| File name: | 724552ebadbd2674c7dd444aaf07920f9a0276587ec647e38a051494a56e7a73.exe |
| Full analysis: | https://app.any.run/tasks/56fa0596-c89f-42cf-a646-57c5a88d7841 |
| Verdict: | Malicious activity |
| Analysis date: | March 12, 2018, 17:31:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DF916CA0E70EC65D6A3248BA4DDBF632 |
| SHA1: | 28AB04AFF4F74F0D3B6D67C9BA682F78CBB9ABBC |
| SHA256: | 724552EBADBD2674C7DD444AAF07920F9A0276587EC647E38A051494A56E7A73 |
| SSDEEP: | 98304:2b/DjdVojm80Cq0xwOy+fYJDX2v0Qfs5kmhn4qC8Qd0Hgg7Rt+SRS93g:2xCrKOyPDm8qs+qC8QuHg793g |
MALICIOUS
Application loaded dropped or rewritten executable
- miniunz.exe (PID: 1648)
- dchcfg32.exe (PID: 2480)
- 724552ebadbd2674c7dd444aaf07920f9a0276587ec647e38a051494a56e7a73.exe (PID: 3544)
Application was dropped or rewritten from another process
- hapint.exe (PID: 2688)
- dcmdev32.exe (PID: 3276)
- miniunz.exe (PID: 1648)
- dcmdev32.exe (PID: 2296)
- dchcfg32.exe (PID: 2480)
- dcmdev32.exe (PID: 2656)
- hapint.exe (PID: 3736)
Changes settings of System certificates
- hapint.exe (PID: 2688)
SUSPICIOUS
Creates files in the Windows directory
- DrvInst.exe (PID: 2100)
- dcmdev32.exe (PID: 2296)
- DrvInst.exe (PID: 3988)
- hapint.exe (PID: 2688)
Modifies files in the system directory
- dcmdev32.exe (PID: 2296)
- DrvInst.exe (PID: 2100)
- DrvInst.exe (PID: 3988)
- hapint.exe (PID: 2688)
Removes files from Windows directory
- DrvInst.exe (PID: 3988)
- DrvInst.exe (PID: 2100)
- hapint.exe (PID: 3736)
Creates files in the driver directory
- DrvInst.exe (PID: 2100)
- DrvInst.exe (PID: 3988)
INFO
Dropped object may contain URL's
- 724552ebadbd2674c7dd444aaf07920f9a0276587ec647e38a051494a56e7a73.exe (PID: 3544)
- miniunz.exe (PID: 1648)
- dcmdev32.exe (PID: 2296)
- DrvInst.exe (PID: 2100)
- hapint.exe (PID: 2688)
Loads rich edit control libraries
- 724552ebadbd2674c7dd444aaf07920f9a0276587ec647e38a051494a56e7a73.exe (PID: 3544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:01 07:28:27+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 167424 |
| InitializedDataSize: | 1580544 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16285 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.0.0.0 |
| ProductVersionNumber: | 7.0.0.0 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Dell Inc. |
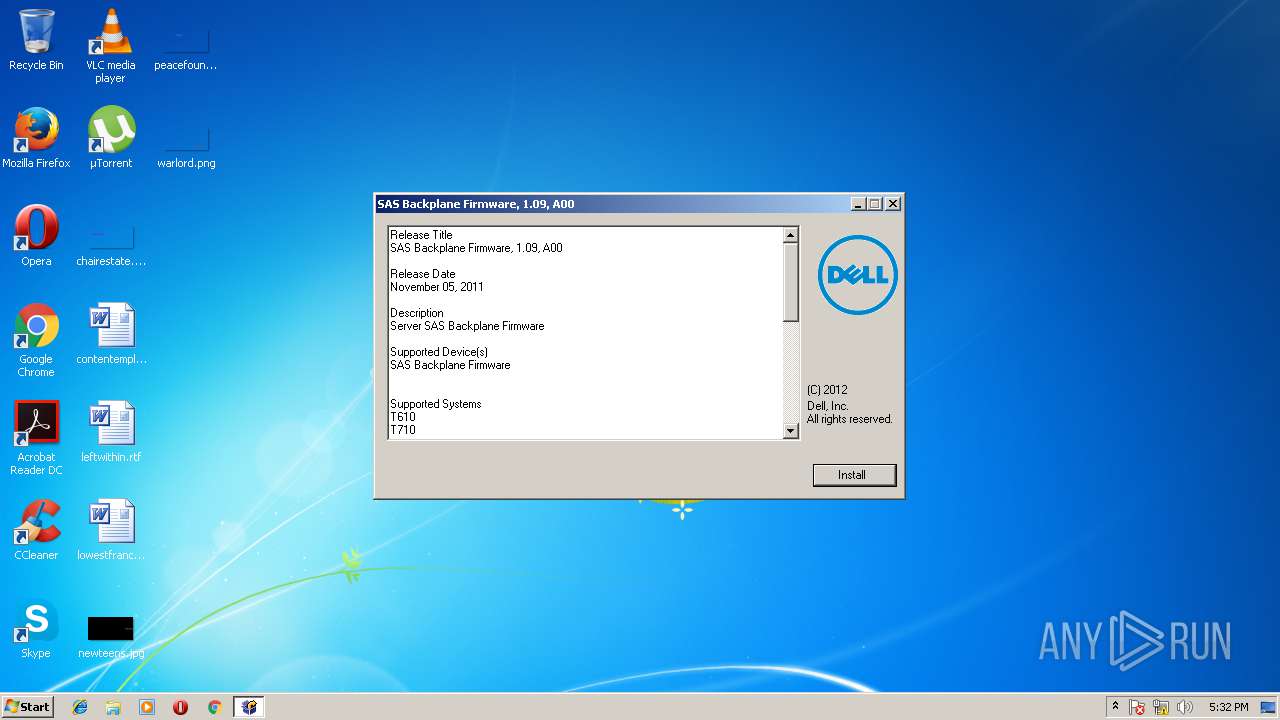
| FileDescription: | Dell Update Package: SAS Backplane Firmware, 1.09, A00 |
| FileVersion: | 7, 0, 0, 0 |
| InternalName: | Dell Self Extractable |
| LegalCopyright: | Copyright (C) Dell Inc. 2012. All rights reserved. |
| OriginalFileName: | SelfExtractable.exe |
| ProductName: | SAS Backplane Firmware, 1.09, A00 |
| ProductVersion: | 1.09 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Feb-2012 06:28:27 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Dell Inc. |
| FileDescription: | Dell Update Package: SAS Backplane Firmware, 1.09, A00 |
| : | - |
| FileVersion: | 7, 0, 0, 0 |
| InternalName: | Dell Self Extractable |
| LegalCopyright: | Copyright (C) Dell Inc. 2012. All rights reserved. |
| : | - |
| OriginalFilename: | SelfExtractable.exe |
| ProductName: | SAS Backplane Firmware, 1.09, A00 |
| : | - |
| ProductVersion: | 1.09 |
| 000, 0001: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Feb-2012 06:28:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00028CF6 | 0x00028E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58537 |
.rdata | 0x0002A000 | 0x00006D72 | 0x00006E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.94052 |
.data | 0x00031000 | 0x00003488 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.36392 |
.rsrc | 0x00035000 | 0x00175AD8 | 0x00175C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.80445 |
.reloc | 0x001AB000 | 0x00003AE4 | 0x00003C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.18543 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.77792 | 357 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.68066 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.68472 | 872 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.81898 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 3.3339 | 3240 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 2.03832 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 2.76813 | 392 | Latin 1 / Western European | English - United States | RT_ICON |
101 | 2.68763 | 76 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
102 | 2.73452 | 34 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
103 | 2.43272 | 30040 | Latin 1 / Western European | English - United States | RT_BITMAP |
Imports
ADVAPI32.dll |
CRYPT32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
USER32.dll |
ole32.dll |
Total processes
53
Monitored processes
12
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1648 | -x hapi.zip -o -d . | C:\Users\admin\AppData\Local\Temp\a11e9e9d-9d98-4c6e-9736-3efae9c18167\miniunz.exe | 724552ebadbd2674c7dd444aaf07920f9a0276587ec647e38a051494a56e7a73.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2100 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{67756fe4-b7c9-403c-92ae-4d5083476773}\dcdbas32.inf" "0" "6dfcb1ac3" "00000570" "WinSta0\Default" "000004F0" "208" "c:\users\admin\appdata\local\temp\a11e9e9d-9d98-4c6e-9736-3efae9c18167\hapi" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2296 | dcmdev32.exe install .\dcdbas32.inf root\dcdbas | C:\Users\admin\AppData\Local\Temp\a11e9e9d-9d98-4c6e-9736-3efae9c18167\hapi\dcmdev32.exe | hapint.exe | ||||||||||||
User: admin Company: Dell Inc. Integrity Level: HIGH Description: WDM Driver Manager Exit code: 0 Version: 7.0.0 (BLD_548) Modules
| |||||||||||||||
| 2480 | dchcfg32.exe command=getsupportedsystypes | C:\Users\admin\AppData\Local\Temp\a11e9e9d-9d98-4c6e-9736-3efae9c18167\hapi\dchcfg32.exe | — | hapint.exe | |||||||||||
User: admin Company: Dell Inc. Integrity Level: HIGH Description: HAPI Config Utility Exit code: 0 Version: 7.0.0 (BLD_548) Modules
| |||||||||||||||
| 2656 | dcmdev32.exe remove root\dcdbas | C:\Users\admin\AppData\Local\Temp\a11e9e9d-9d98-4c6e-9736-3efae9c18167\hapi\dcmdev32.exe | — | hapint.exe | |||||||||||
User: admin Company: Dell Inc. Integrity Level: HIGH Description: WDM Driver Manager Exit code: 0 Version: 7.0.0 (BLD_548) Modules
| |||||||||||||||
| 2688 | hapint.exe -k SPHAPIDA5 -p %SystemRoot%\hapint.exe -q | C:\Users\admin\AppData\Local\Temp\a11e9e9d-9d98-4c6e-9736-3efae9c18167\hapi\hapint.exe | 724552ebadbd2674c7dd444aaf07920f9a0276587ec647e38a051494a56e7a73.exe | ||||||||||||
User: admin Company: Dell Inc. Integrity Level: HIGH Description: Hapi Installer Exit code: 0 Version: 7.0.0 (BLD_548) Modules
| |||||||||||||||
| 3092 | C:\Windows\System32\rundll32.exe shell32.dll,SHCreateLocalServerRunDll {995C996E-D918-4a8c-A302-45719A6F4EA7} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3132 | "C:\Users\admin\AppData\Local\Temp\724552ebadbd2674c7dd444aaf07920f9a0276587ec647e38a051494a56e7a73.exe" | C:\Users\admin\AppData\Local\Temp\724552ebadbd2674c7dd444aaf07920f9a0276587ec647e38a051494a56e7a73.exe | — | explorer.exe | |||||||||||
User: admin Company: Dell Inc. Integrity Level: MEDIUM Description: Dell Update Package: SAS Backplane Firmware, 1.09, A00 Exit code: 3221226540 Version: 7, 0, 0, 0 Modules
| |||||||||||||||
| 3276 | dcmdev32.exe remove root\dcdbas | C:\Users\admin\AppData\Local\Temp\a11e9e9d-9d98-4c6e-9736-3efae9c18167\hapi\dcmdev32.exe | — | hapint.exe | |||||||||||
User: admin Company: Dell Inc. Integrity Level: HIGH Description: WDM Driver Manager Exit code: 0 Version: 7.0.0 (BLD_548) Modules
| |||||||||||||||
| 3544 | "C:\Users\admin\AppData\Local\Temp\724552ebadbd2674c7dd444aaf07920f9a0276587ec647e38a051494a56e7a73.exe" | C:\Users\admin\AppData\Local\Temp\724552ebadbd2674c7dd444aaf07920f9a0276587ec647e38a051494a56e7a73.exe | explorer.exe | ||||||||||||
User: admin Company: Dell Inc. Integrity Level: HIGH Description: Dell Update Package: SAS Backplane Firmware, 1.09, A00 Exit code: 0 Version: 7, 0, 0, 0 Modules
| |||||||||||||||
Total events
99
Read events
42
Write events
50
Delete events
7
Modification events
| (PID) Process: | (2688) hapint.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\hapiTemp |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2296) dcmdev32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.app.log |
Value: 4096 | |||
| (PID) Process: | (2688) hapint.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\TrustedPublisher\Certificates\491FF0241F4AD8C03E1749737D446C6B35F0F7E1 |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000491FF0241F4AD8C03E1749737D446C6B35F0F7E120000000010000005C0400003082045830820340A003020102020A7846C597000000000009300D06092A864886F70D0101050500303F31123010060355040A130944656C6C20496E632E312930270603550403132044656C6C20496E632E20456E74657270726973652049737375696E6720434132301E170D3035303731323233313430355A170D3038303731313233313430355A3079310B3009060355040613025553310E300C060355040813055465786173311330110603550407130A526F756E6420526F636B3111300F060355040A130844656C6C20496E63311F301D060355040B1316496E666F726D6174696F6E20546563686E6F6C6F67793111300F0603550403130844656C6C20496E6330819F300D06092A864886F70D010101050003818D0030818902818100BCDFD6A913404F1F8C2494AF546B91418FEF8C87120542B135D52EE7BA777CA6EE29B9F6CAE79A4D74F55DFDB918B1EFC4E42A1190303111998F875CB047A1C9E8065CE47833A56B8F05107E830E00834EAADB8E3C9A2D158EE9310E9666D7130EEE2FA638BC999262B5679AC1D53A67558834269674B12FA7DED2D28D8ABF730203010001A382019E3082019A300B0603551D0F040403020780301D0603551D0E0416041452D37334A216CA0307E2DFA1604E9943172847FE303D06092B06010401823715070430302E06262B060104018237150887B8D96C8184F80886BD8D0F85F3803582B3995A3385C3ED5F85AFC11A020164020108301F0603551D230418301680143292670CFE546F03507496F257AAB13FA3D6E3DF305B0603551D1F045430523050A04EA04C864A687474703A2F2F64656C6C696E6363612E64656C6C2E636F6D2F63726C2F44656C6C253230496E632E253230456E746572707269736525323049737375696E672532304341322E63726C307D06082B060105050701010471306F306D06082B060105050730028661687474703A2F2F64656C6C696E6363612E64656C6C2E636F6D2F63726C2F415553454341435349474E30312E64656C6C2E636F6D5F44656C6C253230496E632E253230456E746572707269736525323049737375696E672532304341322E63727430130603551D25040C300A06082B06010505070303301B06092B060104018237150A040E300C300A06082B06010505070303300D06092A864886F70D01010505000382010100105602CBA8746B9B6BC6905A95AB8956B374F226C6BAEA6E741116119C384E143433B188F461B961D56D38F2ACEC221ADD6EC9A87BAFF146C5A86AD4FE9B18F661EE560EE9AC9F2F4D469662F57332C000581A55234C9E3F962C0D8881E7F6F858002D289AF1F8687F57F938760CDB1D8AB4A9C51155747451E90906A95AB0DF82285E5C192A73535E75F3762CB8CDA232C612B07A7746C4886E63B545A3C5CDA93CDD96FA65BBC3266418763CEBCE5B0334C093455BFA34901EDDC0F88574A28B5F3A83F9407CFBE2C18053986CCA04BF30389E87FA8100E615996D2C4623A7CAF3BC48FC480ED758CFF7DA4669B38C7F778FD6E514D88311B77CD42E5F4A2C | |||
| (PID) Process: | (2100) DrvInst.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2296) dcmdev32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.dev.log |
Value: 4096 | |||
| (PID) Process: | (2296) dcmdev32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3988) DrvInst.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3988) DrvInst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Setup\PnpLockdownFiles |
| Operation: | write | Name: | %SystemPath%\system32\DRIVERS\dcdbas32.sys |
Value: 5 | |||
| (PID) Process: | (3988) DrvInst.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\CriticalDeviceDatabase\root#dcdbas |
| Operation: | write | Name: | Service |
Value: dcdbas | |||
| (PID) Process: | (3988) DrvInst.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\CriticalDeviceDatabase\root#dcdbas |
| Operation: | write | Name: | ClassGUID |
Value: {4d36e97d-e325-11ce-bfc1-08002be10318} | |||
Executable files
23
Suspicious files
17
Text files
131
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1648 | miniunz.exe | C:\Users\admin\AppData\Local\Temp\a11e9e9d-9d98-4c6e-9736-3efae9c18167\hapi\dcdtvm32.sys | text | |
MD5:2F0E27283EDE4A1E312D3160D8046ECD | SHA256:DAB7724E5BF8559F26E0C3F385D554895E9122FBDEB97015F9F9081A9445978E | |||
| 1648 | miniunz.exe | C:\Users\admin\AppData\Local\Temp\a11e9e9d-9d98-4c6e-9736-3efae9c18167\hapi\dcdipm64.sys | text | |
MD5:2F0E27283EDE4A1E312D3160D8046ECD | SHA256:DAB7724E5BF8559F26E0C3F385D554895E9122FBDEB97015F9F9081A9445978E | |||
| 1648 | miniunz.exe | C:\Users\admin\AppData\Local\Temp\a11e9e9d-9d98-4c6e-9736-3efae9c18167\hapi\dcdbas32.cat | cat | |
MD5:CA0462F182AFB0C03BDE41C031DE648C | SHA256:7FC150A5D664EF6A0B66D40F9742177D8DFC9C383466529B9305580CE706771E | |||
| 1648 | miniunz.exe | C:\Users\admin\AppData\Local\Temp\a11e9e9d-9d98-4c6e-9736-3efae9c18167\hapi\dcdbas64.inf | binary | |
MD5:83E3766AE6D4AEDB7DBC04CDE4F51332 | SHA256:1C5FD251FF8874286D277C6D052042BF21D75DBA9C1D8D6235D6C1F3B782EF14 | |||
| 1648 | miniunz.exe | C:\Users\admin\AppData\Local\Temp\a11e9e9d-9d98-4c6e-9736-3efae9c18167\hapi\dchcfg32.exe | executable | |
MD5:9804C1EDA26E70E343EDEE9F1807BC62 | SHA256:E876F8F7AEC681FEDBC6A7F5588A8849E474E62B86CBD5F30E970124869DF584 | |||
| 1648 | miniunz.exe | C:\Users\admin\AppData\Local\Temp\a11e9e9d-9d98-4c6e-9736-3efae9c18167\hapi\dcdesm32.sys | text | |
MD5:2F0E27283EDE4A1E312D3160D8046ECD | SHA256:DAB7724E5BF8559F26E0C3F385D554895E9122FBDEB97015F9F9081A9445978E | |||
| 1648 | miniunz.exe | C:\Users\admin\AppData\Local\Temp\a11e9e9d-9d98-4c6e-9736-3efae9c18167\hapi\dchapi.cer | der | |
MD5:7B2945CDEFB50BF81A29A37F4409784F | SHA256:E5848A5B86469F896BE2E722CADADC381D3A33CAA22C7539F9CC942D2B18903A | |||
| 1648 | miniunz.exe | C:\Users\admin\AppData\Local\Temp\a11e9e9d-9d98-4c6e-9736-3efae9c18167\hapi\dcesm.sys | text | |
MD5:2F0E27283EDE4A1E312D3160D8046ECD | SHA256:DAB7724E5BF8559F26E0C3F385D554895E9122FBDEB97015F9F9081A9445978E | |||
| 3544 | 724552ebadbd2674c7dd444aaf07920f9a0276587ec647e38a051494a56e7a73.exe | C:\Users\admin\AppData\Local\Temp\a11e9e9d-9d98-4c6e-9736-3efae9c18167\zlibwapi.dll | executable | |
MD5:54789344B07BED58E43851ECA47E2B12 | SHA256:9F8729AC49E0CCEA86FE3B1A9B2C3FAE9986ECD09DB92853E7A588DBDA85BF90 | |||
| 2296 | dcmdev32.exe | C:\Users\admin\AppData\Local\Temp\{67756fe4-b7c9-403c-92ae-4d5083476773}\SETC84E.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report