| File name: | Setup.exe |
| Full analysis: | https://app.any.run/tasks/d437fd35-6e19-4b1d-a75e-203ce7b5926c |
| Verdict: | No threats detected |
| Analysis date: | August 19, 2025, 17:26:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 11 sections |
| MD5: | 8FCE0655BD3873F6DA958BE5DAB02475 |
| SHA1: | 870F6BA199DB0D7DCA41F834F88C1CC67A9621C4 |
| SHA256: | 7271DC77003741C031505804213718F2D6426A1DFBCD18793E692B4919FE849C |
| SSDEEP: | 98304:pLVIF8P3n1BLHxtD59KEKjSvDxPJ0a0tZilk3QbeEAaz2WhVxE/B668AU0H1xhjb:b2pzt |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- Setup.tmp (PID: 6264)
Reads the Windows owner or organization settings
- Setup.tmp (PID: 4888)
Drops 7-zip archiver for unpacking
- Setup.tmp (PID: 4888)
INFO
Create files in a temporary directory
- Setup.exe (PID: 6376)
- Setup.exe (PID: 1668)
- Setup.tmp (PID: 4888)
Checks supported languages
- Setup.exe (PID: 6376)
- Setup.exe (PID: 1668)
- Setup.tmp (PID: 6264)
- Setup.tmp (PID: 4888)
- 7z.exe (PID: 2356)
- 7z.exe (PID: 6820)
- 7z.exe (PID: 6200)
- 7z.exe (PID: 1496)
Process checks computer location settings
- Setup.tmp (PID: 6264)
Reads the computer name
- Setup.tmp (PID: 6264)
- Setup.exe (PID: 1668)
- Setup.tmp (PID: 4888)
- 7z.exe (PID: 2356)
- 7z.exe (PID: 6820)
- 7z.exe (PID: 6200)
- 7z.exe (PID: 1496)
Reads Environment values
- Setup.exe (PID: 6376)
Creates files in the program directory
- Setup.tmp (PID: 4888)
The sample compiled with english language support
- Setup.tmp (PID: 4888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:05:03 14:45:36+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 704512 |
| InitializedDataSize: | 246272 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xacfe0 |
| OSVersion: | 6.1 |
| ImageVersion: | - |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
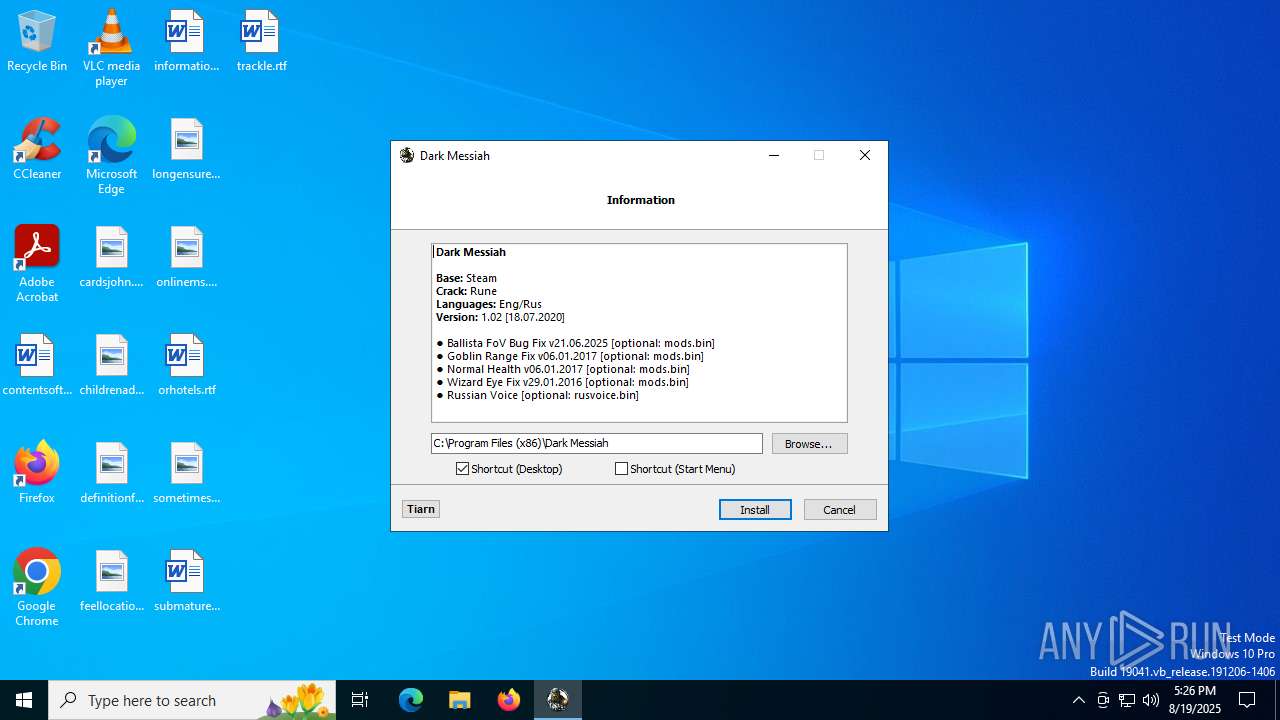
| FileDescription: | Dark Messiah Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | Dark Messiah |
| ProductVersion: | 1.02 |
Total processes
150
Monitored processes
13
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 760 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 7z.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1496 | "C:\Program Files (x86)\Dark Messiah\7z.exe" x "C:\Users\admin\AppData\Local\Temp\rusvoice.bin" -y | C:\Program Files (x86)\Dark Messiah\7z.exe | — | Setup.tmp | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Console Exit code: 2 Version: 25.01 Modules
| |||||||||||||||
| 1668 | "C:\Users\admin\AppData\Local\Temp\Setup.exe" /SPAWNWND=$90356 /NOTIFYWND=$80324 | C:\Users\admin\AppData\Local\Temp\Setup.exe | Setup.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Dark Messiah Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2148 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 7z.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2356 | "C:\Program Files (x86)\Dark Messiah\7z.exe" x "C:\Users\admin\AppData\Local\Temp\data1.bin" -y | C:\Program Files (x86)\Dark Messiah\7z.exe | — | Setup.tmp | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Console Exit code: 2 Version: 25.01 Modules
| |||||||||||||||
| 3628 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4884 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 7z.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4888 | "C:\Users\admin\AppData\Local\Temp\is-71OK2.tmp\Setup.tmp" /SL5="$B0244,1765173,951808,C:\Users\admin\AppData\Local\Temp\Setup.exe" /SPAWNWND=$90356 /NOTIFYWND=$80324 | C:\Users\admin\AppData\Local\Temp\is-71OK2.tmp\Setup.tmp | — | Setup.exe | |||||||||||
User: admin Company: Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 4892 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 7z.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6200 | "C:\Program Files (x86)\Dark Messiah\7z.exe" x "C:\Users\admin\AppData\Local\Temp\mods.bin" -y | C:\Program Files (x86)\Dark Messiah\7z.exe | — | Setup.tmp | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Console Exit code: 2 Version: 25.01 Modules
| |||||||||||||||
Total events
813
Read events
811
Write events
1
Delete events
1
Modification events
| (PID) Process: | (4888) Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\UbiSoft\Dark Messiah of Might and Magic |
| Operation: | write | Name: | mm_gamma_already_set |
Value: 1 | |||
| (PID) Process: | (4888) Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Keyboard Layouts\0000040c |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
7
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1668 | Setup.exe | C:\Users\admin\AppData\Local\Temp\is-71OK2.tmp\Setup.tmp | executable | |
MD5:E9635B047BB844D0BC2E5B76250FAEDC | SHA256:32685B0C5C350F3504B3E8020BF782A0FF47DC2CA650B4DF4AB87C6F44F2BCBB | |||
| 4888 | Setup.tmp | C:\Program Files (x86)\Dark Messiah\7z.dll | executable | |
MD5:043204DFAB6C5038C07DE8DE5186D122 | SHA256:5BD20FB38499D95C39594F41D4781B6181B3304B7F1F4D06B0182F514E7EAA74 | |||
| 4888 | Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-PVL10.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 4888 | Setup.tmp | C:\Program Files (x86)\Dark Messiah\is-9GH8J.tmp | executable | |
MD5:CDCD6DD1E369E47103FA3E37027A5B48 | SHA256:4CD7D776C686427226A151789D2D61F0B2ED2C392148CC4E69C0238362FAFECF | |||
| 6376 | Setup.exe | C:\Users\admin\AppData\Local\Temp\is-I18DL.tmp\Setup.tmp | executable | |
MD5:E9635B047BB844D0BC2E5B76250FAEDC | SHA256:32685B0C5C350F3504B3E8020BF782A0FF47DC2CA650B4DF4AB87C6F44F2BCBB | |||
| 4888 | Setup.tmp | C:\Program Files (x86)\Dark Messiah\7z.exe | executable | |
MD5:CDCD6DD1E369E47103FA3E37027A5B48 | SHA256:4CD7D776C686427226A151789D2D61F0B2ED2C392148CC4E69C0238362FAFECF | |||
| 4888 | Setup.tmp | C:\Program Files (x86)\Dark Messiah\is-NGC8S.tmp | executable | |
MD5:043204DFAB6C5038C07DE8DE5186D122 | SHA256:5BD20FB38499D95C39594F41D4781B6181B3304B7F1F4D06B0182F514E7EAA74 | |||
| 4888 | Setup.tmp | C:\Users\admin\Desktop\Dark Messiah.lnk | binary | |
MD5:F0913CB2429030DFB51EFAE70A0739E6 | SHA256:12EFFE998BAE949E7208DAF278872954B55DF9054F99E7AFC7510401D079A712 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
23
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4800 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
3780 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.26:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
4800 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 420 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
236 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3780 | svchost.exe | 40.126.31.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3780 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 23.216.77.26:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |