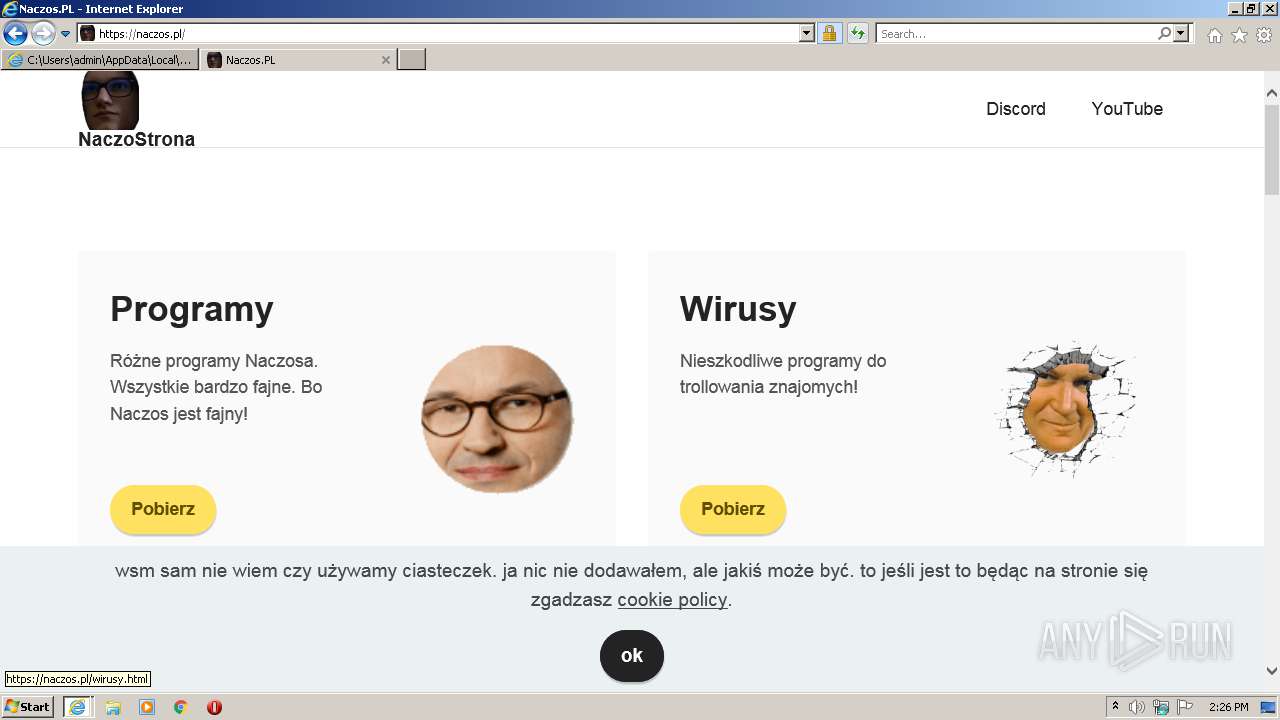
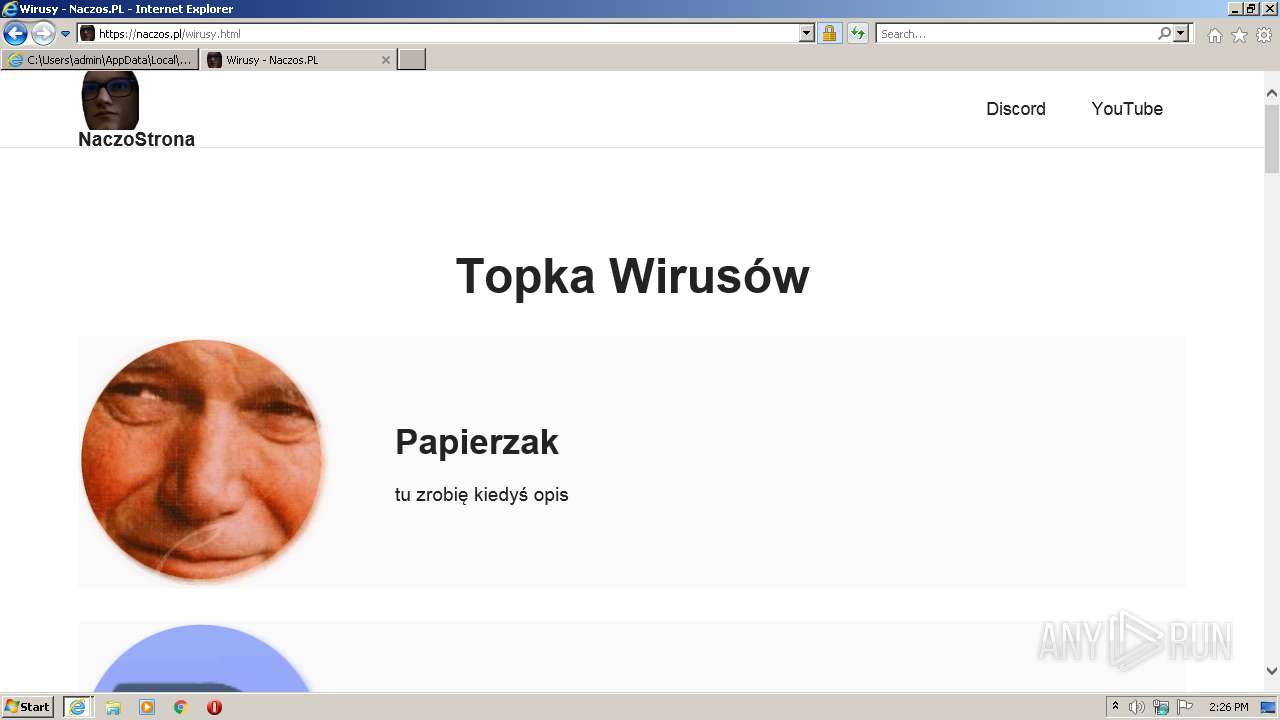
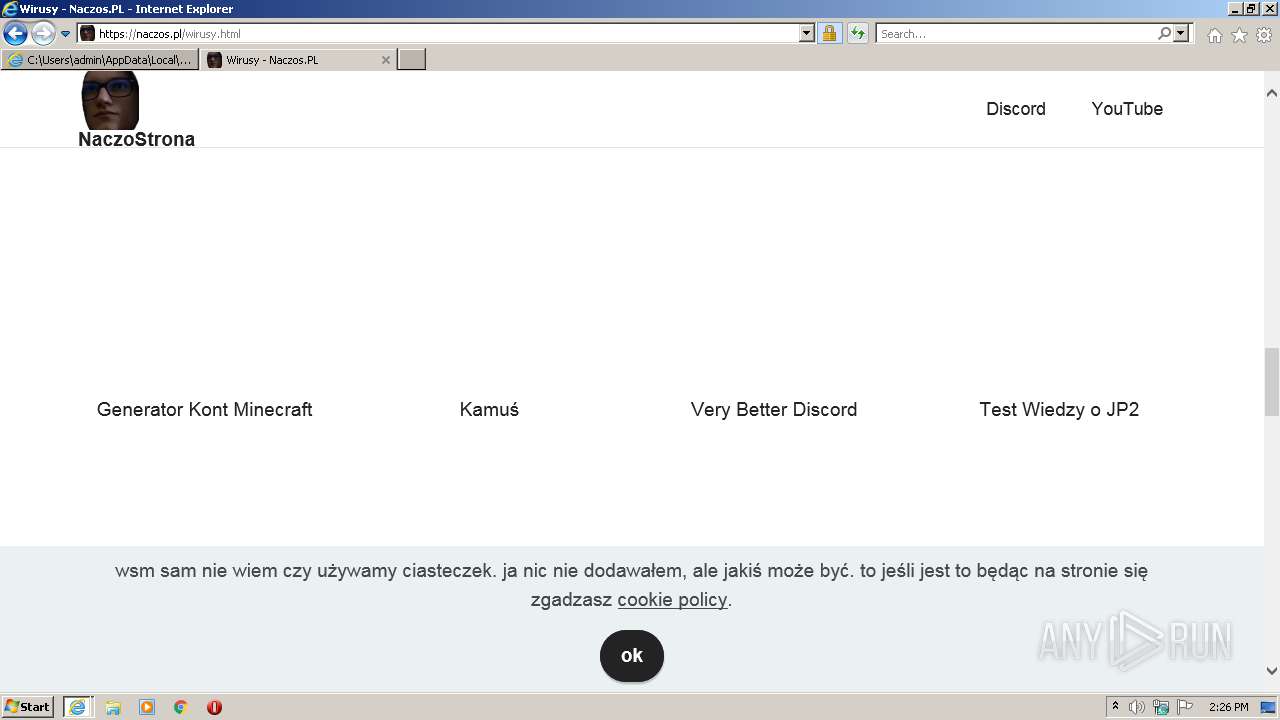
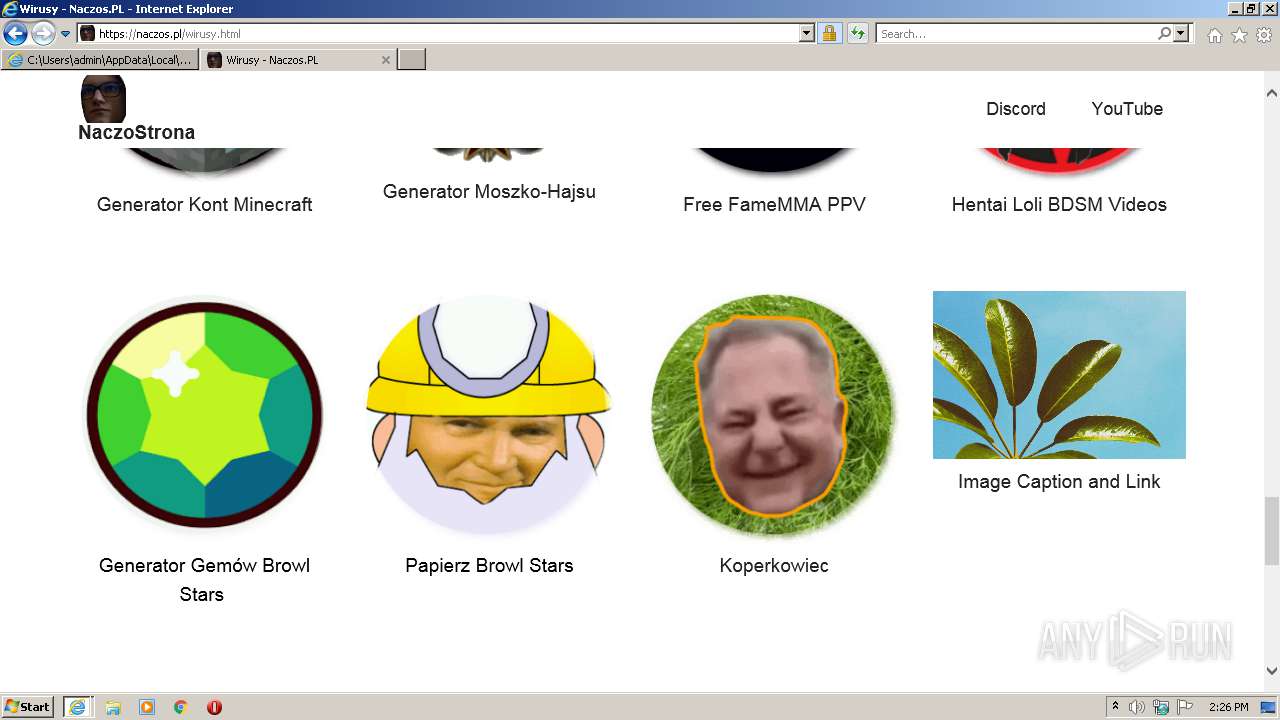
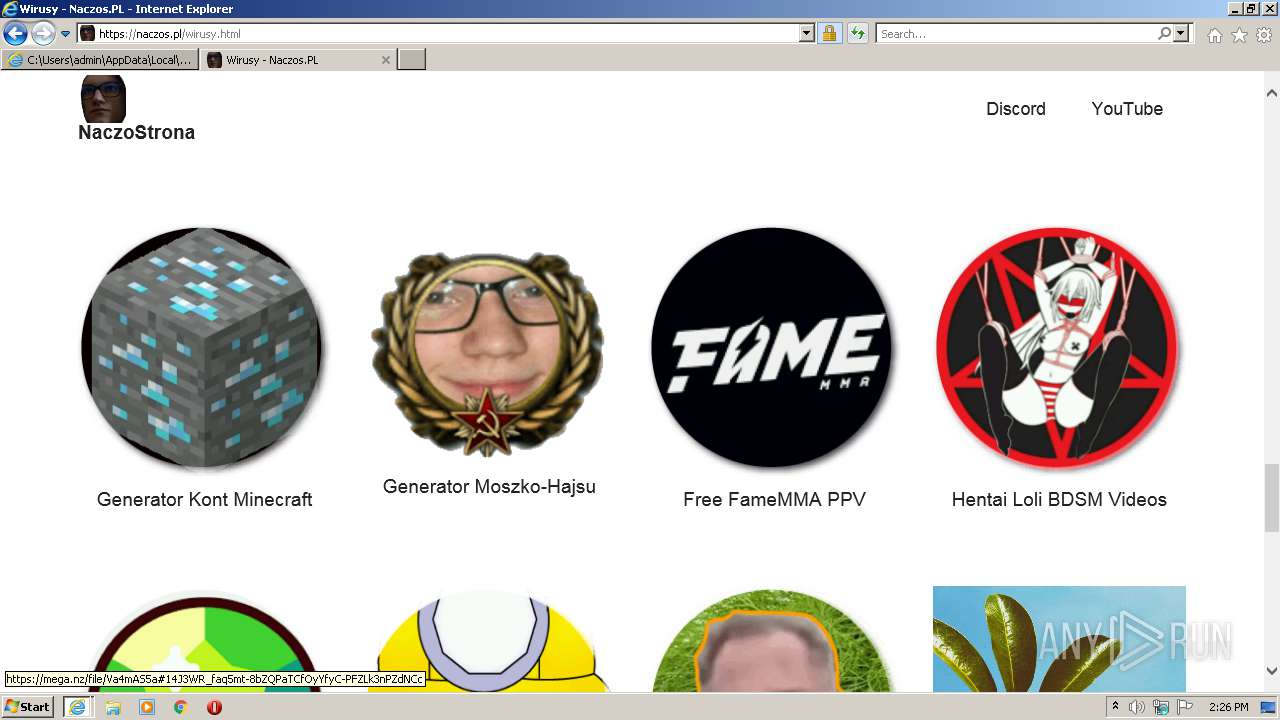
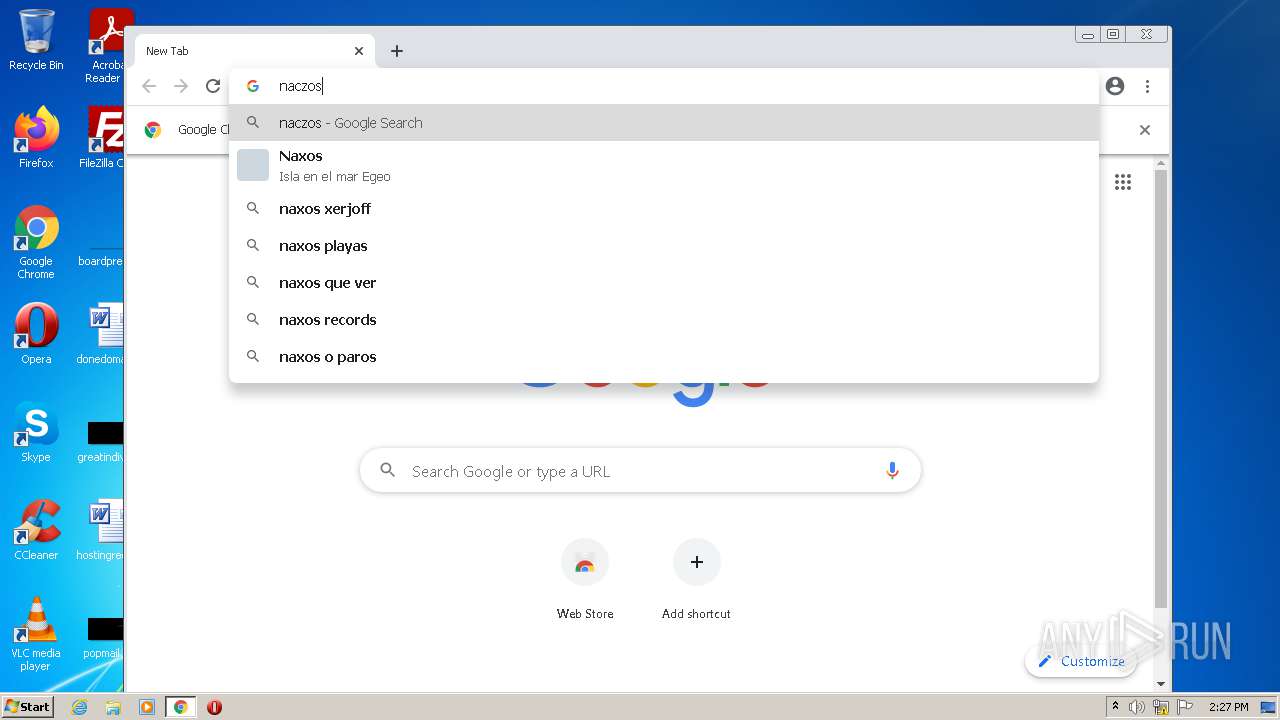
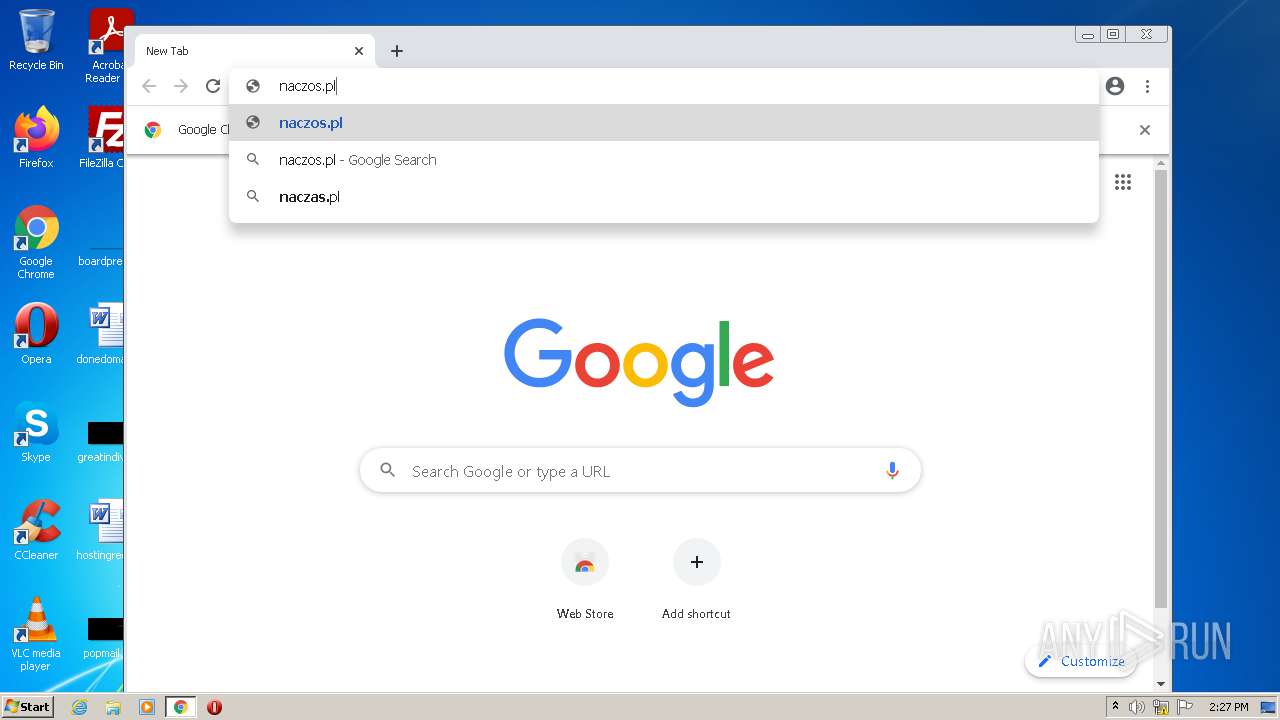
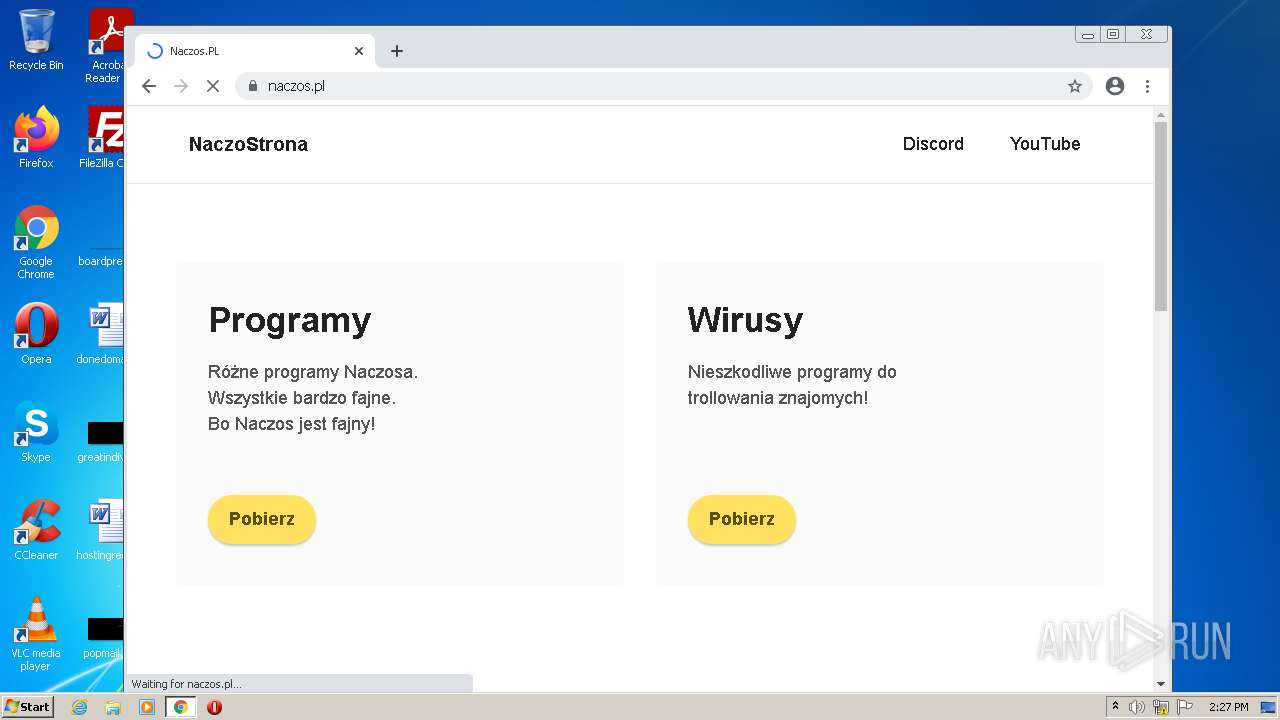
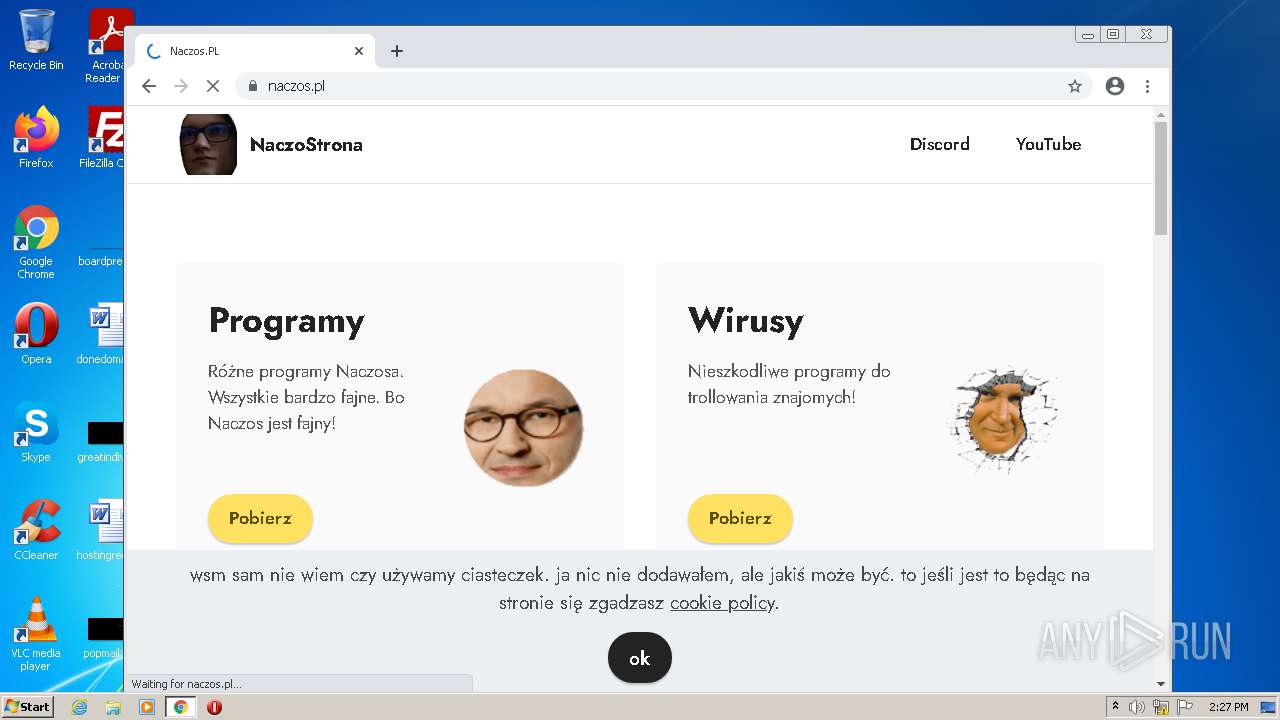
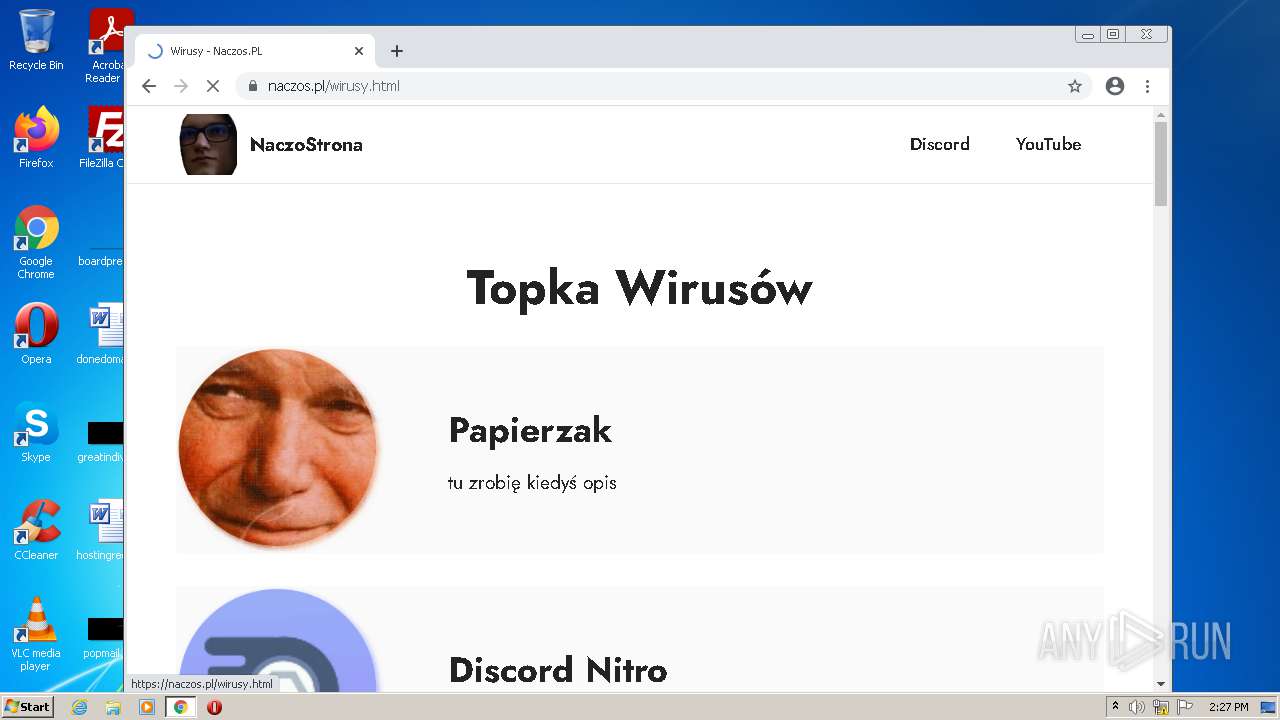
3940 | iexplore.exe | GET | 301 | 91.134.193.82:80 | http://naczos.pl/ | FR | html | 226 b | malicious |
1776 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | binary | 9.91 Kb | whitelisted |
3940 | iexplore.exe | GET | 200 | 2.16.186.10:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | unknown | der | 1.16 Kb | whitelisted |
3940 | iexplore.exe | GET | 200 | 2.16.186.10:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgRsIrv%2BmReOQ9uhV24iDvdOWw%3D%3D | unknown | der | 503 b | shared |
1776 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | binary | 43.6 Kb | whitelisted |
1776 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | binary | 5.76 Kb | whitelisted |
3704 | chrome.exe | GET | 301 | 91.134.193.82:80 | http://naczos.pl/ | FR | html | 226 b | malicious |
1776 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | binary | 7.10 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2100 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3940 | iexplore.exe | 2.16.186.10:80 | crl.identrust.com | Akamai International B.V. | — | whitelisted |
2100 | iexplore.exe | 67.27.158.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
2100 | iexplore.exe | 67.26.81.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
2100 | iexplore.exe | 91.134.193.82:443 | naczos.pl | OVH SAS | FR | unknown |
3940 | iexplore.exe | 23.45.105.185:80 | x1.c.lencr.org | Akamai International B.V. | NL | unknown |
2100 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1540 | iexplore.exe | 23.55.163.58:80 | r3.o.lencr.org | Akamai International B.V. | US | unknown |
1540 | iexplore.exe | 66.203.127.18:443 | mega.nz | RealNetworks, Inc. | US | suspicious |
1540 | iexplore.exe | 66.203.127.11:443 | eu.static.mega.co.nz | RealNetworks, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
naczos.pl |
| malicious |
crl.identrust.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |