| File name: | 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn |
| Full analysis: | https://app.any.run/tasks/00581e44-89b3-448c-840e-a07f6a797745 |
| Verdict: | Malicious activity |
| Analysis date: | May 18, 2025, 20:52:17 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 7AE97EE453C5ECA997A3107C607A85B2 |
| SHA1: | DD565336F53741454C346B94C83281687073F5B9 |
| SHA256: | 7246611A0CE4995E99A14EEE7C98F5E727783B96FAD4E83A977FBFDF49990E8C |
| SSDEEP: | 98304:5cuNcBDYPl8pCiRhUVQ5OHiYOMaE81ATMI8CI0ZTdK1WjopyJ2JWhCrBTA5OHo4R:HanpqDn5pfobNtlI6gYcTe1ztDt |
MALICIOUS
JEEFO has been detected
- icsys.icn.exe (PID: 7884)
- 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe (PID: 7840)
- explorer.exe (PID: 7932)
- svchost.exe (PID: 7972)
Changes the autorun value in the registry
- explorer.exe (PID: 7932)
- svchost.exe (PID: 7972)
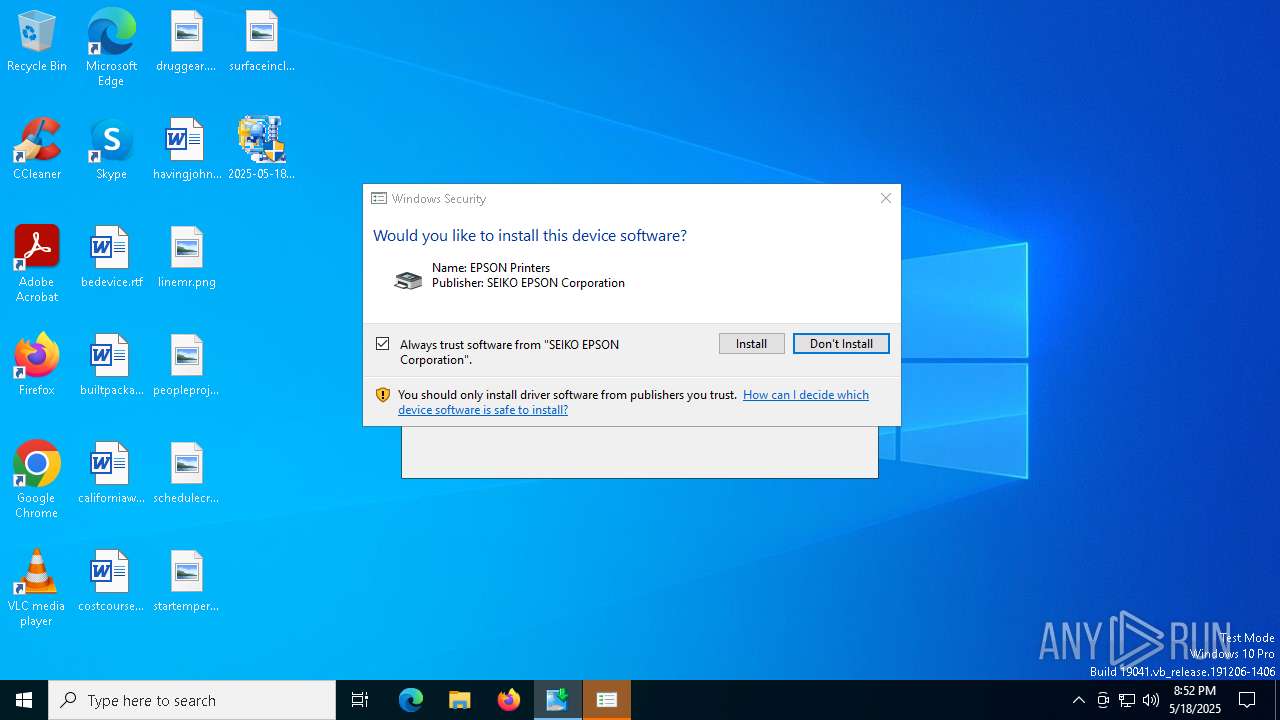
Executing a file with an untrusted certificate
- DEVICEOP.EXE (PID: 6184)
SUSPICIOUS
Starts itself from another location
- 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe (PID: 7840)
- icsys.icn.exe (PID: 7884)
- explorer.exe (PID: 7932)
- spoolsv.exe (PID: 7952)
- svchost.exe (PID: 7972)
Executable content was dropped or overwritten
- 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe (PID: 7840)
- icsys.icn.exe (PID: 7884)
- explorer.exe (PID: 7932)
- spoolsv.exe (PID: 7952)
- 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe (PID: 7864)
- SETUP64.EXE (PID: 8088)
- drvinst.exe (PID: 1056)
Starts application with an unusual extension
- 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe (PID: 7840)
The process creates files with name similar to system file names
- icsys.icn.exe (PID: 7884)
- spoolsv.exe (PID: 7952)
Reads security settings of Internet Explorer
- 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe (PID: 7864)
- SETUP64.EXE (PID: 8088)
Process drops legitimate windows executable
- 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe (PID: 7864)
- SETUP64.EXE (PID: 8088)
- drvinst.exe (PID: 1056)
Reads Microsoft Outlook installation path
- SETUP64.EXE (PID: 8088)
There is functionality for taking screenshot (YARA)
- SETUP64.EXE (PID: 8088)
- DEVICEOP.EXE (PID: 6184)
Creates a software uninstall entry
- SETUP64.EXE (PID: 8088)
Searches for installed software
- SETUP64.EXE (PID: 8088)
Creates or modifies Windows services
- svchost.exe (PID: 7972)
Creates files in the driver directory
- drvinst.exe (PID: 1056)
Reads Internet Explorer settings
- SETUP64.EXE (PID: 8088)
INFO
The sample compiled with english language support
- 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe (PID: 7840)
- 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe (PID: 7864)
- SETUP64.EXE (PID: 8088)
- drvinst.exe (PID: 1056)
Create files in a temporary directory
- 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe (PID: 7840)
- 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe (PID: 7864)
- icsys.icn.exe (PID: 7884)
- explorer.exe (PID: 7932)
- spoolsv.exe (PID: 7952)
- svchost.exe (PID: 7972)
- spoolsv.exe (PID: 7988)
- SETUP64.EXE (PID: 8088)
Checks supported languages
- icsys.icn.exe (PID: 7884)
- 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe (PID: 7864)
- 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe (PID: 7840)
- explorer.exe (PID: 7932)
- svchost.exe (PID: 7972)
- spoolsv.exe (PID: 7988)
- spoolsv.exe (PID: 7952)
- SETUP64.EXE (PID: 8088)
- E_S3LAC2.EXE (PID: 4428)
- drvinst.exe (PID: 1056)
- DEVICEOP.EXE (PID: 6184)
Reads the computer name
- 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe (PID: 7864)
- svchost.exe (PID: 7972)
- SETUP64.EXE (PID: 8088)
- E_S3LAC2.EXE (PID: 4428)
- drvinst.exe (PID: 1056)
- DEVICEOP.EXE (PID: 6184)
Auto-launch of the file from Registry key
- explorer.exe (PID: 7932)
- svchost.exe (PID: 7972)
Process checks computer location settings
- 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe (PID: 7864)
Reads the machine GUID from the registry
- SETUP64.EXE (PID: 8088)
- drvinst.exe (PID: 1056)
Manual execution by a user
- explorer.exe (PID: 8184)
- svchost.exe (PID: 7192)
Checks proxy server information
- SETUP64.EXE (PID: 8088)
- slui.exe (PID: 7172)
Creates files in the program directory
- E_S3LAC2.EXE (PID: 4428)
- SETUP64.EXE (PID: 8088)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 5720)
Reads the software policy settings
- rundll32.exe (PID: 5720)
- slui.exe (PID: 7172)
- drvinst.exe (PID: 1056)
- SETUP64.EXE (PID: 8088)
Adds/modifies Windows certificates
- drvinst.exe (PID: 1056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
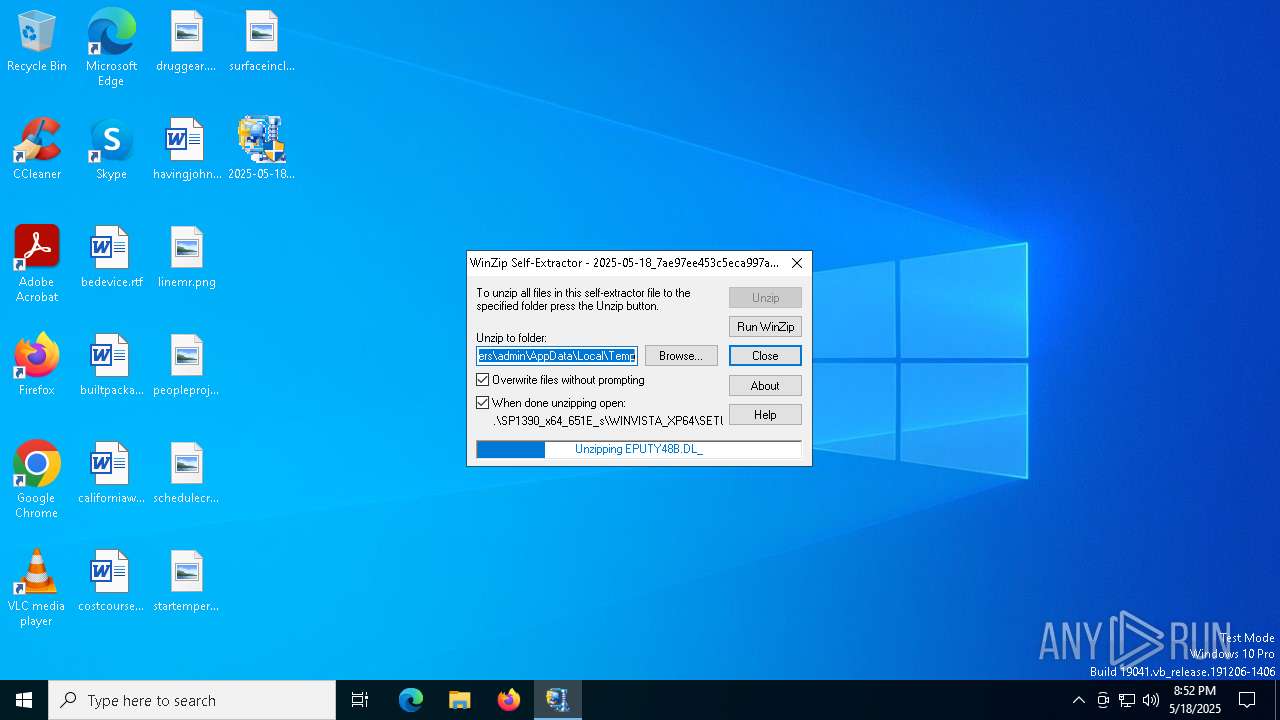
| .exe | | | Winzip Win32 self-extracting archive (generic) (72.9) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (14.3) |
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:04:01 07:08:22+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 106496 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x290c |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| ProductName: | Project1 |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | TJprojMain |
| OriginalFileName: | TJprojMain.exe |
Total processes
143
Monitored processes
16
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1056 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{bf852ca5-53ba-a249-89ce-db2c4cfa6325}\E_GF1BXP_ENGLISH.INF" "9" "4df4f39d7" "000000000000010C" "WinSta0\Default" "00000000000001DC" "208" "C:\Users\admin\AppData\Local\Temp\SP1390_x64_651E_s\WINVISTA_XP64" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
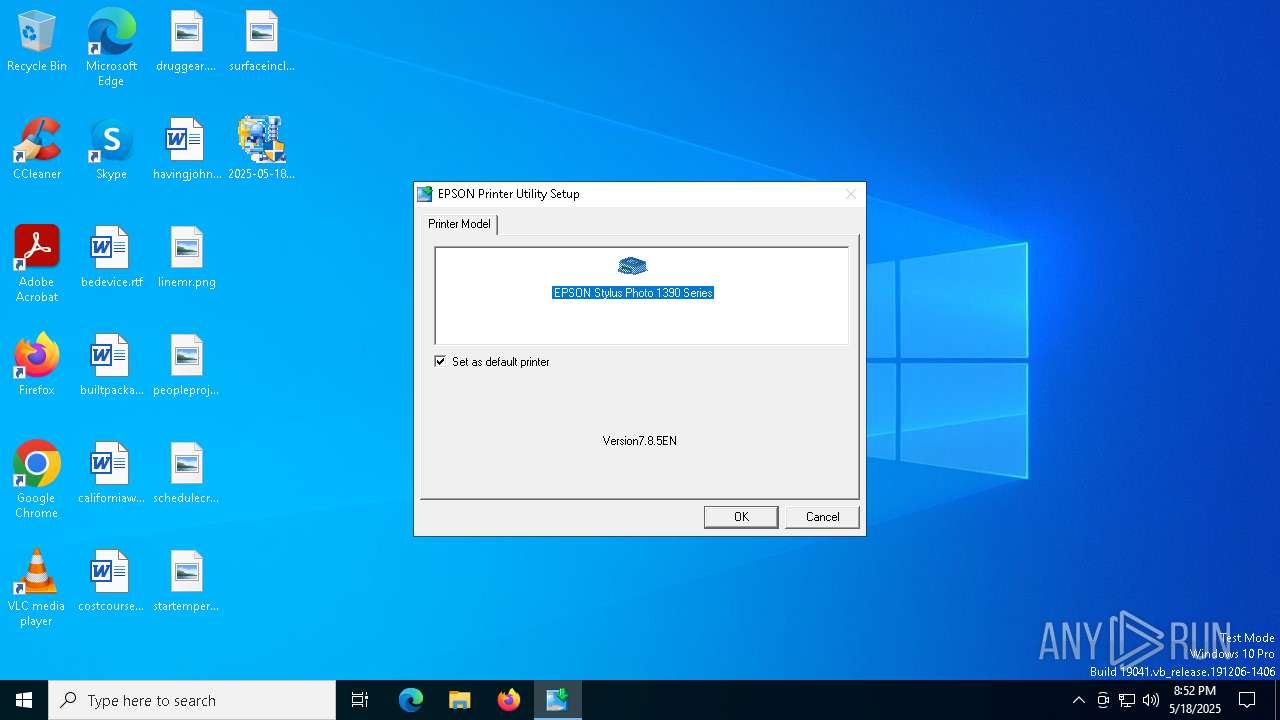
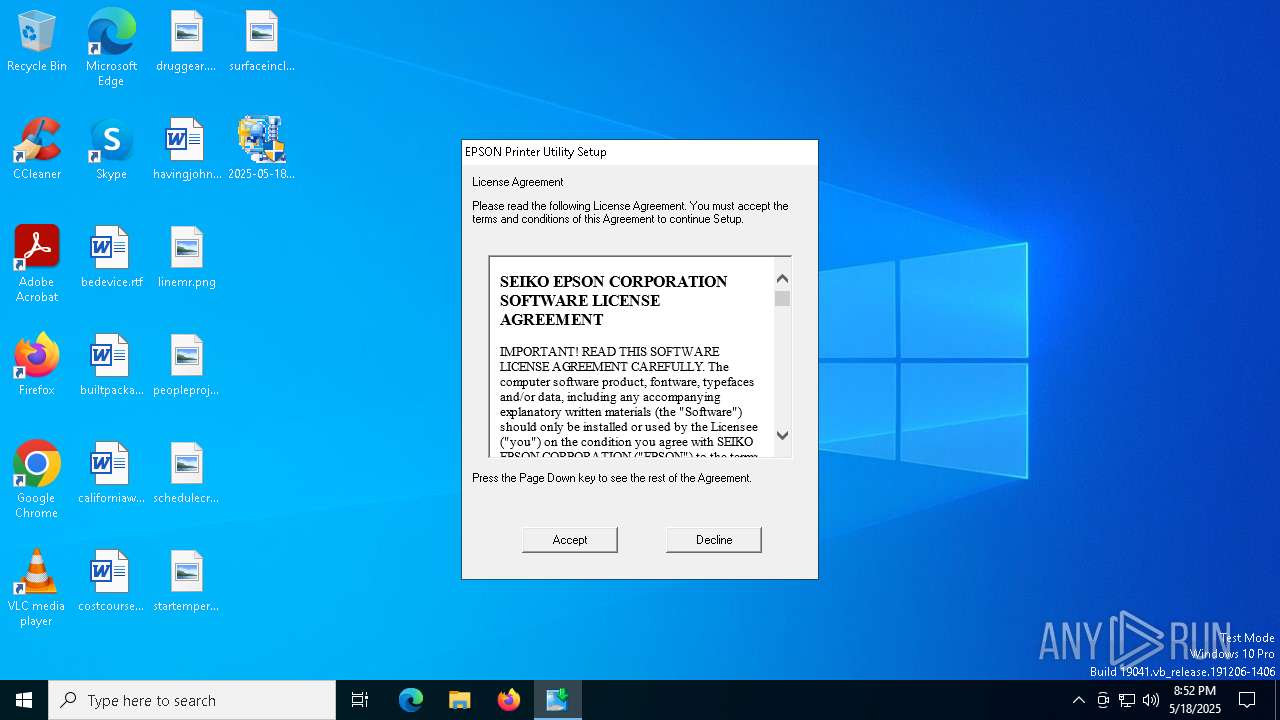
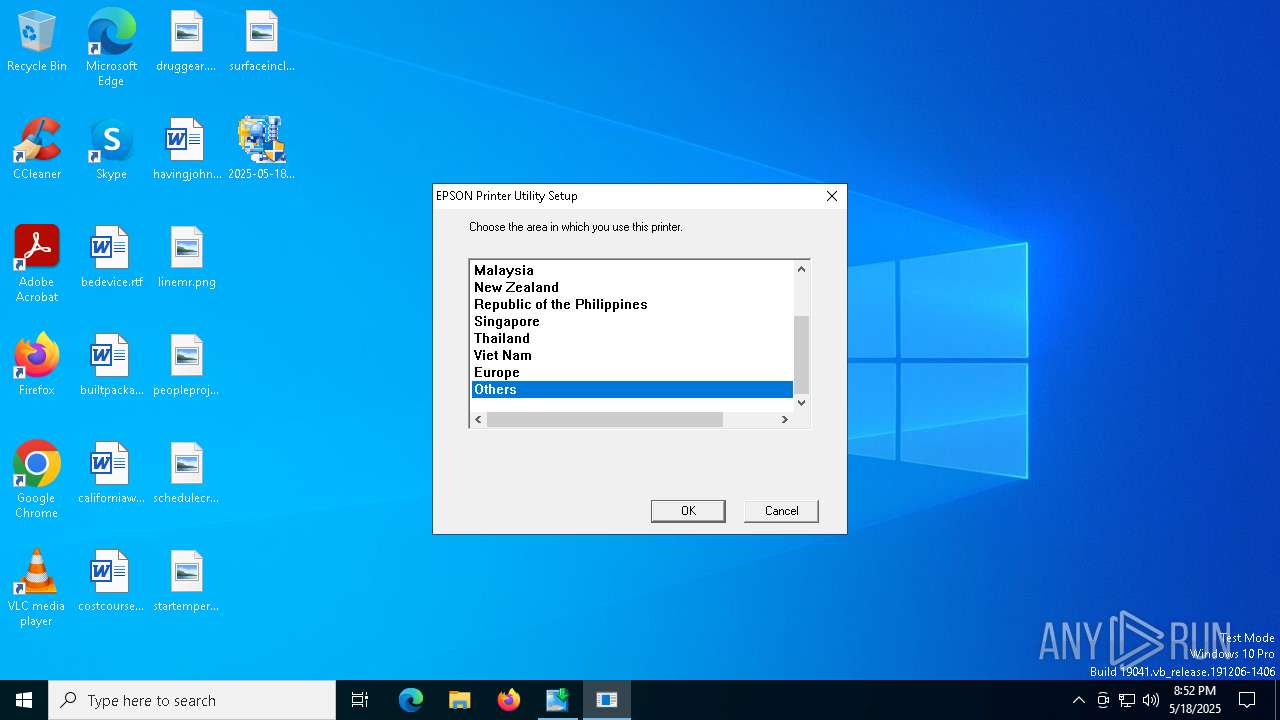
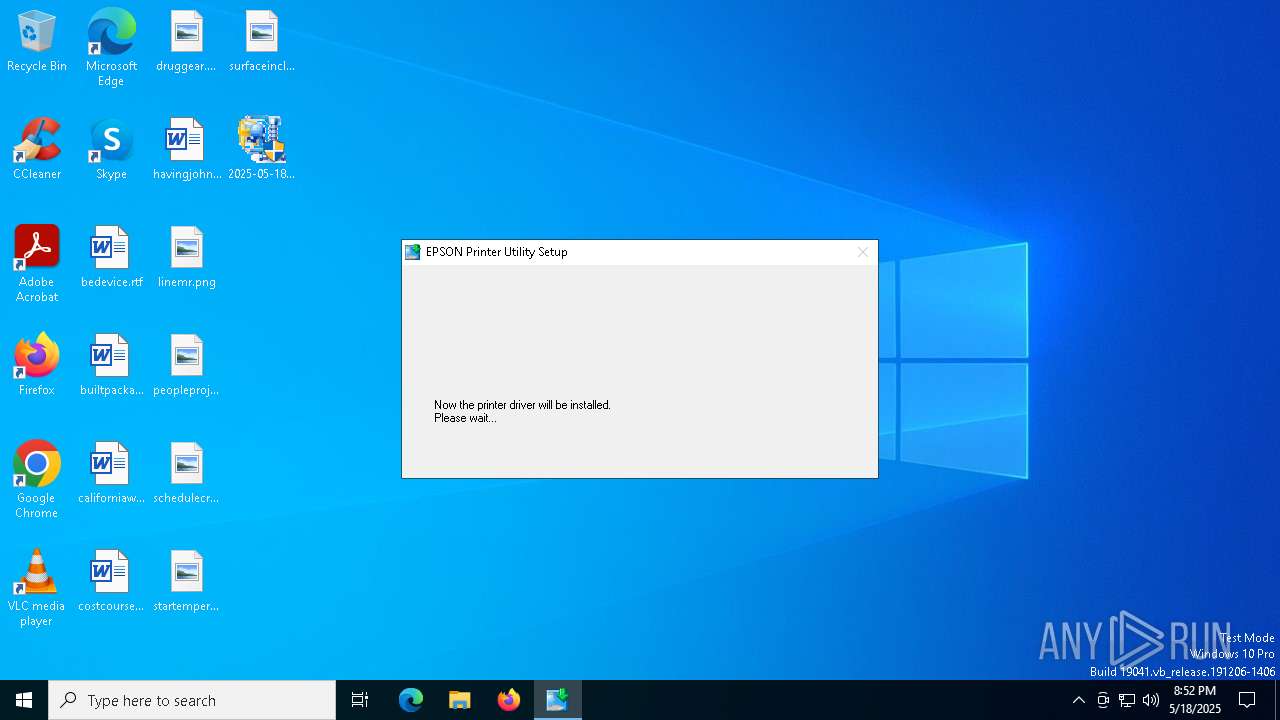
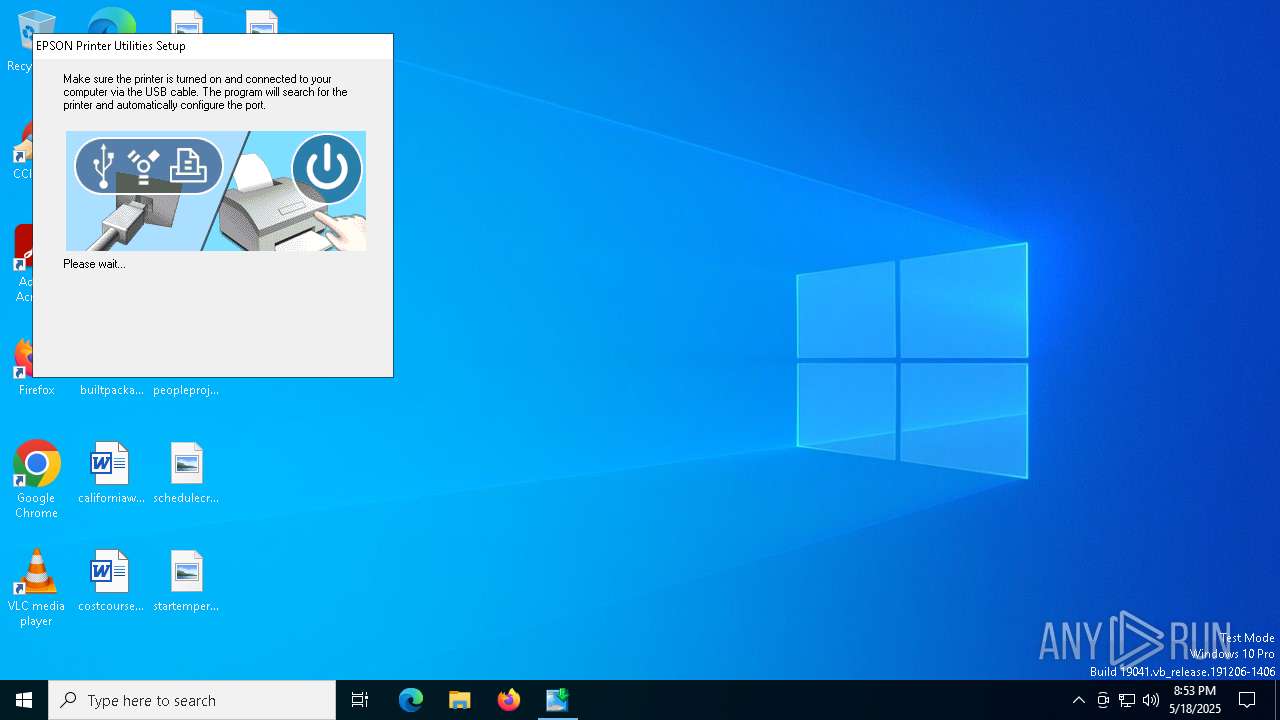
| 4428 | /P "EPSON Stylus Photo 1390 Series" /I:"E_S1LAC2.001" | C:\Users\admin\AppData\Local\Temp\SP1390_x64_651E_s\WINVISTA_XP64\E_S3LAC2.EXE | — | SETUP64.EXE | |||||||||||
User: admin Company: SEIKO EPSON CORPORATION Integrity Level: HIGH Description: EPSON Printer Utility Setup Exit code: 0 Version: 1.04.00 Modules
| |||||||||||||||
| 5720 | rundll32.exe C:\WINDOWS\system32\pnpui.dll,InstallSecurityPromptRunDllW 20 Global\{fff833c5-a4e5-5b47-957c-7b1f020c696f} Global\{cee7a3c6-4f85-9c41-a706-72fe290d97e0} C:\WINDOWS\System32\DriverStore\Temp\{b9054812-b404-374a-9fda-ce251115e045}\E_GF1BXP_ENGLISH.INF C:\WINDOWS\System32\DriverStore\Temp\{b9054812-b404-374a-9fda-ce251115e045}\E_GF1BXP_ENGLISH.CAT | C:\Windows\System32\rundll32.exe | — | drvinst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6184 | /W32:0x60282 /LANG:0x409 /MSG:2000 /MFG:"EPSON" /DES:"EPSON Stylus Photo 1390 Series" /MDL:"Stylus Photo 1390" /DRV:"EPSON Stylus Photo 1390 Series" /PNP /INF:"C:\WINDOWS\INF\oem1.inf" /P:"USB" /P:"LPT" | C:\Users\admin\AppData\Local\Temp\SP1390_x64_651E_s\WINVISTA_XP64\DEVICEOP.EXE | — | SETUP64.EXE | |||||||||||
User: admin Company: SEIKO EPSON CORPORATION Integrity Level: HIGH Description: EPSON Printer Driver Setup for x64 Version: 3.0.4 Modules
| |||||||||||||||
| 7172 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7192 | c:\windows\resources\svchost.exe RO | C:\Windows\Resources\svchost.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.00 Modules
| |||||||||||||||
| 7744 | "C:\Users\admin\Desktop\2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe" | C:\Users\admin\Desktop\2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.00 Modules
| |||||||||||||||
| 7840 | "C:\Users\admin\Desktop\2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe" | C:\Users\admin\Desktop\2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 7864 | c:\users\admin\desktop\2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe | C:\Users\admin\Desktop\2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe | 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 7884 | C:\Windows\Resources\Themes\icsys.icn.exe | C:\Windows\Resources\Themes\icsys.icn.exe | 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
15 568
Read events
15 533
Write events
30
Delete events
5
Modification events
| (PID) Process: | (7840) 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (7884) icsys.icn.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (7932) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Explorer |
Value: c:\windows\resources\themes\explorer.exe RO | |||
| (PID) Process: | (7932) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Svchost |
Value: c:\windows\resources\svchost.exe RO | |||
| (PID) Process: | (7932) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Explorer |
Value: | |||
| (PID) Process: | (7932) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Svchost |
Value: | |||
| (PID) Process: | (7972) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Explorer |
Value: c:\windows\resources\themes\explorer.exe RO | |||
| (PID) Process: | (7972) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Svchost |
Value: c:\windows\resources\svchost.exe RO | |||
| (PID) Process: | (7972) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Explorer |
Value: | |||
| (PID) Process: | (7972) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Svchost |
Value: | |||
Executable files
182
Suspicious files
124
Text files
17
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7864 | 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe | C:\Users\admin\AppData\Local\Temp\SP1390_x64_651E_s\WINVISTA_XP64\COMMON\EPUTY48B.DL_ | compressed | |
MD5:52C9E3E5E24C11EA9E83140BAB520145 | SHA256:41F39CD6E67E4DD5645AAEAFCA4164520C920C6B54E0DB75A9FE511F63F4C81C | |||
| 7864 | 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe | C:\Users\admin\AppData\Local\Temp\SP1390_x64_651E_s\WINVISTA_XP64\COMMON\EE387__4.IC_ | compressed | |
MD5:7F44AD16E8EE64B29D2ECF2CC7DDACF4 | SHA256:513D0DC03B91E3E4BE4E6893EBEB02750AB2C0D896F65A3DFCD68A5826801AF2 | |||
| 7864 | 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe | C:\Users\admin\AppData\Local\Temp\SP1390_x64_651E_s\WINVISTA_XP64\COMMON\EE387__2.IC_ | compressed | |
MD5:E4F9BD0744C34C43CBFB137813D044C3 | SHA256:41B0157AF57092F5004C6943438DFCCAC722DDACBC02571A240DB9222C561BEE | |||
| 7864 | 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe | C:\Users\admin\AppData\Local\Temp\SP1390_x64_651E_s\WINVISTA_XP64\COMMON\EE387__3.IC_ | compressed | |
MD5:175C81F304D4E5BD80B7992E38E50E82 | SHA256:4FBEBBF423FBBF1D872857725B8A87042DD7AADD27231C7CFA5F00BD9B94D0B1 | |||
| 7864 | 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe | C:\Users\admin\AppData\Local\Temp\SP1390_x64_651E_s\WINVISTA_XP64\COMMON\EE387__5.IC_ | compressed | |
MD5:83C6EFD7A3950C42056E369BB87B40FA | SHA256:AC9107D9AE2C9A16C71446813D0755EA87561CEF3FDBA85B7BFC4275DFD7734E | |||
| 7884 | icsys.icn.exe | C:\Windows\Resources\Themes\explorer.exe | executable | |
MD5:C1C5DC8B6F5F4A5DD8359893DBBC1BA5 | SHA256:4E9710D583D5B640B5B400760744DF767942D39BE2A0E1707F067D192EF357AB | |||
| 7864 | 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe | C:\Users\admin\AppData\Local\Temp\SP1390_x64_651E_s\WINVISTA_XP64\COMMON\EE387__7.IC_ | compressed | |
MD5:DBF3C1EFB5099B7CC4D363B84D2FFB23 | SHA256:ABAFA9BDC95F5188DD6725F5D9683B8A6C77275FDE7627469E70ABA2CDED5C19 | |||
| 7864 | 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe | C:\Users\admin\AppData\Local\Temp\SP1390_x64_651E_s\WINVISTA_XP64\COMMON\EE387__6.IC_ | compressed | |
MD5:61B0DE7C6B4DDB656A266D9D79C9CC4A | SHA256:29D4301E5018BA79F64BE42BB35D3DF9D55F82740A709B8C98AF6A380467A615 | |||
| 7864 | 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe | C:\Users\admin\AppData\Local\Temp\SP1390_x64_651E_s\WINVISTA_XP64\COMMON\EPSET64.DL_ | compressed | |
MD5:353ADD0FECB1022E85741D93D97B5648 | SHA256:D167CD978CD80B665049AB2649AA685A48409D52496703DC76F436779967755E | |||
| 7864 | 2025-05-18_7ae97ee453c5eca997a3107c607a85b2_amadey_elex_http-browser_rhadamanthys_smoke-loader_swisyn.exe | C:\Users\admin\AppData\Local\Temp\SP1390_x64_651E_s\WINVISTA_XP64\COMMON\EPUTY48B.EX_ | compressed | |
MD5:CC9F5C77032231A71A3984526856ABC9 | SHA256:97FC769DA765FBB85F30D6B06547B452ACA5CAD7A87A53D9B988434891E8B347 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
43
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7300 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
2564 | RUXIMICS.exe | GET | 200 | 23.48.23.192:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7300 | SIHClient.exe | GET | 200 | 23.48.23.192:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
7300 | SIHClient.exe | GET | 200 | 23.48.23.192:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
2564 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7300 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7300 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7300 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
7300 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2564 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2564 | RUXIMICS.exe | 23.48.23.192:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2564 | RUXIMICS.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7300 | SIHClient.exe | 172.202.163.200:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
7300 | SIHClient.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
login.live.com |
| whitelisted |