| File name: | 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader |
| Full analysis: | https://app.any.run/tasks/ca9c2c6b-925a-4dee-8716-e5733595e458 |
| Verdict: | Malicious activity |
| Analysis date: | April 28, 2025, 09:31:17 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 0B76E370DCB86E4DE5FC9F002F46F1E9 |
| SHA1: | 1049E6587D08A5AA6D63EA2912A8FB68FDBEFECF |
| SHA256: | 72183AEF3E0047EFA93CE1D436234C0421A2518B6E27277CB54ED6ED49CD2901 |
| SSDEEP: | 98304:iefUuZuKAuf5jTFekOefUuZuKAuf5jTFrkHVrGDYwOwjefUuZuKAuf5jTFPkOefq:wwgnElnS |
MALICIOUS
Executing a file with an untrusted certificate
- 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader~4.exe (PID: 960)
Starts NET.EXE for service management
- cmd.exe (PID: 6108)
- cmd.exe (PID: 3240)
- cmd.exe (PID: 5112)
- cmd.exe (PID: 728)
- net.exe (PID: 7276)
- cmd.exe (PID: 5868)
- net.exe (PID: 7380)
- net.exe (PID: 7340)
- net.exe (PID: 7400)
- net.exe (PID: 7368)
Uses NET.EXE to stop Windows Update service
- cmd.exe (PID: 5868)
- net.exe (PID: 7340)
Uses NET.EXE to stop Windows Security Center service
- cmd.exe (PID: 5112)
- net.exe (PID: 7380)
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 2392)
- net.exe (PID: 7408)
Starts NET.EXE to view/change users localgroup
- cmd.exe (PID: 4920)
- net.exe (PID: 7332)
SUSPICIOUS
Starts a Microsoft application from unusual location
- 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe (PID: 5576)
- 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader~4.exe (PID: 960)
- 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe (PID: 5512)
Executing commands from a ".bat" file
- 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe (PID: 5512)
- UpdatAuto.exe (PID: 920)
Process drops legitimate windows executable
- 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe (PID: 5512)
- UpdatAuto.exe (PID: 920)
Starts CMD.EXE for commands execution
- UpdatAuto.exe (PID: 920)
- 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe (PID: 5512)
Creates file in the systems drive root
- UpdatAuto.exe (PID: 920)
- 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe (PID: 5512)
Executable content was dropped or overwritten
- 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe (PID: 5512)
- UpdatAuto.exe (PID: 920)
Windows service management via SC.EXE
- sc.exe (PID: 4424)
- sc.exe (PID: 5776)
- sc.exe (PID: 672)
- sc.exe (PID: 664)
- sc.exe (PID: 5280)
Starts itself from another location
- 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe (PID: 5512)
INFO
The sample compiled with chinese language support
- 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe (PID: 5512)
- UpdatAuto.exe (PID: 920)
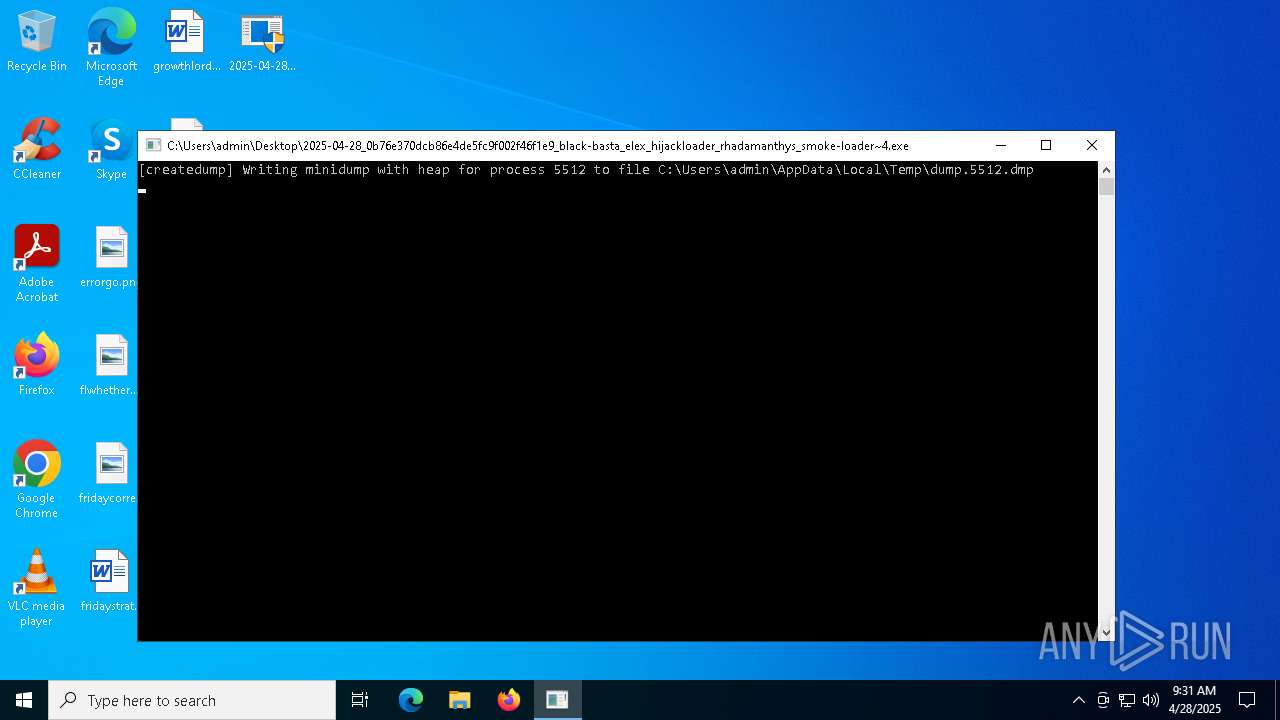
Create files in a temporary directory
- UpdatAuto.exe (PID: 920)
- 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader~4.exe (PID: 960)
- 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe (PID: 5512)
Checks supported languages
- 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader~4.exe (PID: 960)
- 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe (PID: 5512)
- UpdatAuto.exe (PID: 920)
Creates files in the program directory
- UpdatAuto.exe (PID: 920)
- 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe (PID: 5512)
Reads Environment values
- 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader~4.exe (PID: 960)
Reads the computer name
- UpdatAuto.exe (PID: 920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (48.2) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (24.4) |
| .exe | | | Win32 Executable MS Visual C++ (generic) (18.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.8) |
| .exe | | | Win32 Executable (generic) (2.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:03:12 04:30:52+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 102400 |
| InitializedDataSize: | 16384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x27dc |
| OSVersion: | 4 |
| ImageVersion: | 6.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.1.0.0 |
| ProductVersionNumber: | 6.1.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| Comments: | Windows Update Manager for NT |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Windows Update Manager for NT |
| LegalCopyright: | Copyright (C) Microsoft Corp. 1981-1999 |
| ProductName: | Microsoft(R) Windows (R) 2000 Operating System |
| FileVersion: | 6.01 |
| ProductVersion: | 6.01 |
| InternalName: | INCUBUS |
| OriginalFileName: | INCUBUS.exe |
Total processes
176
Monitored processes
48
Malicious processes
4
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | sc config wscsvc start= disabled | C:\Windows\SysWOW64\sc.exe | — | 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 5 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | sc config SharedAccess start= disabled | C:\Windows\SysWOW64\sc.exe | — | 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | cmd.exe /c net stop srservice | C:\Windows\SysWOW64\cmd.exe | — | 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | C:\WINDOWS\system32\UpdatAuto.exe | C:\Windows\SysWOW64\UpdatAuto.exe | 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Manager for NT Version: 6.01 Modules
| |||||||||||||||
| 960 | 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader~4.exe | C:\Users\admin\Desktop\2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader~4.exe | — | 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Runtime Crash Dump Generator Exit code: 0 Version: 7,0,1624,6629 @Commit: 567edafe6106e6b769c64f6a2ed876190baa Modules
| |||||||||||||||
| 1056 | C:\WINDOWS\system32\cmd.exe /c C:\WINDOWS\system32\Option.bat | C:\Windows\SysWOW64\cmd.exe | — | UpdatAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1672 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1764 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
851
Read events
851
Write events
0
Delete events
0
Modification events
Executable files
19
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 960 | 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader~4.exe | C:\Users\admin\AppData\Local\Temp\dump.5512.dmp | — | |
MD5:— | SHA256:— | |||
| 920 | UpdatAuto.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrobat_sl.exe | executable | |
MD5:5757C5EB2E7E81161BDB719C196AD3B5 | SHA256:0C7200EF8B141DF4B897AA67E45D5D11171DF82D382962C4BD055855E80C2F34 | |||
| 5512 | 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\AdobeCollabSync.exe | — | |
MD5:— | SHA256:— | |||
| 5512 | 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\CRLogTransport.exe | — | |
MD5:— | SHA256:— | |||
| 5512 | 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\CRWindowsClientService.exe | — | |
MD5:— | SHA256:— | |||
| 920 | UpdatAuto.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\AcrobatInfo.exe | executable | |
MD5:7E405810A30EB353957ECB69758435EE | SHA256:7950A9F3AF93AFF61119B416F45A4AB39F44535B4238318C5AE4B9197FAADEFF | |||
| 5512 | 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe | C:\ntldr~6 | executable | |
MD5:2F0EC14625D1EEE22ED3E3E12202E8A3 | SHA256:A33462822E4BF756D828D04AC4B5EB8FE6C06250C21A6917D41BB0EE544DEABC | |||
| 5512 | 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe | C:\ntldr~8 | executable | |
MD5:2F0EC14625D1EEE22ED3E3E12202E8A3 | SHA256:A33462822E4BF756D828D04AC4B5EB8FE6C06250C21A6917D41BB0EE544DEABC | |||
| 5512 | 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe | C:\Windows\SysWOW64\UpdatAuto.exe | executable | |
MD5:2F0EC14625D1EEE22ED3E3E12202E8A3 | SHA256:A33462822E4BF756D828D04AC4B5EB8FE6C06250C21A6917D41BB0EE544DEABC | |||
| 5512 | 2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader.exe | C:\Users\admin\Desktop\2025-04-28_0b76e370dcb86e4de5fc9f002f46f1e9_black-basta_elex_hijackloader_rhadamanthys_smoke-loader~4.exe | executable | |
MD5:317441D7B34C31832B3312357E8A9E95 | SHA256:EE7BAC4F48EEC0DE4C0146ACCE4985A4DB71B3DE38DAD6DC9B921815A3B40124 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
20
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.216.77.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 23.216.77.18:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5728 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |