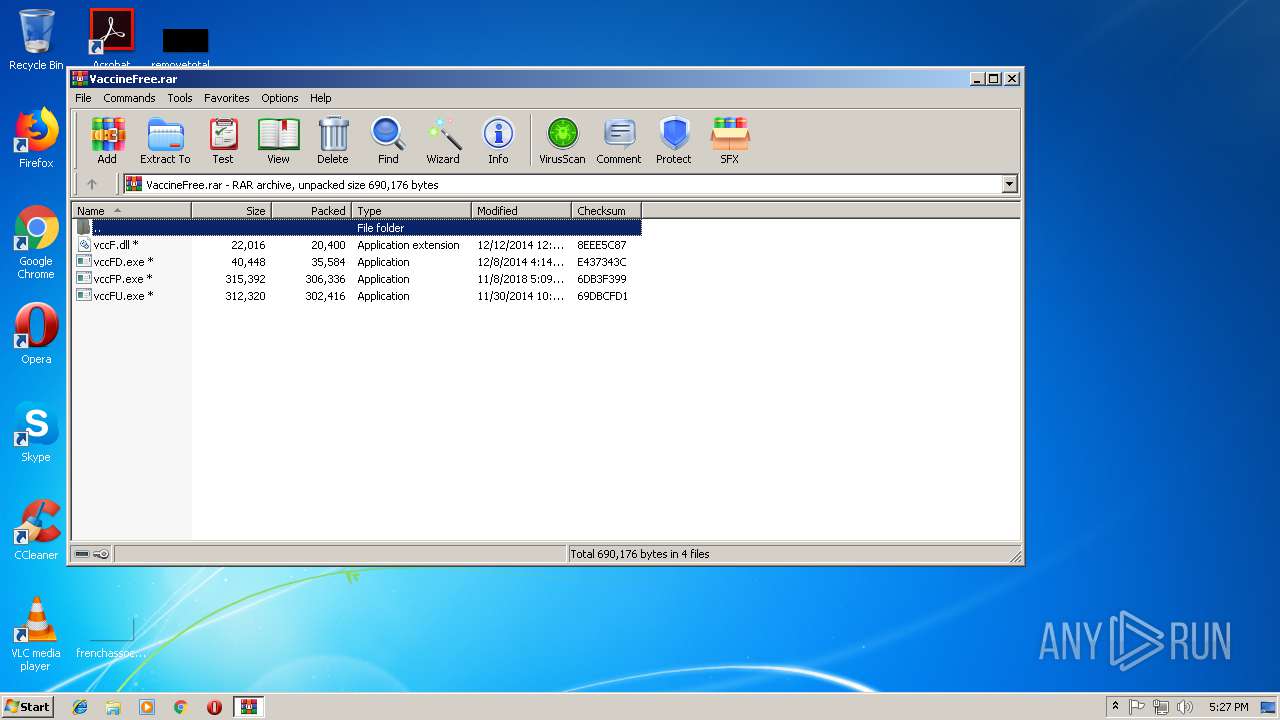
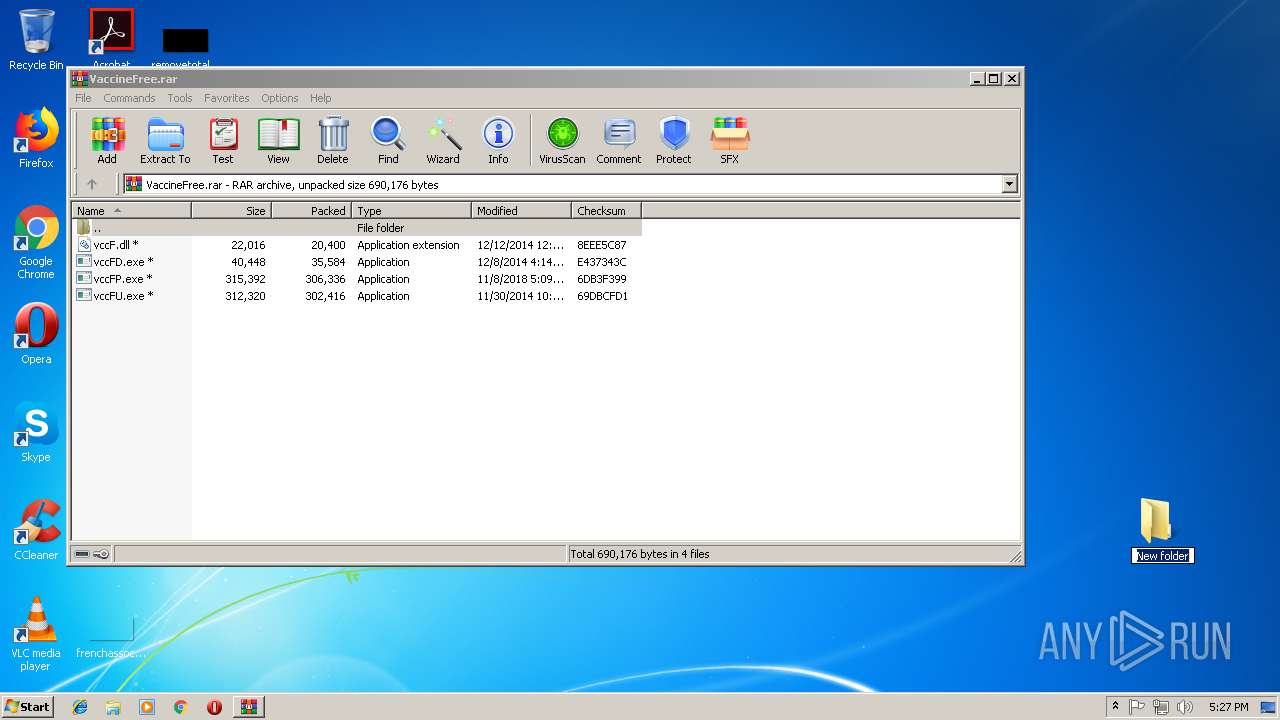
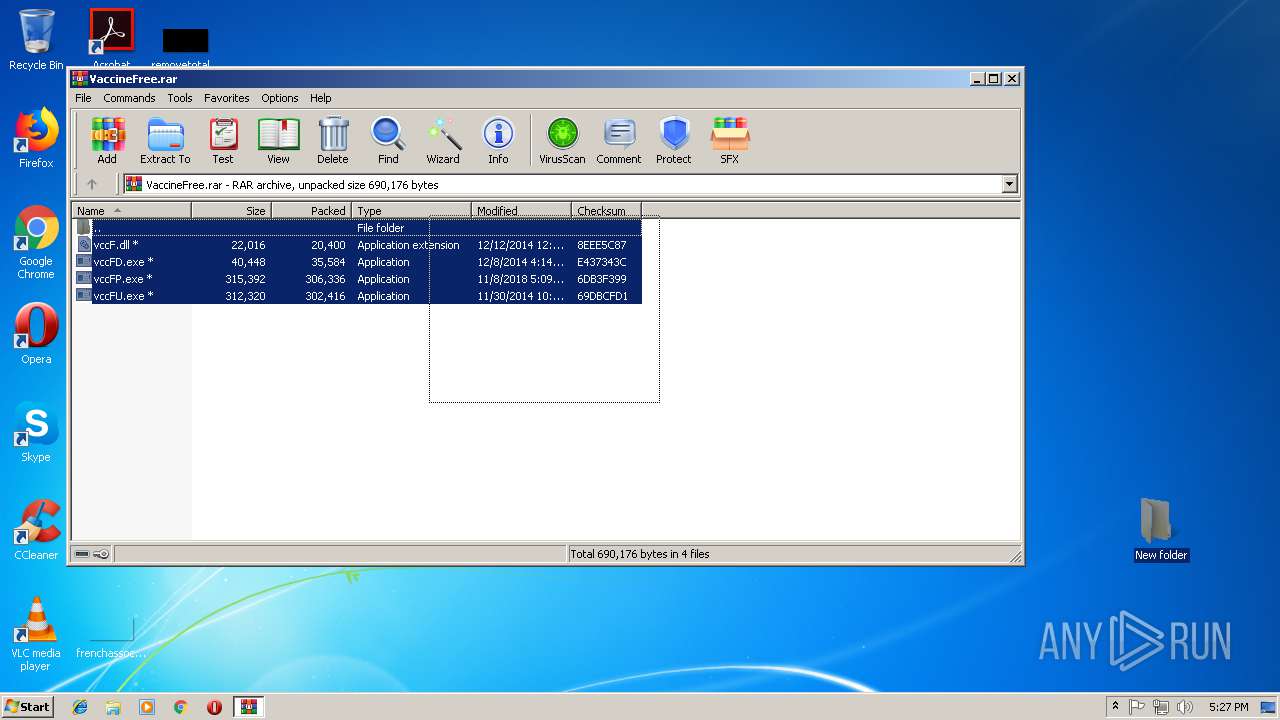
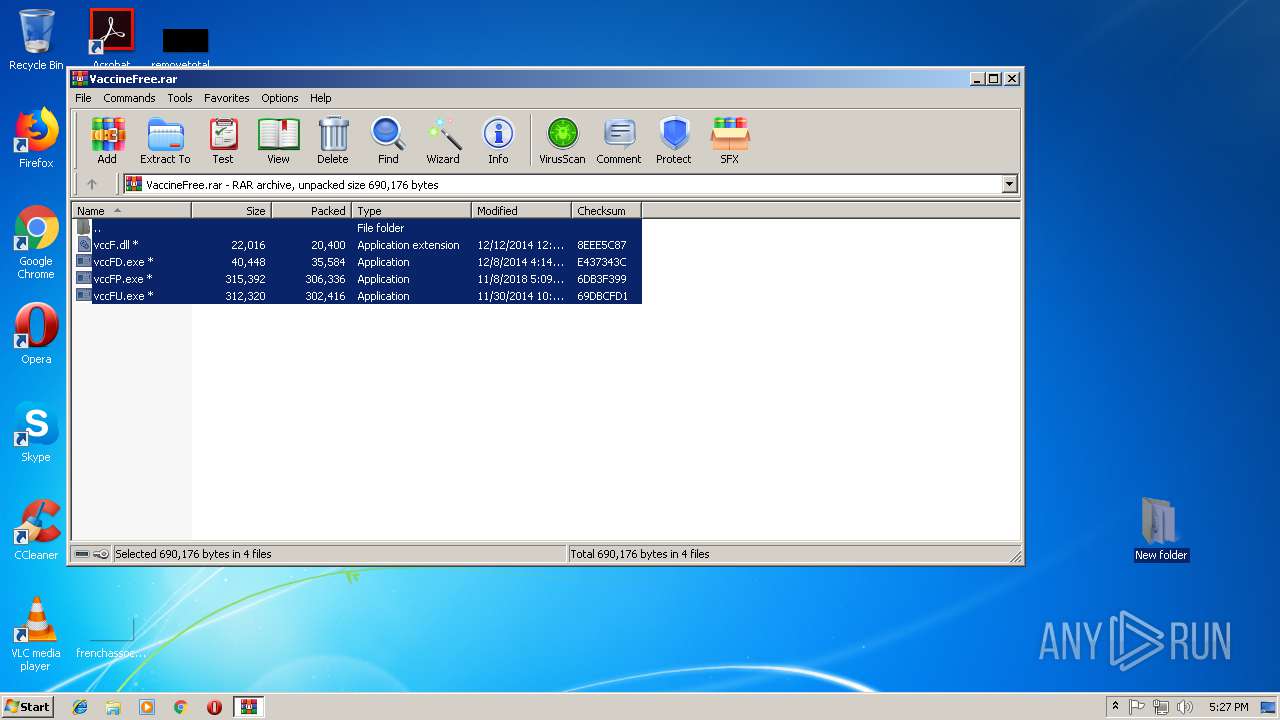
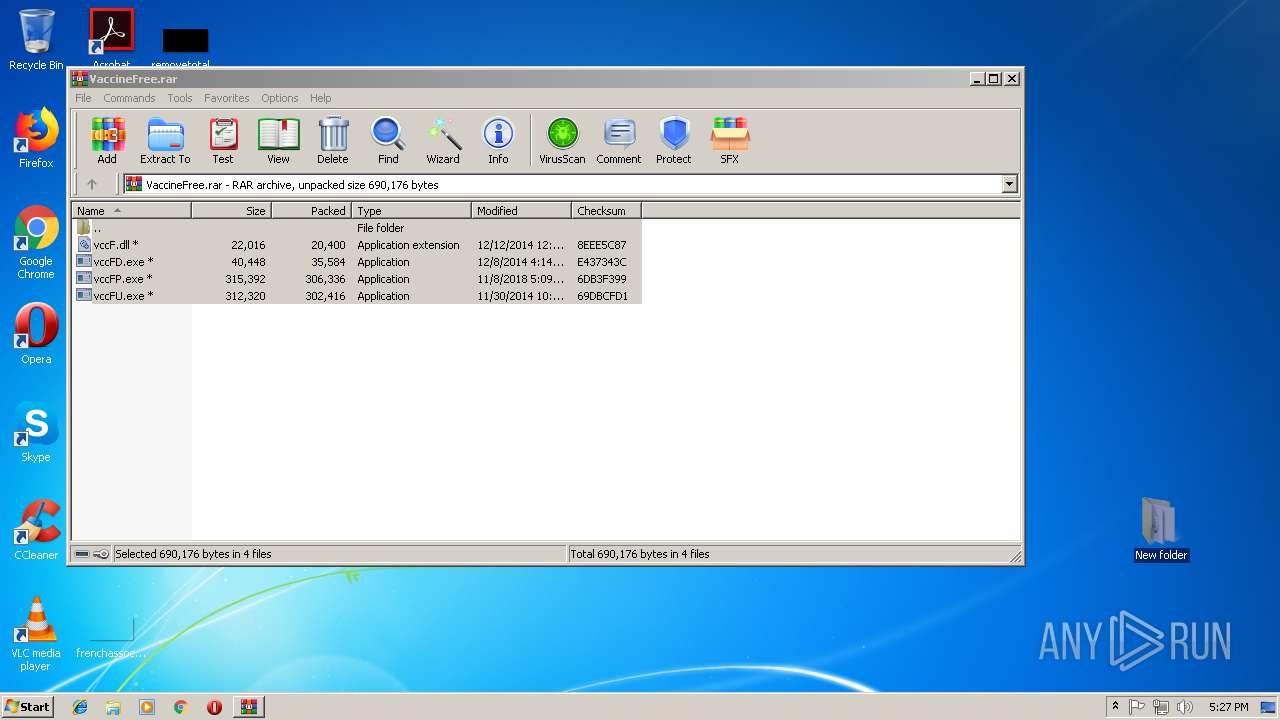
| File name: | VaccineFree.rar |
| Full analysis: | https://app.any.run/tasks/47c6bb3c-faec-4ea9-bfde-530f1aeff187 |
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2018, 17:27:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 31163C467E1F3841349A7AFF8EDCD2DC |
| SHA1: | DE6E2587E983E704E07D9EAF6E8D2AE811A3A127 |
| SHA256: | 72F05F5611FC4D94720493C28DA7EE3342EB677F76543A6A2A1B18C6D425FCE6 |
| SSDEEP: | 12288:3Whe1wfmGyX8oNGeZfDgnLe9in01LyACum6KZE/hB9vdyM7rrBrUdJtb3K:mc1Dx8sGeFEnCcn0QHjZWhBxvQXK |
MALICIOUS
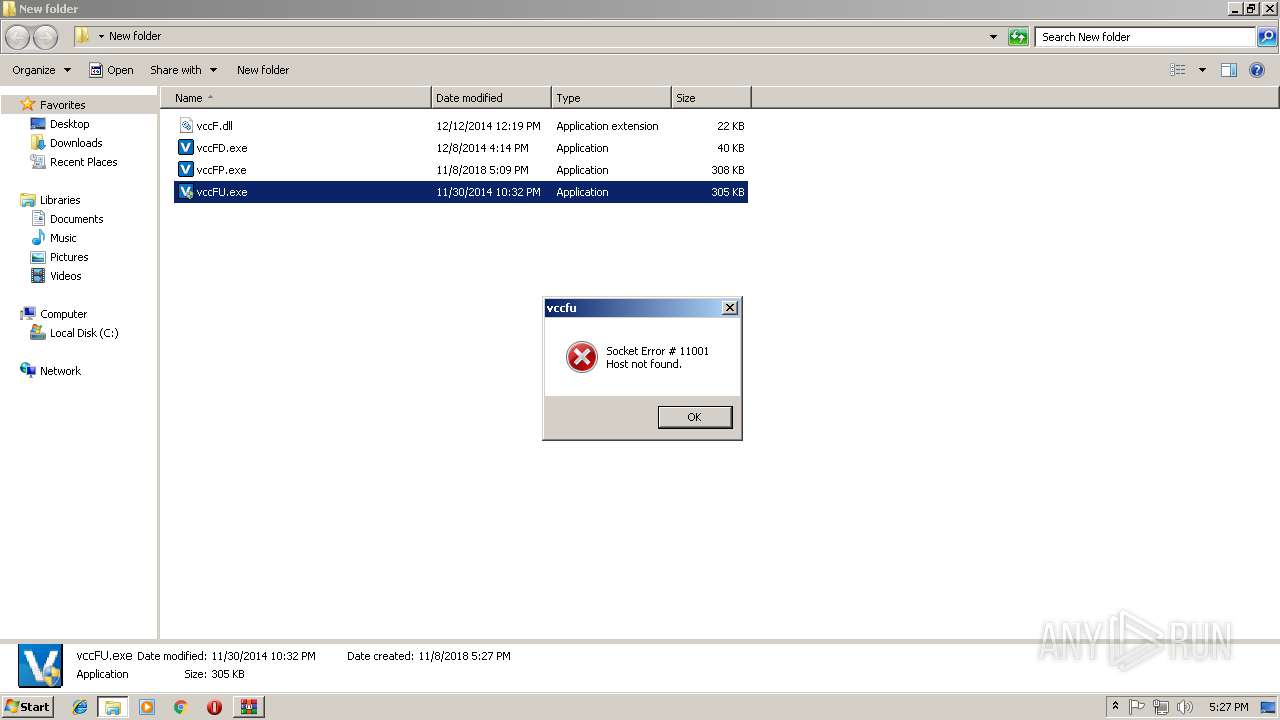
Application was dropped or rewritten from another process
- vccFU.exe (PID: 3916)
- vccFU.exe (PID: 4016)
- vccFP.exe (PID: 844)
- vccFD.exe (PID: 3444)
- vccFU.exe (PID: 2340)
- vccFU.exe (PID: 2748)
- vccFP.exe (PID: 3620)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 716)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2916)
Creates files in the user directory
- vccFD.exe (PID: 3444)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
48
Monitored processes
9
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 716 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe14_ Global\UsGthrCtrlFltPipeMssGthrPipe14 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
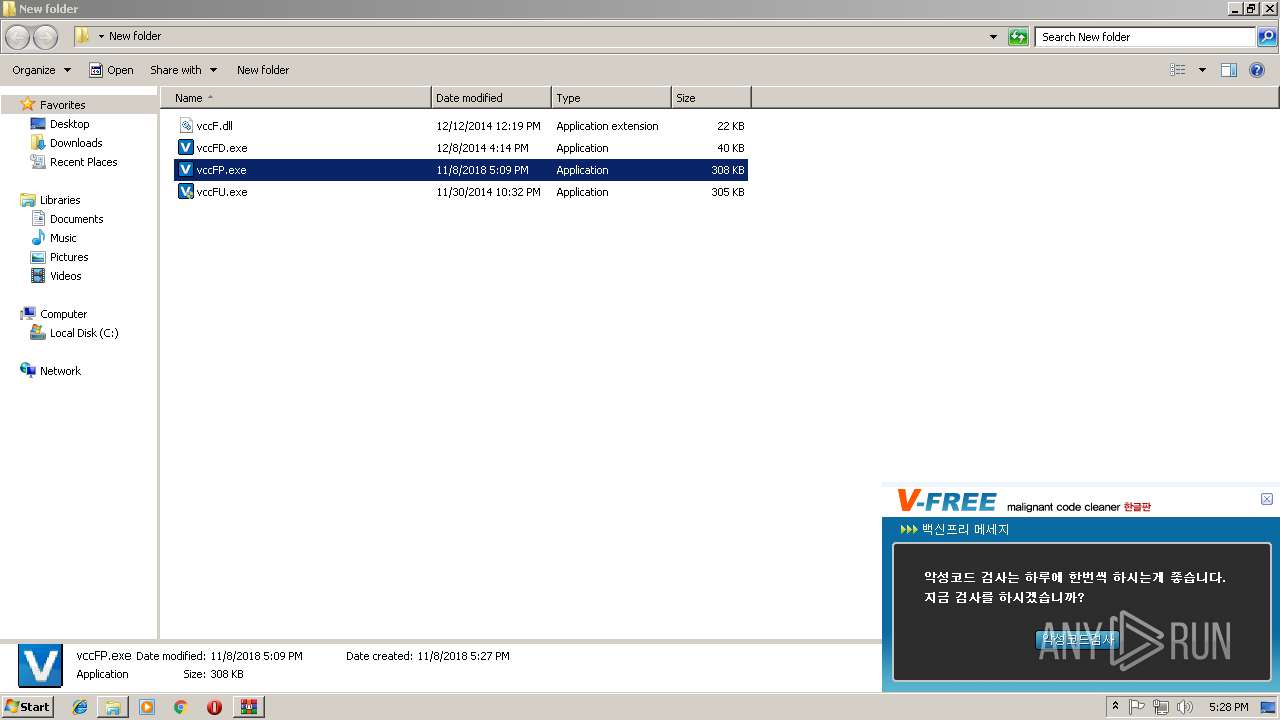
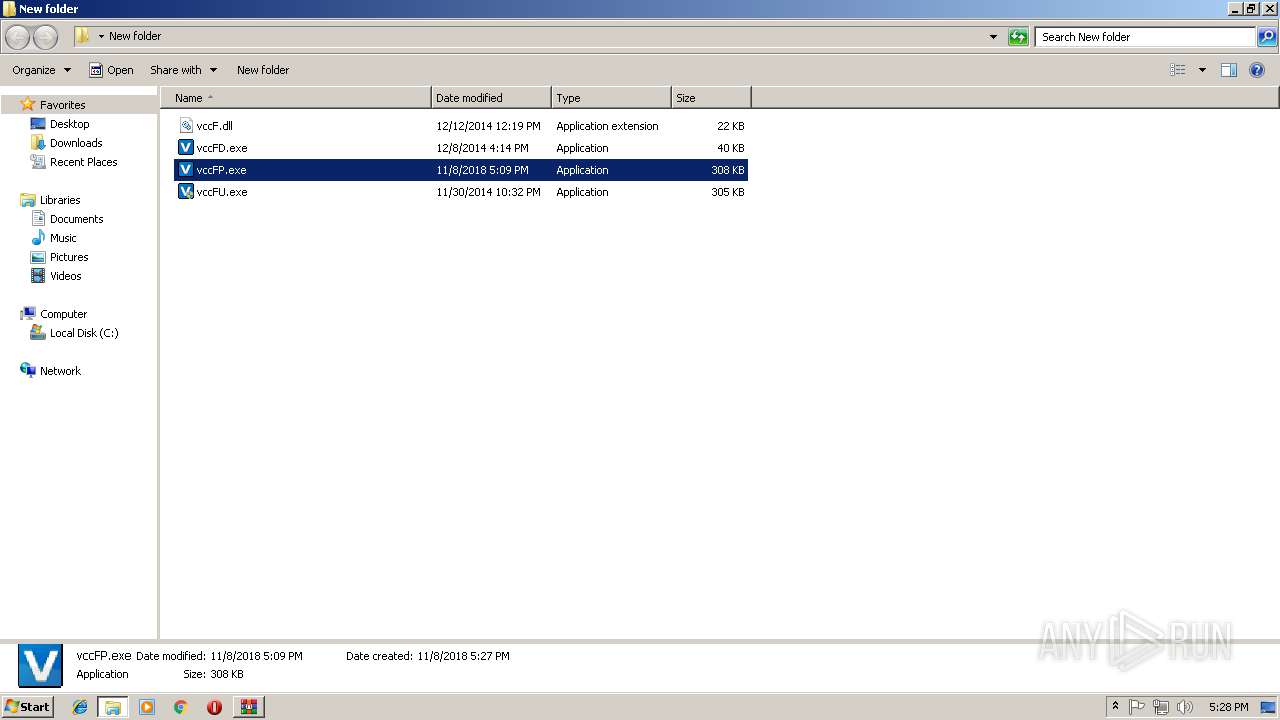
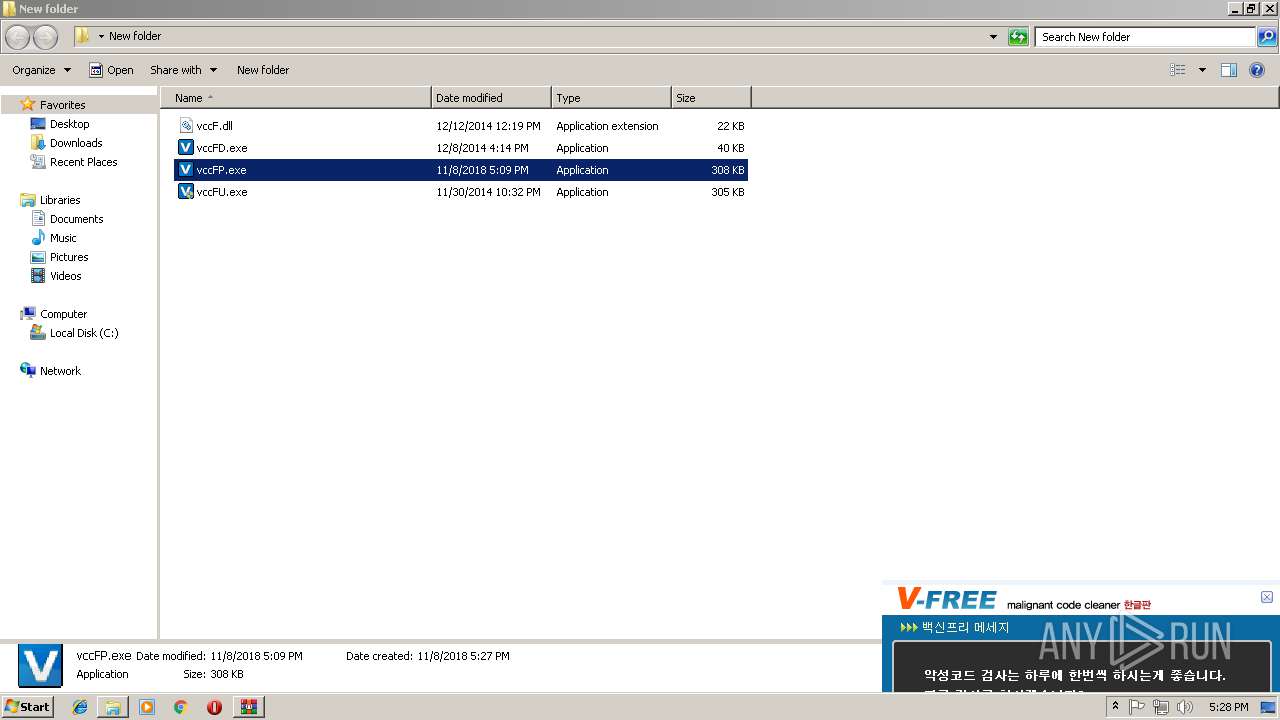
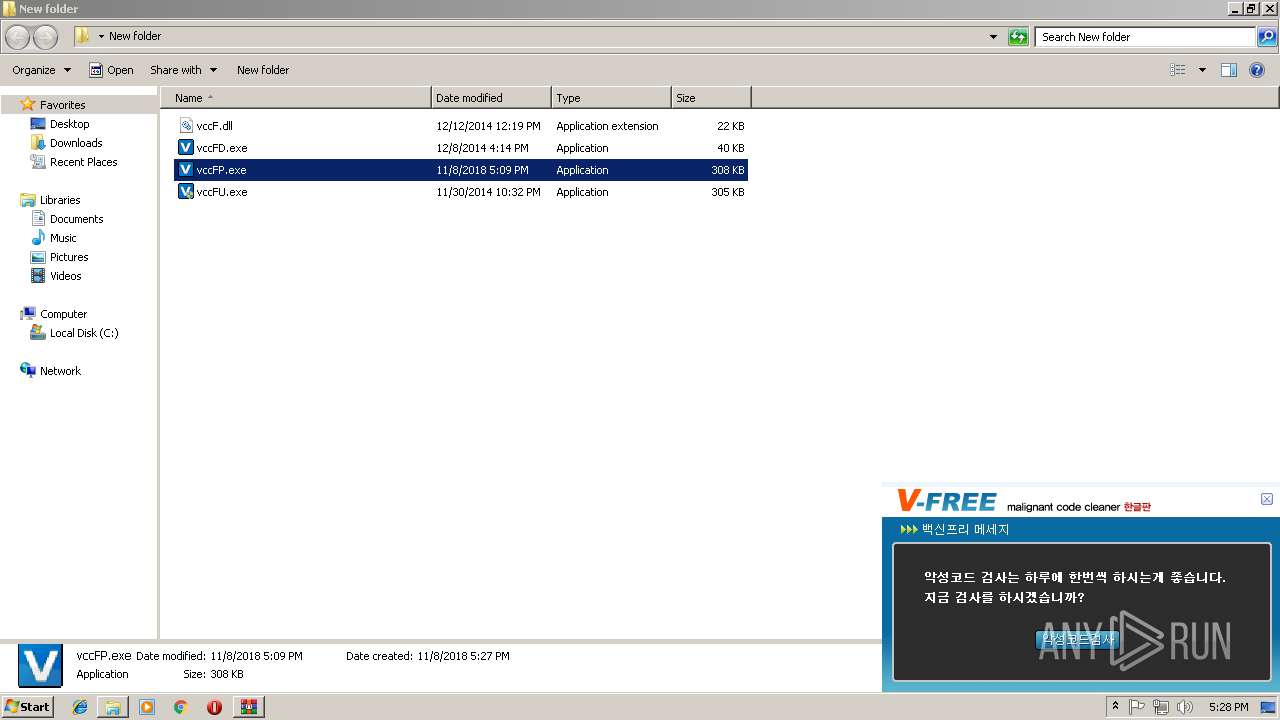
| 844 | "C:\Users\admin\Desktop\New folder\vccFP.exe" | C:\Users\admin\Desktop\New folder\vccFP.exe | — | explorer.exe | |||||||||||
User: admin Company: Akorea company Integrity Level: MEDIUM Description: Vaccine Free Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
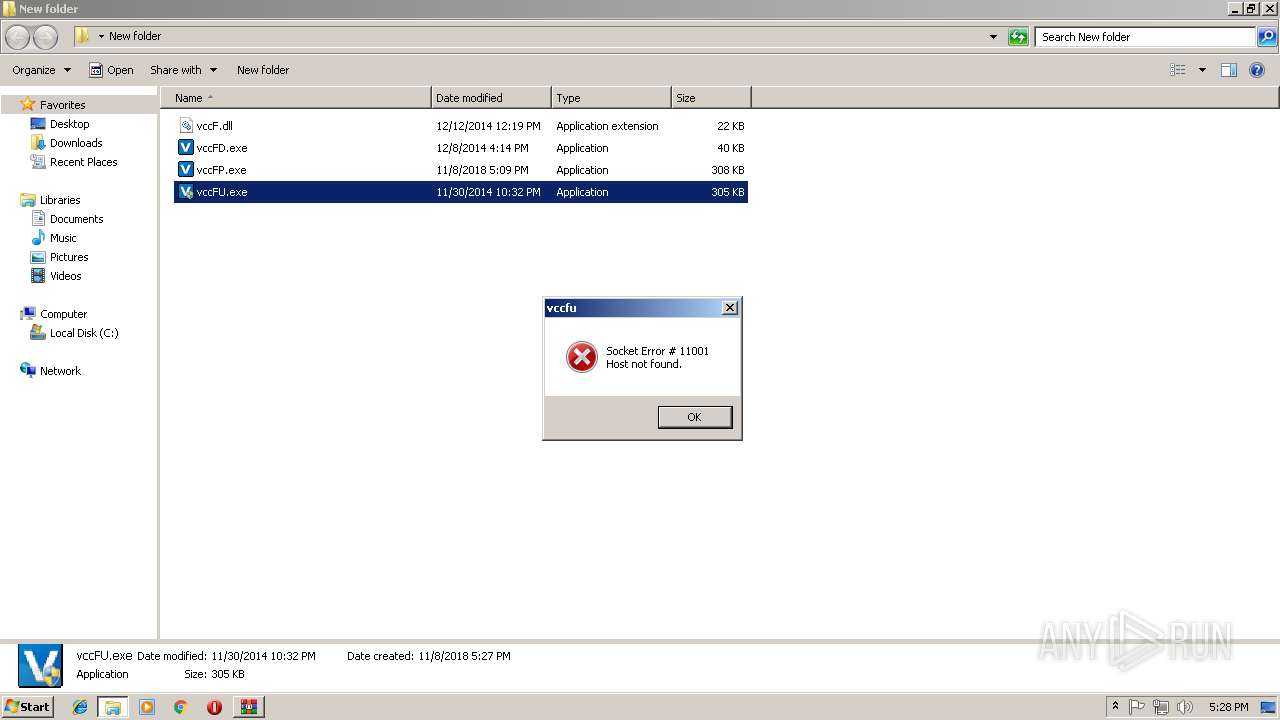
| 2340 | "C:\Users\admin\Desktop\New folder\vccFU.exe" | C:\Users\admin\Desktop\New folder\vccFU.exe | explorer.exe | ||||||||||||
User: admin Company: Akorea company Integrity Level: HIGH Description: Vaccine Free Updater Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2748 | "C:\Users\admin\Desktop\New folder\vccFU.exe" | C:\Users\admin\Desktop\New folder\vccFU.exe | — | explorer.exe | |||||||||||
User: admin Company: Akorea company Integrity Level: MEDIUM Description: Vaccine Free Updater Exit code: 3221226540 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2916 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\VaccineFree.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
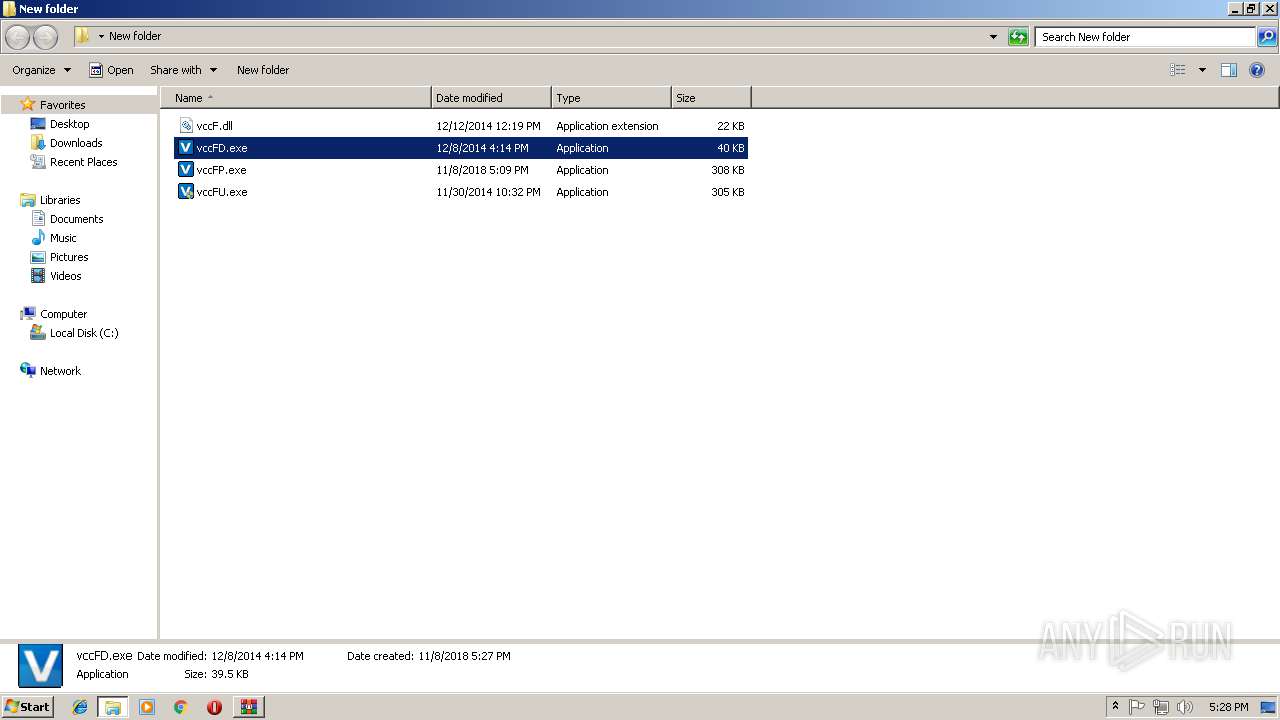
| 3444 | "C:\Users\admin\Desktop\New folder\vccFD.exe" | C:\Users\admin\Desktop\New folder\vccFD.exe | — | explorer.exe | |||||||||||
User: admin Company: Akorea company Integrity Level: MEDIUM Description: Vaccine Free Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3620 | "C:\Users\admin\Desktop\New folder\vccFP.exe" | C:\Users\admin\Desktop\New folder\vccFP.exe | — | explorer.exe | |||||||||||
User: admin Company: Akorea company Integrity Level: MEDIUM Description: Vaccine Free Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 3916 | "C:\Users\admin\Desktop\New folder\vccFU.exe" | C:\Users\admin\Desktop\New folder\vccFU.exe | — | explorer.exe | |||||||||||
User: admin Company: Akorea company Integrity Level: MEDIUM Description: Vaccine Free Updater Exit code: 3221226540 Version: 1.0.0.1 Modules
| |||||||||||||||
| 4016 | "C:\Users\admin\Desktop\New folder\vccFU.exe" | C:\Users\admin\Desktop\New folder\vccFU.exe | explorer.exe | ||||||||||||
User: admin Company: Akorea company Integrity Level: HIGH Description: Vaccine Free Updater Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
Total events
867
Read events
840
Write events
27
Delete events
0
Modification events
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\VaccineFree.rar | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
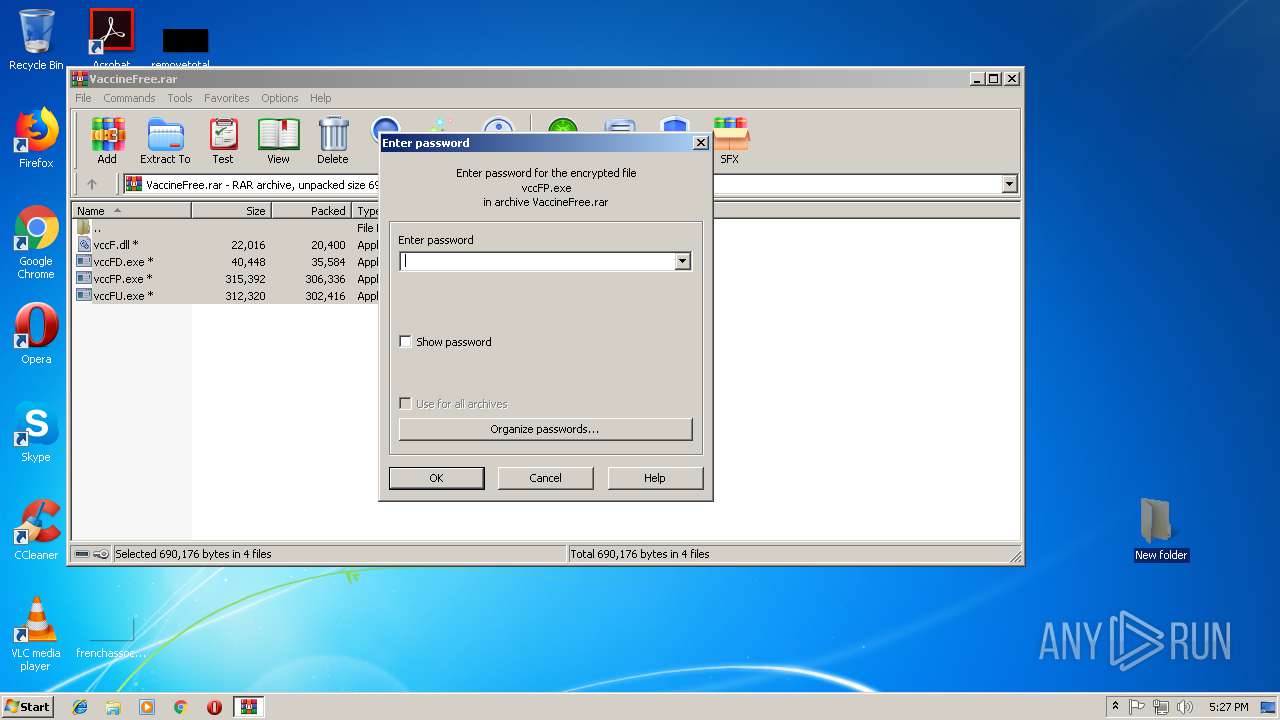
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3444) vccFD.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\vccFD_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
4
Suspicious files
0
Text files
0
Unknown types
1
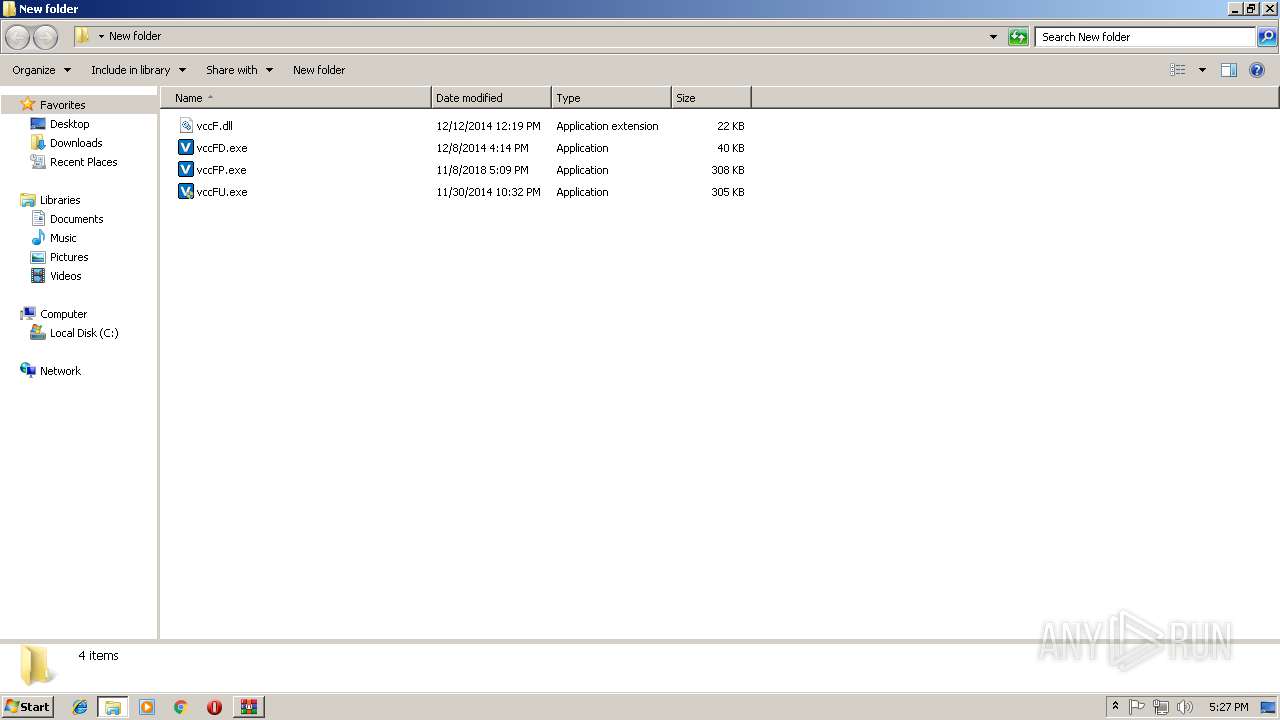
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2916 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2916.6643\vccFD.exe | executable | |
MD5:— | SHA256:— | |||
| 2916 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2916.6643\vccFP.exe | executable | |
MD5:— | SHA256:— | |||
| 2916 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2916.6643\vccFU.exe | executable | |
MD5:— | SHA256:— | |||
| 2916 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2916.6643\vccF.dll | executable | |
MD5:— | SHA256:— | |||
| 3444 | vccFD.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\IETldCache\index.dat | dat | |
MD5:D7A950FEFD60DBAA01DF2D85FEFB3862 | SHA256:75D0B1743F61B76A35B1FEDD32378837805DE58D79FA950CB6E8164BFA72073A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
update.vaccine-free.co.kr |
| unknown |