| File name: | 02322339 |
| Full analysis: | https://app.any.run/tasks/c101ea73-5d61-44e2-a7f7-cb6dbd22c325 |
| Verdict: | Malicious activity |
| Analysis date: | November 30, 2020, 01:10:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 27C602206E8D540F144CCD5BCC72A8D9 |
| SHA1: | 94868B2C2848C20F2CB80EF1D824E0C33882F0A4 |
| SHA256: | 725EE98B90CEF2006B8DA27432326EAEA2FD498B42A995C530EF55706808C362 |
| SSDEEP: | 98304:z/CYwfS5SwIIyn5P3Nkdkf/5omTQu+5dEQZ04WO81uT7q:9w65SOS5P3NkyH58uSZ04WO8C7q |
MALICIOUS
Loads dropped or rewritten executable
- 02322339.exe (PID: 2844)
SUSPICIOUS
Changes IE settings (feature browser emulation)
- 02322339.exe (PID: 2844)
- sjtl.exe (PID: 1028)
Drops a file that was compiled in debug mode
- 02322339.exe (PID: 2844)
Creates files in the user directory
- 02322339.exe (PID: 2844)
Executable content was dropped or overwritten
- 02322339.exe (PID: 2844)
Starts itself from another location
- 02322339.exe (PID: 2844)
Creates a software uninstall entry
- 02322339.exe (PID: 2844)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (3.6) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:07:08 13:48:37+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 937472 |
| InitializedDataSize: | 2417664 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa05ba |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.40.708 |
| ProductVersionNumber: | 2.2.40.708 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileDescription: | 银杏村传说 |
| FileVersion: | 2.1.40.708 |
| LegalCopyright: | 版权所有 游龙科技 |
| ProductName: | 银杏村传说 |
| ProductVersion: | 2.1.40.708 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Jul-2020 11:48:37 |
| Detected languages: |
|
| Debug artifacts: |
|
| FileDescription: | 银杏村传说 |
| FileVersion: | 2.1.40.708 |
| LegalCopyright: | 版权所有 游龙科技 |
| ProductName: | 银杏村传说 |
| ProductVersion: | 2.1.40.708 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000158 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 08-Jul-2020 11:48:37 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000E4CFB | 0x000E4E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57389 |
.rdata | 0x000E6000 | 0x0003A956 | 0x0003AA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18804 |
.data | 0x00121000 | 0x000095DC | 0x00006400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.73585 |
.rsrc | 0x0012B000 | 0x001FF3EE | 0x001FF400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.94986 |
.reloc | 0x0032B000 | 0x0000E0DC | 0x0000E200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.55238 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.3298 | 822 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 6.41134 | 4264 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 6.5878 | 2440 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
4 | 6.21113 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
8 | 2.05573 | 52 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
9 | 0.833805 | 40 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
121 | 2.62308 | 62 | Latin 1 / Western European | Chinese - PRC | RT_GROUP_ICON |
126 | 7.99779 | 1827678 | Latin 1 / Western European | Chinese - PRC | ZIPRES |
131 | 6.75271 | 245560 | Latin 1 / Western European | Chinese - PRC | FILERES |
141 | 5.2547 | 1087 | Latin 1 / Western European | Chinese - PRC | FILERES |
Imports
ADVAPI32.dll |
COMCTL32.dll |
CRYPT32.dll |
GDI32.dll |
IMM32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MSIMG32.dll |
OLEAUT32.dll |
PSAPI.DLL |
Total processes
36
Monitored processes
2
Malicious processes
1
Suspicious processes
0
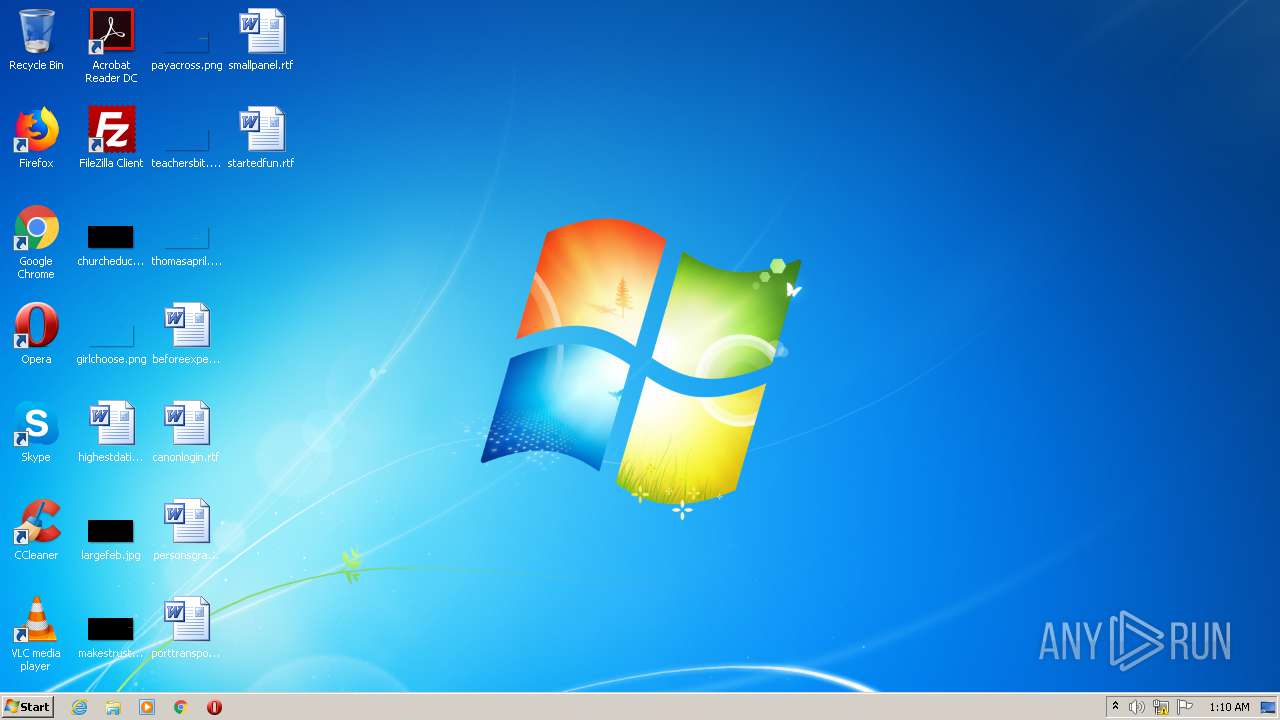
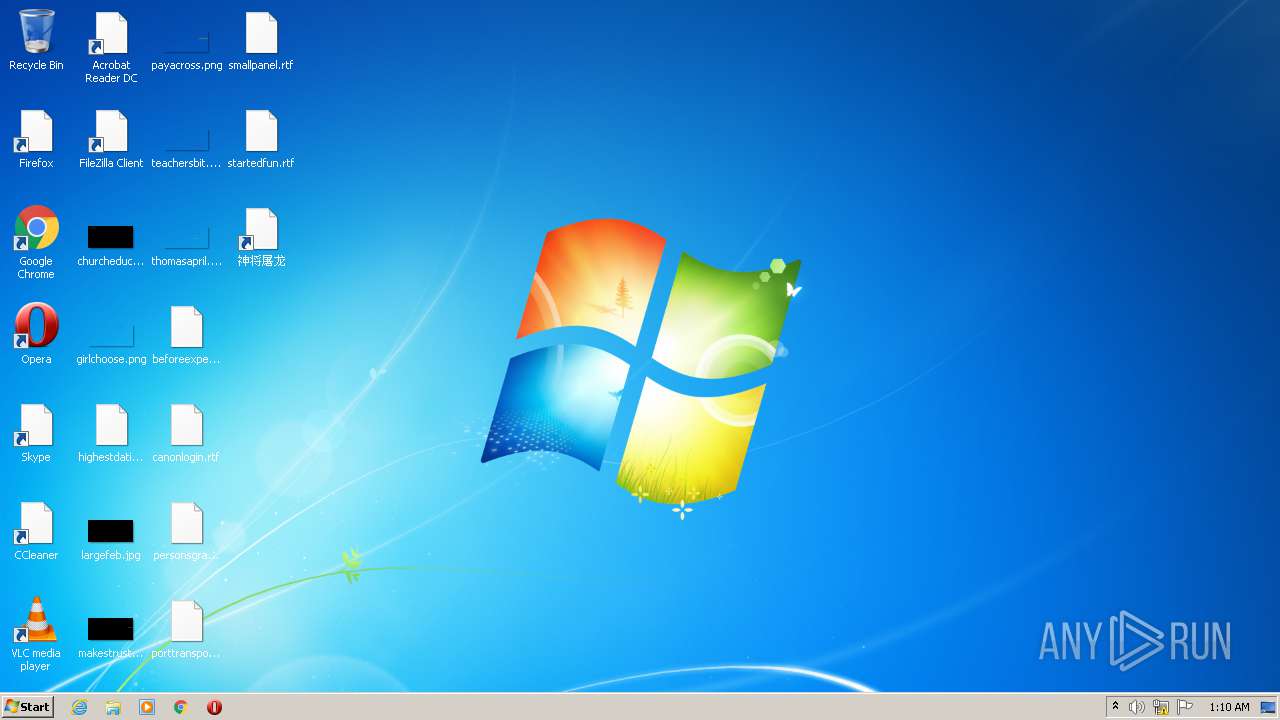
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1028 | "C:\Users\admin\AppData\Roaming\LiteGameBox_sjtl\sjtl.exe" | C:\Users\admin\AppData\Roaming\LiteGameBox_sjtl\sjtl.exe | 02322339.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: 银杏村传说 Exit code: 0 Version: 2.1.40.708 Modules
| |||||||||||||||
| 2844 | "C:\Users\admin\AppData\Local\Temp\02322339.exe" | C:\Users\admin\AppData\Local\Temp\02322339.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: 银杏村传说 Exit code: 0 Version: 2.1.40.708 Modules
| |||||||||||||||
Total events
493
Read events
439
Write events
54
Delete events
0
Modification events
| (PID) Process: | (2844) 02322339.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | 02322339.exe |
Value: 11001 | |||
| (PID) Process: | (2844) 02322339.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2844) 02322339.exe | Key: | HKEY_CURRENT_USER\Software\LDSLiteGameBox\sjtl |
| Operation: | write | Name: | InstallDir |
Value: C:\Users\admin\AppData\Roaming\LiteGameBox_sjtl | |||
| (PID) Process: | (2844) 02322339.exe | Key: | HKEY_CURRENT_USER\Software\LDSLiteGameBox\sjtl |
| Operation: | write | Name: | InstallTime |
Value: 2020-11-30 01:10:57 | |||
| (PID) Process: | (2844) 02322339.exe | Key: | HKEY_CURRENT_USER\Software\LDSLiteGameBox\sjtl |
| Operation: | write | Name: | ExePath |
Value: C:\Users\admin\AppData\Roaming\LiteGameBox_sjtl\sjtl.exe | |||
| (PID) Process: | (2844) 02322339.exe | Key: | HKEY_CURRENT_USER\Software\LDSLiteGameBox\sjtl |
| Operation: | write | Name: | DisplayName |
Value: 神将屠龙 | |||
| (PID) Process: | (2844) 02322339.exe | Key: | HKEY_CURRENT_USER\Software\LDSLiteGameBox\sjtl |
| Operation: | write | Name: | Version |
Value: 2.2.40.708 | |||
| (PID) Process: | (2844) 02322339.exe | Key: | HKEY_CURRENT_USER\Software\LDSLiteGameBox\sjtl |
| Operation: | write | Name: | PID |
Value: lds | |||
| (PID) Process: | (2844) 02322339.exe | Key: | HKEY_CURRENT_USER\Software\LDSLiteGameBox\sjtl |
| Operation: | write | Name: | SubPID |
Value: lds | |||
| (PID) Process: | (2844) 02322339.exe | Key: | HKEY_CURRENT_USER\Software\LDSLiteGameBox\sjtl |
| Operation: | write | Name: | Channel |
Value: lds | |||
Executable files
3
Suspicious files
3
Text files
3
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2844 | 02322339.exe | C:\Users\admin\AppData\Roaming\LiteGameBox_sjtl\sjtl.ui | compressed | |
MD5:— | SHA256:— | |||
| 2844 | 02322339.exe | C:\Users\admin\AppData\Local\Temp\LiteGameBox_sjtl\sjtl.ui | compressed | |
MD5:— | SHA256:— | |||
| 2844 | 02322339.exe | C:\Users\admin\AppData\Roaming\LiteGameBox_sjtl\sjtl.json | text | |
MD5:— | SHA256:— | |||
| 2844 | 02322339.exe | C:\Users\admin\AppData\Roaming\LiteGameBox_sjtl\神将屠龙.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2844 | 02322339.exe | C:\Users\admin\AppData\Roaming\LiteGameBox_sjtl\sjtl.exe | executable | |
MD5:— | SHA256:— | |||
| 1028 | sjtl.exe | C:\Users\admin\AppData\Local\Temp\LiteGameBox2Run_sjtl\sjtl.ui | compressed | |
MD5:— | SHA256:— | |||
| 2844 | 02322339.exe | C:\Users\admin\Desktop\神将屠龙.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2844 | 02322339.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\神将屠龙\神将屠龙.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2844 | 02322339.exe | C:\Users\admin\AppData\Roaming\LiteGameBox_sjtl\NetBridge.dll | executable | |
MD5:8831F7909DB45F47B721A9CD60E6A28D | SHA256:CBF87BFCC410374B15CA60D9CBA2A7CCD4800BD0C0F9CDBB399C48E4D21B1C07 | |||
| 2844 | 02322339.exe | C:\Users\admin\AppData\Roaming\LiteGameBox_sjtl\sjtl.ico | image | |
MD5:9A914EE58297174A0CD62C61EA92963E | SHA256:B291CF26AF907A503D24E75BA381A5D75F6469F84184D06183D61DA0E54C6412 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1028 | sjtl.exe | GET | — | 139.129.105.182:80 | http://wan.ludashi.com/micro/sjtl/index_lds.html?channel=taskpop&from=taskpop_sjtl_wd_az | CN | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1028 | sjtl.exe | 139.129.105.182:80 | wan.ludashi.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wan.ludashi.com |
| unknown |