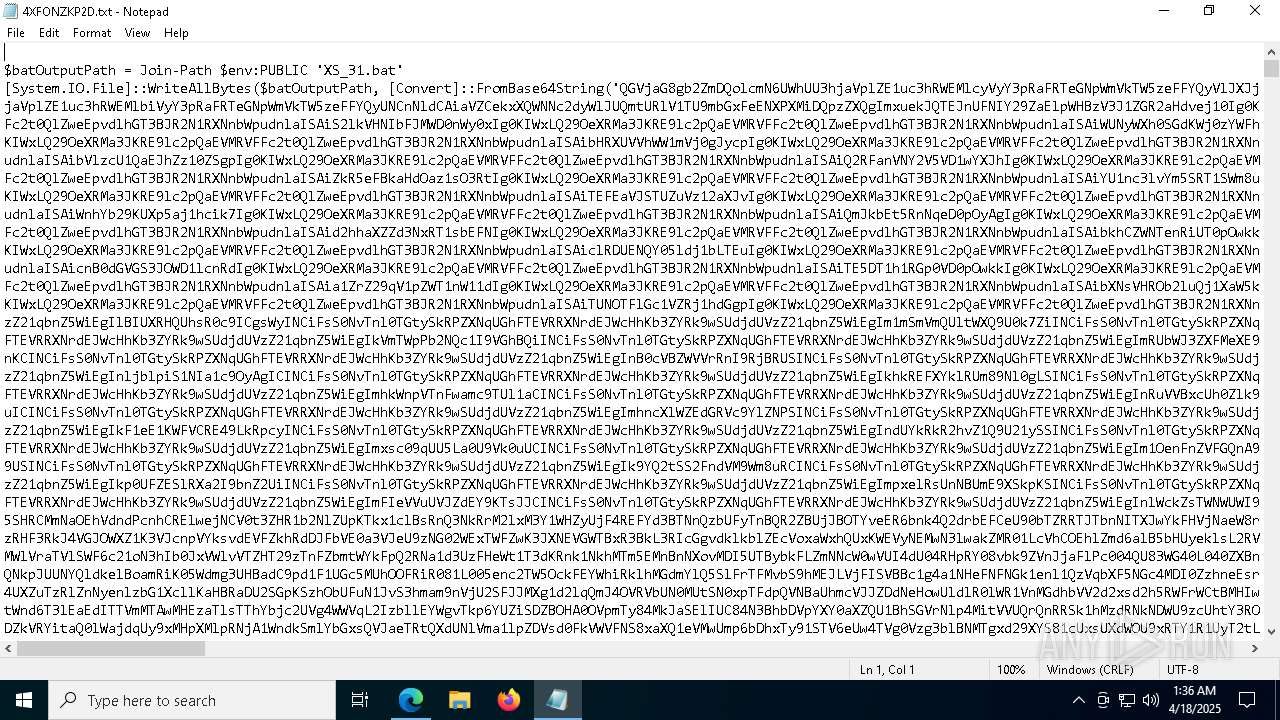
| URL: | https://www.dropbox.com/scl/fi/573ovwi8ow9wfi0zghq1o/4XFONZKP2D.txt?rlkey=pd5i8h9gl8wme4psr3pzw1lwl&dl=1 |
| Full analysis: | https://app.any.run/tasks/c014ffce-bea1-46f8-a49f-0e7f63537f48 |
| Verdict: | Malicious activity |
| Analysis date: | April 18, 2025, 01:36:05 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 67BB69CD98EA676771BCC3B353EF3390 |
| SHA1: | 6A30488C9D1B578023F0C9E0A94A0AD8743FD83E |
| SHA256: | 7288F1216AC0B49AB6FA8B9BDC6696669C53D29CE8B06BFCEAB4B3486062C76A |
| SSDEEP: | 3:N8DSLcVHGkG6QQz/MIWKcrUhHRcprQMQDVkiU:2OLHkfEIxhsEMQq |
MALICIOUS
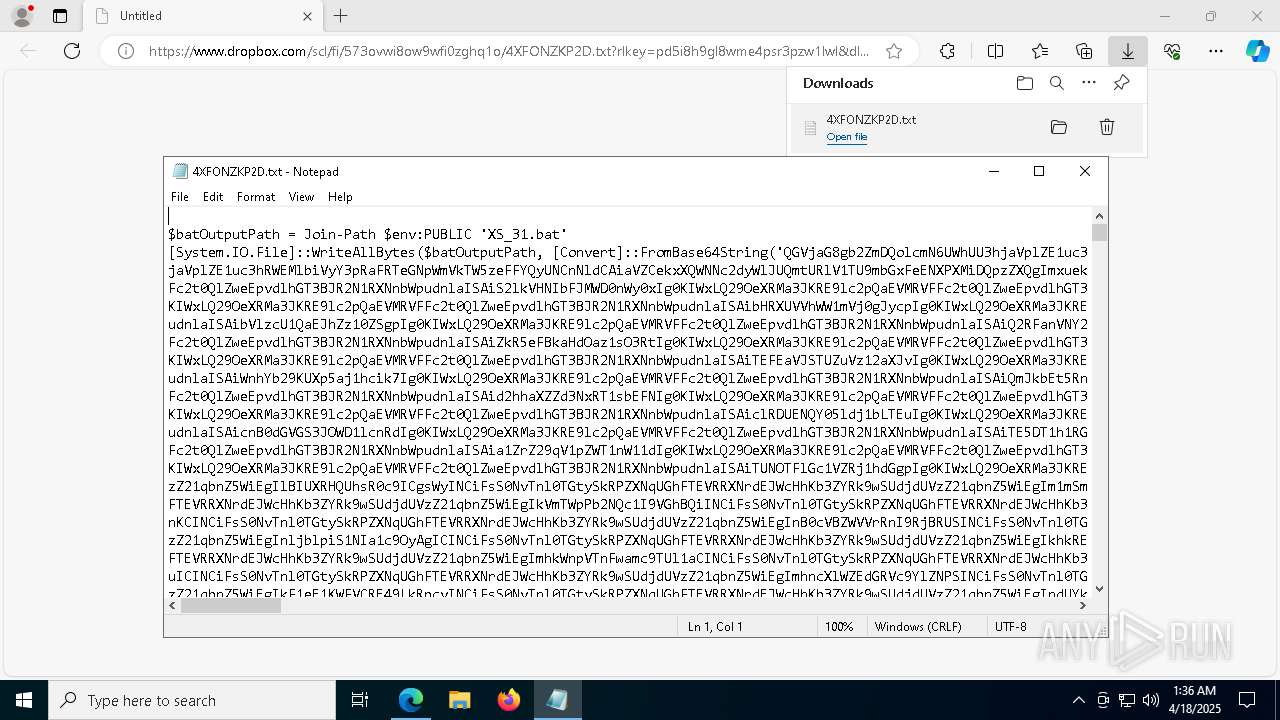
Run PowerShell with an invisible window
- powershell.exe (PID: 2416)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 8280)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 4880)
- cmd.exe (PID: 8216)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 8280)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 8280)
Bypass execution policy to execute commands
- powershell.exe (PID: 7756)
- powershell.exe (PID: 8280)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 8280)
SUSPICIOUS
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 7960)
- cmd.exe (PID: 4880)
- cmd.exe (PID: 8216)
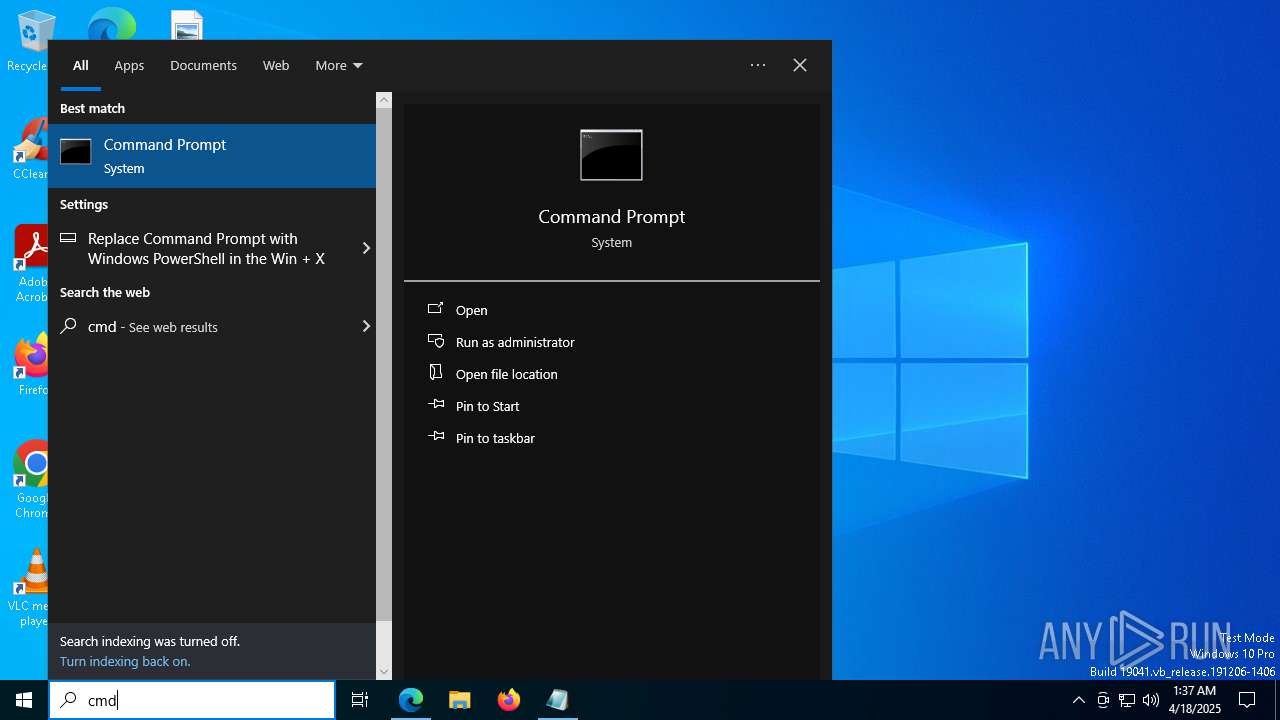
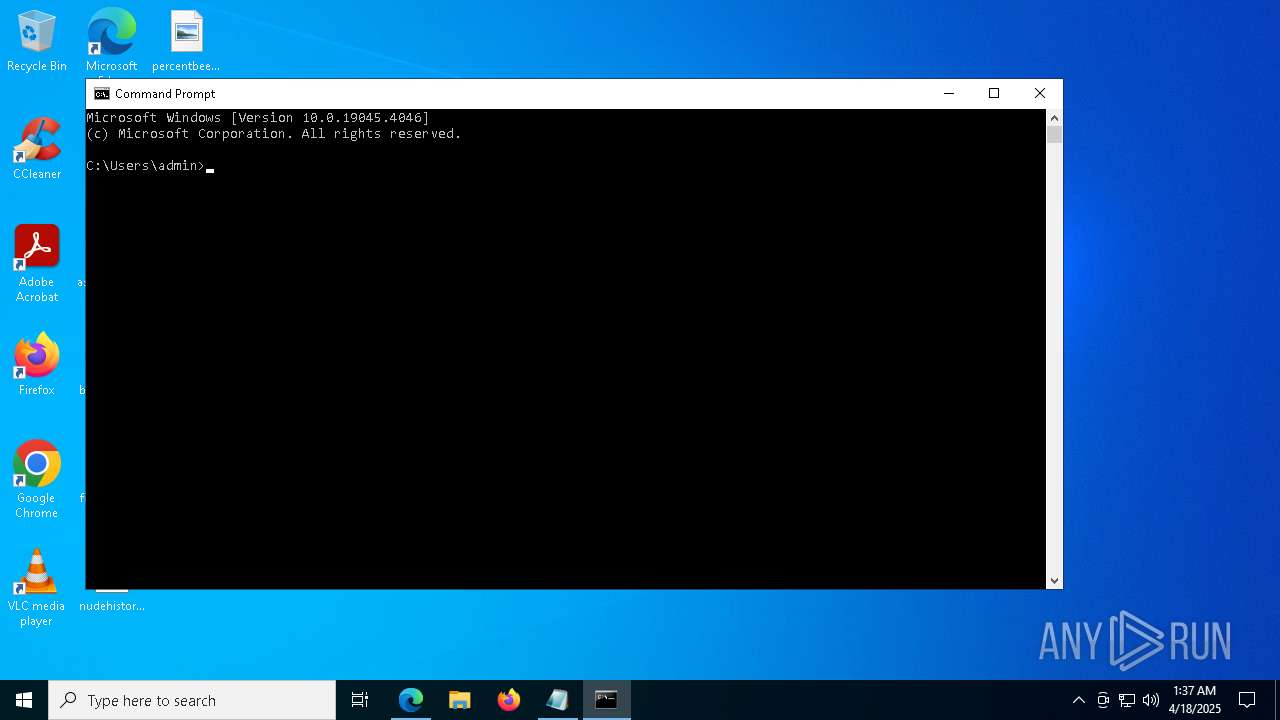
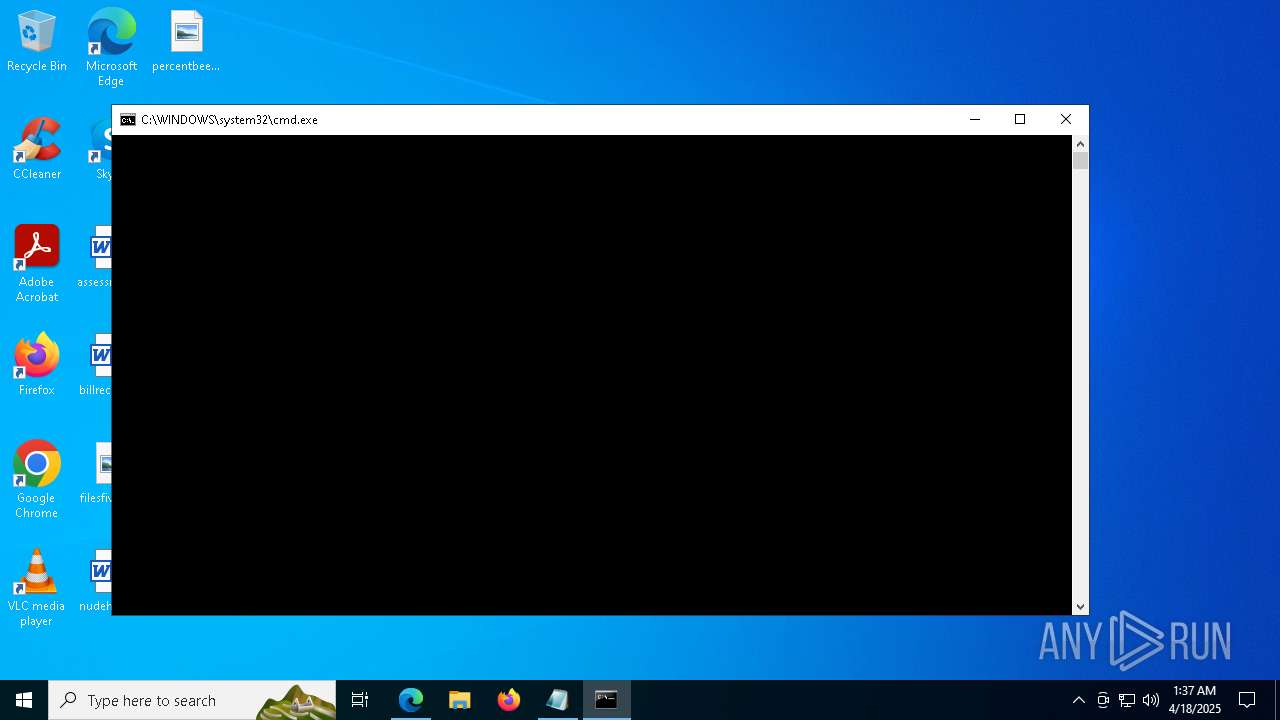
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7960)
- cmd.exe (PID: 4880)
- cmd.exe (PID: 8216)
Removes files via Powershell
- powershell.exe (PID: 2416)
Likely accesses (executes) a file from the Public directory
- powershell.exe (PID: 7756)
- cmd.exe (PID: 4880)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 4880)
- cmd.exe (PID: 8216)
Downloads file from URI via Powershell
- powershell.exe (PID: 7756)
- powershell.exe (PID: 8280)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 4880)
- cmd.exe (PID: 8216)
Potential Corporate Privacy Violation
- powershell.exe (PID: 2416)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 2416)
- wscript.exe (PID: 2192)
Executing commands from a ".bat" file
- powershell.exe (PID: 2416)
- wscript.exe (PID: 2192)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2416)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 2416)
The process executes VB scripts
- powershell.exe (PID: 7756)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 2192)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 2192)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2192)
Cryptography encrypted command line is found
- powershell.exe (PID: 8280)
- powershell.exe (PID: 7756)
The process checks if it is being run in the virtual environment
- powershell.exe (PID: 8280)
INFO
Checks supported languages
- identity_helper.exe (PID: 6540)
Application launched itself
- msedge.exe (PID: 5072)
- Acrobat.exe (PID: 1132)
- AcroCEF.exe (PID: 2984)
Reads Microsoft Office registry keys
- msedge.exe (PID: 5072)
Reads Environment values
- identity_helper.exe (PID: 6540)
Reads security settings of Internet Explorer
- notepad.exe (PID: 6156)
Reads the computer name
- identity_helper.exe (PID: 6540)
Reads the software policy settings
- slui.exe (PID: 6108)
- slui.exe (PID: 1676)
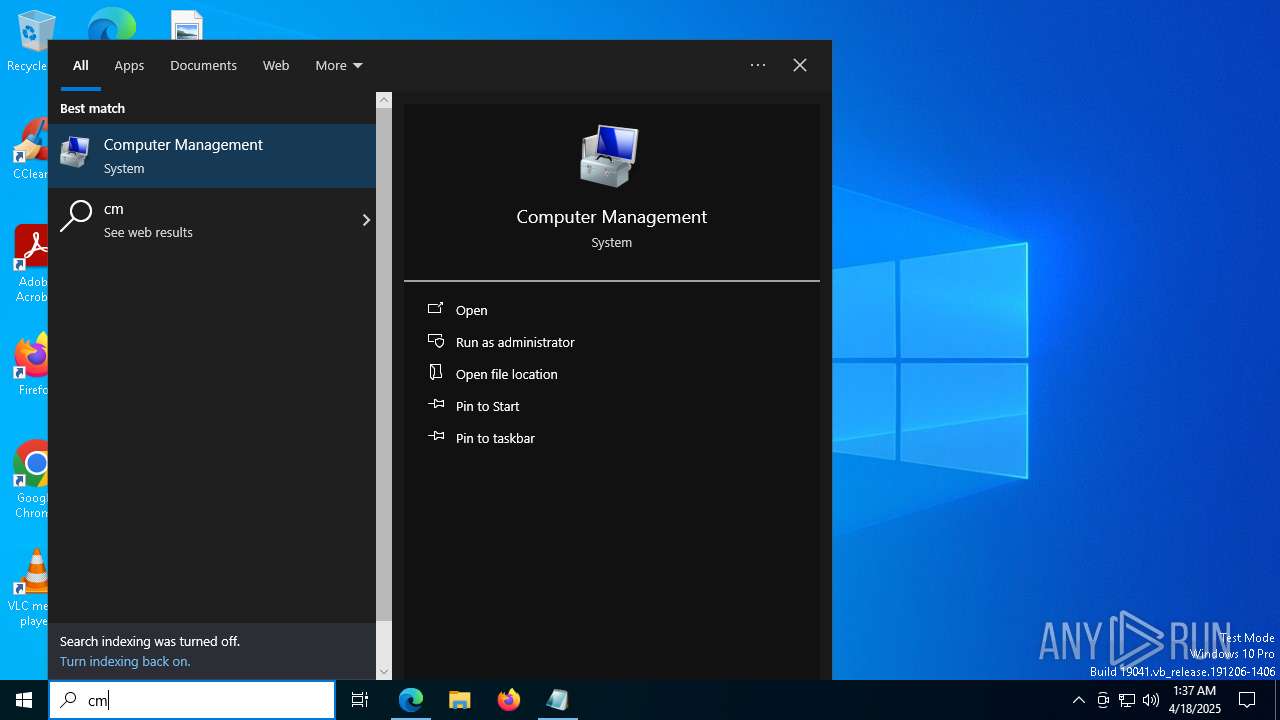
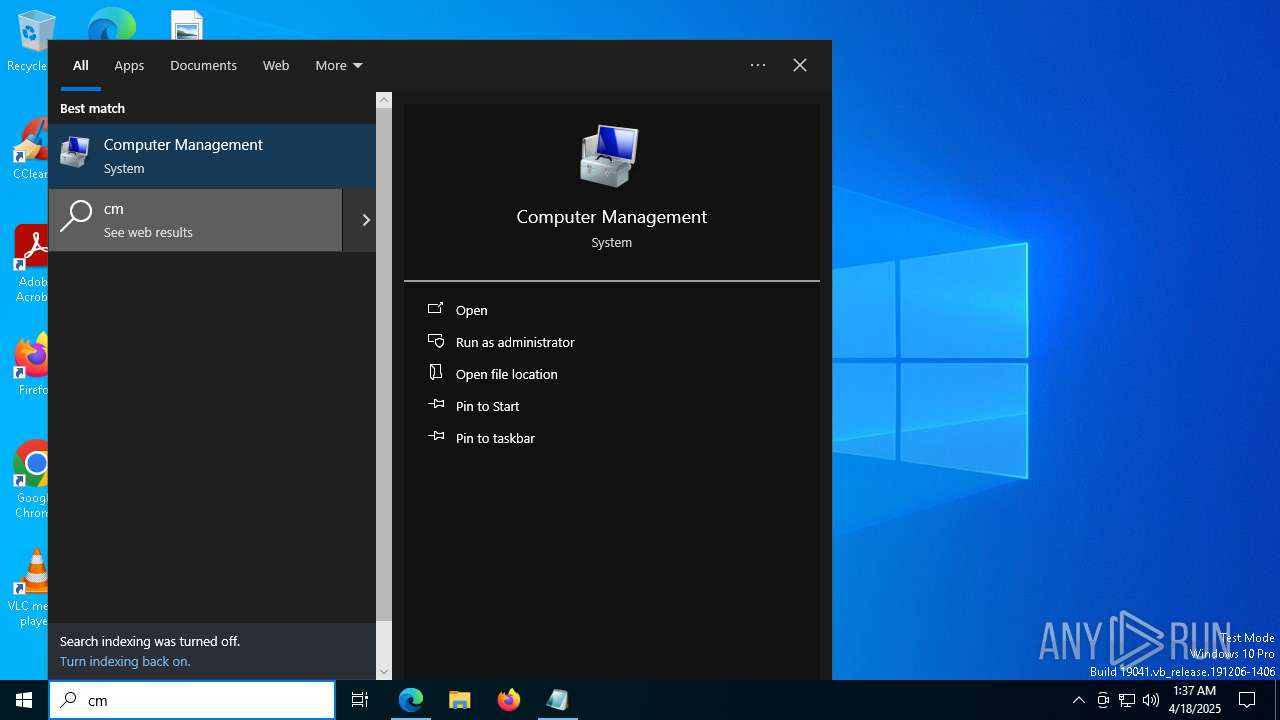
Manual execution by a user
- cmd.exe (PID: 7960)
Disables trace logs
- powershell.exe (PID: 2416)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 8280)
Checks proxy server information
- powershell.exe (PID: 2416)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 8280)
- slui.exe (PID: 1676)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 8280)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 8280)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 8280)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8280)
The sample compiled with english language support
- msedge.exe (PID: 4028)
Executable content was dropped or overwritten
- msedge.exe (PID: 4028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
212
Monitored processes
76
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 744 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=gpu-process --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=disabled --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=2764 --field-trial-handle=1612,i,437340992705335793,17380283934083335614,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:2 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Version: 23.1.20093.0 Modules
| |||||||||||||||
| 904 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=renderer --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --touch-events=enabled --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=2908 --field-trial-handle=1612,i,437340992705335793,17380283934083335614,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:1 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 23.1.20093.0 Modules
| |||||||||||||||
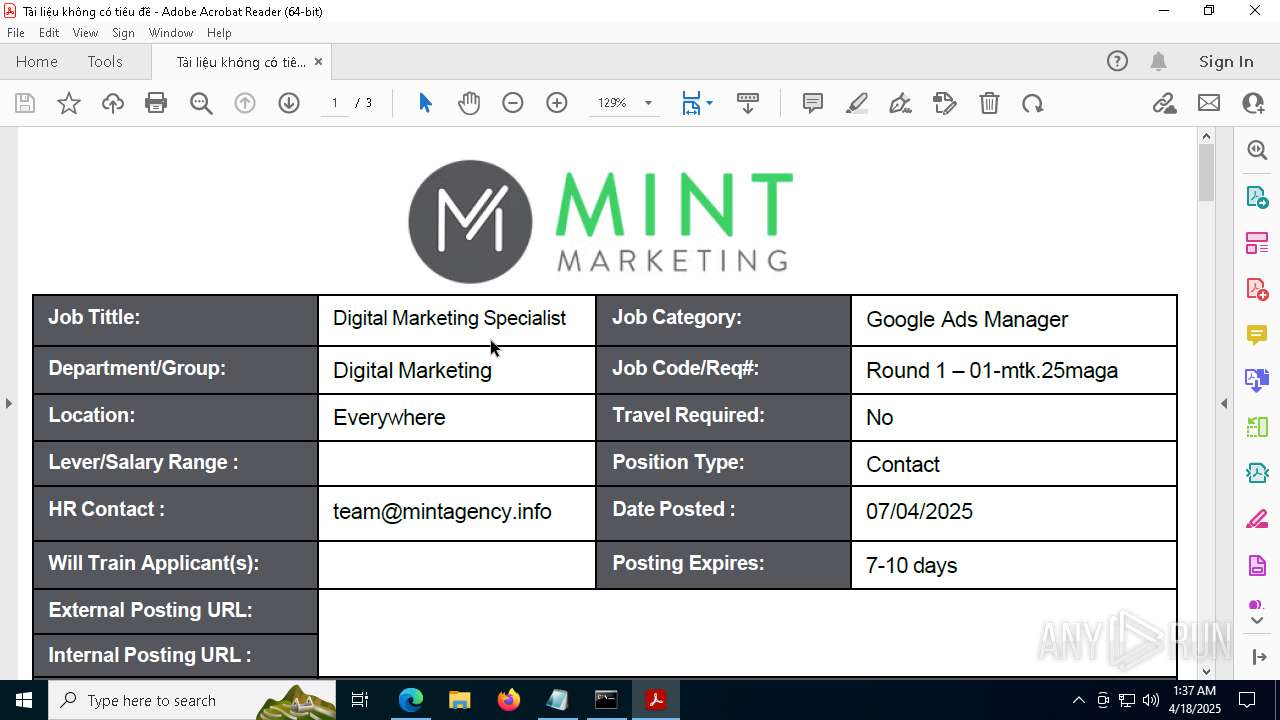
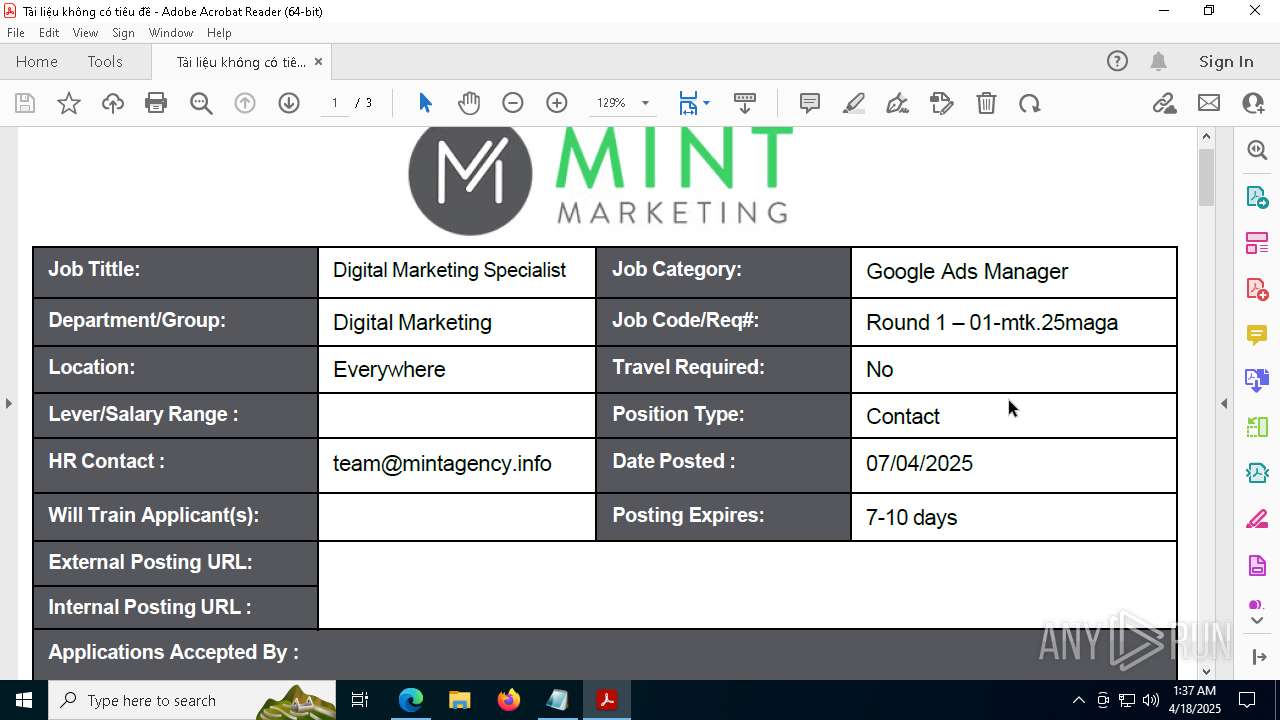
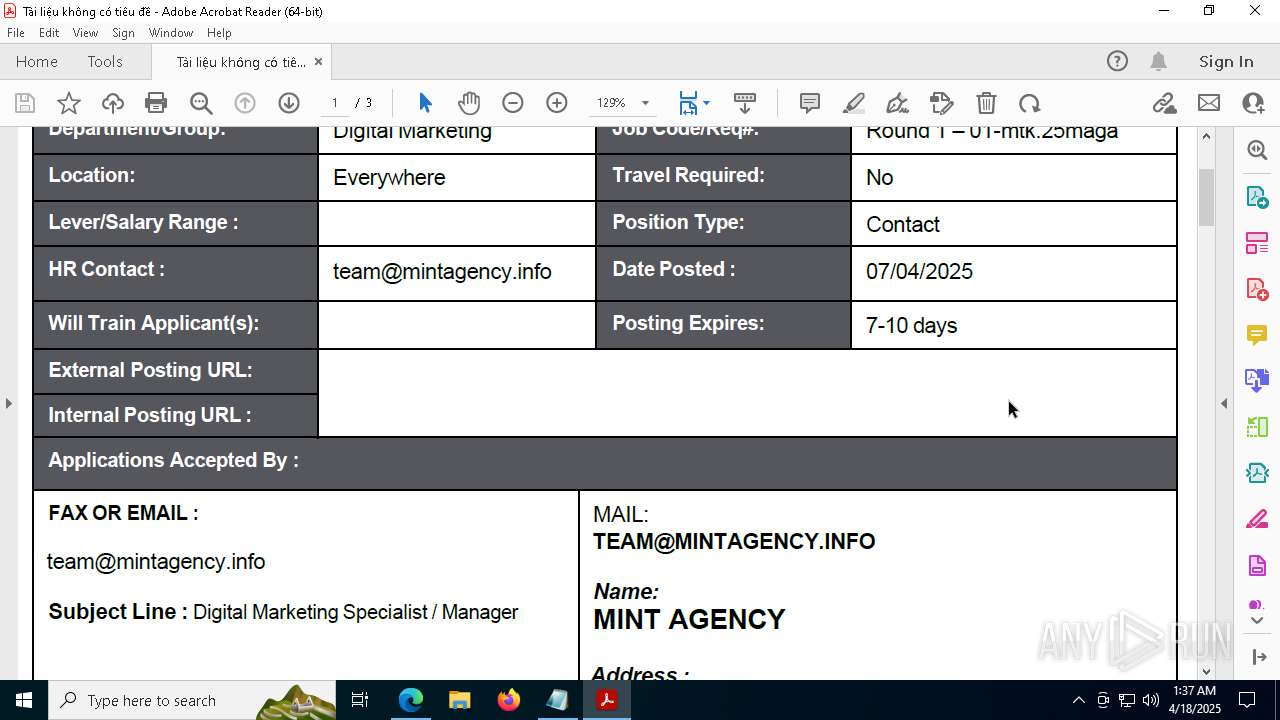
| 1132 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe" "C:\Users\admin\MINT_AGENCY_Digital_Marketing_Job_Details_and_Responsibilities_Overview_2025.pdf" | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe | powershell.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Version: 23.1.20093.0 Modules
| |||||||||||||||
| 1272 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7136 --field-trial-handle=2440,i,4905931885211516283,672043095267910114,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6720 --field-trial-handle=2440,i,4905931885211516283,672043095267910114,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1452 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=5228 --field-trial-handle=2440,i,4905931885211516283,672043095267910114,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1676 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1760 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6720 --field-trial-handle=2440,i,4905931885211516283,672043095267910114,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2092 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5888 --field-trial-handle=2440,i,4905931885211516283,672043095267910114,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2192 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\Documents\NetStats_Sys_493.vbs" | C:\Windows\SysWOW64\wscript.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
Total events
39 256
Read events
39 094
Write events
157
Delete events
5
Modification events
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 647C93D399912F00 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328322 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1D1600B4-A416-42EA-AF63-D0099C3439BB} | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2A5B9BD399912F00 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328322 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {8954CC91-E11D-4A03-BEC5-37A75DC366A5} | |||
| (PID) Process: | (7952) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 010000000000000072AA4C4502B0DB01 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
15
Suspicious files
576
Text files
107
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b613.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b623.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b623.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b632.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b642.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
72
DNS requests
75
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8176 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8176 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6876 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1745355093&P2=404&P3=2&P4=PAlbOhGmoGR7deHyRvn0DGLcnpxLiuHr7dN0aTDhbiZVoTZR4Gd0EBBFzfJmCStcsmXrySXDYyCWIL40%2fuWU%2fw%3d%3d | unknown | — | — | whitelisted |
6876 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1745355093&P2=404&P3=2&P4=PAlbOhGmoGR7deHyRvn0DGLcnpxLiuHr7dN0aTDhbiZVoTZR4Gd0EBBFzfJmCStcsmXrySXDYyCWIL40%2fuWU%2fw%3d%3d | unknown | — | — | whitelisted |
6876 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1745355093&P2=404&P3=2&P4=PAlbOhGmoGR7deHyRvn0DGLcnpxLiuHr7dN0aTDhbiZVoTZR4Gd0EBBFzfJmCStcsmXrySXDYyCWIL40%2fuWU%2fw%3d%3d | unknown | — | — | whitelisted |
6876 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1745355093&P2=404&P3=2&P4=EWmpd%2bPpzX1tnluW2DwgplYcq1jHG4aMN0eOhN8DSPN3BBzsZBLB%2fVjbhVb0Xm4h8eujaLCKH0vQpLZ9lC6s4A%3d%3d | unknown | — | — | whitelisted |
6876 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1745355093&P2=404&P3=2&P4=EWmpd%2bPpzX1tnluW2DwgplYcq1jHG4aMN0eOhN8DSPN3BBzsZBLB%2fVjbhVb0Xm4h8eujaLCKH0vQpLZ9lC6s4A%3d%3d | unknown | — | — | whitelisted |
6876 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0ad45e55-dc4f-4045-88dd-5d926e347210?P1=1745447271&P2=404&P3=2&P4=iJF401SHqV4EUNu11uCLbcOD7vPmrEb9b246bSNiGeuMeXkwXjxTKXUP5ItdPFG0dOnFZz7ufDqM5JzxknnsLQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7380 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5072 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7380 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7380 | msedge.exe | 162.125.66.18:443 | www.dropbox.com | DROPBOX | DE | whitelisted |
7380 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.dropbox.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
uc7d2a3e049d2415ebaded23ade3.dl.dropboxusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2416 | powershell.exe | Potential Corporate Privacy Violation | ET INFO Dropbox.com Offsite File Backup in Use |