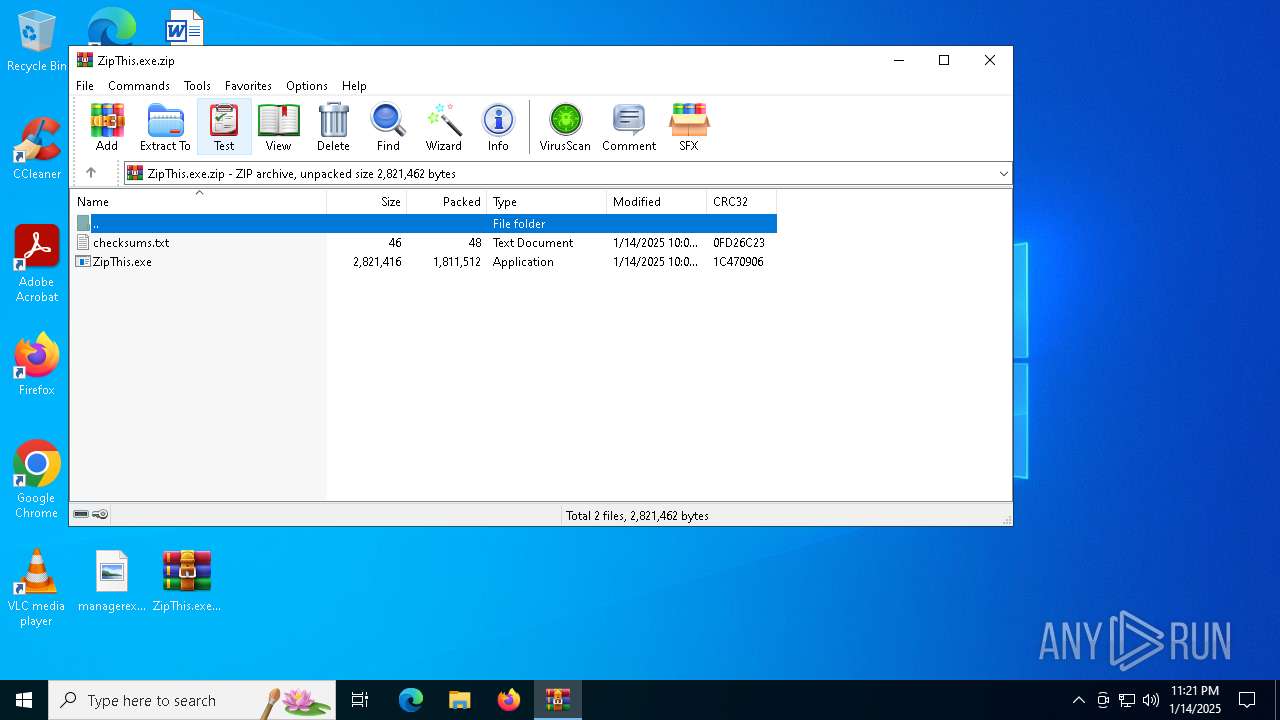
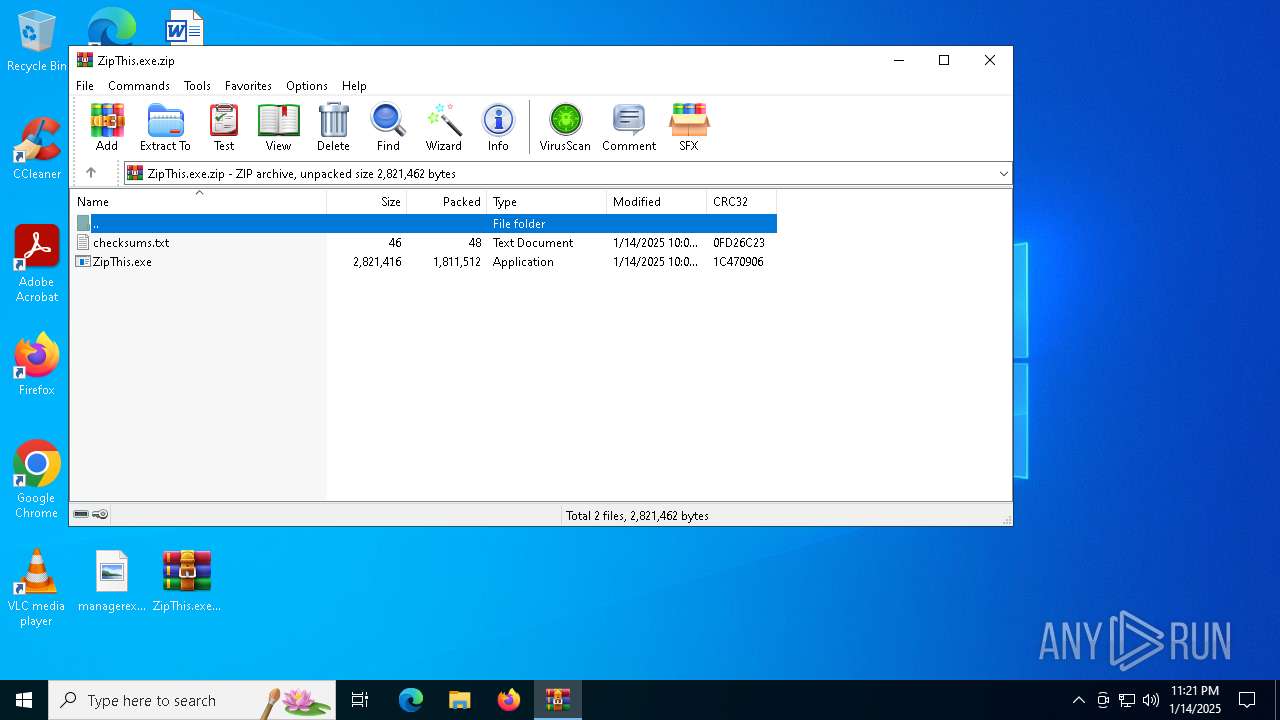
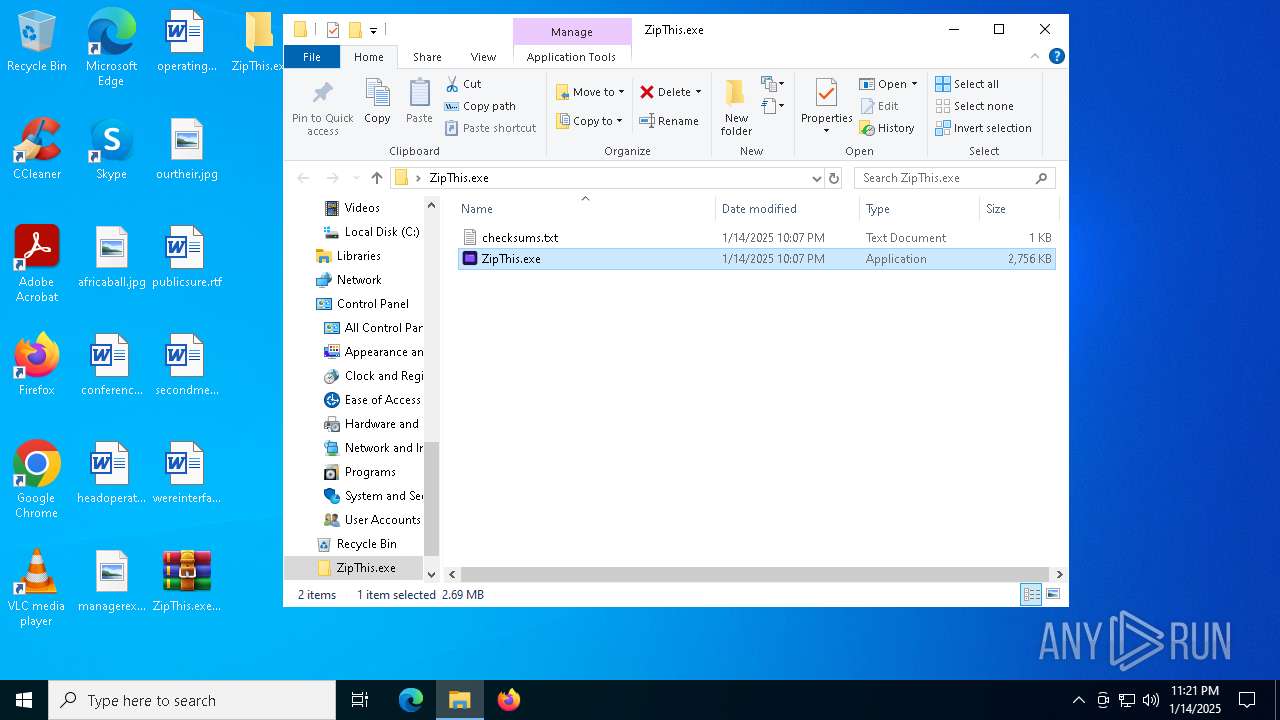
| File name: | ZipThis.exe.zip |
| Full analysis: | https://app.any.run/tasks/379491f0-b1c9-4f12-a79d-04300284c2c6 |
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2025, 23:21:20 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 15DB35DF8AC09548A7A9B9844143BF85 |
| SHA1: | 43F3CB6172022C5D1A537455059E92322642DC0B |
| SHA256: | 72E86E145AA9C8AD3847144184B224ED23FFAF8D120DDDE53C20392E937D5299 |
| SSDEEP: | 98304:RZNf34+RWuF2zehSiNIwV8YIgojxuI0V/Y7DNsbdYhJ5UynXGsvKNPUko90m7D9U:CLfKRm6 |
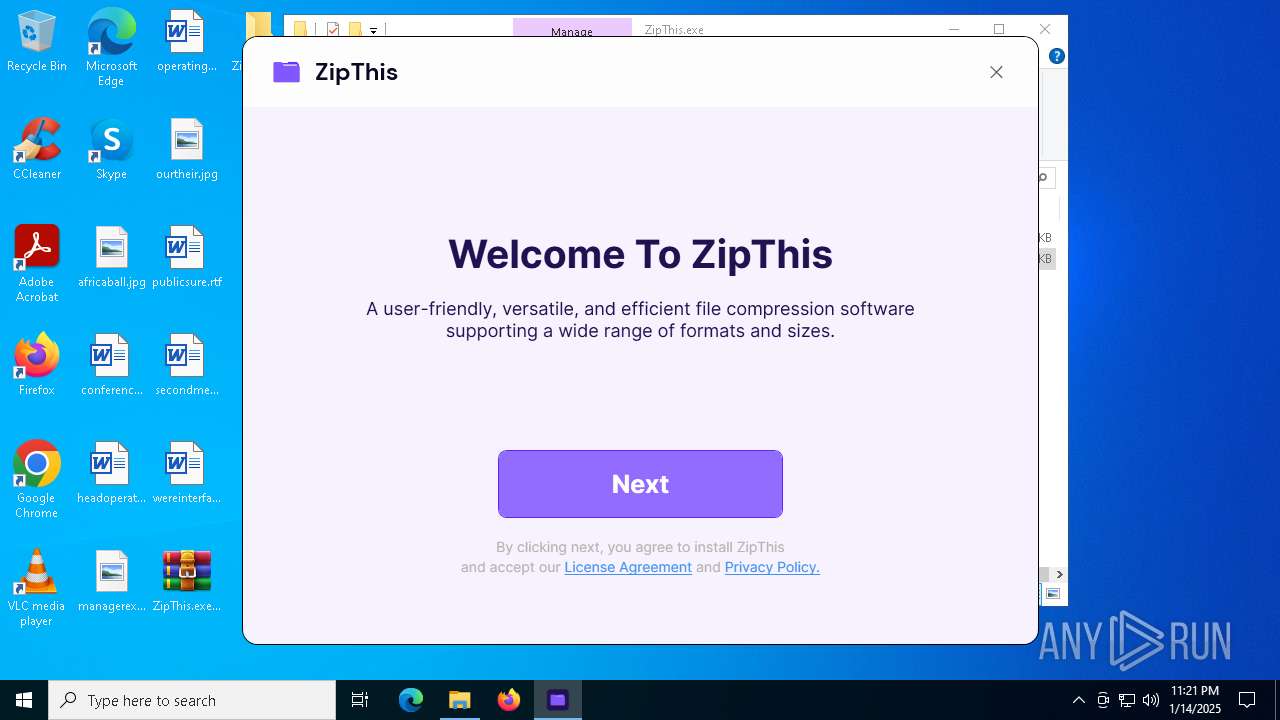
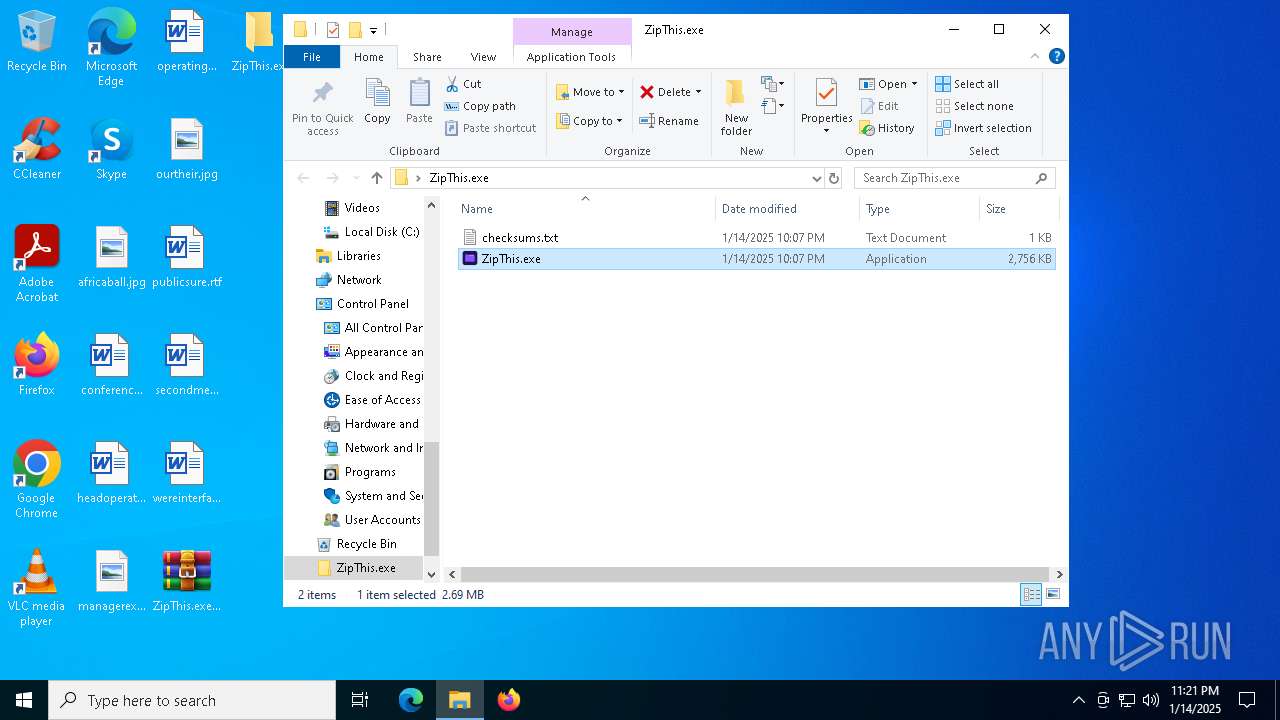
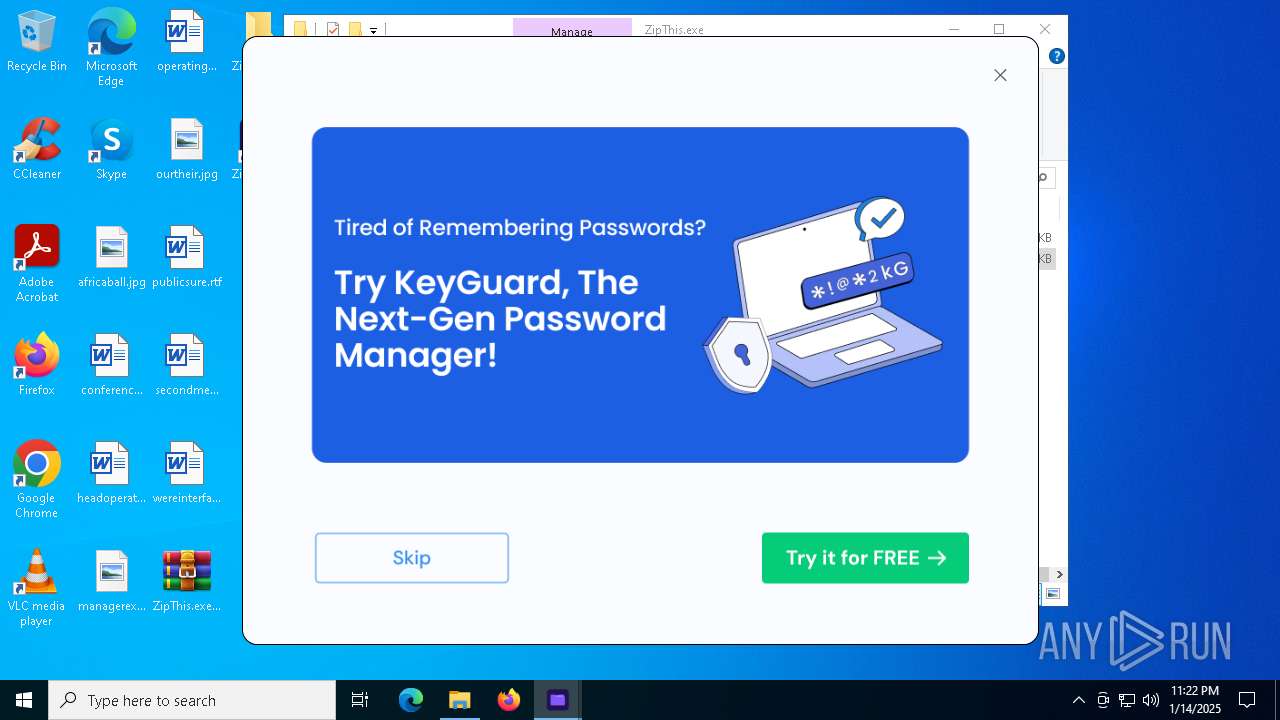
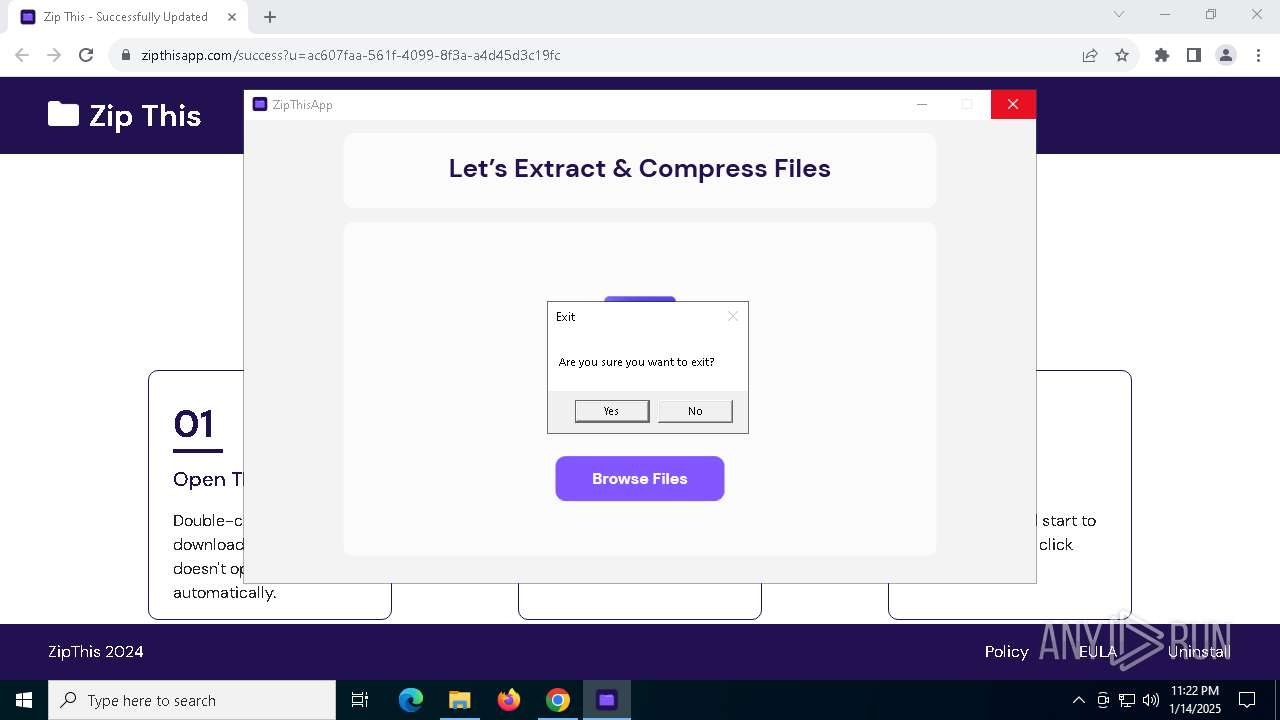
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 1572)
Changes powershell execution policy (RemoteSigned)
- ZipThis.exe (PID: 7128)
GENERIC has been found (auto)
- ZipThis.exe (PID: 7128)
SUSPICIOUS
Application launched itself
- ZipThis.exe (PID: 6956)
Reads security settings of Internet Explorer
- ZipThis.exe (PID: 6956)
- ZipThis.exe (PID: 7128)
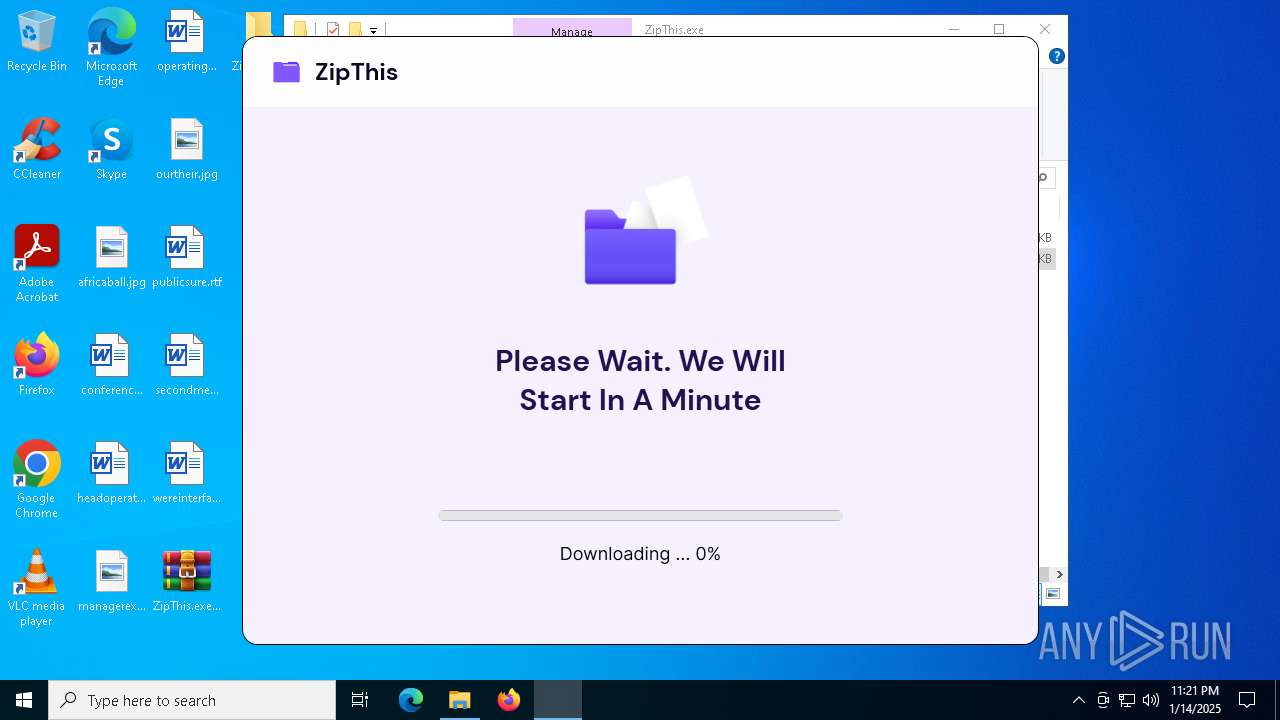
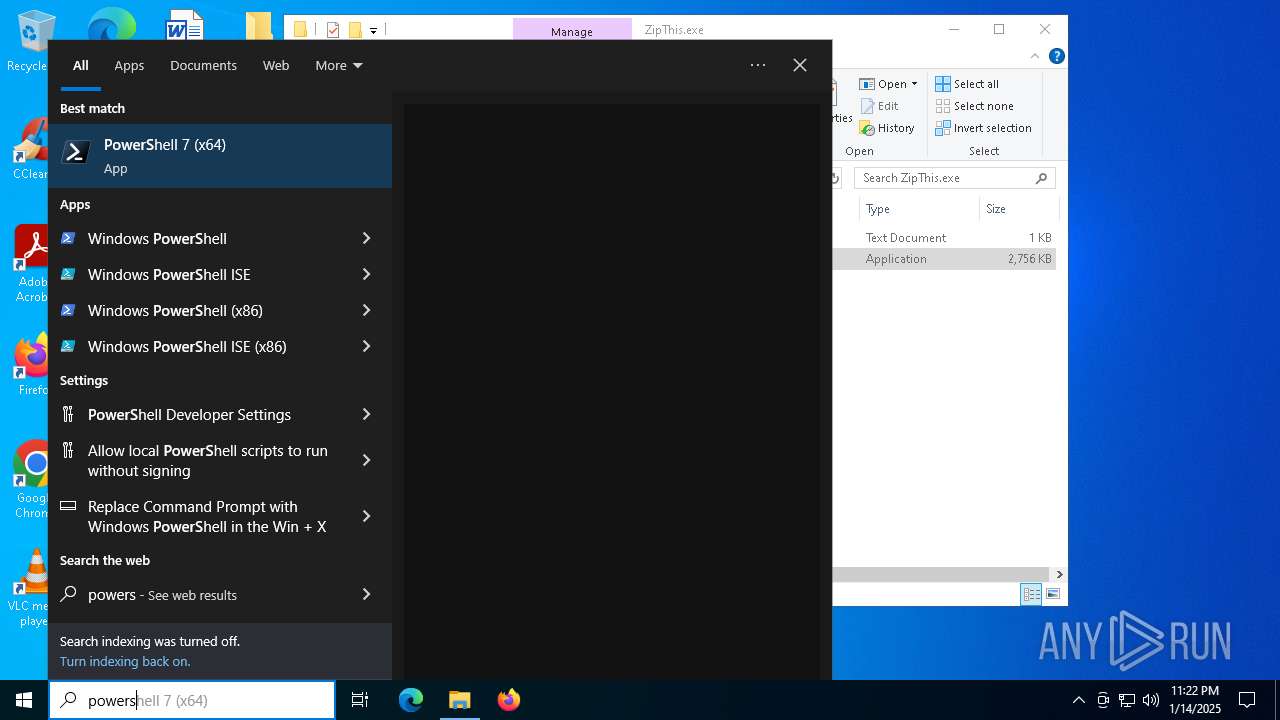
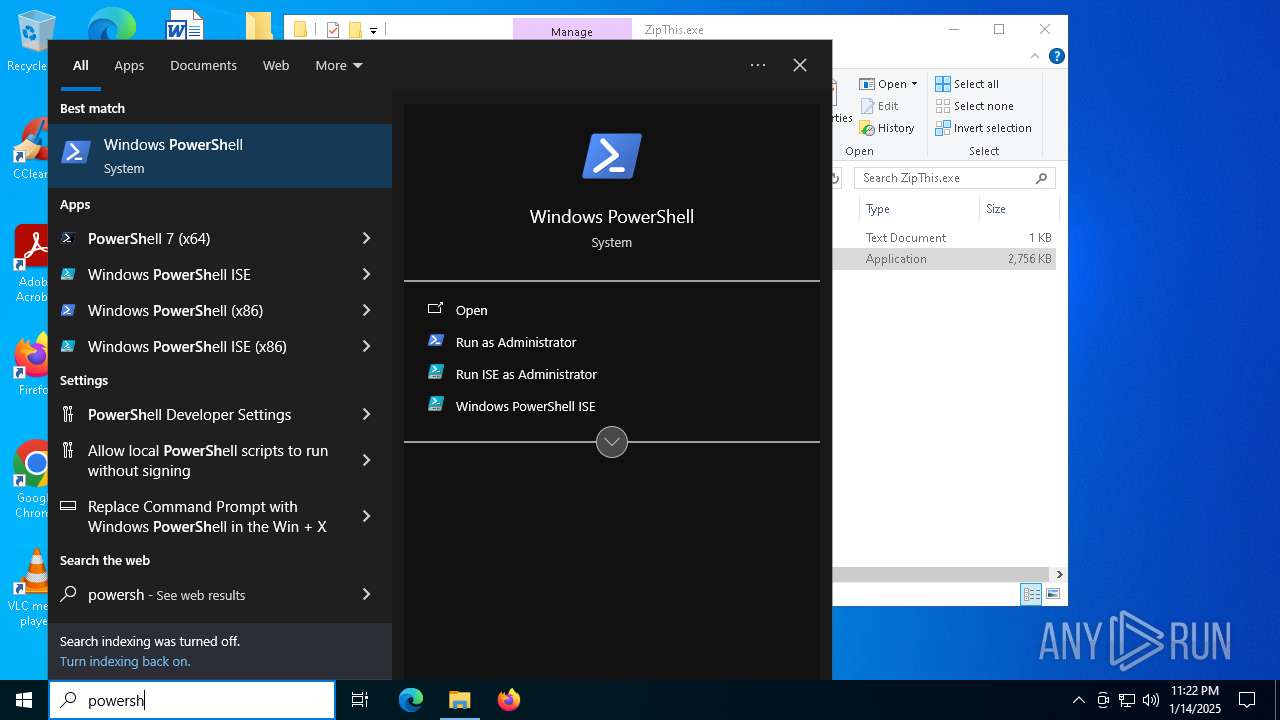
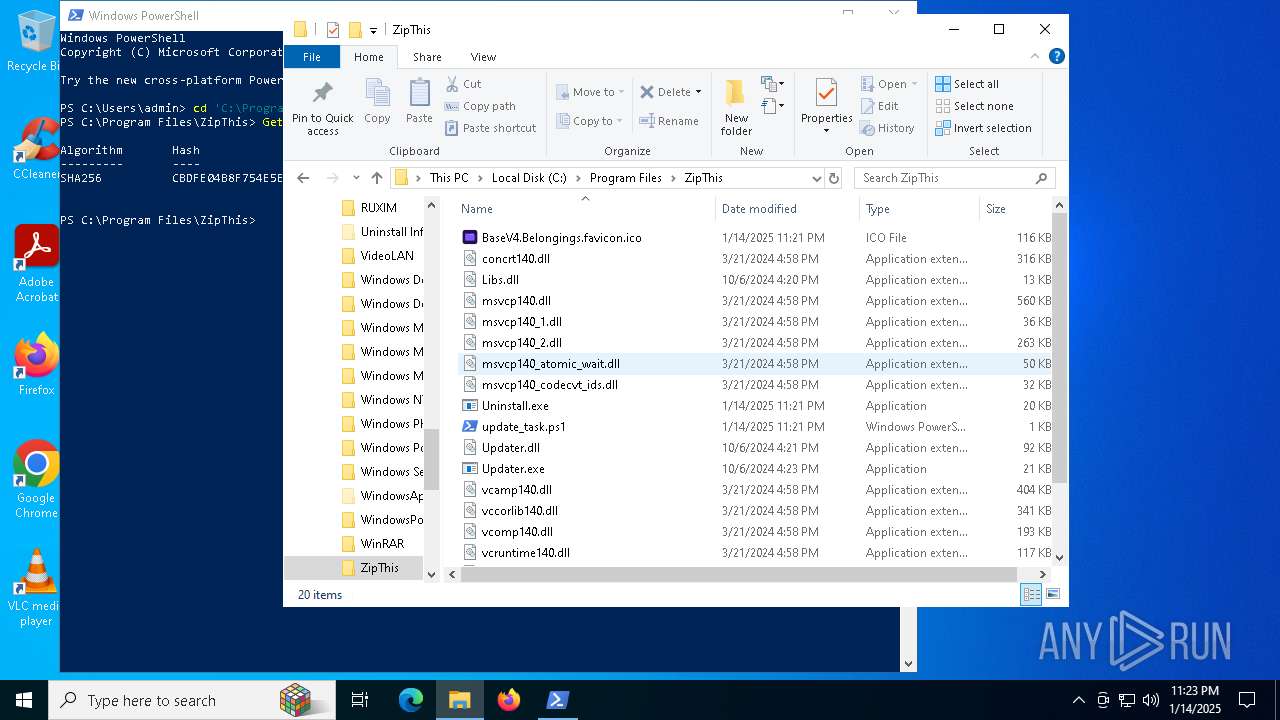
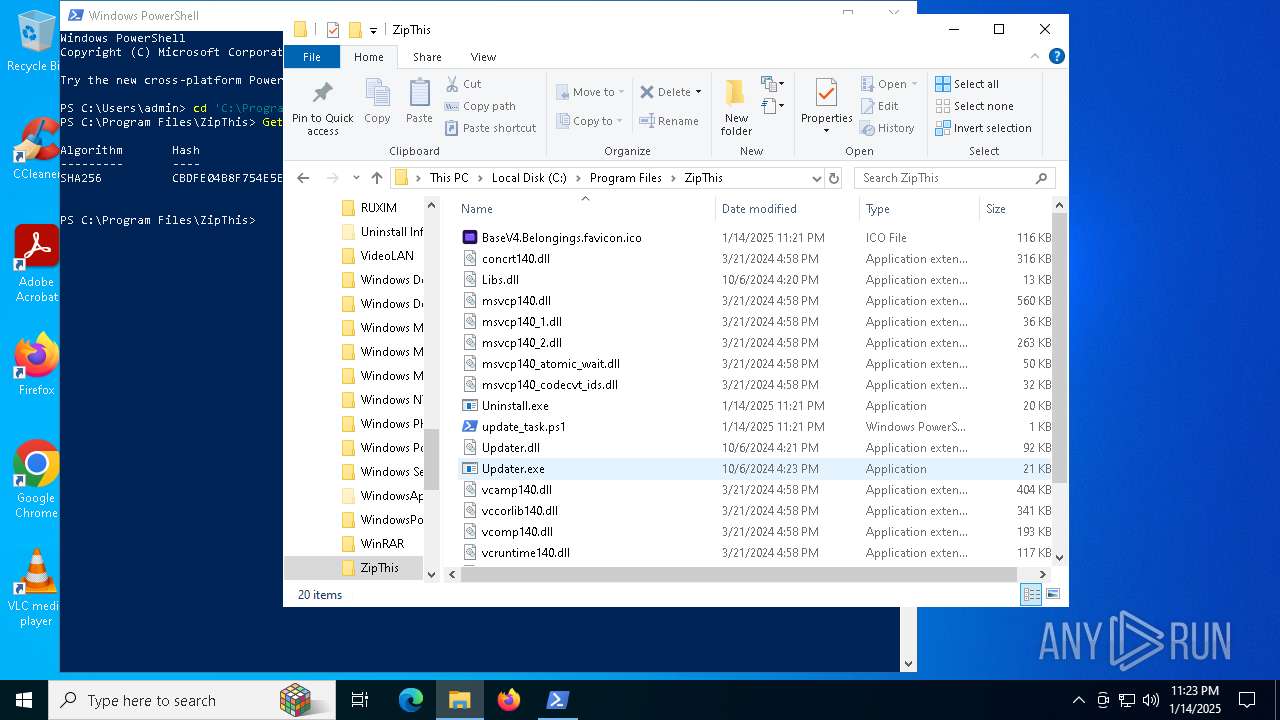
The process executes Powershell scripts
- ZipThis.exe (PID: 7128)
Starts POWERSHELL.EXE for commands execution
- ZipThis.exe (PID: 7128)
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 3608)
The process drops C-runtime libraries
- ZipThis.exe (PID: 7128)
Executable content was dropped or overwritten
- ZipThis.exe (PID: 7128)
Searches for installed software
- ZipThis.exe (PID: 7128)
Creates a software uninstall entry
- ZipThis.exe (PID: 7128)
Process drops legitimate windows executable
- ZipThis.exe (PID: 7128)
Reads the date of Windows installation
- ZipThis.exe (PID: 6956)
INFO
The process uses the downloaded file
- WinRAR.exe (PID: 1572)
- ZipThis.exe (PID: 6956)
- powershell.exe (PID: 3608)
- ZipThis.exe (PID: 7128)
- chrome.exe (PID: 4224)
- chrome.exe (PID: 2132)
- chrome.exe (PID: 4164)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1572)
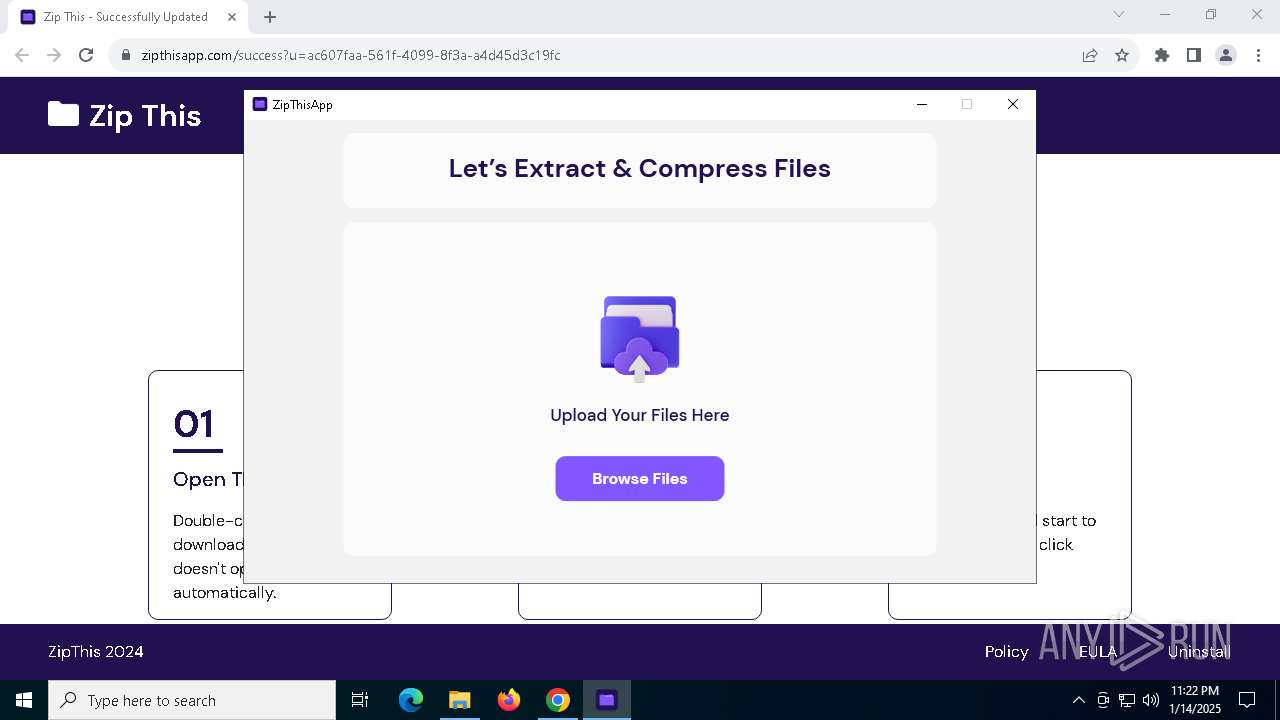
Creates files or folders in the user directory
- ZipThis.exe (PID: 6956)
Checks supported languages
- ZipThis.exe (PID: 6956)
- Updater.exe (PID: 6472)
- ZipThis.exe (PID: 7128)
Reads Environment values
- ZipThis.exe (PID: 6956)
- ZipThis.exe (PID: 7128)
- ZipThisApp.exe (PID: 4628)
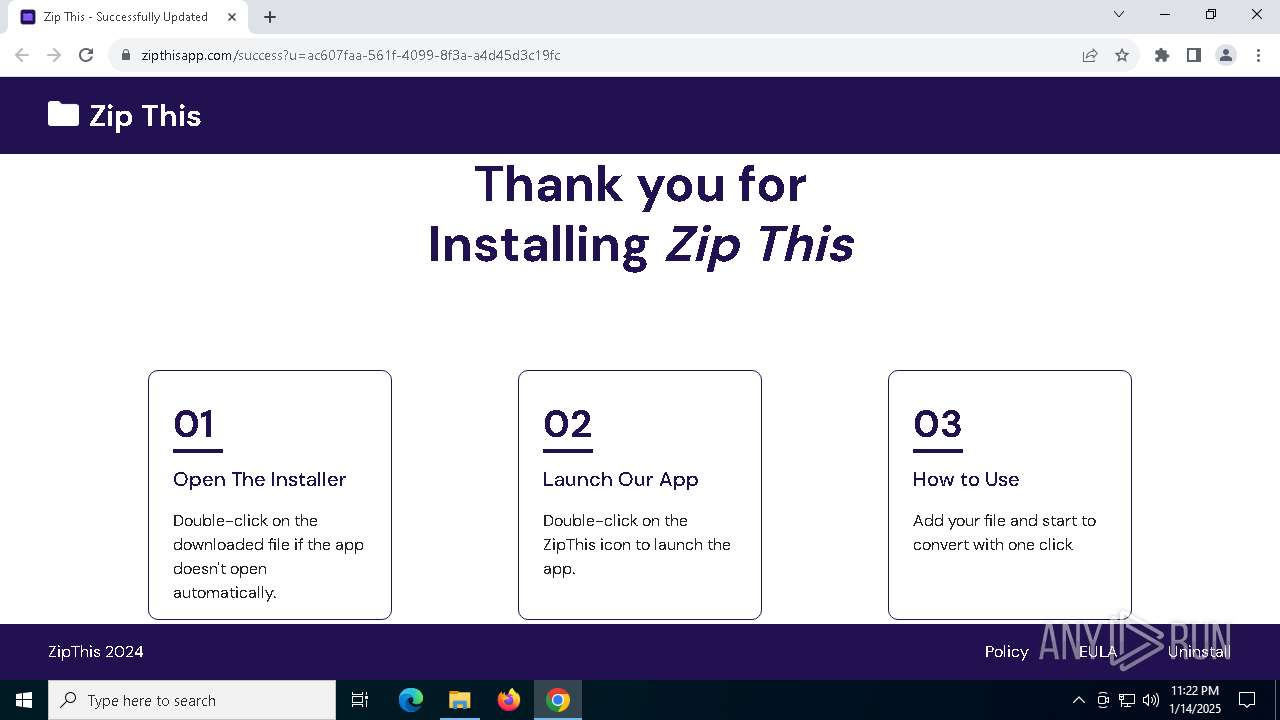
Manual execution by a user
- ZipThis.exe (PID: 6956)
- powershell.exe (PID: 4140)
- Updater.exe (PID: 6472)
Reads the computer name
- ZipThis.exe (PID: 6956)
- Updater.exe (PID: 6472)
- ZipThis.exe (PID: 7128)
Reads the machine GUID from the registry
- ZipThis.exe (PID: 6956)
- ZipThisApp.exe (PID: 4628)
- Updater.exe (PID: 6472)
- ZipThis.exe (PID: 7128)
Disables trace logs
- ZipThis.exe (PID: 6956)
- ZipThis.exe (PID: 7128)
Checks proxy server information
- ZipThis.exe (PID: 6956)
- ZipThis.exe (PID: 7128)
- ZipThisApp.exe (PID: 4628)
Reads the software policy settings
- ZipThis.exe (PID: 7128)
- ZipThisApp.exe (PID: 4628)
- Updater.exe (PID: 6472)
- ZipThis.exe (PID: 6956)
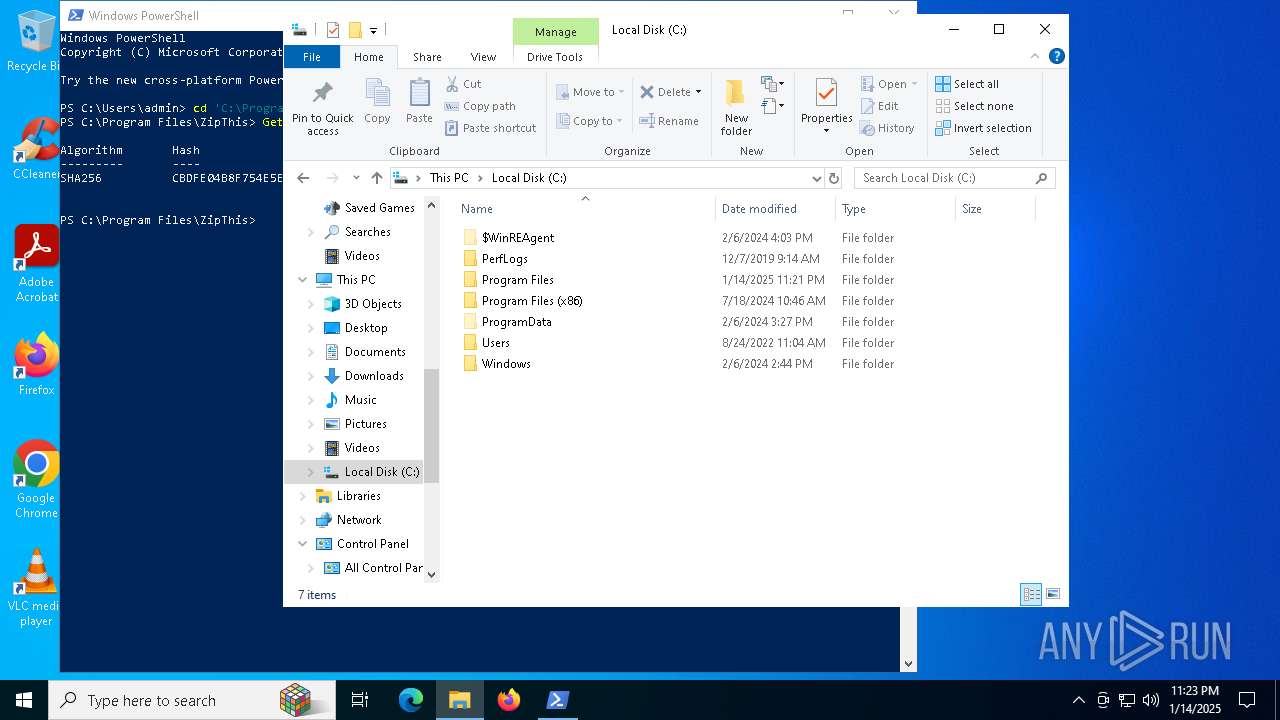
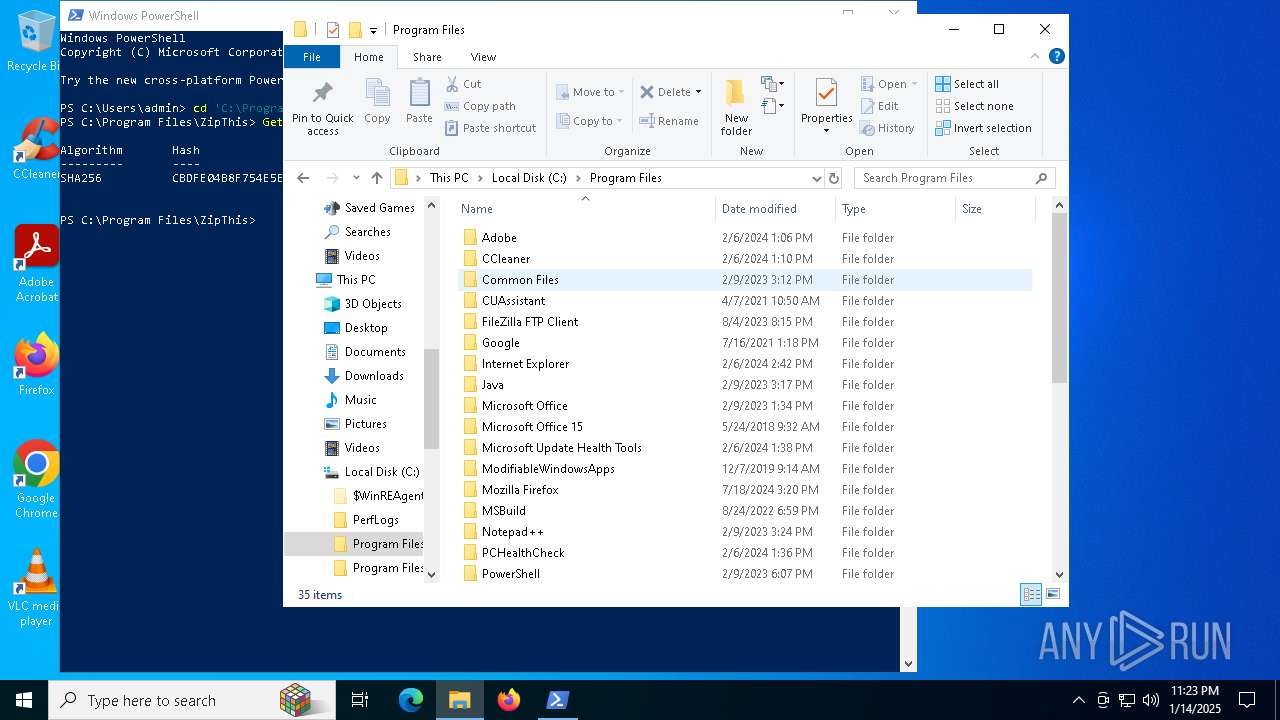
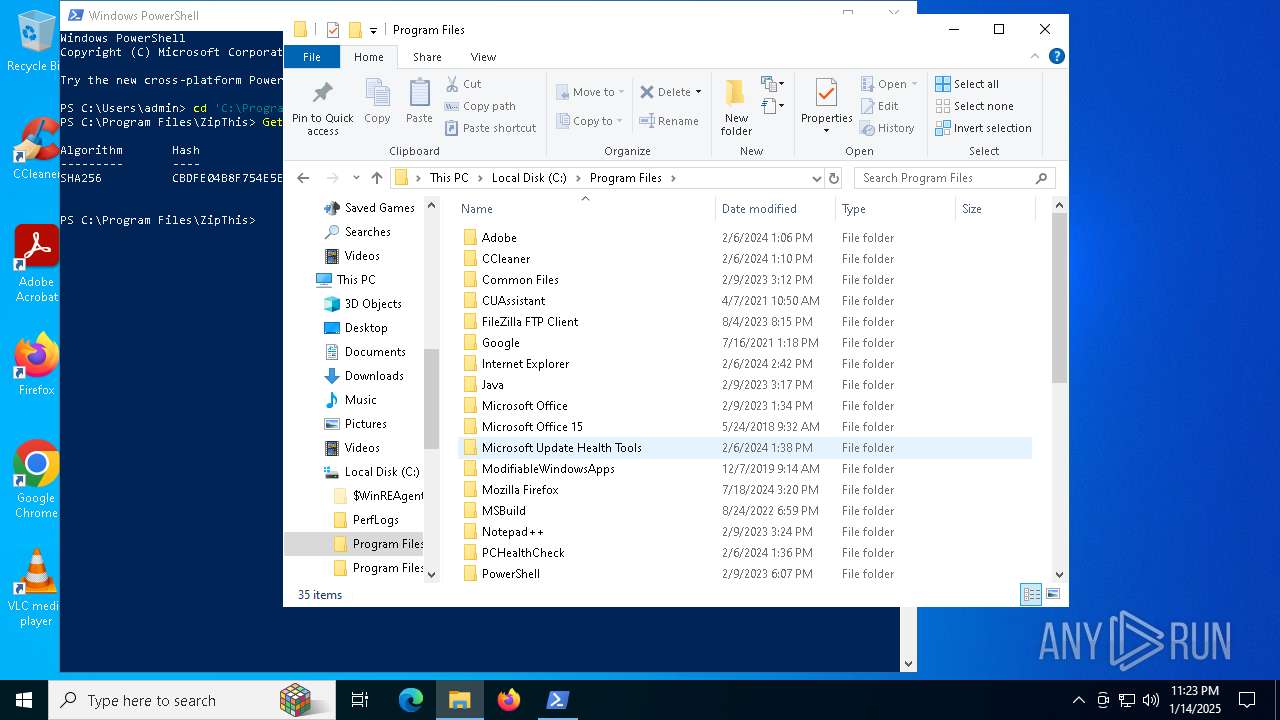
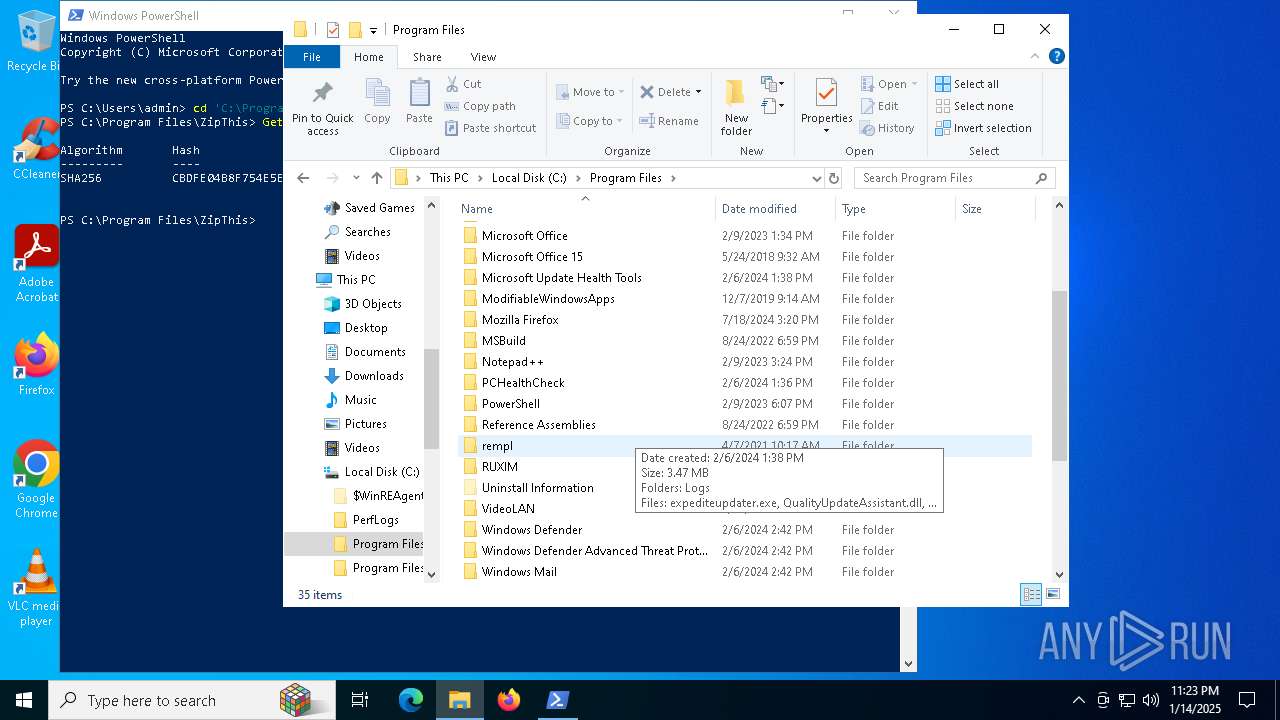
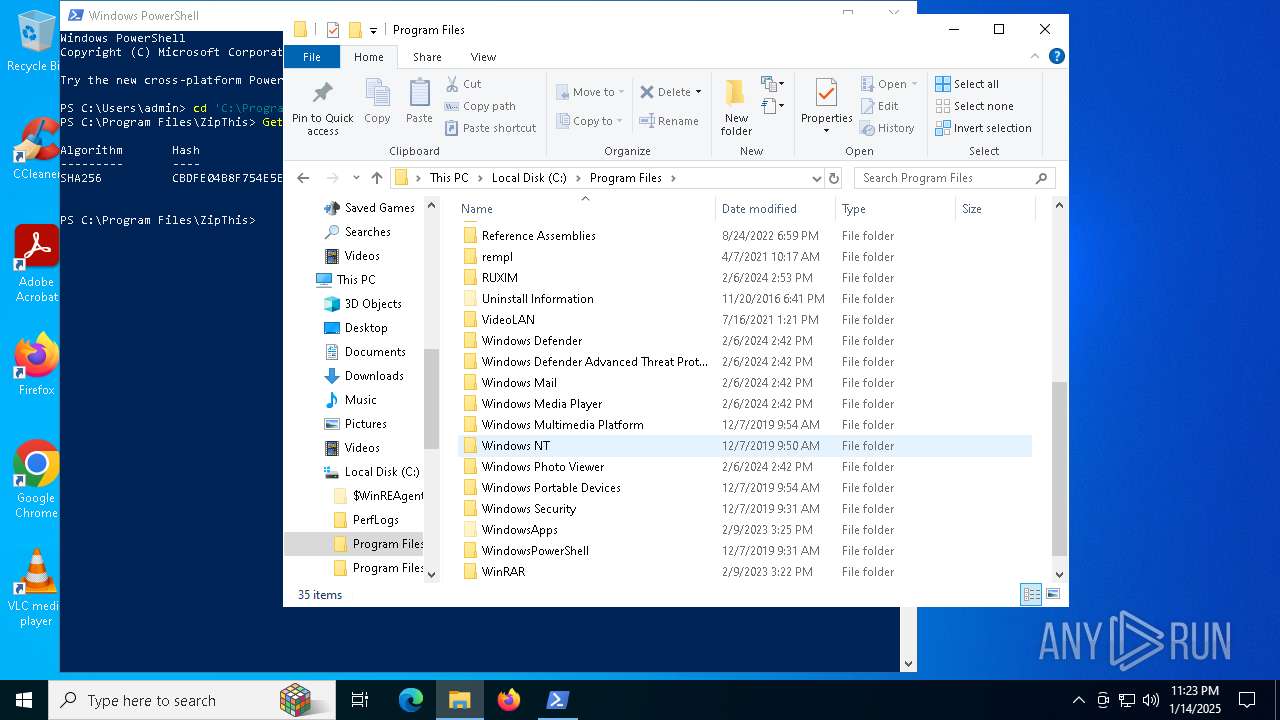
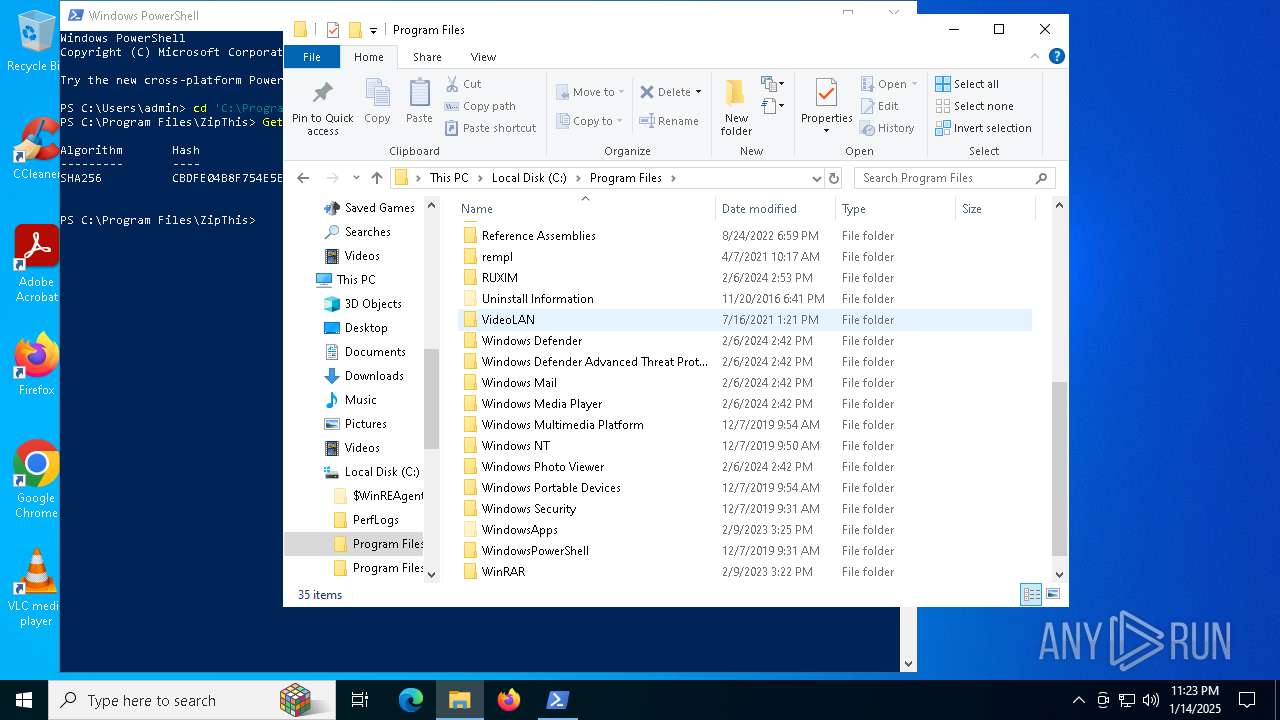
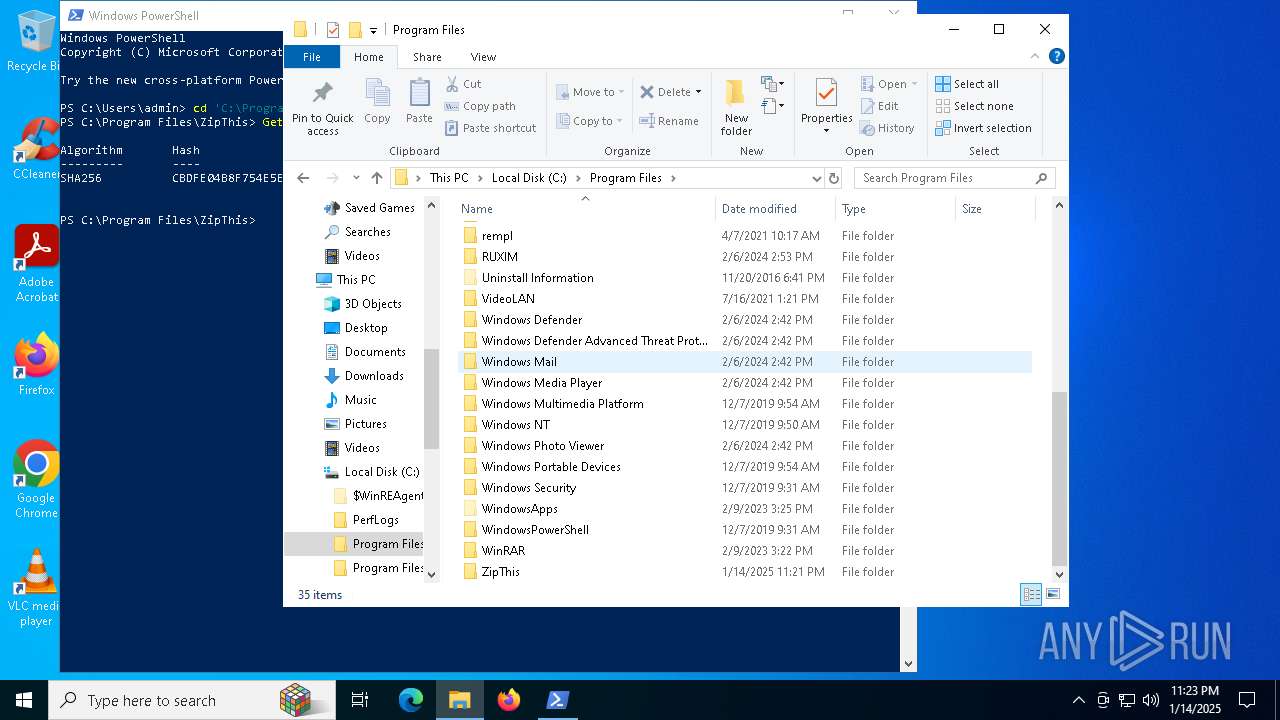
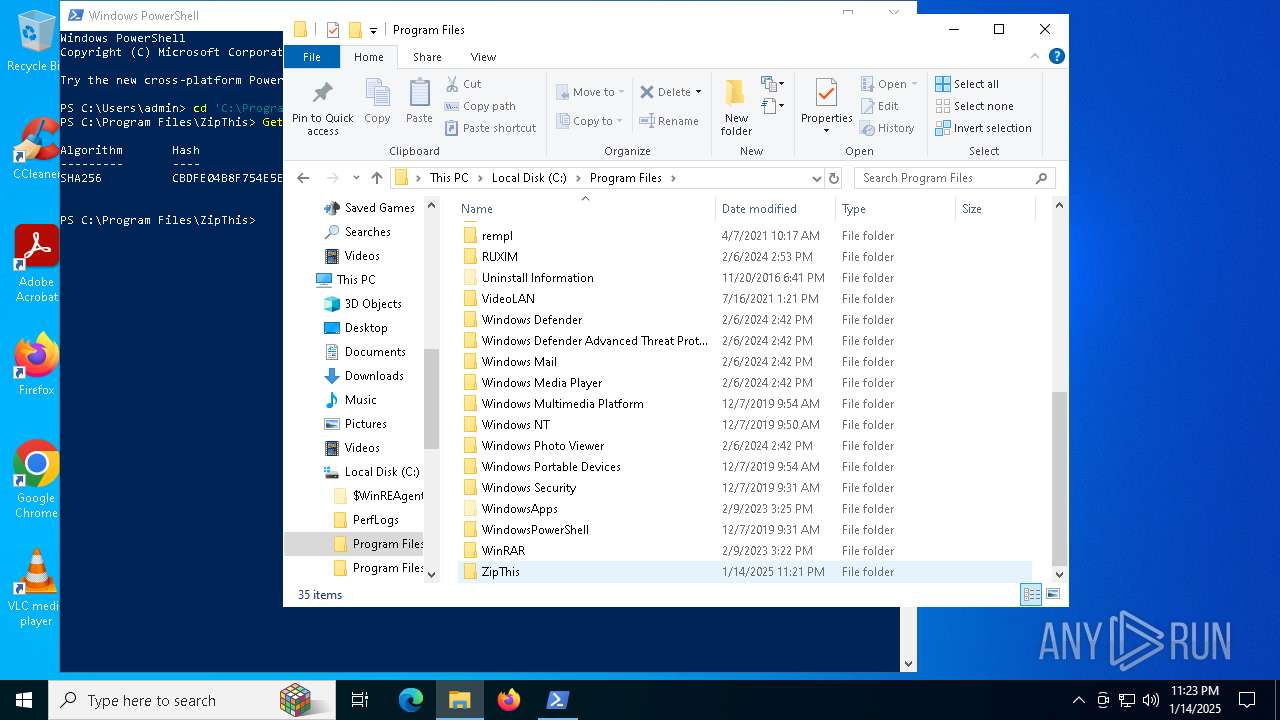
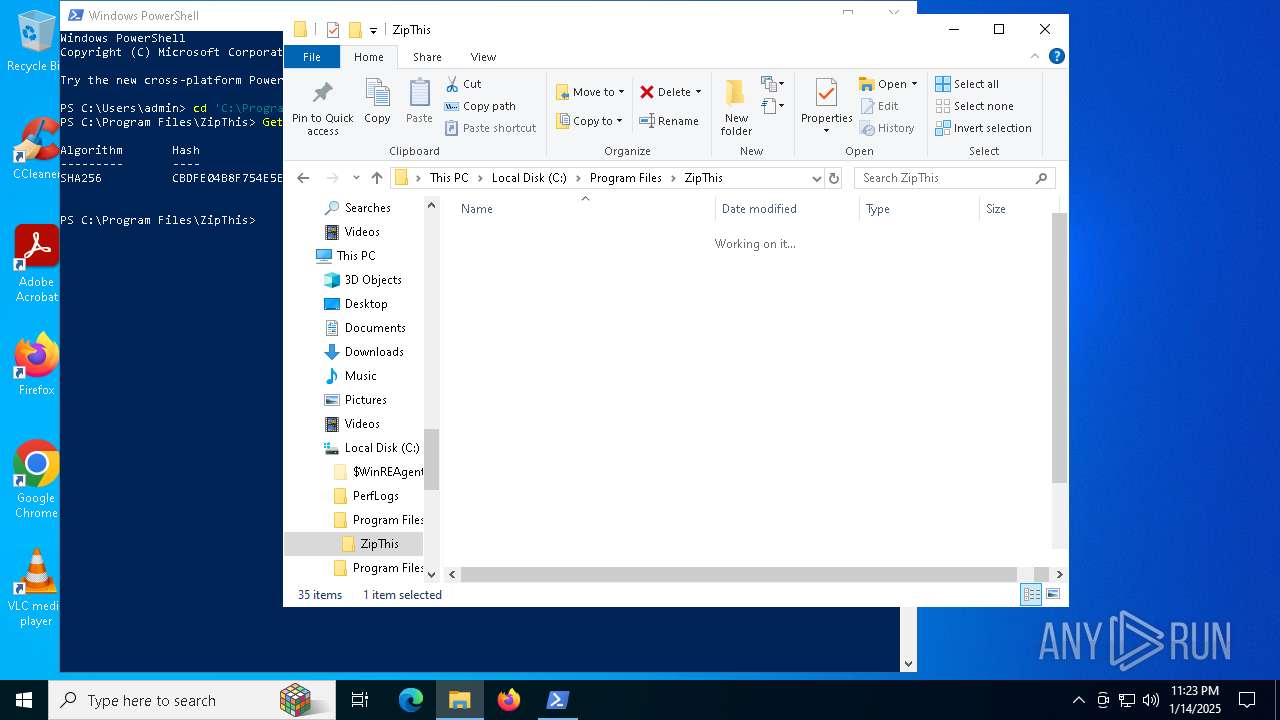
Creates files in the program directory
- ZipThis.exe (PID: 7128)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 3608)
The sample compiled with english language support
- ZipThis.exe (PID: 7128)
Application launched itself
- chrome.exe (PID: 6216)
Process checks computer location settings
- ZipThis.exe (PID: 7128)
- ZipThis.exe (PID: 6956)
Checks current location (POWERSHELL)
- powershell.exe (PID: 4140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:01:14 22:07:22 |
| ZipCRC: | 0x1c470906 |
| ZipCompressedSize: | 1811512 |
| ZipUncompressedSize: | 2821416 |
| ZipFileName: | ZipThis.exe |
Total processes
162
Monitored processes
31
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1572 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\ZipThis.exe.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=4576 --field-trial-handle=1872,i,15887686584713950092,876410279600311895,262144 --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6136 --field-trial-handle=1872,i,15887686584713950092,876410279600311895,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2428 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5648 --field-trial-handle=1872,i,15887686584713950092,876410279600311895,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5608 --field-trial-handle=1872,i,15887686584713950092,876410279600311895,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
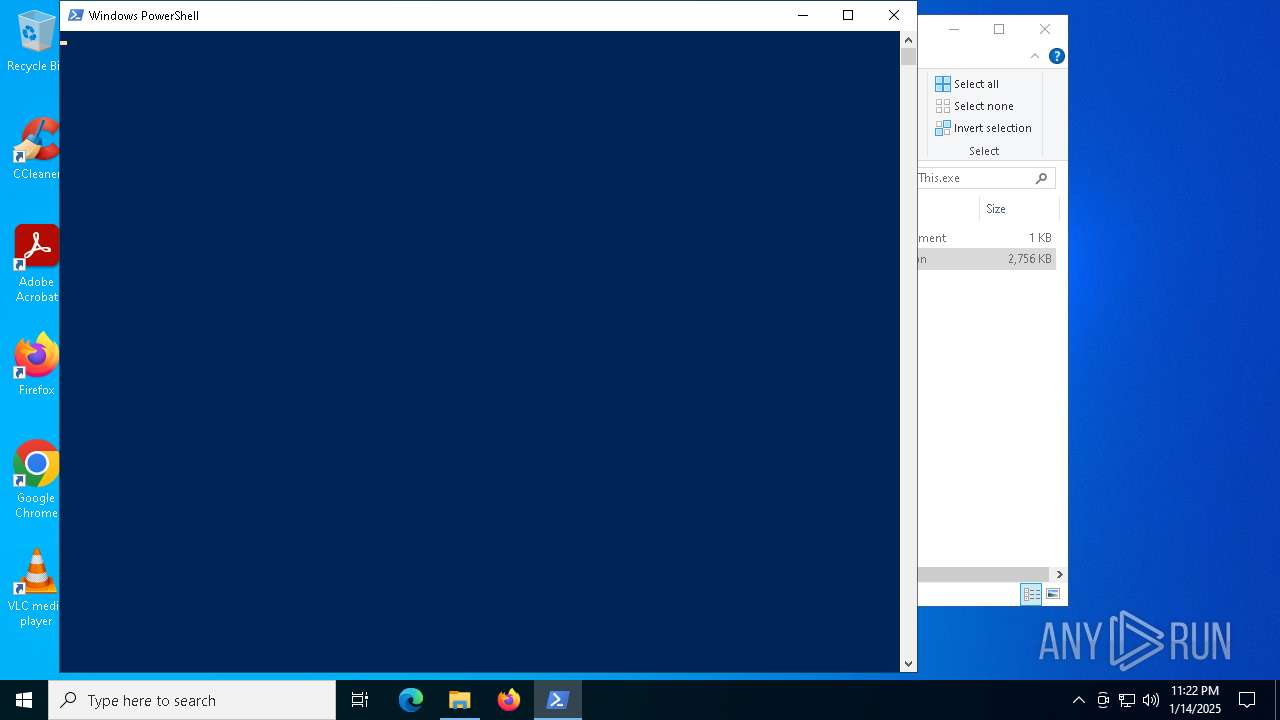
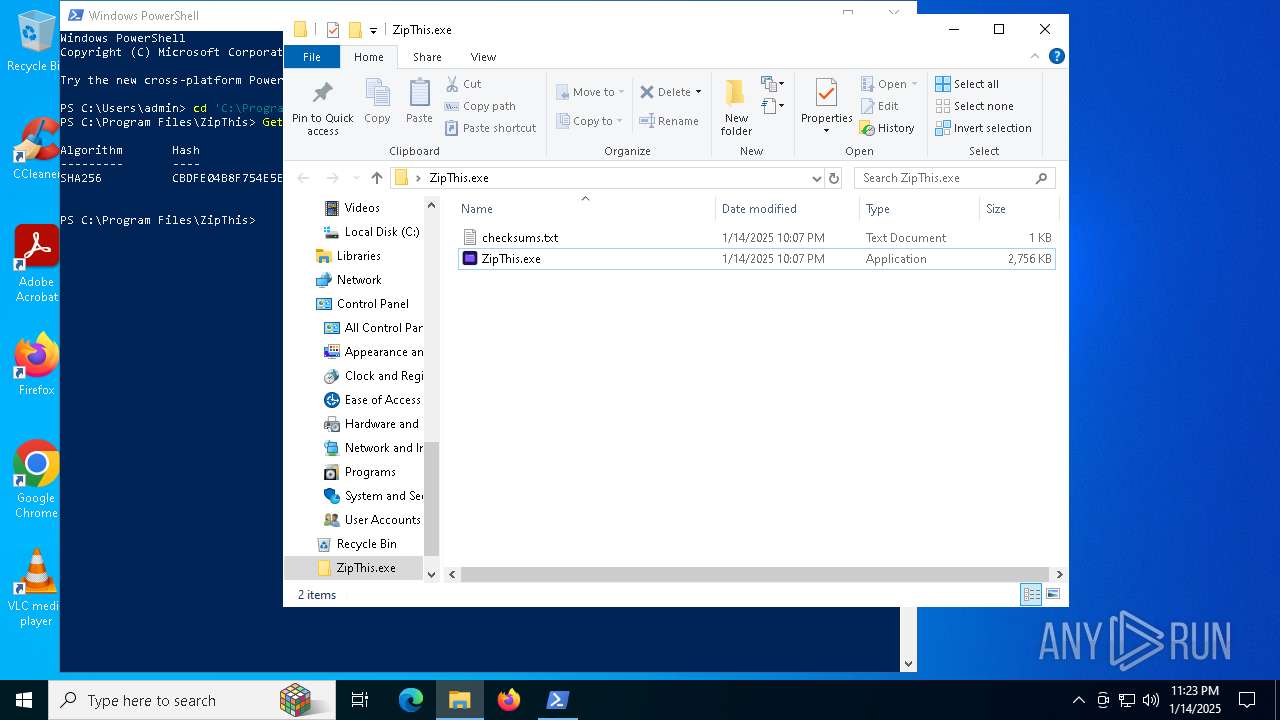
| 3608 | "powershell.exe" -ep RemoteSigned -File "C:\Program Files\ZipThis\update_task.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | ZipThis.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4140 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5452 --field-trial-handle=1872,i,15887686584713950092,876410279600311895,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4224 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6116 --field-trial-handle=1872,i,15887686584713950092,876410279600311895,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
31 623
Read events
31 524
Write events
84
Delete events
15
Modification events
| (PID) Process: | (1572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\ZipThis.exe.zip | |||
| (PID) Process: | (1572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (1572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
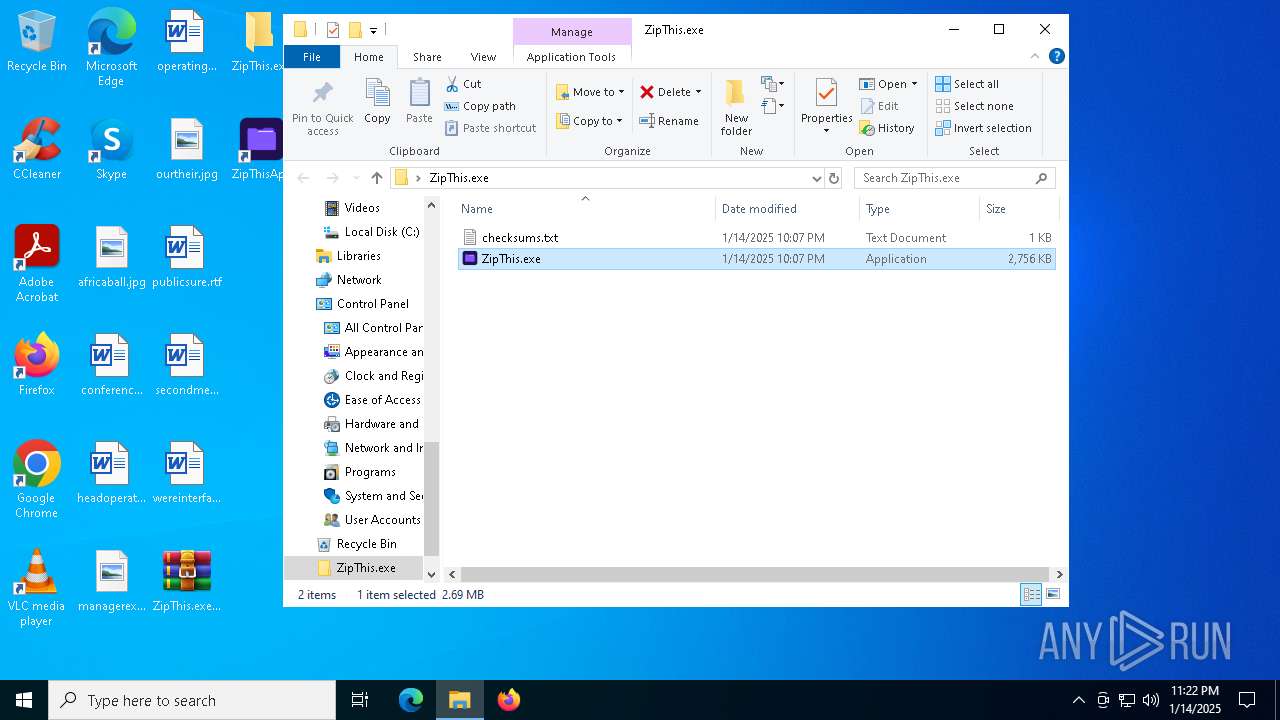
Executable files
26
Suspicious files
110
Text files
46
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
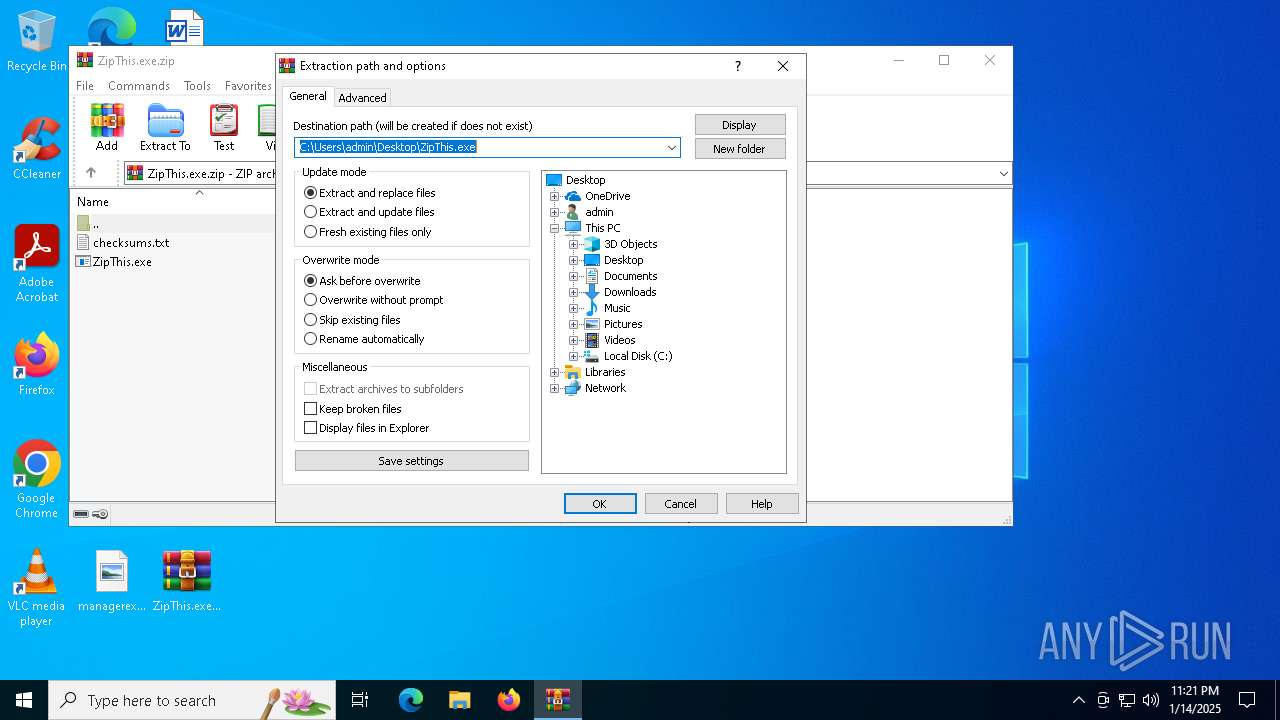
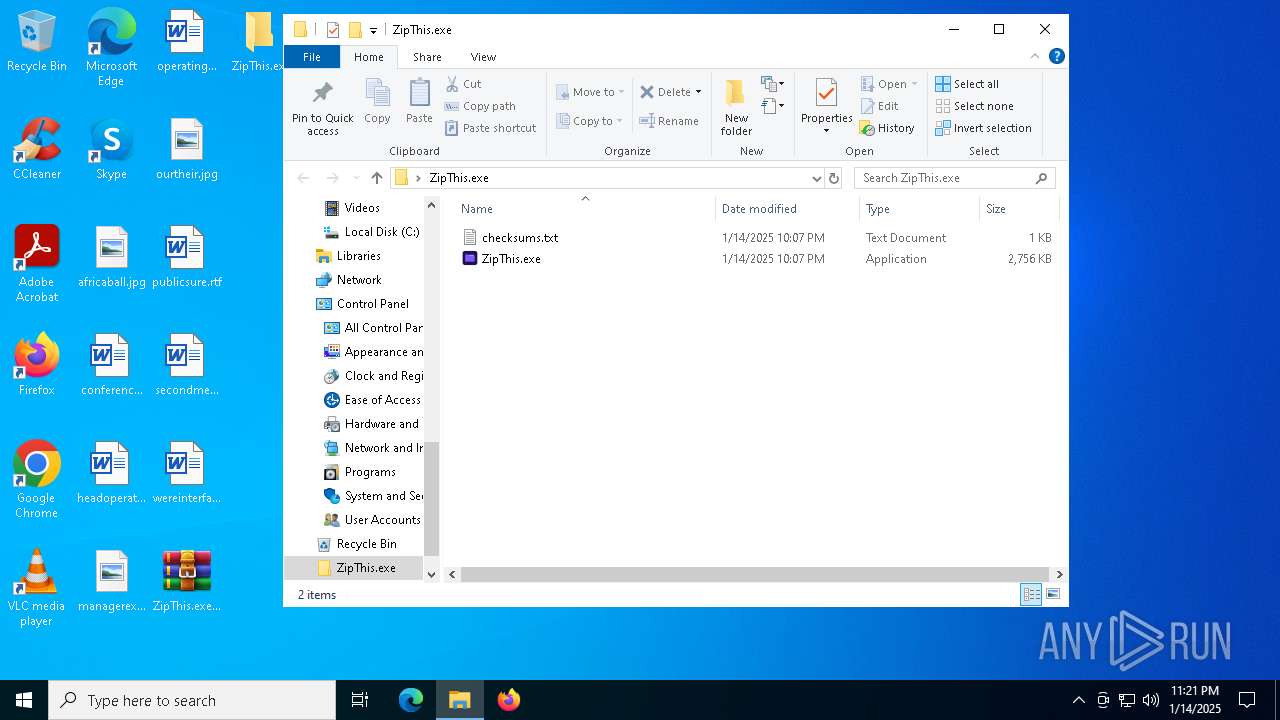
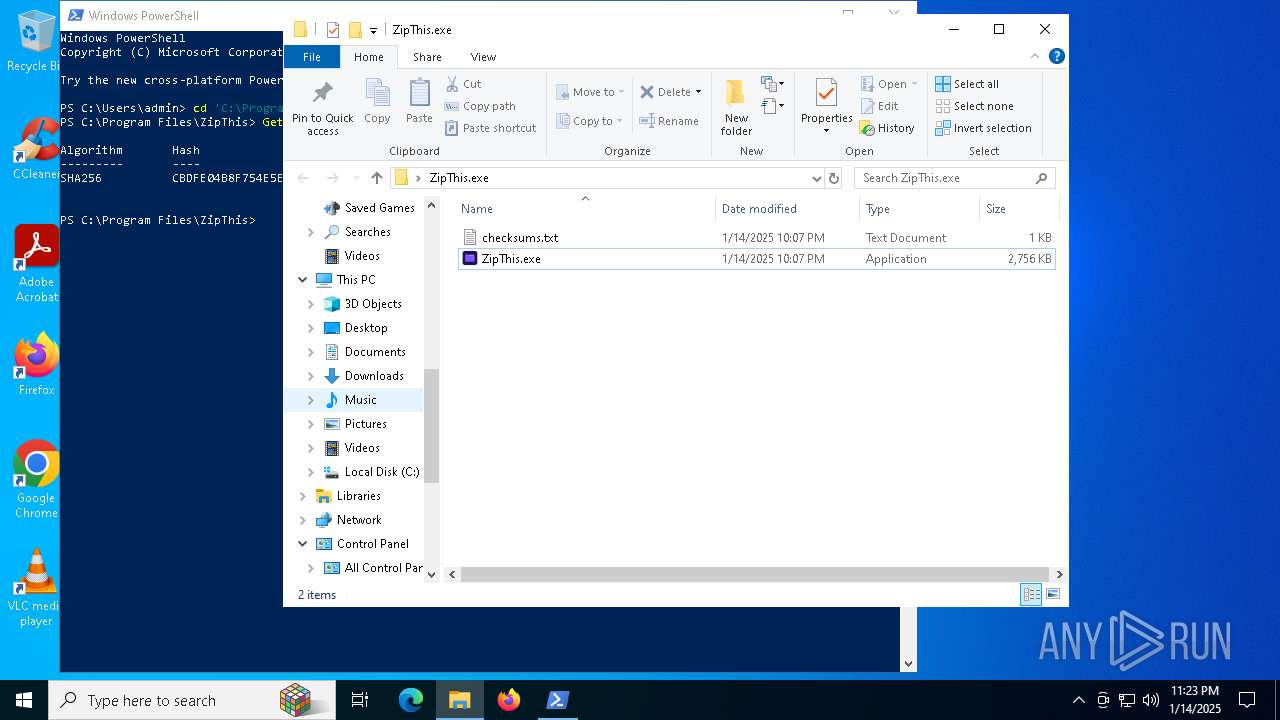
| 1572 | WinRAR.exe | C:\Users\admin\Desktop\ZipThis.exe\ZipThis.exe | executable | |
MD5:34E759DF0CB0BF304C9FD1D6B9631BCE | SHA256:7D607EE9ACBB7C4747B79F4E891736AD4AB30BF7BBF9B3519CA2B6E6553766DC | |||
| 6956 | ZipThis.exe | C:\Users\admin\AppData\Local\ZipThis\zipthisUserId.txt | text | |
MD5:16DC49A140E4C608381A1B98799466FD | SHA256:460AB54E068EE7497F535C16A8898023865919148CF41972EAF51ED53CE85E42 | |||
| 6956 | ZipThis.exe | C:\Users\admin\AppData\Roaming\SMCR\userId.txt | text | |
MD5:16DC49A140E4C608381A1B98799466FD | SHA256:460AB54E068EE7497F535C16A8898023865919148CF41972EAF51ED53CE85E42 | |||
| 3608 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_y2h10y4z.uhn.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3608 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zzgvxm4n.jtl.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7128 | ZipThis.exe | C:\Program Files\ZipThis\zipthisUserId.txt | text | |
MD5:16DC49A140E4C608381A1B98799466FD | SHA256:460AB54E068EE7497F535C16A8898023865919148CF41972EAF51ED53CE85E42 | |||
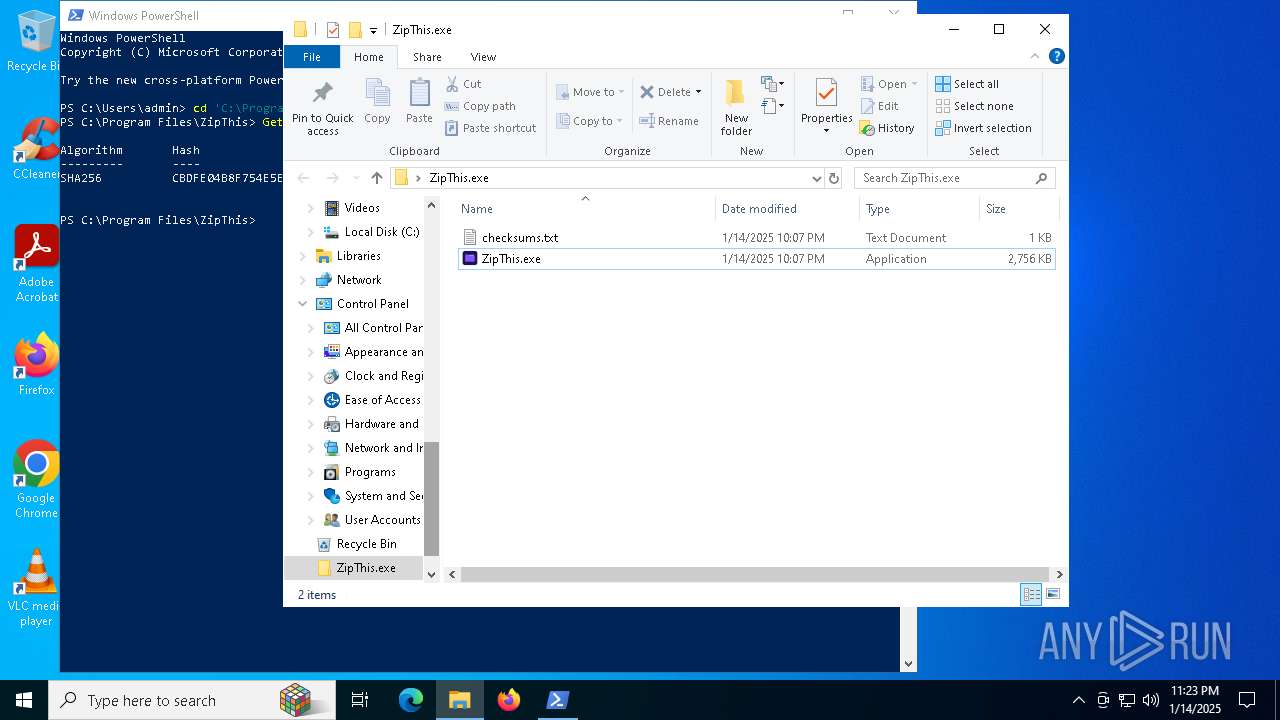
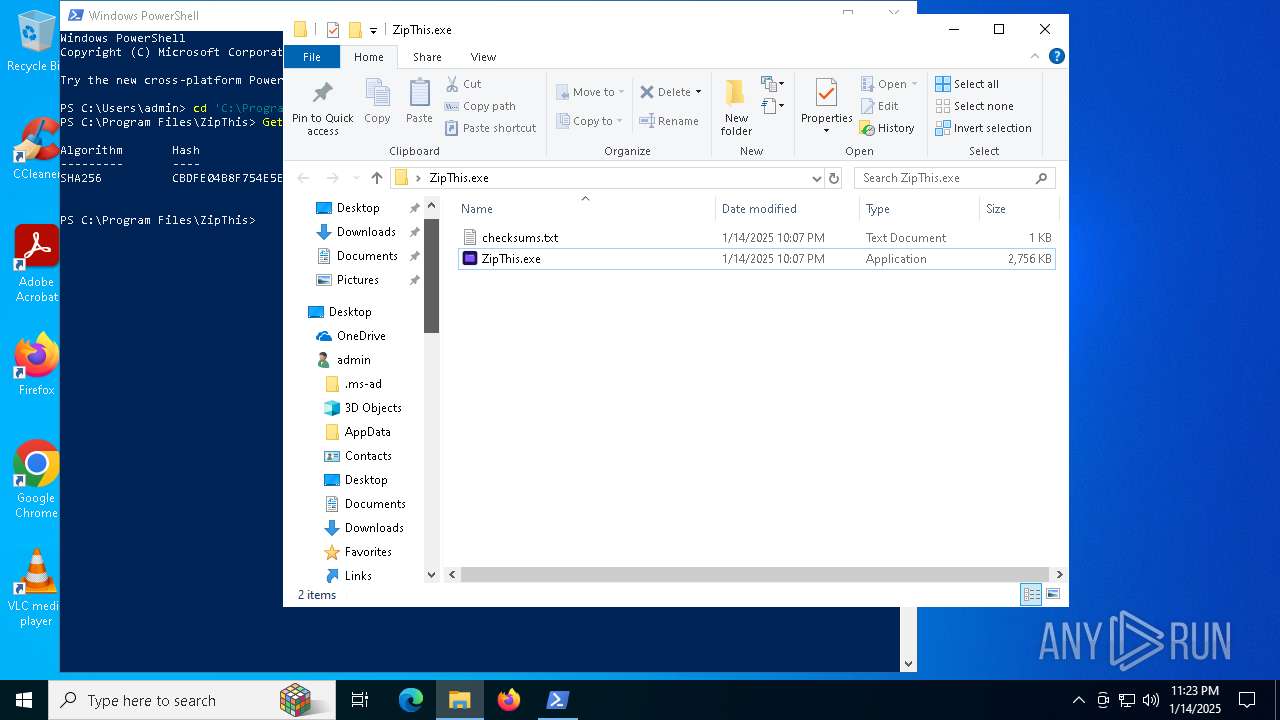
| 1572 | WinRAR.exe | C:\Users\admin\Desktop\ZipThis.exe\checksums.txt | text | |
MD5:105C3FD4A3484D0D4E134222DDEC0DC5 | SHA256:1FE615E15F64F189E86AEA7A32A22DC65DA6CC1671AE464D13376C956A9B9D5A | |||
| 7128 | ZipThis.exe | C:\Program Files\ZipThis\msvcp140_2.dll | executable | |
MD5:AA0148E20D34C10E01A4A9E1BAB1D058 | SHA256:583AD842BCF2F77AF57D07B8F00ECA77BB2DF763DF96BB9C50F7E52031B54E42 | |||
| 7128 | ZipThis.exe | C:\Program Files\ZipThis\vcamp140.dll | executable | |
MD5:8441A618D2CEF67BDEDCA224FD61AFA2 | SHA256:6CD300E597C477260809C5CA036993D923CD8BE304AE323C9C4D7776115FE62D | |||
| 7128 | ZipThis.exe | C:\Program Files\ZipThis\msvcp140_atomic_wait.dll | executable | |
MD5:6722344B74084D0AF629283060716BAE | SHA256:C9FD25862B1B8B2977BF188A4E0C4460DADE43C31710283C2B42DBD3B15B4317 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
84
DNS requests
89
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
540 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
540 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6588 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6032 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3976 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6032 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
apb.thisilient.com |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6256 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
6256 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (stackpath .bootstrapcdn .com) |
6256 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
6256 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6256 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6256 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6256 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6256 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (stackpath .bootstrapcdn .com) |
6256 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
6256 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (stackpath .bootstrapcdn .com) |