| File name: | WinRar 4.1.65.exe_ |
| Full analysis: | https://app.any.run/tasks/91be0571-3aba-41f3-a54a-6ea99b99de5d |
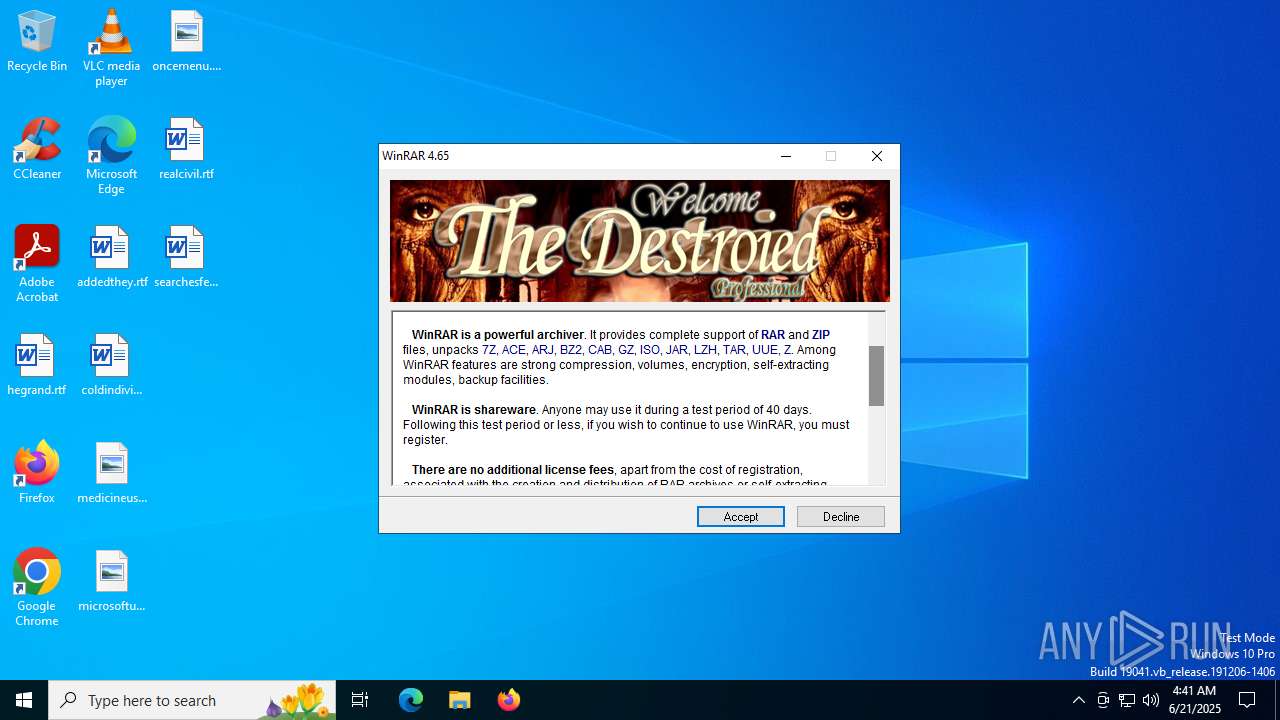
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 04:41:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 7D3BA4C3641809983960D61C67AFFA05 |
| SHA1: | A81CBF73C9D6FCA39E74E46819770CD3C6B2264F |
| SHA256: | 728817FF401F36CC5A766B97212F8495E4F9AD552B564E245AAA5A7E6BB96B27 |
| SSDEEP: | 98304:R3DmF0bfB0kpgWI9g6LMixE4RKvpF8pfOU7d4H1rUOUZGzFfWPR8pWMSD3BfOcuk:l9 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- WinRar 4.1.65.exe_.exe (PID: 3716)
- Uninstall.exe (PID: 2460)
Reads Microsoft Outlook installation path
- WinRar 4.1.65.exe_.exe (PID: 3716)
Executable content was dropped or overwritten
- WinRar 4.1.65.exe_.exe (PID: 3716)
Drops 7-zip archiver for unpacking
- WinRar 4.1.65.exe_.exe (PID: 3716)
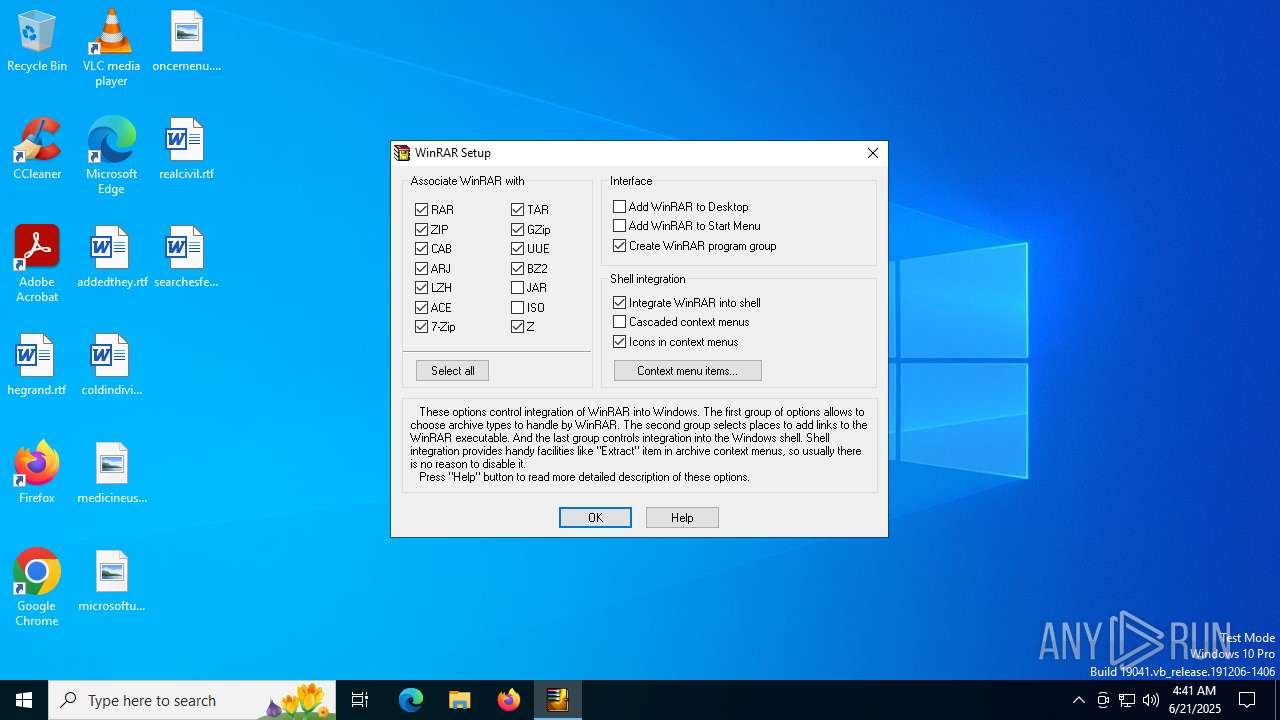
Creates/Modifies COM task schedule object
- Uninstall.exe (PID: 2460)
Reads Internet Explorer settings
- WinRar 4.1.65.exe_.exe (PID: 3716)
Creates a software uninstall entry
- Uninstall.exe (PID: 2460)
INFO
Checks supported languages
- WinRar 4.1.65.exe_.exe (PID: 3716)
- Uninstall.exe (PID: 2460)
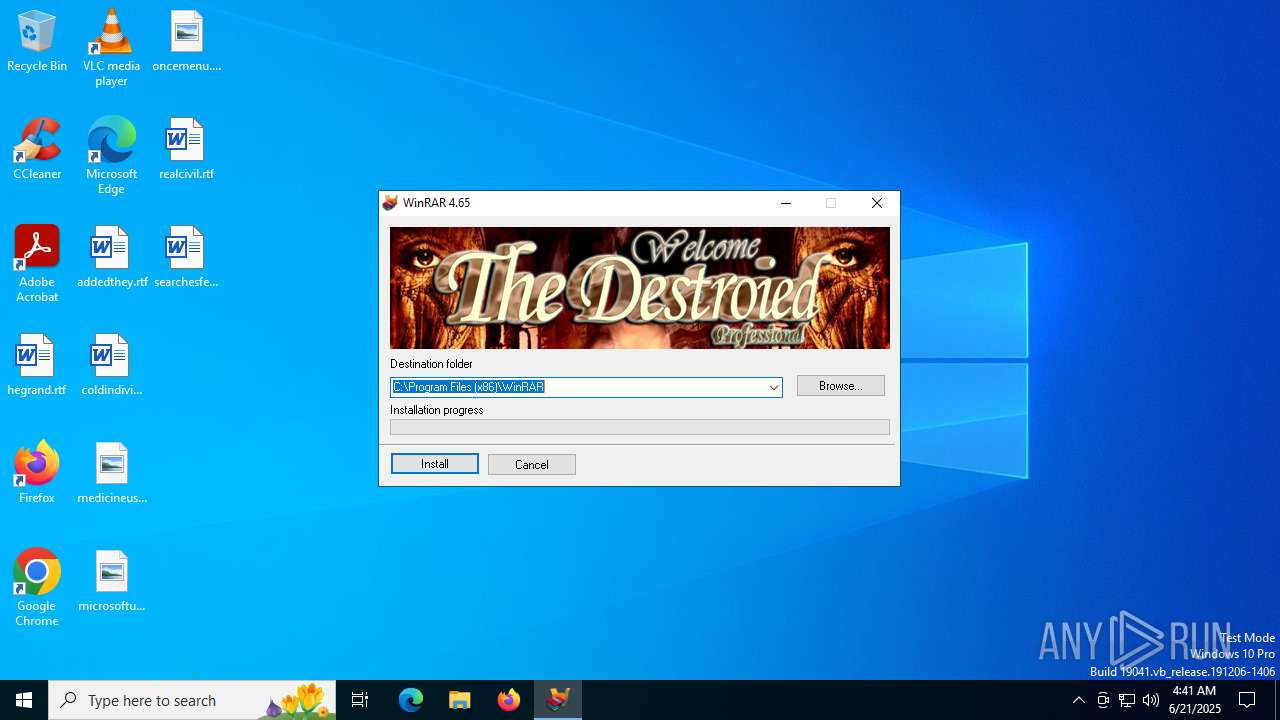
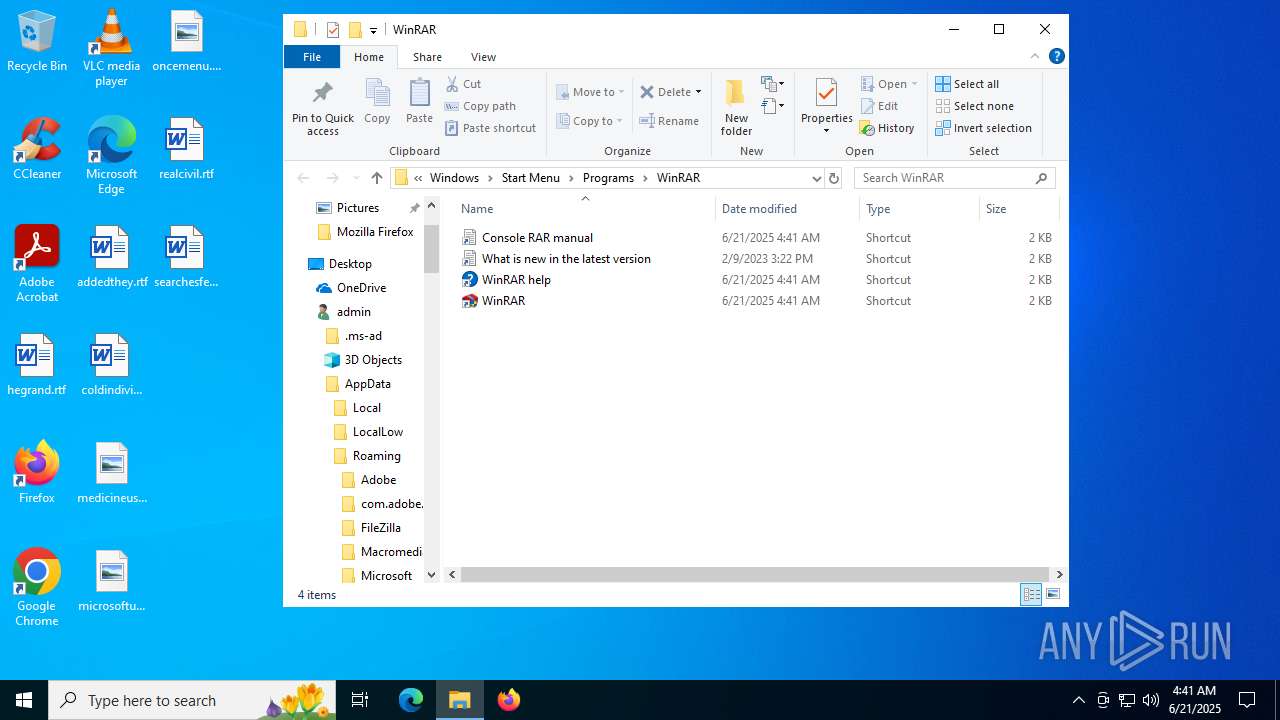
Creates files in the program directory
- WinRar 4.1.65.exe_.exe (PID: 3716)
- Uninstall.exe (PID: 2460)
Checks proxy server information
- WinRar 4.1.65.exe_.exe (PID: 3716)
- slui.exe (PID: 1480)
Reads the computer name
- WinRar 4.1.65.exe_.exe (PID: 3716)
- Uninstall.exe (PID: 2460)
Process checks computer location settings
- WinRar 4.1.65.exe_.exe (PID: 3716)
The sample compiled with english language support
- WinRar 4.1.65.exe_.exe (PID: 3716)
Reads the software policy settings
- slui.exe (PID: 1480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | WinRAR Self Extracting archive (94.8) |
|---|---|---|
| .scr | | | Windows screen saver (2.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.2) |
| .exe | | | Win32 Executable (generic) (0.8) |
| .exe | | | Generic Win/DOS Executable (0.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2005:10:07 09:05:22+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 77824 |
| InitializedDataSize: | 262656 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
147
Monitored processes
5
Malicious processes
1
Suspicious processes
0
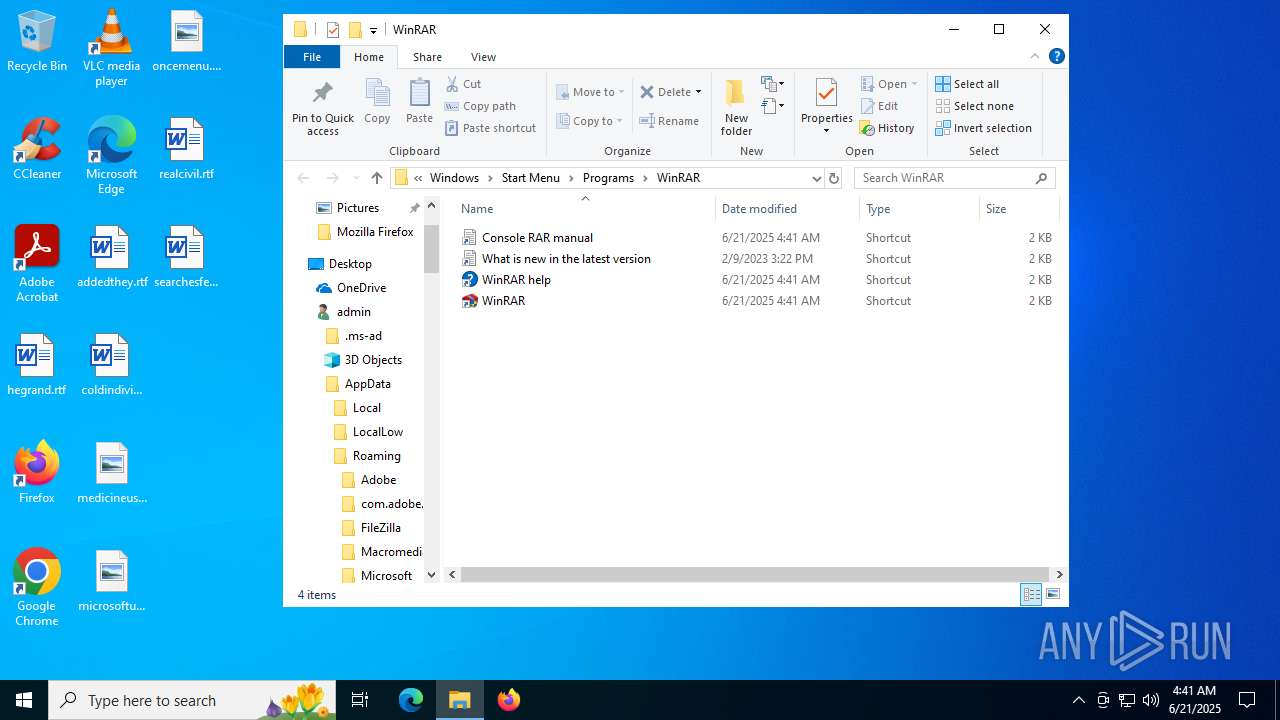
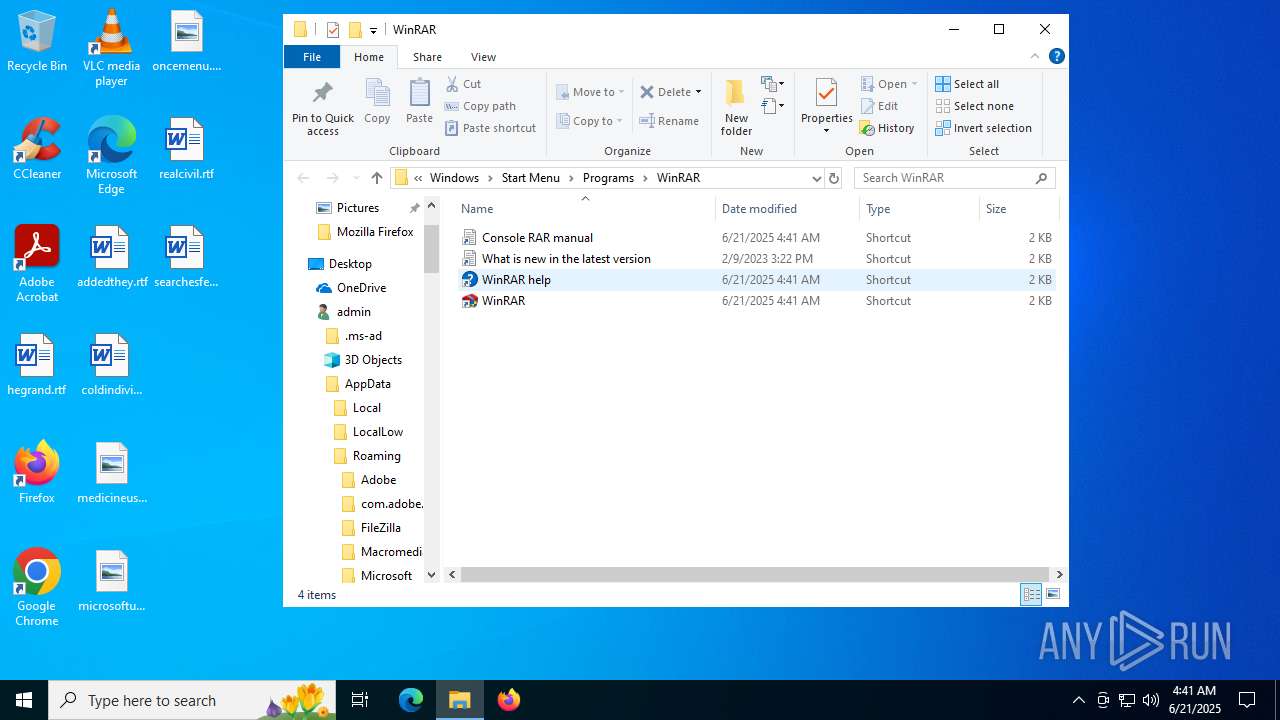
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1480 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2460 | "C:\Program Files (x86)\WinRAR\uninstall.exe" /setup | C:\Program Files (x86)\WinRAR\Uninstall.exe | — | WinRar 4.1.65.exe_.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3716 | "C:\Users\admin\AppData\Local\Temp\WinRar 4.1.65.exe_.exe" | C:\Users\admin\AppData\Local\Temp\WinRar 4.1.65.exe_.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 6684 | "C:\Users\admin\AppData\Local\Temp\WinRar 4.1.65.exe_.exe" | C:\Users\admin\AppData\Local\Temp\WinRar 4.1.65.exe_.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 6700 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 304
Read events
2 109
Write events
139
Delete events
56
Modification events
| (PID) Process: | (3716) WinRar 4.1.65.exe_.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFavoritesInitialSelection |
Value: | |||
| (PID) Process: | (3716) WinRar 4.1.65.exe_.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFeedsInitialSelection |
Value: | |||
| (PID) Process: | (3716) WinRar 4.1.65.exe_.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3716) WinRar 4.1.65.exe_.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3716) WinRar 4.1.65.exe_.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3716) WinRar 4.1.65.exe_.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR SFX |
| Operation: | write | Name: | C%%Program Files (x86)%WinRAR |
Value: C:\Program Files (x86)\WinRAR | |||
| (PID) Process: | (3716) WinRar 4.1.65.exe_.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-500\SOFTWARE\WinRAR SFX |
| Operation: | write | Name: | C%%Program Files%WinRAR |
Value: C:\Program Files\WinRAR | |||
| (PID) Process: | (3716) WinRar 4.1.65.exe_.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-500\SOFTWARE\WinRAR SFX |
| Operation: | write | Name: | C%%Program Files (x86)%WinRAR |
Value: C:\Program Files (x86)\WinRAR | |||
| (PID) Process: | (2460) Uninstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Setup\.rar |
| Operation: | write | Name: | Set |
Value: 1 | |||
| (PID) Process: | (2460) Uninstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Setup\.zip |
| Operation: | write | Name: | Set |
Value: 1 | |||
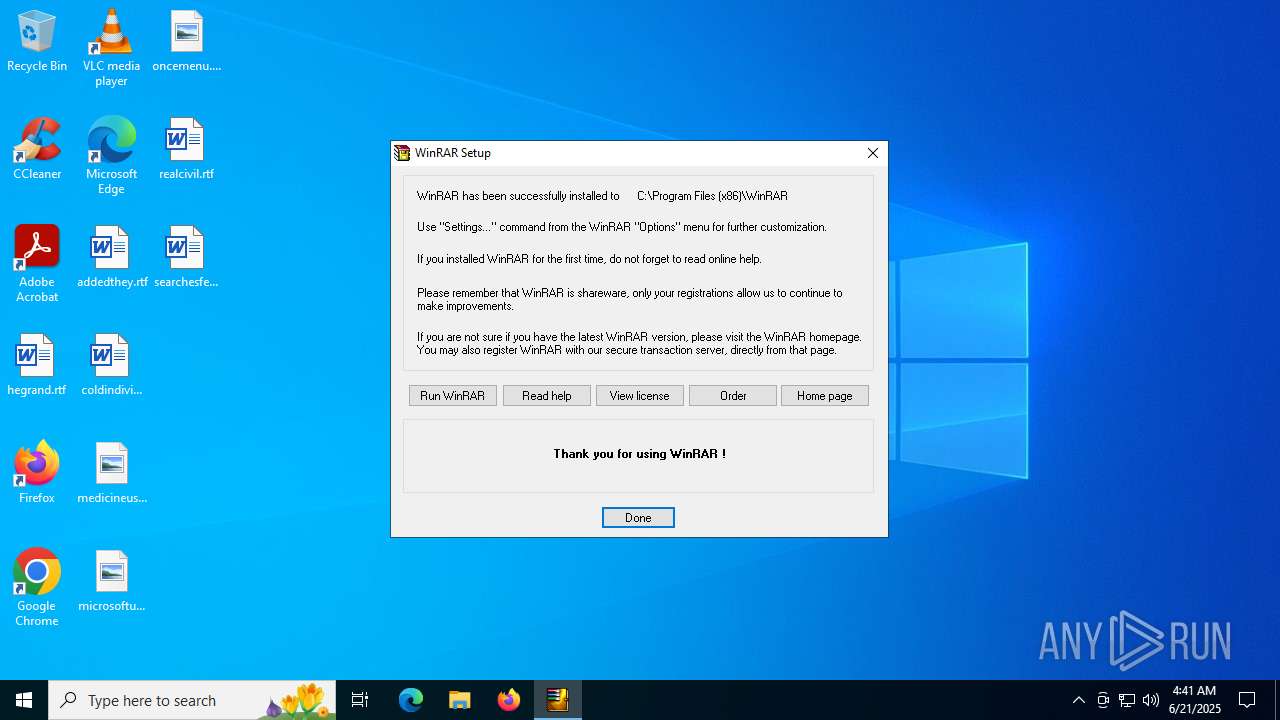
Executable files
24
Suspicious files
9
Text files
13
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3716 | WinRar 4.1.65.exe_.exe | C:\Program Files (x86)\WinRAR\License.txt | text | |
MD5:180F51E019F4477C729C348A76A4D00F | SHA256:A16F9C599E9E3504C92BDEF6BA92FBE0062339A7BF70C57BDA130EC73CA97976 | |||
| 3716 | WinRar 4.1.65.exe_.exe | C:\Program Files (x86)\WinRAR\Order.htm | html | |
MD5:B4475581C5E35D6E813EA5BE995EA457 | SHA256:B27BCAD5B068617CDA66EAA10A0F949F533C563412BCF04614AADA0431F62741 | |||
| 3716 | WinRar 4.1.65.exe_.exe | C:\Program Files (x86)\WinRAR\rarreg.key | text | |
MD5:0E91CB88594EFA20AE6B6A3789075D51 | SHA256:1FA80634C657446E7AFA181028D26C58493BA5837D4AE021419715AB6BBB60DC | |||
| 3716 | WinRar 4.1.65.exe_.exe | C:\Program Files (x86)\WinRAR\Rar.txt | text | |
MD5:1CAD4636F39689BF44C815ACE1E6E57B | SHA256:DAD4D4328E41A69B3CDF5485FAFD2CCA4047F7154E2F211018341874B0264BDC | |||
| 3716 | WinRar 4.1.65.exe_.exe | C:\Program Files (x86)\WinRAR\RarExtLoader.exe | executable | |
MD5:BE2F585891B8FA4DB2AB91ACA1D643EC | SHA256:18246C40E3DA4CEC61DA412B2920B8246E858F60A96E301ABFEA31B4A85687D4 | |||
| 3716 | WinRar 4.1.65.exe_.exe | C:\Program Files (x86)\WinRAR\Uninstall.lst | text | |
MD5:367BB2F0D1C379A4F584DC7BE72AB83A | SHA256:8A7C25A64DB525BCFF43FC928A58667F22E1FB3550DCB9A77910F290AC63AF4E | |||
| 3716 | WinRar 4.1.65.exe_.exe | C:\Program Files (x86)\WinRAR\RarExt.dll | executable | |
MD5:3B42317C8A22B82B04BF8C4E13B27CF0 | SHA256:1D2C9C7354DA1C1D21ABF15B34F1D67280F5DFDC9DE77A2EE903D3229B459F1B | |||
| 3716 | WinRar 4.1.65.exe_.exe | C:\Program Files (x86)\WinRAR\RarExt64.dll | executable | |
MD5:3E5D078EBF7820978331D2A5EA6D0F1D | SHA256:BEC473CFBC7FF7DD21449DC0584B8C279803D312D5EA6EF4F950A92E2A4F5783 | |||
| 3716 | WinRar 4.1.65.exe_.exe | C:\Program Files (x86)\WinRAR\RarFiles.lst | text | |
MD5:0EDE60413958D08E1768EE077658BE45 | SHA256:73E70B464A5572E43382FB33EFAB15EFC2D7EB3F863941A7FF830589397803E5 | |||
| 3716 | WinRar 4.1.65.exe_.exe | C:\Program Files (x86)\WinRAR\UnRAR.exe | executable | |
MD5:E7E15AAEB065E7758141C69105257A98 | SHA256:66591FE3D14E389143014C2BCB6876F35D327AEA6E33FEAB67DC825EE595B376 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
27
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2552 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.24.77.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1700 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 2.23.197.184:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
1700 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5372 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2336 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2552 | svchost.exe | 20.190.160.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2552 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 184.24.77.35:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |