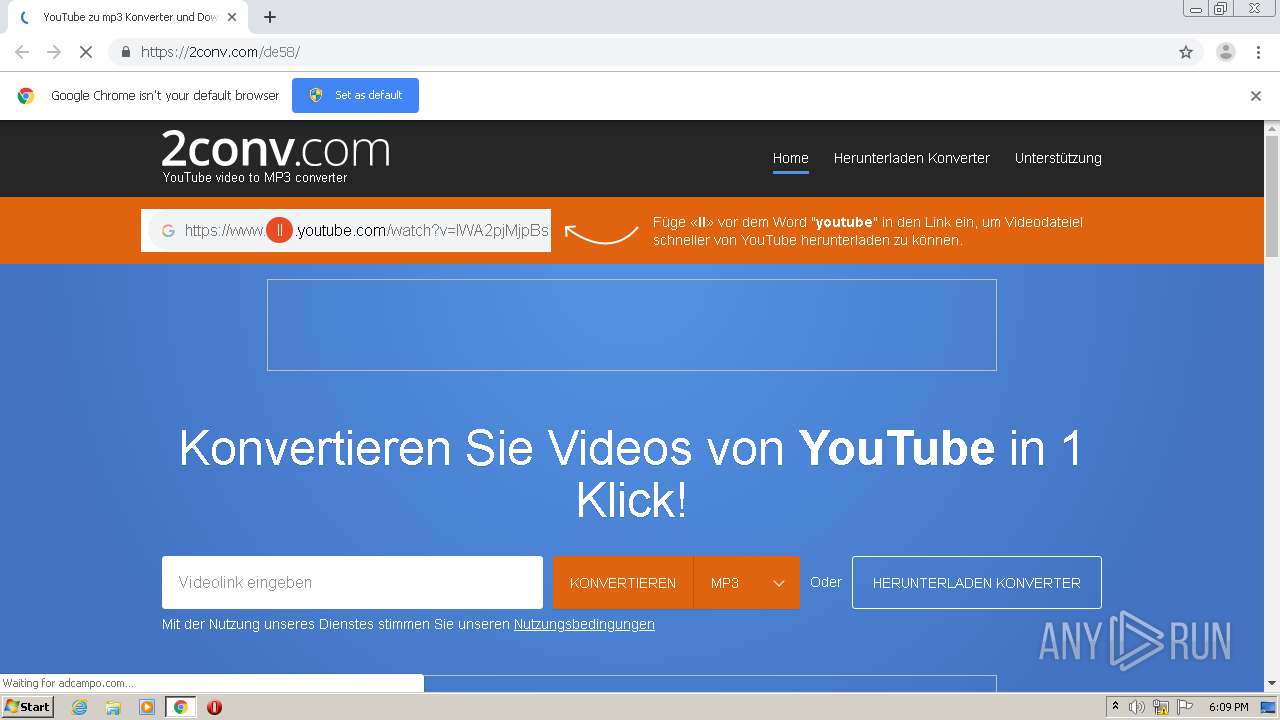
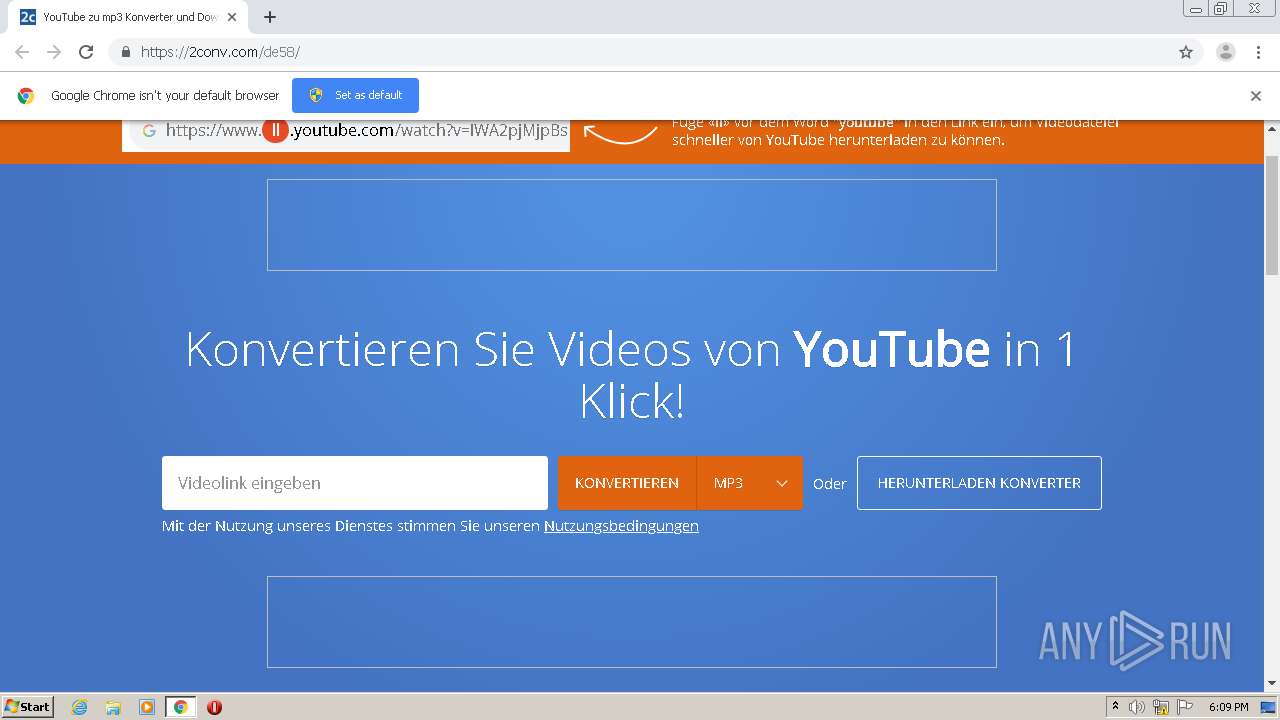
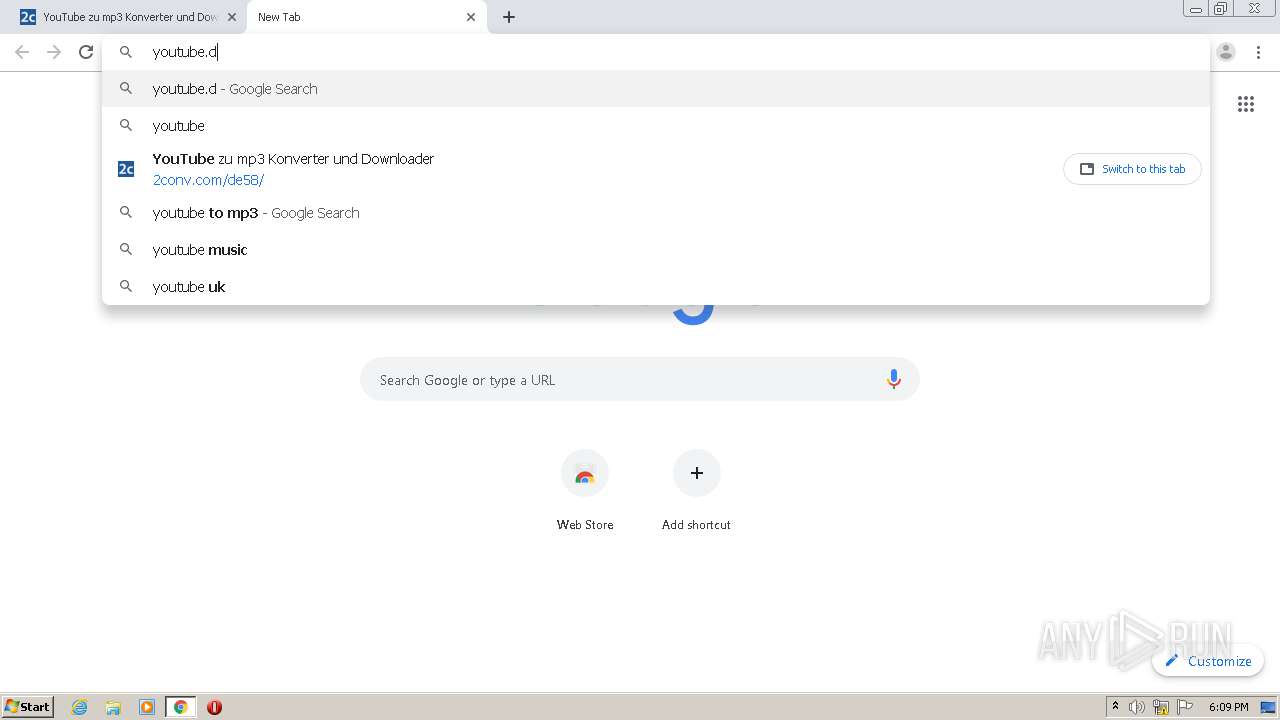
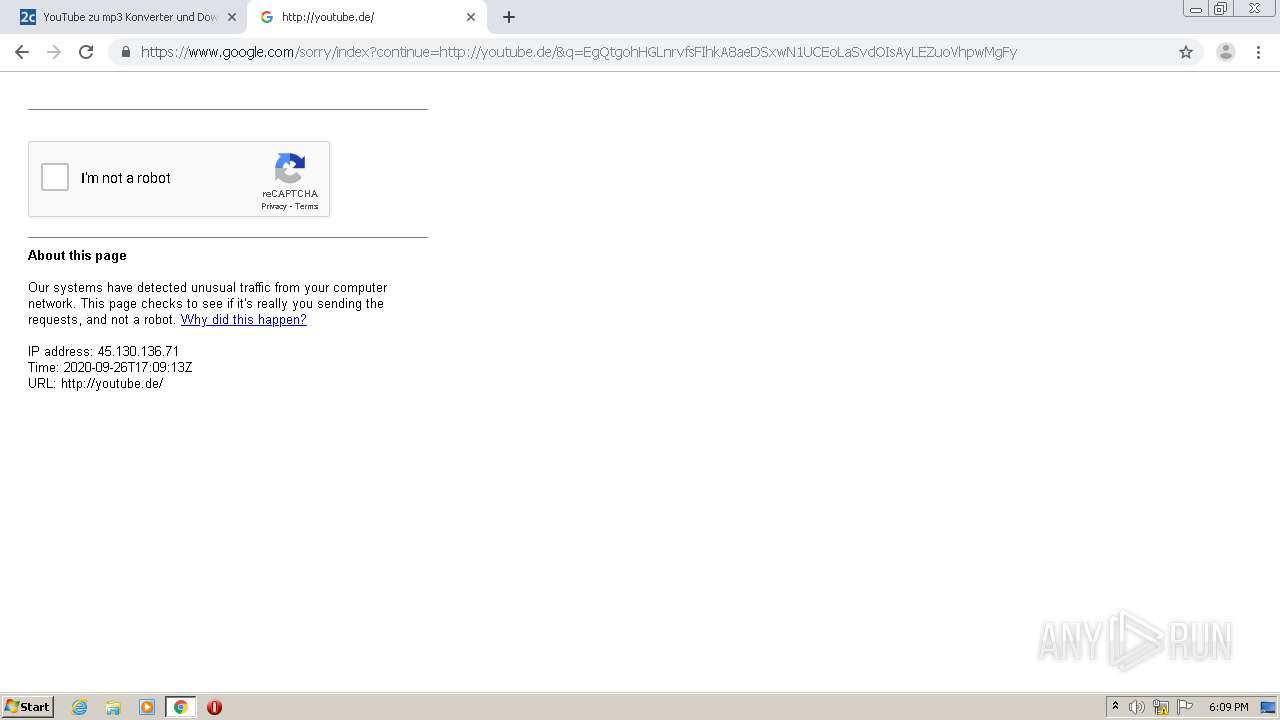
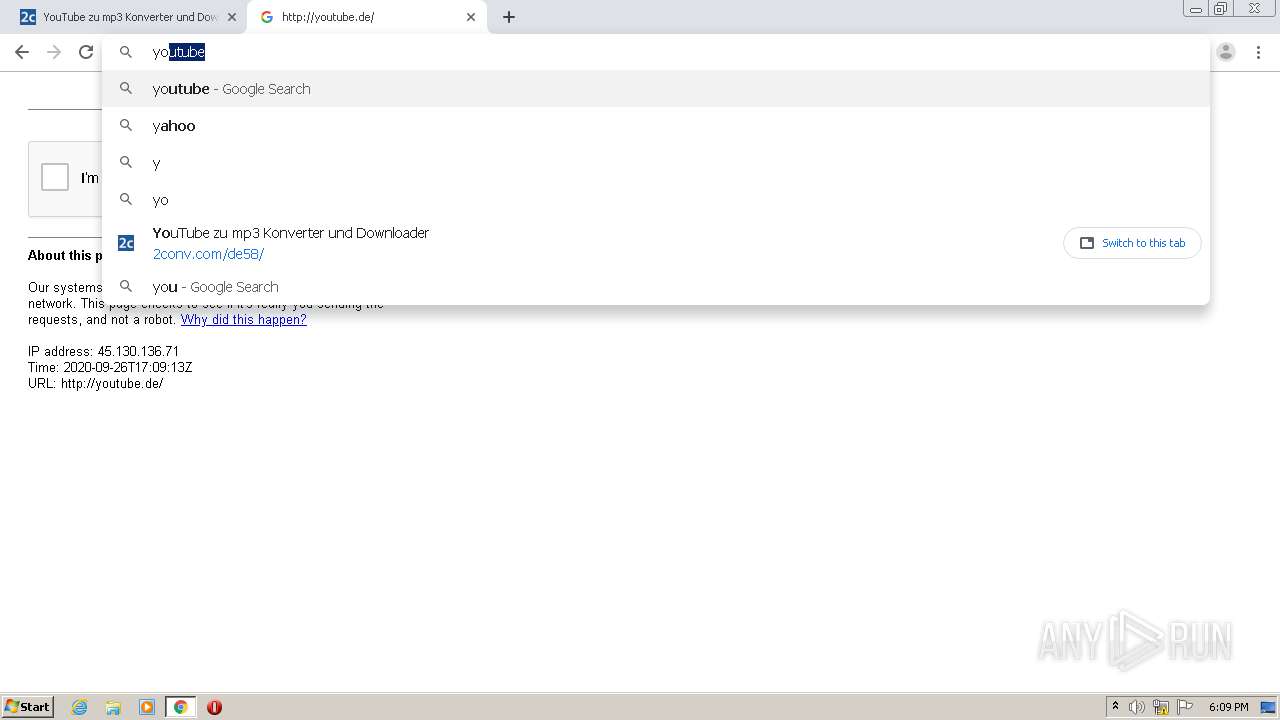
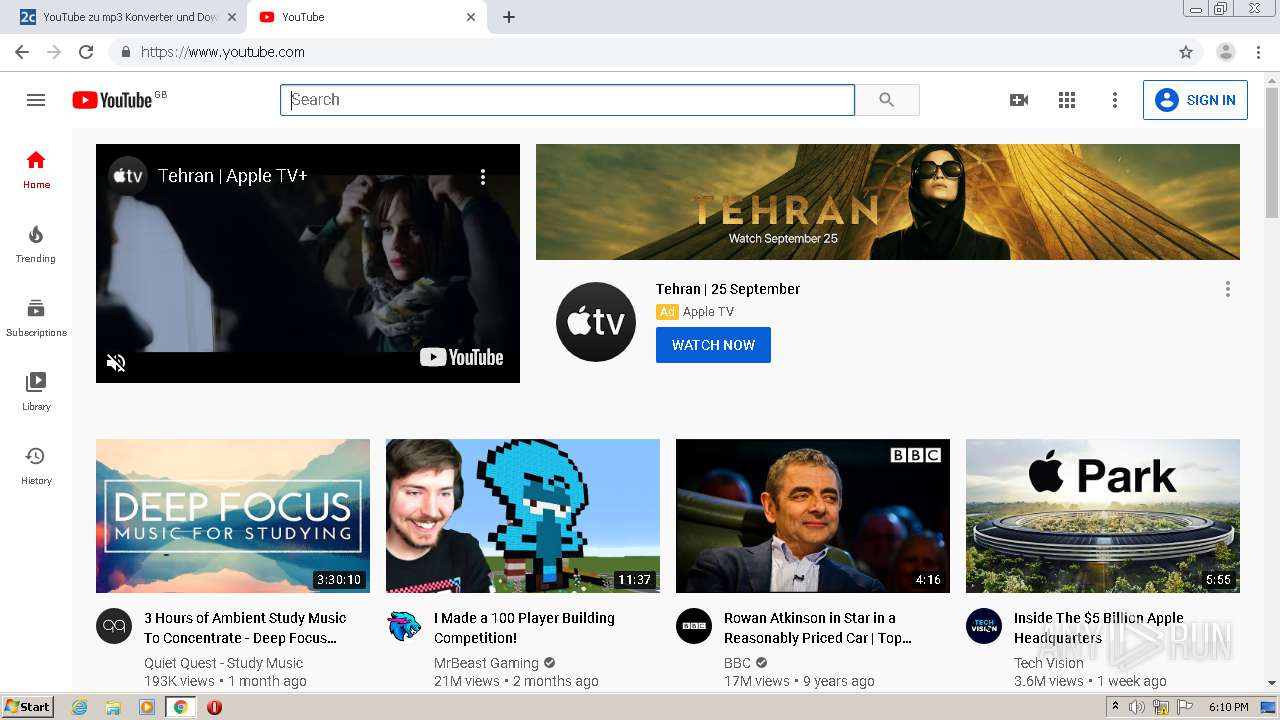
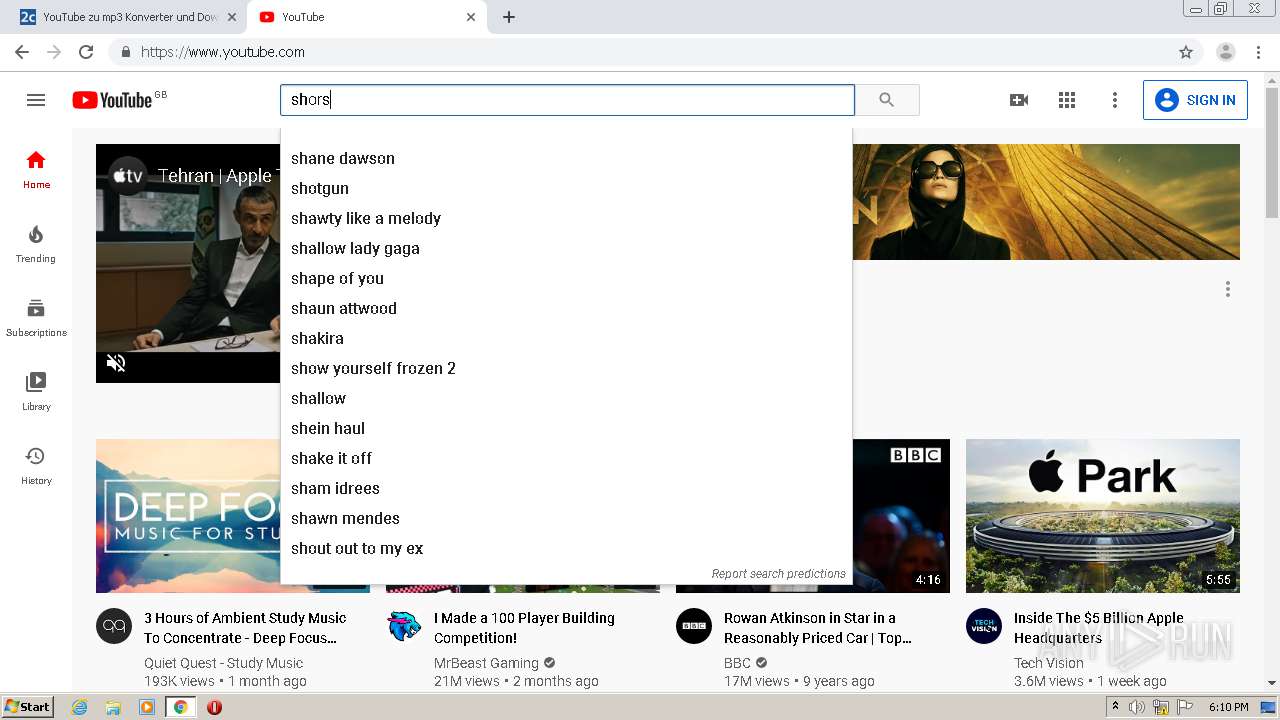
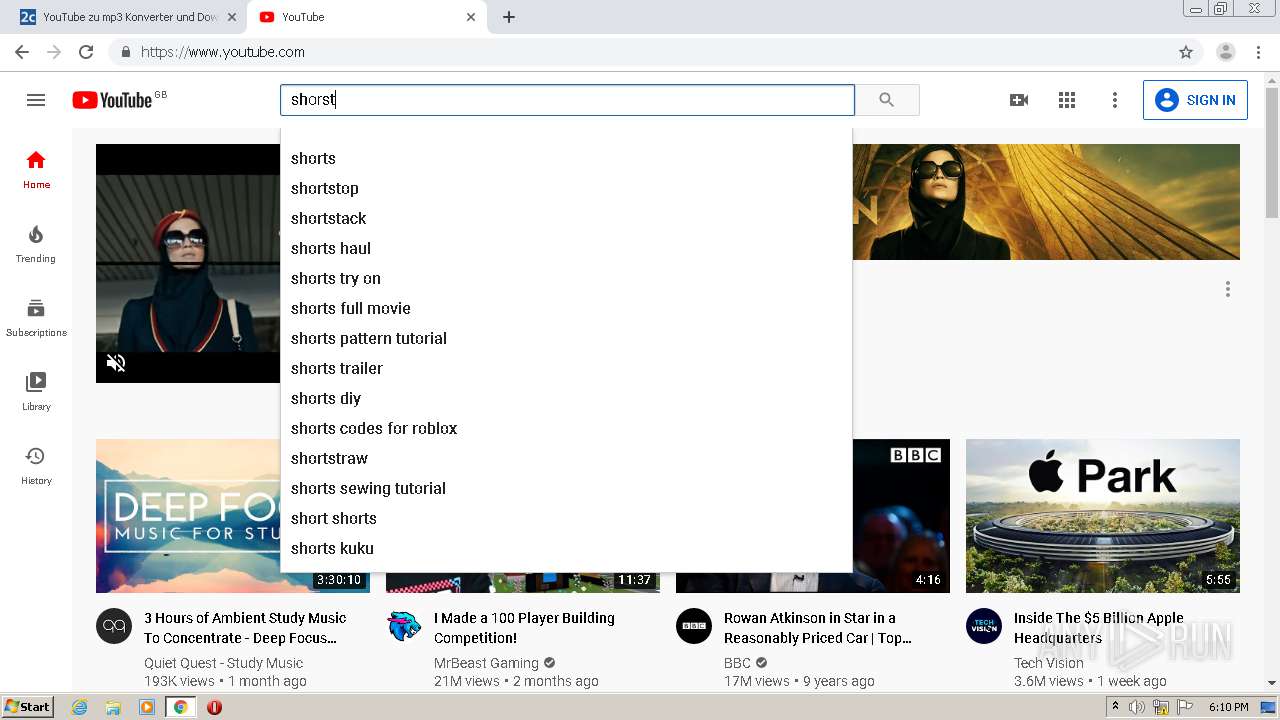
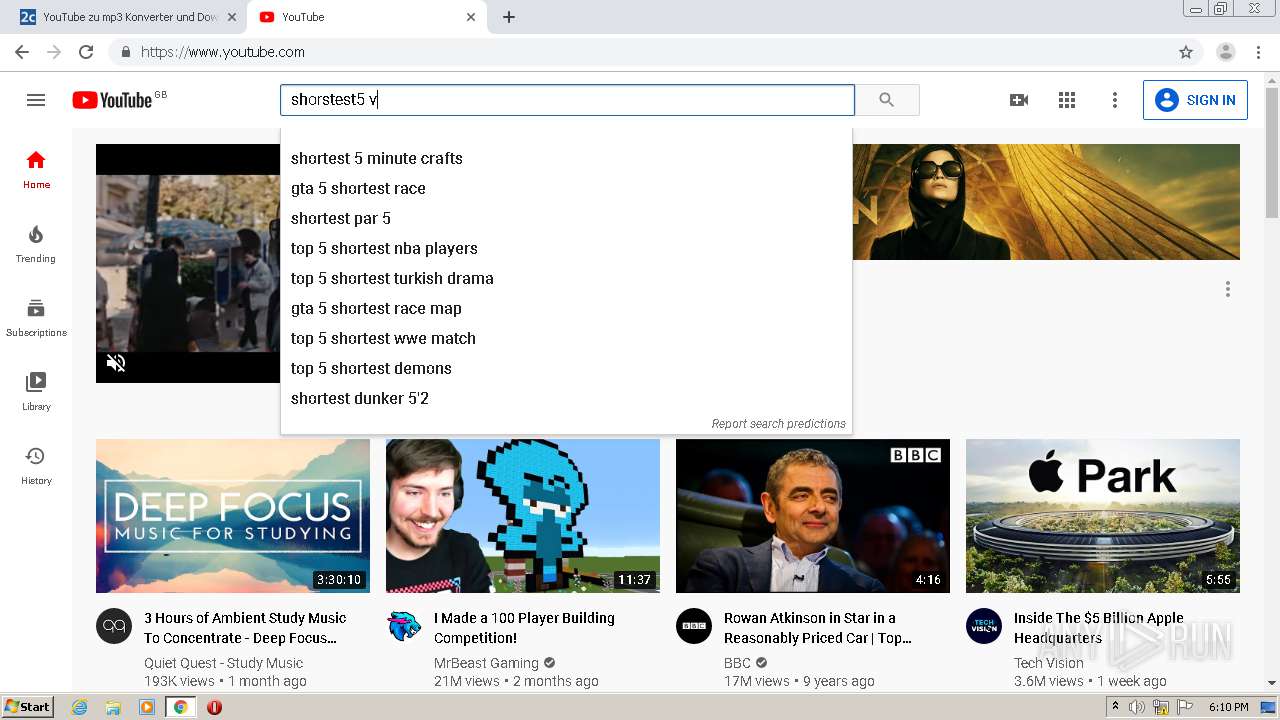
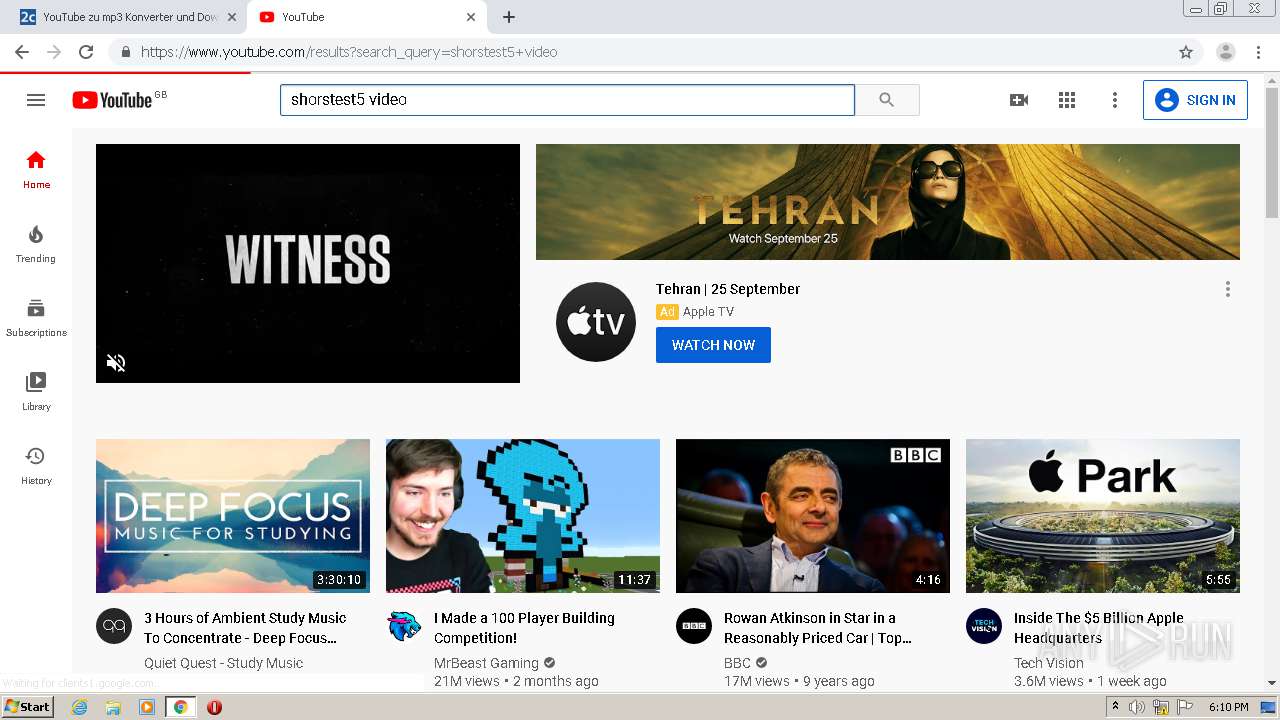
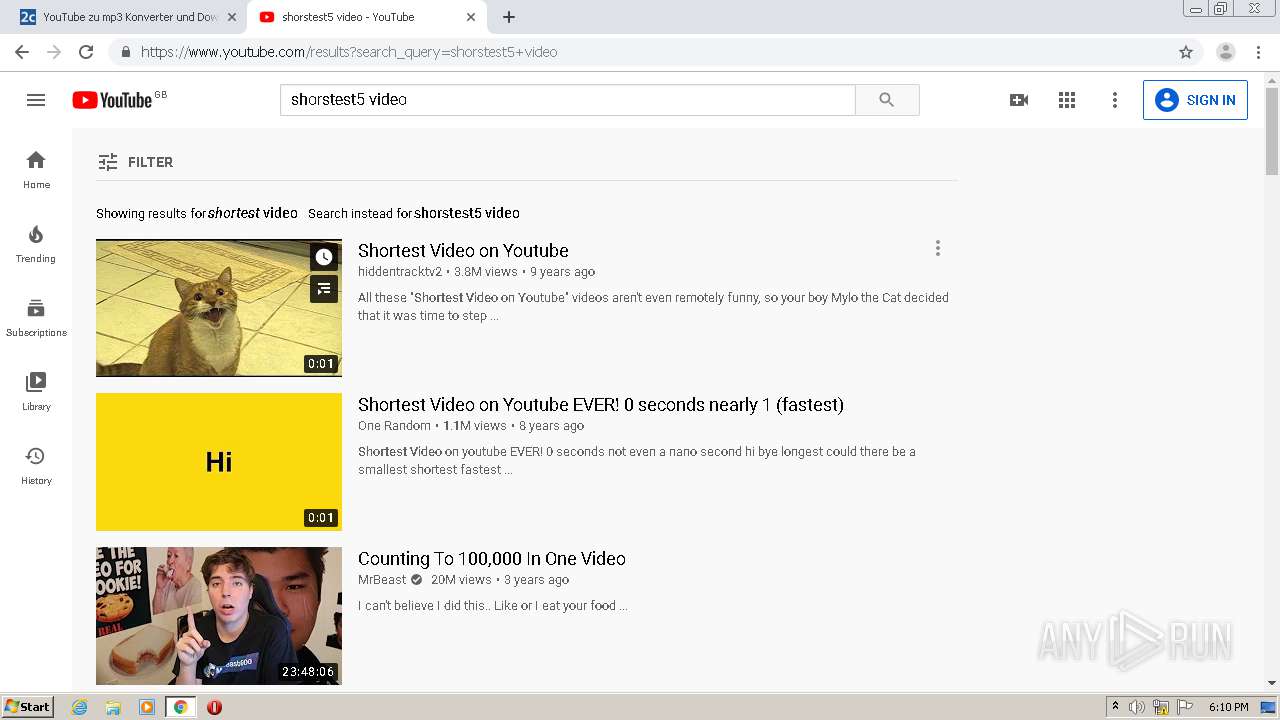
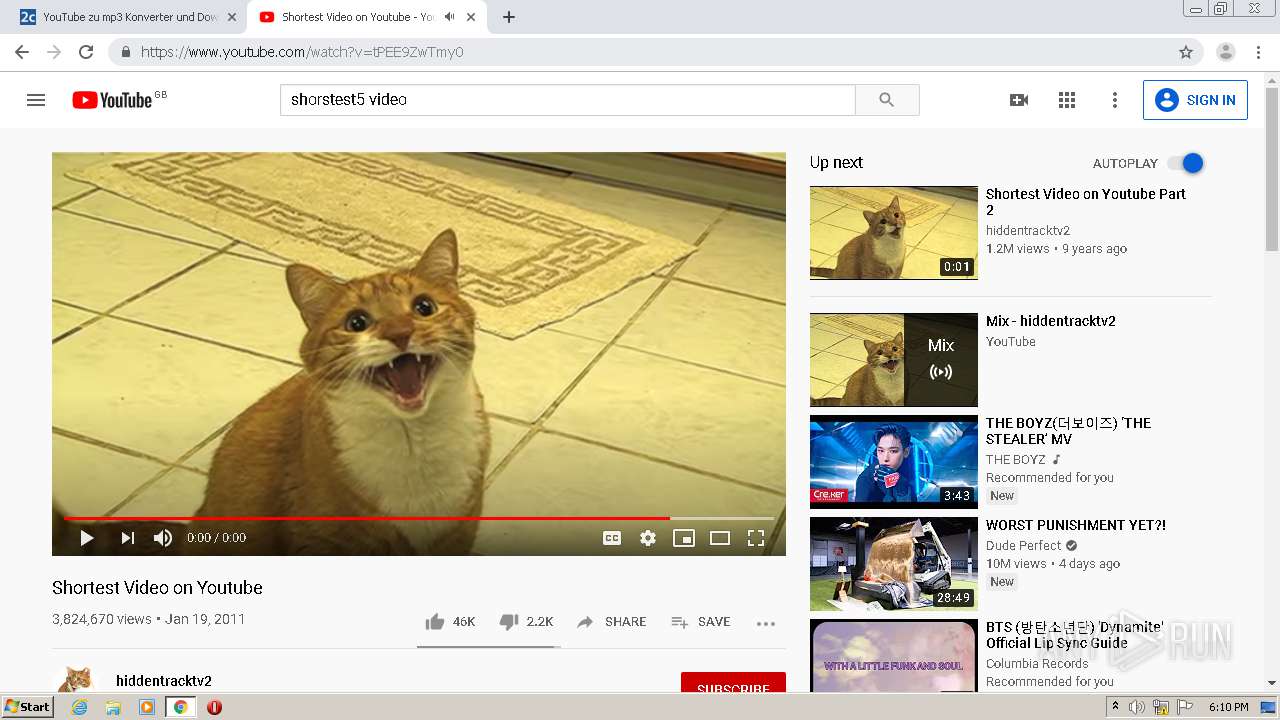
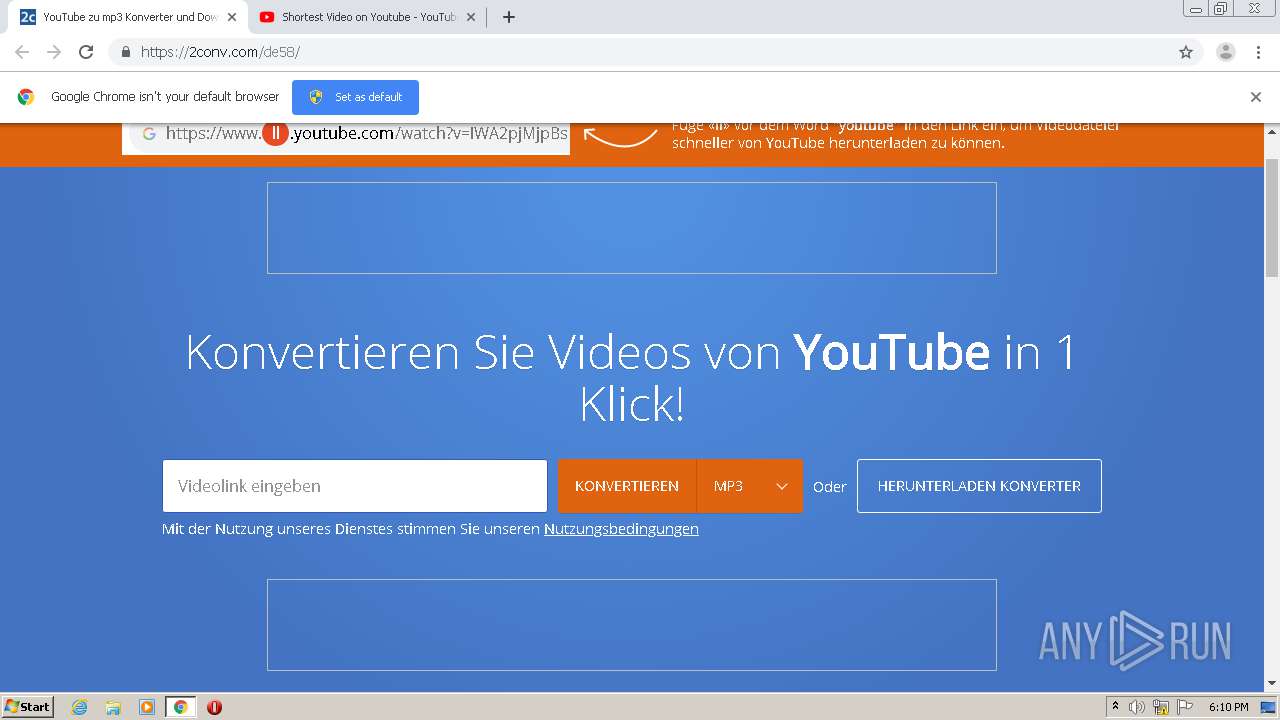
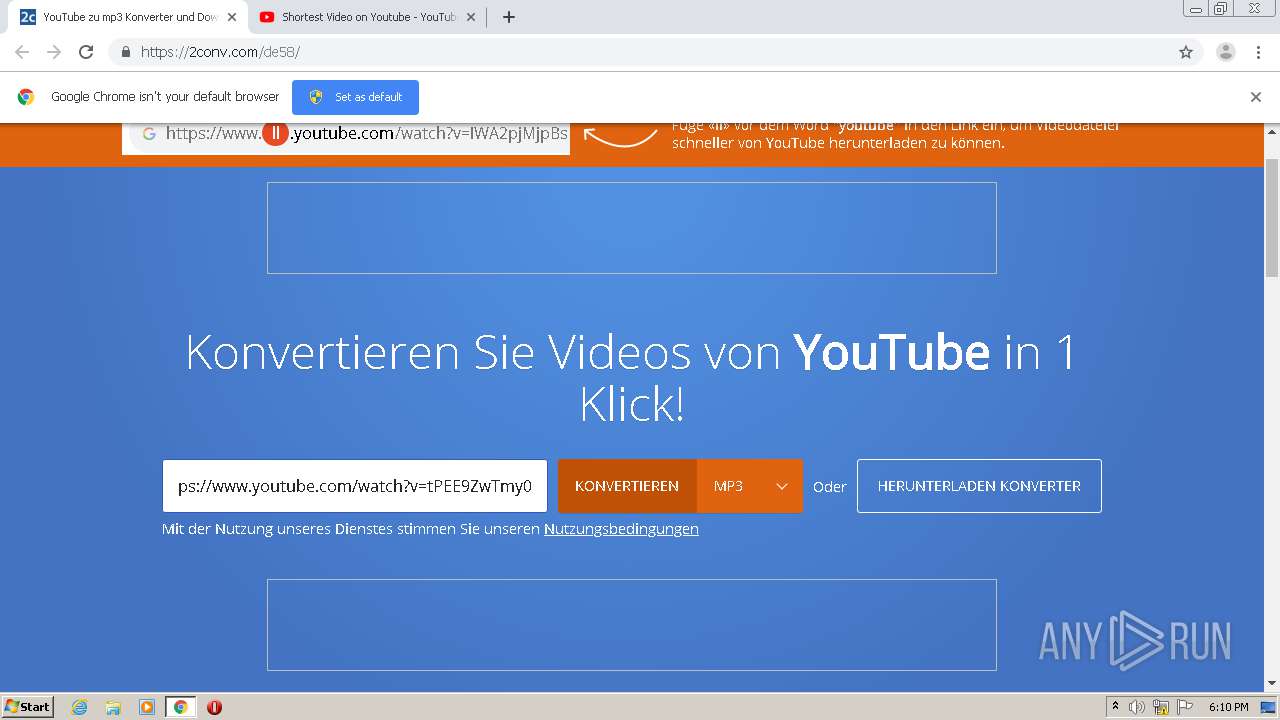
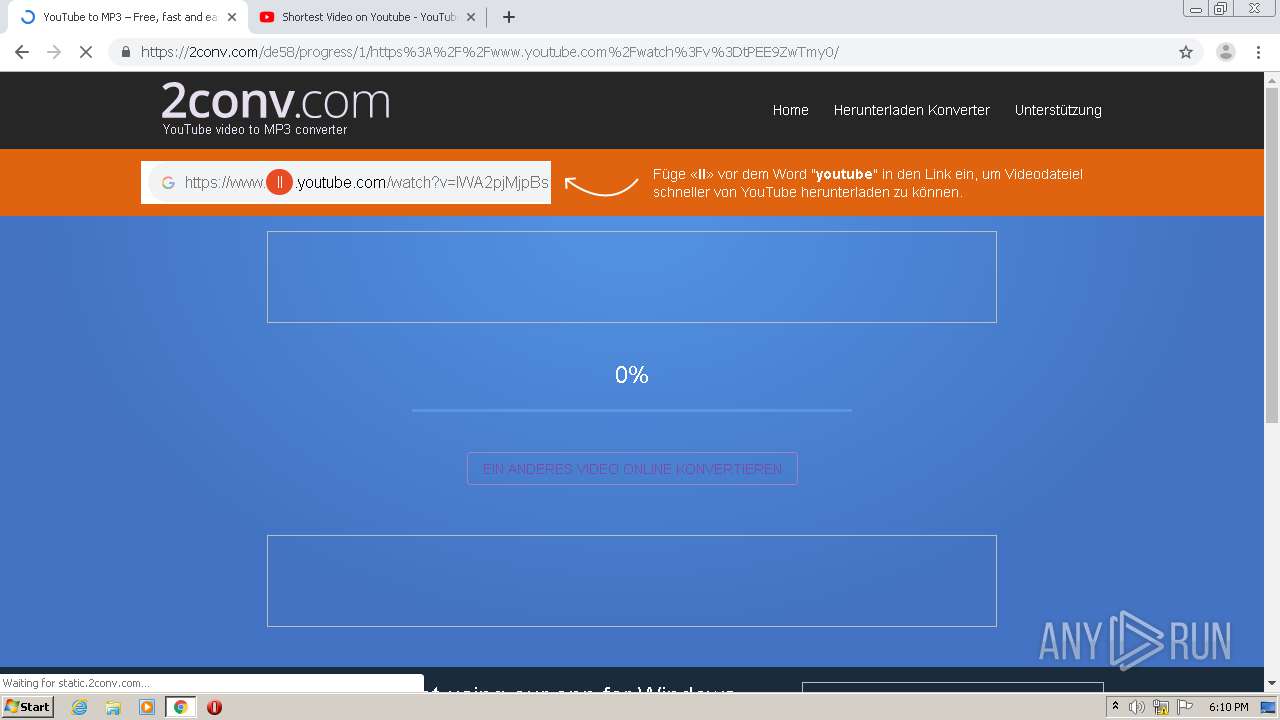
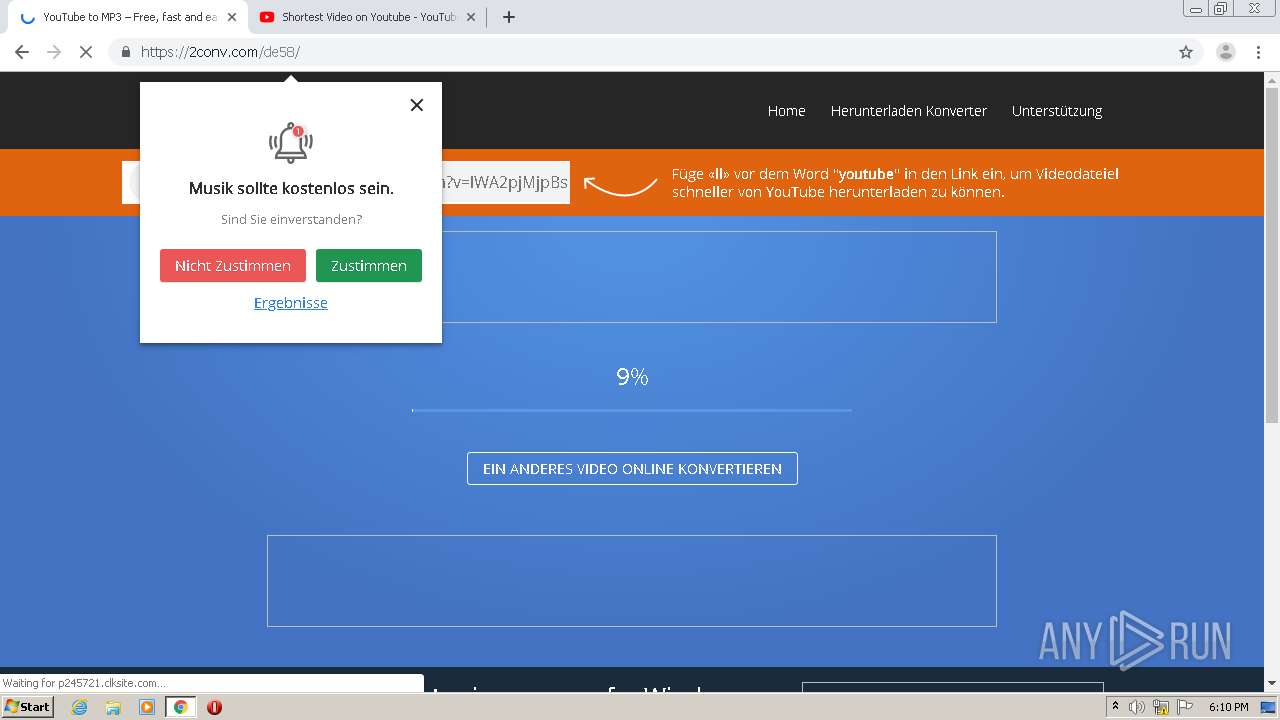
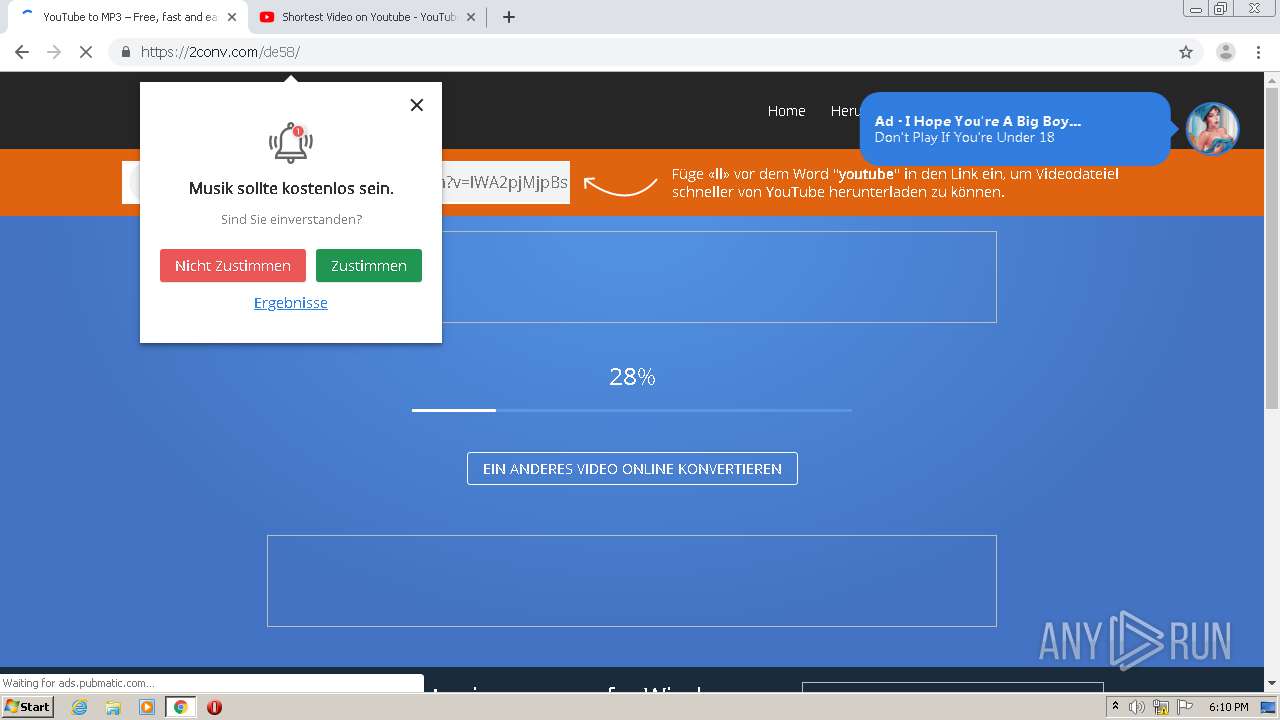
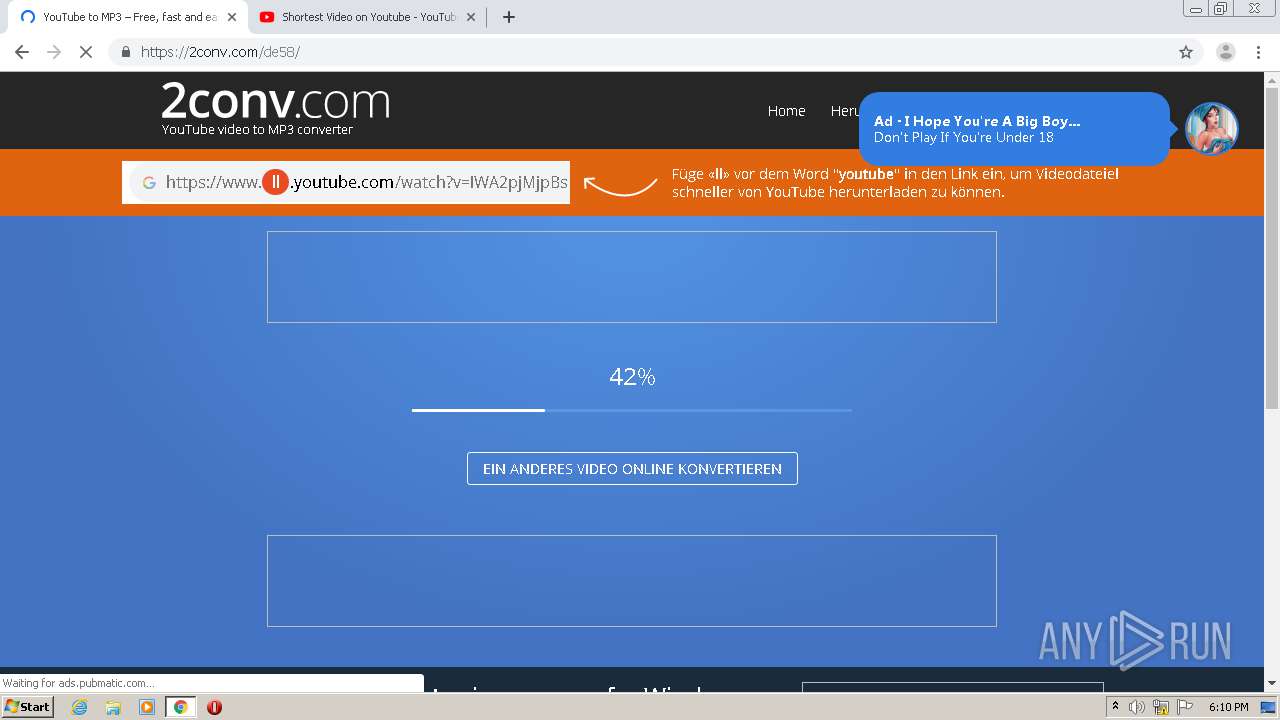
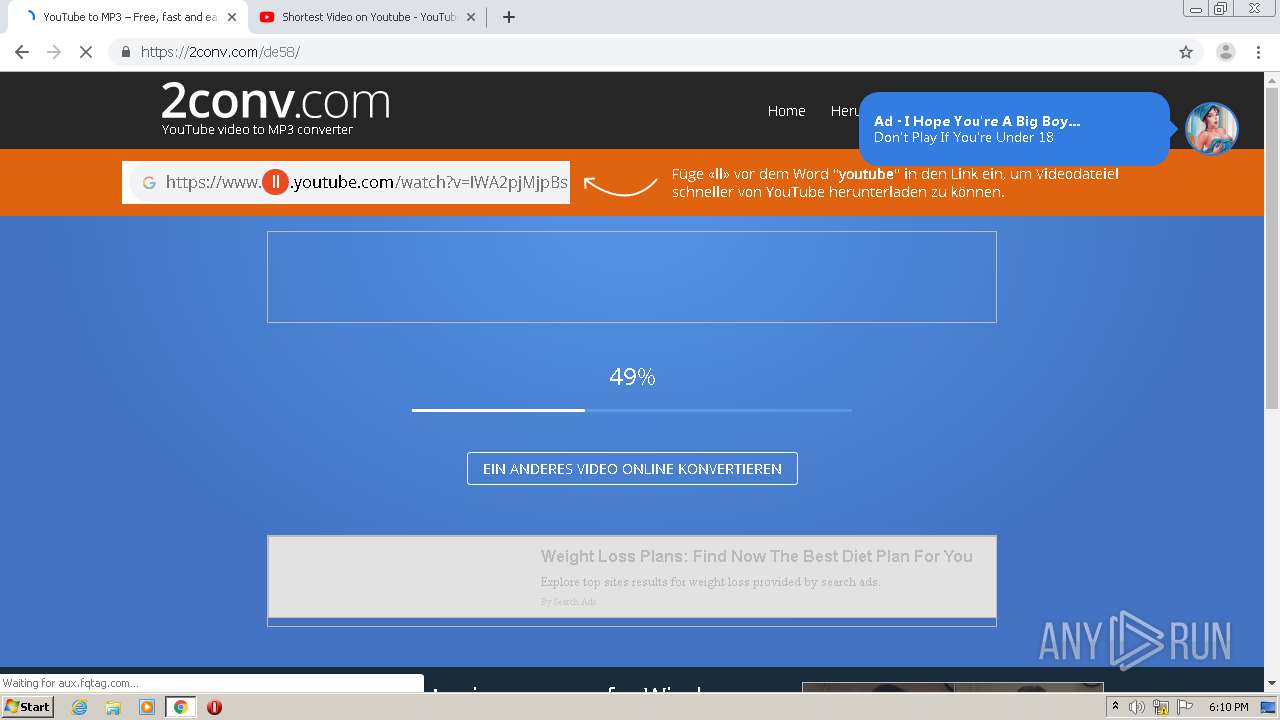
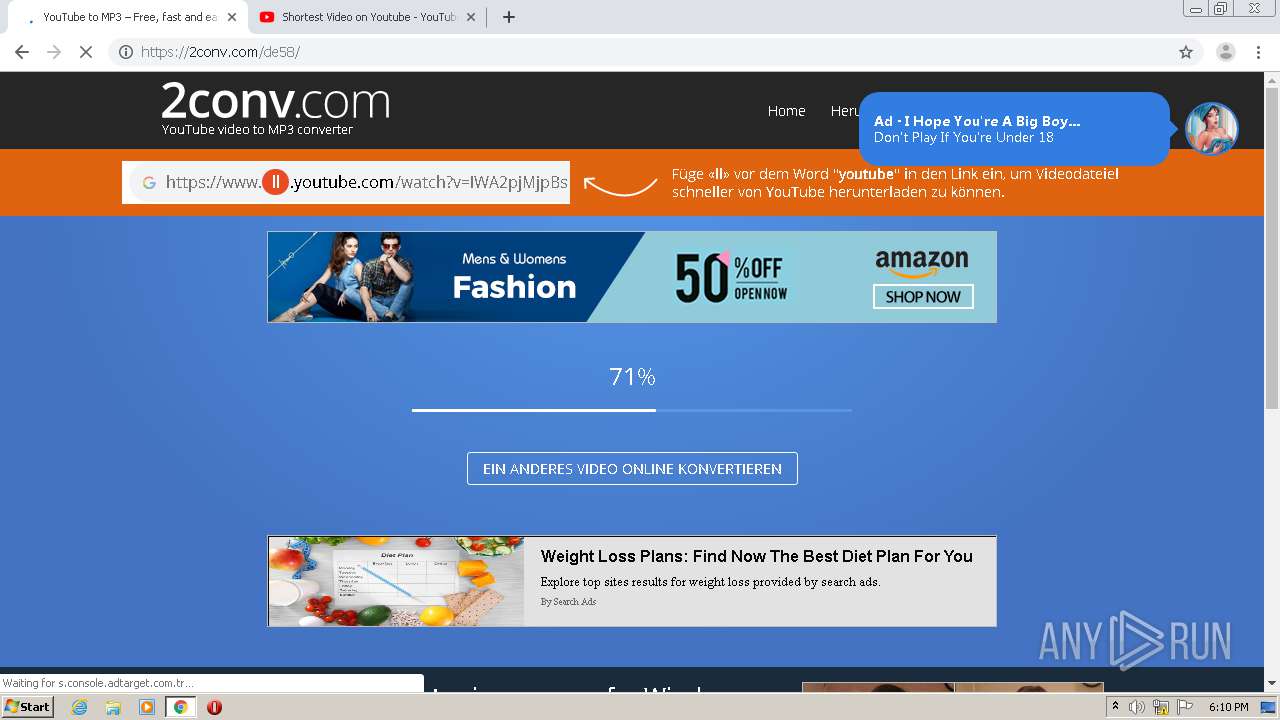
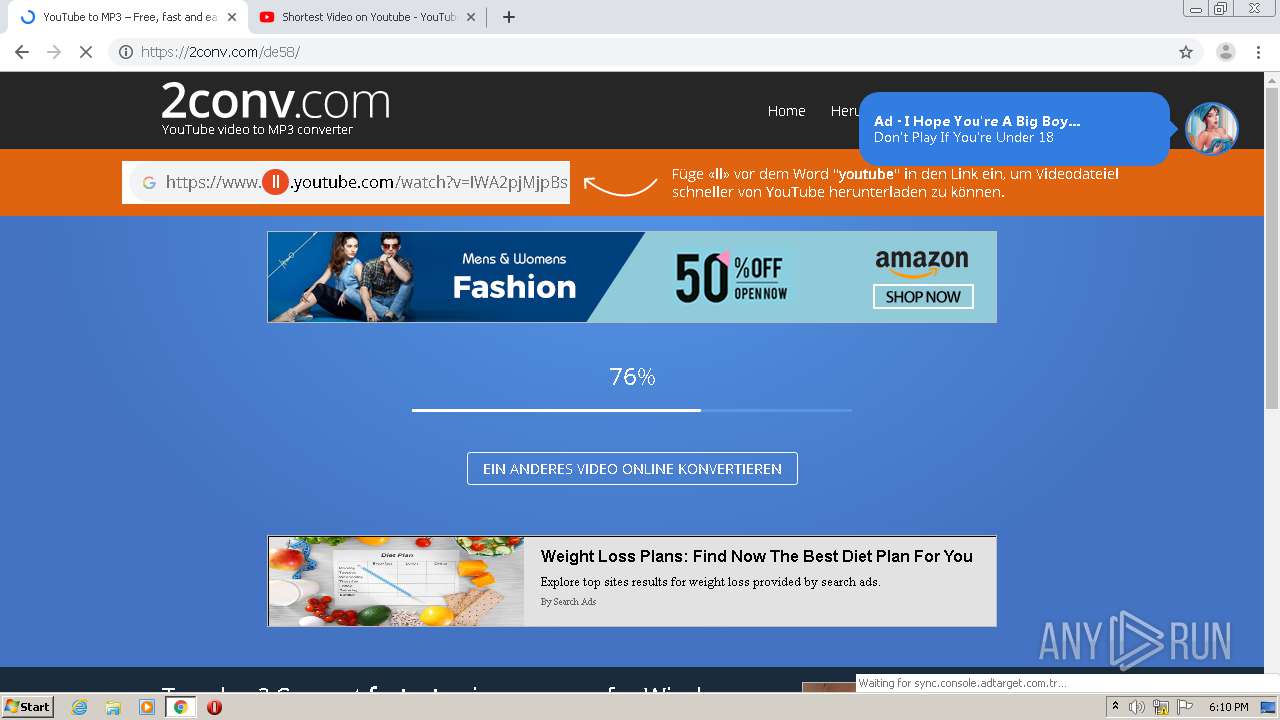
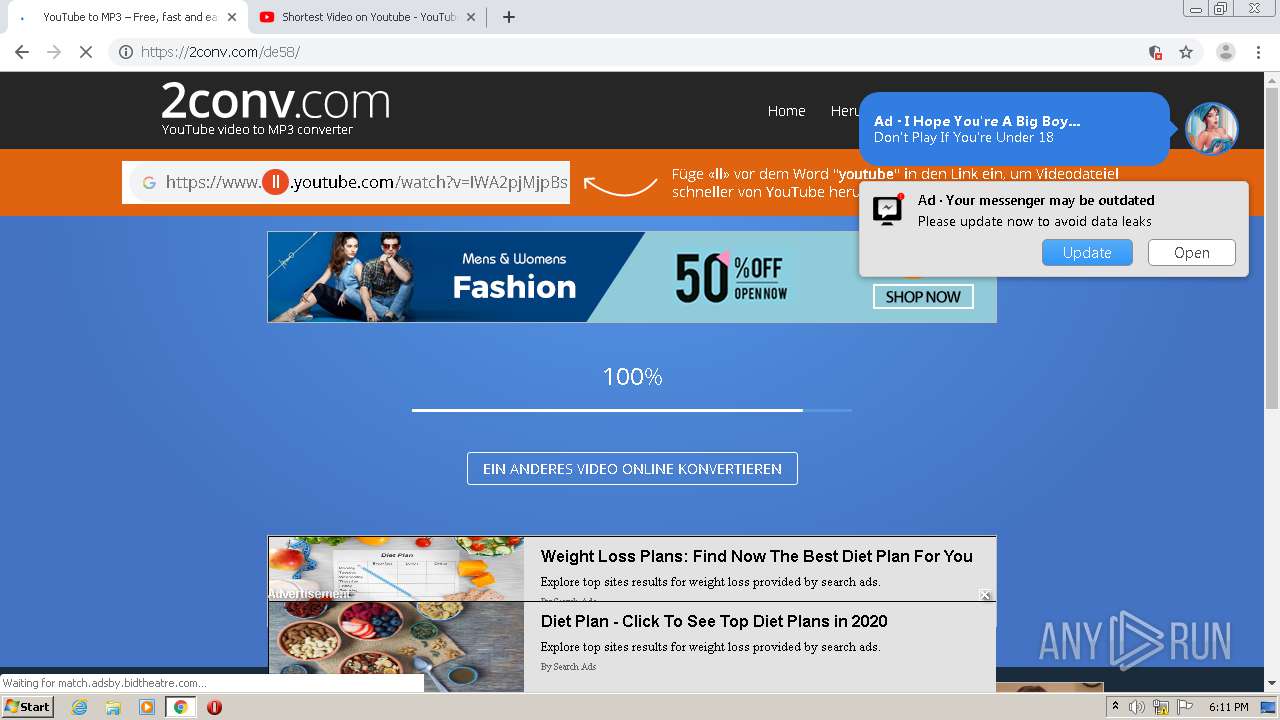
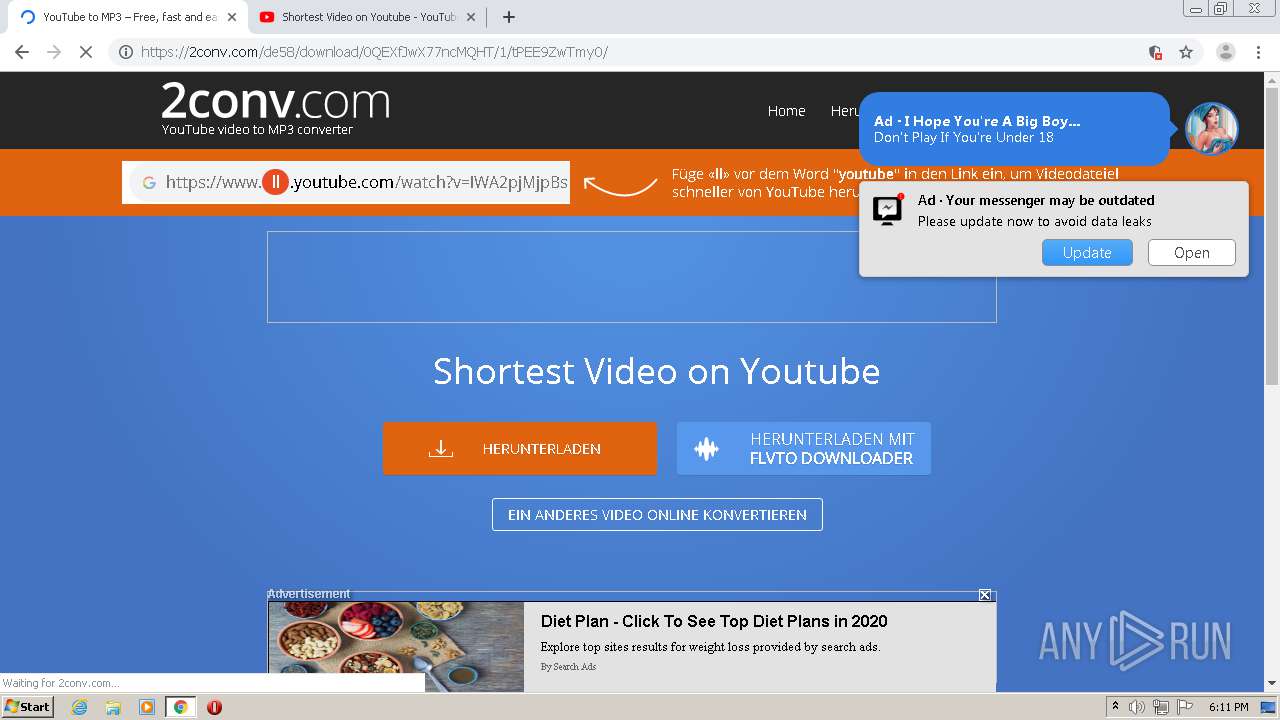
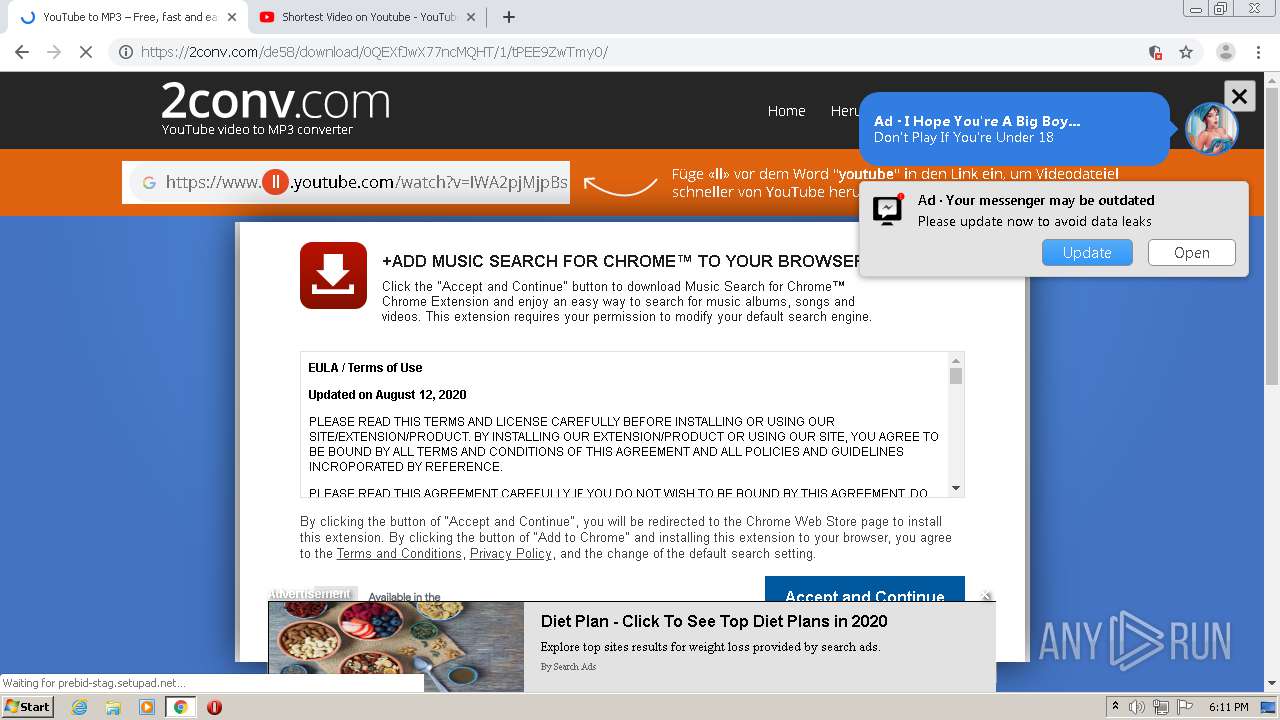
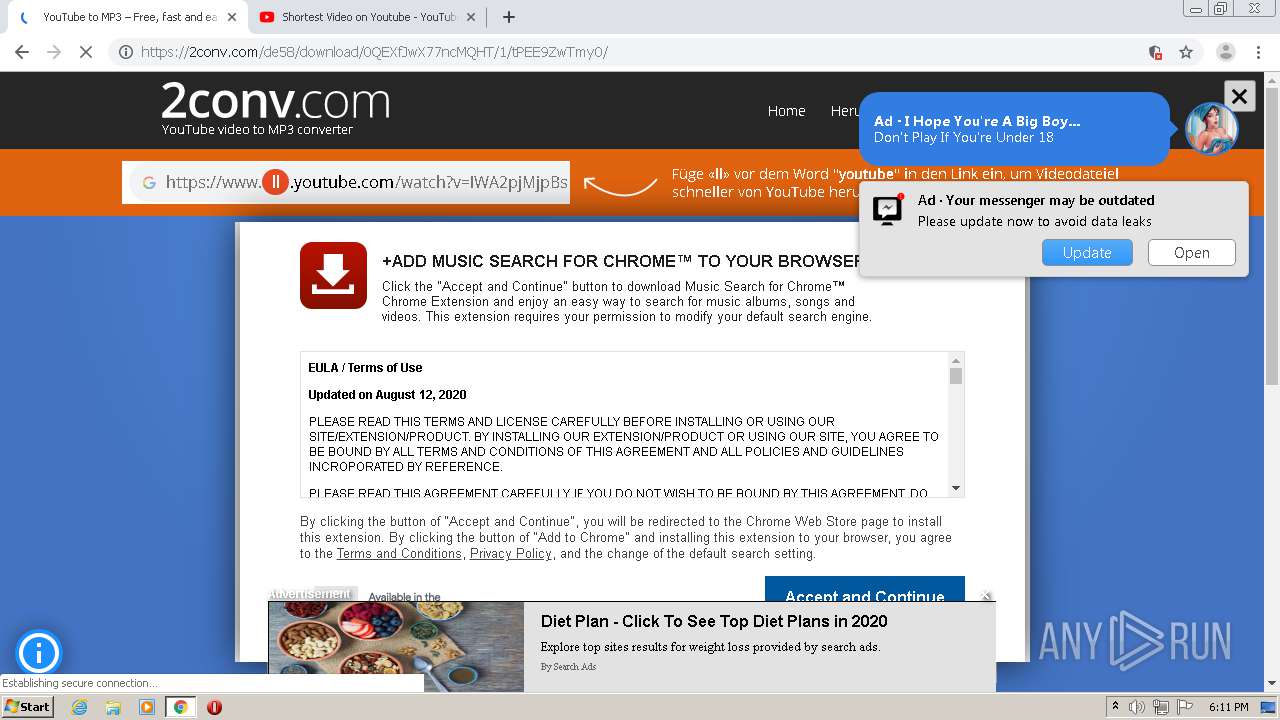
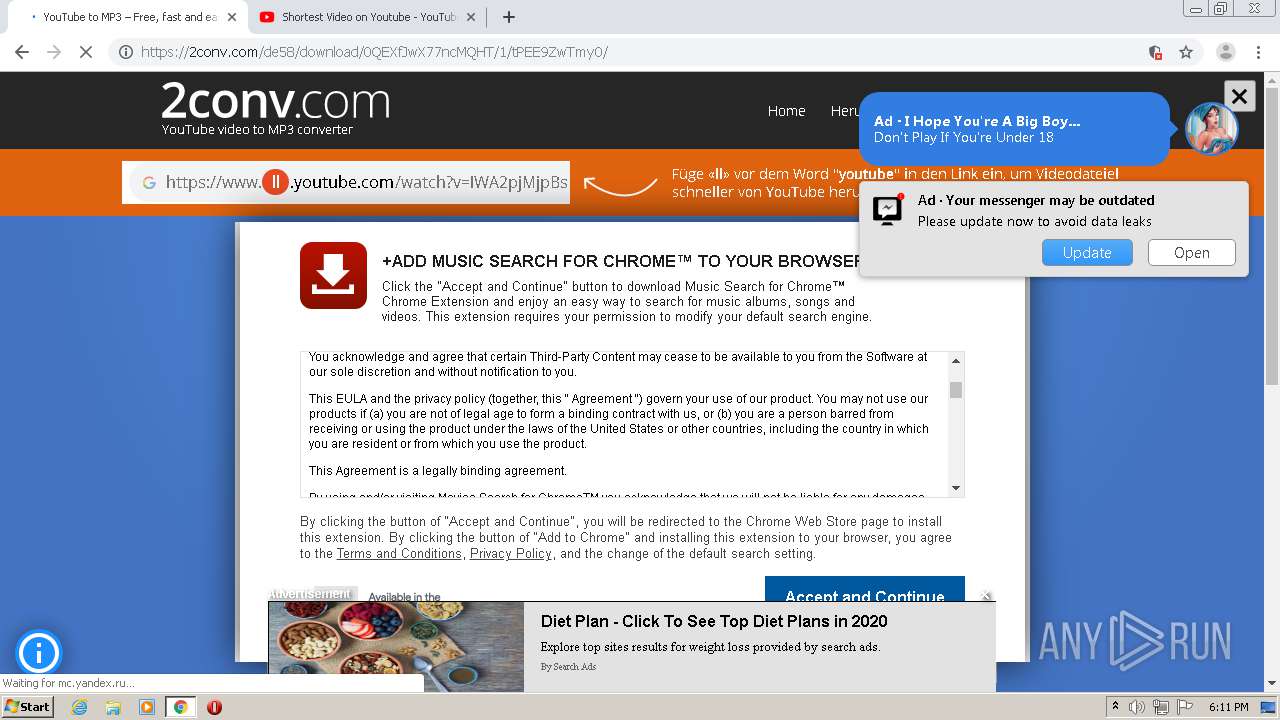
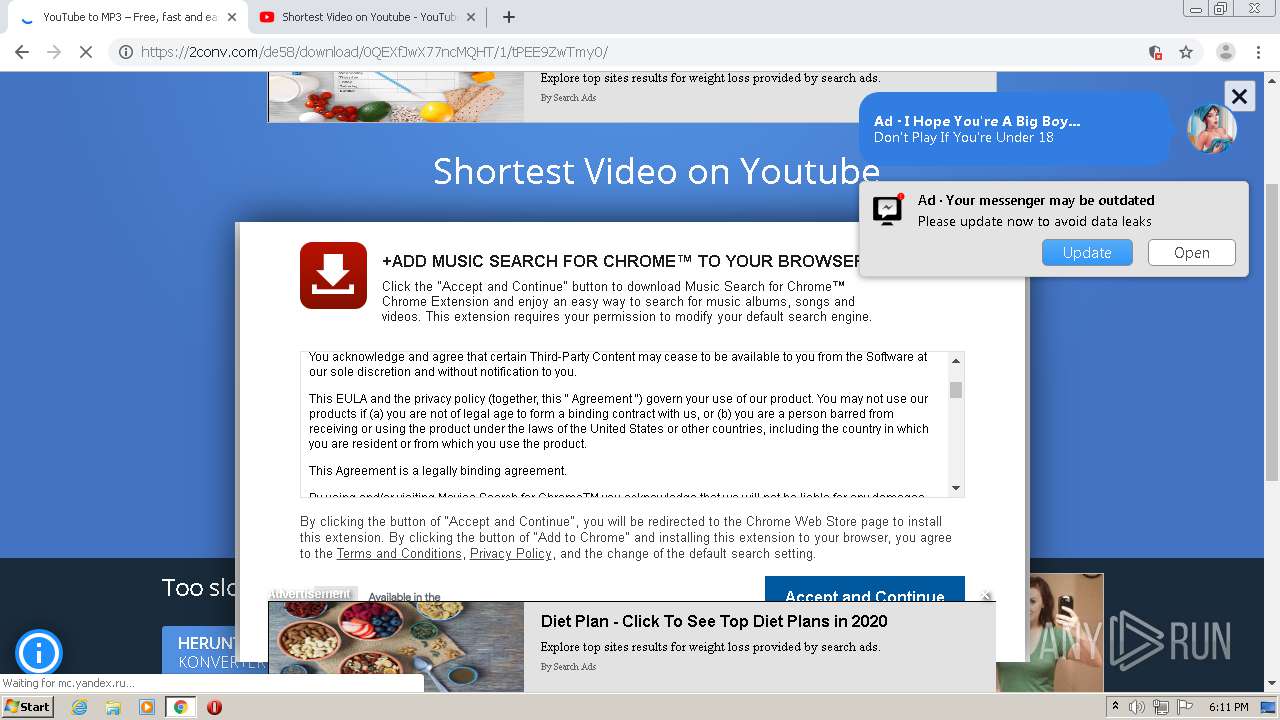
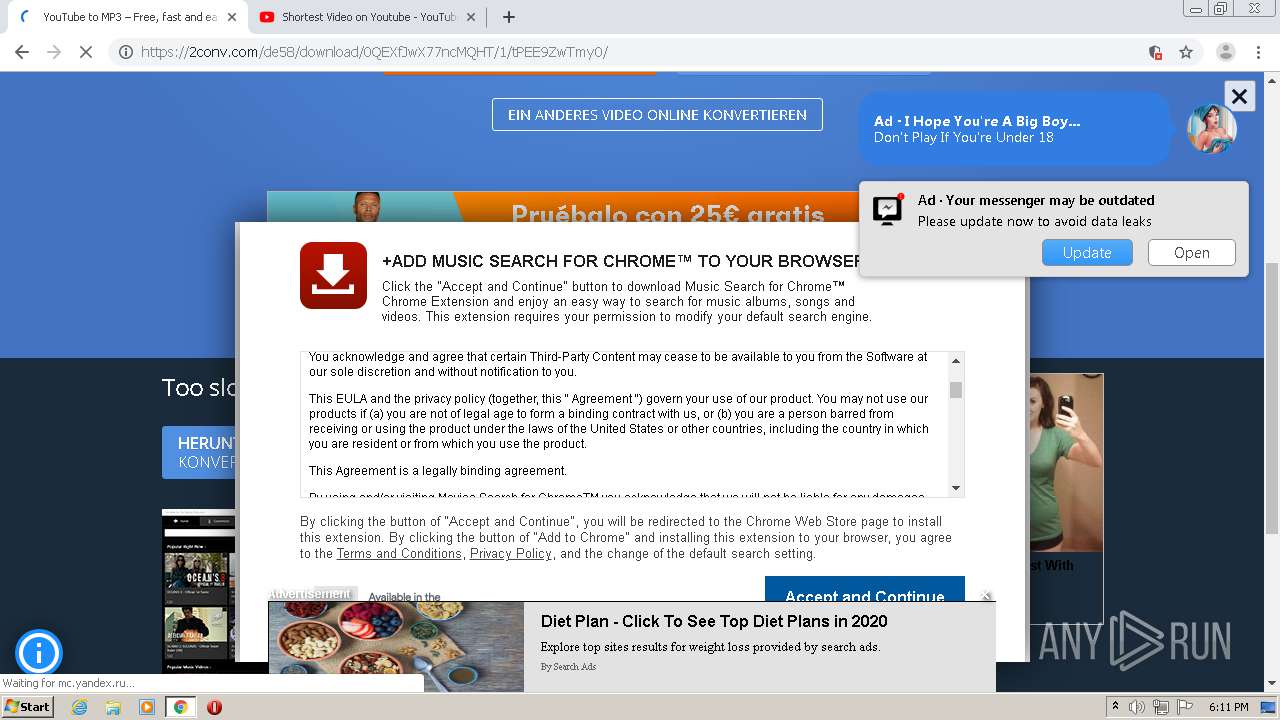
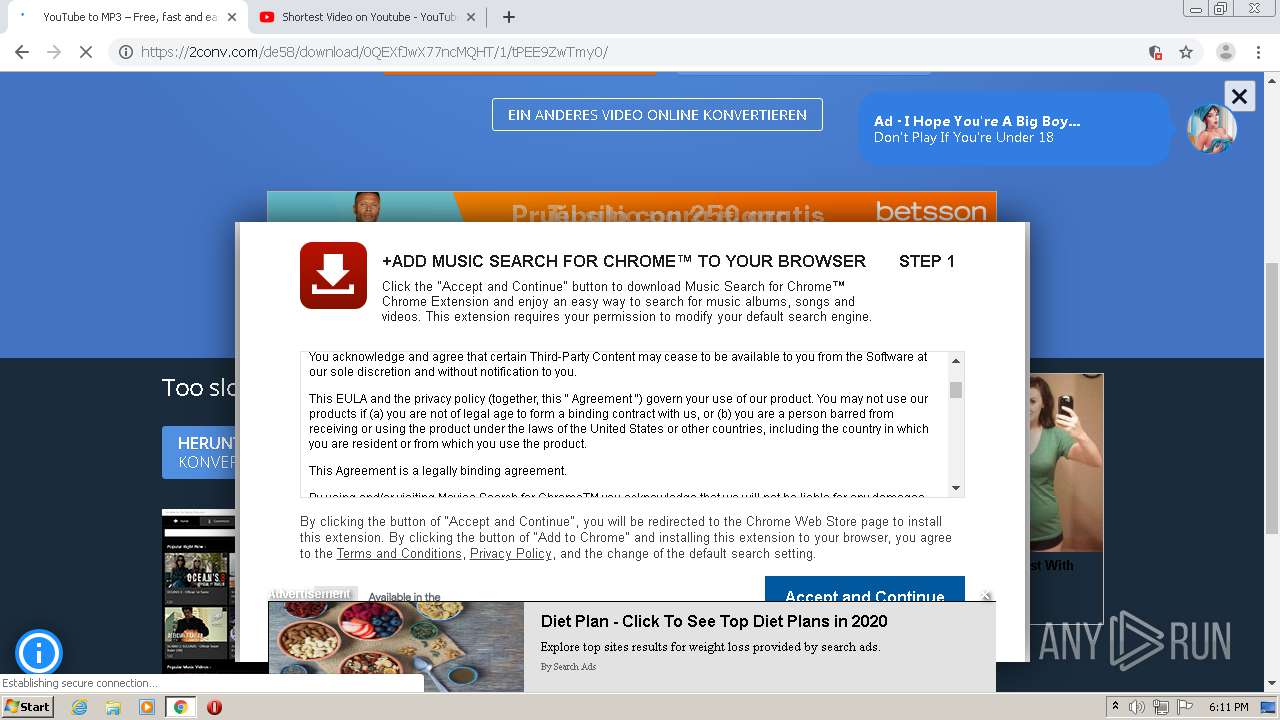
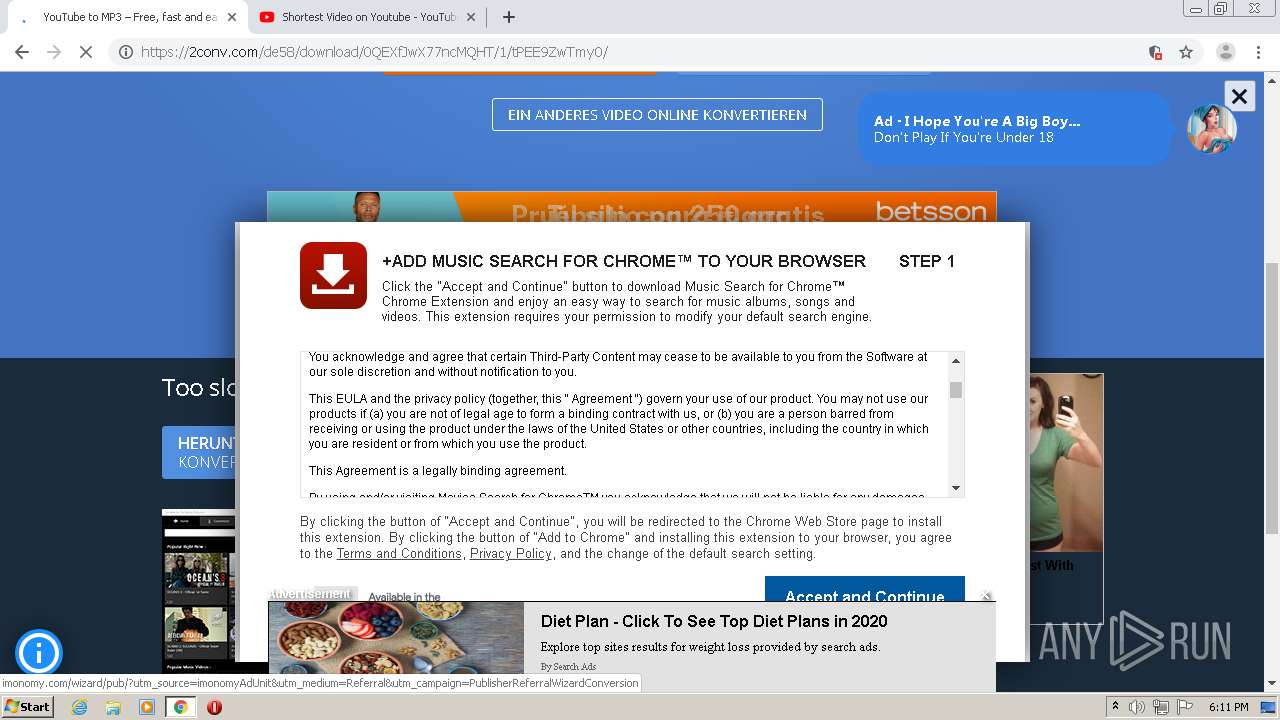
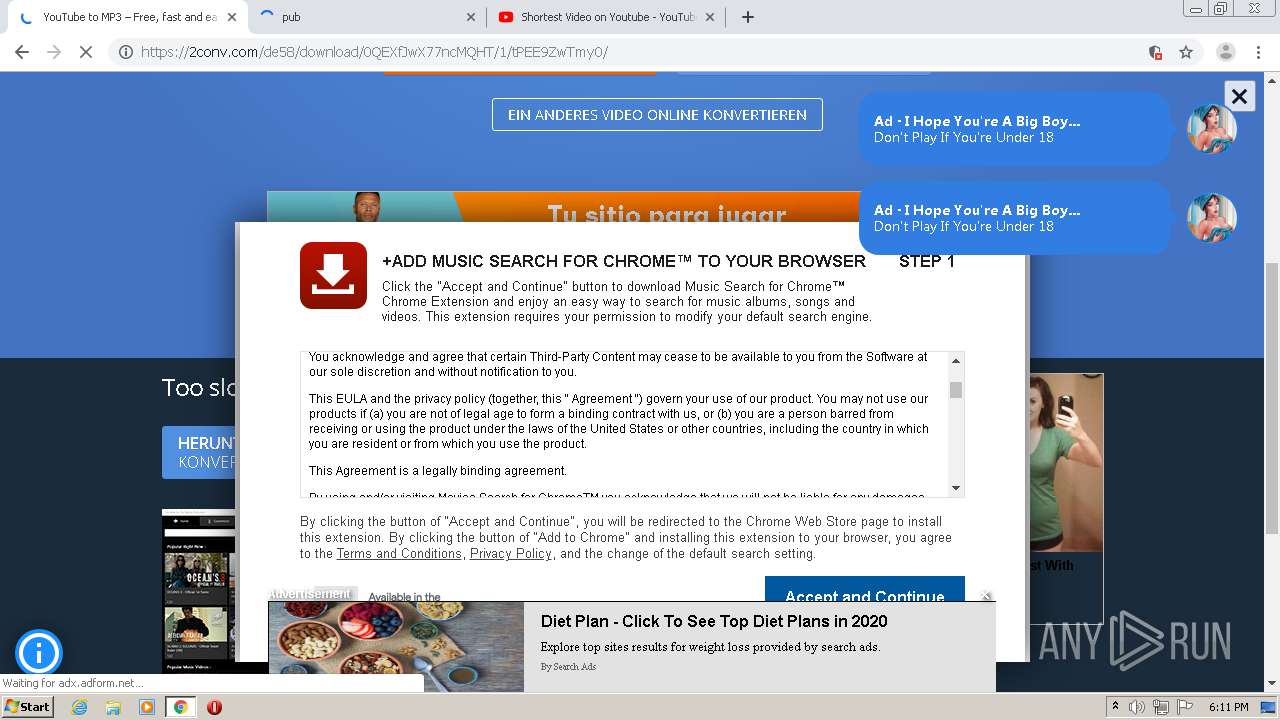
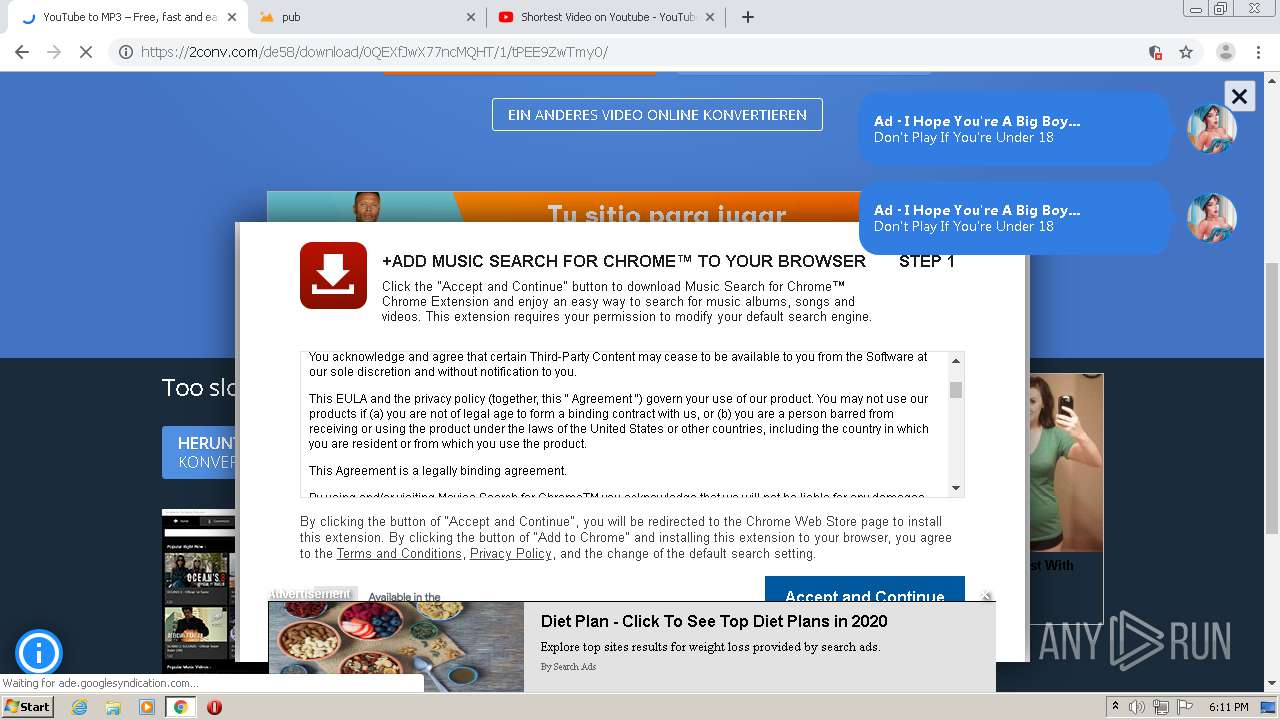
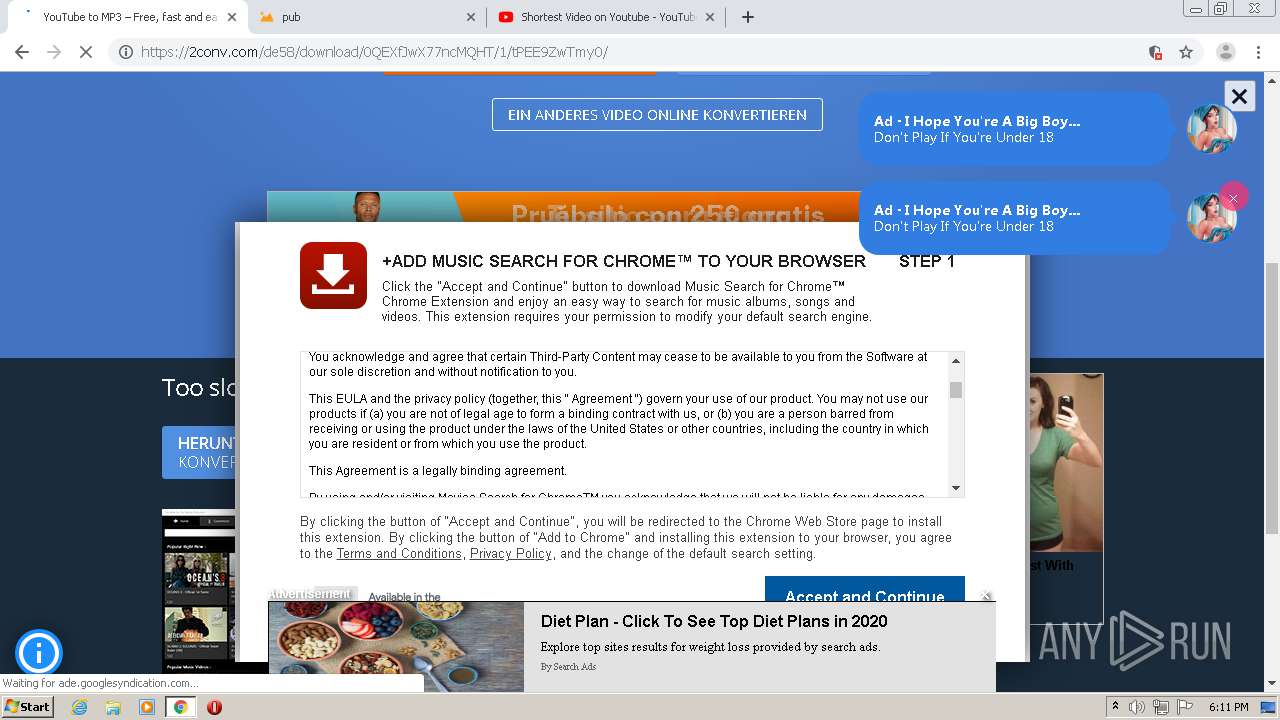
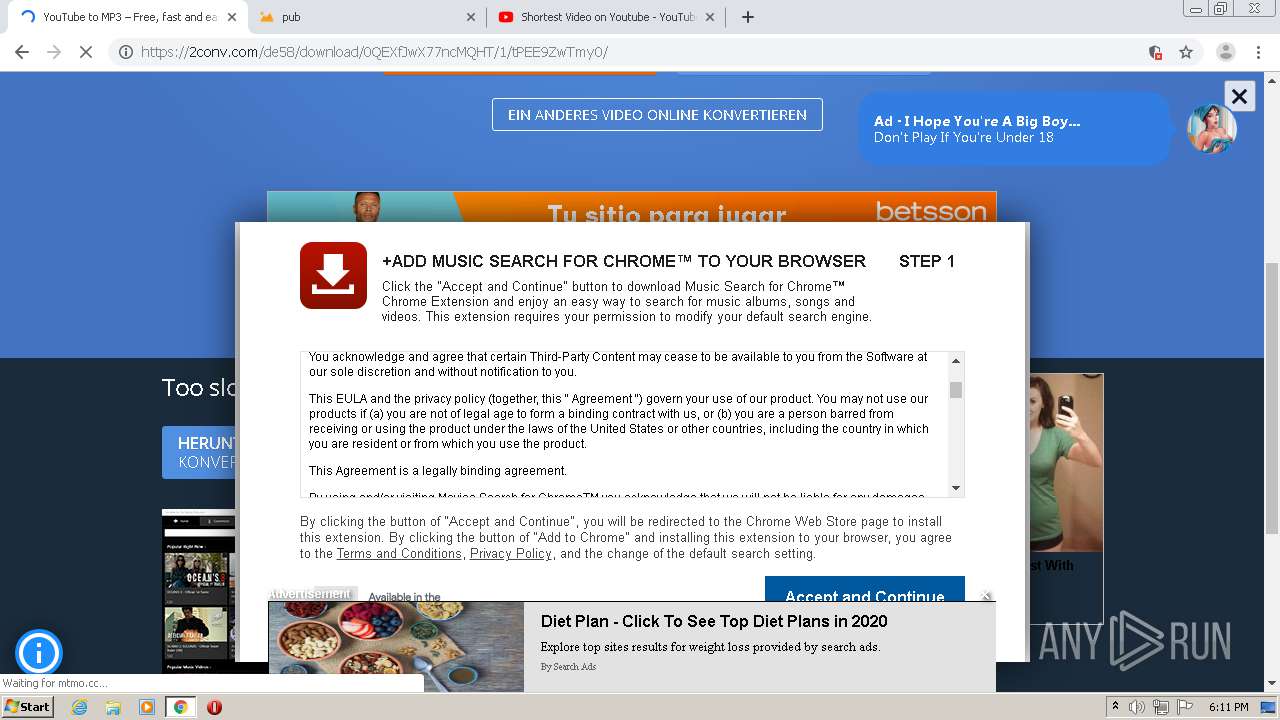
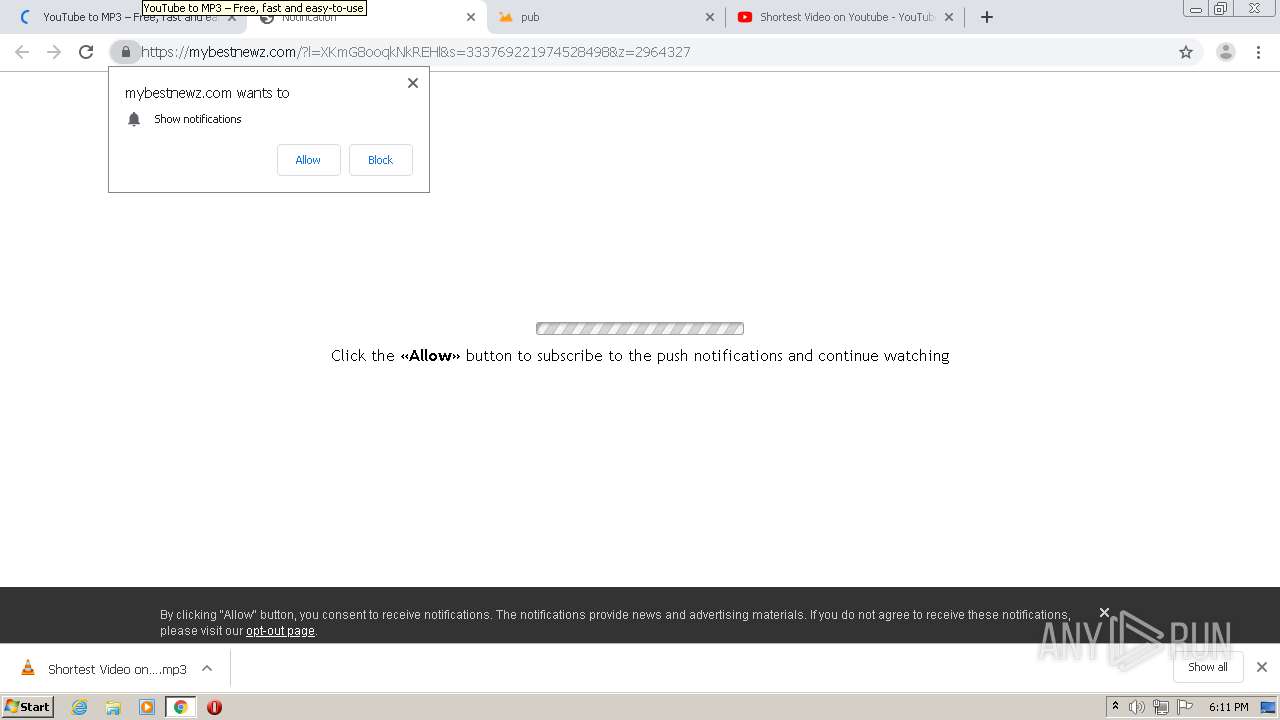
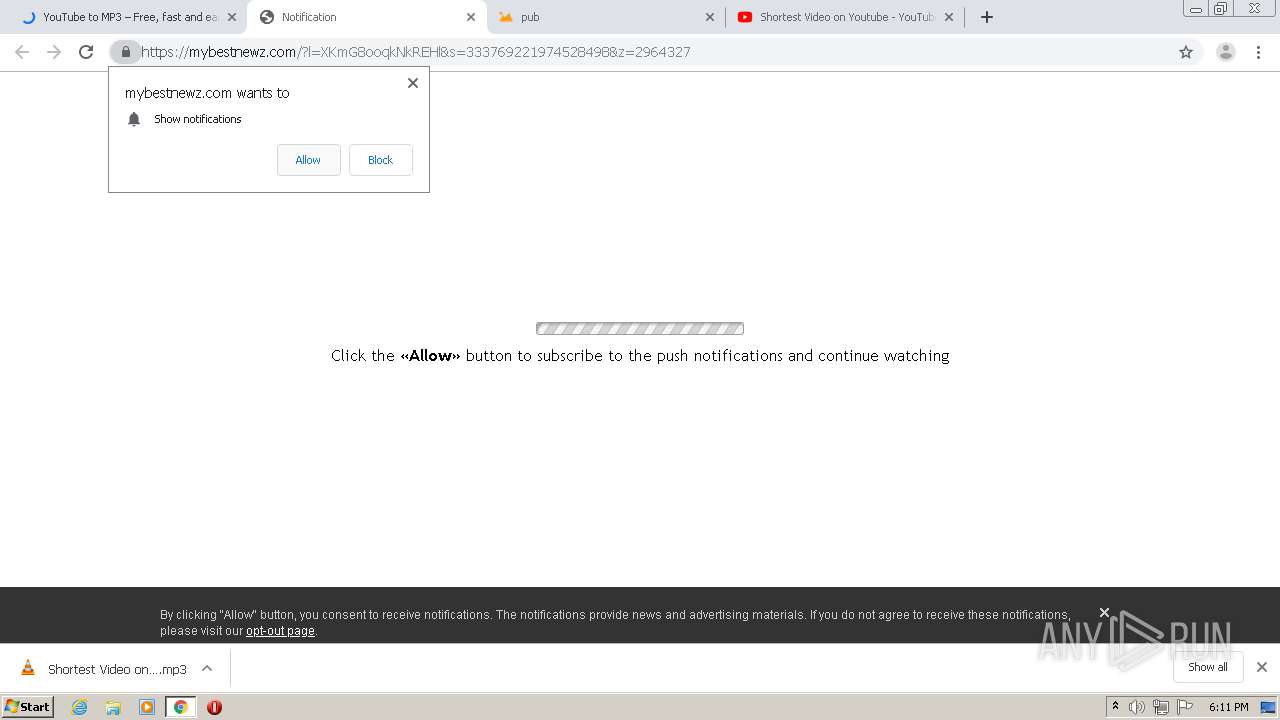
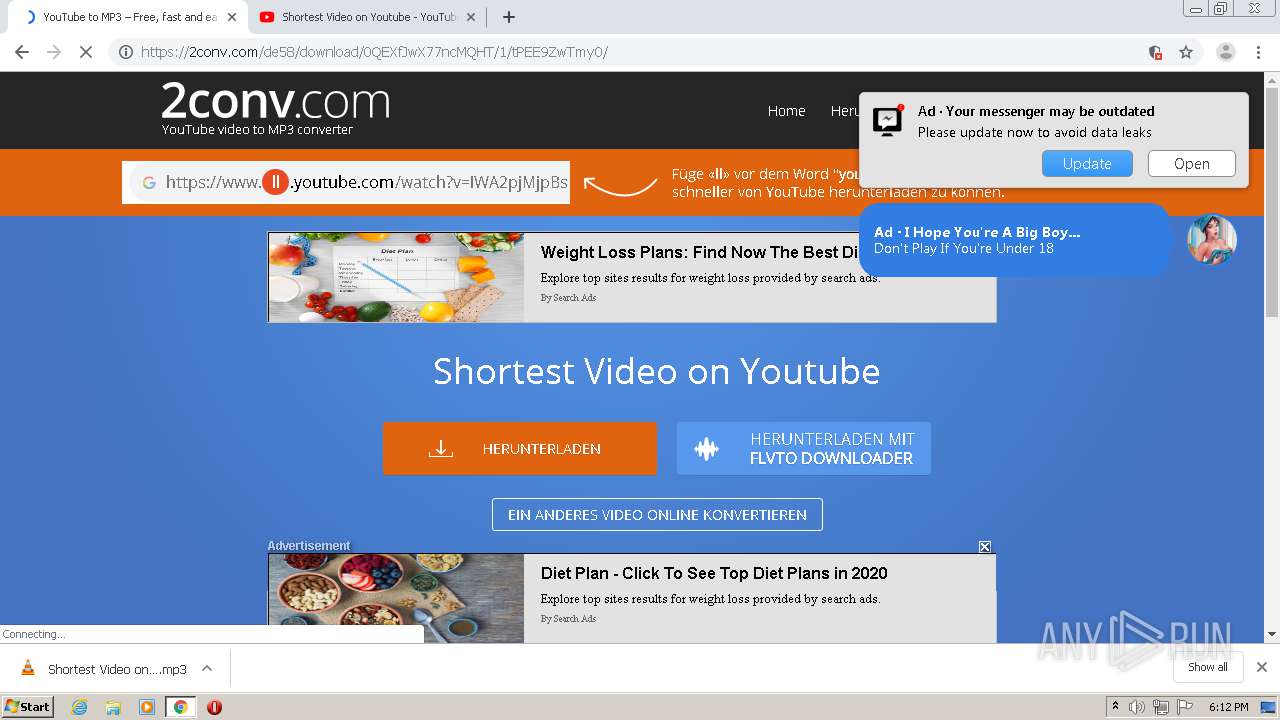
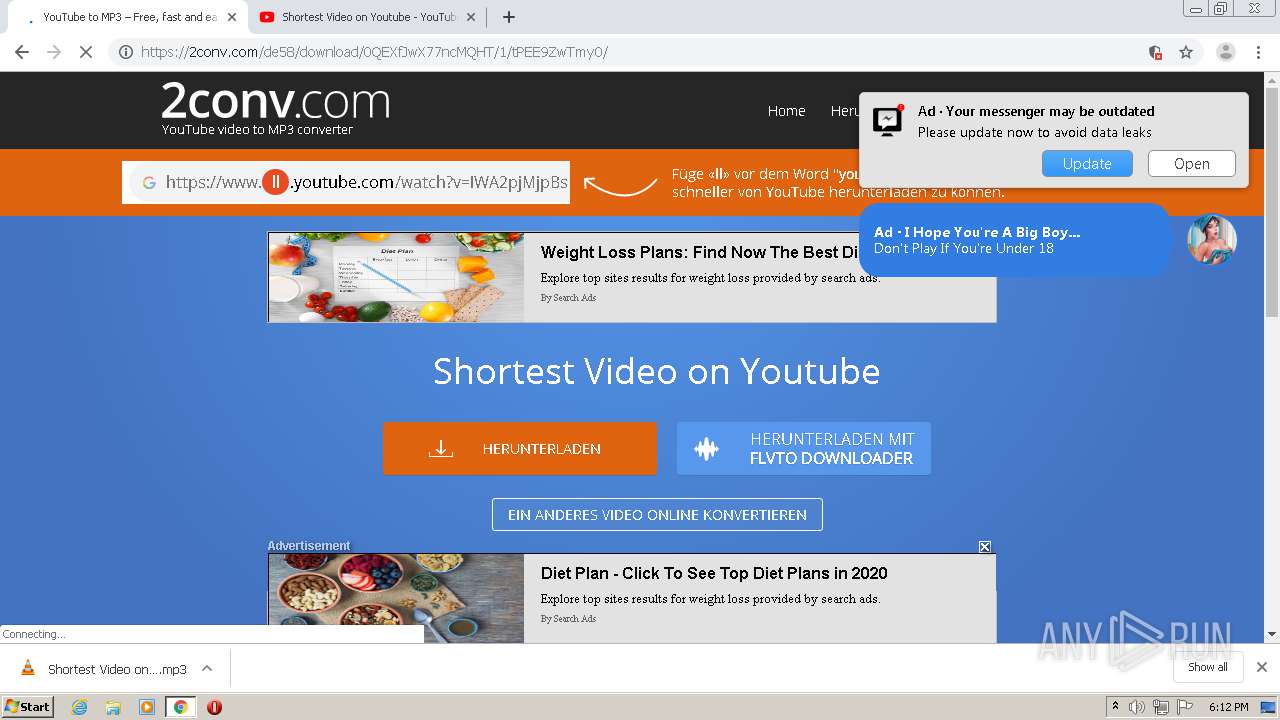
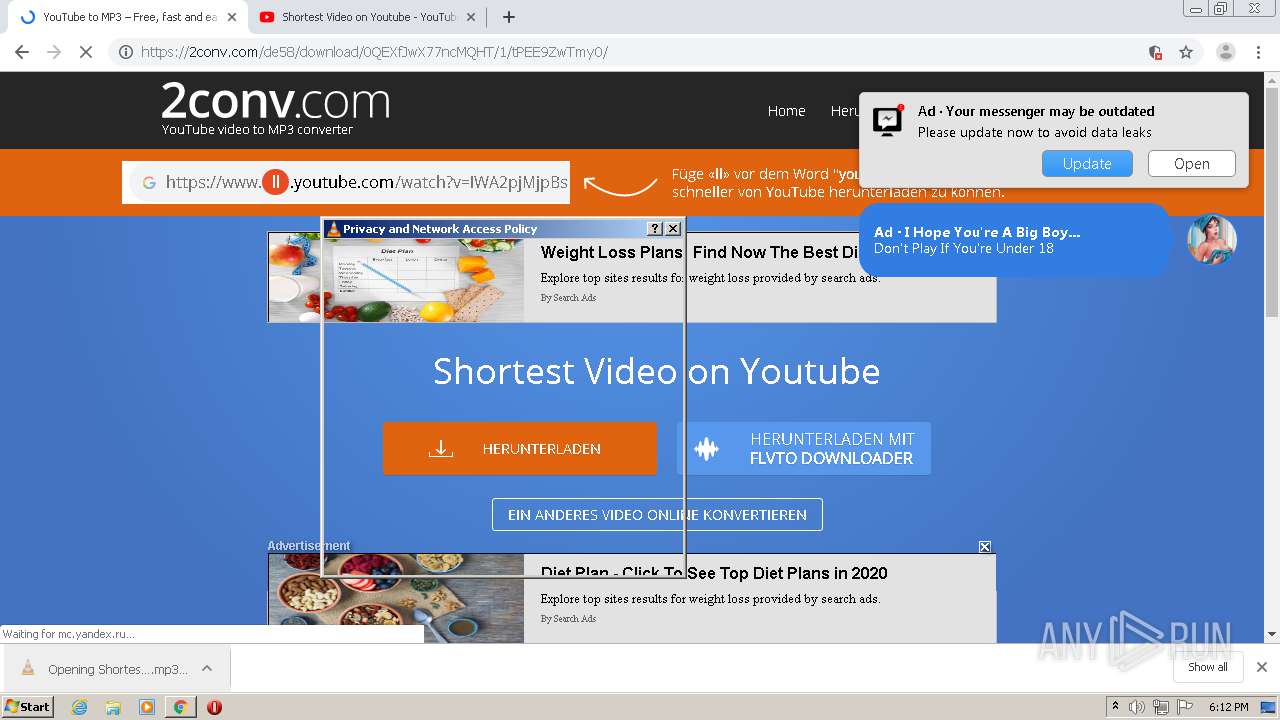
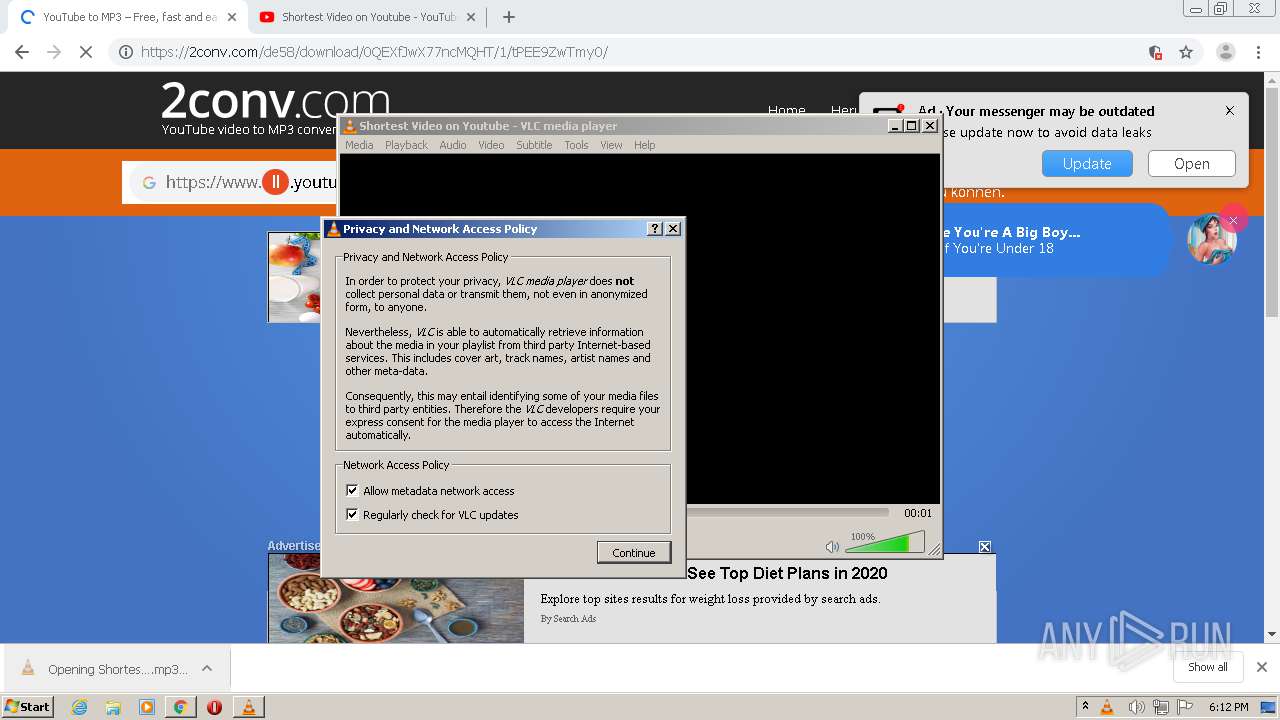
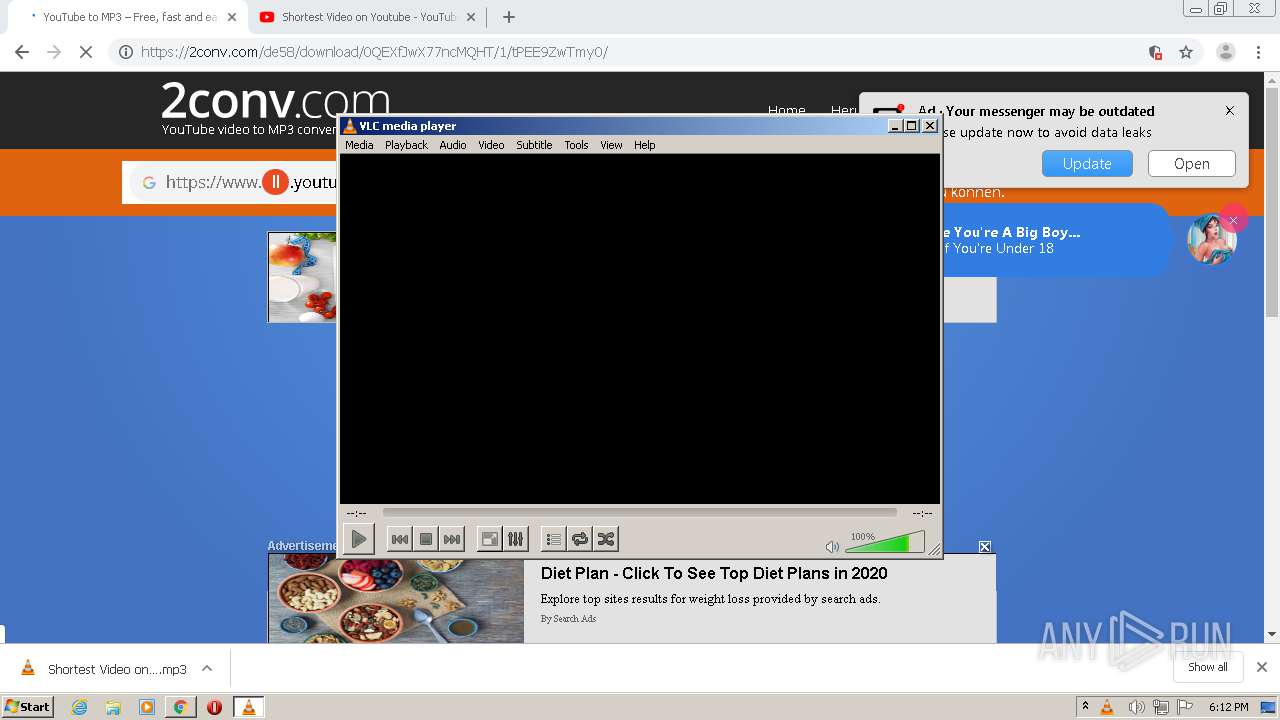
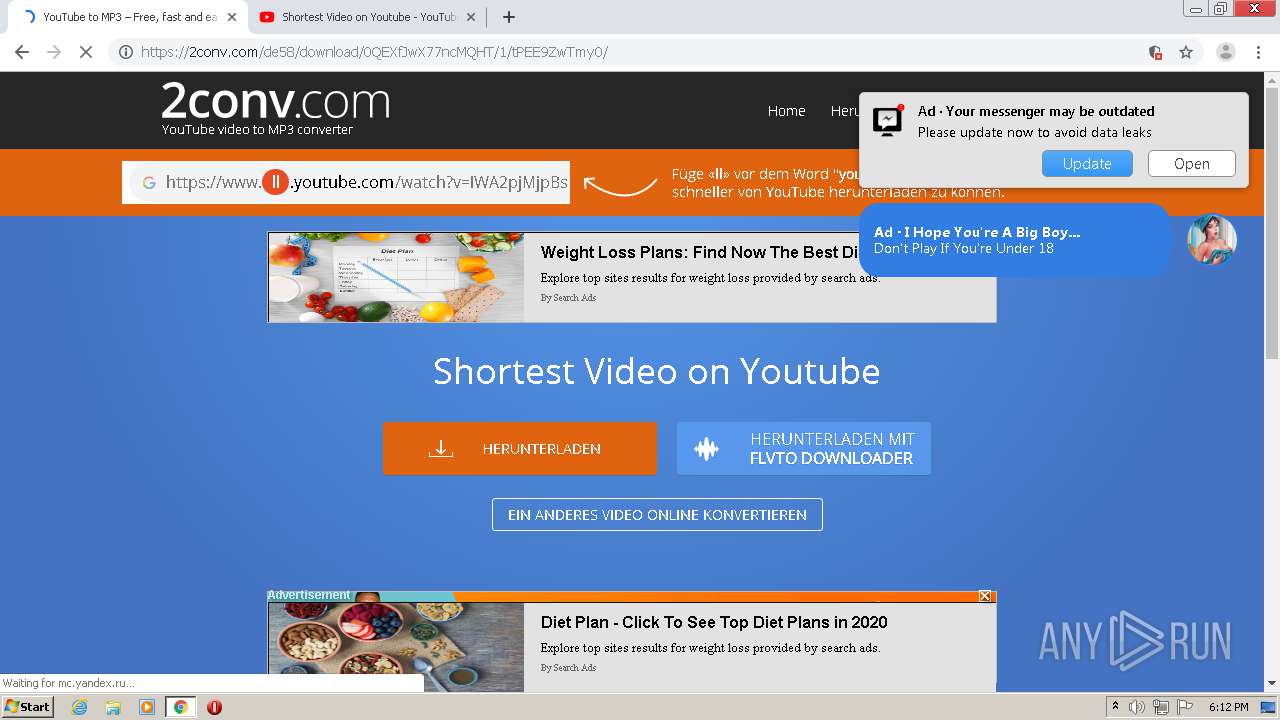
| URL: | https://2conv.com/de58/ |
| Full analysis: | https://app.any.run/tasks/08f10ed0-04fe-416d-bd12-14e303cec040 |
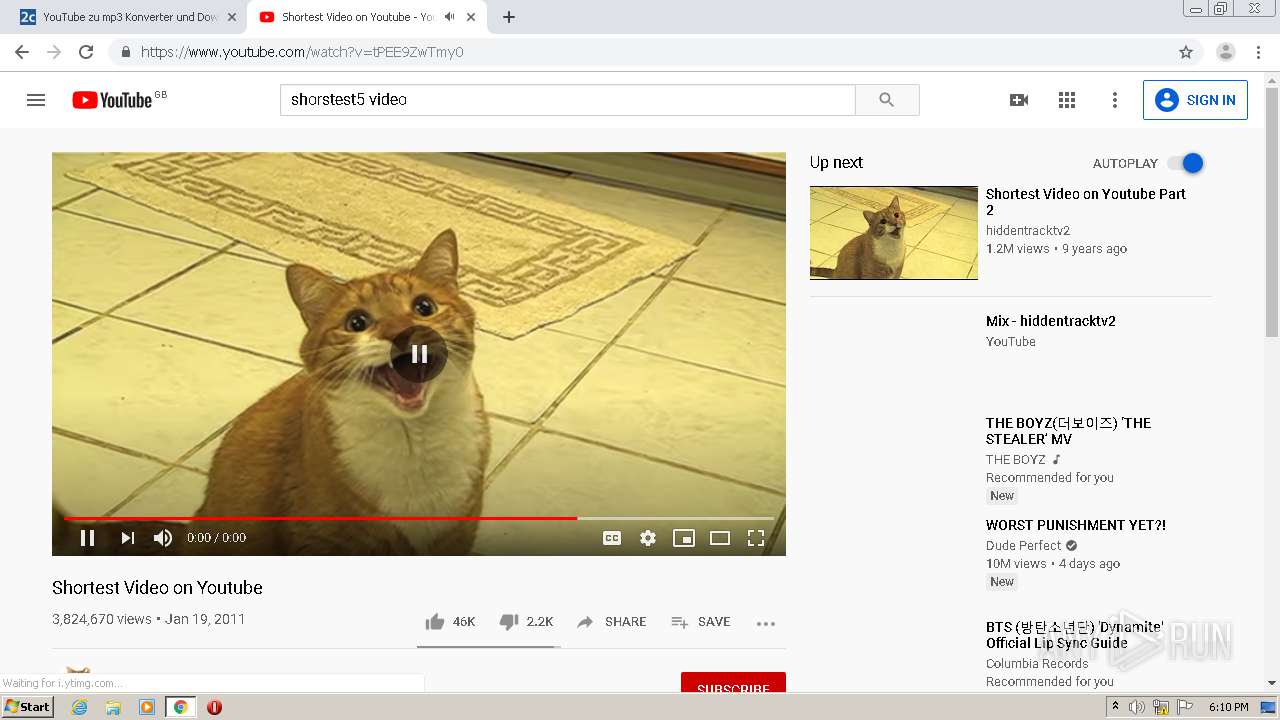
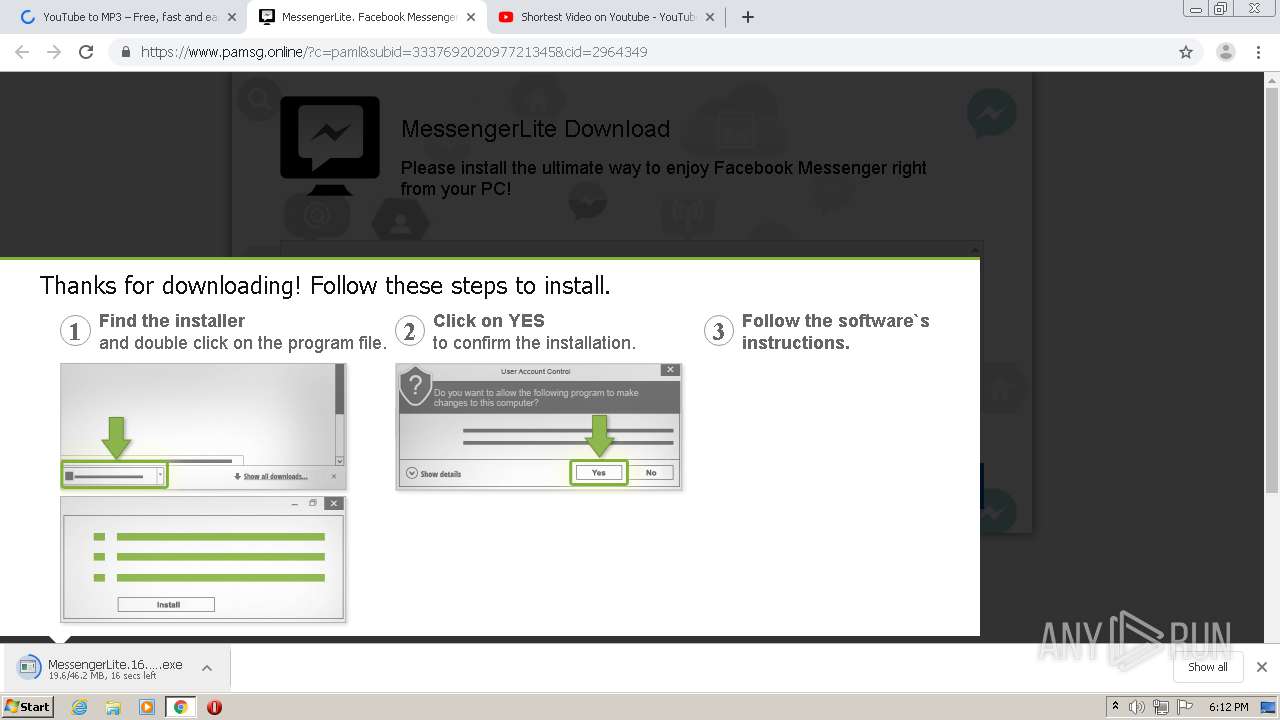
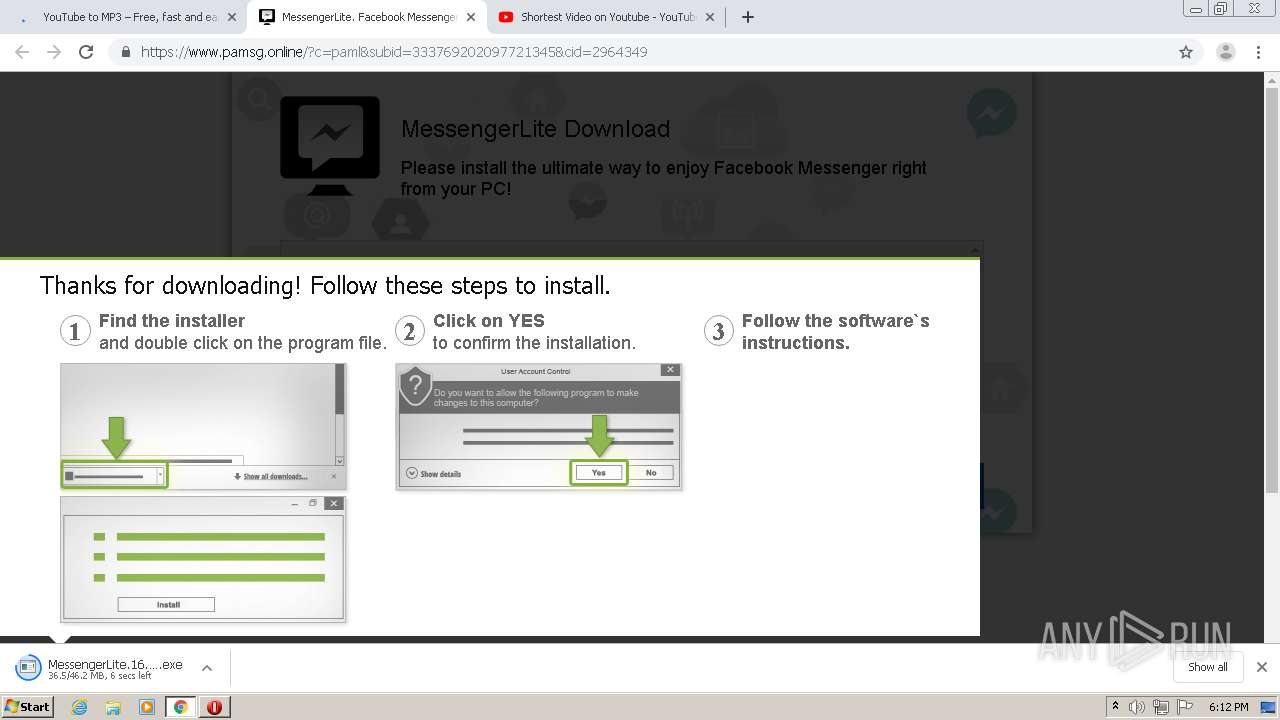
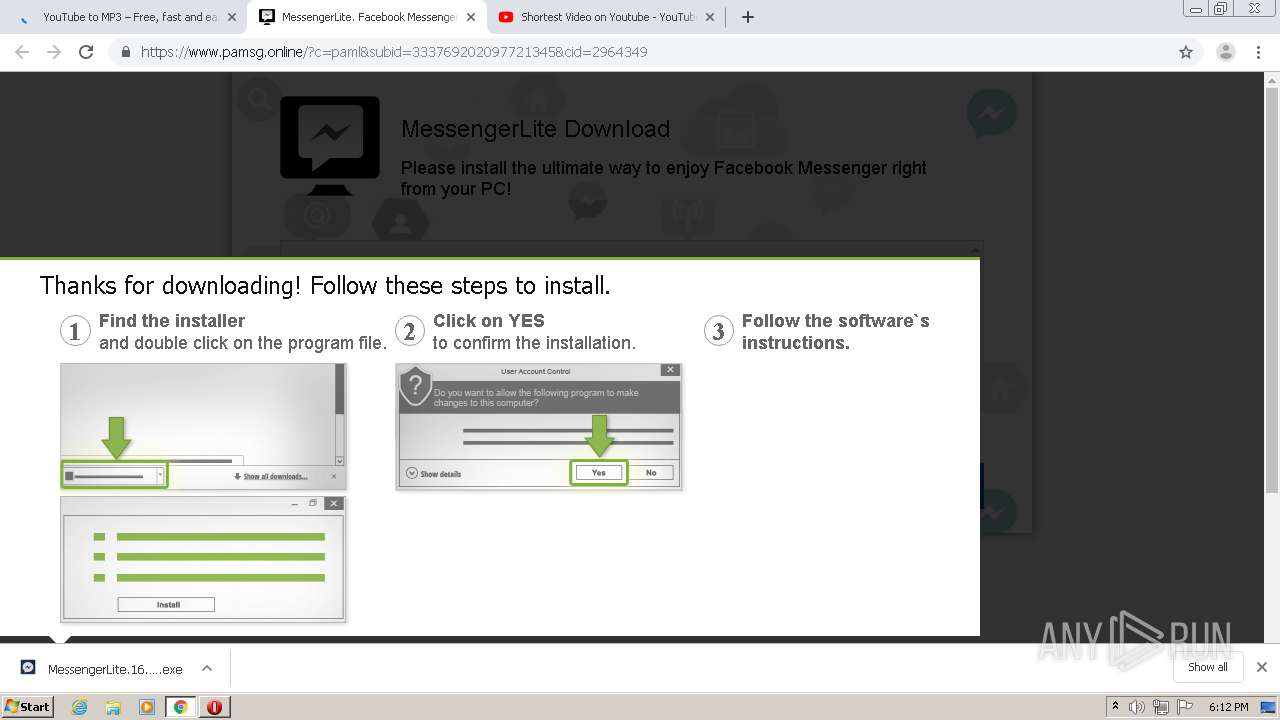
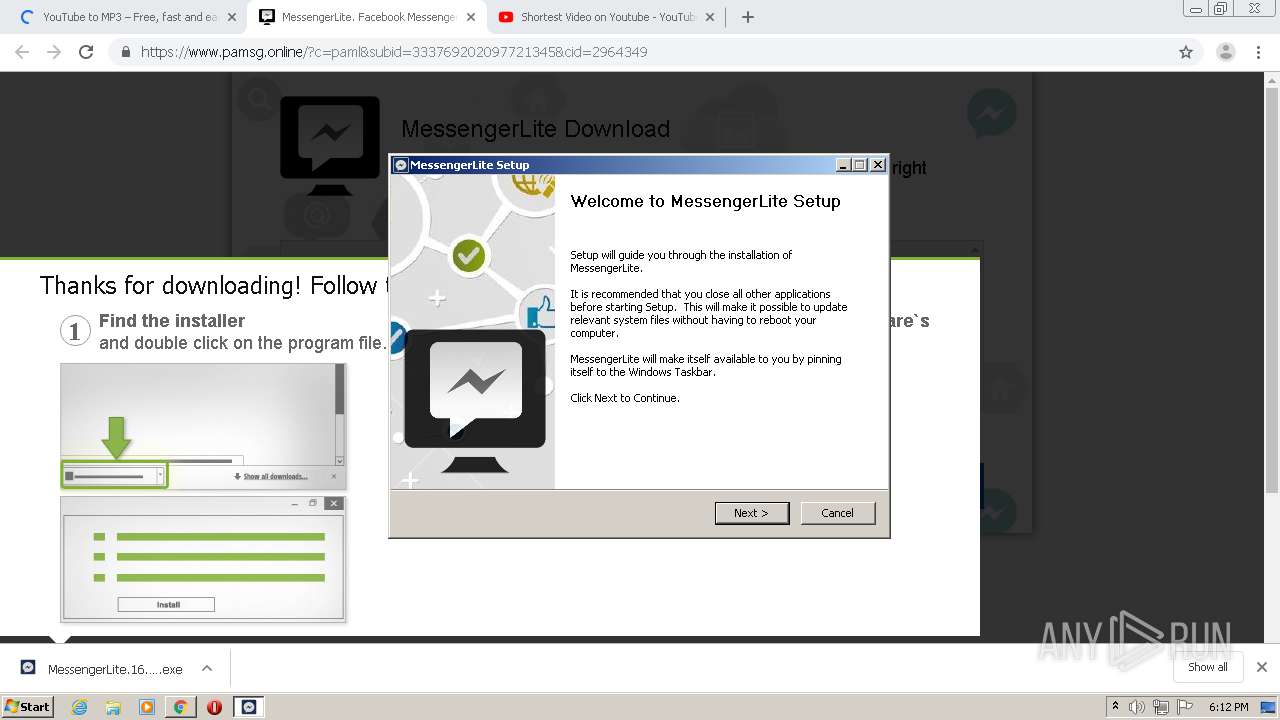
| Verdict: | Malicious activity |
| Analysis date: | September 26, 2020, 17:08:44 |
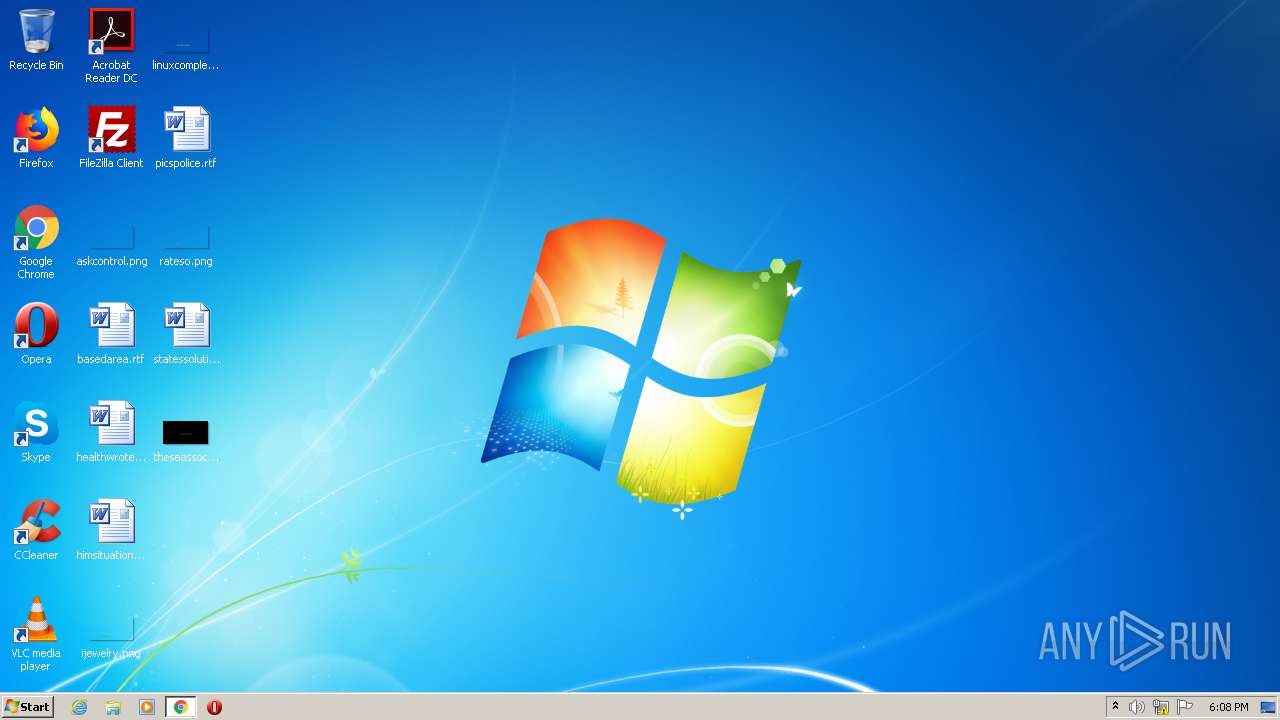
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FD3A0B3D86B24BFBF23AD1E90524640E |
| SHA1: | 014D6E9C5EC19086D931F185CE13A9A31B867655 |
| SHA256: | 724F2597A64EAC719860749B022E5A33503E01FE94217300D71F96B34423D678 |
| SSDEEP: | 3:N8LAQdKn:2LA3n |
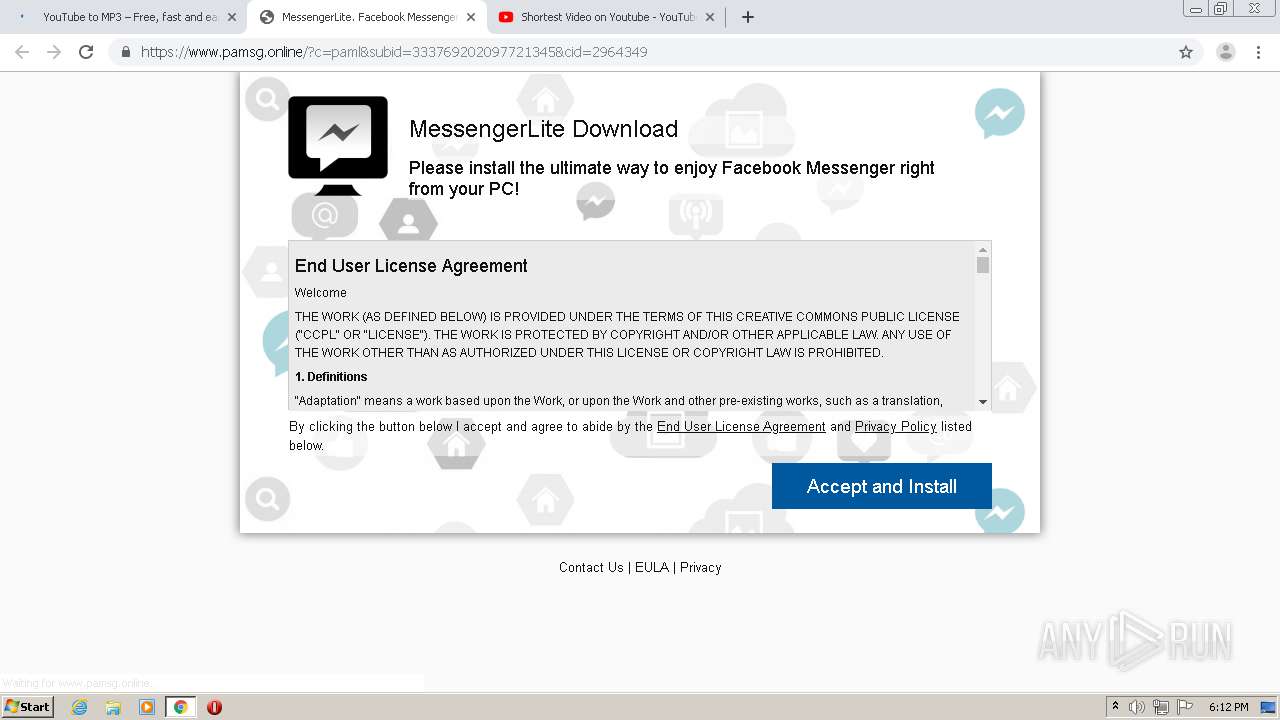
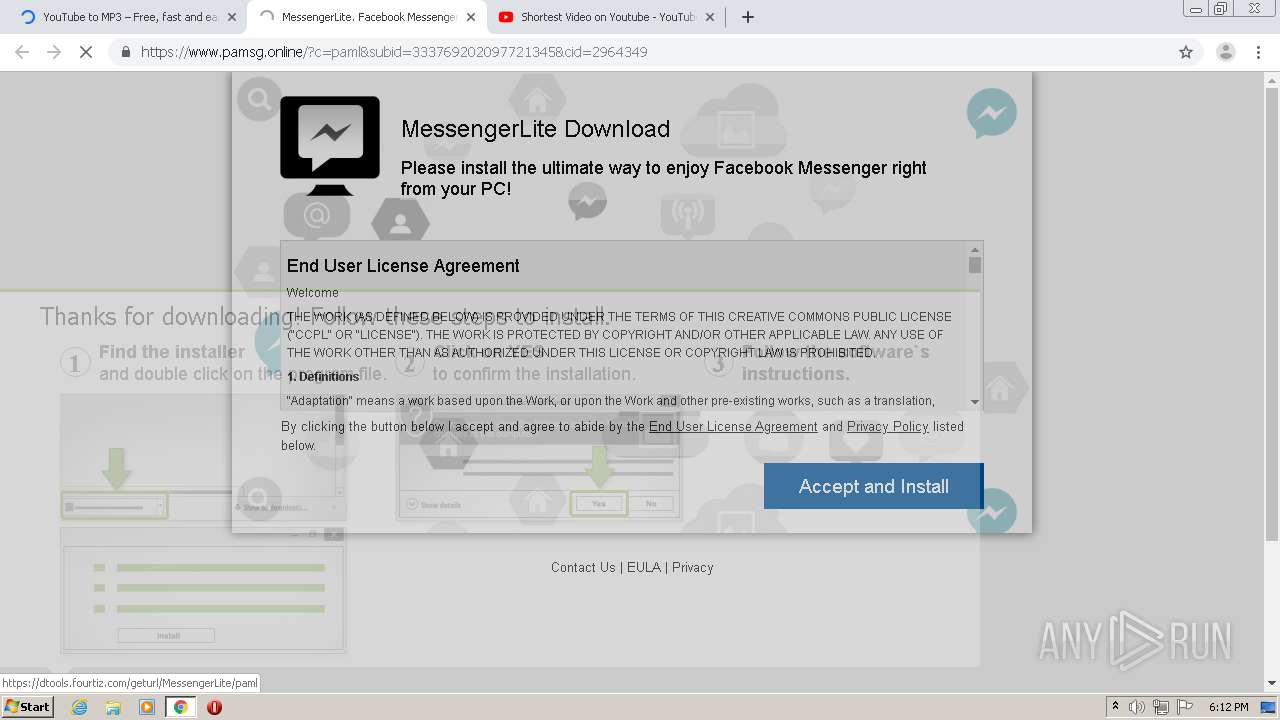
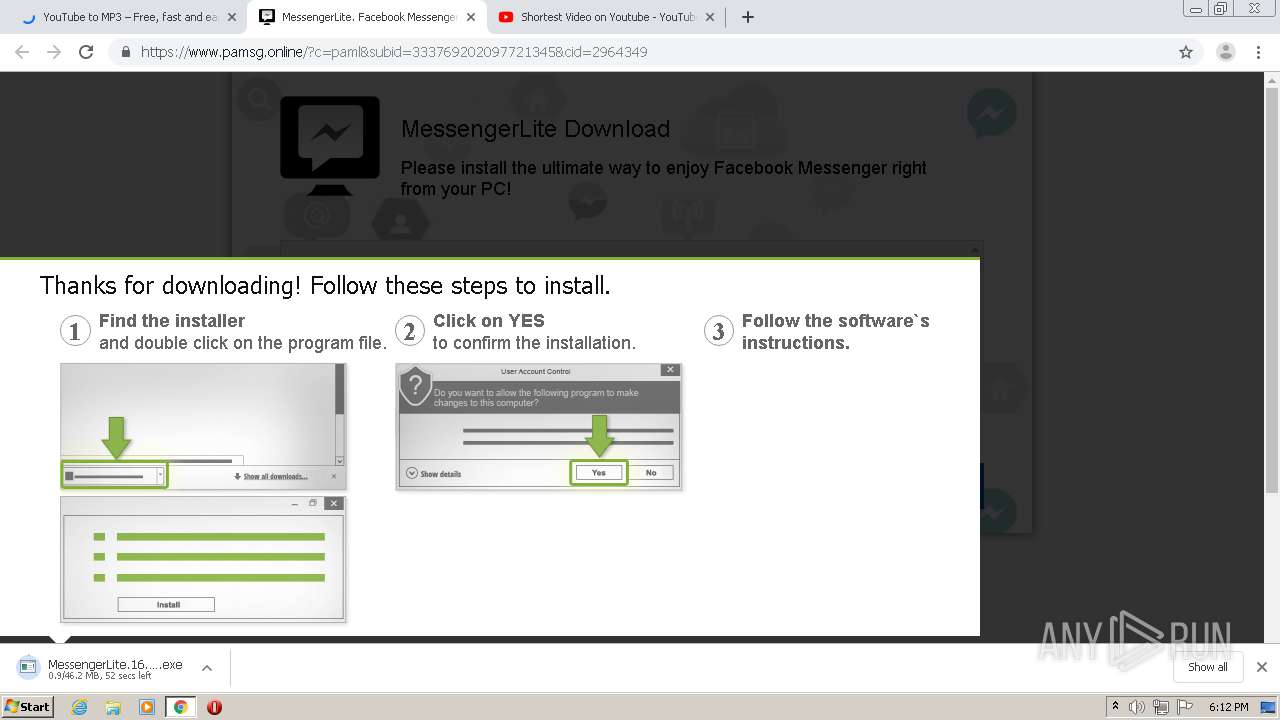
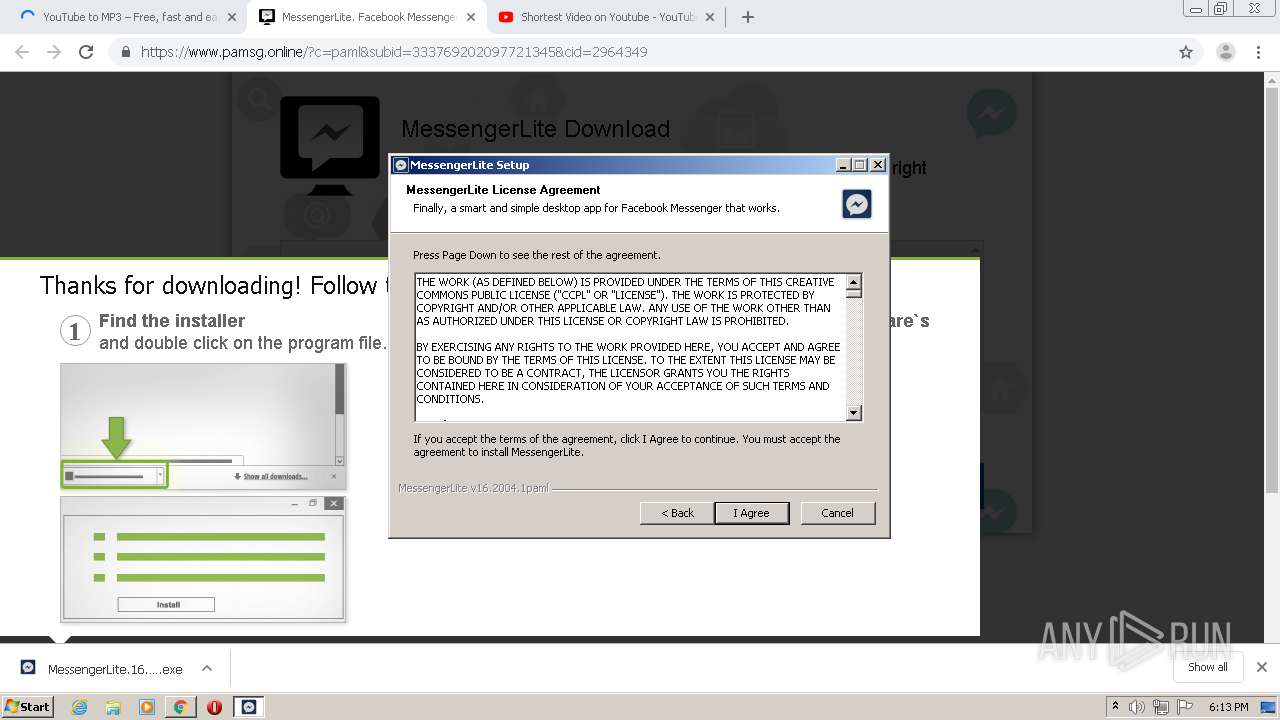
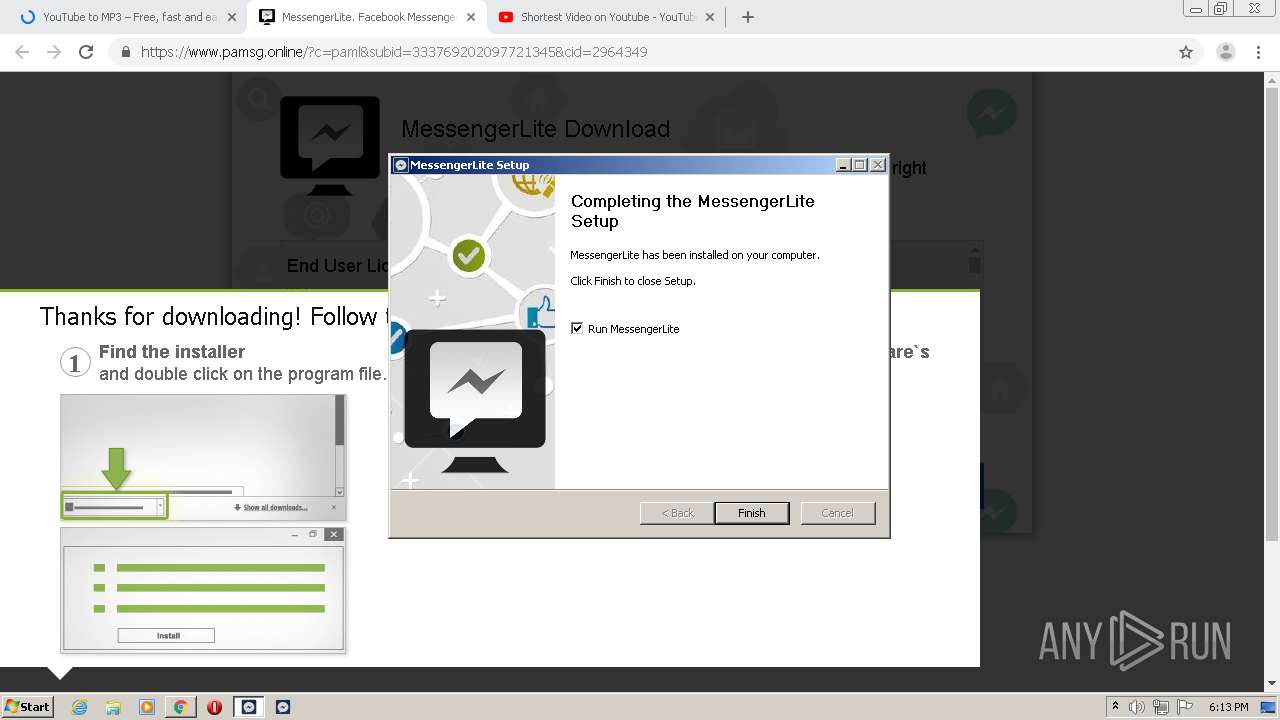
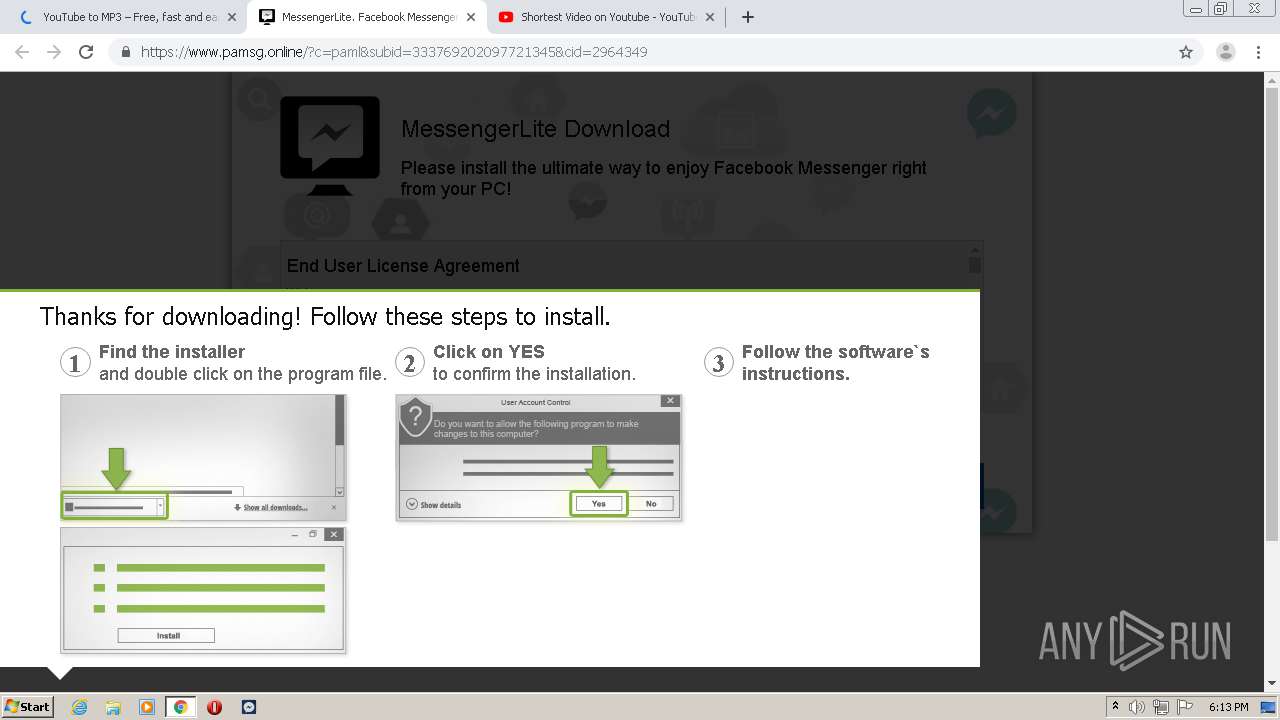
MALICIOUS
Application was dropped or rewritten from another process
- MessengerLite.16.2004.1paml.exe (PID: 3924)
- MessengerLite.16.2004.1paml.exe (PID: 3892)
- MessengerLite.exe (PID: 3036)
- MessengerLite.exe (PID: 2904)
- MessengerLite.exe (PID: 1508)
- MessengerLite.exe (PID: 3688)
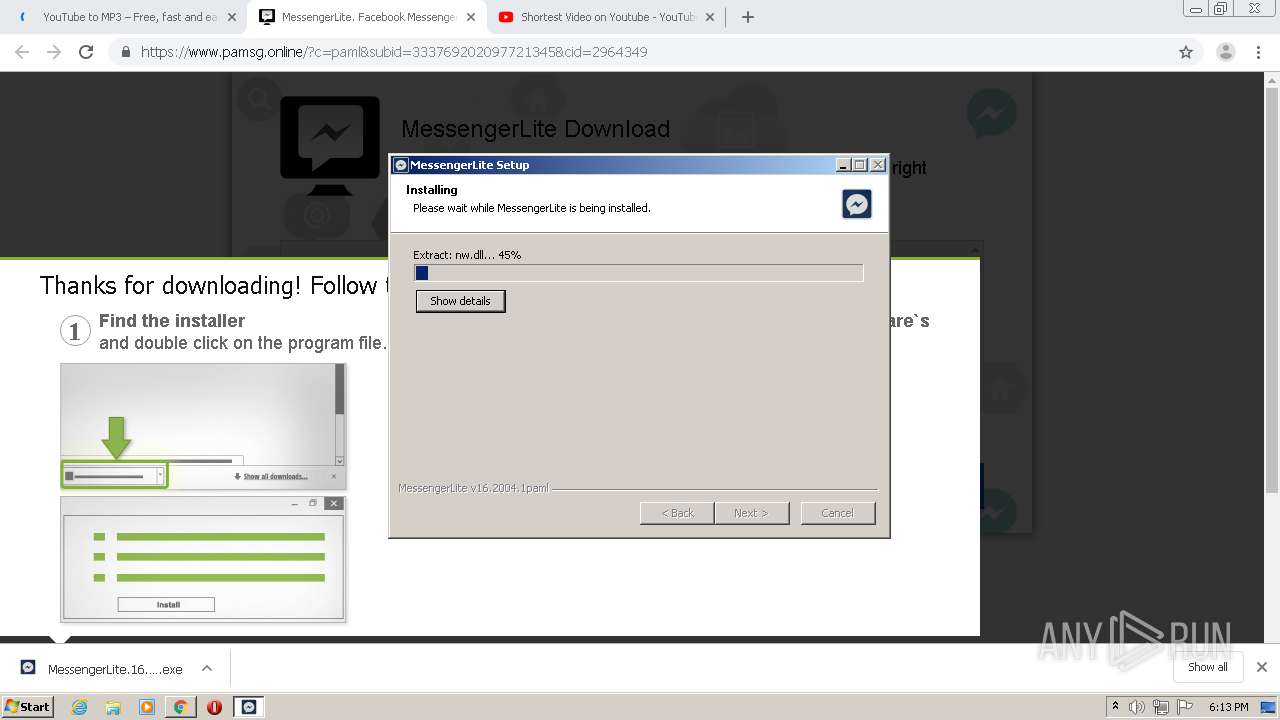
Loads dropped or rewritten executable
- MessengerLite.16.2004.1paml.exe (PID: 3892)
- MessengerLite.exe (PID: 2904)
- MessengerLite.exe (PID: 1508)
- MessengerLite.exe (PID: 3688)
- MessengerLite.exe (PID: 3036)
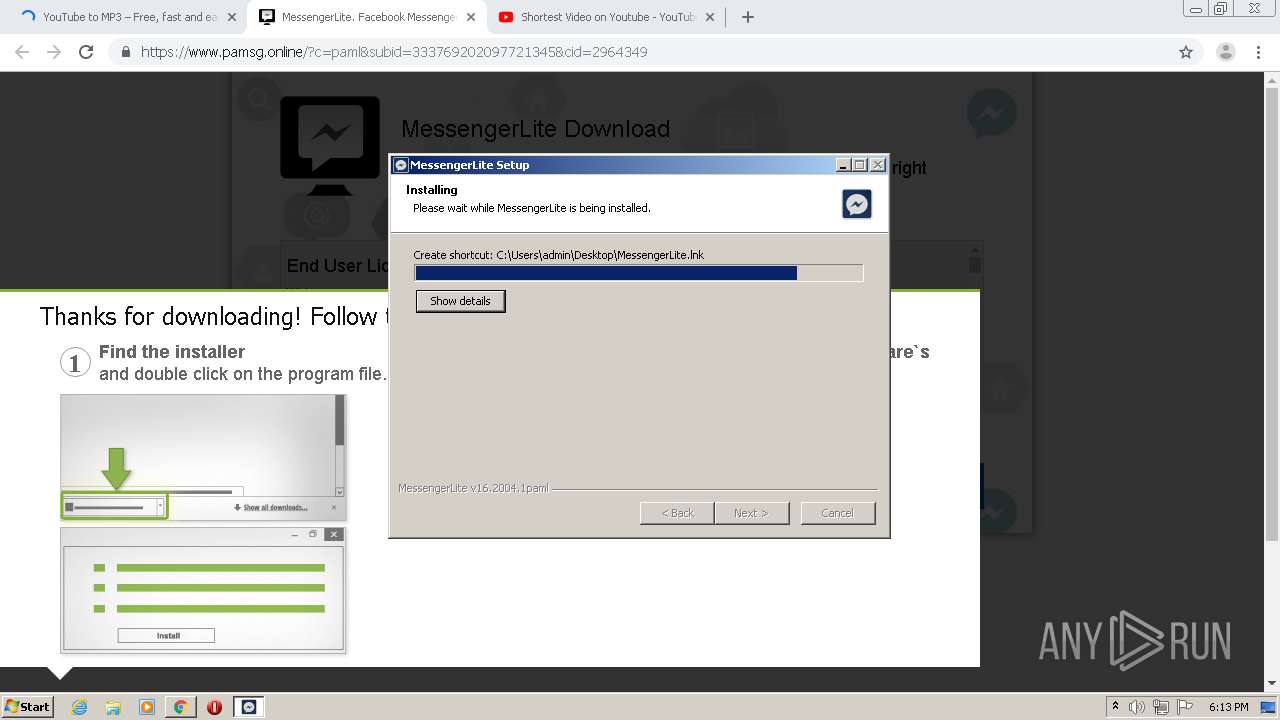
Changes the autorun value in the registry
- MessengerLite.16.2004.1paml.exe (PID: 3892)
Changes settings of System certificates
- MessengerLite.16.2004.1paml.exe (PID: 3892)
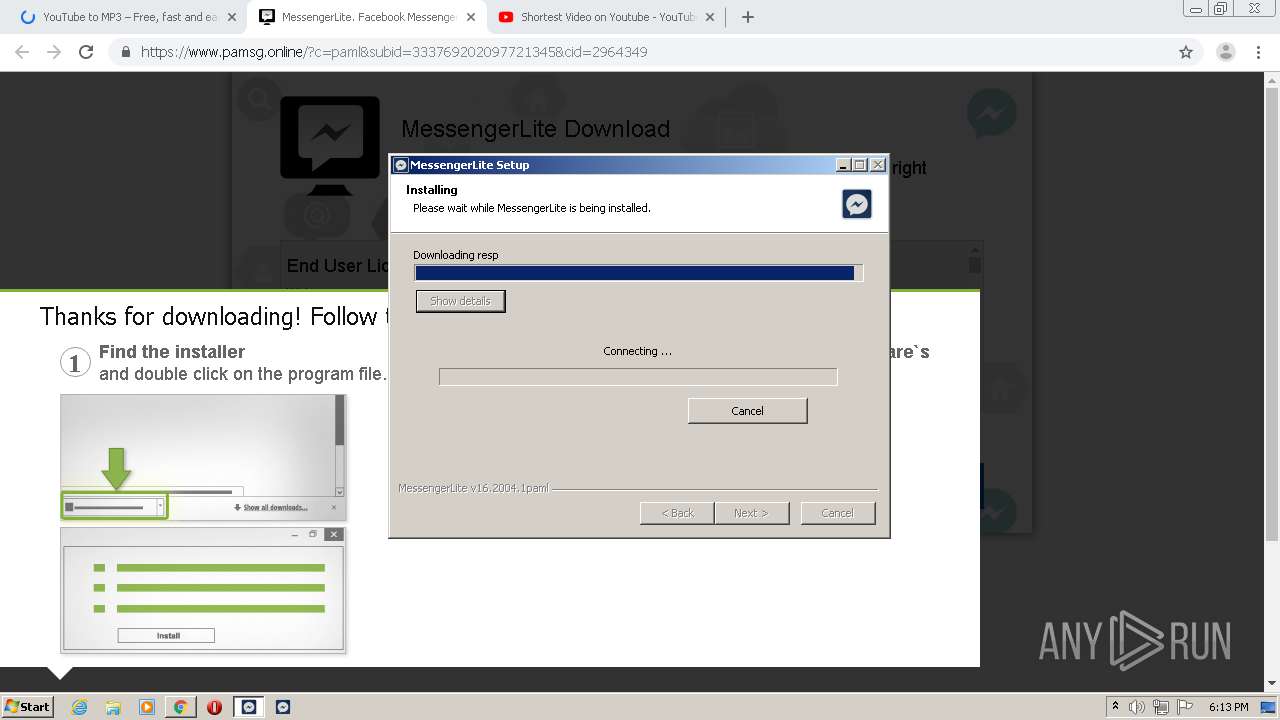
Actions looks like stealing of personal data
- MessengerLite.exe (PID: 2904)
SUSPICIOUS
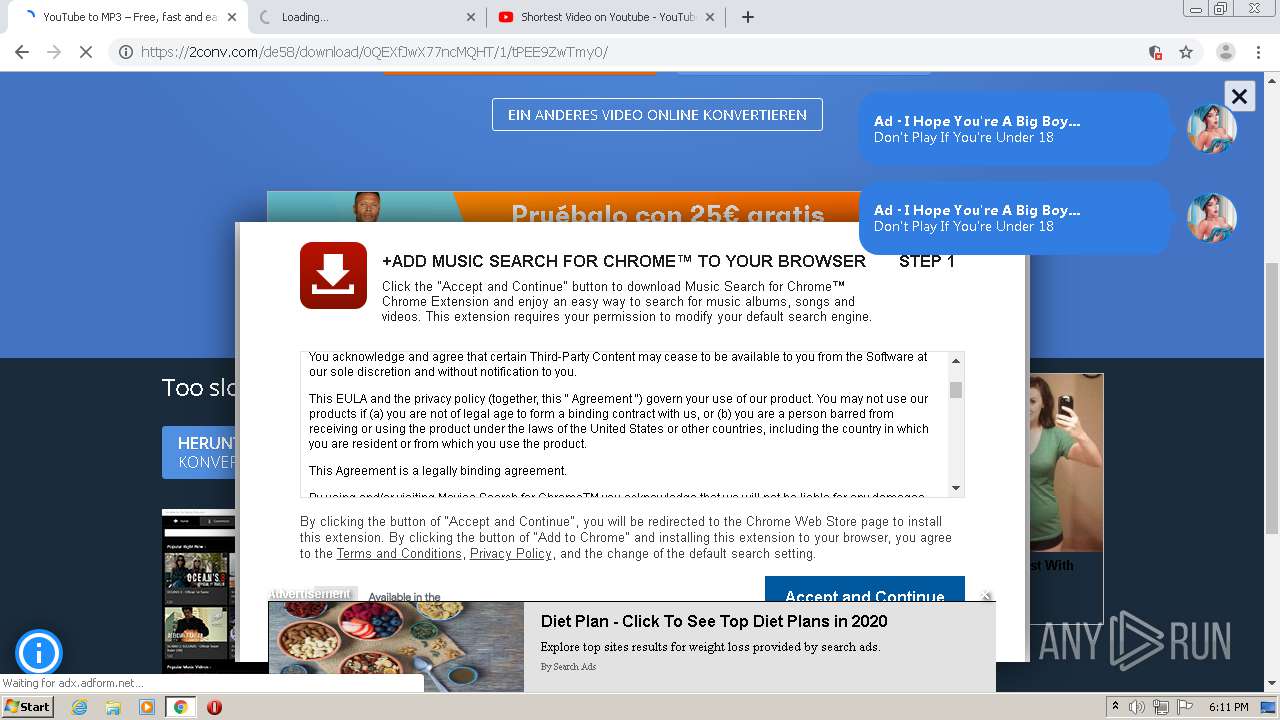
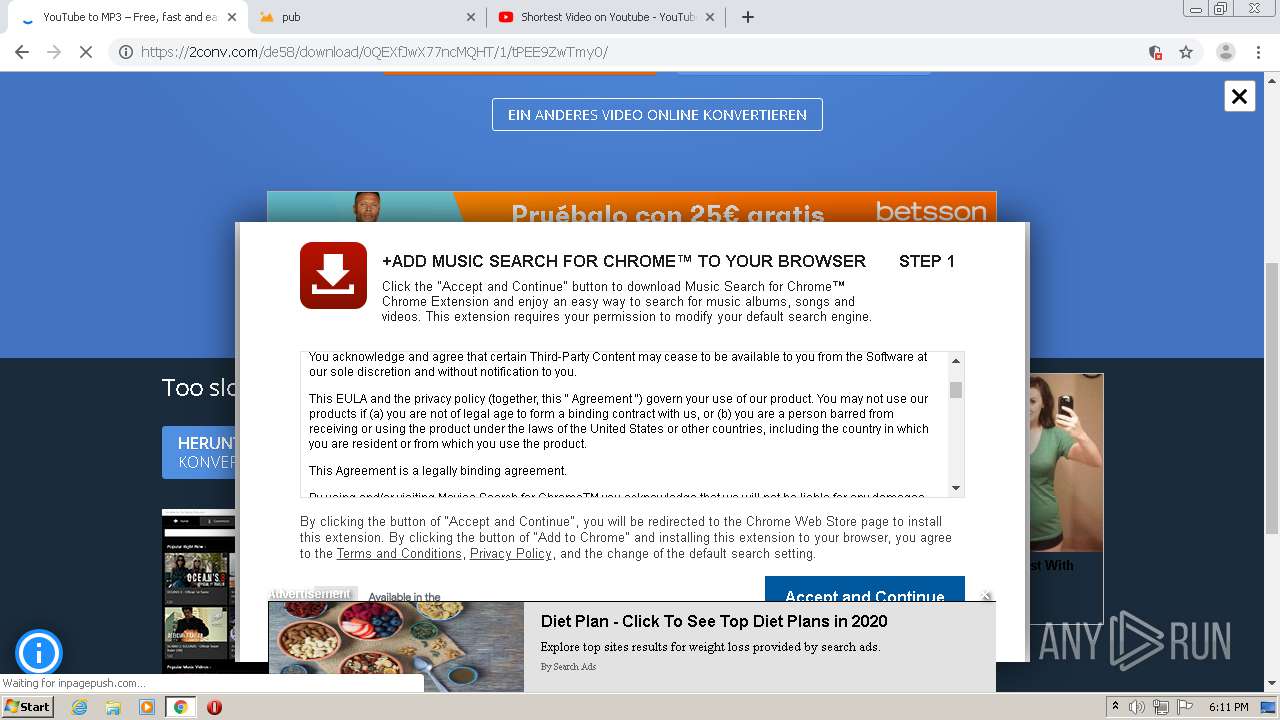
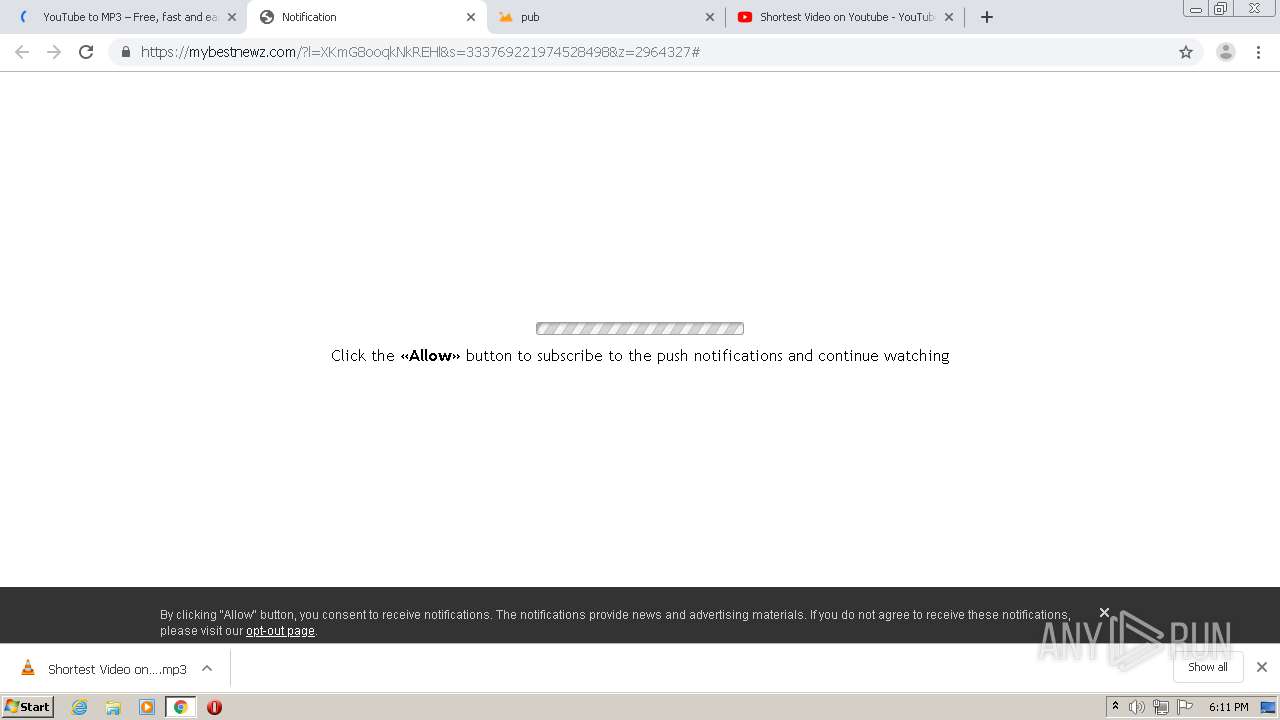
Modifies files in Chrome extension folder
- chrome.exe (PID: 2564)
Executable content was dropped or overwritten
- chrome.exe (PID: 2564)
- MessengerLite.16.2004.1paml.exe (PID: 3892)
Creates files in the user directory
- vlc.exe (PID: 3012)
- MessengerLite.16.2004.1paml.exe (PID: 3892)
Starts SC.EXE for service management
- cmd.exe (PID: 2728)
Reads Internet Cache Settings
- MessengerLite.16.2004.1paml.exe (PID: 3892)
Creates a software uninstall entry
- MessengerLite.16.2004.1paml.exe (PID: 3892)
Starts CMD.EXE for commands execution
- MessengerLite.16.2004.1paml.exe (PID: 3892)
Adds / modifies Windows certificates
- MessengerLite.16.2004.1paml.exe (PID: 3892)
Application launched itself
- MessengerLite.exe (PID: 2904)
Executed via COM
- explorer.exe (PID: 3252)
INFO
Application launched itself
- chrome.exe (PID: 2564)
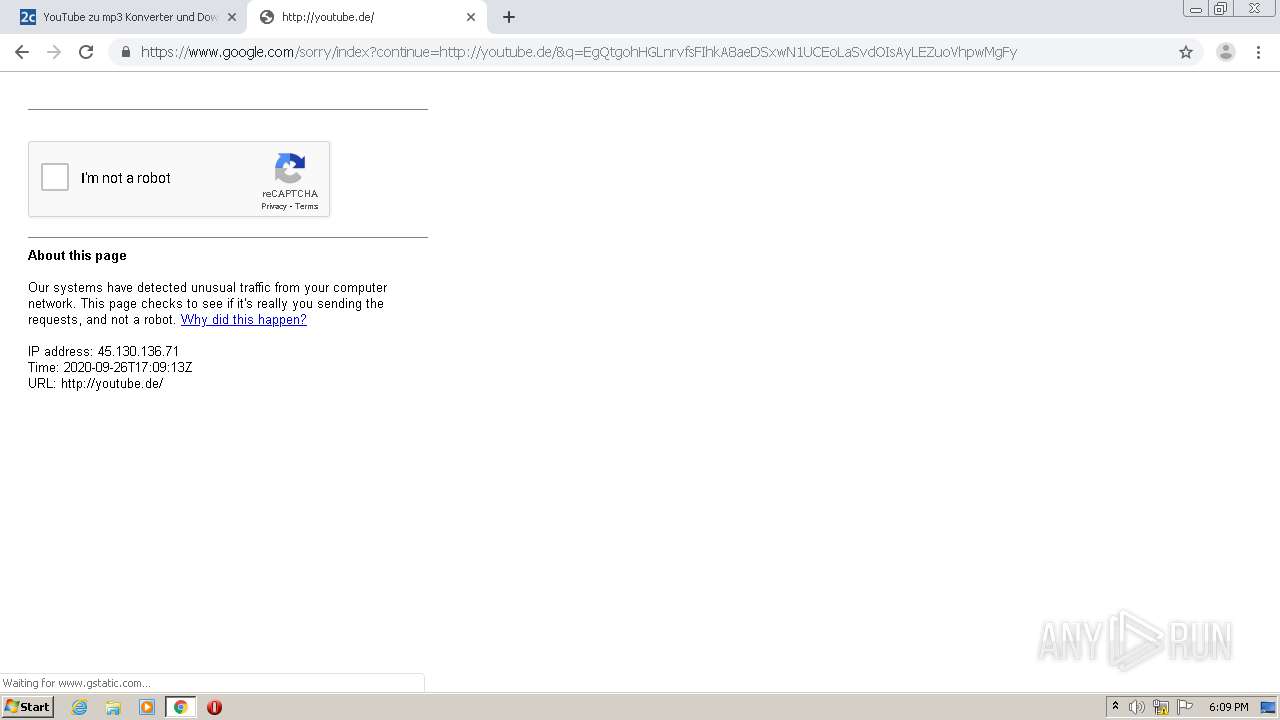
Reads the hosts file
- chrome.exe (PID: 1952)
- chrome.exe (PID: 2564)
- MessengerLite.exe (PID: 2904)
Reads settings of System Certificates
- chrome.exe (PID: 1952)
- chrome.exe (PID: 2564)
Changes settings of System certificates
- chrome.exe (PID: 1952)
Creates files in the user directory
- chrome.exe (PID: 2564)
Reads Internet Cache Settings
- chrome.exe (PID: 2564)
Dropped object may contain Bitcoin addresses
- MessengerLite.16.2004.1paml.exe (PID: 3892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
130
Monitored processes
89
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,12180522103082882563,3474610047477045134,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11276508496061391704 --renderer-client-id=74 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=760 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,12180522103082882563,3474610047477045134,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13551912875886618621 --renderer-client-id=46 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6048 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,12180522103082882563,3474610047477045134,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17273491950452680424 --renderer-client-id=66 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=7072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,12180522103082882563,3474610047477045134,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7784151986228947240 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4204 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,12180522103082882563,3474610047477045134,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7430936186815990799 --renderer-client-id=44 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5732 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,12180522103082882563,3474610047477045134,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6482985623953981355 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3748 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,12180522103082882563,3474610047477045134,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13213139776949992330 --renderer-client-id=49 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6040 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,12180522103082882563,3474610047477045134,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5317129633087326899 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2612 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,12180522103082882563,3474610047477045134,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5145610012582878462 --mojo-platform-channel-handle=3800 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,12180522103082882563,3474610047477045134,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11275521073878329337 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4204 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 183
Read events
1 993
Write events
185
Delete events
5
Modification events
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2564-13245613738349125 |
Value: 259 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
14
Suspicious files
368
Text files
812
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF207a16.TMP | — | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\925bfd34-21e5-4ded-9079-5b48bd82a1f9.tmp | — | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF2079c8.TMP | text | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF207bbc.TMP | — | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
62
TCP/UDP connections
387
DNS requests
236
Threats
90
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
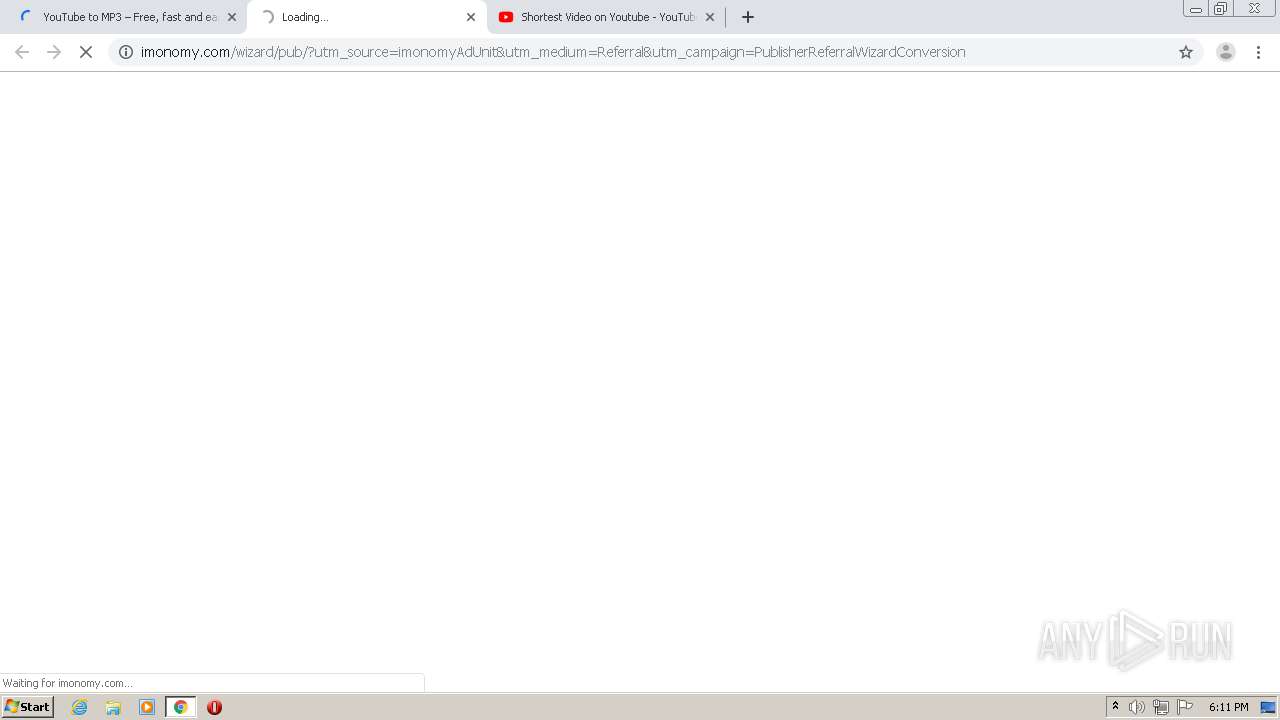
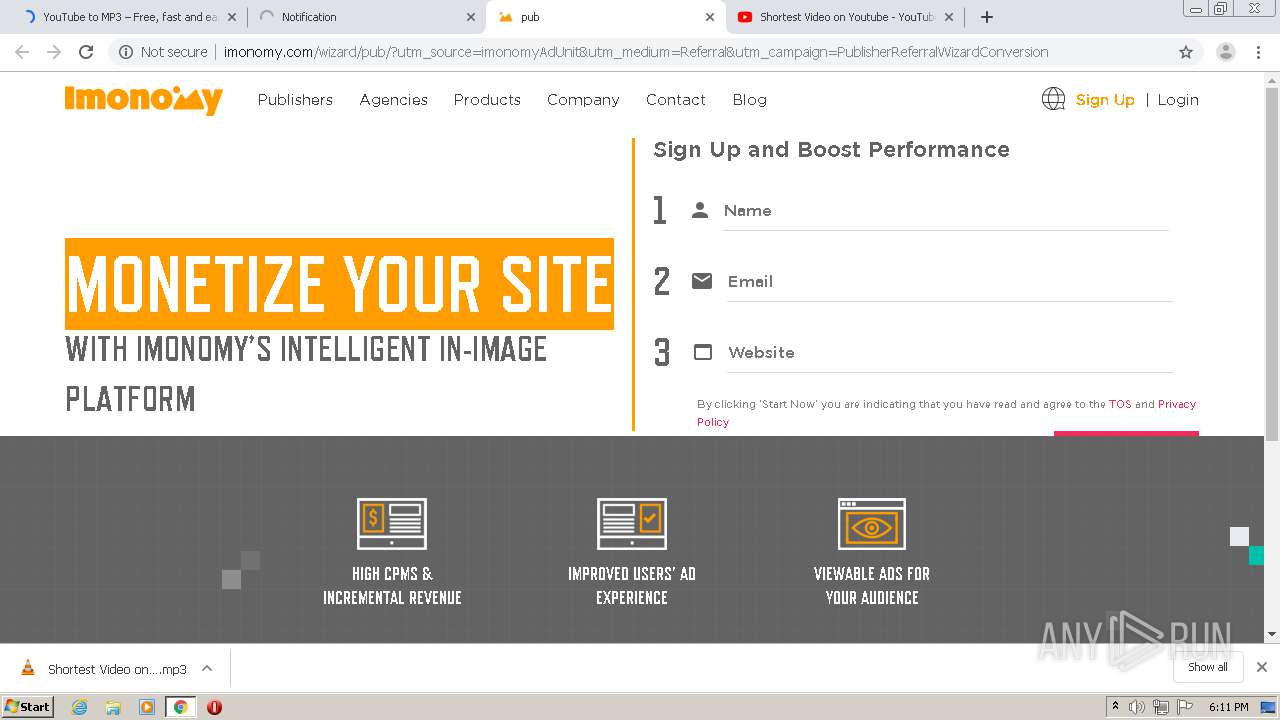
1952 | chrome.exe | GET | 200 | 52.6.162.102:80 | http://imonomy.com/wizard/pub/?utm_source=imonomyAdUnit&utm_medium=Referral&utm_campaign=PublisherReferralWizardConversion | US | html | 7.52 Kb | whitelisted |
1952 | chrome.exe | GET | 200 | 52.6.162.102:80 | http://imonomy.com/wp-content/themes/imonomy/css/style.css?x51181 | US | text | 21.9 Kb | whitelisted |
1952 | chrome.exe | GET | 200 | 52.6.162.102:80 | http://imonomy.com/wp-content/themes/imonomy/css/press.css?x51181 | US | text | 10.3 Kb | whitelisted |
1952 | chrome.exe | GET | 200 | 52.6.162.102:80 | http://imonomy.com/wp-content/themes/imonomy/libs/selectric/selectric.css?x51181 | US | text | 898 b | whitelisted |
1952 | chrome.exe | GET | 200 | 52.6.162.102:80 | http://imonomy.com/wp-content/themes/imonomy/libs/fullPage/jquery.fullpage.min.css?x51181 | US | text | 1.16 Kb | whitelisted |
1952 | chrome.exe | GET | 200 | 52.6.162.102:80 | http://imonomy.com/wp-content/themes/imonomy/libs/slick/slick.css?x51181 | US | text | 560 b | whitelisted |
1952 | chrome.exe | GET | 200 | 52.6.162.102:80 | http://imonomy.com/wp-content/themes/imonomy/style.css?x51181 | US | text | 2.35 Kb | whitelisted |
1952 | chrome.exe | GET | 304 | 2.16.106.186:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 57.0 Kb | whitelisted |
1952 | chrome.exe | GET | 302 | 216.58.207.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
1952 | chrome.exe | GET | 304 | 2.16.106.186:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 57.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1952 | chrome.exe | 216.58.212.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1952 | chrome.exe | 94.237.53.171:443 | 2conv.com | — | FI | unknown |
1952 | chrome.exe | 135.181.25.163:443 | mtmo.cc | — | CA | unknown |
1952 | chrome.exe | 172.217.16.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
1952 | chrome.exe | 172.217.23.132:443 | www.google.com | Google Inc. | US | whitelisted |
1952 | chrome.exe | 172.217.22.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
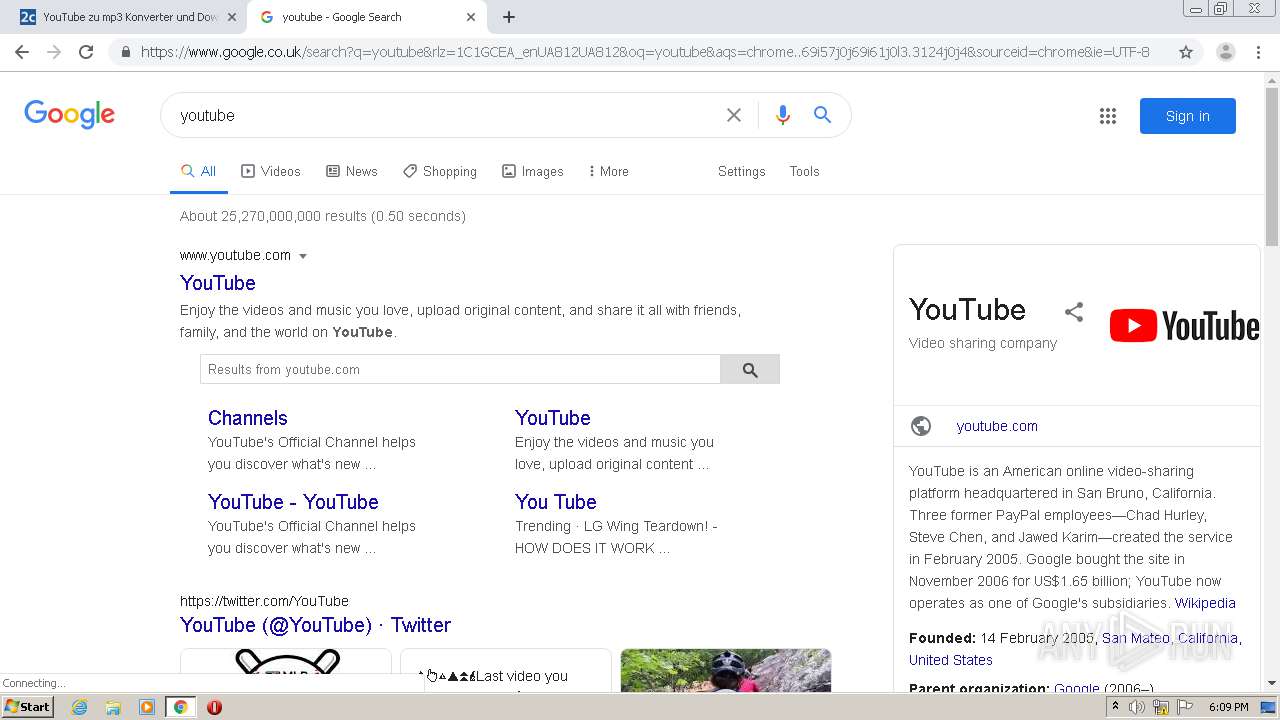
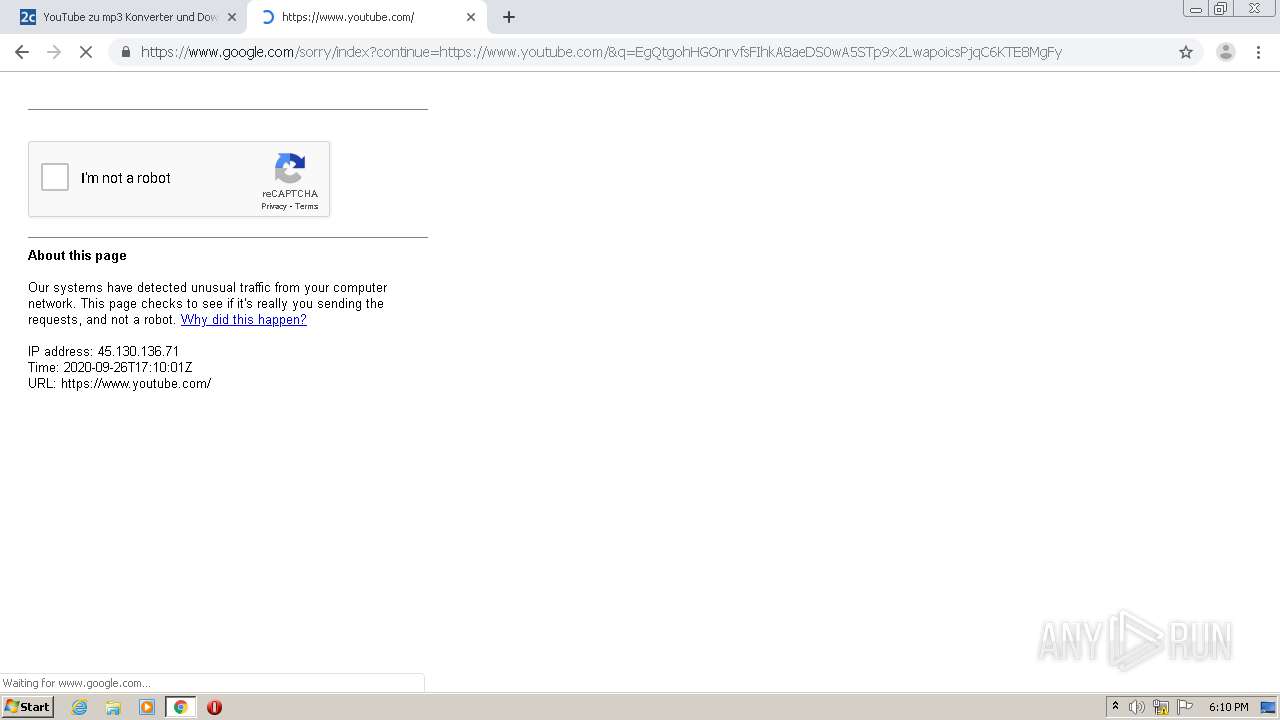
1952 | chrome.exe | 172.217.22.35:443 | www.google.co.uk | Google Inc. | US | whitelisted |
1952 | chrome.exe | 172.217.18.14:443 | apis.google.com | Google Inc. | US | whitelisted |
1952 | chrome.exe | 142.250.74.206:443 | ogs.google.co.uk | Google Inc. | US | whitelisted |
1952 | chrome.exe | 172.217.23.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
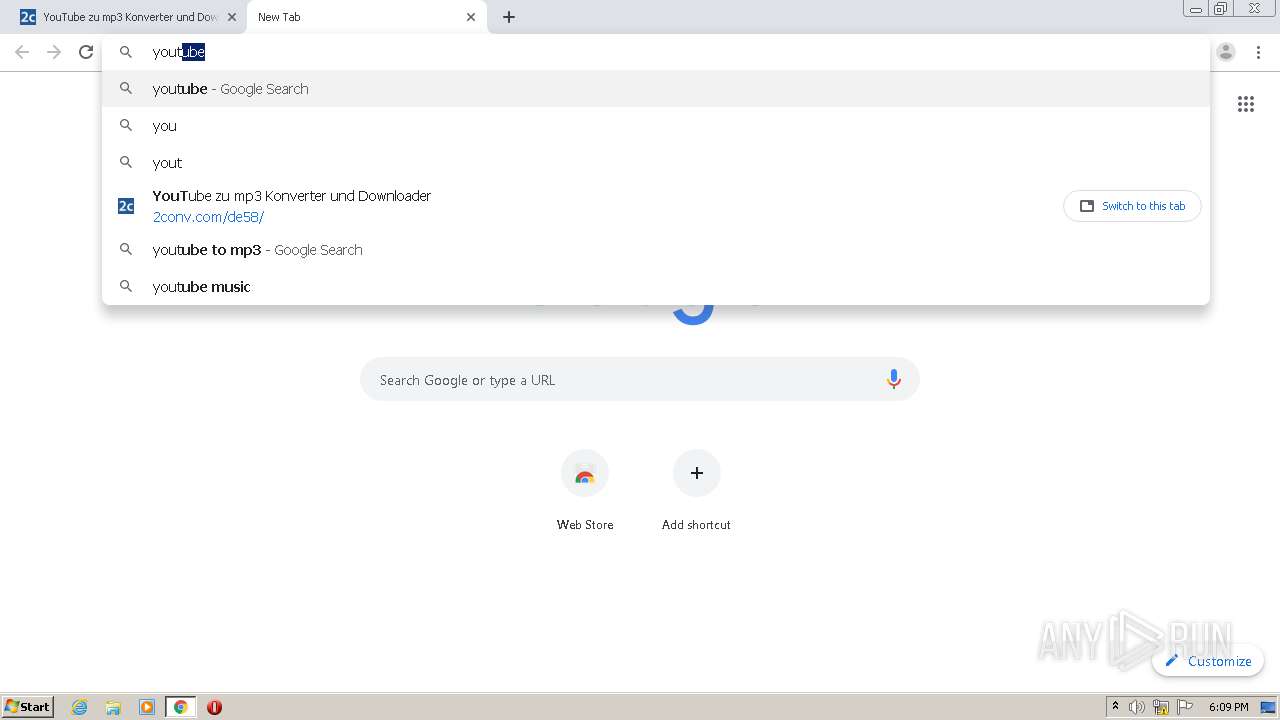
2conv.com |
| suspicious |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
cdn.2conv.com |
| malicious |
adcampo.com |
| unknown |
fonts.gstatic.com |
| whitelisted |
static.2conv.com |
| unknown |
mtmo.cc |
| unknown |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1952 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
Process | Message |
|---|---|
vlc.exe | core libvlc: one instance mode ENABLED
|
vlc.exe | core libvlc: Running vlc with the default interface. Use 'cvlc' to use vlc without interface.
|