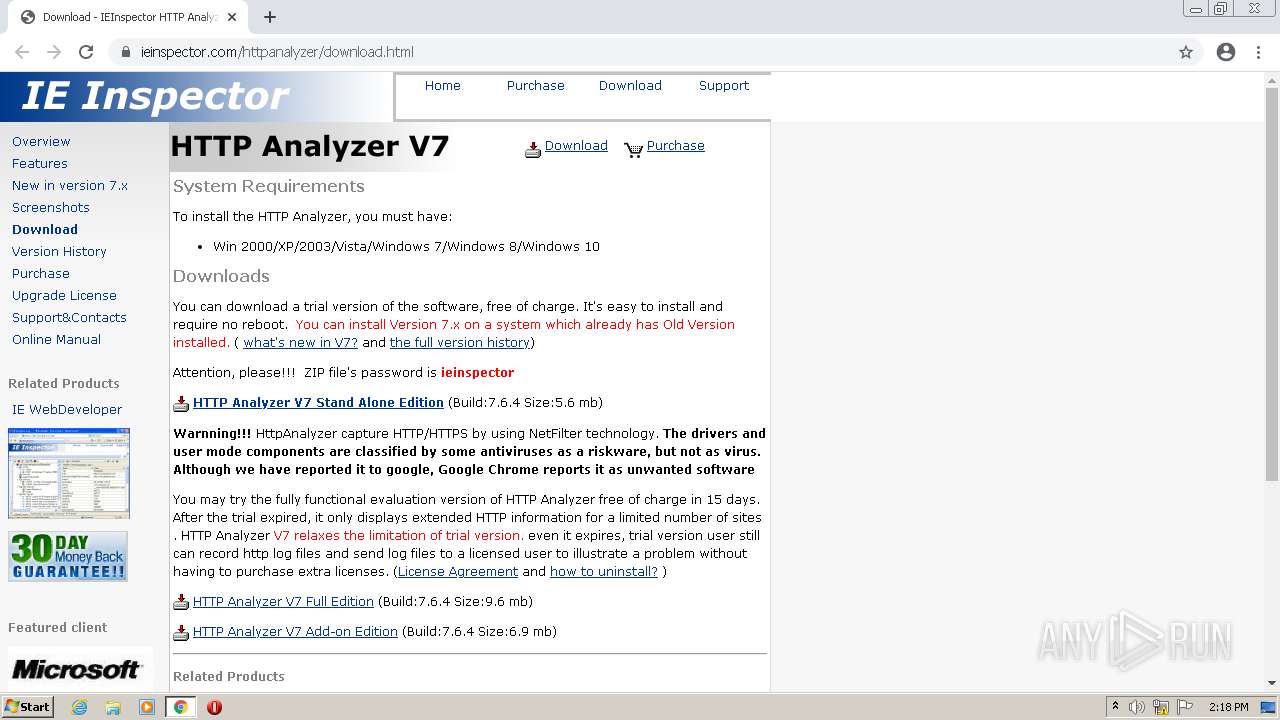
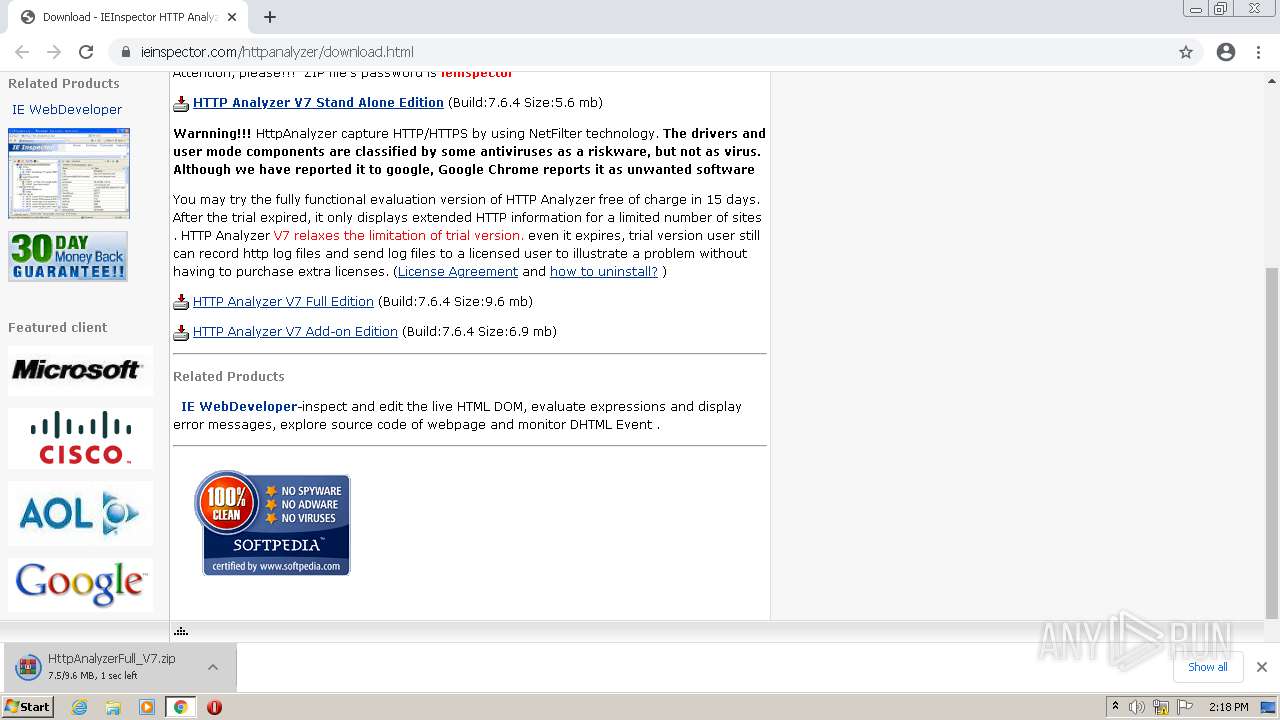
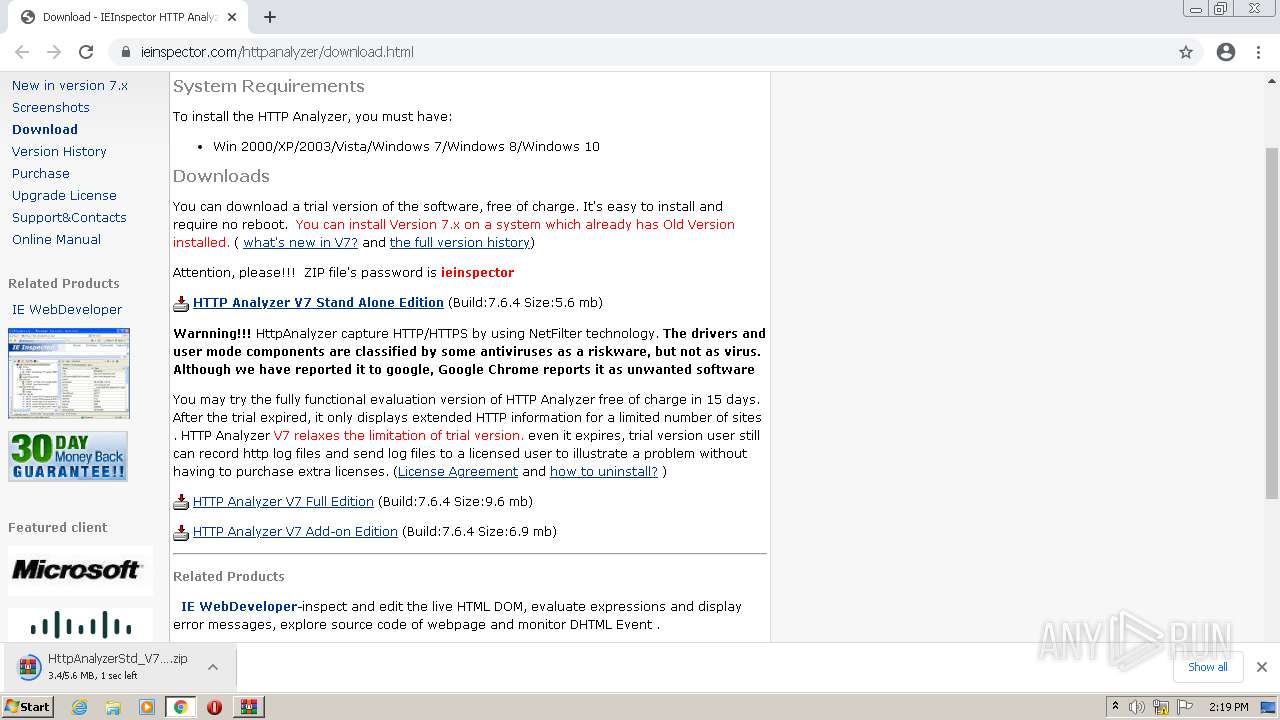
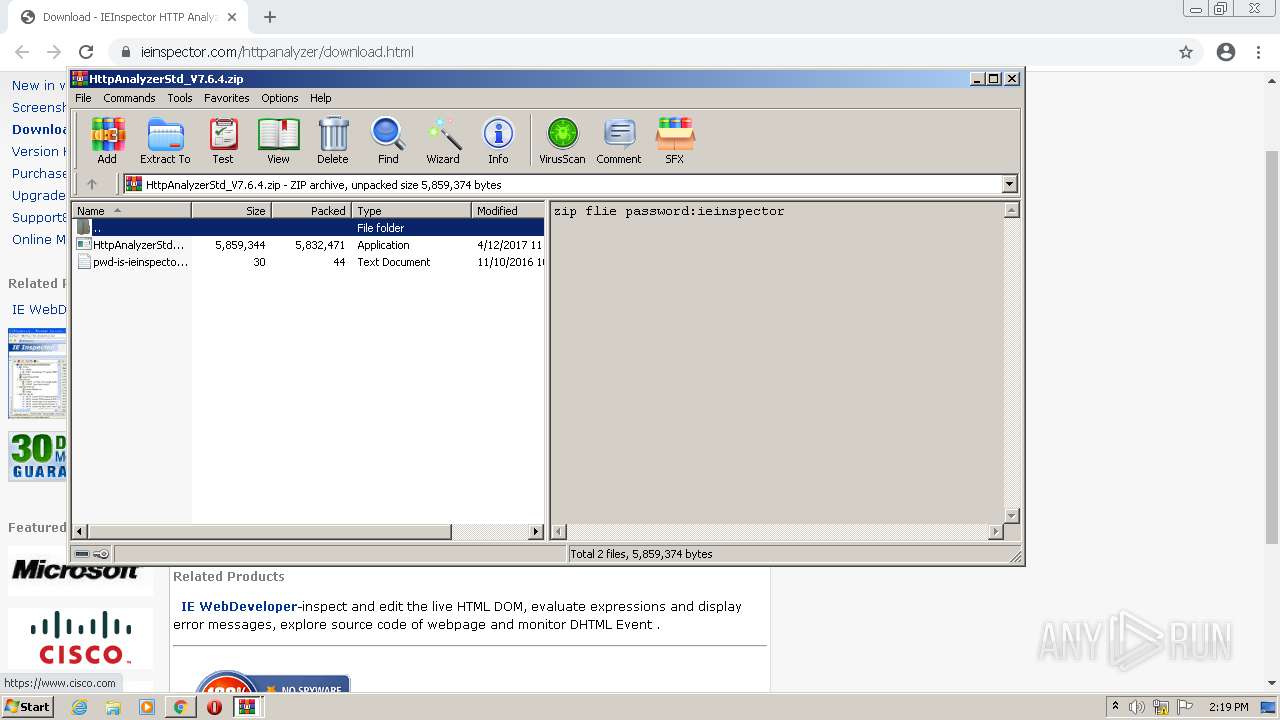
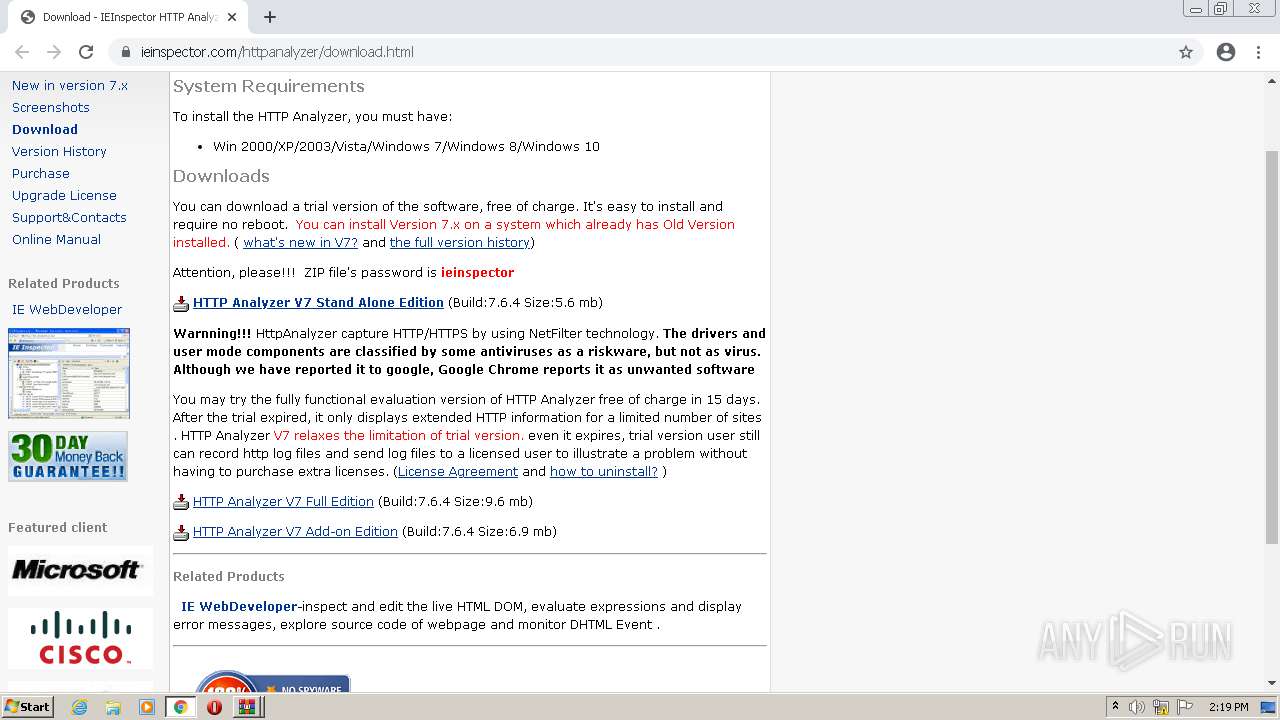
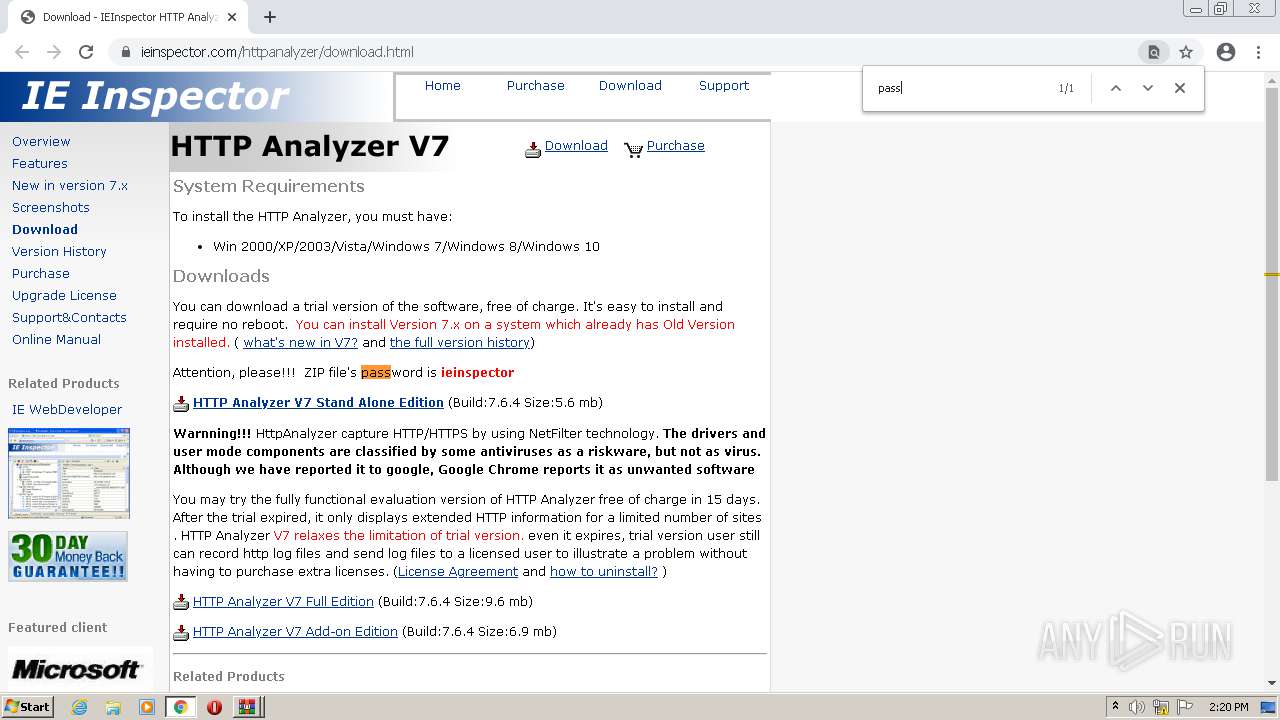
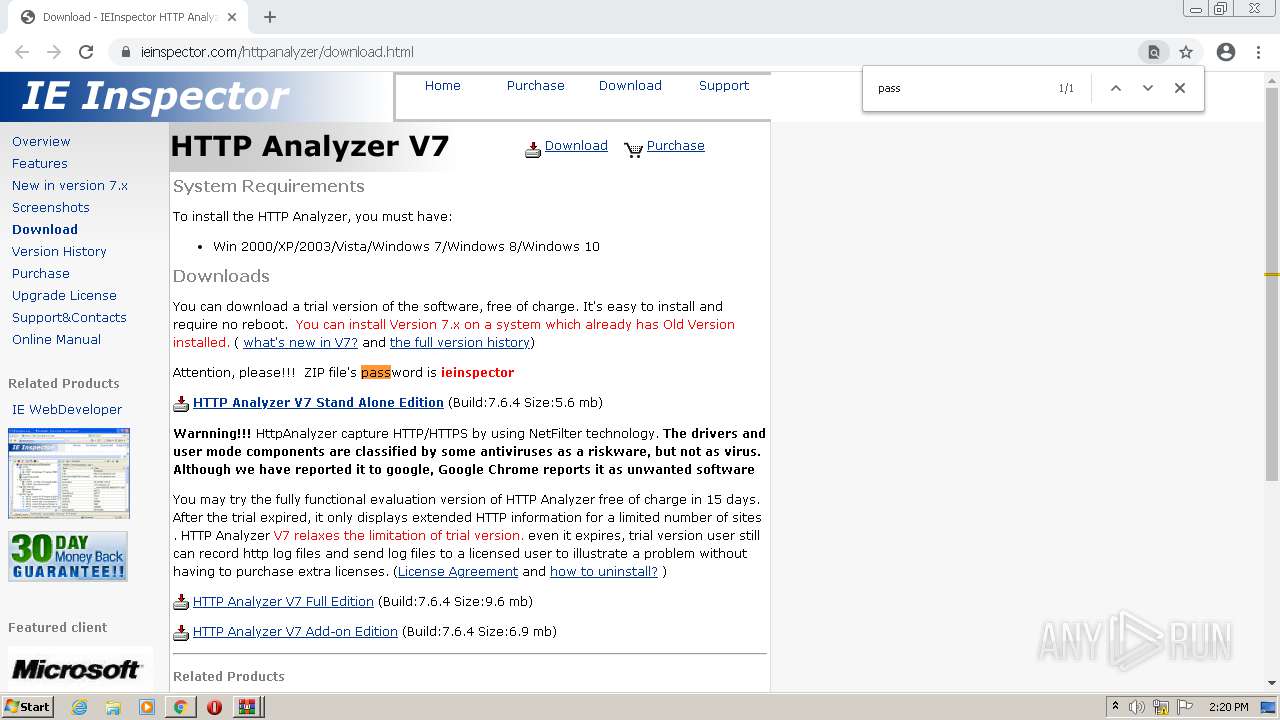
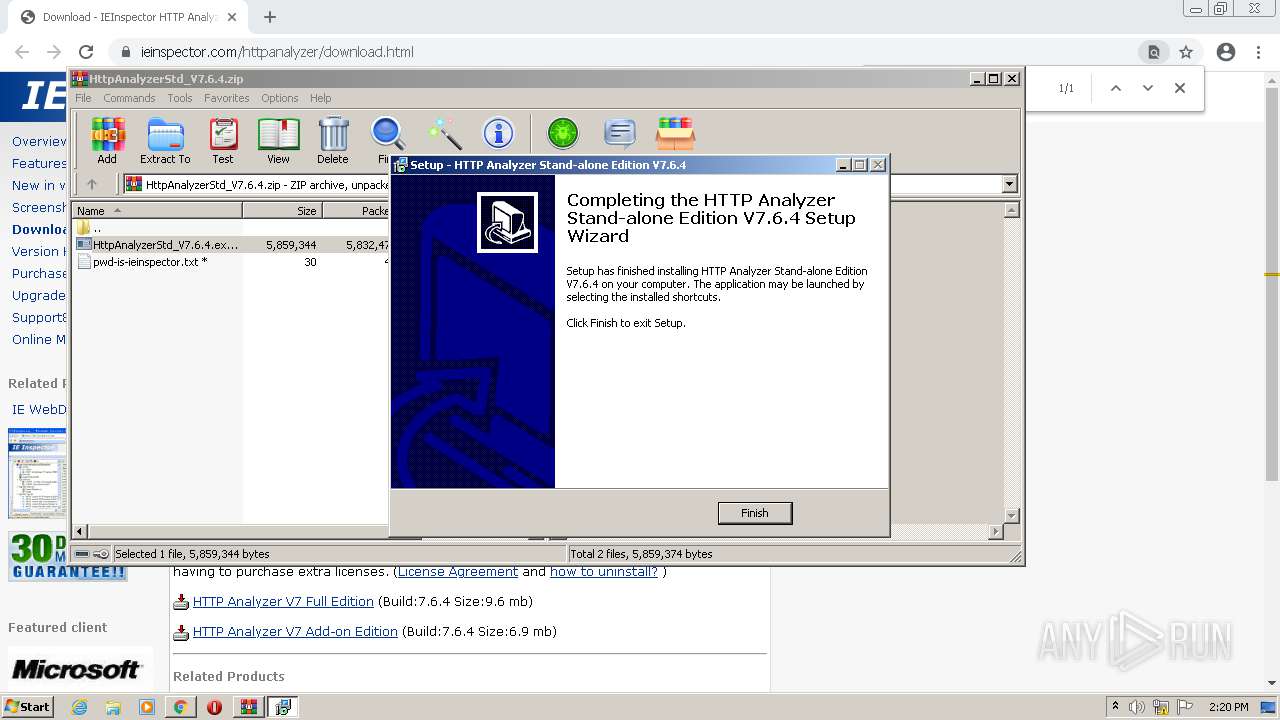
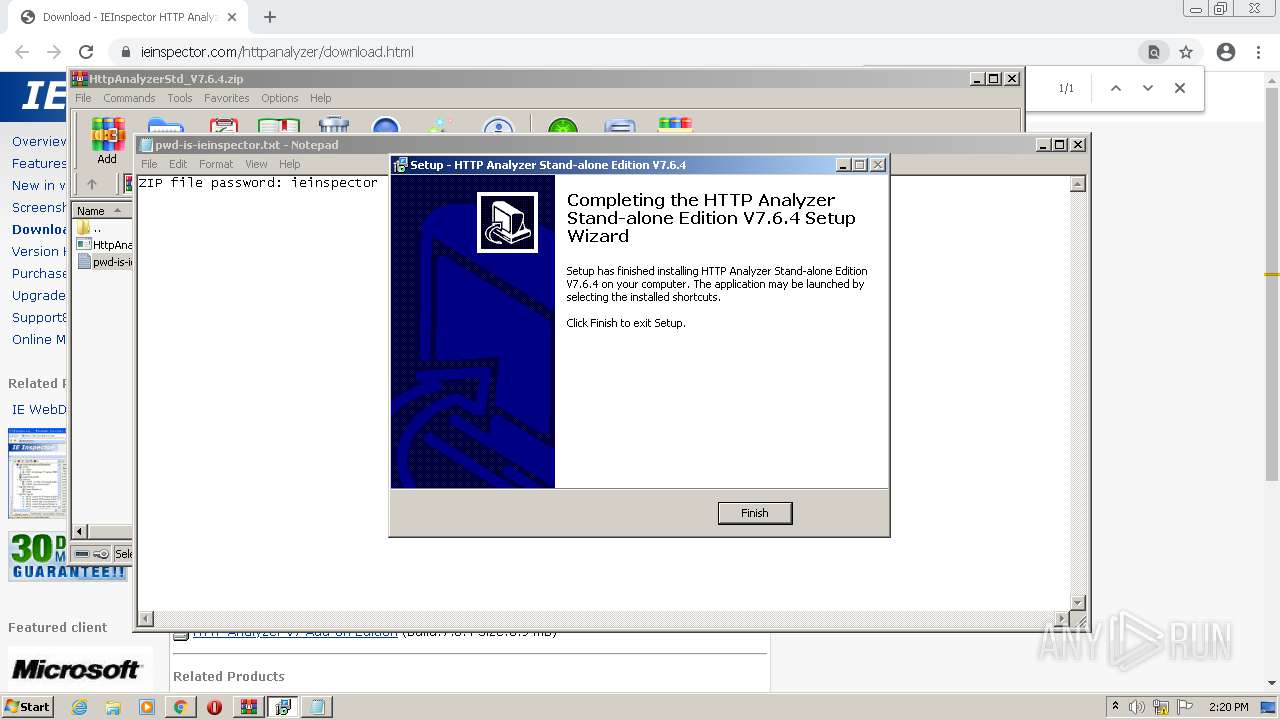
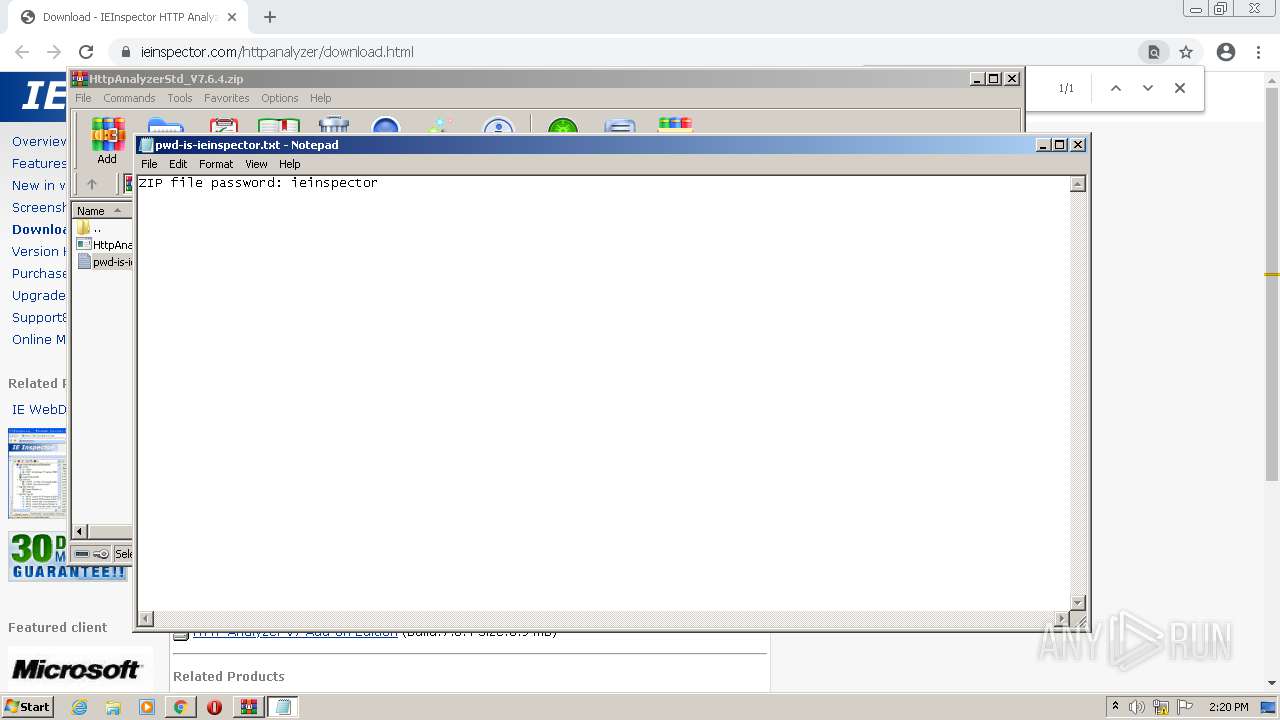
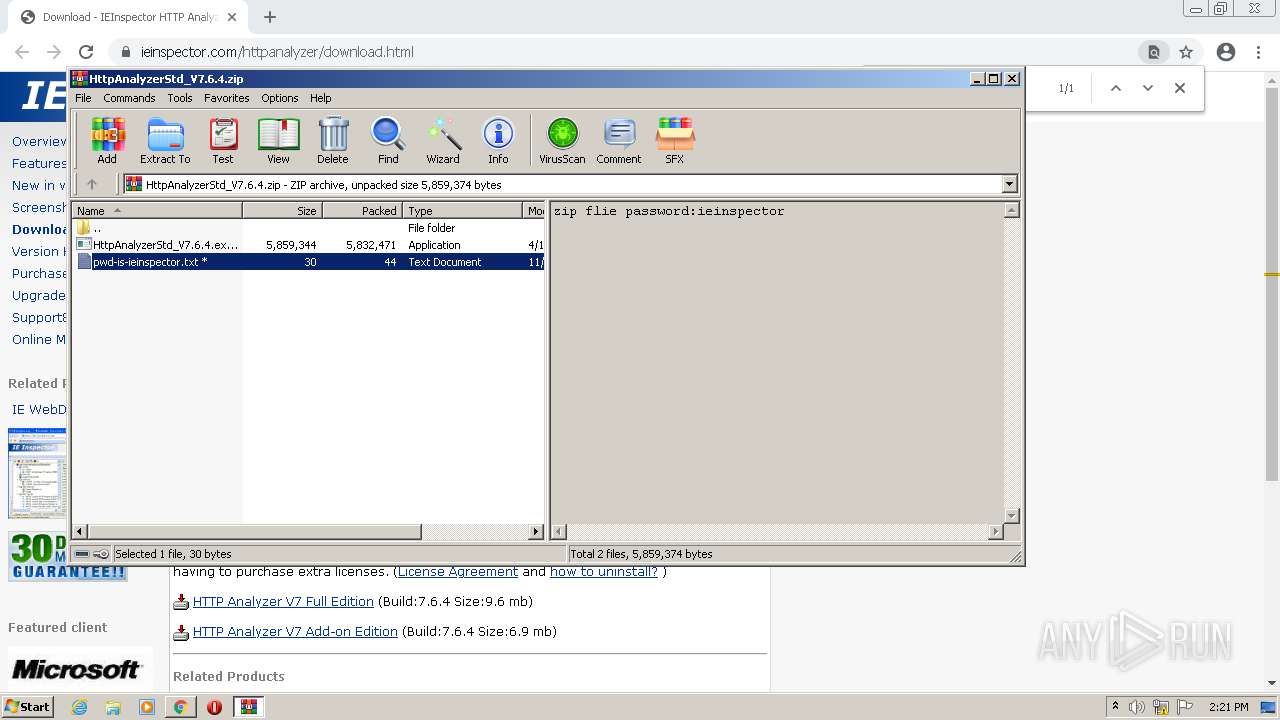
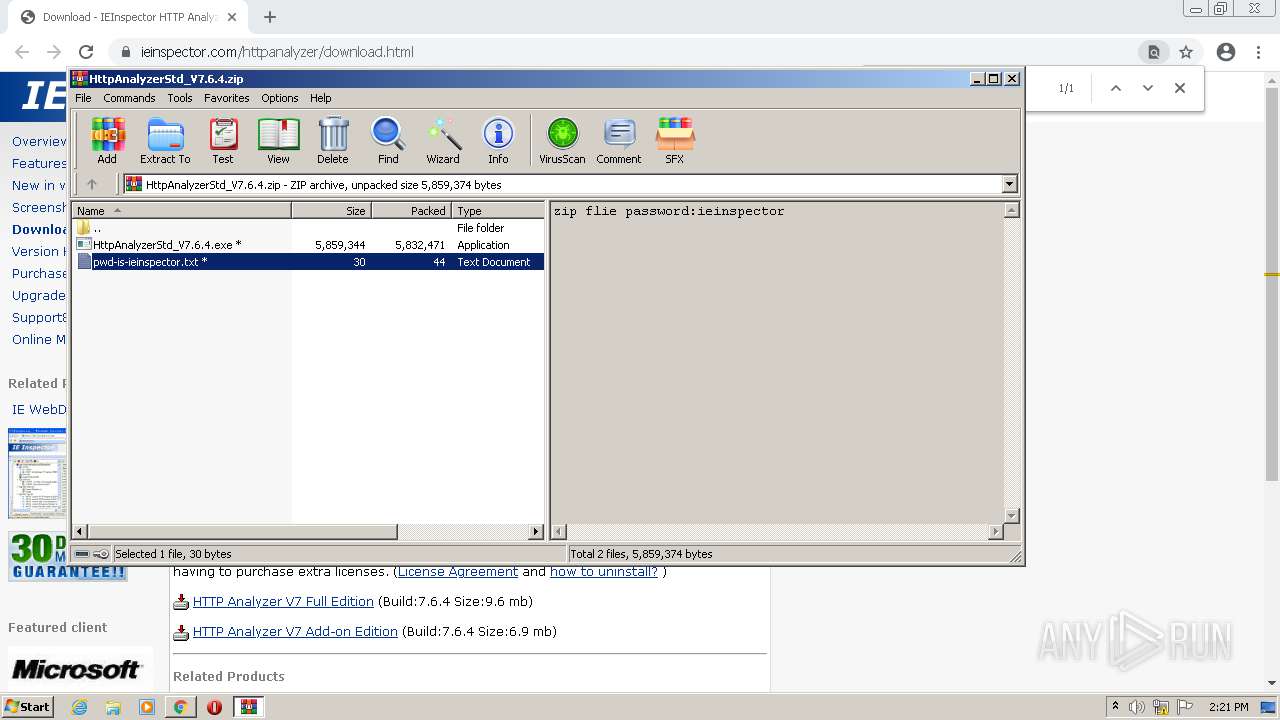
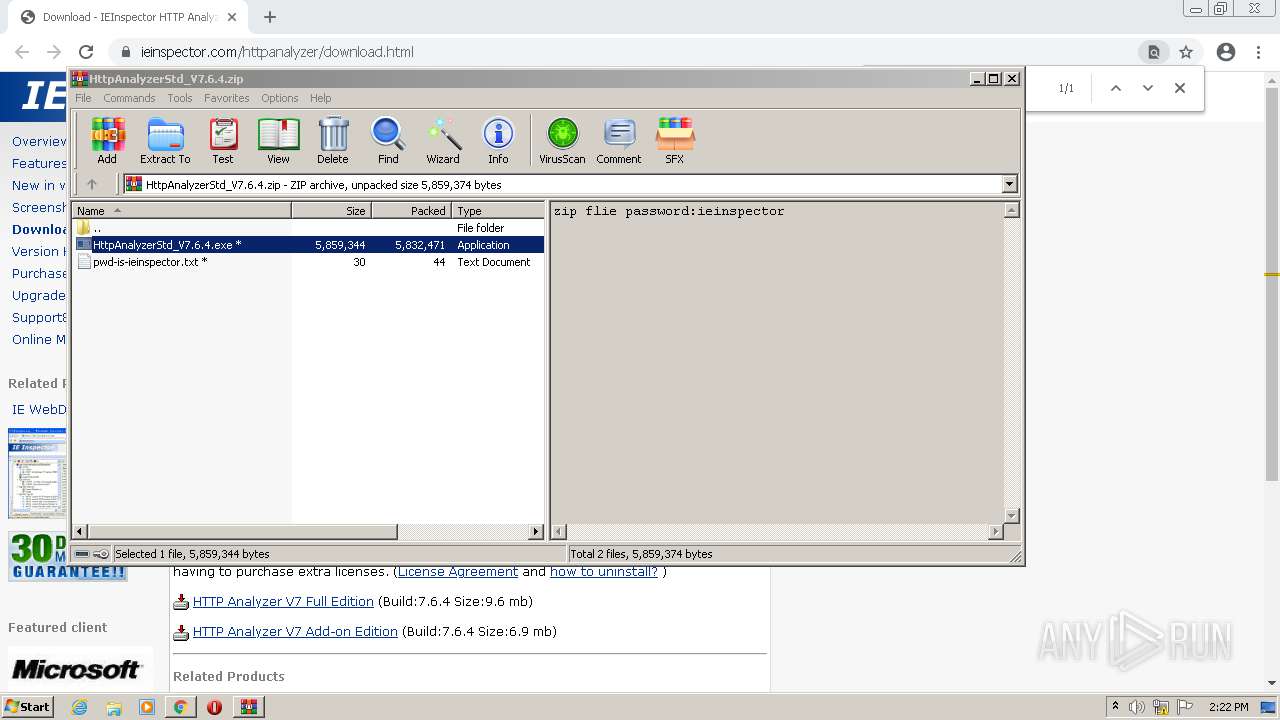
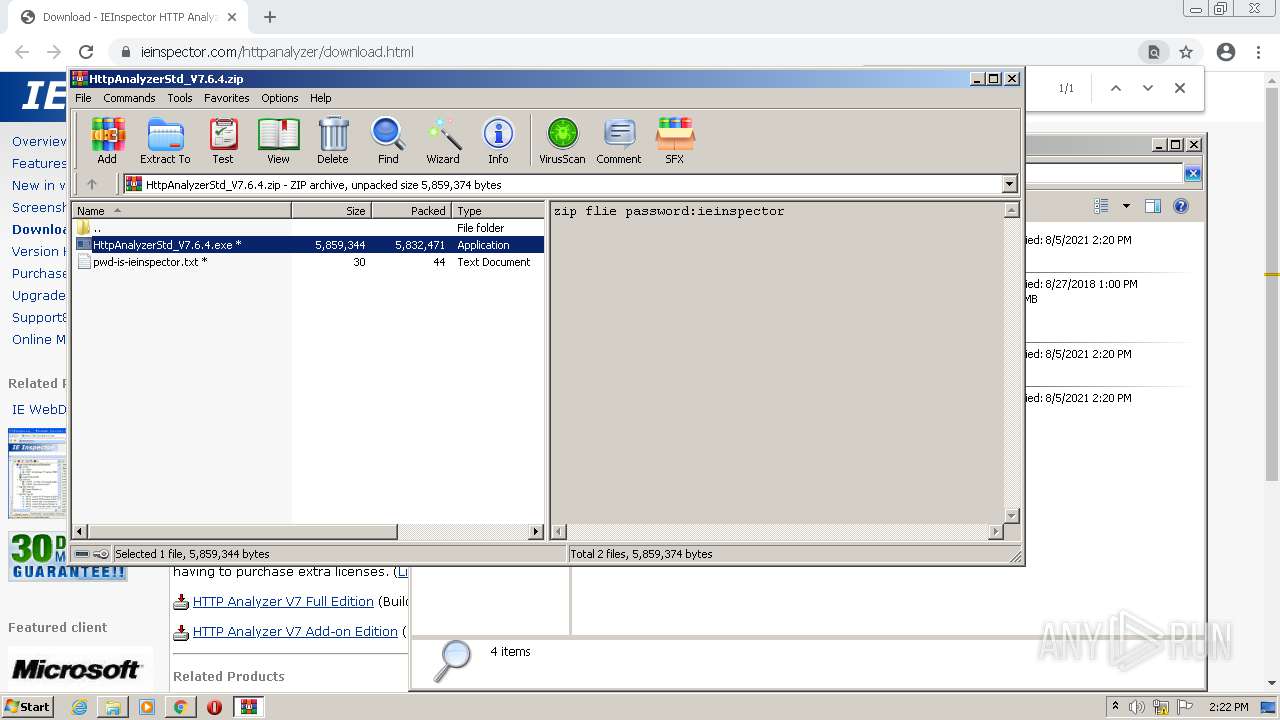
| URL: | https://www.ieinspector.com/httpanalyzer/download.html |
| Full analysis: | https://app.any.run/tasks/caf3c24a-550e-40f8-9a33-b4b28db95237 |
| Verdict: | Malicious activity |
| Analysis date: | August 05, 2021, 13:17:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
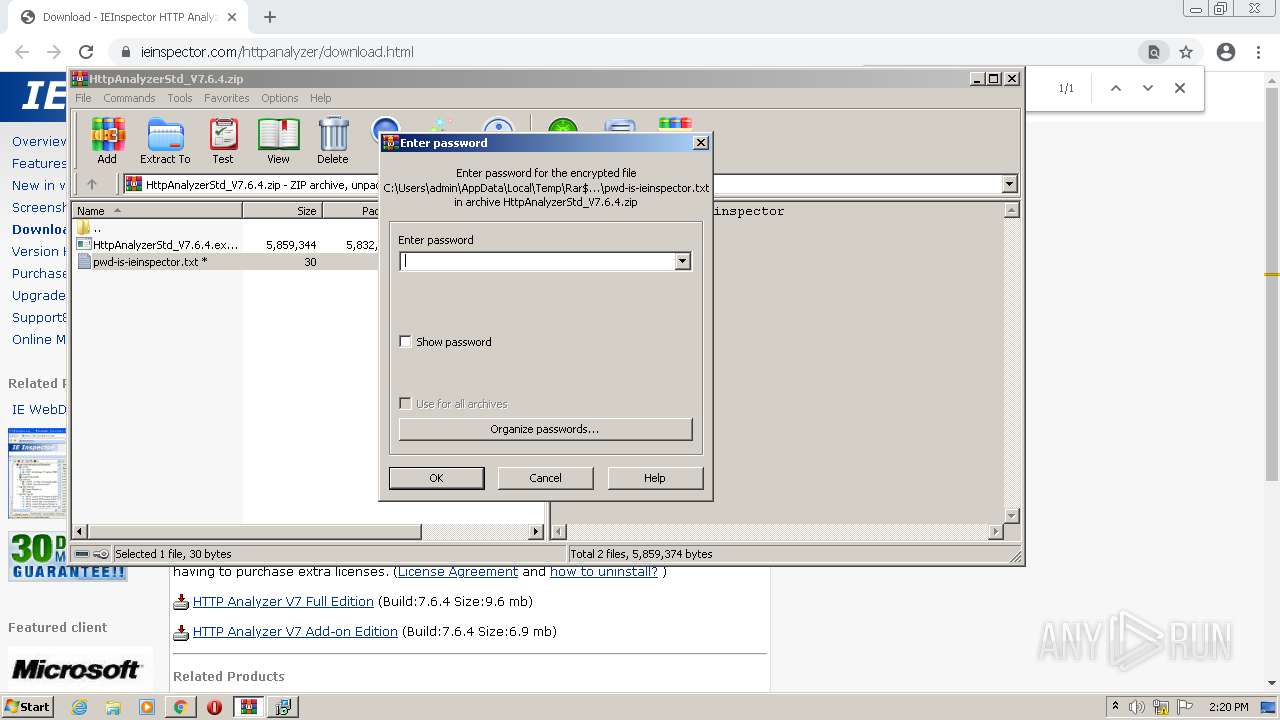
| MD5: | AA77ECF847D6B67FE6114B97EC26833C |
| SHA1: | 3CDEF3BC035D2FFC449A739EC80BA65F7B8F0A0E |
| SHA256: | 727BDB3D8824D2D8BA736E456D5C8D68219047363BD1C0FF8D8A73CBB8D3F77C |
| SSDEEP: | 3:N8DSLEyaWZf/JLJlQ:2OLlvZf/FnQ |
MALICIOUS
Application was dropped or rewritten from another process
- HttpAnalyzerStd_V7.6.4.exe (PID: 2420)
- HttpAnalyzerStd_V7.6.4.exe (PID: 404)
- HttpAnalyzerStdV7.exe (PID: 1300)
- FixPathDataType.exe (PID: 3956)
- nfregdrv.exe (PID: 3176)
- CertMgr.exe (PID: 2696)
- netFilterService.exe (PID: 572)
- netFilterService.exe (PID: 4072)
- HttpAnalyzerStd_V7.6.4.exe (PID: 3768)
- HttpAnalyzerStd_V7.6.4.exe (PID: 1764)
- nfregdrv.exe (PID: 2260)
- CertMgr.exe (PID: 3256)
- FixPathDataType.exe (PID: 3872)
- netFilterService.exe (PID: 276)
- HttpAnalyzerStdV7.exe (PID: 3860)
- HttpAnalyzerStd_V7.6.4.exe (PID: 2760)
- HttpAnalyzerStd_V7.6.4.exe (PID: 4044)
- netFilterService.exe (PID: 2272)
- nfregdrv.exe (PID: 1712)
- FixPathDataType.exe (PID: 2052)
- HttpAnalyzerStdV7.exe (PID: 572)
- netFilterService.exe (PID: 3248)
- CertMgr.exe (PID: 576)
- netFilterService.exe (PID: 476)
Drops executable file immediately after starts
- HttpAnalyzerStd_V7.6.4.exe (PID: 2420)
- HttpAnalyzerStd_V7.6.4.exe (PID: 404)
- HttpAnalyzerStd_V7.6.4.exe (PID: 3768)
- HttpAnalyzerStd_V7.6.4.exe (PID: 1764)
- chrome.exe (PID: 4028)
- HttpAnalyzerStd_V7.6.4.exe (PID: 2760)
- HttpAnalyzerStd_V7.6.4.exe (PID: 4044)
Changes settings of System certificates
- CertMgr.exe (PID: 2696)
- CertMgr.exe (PID: 3256)
- CertMgr.exe (PID: 576)
Loads dropped or rewritten executable
- nfregdrv.exe (PID: 3176)
- netFilterService.exe (PID: 572)
- netFilterService.exe (PID: 4072)
- nfregdrv.exe (PID: 2260)
- netFilterService.exe (PID: 276)
- netFilterService.exe (PID: 2272)
- netFilterService.exe (PID: 3248)
- nfregdrv.exe (PID: 1712)
- netFilterService.exe (PID: 476)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 3524)
- WinRAR.exe (PID: 2500)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 3984)
- HttpAnalyzerStd_V7.6.4.exe (PID: 2420)
- HttpAnalyzerStd_V7.6.4.exe (PID: 404)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 2084)
- CertMgr.exe (PID: 2696)
- nfregdrv.exe (PID: 3176)
- FixPathDataType.exe (PID: 3956)
- netFilterService.exe (PID: 4072)
- HttpAnalyzerStdV7.exe (PID: 1300)
- netFilterService.exe (PID: 572)
- HttpAnalyzerStd_V7.6.4.exe (PID: 3768)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 1996)
- HttpAnalyzerStd_V7.6.4.exe (PID: 1764)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 492)
- CertMgr.exe (PID: 3256)
- nfregdrv.exe (PID: 2260)
- FixPathDataType.exe (PID: 3872)
- netFilterService.exe (PID: 276)
- HttpAnalyzerStd_V7.6.4.exe (PID: 2760)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 2624)
- HttpAnalyzerStdV7.exe (PID: 3860)
- netFilterService.exe (PID: 2272)
- HttpAnalyzerStd_V7.6.4.exe (PID: 4044)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 3144)
- nfregdrv.exe (PID: 1712)
- FixPathDataType.exe (PID: 2052)
- netFilterService.exe (PID: 3248)
- HttpAnalyzerStdV7.exe (PID: 572)
- CertMgr.exe (PID: 576)
- netFilterService.exe (PID: 476)
Reads the computer name
- WinRAR.exe (PID: 3524)
- WinRAR.exe (PID: 2500)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 3984)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 2084)
- nfregdrv.exe (PID: 3176)
- netFilterService.exe (PID: 572)
- netFilterService.exe (PID: 4072)
- HttpAnalyzerStdV7.exe (PID: 1300)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 1996)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 492)
- nfregdrv.exe (PID: 2260)
- netFilterService.exe (PID: 276)
- netFilterService.exe (PID: 2272)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 2624)
- HttpAnalyzerStdV7.exe (PID: 3860)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 3144)
- nfregdrv.exe (PID: 1712)
- netFilterService.exe (PID: 3248)
- HttpAnalyzerStdV7.exe (PID: 572)
- netFilterService.exe (PID: 476)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2500)
- HttpAnalyzerStd_V7.6.4.exe (PID: 404)
- HttpAnalyzerStd_V7.6.4.exe (PID: 2420)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 2084)
- HttpAnalyzerStd_V7.6.4.exe (PID: 3768)
- HttpAnalyzerStd_V7.6.4.exe (PID: 1764)
- chrome.exe (PID: 4028)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 492)
- HttpAnalyzerStd_V7.6.4.exe (PID: 2760)
- HttpAnalyzerStd_V7.6.4.exe (PID: 4044)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 3144)
Drops a file with too old compile date
- WinRAR.exe (PID: 2500)
- HttpAnalyzerStd_V7.6.4.exe (PID: 2420)
- HttpAnalyzerStd_V7.6.4.exe (PID: 404)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 2084)
- HttpAnalyzerStd_V7.6.4.exe (PID: 3768)
- HttpAnalyzerStd_V7.6.4.exe (PID: 1764)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 492)
- HttpAnalyzerStd_V7.6.4.exe (PID: 2760)
- HttpAnalyzerStd_V7.6.4.exe (PID: 4044)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 3144)
Reads Windows owner or organization settings
- HttpAnalyzerStd_V7.6.4.tmp (PID: 2084)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 492)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 3144)
Reads the Windows organization settings
- HttpAnalyzerStd_V7.6.4.tmp (PID: 2084)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 492)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 3144)
Creates a directory in Program Files
- HttpAnalyzerStd_V7.6.4.tmp (PID: 2084)
Creates files in the driver directory
- HttpAnalyzerStd_V7.6.4.tmp (PID: 2084)
Changes default file association
- HttpAnalyzerStd_V7.6.4.tmp (PID: 2084)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 492)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 3144)
Creates/Modifies COM task schedule object
- HttpAnalyzerStd_V7.6.4.tmp (PID: 2084)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 492)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 3144)
Drops a file that was compiled in debug mode
- HttpAnalyzerStd_V7.6.4.tmp (PID: 2084)
- chrome.exe (PID: 4028)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 492)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 3144)
Executed as Windows Service
- netFilterService.exe (PID: 4072)
- netFilterService.exe (PID: 2272)
- netFilterService.exe (PID: 476)
Searches for installed software
- HttpAnalyzerStd_V7.6.4.tmp (PID: 492)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 3144)
Creates files in the Windows directory
- HttpAnalyzerStd_V7.6.4.tmp (PID: 2084)
INFO
Checks supported languages
- chrome.exe (PID: 1212)
- chrome.exe (PID: 2744)
- chrome.exe (PID: 2684)
- chrome.exe (PID: 1004)
- chrome.exe (PID: 1616)
- chrome.exe (PID: 2188)
- chrome.exe (PID: 3520)
- chrome.exe (PID: 908)
- chrome.exe (PID: 4016)
- chrome.exe (PID: 1632)
- chrome.exe (PID: 2260)
- chrome.exe (PID: 3304)
- chrome.exe (PID: 908)
- chrome.exe (PID: 3804)
- chrome.exe (PID: 2232)
- chrome.exe (PID: 2528)
- chrome.exe (PID: 3920)
- chrome.exe (PID: 1100)
- chrome.exe (PID: 2864)
- chrome.exe (PID: 520)
- NOTEPAD.EXE (PID: 3320)
- explorer.exe (PID: 3400)
- chrome.exe (PID: 4028)
Reads the computer name
- chrome.exe (PID: 2188)
- chrome.exe (PID: 1004)
- chrome.exe (PID: 2864)
- chrome.exe (PID: 2744)
- chrome.exe (PID: 4016)
- chrome.exe (PID: 1632)
- chrome.exe (PID: 2260)
- chrome.exe (PID: 3304)
- chrome.exe (PID: 908)
- explorer.exe (PID: 3400)
Reads settings of System Certificates
- chrome.exe (PID: 1004)
- CertMgr.exe (PID: 2696)
- CertMgr.exe (PID: 3256)
- CertMgr.exe (PID: 576)
Application launched itself
- chrome.exe (PID: 2188)
Reads the hosts file
- chrome.exe (PID: 2188)
- chrome.exe (PID: 1004)
Application was dropped or rewritten from another process
- HttpAnalyzerStd_V7.6.4.tmp (PID: 2084)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 3984)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 1996)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 492)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 2624)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 3144)
Reads the date of Windows installation
- chrome.exe (PID: 908)
Creates files in the program directory
- HttpAnalyzerStd_V7.6.4.tmp (PID: 2084)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 492)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 3144)
Creates a software uninstall entry
- HttpAnalyzerStd_V7.6.4.tmp (PID: 2084)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 492)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 3144)
Loads dropped or rewritten executable
- HttpAnalyzerStd_V7.6.4.tmp (PID: 492)
- HttpAnalyzerStd_V7.6.4.tmp (PID: 3144)
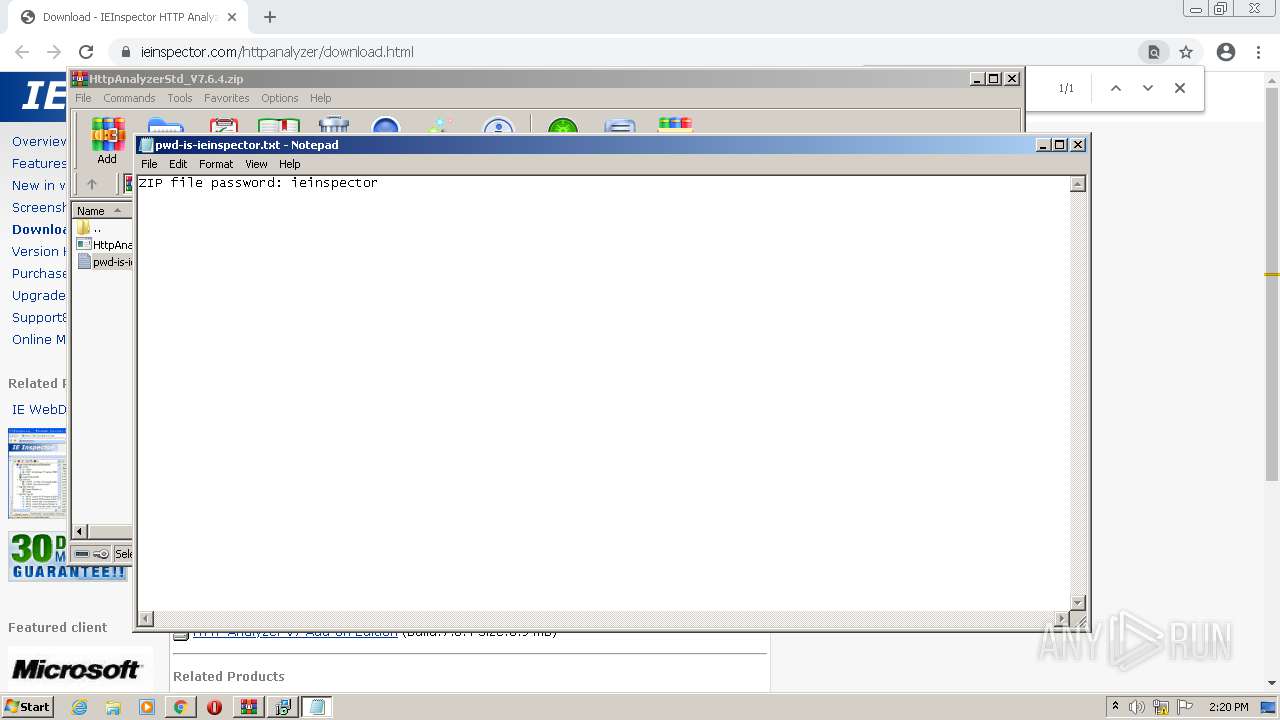
Manual execution by user
- explorer.exe (PID: 3400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
113
Monitored processes
55
Malicious processes
14
Suspicious processes
11
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\Program Files\IEInspector\HTTPAnalyzerStdV7\netFilterService.exe" /Install /Silent | C:\Program Files\IEInspector\HTTPAnalyzerStdV7\netFilterService.exe | — | HttpAnalyzerStd_V7.6.4.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 404 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2500.24879\HttpAnalyzerStd_V7.6.4.exe" /SPAWNWND=$301E8 /NOTIFYWND=$40218 | C:\Users\admin\AppData\Local\Temp\Rar$EXb2500.24879\HttpAnalyzerStd_V7.6.4.exe | HttpAnalyzerStd_V7.6.4.tmp | ||||||||||||
User: admin Company: IEInspector Software Integrity Level: HIGH Description: HTTP Analyzer Std V7.6.4 Exit code: 0 Version: 7.6.4 Modules
| |||||||||||||||
| 476 | "C:\Program Files\IEInspector\HTTPAnalyzerStdV7\netFilterService.exe" | C:\Program Files\IEInspector\HTTPAnalyzerStdV7\netFilterService.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 492 | "C:\Users\admin\AppData\Local\Temp\is-S2ERG.tmp\HttpAnalyzerStd_V7.6.4.tmp" /SL5="$601E8,5600827,57856,C:\Users\admin\AppData\Local\Temp\Rar$EXb2500.35638\HttpAnalyzerStd_V7.6.4.exe" /SPAWNWND=$601EA /NOTIFYWND=$80176 | C:\Users\admin\AppData\Local\Temp\is-S2ERG.tmp\HttpAnalyzerStd_V7.6.4.tmp | HttpAnalyzerStd_V7.6.4.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=976,14332550778998010207,5360752865066377236,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2520 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 572 | "C:\Program Files\IEInspector\HTTPAnalyzerStdV7\netFilterService.exe" /Install /Silent | C:\Program Files\IEInspector\HTTPAnalyzerStdV7\netFilterService.exe | — | HttpAnalyzerStd_V7.6.4.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 572 | "C:\Program Files\IEInspector\HTTPAnalyzerStdV7\HttpAnalyzerStdV7.exe" /regserver | C:\Program Files\IEInspector\HTTPAnalyzerStdV7\HttpAnalyzerStdV7.exe | HttpAnalyzerStd_V7.6.4.tmp | ||||||||||||
User: admin Company: IEInspector Software Integrity Level: HIGH Description: HTTP Analyzer Stand-Alone Edition Exit code: 0 Version: 7.6.4.508 Modules
| |||||||||||||||
| 576 | "C:\Program Files\IEInspector\HTTPAnalyzerStdV7\CertMgr.exe" /add /all /c "C:\ProgramData\IEInspector\HTTPAnalyzerV7\SSL\IEINSPECTOR_CA.cer" /s /r localmachine root | C:\Program Files\IEInspector\HTTPAnalyzerStdV7\CertMgr.exe | — | HttpAnalyzerStd_V7.6.4.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=976,14332550778998010207,5360752865066377236,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3056 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --field-trial-handle=976,14332550778998010207,5360752865066377236,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2764 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
19 360
Read events
18 840
Write events
493
Delete events
27
Modification events
| (PID) Process: | (2188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2188) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2188) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
78
Suspicious files
143
Text files
146
Unknown types
51
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-610BE4FC-88C.pma | — | |
MD5:— | SHA256:— | |||
| 2188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\10c27dcb-f097-4aba-bac1-70dbc37a1053.tmp | text | |
MD5:— | SHA256:— | |||
| 2188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 1212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF10bdb4.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 2188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c49ae944-64c7-4413-9d70-42747c93b108.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF10bda5.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 2188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
31
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
896 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | — | — | whitelisted |
896 | svchost.exe | HEAD | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | — | — | whitelisted |
896 | svchost.exe | HEAD | 200 | 173.194.183.106:80 | http://r5---sn-aigl6nek.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw?cms_redirect=yes&mh=-b&mip=85.203.34.115&mm=28&mn=sn-aigl6nek&ms=nvh&mt=1628168567&mv=u&mvi=5&pl=24&rmhost=r2---sn-aigl6nek.gvt1.com&shardbypass=yes&smhost=r2---sn-aigl6nl7.gvt1.com | US | — | — | whitelisted |
896 | svchost.exe | GET | 206 | 173.194.137.74:80 | http://r5---sn-aigzrn76.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw?cms_redirect=yes&mh=-b&mip=85.203.34.115&mm=28&mn=sn-aigzrn76&ms=nvh&mt=1628168423&mv=m&mvi=5&pl=24&rmhost=r2---sn-aigzrn76.gvt1.com&shardbypass=yes&smhost=r2---sn-aigzrn7e.gvt1.com | US | binary | 5.76 Kb | whitelisted |
896 | svchost.exe | GET | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | html | 549 b | whitelisted |
896 | svchost.exe | GET | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | html | 549 b | whitelisted |
896 | svchost.exe | GET | 206 | 173.194.137.74:80 | http://r5---sn-aigzrn76.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw?cms_redirect=yes&mh=-b&mip=85.203.34.115&mm=28&mn=sn-aigzrn76&ms=nvh&mt=1628168423&mv=m&mvi=5&pl=24&rmhost=r2---sn-aigzrn76.gvt1.com&shardbypass=yes&smhost=r2---sn-aigzrn7e.gvt1.com | US | binary | 15.0 Kb | whitelisted |
896 | svchost.exe | GET | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | html | 549 b | whitelisted |
896 | svchost.exe | GET | 206 | 173.194.137.74:80 | http://r5---sn-aigzrn76.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw?cms_redirect=yes&mh=-b&mip=85.203.34.115&mm=28&mn=sn-aigzrn76&ms=nvh&mt=1628168423&mv=m&mvi=5&pl=24&rmhost=r2---sn-aigzrn76.gvt1.com&shardbypass=yes&smhost=r2---sn-aigzrn7e.gvt1.com | US | binary | 20.6 Kb | whitelisted |
896 | svchost.exe | GET | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | html | 549 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1004 | chrome.exe | 142.250.185.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1004 | chrome.exe | 142.250.184.228:443 | www.google.com | Google Inc. | US | whitelisted |
1004 | chrome.exe | 142.250.186.136:443 | ssl.google-analytics.com | Google Inc. | US | suspicious |
1004 | chrome.exe | 35.190.80.1:443 | a.nel.cloudflare.com | Google Inc. | US | suspicious |
1004 | chrome.exe | 172.67.158.99:443 | www.ieinspector.com | — | US | suspicious |
1004 | chrome.exe | 142.250.185.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
1004 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
1004 | chrome.exe | 142.250.186.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
1004 | chrome.exe | 172.67.158.99:80 | www.ieinspector.com | — | US | suspicious |
896 | svchost.exe | 34.104.35.123:80 | edgedl.me.gvt1.com | — | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.ieinspector.com |
| malicious |
www.google-analytics.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
dns.msftncsi.com |
| shared |
www.google.com |
| malicious |
a.nel.cloudflare.com |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
Process | Message |
|---|---|
HttpAnalyzerStdV7.exe | VCLFixPack patch installed: GetNonToolWindowPopupParentFix |
HttpAnalyzerStdV7.exe | VCLFixPack patch installed: FixTaskModalDialog |
HttpAnalyzerStdV7.exe | VCLFixPack patch installed: AppDeActivateZOrderFix |
HttpAnalyzerStdV7.exe | VCLFixPack patch installed: ControlResizeFix |
HttpAnalyzerStdV7.exe | VCLFixPack patch installed: ActionListAVFix |
HttpAnalyzerStdV7.exe | VCLFixPack patch installed: ContextMenuFix |
HttpAnalyzerStdV7.exe | VCLFixPack patch installed: ObjAutoDEPFix |
HttpAnalyzerStdV7.exe | VCLFixPack patch installed: SysUtilsAbortFix |
HttpAnalyzerStdV7.exe | VCLFixPack patch installed: CmdShowMinimizeFix |
HttpAnalyzerStdV7.exe | VCLFixPack patch installed: MDIChildFocusFix |