| File name: | 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da |
| Full analysis: | https://app.any.run/tasks/2b5ad196-0c44-4c37-a955-6d77b7866567 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 12:10:15 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 030941AAF078A7013FA955F7E324A147 |
| SHA1: | 949C93B77C45A42EFC4E9940A50180EABB019416 |
| SHA256: | 72E8C8D13086DBBC51EB19EAA1D9C2E598B18C2C5F8D2D7241B95E0AA336C8DA |
| SSDEEP: | 6144:xA/jM345P9sH4oL6r++v3+T0xWMbSToZk2uFwqJZPm2vs3:xA/jqsP9O4oLZ23KR9Ok9CqJZM3 |
MALICIOUS
MOFKSYS has been detected (YARA)
- 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe (PID: 7412)
Changes the autorun value in the registry
- 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe (PID: 7412)
Create files in the Startup directory
- 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe (PID: 7412)
Uses NET.EXE to stop Windows Defender service
- cmd.exe (PID: 7652)
- net.exe (PID: 7776)
Starts NET.EXE for service management
- cmd.exe (PID: 7652)
- net.exe (PID: 7776)
SUSPICIOUS
Creates file in the systems drive root
- 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe (PID: 7412)
There is functionality for taking screenshot (YARA)
- 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe (PID: 7412)
Drops a file with a rarely used extension (PIF)
- 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe (PID: 7412)
Starts CMD.EXE for commands execution
- 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe (PID: 7412)
Executable content was dropped or overwritten
- 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe (PID: 7412)
Executes application which crashes
- iexplore.exe (PID: 7668)
Application launched itself
- 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe (PID: 7412)
INFO
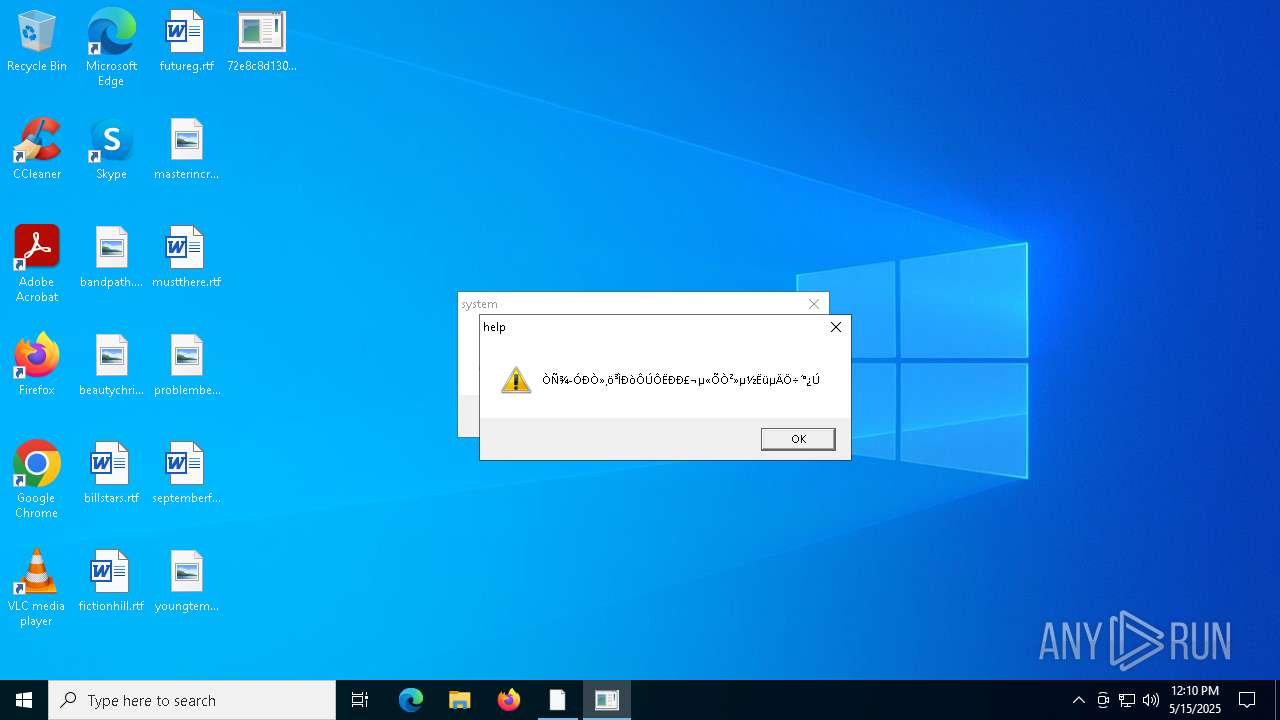
The sample compiled with chinese language support
- 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe (PID: 7412)
Checks supported languages
- 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe (PID: 7412)
- system.pif (PID: 7904)
- help.exe (PID: 7932)
- 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe (PID: 7956)
Reads the computer name
- 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe (PID: 7412)
- help.exe (PID: 7932)
- 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe (PID: 7956)
- system.pif (PID: 7904)
Creates files or folders in the user directory
- 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe (PID: 7412)
UPX packer has been detected
- 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe (PID: 7412)
Auto-launch of the file from Startup directory
- 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe (PID: 7412)
Auto-launch of the file from Registry key
- 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe (PID: 7412)
Manual execution by a user
- system.pif (PID: 7904)
- help.exe (PID: 7932)
Reads the software policy settings
- slui.exe (PID: 6028)
Checks proxy server information
- slui.exe (PID: 6028)
Create files in a temporary directory
- 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe (PID: 7956)
Failed to create an executable file in Windows directory
- 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe (PID: 7956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:05:15 20:00:11+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 28672 |
| InitializedDataSize: | 20480 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6e6a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | |
| FileDescription: | WinPing |
| FileVersion: | 1, 0, 0, 1 |
| InternalName: | WinPing |
| LegalCopyright: | Copyright ? 2013 |
| LegalTrademarks: | - |
| OriginalFileName: | WinPing.exe |
| PrivateBuild: | - |
| ProductName: | WinPing |
| ProductVersion: | 1, 0, 0, 1 |
| SpecialBuild: | - |
Total processes
139
Monitored processes
11
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6028 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7412 | "C:\Users\admin\Desktop\72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe" | C:\Users\admin\Desktop\72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: WinPing Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 7652 | /c net stop MpsSvc | C:\Windows\SysWOW64\cmd.exe | — | 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7660 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7668 | "C:\Program Files (x86)\Internet Explorer\iexplore.exe" | C:\Program Files (x86)\Internet Explorer\iexplore.exe | 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 3221225477 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7776 | net stop MpsSvc | C:\Windows\SysWOW64\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7796 | C:\WINDOWS\system32\net1 stop MpsSvc | C:\Windows\SysWOW64\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7860 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7668 -s 84 | C:\Windows\SysWOW64\WerFault.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7904 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\system.pif" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\system.pif | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: WinPing Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 7932 | C:\Users\admin\AppData\Roaming\InstallDir\help.exe | C:\Users\admin\AppData\Roaming\InstallDir\help.exe | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: WinPing Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
4 011
Read events
4 007
Write events
4
Delete events
0
Modification events
| (PID) Process: | (7412) 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | help |
Value: C:\Users\admin\AppData\Roaming\InstallDir\help.exe | |||
| (PID) Process: | (7412) 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | help |
Value: C:\Users\admin\AppData\Roaming\InstallDir\help.exe | |||
| (PID) Process: | (7956) 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
Executable files
2
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7412 | 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\system.pif | executable | |
MD5:030941AAF078A7013FA955F7E324A147 | SHA256:72E8C8D13086DBBC51EB19EAA1D9C2E598B18C2C5F8D2D7241B95E0AA336C8DA | |||
| 7412 | 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe | C:\Users\admin\AppData\Roaming\InstallDir\help.exe | executable | |
MD5:030941AAF078A7013FA955F7E324A147 | SHA256:72E8C8D13086DBBC51EB19EAA1D9C2E598B18C2C5F8D2D7241B95E0AA336C8DA | |||
| 7956 | 72e8c8d13086dbbc51eb19eaa1d9c2e598b18c2c5f8d2d7241b95e0aa336c8da.exe | C:\Users\admin\AppData\Local\Temp\~DFD3F3D3DA8251814D.TMP | binary | |
MD5:A7927E532661FC1CF2F7BA6150B5BC66 | SHA256:C629A7AD85E40EED1ED4C13E6F5DC64ED848352F8575BE5C94B0355B50C99EA1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
22
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6488 | RUXIMICS.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6488 | RUXIMICS.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6488 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2104 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6488 | RUXIMICS.exe | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
6488 | RUXIMICS.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
2104 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7256 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |