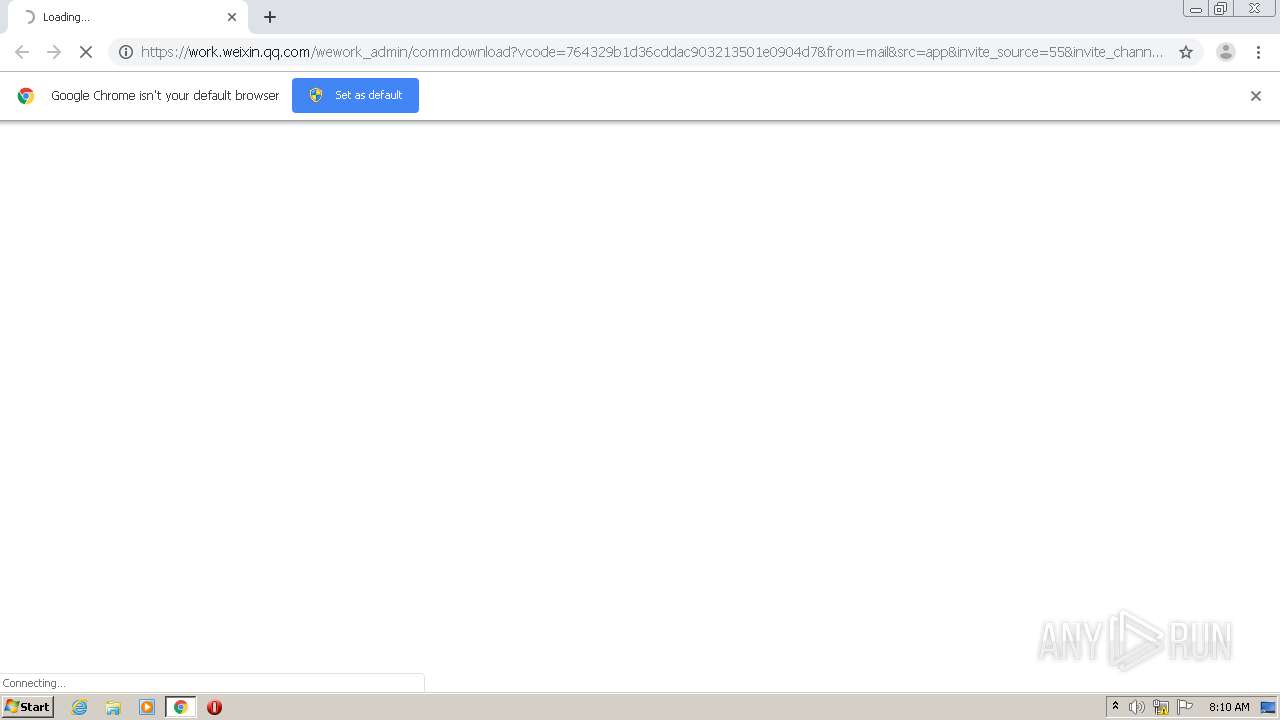
| URL: | https://work.weixin.qq.com/wework_admin/commdownload?vcode=764329b1d36cddac903213501e0904d7&from=mail&src=app&invite_source=55&invite_channel=3&invite_olduser=0&inviter_identity=1&invite_seqid=3 |
| Full analysis: | https://app.any.run/tasks/3dc2a1e5-afaa-4484-93ed-c61cd93483f8 |
| Verdict: | Malicious activity |
| Analysis date: | January 05, 2021, 08:10:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 63C9717EB8EEB8F3A847A79D2B2E9CAE |
| SHA1: | D8868887B6F26AD0F135F7333AB031898F954850 |
| SHA256: | 72ADFB454CB0A8C4DA8ED8379206D97C12D8F9701B157B6B429C15190EC96A1F |
| SSDEEP: | 3:N8bXOLhaAfVRdLF2KahGUBvEGUPRf/JKWp4LAdDMnQf5RtIMRywJdKC7:2iL46dLIhDBsG45KKDMnQftIQhPKC7 |
MALICIOUS
Application was dropped or rewritten from another process
- WeCom_3.1.1.3001.exe (PID: 2760)
- WeCom_3.1.1.3001.exe (PID: 2116)
- MeetingAppInstaller.exe (PID: 3508)
Loads dropped or rewritten executable
- WeCom_3.1.1.3001.exe (PID: 2116)
- wxdriveinstaller.exe (PID: 3060)
- MeetingAppInstaller.exe (PID: 3508)
- WXWork.exe (PID: 2752)
- regsvr32.exe (PID: 1604)
Drops executable file immediately after starts
- MeetingAppInstaller.exe (PID: 3508)
Registers / Runs the DLL via REGSVR32.EXE
- wxdriveinstaller.exe (PID: 3060)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 1796)
- MeetingAppInstaller.exe (PID: 3508)
- wxdriveinstaller.exe (PID: 3060)
- WeCom_3.1.1.3001.exe (PID: 2116)
Creates a directory in Program Files
- WeCom_3.1.1.3001.exe (PID: 2116)
- MeetingAppInstaller.exe (PID: 3508)
- wxdriveinstaller.exe (PID: 3060)
Drops a file with too old compile date
- WeCom_3.1.1.3001.exe (PID: 2116)
- wxdriveinstaller.exe (PID: 3060)
Drops a file that was compiled in debug mode
- MeetingAppInstaller.exe (PID: 3508)
- wxdriveinstaller.exe (PID: 3060)
- WeCom_3.1.1.3001.exe (PID: 2116)
Creates files in the program directory
- MeetingAppInstaller.exe (PID: 3508)
- wxdriveinstaller.exe (PID: 3060)
- WeCom_3.1.1.3001.exe (PID: 2116)
Drops a file with a compile date too recent
- WeCom_3.1.1.3001.exe (PID: 2116)
- wxdriveinstaller.exe (PID: 3060)
- MeetingAppInstaller.exe (PID: 3508)
Creates files in the user directory
- wxdriveinstaller.exe (PID: 3060)
- regsvr32.exe (PID: 1604)
- WeCom_3.1.1.3001.exe (PID: 2116)
- WXWork.exe (PID: 2752)
Changes default file association
- wxdriveinstaller.exe (PID: 3060)
- WXWork.exe (PID: 2752)
Creates a software uninstall entry
- WeCom_3.1.1.3001.exe (PID: 2116)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 1604)
INFO
Application launched itself
- chrome.exe (PID: 1796)
Reads the hosts file
- chrome.exe (PID: 336)
- chrome.exe (PID: 1796)
Reads settings of System Certificates
- chrome.exe (PID: 1796)
- WXWork.exe (PID: 2752)
Dropped object may contain Bitcoin addresses
- WeCom_3.1.1.3001.exe (PID: 2116)
- wxdriveinstaller.exe (PID: 3060)
- MeetingAppInstaller.exe (PID: 3508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
57
Monitored processes
16
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,8792541378595596295,2334159481139442011,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=4189311989878020505 --mojo-platform-channel-handle=1532 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,8792541378595596295,2334159481139442011,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13369512314040319842 --mojo-platform-channel-handle=3420 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,8792541378595596295,2334159481139442011,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6280820279395759963 --mojo-platform-channel-handle=1040 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2640 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1604 | regsvr32 /s "C:\Program Files (x86)\WXDrive\extensions\x86\WeDrivePlugin32_97.dll" | C:\Windows\system32\regsvr32.exe | — | wxdriveinstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://work.weixin.qq.com/wework_admin/commdownload?vcode=764329b1d36cddac903213501e0904d7&from=mail&src=app&invite_source=55&invite_channel=3&invite_olduser=0&inviter_identity=1&invite_seqid=3" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
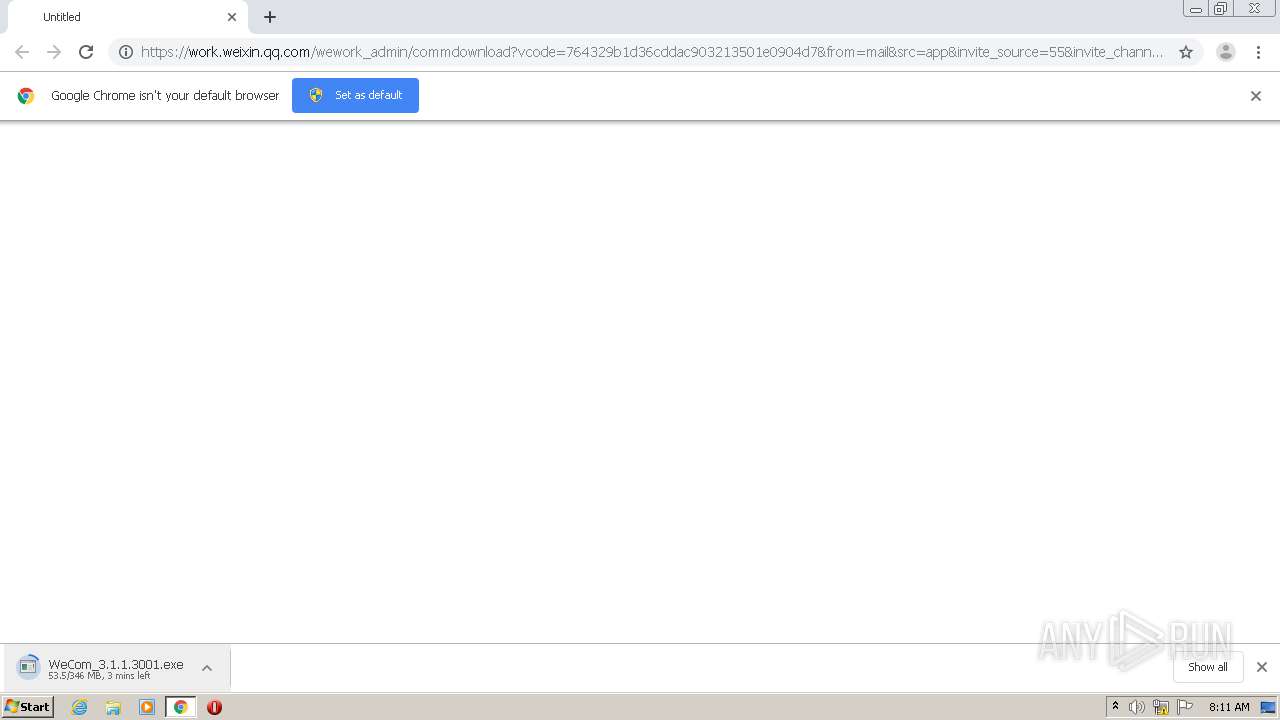
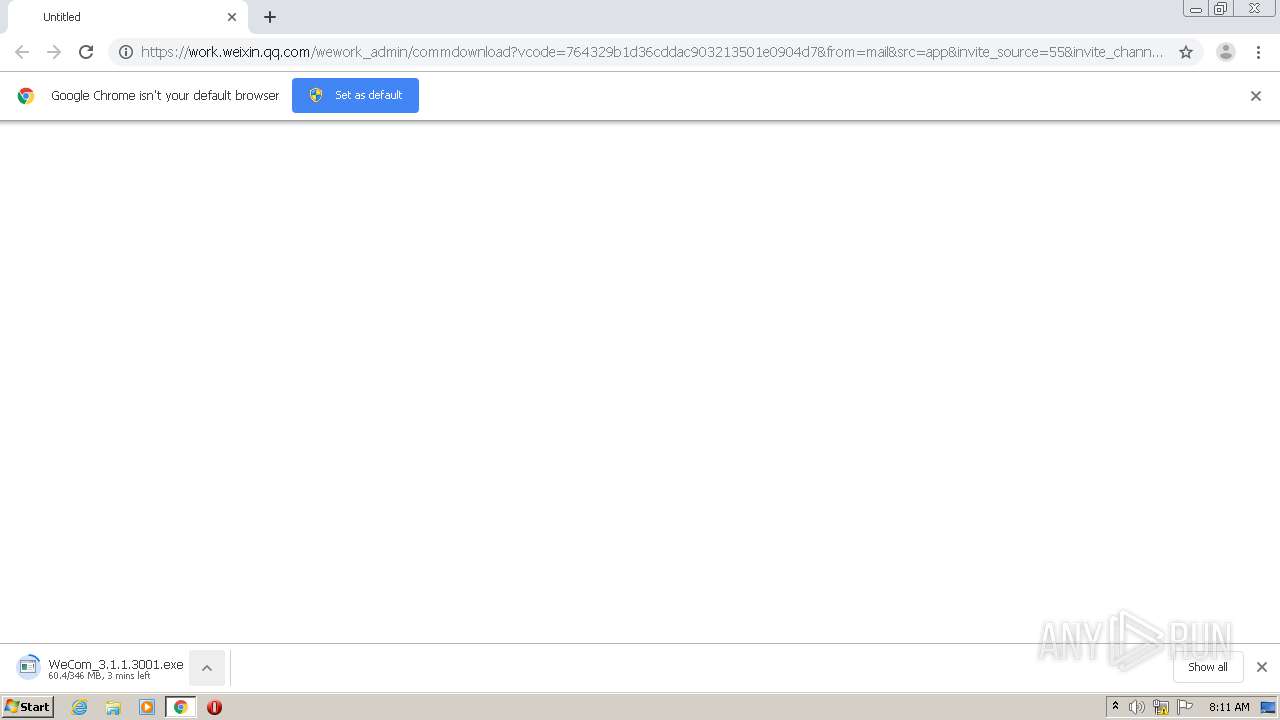
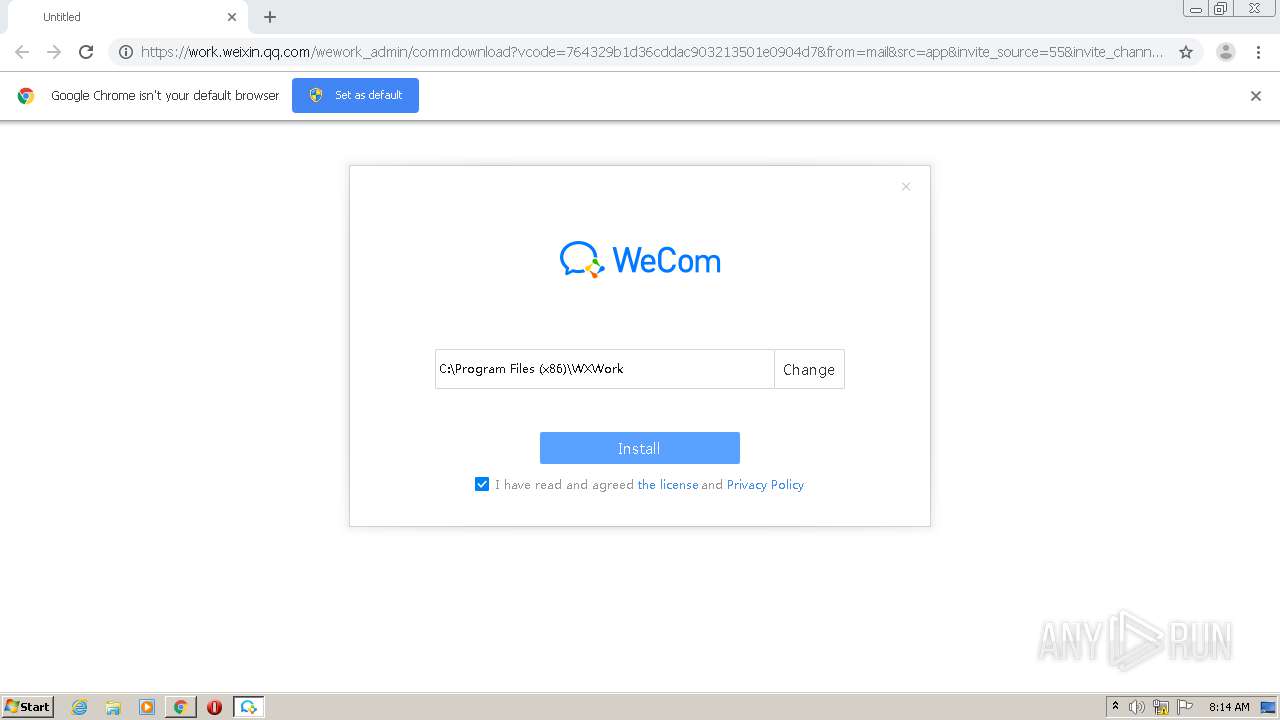
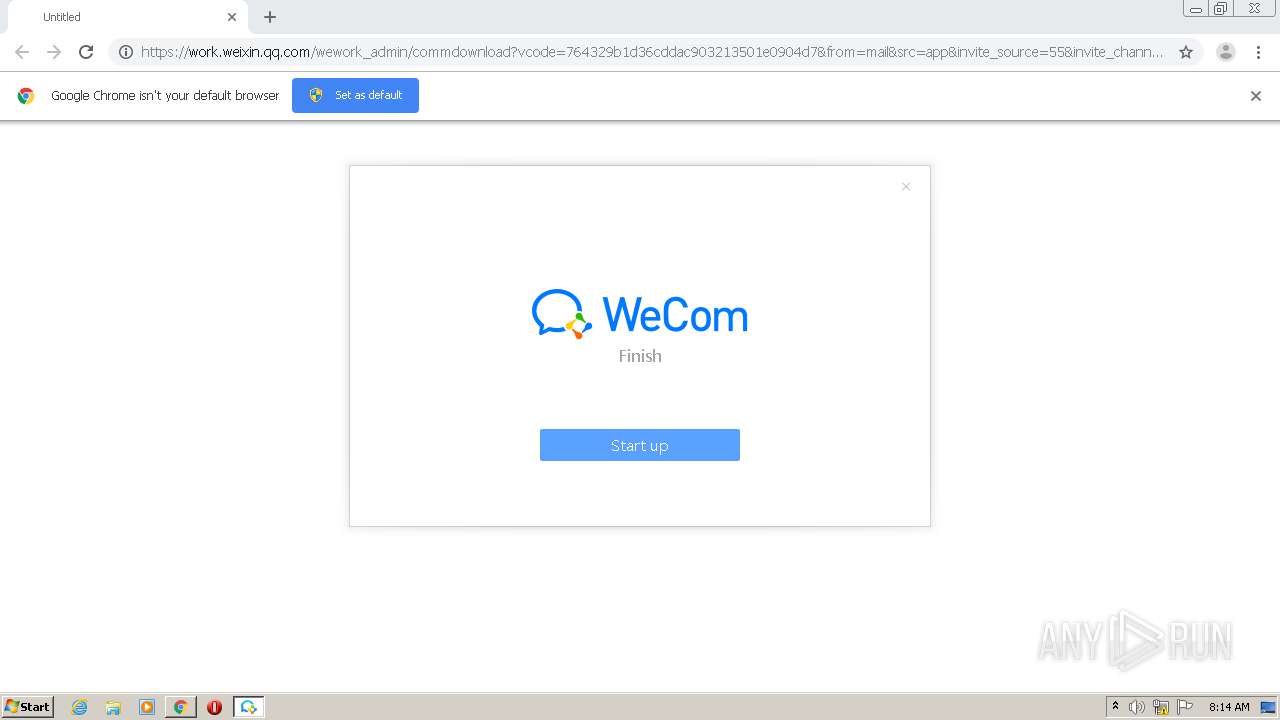
| 2116 | "C:\Users\admin\Downloads\WeCom_3.1.1.3001.exe" | C:\Users\admin\Downloads\WeCom_3.1.1.3001.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 企业微信安装程序 Exit code: 0 Version: 3.1.1.3001 Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,8792541378595596295,2334159481139442011,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1427154657220664124 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2356 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,8792541378595596295,2334159481139442011,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11311492698729143849 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
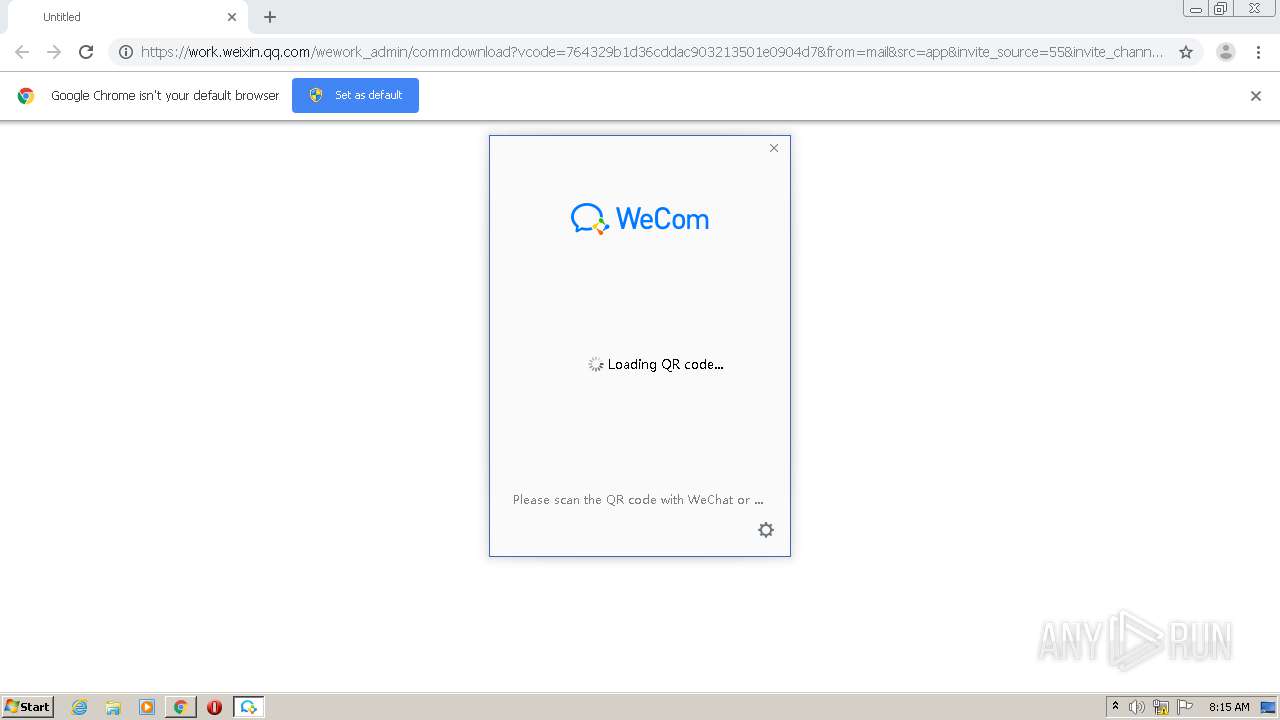
| 2752 | "C:\Program Files (x86)\WXWork\WXWork.exe" | C:\Program Files (x86)\WXWork\WXWork.exe | WeCom_3.1.1.3001.exe | ||||||||||||
User: admin Company: Tencent Integrity Level: MEDIUM Exit code: 0 Version: 3.1.1.3001 Modules
| |||||||||||||||
Total events
1 516
Read events
1 343
Write events
170
Delete events
3
Modification events
| (PID) Process: | (1136) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1796-13254307839734875 |
Value: 259 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
315
Suspicious files
41
Text files
224
Unknown types
82
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FF41F00-704.pma | — | |
MD5:— | SHA256:— | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\11702f04-1033-4900-b140-c0c508981209.tmp | — | |
MD5:— | SHA256:— | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:67F45CAA18C889645F50CD6216C81E65 | SHA256:33ED82CDDDFFD55A5059C147C6CD20F66C6712314F890A39576D3C10914D0029 | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:FB5B20517A0D1F7DAD485989565BEE5E | SHA256:99405F66EDBEB2306F4D0B4469DCADFF5293B5E1549C588CCFACEA439BB3B101 | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:C2DDBA63E4A2BD2E39A8B6C2C6384AAE | SHA256:6D5C1C78341C6F84911055D970ADDB0EC3499F8BF7FADE062122A22209CE67D9 | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF154252.TMP | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF154456.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
19
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2752 | WXWork.exe | GET | — | 182.254.116.117:80 | http://182.254.116.117/d?dn=adc560794679979480c228514177bf94d6216e5c9e9b638d5c179fc7b71c7b76&id=2&ttl=1&clientip=1&type=a | CN | — | — | suspicious |
2752 | WXWork.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/gsorganizationvalsha2g2/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQMnk2cPe3vhNiR6XLHz4QGvBl7BwQUlt5h8b0cFilTHMDMfTuDAEDmGnwCDF%2BaiOCYKNbCkhhpaA%3D%3D | US | der | 1.54 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
336 | chrome.exe | 203.205.254.11:443 | work.weixin.qq.com | — | CN | unknown |
336 | chrome.exe | 172.217.16.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
336 | chrome.exe | 2.16.186.19:443 | dldir1.qq.com | Akamai International B.V. | — | whitelisted |
336 | chrome.exe | 172.217.23.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2752 | WXWork.exe | 157.255.245.177:8080 | gap.work.weixin.qq.com | China Unicom Shenzen network | CN | unknown |
2752 | WXWork.exe | 182.254.116.117:80 | — | Shenzhen Tencent Computer Systems Company Limited | CN | suspicious |
2752 | WXWork.exe | 104.18.21.226:80 | — | Cloudflare Inc | US | shared |
— | — | 104.18.20.226:80 | — | Cloudflare Inc | US | shared |
— | — | 104.18.21.226:80 | — | Cloudflare Inc | US | shared |
2752 | WXWork.exe | 150.109.206.166:443 | wwcdn.weixin.qq.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
work.weixin.qq.com |
| suspicious |
accounts.google.com |
| shared |
dldir1.qq.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients4.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
gap.work.weixin.qq.com |
| unknown |
wwcdn.weixin.qq.com |
| suspicious |
i.work.weixin.qq.com |
| unknown |
Threats
Process | Message |
|---|---|
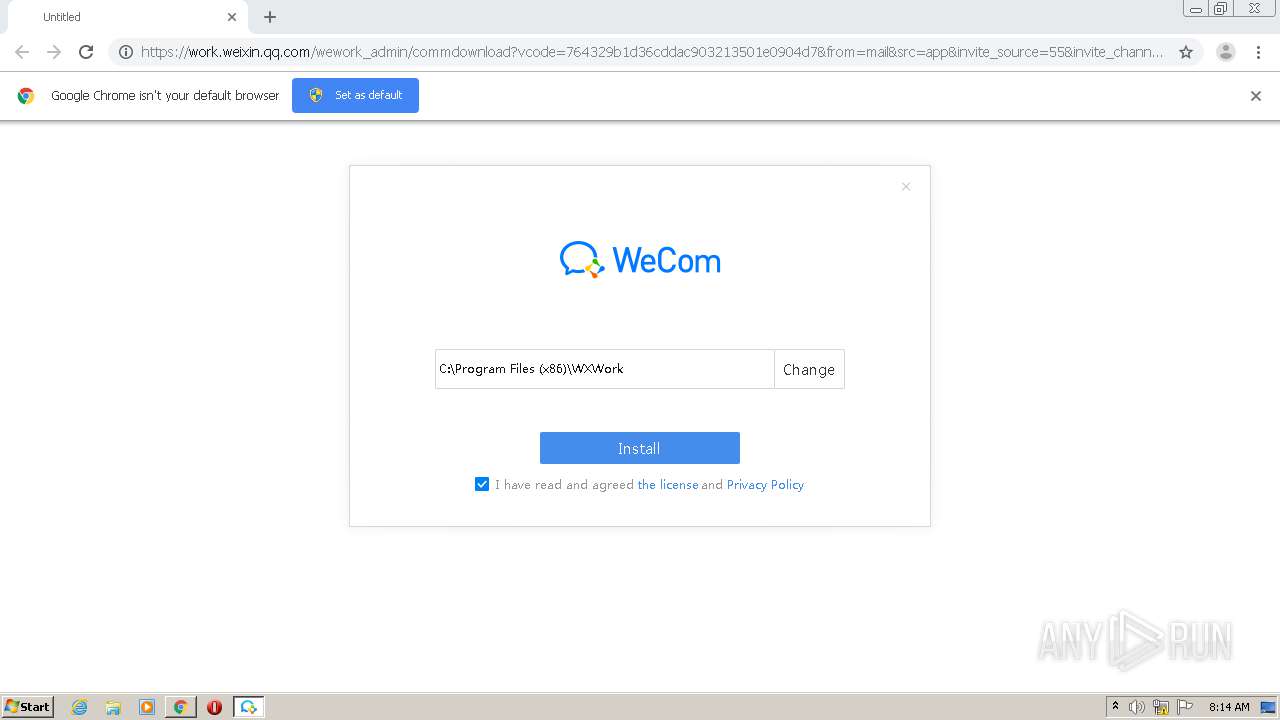
WeCom_3.1.1.3001.exe | C:\Program Files (x86)\WXWork3.1.1.3001 |