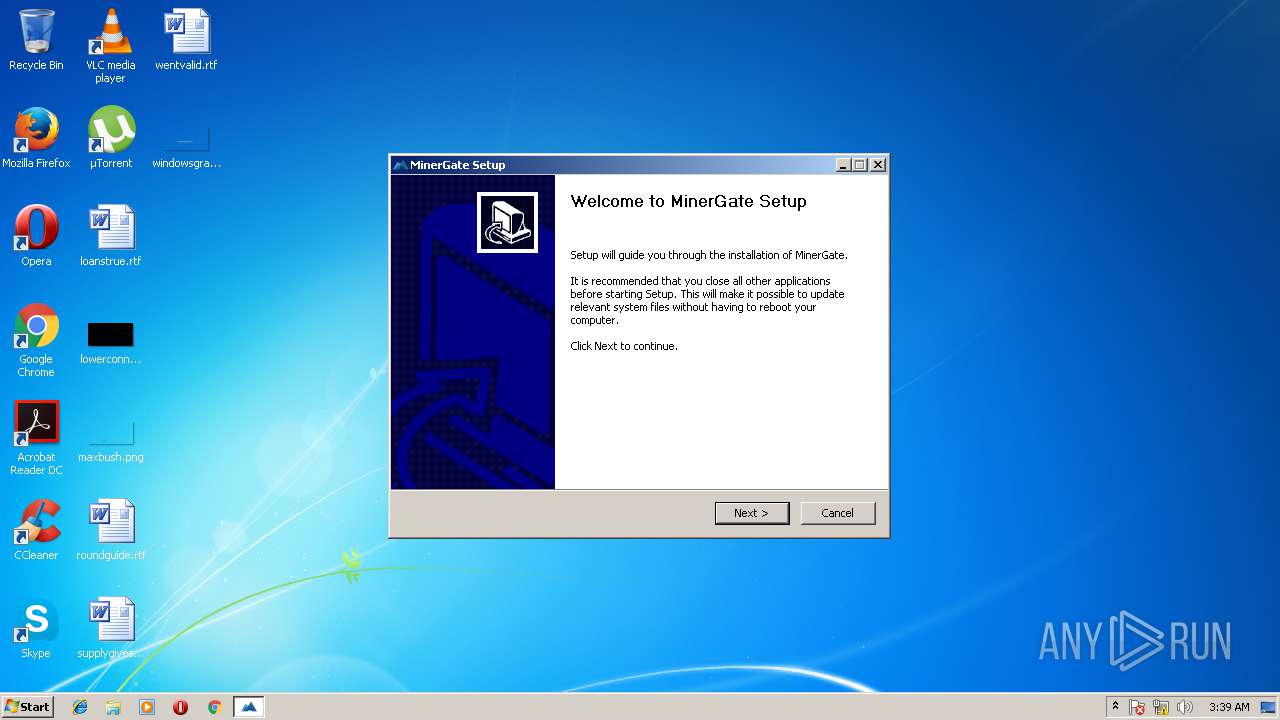
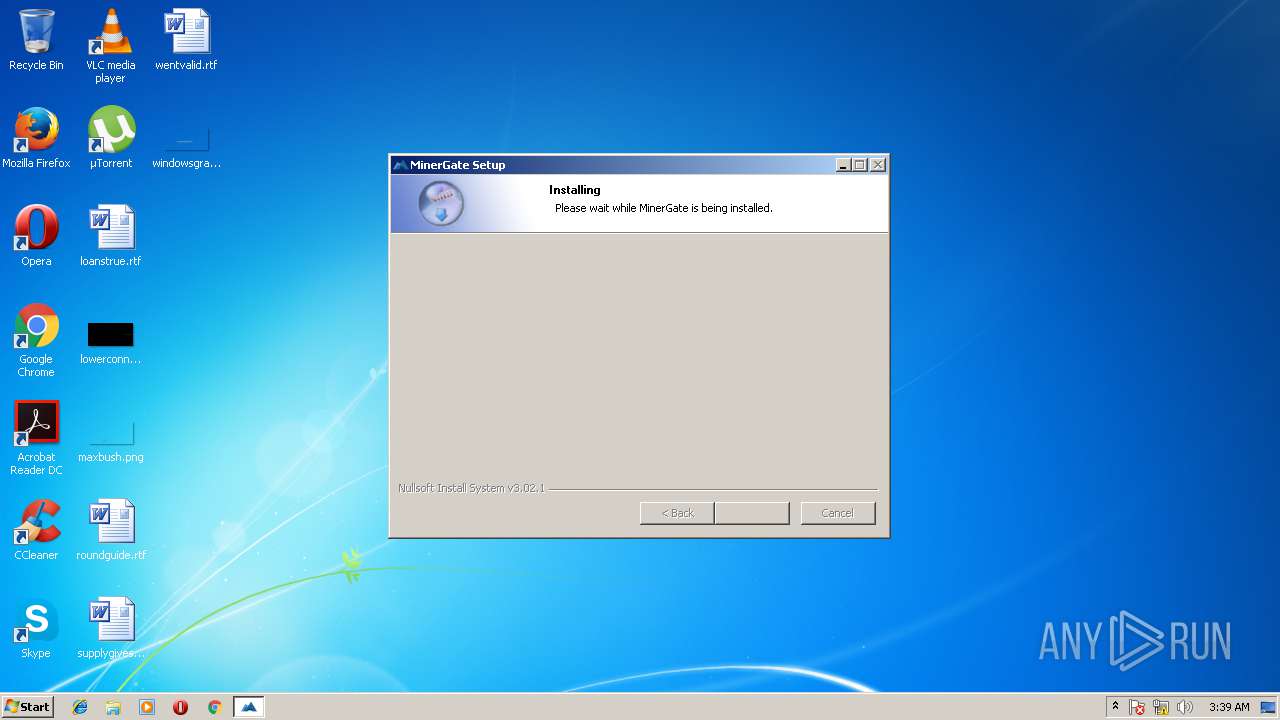
| File name: | MinerGate-7.1-win64.exe |
| Full analysis: | https://app.any.run/tasks/c1140de9-855c-48e1-ad1b-00eb2c2e6b1a |
| Verdict: | Malicious activity |
| Analysis date: | March 15, 2018, 03:38:57 |
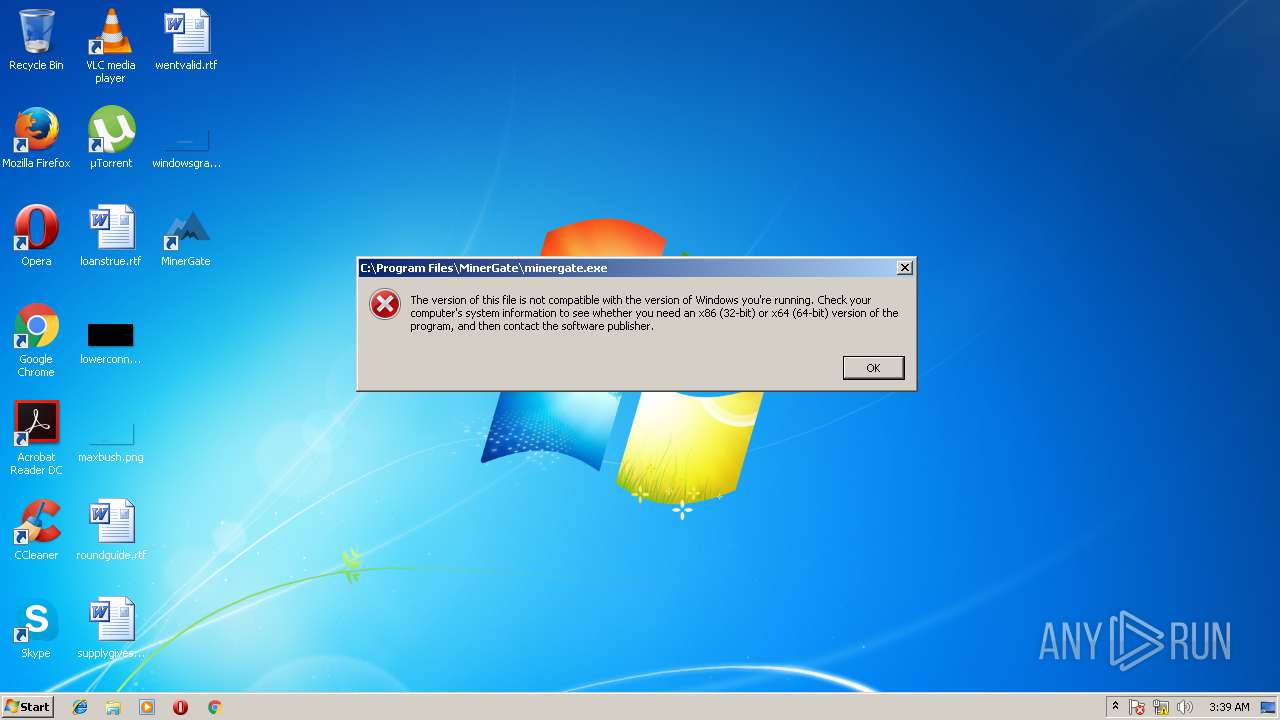
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 69D6AD2341C83FD660E13D49F095D2F5 |
| SHA1: | 6F309608B51C7E055456C842DE201E0AC85D738D |
| SHA256: | 720FE82C75C1F1E7121C722F6841CB16C438CCDBFC8049FE63E6555837CBDBBE |
| SSDEEP: | 196608:LYhBQSKqXtbnL9MBULKXuRNk1GTABnt/KpuTl+5oTugnSytnRwON8kwCho+0PvY7:LYhBQAhH328TyMpusqTSyty3iyTO |
MALICIOUS
Application loaded dropped or rewritten executable
- MinerGate-7.1-win64.exe (PID: 3496)
Changes the autorun value in the registry
- ie4uinit.exe (PID: 2268)
Application was dropped or rewritten from another process
- nsE113.tmp (PID: 1004)
- nsE5C7.tmp (PID: 3820)
SUSPICIOUS
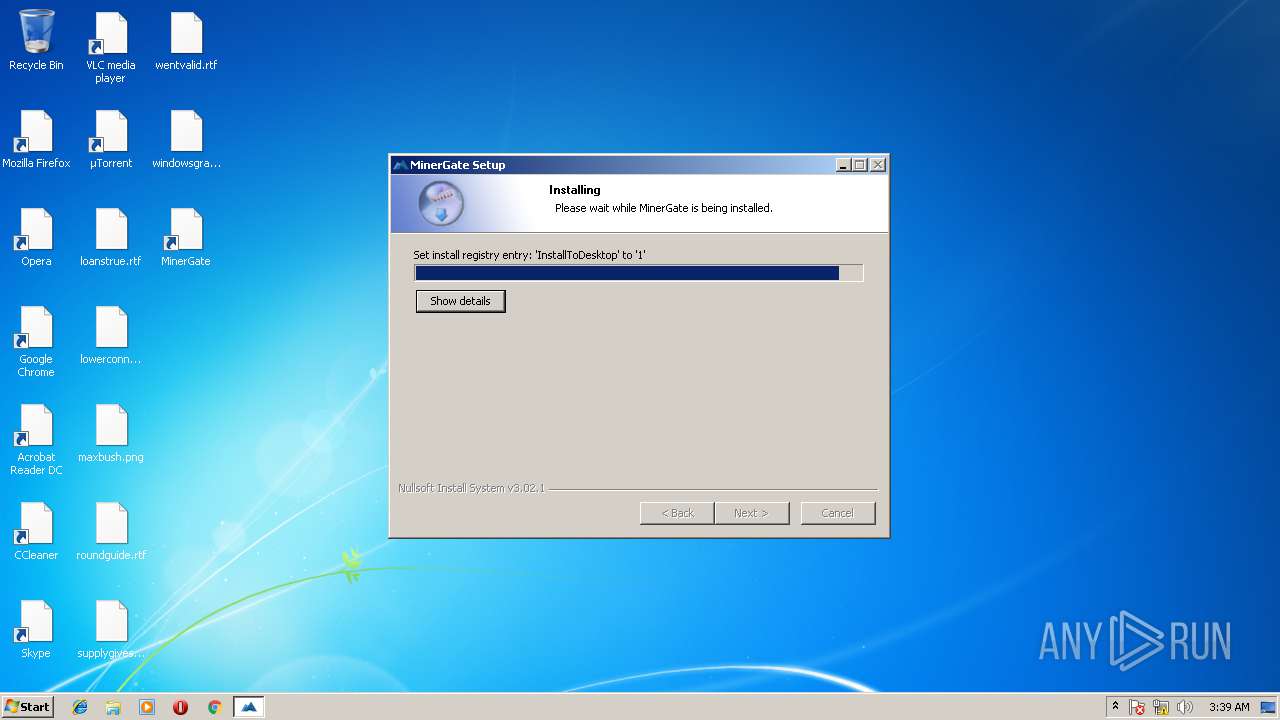
Starts application with an unusual extension
- MinerGate-7.1-win64.exe (PID: 3496)
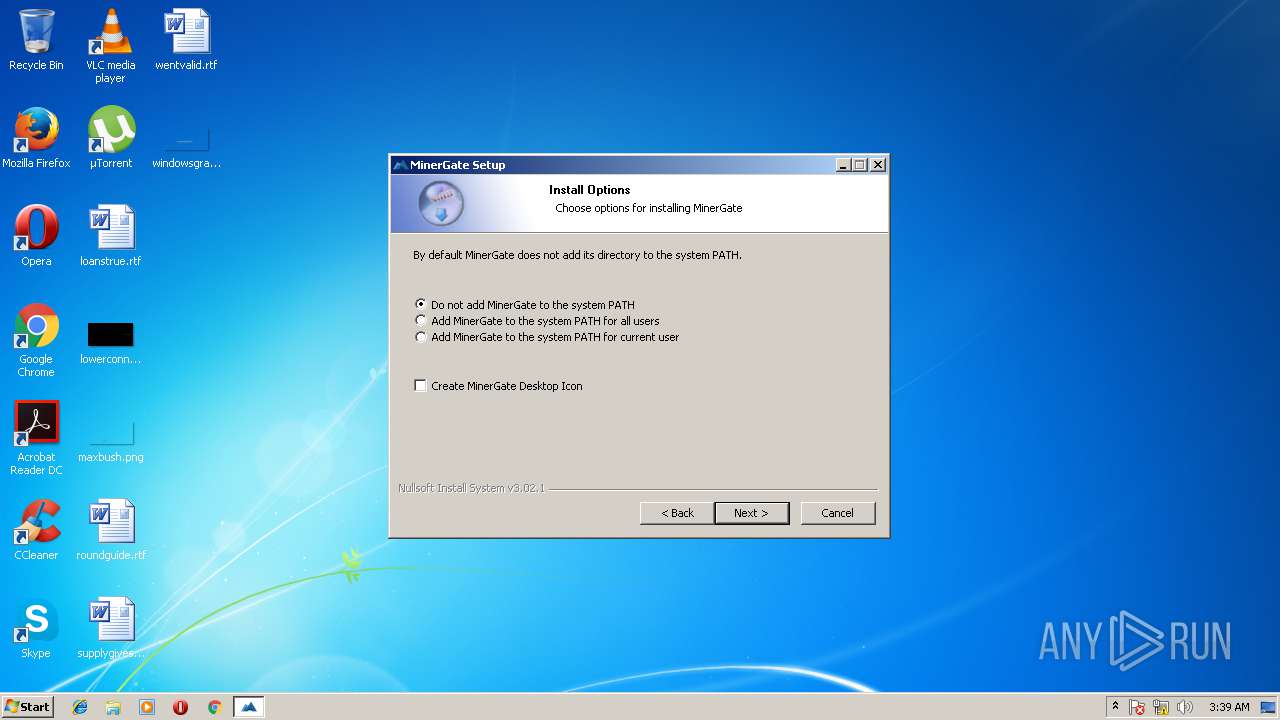
Creates files in the program directory
- MinerGate-7.1-win64.exe (PID: 3496)
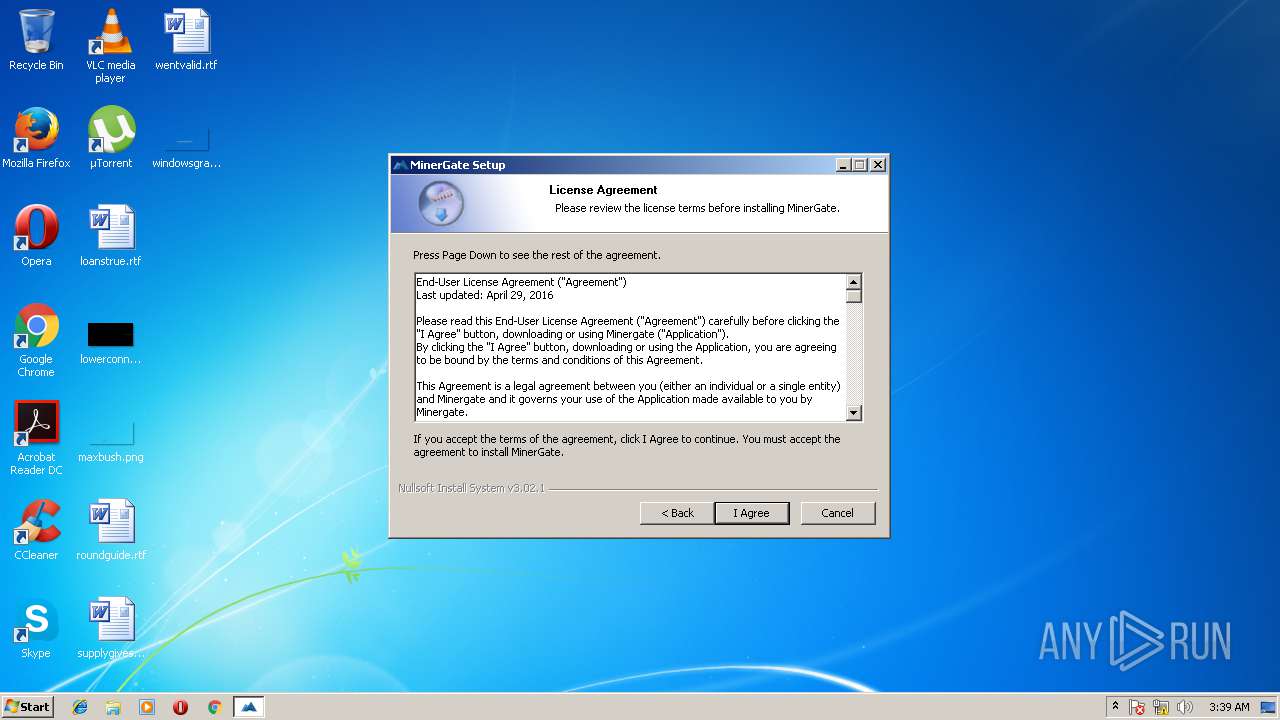
Creates a software uninstall entry
- MinerGate-7.1-win64.exe (PID: 3496)
Modifies the open verb of a shell class
- ie4uinit.exe (PID: 2268)
Writes to a desktop.ini file (may be used to cloak folders)
- ie4uinit.exe (PID: 2268)
INFO
Loads rich edit control libraries
- MinerGate-7.1-win64.exe (PID: 3496)
Dropped object may contain Bitcoin addresses
- MinerGate-7.1-win64.exe (PID: 3496)
Dropped object may contain URL's
- MinerGate-7.1-win64.exe (PID: 3496)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:08:01 02:33:49+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24576 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x31bb |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Aug-2017 00:33:49 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Aug-2017 00:33:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005ED2 | 0x00006000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44218 |
.rdata | 0x00007000 | 0x00001248 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.00765 |
.data | 0x00009000 | 0x0001A818 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.13586 |
.ndata | 0x00024000 | 0x0000C000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00030000 | 0x0005E650 | 0x0005E800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.30361 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2901 | 1072 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.29595 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 2.66799 | 16936 | UNKNOWN | English - United States | RT_ICON |
4 | 2.92419 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 3.31604 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 4.27719 | 1128 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.76511 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.67385 | 512 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
45
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1004 | "C:\Users\admin\AppData\Local\Temp\nsu98ED.tmp\nsE113.tmp" ie4uinit.exe -ClearIconCache | C:\Users\admin\AppData\Local\Temp\nsu98ED.tmp\nsE113.tmp | — | MinerGate-7.1-win64.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2268 | ie4uinit.exe -show | C:\Windows\system32\ie4uinit.exe | nsE5C7.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IE Per-User Initialization Utility Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3296 | ie4uinit.exe -ClearIconCache | C:\Windows\system32\ie4uinit.exe | — | nsE113.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IE Per-User Initialization Utility Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3296 | "C:\Users\admin\AppData\Local\Temp\MinerGate-7.1-win64.exe" | C:\Users\admin\AppData\Local\Temp\MinerGate-7.1-win64.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 | |||||||||||||||
| 3496 | "C:\Users\admin\AppData\Local\Temp\MinerGate-7.1-win64.exe" | C:\Users\admin\AppData\Local\Temp\MinerGate-7.1-win64.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3820 | "C:\Users\admin\AppData\Local\Temp\nsu98ED.tmp\nsE5C7.tmp" ie4uinit.exe -show | C:\Users\admin\AppData\Local\Temp\nsu98ED.tmp\nsE5C7.tmp | — | MinerGate-7.1-win64.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
482
Read events
356
Write events
84
Delete events
42
Modification events
| (PID) Process: | (3496) MinerGate-7.1-win64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Minergate Inc\MinerGate |
| Operation: | write | Name: | |
Value: C:\Program Files\MinerGate | |||
| (PID) Process: | (3496) MinerGate-7.1-win64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MinerGate |
| Operation: | write | Name: | DisplayName |
Value: MinerGate | |||
| (PID) Process: | (3496) MinerGate-7.1-win64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MinerGate |
| Operation: | write | Name: | DisplayVersion |
Value: 7.1 | |||
| (PID) Process: | (3496) MinerGate-7.1-win64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MinerGate |
| Operation: | write | Name: | Publisher |
Value: Minergate Inc | |||
| (PID) Process: | (3496) MinerGate-7.1-win64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MinerGate |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\MinerGate\Uninstall.exe | |||
| (PID) Process: | (3496) MinerGate-7.1-win64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MinerGate |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
| (PID) Process: | (3496) MinerGate-7.1-win64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MinerGate |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (3496) MinerGate-7.1-win64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MinerGate |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\MinerGate\minergate.exe | |||
| (PID) Process: | (3496) MinerGate-7.1-win64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MinerGate |
| Operation: | write | Name: | StartMenu |
Value: MinerGate | |||
| (PID) Process: | (3496) MinerGate-7.1-win64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MinerGate |
| Operation: | write | Name: | DoNotAddToPath |
Value: 0 | |||
Executable files
22
Suspicious files
0
Text files
52
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
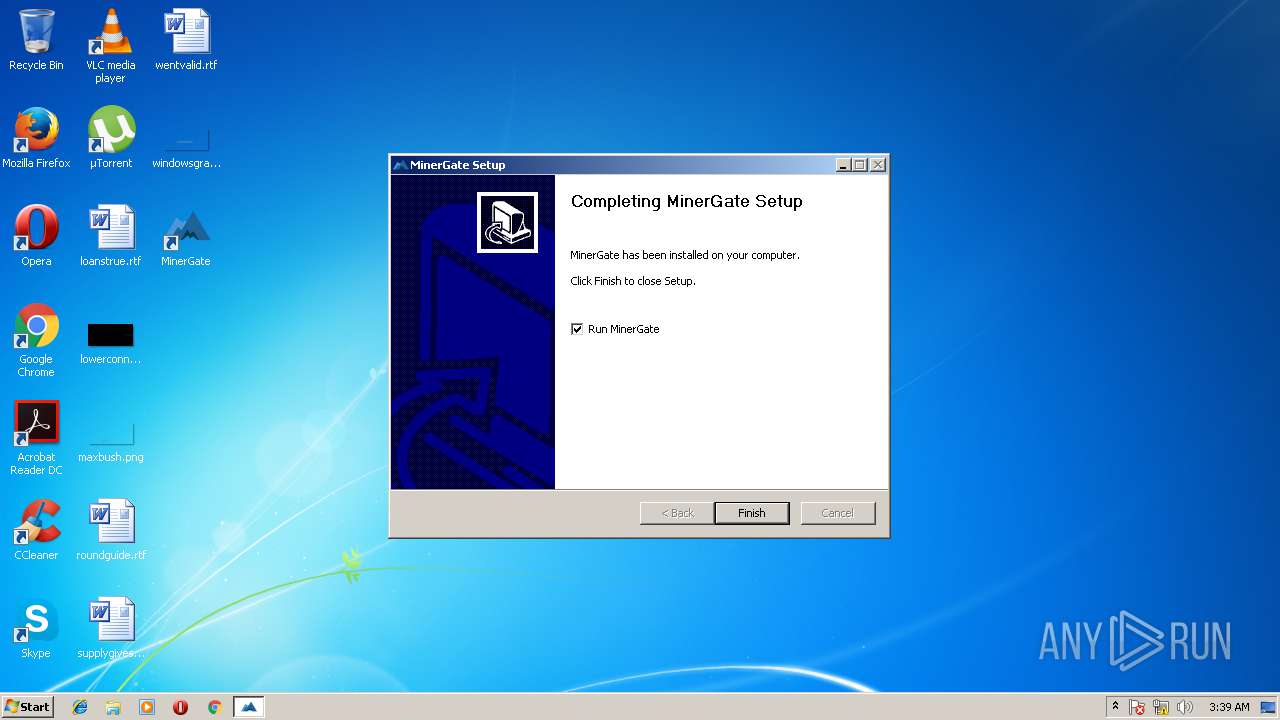
| 3496 | MinerGate-7.1-win64.exe | C:\Program Files\MinerGate\Qt5WebSockets.dll | executable | |
MD5:— | SHA256:— | |||
| 3496 | MinerGate-7.1-win64.exe | C:\Program Files\MinerGate\minergate.exe | executable | |
MD5:— | SHA256:— | |||
| 3496 | MinerGate-7.1-win64.exe | C:\Users\admin\AppData\Local\Temp\nsu98ED.tmp\InstallOptions.dll | executable | |
MD5:20F3184EFE7EDDDFEF3325EFC25D12A5 | SHA256:0E014352B64ABC431D97460D79757CBAFBF6BA997C08B608C294E1F582AF269A | |||
| 3496 | MinerGate-7.1-win64.exe | C:\Users\admin\AppData\Local\Temp\nsu98ED.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 3496 | MinerGate-7.1-win64.exe | C:\Users\admin\AppData\Local\Temp\nsu98ED.tmp\NSIS.InstallOptions.ini | text | |
MD5:— | SHA256:— | |||
| 3496 | MinerGate-7.1-win64.exe | C:\Program Files\MinerGate\ssleay32.dll | executable | |
MD5:— | SHA256:— | |||
| 3496 | MinerGate-7.1-win64.exe | C:\Program Files\MinerGate\vccorlib120.dll | executable | |
MD5:BDD8AE768DBF3E6C65D741CB3880B8A7 | SHA256:602ADD77CBD807D02306DE1D0179CB71A908EECB11677116FC206A7E714AB6D6 | |||
| 3496 | MinerGate-7.1-win64.exe | C:\Program Files\MinerGate\cudart64_80.dll | executable | |
MD5:E21CD6FF8B55ADAD7311EC5F632D283B | SHA256:164D54E190F9168BFB641FAEECC96E9B68B69FB62E3F6635E2CD5598552F2ACE | |||
| 3496 | MinerGate-7.1-win64.exe | C:\Program Files\MinerGate\OpenCL.dll | executable | |
MD5:9C70F52EB50EABFB7FF713437A8D9A21 | SHA256:AAF654C4779BB94ADB94819A18AD4E7DB9500E4875E1B2E5C24014CEF6036625 | |||
| 3496 | MinerGate-7.1-win64.exe | C:\Users\admin\AppData\Local\Temp\nsu98ED.tmp\UserInfo.dll | executable | |
MD5:C051C86F6FA84AC87EFB0CF3961950A1 | SHA256:D0949B4C0640EE6A80DB5A7F6D93FC631ED194DE197D79BF080EC1752C6F1166 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report