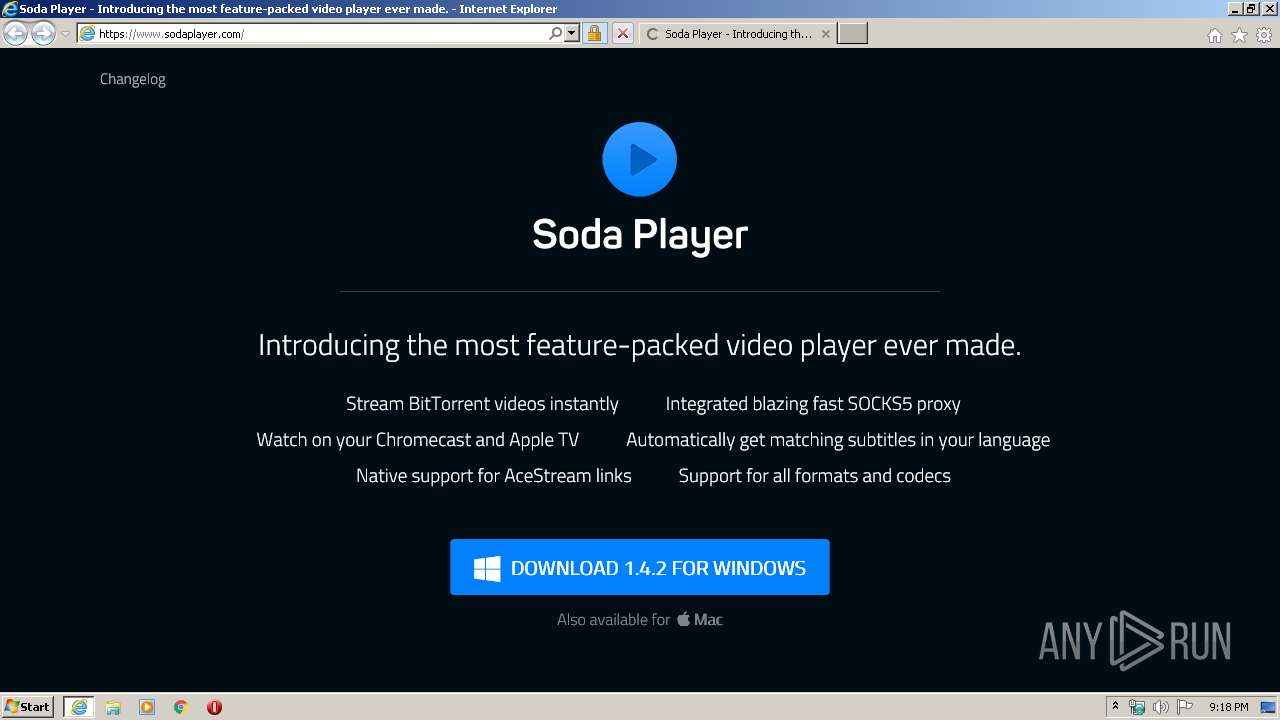
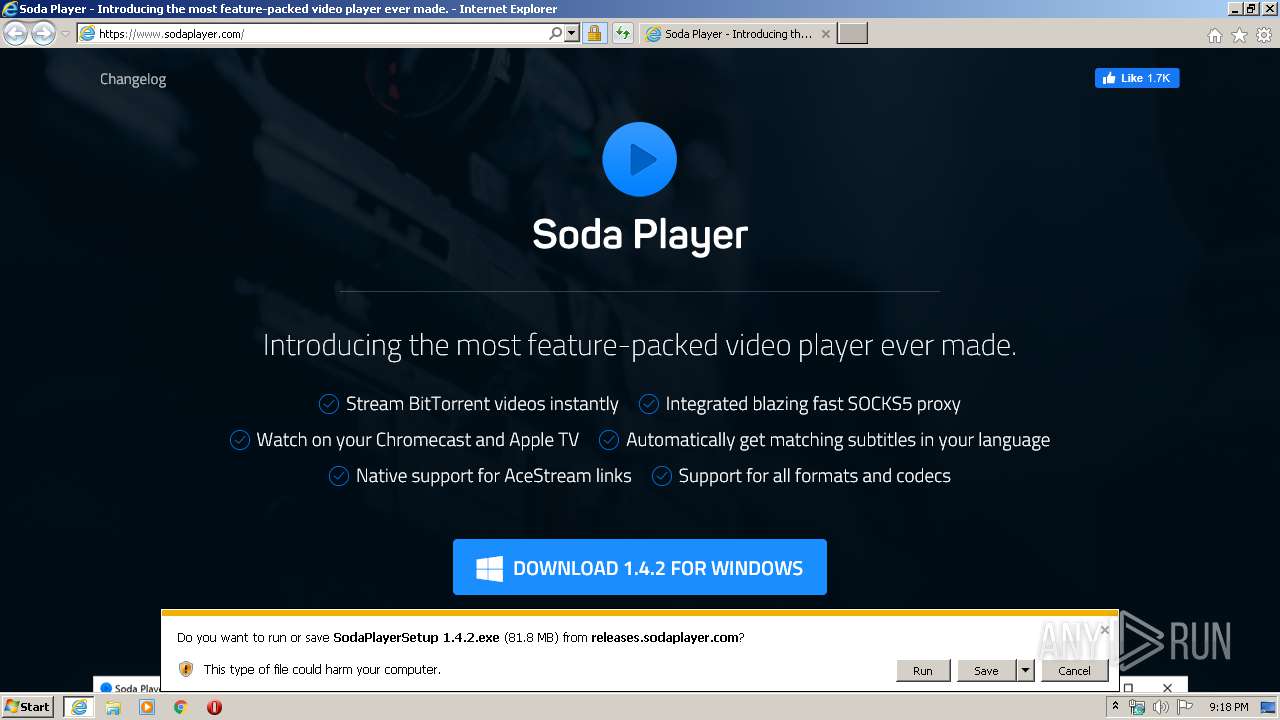
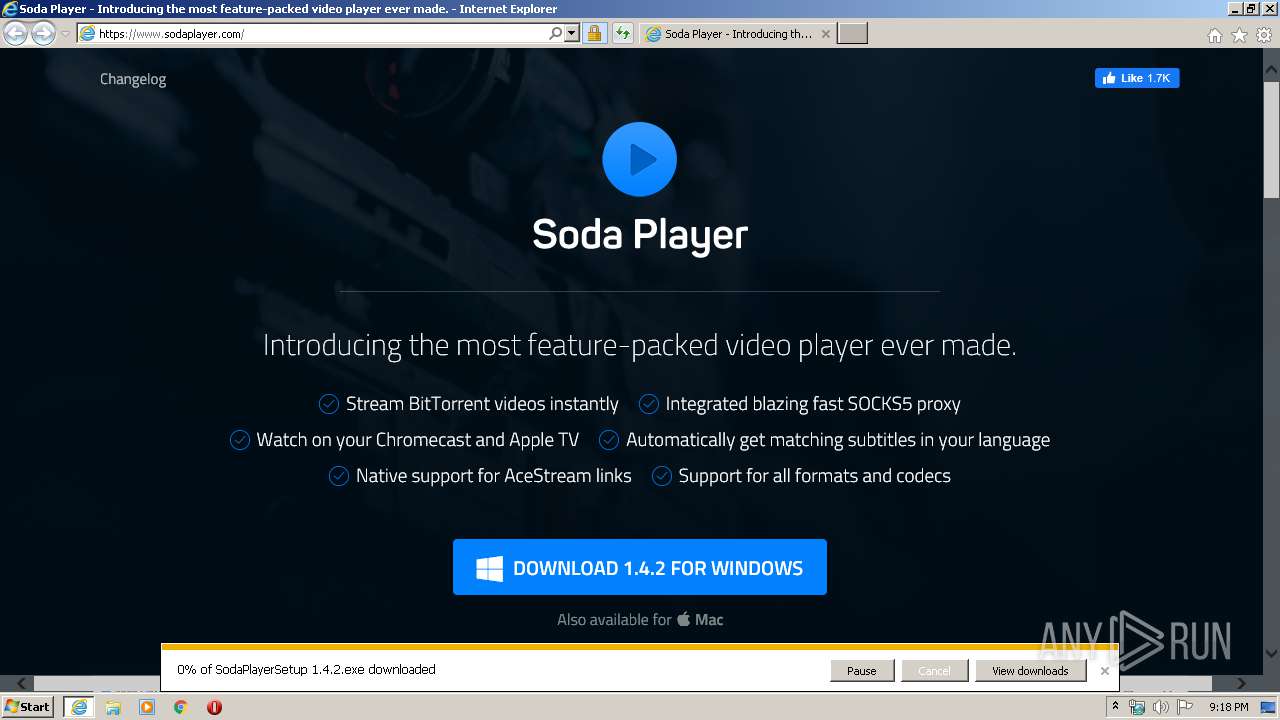
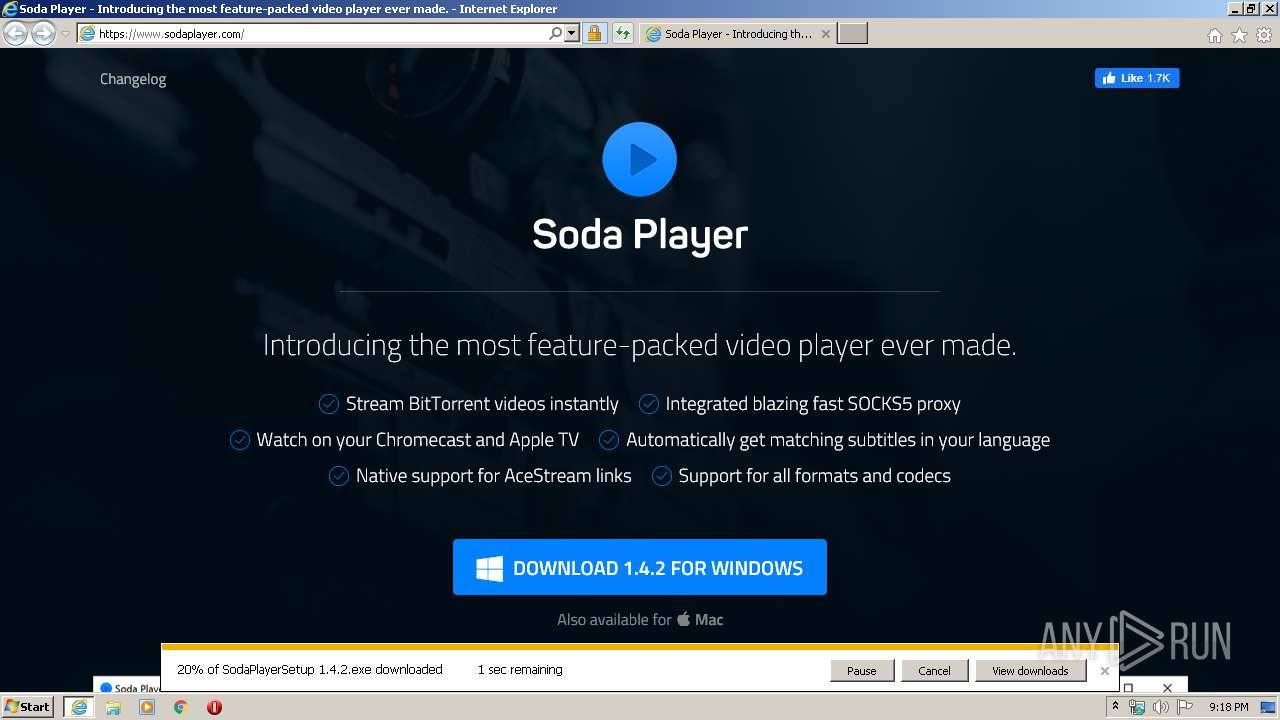
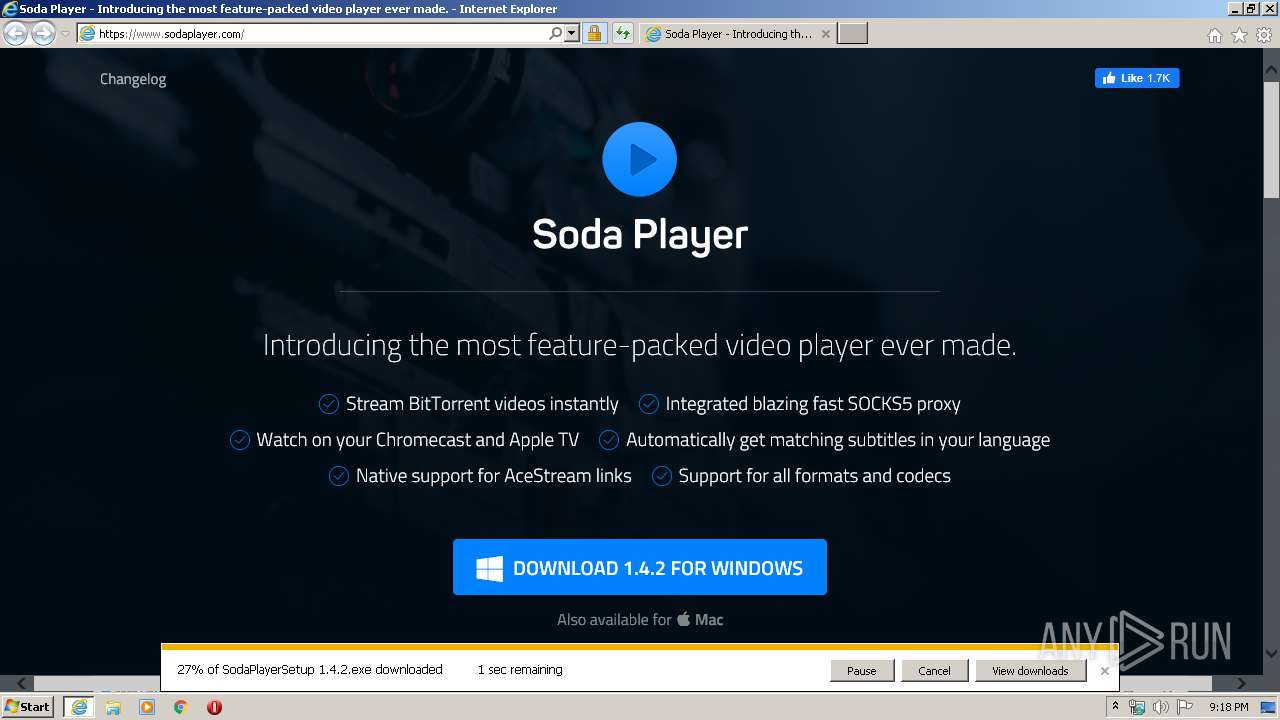
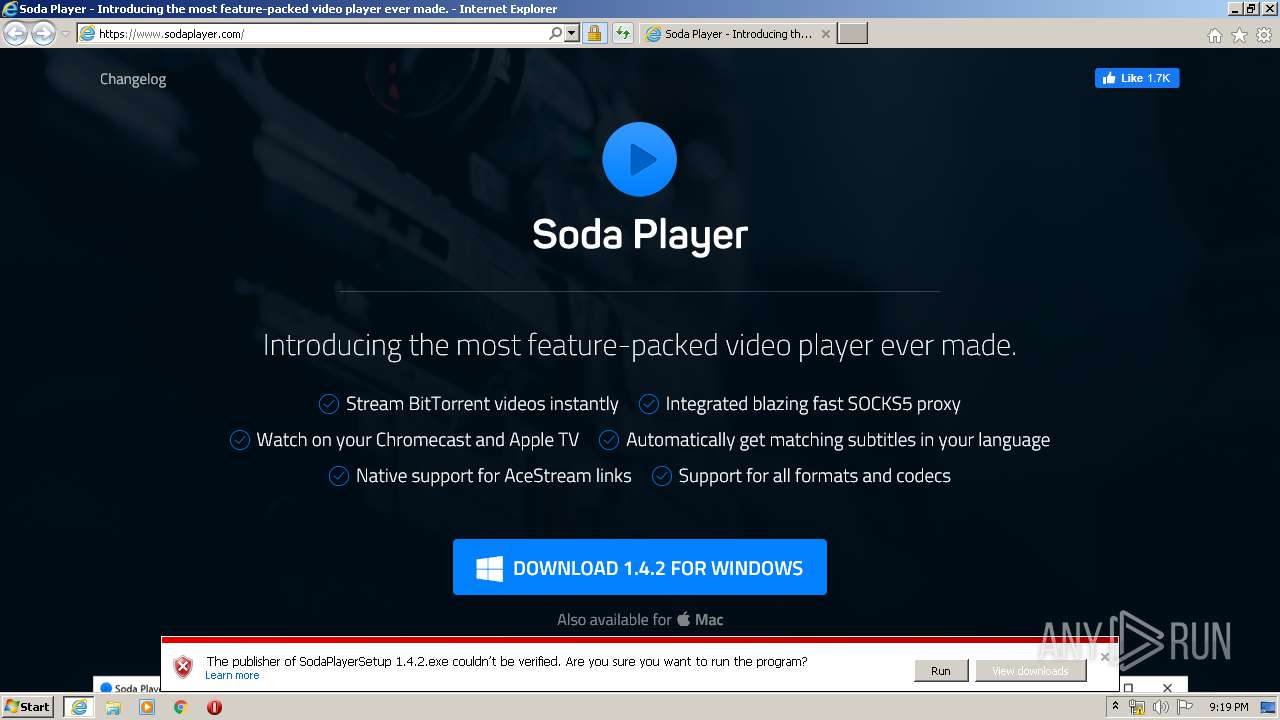
| URL: | https://www.sodaplayer.com/ |
| Full analysis: | https://app.any.run/tasks/c8af82e2-5b94-4983-8b3e-e9dff1475588 |
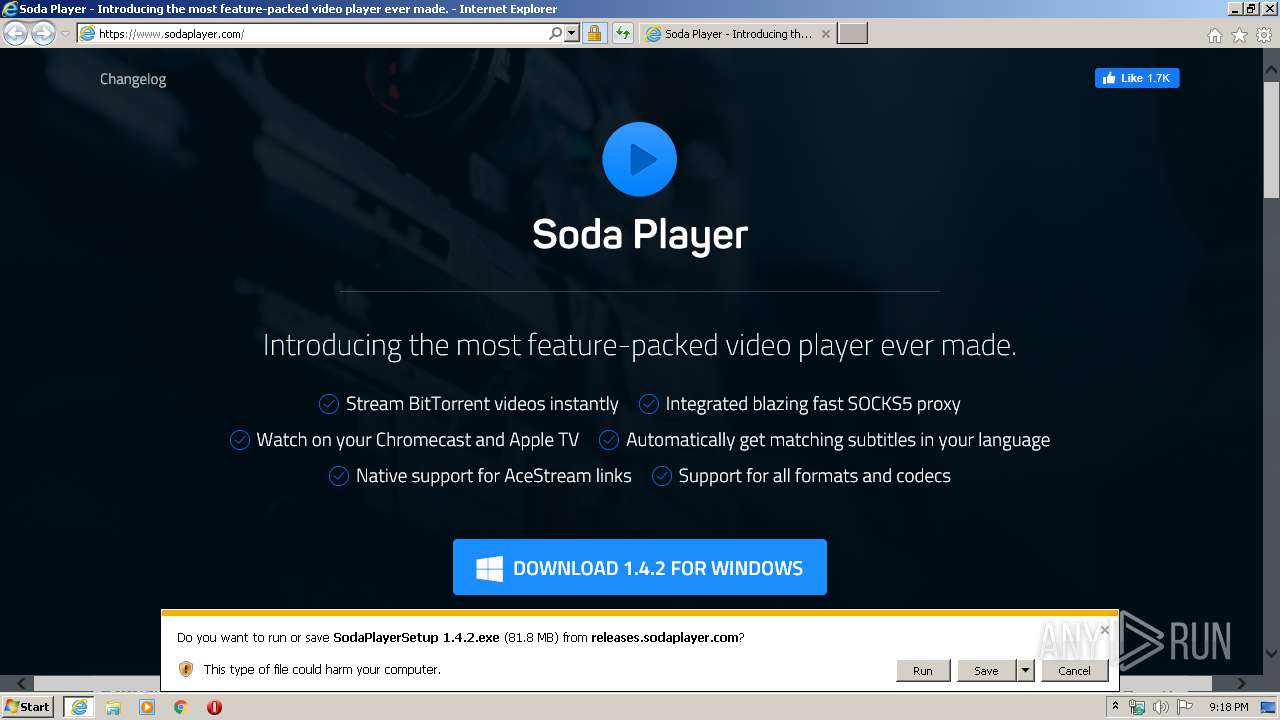
| Verdict: | Malicious activity |
| Analysis date: | February 09, 2020, 21:17:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 008E91134A1536385B8A791D915999B4 |
| SHA1: | 59006F1812E95F64440C73D26EEBF68BEB28159C |
| SHA256: | 72C11B8313C1C4239CD2019CDB9E1E7ACC3A911C5DFDA3BD326A19E830104414 |
| SSDEEP: | 3:N8DSLUEcYR:2OLUEtR |
MALICIOUS
Application was dropped or rewritten from another process
- Update.exe (PID: 3132)
- Squirrel.exe (PID: 1380)
- Update.exe (PID: 2692)
- Update.exe (PID: 1812)
- ace_engine.exe (PID: 2908)
- ace_engine.exe (PID: 376)
Loads dropped or rewritten executable
- Soda Player.exe (PID: 3764)
- Soda Player.exe (PID: 1748)
- Soda Player.exe (PID: 2056)
- Soda Player.exe (PID: 2436)
- Soda Player.exe (PID: 2752)
- Soda Player.exe (PID: 2836)
- Soda Player.exe (PID: 3604)
- Soda Player.exe (PID: 1800)
- Soda Player.exe (PID: 536)
- ace_engine.exe (PID: 2908)
- ace_engine.exe (PID: 376)
- Soda Player.exe (PID: 3864)
- Soda Player.exe (PID: 2096)
SUSPICIOUS
Executable content was dropped or overwritten
- SodaPlayerSetup 1.4.2.exe (PID: 3356)
- Squirrel.exe (PID: 1380)
- Update.exe (PID: 3132)
- Soda Player.exe (PID: 2836)
Uses REG.EXE to modify Windows registry
- Soda Player.exe (PID: 3764)
- Soda Player.exe (PID: 1748)
Creates files in the user directory
- Update.exe (PID: 2692)
- Soda Player.exe (PID: 1748)
- ace_engine.exe (PID: 2908)
- Soda Player.exe (PID: 2836)
Modifies the open verb of a shell class
- reg.exe (PID: 1028)
- reg.exe (PID: 604)
- reg.exe (PID: 3448)
Reads Environment values
- Update.exe (PID: 3132)
Application launched itself
- Soda Player.exe (PID: 1748)
- ace_engine.exe (PID: 2908)
Creates a software uninstall entry
- Update.exe (PID: 3132)
Reads CPU info
- Soda Player.exe (PID: 2752)
Starts CMD.EXE for commands execution
- Soda Player.exe (PID: 2836)
- ace_engine.exe (PID: 2908)
- NETSTAT.EXE (PID: 1136)
Uses TASKLIST.EXE to query information about running processes
- cmd.exe (PID: 3608)
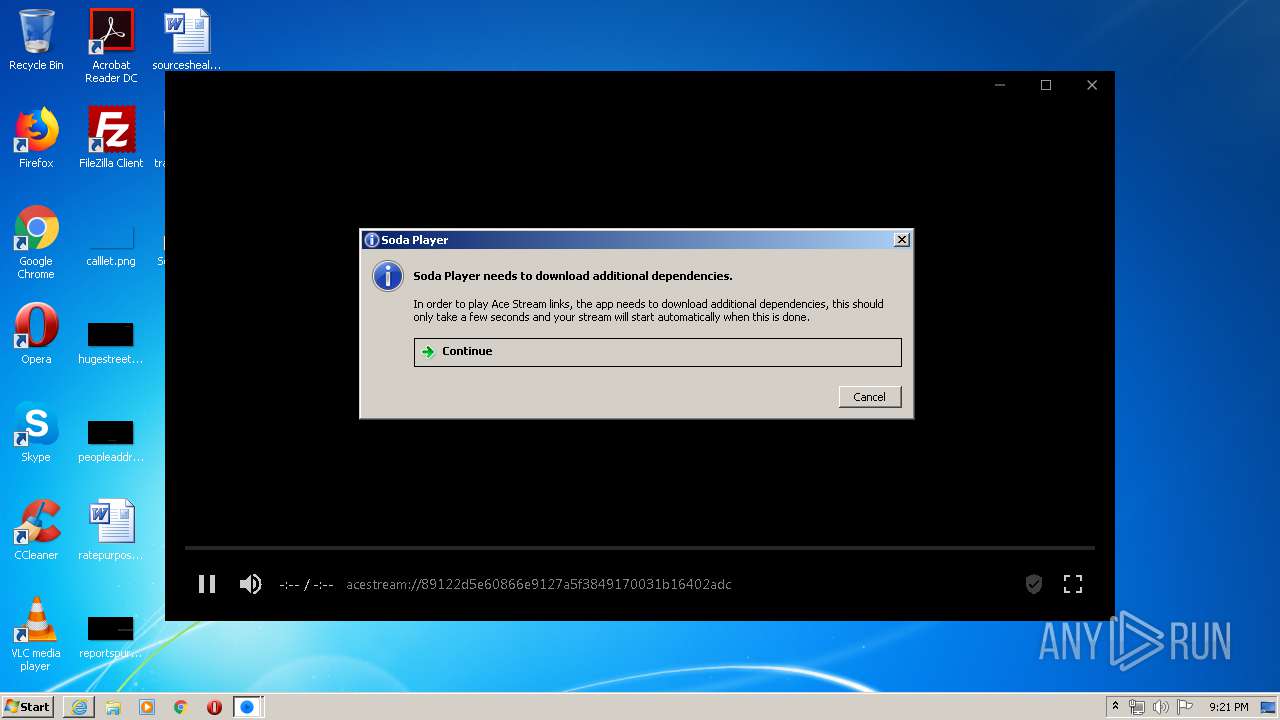
Loads Python modules
- ace_engine.exe (PID: 2908)
- ace_engine.exe (PID: 376)
Uses NETSTAT.EXE to discover network connections
- cmd.exe (PID: 1632)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 820)
- cmd.exe (PID: 2668)
Uses IPCONFIG.EXE to discover IP address
- cmd.exe (PID: 3276)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 2400)
Changes internet zones settings
- iexplore.exe (PID: 2956)
Creates files in the user directory
- iexplore.exe (PID: 2400)
- iexplore.exe (PID: 2956)
Reads internet explorer settings
- iexplore.exe (PID: 2400)
Dropped object may contain TOR URL's
- iexplore.exe (PID: 2400)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2956)
Reads the hosts file
- Soda Player.exe (PID: 3764)
- Soda Player.exe (PID: 1748)
Reads settings of System Certificates
- Update.exe (PID: 3132)
- Soda Player.exe (PID: 1748)
- iexplore.exe (PID: 2956)
Dropped object may contain Bitcoin addresses
- Soda Player.exe (PID: 2836)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2956)
Changes settings of System certificates
- iexplore.exe (PID: 2956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
103
Monitored processes
46
Malicious processes
17
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | C:\Windows\system32\route.exe print | C:\Windows\system32\ROUTE.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Route Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 376 | "C:\Users\admin\AppData\Roaming\Soda Player\acestream\engine\ace_engine.exe" --js-player | C:\Users\admin\AppData\Roaming\Soda Player\acestream\engine\ace_engine.exe | — | ace_engine.exe | |||||||||||
User: admin Company: Innovative Digital Technologies Integrity Level: MEDIUM Description: Ace Stream Exit code: 0 Version: 3.1.8 Modules
| |||||||||||||||
| 536 | "C:\Users\admin\AppData\Local\sodaplayer\app-1.4.2\Soda Player.exe" --type=ppapi --no-sandbox --ppapi-flash-args --lang=en-US --device-scale-factor=1 --ppapi-antialiased-text-enabled=0 --ppapi-subpixel-rendering-setting=0 --service-request-channel-token=48059DFCE059D480EC2185D34E8463ED --mojo-platform-channel-handle=2580 /prefetch:3 | C:\Users\admin\AppData\Local\sodaplayer\app-1.4.2\Soda Player.exe | — | Soda Player.exe | |||||||||||
User: admin Company: Soda Player Integrity Level: MEDIUM Description: Soda Player Exit code: 0 Version: 1.4.2 Modules
| |||||||||||||||
| 604 | C:\Windows\system32\reg.exe ADD "HKCU\Software\Classes\Applications\Soda Player.exe\shell\open\command" /ve /t REG_SZ /d "\"C:\Users\admin\AppData\Local\sodaplayer\app-1.4.2\Soda Player.exe\" \"%1\"" /f | C:\Windows\system32\reg.exe | — | Soda Player.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 740 | C:\Windows\system32\reg.exe ADD HKCU\Software\Classes\sodaplayer /ve /t REG_SZ /d URL:sodaplayer /f | C:\Windows\system32\reg.exe | — | Soda Player.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 820 | C:\Windows\system32\reg.exe DELETE HKCU\Software\Classes\sodaplayer /f | C:\Windows\system32\reg.exe | — | Soda Player.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 820 | C:\Windows\system32\cmd.exe /c attrib +h C:\Users\admin\AppData\Roaming\.ACEStream\a | C:\Windows\system32\cmd.exe | — | ace_engine.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1028 | C:\Windows\system32\reg.exe ADD HKCU\Software\Classes\sodaplayer\shell\open\command /ve /t REG_SZ /d "\"C:\Users\admin\AppData\Local\sodaplayer\app-1.4.2\Soda Player.exe\" \"%1\"" /f | C:\Windows\system32\reg.exe | — | Soda Player.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1136 | netstat -nr | C:\Windows\system32\NETSTAT.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Netstat Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1380 | "C:\Users\admin\AppData\Local\sodaplayer\app-1.4.2\Squirrel.exe" --updateSelf=C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe | C:\Users\admin\AppData\Local\sodaplayer\app-1.4.2\Squirrel.exe | Update.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
7 347
Read events
2 074
Write events
3 552
Delete events
1 721
Modification events
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2077672256 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30793614 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
147
Suspicious files
137
Text files
233
Unknown types
280
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2400 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab6C8D.tmp | — | |
MD5:— | SHA256:— | |||
| 2400 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar6C8E.tmp | — | |
MD5:— | SHA256:— | |||
| 2400 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | der | |
MD5:— | SHA256:— | |||
| 2400 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\main[1].css | text | |
MD5:— | SHA256:— | |||
| 2400 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\main[1].js | text | |
MD5:— | SHA256:— | |||
| 2400 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C1B3CC7FF1466C71640A202F8258105B_0BE5CCF3469D7CC890B58C8BD9E56C1A | der | |
MD5:— | SHA256:— | |||
| 2400 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | binary | |
MD5:— | SHA256:— | |||
| 2400 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | der | |
MD5:— | SHA256:— | |||
| 2400 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | binary | |
MD5:— | SHA256:— | |||
| 2400 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
233
DNS requests
42
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2400 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.trust-provider.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEENSAj%2F6qJAfE5%2Fj9OXBRE4%3D | US | der | 471 b | whitelisted |
2400 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.trust-provider.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEENSAj%2F6qJAfE5%2Fj9OXBRE4%3D | US | der | 471 b | whitelisted |
2400 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
2400 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2400 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrJdiQ%2Ficg9B19asFe73bPYs%2BreAQUdXGnGUgZvJ2d6kFH35TESHeZ03kCEFslzmkHxCZVZtM5DJmpVK0%3D | US | der | 313 b | whitelisted |
2400 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
2400 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrJdiQ%2Ficg9B19asFe73bPYs%2BreAQUdXGnGUgZvJ2d6kFH35TESHeZ03kCEFslzmkHxCZVZtM5DJmpVK0%3D | US | der | 313 b | whitelisted |
2400 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEBi17v2iewEJCAAAAAAqstc%3D | US | der | 471 b | whitelisted |
2400 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2400 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrBBNpPfHTPX6Jy6BVzyBPnBWMnQQUPnQtH89FdQR%2BP8Cihz5MQ4NRE8YCEApBUQa0zRR7ogpt%2FzGoBQ8%3D | US | der | 279 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2400 | iexplore.exe | 104.28.6.182:443 | www.sodaplayer.com | Cloudflare Inc | US | unknown |
2400 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2400 | iexplore.exe | 172.217.22.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2400 | iexplore.exe | 104.16.85.20:443 | cdn.jsdelivr.net | Cloudflare Inc | US | shared |
2400 | iexplore.exe | 151.139.128.14:80 | ocsp.trust-provider.com | Highwinds Network Group, Inc. | US | suspicious |
2400 | iexplore.exe | 216.58.207.67:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2400 | iexplore.exe | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
2400 | iexplore.exe | 172.217.18.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2400 | iexplore.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2400 | iexplore.exe | 185.60.216.35:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.sodaplayer.com |
| malicious |
ocsp.digicert.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
platform.twitter.com |
| whitelisted |
ocsp.trust-provider.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.comodoca4.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
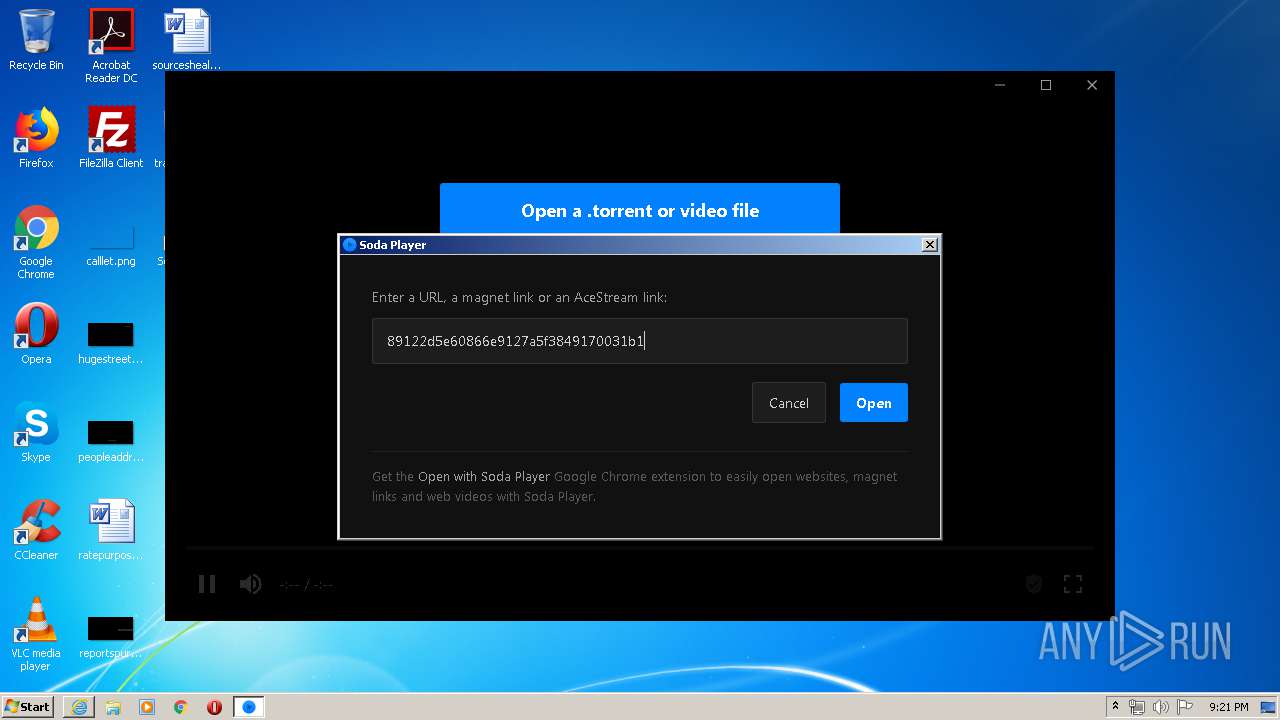
2836 | Soda Player.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT ping request |
2908 | ace_engine.exe | Attempted Information Leak | ET POLICY Python-urllib/ Suspicious User Agent |
2908 | ace_engine.exe | Attempted Information Leak | ET POLICY Python-urllib/ Suspicious User Agent |
2908 | ace_engine.exe | Attempted Information Leak | ET POLICY Python-urllib/ Suspicious User Agent |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
2908 | ace_engine.exe | Potential Corporate Privacy Violation | ET P2P Vuze BT UDP Connection (5) |
2908 | ace_engine.exe | Attempted Information Leak | ET POLICY Python-urllib/ Suspicious User Agent |
2908 | ace_engine.exe | Attempted Information Leak | ET POLICY Python-urllib/ Suspicious User Agent |
— | — | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT nodes reply |
— | — | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT announce_peers request |