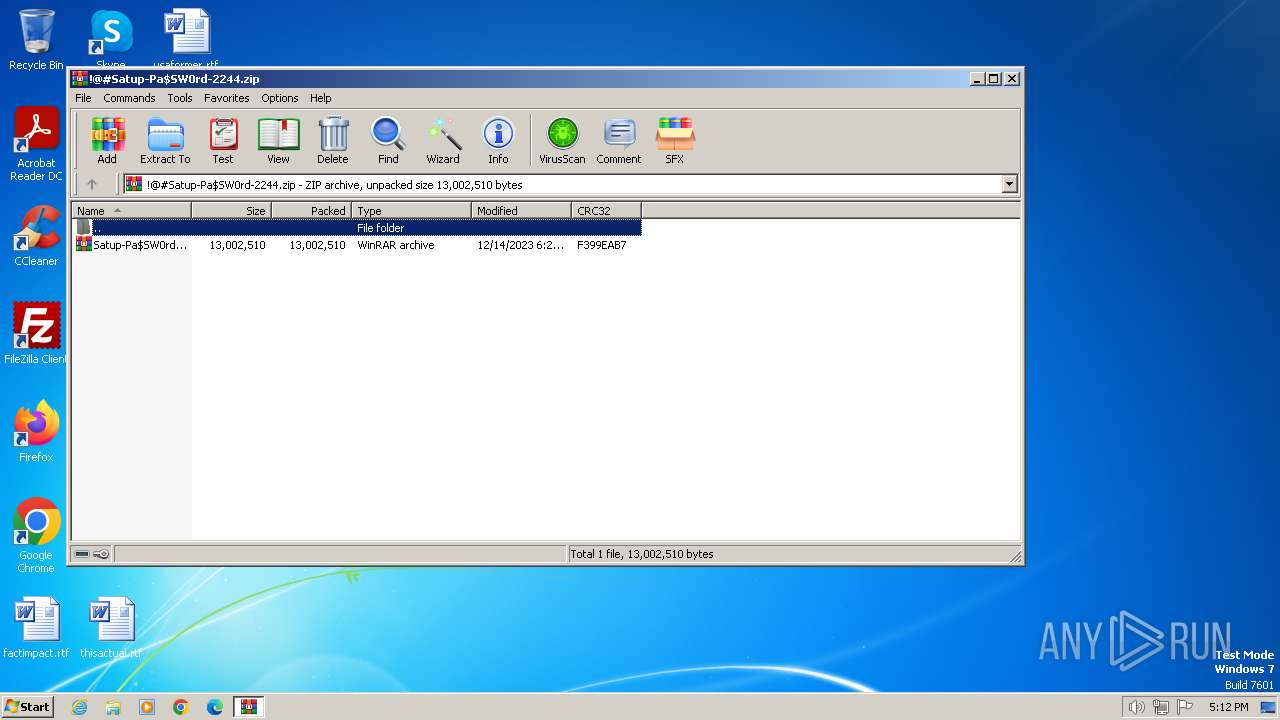
| File name: | !@#Satup-Pa$SW0rd-2244.zip |
| Full analysis: | https://app.any.run/tasks/f4c671e8-6d5c-4286-855c-01dfe8db4e53 |
| Verdict: | Malicious activity |
| Analysis date: | December 27, 2023, 17:12:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
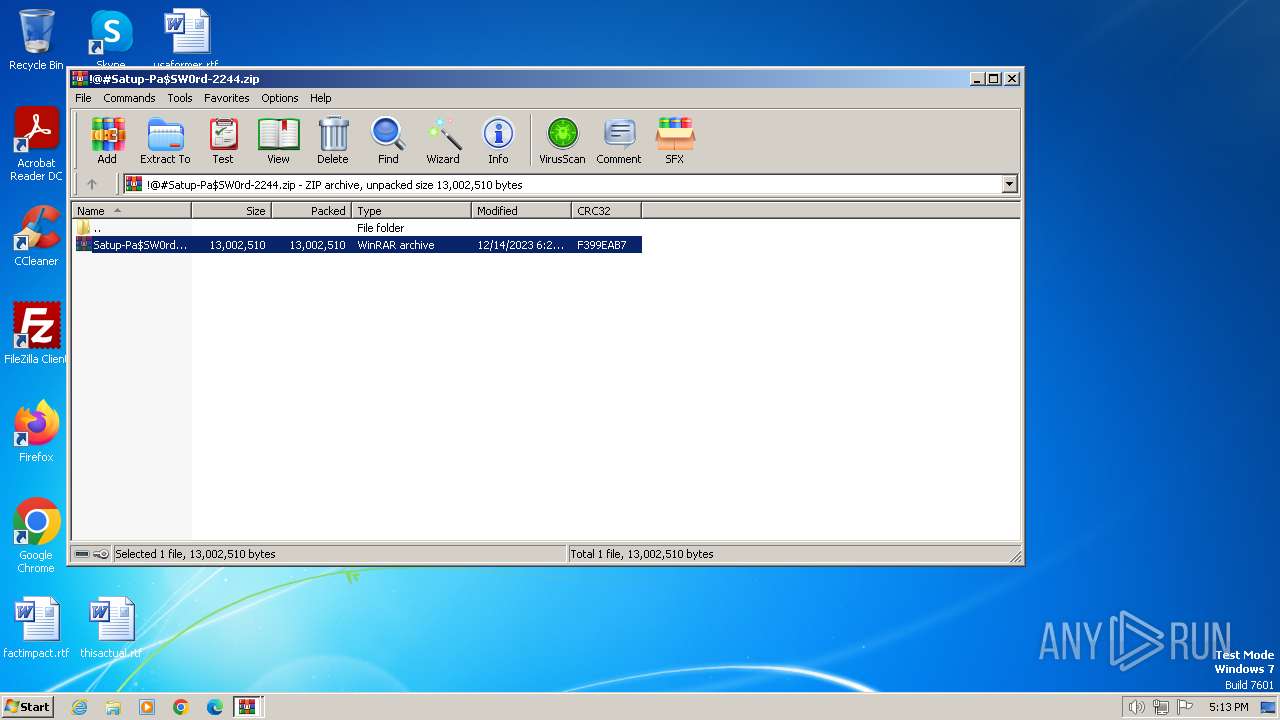
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 6BFD23D2299759DDD9691C584B210325 |
| SHA1: | A6444A29476522A24E0F81FEA6B35028E01D1C6C |
| SHA256: | 723BAEE48C53CCA97FD66FBAF6C6D701FF8AAA99B1BBCC60FE524E16A02C6572 |
| SSDEEP: | 98304:dy3RUIMqJsM1aVL0Ko+QR9e8JrXZg/bdGqZ+P96+WVw79M2ggn7NhljrSH6aX34q:dc2/CzGkegEk2RVVM2ZL |
MALICIOUS
Uses Task Scheduler to run other applications
- cmd.exe (PID: 1736)
Actions looks like stealing of personal data
- Main__App.exe (PID: 492)
SUSPICIOUS
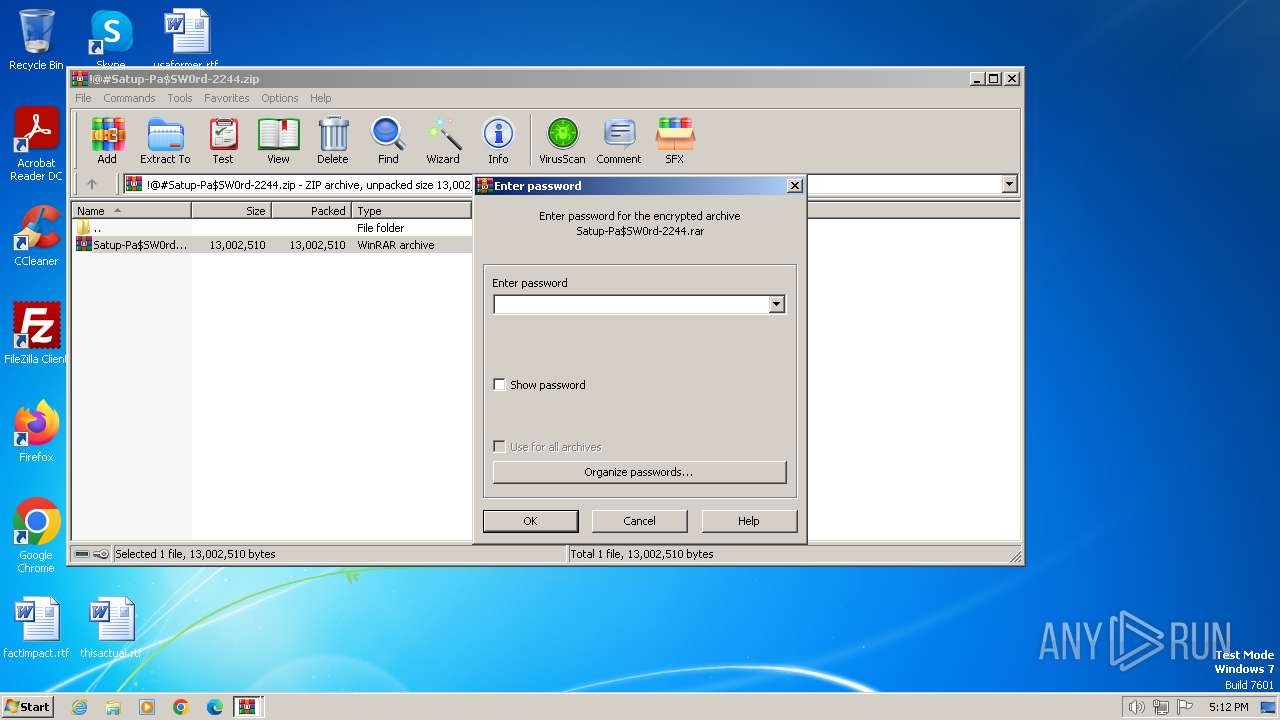
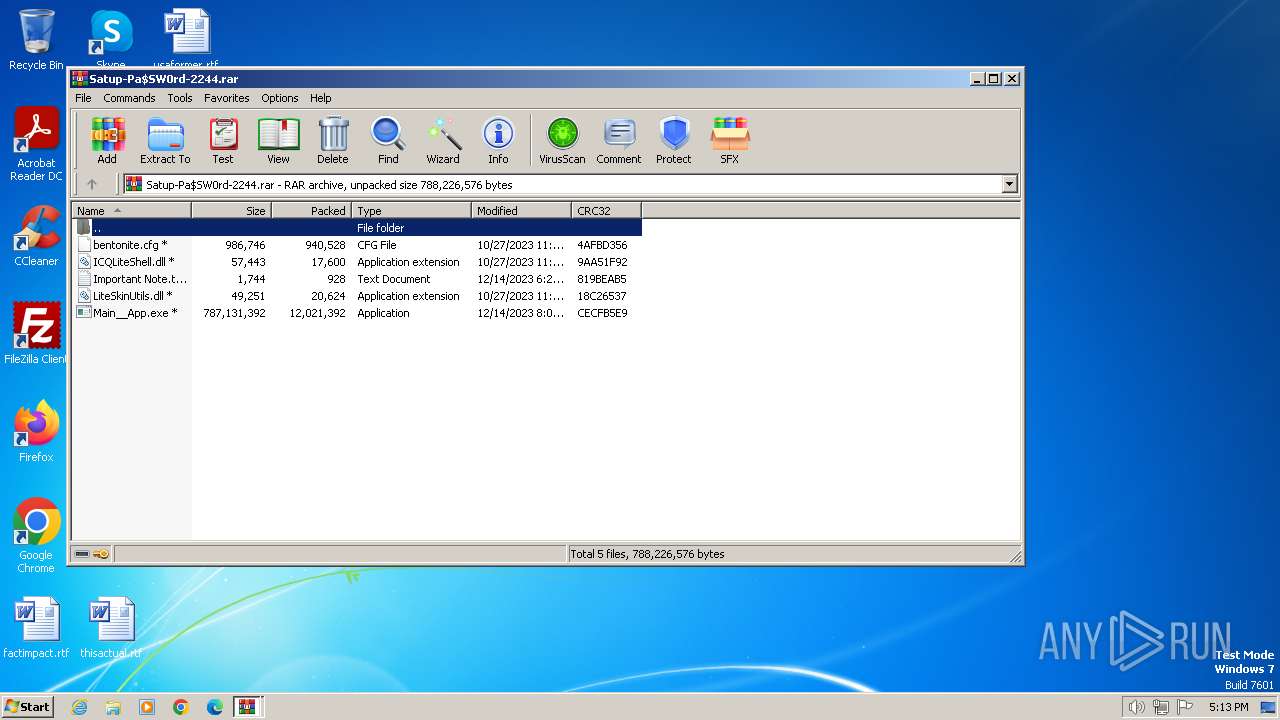
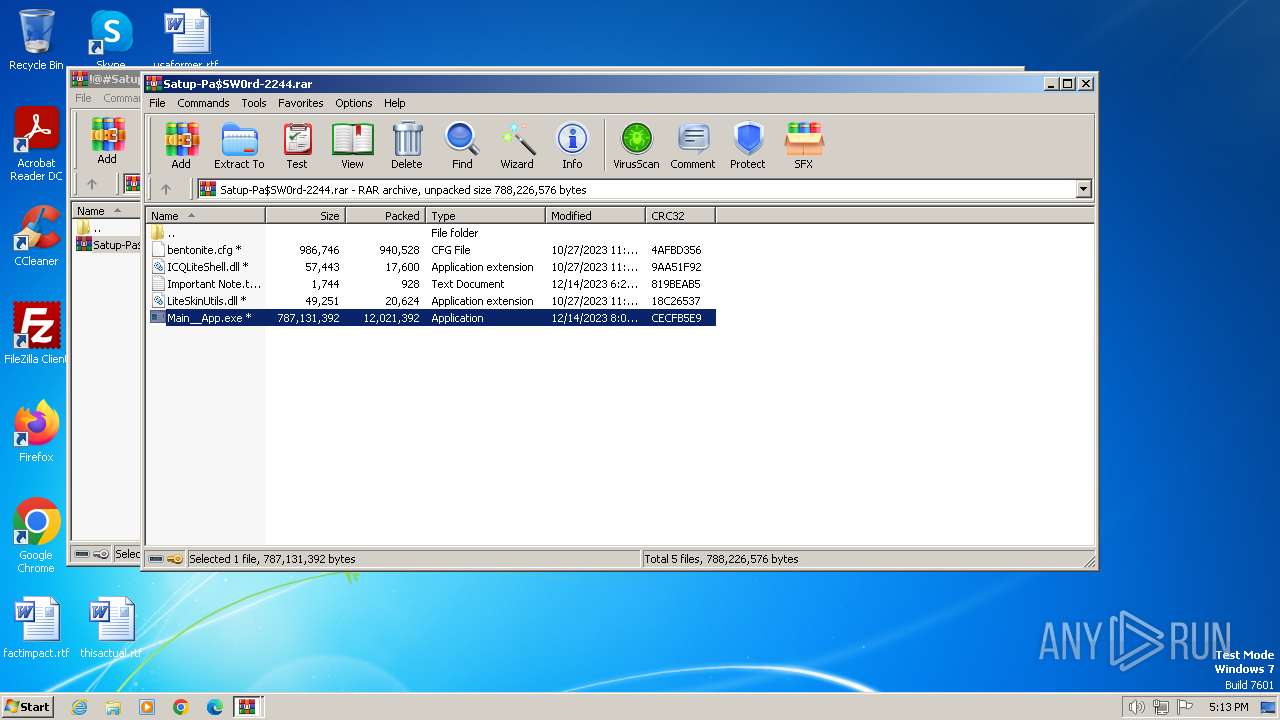
The process creates files with name similar to system file names
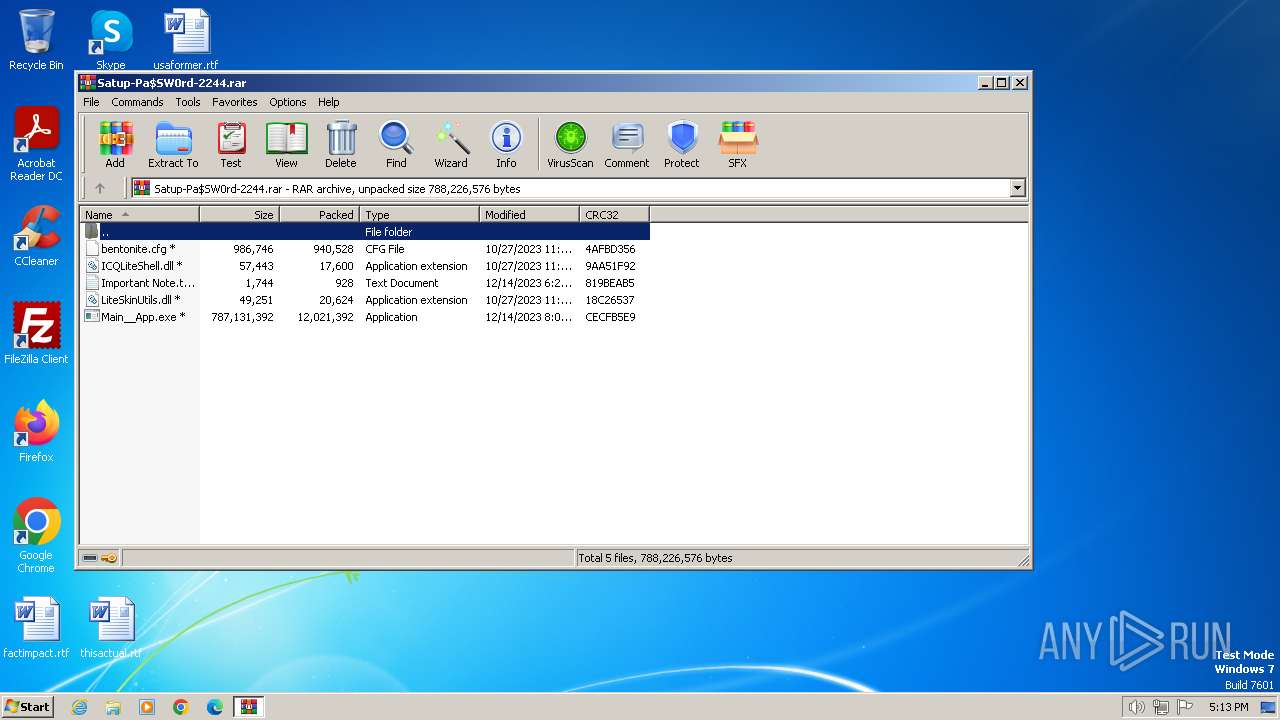
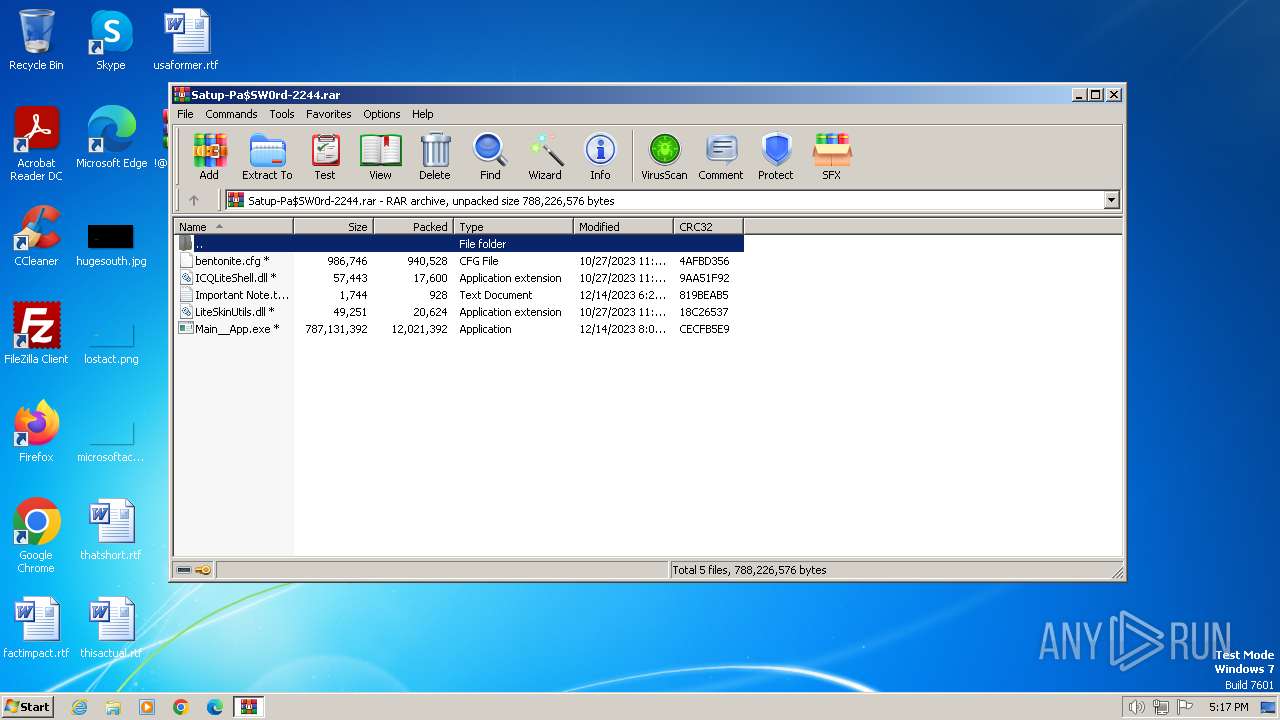
- WinRAR.exe (PID: 2068)
Reads the Internet Settings
- Main__App.exe (PID: 492)
Starts CMD.EXE for commands execution
- Main__App.exe (PID: 492)
Searches for installed software
- Main__App.exe (PID: 492)
INFO
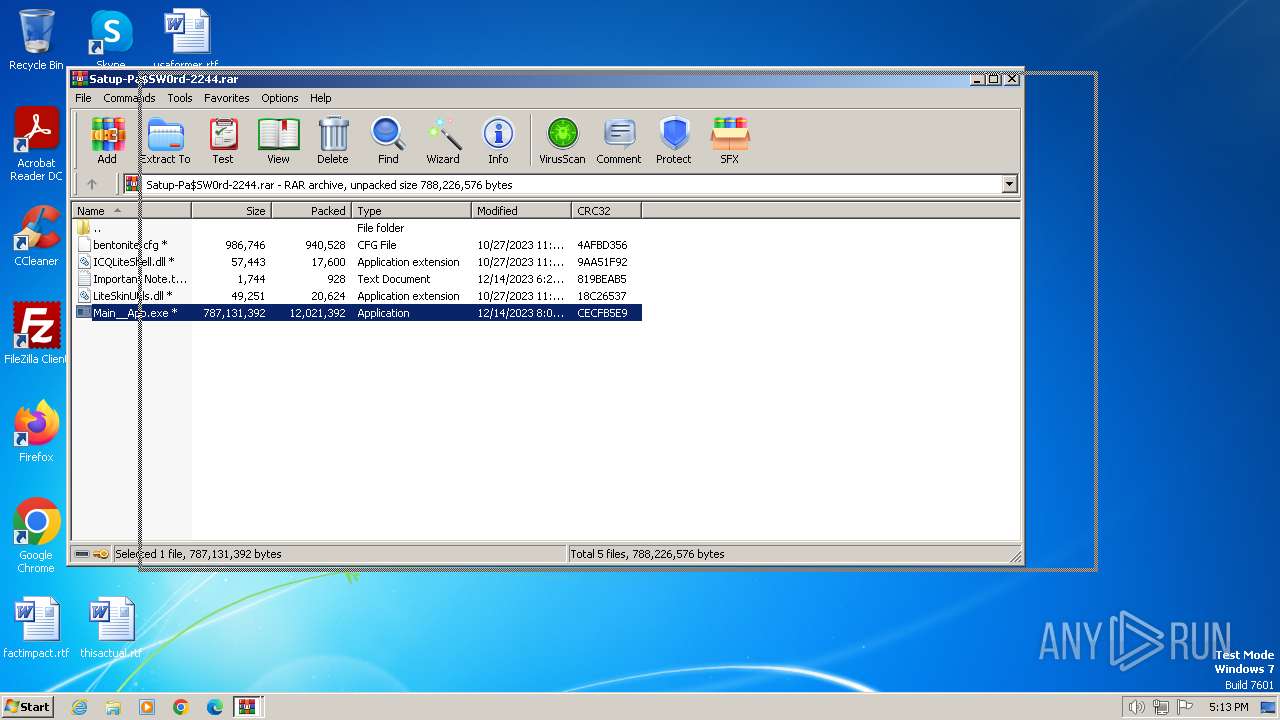
Application launched itself
- WinRAR.exe (PID: 2184)
Checks supported languages
- Main__App.exe (PID: 492)
- Rukevar.exe (PID: 1900)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2068)
- Main__App.exe (PID: 492)
Reads CPU info
- Main__App.exe (PID: 492)
Checks proxy server information
- Main__App.exe (PID: 492)
Reads the machine GUID from the registry
- Main__App.exe (PID: 492)
Creates files or folders in the user directory
- Main__App.exe (PID: 492)
The process executes via Task Scheduler
- Rukevar.exe (PID: 1900)
Reads the computer name
- Main__App.exe (PID: 492)
Drops the AutoIt3 executable file
- Main__App.exe (PID: 492)
Reads mouse settings
- Rukevar.exe (PID: 1900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2023:12:14 23:22:12 |
| ZipCRC: | 0xf399eab7 |
| ZipCompressedSize: | 13002510 |
| ZipUncompressedSize: | 13002510 |
| ZipFileName: | Satup-Pa$SW0rd-2244.rar |
Total processes
42
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
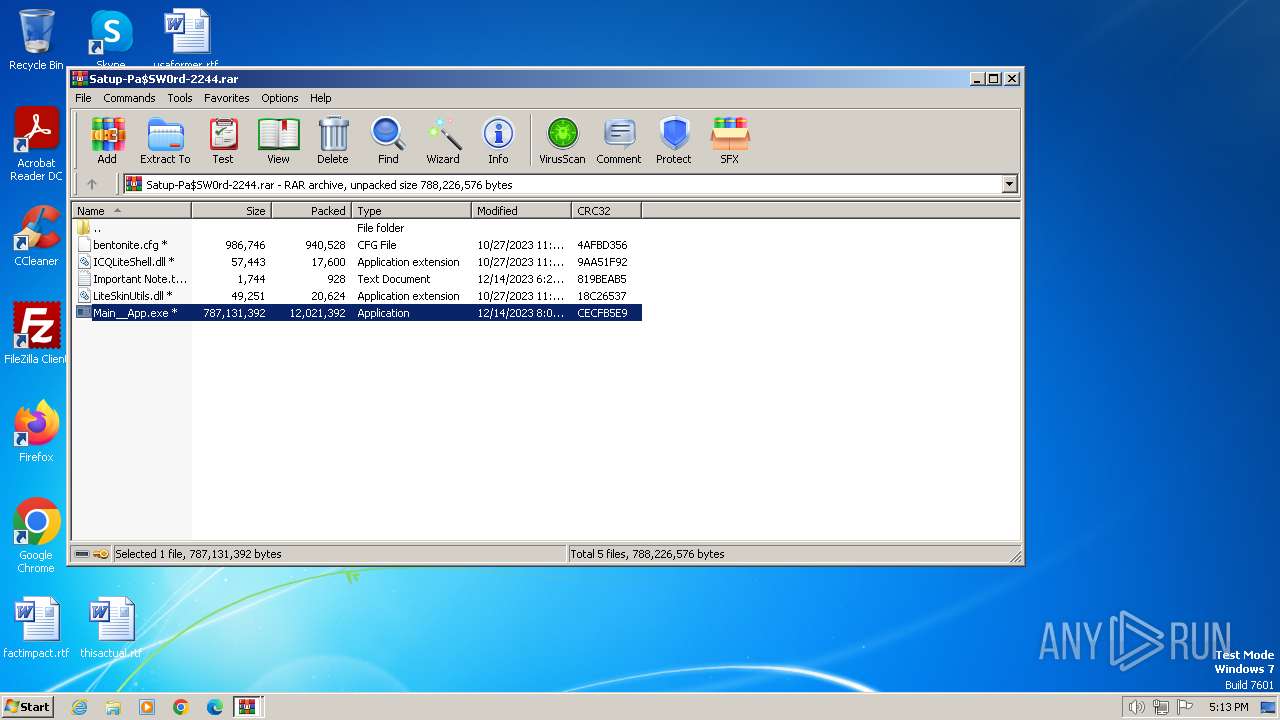
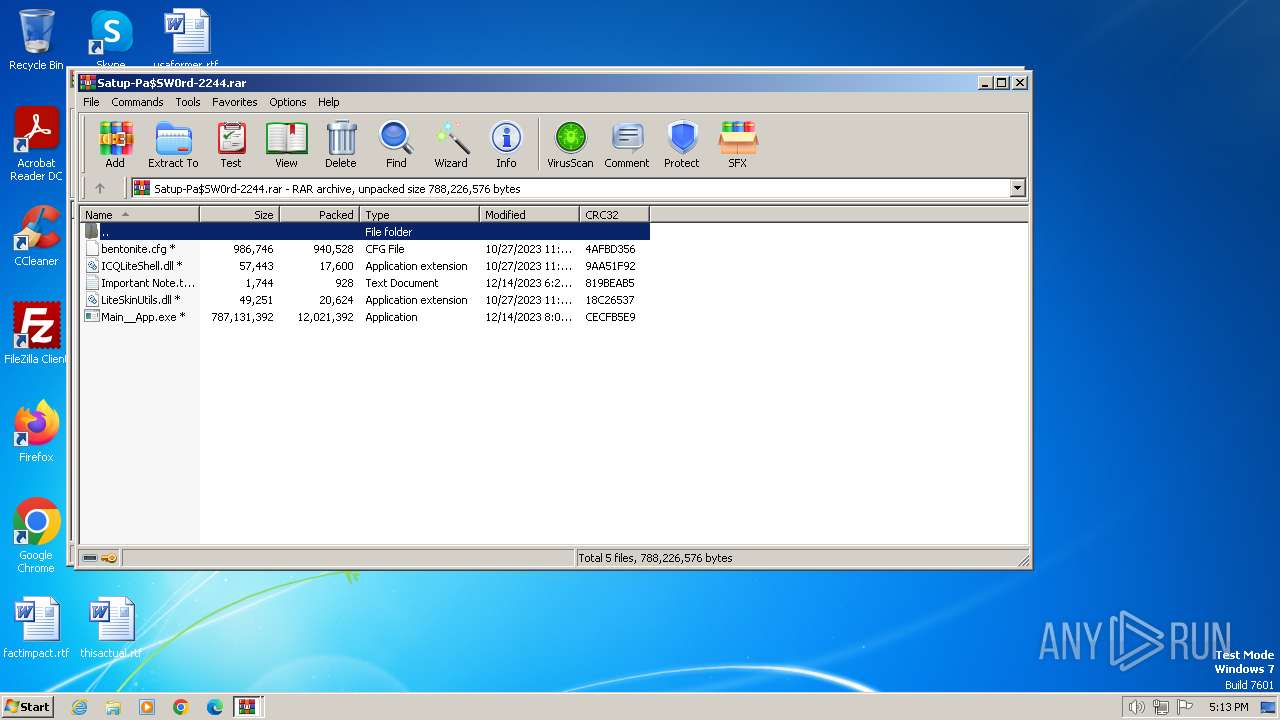
| 492 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2068.16754\Main__App.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2068.16754\Main__App.exe | WinRAR.exe | ||||||||||||
User: admin Company: Busaro Integrity Level: MEDIUM Description: Busaro Setup Exit code: 0 Version: 3.4.3.0 Modules
| |||||||||||||||
| 1736 | "C:\Windows\system32\cmd.exe" /c schtasks /create /tn \Service\Data /tr """"C:\Users\admin\AppData\Roaming\ServiceData\Rukevar.exe""" """C:\Users\admin\AppData\Roaming\ServiceData\Rukevar.jpg"""" /st 00:01 /du 9800:19 /sc once /ri 1 /f | C:\Windows\System32\cmd.exe | — | Main__App.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1900 | C:\Users\admin\AppData\Roaming\ServiceData\Rukevar.exe "C:\Users\admin\AppData\Roaming\ServiceData\Rukevar.jpg" | C:\Users\admin\AppData\Roaming\ServiceData\Rukevar.exe | — | taskeng.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 16, 1 Modules
| |||||||||||||||
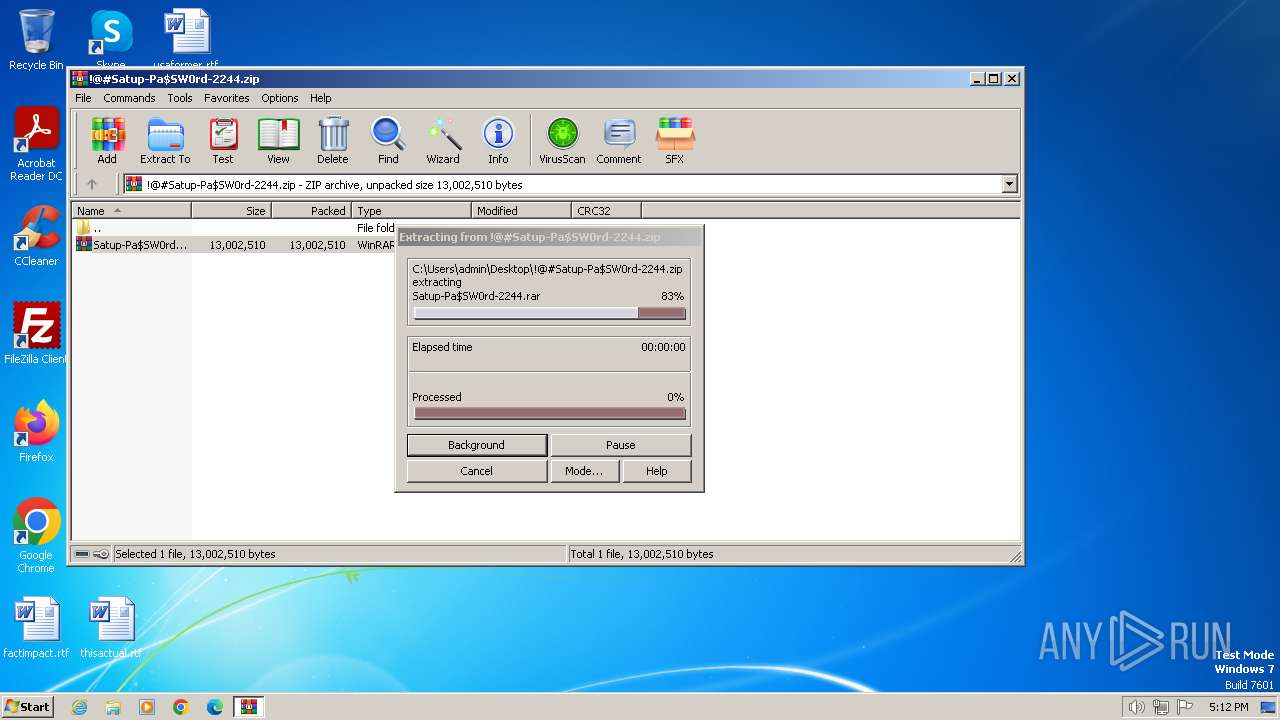
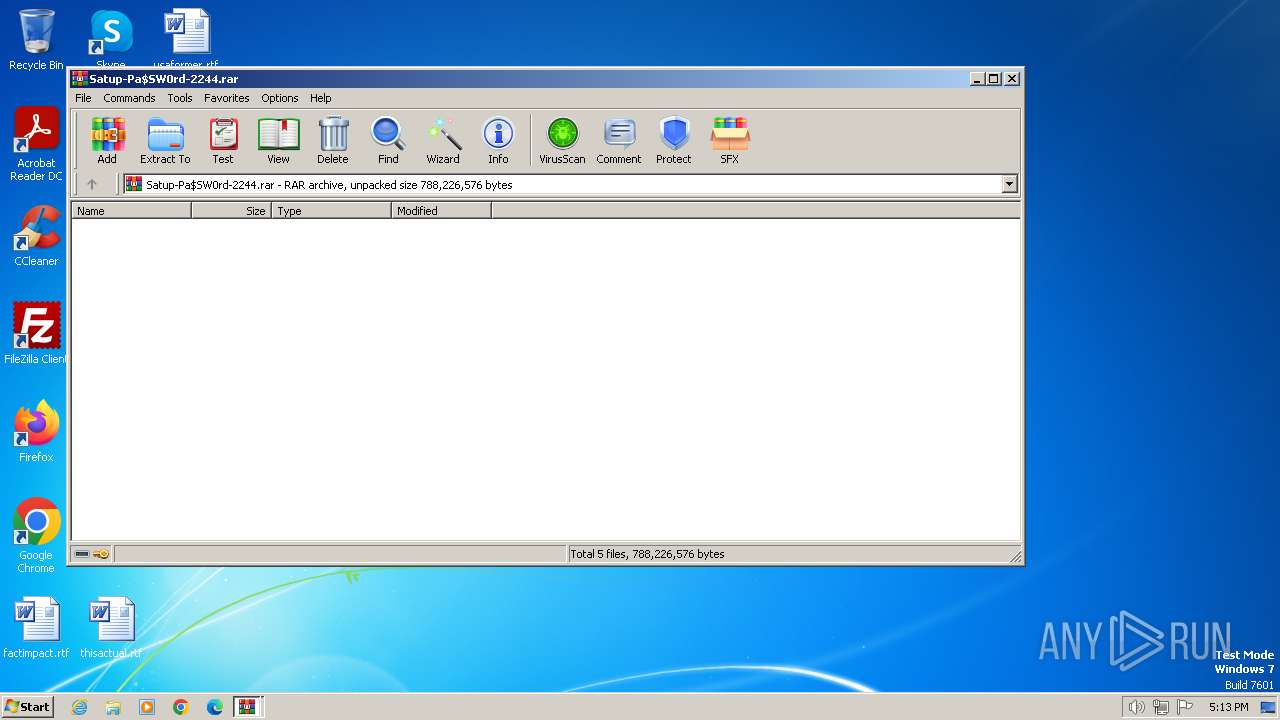
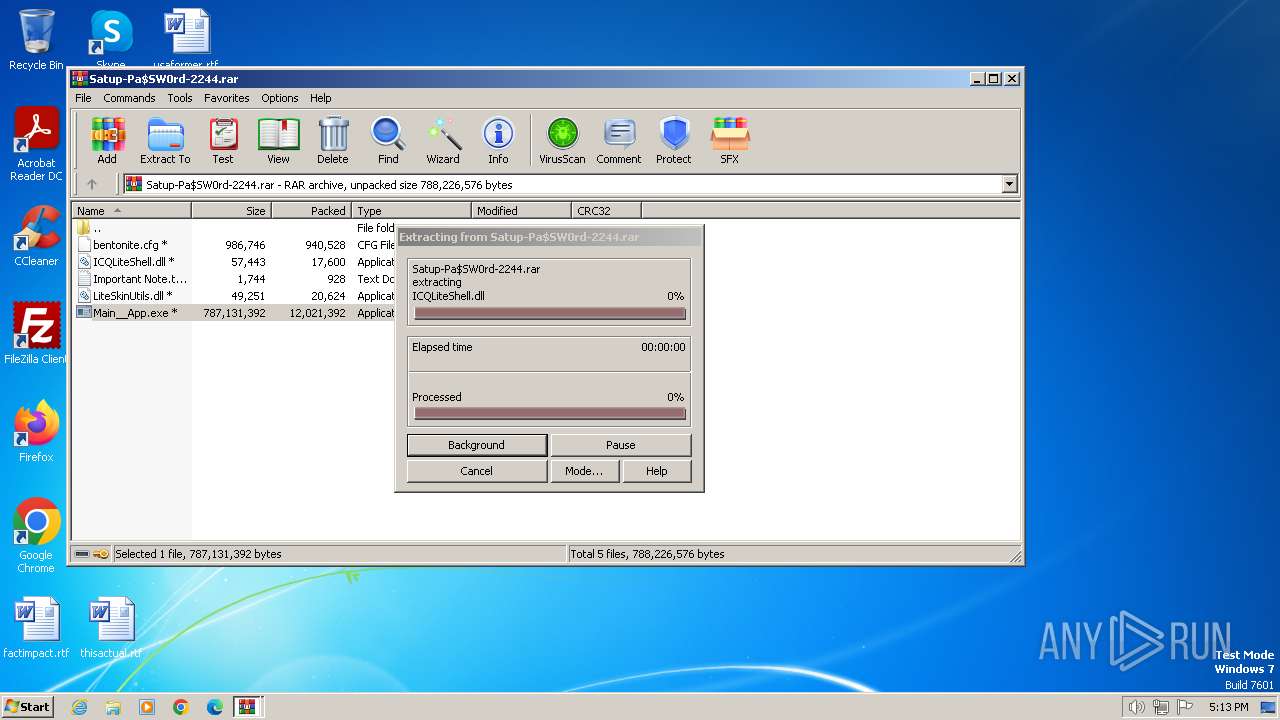
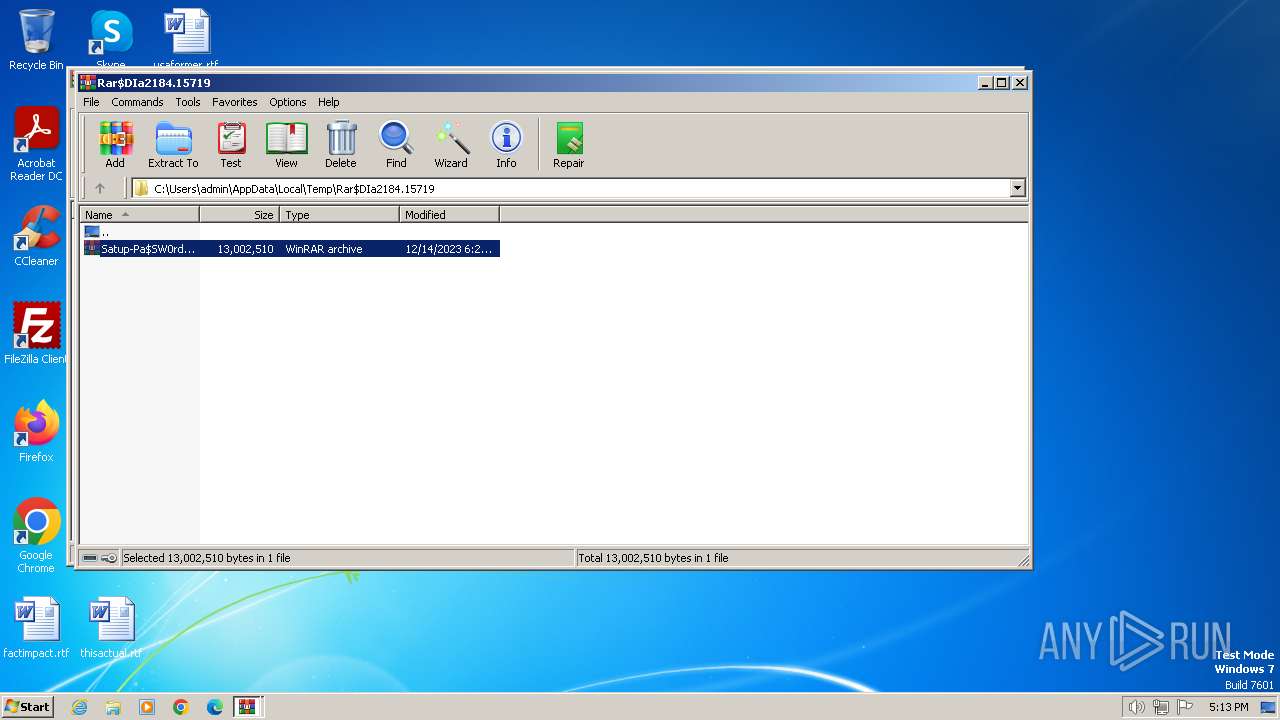
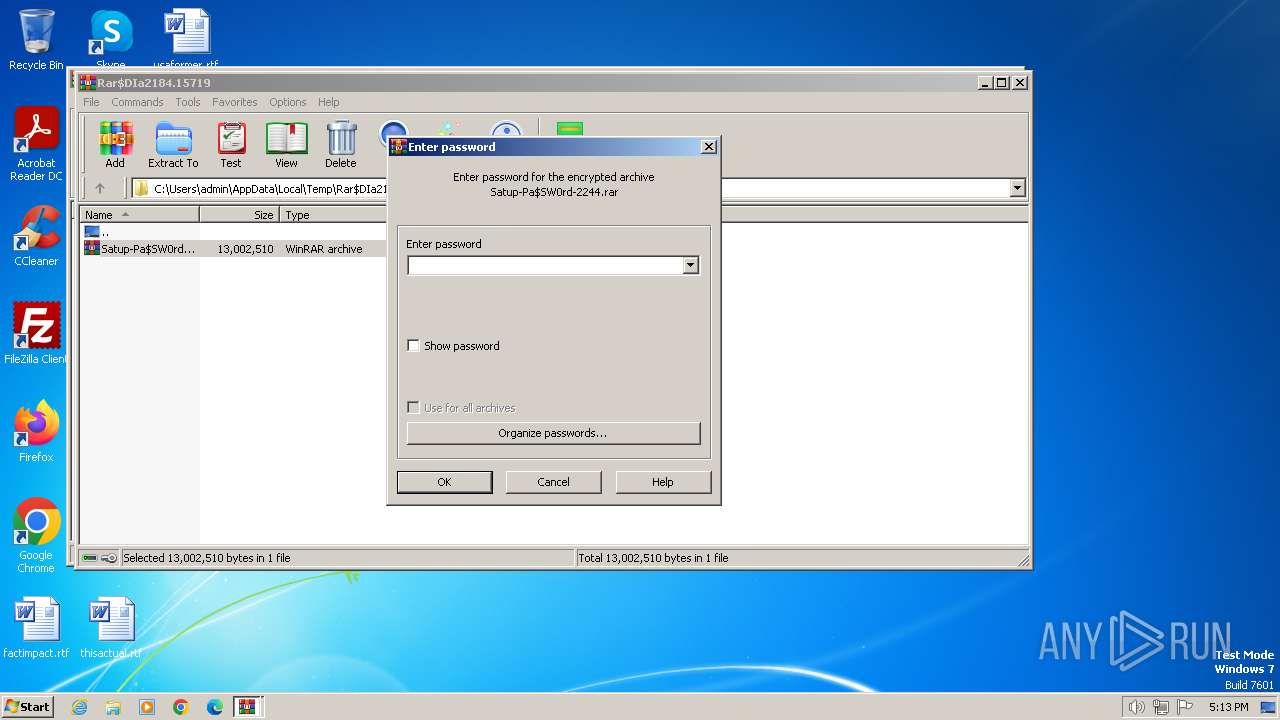
| 2068 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa2184.15719\Satup-Pa$SW0rd-2244.rar | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\!@#Satup-Pa$SW0rd-2244.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2312 | schtasks /create /tn \Service\Data /tr """"C:\Users\admin\AppData\Roaming\ServiceData\Rukevar.exe""" """C:\Users\admin\AppData\Roaming\ServiceData\Rukevar.jpg"""" /st 00:01 /du 9800:19 /sc once /ri 1 /f | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 806
Read events
2 723
Write events
83
Delete events
0
Modification events
| (PID) Process: | (2184) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (2184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
3
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2184 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2184.15719\Satup-Pa$SW0rd-2244.rar | — | |
MD5:— | SHA256:— | |||
| 2068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2068.16754\Main__App.exe | — | |
MD5:— | SHA256:— | |||
| 2068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2068.16754\ICQLiteShell.dll | executable | |
MD5:05E61539B8917FCA37C03756BBDD043D | SHA256:515C8E0B93F0FEF15DA3E2573AD92B7E7840374140E65E5D73DF63D8E22CB3E8 | |||
| 2068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2068.16754\LiteSkinUtils.dll | executable | |
MD5:059D94E8944ECA4056E92D60F7044F14 | SHA256:9FA7CACB5730FAACC2B17D735C45EE1370130D863C3366D08EC013AFE648BFA6 | |||
| 492 | Main__App.exe | C:\Users\admin\AppData\Roaming\ServiceData\Rukevar.exe | executable | |
MD5:0ADB9B817F1DF7807576C2D7068DD931 | SHA256:98E4F904F7DE1644E519D09371B8AFCBBF40FF3BD56D76CE4DF48479A4AB884B | |||
| 2068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2068.16754\bentonite.cfg | image | |
MD5:E7C43DC3EC4360374043B872F934EC9E | SHA256:658AC17F4047CCC594EDFD7C038701FE2C72EC2EDF4AEFE6F3C2DD28AB3DD471 | |||
| 2068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2068.16754\Important Note.txt | text | |
MD5:866EF3EF86ABE30168D0A9569DCDEE4E | SHA256:C11F512628253406BE49F3AD7D3E6C9E0DB6D6770146EF8678E465B699D1FDA6 | |||
| 492 | Main__App.exe | C:\Users\admin\AppData\Roaming\ServiceData\Rukevar.jpg | text | |
MD5:DA64D3CA3C1FCD76F0576005E51B34B3 | SHA256:C4A11017008B380E5C47B521CEB2C1F65F39A31B2E62782A6FA9BCEACF91071E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
2
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
qsone1pt.top |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |