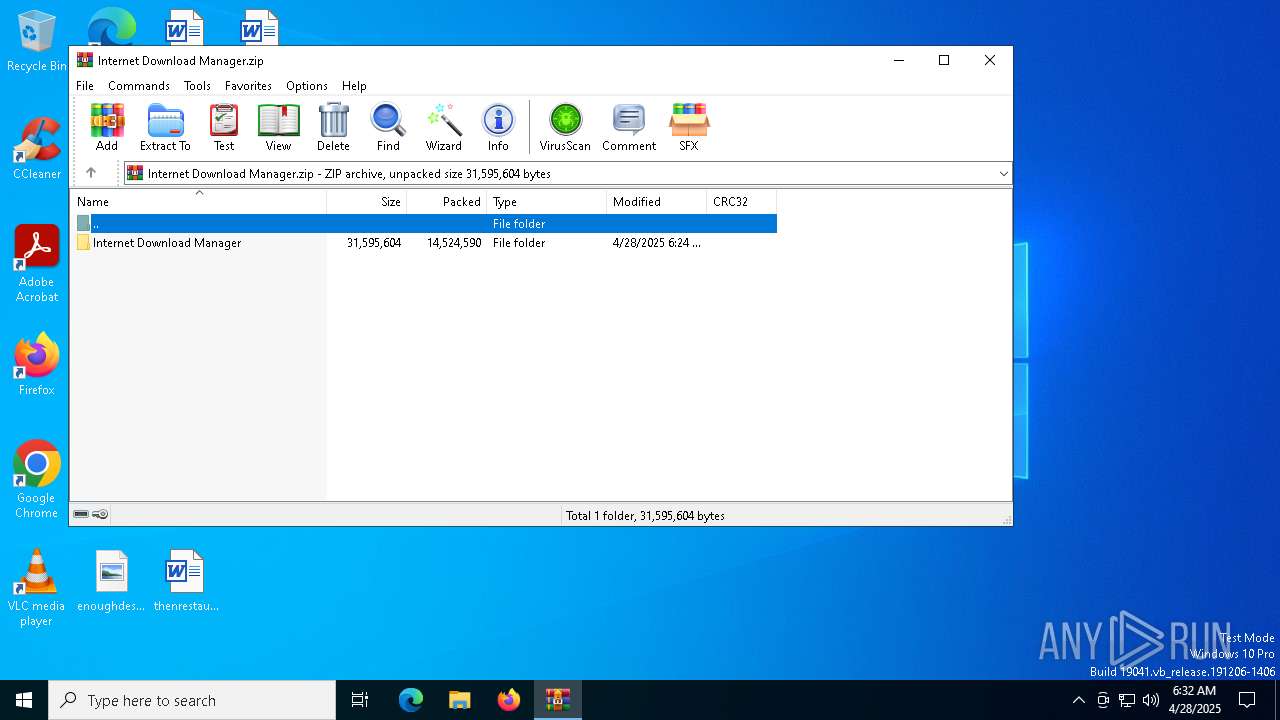
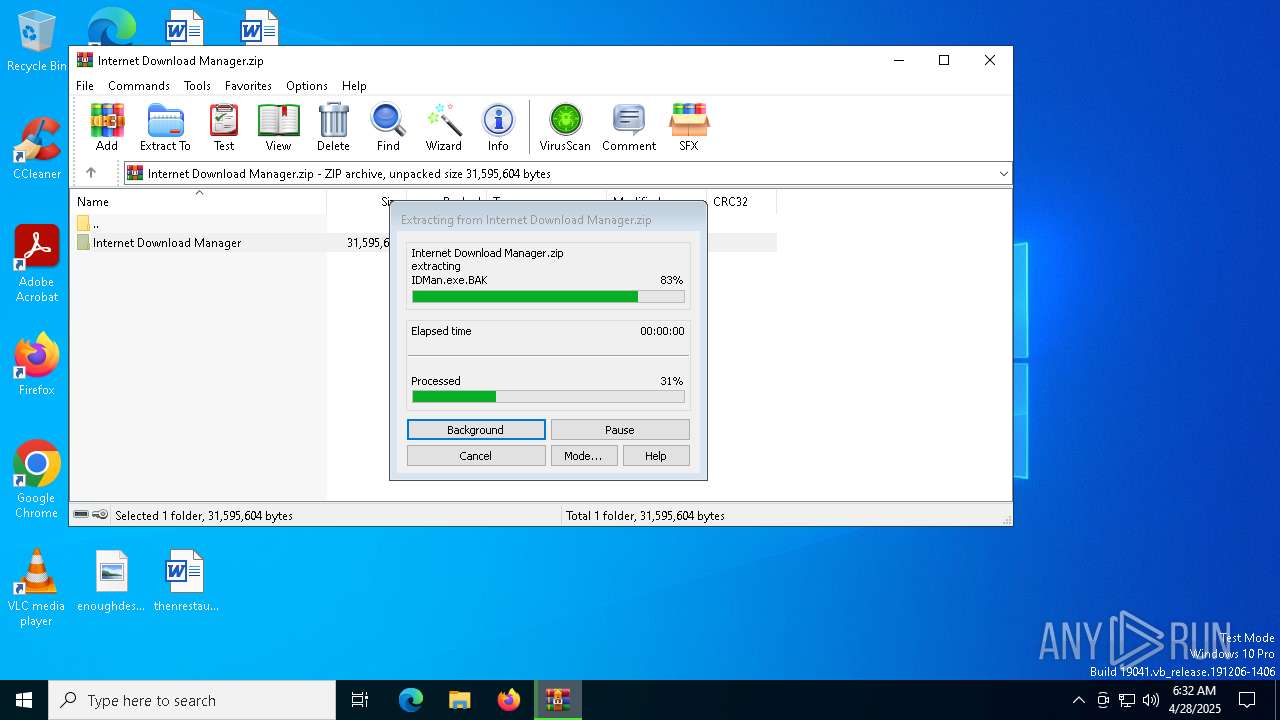
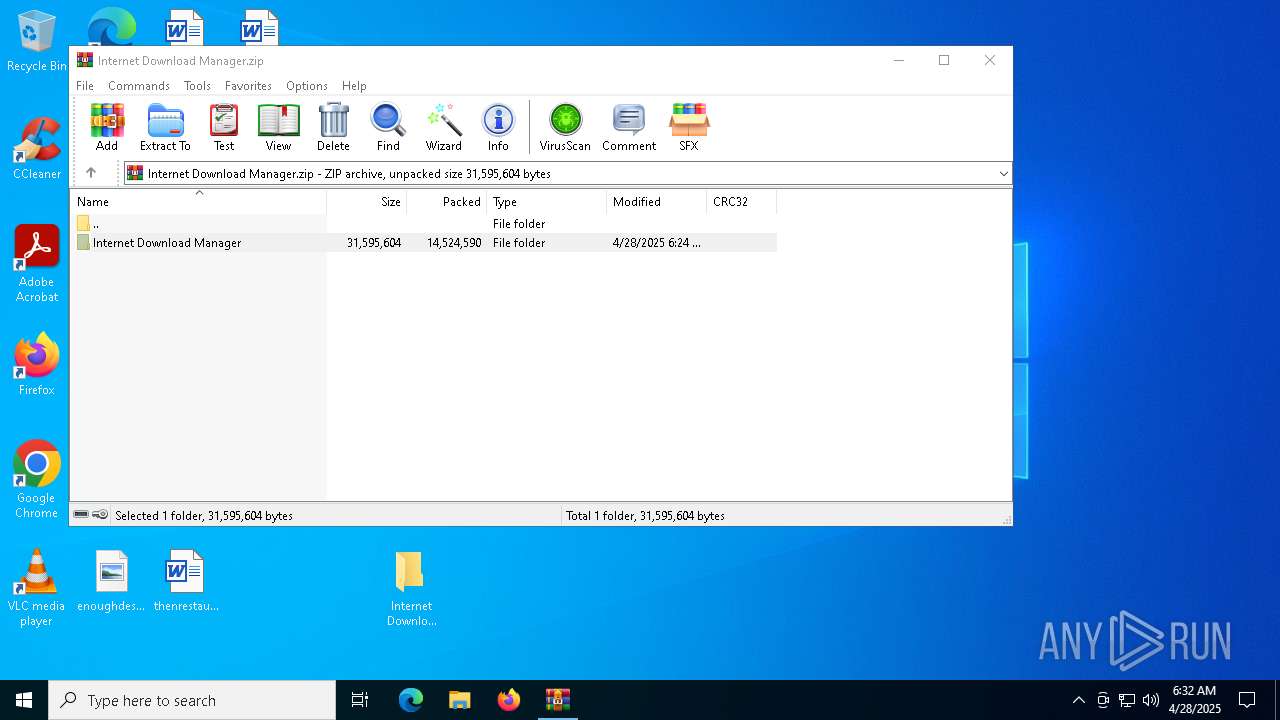
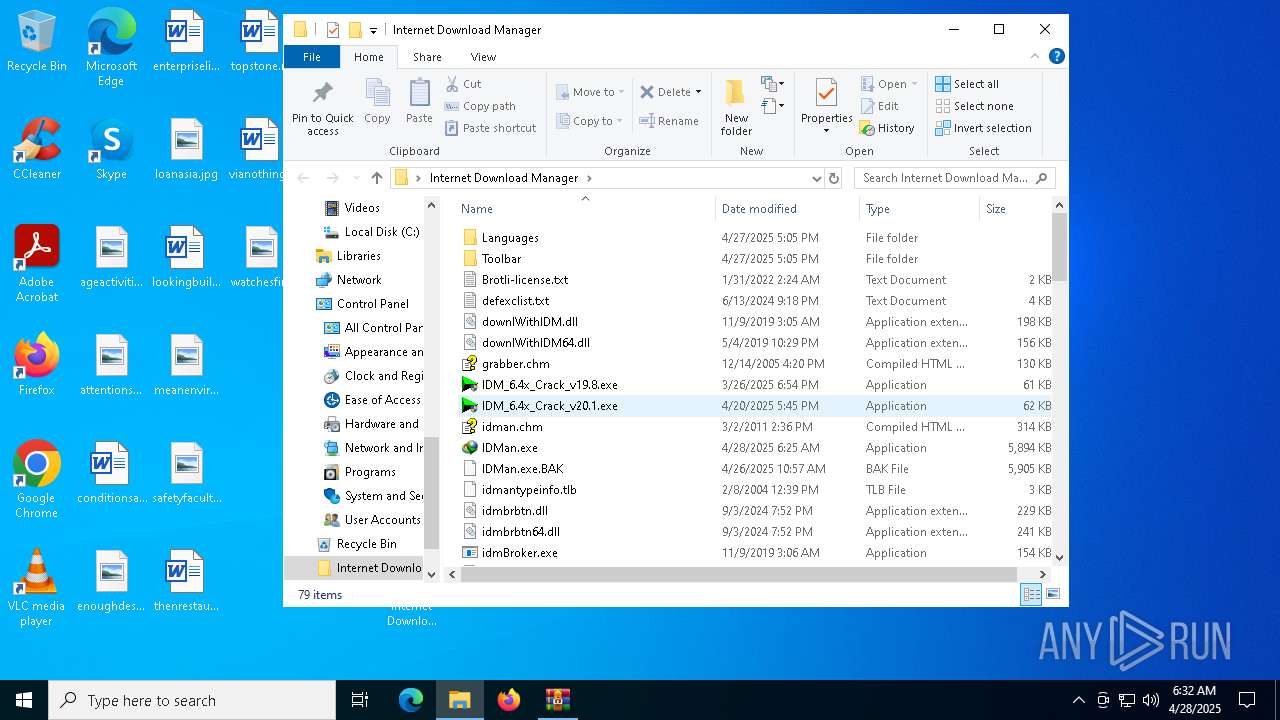
| File name: | Internet Download Manager.zip |
| Full analysis: | https://app.any.run/tasks/c3024148-250b-487b-ad01-92b7f6d72ed0 |
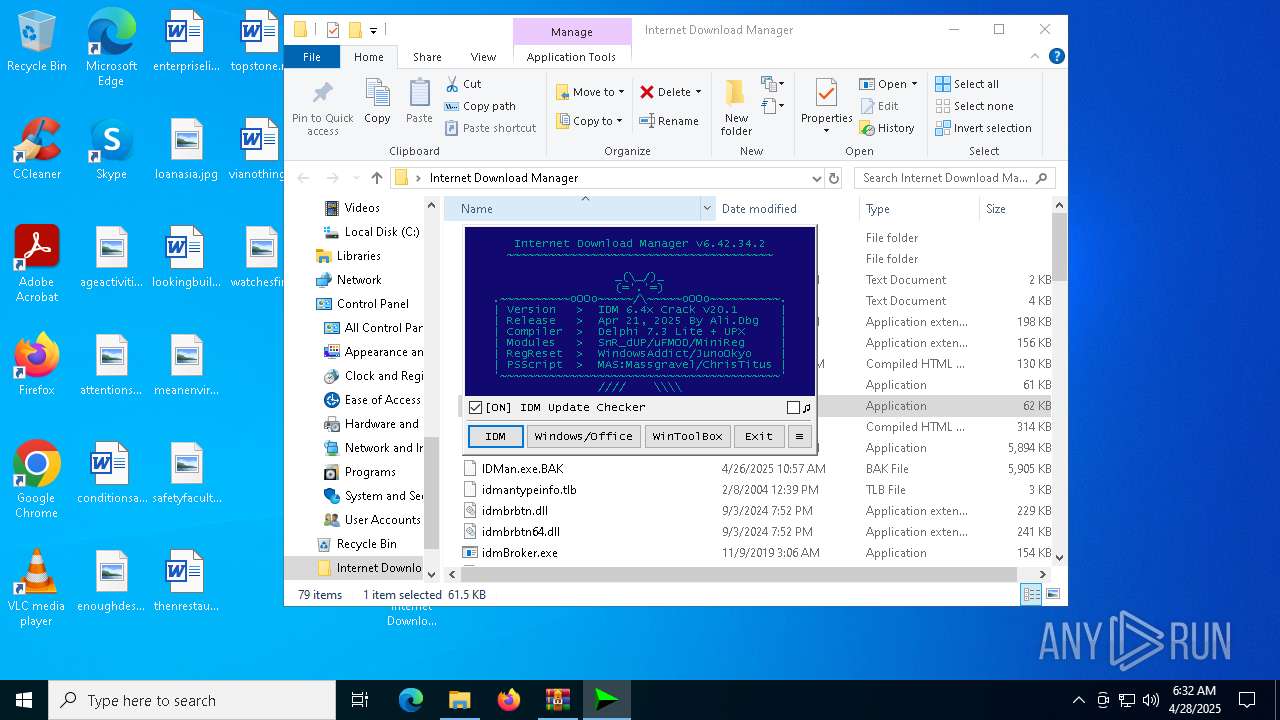
| Verdict: | Malicious activity |
| Analysis date: | April 28, 2025, 06:32:09 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 8FFC90C39004DA8AA948DBF669811FB6 |
| SHA1: | 62E4974BD6678653F2CC4BD0B664947149026C72 |
| SHA256: | 72DDA8DE7CDF2C56F4919768427DF07EAC7A2285A6ABDADA9562DCE549B08C51 |
| SSDEEP: | 98304:VJHK922lWg2EXvNMiVEiu4Ky8MZj8t/MshZLJBTk3Q/VugaFEh5JrojaP0xgS/WB:VrFr9HgYjP1/wvXkI+kZ1Vhfil37/ws |
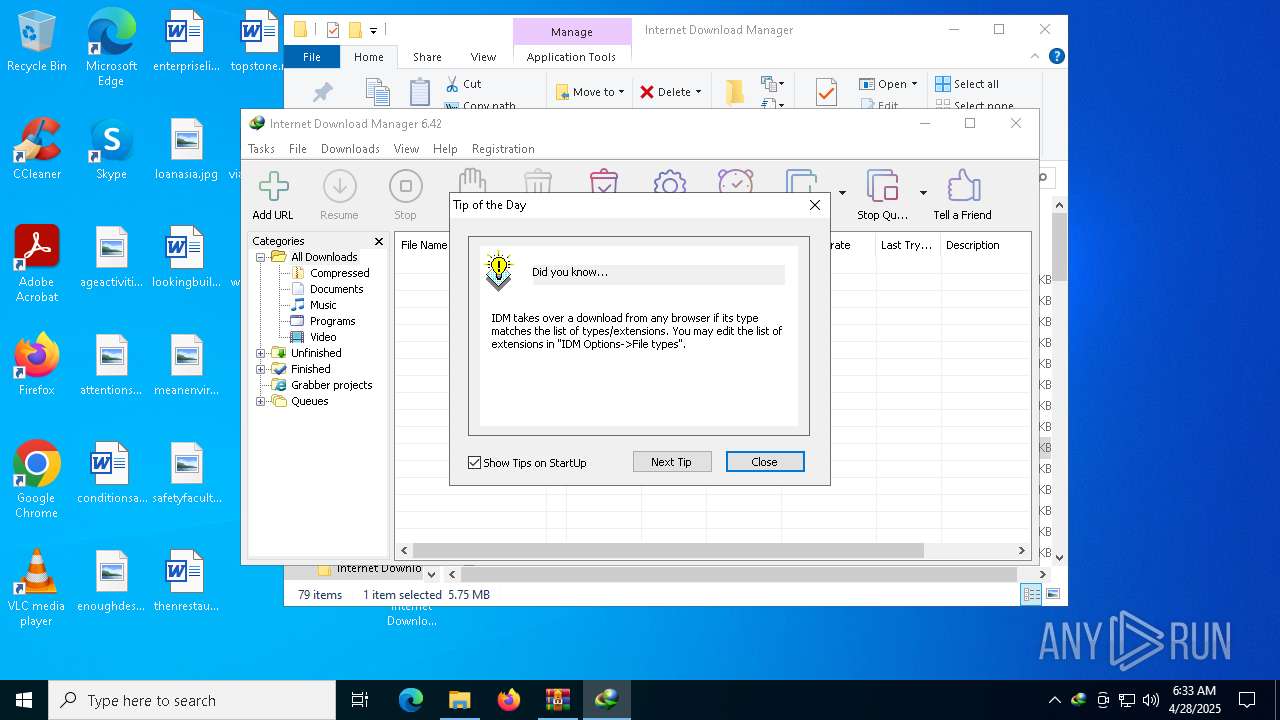
MALICIOUS
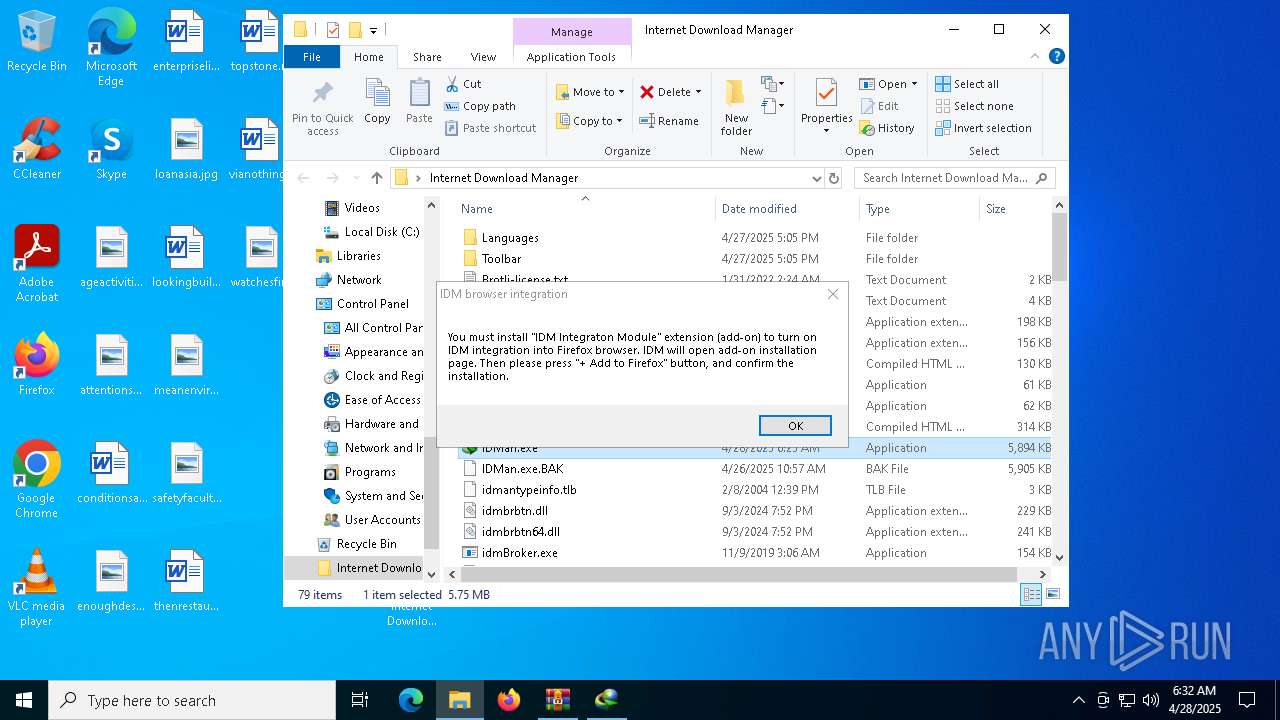
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 7896)
- wscript.exe (PID: 7916)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 7916)
- wscript.exe (PID: 7896)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 7916)
- wscript.exe (PID: 7896)
Deletes a file (SCRIPT)
- wscript.exe (PID: 7916)
- wscript.exe (PID: 7896)
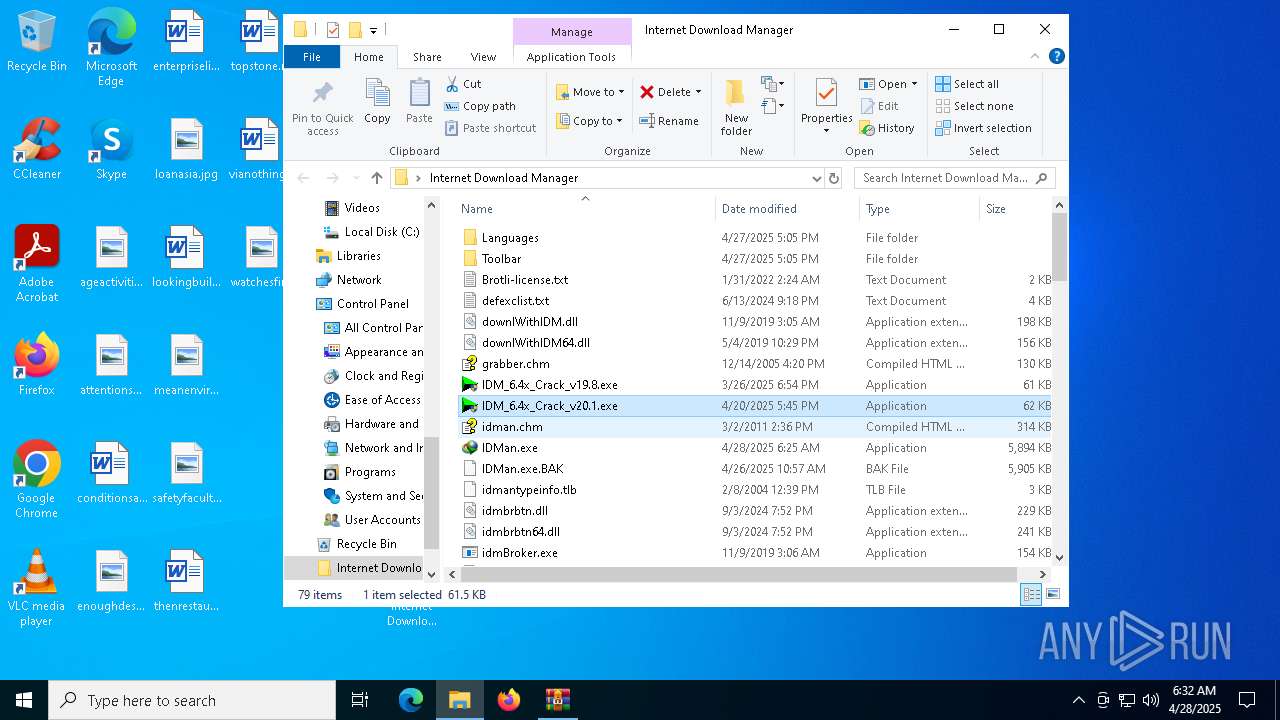
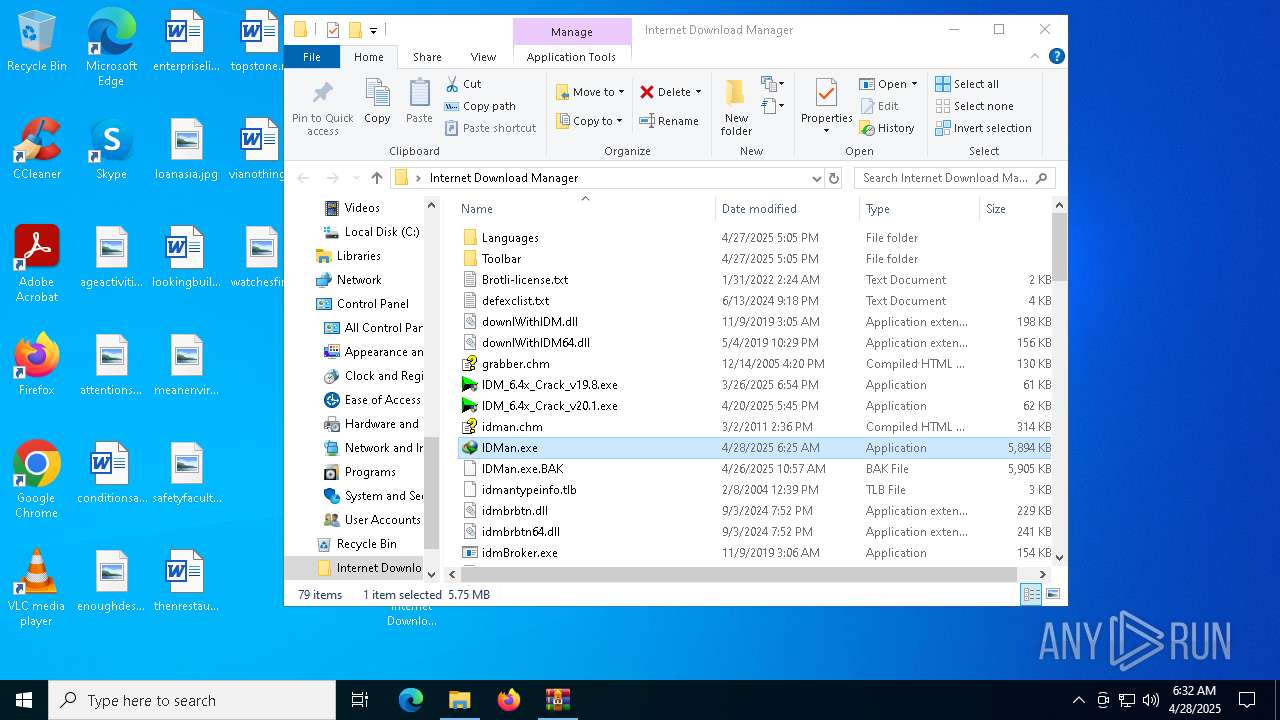
Registers / Runs the DLL via REGSVR32.EXE
- IDMan.exe (PID: 7300)
- Uninstall.exe (PID: 5164)
Starts NET.EXE for service management
- Uninstall.exe (PID: 5164)
- net.exe (PID: 8136)
SUSPICIOUS
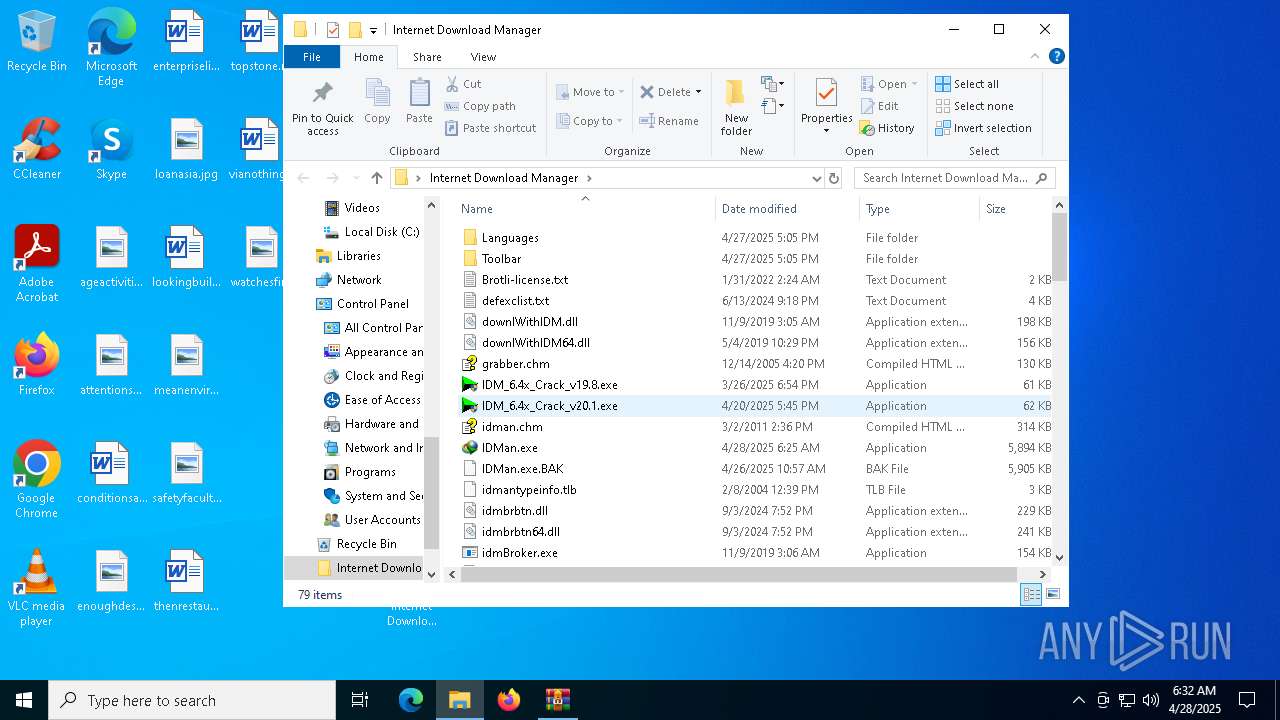
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 7412)
- rundll32.exe (PID: 4172)
- drvinst.exe (PID: 6760)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 7412)
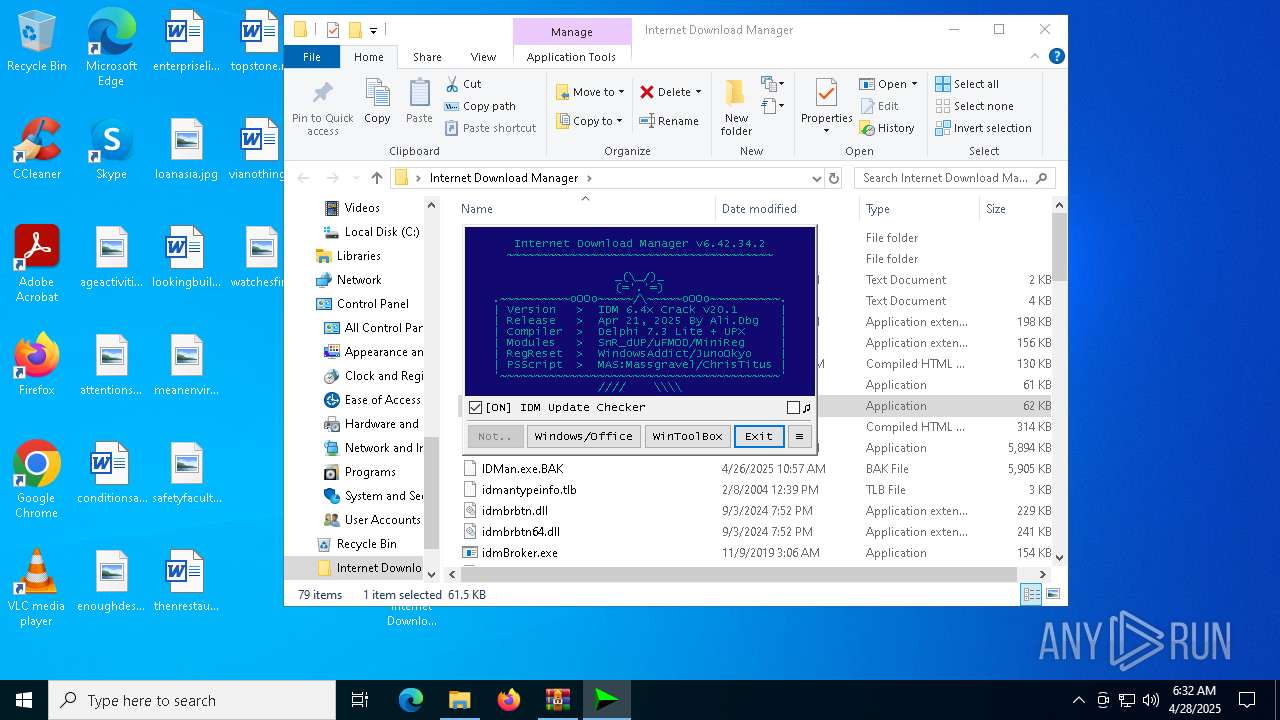
The process executes VB scripts
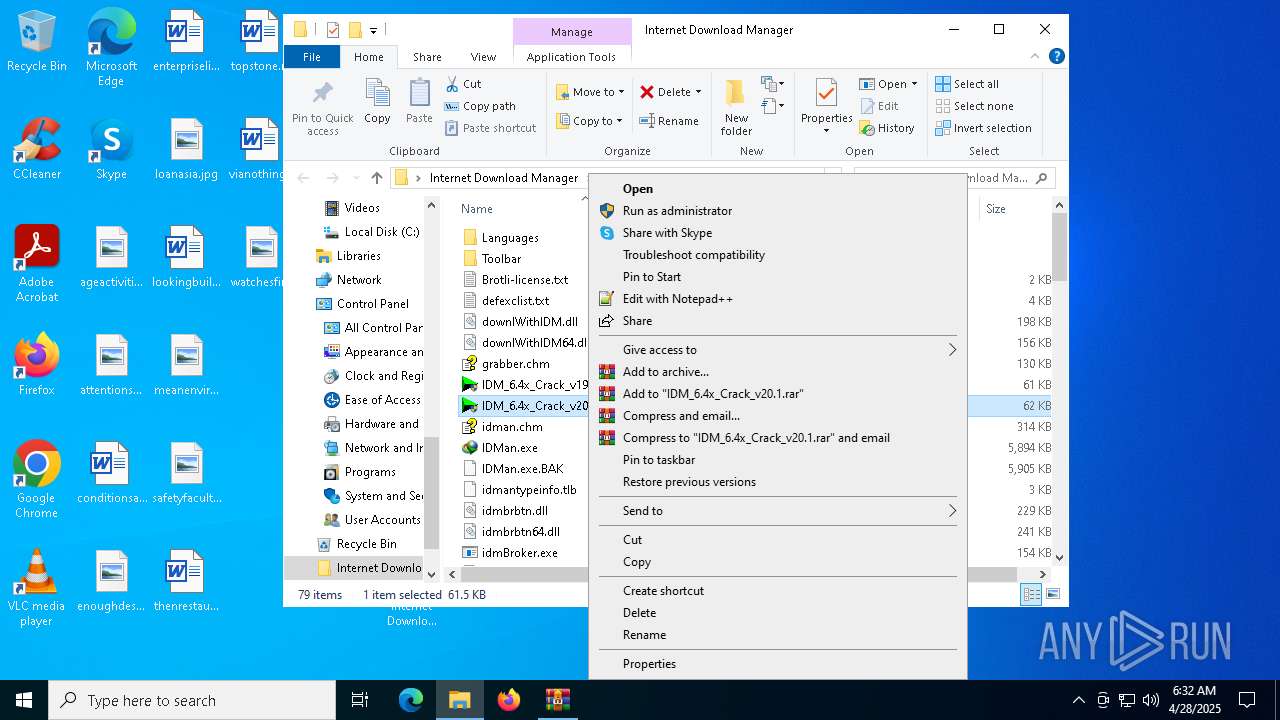
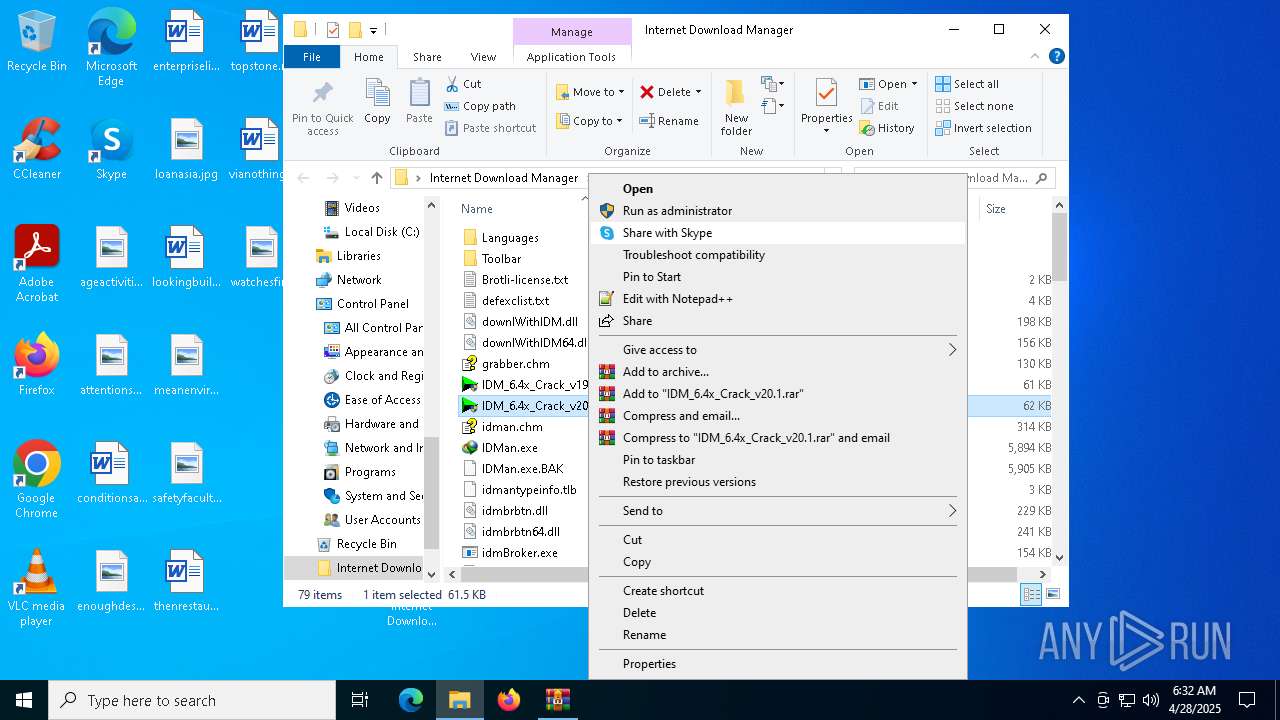
- IDM_6.4x_Crack_v20.1.exe (PID: 7864)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 7916)
- wscript.exe (PID: 7896)
Adds, changes, or deletes HTTP request header (SCRIPT)
- wscript.exe (PID: 7916)
- wscript.exe (PID: 7896)
Sets XML DOM element text (SCRIPT)
- wscript.exe (PID: 7916)
- wscript.exe (PID: 7896)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 7916)
- wscript.exe (PID: 7896)
Uses REG/REGEDIT.EXE to modify registry
- IDM_6.4x_Crack_v20.1.exe (PID: 7864)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 7836)
Executing commands from a ".bat" file
- IDM_6.4x_Crack_v20.1.exe (PID: 7864)
- cmd.exe (PID: 8156)
Starts CMD.EXE for commands execution
- IDM_6.4x_Crack_v20.1.exe (PID: 7864)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 1348)
Application launched itself
- cmd.exe (PID: 8156)
- cmd.exe (PID: 1348)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8156)
- cmd.exe (PID: 5548)
- cmd.exe (PID: 7920)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 8156)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 8156)
Process drops legitimate windows executable
- WinRAR.exe (PID: 7412)
The process downloads a VBScript from the remote host
- IDM_6.4x_Crack_v20.1.exe (PID: 7864)
Reads security settings of Internet Explorer
- IDMan.exe (PID: 7300)
- Uninstall.exe (PID: 5164)
Hides command output
- cmd.exe (PID: 5548)
- cmd.exe (PID: 7836)
Uses RUNDLL32.EXE to load library
- Uninstall.exe (PID: 5164)
Executable content was dropped or overwritten
- IDMan.exe (PID: 7300)
- drvinst.exe (PID: 6760)
- rundll32.exe (PID: 4172)
Creates files in the driver directory
- drvinst.exe (PID: 6760)
Starts application with an unusual extension
- cmd.exe (PID: 8156)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7412)
The sample compiled with english language support
- WinRAR.exe (PID: 7412)
- IDMan.exe (PID: 7300)
- drvinst.exe (PID: 6760)
- rundll32.exe (PID: 4172)
The sample compiled with russian language support
- WinRAR.exe (PID: 7412)
Creates files or folders in the user directory
- IDM_6.4x_Crack_v20.1.exe (PID: 7864)
- IDMan.exe (PID: 7300)
Checks proxy server information
- wscript.exe (PID: 7916)
- wscript.exe (PID: 7896)
- IDMan.exe (PID: 7300)
Checks operating system version
- cmd.exe (PID: 8156)
Manual execution by a user
- IDMan.exe (PID: 7300)
- IDM_6.4x_Crack_v20.1.exe (PID: 7864)
Checks supported languages
- IDMan.exe (PID: 7300)
- IDM_6.4x_Crack_v20.1.exe (PID: 7864)
- IDMIntegrator64.exe (PID: 7368)
- Uninstall.exe (PID: 5164)
- drvinst.exe (PID: 6760)
Reads the computer name
- IDMan.exe (PID: 7300)
- IDM_6.4x_Crack_v20.1.exe (PID: 7864)
- IDMIntegrator64.exe (PID: 7368)
INTERNETDOWNLOADMANAGER mutex has been found
- IDMan.exe (PID: 7300)
- IDMIntegrator64.exe (PID: 7368)
Creates files in the program directory
- IDMan.exe (PID: 7300)
Process checks computer location settings
- IDMan.exe (PID: 7300)
- Uninstall.exe (PID: 5164)
Reads the machine GUID from the registry
- IDMan.exe (PID: 7300)
- drvinst.exe (PID: 6760)
Application launched itself
- firefox.exe (PID: 4068)
- firefox.exe (PID: 7676)
- msedge.exe (PID: 6808)
- msedge.exe (PID: 5960)
Reads the software policy settings
- IDMan.exe (PID: 7300)
Disables trace logs
- IDMan.exe (PID: 7300)
Create files in a temporary directory
- IDMan.exe (PID: 7300)
- IDM_6.4x_Crack_v20.1.exe (PID: 7864)
- reg.exe (PID: 4728)
- rundll32.exe (PID: 4172)
Changes the display of characters in the console
- cmd.exe (PID: 8156)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 1228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
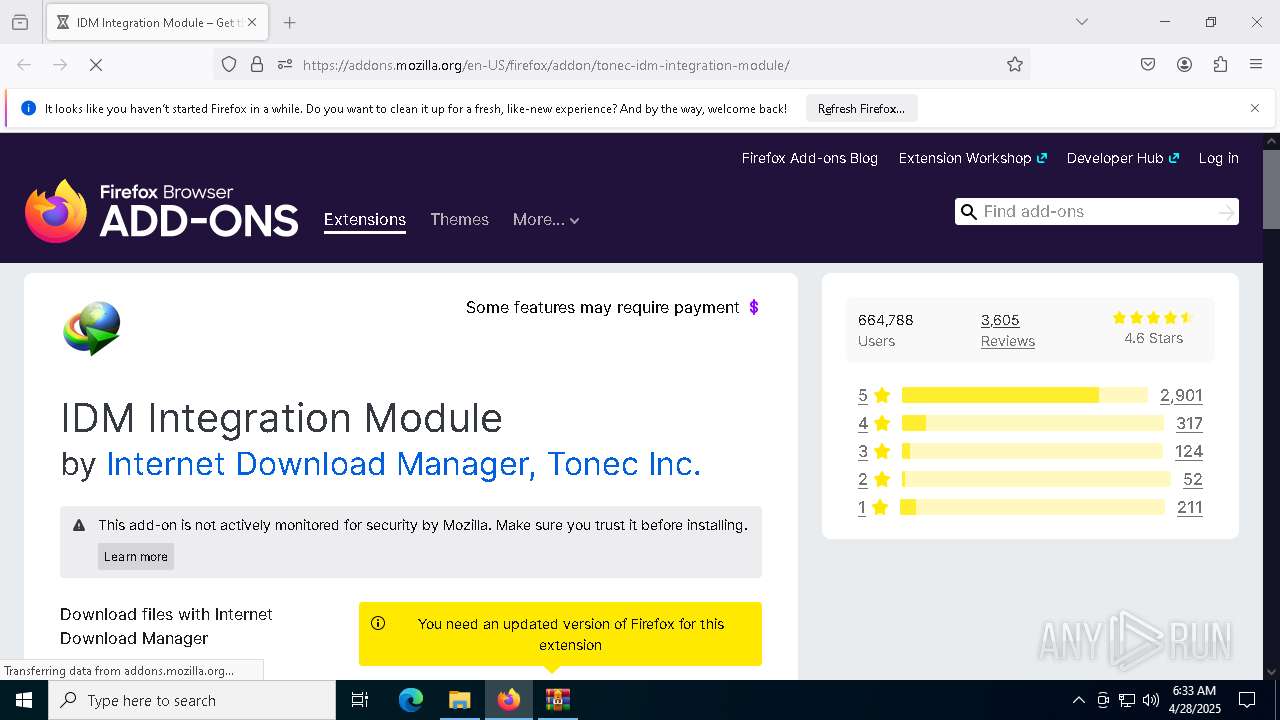
| .xpi | | | Mozilla Firefox browser extension (42.1) |
|---|---|---|
| .zip | | | ZIP compressed archive (21) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:04:28 14:24:46 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Internet Download Manager/ |
Total processes
264
Monitored processes
136
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5552 --field-trial-handle=2260,i,12810185160795508735,12626840868484791136,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 300 | find /i "computersystem" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4488 --field-trial-handle=2260,i,12810185160795508735,12626840868484791136,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2564 --field-trial-handle=2332,i,688759615831544418,16801531464767920144,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 668 | reg query HKU\S-1-5-21-1693682860-607145093-2874071422-1001\IAS_TEST | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4168 -childID 2 -isForBrowser -prefsHandle 4216 -prefMapHandle 4212 -prefsLen 36588 -prefMapSize 244583 -jsInitHandle 1536 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {49435677-7c18-4cd2-b174-15304207fae0} 7676 "\\.\pipe\gecko-crash-server-pipe.7676" 20f326fe4d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5824 --field-trial-handle=2260,i,12810185160795508735,12626840868484791136,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 736 | reg delete HKU\S-1-5-21-1693682860-607145093-2874071422-1001\IAS_TEST /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1012 | reg query HKU\S-1-5-21-1693682860-607145093-2874071422-1001\Software | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1072 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4616 --field-trial-handle=2260,i,12810185160795508735,12626840868484791136,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
53 501
Read events
53 047
Write events
409
Delete events
45
Modification events
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Internet Download Manager.zip | |||
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7864) IDM_6.4x_Crack_v20.1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (7864) IDM_6.4x_Crack_v20.1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Wow6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
Executable files
73
Suspicious files
481
Text files
275
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
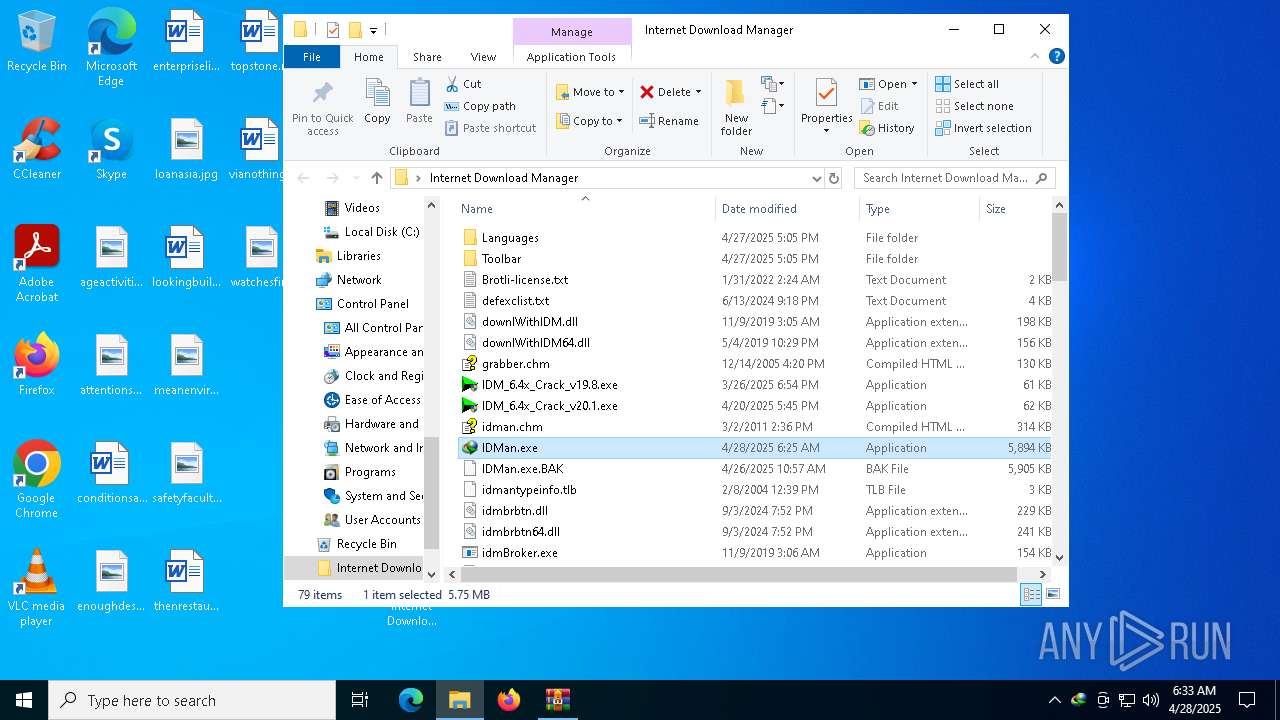
| 7412 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7412.25936\Internet Download Manager\Brotli-license.txt | text | |
MD5:941EE9CD1609382F946352712A319B4B | SHA256:3D180008E36922A4E8DAEC11C34C7AF264FED5962D07924AEA928C38E8663C94 | |||
| 7412 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7412.25936\Internet Download Manager\grabber.chm | binary | |
MD5:4B9506B675606F1003D9EF635A48DB06 | SHA256:B46D8878E0CBD7A7A2F12DE909CD94CF424FA07838A39434146F772784481137 | |||
| 7412 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7412.25936\Internet Download Manager\IDMan.exe | executable | |
MD5:736FB99895D010902C8DBFA25F20B076 | SHA256:E68927C472B252C3162807790B7709121D04D9C8F090356D2B576288D6414048 | |||
| 7412 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7412.25936\Internet Download Manager\downlWithIDM.dll | executable | |
MD5:B94D0711637B322B8AA1FB96250C86B6 | SHA256:38AC192D707F3EC697DD5FE01A0C6FC424184793DF729F427C0CF5DFAB6705FE | |||
| 7412 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7412.25936\Internet Download Manager\IDMan.exe.BAK | executable | |
MD5:F5D5709BF0BF17DAF8BF845329968B05 | SHA256:458351635A2293B46A36F6FE3FF42A85F4D0CE41C078E1AE2F35D2C52B8A3C23 | |||
| 7412 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7412.25936\Internet Download Manager\defexclist.txt | text | |
MD5:12817B3E07DCF514BBEDA8F3AB834877 | SHA256:0BC91B5ECD5A230C67FEC0DFBB66DE80F1323AD990E388E5C75D095ACABDAFAA | |||
| 7412 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7412.25936\Internet Download Manager\downlWithIDM64.dll | executable | |
MD5:13C99CBF0E66D5A8003A650C5642CA30 | SHA256:8A51ECE1C4C8BCB8C56CA10CB9D97BFF0DFE75052412A8D8D970A5EB6933427B | |||
| 7412 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7412.25936\Internet Download Manager\idman.chm | binary | |
MD5:D7CC241B7761965AF371D57BAA94A2BA | SHA256:9E06F65BFA76D1355B44498774B8F96A69C54DAAD2FD6CC9A0FD9338751D23B5 | |||
| 7412 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7412.25936\Internet Download Manager\idmBroker.exe | executable | |
MD5:E2F17E16E2B1888A64398900999E9663 | SHA256:97810E0B3838A7DCA94D73A8B9E170107642B064713C084C231DE6632CB68A9C | |||
| 7412 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7412.25936\Internet Download Manager\idmcchandler2_64.dll | executable | |
MD5:5012EA14F13DD58FFEB14553824D8EBB | SHA256:59AC02F5A0644BF56B7AD7E2B48FC8F89083F8CFE12A0A93F63163A5573A876F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
91
DNS requests
145
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.21:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.21:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1532 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7896 | wscript.exe | GET | 200 | 18.173.205.57:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSOZnI3uW4l91H%2Fnmb99iT4JNV7YwQUv8Fah%2F8o%2BkE9%2FbdP5B2voGFYKb0CEF67H4z5kSV9LdlHbOP2Rts%3D | unknown | — | — | whitelisted |
7676 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
1532 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7676 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.21:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.216.77.21:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
idm.0dy.ir |
| unknown |
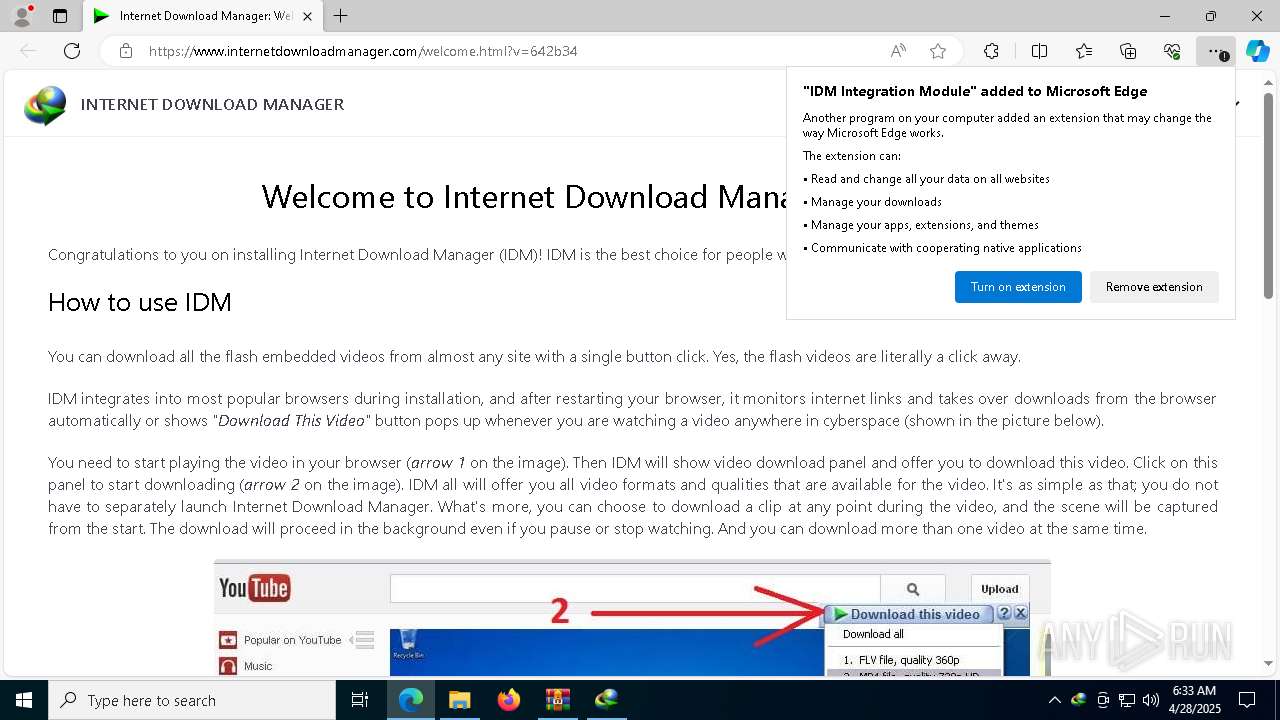
www.internetdownloadmanager.com |
| whitelisted |
c.pki.goog |
| whitelisted |