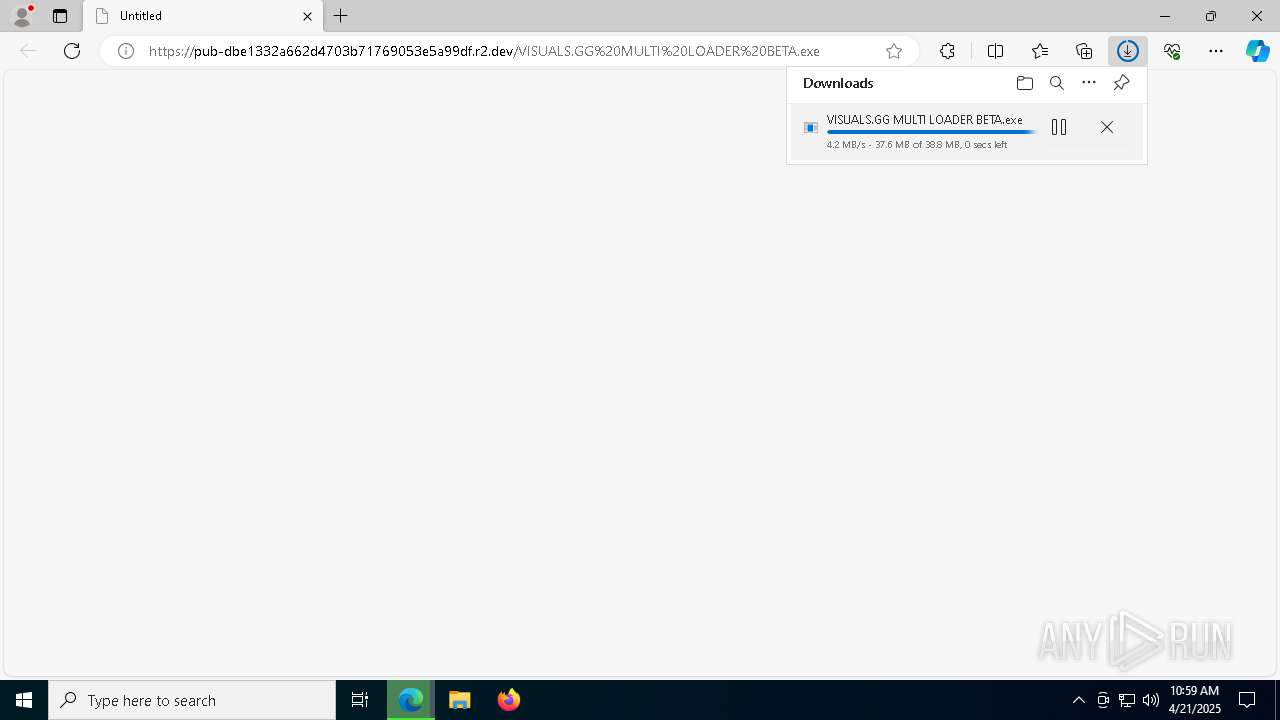
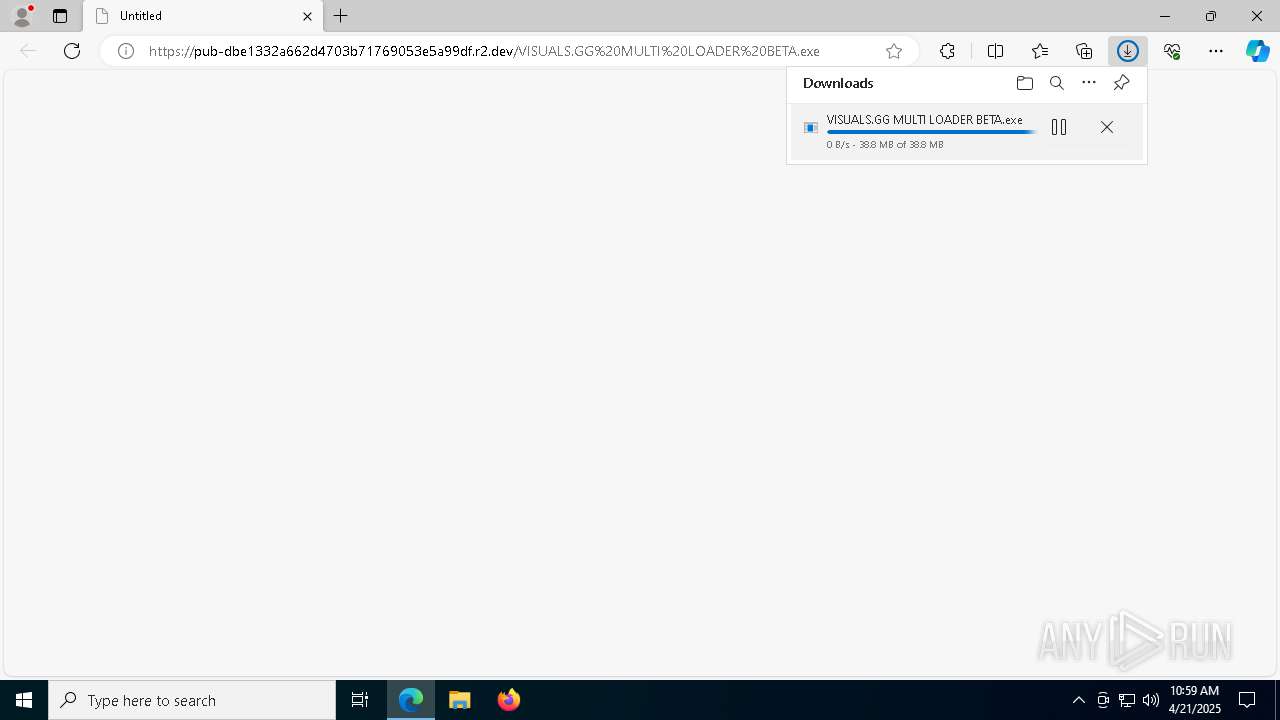
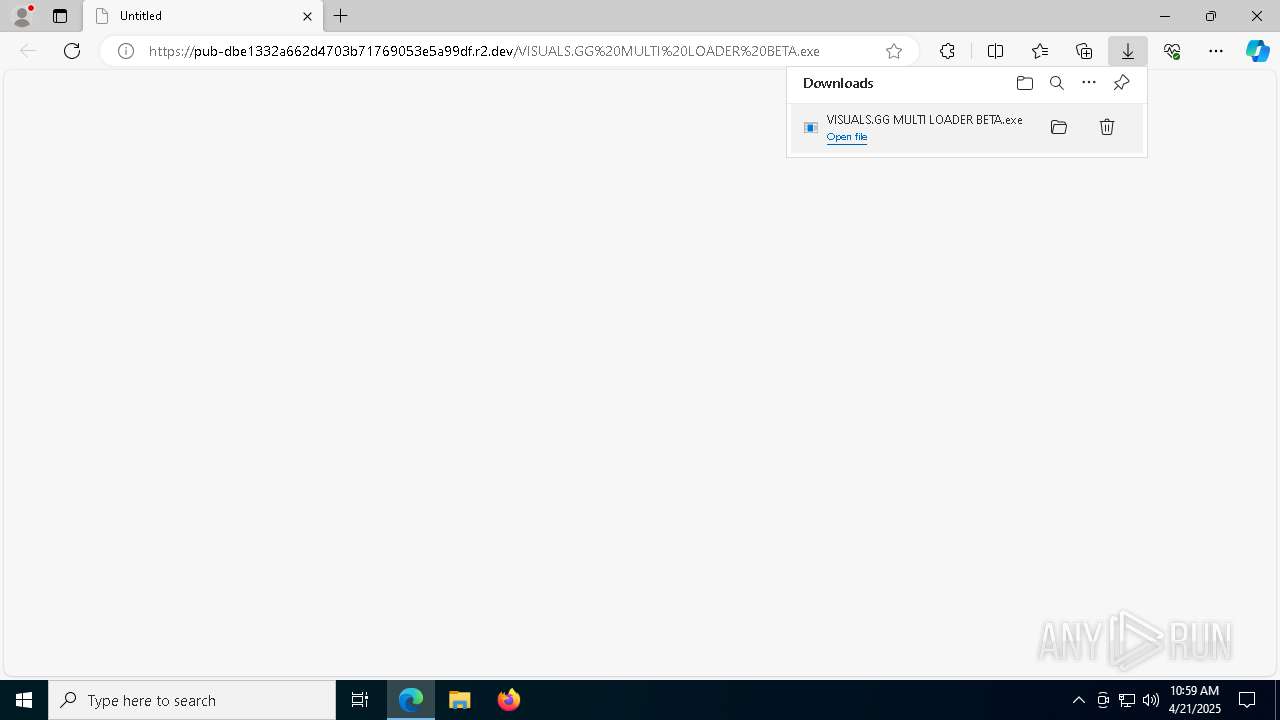
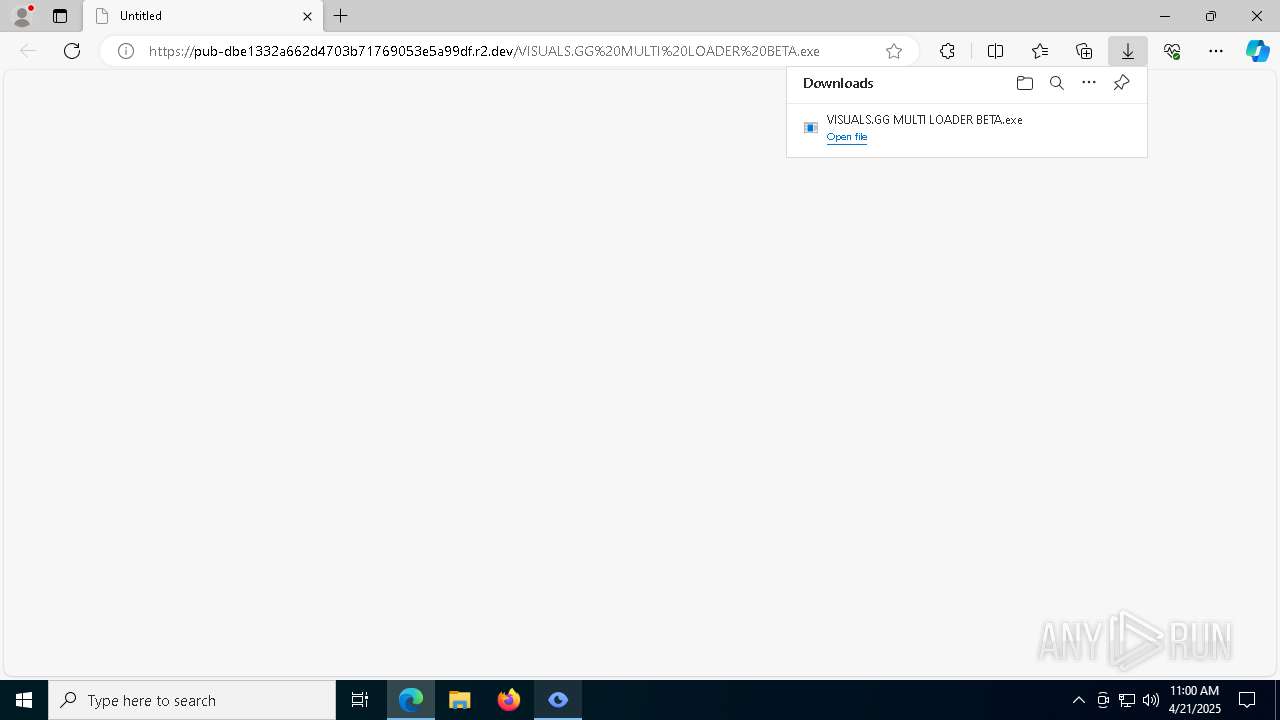
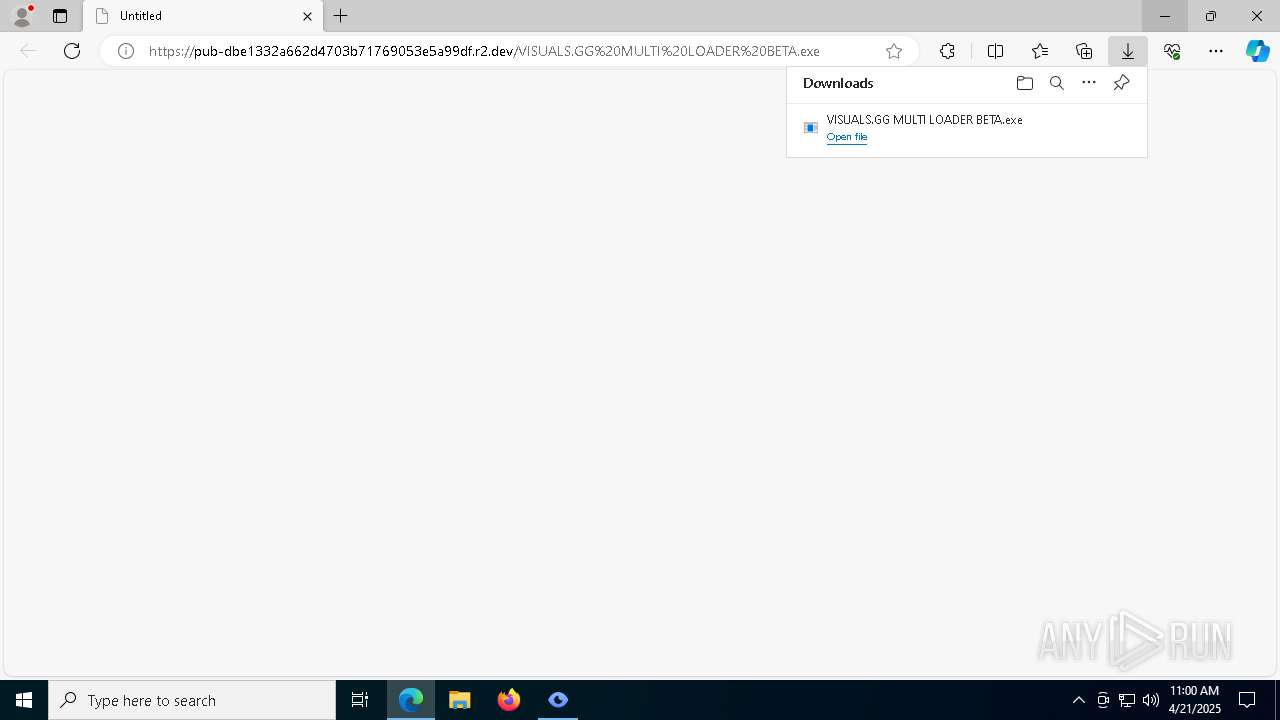
| URL: | https://pub-dbe1332a662d4703b71769053e5a99df.r2.dev/VISUALS.GG%20MULTI%20LOADER%20BETA.exe |
| Full analysis: | https://app.any.run/tasks/2289ffee-d76d-4c13-b43f-8c15530d8fe0 |
| Verdict: | Malicious activity |
| Analysis date: | April 21, 2025, 10:59:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 990726E2D7B4242FB263B8AB744962CE |
| SHA1: | 4A930986B87E4EDD9ACA6337EAA06C6177A44468 |
| SHA256: | 7242B4B54EA17D1B09707A07AB0168EC8D8597D278B335F38EFCB24A36976365 |
| SSDEEP: | 3:N8UcR/hZRXXzXRpDiAXVtfBVd0DCn:2UcdhjH7VtfB+Cn |
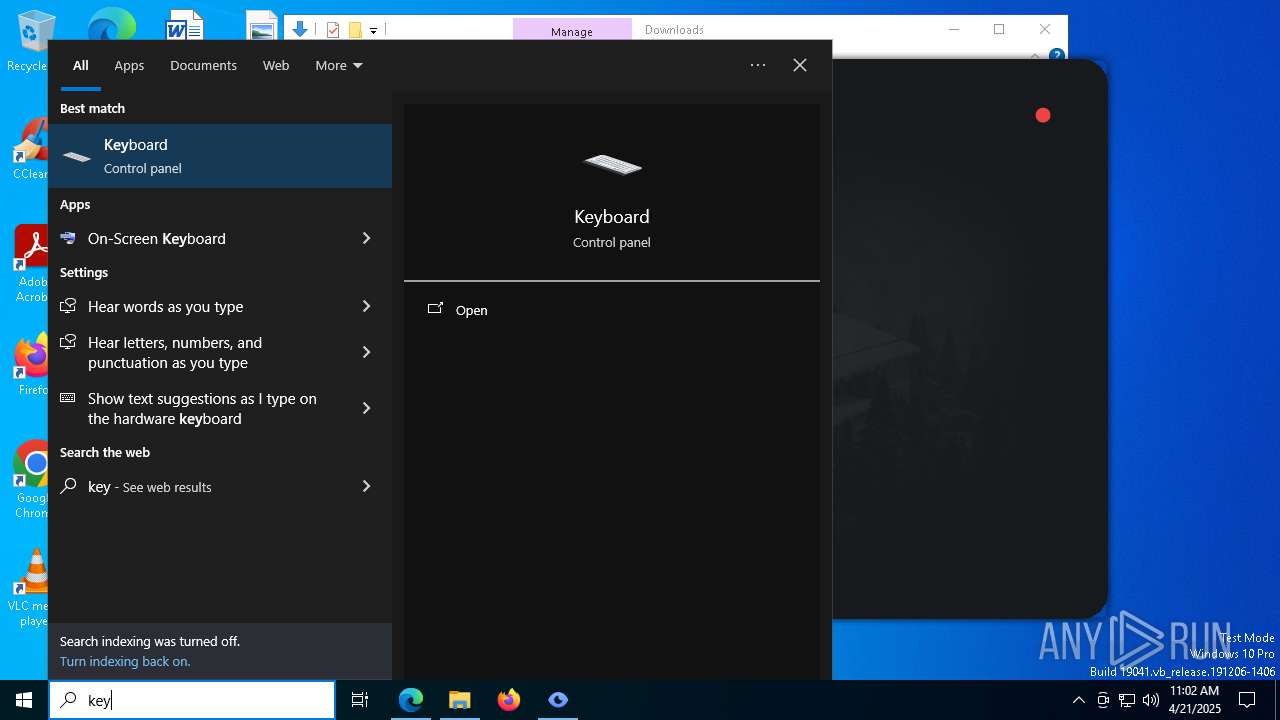
MALICIOUS
XORed URL has been found (YARA)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 632)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 3156)
SUSPICIOUS
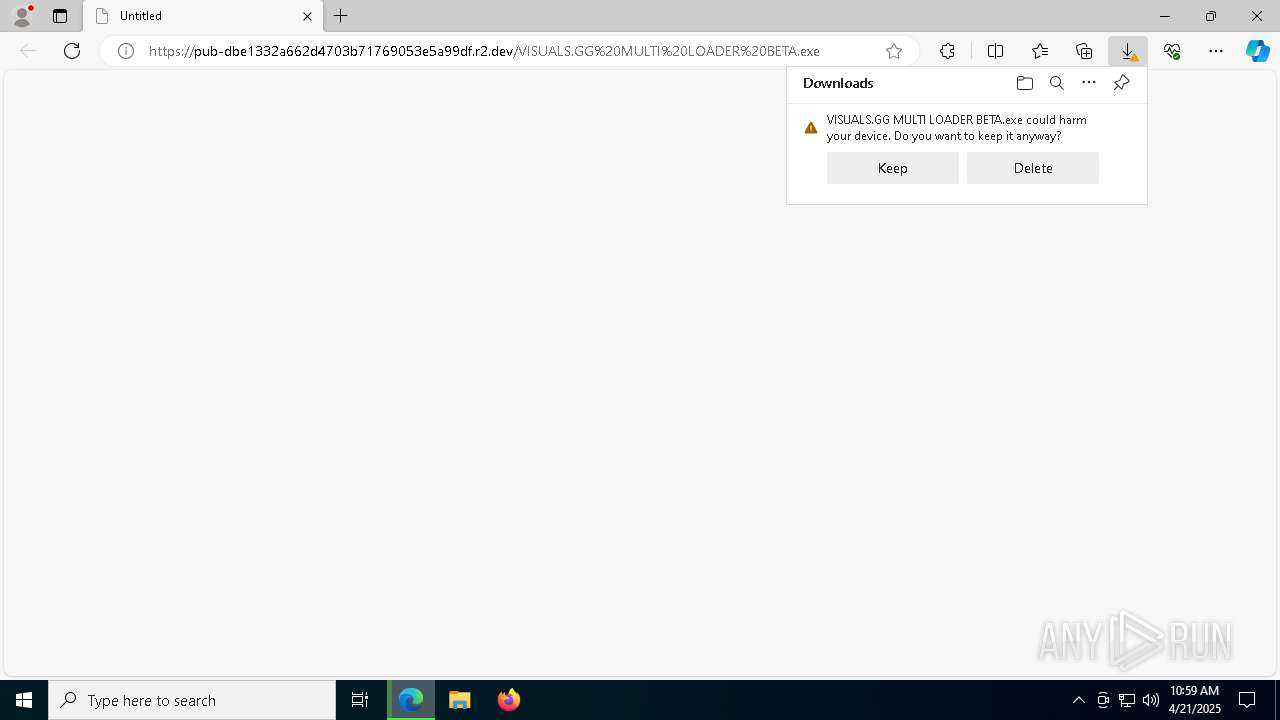
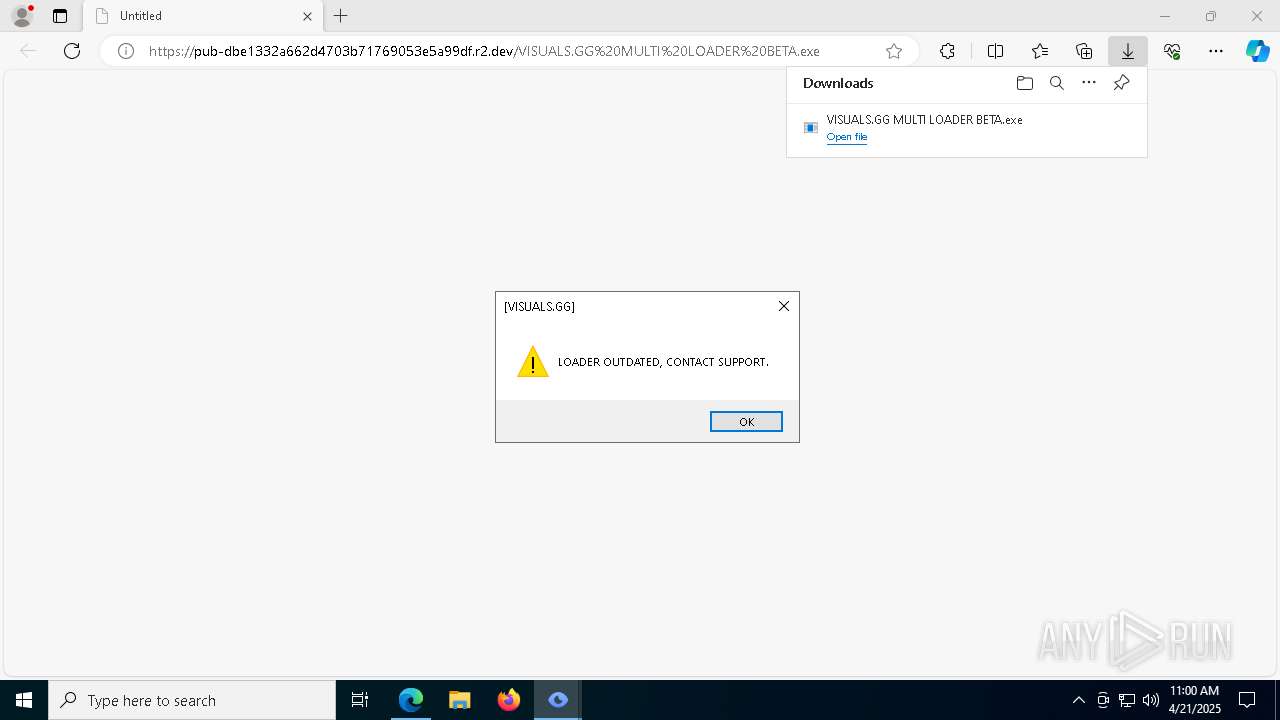
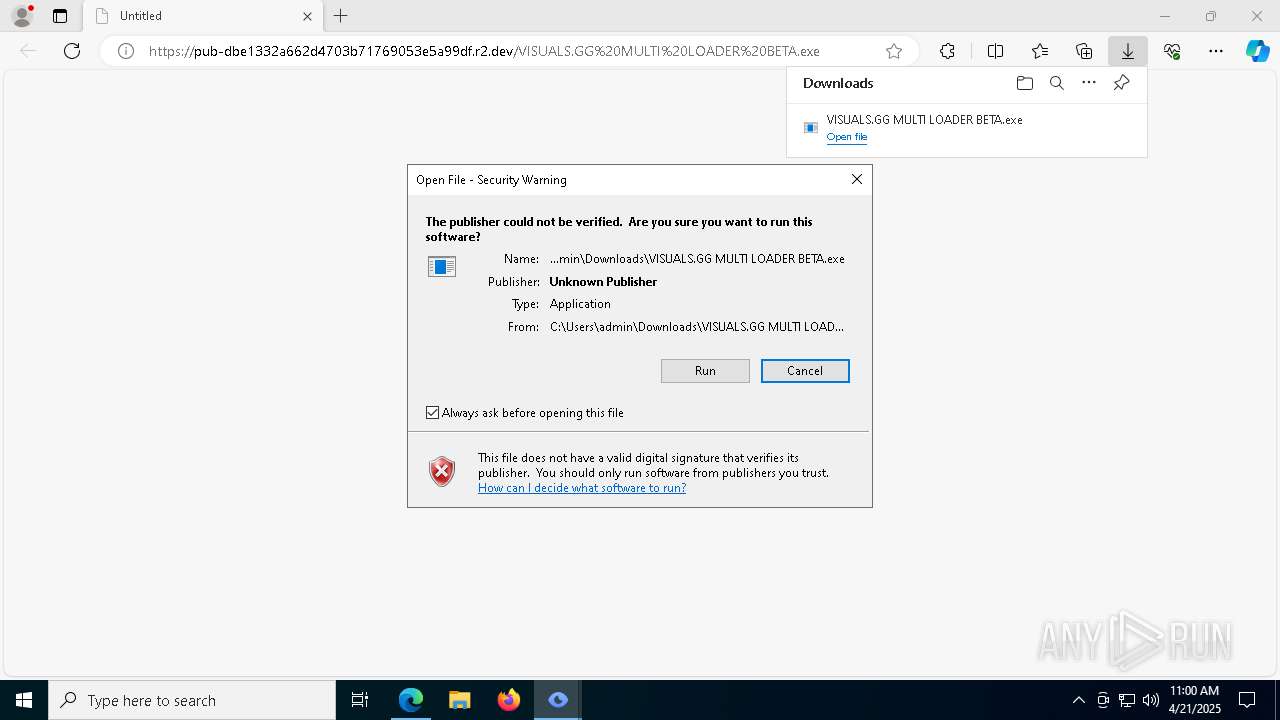
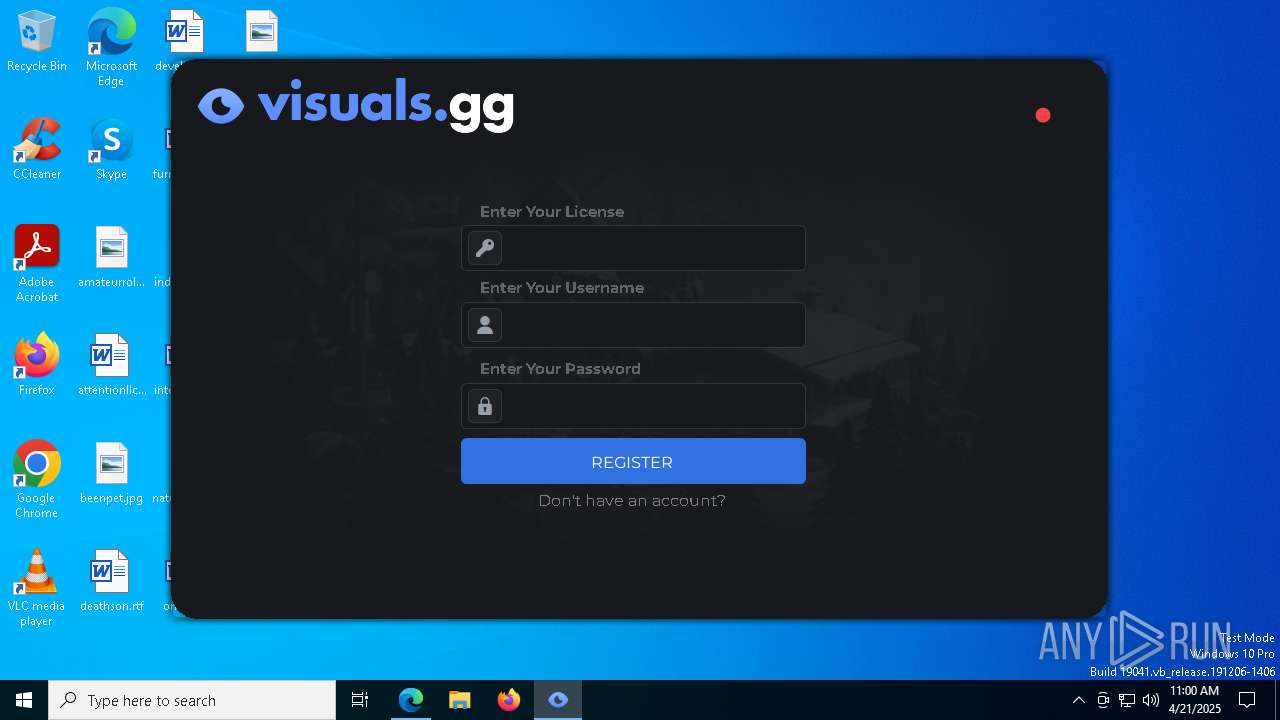
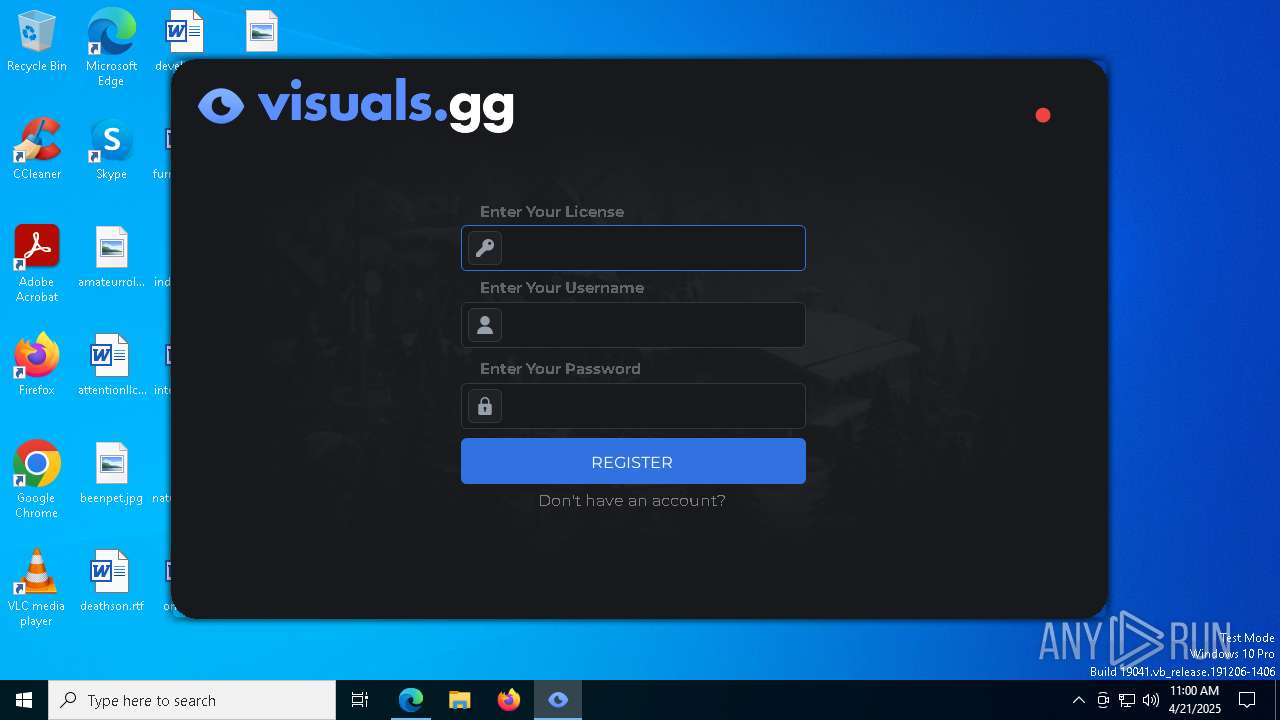
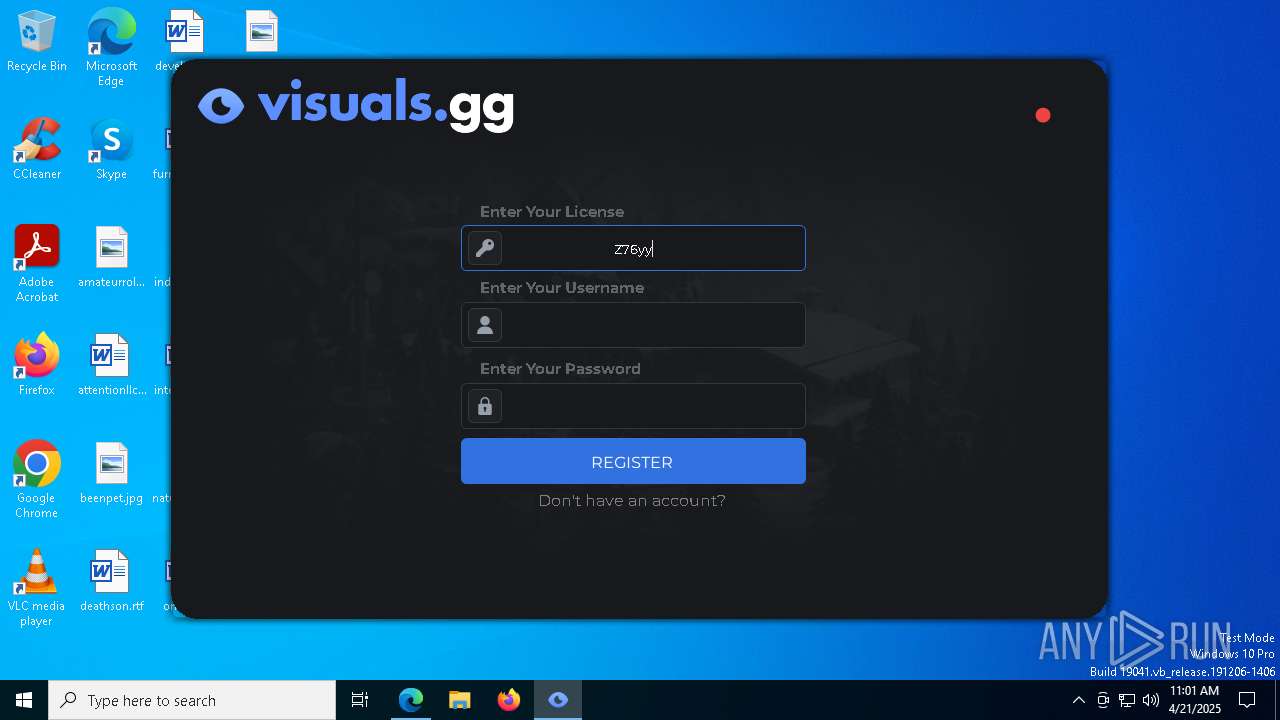
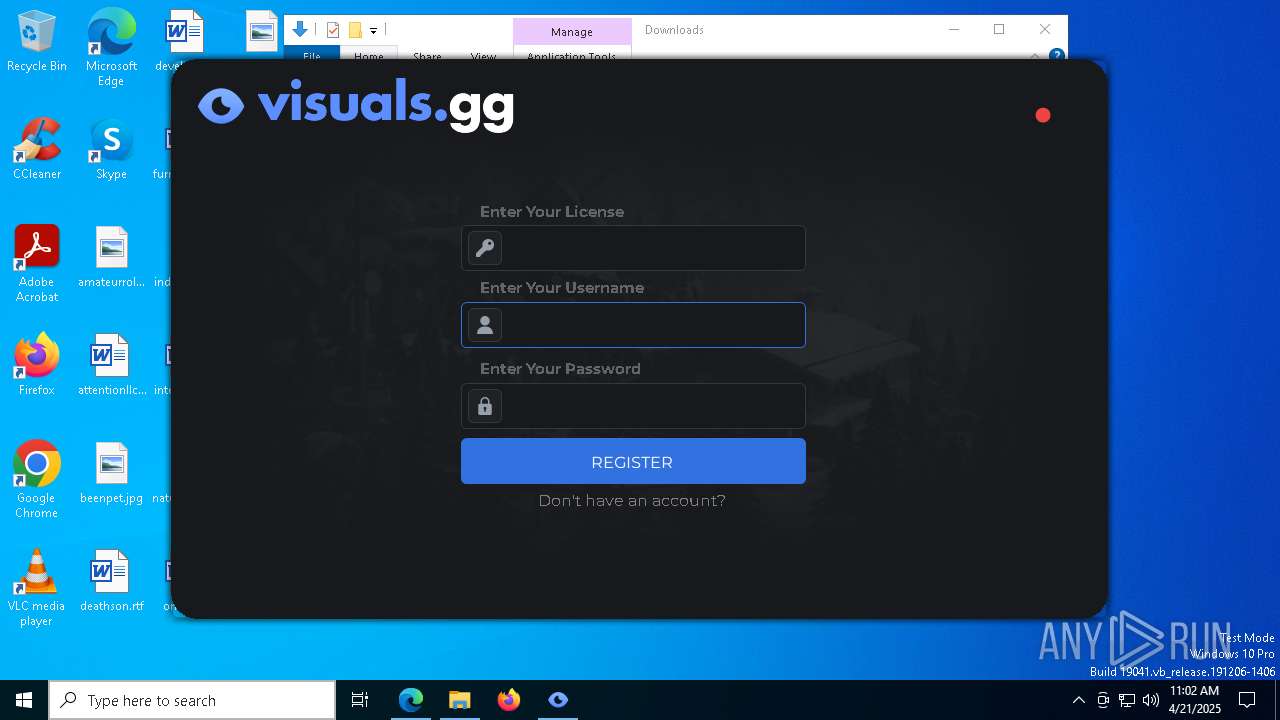
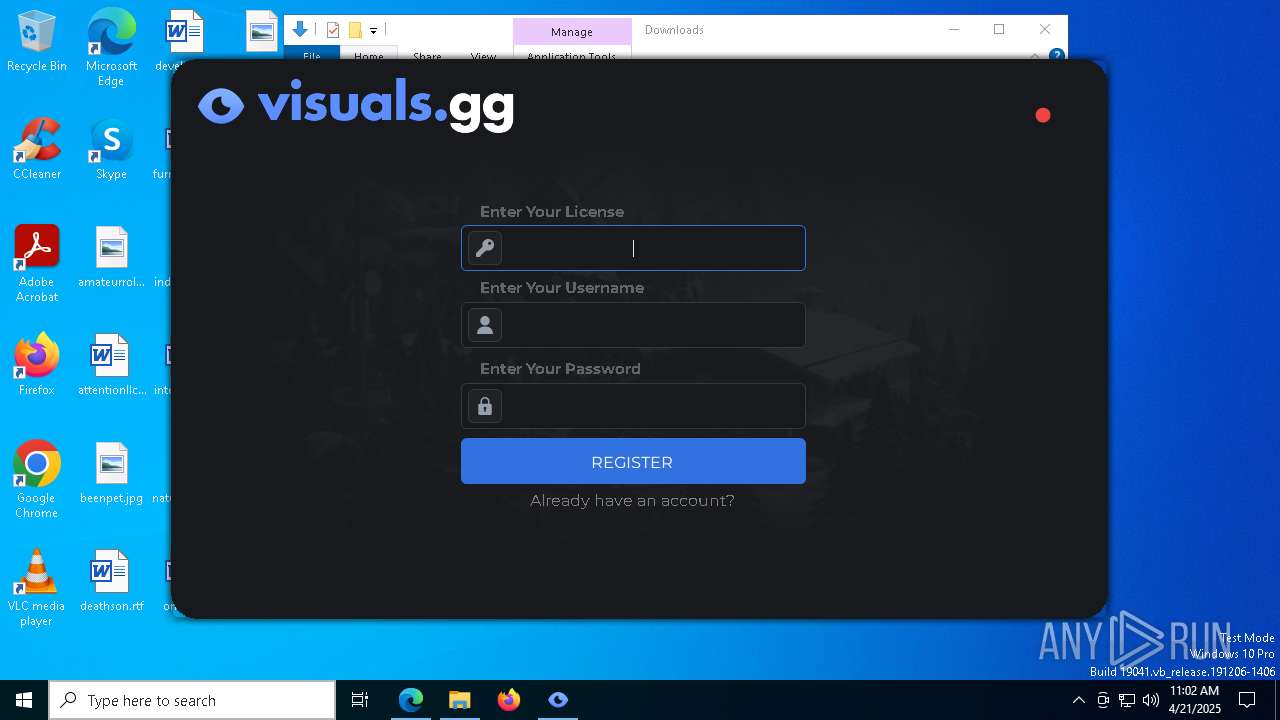
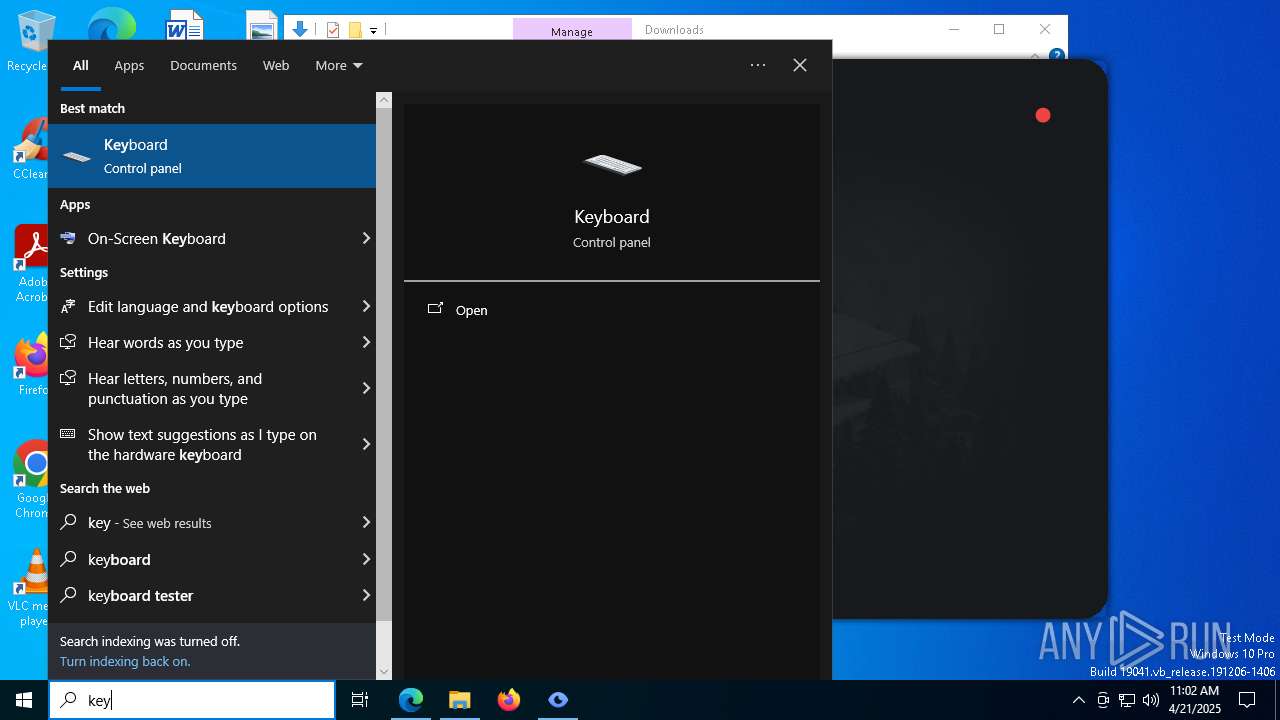
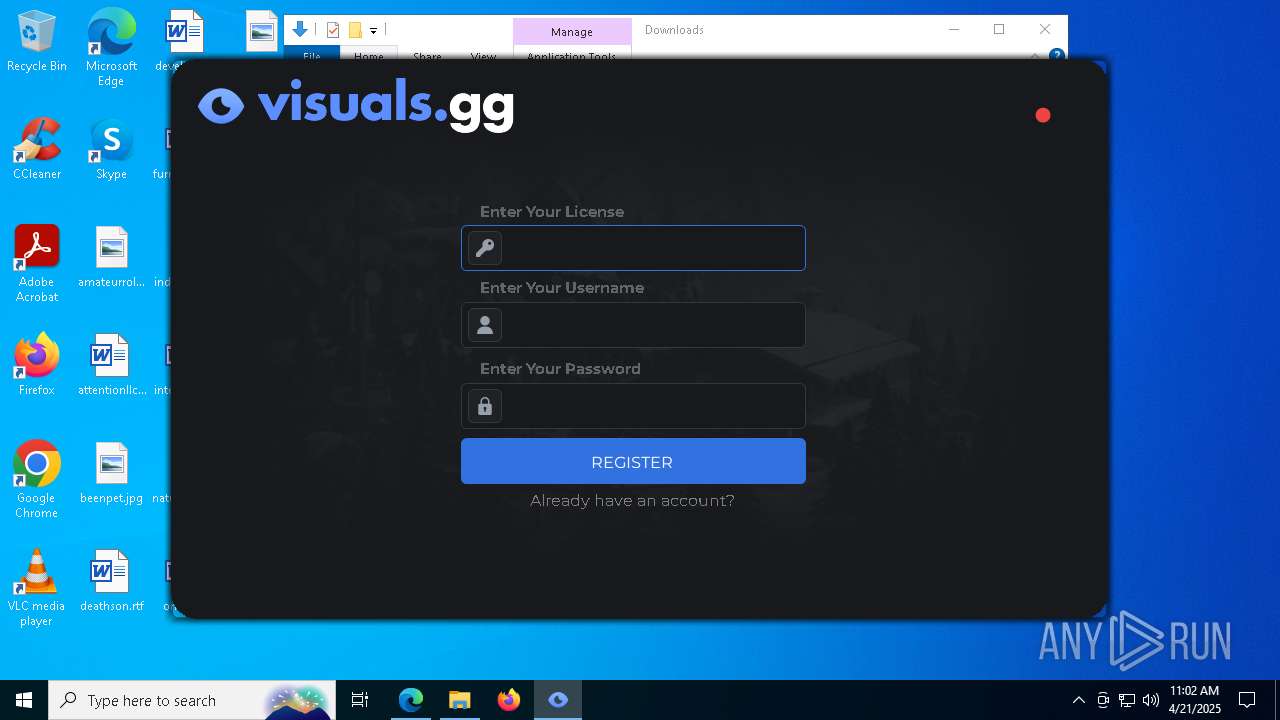
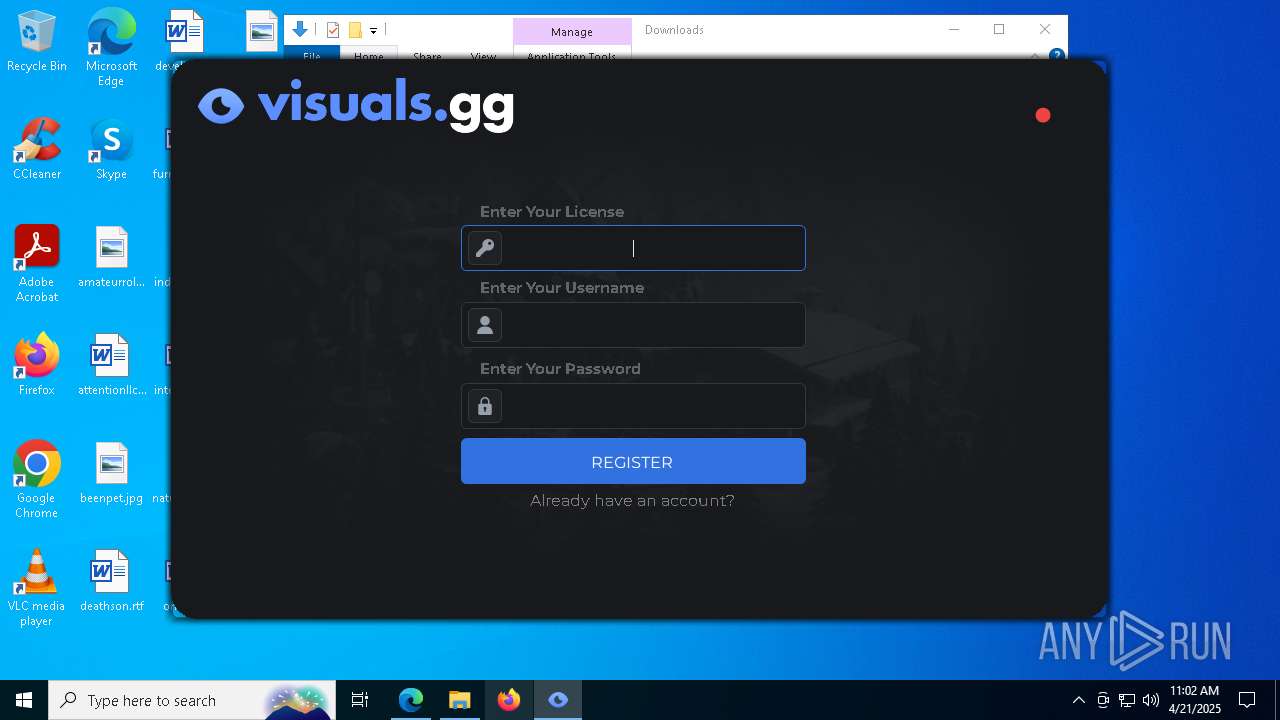
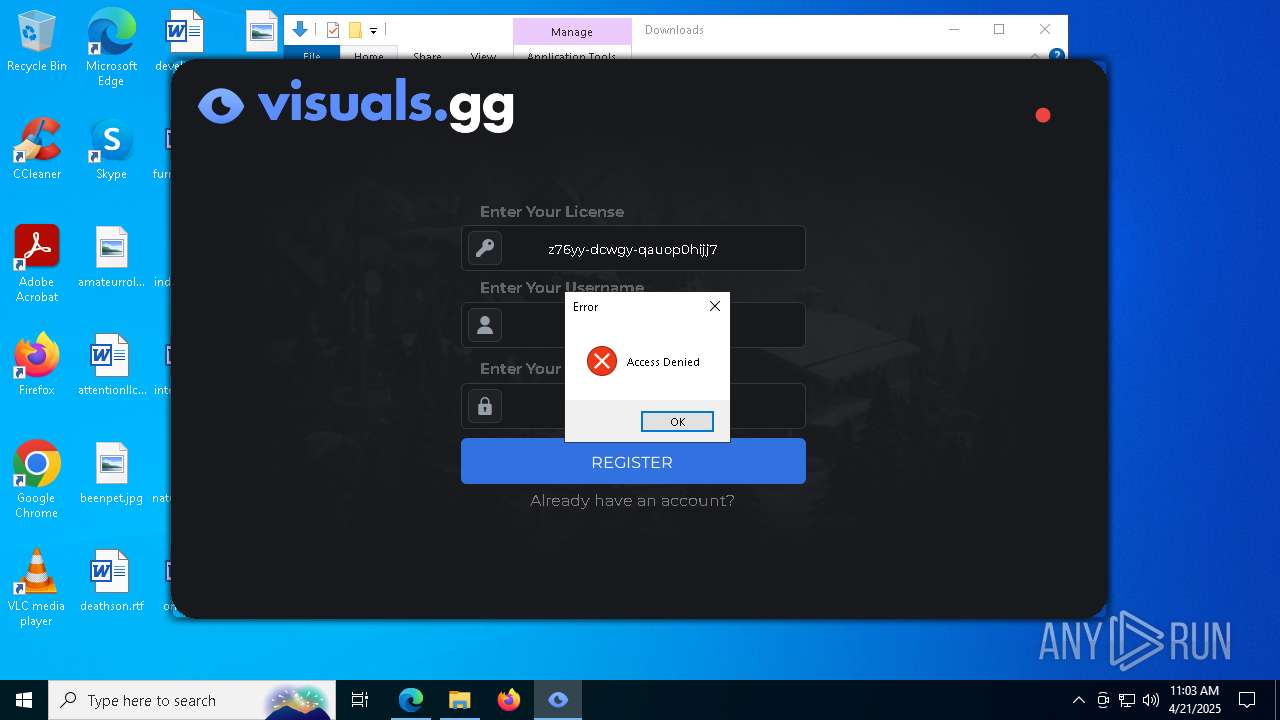
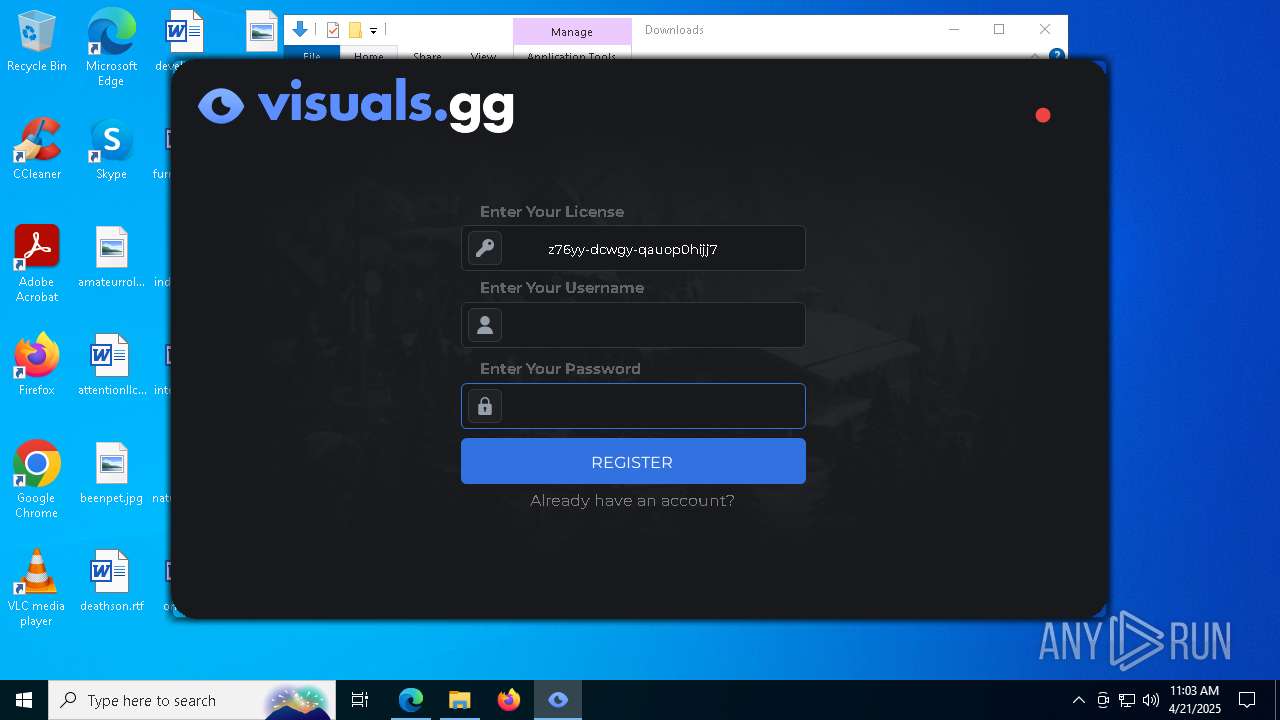
Possible Social Engineering Attempted
- msedge.exe (PID: 7292)
The process checks if it is being run in the virtual environment
- VISUALS.GG MULTI LOADER BETA.exe (PID: 5384)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 1244)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 632)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 3156)
Reads the BIOS version
- VISUALS.GG MULTI LOADER BETA.exe (PID: 1244)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 632)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 5384)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 3156)
Read disk information to detect sandboxing environments
- VISUALS.GG MULTI LOADER BETA.exe (PID: 5384)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 1244)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 632)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 3156)
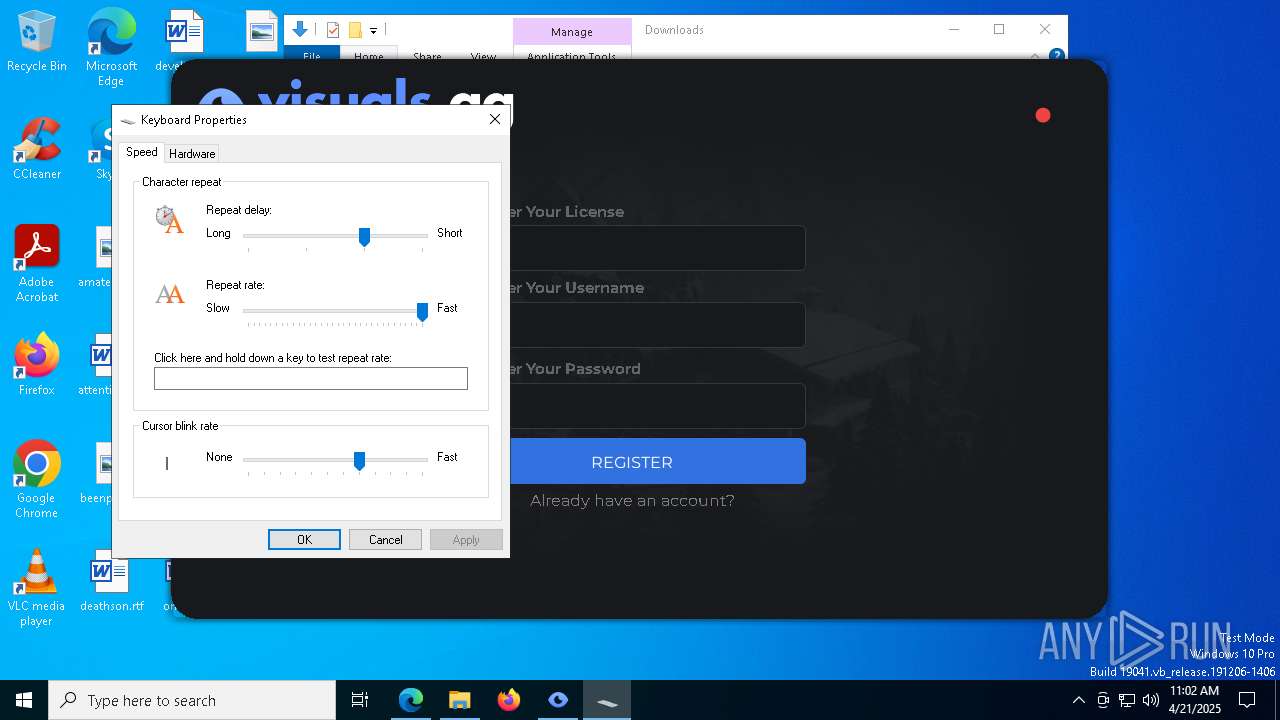
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6032)
- cmd.exe (PID: 5936)
- cmd.exe (PID: 5352)
- cmd.exe (PID: 3140)
- cmd.exe (PID: 7784)
- cmd.exe (PID: 7872)
Application launched itself
- VISUALS.GG MULTI LOADER BETA.exe (PID: 1244)
Starts CMD.EXE for commands execution
- VISUALS.GG MULTI LOADER BETA.exe (PID: 1244)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 632)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 3156)
Reads security settings of Internet Explorer
- VISUALS.GG MULTI LOADER BETA.exe (PID: 632)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 1244)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 3156)
There is functionality for taking screenshot (YARA)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 632)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 3156)
INFO
Checks supported languages
- identity_helper.exe (PID: 7868)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 5384)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 1244)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 632)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 3156)
Reads Environment values
- identity_helper.exe (PID: 7868)
Reads the computer name
- identity_helper.exe (PID: 7868)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 5384)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 1244)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 3156)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 632)
Executable content was dropped or overwritten
- msedge.exe (PID: 2340)
- msedge.exe (PID: 2420)
Application launched itself
- msedge.exe (PID: 2340)
Reads the machine GUID from the registry
- VISUALS.GG MULTI LOADER BETA.exe (PID: 5384)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 1244)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 632)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 3156)
Checks proxy server information
- VISUALS.GG MULTI LOADER BETA.exe (PID: 1244)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 5384)
- slui.exe (PID: 5964)
Reads the software policy settings
- VISUALS.GG MULTI LOADER BETA.exe (PID: 5384)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 1244)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 632)
- slui.exe (PID: 6808)
- slui.exe (PID: 5964)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 3156)
Creates files or folders in the user directory
- VISUALS.GG MULTI LOADER BETA.exe (PID: 5384)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 1244)
Creates files in the program directory
- VISUALS.GG MULTI LOADER BETA.exe (PID: 1244)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 5384)
Process checks computer location settings
- VISUALS.GG MULTI LOADER BETA.exe (PID: 1244)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 3156)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 632)
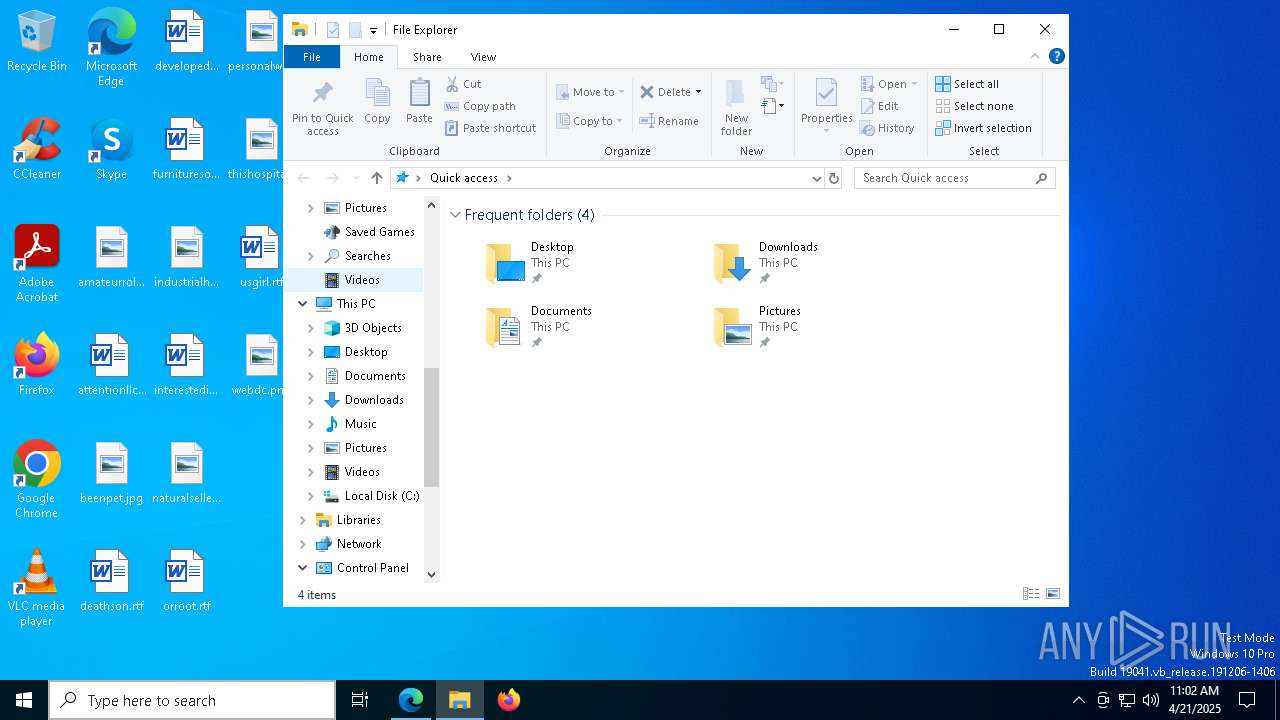
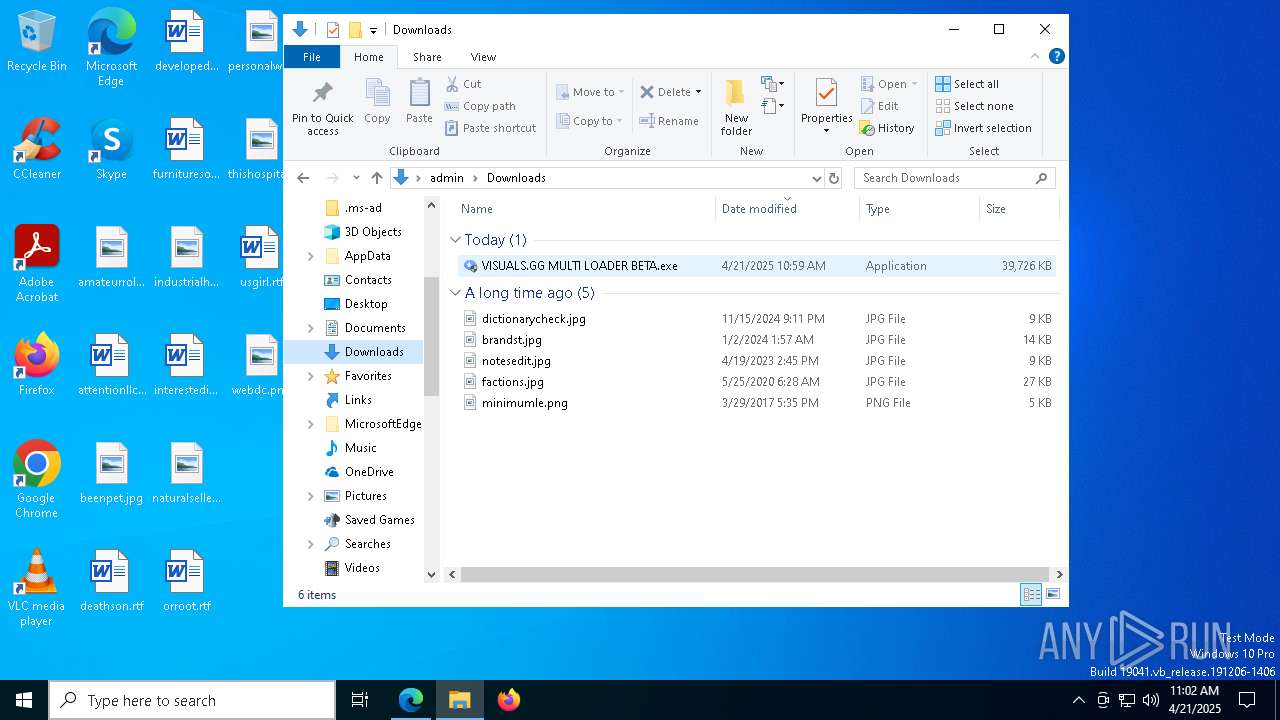
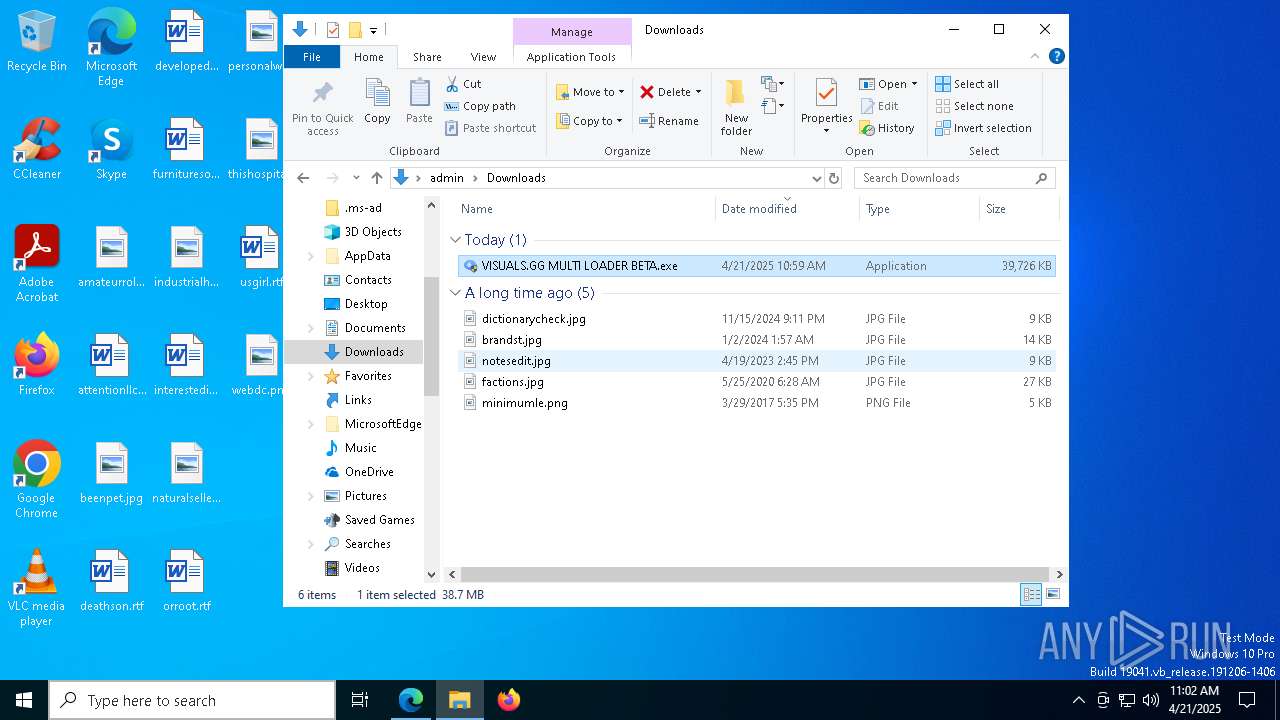
Manual execution by a user
- VISUALS.GG MULTI LOADER BETA.exe (PID: 4692)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 3156)
Confuser has been detected (YARA)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 632)
- VISUALS.GG MULTI LOADER BETA.exe (PID: 3156)
The sample compiled with english language support
- msedge.exe (PID: 2420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
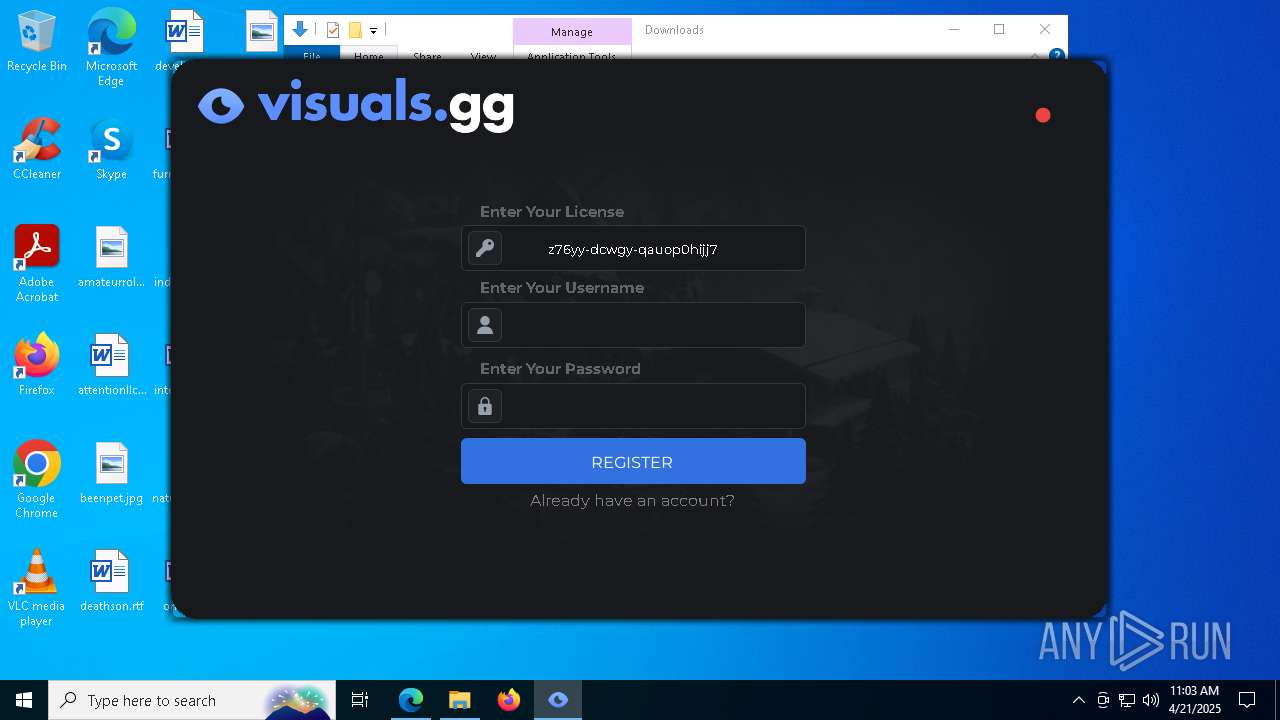
xor-url
(PID) Process(632) VISUALS.GG MULTI LOADER BETA.exe
Decrypted-URLs (2)https://google.com
https://keyauth.win/api/1.2/
(PID) Process(3156) VISUALS.GG MULTI LOADER BETA.exe
Decrypted-URLs (1)https://google.com
Total processes
221
Monitored processes
81
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | "C:\Users\admin\Downloads\VISUALS.GG MULTI LOADER BETA.exe" | C:\Users\admin\Downloads\VISUALS.GG MULTI LOADER BETA.exe | VISUALS.GG MULTI LOADER BETA.exe | ||||||||||||
User: admin Company: Official Integrity Level: HIGH Description: Visuals Official Spoofer Exit code: 0 Version: 1.0.0.0 Modules
xor-url(PID) Process(632) VISUALS.GG MULTI LOADER BETA.exe Decrypted-URLs (2)https://google.com https://keyauth.win/api/1.2/ | |||||||||||||||
| 684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=2200 --field-trial-handle=2328,i,15505868889934252588,9140002980638215086,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 900 | "C:\Users\admin\Downloads\VISUALS.GG MULTI LOADER BETA.exe" | C:\Users\admin\Downloads\VISUALS.GG MULTI LOADER BETA.exe | — | msedge.exe | |||||||||||
User: admin Company: Official Integrity Level: MEDIUM Description: Visuals Official Spoofer Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1532 --field-trial-handle=2328,i,15505868889934252588,9140002980638215086,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 904 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4088 --field-trial-handle=2328,i,15505868889934252588,9140002980638215086,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1244 | "C:\Users\admin\Downloads\VISUALS.GG MULTI LOADER BETA.exe" | C:\Users\admin\Downloads\VISUALS.GG MULTI LOADER BETA.exe | msedge.exe | ||||||||||||
User: admin Company: Official Integrity Level: HIGH Description: Visuals Official Spoofer Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1452 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7072 --field-trial-handle=2328,i,15505868889934252588,9140002980638215086,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1452 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7344 --field-trial-handle=2328,i,15505868889934252588,9140002980638215086,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1764 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5976 --field-trial-handle=2328,i,15505868889934252588,9140002980638215086,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
16 405
Read events
16 385
Write events
20
Delete events
0
Modification events
| (PID) Process: | (2340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2340) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 604D570CDE912F00 | |||
| (PID) Process: | (2340) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: C789640CDE912F00 | |||
| (PID) Process: | (2340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590534 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {23385566-EB0B-4EB6-941F-BE72B17D9194} | |||
| (PID) Process: | (2340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590534 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7520D293-D241-4468-ACDE-225D18D3EEE8} | |||
| (PID) Process: | (2340) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4FD3A40CDE912F00 | |||
| (PID) Process: | (2340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
16
Suspicious files
400
Text files
83
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bb62.TMP | — | |
MD5:— | SHA256:— | |||
| 2340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bb62.TMP | — | |
MD5:— | SHA256:— | |||
| 2340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bb62.TMP | — | |
MD5:— | SHA256:— | |||
| 2340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bb72.TMP | — | |
MD5:— | SHA256:— | |||
| 2340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bb82.TMP | — | |
MD5:— | SHA256:— | |||
| 2340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
61
TCP/UDP connections
153
DNS requests
70
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.82:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5384 | VISUALS.GG MULTI LOADER BETA.exe | GET | 200 | 216.58.206.67:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5384 | VISUALS.GG MULTI LOADER BETA.exe | GET | 200 | 216.58.206.67:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
1244 | VISUALS.GG MULTI LOADER BETA.exe | GET | 200 | 216.58.206.67:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
1244 | VISUALS.GG MULTI LOADER BETA.exe | GET | 200 | 216.58.206.67:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
1244 | VISUALS.GG MULTI LOADER BETA.exe | GET | 200 | 216.58.206.67:80 | http://o.pki.goog/s/we1/YhI/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS5vtXxph5AskGWsMKefhqdi%2Fy1IAQUkHeSNWfE%2F6jMqeZ72YB5e8yT%2BTgCEGISd2Hu%2BLNwERZy%2FOIDSPY%3D | unknown | — | — | whitelisted |
1244 | VISUALS.GG MULTI LOADER BETA.exe | GET | 200 | 216.58.206.67:80 | http://o.pki.goog/we2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuMJxAT2trYla0jia%2F5EUSmLrk3QQUdb7Ed66J9kQ3fc%2BxaB8dGuvcNFkCEAJxg9SoJXkHCj2PYJ4nzeU%3D | unknown | — | — | whitelisted |
5384 | VISUALS.GG MULTI LOADER BETA.exe | GET | 200 | 216.58.206.67:80 | http://o.pki.goog/we2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuMJxAT2trYla0jia%2F5EUSmLrk3QQUdb7Ed66J9kQ3fc%2BxaB8dGuvcNFkCEAJxg9SoJXkHCj2PYJ4nzeU%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.164.82:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2340 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7292 | msedge.exe | 52.123.243.84:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | DE | whitelisted |
7292 | msedge.exe | 172.66.0.235:443 | pub-dbe1332a662d4703b71769053e5a99df.r2.dev | — | US | suspicious |
7292 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7292 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
pub-dbe1332a662d4703b71769053e5a99df.r2.dev |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7292 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] CloudFlare Public R2.dev Bucket |
7292 | msedge.exe | Possible Social Engineering Attempted | SUSPICIOUS [ANY.RUN] Abuse Public R2.dev Bucket |
7292 | msedge.exe | Possible Social Engineering Attempted | SUSPICIOUS [ANY.RUN] Abuse Public R2.dev Bucket |
7292 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] CloudFlare Public R2.dev Bucket |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain in DNS Lookup (keyauth .win) |
1244 | VISUALS.GG MULTI LOADER BETA.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain (keyauth .win) in TLS SNI |
5384 | VISUALS.GG MULTI LOADER BETA.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain (keyauth .win) in TLS SNI |
632 | VISUALS.GG MULTI LOADER BETA.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain (keyauth .win) in TLS SNI |
3156 | VISUALS.GG MULTI LOADER BETA.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain (keyauth .win) in TLS SNI |