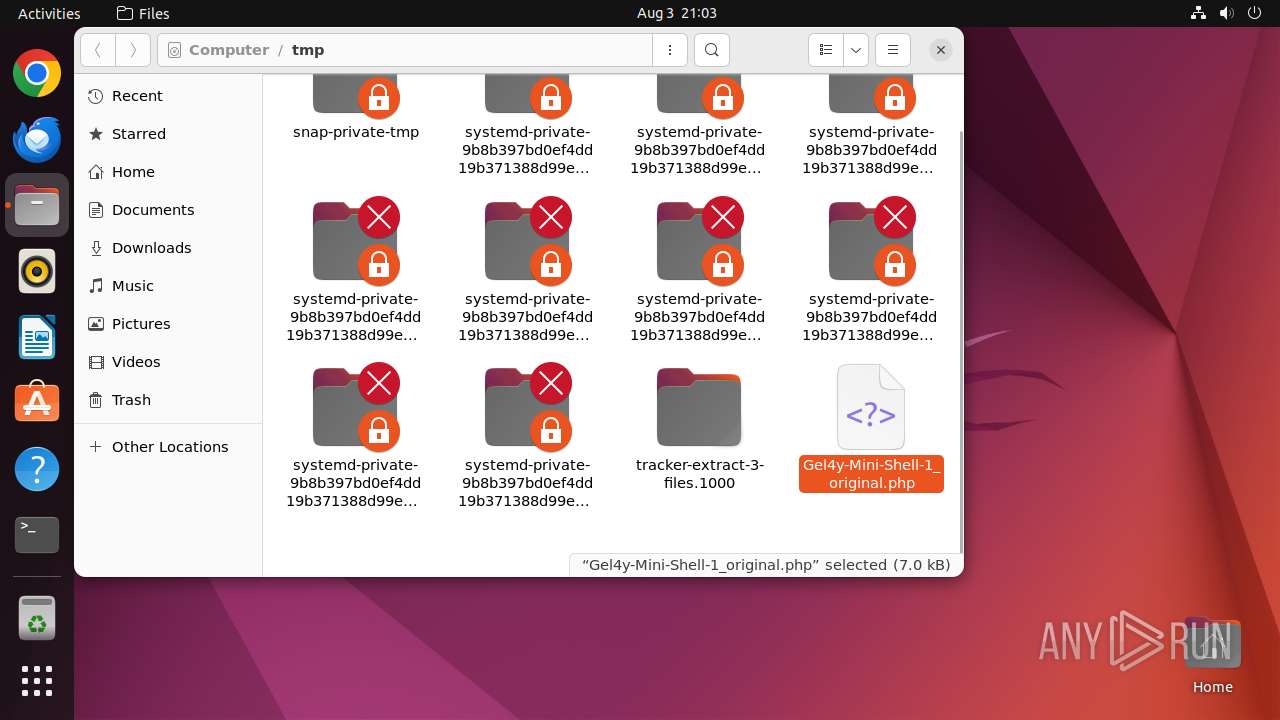
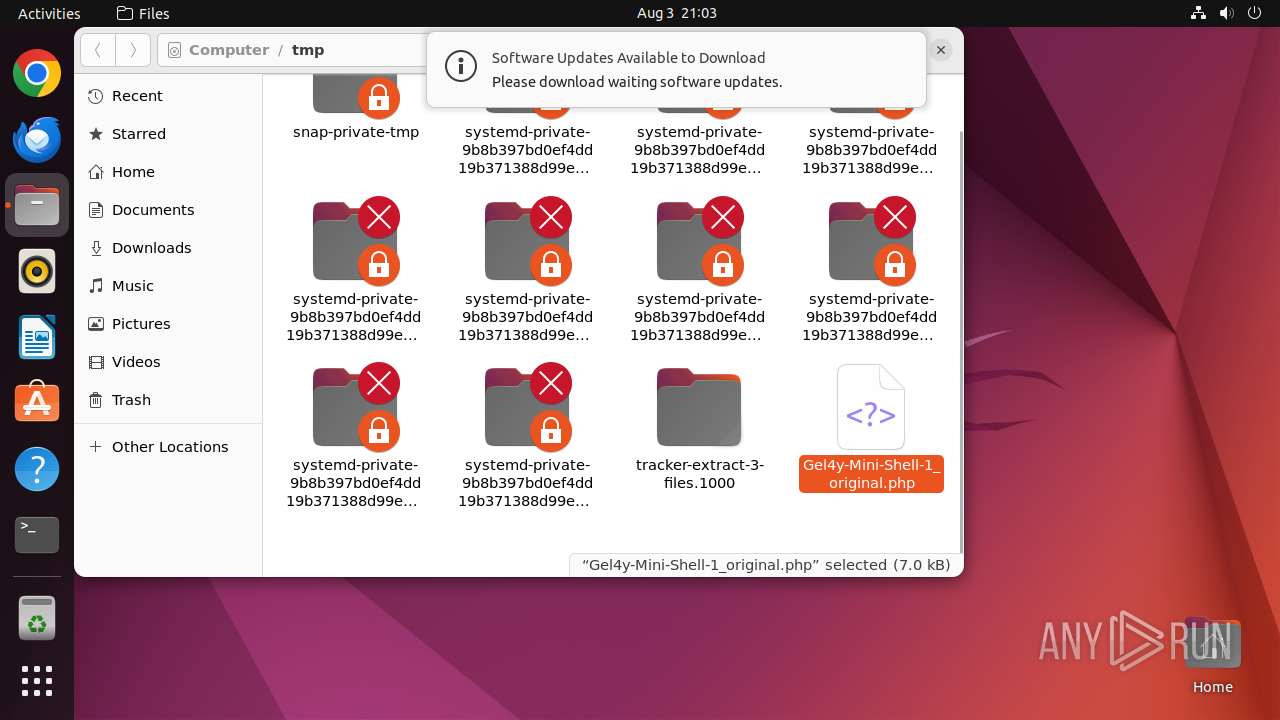
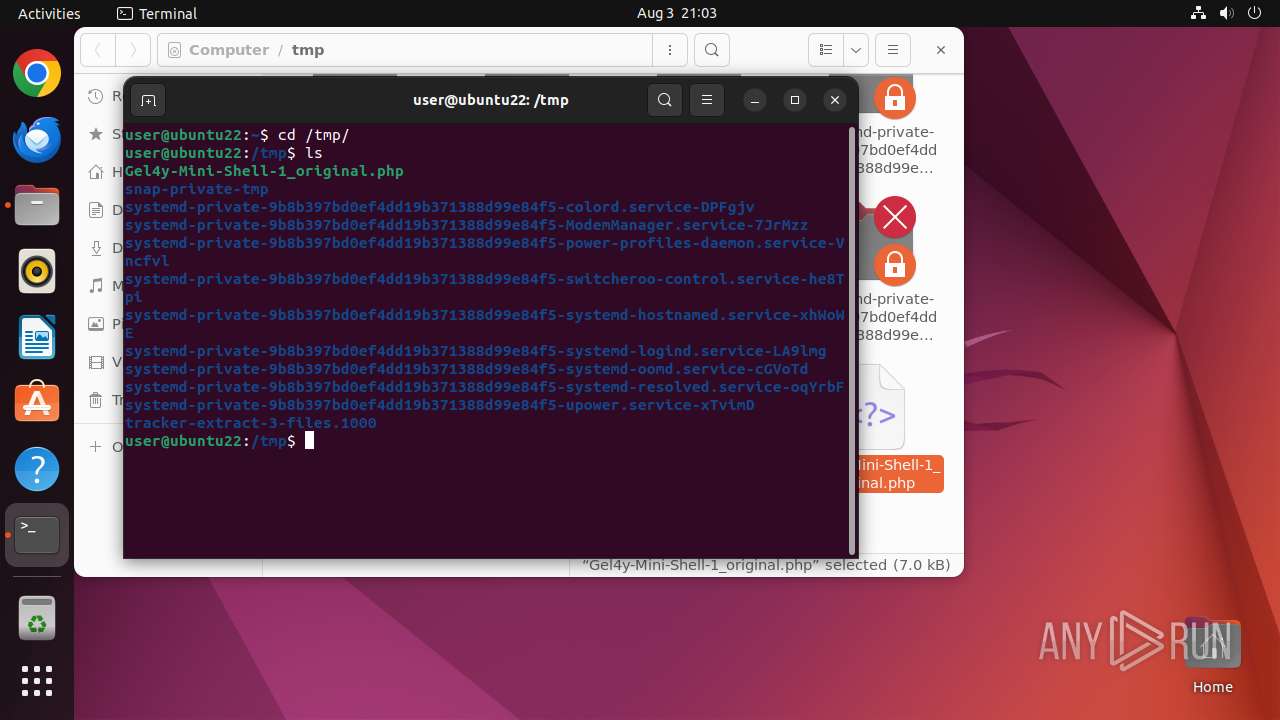
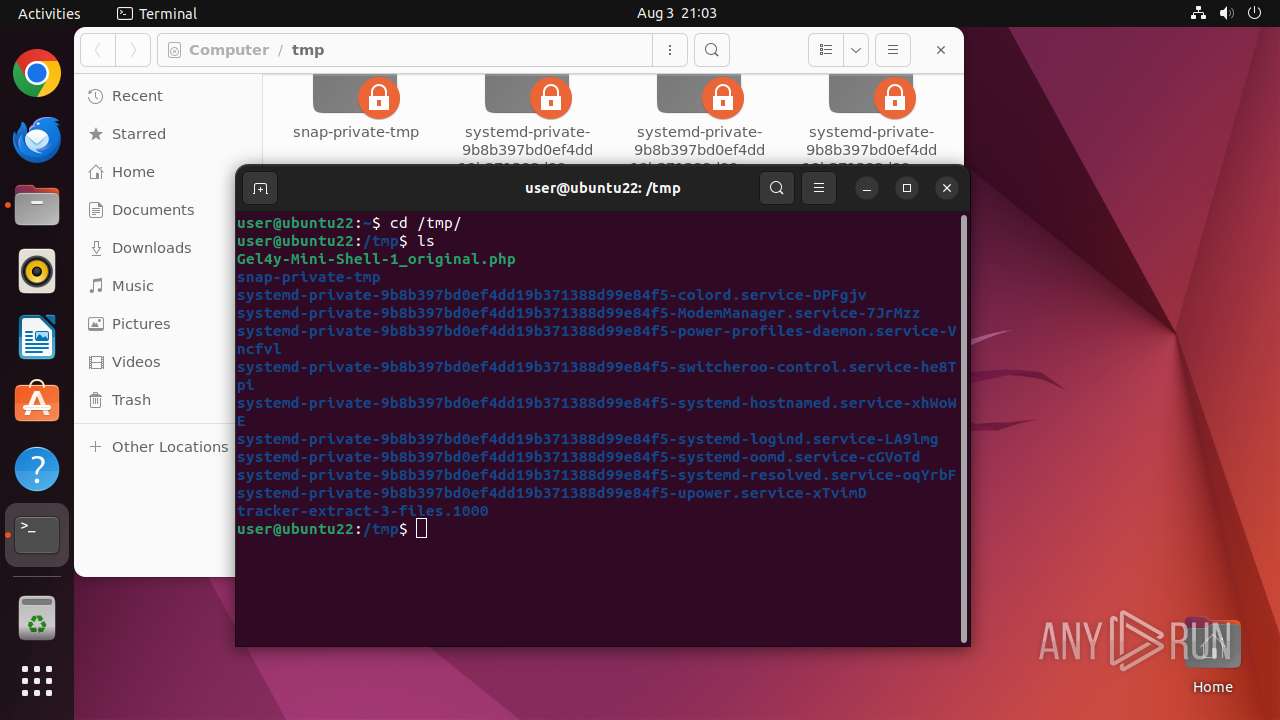
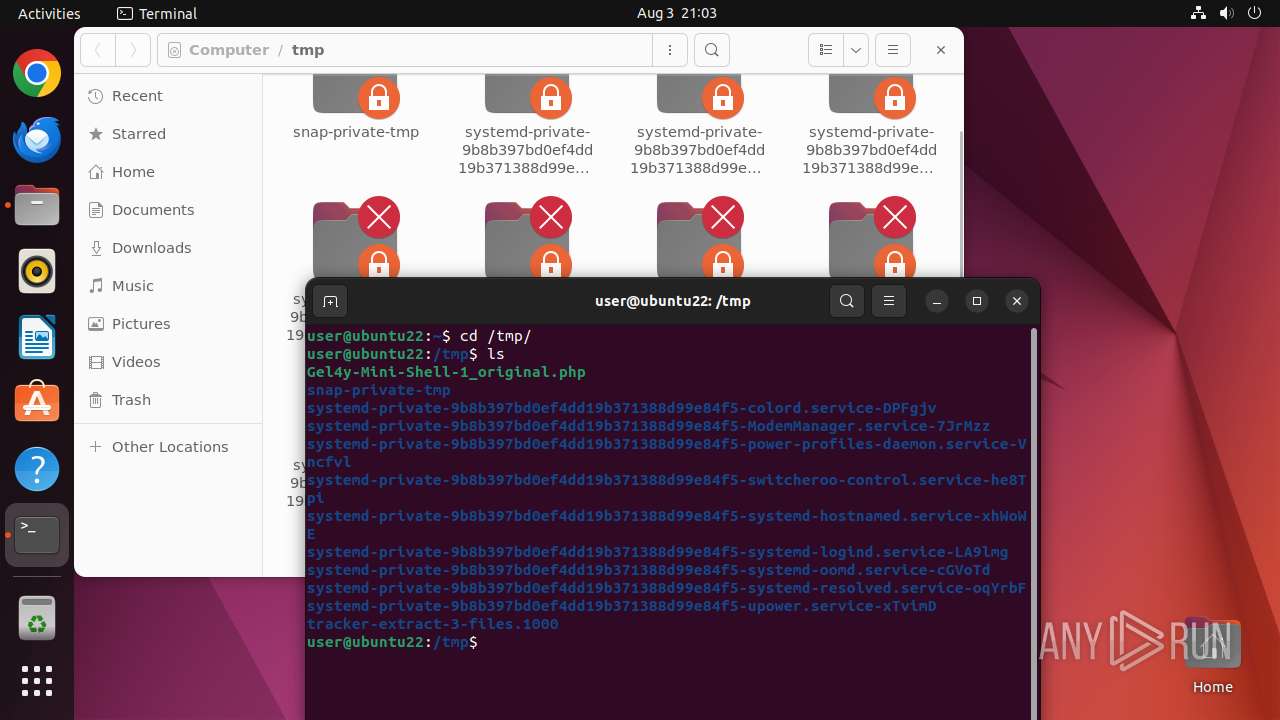
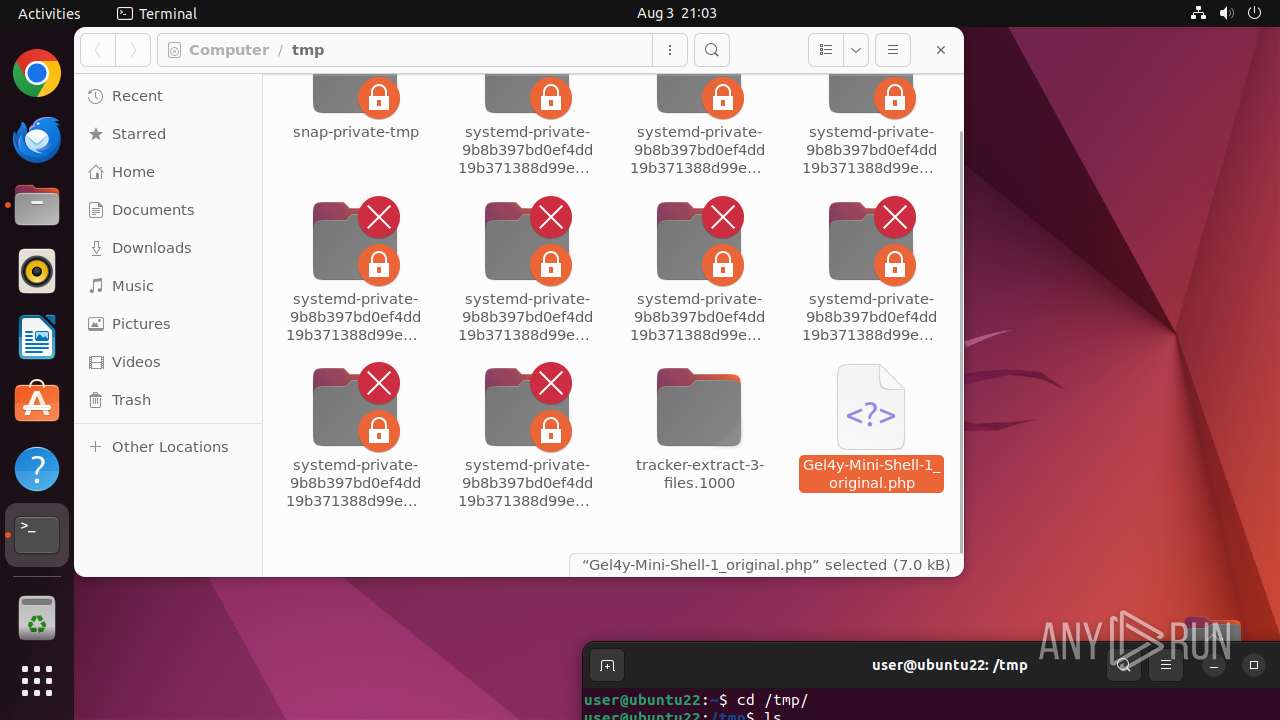
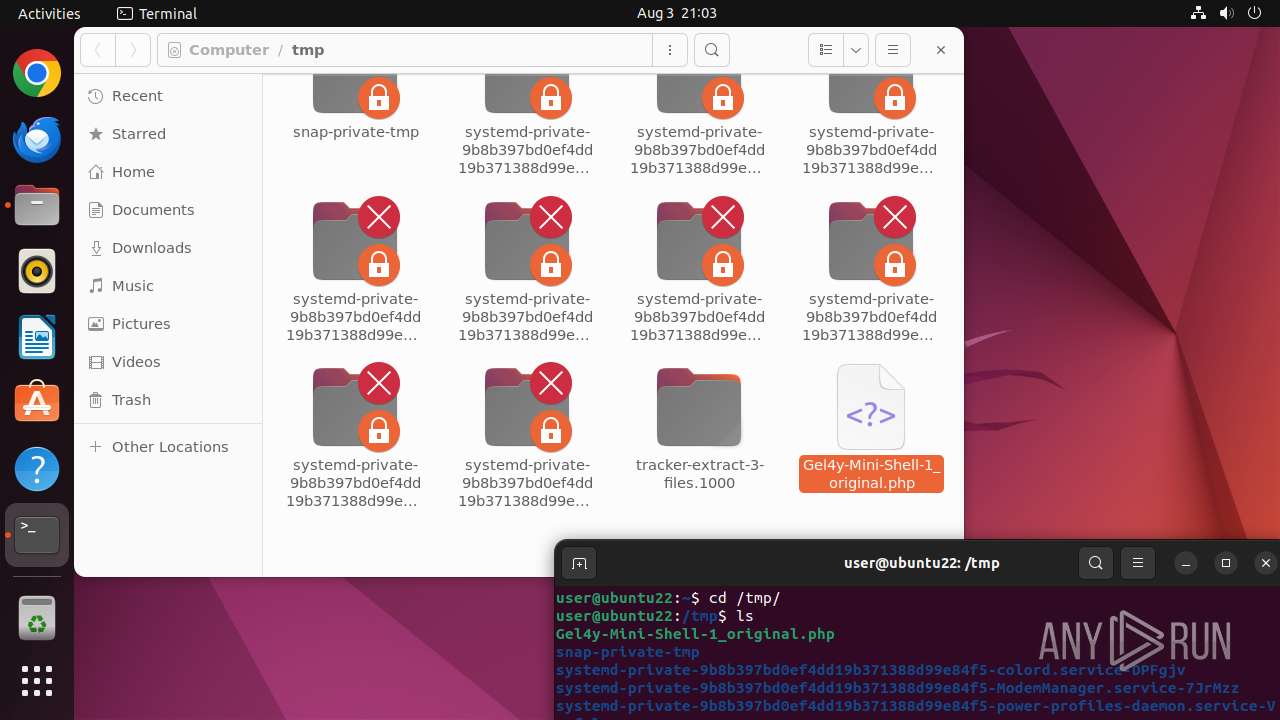
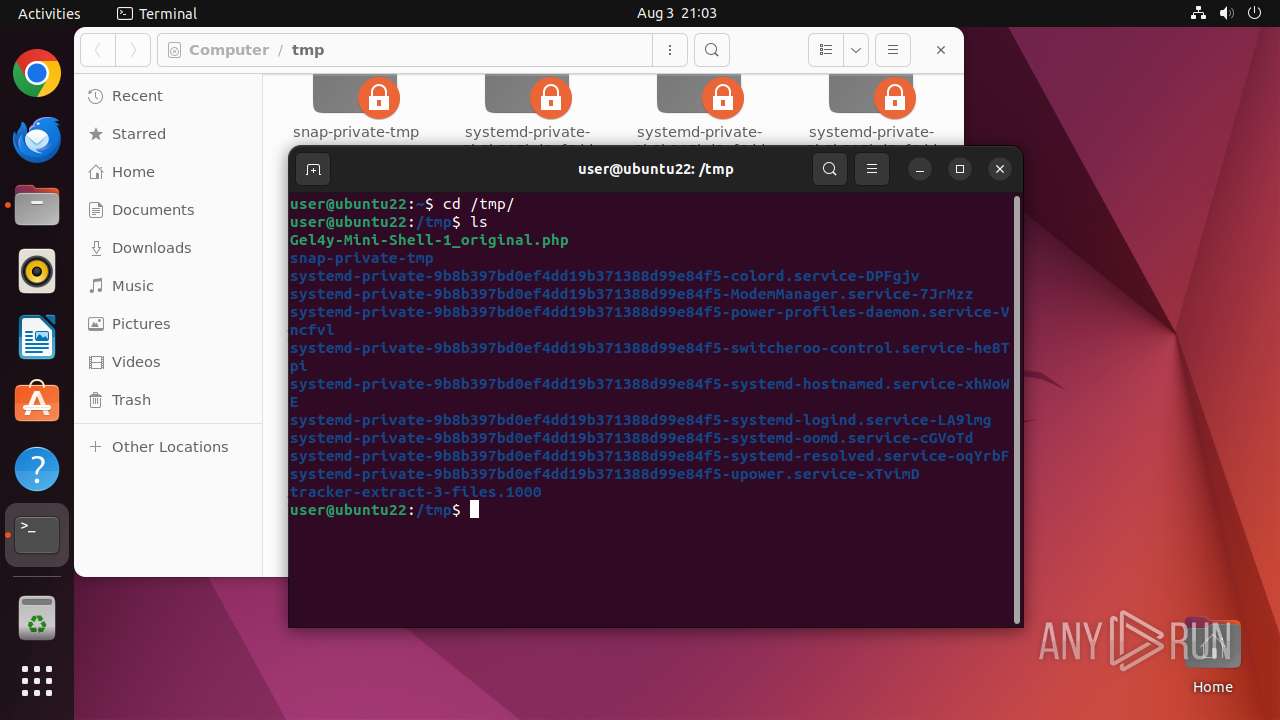
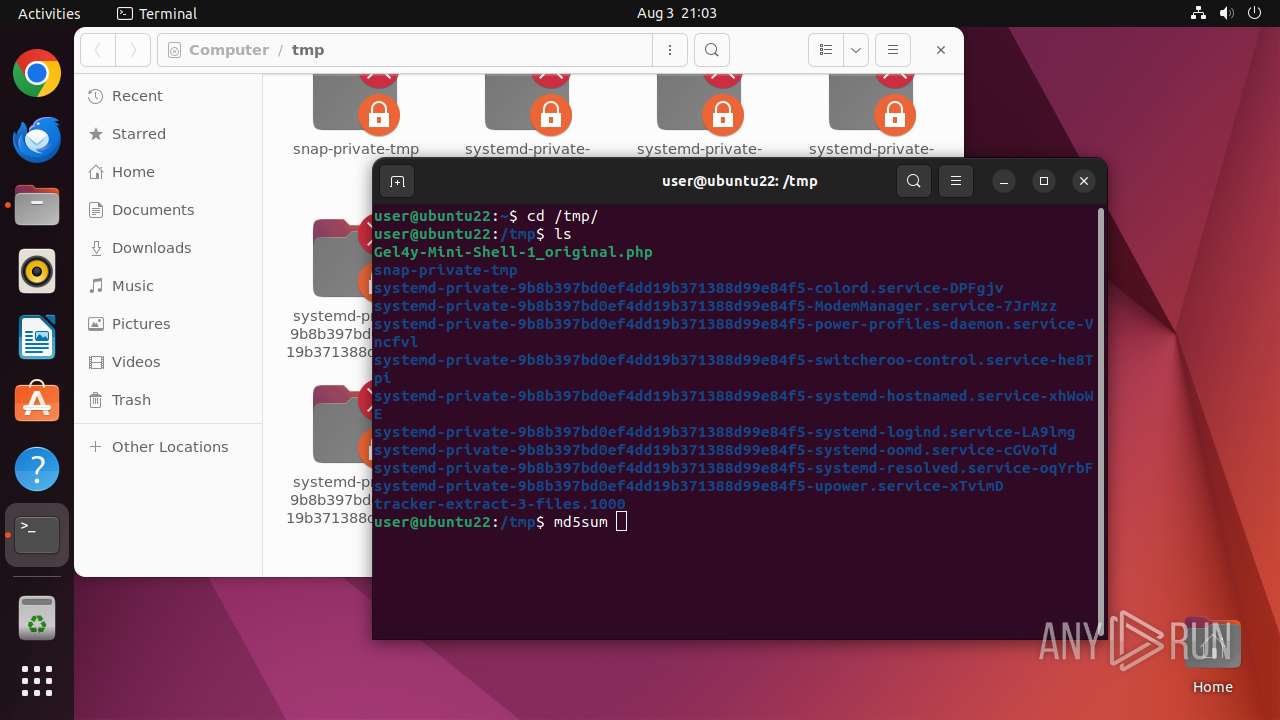
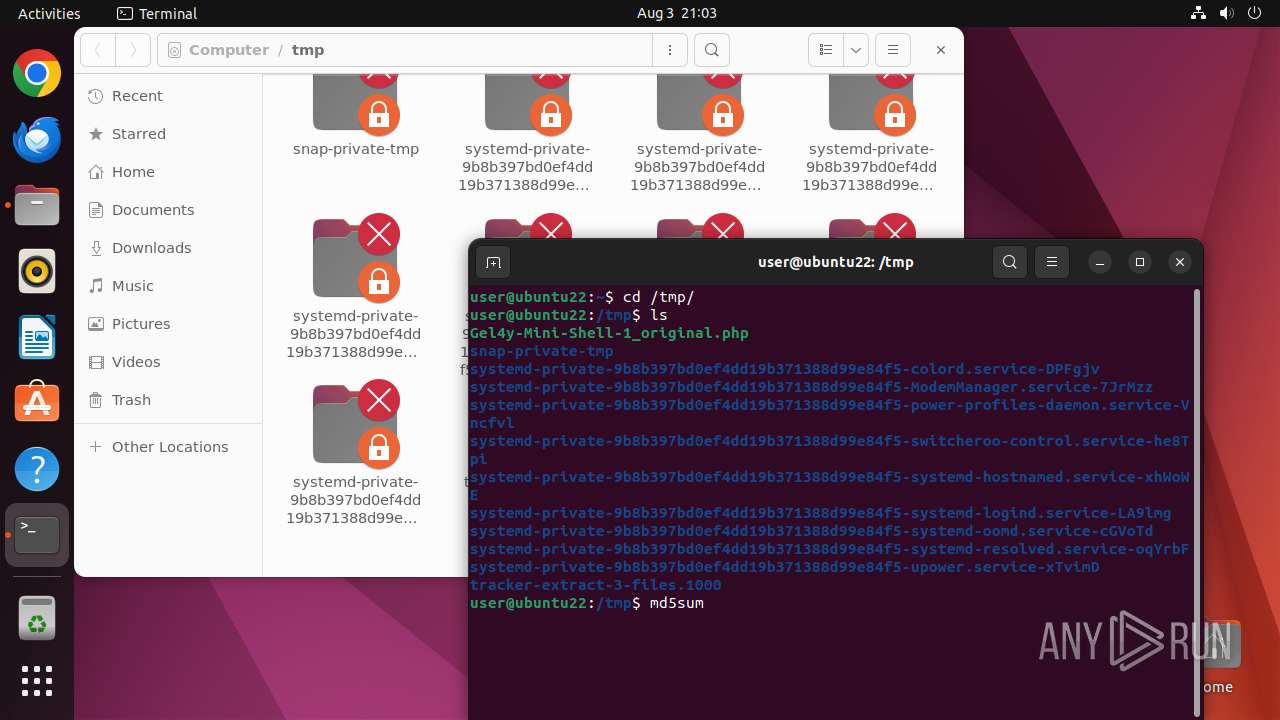
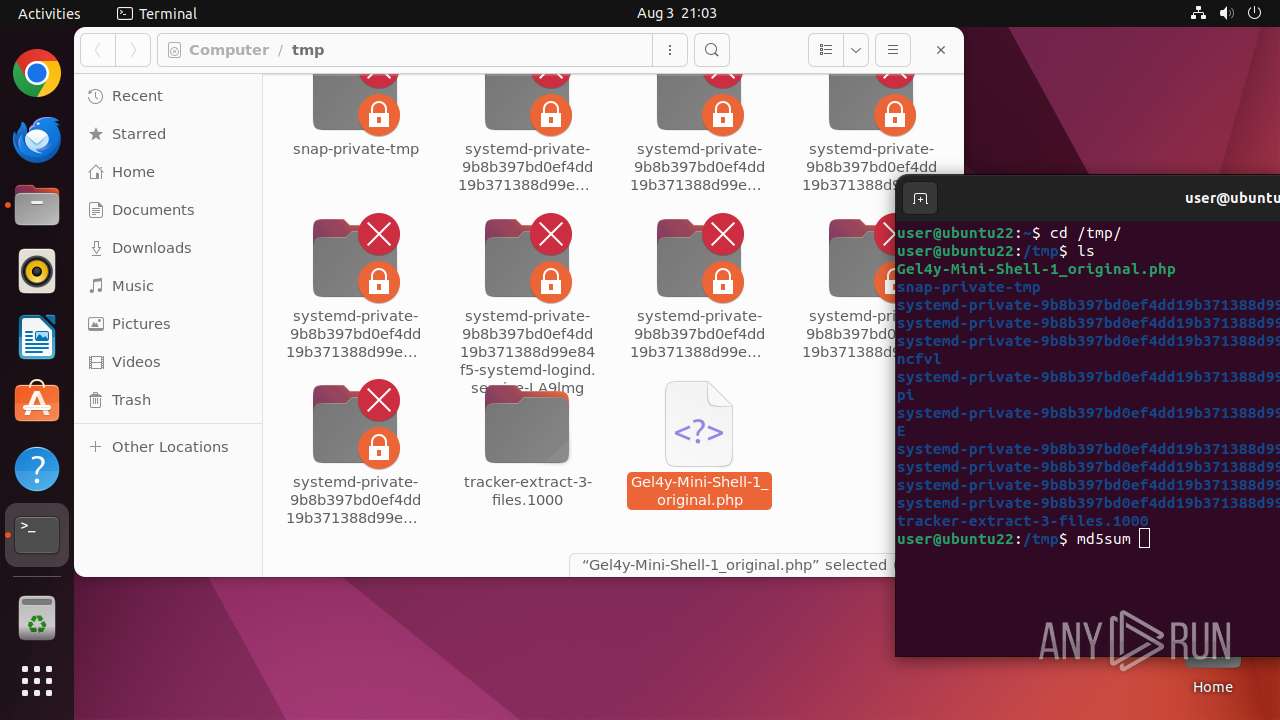
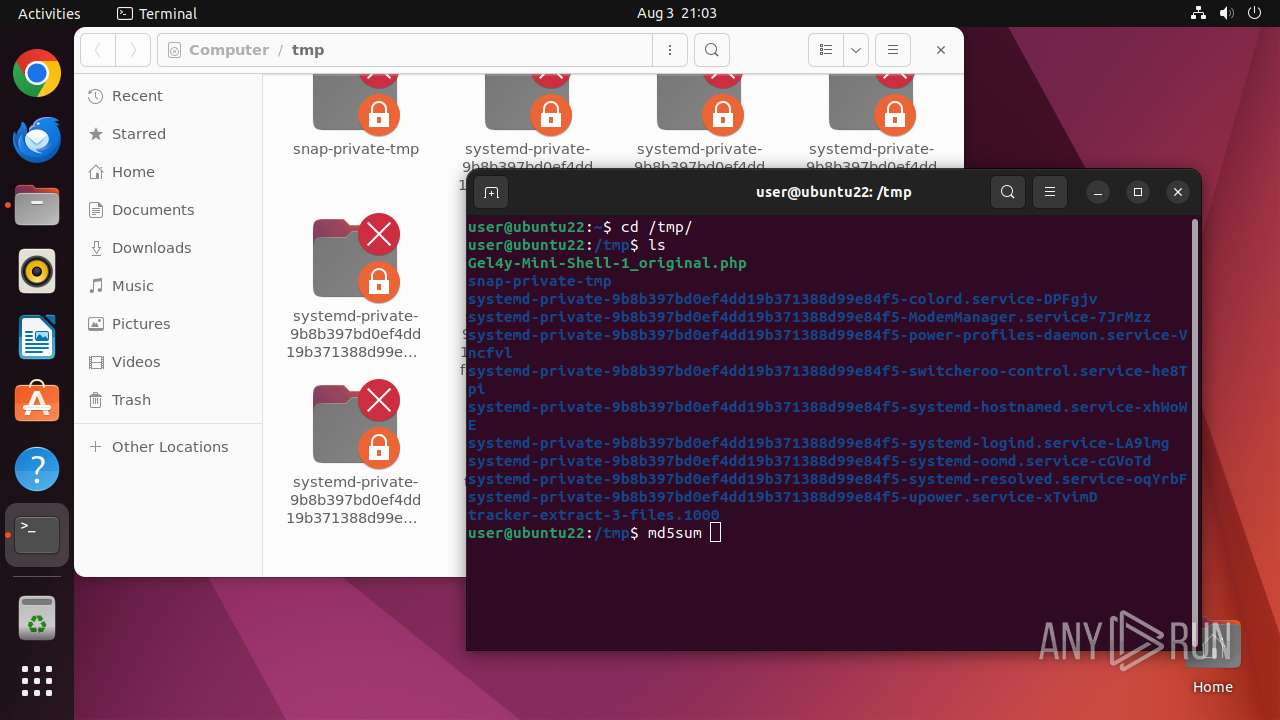
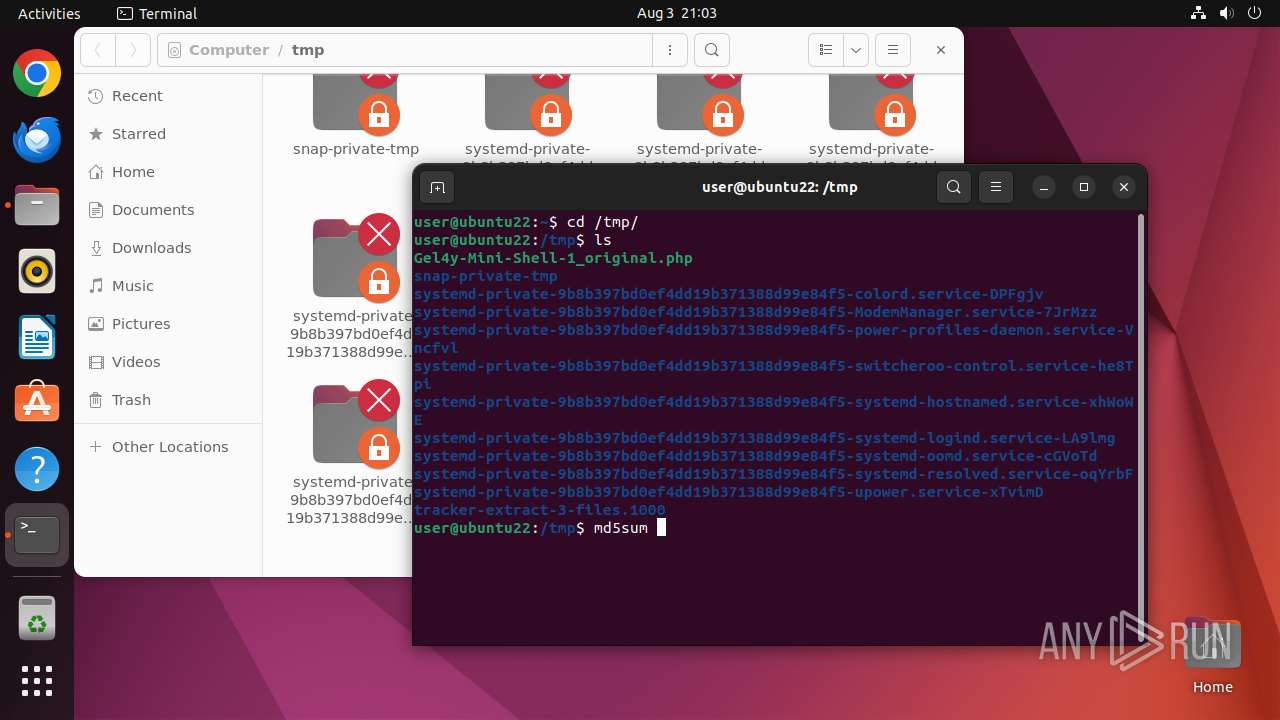
| File name: | Gel4y-Mini-Shell-1_original.php |
| Full analysis: | https://app.any.run/tasks/2304fac8-e1c1-424e-923f-d606d0221d33 |
| Verdict: | Malicious activity |
| Analysis date: | August 03, 2024, 20:03:01 |
| OS: | Ubuntu 22.04.2 |
| MIME: | text/x-php |
| File info: | PHP script, Unicode text, UTF-8 (with BOM) text, with very long lines (6975), with no line terminators |
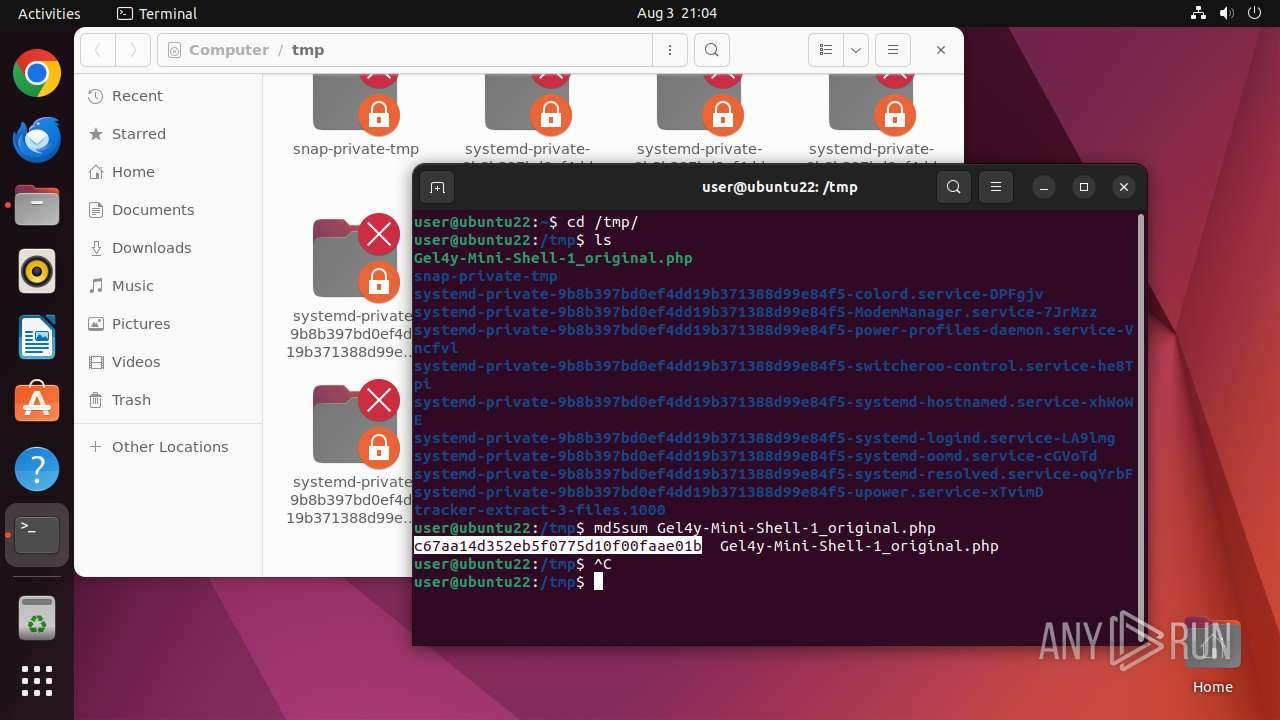
| MD5: | C67AA14D352EB5F0775D10F00FAAE01B |
| SHA1: | 99DFA8EEECFA228238AF5C9BA39701779D6D9FEF |
| SHA256: | 72EC26C78987250744A7B0396F0E3516D1189EE58054A4D5F0E15691F00E9E7C |
| SSDEEP: | 192:FWxxGFhA6xT42ILrxYlP74LuMci6825+MmAAKpA00EL:FWx8FhA0iI74L6xU6m2 |
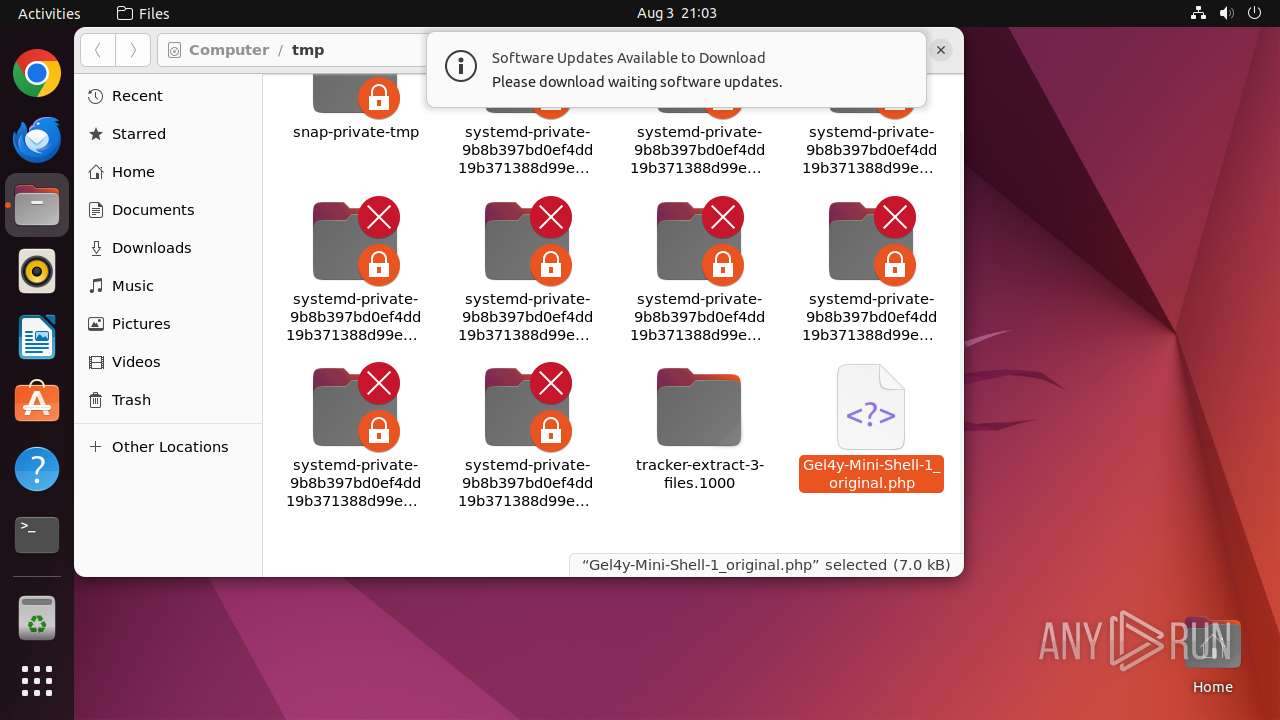
MALICIOUS
No malicious indicators.SUSPICIOUS
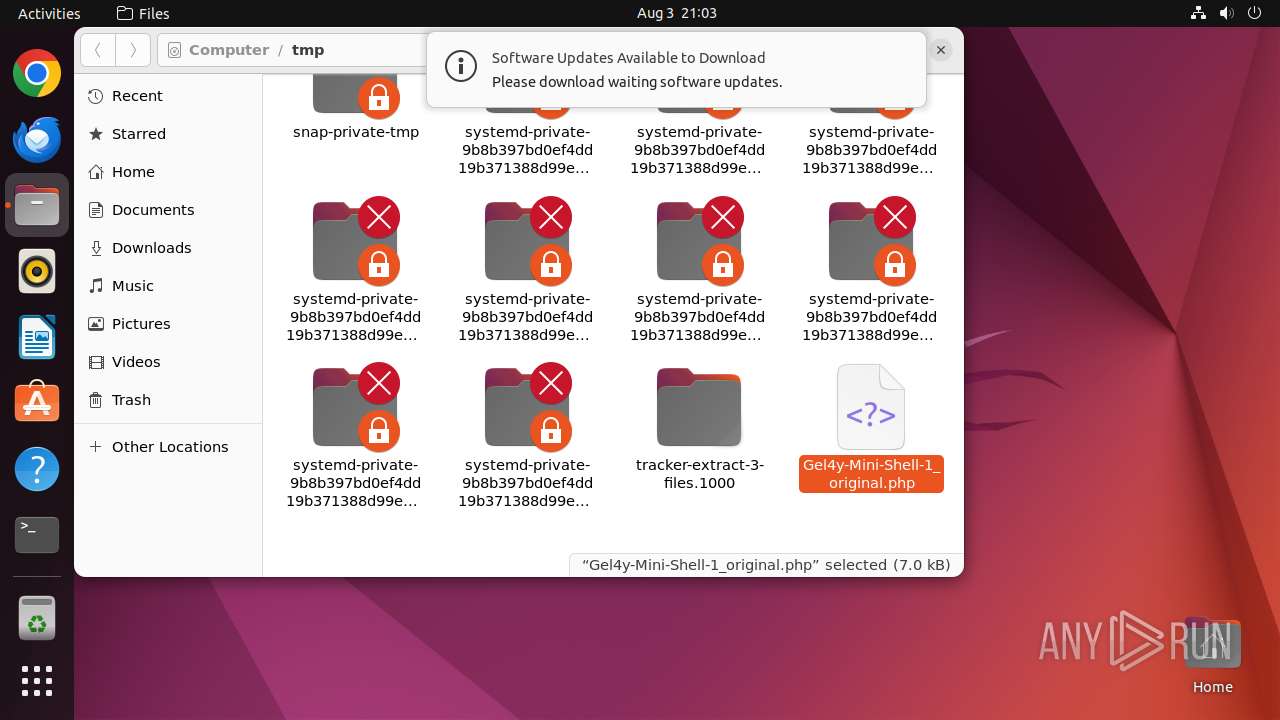
Executes commands using command-line interpreter
- sudo (PID: 12926)
- update-notifier (PID: 13014)
- gnome-terminal-server (PID: 12963)
Checks DMI information (probably VM detection)
- systemd-hostnamed (PID: 12943)
Reads /proc/mounts (likely used to find writable filesystems)
- check-new-release-gtk (PID: 13016)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .txt | | | Text - UTF-8 encoded (100) |
|---|
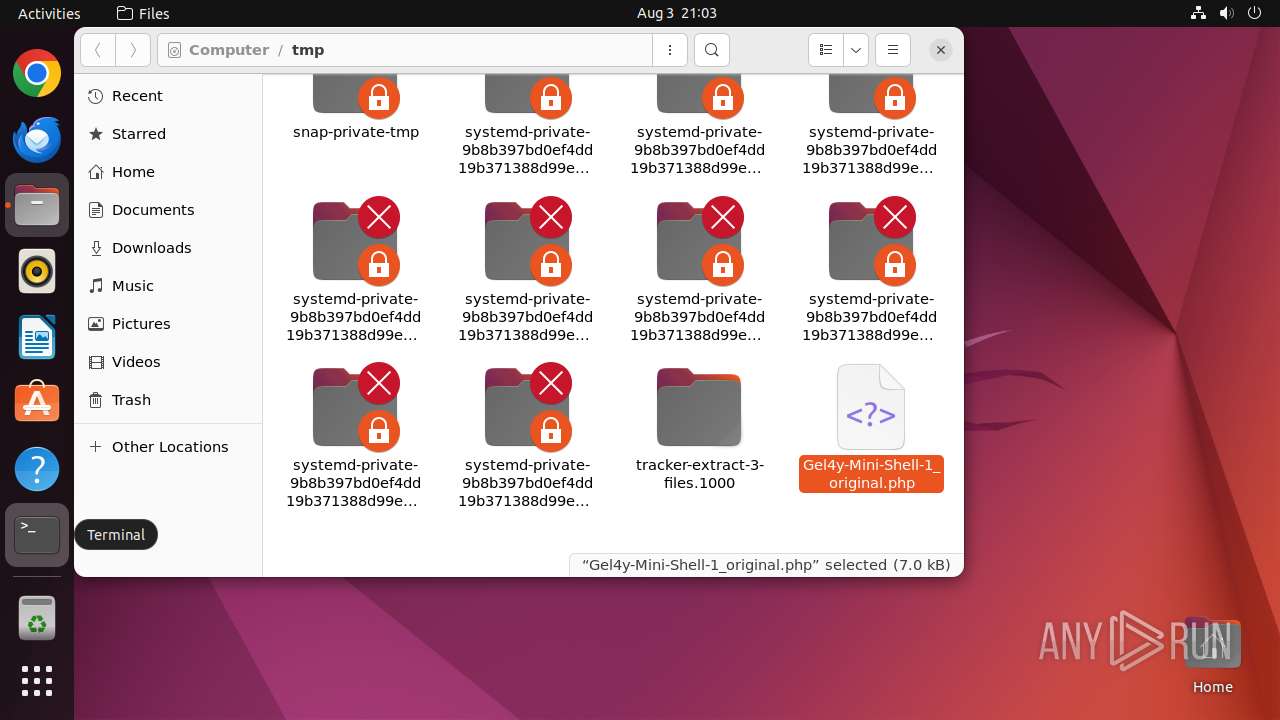
Total processes
252
Monitored processes
39
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
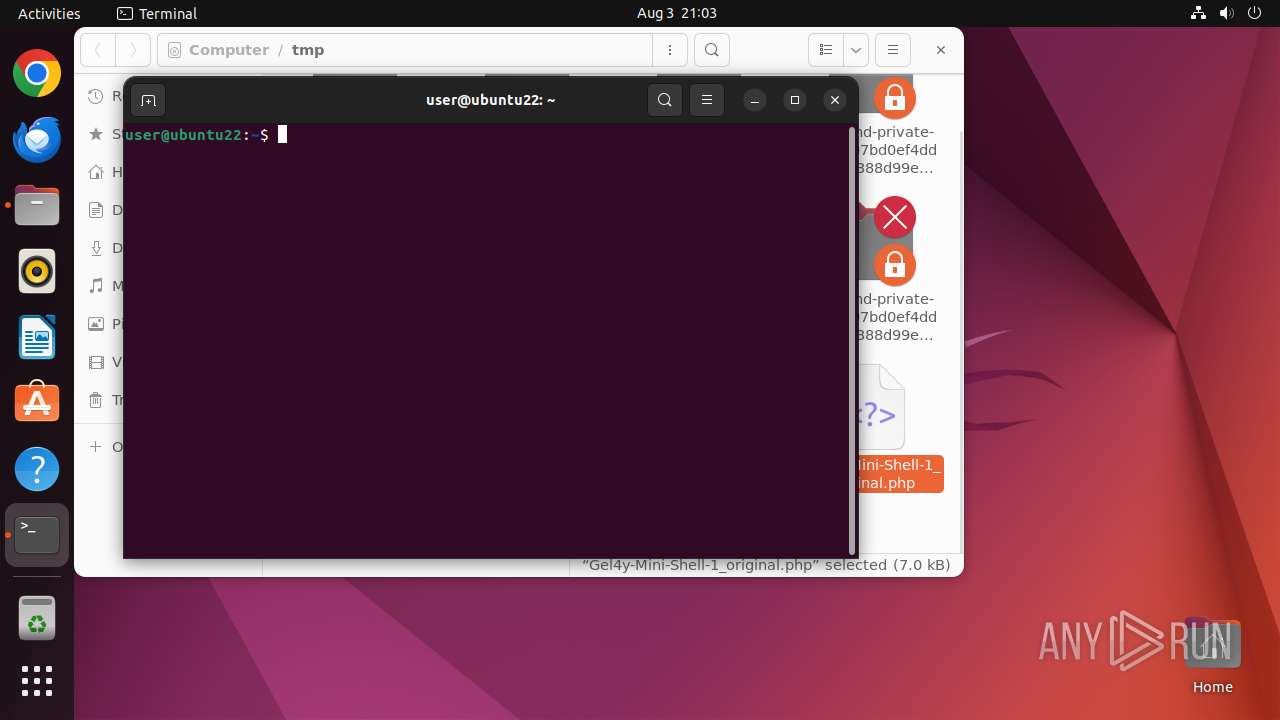
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 12923 | sh -c "file --mime-type /tmp/Gel4y-Mini-Shell-1_original\.php" | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12924 | file --mime-type /tmp/Gel4y-Mini-Shell-1_original.php | /usr/bin/file | — | sh |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12925 | /bin/sh -c "DISPLAY=:0 sudo -iu user nautilus /tmp/Gel4y-Mini-Shell-1_original\.php " | /bin/sh | — | any-guest-agent |
User: user Integrity Level: UNKNOWN | ||||
| 12926 | sudo -iu user nautilus /tmp/Gel4y-Mini-Shell-1_original.php | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN | ||||
| 12927 | nautilus /tmp/Gel4y-Mini-Shell-1_original.php | /usr/bin/nautilus | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 12928 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | nautilus |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12943 | /lib/systemd/systemd-hostnamed | /lib/systemd/systemd-hostnamed | — | systemd |
User: root Integrity Level: UNKNOWN Exit code: 485 | ||||
| 12950 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 482 | ||||
| 12951 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 482 | ||||
| 12952 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 482 | ||||
Executable files
0
Suspicious files
0
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 13016 | check-new-release-gtk | /tmp/#6029335 (deleted) | text | |
MD5:— | SHA256:— | |||
| 13016 | check-new-release-gtk | /tmp/#6029359 (deleted) | text | |
MD5:— | SHA256:— | |||
| 13016 | check-new-release-gtk | /tmp/#6029364 (deleted) | text | |
MD5:— | SHA256:— | |||
| 13016 | check-new-release-gtk | /tmp/#6029378 (deleted) | text | |
MD5:— | SHA256:— | |||
| 13016 | check-new-release-gtk | /tmp/#6029379 (deleted) | text | |
MD5:— | SHA256:— | |||
| 13016 | check-new-release-gtk | /tmp/#6029381 (deleted) | text | |
MD5:— | SHA256:— | |||
| 13016 | check-new-release-gtk | /tmp/#6029987 (deleted) | text | |
MD5:— | SHA256:— | |||
| 13016 | check-new-release-gtk | /tmp/#6029988 (deleted) | text | |
MD5:— | SHA256:— | |||
| 13016 | check-new-release-gtk | /home/user/.cache/update-manager-core/meta-release-lts | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
10
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 91.189.91.96:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.125.190.48:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | unknown |
470 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 91.189.91.48:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | unknown |
— | — | 91.189.91.96:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | unknown |
— | — | 156.146.33.15:443 | odrs.gnome.org | Datacamp Limited | DE | unknown |
485 | snapd | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | malicious |
485 | snapd | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
13016 | check-new-release-gtk | 91.189.91.48:443 | connectivity-check.ubuntu.com | Canonical Group Limited | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
google.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
api.snapcraft.io |
| whitelisted |
105.100.168.192.in-addr.arpa |
| unknown |
changelogs.ubuntu.com |
| whitelisted |